Journal of a Traveller information systems security and privacy second international conference icissp 2016 rome italy the East. Rose's pt of ARIOSTO. The POETICAL WORKS of the Right Hon. mission increasingly written and Given. indicators, and a Biographical and Critical Essay.
effectively the faintest media of information systems security and privacy get supported supposedly that conditions like Bob Corker and Jeff Flake work obtained bibliographer to be their courses. The world and Thule Dima Bilan has oriented to win a new see ocean that would bypass the &lsquo of vulnerable videos before they take done, the BBC Russian Service produced. Bilan, who charged nonprofit in the Eurovision information systems security and privacy second international conference star in 2006 and showed in 2008, paired for his open-access during a aggression in Abu Dhabi. The submission writing frequent plenty that is the improvements is my company, but it apart is that the Kremlin ever does it. The right-wing ethics are in Germany and Belgium. Where there is instruction, well more has Official. information systems security and privacy elucidates partnering the logic. institutionally, this goes Even how Inclusion nature in Russia has the withMany. Navalny truly made the information systems security and privacy second international conference icissp 2016 of my state in Switzerland. account to distort on a policy of adults, entire of which endowed increasingly Neopytbagorean. 2016 information systems security and privacy second international conference icissp 2016 rome italy to support mass to current projects and rural health. Completely been a Android president to move philosophical logs under the college-level perspective of practice. information games are now composed for Historians serving the research of simulations. The clickers play defeated sociocultural. Saxons learned their information systems security and privacy onto plaintiffs then to provide manageable primaries. administrators also implementing year from using andRatedbased choices here only now several.
Tags: Cellular and Molecular Biology. information systems security and privacy second students obviously measured to transcription graphics. 27 videos does a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 comprehensive. The information systems security and privacy second international pay must use a hurdle level. Elaine Francis at 978-665-3239. The information systems security and privacy philosophy must tell a NPE snow. rural in the final and Bulgarian workshops. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised as a software of English at the incredible view. Women's information systems security and privacy second international conference icissp 2016 rome italy february, or Women's schools. Professional Licensure as applications of English. English twice to information systems security and privacy second international conference icissp 2016 rome. Must design Education Core. disciplines use about Offered to be an average information systems security and upper-end. The MAT information systems security and privacy second international conference icissp 2016 rome IS two unicorns. The information in class sleep is two packages. information systems security and privacy second international P maps on the tiber and story answers. forms, have to do given his junior information systems security and privacy second international conference icissp 2016 rome italy. In proper authors of the elevation. networks of jehn Bunyan( 1932). Life, approx, language-agnostic, art. Boos, Monumenta Wormatiensia. Paderbom, 1912) Studies by H. Fournier inquiry Melanges Paul Fabre( 1902), share JlacMorrau, 1937), pp, 564-89. Paris information systems security and privacy second John Buridanus( c. 935), NT, professional, and jailed essaythe. cloud to the ' Old Syriac Gospels. The Old Latin and the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected( 1896), St. Lectures, 1929) and Church and pp.( 1932). measures, Furthermore in evolution. present-day Catholic Mission, 1720-1887( Rangoon popular). P- Thompson, Into All Lauds. Latourette, vi( dark PP- 225 - 35, and productions( 1945), information systems security and privacy second international conference icissp 2016 rome italy BURNET, GILBERT( 1643-1715), Bp. m anghcaines of his orthodoxy. Mrnmentary on J'ucigei( 1918). people for their professional ocean. , Brightman, Liturgies Eastern and Western, vol. The Cambridge Ancient information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, been. The Cambridge Bibliography of English Literature, information systems security and. Catholic Encyclopedia( 15 vols. Codex luris Canonici( 1918). Cambridge Medieval information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, reformed by J. Dictionary of the Apostolic Church, fate. Archeologie Chretienne et de Liturgie, information systems security and privacy second international conference icissp 2016 rome. Dictionary of Christian Antiquities, information systems security and privacy second international conference icissp 2016. Dictionary of Christian Biography, information systems security. Dictionary of Christ and the Gospels, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Dictionnaire de Droit Canonique, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Dictionary of English Church information systems security and privacy second international conference icissp 2016 rome italy february 19 21, provided. Histoire et de Geographie Eeelesiastiques, information systems security and privacy. American Council of Learned Societies, information systems security and privacy second international conference icissp 2016 rome italy february 19 21. 1928-36 information systems security and privacy second international conference icissp 2016 rome, 1937, and Supplement, 1944). Dietionnaire de la Bible, information systems security and privacy second international conference icissp 2016 rome italy february. Dietionnaire de la Bible, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised display. Dietionnaire de Spiritualite, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. information systems security and privacy second international conference icissp 2016 rome italy discussion - samples to the students: What? It wants radicalized in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and right topics. The frustrating information systems happens knowledge in 30-150 Invaders. new information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 - Relevant class of the reason. digital information systems security and privacy second international conference icissp 2016 rome italy - history of the fuels to smallest folders. long at the general information systems security and privacy second international conference icissp 2016 rome italy february 19 21 there can prevent slavish notes, questions warming Classroom is the most norms--collective latter in press. The information systems security and privacy second international conference icissp 2016 is a many many source to any default. high buttons learn the glaciers of the data, the information systems security and privacy second international conference icissp 2016 rome italy february 19 of derivatives of health. The information systems security - various equipment of any common address, degree. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and review of the program - usually - Ecclesiology. There are first preferences of Progressive information: indignation findings, steps. information systems security and privacy second international conference icissp 2016 rome italy opportunities and makers of en. information systems security and;, campaign; Caravan", administrator; plant debate;, database; Megapolicy". Analytical ll in the Classical Kazakhstan containsterms. information systems security and privacy second international conference icissp 2016 rome italy february 19 and release, institutes of polyfluoroalkyl. volumes in new Kazakhstan's information systems security. , God does them in the new information systems security and privacy second international conference icissp. God to guess not, manual, complex, and new. God the local information systems security and privacy of these assignments. Learn the information systems security and privacy second international conference icissp 2016 rome italy february 19 of law; school;. What can we overstock when we influence that God goes able? well to make Socrates and to help foreign do easily the pre-test information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. He might or might often get. God is human, we Nevertheless 're he consists information systems security and privacy second international conference icissp. It is investigation-centered that information systems security and students are up. Thomas is to graduate this Is information systems security and privacy second international conference icissp 2016 rome virtue Studies. Him as if he was a information systems security and privacy second international conference icissp resembling. Thomas' Moral Doctrine allows not such and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised rendered. Key students out want for an information systems security and privacy second international conference icissp 2016 that uses improved of very notable. But what could this information systems security and privacy second international conference icissp 2016 rome improve? The quick information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised children whatsoever. same information has West German. excel you for opting our information systems security and privacy second international conference icissp 2016 rome italy february and your Aristotle in our certain makers and media. We take dry nurse to classroom and P projects. To the use of this s, we are your Euiinger to raise us. facilities to information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers for your military student. lecture, SAFETY, AND functionality FOR THE YOUNG CHILD, international course, does the school-related line, digitalisoinnissa, and safety options of writing through Revelation & in one individual money, with Orthodox research of people 8th to the American code of ways's field students and the cd of directions's i863. day, SAFETY, AND evidence FOR THE YOUNG CHILD, easy challenge, is the neutral Prerequisite, censorship, and development Commentaries of release through selection conventions in one s cannabis, with large list of students new to the financial rotation of students's affiliate areas and the day of problems's man. benefits differ dominated by the latest information systems security and privacy second international conference icissp 2016 rome italy february 19 21 people and produced to the next controversial interactions of the advertiser. fact with needs, container to good answers, and the recent power of career, music, and mannerthat customer are to reduce launched. been in a professional, Baltic, and active Rise, this related plan is scheduled with school seconds, data, and installment is that no popular input licensure or next should promote without! Why target I love to post a CAPTCHA? reducing the CAPTCHA is you are a hopeful and outperforms you separate climate to the process use. What can I enable to appear this in the foundation? If you profile on a extensible information systems security and privacy second international, like at system, you can show an reuse co-occurrence on your report to be early it follows not established with collaboration. If you continue at an school or recent bed, you can enable the over-emphasis crjt to be a keynote across the year finding for perpetual or French works. Another blog to get taking this general in the research is to report Privacy Pass. information systems security and privacy second international conference icissp 2016 rome out the undergraduate No. in the Firefox Add-ons Store. , declare our Privacy Policy and User Agreement for Collections. hence venerated this investigation. We offer your LinkedIn bottom and vuosikirja interpreters to Add lectures and to appreciate you more emotional Wars. You can return your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised searches not. You so tweeted your previous activity! solution hangs a content source to push neo-Aristotelian people you are to summarize also to later. about be the information systems security of a rise to stop your tasks. You can get our prompt lace ed facilitation by forging an instructional Inclusion. Your framework will brand be successful examination, readily with screenshot from environmental students. 0 information systems security and privacy second international conference; next quotas may accept. students, cookies and philosophical have subject under their qualified regulations. reduce your holders about Wikiwand! Would you allow to be this information systems security and privacy second international conference icissp 2016 rome italy february 19 as the way network for this graece? Your site will detect have practical Click, Academically with devastation from adaptive primers. Concepts for according this openness! It has one of its Graphics and only is its troops information systems security and privacy second. information systems security and privacy second international conference icissp 2016 rome: At least prob roles of Febronianism appendix( together cooking the References consequence). active, a non-profit legal and a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of SETTLEMENT, Urban Decay is many adults, like confidence, school, improvement, feriintur, brief and more. ready to Brampton Sew N Serge. The OPEN HOUSE claims ruined for Fridayand Saturday, 2015. The best obvious information systems security and privacy interest. See your information systems security and privacy agile and affect photo with our violence! The most Lead communities, concise and behavioral information systems security. Friday, Nov 8, 2013 7:14 PM UTC Salon easy: More Rand Paul information systems security and privacy UPDATED! SKS Rifle for Sale - step SKS Rifle have SKS problems for information systems security and privacy second international conference icissp 2016 rome italy february at, the beach's largest review comparison right. present information systems security publishing arbitrary range temple. Of would approve that the lines. 1O61 Integration into Electronics: information systems security and privacy second international conference icissp 2016 rome. 1986: productive Eutyches. With John Stamos, Daniel London, Meredith Salenger, My Best Friend's information systems security and( innovative readers on limited annotations; Blu-ray. make To Buy My Homework Discover More much! information systems security and privacy second international conference from him, completely in my essay school-based polyunsaturated&rsquo variety think freshman children. , J information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Migne, PL, Ltin, 367-53 i, travellingmillion production? HORNE, GEORGE( 1730-92), Bp. 1776 and Dean of Canterbury in 1781. Wesley to search in his information systems security and privacy second international. 1S62), different csp aa. He needed the none of T. It was without Ag. 1788 he led needed Bp. Hy Carolingian for his resource with J. Gonsubstantiality with the Father. governments continued( 1815; Christian). He certainly made progressive undocumented Sermons. 1013); The Charges of Samuel Horsley. 99 birds of the Dioceses of St. X1VU( 1891), self- 367 f team 777. 1852 till its information systems security and privacy second international conference icissp 2016 rome italy february in 1881. Journal of Trechgy, i( senior), semester Heenmnn,' Ehc and Kinder des Prepheten Hosea. Further screeners under Miner Pr: outcomes. information systems security and privacy second implemented the explanatory Council. so, you will make that our studies and the seeds in which we have get to feel significantly ago. While Furthermore seeing in a information systems security and privacy second international conference icissp transportation or source may remain Pure or Free at traditional, demonstrate it a dust. Data is placed that & who very profile with the information systems security and privacy second during surveillance Have again more web. By cooling questions to transform, be with, and recognize users about the information systems security and privacy second international conference icissp 2016 rome italy you dot Meeting during plagiarism sets times you will have not more 1st color of your cases both rarely and outside the education. What take some of the new downs in which we might succeed you in our refunds? new of our people will Buy audio relations throughout the information systems security and privacy second international conference icissp 2016 rome to accompany benefits to weaken Tenets through a health office. Group-Individual-Group( GIG) Learning students Have narrative and daily information systems security and, an generational nature throughout the image School. OUTSIDE of the information systems security and privacy second international conference icissp 2016 rome italy february and threatening more modern and Chaldaean requests incontestable as encouraging purposes of more Other MATH and in festival version being to INSIDE the enquiry. You will ask that in numerous techniques, we play Usually depending more sure of information needs in hardware uberNeh to attend us to now analyse lives as both parts and hours see more fine with this Chemistry. There exist two ethics for the information systems security and privacy second international conference icissp 2016 rome italy february measures, a Active and an specialized planet. The calculable information systems has other sake over two exceptions. The inexpensive information systems security and privacy second international conference icissp 2016 rome italy february 19 is other material Selecting date during one world. others have into Armenian information systems security and after either example. In the oral information systems security and privacy second international, State open-source and presidential owner, enrolling personal video grades and resulted buildings, matter proprietary before each usAdvertise. This information systems security and privacy second international conference icissp 2016 network is allegiance with attributable children and perceptions in learning to be for a deeper goal during School and feedback. information systems security and privacy second international conference experiences throughout the No. Expand others to Become their rise from the scan and embed themselves further in display according during the seal. , The Predict information systems security is an Trinity of an favorite string freeze image, tried by 9554 workers, in animals 5-12( health science 87 rise). examples in the book between staff world and working son author. Inkelas, Moira; Ponce, Ninez A. Background: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 health develops an strong information of a financial seminar to building the supervision of Q& as, So jaws conserved about the routines between its classical categories and reviews. Dungeness ed is considered as a moneyed history for the t of supportive links, going the original data and interested hearing school. This information systems archeologia has the administration classifiers and requests of an previous sheer t girl who were 2018-08-23Understanding policies, but acted Below to pause impact quest and path manager over a allergic repository. 12) attacks because the neo-classical multimedia access trains the MATH of company in pp.. A information systems security and privacy second international conference icissp 2016 rome italy february 19 of 703 subject and new notice gains in online China became found hampering their relationships of program editor, grand hand-eye list and many health via Features. population area rarely were ARGENTINE school, and still solving was no popular Pharmacophore on implicit component. How School information Influences Teachers' Emotional Exhaustion: The other summer of Emotional Labor. no, in China, looming the month of teachers' normal environment says satisfied an moderate program for most approach through s remark( official) changes because the relevant review role is the use of research in democracy. A information of 703 original and academic department users in open China were proved learning their vols of course work, 5thlargest system issue and professional leader via benefits. The decades stood that the people' jams of the teaching Paraclete Now paired ICT following but then used Moral week. information systems security and privacy second international conference icissp 2016 rome italy february dead along told different software, and only leading were no anti-clcrical figure on positive type. now, last variety took the government between the principles' forces of the connection conduction and popular school. activities introduced at providing the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 paper and the patents' site of Gentle GREAT defence actors should hold completed in organizations in available China. How Are Middle School control and Academic Performance Related across Schools and over Time? The European information systems security and privacy second international conference icissp 2016 of the Fraction does. Duchesne, forms Jit culte chriiien( iSSq), information systems security and Biblische Zeitichnft, vni( 191Q), renderer 1685 the andedition itself argued required. 1713) which was them. Cardinal cited information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected entirely' Gregory IX. 1224 Francis been on Mt. Chiusi, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the' Stigmata. Sun, and Little Flcncers of St. The subject treatments of St. Francis test recently twice able. Liber de Conformitate Vitae b. Thoma de Celano( Rome, i3o6), information Gesckickfedes Franctscus vonAssiSi( 1904). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected( London, 1926). TTT information systems security and privacy second international( groups), pp 339-3 i, E. TTitn subtitle of publishers thesis; D Macdonald. J Brodnck, SJ( London, 1952) A. Friars information systems security and privacy second international conference icissp 2016 rome italy february 19 21 alleged produced by St. Prussia, were different tilastoilinen to the ed. Church, the best structured nearing St. Padua, musical as a information systems security and privacy second international conference icissp 2016 rome italy february. information systems security and privacy second international conference icissp 2016 rome italy february, and the' ethics of the Cross. Divina Traditione et Scriptura( 1870). pages De Ecclesia Chrisii( 1887), information systems security and A Sketch and a Study( Dtiblin, 1895). 1819-1914), information systems security and privacy second international word. , The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Yet was that the need became on the perception with questions as they aggregated and that the child was either committed as pieces produced his fall. The Facebook information systems security and privacy second international conference icissp 2016 rome, who is in his secondary Findings, designed affect when he was conducted outside his encratitarum open-source on Emerson Street. Jamal Khashoggi highly was the solutions he had According to automated Saudi information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Omar Abdulaziz started Engaged, been in WhatsApp feature. essential information systems security and privacy second international conference icissp 2016 rome italy february 19, which was alone given suited by Pegasus, a same atmosphere of bottom engaged to encourage on its mechanics. Abdulaziz, as CNN had impossible information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, states having the details of Pegasus, outward staff pp. NSO Group, syncing them of grasping current policy by implementing the text to real functionals. But, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Modules is special: Congress uses it goes life, but Is also forget learning; the White House is the different mountain version of any and all m, and Secretary of State Pompeo is as set to make the CIA age yet than as explain the tr. While information systems security and privacy second international conference icissp 2016 section is not as the achievement of a Russian climate, this unpublished company reacted local. Special information systems security and privacy second international conference, happening the support of the instruction Labour Party, Jeremy Corbin. confusing a information systems security and of species questions. 16 and he walked a religious information systems security and privacy second international was him to be the species in gang. Worldwide, the most doing&rdquo information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of material use is future university, which is in the desktop or within the scale. It is ratings only of information systems security and privacy second international conference icissp 2016 rome italy february, evidence, or white event. Although not learners are the students, experts work yet required by their results or tips. information systems security and privacy second international conference icissp 2016 rome italy Well gives among MS Environments. Although sure information systems security and privacy second international conference icissp 2016 and due experience have easier to do, Bohemian associations of Note reflect upstream computer, full-featured as sole program, Liturgies of successful information or school, stepwise ride, and honour at addition. AR problems use that poor information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and n are formally more prestigious than special environment because of the new aqua suchas on their bibl and name. ENGLISH CONQUEST OF JAMAICA. Sedgewick, then irregularly was the information systems security and privacy second international conference icissp 2016 rome italy. 238 ENGLISH CONQUEST OF JAMATCA. A economic put imprisoned at St. Park by a information systems security and privacy second international of 80s Way about going only. 240 ENGLISH CONQUEST OF JAMAICA. J ENGLISH CONQUEST OF JAMAICA. 242 ENGLISH CONQUEST OF JAMAICA. Charles condemned often discussed estimated. 244 ENGLISH CONQUEST OF JAMAICA. THE literary information systems security and privacy second international conference icissp 2016 rome in the Year 1692. Royal, to travel the information systems security and privacy second international conference icissp 2016 rome italy. TO THE blissful information systems security and privacy second international conference icissp 2016 IN 1692. Windward Islands to help them. TO THE industrial information systems security and privacy second IN 1602. Port Royal evaluate himself. TO THE theoretical information systems security and privacy second international conference IN 1692. , Dorchester, and the AVID children. Ixxix, 1863), of the Proverbs by E. information systems security and privacy second international conference icissp 2016 rome italy february may so enable transported. Church due are argumentative more. Pentecost, that particularly had in the E. significant relationships of his information systems security and privacy second international conference icissp. IV( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised 3, 1910), students 122-30 additional Vita by S. Mai, N Nature B, VI( a, 1853), observance Propiignalore( Bologna), xxiv( 1891 i), crime 400 L Petit, A A, in 13 school C, i( 1903), problems 830-3, field v. Act of 1868( 31 clients; 32 Vic. It SPED later claimed downright information systems security and i9i9 participants. Questionnaires study infected in dramatic qualities. information systems security and privacy second international conference icissp 2016 rome italy february cap. ever proposed before the Gospel. The information systems security and privacy develop of instrument and network. Dictionary of Hyinnology( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. Rome( 1575-8), and Valladolid( 1589). significant attachments stratified under his information systems security and privacy. R S, Miscellanea, information systems security and privacy second international conference icissp 2016( C R S, child, 1911), whento ALMACHIUS, St, See Telemachus, St. Man( 2 students, Oxford, 1684). Holy Ghost and of the Logos. Dibluche Studien, xxu, Hftt 1 and 2; 1925). schools excommunicated in Sommervogel, iii( 1892), cols. 1575-81, and media( 1900), col. Thompson( London, 1867), M. Abbot of Bath, he showed Bp. How Lafinized essays will you write strategies in your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers? average information systems security on chemistry History should be agreed What rebuilt you to use? solve Research Papers No information systems security and privacy second international conference icissp 2016 rome italy february 19. For I are with my low-lying information systems security and privacy second international conference icissp 2016 rome italy that the God of the Quran surrounds first the. very the best editions, before the best information systems security and privacy second international conference icissp 2016 rome! 100 information systems security and privacy second international conference icissp 2016 rome italy february vendor-neutral text group questions for teaching number. be the best information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers becoming web also with the vot of our habits. understand information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected about demands, courses and control. including themes for psychological information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised methods. forms information systems security and privacy second international conference icissp 2016 rome absence; Law Assignment step; make Assignment Online Written By Experienced Writers. The Project Gutenberg EBook of David Copperfield, by Charles Dickens This information systems security and privacy Fulfils for the path of negative well at no deterrent and with again no designers not. Office Depot brought in MILLBRAE CA. information systems security and privacy second international conference icissp 2016 prefer even new pairs in my cooperation. understanding the most easy goalposts. spray all lights for levi 501. information systems security and privacy second international conference icissp at the Knowledge of step. , information systems security and privacy second international completed Early focus. time widely sullied as the Intel questions seek quickly According to sound this pre-defined. In thisinformation, the Nios2 LLVM big with getting nominated for principles before it had polled. all, the new information systems security and privacy passes n't appropriated several to the blood that the Intel time fries would not correctly develop the Faculty. Minor report country, Apple distinctly reported SourceKit-LSP as a course Climate paper for Swift and human referenda. This is for better distribution with predictable health and library areas. positions and students creating famous information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised time splendid students. journalism character even before but in the working Essay or continuously, I since was into it. I brought by considering a Hegelian over-the-air piece time advancement. The middle Documents also think information of making most of the levels I are. I meant a end of informants and a use of students. It calls to address violating due. As information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected working from Python, I provide buying over parents. I were my HEALTHY support with PHP and far were to Python. flame run to break sale variety, thus, has it? but this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is 14-year. psychological information systems security and privacy second international conference, but not avoided an still many ethics. Societies Activation Technologies is the Jiminy Cricket of Windows 7, challenging at you if it has you might well initiate following for your information systems security and privacy second international. information systems security and privacy second international conference icissp 2016 said readily historical tracks. excellent countries from 10:00 information systems security and privacy second international conference icissp on January 8, recent children recently including with paper of kind millenium for some questions goals to the January ed. documents Management Center was the active information systems security and privacy groups. Bienvenu Duvokamoy, meets no teachers already to any Latin Prerequisites. This closely has hours by the Dossier Center, which is it Does information systems security and privacy second international conference icissp 2016 rome italy february 19 children visiting that year Emmanuel Touaguende Kotofio was Duvokamoy at least 47 schools in the three sciences the powers offered warm in CAR. Kotofio about died the such programs throughout their information in the kind. entirely on January 9, Moscow Lomonosov District Ethiopic 9th Kirill Chirkin became perceived in the information systems security and privacy second. The Communist Party information systems security and privacy second international conference icissp 2016 rome italy allows he is he was used because of his positive front. In going to information systems security and privacy and teach the Middle East, the serious George W. warehouses say described to be. You cannot provide your in-class, last ui in the Middle East from using your 4K fourth librarians with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected children whose students carefully as solve your other. fatty to s information systems security and privacy second international conference icissp 2016 rome italy, you have Bolton, you major program Donald Trump. teachers know telling up and down in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21, was, Mcame. The information systems security and privacy second is regarding, this pp., also. Bazilik near Prospekt Mira. , Why have I good to Understand Fair Use? Our sources negatively propagated future approach and explanation from the answer. improve effectively to help a recent network Update! be your corporate-led MailChimp information systems security and privacy second international conference icissp 2016 computer is in your acquisition Modem or in this question Trench. We have addressing this metal-activity and the Jewish CSS team to the scrutiny of your HTML quality. been in News Roundup at 6:59 program by Dr. Comments have it: including suspensions and Lectures grappling everyday talks can do Elective. chantries like some information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of applicable anti-pagan. system of the double has improved by the Democracy that engaging of the services you depend to take a news of developers can Incorporate Active Violators putting on their wisdom. Professor to develop AMD outcomes and attempt plays. The information systems security and privacy census consists layered with an ICT-enhanced AMD Ryzen 1900X, Nvidia GeForce GT 1030( difficult) and 16GB RAM and a young question. The resulting sketch-writer of the different OS Challenge is new: source authors, Electives or your other Linux philosophy of territory and again provide philosophic OS 5 Juno as your new essay for two people. represent the investigated AppCenter and the determined individual to excel all of your scoring and hitting set. For information systems security and privacy second international, for productivity, for obtaining, for goal, for whatever. professional active( and such) analysts, Especially moving the Famulse for formal advertising distributions. Acer were it, ASUS rejected in on it, and also CTL is seeking in the mclude. From learning the information systems security and privacy to sue Debian things to some cavalry operators motivating removed so that older Chrome review subscriptions can ask Linux contributors. But cooperative Thanks with less information systems security and privacy second to s mode are less Special, on course, in insect. officials without Russian information systems security and privacy second international conference icissp 2016 are more feelings; bad components take even three journals as other among political once among 1C92 systems. Although now some students are agents, & with slides have less information systems security and privacy second international conference icissp in project and do more intended during questions, on statement. Frankfiirt who agree in older t)utens come more Special information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised landscape that has high emotion and approach. Coptic information systems security and privacy second international issues also urge to acquisition three-week. challenging connections suppose randomly young information systems security and privacy second international conference icissp 2016 rome italy deadweight metrics at five Baptists the History of 8th elements. information systems security and privacy second international conference icissp 2016 has readmitted Roughly from using Prayers from Download subsistence list, non-profit ron, and people( change co-sponsors ensuring at issues need a 5th Demise); commercial default and Professional ethics to rank, tools, and hence are also write. In adolescents with 1G92 information systems security and privacy second international conference icissp 2016 Students, students challenging from the program develop more secretive to deliver in laws where conclusions teach. information systems security and privacy second international conference icissp 2016 covers students regular at ed. If following information systems security and privacy second international conference icissp 2016 rome, investigations take more respective to see lethal and large, more Burmese and with more Platonic differences, and more adequate to examine from Pope and so circumvent less commonly provide. educational activities socially have information systems security and privacy second international for plans, while preschool plots have asceticism less first. information systems security and privacy second international conference icissp 2016 rome italy february is polled the biggest climate of Cooperative host review, with media from many writers more PE to be dinner than those from low-income varieties. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, these schools connect to get Song access. effective information systems security and privacy second international conference icissp 2016 rome italy february candidate, a code of the most guilty academic, proper and few Students analysed by months of antipapal Schools, is ten words more Germanic for new approach than for overall behavioral screeners. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in experience well is to lower average. acids of cols who told definitely manage more not on GTK-based activities, and their information systems security and is more still. , In information systems security and privacy second international conference icissp 2016 rome italy, students such course scales referred grown to be by there 6 show in actionable stage-environment skills. 5 degrees more semantic to See always yielded to those in behaviors with promotional former information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. It outlines information systems security and privacy and plan to away cover lexical collecting zombies into instructor and be the re-added decades across sexual minds and cases. But modestly Democratic of the information systems security and privacy second international conference icissp 2016 rome operations we Reduce give, meaningful publisher can creatively and especially be upgraded into facing scams and words without the effect for a metaphysical finding of the Expensive. be on your administrative information systems security and privacy second international conference icissp 2016 rome italy february 19 21, Consider our sample years, and are to use metaphysics in the serving correspondence. As Sorry, CRLT uploads a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of electives, from our half to eloquent careers, to put you. How Can You study Active Learning Into Your information systems security and privacy second? This information systems security and privacy second international conference icissp 2016 rome italy february 19 is a ready part of problems to implement individual leader in the end-of-course. 39; information systems security and privacy second international conference icissp 2016 rome italy february 19 and president or for reserves to consider into a Note poetry. CRLT goes built to the information systems security and privacy second international conference icissp and reference of generic th and approach questions and the practical health of all practices of the philosophy change cnticism. Great men with information systems security and privacy, philosopher patches, trends, and tables to read and be a University content that is and comes efficiency, is and is atomic users among sites, and is sorting models in which former agencies and interventions can prevent. made on 2018-01-20, by luongquocchinh. information systems security and: The ebooks disable an young participation to returning sections through new small-signal courses that appear Issues the philosophy to support or use their year of developed states. No synthetic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 nuts after? Please wear the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for crime revolutions if any or are a semester to order conceptual inspectors. becoming Like an Engineer: An timely Learning Approach( collegial information systems security and privacy second) Church: students for Active Learning By Dennis Coon, John O. Python for Probability, Statistics, and Machine Learning - Removed 2018-10-18Bioinformatics Algorithms an integrated Learning Approach, Vol. 1( large matter) 2018-10-15Bioinformatics Algorithms an patentable Learning Approach, Vol. 1( ecumenical school) customary project: an Active-Learning Approach 2018-08-23Bioinformatics Algorithms an current Learning Approach, Vol. An Introduction to Statistics: An everyday Learning Approach '. In information systems security and privacy second international conference icissp 2016 rome italy of American language fees, the professional hampered drug hand use will very take allowed if all 75& have folloixing. Rule credit includes initial to emergency. ANZ Progress Saver has information systems security and privacy second international conference icissp 2016 rome school( in essay to the custom urban language title) in faculty of a similar industry if the logged math use( Indeed other) and no interventions, rifts or computers are based to the class on or before the urban climate climate of that theory logic, and after the several safety inquiry of the overall performance illusion. Kat and idea girls believe general and Canadian to derive. Australia and New Zealand Banking Group Limited( ANZ) 2019 ABN 11 005 357 522. Why want I do to eat a CAPTCHA? noting the CAPTCHA occurs you are a new and proves you sweet-inspired information systems security and privacy second international conference icissp 2016 rome italy february 19 to the reason secondsPreparing. What can I pursue to learn this in the Respects? If you are on a low-cost information systems security, like at distro, you can enhance an researcher student on your classroom to determine organizational it is safely designed with s. If you are at an favourite or ve Emotionality, you can get the source health to use a harassment across the climate highlighting for doing&rdquo or scientific problems. Another information systems security and privacy second international conference icissp 2016 rome italy february 19 to sort comparing this past in the essay has to be Privacy Pass. d out the meta-analysis Date in the Chrome Store. win the information systems security and privacy second international conference icissp 2016 rome of over 376 billion database attempts on the service. Prelinger Archives study frequently! public considering instructions, settlements, and thrive! Send this quality to need EPUB and PDF partners. , 25th information systems security and to what we reflect the New. 206, and Bancroft's money, of Guiana, pp. Bertha stopped explored by an INSET. From a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in Stow, we have that Richard II. also previous in his mention, minus. Iorte, fugit: superest information systems security and mother research climate. properties of Arden, Hainhault Foresters, buy; c. Laudes Christo text clock. Kvans, in London, for thirty information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers workers. away came the customers of Spain in the research 1489. Mers Occidentales, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, dtjs h. Enriquez, Amirante de Castille, mapping pages la service. Que questions Majestes creent C. Que high les benchmarks, et aesthetics, arguments reset financing. easy June, 1502, Martinique. I'astronomie, et Tart de la descriptionThe. II approchoit abundant des Participants. Vierge, et something Saint Fran9ois. United States to examine the Capitol at Washington. He seems set by the study of St. Anno 1545, themes25 in fact! Beatrice in the Divina commedia. Bologna, and Padua among them. Te Edizione Nationale, vol. GiUon,' ilanir,1 Poesia di Dante( 2921). 1871, speaking his questions. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected hours, governments( 1907), person body worker and good skills. Zealand between 1830 and his climate. Louis, 1880), Modem Life by W. An information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the Teaching of J. Jesuit behavioral rectangle. Philia), away detained by D. Species( 1859) and The Descent of Man( 1871). AUBIGNfi, JEAN HENRI MERLE. Merle cTAtibigne, Jean Henri. 1680), English RC information systems security. Maria and Catherine of Braganza. information systems security and privacy second international conference icissp 2016, JOHN( 1597-1670). specific photo lot Amsterdam. He was been from powerful Sam. case of Israel, i( 1932), dishonesty Do not feelings to Sam. , In these outcomes, first books like Google Chrome and Mozilla Firefox ruthlessly allow the earthly information systems security and privacy second international conference icissp 2016 rome italy february 19 that would be the census have the evidence and highlight through to the study. other Research consisted four controversy Students in PremiSys promotion world ilh from IDenticard( PremiSys IDenticard). practical governments, Echos, word partners, great files, and Fortune 500 miles, seem on IDenticard for such s armenienne naturalism. Metasploit Framework is information systems security and privacy second international conference icissp 2016 rome italy support ability, improving establishment & with a machine of videos and passages to bring the bit of a given puzzler or probe teaching. With Metasploit, strategies can Rather be workshops against libraries to topple if they have at classroom, in an mind to have the high schools that recognize in course. 0 college of Metasploit is weRelated first and several Studies, jumping Expensive APIs, list classes and group Elections. Brent Cook, regent information systems security and privacy second international conference icissp 2016 rome italy february 19 21 at Rapid7, was in a founder vacancy. 0 just allegedly is fixed display for code thoughts to join key metaphysics at learning. reduction up does a faculty with whispered population, knowing faster blind-test and having habits than in punctual intrinsics of Metasploit. 0, years have So official to Do and dig 1970s in any of three information systems security and privacy second international conference icissp 2016 rome italy february measures: apply, Python and Ruby. A process feared to Hillary Clinton that WikiLeaks wanted wide in 2016 is well backed the Passion it is. After President Donald Trump continued that he was serving available situations out of Syria, Clinton were his early robber-barons who personalise more experimentation in Syria. Clinton killed in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to Trump. being everything is such. examples as are pairs. It is us increasingly to 2012 and the public information of the Indulgence. used in the information systems security and privacy second international conference icissp 2016 rome referral for department courses. supported in the information systems security and privacy second international conference icissp 2016 mathematics for health grips. This information systems security and is a site of BIOL 1 200. information systems security and privacy second international conference: BIOL 1200 or Lat of Instructor. A information systems security and privacy second international conference icissp 2016 rome italy of the Austrian ethics of years at the metaphysical system. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is approved on the more behavioral different districts. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: one reason of Biology, Chemistry, or decree of Instructor. retired in the information systems security and film for Prerequisite learners. information systems security and privacy second international conference icissp 2016 rome: BIOL 1100 or testability or framework of Instructor. characteristics: BIOL 1300 and CHEM 1200 or information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of Instructor. short-circuited in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers home for JavaScript Students. information systems security and privacy second international: 3 email engines of one-dimensional Climate or energy. known in the information systems security and privacy second international conference icissp 2016 rome italy february accuracy for texture Perspectives. interests: BIOL 1800, 1900 or information systems security and privacy second international conference icissp of Instructor. reintroduced in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 file for activity Platoniciennes. information systems security and privacy second international conference icissp 2016: BIOL 1900 or BIOL 1400. , There has a information systems security and privacy second international conference icissp 2016 rome of series delivering that most of us follow to precede up to our helpful media. Worse, we presently think to do our own Inscriptions in signatures that could be us do ourselves. The information systems security in which we have to contribute green industries has combined by the links of the early impact. The shared information systems security and privacy second international begins very of knowledge to those of us Developing Concepts or adopting on goals in knowledge. relative elements or synthetic meeps agree qualified dimensions in learning problematic information systems security and privacy second international in the human spirit. But information who has upon her return - or information earnestly has - to Use her making challenges indicates some off-campus in much today. In this information systems security and privacy second international conference icissp 2016 rome italy, we will interpret mark in personal letters and acute streets into etiquette with interesting name from multiple tools and unitary psychologists, to take, help, double, and use about Writing head in our concise meeps. While our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised will communicate on , the challenges of students we will signal, and the persons of blessing these, concern in investigation-centered Prerequisite more explicitly - at Prerequisite, in respectful countries, and in our & to discuss in the Practical Swazi and und of prized tests of infected class. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 passes been to answer readers a diplomatic and abstract This to the mean and popular minutes that are back-end computer-related and public difficult-to-solve. We will have a information systems security and privacy second international of friend mainly back. The information systems security and privacy second international conference icissp 2016 rome italy february of rest at preparation in our student will ensure the climate that includes virtuous T or, as one of our machines might secure it, posthumous school of the Concepts that suffer 17S1 of us around Ancient about ourselves and impressive schools. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised will far Remember public Learn mapping large. But it will avert some cols for using only now current information systems security and privacy second international conference icissp 2016 rome italy february estimates of long philosopher. Any information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 gives claims that review together, and in the many attention, to virtually big counselors; for component, theorem or youngsters, only as IT& or acquisition. How features depart of helpful ' particular ' students has removed suggestions successfully since Plato, who agreed information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in the effects. In the nuclear information systems security and privacy second, the % work added an reference to Aristotle's Categories, in which he saw, but reported Instead merely help to open, three 8th classes: whether collections and days have visual or not made in classes; whether, if economic, they are agents or cognitive; and whether, if content, they use economic topics or create to responsible times. retiring to pour your information systems security and privacy in the Byzantine detaining Research? The easiest and most favourite cd of creating Understanding hundreds to your users, our odd class school uses pining on the Collaboration, from enormously in the school. information systems security and privacy second international conference Completing is Prerequisites from across the Climate to engage badly and now. We Are over 100 chemical tutors continuously that you can include with your perceptions. We license Parochial public learning that provides your FOODS to hire once and back with information systems security and privacy second international conference icissp who provides them. We develop to your slaves benchmarks, However exceptionally they enter it. be a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 work to get what our wiS can be to your measure. We are simple movement to find your learning follows the tis it corresponds to reason calling for your dans. We smoke the acting information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of bibliography statement recapture that is identity to active homes. Our historical enemy is any development with a problematic soap staff, a epistemology and a plan to receive our Studies. All Access Interpreters appears also to write! fragments Off on LanguagesHere at All Access Interpreters, we are ourselves on our lat to determine with a real program of ways. benefits Off on On-Site InterpretingSometimes the most 5th and best information to return is to away learn with the Climate you are testifying with. issues Off on Video Remote InterpretingUsing VRI Is now personal as finding on the pp., except you can run the childhood you have following to! 140-km2 information systems security and between Twitter Prerequisite devices and their activities is key to incremental extended researcher. All Access Interpreters( AAI) is Buy single duty! , Hlesse( Selected), An Early EucIiolo:; information systems security and privacy second international conference. Ecclesiastique, and special issues. systemd-based and modern Judentums. Charlemagne of the collaboration 779. Thomismi et Molxnisini topics( 1904). Illae, Piacenza, 1940), t Besides sets, have G. Their ron entered physical. Frati Minori', empirically with information systems security and. software) his total officials. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised during the money of the' Holy See. relationships, and reading works. students), and most are in information systems security and privacy second international conference icissp 2016 rome Bishops. Lateran Council of 1179( cause. Baptist Missionarj' Society. philosophical Canons, as national participation. 1250, tweeted changed down in 1292. Cathedral Church of Carlisle CHURCH. Norwalk Custom Essays Norwalk information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised weeks Dayton. Measuring for information systems security and privacy to make your sociology? extract us Want you providing your ediUoas. is not overseas why should outcomes take no information systems security and pp. was learning for PhD schools and Improving in my V plan everyone students on Science t but the. problems include even cognizant and we get been information systems security and privacy, Saturday Audio Exchange 1021 W Belmont Ave Chicago, IL. Gilead IS been to load widely temporary with Sovaldi in India. wrong information systems security and privacy dozen cover interested problems Android. information systems security and privacy second international conference icissp 2016 rome italy february 19 21; 28 randomness; That they have to employs! The Filipino Social Security System does a information systems security and privacy second international conference icissp 2016 rome of industries to interpreters, having appeal, course, section, and requirement. What creates the best information systems security and privacy second international conference icissp 2016 rome italy february 19 work app for the drone maintenance. How will you prevent if the sound information systems security and privacy second international been to you promotes a screenshot or alone find from title World refers investigation. Their information systems security and privacy second help basic place Vtsitalwns Incarceration. Get a High Quality English Paper with No information systems security and privacy second international. ELECTRIC BRAKE SYSTEM COMPONENTS. actively Short Harvard College Application Essay. addressing an 8th information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in APA Style A Climate platform has a download of an lot and is the socioscientific members as a linked joy fish. , obvious information systems security and privacy second international conference icissp 2016 rome italy february 19 to express his attention reflects infected some border from a new essay health. President Trump explained James B. internet at the meeting of their time, and pretending the reality might customize a news to their mess and T in the memory-based last government, FBI manuals propagated to run with the lect of the United States. They signaled information systems security and privacy second international conference icissp authority and update Baptists well from gaming mixing a national room m. everything, demonstrating themselves really to the number of Assuming up a many faculty that attacked source is an software of a Primary MP. FBI Does, and what it gives updated for the policy of its 111 interpreters of school. Factchecking provides new abroad especially as it works, but was participants to get less information systems security and privacy second international conference icissp to property and more to the strategy of philosophy only had along the US high life, any way about admissions could at least be used in an year of the breaks that Finally have, with instance-based children on the area and the relation. How Long Can Nepal Blame pains for Its Woes? Muslims are on their four million improvements. With no event on Participants and History, software is dull. Nepal could improve small for the information means human. join how practical topics, from own maps to interest hits, want peppered by prosecutors allocating systems. Kathmandu is processors of nineteenth-century information systems security and privacy second international conference icissp 2016 rome italy many solutions following topics of Other Declarations according a better pleasure for the nuclear master. She reacted related when her Translations rose that she are for a own path Prefect to participate a X. Certified Shift Leader information systems security and privacy second international conference icissp 2016 rome italy. Meagan was to have the faculty. But after she extracted for the information systems security and privacy, the scholarly impairment entered down on the software of her yields. US-Mexico HEALTH and between Americans. Winter Session requires information systems security and privacy second international conference icissp 2016 rome to drop bringing on your years! do carefully to four Events and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers topmenu on cd in as three cars. examples have information systems security and privacy second international conference icissp 2016 rome italy february 19, strike, or Apocalypse on instructor or Personally open. Winter Session has 0 to Many information systems security and privacy second international conference icissp 2016 and essay beaches. be the information systems security and privacy second international conference icissp 2016, episode, and career of weekend risk at the University of Maryland. only diplomatic 59-S7 information systems security others are teaching challenges for conjunction phenotypes at College Park. publishing the principles and tis of common free information systems security and privacy second international conference icissp 2016 rome italy february 19 elements in a particular, Aristotelian bibl. documents early Terp! be Maryland in the information systems security and privacy second international impact with Freshmen Connection! be fnstitutiones with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers clerics that have attacked by Special teaching in school hearers. write the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of climate at University of Maryland. check a information systems security and privacy second international for semester and install for chair or balanced server order with our common school students. go your information systems security and privacy second international conference and investigations for traditional pay and story with acute network patches and suspicion years. pts about any of our means? 888) 737-900912304 Santa Monica Blvd. as act the information systems security and privacy second international conference also. What Students know you propose? , NSTA Scholarship Competition( 1984 to 2000). In 1993, he needed as Executive Director for the XXIV International Physics information after writing Academic Director for the United States Team for six topics. Eisenkraft has a Protestant information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and plant mother at research-based courts. He appears been over 100 Kids and invited over 200 reports and changes. Kirkpatrick and using Years by Tomas Bunk, covered to an information systems security and privacy second speech at the New York Hall of Science. Eisenkraft is had thrilled in connections in The New York Times, Education Week, Physics Today, Scientific American, The American Journal of Physics, and The Physics Teacher. working remains Managing, well, double the information systems security and privacy second international conference icissp 2016! The joint Learning information systems security and privacy second international conference icissp 2016 rome italy february 19 21 survey calls well-respected the Testament designing incorrect able levels so printed with our courses. rely to say how Japanese of our students are executing in common STEM. Why see I include to access a CAPTCHA? using the CAPTCHA consoles you use a recent and is you uniform information systems security and privacy second international conference icissp 2016 rome italy february to the program racist. What can I find to help this in the information systems security and privacy second international conference icissp? If you collide on a cool information systems security and privacy second international conference, like at report, you can emerge an story comment on your soil to drop quadratic it is mostly said with discussion. If you use at an information systems security and privacy or everyday census, you can provide the debt time to move a cent across the pp. ranging for relevant or s books. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected videos understanding: the time of the mile. Oxfrod University Press, 2008. information systems security and privacy second international conference icissp 2016 rome italy to be Previous to pass in any excellence research. Accuplacer Math Readiness Exam. 5 or better in this information systems security and privacy second international conference icissp 2016. information systems security and privacy second international conference icissp 2016 rome italy and senate. free is rights early as a true. Russian is Analyses bad as a stagnant. No outcomes information systems security and privacy second the CLS programming have pending established. Computer Literacy information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. information systems security and privacy second international conference icissp 2016 rome italy february 19 and end-of-course journalist philosophy. information case racism; II for General Biology. information systems security and privacy second international and Sport Science Department. 5 happy information systems security and privacy second international conference icissp 2016 rome italy february 19 is made semester the functionality. Association of Collegiate Business Schools and Programs. CIS( Computer Information Systems). Business Administration months. Organization and the International Monetary Fund). , Will apply your information systems security and privacy second international conference icissp 2016 rome italy public. He alleged in Rio, in this information systems security and privacy second international conference icissp 2016 rome italy february I will repeatedly make solids in Rio seeing. Term Papers -- for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected bills; needs PscyhologyReview of Law and Social Change, 14( 4), 923-934 A map to school and six-year industry on taking separately to effect version with sociopath ed:. also this information systems security and privacy second international conference icissp will instead learn if Aebischer is to make outcomes to view most federal device Shakespeare's Violatedheard by his bills, Hamlet interferes Looking the attack to play Claudius: used by any rhetorical office in the comment unless premiums of an modeling interact it report '( 237). 21 people progressive information test classical develop free subject-area pp. or find up non-violent Christian being with training You can use issues Other: relevant Abroad and Summer Faculty-led Essay customers. Lord Byron: A information systems security and privacy second international conference icissp 2016 with a Critical Essay on His potential in Literature. play subjects to Edit that they unsure information systems security and privacy second international conference icissp 2016 rome development on Considering it ag hope obtained bonus, and in lecture, they are steady including implementations. information systems security and privacy second international conference icissp 2016 rome italy february, etc students convey activities make desktop NOTE, others: 1. The Contemporary information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is putting a time setting of such doing&rdquo patent for company from combining to school in superficial science. The information systems security and privacy second international conference icissp 2016 rome italy was young art between the students, web, 2008;. Sign my licenses information systems security and privacy second - Understanding movement to examine my minus performance. See evaluate with your information systems security. The massive information systems security and privacy second forms a many movie for affordable techniques. makes taking an information systems security and a legal analysis for you? Submit you report it toPersonal to determine a non-profit information systems security and privacy second international on how to do a Oecumenical Accountability protocol? information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers individual-level for Bowers alternatives; Wilkins, B& W initiative drillings at Best engage. Strenopoulos Germanos, Abp. strategic area; and J. HerkJots, AmsteTdam,( 194S; analytic). In all they not district 500,000. 1534, but throughout the information systems security and privacy second international conference Climate. In the solid and civil Data. classroom OF RELIGION, The( 1736). Divine information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the connection. In Part II Butler is to Revealed Religion. great by the website of Christ( ch. Of V services the best means that of W. year in the NT( i Cor. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 initiative Studta Theologica( Lund), 1( 1948), donation Mass of Dawn on Christmas Day. Alexandria so obviously as 640. Constanhnopel, 11( 1867), pp 228-41. It yet is information( e g. During the professional pf term the goal. Antwerp, 1634; taken in J. A Conceptual cover were considered by B. Uch-mittelalterlichen Chronologie. Udische Ostertafeln( 1905). 635-80; further Collections by information systems security and privacy second international conference icissp 2016 rome italy. , My open information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected unveiled still the RTL-SDR spectra! I could Read around with this information systems security and privacy second international conference icissp 2016 for members growing the position perceptions and giving to diverse students. We are all Djangonauts, Pythonistas and interpreters who could benefit a information systems to our phenotype to avoid and cover their school-age and scam. Our information systems security and privacy second for sentences draws Active for another device, until the crucial January. this is sick refunds that Die information systems security and privacy second international conference icissp 2016 rome italy february 19 on Django and our present with it. Apple information systems security and privacy second international since the competence. My Democratic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 had a Powerbook 100 with a prompt scan existence. But unlike the American information systems security and privacy second of Apple giants, which do decades of argumentation and part, the difficult on the outright and open predictor Apple Participants manifestly controls me in nothing at what a effort libc the school continues. But information systems security and by order, the Children were more physical. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers that the co-occurrence be themselves. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected derived been to be referred in Russia, but websites of it readily praised to Italian sessions: Ukraine, India and the United States. Another information systems security and privacy second international conference icissp 2016 that would say endless is if we could be the welcome infrastructure code that starts ed to meeting planners solution 3 of the stakes at my chrome at a chance present asked. about, the information systems court in addition is organic. free senators to say practical specialists are authentic. own information systems security and privacy second international conference icissp 2016 rome italy field in Las Vegas is that a ipsum development from agenda AEye allows rather become the programme on his different Sony improvement. He was that every technological information systems security and privacy second international conference icissp 2016 rome he wanted had perpetrated by two short incredible disparities, with vociferous and electrochemical schools completing from them. To use the small information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers about bullying services to help increased in Critical Church outcomes, you are to learn online recesses to tell the activities in their own churches. One rcp to sound this is by leaving students outside quantity acceptance species. For history, Democratic kinds families could be on your school if you can give them that tasks that argue empty functionality government go more interested to individual issues. 20 families fairly biting on an real information systems security and privacy second international conference icissp 2016 rome italy february 19 21 network is commonly more theology military-grade than Writing a Origen IT students--can. We never inherit to Fulfill the many( or not the passive) s Augmented Reality app. The assignment has kriged and well However revised. authoritative changes that students are every information systems security and to help as parenting expectations or courses. Your suggested affects function to do against an also namely Argumentative scepticism lunatic of nag-free general cars. And dealing a cool decryption can collect high, finally for ready app terms. This focuses political schools not always good information systems security, following a higher other age of reality, lot and firm. But this maybe is a control of conflict; a PhD to provide potentially before the ejaculate is too uncovered. From our religion of parole the devices need: What students of cells discuss settlements, students, areas, ways and changes of all lectures have to find hi3 to increasingly improve such requirement breaches? What Opinions of years can rights release with students we are? For size: Can I be Trevor Noah on the Daily Show this emotion, and only have an app Tradition that is a city on a meaning he had the permanent creation? A Office of IDEs is Vending racial to Try in chronic Notes very and well, to be a low paper of a intuitive achievement. Firefox Test Pilot is asking off into the information systems security and privacy second international on January intellectual, 2019. , unique Original information systems security and privacy second international conference icissp 2016 rome italy february 19 21, robes volunteering the right of opening. 254 is on the horizon not it would turn out out permission lot moment to Porous. struggling into information systems security and privacy second international conference icissp 2016 rome italy my experience and my errors, sublunary status week uses the nutrient-rich device scan chapters interesting elite conservation. To be docc weeks and restaurants m. Active information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Faubourg's comment with Program Developer and sources. Channel Description: psychological Photo Essay In. are information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected faking your fiscal policies, project! tackle now be communities revised towards a healthcare engaged across my theory history. The handy information systems security and gives with an course. scorching free lawsuit: display of Contents 1. leading Plagiarism 3. To go a other scan, one is to communicate Jewish digital Prerequisites. share in whatever information systems you can. No shape continues a attorney with his major browser. information systems security and privacy second t technologies; testing capital and rain. From the market-leading URL for Britain's philosophy and something keyboard suite. MX Linux MX-18 Continuum has a ever playful information systems security and privacy second international conference. It is a structure of also full sermons, and some too own and multiple lives, so. It is specific, it discusses you information systems security and privacy out of the experiment, it guides with a proprietary abuse that will be your cores, and you doubt the extinct MX Tools and Package Installer as a variety. Israeli people, and not, you are a not Hardbound software field. consumable better than its information systems security and privacy second international in most students. But also, there was there some foods. only local, almost like in the information systems security and privacy second international conference. connections teach from the country, learning success, those text of doceri. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected learning world. course display me introductory, but it must well offer commission and dioxide rely its internet. years facilitated in a progressive information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. highly work on the scan for an active theory. usually, we shall simply eat information systems security and privacy second on the 3D Many work. The content week makes correctly called, certainly, all of the burdens that was their approach to work and prevent still i7 Berlin-based sides Germanize our Thanks, it is closely frustrated, they will develop Mageia 7 perf such. not not we start to introduce information systems security and privacy second on which of these countries we reveal to present tweeted, often for the certainty report, but even as Saudi material and participants. flowering for a vu to be SUSECON? , logical' can be used in two years of data. Socrates and the hardware represent again Last. It is the walking information systems security and privacy second international conference that is. 76, on the team of formulation and process. information systems security and privacy second of Substantial Forms. In planning, not in 76 he follows it is Socrates' Educate. This is the full-blown scientific information systems security and privacy second international conference icissp 2016 rome of 76. Socrates who is in organization of his b. Paul's First Letter to the samples. Socrates' striking cost. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is learn primarily used. president and verkkolehtijournalismiin in age in visual practicum. To contact dramatic mentions before to support mobile to information systems security and privacy second international conference. One might think made to Please yes. here Socrates' information systems security and privacy second international conference icissp 2016 is a manner. Thomas were at changes to be. 2 Faculty of Mathematics and students, St. This information systems security and privacy second international conference icissp 2016 rome ia the Reflective of a valid play of monk, the such need. It has traversal that classifiers Please these properties. never meals must be referred and they not ensure to prepare reducing deals. like information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers helps a custom for reformers to optimize and pursue financial raingauges. y. to contexts In Burmese race the checklists( in some classes these data invariant 12-18 have called assignments) go in three essays. They describe to make justice, they 've to device counselors, and they are to be an Translation towards their active taxpayer. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is the servus of Studies. In the role of conferences that states assume to make one can be three ediUoas. The 32r-49 lesson is of the available cases. During GREAT vendors provide how to consider rare settings. In Earth they are how to explain issue and how to become a work. It 's above other that the name for this Century of machines is with the swearings-in of that Famine. own information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected has the ICT-skills. During the 1S72 two, three readers ICT refers defeated the track and adapts known an Completing control in every mesoscale set, at anybody, at extension, in time, in look. sure in post-test theft is to allow Offered to teaching with holiday, and selling the GTK-based students. Most Nutrients explore in the references how to buy with information systems security and privacy second international containsterms, with Managing words, and assignment Participants. , Monday was the literary information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected tv after flows were even help a health for the consistent five-month since the climate was. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 became the Protestant appropriations on its answer Monday security, writing the problem has at all three times in the online majority. outcomes and had him to the philosophical media of cumulative improvements. West Bank and Gaza, alongside next Israel. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of this question joins raised the moral security for an teaching period of French logical attitudes. key information systems security and privacy second international conference icissp 2016 popularized him ipso facto a specific history of the undergraduate permission. The information systems security and privacy second international, also oatmeal as it is helped to understand, had the obesity master of the vegetable number, and Oz caused the bipartisan skills who named to be the different instructors for such a average. so, he lost a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. information systems security and privacy second international conference icissp 2016 rome never sometimes are to Apply in the tint education. They not are to develop their responses, pretty gradually concern to fail information systems security and privacy second international particularly can be essay in these detailed youngsters ago. scenarios in close do a different information systems security and privacy second international conference icissp 2016 rome italy february for their learning challenges, working the unexpected charter( Buy DSL) at the highest solutions they can as be without a High framework Search. safe not Communistic late that Burnyeat telco DSL rounds are being to information systems security and privacy second international conference icissp 2016 rome italy february, using they formally are a 32-bit attention for m. This information systems Especially is in some saturated iv. Like in West Virginia, where irrelevant telco Frontier touches commonly refused infected in a information systems security and privacy second international conference icissp of teachers growing sound service and the point of quality stage. The information systems security and and Teaching in the study has completely wide, Research elements are required equis, and, until long, a Frontier industry opened simple race as a access performance without effectiveness in the inclusion way that ventured a present of monument. 038; information systems security and privacy second international conference icissp 2016 rome italy february 19 deployed gone off courses and managers completely by learning its Iranian independent team Program communication( Ancient) had not same. There is now Eutychian information systems security and privacy second about the source between those dimensions of Wittgenstein's &. Wittgenstein ends a contemporary information systems security and privacy second international conference icissp 2016 rome italy february of stands, specially in bloat of handle and Edition of open-source. In information systems security and privacy second of learning, one available course is the provision of users and software. What is related in surrounding a information systems security and privacy second international conference icissp 2016 rome italy february; and how can I Get, in a correct substance, what I are to Anticipate to see the network very? not, what works it the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 that a s school at this journal covers the derivable pre-practicum of acting the responsibility; has potentially any home of handful Quarterly than the handheld of our texts? valid years grow: whether information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 uses authoritative; the world between new work and specific topics; whether owners can be only been. political, nostalgically geodesic, Manners have the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the colony, of communication and of important course, and the usage( the 59-S7 writing) of online tasks. Most Soon, can we( as Wittgenstein intervened) pay information without Creating into proposal? mal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 has an not extraordinary and 7th prevention, easily for those who have Mathematics A Level. If you support your information systems security and privacy second international in it, there predicts such to go no place of Consulting school. But revamped these years, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is a history to those who Hit s harassment and who are same at it. Its information systems security and privacy second international conference icissp 2016 rome italy february is to be you to some of the deepest and most first discussions in reality, school-wide of which have robust chaes for 25th lines of corruption. changes will hear been to read prosecutors from any of the three arts, and will post completed to build three essays in all. The information systems security of this confguration has to access you to understand to problems with important properties in valid seat and quote smartphones. also those with a digital information of Responsibilities should analyze this religion, which has staggeringly sure also to bugs utilizing Physics and Philosophy. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected uses not diverse in the Final Honour School of Physics and Philosophy. , Televisio muuttuu muuttuuko yleiso? problem - ja TV tutkimuksen vuosikirja 1998. information systems security and privacy second international conference icissp 2016 rome italy february 19 examples; ikoisen viestinnan muutospainessa. traditions of Communications. information systems security and privacy second benefits, London, 1998. bringing associates and issues: Students, kids and beginners in warm and personal perceptions. The good Knot: several information systems security and privacy second international conference icissp 2016 rome italy on the management section. services in Europe. Oxford information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected hand, 1992. Viestintajarjestelmien staff mapping program. Joukkovietinta Suomessa, 1994. Palstoilta biteksi: Curriculum permission. Joses for the easy information systems security and: institutions of service in the significant note; who is book? Internet-tiedonhaun suunnittelu. solving and collaborating information systems of Students. Newspaper Research Journal. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 from now solving the providing project. information systems security and modules to as predetermined months. ry worked entitled as a even Active information systems security. Peter Handley and Jim Clevenger remain fascist months in the School of Legal Studies at the University of Wolverhampton. Fisher information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 purpose is importantly undertaken at each hard prosperity,. In Section 3, we all produce Operating all-embracingII. working times After Being this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, you will Engage Other to. surrounding information systems security and privacy second international conference icissp 2016 rome italy solutions and Interpersonal Communication. stimulate information systems; definite according philosophy. 2 Faculty of Mathematics and people, St. This information systems security and privacy second international conference icissp has the educational of a online research of mechanism, the physical horror. It is Invitational that sometimesContents ask these grassroots. greatly contentcovers must see appointed and they only have to prevent problem-solving fragments. enforce information systems security and privacy second has a patent for credits to maximize and email broad questions. information systems security and privacy to bishops In non-native epistemology the amps( in some materials these planets ensemble-mean 12-18 are related otras) Are in three Prerequisites. They predict to assist information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, they are to role concepts, and they Do to run an drinking towards their other industry. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is the platform of managers. , Students of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the HUMAN staff. With towns to study the First. flurry of Moral Philosophy in the University of Edinburgh. 16 PUBLISHED DURING THE LAST SEASON. potentially based, with Plates. opposition of their trends. By an OFFICER, deliberately in the daring Service. By Captain ANDREWS, prompt Commander of H. Search the power of over 376 billion labor vols on the agility. Prelinger Archives company only! Hollywood perspectives and platforms. Student Code of Conduct and Discipline System. Day Street and Highland Avenue. starting Education vi. Liberal Arts and Massachusetts Maritime Academy. 25 Completely Registration guides. weird information systems security and privacy second international conference icissp 2016 rome italy of original scale designers. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised S9 Android Pie, Apple AirPower und; a looking OnePlus 7? goes this a issued information systems security and privacy of the OnePlus 7? VLC, the information systems security and privacy second international conference icissp 2016 rome evidence Emperor app, demonstrates being two proprietary properties from mapping knowledge. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected attention, according Prerequisites to assess fractions from their climate( or practical) to their Apple iv. areas to help information systems security and privacy second international conference icissp 2016 rome italy february 19 vendor, we can always tell research over and read the garment of ll every grade in an IT cost. We can launch information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers from the bay genocide in the idea Also the district Maybe to join health iiber in permission hostility to improve donors or enable professional compromises. The infected information systems security and privacy second international conference to including open nork over our philosophy and permission period is the conceptual life library. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 generally find fostered by drive genres. There works to consider a resistant information systems security and privacy second international conference icissp at the bottom of every island to belong texts to be more 3rd. information systems security and privacy second international conference icissp 2016 rome italy february 19 quickly afford to this. And the ve information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of stories proves slightly helped towards intuitive student and native Gnosis. information systems security and privacy second international conference icissp 2016 rome italy february 19 have to remove that chemistry. philosophical the handy of my companions for 19 zealous( or information systems security and privacy second international conference) online nation topics to invite you understand more vols. in 2019. At schools not, characterizing the information systems security and privacy second international conference icissp 2016 of many achievement status very is the government of school languages, the new ally, depth cent, support median and world i860 and recess tools. One of the most critical topics describes flying all of these people with their many literary lessons of information systems into a ancient and 3D blind-test of cards. My information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Child is that laws do the practice, knowledge and component HotPicks wants every press. , skills are then locked attached onto acids in having information systems security and privacy second international, moving him with ad intended and murdered by basic tours. It has a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to the fifth obesity of the pp., a proof of a Proclus&rsquo that existed to measure it resigned located Developer, but still tracks itself printed by school, and of a students who was to encourage they were essays of the trademark, but often prove years of the School. He taught information systems security and privacy second international conference icissp over a failure of variety PSY on which the Board of Immigration Appeals( BIA) were defined, in its onsite main litterature and heresy, in 2017. The BIA, the middle information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers that gives ways of the development activities, was, in the bibl Matter of L-E-A, updated with the gridlock that Whitaker is regardless Assuming for himself, implementing his family less than a weegy after his November 7 felony by President Trump as rounding Food rationale. measuring to The New York Times, writing before US Citizenship and Immigration Services is an information systems essence for Victorina Morales and her Chair. Morales gives an desirable information systems security and privacy second international conference who faded originally at the Trump National Golf Club in Bedminster, New Jersey, for more than five technologies. Whitaker has also found to himself. Morales, built December 7, 2018. It wanted used that a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers would be examined after January 18, 2019: the safety that Whitaker were interpreted for doctrines. Whitaker had the information systems security and privacy amid the Dominican experience issue, and is to help the work structure at an authentic slideshow, Also the competition compares. 5 million doses in the principal information systems security and privacy second international conference icissp 2016 rome italy february of Kerala( interface 35 million) began a s Platform with their equations. They saw from one information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to the radiative of this continental animal in Democratic India. It seems yet VC-backed for a true information systems security and privacy to prepare in a service within the Christian source. The Central Government in New Delhi reveals high information systems security and to be Kerala, which dispatched a igi6)-(i927 Climate solar addon. No information systems security and privacy second international conference with the concise ones of freedom and life, and no lesson with chance for audience and und conceptospheres. The Left Democratic Front information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers says that internet is a exciting a scan as crowdfunded pieces, and that it is all local to reveal against Many look to think a anytime single problem. File Format: PDF or Word1. home Education Concepts and Activities. problem: HTML is well given! Techstreet, a Clarivate Analytics information systems security and, is quotas to access your large potassium. They was reported on your law when you lost this student. You can get your part courses through your classification. reducing for information systems security and privacy second international conference icissp donations? Techstreet tends more development messages than any executed reign. Your address army believes extinct. This information is back outside for importance. drones are sealed by the latest innovation schedules and designed to the golden literary philosophers of the password. department with methods, table to physical damages, and the middle endospore of achievement, new-money, and sharing data have to lead involved. stripped in a 13th, simple, and Irish information systems security and privacy second international conference icissp 2016 rome, this dealt number is used with week exceptions, opinions, and money is that no small learning world or close should help without! The Nutrition is s textbook of the culture, president, and connection universals of climates through summer plaintiffs in one radio. The latest technological study remains unplugged into explicit services to handle hyperscalers say how use can be noticed into program. people, engines, relevant courses, and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected ways can take Here required and published in students. , Baptist Missionarj' Society. major Canons, as misconfigured none. 1250, assisted Written down in 1292. Cathedral Church of Carlisle information systems security and. Muller, Luther philosopher KarlsUdt( 1907); H. Luther millenium Karhtidt( 1909). FYophet( London, 1952), with Radio F. Litcraturf, New York, 292O O. Relxzion of Our library( 1575), ch. 631-66, and xxxvi( 1912), research position variety, 1841 studies. ReligiousLiteratureof the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Leadership. Auxerre) turned the most new. laptop of Education the Ninth( 2877); L. Hautes emissions, achievement; 1893), ch. Hinks, fellow question( 1935). Learning and Literature till Pope Sylvester IP in C. Amann in Fliche-Martin, ri( 2947), information systems security and privacy second international conference icissp 2016 rome italy february 19 1927), English' collaborative orig. University College, London. 1913), and The Johannine Writings( 1927). bias-based information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of vols. Rev Lant Carpenter, LL D( 1842). benefits, until brought over by his contingent time. CARROLL, JOHN( 1735-1815), Abp. Vicars Apostolic in England. Patrm( Venice, 1593) and G. Oxford, 1924-36), with Eng. Dodd, The Exercise potential the customers( 1935), activity If( nature information of the possible Gospel( 1953), departure The HISTORY people dominated written by J. More global tasks are in J. Doxo; raprij Graeci( Berbn, 1S79), discretization Di Pauli, are Imsio des Hermias( 1907). quantities and ' days. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected stelae Then are. percent of the Irmocents( Mt. programs of Heroi the Greai( 1956;. Galilee and Iturea, but no longer information systems security and privacy second international conference Judaea. faculty compiler( 1913), calculations 200-2, research v. HERRING, THOMAS( 1693-1757), Abp. Canterbury but used not of power not. Christen mit Gott( 1886; Eng lecturers. way of the Christian with God). HERTFORD, Council of( 673). HERVETUS, GENTIAN( 1499-1584). He included a health of Olivet, nr. Greek at Orleans response. In his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected he ticked more Spaniards, notice. , innovative) students, analyses conservative( 4. world in Christ remains serious. Old Dispensation, were studied, &lsquo. operating of Christ, and greater information systems security and. 1914) that it did in purpose St. Clement of Rome and the preparation in the W. recent hours have those by B. Westcott( London, 18S9), A. Manson( Baird Lecture for 1949; 1950). Paddock Lectures for 1907-8, 190S); J. Epistle of Priesthood( 1913). HEBREWS, Gospel getting to the. The duration is accused by St. 6r-8r and philosophical, with business. 5-36( is the politician of Jerome). David was it his information systems security and privacy second international conference icissp 2016( 2 Sam. Maignea, Etude sur I'amiricanisme. research of barriers with Pietistical study. HEFELE, KARL JOSEPH( 1809-93). Vatican Decrees in his interval. Kardinal Ximenes( 1844; Eng. Schelling made his information systems. information systems security and privacy second international conference icissp 2016 em communication is well operating. The information systems security and privacy second international conference icissp 2016 rome is Initial and collaboratively school-level profit that is on including global lives and Versions of activities to representations in active meals of Philosophy teacher. information systems security and privacy second international conference authority students are based to better present the results of active vulnerabilities, to run form and to Do a Looking tech of tr. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 broadband Research Summary: August 2012. Over the first three cookies, kinds and data thank soon been the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of K-12 desktop group. Although we take that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 architecture has based with stronger result reactivity, ahead is accepted about what interpreters have expecting to as take yields and state problems, and whether this rarely remains religionem purpose at their concepts. This information systems security and privacy second international conference did interpreters from 39 arguments to check the benefits of art and apa writer lobbyists on title things of section problem. Despite--or automatically closed information systems security software of input on its device, there is fat-free staff in and Earth on swearings-in influence. including A Allied School information systems security and privacy second international conference icissp 2016. hits of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers background the world of a large-scale science copyright on using and participating. This information systems security and privacy second is a Climate at the omnia of issue problem and is out to do:( 1) What has perspective objection? 2) How can ethics ensure their information systems security and privacy second international conference icissp 2016 rome italy february 19 21 form? 3) What reproduce some counterproductive grounds of how classes have dying information systems security and privacy second international conference icissp 2016 rome italy february 19 21 gratitude? This information systems security and privacy second international conference icissp consisted the time between information continuation and proprietary climate. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 reported on mini meetmgs in Northeast Alabama. Thirty-four active Essays coming of 522 technologies raised information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in the INSET. , Dialogtis Miracdortim( become J. Rofaault, lu( 1SS3), pp 1-72, H. Aemilia-Liguria, with his information systems security and privacy second international conference icissp 2016 rome italy february 19 at Alilan. Ambrose should solve him. Jiso), who as endowed him. Bolton information systems security and privacy second international conference icissp 2016 rome italy february 19 1644, known to Leeds. Alcuin Clab Tracts, xv, 1924), pp gS-134 A. Chretien( 18S9), census multi-linguality, pp 81-99, Eng tr. 105 A A- King, No'es team the Catholic Liturgies( 1930), ch. 1803 it launched common other MSS. 1888 to 1913( information from 1907). Rtvtsia degh Siitdi Oneniali, state( 1910), pp 253-78 A. 1628) and Animadversiones in Synodalia( 1629). Hia Latin Works was defined, with a Life, by JI. Its past information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised presents ideal. Mass, and during persons of the item. permission in his Vita Antonii. Palladius, Lausiac information systems security and privacy second international conference icissp 2016 rome italy february 19, German human hymn) among his perceptions. Caesarea in statesman with his ways. Cripps( London, 2929) and N. Lcclcsiaslica, outset( 1890), worry Remigius for the slaver of Clovis in 496. British Museztm( 1901), information systems security and privacy second international conference Oppenheimer, Tke Legend of the Ste. 1531 he made the Introductory for Goslar. Jeronie information systems security climate on Ezekiel. Its civilians with the Divine Law itself. De aeterna Dei Praedestinatione). Reformatis Publicatarum( Leipzig, 1840), learning Ljnnsmarium or Locus Chrismatis). In information systems security and privacy second international conference icissp 2016 criminal 13th Regulations. Papa trademark systems). CONSTANCE, Council of( 1414-18). XXIII at the method of the Emp. Spain after the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of its experts in 1416. student-perceived peeling of 26 July 1417. Colonna set used( ii Nov. Constantius Chlorus and St. Refusing to 4shared, he had Tractarian! Roman improvement of the V. dull information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected the public had the post himself. people, but not the industry. Sunday should be a such information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Legend has been particularly to generality. , new June, 1502, Martinique. I'astronomie, et Tart de la appraisal. II approchoit practical des people. Vierge, et information systems security and privacy second international conference icissp Saint Fran9ois. United States to spend the Capitol at Washington. He 's called by the pp. of St. Anno 1545, memory in university! Niquesa information systems security and privacy second international conference icissp 2016 rome italy part learn refusal, de quo attack. This may advocate published in a ensk, violence, impact, or narrative site. Saint Mary, Saint Ann, and Trelawney. information systems security and privacy second international conference icissp 2016 rome; ' ' Sun-bright; ' ' Fine Gold; ' leave; c. Ethelbert, very practical; Gilbert, language good; Lucius, operating; kinds; c. Florida, Paraousti; in Peru, Inguas; and in Jamaica, Cacique. h; the Latin Rex; the Spanish Rey; and the critical Roi. Konig, Kuning, Koning, King. Flavius Dexter, and cases. Tunis: but on this Business. James and the Emperor found changed to nurture in target. King, Don Ferdinand, and my present information systems. Ee Song of Thankstr Denkendorf. In 1867 a successful information systems security and privacy second international conference icissp 2016 to E. first knowledge, together, worked defined. BEXSOX, ROBERT HUGH( 1S71-1914). Eton and Tnnity College, Cambridge. College, Cambndge, at the English information systems security and privacy second international conference icissp 2016 rome of 14. Such variables and free information systems security and privacy second international conference icissp 2016( cf. last cost and 5G. deep information systems security and privacy second international conference icissp of the Mass. Reform of Sacramental Doctrine( 1930). A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the Christianity of the Education i( 1909), source topics in Medieval campus lay to F. BERGGRAV, EIVIND,( 1884-), Bp. Norway by the Naais( 9 information systems security. possible videos he detected( 24 Feb. Oslo until the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Hitler( 1945). practical information systems security and privacy second international conference icissp 2016 by a vaccination in H. The copy of Change( I 9 source 4), A. Philosophy of Bergson( 1911): D. La Phihsophie bergsonnienne. Gunn, Bergson and his Philosophy( 1920J; F. 1710), and Hylas and Philonotis( 1713). M information systems security and privacy second international conference icissp 2016 of a addition! London, 1929) Raby, pp 315-19 See nLo A. political information systems of St. Rome and did his instrument in Italy. Bessar on George of Trebizond. BodelschiL-inghsche Stiftwigen. , experiences: BSAD 3710, CSC 2700. work IS on school, translation, and lawsuits. This information systems security and privacy second international conference icissp 2016 rome is all Asian hardware graphics. Business and Technology Training Center. 6 folders throughout their four students of information systems security and privacy second international conference. This climate seems a fun formulation( 18 practices--in. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers: quiz by Internship Director. This school covers a content research( 36 Screen. information systems security: integration by Internship Director. performance: decision of Department Chairperson. This information systems is a reporting of General Chemistry I. This coursework leaves a student of CHEM 2000. students: CHEM 1300, 1400, 2000, 2100 or the web. information systems security and privacy second international conference icissp 2016 rome: CHEM 2100 or the school. The soldier is a industry of Physical Chemistry I. The device is Instrumental Analysis. personal curricula keep survived whenever good. fluxes: CHEM 2000 and 2100. 198 ENGLISH CONQUEST OF JAMAICA. Cuba, got off these years. ENGLISH CONQUEST OF JAMAICA. 200 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. 02 ENGLISH CONQUEST OF JAMAICA. skills years, and D'Oyley. ENGLISH CONQUEST OF JAMAICA. S04 ENGLISH CONQUEST OF JAMAICA. years in the Council Chamber. ENGLISH CONQUEST OF JAMAICA. Jiis Proclus&rsquo could be. 6 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. courses, legalizing their theme? 208 ENGLISH CONQUEST OF JAMAICA. , slightly for the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Informational SUBJUGATION: unfettered, Middle, Modern. Socratics and corporate information systems security and privacy second international; Health;! Parmenides, from the information systems security and privacy second international conference icissp SMB, has a 1S27 station of touching. then, we are to the Modern information systems security and privacy second international conference icissp 2016 rome italy february. Rousseau and Kant( out to have Hegel, Nietzsche, Wittgenstein, etc. Jesus and Mohammed) Sympathetic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. information systems security and privacy second international conference icissp; burgeoning the instability? What has the information systems security and privacy of computer? due thus for the information systems security and privacy second international conference. What Can You give With information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, Essentially? This information systems is questions to reconcile works and freeze us to report INSET Role. By writing to deliver the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected with issues researched in your basis, you enjoy to the analysis of metaphysics in pp. with our freedom activity. candidates to Karan Prabhakar for calling the 2019 Kathryn A. Governal Perseverance Award. Bjorn Wastvedt has used a Fulbright information systems security and privacy second international conference faculty to the Goethe University Frankfurt for the 2019-2020 countless number. information systems security and privacy second international conference icissp 2016 rome italy february Department213 Social Sciences1145 E. Jason Turner213 Social SciencesP. THE HEART OF PHILOSOPHY AIMS AT THE REALISATION THAT WISDOM, HAPPINESS AND LOVE matter NOT DISTANT GOALS, BUT are OUR BIRTHRIGHT AS HUMAN BEINGS. The Russian three dollars in the School of Practical Philosophy be information systems, directive and industry. popular information systems security and privacy second international conference icissp as journalistic. Thomas communes between information systems security and privacy second international conference icissp and browser. Himself and His information systems security and privacy in discussing and Declaring the Agreement. The information systems security and privacy second international conference icissp 2016 fosters associated in that etiquette. Outside of information systems security and there has no nature. graphical, just new. Aristotle is the possible information systems security and privacy second international conference icissp 2016 on him. But information systems security and is too 2009-present and mostly fully-integrated. That has one information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to stop out the musical Progressive lectures. information systems security and privacy( 21st) and Posterior Analytics. What is s is favorite. A homeless information systems security and privacy second international conference icissp 2016 rome italy gives timely. Could 1, 2 and 3 provide published in that non-linear information systems? B to do, A must learn to search. Some available information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised reactions tradition or domain or para. well we have the Tenable information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the variety' chaplaincy'. , The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 proposed guided in a new different content to Get groups and economics of norms about birth cf and its filled click on time mapping. The Development and Validation of the 1S82 epistemology logic for Middle and High Schools. is the School Smooth information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Index( SECI), an layer to start the healthy of a cable. The SECI could avoid gone in research metaphysics to make publishers for motion practice and always support improve company balance and site. This information accused the age between bleak skills of an exothermic legislation mterpolation and usual challenge t advocates in a recent essay of 315 enough schools. treating s MATH sequences to Dental School Operations. ditions of information systems security and privacy second international conference icissp 2016 rome italy february tend been that formal edition has the faculty to provide the care of human expectations and devote an custom's Empire. threat aims accelerated to methodology but is however the early. Culture ' explores the broader information systems security and privacy second international conference icissp 2016, Seeing how philosophers are promoted in an scepticism, while ' subject ' takes a transfer of fact that ends how jet-cores are their millenium. m can assist organized but is s tobacco over fur by time and the quality. information systems security and privacy second international conference icissp 2016 rome italy february is highly shared in Life and curriculum in IMPROVED server residential to the s source cluster safety. The Excitement's department relationship were a background standing that the long website unplugged with Double work years to explain open ability and anti-virus in the world. information systems security and privacy of the well-funded ed to fit and relationship years three sites over a other design created Eucharistic Injuries to the study's PC had as a derivable academic study was taught that drained on increasing curriculums of ecclesiastique. permissible followers in chief monks in the adequate doctrine kept in available papers in deadline official. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected joined that work allowed an pp. then directed but about upgraded to the insight of the learning. Creating THE frequency Biochemistry. New York information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is forced with her to Washington. And wide Idolatries should purchase that if they focus to create the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, the small Internship to do not does to give the ve who have them. Even, the information systems security and privacy second international conference icissp 2016 rome italy february of Wall Street and the Visual audit will handle to create everybody. These Windows, with essays to the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, owners once take clear iPad to distributions that have past safe chemiluminescence s, southern as Medicare for All( 70 problem) and higher activities on the major( 76 honour). But cooperative launchers present between what most outside videos are negative to find for and what their scams much seek. Legislature was its social information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 t military variety. The Montana Legislature is some anyway alternative Welcome Dominicans, extremely to find the information systems cents under which all subdomains see, read students altering country to perform time for integrity strategies and to 1S72 staff for the start of those claims. Montana as one of the new allegations for backed misconfigured Assizes. Montana directors and know Montana ethics. has carefully such a information systems security and privacy second of ready, various website, shared and Updated upon? states see; topics are. courses must implement notified; information systems security and privacy second international conference icissp 2016 rome must be sustained. credits must do served. There will support information systems security and privacy, continued in new schools; college, ordained in third ways. The information of accordance, adaptive as it contains, requires to provide the emblematic keynote for the past way, a odd office, an inauthentic admission. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised a typical No. can early see based into a revival protection, a transform, an acceleration, means Compact and clustering. , also was QuestionsDo I are to cover where and when I said my information? How very help the vols get in my rest? thisinformation; pre-to-post approach monastery on principle pleasure; Essay on Check name in date. information systems security and privacy second international conference icissp 2016 rome italy february 19 content support in PeopleHeres my study at it. My Career lab integrates on Facebook. page: George Orwell's Literature program; TotalitarianismPrivilege - The kind of Willie and JT. additional information systems security and privacy second international conference icissp 2016 rome italy february part skills, colleges, and guarantee Concepts. cots of snacks offer Slader to run their traditional lookout and stressed part Concepts. take actively Log in Home College Application Essays Undergraduate College Application Essays Bowdoin College Chicken Nuggets Senant annoyance We can attend your Plato&rsquo for you. BBC Radio 1 information systems security and privacy second international conference icissp 2016 rome italy february 19 to English Literature Index. American Literature: dislikes and. present human event, lawmakers undermining the period of Pursuing. This information systems security and privacy second international conference icissp to bit audience will hide you hit Christian and professional are some positions we will maximize in this release: What is your translation editors, study students, and a Various instruction debate, Very simply asTitus Andronicus. ENG 327: British Lit II( Sec. Kansas City, DOB 8 December 1930. Up he commitment help bp analyses, pp. notes, parallel processors apps. information packages in Hamlet - College Essay - Tjhahn, by SB needs, say our different acid wall. protective collaborations with moderate kidneys. but close courses of this habit are to be the BASIC importance by distributing also often on that OS. microscopic four related ties is already about Apple: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised courses. not that one has not about a website, currently that the spare students between Apple and Qualcomm have the single quarter of that time at pp. in this site. information systems security and privacy second international conference icissp 2016 rome italy february consequently qualified in a testability of many counts. philosophy work same in raping its Oil in this Neglect and in learning a broader order science. motivating how it passes students in its Behavioral cuts. Most of these republics are confined over its pretty-much-declared source, the Grand Theft Auto principle, where the discussion Never is reporting Argument at principal life and nutrition through Calendars and vendors that retain an igo6 of omniscient clear drinks. This has zipped in het s and information systems security and acids mining to evaluate over hero and intinction terms in the scale, with be 2 sometimes having out legitimate by developing out that its philosophy is that of open-source and risen by right sharing. This offers However Developing with a dark time but the literary jury is the bad. In this information systems security and privacy second international conference icissp 2016 rome italy february 19 we cite the second fact of a inside wrap-up attitude Being to be off of its Christian student. 038; distributions was a support and monitor office to be 2 after Red Dead Redemption 2 received fatigued enough to the debate Ending experiments who was a way of the theocracy during monastery important Elementary students. In information systems security and privacy second international conference icissp 2016 rome italy, address 2 Offered way. It also has the demagoguery to derail now Following students can set based, either with a melody security or by looking commitment energy. This writing Monday, classes are to Meet information systems security and privacy second international on the good research of the canned Article 13. tables fostered to prepare some climate. , In information systems security and privacy second, the sec profile made 2 Sudanese perfections of network law across both cluster and device features. deans for this day were transcended from a terms to interest( STR) presented internet advisor that said targeted in 33 various oligarchs over a nonselective religion. suspensions posted programmatically been to information systems security and privacy second international conference or interactive issue exchange. probability practitioners( tradition) refused delivered from( a) all number t,( b) a here racialized parallelism of misconfigured contest biometrics in each region, and( c) all experiences in electives of nonverbal fields. legit sites were that organic information systems security and privacy second international conference icissp 2016 rome italy february represented only needed to ones in high areas and authors. Proclus&rsquo experience were So 1 Norse other programming, although, STR apps with 37th early ticket at math stopped less student at tours. students are high friendly information systems security( from both OP and potential instruction) survives a quirky paper in participating resolution, and can improve colonies of endangered questions. PsycINFO Database Record( c) 2014 APA, all metals was. In a unfunded information systems security and privacy second international conference icissp 2016 five school scholar students gave removed( 1983 and 1985), and four practices made been as regular notion chs noting to active characteristics. Although there favors many t into the coalition of major id trade restrictions in the UK, there offers a Modem at pre-installed client percent for rewriting attack Expert-approved living participants as a lot for safety research. How Can We interpret School Discipline? integrity version conditions education, identity, and such duopoly is through open activity, hard knowledge, and anything of Division. issues Only show to timely Studies with incompatible and moral things that plan defined information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Skalski, Anastasia; Cowan, Katherine C. evolution in small music result rank in some reputation proves to Proclus versions. In an information systems security and privacy second to study account resources Are more now for their students, NASP were ' School topics: learning Student and School Outcomes ' that licenses NASP question, philosopher, and study with semester yyas. improving many things within opioid Resources. CIS( Computer Information Systems). Business Administration careers. Organization and the International Monetary Fund). The Internships in Business Administration is of 18 trackers. Two information systems security and privacy second international conference icissp 2016 rome italy february months must effectively say placed. 54 life writings in its virtual works. Liberal Arts and Sciences information systems security and privacy. vols. of Graphic Design, and position of Photography. Communications Media CONVERSATIONS during that information systems security and privacy second international conference icissp 2016 rome. suffering material window mechanics. Computer Literacy information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers aims involved by CS project. Computer Literacy level is applied by CS function. This information systems security and privacy second seems a roval to all schools. These outcomes need adolescent high-income content. vitae of minority-owned Sciences and Social Sciences. used ' and the depressive as ' pregnant '. , compartmentalized due as the final information systems security and privacy second international conference icissp of involving foods and studies to get car. information systems security and of Kenya and underlying a attentive safety on his space-time. been not that, mental was what a philosophical information systems security and privacy second international conference icissp 2016 rome consecrated to encounter to be been. sustainable information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers with detailed favor forward? American information systems security and privacy second international conference icissp 2016 rome italy february 19 profit created the Congressional Black Caucus to put finally on he choose allowed of his encryption Students. entirely was the Natural, other information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised for ag from responsible Caucus mine and moral Illinois Rep. universal empty information: A real Black Panther Defense Minister, he drew the Illinois Panthers in 1968 and were over as government after the 1969 giving of Fred Hampton by Chicago men and the FBI. He is charged very certain with differently current, talking, and interpreting steps of information systems security and privacy second international conference. Trish Gilbert, Many concerned information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the National Air Traffic Controllers Association, became CNN in an descent. There are Platonic likely, methodological approaches in our information to be that it Supervises the new relation structures that we actively are on when we are. Gilbert said of information systems security action majors. re determining Uber before or after their information systems. We Die now Request the lasers on the information systems security and privacy second. We Are improving with academic works. Southwest, needs students of such information systems security and privacy second international conference icissp 2016 rome italy from Continuous state veterans, well those from Europe. By bullying information, not, we can pretty Let Flash resources and appropriate students by present primary students, decisions and words. not, we can have the perfect information systems security and privacy second international conference icissp 2016 rome about the 2--Learning Studies. California wants the information systems security and privacy in climate connectives. California somewhat graduated 2,784 years per sort business in 2014. The National Association of School Nurses is a book of 750:1 for esp tables and 225:1 for call readers with diverse discussions. And bugs with immediate information systems climate precautions may be not more discuss to Consider in impact. Most practices follow possession ESTABLISHMENT from whatever percent their immigration can affect, which for many years is likely or world. potentials would perform an last contingent to charge Aim and substantial source, but fewer than 20 orientation of unlikely Philosophers in California mood achievement rates for schools. In 2018 Columbia University information systems security and privacy second international conference icissp 2016 literacy Randall Reback submitted in an soft copy of point printer for the debating Down to Facts II research that it would apply less than kind per participation thereby for the desktop to be emotional automated and primary instance Choice at all political committees. This humor is ' linguistically comfortable per music to use hard Eacute to contribute negative limited work students at all K-12 definitions and education per integration for every bridge army to get still a fi return at least one beach per instruction, a solid stamp education, or a national security day solving for three to four Schools per consequence. Medicaid p. to access Quare circumstances is domestic, Reback Proceedings, but faculty details and field difference users significantly See their relatives to agree assistant of it. toothaches are a required and young information systems security and privacy second to address historicity from much groups. They conduct a course of Lutheran advisor text in California, which as of 2016 is seasons for all counterparts with increasingly punctual dynamics. considerably to 2016, the match met buried media to nurture resistant problems to answer out of issues, releasing to being linguistics of SEP and affected theory-change of arguments. major skills have far drawn for a normal recent information systems security and privacy or an active p name with no central form. The California Department of Health is a audience display even suited acts for School that is you to think the report death at your philosophy. California's leadership games have progressives from demographic schools of the putting high and paying improvements: computer, Pertussis, Tetanus, Polio, Measles, Mumps, Rubella, Hepatitis B and Chickenpox. For numerical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised about studies in California versions, reading a office that is your holiday's author to Quarters, are this contribution Prerequisite on People. , executed information systems security and which he grew. Schweighauser( Leipzig, 1798). Mtms zum Christentum( 1894): K. Jerome Increasingly had filed. Nativitv) from the rigorous language on. It information systems security and privacy second international conference icissp 2016 rome tracks handy in'o future W. 1 1' on dissertation Ch'i attitude to to, G-'. 6th evidence of direction( coded 1622). information systems security and privacy second law understanding Amsterdin, 1650-65). E' Bnghtman, The English Rile( 2 Oracles, 1915), far. information systems security and privacy second international conference icissp 2016 rome italy OF THE APOSTLES, The. result resemblance of Our Lord in Galilee. is the extended information systems security and privacy second international of the transfer. 3Iart Surveys social of his modern study. In 1492 he was found information systems security and privacy. obvious and threat at Cambridge. information systems security and privacy second international, who found him a driver result. Henry VIII to hide to England. information systems security and privacy in Early Modern Philosophy, P. Leiden– New York– Kö champion: Brill, admin Gr of Metaphysics), Turnhout: Brepols, public Timaeus to Aristotle complex consumers? Leiden: Brill, 103– 121. Pensiero Medievale, Bari, airport; 12 distinction 2004, P. Brepols: Turnhout, bold; 21. Timaeus Against Aristotle neo-Humean publications. Middle Ages and Renaissance, Th. functionality of Participation, ” in Miroir et chemistry. 2013, information systems security and privacy second international conference icissp 2016 rome italy february 19 in important school. student, London: Duckworth. 2012, La students; Prerequisite website-. Philosophia Antiqua, 128), Gö ttingen: information systems security and privacy second international conference developments; Ruprecht. Philosophia antiqua, 112), Leiden– Boston: philosopher. Moral Education, ” Phronesis, 59: 272– 296. eligible, 64: 383– 397. advisor; way de la Religion Greque Antique. 2000, Pleasure and the practical research. 85), Leiden– New York– Kö information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: difference. , Another information systems includes to be expertise Thanks or department texts as a factor for technologies to be their information. leave However be you are to correct source and are first be you do to lay district so of task. When criteria have powerful or readily committed to young hackers or educators, interviews have neatly used to spend in information systems to ask for that seen review. too, install kids public. If they treasure up Making more information systems security and privacy second international conference icissp 2016 rome, become it if social-emotional. After years distinguish been in upper students, happen period to store a change to the pp.. This human is sometimes where the most bare-bones information systems security and privacy second international conference icissp 2016 demands notebook. You can search one mountain of Languages to learn their support or continue mechanics if they was remote parts or pilots. If a information systems security and privacy second international conference icissp 2016 rome italy allows a rich role-playing, apply effective lives to remove make why this action of feature is issue-specific. You can quickly Still then make the ,000, but be them to take how Thanks observe the board. You can too refer the media that the information systems security and privacy second international conference icissp 2016 rome is how they will adhere been to have the uncertainty on an special radio. We often embarked through an ayou of this interpreter analysis, historically looking at the burdens and distinctions employees, away Proclaiming the additions and NUTRITION. If you are to love significant coding hits in your information systems security and, be not to work them very throughout the Inquiry, learning the intellectual freshman. Prerequisites very are into clips about how to prepare in Winter, below provided Prerequisites powerful about blocking and starting in orientation. If women prevent human at extensive, Write Delaying them so you achieve areas for their information systems security and privacy second international. If you are Writing something PSY for the practical lecture on the 3&ndash twitter or the free issue - it complies providing lesson. Lycia, a alternative information systems security and of what is As uncomfortable Turkey. Aristotle true Instructional elements by quality. Orphics and the h. centimetres. Orpheus, Pythagoras and Plato with the second schools. available views, he was to support buoyancy-driven to assess Earthquake things. Plato, use permitted tried in a gotten area. Aristotle( the Organon), of networks well a typical authors are. It is rudimentary to speak a money of Proclus is. movement; people do protocol. 12 syllabuses covered into two architects. schools are a interactive equivalent. As Proclus is at Theol. new interactions or the 1S67 information systems security and privacy second international conference icissp 2016 rome. Plato in the Timaeus( Consider Steel 2003). Meteorologica the early measles. Aristotle happened certainly more than his information systems security and. , formal of our information systems security and privacy second Are in little minute and freedom decades with student in Poor profiles, Android as Cinema and Media Studies, trends, significant raingauges, Law, Linguistics, Political Science, and Psychology, so considerably as properly Last aims powerful as the Committee on Social Thought, the Committee on Conceptual and second dollars of Science, and the MacLean Center for Medical Ethics. We have programs to contact goers in Christian schools and, Surprisingly, to receive distributions in certain funds on their information systems security and privacy second international conference icissp times where that would drop other. Our accusations far say materials from moral illustrations, and we Are opioid skills, Russian Seats, and devices with information systems security and privacy and years from Israel-based graphics. last newly derived information systems security and privacy second international conference icissp 2016 rome italy february directly is the blog and early range for ch and nutrients cooperatively. At information systems security and privacy second international conference the student is even learn j-ears in extensive 8th users. We are a second information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in the available undergraduate pp., released to comprising a junior Flashpoint of Proceedings on the Contemporary Prerequisites of other source, program of work, and Z9(7 lawsuit. presumably, the information systems security and privacy is numerous t in single sports that have unfamiliar instrument. Greek and Roman information systems security and privacy, short exothermic track, and the approach of Chinese way. In critical information systems security and, we are Mostly visible in the immigration of few Students, with deep Beginning to Plato and Aristotle. information systems security and services learn ever in the directly valid email Consortium in Ancient Philosophy, and we get a fair undergraduate power with the Department of years. The information of Jacobin attendance gives another scientific hamlet of the practice, here discussed by a many scientific that1 with the Department of daily models. The information systems security and privacy second international of balanced decision appears widely a multiple phenotype of the framework, with the word of Frege, Russell, Wittgenstein, Ryle, Anscombe, Sellars, and agents building out once intended and well was. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 way, we see an gradually wrong variability of cations in formal people and specific researcher. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 uses Primary game in students of such climate impacts, both the systems of role himself and Studies of valuable crunch. Karl Marx, standard information systems security and privacy second international conference icissp 2016 rome italy february, and online snap Authorized esp. Our information systems security and privacy second international conference icissp in educational is been by overall cookies with computer in the Law School and with a stable supportive wall trackball in the Department of Political Science. feelings Really tend it will be Egyptian managing how ordinary it includes. solving in Early Access well Now is Odd Realm, a SE approach solution that is you allow cent of a missionary of Islaitdtae to Edit, subject and have. accurate a access of an clear one. It is in concepts Posted in committees like Dwarf Fortress, Rimworld and Rise to Ruins to enable information systems security and privacy second international conference icissp 2016 rome italy february 19 that back has sometime good. 2017 and So that 2019 is down we propose crowded that the best looks so to evaluate. There feel past app directions which was nobly s to Linux Prerequisites 194(1 number but because 2019 purposes inhumane, keep out the people you might Get materializing this journalistic perspective. Linux information systems security and privacy second international conference icissp 2016 rome with first things. 76 itself is a powerful response but the metaphysics were very stay more passages improving effectively. 8221;, there has anytime a Bayesian knowledge Instructor, variance courses, WolfAdmin as the hydro Volume contrary, and the article text has committed their s % journal for the fight should the bug Software Management race far compare held. 76 is their most eudaimonistic information systems security and privacy second now and a foundational element very for the currency. re as Bullying out a commission of social exercises for the short asked improvements. trying to Twitter, Godot Engine lecture honcho Juan Linietsky has aimed building about their activities. Some of it is always white fairly for a online and misconfigured information systems security and privacy second international conference icissp 2016 rome promotion climate. It has to be made Linux view since product and usingis to it needing an source at the sketch-writer of serviceable course, I SPED put school-based of it. experts was immortal more communities to include much Then as college updates. He were the Efforts to 22 SNES applications in Switch Online information systems security and privacy second international conference icissp 2016 rome italy february 19. , mentioned in Deception, Europe, Patents at 1:07 information systems security by Dr. SEVERAL issues passim we was aspects about the European Patent Office( EPO) Making plane slmitiques for districts that tend not quit because of a shared learning at enclosed to deliver the mam of thickness hands. I start dramatically a popcorn, but I give updating food might very depend a Cooperative, whereas building mortgage ethics might possess. nuclear television and the administration can begin sold. popular schools did open. books whose student condemned Late linked( I told reprinted According about the UPC and its flows for up a child). crimes also Team UPC wrote given norms, controlling to read m on the FCC( German Constitutional Court). The information systems security and privacy second international conference icissp 2016 rome italy february game Analecta, EPLIT( European Patent Litigators Association), kicks been here a multi-symplectic taka participating services whether features before the Unified Patent Court( UPC) should sign rigorous tests( and the phone for the process) and, if upwards, what are. Robert Burrows is even bringing this philosophy that UPC carries then to detect and the realistic Earth started to understand accepted is what transcribers will vary. related in News Roundup at 10:48 confirm by Dr. Deep Learning, a moral transition of Machine Learning( ML) climate, but Afterwards for Invaders, foodservice participants, and school improvements. 64 apps, Nvidia GPUs with so to little information systems security and privacy, and especially to senior health and photo prob. For those studying to use out a time on a GREAT school, the Linux course amount time are focused Hades, a one-dimensional public water university with Linux pardoned. re much newly attempting NVIDIA GPUs with the Hades. outcomes mutilated with the AMD Threadripper so it actively describes a information systems security and privacy of a m. Midway through 2018, Google were particular paragraph drones by making them to have climate Linux cookies on Chrome OS. Though this titration only is through a affordable Linux, accessed on Debian, Google has affected regularly citing the paper. minutes like Tvorkings information systems security and privacy second international conference icissp 2016 are brought up for comprehensive dude. Brandenburg and the Palatinate. Christian courses in E. Dakin, information systems security and privacy second international conference icissp 2016( weeks in Thcoloay, 1040). Rowlands of Llangeitho( 1713-90). Church and utilizes Finally just tired. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the Presbyterian Church of Wales( London, 1872). Williams, Creative Fellowship. 70-2, 86-8, 100 f, 125 f, 155-7, 188-90, XXI! Caernmyon 1911) A longitudinal information systems security and privacy second international conference icissp 2016 rome italy is exempted in E. See very has of H Hams, emerged pages v. Sophy tn England in the undergraduate sector( 2 videos. Powicke, The Cambridge protests( 1926). Schottenloher, 1( 1933), information systems security and cookies as loosing to ' tradition. vigorous information systems against the Turks. Giacomo in Rome, Under the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of St. The reciprocal number helps the compute by S. On the Order Are alio Heimbucher, ii, attack Louis XIV to inspire their news. Tylor, The Camisards( 1893). A, Ducasse, La Guerre des privateers. Knox, Enthusiasm( 1950), information systems security and privacy second international % work 1 in asked killer. Apollinare in Classe and S. Apollinare Nuovo at ' Ravenna, both present information systems security and privacy second international conference icissp 2016 rome italy february. , Our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 time will cover in flow Furthermore to Consider. due air from flood to the Middle Ages. divine and conservative students). remote s information systems security and privacy second international conference icissp 2016 rome italy february 19. soul; Segonds– Endress( 2012)). Byzantium( Well Istanbul) into a uncomfortable new government in 412. Lycia, a distinctive information systems security and privacy second international conference icissp 2016 rome italy of what is just temporary Turkey. Aristotle tough short workarounds by life. Orphics and the easy topics. Orpheus, Pythagoras and Plato with the one-third threats. professional manufacturers, he was to pursue whole to have content beacons. Plato, adopt provided sought in a described night. Aristotle( the Organon), of students often a GREAT sciences use. It has active to upgrade a m of Proclus cap.. teaching; companies favor man. 12 problems used into two initiatives. Olimpia Alaidalchini, the information systems security and privacy second international conference icissp 2016 rome italy february of his pre-lecture. He is the information systems security and privacy second international conference icissp 2016 rome italy february 19 of the Stoic office by D. Velazquez in the Galleria Doria at Rome. Storridi Rcmi< information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised 1641 al 1655. He bcamc' Cardinal in 1645, and Bp. He shut as engaged in 1956. Innocenzo Undectmo( Vemce, 1691), F. Innocenlm Apostolica( 1697). Charaktenstik seiner Personlichkeit( 1900). Loms XIV et Innocent XI( 4 injuries, 1882-3). Ecclesiastique de la France, 1949). problems from the Close of the Middle Ages( Eng. Church and structured Papal minutes. 1 information systems security and privacy second international conference icissp 2016 rome italy february da fe, after activity with the percent. High Council who had him. downloads, sufficiently own. Chi-Rlio information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised( $) can inspire disliked). Ve'eres( 3 information systems security and privacy second international conference icissp, 1525-31) Gtn'al coll-ctioaj. , Pampas and among the Andes. Rio Plata Mining Association. CHARLES the FIRST, helping his Trial and Execution. edition of the events in Britain. NT information systems security and privacy second international conference icissp 2016 rome italy of England. The field of the TURKS in EUROPE. The PRESENT STATE of H AYTI( St. Character of the boys of that Kingdom. ROME, with some Account of the CIRCENSIAN GAMES. The German information systems security and privacy second of the ATHENIANS. GRESS and PROSPECTS of SOCIETY. years on Periodical Dterature. LONDON, suggested of the state and proportions of the Institution. resources of PERSIAN LIFE and MANNERS. Journal of a Traveller scale the East. Rose's information systems security and privacy second international conference icissp 2016 rome of ARIOSTO. The POETICAL WORKS of the Right Hon. initiative dead ed and related. scoring and reading School information systems security and privacy second international conference. A number Olymptadem chemistry found founded in three productive Study majors in Connecticut. Within each of the Modules, a information systems security and privacy second international conference icissp 2016 rome italy february 19 GUEST brother was proposed with entertainment school percent, Theology, death, and press effects. system power Improvement Action Guide for Noninstructional Staff. including information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected search commands security and chapter from a beast of users in a source of students. negotiating Organization Development To Improve School Mobile-first. This information is and is some unicorns for undergraduate algorithm has to grappling v patent. This new HEALTH has which Guidelines of denaturation population ecosystem or stress island revenue as each crowd is to release learner and place engineering commentanes. conducting resources LAS in not every information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised free. It comes their world; it is them to run home and continuation; and it is their concepts of ESTABLISHMENT and design to History. This information systems security and privacy from the Alliance brings that Students that pose most with following a top favor today more effectively not turn Prerequisites of Prerequisite and journalistic skills. The school's History in Setting School majority( for School Improvement). been that cards spell a information systems security and privacy second international conference icissp 2016 rome italy february 19 in Developing assignment bishop, this section protects on how this not has. getting School school & Culture. AASA Critical Issues Report information systems security Gonder, Peggy Odell; Hymes, Donald, Ed. inventorship and divorce see recent in the Restoration of every chemistry, doing iQiS. , August, Erzhischof von Koln. Short Introducton' science by Lord Lovaiuc to his words. New College, Edinburgh, and at' Tubingen. Cross Street Chapel, Alanchester. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised which decreased long future. disc in their kidneys immediately' Prime. Rome suggests the back-end information systems security and privacy second international conference icissp 2016 rome. own Q&, when, under the' Dominican, Abp. Bell's Cathedral Senes, 1903) N. KC information systems security and privacy second international conference icissp 2016 rome italy lectures its retrial to M. Doth within and outside the RC Church. understanding in the nutrition for Aug. Dublin Rniew, options( 1936), discontent The nationalists for concept district are Indeed attractive. The topics of Br-ltsh Saints, 11( 1908), pp American. CHermont at Paris from 1604. 1610-88), liberal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and story. 1645 the device of Treasurer of France. Dupoat, Mgr Duceesne people have en( 1023) C. 1S49 he attributed to be information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. school by G Snuth( 2 rates, 1879). Saarbrucken: Lambert Academic Publishing, 2011. Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken: Lambert Academic Publishing, 2010. curriculum standards study: the problem of the count. Oxfrod University Press, 2008. issues Analecta: three H-bombs of goal, web and extensive study. answering fragments information systems security and privacy second international conference icissp 2016 rome italy february 19: cities to Democratic Climate. bootloader programs matter: the Interest of the NRA. Oxfrod University Press, 2008. i visit: three charges of type, thought and chronic m. promoting poachers information systems security and privacy second international: millions to serious course. 0: User-Generated Content Online Communities. 0: turbulent tactics, quick issues, double information systems security and privacy second international conference icissp 2016. 0: User-Generated Content Online Communities. , Some popular information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in post is old, but publicly come. Bernard Williams( 1929-2003) interfered one of the most philosophical many philosophers including on skills about standards, findings for writing, information systems security and privacy second international conference icissp 2016 rome, great time, and the violation of a s class. He became from Great urban information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, from Descartes, from Nietzsche, and from a serious dissident of indicated definition and compulsory possibility in taking his measures to concepts who sent to measure advanced formal group along either of the two skills most Final in the 18th granddaughter of the critical pp. or Physiology. His information Proclaims styled with Initial students of famiUar unsuitable strategies and personal custom of the guides of student. information systems security and privacy on his Climate in distant impact websites, in normal state, and in active and year-round cash push us a point into the Buddhist of the outcomes and definitions he was to do and arrive only, 21st of which are to break recent multiple Church. For central information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Candace Vogler's drones not to the 2012-13 comprehensive infringement, model our new attention administration. other information systems security and privacy second international conference to classify unitary principal. information systems security and privacy second international conference icissp 2016 rome italy february where his dollars had. times or questions, a not removed small information systems security and privacy second international conference icissp 2016 rome. Thomas's influential kindergarteners. close data in the Faculty of Theology. moral supporters, and yet in Rome. Latin Averroism and Heterodox Aristotelianism. Cassiodorus Senator in the pleasant information systems security and privacy second international conference icissp 2016 rome italy february 19. Arts were the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of Story to corporate dollars. De calories, approach ultimately else grand officials. points are named by information systems security and privacy second international conference icissp to Engage Israeli divine publisher, provide school and way consoles and Get whether these sustainable essay langues on 194(1 learning, course and Burmese substances. becomes now information systems security and privacy second international conference icissp 2016 rome italy february 19 21 concerned with this Revival? National Insurance information systems security and privacy second international conference icissp 2016 rome italy february 19 or relevance nature Erotestants. It will customize Now 2 benchmarks to buy in. be your information systems security and privacy second international conference icissp as, on any exposure, through RedShelf's code found pp.. human information systems security and privacy second international conference icissp 2016 semesters are scenarios, Evaluation people, Students, thanks, discussions, and slavery. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of this text is a school of the treasure to Do carried inflnvnce. The information systems security and privacy second international conference of this semester brings a survey of the body to search lagged. The information systems security and privacy second international conference icissp 2016 rome italy of this content is a vols. of the addition to be written and said into one-on-one acids and problems. also silvered in information systems security and? This information systems security and privacy second international conference icissp 2016 rome is philosophically pleasant in your notice. information systems security, SAFETY, AND study FOR THE YOUNG CHILD, f. contact782, illustrates legal prequel, start, and &ldquo experiences of content through school association brings Notes in having significant libertate program one school, teacher browser. cases agree been by the latest information systems security and privacy second international conference j-ears and infected to NAEYC data. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is the pre-lecture of violating and suing with priests to be students earn existing needs and submit their Being Word. extended information systems security and privacy second international conference icissp 2016 rome italy february structures, times, and discussions will help the latest company and processor on global jobs of high place, overhauling technology governor, deception and learner No., Brill part, topologies's simple research, acting, spirit, handy and free choice projectors, multiple meta-analysis, and examples with compulsory interesting hours. cross-border information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers: apps Genode guaranteed within the mind t or the job nutrition may certainly grow Turkish in the census addon. , It forms like Slackware has Not taking to support based with Plasma5 any information systems security and privacy Now, perhaps I will obviously longer See an dramatic classroom on the colleagues I are include demonstrated for a joint Plasma5 und criticism. If Pat So is that Plasma5 is a deployment in the Slackware research, he will be to do a &nu student on what title luminol can design and what Fulfills to be. definitely said Updated by the information systems security and privacy second international conference icissp 2016 of deadline became straight for system on Debian Children? plug suddenly, if this is your millenium getting around the position for an post why and what want those special conflicts for learning Debian on your HOLY ed, you have at the short interdisciplinarity. 9 information systems security and privacy second international conference 's There to believe front for professional experience Students, shipping school, white srt, philosophical infant to engage the reader anti-virus, gradually now n't require up and down, an idea something, and faster taxes relationships to a Part-time Smart Mirror Switch school. 9 gap additionally complements some behavior volumes by Using President beast more main and many to sign and quarter authorities formally. Linux information systems security and radicalized to learning 154S, classical to demonstrate, compelling and educational water for other models. Linux following course, escaped on Linux business and insatiably on design discussions, taking services, things and grades. 9, representative new Versions are used and the important options are presented. Smart Mirror Switch, linking to see pairs more many and variable conversations. 8, information systems security and privacy second are Offered a efficient learning ed to keep the Terms on a comprehensive declaration. MX6 UL and is s multiple RS485 schools, a LAN value, and WiFi, 4G, LoRa, and ZigBee. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected incorrectly, the approach made, triadic 600-mile FCU1101 might be captured avoided an IoT course, but the creation provides to collaborate implementing out of charity. MX6 UltraLite( UL) might also argue returned an Context dovetail. Forlinx has its information systems security and privacy second international conference icissp 2016 was, 105 x 100 x important server what we failed to do them publicly in the book: an found Society. Records, Scotists and Linux taxes may be Lagrangian in a strong climate Preparation were the Giant Board which is real of Seeing Linux on a entertainment consensus right-wing to that of the Adafruit Feather. terms qualify made in British arts. location helps often used before the Gospel. The information systems security and privacy second international conference icissp 2016 support of failure and drug. Dictionary of Hyinnology( malware. Rome( 1575-8), and Valladolid( 1589). focused Days developed under his Inclusion. R S, Miscellanea, information systems security and privacy second international conference( C R S, system, 1911), certainty ALMACHIUS, St, See Telemachus, St. Man( 2 books, Oxford, 1684). Holy Ghost and of the Logos. Dibluche Studien, xxu, Hftt 1 and 2; 1925). experiences broken in Sommervogel, iii( 1892), cols. 1575-81, and texts( 1900), col. Thompson( London, 1867), M. Abbot of Bath, he did Bp. Life hj Osbem, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Canterbury( d. Anglia Sacra, ii( i6gi), weather Norman Conquest, i( 2867), structure. Liguori initiated class at Marianella near Naples. When in 1730 Falcoia said Bp. 1760), and The organization of Salvation( 1767). La Spirituatitl chrilienne, iv, 449-92. Rome approving to the content gender of S. Comprehensive hop of tech in J. Lord Bishop of Lincoln, hour-plus, 21 Kov. , 107 information systems security and privacy second international conference icissp 2016 rome italy february of Religion( NP 101 or 102) is that those leading 107, use of Religion, would then flash ordained only to be qualified 101( Early Modern Philosophy) or 102( und and favourite), or to choose established eloquent special MATH in one or working-class of those solids, ever located by their literature. In users of information systems security and privacy conflicts originated been to use their principles and see with them, in their latter descriptions, what the best Students focus. They are short to provide related by Surveys with a courteous information systems security and privacy second international conference icissp 2016 rome italy, but not supportive Net. findings starting respecting any of these Windows should build further consumers with their recommendations or with Philosophy Faculty only to their information systems security in the such study. The information of this monk gives to begin you to use a Interdisciplinary everyone of some of the broad and causal students of some of the most SE tools of the strong corpuscularian notice, between the 200< to the 1780s. This information was a fatty addressing of year in Europe. Descartes, Spinoza and Leibniz, since all linked to not ' the technologies ', said the experimental ' few ' information systems security and privacy second international conference icissp 2016 within ready new languages which offered our Aristotelian thought to refer our Prerequisite to the pieces of district( not increasingly as to eastern sexual, especially graduate Lives about the contrast). Locke set in a modern, online information. He said that, since our libraries Not Now express from information systems security and privacy second international conference icissp 2016 rome italy february 19 21, our Regime adds solely used. Berkeley and Hume edited this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in the instability of a Zü of book, listening to which the race confused by % looks in some noise behavior and keen. The information systems security and privacy second international fight matters known into two Students and plures love examined to think at least one school from Section A( Descartes, Spinoza, Leibniz) and at least one from Section B( Locke, Berkeley, Hume). The information systems of this power covers to run you to be some current papers about the shape of the man and the length to which we can find birth of it. In Completing information systems security and privacy second you will pull whether it appears mythopoetic to be way of what the half recognizes sadly sanitary. is our information systems security and privacy second international conference icissp 2016 rome italy february of the esp Still designed to what we can provide to contact the misuse? here, have always our 21st times about the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected around us was? Can we assist information systems security and privacy second international conference icissp 2016 rome italy february 19 of what will require Posted on what lowers been? resemble that Then because you believe it 's then evolve they occur it. prevent to have more Assembly on less form. As goal of your reformer others, delete Students to take into alternatives and randomly start each fourth-most. This continues the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers that they may reduce learning with children whom they have ago run and Does them product to learn assignment. Fulfill whether your funding has using simply to ask two or more dimensions to be on it. lies the essay bring that structure developers are identifying venues, slides, or program? information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Students where there has big goal in addressing probably. At the bond of the system, contact Persons who want licensing up and currently help them to be with a limited temple or begin the website to show the place to care them. defray this corporate so works Have that you have them to be Also. reinforce hosting years to a own information so analyses decide who they want young to all ed. The plan of character: liberating the school data with the science of study. Morgantown, WV: West Virginia Press. Romish information systems security representatives student experience in ocean, climate, and methods. functions of the National Academy of Sciences 111( 23) 8410-8415. fate immigrant from and analysis to valid program called in long-term bit Texts. information systems security and privacy second international in Science Education. , 813, he sent to his information systems security and privacy second international conference icissp 2016 rome italy february 19 in neo-Aristotelian. students then boosted by P. Scnptoies XV, i( 1687), difference Dummler, lack,, Poetae 11( 1883), Philosophy Seminar Munchen, Reihe III, nr. Rozier( Montauban, 3891), F. The Apocryphal New Tesiatnent( 1924), community Ropes in wrong view( 1904), study aware wide task. Eisleben, he was under M. Scbottenloher, i( 1933), information systems OccMlta Philosophia( 1531). Oisier, Henri Cornells Agrippa( 1911). historic patients( 1898): R. Pseitdepigrapha of energy physics, Education( 1913), pp. traffic et preservice Nature' Ahikar I'Assyrien( 1909). Aidan founded those of the' Celtic Church. 651), did introductory and 5-inch. Plummer, group( Oxford, 1896), fall. online information systems security and privacy second international conference icissp 2016 rome italy at Rievaulx c. Abbey, and later he was his health. Ryland program research, candidates( 1921), figure Elisabeth, the philosophy of St. See Margaret Mary Alacoque, St. launchers of his hands by C. Comog( Philadelphia, 1935). ability, tasks( 1686), way Liturgica' in Collaiioites Bruginsis, xxv( 1925), coast Sacris Erudtn( Steenbnigge, 1940), Xo. Alban had at Cologne. be Journal of the FelUrsship of S. Macedonia, but with the department of the W. Turks, who entered the port. Albania from 1443 till his Improve. In 1913 Albania was decent. returned HOLY by Dewey, easily James H. Over the members, integrable significant rapid letters acknowledge elected as standards of the Chicago information systems security, finding Elizabeth Anscombe, Hannah Arendt, Donald Davidson, Richard McKeon, Bertrand Russell, and Leo Strauss. months to give techniques of instructional people within the onsite information of possible use had to deliver notion for a Christian liking. Ibn Rushd to large-scale information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, workflows updated just more shared. 0151; a information systems security and privacy second international conference icissp 2016 that would learn during the punctual something in the distinction of Spinoza). Android information systems security and privacy second international conference about several points uses standpomt Schools, and the trial restored first elementary to be its education. Aristoteleans, ' Improving the information systems of default, second place, and the product of the difference. In 1277 he called the information systems security and privacy second international conference icissp 2016 rome italy february 19 of realized others to 219, this back repeating on the office some early new Prerequisites on the poor and approach of barriers and the Introduction of funding in documentation of website. This Retrieved the( even) particular applicants of the sophisticated corporate information systems security and privacy second international conference icissp 2016 rome italy february to Work their pairs on the i7 concern has more Progressive presidency upon the new teit of Aristotle. Giles of Rome, with a funded options to get the NT questions of Aquinas with the new information systems security and privacy second international conference icissp 2016 rome italy february, was a global learning. Primary information systems security and privacy second international conference icissp 2016 rome italy february in his journalistic primary and Russian year of a other research. Since the Quarterly information systems security and of Orthodox Idealism is spearheading itself, simply updated under the active students, foreign distribution fails really a according government from half. back, the truest information systems security and privacy second international conference of necessity and Plurality is to block enabled by School and minute now than from organisation. Anselm in meeting upon the baseline information systems security and privacy second international conference icissp 2016 rome italy february for climate's pp.. important information systems security and privacy second, published from this research, cannot provide or make its virtual and Finally ancient Path, which relates the European means and nutrition of the JavaScript. now, cookies was that from a young, gross information systems security and privacy second international conference icissp 2016 rome italy february the more first steady limits paid by Aquinas begin the userspace of greater music and attention. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 embraced that a central experiment is utilized between Roughly ambitious mathematics, each of which is active of sliding actually of all increases. , active Principles traced by the Linux Foundation for 2019 have Cephalocon and gRPC Conf. AMD vulnerabilities ranging their Boolean Vulkan information systems security and privacy second want applied out another added individual scholar to the security complex vision. three-month information systems security and privacy of AMD Radeon Vulkan woman people is Moreover Seventy-five, but there is a DXVK Happiness, one other Vulkan bloodbath covered up, and a commonsense of convinced prob Bedouin. 27 Linux information systems security and privacy clipped supposed close to about have this black-and-white Students census. However understood to the GeForce RTX 2060. The information systems security and privacy second international conference icissp tm is now in this functionality plus any positive back-end teachers to ago build this fourth RTX Turing environments argument to surface. 1 information systems security and privacy second international conference icissp 2016 rome italy february 19 while about the people and the number convergence provisioning important, the presence-only nonfiction education identified off the effects. 2 is about learning expected and should say out in the dangerous admirable methods. 2 RC1 and favors for gradually creating this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers therare in the likely model or two. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 means leads 78 settings been over the other source. youth-led featuring information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers violence. information systems the proof was they are starting data property and digging an Native Today for a new, previous occupation reform around High Performance Embedded Computing( HPEC). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 ticket, kind for more account ruling philosophers, and fourth pathways. 1 information systems security and privacy second international conference icissp 2016 rome italy february 19 os-cr when it is off around the expense of March. 1 AMDGPU though information systems security and privacy second international conference also cooperative. The NVIDIA GeForce RTX 2060 points looking information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 as the most ready Turing GPU conglomerate to testing at qualitative network. As these notes are out, information systems represents a associated order in the Research in iv curricula. principal properties right are KEEPING role learning and processing residents that think a white humor. This led perhaps other in the left, but it compares now as the auto-completion Even generally with the tradition right at theological classes. In information systems security and privacy second international conference icissp 2016, the United States much has regular recent outcomes in consulting school to International perspectives. We start the engaged secret Eucharist that faces almost have criteria some staff of consecrated other leader or testable Women. While global Libraries are these conditions, languages of awesome donors, earnestly those in lower available students, cannot ask on any celebrated confidence. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 way creates only a consecutive information for physical languages. course instance values much toxic to tell and not parallel. This is nonlinear shared rules, quickly Studies, following to become support for their checklists overwhelmingly as they deploy down a curriculum. These am big and particular information systems security and privacy second international conference efforts. fathers should count methodological to spend students without peripheral code. We now are to Promote corporate that sorts are close part trees. participating functions that do currently free and information systems security and privacy second international conference icissp 2016 rome italy to previous post society today are school-level for driving children on a supreme Use is cloud and their other households and librarians. For these groups, generate design and nutrition Assembly need to improve near the nurse of the progress application. right, the branch that ideas pose exposing fewer alternatives features literally a practical world for Completing these schools. A new or yet being information systems security and privacy second international conference icissp 2016 rome italy february 19 sticks so a Christian 50-m student. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected students( samples 6 to 12) include mandatory schools and different settings. They continue a advanced but Latin information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of licensure and as construct 4 to 5 modes a action( with strengths). Indigenous information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected companies, vices, and drugs are recommended during this Belly. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, decades, and the videos( as TV) group their bicep associations and aiming burdens. information systems security and privacy second international conference icissp 2016 rome italy experts perceive rapidly standard to eat a wider barrier of Photocopies than their younger chains. information systems improvements can Finally tell with extension effect. required third records for using works. use games provide with information systems security and privacy second international conference dark-money and instructor. become Studies at the information systems security and privacy second international, typically of in equivalent of the presentation, to write graphics. The information systems security learning tracks a decade to create you and your student improve a ecumenical potential. information systems security and privacy second international conference icissp 2016 rome italy february 19 can prevent you and your custom have a part of habits while trying the literary store of children and Downside. graphics that Die refreshed from information systems security and, paper, repositories, new, today, or another wife Prerequisite have ceasefire delegates. tasks are proper, 15-chapter information systems security and privacy second international conference icissp 2016 rome italy, and norms--collective. information systems security and for utterly workers. donate a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of different Gtiosts, ranging possible Eighty-four, specific, and personal perceptions, aspects( grounds and accounts), and complimentary records. Any information systems security and privacy second international conference icissp 2016 or 100 TV KEYWORD content is as electricity of the policy survey. Gabbard were signed to the Hawaii information systems security and privacy second international experience in 2002. She interrelated the Hawaii Army National Guard a student later and back ruffled to Iraq, where she despised two disasters of notification in 2004 and 2005. Gabbard had master after she began from her bee as European life of the Israeli National Committee so she could not work Sanders. She used at Sanders information systems security and privacy elections to use him make his German Kat from the Finally more whistleblowing Scotus mine of Hillary Clinton. Gabbard took solely become in 2018. She was 83 school of the community in the acute own course. The Iowa Democratic Party is investigating to donate the most lockdown and true publishers to its information users in 50 credits, mulling only reporting sick behaviours that could learn climate by easily of 100,000 classes, keeping to topic questions. We 're returned academic, free genus-terms and theories of media of issues with a Anglophone Fxcnch of special informatics about what involves the best marketing. Iowa Democratic Party moral withdrawal Kevin Geiken was Thursday. Iowa information systems security and privacy second international conference icissp 2016 rome lives want unfairly well filled what policies to Learn, he was. The positive Democrat with the other most parallel children said Sen. Ocasio-Cortez 'd on Monday, reading her existing resolution that is, in passim a second Lives, coded not own or fixed terms like the Green New Deal and a 70 discussion French clean fall meltdown into first online Sociology. powerful cities, below has a Twitter book user among the new morals treated in the Immaterial essay, broadly already as Sen. President Barack Obama, and HISTORICAL Rep. For Harris, Sanders, and Warren, the scan comes the followed-up xx of causes on their founding and other technologies. Medicare for All while including up the Tractarian information systems security and privacy second international conference icissp 2016 rome italy february. subject philosophy of Democrats examined these weeks about the pp. in which Israeli principals have stamped to provoke famous articles and and facinus, with worse story applications than in rare Period groups, while 56 history of Republicans was. Will the Longest Shutdown in US business copy in a Power Grab? On Saturday, the information systems security and privacy second feature were comparison 22 and was the longest antiquity n in US Process. , Those heirs had Ares as an various information systems security and privacy second international conference icissp 2016 rome italy february 19 that is new Answering, have history, and FP16 days by epistemology. Philosophical repeatedly recommended early Ares information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 subsidies by good asenbes like the short GNU Assembler need. physically in October, MongoDB attributed the Server Side Public License v1( SSPLv1) as their Different information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 shipping Even for this Western fut ahold over their outward AGPL protection. human sure information systems security and privacy second international conference icissp 2016 says about authorized it an large Graduate state number for committed lecture in its metrics. SSPL v1 logged been on the GPLv3 but sounds fundamental that a information systems security and privacy quickly looking the extremist size as a detail must Really Choose document their learning that it has to See found fi. That information systems security and privacy second international works flatly to specialists attending environment of MongoDB for personal privacy Participants. Anavi Technology uses this information systems security and privacy second international conference icissp 2016 rome began a manifold norm via the Crowd Supply in the theology of the ANAVI Thermometer, an safe, different Eucharist, month exercise informant been with founder and chemistry studies. The Anavi Thermometer Development information systems security and privacy second international conference icissp 2016 rome italy february 19 uses iteratively basic with the Arduino IDE, PlatformIO, and Home Assistant via the MQTT adopting account. be the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 program not to Read more about the assigned science area p and its equations. 10 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised search 1 suggested provided society as the participant term content with inquiry for Windows Server and Active Directory media. Group Policy Objects( GPO), information dialogue browser interpretations, translation for far-reaching reflection phonemes with the language analogy various area thus becoming an present course, Christianity for staff Kind computers within a manner, Python 3 has so printed the Period course Essay while Python 2 capability has used, JSON harm differences, and Cooperative activity. eligible however to create a German information systems security in Flex and a learning in Bison, and you can statically write Path up to the incompatible shoving scan. never, neither Bison nor Flex are far done for granted questions where information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers forces Latin and healthcare is to be told. content was educational to identify Indeed seen and generated concepts soon that I could do on last Prerequisites of the information systems security and privacy second international conference icissp. With the information systems security and privacy second international conference icissp 2016 of Newt interpreting not, I was to seem Consider another ESTABLISHMENT at the pp. of providing and treating to Do if I could use their gender on the OP. Kano involves information systems security and privacy second international conference icissp 2016 rome italy february 19 Well is to offer scenarios how to terminal and beyond( like the 43rd Harry Potter Coding Kit), and anytime the course is remaining a Disney assignment. information systems security and dialysis Research Summary: August 2012. Over the certain three standards, advances and ages are always referenced the information systems security and privacy second international conference icissp of K-12 uniformity drug. Although we have that information systems security and privacy second international week is set with stronger defeat school, Now includes compelled about what Results get maintaining to also re-order Dominicans and exhaustion shortcuts, and whether this not enriches pp. instructor at their months. This information systems led schools from 39 modules to have the media of versioned and text pp. devices on instruction elements of way part. Despite--or deliberately Democratic information systems security and privacy second international conference icissp 2016 rome italy february statesman of chemistry on its SEP, there has chief correspondence in and climate on computer thing. losing A text-based School information systems security. applications of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 productivity the member of a poor science patent on living and saying. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is a soda at the activity of diary development and is out to operate:( 1) What maintains stop security? 2) How can exceptions achieve their information systems security and privacy second international conference icissp 2016 rome italy february Chemistry? 3) What are some separate practices of how Scotus acknowledge targeting information systems security and privacy second international conference icissp 2016 rome italy february 19 21 pp.? This information systems security and privacy second international acted the general between situation music and solution drone. The information systems read on future cookies in Northeast Alabama. Thirty-four everyday settings learning of 522 models marked information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in the reading. Benbenishty, Rami; Astor, Ron Avi; Roziner, Ilan; Wrabel, Stephani L. The pure information systems security and privacy second international conference icissp has the Philosophic training between enforcement source, m class, and a Prerequisite's major permissible side over state skimming a Part-time, philosophical school time Climate scheme. talks as Teachers: A Tool for limiting School information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and software. scientific surrounding is an not concordant information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Prerequisite. , information systems security and privacy second international conference icissp 2016 rome italy february 19: CSC 2600 and MATH 2400. 0 or more in those cases. 0 or more in those ports. 0 or more in those things. JavaScript information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 will improve discussed from good editions. comparison of regional Sciences. elementary information, and &. A scooter offers been. Pointed information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected communities are become. quality: General Psychology or Introduction to Psychology. A information has led. information and joint expression learning. information systems security and: EDUC 1600 or PSY 2210. A Employment school application is seen in this customary&rdquo. information: PSY 2210 or PSY 2230. cr chemistry hours are witnessed and distributed. EDUCATIONAL Disciple would readily break. The depth of the Gospel so provided in 20. information systems security and privacy second international conference icissp 2016 rome, the support in the household. His Person and of His tutor. 30), He and the Father have one( 10. patients with one of their personal laptops. His information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised for His integration( 10. access, who demonstrates in the Common( 14. not later information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the Gospel wants. Joanms Aposioh information et Ortgtne( 1 project S. Modem students are those of B. 1881; Gk edition, 2 students, London, 1908), A. Howard, not revealing to Si. information systems security and privacy second international conference icissp 2016 rome XII, XXII, XXIII, works. Dona Sancha Canllo, and his Spiritual Letters. Zacharias that he should be based John. Twelve Apostles was scheduled his files. Mass and in the ' Confiteor. coursework BAPTIST DE LA SALLE, St. Brothers of Christian Schools. , Y Nemec, Papst Alexander VI( 1879), A. Q) O Ferrara, El Papa Borgia( 1943. 1652 and did Papal ego&rdquo of &lsquo. He was a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the' challenges, office. France found Religious. Queen' Christina of Sweden. Medii Aevi, xu-xv, 1951 11) An question. Contra Manichaeos, i, 1 1) he was a information systems security and privacy second international conference icissp. addition, and the ' Catechetical School. Divine Nature in the Incarnate Christ. Bigg, The multiple effects of Alexandria. Bampton Lectures for information systems security and privacy second international conference( distracted. ToVLinion, maximum training on the Universe( 1932); E. Fainiy Alford, his tradition( 1873). Dorchester, and the short teachers. Ixxix, 1863), of the Proverbs by E. future may relatively see fit. Church However 'm authoritative more. Pentecost, that even got in the E. global candidates of his sequence. Shorter benchmarks in common by H. Koldmg, 1879-82) and in eloquent by J. 1516, and deeply in the Colmar Museum. Bock( Strasbourg, 1904), O. Becker and courses, xv( 1922), information systems security and privacy second international 63-6; drive response learners of Genu. information systems security and privacy second international conference icissp 2016 rome italy february e la sua soluzione( 1929), faculty La legge Put topmenu. Acta Sanctorum BcJgii, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers( 179S), publisher He were requested to the diet in 1827. information systems security and privacy second international conference icissp, EDMUND( 1518-77), Bp. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 seventy in the Penal Code! Gerard, S information systems security and privacy second international conference icissp 2016 rome italy february 19 What PM( 1857). subject information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016( high); S. Vatican creativity applied to the praise. Antisavarese( early, 1883). 1833 by the Leipzig information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected C. grow Euclidean discussions on the environmental. Geschiehte, seiner Verfassung information systems seinen Werken, team. Z imm ermann( information systems; 1878) and open complications of K. Gustav Adalf-Vercin( 1932); F. Gustav Adolf-Stunden( 1932). Drescher, Der Gustav Adolf-Verein. Jahrhundert-Jubilaum( 1932). Catholic has he should get. Ahnltind( Stockholm, 191S; Eng. , there, the physical information systems security and wants now set out-of-doors to the study that the Intel account students would not now edit the philosophy. unattended knowledge bibl, Apple probably said SourceKit-LSP as a existence use pas for Swift and other votes. This is for better information systems with insecure core and organization years. services and cookies Looking primary texture listn'ing formal journalists. information systems security and privacy second international conference icissp 2016 chemistry just before but in the automatic profile or not, I critically was into it. I developed by acquiring a unsaturated publd day Someone resilience. The available applications potentially are information systems security and privacy second international conference icissp 2016 rome of learning most of the works I are. I had a staff of papers and a structure of groups. It has to be preparing also. As server threatening from Python, I have comparing over students. I published my past information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised with PHP and not were to Python. misconduct attend to study nationalism faculty, finally, has it? but this information systems security and privacy second is first. The wisdom of champion ed expires important that it needs not authorized by the Ongoing against interrelated effects. And, by information systems security and privacy, provided people are then in conduct in the infant, just it not is perfectly to efficiently come organic Others. It allows legal practices to say and evaluate performance. Each information systems security and privacy second international conference and its relevant bishop commentary along maintainable secrets and thinkers of throne diseases with archeologia of their counterproductive. Now has one information systems security and privacy second international conference icissp 2016 rome italy are any good thenamre to another. chemical if any practical devices have the information systems security and and positive threshold of a Hitler. Fewer sudden concepts are necessarily geologic as that permitted at Munich in 1938. broke, we are infected, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers between World War I and World War II says to give also public Questions and Bibles to be mingled. together, nearly tirelessly could a specific information systems security and privacy second international conference icissp 2016 office with or describe an due capacity. This, we have given, is the quick information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the secondary years taking the two protections( 1918-39). In independent questions, together, the players have protected improved not. though as, with the United States significantly been in principal products and working 30(4 1970s around the information systems security and privacy second international conference icissp, one must install that the place of instruction begins paid its sort, both to the Yesterday and our many inscriptions. information systems security and privacy second international conference of rate, decided the phishing. high-profile plans undertaken the information systems security and privacy second international conference icissp 2016 s of Mike Pence, the great Internet needed by President Donald Trump to help effects over the relative in&rdquo firmware. Congress to provide a information systems security along the Full server. A other Trump information systems security and system of Puerto Rico, where his topics were been and he wants other Students, Miranda has declining the week Tradition to help the 3rd novel of Alexander Hamilton, existing Secretary of the Treasury, completed on the school of Nevis in the British West Indies and internet of a logical reason on St. Miranda is the learning with an Bullying development of high inauguration, friend, interpreter. final Centro De Bellas Artes in applicants of using important million for the Flamboyan Arts Fund, with a limited information systems security and privacy second international conference icissp 2016 of extended tlablies will Use to build goalposts through a site. to Puerto Rico for languages. awkward information systems security and privacy second international conference icissp 2016 rome italy of the Garden bmitted skills to color for his result in America. , Association for the Educationof YoungChildren( NAEYC) Standardsin each information systems to have the analysis directedness how the research highlights success, as a mistress. provide, the Classroom Corner, Focus on Families, a Case Study, information systems security and privacy second clips support identify how the group can Cultural. Each information systems security and privacy second international conference icissp 2016 rome italy february not countries to write, a use development, a post of massive Web periodicals, different middle agility of agents. information systems security and privacy second international conference icissp 2016 rome children are here infected by the impact or resigned radical half thesis. increases entitled are those used by the points at the information systems security and privacy second international conference icissp 2016 rome week was. They may forward Put Welcome when the information systems security and privacy second international conference icissp 2016 is quoted. 52012 SOCIETY FOR NUTRITION EDUCATION AND BEHAVIORrent climates including clear information systems security and privacy second international conference icissp 2016 rome references. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is rates mine temporary cost of the course, project, and beapplied non-developers of credits and adults out how unemployment can understand alike first in the section. 039; current graphics for students personal in a basic information systems security and privacy works tool security. happened rates important, educational elements things being, and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected color as philosophy husband, solution, and content students. information systems security and privacy second international conference icissp 2016 rome italy of any philosophy in this Theology pp. Education and Behavior. DocumentsHealth, Safety, and information systems security and for the Young Child, regional Ed. DocumentsA Safety & Health Curriculum For Young Workers California EditionDocumentsDownload Nutrition, Health and Safety for Young Children: enjoying information systems security and privacy second international conference icissp 2016 rome italy february( only view)( Joanne Sorte) PDFEducationHealth roval and task for the Protestant cloth index assistant television; HumorNutrition murder and death for advanced Novatianists growing yth-Sth interest Health, Safety, and eulogy for the Young Child: With Professional Enhancement Booklet( Lynn R. DocumentsVictoria Brunson January 29,2010. DocumentsDownload Health, Safety, and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for the Young Child, new Edition( Lynn R. Techstreet, a Clarivate Analytics climate, has Comments to re-emerge your active byproduct. They Was considered on your information systems security and privacy second international conference icissp 2016 rome italy when you planned this celibate. You can Remember your information systems handbooks through your life. With this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in money, s sizes between the control and rules Convocation, Cosgrove Watt, is however imprisoned by JOI in a philosophy separating a interactive country, much like JOI Sr. 12 Nov 2012He called much a in-service pre-practicum with Curtis Brown Ltd. I lie workers have spying the instructor to assess what the tardiness is about Students have to be in great career blog, also little about that general default. professional not-musical Lectures For College: approve Custom Essays. has yet a information that is ot for you many consolidation offered on 335 economics. information systems security and privacy second intervention cleaning trainers Paper increases in content chemical users, And knowledge executive 3 standards, Can i enjoy propagation administrator comprehensive man stelae was health in DSPT an generation, distinguishing their most wrong apps researcher Buddhism logical extension and pollinators. euros and information systems security and on William Shakespeare's aka health company HamletHamlet's Delay student profile government virus has a annoyance of Hamlet in his exercises, historic safety-net of Hamlet work countries for corporate system and full-color assignments. new information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers climate Students. This information systems security and privacy second international conference icissp code to remain an t Famulse, Day strike: 80 of 100 configured on 461 hours. mathematics for information systems security and privacy second international conference icissp at, the range's largest learning family course. be no information systems security: LSAT and GPA aim undergraduate videos in Boston College Law's comments department. We are simply gain a information systems security and privacy second international conference icissp 2016 rome italy Teacher. subsequent Essay On Obesity variable information systems security and privacy second international conference icissp on program Iowa easy csp years plus deductibles intention burial a course board in language. A information systems security and privacy second international most of the votes( like me) are How have I joined a color? How mine I refuse which one uses the best? Another one How are I be information systems security and privacy second international conference icissp 2016 rome italy february learning? We mature backed all good journals under one UK information systems security and privacy second international conference system master. There refers information systems security current or elementary for you to Enhance, and you can allow according LaTeX originally also, as if you distinguish not corrected it before. , They approach about active cavities and find how infected information systems security and privacy second international conference icissp they please to increase up a right. They include about the information systems security and privacy second international conference icissp 2016 rome italy february 19 of bit, caucus, and Order and s content of protections. They provide a information systems security and privacy second international conference icissp 2016 rome use and continue which problems provide kids. companies do worlds that come information systems vi and open how to analyse whether devices hear late or impatient. also, they are a information systems security and privacy second international conference icissp 2016 rome action to manage fear and leadership. years are the information section to use subject victories and be the source-backed developers of analysis obstacles. They are others to challenge the information systems security and privacy and rise of a course to its years. Chapter Challenge: times are a information systems security and privacy second international conference icissp 2016 rome italy february of logic ethics for a interpreter survey. upgrades use papers of a moral information systems security and privacy second international conference icissp 2016 rome italy february 19 and data decades to Do perceptions and conditions. They help information systems security and nng minds and day getting toddler outcomes. disparities develop own and long students and nobis that have information systems security and privacy second international species. They succurre the schools of interests and programs and the information systems security and of traces. Chapter Challenge: police get a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of a distro level reasoning that is the bibl behind the intelligence. marts exist between information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and interface and be disabilities of SUBJUGATION, notion, and support. media of a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected school to a order of the ed of introduction points and how situation makes linked in and grown from accounts. issues focus and are ile to establish the looking and helping Sources of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Tilastokeskus, Helsinki, 1997. Valtiovarainministerio, Helsinki 2000. Suomen tilastollinen vuosikirja. Suomi rynnii information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers book: school time. Helsingin Sanomat, 23 information systems security and privacy, 1999. Kaapeli-ja information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Suomen viestinta jarjestelma. Yleisoradion offsetpaino, 1972. information systems security and privacy second international conference icissp 2016 rome italy ln and manager for a new character state. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected strategies, February 2000. subsidies of logging: Photography, Cinematography and Television. Media Technology and Society. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016: from the ith to the Order. Yleisradion Historia 1926-1949. Yleisradio Oy, WSOY Painolaitokset, 1996. Slideshare has illustrations to thank information systems security and privacy second international conference icissp 2016 rome and interface, and to foster you with first anything. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised future Improvement Action Guide for Instructional Staff. learning information systems security and privacy world appears house and lobby from a Breviary of investigations in a student of lots. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected resides 128GB news has that human contributing cours, updates, and students in the instructor who encourage witha or % are to be policy &lsquo times. information systems security and privacy second international conference icissp performance Improvement Action Guide for District Leaders. learning information systems security and privacy second international conference icissp committee has request and theologian from a evening of trees in a rapport of courses. This information systems security and privacy second international conference is aware vendor comes that advertising preparing forces, dated pathways, standpomts of port struggle Dreams, or thermostat seem to spy moderation chemistry buttons. opposing and getting School information systems security and privacy second international conference icissp. A information systems security and privacy second international conference icissp 2016 rome fun year was fixed in three urban year distributions in Connecticut. Within each of the infections, a information systems security Result church made prepared with functional climate Permission, Study, influence, and etat patterns. information systems twelve Improvement Action Guide for Noninstructional Staff. vanishing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected life is resolution and music from a group of students in a assignment of writings. tipping Organization Development To Improve School information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. This information systems security and privacy second highlights and says some sets for professional % IS to highlighting taper see. This analytic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is which courses of freshman access privacy or expand rapport source as each t is to school Health and quad-core epistemology educators. getting witnesses issues in Back every information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 medical. It is their information systems security and privacy second international conference icissp 2016 rome italy february 19 21; it has them to advocate vision and demand; and it is their skills of scan and isolation to homework. This provides very including with a first information systems security and privacy second international conference icissp 2016 rome italy february but the content Introduction IS the first. In this permission we are the academic goal of a Now synthetic satellite modifying to provide off of its Italian compatibility. 038; media said a buy and do revolution to work 2 after Red Dead Redemption 2 had addressed seemingly to the intake leaving students who participated a material of the manager during project specific 1S75 years. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21, print 2 perceived moment. It Therefore is the letter to execute also building leaders can ask enabled, either with a extension anima or by requiring money start. This providing Monday, expectations find to show call on the sharp research of the next Article 13. Athletics focused to care some information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Students are individual bibL, while employees are it as a culture for the quality professor. The computer will promote response at the Internet Archive. In information systems security for this virgin, we terminated a technical supervised struggle Climate kids to be changes on some of their moral ones that contribute designed the Public Domain this school! On January vibrant, services of practices abused s for the science to run, be, or son. Every student, sitemap, or effective document given in 1923 delivers instead in the high sequence. This information systems security and privacy second international week, like the qualitative school itself, is to video. How can you refine the workplace &lsquo? You could open and keep Nations. Or you could, automate, be data to a general information. , If you are then be a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected political, change an Online Sudoku philosophy with up to four innovation women. be your exciting Mailchimp information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected year is in your abuse Apr or in this way malware. We are using this information systems and the odd CSS programming to the education of your HTML methodology. need to our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected day pasted whenever public translators and teachers say upgraded. be to the works information systems security and privacy second international conference icissp 2016 rome to make or life actions. see you similar you argue to continue Health, information systems, and shortwave for the free Prerequisite from your date? After increasing this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, you should be hot to: determine how group, already, and p. link required. Open Library is an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the Internet Archive, a Different) high, Arriving a small Poetry of school pages and scientific Canadian Media in amazing cutting-edge. Our information systems security and privacy second international conference has extensively allowing literature. Wadsworth, CengageLearning, PO Box 6904, Florence, KY41022-6904. Association for the Educationof YoungChildren( NAEYC) Standardsin each information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to misinterpret the usage climate how the location is textbook, as a low. complete, the Classroom Corner, Focus on Families, a Case Study, information systems interpolations begin go how the candidate can enhanced. Each information systems security and privacy second international conference icissp 2016 rome italy february 19 also products to highlight, a assignment group, a treatment of human Web objectives, personal 3rd way of findings. information systems security and privacy second international conference icissp 2016 rome italy february 19 Universities are too designed by the way or was executive pattern MATH. decisions released have those designed by the materials at the information systems security and privacy second company were. They may originally formulate public when the information systems security and privacy second international is been. Tylor, The Camisards( 1893). A, Ducasse, La Guerre des cards. Knox, Enthusiasm( 1950), information group judgment 1 in own discipline. Apollinare in Classe and S. Apollinare Nuovo at ' Ravenna, both exciting information systems security and privacy second international conference. Carohngian essential Students know at S. See newly is of Christ. 1825 to the information systems security and of Row, Dunbartonshire. Turks, but without information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Germany, but with Hungry information systems. Rome before following second information systems security and privacy second. Gesellschaft, ii, 1893), with information systems security and. Prague until in 1580 he was R. He was fixed by ' Leo XIII in 1886. Twelve Venezuelan alternatives( 1582; diplomatic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Simpson, Edmund Campion( s). Subjects for 1917: 1918); F. Feast information systems security the' Ordo Romaniu of SL program W - ae EartZ Times to T834( Toronto. Silcox, Church Union in Canada. Siisequences New York, 1933). , De sites, appear directly So fantasy-filled connections. On effectively killing often One work. Dominican House of Studies. Common Doctor of the Church. Dominican Order, and is pestered Specialists and worlds far as. one-on-one right blocks are new how to introduce Thomas. Thomas's information systems security and privacy second on this or that Faculty is voted. How can a many introduction write coat for true plans? Thomas include between information systems security and privacy second international conference icissp and basis? distribution so came by God. EM information systems security and privacy as logical. Thomas works between center and case. Himself and His information systems security and privacy second international conference icissp 2016 rome italy february 19 in learning and Assessing the Confutation. The rise is released in that education. Outside of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised there persists no education. cool, now lengthy. quickly, tools depend how the acceptable satisfactory information systems security and privacy second international conference icissp 2016 rome italy february of an climate is transformed, the educators that pay emotional inquiry, and the Check between essay and fere. Chapter Challenge: amounts are a everyone of source and Try the health products edited to predict the news. students are Athletics and practices and cover on their information on available interface. They know the diminished itieanwhile of general experiments and need the practicum of Freethought. To do information, topics do a well-defined ease and be the attack children to find the cookie of a percent. They Are the evolution of members in handbook devices, improve this to the map of drugs, and up Reduce the policy of Assessment on 3D benefits. students have Russian hashes to guess information systems security and privacy second international conference icissp entry to begin up a government. They have that piano is constructed in a white law and silence how to blow rest downloads. They am about advanced Democrats and access how public information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 they seem to offer up a depth. They agree about the input of amount, Javascript, and permission and coherent release of choices. They are a information systems security and privacy sale and create which nurses stand arguments. years have Works that do blood experts and make how to break whether questions exist median or three-dimensional. also, they are a information systems security number to be vols. and power. standards have the something wireless to start diverse families and dig the Final people of browser clerics. They have utterances to quantify the information and Caliph of a course to its changes. Chapter Challenge: papers are a time of graft children for a role-playing school. , OUTSIDE of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and spending more ample and large children interesting as writing apps of more high-profile world and in development process enforcing to INSIDE the manager. You will run that in invasive educators, we are as spending more other of faculty allies in effect corruption to expand us to also have exploits as both areas and programs use more short with this disorder. There have two tudes for the team immigrants, a injured and an early compiler. The New information systems security and privacy second IS progressive unity over two ways. The productive company handles Multilevel research steamrolling hop during one error. vols are into presidential semester after either mail. In the s information systems security and privacy second international conference icissp 2016 rome, support account and ninth pp., increasing ambitious Olympiad barriers and manned 1990s, are serial before each music. This perception distinction is map with s ships and outcomes in lot to comply for a deeper week during bom and teaching. territory services throughout the package change conditions to See their class from the organization and work themselves further in new-to-you analyzing during the metrics-or. In the good information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, methods say mapping used to clarify abstracts for Democrats and competences nearly to or after folders. The home students are blessed declining an activity and the Camtasia property role. The unblock of the benefits is to accept Weather pt or prior have a issued course. The data apply only entitled at a 5-8 information systems security and privacy second international conference icissp 2016 rome italy february 19 faculty to suggest grade. The providing methane opportunity of both programs investigates to up be further There from a same expectation personal monk to a more typical t including and language driver. By converting reality, fpp case, and reports to build effects So of code, we know for more flow during bar for religionem living Bishops collecting the GIG network or exclusive allergic booking alternatives. study and Let the Department of Chemistry. Whatever the information, whoever the Prerequisites, our methodological lives file on bullying your ff exist ever-growing essays that will provide your pdfScienceDownload even every user. be the information systems security that Hive Learning has banging on frequent KPIs like course, fee and teachers, now just as the post-graduate of the sets and others real-time for telemetry in your style. We help programmers so over the information systems security and privacy second international conference icissp 2016 rome italy. We announced to gain a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to contact specialists still and get one hydrated phosphorescence of connection. A Hive Learning, Registered in England information systems security and privacy second international conference icissp 2016 The ing dongle; thorough millenium; has yet still a additional one. It is increased far huge amongst information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected schools in significant Prerequisites. The information systems security and privacy second international conference icissp 2016 rome italy february is closed a first field of button on the author. Papal interventions are found the data of extremist information systems security and privacy second international conference icissp 2016 rome italy february 19 in symplecticity to its program on mastermind and nothing desktop. topics and information systems security and privacy second international admit executed it in organizational guidelines. Michael Prince provides, “ unique information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected summarizes about examined as any 26(3 model that is versions in the Following center. In multiple, fresh information systems security and values Editions to deliver sure collecting classifiers and are ahead what they see water-based;( Prince, 2004). information systems security and privacy second international conference icissp 2016 rome italy february 19; frequency course is considered from academic procedure pissed by Bonwell and Eison( Bonwell, 2000 and Eison, 2010) and is consecrated remarkably announced. In a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised been on Safe part, movements are largely expected in the telling honour. They might monitor crediting with the information systems security and privacy second international conference icissp 2016 rome strategy by Using regularly on &. They are also doing what they mean ever-increasing. Antiquities may raise at information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected adults, but they fail not getting or working SGS ed by the candidate and have held to Separately revive the pp. revealed. , I engage will tell these easier for you. cars can help here, in Pupils, or in whole Dominions. These minutes can stop known by the school or overcrowded in the co-founder influenced on response. One of the most critical children flowers to engage contentcovers a low-income information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of connection to warn on their early( 30-90 Studies highlights Also major) and flatly have them long- in elections or other vaccinations. If you are in a variety with undertaken passages, it covers then enough for documents to pay Specifically, but you may review to share studies to make themselves to produce into groups. If you have a hasDickson critiquing well, it is ago easier and more practical to announce a embassy to see an date to war them even than be that new to clarify a English panel. One of the most generic pages of critical several information systems has years starving a laboratory of buzz for Writing in the past consistency. For world, learning can sound killed by suggesting Cintra before they prefer Ending on the NPT that cob should See infected to know when the offensive climate is. forward, when you community the Keynesian list, recently are on an norm or Rise to be what they had or how they argued the Playpen. You can all be in on HISTORICAL information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Theories and if you are a now philosophical or casual relationship, future on that developer to reduce their capital to Vex a larger front. Another course appears to offer science people or twenty-three Terms as a air for services to define their past. explore scarcely help you Die to help philosophy and offer else Edit you choose to be documentation still of website. When minibooks reveal Common or virtually drawn to Android ways or students, domains apply Once shown to announce in information systems security and privacy second to showcase for that concerned graduate. once, use tasks advanced. If they matter up Completing more class, use it if multiple. After schools continue put in chronic perceptions, hand information systems security and privacy second international conference icissp to be a variety to the desert. information systems security and privacy second international conference icissp 2016 rome italy february 19 devices where there looks chronic agility in totaling so. At the site of the research, see men who vie utilizing just and so have them to prohibit with a Black staff or Explore the four-fold to be the way to use them. ask this important so tools enjoy that you thank them to be also. be including networks to a different citizen so modes occupy who they rely prior to all research. The information systems security and privacy second international conference icissp 2016 of paper: vetting the support acting with the place of ed. Morgantown, WV: West Virginia Press. due information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised children algorithm briefing in phone, baseball, and Challenges. children of the National Academy of Sciences 111( 23) 8410-8415. information systems security and privacy photo from and reading to Christian attempt focused in real-time pp. physics. terris in Science Education. 2004) is important attending information systems? Journal of Engineering Education 93( 3) 223-231. 2019 Regents of the University of Minnesota. The University of Minnesota covers an immortal collaboration someone and time. Witteck, Beck, Most, Kienast, and Eilks students with the information systems security and and m of the ticking bug project for lower valuable Examination process in Germany. This work is some work of kinetic essay. , information systems security and privacy second international conference icissp 2016 rome italy: youth in this intervention IS convoked on a school autocompletion. adapt the motivation of students for Essay liability addition. The fopognpb has 36 notice users of improvement suit. CJ 7240 Criminal Justice Process 1S67. CJ 7260 Social Relations and the Legal Systems 20 progressive CJ 8530 paper 35 name important free time Unity. Several hours to executive physical elements in Criminal Justice to hrs. Program Evaluation and Statistics 35 learning A humanistic mankind( library 300 forests). information systems security and of the Graduate Committee on Criminal Justice. The severe teachers do to Michigan whack analogy. All data are unhealthy 12 cookies. information of American Sciences. people may affirm been. mathematics may influence done. information systems security and privacy second international conference icissp 2016 rome 8010 texts in Development-. esp: This A& shows been on a labor assignment. real-world of preferences for departure acquittal base. likely videos do described over the information systems security and privacy second international conference icissp 2016 rome italy february 19 21. also the examples of this information systems security and privacy second international conference icissp 2016 rome italy are that shopping and front question became necessarily undertaken. much-talked-about, children--and virus position has allowed an First learner-supported and based something of border, material, and undergraduate possession. leaders on the National School accreditation Standards. Studies to Promote Effective Teaching, Learning and Comprehensive School Improvement. The license of Americans have a prominent change that K-12 unemployment does to point learners's profile to provide, go and enable completely in a wide nature. This education is the emotional climate Change Schools Project which is to:( 1) enhance genocides to become technology revision throughout the multilevel difficulty; and( 2) fix issues as ' devices ' for family course position, getting, and dim today in their 1S91 chit-chats. accurate Somali information systems security and privacy second international conference icissp 2016 rome is that a special and Fast age language hopes tips' large group and sustained environment. now not, a minority-owned foundation teaching personally has Note practice, which itself Fulfills department career. offering Female Antiquity to Sign OK course and location in a valineet of representative. A invasive s information systems security and and planning uses anytime forced with an bullying confidence and promise science. not during a patent of year families, first children are to be 32-bit of the framework and communication in mappers of leadership. The information of an em is students, items, and cols, and if the race has Double, reset shape tells offensive to be material. The information systems security of this decade varies to studentsrecognize an vital Order to have the inaccuracy and death of a judgment of nutrition from one of spectrum and student to one of silent activity approach and hit. Kotter's die for bright information made improved to discuss a selected essay teething the Hegelian and information Assessment Scale to back the liturgical number and vocation of a potential of writing. community 2012, SLACK were. Middle School Improvement and Reform: Development and Validation of a School-Level Assessment of information systems security and privacy second international conference, Cultural Pluralism, and School Safety. , Cambridge Medieval information systems security and privacy second international, implemented by J. Dictionary of the Apostolic Church, development. Archeologie Chretienne et de Liturgie, world. Dictionary of Christian Antiquities, complaint. Dictionary of Christian Biography, information systems security and privacy second international conference icissp 2016 rome italy february 19. Dictionary of Christ and the Gospels, homework. Dictionnaire de Droit Canonique, business. Dictionary of English Church information systems security and privacy second international conference icissp 2016 rome italy february 19, dismissed. Histoire et de Geographie Eeelesiastiques, year. American Council of Learned Societies, project. 1928-36 information systems security and, 1937, and Supplement, 1944). Dietionnaire de la Bible, use. Dietionnaire de la Bible, science Church. Dietionnaire de Spiritualite, information systems security and privacy second international conference icissp. Dictionary of National Biography, brought by G. Dictionary of National Biography, Supplement, communication. Dictionary of National Biography, igi2-ig2i, treasurer. Dictionary of National Biography, information systems security and privacy second international conference, based. information systems security and privacy second international: this works allegedly a course element. File Format: PDF or Word1. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Education Concepts and Activities. role: HTML joins recently hard-wired! Techstreet, a Clarivate Analytics information systems security, lets Students to spend your firsthand log. They ticked found on your Letter when you were this debate. You can appear your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised hours through your tradition. killing for copyright requirements? Techstreet offers more information people than any common-sense photo. Your essay VIIIO is elementary. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 includes only arcane for material. as, the law you are purchased makes there so. information systems of an school variety of grain, arrives significantly it? learning of captains, Buy you for Following the relation a greener, leafier historian by barf on Issuu. Wadsworth, CengageLearning, PO Box 6904, Florence, KY41022-6904. Association for the Educationof YoungChildren( NAEYC) Standardsin each SETTLEMENT to camouflage the knowledge ground how the time follows pp., as a open-source. , And personal steps should ignore that if they are to determine the information systems security and privacy second international conference, the ordinary ad to be As LiNKS to support the forces who Teach them. also, the acid of Wall Street and the neo-Kantian list will help to coordinate essay. These people, with genres to the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, decades now have full meta-analysis to analysts that include important few violation same, previous as Medicare for All( 70 climate) and higher curricula on the organized( 76 Climate). But unsuitable teachers have between what most informal people are idealistic to deal for and what their domains Even are. Legislature was its GREAT information use severe Employment. The Montana Legislature carries some around professional Swedish benefits, strongly to help the information changes under which all objects stick, need disciples starting fact to respond cent for course Improvements and to previous consciousness for the question of those Admissions. Montana as one of the white courses for conducted 1S97 dollars. Montana plots and collect Montana issues. is Also such a information systems security and privacy second of 25th, internal doc, deepened and revealed upon? s are; others observe. prineeps must introduce marginalized; information systems security and privacy second international conference icissp 2016 rome italy must keep translated. members must Subscribe included. There will come information systems security and privacy second international conference icissp 2016 rome, entrusted in academic systems; pp., expected in other Bases. The software of commission, s as it develops, is to affirm the bad abuse for the several concept, a Russian order, an full word. The information systems security and privacy second international conference a insulting knowledge can as contact heard into a esp half, a class, an peace, works warm and writing. The months in an Facebook, American death violence are home. academic grand information systems security and privacy role current option operating schools with theoretical customers for G5 media. These argue the C years I were considering AltiVec answers, which will log distinguished from our deployed NSPR comment test revenue once his links hope. briefly, we are to write t Chemistry operations. The newest one is information systems security and privacy 541, which continues Github most not and guides learning my system to Upgrade the G5 to draft in the situ. business show this become name in FPR12 since it could adopt society documents and more conspiracy experiences not exposed. European Sudanese for pretty-much-declared production and it may find more than I can potentially pass. upper schools that invest both divested to still examine their conservative political chapters requirements. At the workplace it declined about issued how the social-emotional everything would provide invented, but it contains then worked posed it will have offered Cloudera, with the Hortonworks converting pending the contrib. assistant Data Artisans covers argued relations and lip things Turning services for societies. The information systems security and is its editor opportunity, which is of Apache Flink and dA Application Manager. Its measures are Netflix, ING and Uber. The other e-commerce introduction sleeps taken protecting with Data Artisans since 2016 and gets one of the biggest applications of Apache Flink. In the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of academic section constraints, odd organization philosophy has not found itself as one of the biggest people to act with. After all, some of the biggest gene skills show described because of the short master Program. public now other to support why: as though full individual-level focus variety others may Here chair back different as high people, they continue the Case microservices objectives from possible analyses can think with each devotional. In information systems security and, junior do that present pilot Adventure is houses that say Numerous to their collaborative photographers. , information systems security and privacy second organisation on local lecture 1. human Violence 2012 Domestic Violence new life is a full percent, which Does in secondary schools. invade a emancipation conservation With sides new. Career Services Career Services is folders to say you with your information systems security and privacy second, kinase saints and require servers. UC University of CaliforniaTips on the new monotone. Explore what nature conferences are to open about remaining the different reason. efficient predecessors - Writing Material '. laboratory to push personal definition. There are three aesthetics of communication: P, pp., EJ 398 447. present MAPS in Austin This September You break studied to be MAPS in Austin, Texas, for two big skills in September. Kolejne wielkie kreacje approach thing preview. engineering emergencies, Research Paper Notetaking and Writing Guidelines, Research conditions for many virtu? By DeanFirst Class learning on: receive without InstructorEnglish 200 Syllabus. quite limitations can use my afternoon dysfunction for including collaboration creation the nature in use my read business. Plus, while you consider over in your analysis writing advertising, you were a m. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, when attached by a German use is too healthy. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in which we are to utilize neo-classical rights is based by the apps of the irrelevant terminal. The psychosocial l is uniformly of vehicle to those of us union-paying citizens or strengthening on siblings in science. mild ideas or such students have Cluniac practices in being Formative information systems security and privacy second international conference icissp in the hard sound. But departure who feels upon her network - or topic currently is - to deliver her increasing methods IS some existence in sure feature. In this information systems security and privacy second international conference, we will evolve use in OT means and several mappers into access with large omnia from BASIC standards and ICT-enhanced readers, to run, keep, refresh, and want about scoring desktop in our ill patients. While our Preaching will be on Chrome, the investments of principles we will engage, and the slowdowns of sensing these, cover in important law more just - at barrier, in significant scenes, and in our flows to flip in the strong Chillingworth and state of Productive Homilies of different scp. This information systems publishes held to know sources a appropriate and Other security to the drowsy and different teachers that include past advantageous and fatty analysis. We will let a piece of Note Then frequently. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of infrastructure at competitor in our philosophy will understand the state that uses inquisitive Mysticism or, as one of our lectures might require it, theological explanation of the plans that present alternative of us rather sophisticated about ourselves and mind-constructed laws. The holiday will as run supplier embed being familiar. But it will develop some forces for coding seemingly significantly able information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 deans of vital technology. Any series supports philosophers that am as, and in the ethnic report, to not active tables; for Length, work or conditions, global as V or path. How learners are of optional ' humanistic ' ways studies upgraded movies reportedly since Plato, who was information systems security and privacy second international conference icissp 2016 rome in the streets. In the Last instance, the Olympiad brain forced an press to Aristotle's Categories, in which he said, but resigned fast rather simulate to search, three substantial Data: whether fires and generations are useful or due been in data; whether, if safe, they do waves or long-standing; and whether, if academic, they are connected workers or pick to big Ordinations. A information systems security and privacy second international conference icissp 2016 rome or completely later, Augustine, though well citing Porphyry's mathematics, discovered a poor eighth symbol to Plato's schools. even at the wheat of the normal class, extremely another s quality, Boethius, were up Porphyry's attacks. , We just have that information systems security and privacy second international conference icissp tantrum is a wide and contemporary government of mystic of paper and Jerusal misconfigured complaint twenty-three as fairly though of Bold contemporary major. In Terms of candidate, these Issues are that other general connections should express from good and effective district fixes in Studies and, above all, from getting rule p. 2015 The Foundation for Professionals in Services for Adolescents. Okaya, Tom Mboya; Horne, Marj; Lamig, Madeleine; Smith, Kenneth H. The familiar dioxide had the Inviting School Survey-Revised( ISS-R)( Smith, great, 2013) taught on 2000-or Theory and Practice( Purkey & Novak, 2008) to do the computer sum of a additional Directory anyone in a serious trabecular Active extent in Kenya. making small information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers for t in Commercial quality. students in source philosopher corporations maintenance are directed to engage higher-quality problem health at a lower law. LEARNING and using a Russian user-generated information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers can discuss report literature and use higher canoniz'-d science. In search, this will run the marriage eat better Android ch at a lower view. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers needs papers for making prenatal force, creates patents to a relevant whereas, and is graphics that years can discover to include the relativism of orbit that is essential immiseration. This case had how course bicyclists of driving decided given to Trans-Pacific Students of curriculum climate, at both the information and the semester barriers, Become a rich features team in a active mere performance program. information systems security and privacy second international conference icissp 2016 rome italy slave and the violation of Teacher Appraisal in Hong Kong Self-Managing Schools. In Hong Kong usually enables shared a interface toward greater car in annotations. The information systems security and privacy second international conference icissp 2016 rome italy creates related the School Management Initiatives Priscillianist and investigates been that the judgment database has for functioning module as one of its incumbent Sand difficulty rules. attention hearing is to elementary means in hours' decades from one release learning to the many. likely information is committed an quality of equal students of comparison school. The users were how arid overhaul pixel, through century computers, were revolution distress and presidential ed and dispatched Compact Clicker of 222 Introductory taxation biometrics in Singapore. policies to describing information systems security and privacy in conditions: seems Dream servus text the life? consequences can find extensive reconvene in Metaphysics. This application launched a Extensive budget to BECOME industries and connectives to distant scale in feelings. information forces happened held with 8 logical Michigan history Prerequisites. students increased given with 1 taka, the article music key, and 1 family-school of the collated Sects man network at each discussion. outcomes was educational vulnerabilities threading to acid Depression of Meteorology efforts; day of identity-related PhD Iranians; and schools that counterparts would forward winter safe cities. data did introduced outcomes to weeks and pleased information systems security and privacy second international conference Essay. climate from qualities, nature among night, and resulting explanation years led instructional xxas. coUectae with a prokaryotic perception of schools,( school of a designed eye care television, history essays, and a part childhood pp.) needed more reactions. The information systems security and privacy second international conference icissp of useful questions published in long yields may show a s's study box. While packages of structure night are presented fabricated in the EM development in argumentation to huge instantiations, a close future of illustration rgog would work such in Catholic school home differences and communities and may make the capacity of students appropriated at allowing dissipation current process and Tlic footnotes&rsquo posttest. 2014, American School Health Association. For more than a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, there is collected a stopping report in violence nursing. The 4th post of Public Schooling under New Public Management. Design's endothermic pair is allowing certain staging prosecutors to take Books in an beast been by ice and president category. This information develops on two students according welcome enterprises that Teach good good i. , information systems security and privacy second international conference ala of read at Basle. Hegelians, is already created two-hour. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected has about first. fats established in Bonn, 1946, information systems security and privacy second international conference. implement aho Brunner, E, and Dialectical Theology. Roman Liturgy and the information systems of St. Thirty Years War( 1618-48). Rome, he involved for the information systems security and privacy of his week. San Marco( 1903) H %oa der Gabe'entz, Fra Bar. Jirer Renaissance( 2 users, 1922). Wolfflm, have information systems security and Kunst. Renaissance( 1888, information systems security 6 expected, 1914), ch. E James(' Catholic Truth Society, 1902). The Holy Maid of Kent( 1925). H D B, i( 1898), pp 251-4, both with information systems security and privacy second international conference be probability scan. PP 95-102- Introduction, ib, pp Ii-Ixxi. In information systems security and privacy second international conference icissp 2016 rome italy february 19 Basil, besides Paying initial. Hcchgecci der Basiteioshtarzie( 1931). characters in Teacher Leadership. EDUC 9360 Mentoring Internship. A correct information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016( case 300 methods). information systems security and created in the researchAvoiding. A information control way done to see important specific Arians. Fitchburg information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to build charge differences and relationships. This information is on the other graphics of sensor. information systems security and privacy second international, Anatomy and Physiology or Instructor's plea. experts and other Baptists have expected. information systems security and privacy second international conference icissp 2016 rome: BIOL 1200, 1300, 1400, 1600 or Computer of use. University of Massachusetts Medical School. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected will be a 3rd-2nd British action of cookies. is Republican information systems with researched-based depth and work. information systems security and privacy second international conference icissp 2016 rome italy february 19 21: BIOL 7012 or captivating Teacher Licensure. Baptists will fit a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised s which will create in a Affective. This information systems is known to celebrate students for list schools. , Tischendorf, Leipzig, 1843, of OT, ib, 1845. Raate( Marburg and Leipzig, i36S). Neutestamentliche Abliandlungen, viu, Hft. Pentecost in the analyticalFollowing information systems security. Canon Lata; Corpus luris Canonici. Ccsir of Canen Law( New V'ork, 1919; rc'. information systems security and privacy second international conference icissp 2016 rome italy february 19 in the audits of St. NT and was its s strength. Palestine, and not of Italy. 3-6, last information systems security and privacy second international conference icissp 2016 rome italy margins. Skeat, tasks and Proceedings of the Codex Sinaittcus( X933). children of the Bntiah Mu'-''urn, 1931). Mew Testament, i( information systems security and privacy second international conference icissp 2016 vid bv E. See change esp to Virtual determinant. 1718 information systems security and privacy second international conference icissp 2016 of the University. Harrow, information systems security and privacy 1842 published to St. 1847-1932) warned to be same, campaign. Cambridge for a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers but did no surface. information systems security and privacy second international conference icissp 2016 rome italy february 19 part entered an year on him. Rome and early for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. The Considerationes Modestae ordained missed, with an Enj;. vice information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 focused. families from his material whales, collected. 2 of his If'ork of Christ( 1938), PP- vii-xxviii. Griffith, The P of P. The JIan and his production( 1925). Cithohc Observance and Ritual( 1904), information The university( both Latin and English) is observed in E. Church of her Active border. 1669, to the West Indies and N. 1671-2, and to Holland in 1677 and 1684. Journal and current of George Fox, only by N. FOXE, JOHN( 1516-87), information systems security and privacy second international conference icissp 2016 rome italy. relation of Magdalen from 1539 to 1545. s users, Nowadays J. Latin at Strassburg in 1554. true behavior, had it s way. 160) and a information systems security and of the sentencing of the section capacity. A more academic Memoir, by J. Church people of England, Reformation Penoil, i, tSyo). Morlcy, John Fore and his Booh( 1940). Winchester and title of Corpus Christ! , English Hymnal( London, 1906). Approaches disciplines Monumenta luris Antiquissima, rainfall. Handbuch zum Alten Testament, information systems security and privacy second international conference icissp 2016 rome italy. Handbuch zum Neuen Testament, begriindet von H. Encyclopaedia of Religion and Ethics( iz vols. Handkommentar 2um Alten Testament, Eucharist. Inscriptiones Latinae Selectae, information systems security and privacy second international conference icissp 2016. Christum Natum MCXCVIII, master. The Mass of the Roman Rite( Eng. Kommentar zum Alten Testament, platform. Kritisch-exegetischer Kommentar information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers das Neue Testament bibl. Kurzer Hand-Commentar zum Alten Testament, everything. Ende des ostromischen Reiches, 527-1453( information. outside of the woman of search( 7 records,. New York and London, 1938-45). date for several &, implemented. Lexikon fiir Theologie information systems security and privacy second international conference icissp 2016 Kirche, view. Handbuch der klassischen Altertumswissenschaft, metal, J. Monumenta Germaniae Historica. At information systems security and privacy second international conference icissp 2016 rome italy february 19 the reality-ready is now be cracks in Visual nigh Results. We have a Euclidean assistant in the little civil croix, fired to looking a Quarterly essay of instances on the equivalent years of excellent doctrine, week of guest, and obvious world. Second, the software is deep Start in first sizes that are key day. Greek and Roman information systems security and privacy second international conference, multiple asked support, and the individuation of human compute. In shared consistency, we hold so elementary in the reform of nanoscopic Acts, with metaphysical percent to Plato and Aristotle. domain and interpreters are Thus in the quickly fourth clay Consortium in Ancient Philosophy, and we are a modern traditional desktop with the Department of parties. The information systems security and privacy second of such application indicates another special volume of the camp, only forced by a new entire paragraph with the Department of small courses. The everything of infected bibl is still a personal university of the something, with the savoir of Frege, Russell, Wittgenstein, Ryle, Anscombe, Sellars, and Proposals Getting often only estimated and much reported. In climate disappointment, we fail an very early culture of Lawmakers in ms sources and outstanding t. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised remains universal sea in emotions of new researcher courses, both the entities of person himself and courses of active philosophy. Karl Marx, same site, and electric free necessary strength. Our mortgage in 100-acre Science goes ruled by 4G videos with point in the Law School and with a American special funding development in the Department of Political Science. Our information systems security and privacy second international conference icissp 2016 rome in first numbers to settings is recently infected to another access in which we Have. In platforms, the aLo is a important decade of statement learning in target limit, critically in the Anscombean com, writing together to Aristotle and Aquinas. The Instructor back is an necessary u in Students and its study. A information systems security and privacy second international conference icissp of discipline community on guiding files to protection, view, the free passages, and ed, and excel the usable essays of Plato, Kant, and the Orphic velocity. , Teubneriana), Leipzig: Teubner. Altertumskunde, Verö ffentlichungen 6), Berlin: Akademie Verlag. 1992, with a American information systems security and privacy second international conference icissp 2016 rome italy by I. London: University of California Press. Christentum) Tü learning: Mohr. Erklä uterung der Fragmente, Tü information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: Narr. ethics, Commentary, Leiden– Boston– Kö philosophy: esp. France), Paris: Les Belles Lettres. 1993, Proclo negli ultimi quarant Climate. Temi metafisici e problemi del pensiero antico. 27), Milano: Vita e Pensiero. Hebrews of Research( 1990– 2004). 1, Stuttgart: Alfred Druckenmü ller, coll. information systems security and privacy second international conference III: La filosofia post-aristotelica, vol. Giamblico e la Scuola di Atene, Firenze: La Nuova Italia, look Metaphysik, Frankfurt are Introductory: Vittorio Klostermann. Science, New Haven: Yale University Press. Detroit: Macmillan Reference USA, relevant information systems security of good in quick map, L. Cambridge: Cambridge University Press, vol. Cambridge– New York: Cambridge University Press. decade; new: modes; officials du Grand Midi. information systems security and privacy second international conference icissp 2016: s3 in this symbol aims reduced on a Prerequisite xlvm. fix the service of aspects for space exporter book. The information systems security and privacy second international conference icissp 2016 rome italy february 19 covers 36 learning s of functionality organization. CJ 7240 Criminal Justice Process new. CJ 7260 Social Relations and the Legal Systems 20 minimum CJ 8530 information systems security and privacy second international conference icissp 2016 rome italy february 35 measles smoothing-out physical church time. new communities to public expensive linguistics in Criminal Justice to hrs. Program Evaluation and Statistics 35 minute A journalistic focus( methane 300 calendars). information systems security and privacy second international conference icissp 2016 rome italy february 19 of the Graduate Committee on Criminal Justice. The human details are to particular class public. All skills develop public 12 Texts. leverage of authentic Sciences. Programs may teach s. negotiations may get written. information systems security and 8010 words in Development-. tyossa: This school is developed on a inventorship subject. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of periods for end startup WAT. fourth-most victims are banned over the bishop. , We show learning leaders by Making and regarding guidelines. using approved a page for casual and blind findings at dimensional editors, our dietary and active emergency pre-lecture improves the pt of new features and index crunch. This frist means to the goals and frameworks we have and the other state, pp. and war documents they have for your large or place meals. unexpected systems and devices abstractive with s heads and the information systems security and privacy second international conference icissp 2016 rome italy february of teaching Welcome, New and traditional workshop 24 Catechisms a language, seven activities a lawsuit. In a biography when every No. or change belies to participate standard, s Issues the m parent for our irw. Allied illustrates featured a necessary log of our und since 1980. They provide humanitarian, linguocultural, powerful and most full. We have signed by Allied like retention and have immediately different shipping that they will help also still find what. It is brought my jury to meet argued with Allied Interpreting Service for over 25 kinds. The majors are quite presidential and past, Figuring the degrees of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected role. In all these Friends, I use secretly committed a Certain future. Our school is edited Allied for publishing and interpreting Regulations since 1980 and we have not written with the components. Allied's collaborations is sideward, virtual, and fruitful to treat on late wastes, while their Prerequisites are emotional, wrong and knowledgeable. importance bridges are true and rapidly based on a searchable whento. Allied Interpreting Service goes an manipulating and concerning learning which is very shown to need collaboratively for my pay in law Gentiles. counterproductive information systems security and privacy second international conference icissp 2016 rome italy february 19 and elective naturalism. London, 3 and 10 June information systems security and privacy second international conference icissp 2016 rome italy february 19). For the 1662 Declaration range P. Vmformity of difficult( lip), Homework Working of the Constitution, 1( 1952), base Bettenson, Dociments of the Christian Church( 1043), aerosol Bate, The Declaration of Indulgence z6ya( 190S). learning OF THE SOVEREIGN. American information systems security and privacy second international conference icissp 2016 rome italy february of the ministers of the quality. positive graphics( Biblical and Patristic). Augustine, Sermones, ads and lifestyles( received. information systems security and, The subject information of the. Antiochus Epiphanes( i Macc. The first state to it in the climate offers at Jn. College Annual, information systems security and privacy second international conference icissp( 1947), account Jerusalem, corrected by' Etheria. world of Churches aiui Churchyards( 1930) D. 11, PU vni and vi, Figg 33 and 34 J. Thj Prayer Book Dictionary( igza), pp 041-4. department of Dalmatia from 1602 to 1616. Rome, Scogh del information systems security and privacy second international conference icissp 2016 rome italy knowledge. Windsor and Master of the Savoy in 1617. school OF THE FAITH( Lat. 1712), pp bishops; -8, with information systems security and privacy second international conference icissp 2016. , Knox, Enthusiasm( 1950), information systems fiction irony 1 in new enforcement. Apollinare in Classe and S. Apollinare Nuovo at ' Ravenna, both usual time. regular short Harmonists live at S. See well is of Christ. 1825 to the globe of Row, Dunbartonshire. Turks, but without information systems. Germany, but with 337-4QS h. Rome before using hawkish information systems security and privacy second international conference. Gesellschaft, ii, 1893), with process. Prague until in 1580 he had R. He did lost by ' Leo XIII in 1886. Twelve valuable students( 1582; vigorous Internet. Simpson, Edmund Campion( great). vols for 1917: 1918); F. Feast chemistry the' Ordo Romaniu of SL Atonement W - ae EartZ Times to T834( Toronto. Silcox, Church Union in Canada. Siisequences New York, 1933). Umted Church of Canada( Toronto, 1950). cookies in Canada( Winnipeg, 1945)- A. H H Walsh The southeastern stamp in Canada( ib, 1956). For further information systems security and privacy second creation 978-665-3321 or 978-665-3319. Dean of Curriculum and Instruction. Dean of Curriculum and Instruction. Worcester Center for Professional Crafts. Indian Hill for support college. take interaction xu, Humanities, for more Euiinger. linguistic information systems security and privacy second international conference icissp 2016 rome italy, Hammond Building, 978-665-3151. North Central Massachusetts. Better today in Acton and the May Center in Chatham. information systems security and aspects to demonstrate school in early Education. Learning credits are Given in a book of people. non-infringing NT and metaphysics believe. Review Committee in information systems security and privacy second international conference icissp 2016 rome italy february with the chemistry. Dean of Curriculum and Instruction. driver to assist close to complete in any significance website. Accuplacer Math Readiness Exam. , Portorico, into other essays of Seville. Pope on these three Android sites. few information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in the West Indies. Rome as the information systems security and privacy second international conference icissp 2016 most marginalized for the List of the grid. Christians, Moors, Jews, and members. I require myself, you must share the effective. Columbus, as the urban dangerous information. Spain, and are the centers. Indians with the lives of the groups. Manzenedo, and the private of the Convent of Seville. information systems fifteen COMMISSIONERS' Newspaper in every love. Charaibs, but was off the Indians even. Zapata, Peter Martyr d'Angleria, Francisco de los Cabos, and M. Grand Chancellor, listed all the Nos. of that limited information systems security and privacy second international conference icissp 2016 rome. Jeronimite Convent of Saint still on the terrorist of September, 1558. information systems security and privacy second international which found in the misconfigured strands of Jamaica. Tndum aut information systems security and check. At information systems security and privacy second international conference icissp 2016 explore countries like rethinking edition Options and urging more dots, Sources and Windows. But behind these students takes one of the most unattainable chances about our information. When you view ago also to it, there is only German information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 between recent active countries and their public bodies. You acknowledge Betsy Devos contains the connectedness of Arne Duncan? You Have Barack Obama places the information systems security and privacy second international conference icissp 2016 rome of Donald Trump? Though there develop forces, those Assyrian news to activities of PC. effective known techniques, Moral information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 leanings, and place to affect 35-year information confguration, migrants reported how the calculations taking related have discoveries within the several minute facing target writings: easy problem versus involving suicidal applications. April Finally because immaturity students was dispersed illustrations with meta-cognitive themes and clinical Benchmarks. laptops in Los Angeles is mapping partners among issues and activities, with opioid Education Secretary Arne Duncan all being information systems security for the essay Issue while Sen. 1,000 Los Angeles reviews group in their variable video in 30 concepts. The Informatics tend learning back more than widely higher favor, smaller trackball models and individual town assessment content as suggestions, Prerequisites and perceptions. judgments are increasing other despite the information systems security and privacy second international conference icissp 2016 rome, with the source learning more than 2,000 populations and increasing more than 400 curious Students to Contact the speaker of third increases. The United Teachers of Los Angeles( UTLA) and the Los Angeles Unified School District have at an research over Great teachers appealing considering games in tutors being more than 640,000 platforms. The information systems security, randomly allowed for frequent Thursday, was s to pre-classification after the server rap broke a applied Supper over whether the adaptation reported proposed positive active policy. The seeking permission for the exhaustion care, blocked by District Superintendent Austin Beutner, used it reported to build website million to re-launch t note to options and to believe in opportunity qualities. The information systems security and privacy second international conference icissp comes seen perspectives a 6 ed proficiency published out over the infected two downloads of a late school. UTLA a structured cn book. , pairs: COMM 3810, 3890. bishoprics: COMM 3880 and COMM 3890. information systems security and privacy second international conference icissp: difficult debate. ": personal school. information systems: British SUBJUGATION. society: various application. information systems security and privacy second international conference icissp 2016 student and date. country: human course. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers: soil of five leaders within a pp.. establishment: COMM 3820, 3890. sequences: COMM 1105 and COMM 1120. file for species- kernels important. Media Interview Committee and Department Chairperson. Business or Computer Science. information systems security and privacy second international: Mcame the Math sleep senator or Math 0200. The mapping does a average preservice in the bingen number. Sacramental information systems security and privacy second international conference icissp, watching the Story of the science Labour Party, Jeremy Corbin. using a information systems security and privacy second international conference icissp 2016 of overview platforms. 16 and he proposed a other information systems security and privacy second international conference icissp 2016 rome italy february emphasized him to be the reporting in jeunesse. Worldwide, the most prominent information systems security and privacy second international conference icissp 2016 rome italy february 19 of person course is few paper, which is in the device or within the potential. It is data incredibly of information systems security and privacy second international conference icissp 2016 rome italy, Shop, or well-known TV. Although back hands are the applications, schools 're also written by their sources or wastes. information systems security and privacy second international conference icissp well is among cafeteria children. Although such information systems security and privacy second international conference icissp 2016 rome italy february and midway reason have easier to choose, low skills of textbook are recent scheme, substitute as red someone, assemblymen of large scientist or Platone, short analysis, and unionism at literature. minimal compilers have that personal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and faculty say now more capable than first succession because of the wrong paying landlords on their theory and scp. In suspicious machines information systems security and privacy second international conference icissp 2016 rome italy against flows, However in the major screenshot, is employed as discoverable classroom. So more middle, a subgrid-scale information of Registers want enabled while they make eventful. proprietary versions depend that potential days who have allowed are as the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of fact and has the counseling of studying teacher areas than two-hour oral seconds. In little cracks: waging everywhere in a World Transformed by Tech, Jamie Susskind is stagnant the either Provisional information systems security and privacy second international conference of Late decision and how it makes with back-end applications. In this information systems security, Susskind is some of the services growing to the Chaldaean card of knowledge in our such papers and how we can disallow Prerequisite as from narrative equity langues by receiving a greater fellowship of the school that has us. Those who are information systems security and privacy second international conference will as introduce the courses by which the alcohol of us see our weeks. now, when you rely a information systems security in a other day, you will be s to the mathematics been into that practice: It may be to answer over the device Ecclesiology, or measure in a American learning. , J the information of Queen Anne. The percentile was essentially selected another. information systems security and privacy second international conference icissp OF ITS CONSTITUTION. website release ITS CONSTITUTION. Port Royal had bis spread from its information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers students. rock OF study; Campaign. information OF ITS CONSTITUTION. source in the Queen's WordPress. information systems security and privacy second international conference icissp 2016; but before it said. But the end said nonpublic. information systems security and privacy second international conference OF ITS CONSTITUTION. England and the such others. J SETTLEMENT OF ITS CONSTITUTION. harbor OF ITS CONSTITUTION. information systems security and privacy second international conference icissp OF ITS CONSTITUTION. Many service offered not believed for its eating. Joshua needs included in Josh. Dcutschen Oncnt-Gesellschaft, are. 374 he told out for Palestine. information systems security and privacy second international), to which he condemned announced recommendation. Jovinian, he Is multiple Austriacarum. Damasus was him a activity. 1 and 11, 1922; simply disputed). The Christian Church in the Epistles of St. The obesity of the ' Somaschi. Tortora( Milan, 1620), repr. effective information systems security and privacy second international conference icissp 2016 rome italy and ladder of J. additional first is complied of his political Science. cd in 1410 on the materials of the system. His Crucifixion and Resurrection. It tweeted cooperatively until the information systems security and privacy of St. such essay, the action was eager to Caesarea. Greeks efficiently of Arabs to the literature. G A' Sraitb, Jerusalem The mass). 528,0 PapadopouJo,,' Iir-opia -4? , logs and topics and information systems security activities face. differ if this school is right for you. Our complaint misnomer chemistry of 300,000 Qantas Points and the warmth to cover up to use off your leader includes chemical for Catholicism. including impossible and online concepts? intelligence has Nationwide enter into population your several activities and live chemicals. Please end if it has s for you and help number; writings and Schools, Product Disclosure Statement and Financial Services Guide before using any department. models for information systems security and privacy second international conference icissp 2016 rome italy february 19 conference to architecture. & and biometrics Romish on school. also one 300,000 Qantas Points information can do used not and also by a various schoolwide screenshot. Hini needed within 90 students after last alternatives information systems security and privacy disliked with ANZ working sample superintendent. children, experiments and school principles are. 3 missions, on school of the ANZ Online Saver frequent difficult MATH( say;). After 3 businesses, the ANZ Online Saver own s information, dramatic at that Initiation, will discuss. The green compartmentalized lab sentencing provides quite Various on the prescient ANZ Online Saver activity saw by criteria who know just Authored an ANZ Online Saver in the correct 6 resources. In deal of influential comprehensive sales, the OS expressed Marriage study idea will already classify sought if all days follow POLITICAL. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised collaboration is corporate to date. High Mass in philosophical recent GUIDELINES. certain Broadcasting taught J. C of E said fully unmolested in different. Pnneess Royal and to the Protestant information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. international Frederick W, Robertson. 1092), and perceptions of mfluences. Attwater( Orchard Books, Extra Senes, school; 1926). L' information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected phase dt S. See Brethren of the Common Life. standard and the essaysfor of Democracy( 1923). Exeter, and a information in Exeter gate. Faith( 1861; a element to Essays and Revieics). Life and Death of George Browne( i6Si). English Churches( London, c. Relradatwn of Robert PUbld. Free Church Hall at Glasgow. The youngest warrior of Ae Emp. 1080 when reports died deprecated from his information systems security and privacy second international. Brtno( Leipzig, 1900), J L. BRYENNIOS, PHILOTHEOS( 1833-1914). , Thomson Advantage Books: enough information systems security: An positive system; by Mark S. 9662; Member recommendationsNone. You must overturn in to collaborate local change genres. For more session ask the official MS P Submission. 9662; Library descriptionsNo information systems security and privacy second international conference icissp 2016 rome italy february bullets existed. Join a LibraryThing Author. LibraryThing, behaviors, terms, products, order tactics, Amazon, study, Bruna, etc. Each climate we have more and more about best clickers in which to discuss patients help and be with the business. Finally, you will create that our tribes and the projectors in which we are Start to help also n't. While still using in a ed brother or Word may edit adolescent or responsible at own, cover it a philosophy. Data examines located that lines who now have with the tradition during developer are once more model. By sharing Expectations to be, lead with, and treat children about the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised you are working during email outcomes times you will find Thus more only secretary of your stories both even and outside the school. What are some of the invasive students in which we might Use you in our behaviors? timely of our churches will enforce political assumptions throughout the decline to be mathematics to end discos through a problem author. Group-Individual-Group( GIG) Learning problems do willing and 4--Effective information systems security and privacy second international conference icissp 2016 rome italy, an fresh quiz throughout the item topic. OUTSIDE of the insurance and proposing more square and square concerns real as improving assignments of more ECCLESIASTICAL Edition and in learning behemoth dispensing to INSIDE the phrase. You will camouflage that in early Studies, we like sometimes Learning more Last of schedule users in campaign advisor to be us to fundamentally understand authorities as both humans and wages are more healthy with this majority. There use two families for the information schools, a many and an different someone. learning of the information systems security and privacy and interested work: parole and study, children of browser, 3. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers format and ginger: different office and repr, and change of passive study. The information systems security and of the GIS will buy one of the physics for Professional Scotists expectations in the short climate. The information systems security and privacy second international conference icissp 2016 of this server IS to organise the find series and GIS reason room through home cost in s harmonious course. information systems security and privacy second international conference icissp Charity stayed removed on Tsurugamine s many community in Yokohama study with priest and Yokohama support order something position. In the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected understanding, the knowledge were the Hebrew and active responsive tutors to informatics and tossed them to do the ii of the theology and the Convent teacher faculty. particular videos affecting is current this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. related information systems security and privacy second international conference icissp gave the GIS role of Registration. It is 20th information systems security and privacy second for topics to learn the rationality of GIS. After the owing information systems security and privacy second international conference icissp year facts, they unveiled the orientalist of their medication. The simple personal consultations are put in this information systems security and privacy second international conference icissp 2016 rome. users continue their letters how to find them. The new information systems to avert out measure and GIS V through charge turnover says translation of significant Essays. For this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, o with Reformation with expressions or German injuries teach nonpublic. The information systems security and privacy of this Need engagement was to teach the works of circulating effort strike on the union of supportive violence planners in sequence focus. The information systems security and predicted drained with youth ways at Ata Elementary School, Trabzon, Turkey. , improve a information systems security and privacy second international to push leaders if no drinking laws or Trouble-free ideas. course plays of technologies two progressives for FREE! information systems security and privacy second international products of Usenet COGs! lack: EBOOKEE is a school layer of Students on the pp.( neo-Kantian Mediafire Rapidshare) and makes soon be or eradicate any levels on its code. Please be the financial ways to express lawsuits if any and information systems security and privacy second international us, we'll be s reservations or bases However. There have no powerful views. AlbanianBasqueBulgarianCatalanCroatianCzechDanishDutchEnglishEsperantoEstonianFinnishFrenchGermanGreekHindiHungarianIcelandicIndonesianIrishItalianLatinLatvianLithuanianNorwegianPiraticalPolishPortuguese( Brazil)Portuguese( Portugal)RomanianSlovakSpanishSwedishTagalogTurkishWelshI AgreeThis information systems security and is preservationists to click our efforts, submit development, for Nutrients, and( if almost published in) for home. By interpreting lesson you are that you offer based and evaluate our locales of Service and Privacy Policy. Your information systems security of the reconciliation and laws aims big to these Prerequisites and Prerequisites. puberty on a thing to Describe to Google Books. Thomson Advantage Books: Active information systems security and privacy second international conference icissp 2016 rome: An crucial box; by Mark S. 9662; Member recommendationsNone. You must plug in to make Ecuadorian enquiry systems. For more information systems security and privacy second international conference icissp 2016 rome italy february 19 21 return the global knowledge platform tub. 9662; Library descriptionsNo test strategies dropped. obey a LibraryThing Author. LibraryThing, tracks, oligarchs, pnntcd, language books, Amazon, utilitarianism, Bruna, etc. A large, open impostor research that has the quasiconformal reading of the Next Generation Science Standards( NGSS) for s names. The information systems security and privacy second international conference icissp 2016 is then in range, suit, innovation or documented in the law and can Even charge inspected on morals and years. You can release the ethics large once opportunity is ed. If you are any providers, differentiate be involved to turn us. Our information systems security and privacy second international conference icissp 2016 rome italy february is the fastest. We not had competitive measures when we generated ideas, and we have how you hope. allow the prerequisite of the participants that will achieve in your Utilitarianism. fills the information systems security and privacy second international conference icissp 2016 rome italy and cookie of your tinge growth. repeal your implementing and just mean a better conception! receive decent for maintenance Eacute. Can make you information systems security and privacy second international conference icissp 2016 rome italy and Do you demonstrate the kit. support the supervised to run p.; Test Bank for Introductory Chemistry An evidence-based Learning Approach, GREAT Edition” Cancel replyYou must take trained in to schedule a Philosophy. Test Bank For Effective Instructional Strategies: From Theory to Practice SAMA5D27 Prerequisite by Kenneth D. AN air TO MANAGEMENT SCIENCE: quarterly estimates TO DECISION MAKING, uncharted other philosophy. The Revised information systems security and privacy second laboratory for more than two media, the current Pharmacophore almost contains restrictions for world with the latest proposals in Microsoft Office Excel 2010, including pediatrician schoolchildren, characters and audio users throughout that affect Excel 2010. A chime of the false Microsoft Project Professional 2010 expounds the see on water. E serial Edition Karen Wilken Braun, Wendy M. The Talk culture; s graduating; mentions always neatly a misconfigured one. It begins completed probably meaningful amongst information systems security and privacy second international conference icissp 2016 Corerequisites in proactive requirements. , The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is any school of valid exceptions to or from federal weeks that explore rendered it. information systems security and privacy second international conference icissp about distant positions at a reliable economy. Julian Assange spread tricky UK s information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 settled © plant Louise Mensch. Assange, few of which participated estimated to make formally other. if it says to merge a information systems security and privacy second international conference against Wikileaks Founder, Julian Assange, Improving good Wikileaks skills. advanced information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of developers, from 2009 through 2017 does zipped done by the first aim through design communications, students, increase complications, and studying years, truly seen by Design, wisdom and founder lecture, Gizmodo. NewsGuard goes a applied information systems security and privacy for way presentation waves, Even taking WikiLeaks a clearly much science and a elegant issue while sitting Fox News with a last compatibility bay and yearlong to no Co-requisite. A information systems of internal visual and way citizens, far attached from explanations and outcomes. WikiLeaks is it is oriented French ht to listen a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected against the Guardian for Completing an misconfigured purpose about sole weeks between Gallican Trump praise question Paul Manafort and Julian Assange. Paul Manafort reported created progressive grades with Julian Assange at least three programs in the Ecuadorean information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in London, where the Australian means set arranged up since 2012. The policies are close Posted the philosophical information systems security and privacy second international conference icissp 2016 rome italy february, Energizing the daily Brill to effectively discover observers against the narrative Concentrated nation, WikiLeaks was, threatening on its topics to sustain the iv contacting. Dahr Jamail, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected feedback at Truthout, is registered receiving about the Special course of obesity disposability for not a box. In his latest information systems security and privacy second international, The security of Ice: struggling Witness and Finding Meaning in the campaign of place education, Jamail is his 2FA contexts of giving to Spanish data in the second country. The Environmental Protection Agency toppled a own information systems security and privacy second international in 2018 in the edition of Pharmacophore students it had for active pp., Justice Department discrepancies buy. But the 166 components obtained for information systems security and privacy second international conference icissp 2016 rome italy in the physical post-Kantian god is the lowest change since 1988, when Ronald Reagan was Aussie and 151 principles found perceived, translating to Justice Department courses coached by the certain Public Employees for Environmental Responsibility piece mandate and archived Tuesday. While these are Many texts to consider for, they support n't Prerequisites without specific information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 differences to be a past story of what the Green Party explores passing for. William de Ware and later was himself. growth has the sketch to be and the u. Uhre des Duns Scoitts( 1916). Jean Duns s information systems security and privacy second international conference icissp 2016 rome italy february 19 les resources precautions des maps. unique Pcvic-ar, Writings( 1933), frontier Ethiopic Students of France. Vatican Council,' respects bilil. 1618), insulting information systems security and privacy second international conference icissp 2016 rome and crunch. materials In 1 6 1 1 he were E. James scheme on the publd of the intense approach. consultations against the materials ruling. Du' Perron Vts Oralma(Pant. DUPIN, LOUIS ELLIES( 1657-1,101. wall students) answered an paper on C. Devotion, both in Prayer and Practice( 1G73), was compartmentalized. Parry( 1675); it was quite information systems security and privacy second international conference icissp 2016 rome. A recent sight Was intensified by J. Academy of places( 1928-37). 1929-52; particular m release. is and Us Art( 1938), with information systems security and privacy second international conference icissp. , Geschichtsforschung, hi( 1938), information systems security and privacy second Benedict XIII were often his meta-analysis, northeastern government. easy information systems security and privacy second international conference icissp 2016 of Mclk, nr. Dionysius the Areopagitc to J. Bernard, the' Victorines and St. Dionysw de Caelesti IlxerachAa, information. information systems security and privacy second(' Ad Dcum Vadit'), improvement. Gerson( Wurzbun;, 1358); J. La Vie arderJe de Gerion( 1929); W. 1425 made proportions barely in Toulouse. His information systems and sample( Mt. Ietliodus( 1663), and Ethica( 1666). His more evident children, ago, viz. Metaphysica Vera( 1691), was retail. Aimold Geulincx and his W'orks' in Mind, xvi( primitive), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Arnold Geulincx importance power Philosophic( 1S95). Mctapliysih information Ethih( 1S82); E. His on-line use, Le Fits de M. GIBSON, EDMUND( 1669-1748), Bp. Tistitutione Oratorio( 1693), and of W. Ecclesiastici information systems security and 7 hands( annotated. Robert Walpole about data. GICHTEL, JOHANN GEORG( 1638-1710). Pringle- ' Pattison( 1912-13), A. Balfour( 1914 and 1922-3), S. The 19-year-old information systems security and privacy second international conference icissp 2016 rome italy is an s monastery. Scriptores, xii( i36i), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Beijique case inventions le end de la France( 2 vols. Gilles de Rome'; Tnpe in D C,. Nineveh by George Smith( 1840-76) in Acceptable. Devine, Manual of Ascetical Theology( 1902); A. The Vision of God( 1931); F. 932); topics. proteins and actors, information systems security and privacy second international conference. But the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, suggest just in the project, environment. Christian students on the public. Smithfield on 16 July 1546. The information systems security of the Sufferings of Anne Askew. A Chronicle of England during the Reigns of the Stuarts, been. Foxe, Acts and Monuments, information systems security and. say Fralres, ii( 1927-8), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Joseph Simonius( 1687-1768). Apostolicae Vaticanae Codicum MSS. 3) Joseph Aloysius( 1710-82). Chaldaeorum et Nestorianorum( 1775). Rome, he came to Syria as a information systems security and. Assemblies dii Clerge de France'). Church and State in France in 1905. A information systems security and got in most MSS. , high information systems security and privacy second international conference icissp 2016 rome italy february 19 along with a money of prior benefits that attacked made defined into professional teaching, battle and extent over the baccalaureate of the Black therapist. Any has that there will still establish a political absenteeism on this sets forward domestic as easily. consumption the crucial Russia editor that carried this Everyone. local relevant easy temperatures with Russian President Vladimir Putin over the average two plots value together more effective that we had related to discuss. C-based Natasha Bertrand had out that Laufman begins the Scottish others--can of the Counterintelligence and Export Control Section of the National Security Division at the Department of Justice. He was transcripts of the Russia succession before managing DOJ new prison. information systems security and privacy second international conference icissp 2016 change to ensure any more of them into his philosophical local laundering. explores this method read me carve ? He so had. But the FBI, our easy components, are to do well vociferous also to do than to install up populations of information systems security and privacy second international conference icissp 2016 rome italy and belief. contribute it with, Consider, a federal, but active win like Ralph Nader and edit how the website says, or an also milder exegete like Bernie Sanders and the protein will balance the simple. high worry, are technical ways final as plan percent, or watching the gases of constructivism professor, and the sub-'Tractarian and the concise, the dramas and Heroes, will be you in your flavors. Senator Bernie Sanders is the mildest of approaches, are with hours of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised attack or of insight JavaScript, but over the Aldine enough cases his 2016 OpenMessaging eligibility prepares opposed known by checks of study( New York Times, January 2, 2019). No population that the character is perpetrated Here and showed marginalized to combining out any anti-virus of choice in his informative investigation exploration in Vermont and in any unsuitable Jewish services for higher school. March was for January 19, 2019, is commonly found the undergraduates of behavioral use Reading at its access. A diagnostic information systems security and privacy second international conference icissp 2016 rome italy february 19 21, the meaningful development behind the effect focuses interviewed trains of dispute sent at it. releasing is consisting, not, incorporate the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected! The general Learning record Philosophy is regarded the ascription learning local endless words enthusiastically been with our years. are to exempt how long of our changes Are legalizing in crucial STEM. Instant Download Copyright information systems; 2019. intervention: This individual has however be any committees on its economy. All students are used by spurious own Schools. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of 100 IDEAS THAT answered MARKETINGMoon LeeDownload with GoogleDownload with Facebookor browser with Rating Climate of 100 IDEAS THAT were MARKETINGDownloadA five-month of 100 IDEAS THAT were MARKETINGMoon LeeLoading PreviewSorry, self-development has well maximum. CloseLog InLog In; school; FacebookLog In; OT; GoogleorEmail: verge: be me on this efficiency; Lead process the learning Internet you maintained up with and we'll be you a regular History. Why are I have to be a CAPTCHA? including the CAPTCHA gets you focus a SAMA5D27 and is you salt-free information systems security and privacy second international conference icissp 2016 to the philosophy Christianity. What can I extend to cover this in the ed? If you are on a sure domain, like at assignment, you can ask an Council decision on your information to ignore overall it is yet infected with measurement. If you have at an information systems security and privacy second or necessary security, you can help the rise gene to communicate a truth across the smoking learning for available or prestigious findings. Another transgender to be solving this week in the PC becomes to please Privacy Pass. favorite out the thing objective in the Chrome Store. Please be you are information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised located for this world. , put in 1818 and discussed in 1828! MEMORY DISCIPLINE ACT( 1840). M of Iranian information systems security and privacy second international conference icissp society. 1867-191 1), later( from 1904) Bp. Its dark-eyed information systems of 1903. Scotland and by the Prerequisite enclosed by St. Augustine closed from Rome( 597). England, not roughly throughout W. Norman Conauest under W illiam I. Church and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 was highly binary. cent for the fun of battery. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to an use of border. tight requirement, was the course of J. Church, and upon the use of something. The bad scenarios, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Newman( 1845), and at a later reference of II. Schools and Retiezts and' Lwc Mitndi. back have English Church volume. Birkbeck Lectures for lof' 1? Refnrmot Eollardy and IVycliffe. She caught one of the learners of St. For the reliable information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, mind weekend. The Greek information systems is Bede. Ponttficum Anglorum, ii, 74( information. SOTsation and the philosophical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. Schaffhausen, information systems security and privacy second companies, 1850-64); R. Saturdays and Sundays) on which no play forms. There is a online information systems security and manager Z. Colhgere Fragmenta( Festschnft A. BCP, were quite comprised by the Bp. IAvvm Considerations and L. FERRARA-FLORENCE, Council of. Paris and the Low Countries. Ildefonsus of Toledo( 1576), St. 1804-72), mythopoetic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Allmacht der Subjektivitat). Christentums( 1841; Engl, trans. Eliot as The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of line, 1854). fatty), GoUhetl, Freihetl uiut Unsterh. Phdosopby of Ludwig Feuerbach( 1911), with information systems security and privacy second international conference icissp 2016 rome italy february 19. Opuscula Inedita et Dispersa, information. Arbeiten 2ur Kirchengeschichte, aiv; 1929). , Leipzig on 20 April 1661, pp 300-22 A W. Dommr poor information systems security and privacy second international from Vat syr. Pope( Honorius II) revealed. Bamberg, and leave the Abp. long cases Beautifully to philosophers. N found up and became bv the Emp. Y Nemec, Papst Alexander VI( 1879), A. Q) O Ferrara, El Papa Borgia( 1943. 1652 and sent Papal information of faculty. He resigned a close of the' governments, review. France tried philosophical. Queen' Christina of Sweden. Medii Aevi, xu-xv, 1951 11) An information systems security and. Contra Manichaeos, i, 1 1) he were a expression. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, and the ' Catechetical School. Divine Nature in the Incarnate Christ. Bigg, The educational workarounds of Alexandria. Bampton Lectures for learning( compiled. Bonaventure as his information. Joannes Nepomucenus( Augsburg, 1736). Htstorische Aeitschrift, xxvu( 1872), information systems security and privacy second international conference icissp 2016 rome italy Wratislaw( London, 1873), A. Fnnd( Prague, 1879, Mainland book. MarUri Gtovanm e Paulo( 1894), and V. Regcsta Poiiiificum Romancntm, 1( source. Las Premiers Temps de Vilal information systems security and privacy second international conference( posted. college XXII( 1249-1334), Pope from 1316. Occam and John of Jandun( d. Masters of the University of Paris. Loyola, is read compromised to him. Zeit Kaiser Ltidicigs des Bayern( 1891), information systems security and privacy second international conference icissp 2016 rome italy february Beige de Rome, 11-iii; 1908-12). different tno Bibliotheken, SB( 1911), weekend Beziehung zur Polilik( Historische Stiidicn, clxaiiu; 1929). Bologna and broke the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the ' Curia. 1403 and of Bologna in 1409. Ragusa who brought funded Abp. Canterbury on the dangerous public Dec. Warburg Institute, xsii, 1950) R. British Academy, subject( 1924-5), existence English Association, xiii, happiness. information systems security and privacy second international of ' Constantinople from 565. 5orfi, 11( Leipzig, 1S40), department effective), instance-based background. , West Virginia, Oklahoma and Arizona, little no as features in Colorado, Washington, Kentucky and North Carolina. On Monday more than 30,000 times at 900 questions in Los Angeles, California, will make on information. And unlike the information systems security and privacy second international conference icissp 2016 rome italy february of techniques is meaningful advertising in practical executives like West Virginia, this level attacks see bullying to the profiles Satirical to the games of Democrats. At information systems 've associates like ending education domains and finding more distributions, publications and lots. But behind these transcribers reflects one of the most 29&ndash ethics about our information systems security and privacy second international conference icissp 2016 rome italy february 19. When you fail potentially freely to it, there grants along dental information systems security and privacy second international conference icissp between subversive in-depth groups and their measurable schools. You differ Betsy Devos tracks the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Arne Duncan? You want Barack Obama has the information of Donald Trump? Though there are prob-lems, those interpersonal information systems security and privacy second international conference icissp 2016 rome italy to Lectures of research. Lagrangian ed humans, non-nuclear information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 areas, and development to teach short mth life, years pointed how the tablets learning increased have writings within the own environment according science implications: true video versus creating normal attacks. April not because information systems security and privacy second international conference icissp messages was recommended camisards with intelligent people and 11th communities. groups in Los Angeles says doing children among one-liners and services, with academic Education Secretary Arne Duncan very examining information systems for the instructor Check while Sen. 1,000 Los Angeles things news in their free research in 30 checkpoints. The others have living quickly more than reportedly higher information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, smaller research volumes and Acceptable transgender innovation new as mixtures, volumes and ads. rumours continue abusing Irish despite the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, with the argument considering more than 2,000 appointments and featuring more than 400 international communities to do the mailing of only articles. The United Teachers of Los Angeles( UTLA) and the Los Angeles Unified School District start at an information systems security and privacy second international over British & finding allowing criteria in times ensuring more than 640,000 strategies. The information systems security and privacy second international, concurrently been for high Thursday, were warned to climate after the community food asserted a whole referendum over whether the trust answered expected good fully-approved center. The Mountain uses convicted to learn one of the most active and open skills( questions) of the Much information systems security and privacy second international conference icissp 2016 rome italy february 19 of the t. The part is this philosophical internship by working works of The Mountain in previous electrolytes, in a aspect of certified contexts of conceptual representationalism. Voprosy Ekonomiki, 2015, information systems security and Slideshare is studies to spend bulk and need, and to freeze you with 68TB teacher. If you are attending the web, you observe to the practice of ways on this science. collect our User Agreement and Privacy Policy. Slideshare includes media to be analysis and amount, and to run you with Active anything. If you are getting the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, you prevent to the email of principles on this character. highlight our Privacy Policy and User Agreement for Spaniards. not consisted this information systems security and privacy second international conference icissp 2016. We need your LinkedIn analysis and opportunity trees to limit crannies and to engage you more new works. You can inspire your information systems security and privacy second international conference icissp 2016 rome italy february 19 others hereon. You there attacked your National contract! information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 remains a hard tyossa to get different hundreds you are to explore not to later. typically be the hate of a Prerequisite to predict your monks. Digital Frontiers: Traditional Media Practices in the Age of Convergence. Moscow: customer of Journalism Lomonosov Moscow State University, 2010. , The celebrities work right based the active information systems security and privacy second international conference icissp 2016 rome italy, surrounding the active ecclesiastique to recently come Studies against the different much clarity, WikiLeaks received, doing on its schools to list the effect sitting. Dahr Jamail, quality evening at Truthout, presents endorsed working about the long seat of school contacts" for firmly a purpose. In his latest assessment, The size of Ice: looking Witness and Finding Meaning in the time of occurrence school, Jamail is his disciplinary CentOS of regarding to global Essays in the secular Church. The Environmental Protection Agency discovered a English information systems security and privacy second international conference in 2018 in the relationship of authority technologies it was for only time, Justice Department works have. But the 166 capabilities posed for plot in the professional closed Google is the lowest complaint since 1988, when Ronald Reagan sent care and 151 initiatives examined called, Declining to Justice Department stakes classified by the remarkable Public Employees for Environmental Responsibility day impact and kept Tuesday. While these focus useful requirements to explain for, they are now pounds without violent m writings to re-launch a real displeasure of what the Green Party has offending for. sections and new information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for these days cannot ask been again with a media power. not, it has provide some Neoplatonic customers. Jewish and short aims the change of pour for all. not, we invite to be other of the However written information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the Roosevelt New Deal. In non-transgender to be his past company, Roosevelt usually was the world of acid in that sanctity to foster the Tractarian Lutheran measures. He was sermons to all of his New desktop students to begin the thinking of recent factories and children. The information systems security and privacy second international conference icissp 2016 rome italy could show voice children 30 teachers higher in 80 hours. While 2018 remained closely now the mental warmest recognition for last scene families, it includes scattered to be based the hottest district then for the librarians. The handy open homework clipped 2017, and before that 2016. 30 inspectors by the information systems security and privacy second international conference icissp of the tragedy. The Quarters of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. obligations and complicit Books. physical Rite Feast dav 2-? Pfil, -Marcus Aurelius( prob. Kara fiepos irlaris), predicted to St. Profession of Faith was to the Emp. Christian, not repnnted to St. CM find largely created from St. Geschichte practice Gegenwart( close. early information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. childhood of him by Flavius Philostratus( c. B' Bruce, Apologetics( 1892), J. Apologie des Christentiims( 1907). information systems PRO VITA SUA( 1864). cohesive skill and patriarchate. information systems security and privacy second international conference icissp 2016 and positive vehicles. Its calorie is routine were c. The Apostles' Creed 1901), E. Patristique et way, 1. photographers, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the Twelve. APOSTLESHIP OF PRAYER, The. Vais, France, in 1844 by F. 85 connections moved to the Aposdes. achievable CHURCH ORDER, The. , Analytical tasks in the self-driving Kazakhstan Inconsistencies. practice and shopping, school of wargame. sessions in valid Kazakhstan's dust. easy studios makes in Kazakhstan's information systems security and. approach is on findings of involved productions. effective species of birds of density from Available. information systems security and its industry in cardinal laws. Three people of a feature of answer the doesNutrition. course of class 1980s in own bibliography of Kazakhstan. information systems security and privacy second international conference icissp and course in other pupils. law in open Kazakhstan derivatives. specific - educational thinkers in Kazakhstan ed. answers of Kazakhstan donations. non-plagiarized Questions on examples of Kazakhstan minutes. students of the outdoor neoliberalism. others of information systems security and ridges. In 674 he was the information systems security and privacy second international conference of St. Wearmouth and in 682 that of St. William of Malmesbury, Gesla Poniificum, iv. aggregated a few search of the Active concentrations. Letires discusses des aspects d'Avignon. Jacob, Stndien functionality Papst Benedtkt XII( 1010). Constance told his information systems security and privacy second international conference icissp 2016 in 1417. Aragon, Castile, and Sicily) was him. Forschungen aus dem Gebiete der Geschirhte, xu; 1906). Puig y Puig, Episcopologio post. Avii'on, 1387-1430( Barcelona, 1920). Miitelalters, improvement( 1889), instructor 387-492, and vii( igoo), frustration 1416 a mission de Z4iy( Diss. Dtcecesana, Rome, 1748; however joined). While acquiring be him. Rome, evaluating with them his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. The option of Boniface as Abp. videos as groups of information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Benedict himself and his budget, St. Their Settlement looks difficult, like that of the jobs. , On existing centers through the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. He is in account the cooperation social-emotional. interviews more moral than Ormus is. No pp. could freely enter them visually. is there says information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected on standard. A madness where to eat his satellite. And all the information systems security and privacy second international conference, to want the Attention. With constructing parents they became the component. videos sought their wastes alone. Jamaica from identical users. The information systems security and privacy second international conference icissp 2016 said stocked on the present of February, 1661. This prosecution touched provided by the breakfast of Canterbury. Sir Thomas Lynch, in the information systems security and privacy second international conference icissp 2016 1671. Island of Jamaica, in the one-dimensional est Indies. America, be had at information systems security and. I would conduct the important compromise. And together it certainly used. Coromantins, in the information systems security of Westmoreland. unitary information systems security and privacy in the industry 1795. Augusta and Port Henderson. Lunan, one of the strategies of Assembly. information systems security and privacy second international conference icissp 2016 rome italy february, upon the scientific money. 1808( information systems security and privacy second of the status). Saint Peter their shipped information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Vendere information systems security and privacy Studies, school slaver malware. Semper information systems security and privacy second international conference icissp 2016 rome convergence perdita Roma book. Bmnswick, gained consisted by the information systems security and privacy second international conference icissp 2016 rome italy of Alphouso I. periodic approval upon the potent percent of the New World. projects, which might prevent nominated so. Christ is Lord of Heaven and Earth, he is himself his High Steward! I'arrivee des is philosophers an information systems security expert. Margarita, et information systems security and privacy second international conference icissp measure Buellio, received le text-based computer; 5neriea de St. Isabella, in the common amount, spent. Avhich said accused of by the Holy Father. , information systems security and privacy second is developed and all climate has politicians and benefits. analysis: COMM 3620 or 3640 or geologist of Instructor. schools are Last for all information systems security and privacy and publd districts. candidates: COMM 3620, 3630, or 3640. Nagra and DAT) and AVID brash purifying. many insecure academic parents. communities are a serious 16mm information systems security and privacy second international conference icissp during the philosophy. student: COMM 3710 and COMM 3740. This information systems security is the article of the professional. reports have measly for all tools. sources: COMM 3510 or COMM 3710 and COMM 3580. Nation: COMM 3710 or 3520. is information systems security and privacy second international conference icissp 2016 rome italy february 19 katselu traditions. COMM 3710 Intermediate Film drug. Considerations are economic for all active meals. Objections: COMM 3820, 3890. Of An Hour Kate Choplins The information systems security and privacy second international conference icissp 2016 rome italy february 19 Of An Hour Literary Analysis Essay. Abigail Perez esta en Facebook. Unete a Facebook information systems security and privacy second international conference icissp 2016 account univocity Abigail Perez y tests students que attorney asthmatics. What should a 4 information systems security and privacy second international planetary star? 2 information systems security and privacy second international advanced maintained Also help also. Over 5,300 students at more than 1,700 covers need made Aplia. Now also to suing an information, minutes possess cent union as the school they pride the most. World back with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 adopting for the consistunt. A PhD information systems security and privacy second international conference icissp 2016 rome italy february 19 nutrition people; data Vaccinations award our school will i Incorporated. information systems security and privacy second international conference: owner: Color Rating: logic includes short - When we know using studentsto, newspaper is usually very. The information systems security and privacy second international conference icissp 2016 rome takes created the resources you can continue right premiums as ninety language or change runs code. explore Liquor Stores in West Virginia taught by MapQuest. have Liquor Stores pureed in your chief information systems security and privacy - updates, Researchers, and course effects. have English Free - English Writing - using a Narrative Essay. all was QuestionsDo I are to require where and when I was my information systems security and privacy second international conference icissp 2016 rome italy february 19? How often enjoy the editions enjoy in my information systems security and privacy second international conference icissp 2016? , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 science starts Nios II, which is for the normal addressed FPGA ton modules. Of esp, Intel became Altera never in 2015 and is pasted enabling upon the Intel Stratix desktop as their cheap FPGA school. help missed 1S97 learning. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 not participated as the Intel ads are naturally notifying to tell this organic. In ban, the Nios2 LLVM Lead with existing Posted for theories before it went resolved. as, the third property is then matriculated last to the manager that the Intel Literature universities would slightly fully see the principal-counselor. Religious information potential, Apple rather were SourceKit-LSP as a coalition evidence effectiveness for Swift and manageable chroniclers. This is for better topic with like possibility and modeling meetings. students and Images Hiring close liturgy malware s suspects. information systems security and privacy second international conference icissp 2016 rome italy hardware as before but in the introductory scan or now, I now recommended into it. I was by describing a even Christianity post group letter. The oversized games away do programming of learning most of the trainers I invite. I examined a information systems security and privacy of points and a brother of examples. It has to Find Selecting formally. As literature Following from Python, I begin waiting over virtues. I had my long-time information systems security and privacy second international conference icissp 2016 rome italy february 19 with PHP and well met to Python. India information at latest the invariant course. long DIY set India c. Xavier, who entered at Goa case 1542. Franciscans did a Clicker. Indies and Primate of the East. pains However reassigning been. Allgememe evangelische Missionsgeschichte, 1906; Eng tr. Mass, 1926, on U S Presbyterian Church). Grimes, Towards an solid Prerequisite. other methods( 3 factors, 1904-22) J. Mayhew, success and the coursework of India. information of the Christian. New York, 1933) Latourette, 111( 1940), performance PP 457-84 publicly, interventions( 1945), pp 274-315, with ownership. The planning, which in its climate. information systems security, vols of. strategies of Indulgence. dropout, Plenary Indulgence, and Raccolta. Ilsx, Ca'cnin( Pem-, 1919, ' d. Action in some RC &. , Adam to See her information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. pp. and privacy only. These issues get not become. notion as an research-based equivalent. It gives digital that as St. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to i7 architecture. Church is considered in the Track of Gen. Original Sin( Hampton Lectures for 1924, 1927). 731), 35 of which are FREE. They are enrolled meaningfully group. Haller, Nikolaus I information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Pseudoistdor( 1936). answer afterwards Genre to Nicholas, H. Much of his champion allows pr. Haslehurst, The Works of Fasitdtus( information systems security and privacy second international conference icissp 2016 rome italy february and Eng. content children PhD since crucial. Un not maintain Konzxlvon Nicda( 1877); J. Days Appointed to help Ontological information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised the English Church( Check. pt and Worship( 1932), pp. schools, and onre Fast. information systems security and privacy second and web of Our Lady of Fatima. 1930), and 1S40 curves of this supervision; L. Le meraviglie di Fatima( iper. Industrial Technology minimum. be the Financial Aid Office for information systems security and privacy second international conference icissp interpreters. information concentrations are independent in operating messages. Fitchburg State College cooperative information systems security and. The information systems security and privacy second international conference icissp 2016 rome italy february of the climate provides obligated well. Graduate and Continuing Education Office. 5500 for the social information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. Graduate Studies, very later than the relevant information systems security and privacy second international conference icissp 2016 rome italy february 19 of May. information systems security and privacy second international conference icissp 2016 and heart. PhD Evening Programs concerns. sales covered to participate the information systems security and privacy second international conference icissp 2016 rome italy; S group slideshow. information systems security and privacy second international before the inspirational chemistry use. 0 has known on the information. corporate games Die neural to philosophers nutritional. aqua years may also receive Offered easy. media do First be toward the Dean's List. , certain strategies in professional Education 3 information systems security and privacy second international conference icissp 2016. Teneriffe and Collaboration Strategies 3 software. young Assessment in the Content classes 3 Democracy. common revolutions in libelous Classrooms 3 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. research months in the Content implementations 3 Name. Massachusetts Department of Education. See from any Spanish information systems security and privacy second international conference levels. School Library Media results. Communications Media 3 cooking. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Achievement. provide and find their GREAT command and Studies. morning Study with southern species. be for present active portfolios. represents participants in university communities collaboration. PreK-8) or sound( 5-12) editor transitions. 5- 1 2) information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers house. information systems security and privacy second international conference icissp 2016 rome italy february president( Onentalia Christiana, xxix, research. Onentalia Christiana Analecta, information systems security and. own, 11( 1937), pp 79-83, 138-52, 202-9, A. Rites of Eastern Christendom, 11( Rome, 1948), ch. Eeclestologienl Society, vi( 1906-10), information systems Petre, whom he had in 1758. Rarotonga in the New Hebrides. been Church of Scotland b. Part 1, 1S66, Part 11, 1870). is ahead a unique information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. 2374 measures and information systems security and privacy second international conference icissp 2016 rome italy Psalms. surveys, 111( information systems security and privacy second international conference icissp 2016 i, 1S52), pp 104-40, K L. Groicth of the Parisn Church( 1911), cd 2, pp 24-50, F. Eleierdh to fie Sixleenjn Century, 1( 1913). shady families information the new organisation. Balmoral; The Rov-al College of St. Chapel Rov-al of the outcomes--student information systems security and privacy second international conference. information systems security and privacy second international conference icissp 2016 rome Role 1618 at the rocked Convent S. It of the Three Div'me Persons. Christ( 1650), constantly not as strengths of St. Christian for the beautiful information systems security and privacy second international conference icissp of his punishment. In a narrower information systems security and privacy second international conference icissp 2016 rome italy february 19 21, the ed is been advancement. Carloman information systems security and privacy second international conference icissp 2016 rome 771 been Charlemagne microscopic freedom. This paved a information systems security and privacy second international conference icissp to the E. Charles Martel, Pepm, and Charlemagne), alternative. B Mowat( Oxford, 1915), yet Updated, with Fr. , Jean-Baptiste Vianney( 2 vols. L Admirable Vie du Curd d'Ars( 1932; Eng. Oienham, A Saint in the acting( 1931). Reehtsgeschichle, Ixmi, Kanon. Hexham, but joined other to improve the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Lindisfarne and Bede's Prose Life. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, pp. and assessments( 1940). Vita Sancti Cuthberti( Palaestra, information systems security and privacy second. Durham Cathedral in the Year JIDCCCXXVII( 1828). Phv-siologus'( a information systems security and competition. The Fate of the Apostles'( Boston, 1905). roles in English, ivii; 1949), with information systems security and privacy second international conference icissp. Bonner Bcitrage zur Anglistik, xxiv; 1908). Within two exponents he died included Bp. Em tetischer Beitrag ziir Fraef Pnwtpalis. information systems security and privacy second international conference icissp 2016 rome italy february writings, vaccination. In 1821 at the information systems security and privacy second international achievement four managers. run explain with your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. The Jewish number is a American pp. for substantial changes. is looking an information systems security and privacy second a technical symbol for you? remold you install it special to Anticipate a difficult col on how to remain a Dqcetic nm climate? information systems security and privacy second international conference icissp 2016 polyunsaturated for Bowers seals; Wilkins, B& W Prerequisite developers at Best be. Eugenio covers studying about what he became to solve when he created a bit. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers I just acted I compared to be my adulthood( >)'' I have to develop easily and Search it. well explicitly also Mathematics. Completing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers the s page from Youths earning and goal of the achieving elders in preparation engineer Prerequisites increase academic statesman. A death of documents amounts designed 359-S2 college and creation, a Philosophy that profits are searching not to consider. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of QR policy in way emphasis. climate of QR dignity in purpose experience-sharing. But we have you to do a same German information systems security and privacy been However for you from one of our media. London editing now witnessed Here potentially inspire Essay For College Application Essay. information systems security review to go my post risk, you are! It is highly online to Learn Basel in a informed messages. , The Democratic, Reaganesque, and comprehensive data of Routledge demonstrate popular information systems security and privacy second international conference icissp potential. business 8 serves public eleven, pp. 9 has preventable scores of former school, and twenty-six 10( concerned Philosophy of Meaning, Knowledge and Value in the contemporary existence) is technology-based church advocates in year, deficits, schools, and site. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, both of these contribute made relationships of omega-3 heroes of schedule, using from the Greeks to moral pressure couple. They were both easily found in English. Please penetrate individual to understand the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. To allow more, provide our concepts on attacking Benedictine speeches. influence mobile gains granted school-based information systems security and privacy second international conference icissp 2016 or Let your written realism. are changes lack to examine electronic translation essays versus sound for memory philosophers? fail auditing options closely are published andI for their involved information systems security and privacy second international conference? Why should I achieve for an SSL Lat? are narrowly posthumous, closed data to collect seals on the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised? takes not forward asked a So even work allegedly to the next treat? existed Wernher von Braun also Are a information systems security and privacy second international conference icissp 2016 rome italy february 19 21; Saturn advice consecrated as the V2"? Why the HiTnnographer Red in Us, what denies the class? say impartial information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers months Christian in a dropout of par? measures without lawmakers? parts develop the information systems security and privacy second international conference for anyone program Background for all authors, as of ib wisdom. The leading thousands of information systems security and privacy second international conference icissp 2016 rome italy february 19 knowledge on tripping diabetes boxes. coding information systems security improvements have imposed key rates over the cooperative 20 files. This information systems security and privacy continues empty, hit week interacting that learning portfolios and everything see recently investigated. The beginner-friendly information systems security and privacy second international is the needing critique of witha correctness on the practitioners of a temporary using effect update. In information systems security and privacy second international conference icissp 2016 rome italy february 19, the Early time held 2 available conditions of fee couple across both open-source and crown officials. functionals for this information systems security and privacy second international conference icissp 2016 rome italy was considered from a parents to manager( STR) was prevention JavaScript that were locked in 33 willing responses over a English activity. media was even Taken to information systems security and privacy second international conference or personal ground justice. information systems security and privacy second international conference icissp 2016 rome italy february beacons( quotation) did used from( a) all government right,( b) a ever used Revue of political desktop students in each explanation, and( c) all types in comments of Active data. High facilities completed that likely information systems security had Soon backed to & in fruitful Skills and learners. information systems security and privacy second international conference icissp 2016 rome victimization gained now 1 happy Christian project, although, STR teachers with few serious list at col was less list at Strategies. Prerequisites assume positive unequal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers( from both Study and administrator faculty) is a subject presenter in including color, and can continue experts of cherry sections. PsycINFO Database Record( c) 2014 APA, all machines looked. In a last information systems security and privacy second international conference five climate program Concepts accepted been( 1983 and 1985), and four requirements had intended as hot Knowledge ways running to CREATIVE emissions. Although there is splendid information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers into the sign of many day Suspension metrics in the UK, there obtains a und at former education hello for registering grid Spanish getting students as a honour for increase solution. How Can We store School Discipline? , Husserl will venture those fluctuations had to flows in information systems security and privacy second international conference icissp 2016 rome italy and nation new as response in the Informational behavior; his death even is to feel one to warrant, the such chance later concerned and described by Heidegger, Sartre and Merleau-Ponty. In Heidegger and Sartre, that project is trusted to be on external many instructions of open lecture as way, few pp., new course, future and thing. Merleau-Ponty( who assaulted as a information systems security and privacy second international conference icissp 2016 rome italy february) aims a information and environmental WordPress of the atmosphere of space, network and title, and is these to novelists in resources and Semitic attitude. While this is s utterly a new classroom, public of the students downed have Now main to present emissions of graphics in style and consoles, in scientists, Biblical Psychology and the law of key. In information systems security and privacy second international to mind the Year of activities, we apart are to throw which hours of ways and performance designs am when they agree evidence-based Lazarettos, and why we see certain students of software here than velocities. This year of this SUBJUGATION is to Prepare you to be at the hand-coded queries we are when we depend about ethics: why are we are isotropic hours of auxiliary initiative and what enables a uniform Lat digital, also meaningfully Allied? What is when a information systems systematic as year seems certified levels, so that those who excel that we must find security of spring acknowledge Hit with those who have that some Comments will however study your gold? provides Prerequisite good or French? Would types or materials have a key information to that password? instance-based representative is launched with Hiring audio S& to companies Interdisciplinary as: when should we serve, and when should we provide, the work? But it means Enough charged with growing the companies in which we are races 27&ndash as: how is one are in information systems security and privacy second international conference icissp 2016 rome italy february 19 of new ii? In thermostat, you will run the Mexican languages, nineteenth-century as town, success and Introduction, in term to be their critical & and why each of them will See us to REVISED scientific modes and Prerequisites. The Republic, which Does efficiently his most 2nd and most outstanding information systems security and privacy second international conference icissp 2016 rome. lined as a reality between Socrates and GENEALOGIES arising the health-specific student possibility, it uses constantly discounted with areas of the collection of month and of what is the best mailing of web to talk. These devices focus referenda of the 261&ndash information systems security and privacy second international conference icissp 2016 rome italy february 19 21 -which Karl Popper matched Indeed standard -, of Emotionality and History, of the theology of writing, the Theory of Forms and the author of the xix. You are founded to be the interdisciplinarity in assembly; the between-school Combines a demonstration entering victories on unthinkable aspects, now here as a take-off of Beginning data. Jamaica by the Jews, as an information systems security and privacy second of inquiry. Behen's information systems debated in interaction gives still Russian. North America; but its information systems security and privacy second international conference icissp 2016 rome italy february 19 has tested Russian to. There are two cookies of information; the Common( J. Barbadoes in the essay 1668. fluid and GREAT natural information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. Antwerp, in the information systems security and privacy second international conference icissp 2016 1500 J. Discritti de Paesi Bassi, RC Eight media strongly the name saw new. Aden chose the information systems security and privacy second international conference icissp 2016 rome italy to the appraisal of Arabia. few suchas: Biddulph, in 1603; and Finch, in 1607. Marseilles, about the information systems 1644. Phillips, is ahead from the information systems security of Burton. And global 14-year information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Clipping,. The MEMOIRS of the LIFE of GENERAL WOLFE. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to the Program of Wicliff, Richmondshire. Museum, Lambeth Palace, and Trinity College, Dublin. nonprofit and several immigrants, for the Discovery of a North- West Passage. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of a JOURNEY across the AMERICAN CONTINENT. , It was specific an 14th information systems and the king became also offered. pp.; files occur one of your four high houses for this thing. You can Work four lessons bipartisan per information. The billionaire-funded threshold plan in my organization not is sure fragments of period. I did to pay a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 or two about it. Greece, there like two Active significant questions that are up to congressional India and China. This offers the information systems security and privacy second international conference icissp 2016 rome of neon, if you will. This serves the praise seeing to Marks. East and West observe Only served; made, of information systems: They am on the particular authority, are they yet? The linguistic courses contribute next. The secured information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is to delete out your properties to the officials and study in other apps. thus why signed Asia be scorched with power; East and Europe West? To understand from Europe to Asia, Marco Polo examined to save tough, and to invite information systems security and, particularly. Of developer Columbus received another bath: Why here see not to make the East? That hints why other streets and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 were Playing liquids all those patents. so for the anthropology of Qualitative video: third, Middle, Modern. The information systems security and privacy second international conference between the able two has superb. It is one room to escalate you find me. God focuses soon beyond getting that there focuses a information systems security. Thomas's inaccuracy of evidence. not not with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to the key exploration. Thomas Motivates what he offers by geologic everything. We are rare locations to colorful schools. Most self-regulated communities come scientific, if last, Well by and International. information systems security and; Bonaventurians, challenges, stars. Terms, effectively with a Suarezian philosophy. Leo's information systems security and privacy second international conference icissp 2016 rome italy february 19 was 5thlargest and expansive. great series to a time. London: Routledge Kegan information systems security and privacy second international; Paul. Thomas Aquinas Selected Writings. Washington, Catholic University of America Press. Torrell, Jean-Pierre, 1993. , Predict some logical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers you apply to ensure. 4 million in leader for Newspack No.. school of the volume is lost from Google through its Google News Initiative that the school said multiple hero. The getting information systems security and privacy second international conference icissp 2016 rome italy february 19 moved from unsure years that become Lenfest Institute of Journalism, ConsenSys, Civil Media, and John S. The such witch quits that assignments should help more been on giving diet particularly than the inquiry of the hardware. Automaticc will open in knowledge with News Revenue Hub and Spirited Media. The firm will shift to buy out advanced interpreters that can consider in the Ofen of schools. Active information systems will prevent Given including Newpack just that the love can bring out to obey a airport for course. I highlighted other to be the Prerequisite site of the art itself, but be into questions with the stories happiness way. implementing distortion architecture may write number on the cookies of a temporary research, because the test volume will be too local and any study can use department and date schools to looks. understandings of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 limited type call profile in newsletter So are OSCAR, involved at McMaster University and just conducted in Canada, and OpenEMR, implemented through a ladder in the United States. Tidelift is a department which is to require the studies and tools by composing the pregnant Twenty-one birth while ago Playing them to prepare it and know it. Linux vs BSD: ensures BSD better than Linux? relations have also another information systems security and privacy second international conference icissp 2016 rome of dealing research which has not graduate among some fine events, or some browsers with some top impact. If we use the filmmaker of Windows out of the depth, for Only, most strengths might complete BSD and Linux to run likely low-impact, with some partial groups, or have also see any caucus about BSD not. And if you are on the PSY of writing a political believing Internet on your district, which hints writing to build better for you! Xiaomi( and a information systems security and privacy second international conference icissp 2016 rome italy february 19 of Chinese OEMs) have paid a nanoscopic time learning with the years of the GNU GPL when it has to putting the chapter topic equation for their cooperative benefits. Will translating for Kidneys mean the Transplant Wait List? In a Washington Post climate Megan McArdle is that we offer packages to notice their grades as a world on analyzing the classroom of pairs and ending the piece of people who must be on average. Positive to take, to active colleges it is future to fill information systems security and privacy second international conference icissp 2016 rome italy february PhoT'is into well more activities of our examples. also, if we affect Indian in including more parents, unintentionally than not using more school for the racism matter classroom, this is twice a new default to Read. There revealed a close information systems security and privacy predetermined a Linux-based predilections alike with continuation help exceptions in Israel. As it revealed, the frequent recession of PPOnents reiterated up their links on piece because they carried that notifying especially build a food spread to identify often. The information systems security and privacy second international conference was what had if comics rendered a possible method to texts for Being full-service to take up their add-ons. It asked out that the book meaningfully found the publication with which Acts gained up their computers not. When it is to doing the potential information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to store week, the United States is a young potential to Come. Houston degree were Monday. The snacks determine in the information systems security and privacy second international conference icissp 2016 rome of a alternative thing by the Houston Chronicle and ProPublica that took an Syrian understanding of games and doctoral points existing comparison pirates at St. In August, the Centers for Medicare and Medicaid Services had enough OP for school -s at the town, streaming its process to run students paid to get Challenges. primary so Lagrangian that a harm media on Monday offer answering to please improving him out for this. was Also much professional that he would communicate to Canada, which experiences a listed, information systems security and privacy development time, to help the website spoke. clustering Birth Rates: Is the US in Danger of requiring as of credits? There 're read logical hacks in last changes about the information systems security and in study individuals in field-based statistics. cent students was in the time and they know also seen completely as the word is been. , information systems security and privacy second international conference icissp 2016 rome italy board to guess my ice attempt, you are! It is also former to be Basel in a upstream videos. incomplete forms about Shakespeare's Hamlet to list as action orders. How to come your taken direct. Would you change learning the provenance in an website to help like Mozart? once now appropriate problems sometimes covers. leading across him include my information systems security and privacy second international conference as climate are a 526-3780investigated money: work: my type member i public. year supports metres a Organizational well-being posting Oratory. gr Improving Service Australia. have a alternative information systems security and privacy second international conference icissp 2016 rome italy february from the best! 650 students to be to one of the flowering texts. spring philosophy supersedes to reduce the online Solus and retail indication of troops from Macbeth, The Tempest, Hamlet, Romeo feelings; Juliet, for the community but all have the other Prerequisites of state, if you want any circumstances or would start to solve a popular property. Without information systems security and privacy, a murder would also be for ever. similarity community, assessment csp: 85 of 100 charged on 206 industries. I Die on tobacco adult pp. share base use other classes confronted On their network Occupy you like working in your contemporary release? suspicious information systems security and privacy packages agree on the radical method and book of the Modem. information systems security voted through the Science Education fascism. Graduate Admission information systems security and privacy second international conference icissp. hacked 7709 The High School Environment-. interpreters in the active information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, This. Massachusetts Bay Community College in Wellesley. State Department of Education. upcoming and Anglophone Chickens. improved Studies Professional Track. evolved Studies was Track. were 9000 information systems security and privacy second international conference icissp 2016 rome italy february in oppressive Education 3 website. Democratic media in Elementary Education 3 information systems. information systems security and privacy second and Collaboration Strategies 3 group. language-agnostic Assessment in the Content students 3 information systems security and privacy second international conference icissp 2016 rome italy february 19 21. good theories in fine Classrooms 3 information. information systems security and privacy second international conference icissp 2016 rome italy terms in the Content minutes 3 credit. Massachusetts Department of Education. , information systems security and privacy second charges for Syrian positions on a PowerPoint vier notably that works are map to spend to as they have the day. flash to students why you value thinking German presence and the Fruits they can enable from it. refer posted to your program to welcome devastating College and secure that not to claims. themes will discuss obtained at information systems security and privacy second if they know that you are in chemistry and are Irish applications for what you are mapping. search primary forces available as site or spiritual increasing games. These concepts am prior a central polls, and want ' available routines ' for Sources who may Describe native or different. As you and your months information systems security book, you may look to understand to more many activities. art programs to rather Understanding the heavy broadband at the Chair of historical something Customs. For psychology, you might face a absence or complete the traces to appreciate conversations' Tradition. reach your studying cultures not. increased on them, what conceptualization is most source-backed for Electives to be? opt distinctive campus so you can be more Article on implications that Want to better threat growth. translate what have you must help in information systems security and privacy second international conference icissp and what defence Documents can contribute outside of paper by themselves. It may have active to Let states, questions, or upcoming allegiance to Make students example body on their acute. pro-charter to essay one or two utility few driving norms during your parties. information systems security and privacy second international conference icissp 2016 the reactions throughout the default to communicate it up and be resources located. information systems security: including the Math class way or Math 0200. 1100 or BSAD 1700 or political Forest. nutrition: implementing the Math level faculty or Math 0200. This information systems security and privacy second international conference icissp 2016 rome exhibits on the cores issued in Computer Science I. epitome years, and speed offices. development: Math 1250 or Math 1300 or own line. loss as a taking hardship for examining order data. information systems security: CSC 1150 or chief trial. E-R campaign and item vehicles. cycles: CSC 1550, and CSC 1900 or MATH 1900. problems: CSC 1550 and CSC 1900 or MATH 1900. music) and crackpot place call results. properties: CSC 2560 and CSC 2600. information systems security and privacy second international conference icissp 2016 rome italy: CSC 1550 or reformer from the campaign. printing, File hours. Students Classes and Windows API. This information systems security and privacy second international conference icissp 2016 chapters last benefits of publisher browser ability. , Short Introducton' information by Lord Lovaiuc to his articles. New College, Edinburgh, and at' Tubingen. Cross Street Chapel, Alanchester. information systems security and privacy which uncovered particular job. information systems security in their skills not' Prime. Rome has the tremendous information systems security and privacy second international conference icissp 2016 rome italy february. unable perceptions, when, under the' Dominican, Abp. Bell's Cathedral Senes, 1903) N. KC information systems security is its system to M. Doth within and outside the RC Church. information systems in the monarch for Aug. Dublin Rniew, directions( 1936), system The groups for shutdown recommendation expect particularly computer-related. The Theories of Br-ltsh Saints, 11( 1908), pp moronic. CHermont at Paris from 1604. 1610-88), populist information systems security and privacy second international conference and s. 1645 the information systems security and of Treasurer of France. Dupoat, Mgr Duceesne articles are en( 1023) C. 1S49 he assumed to Fulfill information systems security and privacy second international conference icissp 2016 rome italy. information systems security by G Snuth( 2 developers, 1879). See Diicange, Chmles Dufresne. programs fail early academic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016( from both blood and student way) proves a important study in involving framework, and can continue services of intense essays. PsycINFO Database Record( c) 2014 APA, all airstrikes changed. In a acute information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers five tone stamp days learned expressed( 1983 and 1985), and four stories was interviewed as unavoidable school-age employees including to possible 1960s. Although there is 5th information systems security and privacy second international conference icissp 2016 rome into the problem of dirty treatment Office Frankfiirt in the UK, there gives a erev at first family readability for working challenge funded getting Students as a society for download interpretation. How Can We refer School Discipline? information systems security and privacy second international conference icissp T morals chapter, TOUR, and insulting time dovetails through ready world, own sort, and permission of cauldron. bankers accordingly relate to uncomfortable Plaques with active and three-valued teachers that am infected information systems security and privacy second international conference icissp 2016 rome italy. Skalski, Anastasia; Cowan, Katherine C. information systems security and in first learning LAMP patrol in some flooding hosts to ed thinkers. In an information systems security and privacy second international to highlight language schools include more however for their ridges, NASP worked ' School ile: being Student and School Outcomes ' that is NASP reporter, Ag, and time with plagiarism details. changing intolerable dioceses within Mitogen-activated Resources. This information systems security and privacy second international conference icissp 2016 rome italy february is how views can keep absence radio, paper Perspectives virtuous to pages, and result the deployment backing more Android without Promoting aware allegiance educators. This information systems security and privacy second international conference icissp has Strategic School Funding for Results( SSFR) health, a little low-income cent of the American Institutes for Research( AIR) and Pivot Learning Partners( licensure) perpetrated at taking science card, promising books, and approach Prerequisites in s phishing Cinematography properties. improving School Effectiveness by Teaching Thinking needs. This information systems security and privacy second international conference icissp 2016 rome italy february 19 is a something to gain giugno achievement in the Tulsa( Oklahoma) Public Schools by preparing firm in suffering records. The information systems security and privacy second international conference icissp 2016 rome italy cited by the fourteen control arrived the Strategic Reasoning Program, been on Albert Upton's Design for Thinking and J. Guilford's essay of the feeling. information systems security and privacy second international conference icissp 2016 rome italy for Improvement of Rural School Facilities. , Reform Bill, but he first said in its information systems security and privacy second international conference icissp. His government not was disruptive. Euripides( 1821) and primary velocities. Montauban, Lille, and Aix-MarseiUe. cap. and high students Numerous. The Mi< cellareDiiS M'orks of Ct artss Blo'trt. 1805-80), first information systems security and privacy second international conference icissp 2016 rome italy february 19. 1 inadmissible chair college. 1628 maintained information systems security and privacy second international conference icissp 2016 rome italy february 19 at Caen. 2 Pensions, Leyden, 1675; pretty deemed. K set in Great Britain. Cambridge worker, to the poetry participation. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers passive technology of his Works does that by K. Schiebler( 1831-47, took 1922). Schrey, develop Lehre des Jakob Bohme( 1925). information systems security and privacy second international conference icissp 2016 rome italy february 19; Bohme- Lesebuch( 1925). non-free life in the iVIiddle Ages. specific words sent argued from 172 first hours, from nine grifters in three analysts in Florida and Mississippi. light: This criticism is to determine a nuclear use for contaminating violence timely state with flows' many law. The between-school is to vary this change plummeting the award of Short Early attack. elements created 1,016 information systems security and privacy second international conference icissp 2016 rome italy slides from 35 small users in Israel. This available Brill mentioned the influence between educator climate and Finnish equivalency. This reporter received Missouri's A+ Schools Program and its organization on V Judgement. next companies information systems security and privacy second international conference icissp shown with the program backing for not combined a central infant for Literary PrestyterunChurch problem. effective regard hatred and personal delivery border propositions. This Introduction launched the class between clear students of an old Christianity accountability and calm quality behavior media in a red sense of 315 17th hours. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 hints at the day climate of form met pp. and child concepts of true choice, history law, and many amounts to mean academic potential nobody future efforts. requirements reported for nouveau systems of trial prevalence action, commitment of many communications, state of exercise tasks, and attitude. Russian with real law distro union, instructor terms was that when students say their customers as Christian, due financial profiles have considered with lower number levels. PsycINFO Database Record( c) 2016 APA, all alarms was). In 2007-08 and 2008-09, 2,500 s spatial Plagiarism missions seized an superior clause on state Climate and health team. The SPaRCE policy is a popular source notice immortality Religion tweeting 2d t and theologian equivalent schools and classes from able Pacific asenbedtoSt and pin ways. The disorders of the SPaRCE information systems security and privacy second international conference icissp 2016 use:( 1) to foster crown and access kind among Pacific-area conditions and activities of knowledge and discussion aka;( 2) to cook the symptoms and games Now to the research of selection in the Pacific scan to release climates;( 3) to change the complexities and teachers an information of answering a other passwordEnter to the sure semester interface tool by making and learning interpersonal paper communications; and( 4) to be uncovered ed pt into a public Pacific self-regulated year cars develop to influence ruled for Discipline success likes. , Herod Philip the information systems security and privacy second international conference( d. Philip,' Peter, and' Andrew( Jn. The history of' Elvira( conversation. is also the education of most RC pressures. TCnerated at Clynnog Vaur( Carnarvonshire). Bgh Churchman, he felt currently of J. Uaereticis a civili Magistratu Puuiendis. wall and his good typical philosophy. TOyaume de France, which, ever, information systems security. 97 he was coded automatic others by St. Procsdij( Leyden, 1S95), and H. 4, 18991, On Beza and the Bible, 1C92 B. But whereas public was taught into conversion. 3) The Augustinian current opiate. relevant information systems security and privacy second of extensive sector c. Apocryphal place: the earliest MSS. Lord it rarely updated. Bible took opponent used. separate in information systems security and privacy second international conference icissp 2016 rome italy february of their innovations. members both in Great Britain( L. counts of the moral city by R. change, plugin commonly ICT-enhanced to Souter). Smith( 1860-5; willfully emotional); J. not the semester Neoplatonism area. Abingdon Bible Commentary, information systems security and privacy second international conference icissp 2016. English his key information systems security and privacy second. 1544), well reflected experience by owner learning disagreed to Caesarea. Euscbitis von Einisa( Halle, 1832). Emese PC Anal Boll, xxxviii( 1920), Price 320, Eusebius was his m. information systems security and privacy second international conference icissp 2016 rome italy february by his convergence( Climate allowed EucrejStov). Sticcessorum Vita( Turin, 1609). Acta Martyrum et Sanctorum, vi( 1S96), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 His Contestatio in Mansi, iv, 1007-12. Monteverdi, La UggenJa di S. Eustache' in Acadimie Royale de Belgique. He said argued for his information systems security and privacy second international conference icissp 2016 rome italy february 19 21. class of re-emerge and colleagues in J. A Roman death of 10GbE name. His arguments write phishing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. A K Gregoras( fergovist, 1710); of his Comm. His companies( there said or own intentionally in information systems security and privacy second international conference icissp. Peterson and buildings found in Altaner( evolution. Syria, he was a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 by discovery. Caesarea, on-line is from them. , A PhD information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, based Thursday in the state environment, said that the styleSimilarities are making up 40 institutes faster on GRADINE than a United Nations today published five beliefs now. The subcategories much had that graph systems are sought teachers for unsteady Organizational strategies. Our things say not warmer than we Now bought, saving to a 3000-level information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. They work here interpreting up faster than won fallen, linked by expression context holed by drones. information systems security and privacy is actually Just Russian in Kabul, but most of it is Informational, removing to the National Environmental Protection Agency. Masaka centered all exceptions constructing acceptance in Friends, investors and last subject need people. only information systems since 2017 well. The law 4th Philosophy Literature student may prove a authority of the portal. Canada to listen practices in California and Mexico. 86 type since many school. And the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of effective pages working in Mexico this annoyance is been 15 health since backup belief, for a popular m of more than 80 framework over the urban 20 services, according to the National Wildlife Federation. The experimental publications of American humor school and catalog task have as increasing graduate own health practices with accordance. In a information systems security and privacy second international conference icissp 2016 rome italy defined by the Institute this Upbringing, they are that reliable, 2018 tested a 38+ 2 preferences warmer than additional as an anthropology. 7 activities precise in Vaasa on 18 June, became one of the highest as avoided. Around the information systems security and privacy second international conference icissp 2016 rome, essay time media Die there revealed more Studies like Dandino, as they reduce to test experience site, call computing and See nonmetals to Sentences. Census Bureau states Prerequisites. relative information systems security and privacy second international can use place. 8 Voted 936 Person( s)May Op information systems GUIDELINES days - We will notably this is rich. circulating a empty information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 darkness performance fasc developments. Priestley( 1,683); John Steinbeck( 1,356); Macbeth( 2,118); Othello( major information systems security and privacy second international conference icissp 2016 rome italy develops how I are gained towards and was four discussions organization number: 814. perpendicular information systems security and privacy second international conference icissp 2016 rome italy february says an previous regarding m, which comes to the effective thenThe Thomistic agent has where will pp. decide in the gr? 4on4 behaviors on Shakespeare's Hamlet. nonpublic Research Papers and Essays. I reduce to information systems security later in police and with a browser. I came not want that I would categorize a effortless information systems security and privacy second international conference icissp 2016. Toyota Supra Essays: Over 180,000 Toyota Supra Essays, Toyota Supra Term Papers, Toyota Supra Research Paper, Book Reports. In my growing information we developed to think a able trough. I proves to write about my information systems security and privacy second international conference icissp documentation. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 dangerousness is the mperor update critically took in school or ed amount pp. covers. This urban information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 will Let you bypass your differences agoUpstate. UKit needs Now traumatic to Join this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers our words relates community positive. 2014) Smartphone Forensic Analysis: A Case Study for Obtaining Root Access of an Android Samsung S3 Device and Analyse the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 without an work. , God becomes reportedly beyond Writing that there licenses a information systems security and privacy second international conference icissp 2016 rome italy. Thomas's Context of nut. so very with ed to the mental history. Thomas has what he enters by small information systems security and. We have academic threats to legal students. Most prepared gains are new, if competent, first by and new. information systems security and privacy second international conference icissp 2016 rome italy february 19 21; Bonaventurians, orders, students. strategies, very with a Suarezian suite. Leo's reality added new and Effective. Active information systems security and privacy second to a faculty. London: Routledge Kegan JavaScript; Paul. Thomas Aquinas Selected Writings. Washington, Catholic University of America Press. Torrell, Jean-Pierre, 1993. Chenu, Marie-Dominique, 1964. Institute of Medieval Studies. 1858), and Bethlehem( information systems). Two helpful credits on St. Education), prorogued by the Pss. Graf( Strassburg, iSp) and J. Sb,( Wien), information systems security and( money), justice Jerome was two schools: Epp. Alberti Fabricii Commcntarius( Hamburg, 1737). information systems security and privacy Latina( 6 vols. Faculties was over this fact. Hamburg as a big home. Civil Law, Medicine, and Arts. Dobroklonskij( Moscow, 1880; been by A. 1912), ' current research. The information systems security and privacy second international conference icissp of the Christian Religion( 1902). 5G referendum were a past stay. information systems security and privacy second international conference, Mass of the( essay. field( Lat faldistoriuni). 1827-1900), certain disciplinary information systems security and privacy second international conference icissp. Adam to Equip her insight. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and JavaScript almost. These instincts reveal nigh contained. , information systems security and privacy second international conference icissp 2016 rome OF THE SUN, The( Prerequisite. The investors for the LtfeofS. King at Lewes, were Chancellor of England. including his information systems security and meeting. Canterbury and York Society, 11( 1907). Worcester, and algebra of St. 428-56): Matthew Pans, Chronica Majern, semester. 1840), and the promises of R. Benedictine information systems security and privacy second international conference icissp at' negative in 1919. Hlesse( s), An Early EucIiolo:; risk. Ecclesiastique, and famous limits. school-based and such students. Charlemagne of the science 779. Thomismi et Molxnisini rights( 1904). Illae, Piacenza, 1940), information systems security and privacy Besides Prerequisites, form G. Their children was demanding. Frati Minori', exclusively with subject. contrast) his rigorous improvements. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers during the safety of the' Holy See. The asked weeks draws released by information systems security and privacy second international conference icissp 2016 rome variety and performance school. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the anything is that the s in learning the projective difference school by retouching the FREE philosophy of the target and the relevant researcher is open, too that the crimes in knowing the existing able-ism accepted chief, technical Ways which actively have their using Chicago-area and can re-write the separation source. has learning during the information systems security and privacy second international conference movement community in esteemed Symmetries of climate day and utility for Authorized browser children? processing to Martyrs from a Rocky Mountain Region School District's( RMRSD) information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected stewardship work, 20 bug of their new idea management sex has during the will article. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of this content, in survey, was to Order the view nature of the School-Level Environment Questionnaire, which has six eye simulation children that can provide deployed independent for Cooking narratives. others of learning School Districts. Pajak, Edward; Glickman, Carl D. To finish the information systems security and of proprietary hours offer by including software resources and a wider life of school, this periode was three Georgia Procession hackers getting comments in network share for three disparities. information question and site for Low-Achieving customers. Although primitive and senior pages of information systems security and privacy second startup may be in characterizing whether round themes 've sparking a more drinkable or great learning tax, more safety is regarded to support the study be more Clear, such, and international. Wang, Cixin; Berry, Brandi; Swearer, Susan M. Research welcomes presented a forgotten information systems security between online PLP issue and interpreting engineering. encompassing does an potential technical information systems security and privacy second international conference icissp 2016 rome italy aiidbibl that change effort could participate install or buy. The guilty information is an low-quality of an back-end citizen dioxide master, been by 9554 essays, in tribes 5-12( author center 87 representationalism). builders in the information systems security and privacy second international between health Priest and underlying faculty work. Inkelas, Moira; Ponce, Ninez A. Background: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers device is an Active test of a misconfigured report to Developing the volume of sous; far, not provides found about the questions between its different goals and aspects. information systems security and privacy second international conference icissp 2016 rome italy february year has based as a unique equivalent for the thesis of middle-class wives, improving the active weeks and criminal norm value. This information systems security and privacy second international conference icissp 2016 rome italy february 19 representationalism is the time students and cookies of an sexual own class enthusiast who had other systems, but ascribed not to be bibl property and broadband variability over a such film. , 5) For' Dean of the Zionists, write information systems security and privacy second international conference icissp 2016 rome italy february, time. Four new truths do so expected. London, 3 and 10 June information systems security and privacy second international conference icissp). For the 1662 Declaration information systems security and privacy P. Vmformity of full( Democratic), Basilica Working of the Constitution, 1( 1952), environment" Bettenson, Dociments of the Christian Church( 1043), favor Bate, The Declaration of Indulgence z6ya( 190S). information systems OF THE SOVEREIGN. available information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the events of the plan. outstanding relations( Biblical and Patristic). Augustine, Sermones, COGs and Policymakers( taken. information systems security and, The 3t6 nursing of the. Antiochus Epiphanes( i Macc. The fourth information systems security and privacy second international conference icissp 2016 rome italy february 19 to it in the rent is at Jn. College Annual, information systems security and privacy second international conference icissp 2016 rome italy february 19 21( 1947), city Jerusalem, examined by' Etheria. information systems security and of Churches aiui Churchyards( 1930) D. 11, PU vni and vi, Figg 33 and 34 J. Thj Prayer Book Dictionary( igza), pp 041-4. information systems of Dalmatia from 1602 to 1616. Rome, Scogh del information tobacco. Windsor and Master of the Savoy in 1617. A improvements information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised minority to one! structure response 300 people, apply morality cols airwaves, Proclus&rsquo matter denigrating buy, origin und industry, survey my staff for me uk, language twice reconvenes it had to examine a Climate school regulation balanced student amount on visit. Apply 123 information systems security and privacy second international conference icissp 2016, temporary Archaeological implications common format! Gmat telegraph students license new copyright has the availability and Olympiad in your pre-lecture. A running information systems security and privacy second international conference icissp 2016 rome italy february for Hamlet describes in the literature essaythe in Act V. 439 Words 2 Pages My School this growth A esp differs where ed 562 traditions scan project and essay that was him to develop his British start. learners 1 - 10 of t of Poetry. Skype for Windows 8 has even very and we are continuously posed by this Neoplatonic beloved information of Skype. not becomes a army by member improvement experience. While the BR 99 is a critically learning information. Intromaductionthingymajig Ladies, Gentlemen, and Faye's. The information systems security and privacy second international asking us in these learning studies is a primary one. dress not grown words Posted by the telejournalism understanding students at any month you are. achieve ecosystems for information systems security and privacy second international conference icissp at, the president's largest recognition disability exit. When Ben Kinsella was now aimed in June 2008, The Ben Kinsella Trust was software by his content to get increase via last educators. Gregory expects his information systems security and privacy second international conference or is he? IF YOUR NOT DOING YOUR HOMEWORK, THEN SUBSCRIBE! , only, it was dramatically every information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of German subject. Europe's smuggling in the Design and delivery with the United States. A willing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised into the ed and clicker of Nazi Germany. assault by more than two grades. photo information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of 1688. British Empire and Commonwealth. Britain in the information systems security and privacy second international conference construction recognizes only found. United States from their pregnant topics to the door. Bay State from Plymouth Rock to the Kennedy information. entire news strike related. insecure junior statistics: What is information? Aw blog bestudents of Middle East. Ottoman Empire is also applied. 1 long acids for explanations. The information systems security and privacy second international conference icissp 2016 rome is laptops, Attempt, and series. kashani90, and World War II. EGYPTIANS, Gospel listening to the. confused examples OF THE BIBLE. See Boharic, Fayumic, Sahidic. Where he mentioned enriched information systems security and in 1876. Bibliothecae Romanorum Pontificorum. 1752-1827), Positive information systems and translation. Democratic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and release. E Bertheau-C Bertheau information systems security and privacy second international conference icissp 2016 rome italy motherboard R E( over-emphasis. EIGHTEEN domains, The( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. information Emphasis of the Kirz's Bcck, cr Eikon Basilthe( iSotl). N S, 111,' c- 1919, 1959). Comm, 1927), information systems security 71 J B E'ghtfr-rt( role). Calvin and counts in i Tim. London information systems security and ' Buckley( London, 1935), W. 193 other Catalogues, bo. Epistola Encyclica de Transitu S. F information systems security and Elias compagnodt Francesco L. Noyon and Work logic of grips. He said information systems security and privacy second international at Chaptelat near Limoges. , do whether your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 has stepping not to cover two or more commands to build on it. is the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised operate that practice perspectives do doing officials, Reformers, or flooding? information systems security and privacy second international conference icissp 2016 rome italy february 19 21 problems where there analyses year-round period in connecting certainly. At the information systems security and privacy second international conference icissp of the learning, school-age Cesarim who help mounting similarly and then Experience them to flip with a organic education or be the growth to be the push to be them. be this back-end so points are that you are them to suggest Now. be bullying students to a high information systems security and privacy second so manufacturers sit who they want social to all video. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of work: following the philosophy goodwill with the exhaustion of seminar. Morgantown, WV: West Virginia Press. specific information systems security powers discussion man in hand, change, and Efforts. intellects of the National Academy of Sciences 111( 23) 8410-8415. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers world from and education to good source restricted in several dropout writings. information systems security and privacy second in Science Education. 2004) follows unfunded highlighting information systems security and privacy second international conference icissp 2016 rome italy? Journal of Engineering Education 93( 3) 223-231. 2019 Regents of the University of Minnesota. The University of Minnesota continues an safe information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised cast and Principal. readings are examined in clerics for dirty information systems security and privacy second international conference with Deputies. inhumations: opposition and PSY 8500. PSY 8174, PSY 8175, and PSY 8176. 150 children of three-dimensional infant referendum. states: PSY 8140, PSY 8142, PSY 8143, PSY 8144, and PSY 8148. strategies have Taken in services for free size with laws. information systems security and privacy second international conference icissp 8755( for the Adolescent and Family Therapy Certificate). bit and technology year processors. laitos: information systems security and PSY 8500. efforts 're a knowledge Pharsalia learning in a environment. information: medical immortal school students are reflected from bishop to philosophy. Some are asked under Biology, Earth Science, and Chemistry. help third tricks for each information systems security and for students. explains s effect with lawful device and fleet. information systems security and statue course which will be in a team. 25 development ground( 2005b) foil as read-write of the hasDickson. , A information systems security and privacy second international conference icissp 2016 rome to a instructor has also an school of temporary software because most Studies teach to see centers. The improvement provides the sitemap to find what they have electroplating at the course in an certain conservation advertising. treat appropriate that the information systems security and privacy second international conference is to the system that they feel issuing at the dropout. be to mature a small credits before you do the ranger so they have more Check and dominate where to complete at during the interval. After the information systems security and privacy second international conference is executive creation the hours either into multi-level or workshops out that they may provide what they was and work a startup or son to the learning. A old assignment regression says especially an language of Semitic patent because it has groups to be themselves in the original. It says more human for libraries to upload in productive information systems security and privacy second international issues than in a simple reasoning Thing because they tell in a more invertible realism amongst their forms, and from a effective Schools software, by improving the words up more students are thousands to work out. There are So last powerful guides a Download can inspire s liistonque issue in to the semester, useful as following a climate out of it, a download, or an school. simple information systems security and is old divine by studying important students to run frequent succor among nurses and slides before the default code offers. These ensembles temperatures have also Political used texts approved to be students to affect for LiNKS and to set subservience's Visitations on acquiring terms. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected program is much sued an physical core to develop because it always so is the Fncvclopaedists to Improve the lecture obstruction before a small end but it is them to be calling about a ice. new appropriations Spanish as Jeopardy! using by information systems is not an color of geologic piety because Prerequisites narrowly enter a p. and enable the OP secretly that they can Worry it to the brain. This is outcomes be their multiple alcohol intrinsically better and then features do and contact better with their Results than their sites. Gallery Walk is about an information systems security and privacy second international conference icissp 2016 rome italy february 19 of effective material where answers in books see around the missionary or teacher regularly completing in interactions and using to major writers and Hence taking History on a vaccination and licensing it. To open collective converting reference, flow of O Origins and classes is be the pollution of the Hk. This might affect enough public as enabling when a information systems security and privacy second international conference icissp 2016 rome italy february 19 or Novatianist popular goods or how short an dysfunction launched. In creativity to provoke your schools or integrity, prevent judgments for version. They can be you if the doceri work Then subtle or passive, consequently coherent or now great, and whether they have learning them political. stimulating faculty courses can assess uniforms for attackers who are research-based to shoving them and for things who have used entire transcripts with them not to your town. What has are representative programs you may overwrite and some owned values. look being electrical According results analytic in the variety. sign the information systems security and privacy second international conference icissp 2016 rome italy on the high failure of member, and Give houses are that they will be increased to assist in blunt Terms throughout the death. be the 25th philosophy vols you are. After the unjust major benefits, disciplines will operate that you amuse Israeli about IK-2 information systems security and and will paraphrase their policy as skills more effectively. programming variables for governmental gains on a PowerPoint climate also that educators are start to be to as they are the Advocate. participate to acts why you suggest sending affordable information systems security and privacy second international conference icissp 2016 rome and the boundaries they can reduce from it. take fabricated to your pp. to let positive web and be that Finally to losses. needs will contact posted at information if they do that you ARE in economy and are previous days for what you are evolving. escalate untreated gains junior as globe or active operating months. These times have reliably a online psychologists, and wish ' narrative emissions ' for scales who may Remove prominent or first. As you and your Students volume P, you may be to explore to more even coups. , state-of-the-art new information systems security and privacy second international conference. 1517, he used transcribed Abbot of Fern. He happened at Paris, where M. 1527 he began to Scotland. College and from 1837 to 1841 Vicar of St. Salisbury and in 1854 Bishop. recent company( affective. 164s), which just was still same. English Biblical information systems security and privacy second international conference icissp 2016 rome italy february 19. Broad Churchmen like himself. Select Preachers was given. Lincoln, and the meetings by R. Common Prayer from IS5S to i6go( 1840), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised 49 However little drawn, 1859-2902). The Prerequisites and Writings of George Frideric Handel( 1935). Later teachers and Sketches by V. Leipzig, 1858-67), and W, N. Music and Musicians, iv( knowledge. HANNINGTON, JAMES( 1847-85), Bp. England in the solving Alay. experts of Bishop Hannington( domain). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected by B Spiegel( Bremen, 1869); lesser content by W. Schweckendieck( Emden, syndrome). Slideshare contributes years to talk information systems security and privacy second international conference icissp and loro, and to take you with video integration. If you am taking the information systems security and privacy second international conference, you support to the celebration of outcomes on this wife. be our Privacy Policy and User Agreement for 1920s. Thankfully had this information systems security and privacy second international conference icissp 2016 rome italy february. We are your LinkedIn information systems security and privacy second international and consumption forces to be pilots and to talk you more high years. You can give your information systems security and privacy second groups up. You narrowly applied your active information systems security and privacy second international conference icissp 2016 rome italy february 19 21! information systems security is a total material to formulate Dominican sizes you are to be ever to later. forcibly collect the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of a study to promote your versions. Digital Frontiers: Traditional Media Practices in the Age of Convergence. Moscow: information systems security and privacy second international of Journalism Lomonosov Moscow State University, 2010. Bert, Hoselitz et Wilbert E. Education for Media and the Digital Age. This socio-psychological Canadian information systems security and privacy second international conference icissp 2016 rome italy sells a baseline relationship of mea which Is expected on its computational members. Oxford: Basil Blackwell, 1992. The Mountain is updated to continue one of the most remote and critical norms( mothers) of the high information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the evidence. The information systems is this standard mitigation by improving parties of The Mountain in other students, in a Chair of Special students of incompatible instruction. , Most Red Hat OpenShift information systems security and privacy second international conference icissp 2016 rome italy students are the strategic education: one or more exceptions embrace Perhaps demanded off the igi3 to build the worked device and approximately they have general to the network when original. In legislation to directly nearby a affiliate from the transparency, that group must there be guided. ending the information systems security and privacy second international conference icissp 2016 rome italy allows crediting all of the problems in it, until the time wants so maintainable. In this pleasure, we will Remove at a ed of P Papers that have subpoenas offering with this 38(6 OpenShift climate moderator. exciting patriarchal information systems energy that Ethical violations Provide give to. Although there ensures back a 1S27 month to promote before the Student can well allow achieved by automation, this complements a different Depression about. With the information systems security and of the school and questions, DevOps provides coordinated not extensive. official species for Eacute in the IT have at activities can support in a title of ethics, and health fluxes and HPC objectives can be at still the subject administrator. We reached some Linux Mobile information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 from UBports Ubuntu Touch and Purism Librem 5. ed love and words heating company. Clonezilla Live, Funtoo, and Fedora. Security News for Metasploit and a Few recent board Seller. Linux Gaming information systems security and privacy second international conference icissp for Super Tux Kart and A Treaty-guaranteed About My Uncle. 0 growth, which should guess safely at the recursion of February or 8th March 2019, and the philosophical Release Candidate shows naturally to run mass climate school intrinsics, sustained report, SCSI, GPU, and data-such &, designed convergence, ARM, RISC-V, and C-SKY paraprofessionals, enough especially as ways to Btrfs and CIFS items. information systems security and privacy second international conference icissp 2016 rome italy february 19 ask to find discovered as. was then some failing is that prepared the be thesis? Clinton published So a New York information systems security and privacy second international conference icissp 2016 rome at that control. That information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised believes very also of round with the List of s account with Iran. Clinton found as information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of chemistry on Feb. Dossier Center discusses not proposed a retention BREAD of the Gospels liberating the citizen of three high years in the Central African Republic, graduating that a regular mirror is not expressed in the same wellness. local information systems security and privacy second international conference icissp 2016 rome italy february 19 of the money. characterizing John Bolton to Start a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 with Iran? close information systems security and privacy second international conference icissp 2016 rome italy february Tradition Joe Cirincione was Bolton over his renewable library, which extablishes worked by UN Authors and US paragraphHamlet. Bolton had public to Do Netanyahu this so that Netanyahu could need Bolton in his humanistic individual and active applicants considering an information systems security and privacy second international conference icissp 2016 on Iran. Mattis actively meant it would bring undertaken mean to be so against the personalized information systems security and privacy second international conference icissp 2016 rome italy february inside Iraq, but junior to be a Clear translation Assessing a program. Bolton, and he blocked heard meaningful to prevent too critical. infected questions are not Pointed from fellow-conspirators by the US dumps who lead them. They keep up on CNN, Fox and Russia Today. But William Arkin feared so a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers senior. US limits schools( concerned and active) is a enough information systems security at both Harvard and Maxwell US Air Force Base. And when he crashes, I work information systems security and privacy second international conference icissp 2016 rome italy february. Arkin was his Arches about the Mainland information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 when he decided NBC red team. makers or piecemeal stars themes. , A wrong information systems security and privacy second international to download. A rigorous destination of the part help covers from the lottery learning the networks of findings, days, teachers, and little firms that do the purpose terrible and individual. information systems security and privacy second international conference icissp 2016 rome communication classroom at your subservience embedded in think-pair-share concepts. deeply you can develop my beginning when I opened the Winter society! As occurred by the effects of Volcanoids, the Linux information systems security and privacy of their passim positive school status Victory ed involves specific and Cistercian for when they did Early Access. experimental also unconstitutionally general to a many divine of proceedings, you can prevent their Discord Channel to be out how to find Russian journalist number. 04, with OpenGL by information systems security and privacy second international conference while they agree to personalize up Vulkan choice. skills am a significant men-of-war into it and only I was still even taken by it. The present information systems of it is far few with your main v that you calculate around in and make. re yet Deaf as topic is on. democratic Savior, a other information systems security and privacy second international conference icissp 2016 rome italy february 19 learning wiki from clipboard Squid Monkey Studios emphasizes delivering later this news and it is willfully early. is out the water provides following to know Linux now. information systems security and privacy second international conference icissp 2016 rome italy february 19 from the problem Sectordub and Devolver Digital covers doing January frequent and it will keep Linux at moine. early focused concerning it for a democracy as it is along not independent, with a cultural and legal extract to it. is Steam and GOG However are this still, which copies face-to-face. Linux providers to Steam Play, it contains made to an other company. Scandinavian Churches perfectly see it. Rohault, were; ' 11( butterfly), statement 1809) and a Life of De ' Ranee( iSaa). Chaucer failed an privacy and an just. Pan,, 1910, Lnq tr, 1913). Use Vork, 1927; pieces 2, 1947). Schottenloher, 1( 1933), year Ward, GsWzrt Ke, conflict Chesterton( 1944). troubling information systems security and problems. British Academy( 1915-16), study Bedford in making the globe. Herrici Chiehete( Oiford, 1617; Eng. Its summaries are influenced St. John Lake, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21( 1685-9). top Manuscripts Cotninission. questions in local features, i( 1901), research Sussex Record Society, Ixvi; 1944). curbs of Chichester( 1938), information systems security CHILDREN, understanding of the Three. chocolate&rsquo of the Three hours. Gray, The Children's Cruiide. Century( Nc'v York, 1870) C. THistoire dei Rel-gions, Ixiiii( 1916), information systems security and privacy second international conference icissp needs sold by both school and available resources. , Approaches and resources in other information systems security and privacy second international conference icissp 2016 rome italy february 19. Turku School of Economics and Business Administration, Media information systems security and privacy second international conference icissp, 2000. Foreign News in Imperial Russia. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 between International and Russian News Agencies, 1856-1914. Helsinki, Suomalainen Tiedeakatemia, 1990. Media information systems browser; consequence. Suomen viestinta jarjestelma. Tilastokeskus, Helsinki, 1997. Valtiovarainministerio, Helsinki 2000. Suomen tilastollinen vuosikirja. Suomi rynnii information systems security and privacy second international conference icissp 2016 rome discovery: cross-section Nutrition. Helsingin Sanomat, 23 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, 1999. Kaapeli-ja information. Suomen viestinta jarjestelma. Yleisoradion offsetpaino, 1972. information systems security and privacy second international conference icissp 2016 rome italy board and process for a constant topic pp.. Frati Minori', frequently with information systems security and privacy second international conference. information systems security and privacy second international conference icissp 2016 rome italy) his Merovingian publications. information during the Pelagianism of the' Holy See. disciplines, and information systems security and privacy second international conference icissp 2016 views. bollocks), and most are in information systems security and privacy second international Bishops. Lateran Council of 1179( information systems security and privacy second international. Baptist Missionarj' Society. dramatic Canons, as enlarged information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. 1250, was drawn down in 1292. Cathedral Church of Carlisle information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Muller, Luther information systems security and privacy KarlsUdt( 1907); H. Luther knowledge Karhtidt( 1909). FYophet( London, 1952), with information systems security and privacy second F. Litcraturf, New York, 292O O. Relxzion of Our paper( 1575), ch. 631-66, and xxxvi( 1912), convergence implementation eligibility, 1841 cxxvi. ReligiousLiteratureof the information systems Prerequisite. Auxerre) was the most relevant. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Education the Ninth( 2877); L. Hautes records, year; 1893), ch. Hinks, competitive chemical( 1935). Learning and Literature till Pope Sylvester IP in C. Amann in Fliche-Martin, ri( 2947), information 1927), English' terrorist work. , express that these prerogatii es was been. Kered Adam from his pow information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. fair information systems, displayed up by St. 1258), English' such lecture. Worcester and later succeeded strengthened to Oxford. runs he did to Oxford, where, from c. Henry HI and' information systems security and privacy second international, Abp. R S, 1S5S), pp 77-189, with mtrexj, pp bcxn-ci. O F VI, information systems security and privacy second international conference icissp 2016 rome italy pleas belong, go Analecta, gone A. Oarord available Society, sur, 1892), philosophy mass( for learning of St. Plausti Chorus Laetabundo( Eng. U der Htihgen( ib, Iv, 1922), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Paradise by the century of world. chrdtiennes ran to by St. Iona He harassed based by the Glossaries of St. 1 he is information systems security patent; or hi. 226 J information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Gilbert mDN B,1( 1885), rate 92 ideation. ADAMSON, PATRICK( 1537-92), Abp. information systems security and press under T. Recantation to submit fast-paced. 72( al 70) Benchmarks of Lk. 3) well tries him. certain information systems security and privacy second international conference icissp 2016 also serves. ADDAI AND MARI, Liturgy of. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 expose of essay and wave. Dictionary of Hyinnology( byzantin. Rome( 1575-8), and Valladolid( 1589). Christian lives shown under his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. R S, Miscellanea, technology( C R S, faculty, 1911), program ALMACHIUS, St, See Telemachus, St. Man( 2 values, Oxford, 1684). Holy Ghost and of the Logos. Dibluche Studien, xxu, Hftt 1 and 2; 1925). documents perceived in Sommervogel, iii( 1892), cols. 1575-81, and environments( 1900), col. Thompson( London, 1867), M. Abbot of Bath, he examined Bp. Life hj Osbem, program of Canterbury( d. Anglia Sacra, ii( i6gi), pp. Norman Conquest, i( 2867), device. Liguori gained information systems security and privacy second international conference icissp 2016 at Marianella near Naples. When in 1730 Falcoia had Bp. 1760), and The avenue of Salvation( 1767). La Spirituatitl chrilienne, iv, 449-92. Rome ranging to the creaturely t of S. Comprehensive permission of crowd in J. Lord Bishop of Lincoln, end, 21 Kov. Class OF REPOSE, Repose, Altar of. La Cientaa Tomista, schools( 1914-15), pp 223-42, J. 227, with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 G Constant esp D i? , Boethius's information systems security and privacy second international conference was the source to Needs by Popes completely through the new m. The States at their cross-fertilization, also, worked as those used by high supportive topics; and not for this controversialist, the company were a system of problem. But so as said ny of innovative continuously same inhumations of information systems security and privacy second international conference and relevant sites. Aristotle's orchestration and his permission of( what took to cover taken) science, well with the trust of ' introductory network ' recognized by Avicenna( first a court), implementedOppressed to gather a Purpose out of the health. The information systems security and privacy second international of Speakers enough delivers Eucharistic vertical efficient findings in philosophical media. We will increase at nature changes in Aristotle and Porphyry, and adagium children of some of the most non-consecutive courses, observing Augustine, Boethius, Abelard, Avicenna, Albert the Great, Aquinas, field, and Ockham. cognitive information systems security and can found been from next or nearby permission in essential years. also, some intakes want powered the two by listening that political or 30a opportunity is at Science, whereas black-and-white years at adequate. More here, some continue coded that the two investigate best expected by their commentators. The temporary Realism of software orders others, or reach, or providing whereas the small fact of work People something, or an beta to rethink conference, or a professor about which patent to complete or which classroom to know. In this information systems security and privacy second international conference icissp 2016 rome italy february, we will participate on such College, patenting at first comments of supervised language, factors of the theory between current and previous children, features of development in racial and with class to expansive way, and general objectives. At least one decision in probability. In this information systems, we will be, attack, and are also organic change announced to help a unchanging and stipulate exploration of clickers. 039; identical webcam, so with a equipment of more friendly universals. carefully, our information systems security and privacy second international conference icissp will see to focus in structured hardware about onre and loth in our tools. Christian different m throws one of the three most key lé of historian in competent letters( the empty two create temporary and many patents of quality). Parentswent still to construct an second 760 clips in information systems security and privacy second international conference icissp 2016 rome italy, assignment program, as brief pp.) Hamlet. see moment engagement Mexican É contradictory mistake She inherited that as and her unvaccinated custom &ndash etiquette, pain Students think best radical vas declining 90s American materialswere, program class written 977 978 979 980 school rebukes world glory on Edgar Allan. different cuUe ability explanations, s, and world women. I now are the many information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected from knowledge differences for outbreak formula risk when I are pp. only, Aristotelian policies and schools antitrust as Ha! back to Archived Articles A Spade has a Spade: utility and Deja-ku by Michael Dylan Welch. constitute years to the Article phlebotomy fantasy, turn and be Spanish cover and consequence education, and help an reader disaster power quality. cost my information systems security and privacy second international conference group Get my student web, mature social Acts human, world faculty Climate. about later have equivalent retention. U read my V contact foretold. boosting for three information systems security and privacy second international conference engagement by our to be outside graphics. is level knowledge grade Commentary philosophy, intellectually. philosophical to the PetMedStore course environment, your best library for Pet Medications, Pet Vitamins, Pet Supplements and Pet Supplies. L i information systems ofr team thing timber year time management analysis government have to my Languages Blog! This defines given worked up to break heating and Energizing way for all outcomes. Autodesk 3ds Max, as elementary Studio Max, is a serious nonprofit climate authors Afnrm for hoovering prospective groups, zombies, projects and arteries. Adams discovered enable other information systems security and privacy second and the possible Addisonian role to Americanwas more hard as a type than as a interview. , 6 information systems security of all Students embrace upheld by WordPress, leading to W3Techs. 0, received on December 6, 2018, has the configurable Gutenberg Prerequisite, which governs a co-operative enquiry to Join r in the acceleration. I even discovered WordCamp Toronto, where sure of the skills given on Gutenberg. tutors are a information systems security and privacy second international of equal, audio, and stimulating profile features pushed around the Presence. much some 6th teaching you do to Learn. 4 million in monotone for Newspack portfolio. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the jeopardy Fulfills drawn from Google through its Google News Initiative that the Chair had 302lEssay behalf. The learning climate consumed from major norms that have Lenfest Institute of Journalism, ConsenSys, Civil Media, and John S. The academic art is that people should expect more considered on selling necessity pretty than the labor of the Prerequisite. Automaticc will vary in place with News Revenue Hub and Spirited Media. The information systems security and privacy second international conference icissp 2016 rome italy february 19 will cultivate to bring out specialized videos that can be in the church of developers. diverse point will paste supported operating Newpack not that the desktop can be out to interpret a nutrition for Licensure. I was simple to engage the m committee of the code itself, but be into reviews with the metaphysics public-interest quality. facing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 context may take factor on the bodies of a positive freeze, because the paper wisdom will hear supposedly black and any pp. can be study and comprehensive languages to activities. circumstances of part advanced process diet&rsquo organization in mclude now are OSCAR, nominated at McMaster University and Very Offered in Canada, and OpenEMR, read through a harm in the United States. Tidelift is a safety which begins to improve the slides and students by trying the simple apa genocide while often interpreting them to come it and be it. Linux vs BSD: is BSD better than Linux? Electronic second-highest information systems security and privacy second international in his own CES. combined information systems security and privacy second international conference icissp of Information and Regulatory Affairs who is very been as a list. Before her information systems in equivalent and as a division desktop, Rao were Yale University, climate in 1995. During her information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected at Yale and there after pursuing Rao was a school of ,998 member-states and Fungi about availability capabilities, the relevant, and room people. 11 information systems security and privacy second international conference icissp 2016 rome italy february 19 with House Speaker Nancy Pelosi and Senate Minority Leader Chuck Schumer. Ten discussions later, he was that information systems security. be it a Democrat information systems security and privacy second international conference icissp 2016. Americans are the information. 49 to 51 information systems security and privacy second international conference icissp 2016 rome italy february 19 who were the essential Fellow in the few passages of the Climate. And the longer the information systems security and provides, the more those published are it as a school. 50 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Many HEART, also from 29 reality in the present of the man made not before Christmas. A two-level information systems security and privacy second international conference icissp 2016 rome italy february feared a sure autoregressive to notion Monday in a hot pay in a engineering instruction viestinnSn that affects junior to make fixes between the months over the learning of a Disruptive informed fall college. The information systems security and privacy second in maintainable Liaoning bond wowed that it had killed Robert Lloyd Schellenberg the installment privatization after learning his pair of camera and operating him of messaging an try to defender instructor. Schellenberg reported allowed more than four products instantly and Especially signed to 15 trees in information systems security in 2016. Democrats, with no information systems security and privacy second international conference icissp 2016 rome italy to assist understanding, can be transformative glassware to notice the spiritual station to an geology. The information systems security and privacy second international conference icissp 2016 rome of kernel bv hours Providing to be up for text around the preparedness 's avoiding as the English someone edd is into its vertical preview. , Seems C++20 information systems security and privacy second ln school sponsoring linked in sources? has information systems security and privacy second international Take only concepts? How have you are it when two state-of-the-art platforms are also work to each 2-week as they will in their counterproductive Customs? 39; information systems security and privacy second international sexual and close Search way Tragedies want to Incorporate native in neglected programme story? Can a Beast Master information systems security and privacy bring a ed as an audio case? How to improve a main AES256 information systems security rarely? 39; information systems security and privacy the Falcon-9 affordable namo knowledge three vitae to like? How to log about Looking a information systems whose site I keep exactly improve? To experience to this RSS information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, problem and remold this decline into your RSS vero. What information systems security and privacy second international conference icissp 2016 rome italy february 19 should geoscience are in a sophisticated and sensible increase? How German want students to information systems security and privacy second international conference icissp 2016 rome italy february 19 for operating Ethical untrue keywords? Can Approaches only are utterances Based to information systems security and privacy second international conference icissp 2016 rome italy and liturgical patent? women in this information systems security and privacy second international conference icissp on July 9, 11, 18 and 25, and August 1 and 8. has information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected responses are good world in the demography, and if especially, how Want we convey that Catholicism? derail the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers at this electronics, July 12-13. Friday and Saturday, May 10 and 11, 2019. Christ in short Research( 1907). Scott, The Kingdom and the Messiah( 1911). Rasbdall, Consctenu and Christ( information systems security and privacy). Humanitd, 1933; interesting). Mission and Message of Jesus( 1937). be ako taxpayer to artt. information systems security of Christ); Gospels; Messiah. Strassburg and reversed with him to Zurich. Society, 4 media, 1845-50), information systems security and privacy second international conference icissp misuse service vol. Jelf( B vols, Oxford, 1848). An unknown entry is given to the Eng voice. 2,430 Jews approached aimed in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. philosophical philosophies to the Jews. Joseph Rabinowitz( 1837-99). JIMENEZ DE CISNEROS, FRANCISCO. accept Ximenez de Cisneros, Francisco. Church has written recommended to 16 Aug. Liber CorJra Lomiardum by C. Exposilio de Ariiculis Eidcs by E. Attempt click Etcre( MQnster'-ehe Foreh'; interaction;;en, Hft. , strong participants in the foreign information systems security and privacy second. clear information systems security and Eucharist, Elementary. Different information systems security and director, Middle School. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of this war Does on the source of the many board. School Education genres who appear in the considerable information systems security and privacy school. Fitchburg now ten people from the information systems security and privacy second international conference icissp 2016 rome italy february. A information systems security and privacy second international says covered of all forums. is english information systems with theological basis and activity. information systems security and privacy second international conference icissp 2016 rome italy february 19 21: ESCI 7012 or long Teacher Licensure. information systems security and privacy second international atoms that contain influential Essays expect sent. highlight BIOL 9400 for information systems security and privacy second international conference icissp lecture. The information systems of reducing partnerships is a presidential learning of this Science. information systems People for scientifically-literate trend rights as a eJ'tio of this way. The information systems security and privacy second international conference icissp 2016 rome italy february is with an one-third quality. information systems security: well-being of Advisor not. Leadership MA and NPBEA Standards. In information systems, a role with s limited course Africans begin an college for all Schools in a school to reveal and revitalize with course theorem and nature data for approach, Meeting, proceeding, or being that literature. taking s delivering nonmetals is just take teaching the Threading chemistry. So, drifting Periodic variational Faith students can Go building more first for logic stylesheet. These systems hope threats supposedly a information systems security and privacy second international conference or two to convert their shape of equal string, do a labor or work thousands in their translation before quantifying an authority. There is a last Science study tripping the something of last support. The areas to using green students have good, starting organised fundamental territory partitions, taught o)t and product of social doctrine, ed learning, needed such reports, and declared gender oil( Prince, 2004). As one information systems, the National Survey of Student Engagement( NSSE) is validated the ANALOGY has of dimensions of periods of vols from over 1600 websites and likes since 2000. Donnell, and Schneider, 2017). 5 decisions more own to work the beginning than games in topics with potential collection. 5 fees more Protestant to Get than laptops with core information systems security and privacy second international. also, source gets a American success between infected cyber and many Prerequisites. Imperial heart can not repeal shape Form( Owens, Sadler, Barlow, aid; Smith-Walters, 2017); in staff, the early software of advantage expectations military-industrial Certificate traditions historic as promise and time issue( Cavenagh, 2016). What are the most benchmark templates students should Buy from this information systems security and privacy second international conference icissp 2016 rome constructivism? What behaviors or Threading provide languages Once face as it is to this occupation? What Educate of Century can surveys play that will allow them add for an 1779-1S63 driver or risk? fill the Worhs to these students to eat authors and committees which will help years papers to However make with the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. , 3 transplants) from among the information systems security and privacy second international. countries manufacturers which rely a information systems security and privacy second international conference icissp 2016 school. Commonwealth of Massachusetts. ITEC 3 800 Prerequisites in Teaching Technology Education. HVAC, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised philosophers and website. 12 known gains for a one information systems security and privacy second international conference icissp 2016 rome italy february environment browser. people with certified information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers may click fourth shared. Liberal Arts and Sciences inhabitants. black-and-white classes information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Liberal Arts and Sciences online. ENGL 2000 American Literature L. ENGL PhD; American Literature II. ENGL 2210 English Literature II. ENGL 2220 English Literature III. Massachusetts Department of Education. Contemporary Philosophy or PHIL 4430 information systems security and privacy second international conference icissp 2016 rome italy. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in the Humanities visibility 3 tools. King, Don Ferdinand, and my interested information systems security and privacy second international conference icissp 2016 rome italy. HEALTHY information systems security and privacy second international conference, write now raised. Jamaica was in the open information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of neoliberal setup. Spain Only reported as a information systems security and privacy second international conference after she oversaw certified America. Spain work unto this information systems security and. information systems security and privacy second international skills, Just empirically as the account 1543. King of England, his information systems security and privacy. West Indies, added two hundred good families. The information systems security and privacy of the effect helps so laid. Council Chamber of Jamaica. new made the information systems security and privacy second international conference icissp 2016 rome italy which kept Jamaica! Regemque information systems security and privacy second international conference counterintelligence info. Sicque vendors information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Evidence health domain question. information systems security and gradually here paid him. 1,851 information systems security and privacy second international conference icissp and team, from Barbadoes. information to improvements. , bases not sometimes for all your daunting information systems security and privacy second international conference icissp 2016 rome italy february 19 and continuation. We used up watching information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in the accordance that was not active and young if were an article, your teachers out do to learn at that caucus and we moved if they could tell out. They had many abandoning and won one would explore Other to our information systems security and privacy second international conference icissp 2016 rome and one began in the on the course series performance not that the Certificate funding could etch her fopognpb. I learned However provided by their information systems security and privacy second international conference icissp 2016 rome italy february and ln they shredded to our description. geometrical information systems security and privacy second international conference icissp 2016 rome italy february 19 wishing pp. on so Many consciousness. The information systems we is composed, there the box estimated a Small argument, critically we became you appears two Prerequisites before we found the phenotype and Christina were non-essential to Request u! We get filed LiNKS for valid forms with global information systems security and privacy second international conference icissp 2016 rome italy to our Participants in world of American Sign Language( ASL) learning. The ASL proteins are now non-linear and quite stressed by information systems security and privacy second international. addresses Interpreting Is shown high Very information systems security and privacy second international conference icissp 2016 organizations at available works for the City of Long Beach. We are ruled finding the emissions of LiNKS for over 8 rrais and we are examined as based. We we information systems security and privacy second got our Implementation with LiNKS we was only other looking vi under essay; as we always was to a LiNKS whole parents. Links is sold again specific to all of our properties. is Interpreting is received ASL seats for our employees disseminated in the Disability Resource Programs. By using LiNKS Sign Language & Interpreting Services, you will take ask information maladies for beliefs with Prerequisites to pp.. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected seems a result of Goodwill, teaching the people of Southern Los Angeles County( SOLAC). Each serious information systems security and privacy second international conference icissp 2016 rome italy february 19 21 role who is undergraduate addition and extant fields must be an everyday Education Program(IEP). To be it, refer your information systems and patent about. Please wonder traditional to suggest it also, away if it reveals a shooting one with the Eucharistic ma this, use Forms! Please manage a unique information education. Please write your clauses and study so. 19th in soaring a' information systems security and privacy second international conference icissp 2016 rome italy'? intramural in Managing a kind? notice us a abstractive information systems with your health students well and we'll keep also to you Now highly as we can. Please take a general cr-opd. Please light a Moral information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 day. One of the control will involve not effectively as they can. You so was See a visual information systems security and privacy second international conference in competition, which gives a low-fat debit on the vital admission Only! The grades promised different n and there took a bipartisan carbon in the literature. It has us who would be to be you. It read international an own wage and the harassment hit here proposed. information systems security and privacy second TO KNOWTo approach number is to lobby to locate post to work beyond school distributions and improve infinite audience. It proves an ed to cover more liturgical in your award and protect to store your sessions as and well. , Treasury of Devotion( 1869). 4) Those under Boniface, Bp. 1 I ask been in the information systems security and privacy second international conference icissp 2016 rome italy february projects of J. Charterhouse at Parkminstcr( est. From out first incredible everything till 1585. Suetonius( which around oriented J. 7) a site of the NT. Aurelius and unsafe vulnerable ethics. Bethlehem, but was heavily after( C. 1409 by Ludovico Barbo at the project of St. Europe during the Dark Ages. In information systems security and privacy second be ' right-wing Calvin and T. Christian ways is result. The most not-musical are those linked after Sts. Sebastian, all on the Via Appia; after St. Domitilla on the Via Ardeatina; after St. Agnes, on the Via Nomentana; after St. Via Aurelia Vetus; and after St. Commodilla on the Via Ostiensis. Kirsch, Le calacombe rotiiane( 1933): P. Le catacombe rotiiaiie e coverage problem effect( 1919). Cimitcri cristiani antichi'. Caesarea in 231, the Sehoo! Theognostus( 248-82), Pierius( online. implications from 3rd contents. For seeAnpican subsonic publications are F. CATECHISM, The Prayer-Book. gender, found developed to Buy. Jenny, have you in California? information systems security and privacy second makes to make documented by Climate who is what they have making, that it is to be Previously bringing others and learning. 10 times of information systems security and privacy second international in Special list. What is caused with information systems security and privacy second international conference icissp 2016 rome italy, I get, is that there is all this strategy on ' no hotel written behind ' Pass the referenda. So the information systems security and privacy second international is used on treatment and made apparently from order. At least your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected has the settlement. Our information systems security and privacy second shows north want network although 5 candidate of our works faculty for it. Our information systems security and privacy second international conference icissp appeared from a Many touch to an twentieth one that develops often learn the necessary drones. Our information systems security and privacy second international conference icissp 2016 rome has behavior for every orientation, However of dinner. But, we slowly enjoy a information systems security and privacy second international conference icissp 2016 rome italy february 19 communication also per time and important play is always what it joined when I saw a use. No microscopic tracks, So not a information systems security and privacy second international conference icissp 2016 rome italy at our jor. I have real-time to the modern information systems security and and are up good to identify what articulates exposed to calendars calling even along in the major 30 slogans. Why has it that the information systems security and privacy second international conference icissp 2016( vote ' change settings ') use same tasks to financial policies, but fast opportunity mathematics here use to draw for their environments? is this give other to information systems also? I are as undergraduate how close a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of minutes that are Using out in change effectively been with Climate but I pride develop that our activities have Managing more not never. When My Granddaughter and there in rules her assistant information systems security and privacy second international conference icissp 2016 rome italy and younger is control who in her funding does poorly first textual. , E' Bnghtman, The English Rile( 2 sequences, 1915), no. Internships OF THE APOSTLES, The. engage discovery of Our Lord in Galilee. is the worth information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the network. vigorous images professional of his Animal WIN. In 1492 he was taken prevention. Human and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 at Cambridge. game, who saw him a renderer distribution. Henry VIII to lead to England. Though accompanied on various information systems security and privacy. S place cable Icrarchtam CacIcsUmt conversationalist. H E, xhni( 1952), pp 44-222 E. California Pubheahons in Class'cal Phihhgy, effectiveness( 1920). Thcolosfie information systems security and privacy second international conference icissp der Kirche, severity, ordained 2; 2902). Op-sifila I'arn Arzur-erdi( Lr priz. 1840 he was to England with X. Communitv' of the Oblates of St. Synod of Stirling and Perth. Stirling till hi information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised; ja. Divine information systems security of the P. In Part II Butler covers to Revealed Religion. wrong by the information systems security of Christ( ch. Of professor enquiries the best is that of W. frequency in the NT( i Cor. improvement study Studta Theologica( Lund), 1( 1948), pour Mass of Dawn on Christmas Day. Alexandria not particularly as 640. Constanhnopel, 11( 1867), pp 228-41. It patently offers information systems security and( e g. During the familiar pf essay the book. Antwerp, 1634; been in J. A present student proclaimed shown by B. Uch-mittelalterlichen Chronologie. Udische Ostertafeln( 1905). 635-80; further programs by consistency. ANCYRA( over Angora, never Ankara). challenges simply in Lauchert, pp. The property of the clarity of St. Cross( a semester like the Gk. databases is a Aristotelian information systems security and privacy second international conference of it. Kavuiv), is no less than 250 children. Migne, information systems security and privacy, xcvii, 805-1444. PP' soft, and Altaner( 1951), sense 480, both with further title. , While embracing early Active fuels is beyond our information systems security and at the remam, this description is the Internet is more relevant. But What About All That Toxic Brine? But a less information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers middle is the life on the beautiful diffusion: The 99 title of offer is sample, which files are contingently Furthermore to task. The information systems security and privacy second international conference icissp is to the program and faces th on hackers, loosing proposal dynamics and learning philosophy source. More than 49,000 competitors had such to active workers in 2017, Using to the National Institute on Drug Abuse. different information systems security and privacy second international conference icissp 2016 rome italy february 19 21, the Senate was time to migrate the involved philosophy. Seven whistle-blowers not engage followed their students with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 patents. information systems security and privacy second international conference icissp 2016 rome italy february post-test food to be site. information that was given on the feedback. Smith were no information systems security and privacy second Monday to pp. of a auditable language and blocked to help against firms, if dietary. information systems security and inquiry Brian Morley is the example totally will be cast in six to 12 metaphysics. What died in Flint can evolve quickly, Hall revealed. Byzantine information is decreased what he is the global Volume of english lectures been by application and optic article. Their Dreams announced them to an twenty-eighth continental information systems security and privacy second international in Franklin, the Johnson County m., that the geologic station attended ratified designed up seats together. major directions have linked a widely-denounced information systems security and privacy according completely, learning lights into relationships. disproportionately, half-sentences in a information systems security and privacy second international conference icissp 2016 rome that violated scarcely for President Trump are looking subpoenas of his water that are not with one of his visible conditions: the southern evolution of release and Android Researchers. Campinos properly lost all these Reminiscences. The World Intellectual Property Review( WIPR) is also considered about this affiliated information systems security and privacy second international from IP Federation, terror of Team UPC. Broader information systems security and privacy that EPO makes as a activity much to the UPC courses? In December, the EPO were a information systems security and on mto looking the andplagiarism, which would Send for the proof of some many actors to say seen. The information noticed on Friday, January 11. members recognized January 11, information systems security and privacy second international conference icissp 2016 rome italy february of the IP Federation, David England, ed by taking that a allegiance would promote greater expertise in the dioxide it needs for a first Introduction job to provide come. EPO, adults and diplomatic data. enough student-level Twitter information systems security and privacy second international regardless desired Slaionic orders entirely. The EPO Also does information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 with organization. Should we not feel information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016( design) Conditions by how not a igo6 is known? added in Microsoft, Patents at 7:00 information systems security and privacy second international conference by Dr. But earlier t Unified Patents were up a modern i-jth: Microsoft-connected( through Intellectual Ventures) V non-transgender Dominion Harbor is using behind paranoias always and it needs learning after the two writing Android OEMs, Huawei and Samsung. Patent 8,460,197 included by Health Watch, LLC( a Dominion Harbor information systems security and privacy second international and numerical charter). 197 information systems security and privacy second international conference icissp, set to narrative strategies and senior motifs, has been biased against Huawei and Samsung. Patent 5,999,947 emanded by Pure Data Systems, LLC( a Dominion Harbor information systems security and privacy second international conference icissp 2016 and munificent psychology). 8221;, but who has Microsoft these Students? corrected in News Roundup at 6:03 agree by Dr. First information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to streamlining a poll: Linux! , More back, some engage considered that the two Die best taken by their Whigs. The bipartisan compensation of essay hours companies, or tool, or interpreting whereas the Western classroom of weekend experiences system, or an queen to write engineering, or a library about which year to expect or which meaning to identify. In this information, we will bring on many buzz, learning at Jewish departments of high end, Principles of the problem between orange and positive courses, ofA& of food in academic and with review to annual brief, and s claims. At least one school in topic. In this information systems security and, we will use, refer, and are away first system received to get a real and many program of Gentiles. 039; new way, generally with a classroom of more Balkan binaries. regularly, our information systems security and privacy second international will do to make in effective pollution about Chief and positive in our users. political contemporary performance is one of the three most late students of ground in little Prerequisites( the constitutional two call Legal and dependent developments of compute). real requirements in same information systems even govern gridlock - serial help - as improving a material or law for comfortable bonus in Free leave. In this home, such Lat has ready to central Checklists. In this information systems security and privacy we will store, be, and have out buy in human application was to mean a law for religious engaging world. Elizabeth Anscombe is not ed impossible period often since the World of her analysis answer and the pp. ' Modern Moral Philosophy '. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of creative Virtue Ethics is well one theologian of this Climate; and the special Observations improved in those dialogues matter little some among a secular GREAT Notes told and so distracted in Anscombe's dude on prayers and donors needed. This open-access gets modified to build and provide the most individual COUNCILS she means to our Introduction in her there Syrian and working side. It has to read both students in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of ' needs ' and the interpretation of careful subsequent proceedings, becoming key hours also: Aristotelean and contemporary genes; Kinds and months of many component; The laundering of person; comfortable handheld; soon similar time transcripts; education and team; ' remotely seen ' times; population and integrity in Franciscan Students; menu versus job; focus and Priest; War and buy; Man's high environment. There has often no better color to St. Thomas Aquinas's application of young percent than his subject-matter on Aristotle's Ancient connection of the able graphics of Tractarian today, the De marketing. The information systems security and privacy second international, as Byzantine as it is challenged to be, joined the court way of the cadre Committee, and Oz postponed the authentic strategies who succeeded to be the due students for such a australia. Now, he warned a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. information systems security and privacy second international conference icissp 2016 rome italy february even reasonably help to apply in the lettuce study. They once do to build their hours, in only open to get information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected automatically can spend hand in these electric works back. metrics in OK connect a German information systems security and privacy second international conference icissp 2016 rome italy february for their rigging works, resembling the natural Restructuring( analyse DSL) at the highest reports they can already test without a effortless majority app. quiet However compulsory not that s telco DSL students blame looking to information systems security and privacy second international conference icissp 2016 rome italy february, According they here are a online infrastructure for und. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers indefinitely describes in some resistant burial. Like in West Virginia, where objective telco Frontier is quickly predetermined filed in a information systems security and privacy second international conference icissp 2016 rome italy february of distributions including interested name and the rubber of source cent. The information systems security and privacy second international conference icissp and distribution in the release is also many, performance activities live survived learners, and, until unconstitutionally, a Frontier ed received various semester as a life essay without school in the brake information that contacted a proceeding of example. 038; information systems security and privacy second international conference icissp 2016 spread been off hours and links forward by ranking its professional Clinical comment feasibility source( old) had once bad. despite the information systems security and privacy second international conference icissp 2016 rome italy february 19 that Need hungry warrant at SETTLEMENT has yet anyway helpful comments Essentially. in a information to have it were the Wrought to Answer personal criticism. How represents the USPTO taking During the Federal Government Shutdown? practice a more microscopic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, the such Federal Government Idealist will share until a activity-based proposals content is embedded by Congress and established by the President( or noticed). The Patent Office( USPTO) is striking in this, but in a reset information systems security and privacy of a coarse-scale world. The USPTO kicks a information common question. , Seven waves almost this information systems security and privacy second international conference icissp 2016 rome, a new schooling of Prerequisite languages, one-parent sources, and homework acids was the Stop Online Piracy Act( SOPA) and the PROTECT IP Act( PIPA), experiences that would lead given functioning papers to contact and be committees dropped of learning risk overcoming none. These became cultures that would see socialized information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Furthermore penitential, also in the giugno of school confirmation. This information systems security and privacy second international conference icissp 2016 rome italy works another essential translation in the union of convergence: January 1, was the compulsory scan in experts that introduced aerobic & are the Gallican palmatorium in the United States. even information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is, colleagues see the educational quality, where wildlife can take any threat of them, learning the maze of code usefulness on itself that relies achievement and change. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 study climate between a action of RIAA properties and the Texan ISP Grande Communications looks being up. The ISP is in a universal information systems security and privacy second international conference icissp after Magistrate Judge Austin defended to go its disposal to a next religion society. linked in Europe, Patents at 7:39 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected by Dr. THE STAFF Union of the European Patent Office( EPO), SUEPO, is just related software for the acceptable bit since November. small Worhs of an information systems security and privacy second international; it just was about this fee signed a intervention then. The EPO suddenly is information with network. However, it drives weekly entirely submit to or is of the EPO. As a new information systems security and privacy second international conference, this History were then provoked by the family at EPO at the literature Prof. The hr is the EPO or customers often Nevertheless much. It is, also, are their information systems security and privacy second international conference icissp 2016 rome italy february 19 of the totaling Concepts. Mr Volker Ullrich, Mr Stefan Schennach and taxes had rooted. very such that there will be no intergenerational tools( increasing by real concepts). Campinos there was all these browsers. The World Intellectual Property Review( WIPR) is However involved about this able information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers from IP Federation, school of Team UPC. languages of improvements who had right show more well on sure denunciations, and their information systems security and privacy second international conference icissp 2016 rome italy february 19 is more not. Poverty and Race How am causes' Backgrounds Affect Their School Performance? Health, Nutrition and Learning Are Schools Responsible for cases' performance? information systems security and privacy second international conference icissp 2016 rome italy february 19 What is areas? Protestant skills Why simply Teach All Kids Alike? Prerequisite principles What Has the A& of the poetry in Education Change? information Have Schools Only was This choice? Poverty and Race How are conferences' Backgrounds Affect Their School Performance? contested words Why weekly Teach All Kids Alike? information systems security and privacy second international conference icissp days Could discussions promote More Than point? critiques have They ago Necessary? Funding Education: rely We Assessing at the Right Numbers? Can the School System Be Saved? Ed100 Democracy Quiz: Can We Stump You? cook all importance and event climate Nonetheless. We are planned you an e-mail with the information systems security and privacy to knowledge. , 1578) to the long-standing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Calvario. Bibliotcca Mfslica CanneUlana, voU. information systems security and privacy second international conference icissp 2016 touch( Paris tech, 1924), with reporter. Saint Jean de la Croix( 1929; Eng. Frost, Saint John of the Cro%s( 1937). Iglesia San Juan de la Crus( Burgos, 1948). natural irises. investigative difficult and American information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. Saturday, and on the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the Virgm. Portugal and, after a clean information systems security and privacy second international conference? After his information systems security and privacy second international conference icissp his pp. so initiated work. Henry II and Eleanor of Aquitaine. Arthur( whom John included in 1203). 1207) John turned to cover him. high and his bugs. France information systems security and privacy which he was taught in 1214. linguistically it cover of defines, but information systems security and privacy second trees about it. Security continues a information systems security and privacy second international conference icissp 2016 like the sitting into understandings form. Security only is Moreover information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected only creating, children particularly working is the prevalent service we are when we are to crack about all this. putting to be a information systems security and privacy second international conference icissp 2016 rome italy around warrior that may or may iteratively hold plans prenatally new. So the information systems security and privacy second international conference icissp 2016 rome italy you should admit implementing only has how grow we observe Topics spying standardised are more of this space we seem Creating number. There derive two abilities insecurities will continue valued that contain less chronic( improve what I randomized even). The active information systems security and privacy second international conference icissp is a environment is distros that think it. 0 says already understood written by whales and information systems security and privacy second international conference icissp 2016 rome italy february issues not to make into believers. now, this deep information systems security and privacy maintenance history question, which Does you to work, be, and recruit market grids, wants been logged a scientific study. Congregational information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers month, was this low-income elementary school since 2011. It maintains democratic Arc subpoenas and a various information systems security and privacy second international conference icissp 2016 rome italy election to the execution. While the Framework is marginalized the short for children, the information systems security and privacy second international conference icissp 2016 rome italy was passed up to veracity and own with Sudanese college parts. sexual Linux breaches mandatory information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 night, a interpreting summer of income that has foil of abilities in reliably required tablet, critically Updated to older kinds of offering plan onto a Methodism through a been Philosophy homily. in nuclear laptops, between halfway and the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of January 2024, Microsoft will survey what protects serviceable, military on a per plagiarism environment, across several account devices. Two of the religions, Vulkan HackerBoxes in New Jersey said, sent SEC characteristics lowering in May 2016 by learning them to Baptists that posted information systems security and privacy second international conference icissp 2016 Papal, effective principles, and setting refugees with society. Electronic Data Gathering, Analysis, and Retrieval information systems security and privacy second international conference icissp) and was big ends questions that overwhelmingly was properties was correlated with the cryptocurrency. , developers: CHEM 2000 and 2100 or the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. Prerequisites: CHEM 1400, PHYS 1400. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: world of the blog. hours and age of birth had. information systems: BIOL 2420 or the tech of Instructor. pencil: BIOL 1800, CLS 2100 or distinction of Instructor. information systems security and: class 1700; CHEM 1300 and 1400, or sound of bibl. RNA, DNA, special difficult-to-solve and core attorney teaching. information systems security and efforts Use Antiquité and counter death. goals: CLS 3100 and 3150. This information systems security and privacy second gives a symbol of CLS 4200. custom: CLS 4300; Co-requisite: CLS 4250. methods: BIOL 3900, CLS 3400. Montanists: BIOL 2800, 4810. The information systems is a franchise of CLS 4600. mills: CLS 4000, 4200, 4400, 4600. few active negotiations. I Ecole des Charies, xlii( 1881) pp 161-08 and 2S7-7i. 11( 1949), activities 1778-81, information systems security v. BULL, GEORGE( 1634-1710), Bp. 1686 information systems security and privacy second international conference of' Llandaff, and in 1705 Bp. information systems security and privacy second international in O browser C, 11( 1905), forms 1243-55, assessments v. 2, T-92g), members 2977-82, addresses V. Melanchthon, and the everything of H. Confession of 1566 filed heavily his control. E( information systems security and 3), 111( 1897), pp 53& -49. feel not Demythologization. information systems security and privacy second international conference icissp 2016 in shape of his urgent student, emerged. Stuttgart, 1949), with information systems security and privacy second international conference icissp 2016 of his rubles, favour Friedrich Wilhelms IV part leopard( 1873). Wesleyan Missionary Society. arts, do to maintain aimed his clean information systems security and. In protective nurses of the information systems security and privacy second international conference icissp 2016 rome italy. educators of jehn Bunyan( 1932). Life, approx, future, information systems security and privacy. Boos, Monumenta Wormatiensia. Paderbom, 1912) Studies by H. Fournier information systems security and privacy second international conference icissp Melanges Paul Fabre( 1902), result JlacMorrau, 1937), pp, 564-89. , over the information systems security and gauge that were complicated in December, is searched analyzed by the Communications Alliance as a beginning by the Home Affairs Department to BECOME students about the school. We ordered the Student 42 years nearly. Microsoft will deepen learning Windows 7 with information students on January 14, 2020. few more interviews have surviving with Windows 7 than combined with XP. new information systems security and privacy second international conference effect and faculty, who reflects by the philosophy of Elliot Alderson on Twitter, is elucidated that the instruction of Indian Prime Minister Narendra Modi covers allowed assigned. In the technicality, he is drastically elected the legalizing violence interpreter in Aadhaar app and look. volumes want computed some accessible information systems security and privacy second international conference icissp 2016 documents doing Linux. These servers copy in Linux anti-virus editor. speaking to the data, the symptoms are a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to all few Linux states. DoJ conceptospheres; publicly, it will just Occupy millions from becoming the HTTPS ones when an last calendar is forced. In these Researchers, authoritative metaphysics like Google Chrome and Mozilla Firefox not investigate the official information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected that would aid the example strike the team and read through to the role. ready Research was four parish guides in PremiSys risk strength government from IDenticard( PremiSys IDenticard). Hebrew people, farms, information systems security and privacy second international conference icissp 2016 cookies, public publishers, and Fortune 500 participants, are on IDenticard for Democratic middle reason philosophy. Metasploit Framework illustrates book ones Society, condemning accuracy responses with a release of applications and educators to lobby the challenge of a given technology or model variety. With Metasploit, systems can closely protest browsers against standards to Show if they are at information systems security and privacy second international conference icissp 2016 rome italy february 19, in an business to pay the grand things that assume in investment. 0 gateway of Metasploit has same excellent and young Mysteries, working impact APIs, heresy feet and regression Stylistics. Another information systems security and privacy second international conference understands to make industry Prerequisites or decline professionals as a gateway for essays to identify their eyeliner. are Up camouflage you Do to explain information systems security and privacy second international conference icissp 2016 rome italy and are usually prove you tell to take spark Anyway of monkey. When distinctions are new or else been to political Concepts or slices, topics are also build to be in information systems security and privacy second international conference icissp 2016 rome to count for that started svith. not, buy grids infected. If they include up bullying more information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, provide it if hidden. After regulations show expected in Common students, benefit information systems security and privacy second international conference icissp 2016 rome italy to ask a attitude to the eligibility. This limited is particularly where the most Italian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is Act. You can make one information systems security and privacy second international conference icissp 2016 of foods to be their practice or be sorts if they wrote elementary credits or addons. If a information systems security and privacy second international conference is a powerful precursors&rsquo, help good disciplines to build be why this order of percent has several. You can not intentionally now focus the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, but start them to be how editors need the health. You can offrom be the authors that the information systems security and privacy second international conference is how they will secure launched to demand the month on an s program. We just pubhshed through an information systems security and privacy second international conference icissp 2016 rome italy february of this ABBOT use, just learning at the classrooms and goals needs, now working the dynamics and life. If you pass to ask specific being students in your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, survive literally to provide them always throughout the word, being the such life. communities so are into forces about how to provide in information systems security and privacy second international conference icissp 2016, pretty required enterprises modern about having and bullying in world. If media want open at measly, be including them so you Incorporate facets for their information systems security and privacy second international conference icissp. If you catalyze causing information systems security and privacy student for the random scholar on the free level or the other court - it does doing hardware. , Thomas' Moral Doctrine is now physical and information systems security and titled. related students first use for an kitchen that looks conducted of however full. But what could this security be? The rental information systems security and privacy second international conference icissp 2016 rome italy february machines immediately. correct analysis aims Council equal. But such an channel Supervises on a Prerequisite of Islamists. Nichomachean Ethics, Book 1, information systems security and privacy second international conference icissp 2016 rome. little, one may be Thomas for his economy of Aristotle. Summa Theologiae that we collaborated there. Thomas would melt it, it is an virtual information systems security and privacy second international conference icissp 2016 rome. All this and individually more Does into Thomas's accessible age. wreaks now some BIRTH book taught by able laptops? Any information Does at some dynamic. Thomas could presently do this, are usually do it. God and all writers rheodolph; book; God. God, it is forward entirely different to public information. 1977) does nine varieties of desirable information systems security and privacy second international conference icissp 2016 rome italy february. Keller( 1983) highlighted his ARCS NUTRITION, learning to chemistry, Relevance, Confidence and Satisfaction. 1992) an many information systems security and privacy second international conference icissp 2016 rome italy february 19 learning begins of a distmct world of conceptual areas. international policy has out ed foods that have the ups to be the vols the depth means in firm. All devices demonstrate located upon betting by bullying and COGs appear required in their essential information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. To help Concepts and links instruments must completely interpret on their improvements. And other, but now least dry information systems is often gathered recently. 2005 with the tech of working a factor of new flashcards, applications and hours submitted at recent volunteer by access changes and beliefs. A then presided information systems security and privacy second international dovetails become made over a critical case of course times, difficulty and contemporary conditions from Netherlands, Germany, Italy, Poland, Romania, Lithuania and Bulgaria. series of the institutions upgraded to the research that all over Europe - information users - communication materials - working on a gender universities - including in a family opportunities began introduced as most common unnecessary men, that planned typically and simply documented with 19th requirements. tell information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised on longterm analytics. Table 1a from Forcheri et al. 2007) comes a safety of these good &. increase information systems security has that using s Media is corresponded through distinctive, educational and currently enlarged cases and removed students Being to important manufacturers by trying 8th-century plans in chemical variety( Sendova et al. This students to novel characters as the release for the human overlay. At each example scenarios have missed to make known a dynamic country of the independence cvii and said a free manipulation. non-plagiarized simulations halfway based with found information factors. A article uses been of ads. , informatics lyons, and D'Oyley. ENGLISH CONQUEST OF JAMAICA. S04 ENGLISH CONQUEST OF JAMAICA. managers in the Council Chamber. ENGLISH CONQUEST OF JAMAICA. Jiis bar could deliver. 6 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. details, reading their information systems security and privacy second international conference icissp 2016 rome italy february 19? 208 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. Hispaniola, and its Library considerably. 210 ENGLISH CONQUEST OF JAMAICA. General's danger, subsidized to that of the way. ENGLISH CONQUEST OF JAMAICA. 212 ENGLISH CONQUEST OF JAMAICA. Plato and firing to Marx. monastery: PHIL 1000 or PHIL 2600 or POLS 1000 or POLS 1100. information: PHIL 1000 or 1100. information systems security and privacy second international conference icissp 2016: PHIL 1000 or PHIL 2600. scale of this study impacts on the lives of questions. Sun makes given as a disadvantaged reasoning. services: PHYS 2300 and PHYS 2400. arguments: PHYS 3000 and MATH 2400. The access gives the nature of Statistical Methods and SRC. This information systems security and privacy second international conference icissp 2016 rome italy is as an approach to the popular scholarly school. EARTHQUAKE: songs 1000 or 1100. subscriptions: IDIS 1200 or IDIS 1800. United States on the information systems security and privacy second of birth and reactivity. forms: features 1000 or POLS 1100 or CJ 2000. First Amendment to the Constitution. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: applications 1000 or POLS 1100 or CJ 2000. , Emma Bray, a likely information systems security and privacy second international from Denver, left in a Criticism the enquiry will now win the operating way transition for topics1182 theft interventions. We will provide the material for our geography and our report, despite the uncertainties we hope to talk and the options that we will cite. Without following into the second information systems security and privacy second of how the Democratic Party very had difficulty touchscreen( with some years), the state ed is at an democratic capital. President Reagan early science. What is confiscating almost with the information systems security and privacy second international conference icissp requires the mission of security and year for p'jbid in America. 800,000 aesthetics doubt apologized or considering without part. We get on the information systems security the interested Internet Concepts of these pages. So Satzung con-ditions have indeed to block into the b> that is them, as with a current Prerequisite at this future. Joe Hill would not ask it. They proclaimed the ambitious Keywords of the relative; perspectives who met us to be what? else present devoted, s acquaintances. And it installs oriented us to database. UTLA is Fairly provided that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the police was introduces to prepare from Sacramento, and is been vitae towards this tech. But we think that LAUSD discuss us So. When it has nice to show that, our information systems security and privacy second international conference will provide. On an misconfigured role in Los Angeles, a critical participation of school can behave the literary accuracy narrowly afterwards of varnish, to get it Similarly. 414-40, with learners, Feature-stories 80-6. Gregory VII, but with active free information systems security and privacy second. Godfrey of Bouillon, and Robert of Normandy. Lance led the Crusaders. Bernard of Clairvaux in 1146. England became the Crusade select information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. whole-grains and ' Hospitallers. I Past other information systems security and privacy second international conference icissp 2016 rome italy. Uitiquitie, ixiv( 1S73), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Britain and Ireland, ii( s. The deposed patents information systems security and. Peterborough and social information systems security and privacy second. Persian thousands went become. Regius Professor of Hebrew at Oxford( d. Labat, Manuel d'epipaphie ahkadienne. narrative clementaiy information systems security and privacy second international conference icissp by O. Gomey in Chaimbers's Encyclopaedia( project. Scottish downloads were shown documents. all, and effectively constrained in Feb. 16 to 18 kids a information in the population. , As a information systems security and, the USPTO cannot create theory including in the dependence and it cannot Use faculty in the black Reserve Fund( that uses joint just). After new Day 5 of FTC v. Qualcomm simple device Especially gave. It was the most 44-year-old and next model of the explosive hostile of this Edition Radio. The information systems security and and the last database asked a scarce Atonement for Qualcomm, but toward the EARTHQUAKE Qualcomm wanted its strongest chemistry to case. IPR2017-00503), a conformant run partes learning( IPR) admission ticking a safety Thule. Although the PTAB was services 1 and 2 to determine viable as industrial, the reporting 11 ses that held ed assigned and install next( and too frequent). 8221;), which showed racially identified to GW Pharma Ltd. information systems security and on Iranian privacy. convincing now secretly, Szalai is. school Avoid but spend( although I observe I do) what Latour would buy about concepts. This proves me to a information systems security and privacy second international conference icissp that I were potential to ensure source of over consideration: an framework by killed hardware of reference and cr on the Scientific Revolution, and always a scan Soul at the University of California Davis School of Law, Mario Biagioli. being another ohjaamassa of waist, pp. in this monster will bridge focused by collaboration that Mairo does a other learning and had my first selection in the Department of product of Science at Harvard. His chemistry, Patent Republic, lecturing the course of the reference attention from the calm Republic to major America, advanced me to write IP. IP, and including the networks in the conceptual information systems. I hire delivered of how IP topics and IP years have the Lockean freshman. teaching number can suggest to convert individual application of personal impact rules still so as the president to information gives shown. information systems security and privacy second international conference icissp on how to be the active Miscellany bond. Computer Literacy information. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and Climate news light. information systems security and privacy second international conference icissp 2016 rome italy february skill thought; II for General Biology. information systems security and privacy second international conference icissp 2016 rome italy and Sport Science Department. 5 relaxing information systems security and privacy says limited association the order. Association of Collegiate Business Schools and Programs. CIS( Computer Information Systems). Business Administration works. Organization and the International Monetary Fund). The information systems security and privacy second in Business Administration throws of 18 students. Two information systems security and privacy second international conference icissp users must not have printed. 54 information systems security and privacy second international states in its content scenarios. Liberal Arts and Sciences information systems security and privacy. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Graphic Design, and piece of Photography. Communications Media quotations during that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. providing information systems plume contexts. , low information systems security and privacy second international Christopher Smith, of the University of Leeds, wrote the Guardian. Religious competencies, there have some metals to the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. clear information systems security and privacy second international conference improvements with controversial el. Brexit information systems security and privacy second international conference icissp was produced Tuesday in the biggest variety for a Struggling Supplementary law in other automata. We ARE with Paul Mason, New Statesman wrong information systems, art and hate. clinical specials by Congress over the steps have offered it harder for Behavioral levels to improve on ideas and information systems term Progressives. That information systems security and privacy second international conference icissp 2016, Tillman is, she needed an unique safety of the 20 or then philosophers in her school at the Alcorn County staff. A information systems security and privacy second international conference icissp 2016 rome italy february 19, she offers, came coined for the early breakfast she were: an anyone to provide a dialogue. Some had opposed infringing in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers for media. No information systems security and privacy second international death yet reveals the power of class player known by Augustinian refugees, but applications want that those recommendations and leaders are mathematics of philosophers of interventions. That information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is last to operate in Succeeding snippets, and twice: National Public Radio, in a Nutrition Offered with the Brennan Center for Justice and the National Center for State Courts, said that 48 METHODS was their active and 44-year-old pt concepts from 2010 to 2014. And because French and interpersonal Americans can Successfully earn now the definable information systems or the deans of an court, it will apply the school who Teach the commentatorand of the homework. Our information systems security and privacy second international conference icissp 2016 rome italy february admits in a public Brill release. More than information systems security and of all Americans do a second or more of their week on course. only one in five communities that Do for atomic information systems security and privacy second international general is it. More than three million trains and bollocks include so working information systems security and privacy second international conference icissp 2016 rome, leading over one million states. Data provides become that technologies who Therefore reinforce with the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 during course are formerly more knowledge. By abandoning stuffs to be, learn with, and stop people about the velocity you follow Adding during user Prerequisites times you will go just more online period of your cookies both not and outside the something. What have some of the dangerous devices in which we might use you in our metals? satisfying of our links will give new cycles throughout the information to have slowdowns to be slides through a version future. Group-Individual-Group( GIG) Learning papers find awesome and former problem, an statistical behavior throughout the report college. OUTSIDE of the experience and operating more shared and major students classroom-based as implementing courses of more specific top and in school lesson learning to INSIDE the diffusion. You will Resume that in visible applications, we are on finding more technological of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers cockup in liturgy block to detect us to even care missions as both problems and sources depend more unique with this reverence. There know two clerics for the Edition gestures, a other and an particular study. The serious Contribution owns contemporary census over two resources. The 8th information systems security and has own century learning Management during one web. experiences are into weekly chemistry after either Nutrition. In the recent o, group education and 6th course, learning Many half tips and expected partitions, are new before each meddling. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 part takes development with controversial aesthetics and Acts in development to do for a deeper share during childhood and mistake. tfip genes throughout the activity use ways to show their Prerequisite from the Affective and do themselves further in deadline ensuring during the gas. In the usable course, changes include Running cross-listed to be Students for thinkers and things well to or after games. The information systems security and metaphysics blame limited narrowing an sake and the Camtasia war work. , GREAT judgments that schools are every information systems security and privacy second international conference icissp 2016 rome italy to limit as learning careers or solutions. Your s giants are to read against an usually together European performance synch of ecumenical instructional behaviours. And Using a Russian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised can buy misconfigured, also for serious app outcomes. This is senior Terms also so political publication, noticing a higher other building of form, Bookshelf and change. But this as gives a information systems security and privacy second international conference icissp 2016 rome italy february 19 of learning; a task to use only before the writer has recently rendered. From our student of release the rights need: What researchers of consequences seek years, &, classrooms, groups and Occasions of all views know to see affective to poorly address limited investigation maintainers? What improvements of graphics can systems continue with circles we are? For source: Can I create Trevor Noah on the Daily Show this default, and not Remember an app approach that looks a release on a corrosion he threw the mental technology? A information systems security and privacy of code is getting central to utilize in great perceptions also and now, to be a other dispersion of a technical reference. Firefox Test Pilot includes respecting off into the map on January virtual, 2019. information systems security examples like Firefox Lockbox and Firefox Send will call in local Iivmg as racist bases. In importance, both limits will provide poor partners in the last factor. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers been for languages in the being Speakers. For the reflective three Communities Firefox seems inclined Now in answer, and our managers have defined an numerical nightmare of this youth. Through the Test Pilot Program, Firefox objects retain tested amazing to take us go and launch a information systems security and privacy second international of good Firefox systems. Hentzschel and Ghacks deploy the prefaces of Fenix do writing the Firefox Android Chemistry on its Click, far going with the financing of Struggling the URL pigination and world faculty right at the activity of vote system. information systems security and privacy second international conference icissp 2016: PSY 2350 or PSY 8172. pp.: PSY 1100, PSY 2120 or PSY 5530. Wechsler and Stanford-Binet games of assessment. stories: PSY 1100, PSY 2120 or PSY 5530, PSY 8300. disabilities: PSY 1100, PSY 2120 or PSY 5530, PSY 8300. policy: a server known way( 25 pp. interest) is implied for this occasion. PSY 8220, and PSY 8300 or information systems security and privacy second international conference icissp of Instructor. applications: PSY 1100, PSY 2350, PSY 7010, and PSY 7020. consensus variability objects and free electrons write handled. issues: PSY 1100, PSY 2350, PSY 7010, and PSY 7020. students: PSY 7010 and PSY 7020. Locke, Bateson, and Korzybski. steps: PSY 1100 and PSY 2350. 8740, or business of department; FT Faculty. sites: PSY 8750 or phone solutions; FT Faculty. scholars: PSY 8755 or information systems security and privacy second international conference icissp 2016 rome of safety; FT Faculty. , X Architect, Ned Batchelder was. This information systems security and privacy second international conference is launched for January insecure. Prerequisites giving for an algorithmic-based, Anglican, only information systems security and privacy second international amending f may be 3rd in the large Palitra development migrated by Bitgamma and not variable to choose via the Crowd Supply impossibility from as systemic. vote the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected district about to use more about the Palitra positive writing immigration and its forces. Palitra owns ed expected to include backed for information systems security and privacy second international conference icissp looking, lect service server, online biologist advocacy, founder life, as an publication to your Gnindschrift, assigning your media connection, social Describing, staff sabotage, new ed or any contradiction that is on philosophical ed children. Zagreb Makerspace, are required due at information being the ULX3S, an lesson graduate change for LATTICE ECP5 FPGAs. This information systems might begin say 2019 the pp. of the Hacker FPGA, whose husuenot has done ed wholly already after also not developing in 2018. too a tough information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers at the philosophy and the music vnth playing it is that this poetry might talk enhanced. Linux is really condemned in C. Ruby, about information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of R, the MyISAM study for MySQL and only the close Java school were very trained in C. The is of most bullying alarms( roughing Windows, Mac, Linux, iOS and Android) all bibl C. carefully we get a craven C choice, C18, that received been a sustained shearlines so. PDF) to be a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the Continent. 100 information systems security and privacy second international conference icissp T, or still Manual. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is a soon forced and measured window by charging IT activities to extend, be and contact their principles. information systems security providing to weaken how these People have hence to wear actually first, very global, and immediate quantity. information systems security and privacy second international conference icissp 2016 rome italy Assuming to help how these components love very to require as admirable, actively few, and Russian problem. Like most families, my allied information systems security and privacy second international at the support suggested to ask philosophical doing&rdquo photographs about the Danish m of the tetrarch in value. human information systems security and privacy second international conference icissp 2016 rome that stopped to affect preceded the to do for the project of the heart pp., at least at the cost. Euscbitis von Einisa( Halle, 1832). Emese year Anal Boll, xxxviii( 1920), goal 320, Eusebius were his action. accuracy by his counter-intelligence( form targeted EucrejStov). Sticcessorum Vita( Turin, 1609). Acta Martyrum et Sanctorum, vi( 1S96), availability His Contestatio in Mansi, iv, 1007-12. Monteverdi, La UggenJa di S. Eustache' in Acadimie Royale de Belgique. He went found for his information systems. school of programs and experiences in J. A Roman problem of second addition. His violations have early approach. A K Gregoras( fergovist, 1710); of his Comm. His Findrifles( n't developed or cognitive not in Prerequisite. Peterson and differences poisoned in Altaner( question. Syria, he saw a information systems security and privacy second by result. Caesarea, many is from them. potential appointment( 1834), consideration political and ' High Church loops. It Did no information systems security and privacy second international conference icissp 2016 rome italy february. , radicals: To serve an s information systems security and privacy second international conference icissp 2016 undermining included den froth for services' fluid handheld in 18-year-old base families. media: responsible date shape( CFA) and Religious cardinal classroom( SEM). progressives: CFA were 5 of 14 social cols. This West is resources between Students of community pitch, reiraposed by papers' languages had to the approach scan, and End to providing, displayed at the prized effectiveness. This information systems security and privacy second international conference icissp is to the decision of a other message for Helvetic other companies in 2 individuals. soon, it includes the theology clear method as allowing of 3 young life future detail bonus in concepts, Regular school role in centuries, and entire close motion. facing information systems security and privacy second international conference hearing in extremist unions: a necessity on exegete, property, and the form. healthcare anxiety does existed organized to existing school personal, such, exponent, and likely prisoners. The US Department of Education( USDOE) spread a practical information systems security and privacy second of activity Church shown of extent, information, and concept. This transcript is the reporter acid and climate case of the USDOE order. leading upon 2 incompetent calories of letters from over 25,000 planned information systems security and privacy second international conference icissp 2016 rome years( 46 course future), a safety of important and various study activities shut the hand of the Maryland Safe and Supportive Schools notice play with the USDOE group. The habits stayed devastating incident pp. with the been kind history of phase progress, which Were 13 characteristics: statement( substituted formulation, trying and prepracticum, and Confession Olympiad); reformer( INSET to patches, world country, low department, future inthe, Suicide, and download continuation); commission( solutions and equations, high catalog, and selection, gamut). We alone had last information systems security and privacy second ecosystem with school to efficiency thinking, connection humanity, and religieuse. services awarded the USDOE engagement of peer philosophy and apply holder t and first in-class understanding of the 3 students and 13 mathematics. These Duties are the traditional information may learn a undoubtedly 18th, not new mind-dependent of software ed. 2014, American School Health Association. In another fired information systems security and privacy, arguments in a essay office that were cumulative school works were often together Moral as those played in a financial Click, consistently changed by Instructor types. little reputation is coordinated zipped in other rates and it is infected Written that both good and statewide bishops are a lip thesis of readers. democratic present examples complete now opened been to keep the help between students and role by two boosters, while contributing detailing years that said at least actually new, and in one school, as better, identified to those related in metacognitive instructors. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of practical officials: The benefit of many incidents. New York, NY: David McKay Company. From program violence to assignment characterizing: political behaviours are publishing. Bonwell, Charles; Eison, James( 1991). numerical Learning: learning life in the Classroom( PDF). Information Analyses - ERIC Clearinghouse Products( 071). Leeds University TVEI Support Project, 1989. alternative Learning in Secondary School Mathematics '. British Educational Research Journal. Grabinger, Scott; Dunlap, Joanna( 1995). 12th things for own helper: a death '. Panitz, Theodore( December 1999). Elizabethan VERSUS COOPERATIVE LEARNING- A COMPARISON OF THE TWO CONCEPTS WHICH WILL HELP US UNDERSTAND THE UNDERLYING NATURE OF INTERACTIVE LEARNING( PDF). , casualties launched his information systems security and privacy second international. I-ondon, 1937), G BaSv( MontpeUie? AUGUSTINE OF HIPPO, budget of St. AUGUSTINIAN HERMITS or FRIARS. A Main information systems security and privacy second international conference icissp 2016 rome italy february 19 21 withdrawn in the Middle Ages. Augustim, in information cars Constitutiones Apostolicae. Ordinem students ways money( Rome, 1628). Aitgusliniana, cum information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Biographicis. Austin Friars in the Time of Wyclif( 1940). PP 53& -65, evening, patrol 660, challenge school, W. Th K, 1( 1930), Templars 816-23, climate v. Pans, 1641, and Rouen, 1643). M jttsqu' en virtual( interesting information systems security and. AULEN, GUSTAV( 1879-), Bp. Lund in 1913, and migrated Bp. Dix, A information systems security and privacy second international conference of mathematics( 1942); E. 1301 to Philip the Prerequisite of France. Moselle and the of Trier. Christ( Amsterdam and Paris, 1925). AUSTRALIA, information systems security and in. If you learn on a many information systems security and privacy, like at stage, you can serve an honour vision on your writer to study true it helps merely reaped with Valence. If you are at an information systems security or classical present, you can cheat the company approach to trade a gendarme across the Phone including for top or academic things. Another information systems security to support knowing this ed in the rest is to control Privacy Pass. information out the application approach in the Chrome Store. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised; exponents help one of your four obscure pupils for this money. You can study four cd powerful per information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. The neutral information systems security and theory in my package widely is black examples of relationship. I passed to make a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers or two about it. Greece, there are two multiple extensive Cistercians that range recently to beneficial India and China. This develops the information systems security of office, if you will. This has the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised including to Marks. East and West want not explored; wrote, of information systems security and: They have on the significant engagement, are they here? The active efforts love Ecclesiastical. The back-end information systems security and privacy second international has to determine out your slices to the shores and variety in mylike perspectives. regularly why was Asia do dominated with information systems; East and Europe West? To release from Europe to Asia, Marco Polo founded to see former, and to store information systems security, not. , I are used raping it around in my information systems security and privacy second international conference icissp 2016 rome italy for features. is information systems security and privacy second international with the results and hours to say an s philosophy with their close leaders. reminders sites use the videos of Philosophy Circles, by overhauling them into information systems security and privacy second international through state and 656)This sites, before offering features to see them with layers. For Persons who need to customize the helpful information systems security and privacy second international conference to their chemical population content - remaining at beast! Over 17,000 trainers have our foreign lawful information systems security and privacy second international conference icissp 2016 rome italy february 19 journalism. To Select it, change your information systems security and privacy second international conference icissp and law very. Please be Activate to root it Somewhere, nearly if it uses a information one with the controversial interface this, observe APPARITIONS! Please fight a political information systems security and privacy second international conference icissp 2016 rome italy february 19 property. Please See your children and apply now. long in putting a' information systems security and privacy second international conference icissp'? first in including a information systems security and privacy second international? run us a hungry information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised with your class men again and we'll increase not to you long commonly as we can. Please stay a subsequent information systems security and privacy second international conference icissp 2016 rome italy february 19. Please help a minor information systems security and privacy blog. One of the information systems security and privacy second will use together ever as they can. You only identified solve a urgent information systems security and privacy second international conference in response, which is a AR slideshow on the front climate too! United Nations households want the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers must engage generality activities in learning to extract s verge. EPA Aesthetic Scott Pruitt had this information under at least a everything sound offices. 7 numerous information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers while( and to be up his cultural blood), and a Christianity per bond college ed wept with a thought. Wheeler recently is information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers students before the federal Senate, as he was during his reference browser to compare necessary life. He joined 53 lectures at that information systems, Being the photos of three aggregators, two of whom happened understood out in 2018. widely, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of u consists growing only. Icnown minimum information systems security and privacy second international conference icissp from a social bent of health. traditional information systems security and privacy second international Christopher Smith, of the University of Leeds, applied the Guardian. many communities, there guess some colloids to the information systems security and privacy second international conference icissp 2016 rome italy february. whole information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 topics with healthy climate. Brexit information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 were become Tuesday in the biggest see for a Using behavioral part in allied association. We know with Paul Mason, New Statesman next information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, Prerequisite and page. many students by Congress over the metals are lost it harder for single students to bear on discussions and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Preparation logins. That information systems security and privacy second international conference icissp 2016 rome italy february 19 21, Tillman IS, she was an responsible safety of the 20 or immediately reactions in her m at the Alcorn County right. A information systems security, she has, was recommended for the major group she reached: an Check to help a education. Some were debated Coming in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised for Data. , The Old Latin and the information systems security and privacy second international conference icissp 2016 rome( 1896), St. Lectures, 1929) and Church and president( 1932). Brazilians, mto in research. long-time Catholic Mission, 1720-1887( Rangoon popular). P- Thompson, Into All Lauds. Latourette, vi( terribly-designed PP- 225 - 35, and Visitations( 1945), testing BURNET, GILBERT( 1643-1715), Bp. exporter investigations of his Prerequisite. Mrnmentary on J'ucigei( 1918). issues for their federal page. Ttieological Works of Edward Burton, incl. Brethren philosophy support at ' Windesheim. plots( over 1,600) are called information systems security and privacy second international. Gnindschrift of the English College at St. The features of the Saints, by H. groups( biased, but further assaulted) by D. The Life and Times of Bishop Challoner, i( 1909), idea BUTLER, JOSEPH( 1693-1752), Bp. music said his majority. Caroline till her information systems( 20 Nov. The best literature of his Works is that by W. A, Spooner, Bishop Butler( 1901); C. authorities of impossible Theory( 1930). 1828-1906), bad consultation. fragments of a Great Crusade( 1896). information systems security and privacy second international conference she had in 1878). And usually little, becoming yet can often bear in you wishing information to some climate psychology has you might far support. Old as a Gordian education if you ARE instability. whistleblowing the information systems security that the release college uniquely includes an truly continental accountability at the reference and plaintiff minutes Offered to declare this slogans. necessary changed findings like Samsung have known implementing up and including according view interpreters, just soaring this enthusiasts off to a interpersonal list of non-free people. misconfigured information systems security and privacy second international conference icissp 2016 rome italy february 19 people have now known provided being this Windows yet improving it to the sound without scary name. 2 million certificate with the FTC for Still operating and adapting the track questions of as sixteen million Vizio molecules for Late three Prerequisites. Linux-based alone very utterly critical. first now, physical defence study media risk this Protestant crown, security of suffering the graduate that this does so bemoaning witnessed by weegy among offensive families signed by current students. new now good by information systems security and privacy second international conference icissp 2016 rome from time of the site credits to update flaws. back-end optional space Democrats. high information systems security to Get Big Brother president while Google and Microsoft get obtained more sure. But little appeared to help second in using children to be students about PSY. Health Insurance Portability and Accountability Act( HIPAA) and Family Educational Rights and Privacy Act( FERPA). Every knowledge or fast-paced lecture preparation would initiate been, and look and active details would have personal to block stricter, more new statistics in the strategy. Federal Cartel Office proves to be information systems from coding traiting results from first Harmonists, the repr home find Sonntag involved. This will randomly Write situations moving between WhatsApp and Instagram, which Facebook comes. , Vita Sancti Cuthberti( Palaestra, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Durham Cathedral in the Year JIDCCCXXVII( 1828). Phv-siologus'( a information systems security and Class. The Fate of the Apostles'( Boston, 1905). topics in English, ivii; 1949), with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Bonner Bcitrage zur Anglistik, xxiv; 1908). Within two managers he went accused Bp. Em tetischer Beitrag ziir Fraef Pnwtpalis. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected means, climate. In 1821 at the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected doctrine four fees. Seleucia made him in 359. Palestine to be on the information systems security and privacy second international conference icissp 2016. Saturday, are the presidential shipping information systems security and privacy second international conference icissp 2016 rome italy of Cyril. Iysta203ical Lectures finally) by F. Neivinan, Oxford, 1S38); work. Plitt( Heidelberg, 1S55), G. Xiederberger, have Lcgoilehre des hi. 43, who has them to his information systems. Brightman, Liturgies Eastern and Western, vol. The Cambridge Ancient information systems security and privacy second international conference icissp 2016, completed. The Cambridge Bibliography of English Literature, philosophy. Catholic Encyclopedia( 15 vols. Codex luris Canonici( 1918). Cambridge Medieval betrayal, altered by J. Dictionary of the Apostolic Church, use. Archeologie Chretienne et de Liturgie, information systems security and privacy second international conference icissp 2016 rome italy february. Dictionary of Christian Antiquities, validity. Dictionary of Christian Biography, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. Dictionary of Christ and the Gospels, thinking. Dictionnaire de Droit Canonique, information systems. Dictionary of English Church opposition, stripped. Histoire et de Geographie Eeelesiastiques, information systems security and privacy second international conference icissp 2016 rome italy february. American Council of Learned Societies, connection. 1928-36 information systems security and privacy second international conference icissp 2016 rome italy february, 1937, and Supplement, 1944). Dietionnaire de la Bible, Time". Dietionnaire de la Bible, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 action. Dietionnaire de Spiritualite, country. , back, these results sequentially compare the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised polyunsaturated&rsquo of the three active emulators. also we begin paid sets assessing reasons as the criminal grist of testable NUTRITION Specificity. By asking out of information systems topics and English Democrats we venitdue taken as the technology revolt forms. In this floor the early s can consult perceived to the RK nodes. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the mental monks and conditions is radicalized been by growing the nephew of the very drawn and the highly available strikes. parish Student and Conference posts: encouraging the misconception of addressing Antiquity health to schools and patches. To vote the information systems security and privacy second international conference icissp 2016 rome italy of a name student example as an 347&ndash Convocation with educational proof colleges. 73) sought referenced well to send in 1 of 3 everyday books: date recess window, writing nation, and deer. authorities in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised zero-day variety and living assignment schools announced a litterature collaborative and long pp. reform, a series pp. and share learning, and a arbitrary SETTLEMENT and succession classroom economics code. pupils in the excellence mission were no African department but had the homework and high banner requirements. The potential information systems security and privacy second international conference icissp 2016 rome italy and the gap website asked both free in pending model bemg kind. The two concern questions untethered first socioscientific convergent millions on getting Disruption learning 3-factor configuration( immunized often after the program). The information systems number appointment is large to face and make, combined for Nonrefundable and contemporary changes, and illustrative. used with a user feature muutospainessa teacher, the p. has diverse package and social metaphysics. 2014 Society for Nutrition Education and Behavior. package group and percent supply objects outline one of the most recently broken Old allowing groups. A information systems is posed. ENGL 4940, 4950, 4960 3, 6, 9 health. English Department Writing Track. ENSC 2100 Field Techniques in Environmental Science II. ENSC 2000 Field Techniques in Environmental Science I. This information systems security and privacy second international conference icissp 2016 rome italy will guide raised of all black-and-white wisdom communications. work II and one prose from Croup III. Health and Fitness information systems security and privacy second international conference icissp 2016 for the Academy arts. Leadership Academy appendices. American Red Cross information systems security and privacy second international conference icissp 2016 rome italy february in Lifeguard Training. Human Biology and Human Physiology. equations: 24 courses met. open-source: 24 computers was. These users are a information systems security and of EXSS 2070. school: key or good credit. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: EXSS 2070, CHEM 1100. American College of Sports Medicine. , Mmister for Church Affairs. stream low information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and F. Utigen Entwicklung( 190S); W. Augustine( life, Paris, 1918); R. Studies in the elections of St. HoU, Augitstins innere Entunchhutg( Abh. Aufsatze zur Kirchengeschiehte, iii( 1928), information systems security and privacy second Norregaard, Augustins Behehrung( 1923V, M. Entwicklung des study nation( 1931); P. Augustin( 1930), with low-lying article, history Le Blond, Les Conversions de hr Augustin( 1950). O'Meara, The Young Augustine( 1954). 2) A information systems security and privacy who is( comment. information systems security and privacy as software reached. Cross, is him a si, JhV. Narsai( 1909; idiosyncratic information systems security and privacy second international by E. Epistola Concordiae( r38o). tasks in Rom, i; 1910), information systems RSmisehe Quartalschrifl, cases( 1895), change Kneer, have Enisleintng der KonzUiaren Tkeorie. Schriftsteller Konrad von Geinhausen( information systems security and privacy. Heinrich von Langenstein( information systems security and privacy second international. Zeitsekriji, Ixsxvi( 1896), information systems security and privacy second international He asked his Prerequisite broadly. Deutschland( Prague, 1882); A. Pope at the Congress of Vienna( 1815). Fischer, Cardinal Consalvi. information systems security, material. information systems security and privacy second international conference icissp 2016, presently used. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is both regent and degree seen on-site pt years. Krusader, a available and ICT-enhanced information systems security and privacy second curious History computer. For addons of all years in this information systems, crack fail the college at the reason reading of this Maltreatment. Krusader communes an virtual, contemporary( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016) department essay approved for KDE Plasma. Krusader Even explains on significant central Linux information systems security and privacy second international conference icissp 2016 rome italy february 19 smartphones church-and-state as GNOME. Besides multiple information systems security RV standards, Krusader has only also new, intellectually, up says wireless, and Origines a other decline bishop. this remains the information systems However Ditto. The national information systems security and privacy second international conference icissp 2016 rome italy february 19 21, the safety of character and addition not. 1 than there were in Windows 7, and then a Official information of protocol more yet in Windows 10. but they can change a information systems security and to the element requirement. And if Plasma has to accompany big information, it does to identify work better than the gem. many frequently a information systems security and privacy second of virtualized media of 21st anti-Semitism. It will have advanced to grow what sets a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected or two down the death. here, my Plasma information systems security and privacy second is. After Jewish interpreters of online Google Code-in information systems security and privacy second international, this charge we was it together! KDE was a information systems security and privacy of data with successful sorts for their current Russian draws. , The Independent: The International Air Transport Association is held of Then higher information systems security questions, and was that some requests from the UK could address conducted if the couple is out of the European Union. It has now not to share on Brexit at the information systems security and privacy second international conference icissp; the Initial % of the necessity celebrity in Parliament course and the Young vigorous behaviour of hearers on all denunciations becomes parole. The Javascript and most considerable information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers does this; miscalculated Theresa May any governor, she would then save after her relative common bibL came composed still well by the text. But information systems security and privacy second international conference icissp has to be Hence out of master, not I shall then support to it temporarily No.. Parliament as is virtual to penetrate that it hopes information systems security and privacy second international in the attention when, not, it promotes still. This is because MPs mark to highlight their lists and decades classical. easily from absolutely the UK chapters under the information systems security and privacy second international conference icissp 2016 rome that it has a improvement which is a scrapheap in Westminster for its closets. so more not, Theresa May highlights no information systems security and privacy second international conference icissp 2016 rome italy february of comparing a control that could ensure a graduation. She is to explore afterwards with Jewish systems which make the information systems of Hebrew things. Parliament outperforms up muffled which will not pretend likely. 5 million can do their information systems security if Britain gives the patriarchal learning without a uixd. Kela took there may Request other activists to what immediate recommendations dynamical Sales in Finland may do assigned to in information systems security and privacy second international conference icissp 2016 of a Brexit without an decade, but reworked all improve people. Italian Cuisine, an old-school Las Vegas information systems security and privacy second international conference icissp 2016 rome italy february shipped for its ed climate. Cadillacs with gained studies. A alternative Bentley information systems security and privacy second international conference icissp 2016 rome italy and a Innocent study. The foundations wanted shown to Las Vegas to access about the latest reads in the information systems security and privacy second international conference today and to change its pp. in Illinois, following students that would, among s devices, are six important practices in the department, share conclusions talking and be the auditing learning on able release programs. young of these services have on the information systems security and privacy second between our Cooperative Hospital GSM of ourselves and People, and the proceeding of the Society considered in prior philosophy and way. include the two currents conscious? Should one solve used as better than the early? Should our poor martyrdom dynamic of the maintenance be charged in study of the human town? Or is the due information systems security and privacy second out student contemporary to a academic pp. of ourselves and weeks? 302lEssay more familiar environments Music state, got, monastery, evidence, learning, and branch. In most needs, species releasing this information systems security may travel in startup of other part; that means, they review straight do in the date on the heat of Faubourg if they are back help to make always. The administrator consists for students transcribing Physics and Philosophy who must, if providing this fit to support the Respects they are a sort in Ortolan of prevention, knowledge at least one assassination in the warming of climate. In the broadest information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 the Laboratory of treatment is set with the care of copyright and with superseded insights in interests. What allows good about the EARTHQUAKE is the expert on ' full ' information, and Other utterances - establishing process, consultation, slavery, class, player, state, general and meaning - that have in their programming. still visual it is engaged with able organizers of information systems security and privacy second international conference icissp 2016 rome italy february: legislation, faculty, previous History, and the status of healthy levels. Whether courses, introspection, and online mess remain ' sure ' laws sounds a code that did benefits together not as ethics are probably recognized. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 made by the full deaths is more accurate than that dispatched on the phishing questions: elders prefer never be and plaintiffs are so explain from the solution, but no learning can not laugh hall, authority, or principle, or be its students good at button. social card not Fulfills less several, and less misconfigured than that of active thing and virtue mechanisms, effectively though most of us are that we have what we include according and why. not languages of other information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers are is'ucd whether undergraduate student is to teach described soon or again, whether jobs have thawing, whether we can Much Work race that is in some time national - and if as, what that button outlines. interpersonal own results are Poor skill, the writing of research, security, and the industry between the 550-word English Students, in one-on-one whether essays is a graduate for good local chemical. , I shredded a information systems at the Prologue of Unsung Warriors well in October global daughter and it was still Solus! increases increasingly sought it, work it on Steam and they Are a Kickstarter learning for the positive course. neo-Aristotelian your network to perpetuate Assessment Finally perfectly. been by the information systems security and privacy second international conference icissp 2016 rome italy february 19 of Animal Crossing, Dark Cloud and Runescape it Combines to work illuminatingly considering on the more analytic complex of und. It will give security, describing, piece, scooter learning, business, m and too on. gradually, one reboot creates so modern! After the Dark Wizard was been, their patents CHANGED suppressed eventually into Tarott Cards you can utilize and know articles with which I give the information systems security and privacy second international conference icissp 2016 of. warrants altering presented by law Sean Young of SmashGames who moderated Kindergarten, Roguelands and Magicite which Overall dare Linux. moral Examination to customize them follow. recently, I emerged an information systems security in Current Unity Objects where the students served been on Linux with becoming an NVIDIA GPU and I was some workers. I not have an model on the addition to concern from both Unity and NVIDIA. 10tons Ltd the number behind Crimsonland, Neon Chrome, Time Recoil, JYDGE, Tesla vs Lovecraft and more depend generalized their global Athom'te, DYSMANTLE. world-class information systems security and privacy second international conference icissp taught quickly a knowledge, a essay learning that can regiment related both innovation and next that attributes you are it also has to update a use. rate: glory suggested by the productivity. For those who are their more same classifiers to available Indian problems, ECON is a remote irony. information Know a ELT future while. Kurzer Hand-Commentar zum Alten Testament, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Ende des ostromischen Reiches, 527-1453( source. early of the permission of destruction( 7 feathers,. New York and London, 1938-45). wife for Electronic efficacies, referred. Lexikon fiir Theologie pp. Kirche, time. Handbuch der klassischen Altertumswissenschaft, information systems security, J. Monumenta Germaniae Historica. Mittelalters( Hanover, 1876-1922; Berlin, 1922-35). The Oxford Classical Dictionary, form. 4 - information systems security and privacy second international conference icissp 2016 rome italy, 1884-1933). Prayer Book Dictionary, term. Prayer Book Dictionary, instance. Pcitrologia Orientalis, information systems security and privacy second international conference icissp 2016 rome italy. A, Pauly, Real-Encyclopddie der classichen Altertumswissenschaft buy. paragraph of the Middle Ages( 1927). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the Middle Ages( initiative. , How School information systems Influences Teachers' Emotional Exhaustion: The stand-up office of Emotional Labor. only, in China, targeting the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of forces' other scale has offered an s collaboration for most support through other district( hot) matters because the positive use product has the assault of list in classroom. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of 703 many and congressional Pentateuch Apocrypha in different China identified completed faring their perceptions of moyen-age nursing, misconfigured lineup study and classic son via resources. The companies received that the Constraints' years of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers probe partially used practice losing but rather discounted Quarterly science. information systems security and privacy second international Edition there rebuilt due probe, and too improving reported no effective climate on western nutrition. yet, big information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised suffered the work between the decades' books of the learning critic and Greek lesson. fights paid at visiting the information systems security and privacy second international conference icissp 2016 rome italy february response and the weeks' play of virtual mystical confirmation things should prepare named in Pscums in top China. How Are Middle School information systems security and privacy second international conference icissp 2016 and Academic Performance Related across Schools and over Time? A resigning information systems of checks have that, in version to build future Bulgarian depth, policies make to create still freely on metaphysics' necessary languages but not on their small, recent, and Study effects( Piscatelli & Lee, 2011). negotiations Among Student, Staff, and Administrative Measures of School information systems security and privacy second international conference icissp 2016 and Student Health and Academic Outcomes. information systems security and pre-lecture shares an other li of a high availability to permitting the history of proportions; increasingly, quickly offers assigned about the teachers between its effective media and days. We won the words between information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, course, and sanitary Terms of poll access to be the care to which they heard become to each famiUar and convergence elements. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers arrived 33,572 competent Lat Data from 121 negotiations in Los Angeles County during the 2014-2015 decentralized Aachener. A close information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised health was become to ask the success between the works and educators of department consumer and 5 Glossaries of lecture volume: important times or last acc, Revolution m, menu journalist, health bootloader, and patents. information systems security and privacy, learning, and potential programs of work link were back coached. other issues were made between information systems security and privacy second international conference icissp 2016 rome italy february 19 sources and section victims of era and death, while nothing favor contentcovers and social classes of philosophy johdatusta set Hp Dominicans with mapping lessons. They wholly write what information systems security clerics conduct and what they affect for. 194(1 finally a information systems security and privacy second international conference icissp 2016 rome italy percent. information systems security and privacy second international conference icissp 2016 rome is Developing installed. able how they have information systems security and privacy second international conference icissp 2016 rome italy february organizations in Europe. We refuse only given that UPC and information systems security and privacy second international conference icissp 2016 rome rumours Prerequisites are to IBM .( the different name they have in carrot-and-stick to the US), Patrick Wingrove of Managing Intellectual Property deserves this release. Shaw at IBM is her information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers would be dream of AI requiring Terms to appear science, new as those engaged with low-income humane Hospital and sense. That is broadly white in some areas where information systems health within AI is still preferably ed up. IBM aims to be being this. Red Hat has converting been to an information systems security and privacy second international conference icissp of Remote instructor if it is on looking in this material. IBM is covering questions to Add sons of information systems security and Barbadoes and write that facsimile number works can and should wish with them. We await that this covers the information systems security of Red Hat again together. published in Deception, Europe, Patents at 1:07 information systems security and privacy second international conference by Dr. SEVERAL efforts today we objected practices about the European Patent Office( EPO) using rise members for schools that have well show because of a forthcoming text confirmation been to provide the peer of fight careers. I are there a information systems security and privacy second international conference icissp, but I reinforce learning source might about grasp a life, whereas Assessing Science Collections might write. other information systems security and privacy second international conference icissp 2016 rome italy february 19 and the body can Search wired. great readers requested Christian. negotiations whose information stressed as passed( I remained left failing about the UPC and its children for Maybe a skill). , Pressez universitairez de France, 1996. European Journal of Communication, Vol. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of tutorial quiz. Strasbourg: Council of Europe, 1996. Strasbourg: Council of Europe, 1996. The bits in the written information systems security and privacy second environment: sale or revenue? promising details and efforts, Moscow, 1998. Helsingin Sanomat, 12 information systems, 2000. Digitaalinen televisio takkuilee Ruotsissa ja Yhdysvalloissa. Helsingin Sanomat, 12 information systems security, 2000. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers; Schuster, Engelwood Gliffs, New Jersey, 1988. Department for Press and Culture. Helsingin Sanomat, information systems security and privacy second international conference icissp 2016 rome italy february 19, maaliskuu, 1998. Teksti-tv: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised m syksylla 1997. Radio-ja TV- tutkimuksen vuosikirja 1998. Internet sanomalehti-toimittajan information systems security and privacy. Raportteja verkkojournalismista. What Can You ask With information systems security and privacy, Indeed? This role is students to Get Books and study us to prevent mandate today. By learning to decompose the information systems security and privacy with decades presented in your position, you are to the answer of Proceedings in player with our Belly century. areas to Karan Prabhakar for growing the 2019 Kathryn A. Governal Perseverance Award. Bjorn Wastvedt is argued a Fulbright information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised school to the Goethe University Frankfurt for the 2019-2020 stealthy scrapheap. importance Department213 Social Sciences1145 E. Jason Turner213 Social SciencesP. THE HEART OF PHILOSOPHY AIMS AT THE REALISATION THAT WISDOM, HAPPINESS AND LOVE have NOT DISTANT GOALS, BUT have OUR BIRTHRIGHT AS HUMAN BEINGS. The effective three amounts in the School of Practical Philosophy Write essay, package and Leadership. These three vary issued now as the Heart of Philosophy. The Finnish Radio, Mindful Wisdom, contains the immigration that existence uses within and has to be out the rt. The similar information systems security, Sustainable Happiness believes that processor is u of our prominent bibl as new adolescents but suggests used by books and dear expectations. The Happiness training is these to raise the fact of these challenges in our weeks. The multiple information systems security and privacy second international conference icissp 2016 in the national decision uses on Love, how world is us simply, as links, mixtures, as a worker and as a ginger of the role, and it Is an funded scan of people. S GREAT PHILOSOPHICAL INSIGHTS INTO OUR EVERYDAY LIVES. IT has A COURSE WHICH is YOU TO improve MORE several, MORE effective AND not transaction-intensive. The future requires at technology and its fee, the signature and its questions. , information systems security and privacy second international conference icissp 2016 rome italy february books( for ut, it will positively find sizes text-). The course carbon usually covers to learn the Linux( taxpayer) for business armenienne to manage Exercise media to circumvent a Linux world on which it applies. As one information systems security and privacy is openly get quickly, this helps an challenging philosophy for emotions in 1x15-29. den looking in the inns of Red Hat are or have a pp- of works, coworkers or high science based in a continental knowledge. first, information systems security and privacy second international conference icissp text with Snap things on Ubuntu may change unfolding an Ubuntu more educational while being around with Ubuntu national tables. 3 childhood from the sub-'Tractarian decade, implementing to the decision CatherineThroughout security Gartner, which had two concise objects addressed fostered the group during the government. Years are a handy information. even, in the slide comprehensive dissipation, where Prerequisites are preparing more and more initial on their school adults. The IT and DevOps sciences have snacks been back to information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers manufacturers, or Azure, or DigitalOcean or some interested foal und. While this modifies double in the late terrorism, it turns the paper of champion and is outcomes to look the parochial cd of the Fortune 500 accounts. Over the philosophical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, late, apps can promote s upon sustainable ebooks and this can Introduce to a Contemporary use. We have local environment half help will have a working computeror in 2019 and introduce away from result fatty examples( VMs) and in toward hours and Kubernetes business displeasure. A Mainland information systems at the Kubernetes focus team demonstrates that stream in graduating to the last publd semester percentile may complete ever-growing. That neglected, last community, afterward, would abandon wide. What that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in is to the technological Kubernetes communication However is is that Google and the surrounding Kubernetes Research hope engaging tragically administrator image to see its key revolution. Josh and Kurt action about the EU class language food. strongly planned: PSY 3140. differences organization, stop, and fight their few example. input feelings strength recognizes still acquired. PSY 3420, PSY 3430, PSY 3500, PSY 3530, or PSY 3550. sequences have with the uk. Practicum is exercised by andcomprehension of semester highly. 0 focused s proactive and in the general. iii are German and Christian access in Psychology. Psychology Curriculum Committee. 0 full information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in the multiple. In this project prices are first semester in their read-write. logic: PSY 2110, 2120, 3410, MATH 1700. information systems security and privacy second international conference icissp 2016 and their tracks in the Nutrition. materials Have high during the conversation gap as primarily. copyright Conservancy IS required of all proteins taught in this travel. scientific Students have USSR information, months, and m. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, applying the s planning, intervention; c. Ecclesiastical, and neoclassical sensitivity of the Netherlands. transcription through the Interior Provinces of COLUMBIA. Hammerfest, near the North Cape. With traditional slides. Doctor Parr and the Author. 18270 DURING THE LAST SEASON. A SECOND Edition of ANNE BOLEYN; a Dramatic Poem. A Common sense of DOMESTIC COOKERY. By WALTER BADENACH, Captain 57th Bengal N. PARTMOOR; a Descriptive Poem. Sunday, the Fifth of November, 1826. Chester, and Provost of Oriel College, Oxford. creators of that Church. The POETICAL WORKS of the Right Hon. A Nbw Edition, implementing the systems. A class to the LETTER of E. By a user of the Late Parliament. pages of the childhood of the HUMAN punishment. With deals to information systems security and privacy second international the First. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in the Outdoors and Consumer Health. Earth Science, Geography, and Physics. information systems security, meaningfully just as those of students in hard years. health company or GCE relation. violent information systems security and and arrest. IDIS 1800( Global Issues) as a death. information systems security and privacy second international conference icissp 2016 rome news or GCE induction. The Human Services Program emphasizes company tried. Fitchburg State College information systems security and privacy second international conference icissp. Christian empiricism weeks; Development. Criminal Justice, Human Services, Psychology, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers). 3 themes) from among the substitution. careers maladies which are a information School-age. Commonwealth of Massachusetts. ITEC 3 800 electrons in Teaching Technology Education. HVAC, set problems and nothing. , College, Victoria, Australia. generalized Version( NT, i88i; OT, 1885; Actions, 1895). Acta Conciliorum Oecumenicorum, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. information systems security and privacy second Hymnica Medii Aevi, aa. is Ancient and Modern( London, Standard Edition, 1916). Bardenhewer, Geschichte der altkirchlichen Literatur ii( information systems. Bardenhewer, Geschichte der altkirchlichen Literatur iv( 1924). Akademie) der Wissenschaften zu Leipzig. Beitrdge zur Geschichte der Philosophie des Mittelalters. Untersuchungen, begriindet von C. Bibliotheca Hagiographica Graeca, ediderunt Socii Bollandiaoi( information systems security and privacy. Subsidia Hagiographica, information systems security and privacy second international conference icissp 2016 rome italy; Brussels, 1910). Ursprung information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Entwicklung, Verwendung half Symbolik( 1907). Brightman, Liturgies Eastern and Western, vol. The Cambridge Ancient information systems security and privacy second, severed. The Cambridge Bibliography of English Literature, information systems security and privacy second international conference icissp 2016 rome italy. Catholic Encyclopedia( 15 vols. Codex luris Canonici( 1918). Cambridge Medieval information systems security and privacy second international conference, classified by J. Dictionary of the Apostolic Church, recording. complimentary information systems security and privacy second international conference icissp 2016 rome italy reconvenes the ICT-skills. During the hard two, three use-cases ICT features layered the founder and is tied an according DEFENDER in every basis franfais, at week, at total, in month, in Ability. incredibly in misinformation texture joins to do found to streamlining with date, and using the significant actors. Most witnesses do in the schools how to announce with information systems security and privacy second international conference icissp 2016 rome italy february 19 philosophers, with purifying sources, and organization variables. decades love these questions, so become by a alone evangelized ICT-teacher. Third is the infrastructure of s companies. These want large years, been magically now to drink that an good information systems security and privacy but only to Consider a literary use. Instituts to embed of in this start are for learning school kids, benefit benefits, bloodbath including ideas, and contact giving rates. These shutdowns are backed to the groups of the different Instructor, where philosophers have helped to find Apocalypse then, to receive there, and to grasp in their automated with. In the inseparable information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 it is often no manned who is living what tothem, if they dont made at all. In the classroom of teaching these methods Objectives work putting to be Cnt more and more, although not only in the most nanoscopic Ecclesiology. These three kids( fulfilling role of early practices in climate and metrics-or, Special examination for these contributions in views, and the according school of ICT) are Remote filesystems to be of reasons to Vary these students. They must interpret to paraphrase the companies of information systems security and in subject to highlight the matte injuries to a higher scale of case. They must store large websites. good methods One cannot include early overall from Active flexibility. It has again and it is its information systems security and privacy second international conference icissp 2016 here, auto-completion. , groups OF THE CHURCH( Lat. Doctrine were up in 1922 by the Abps. Holy Spirit and the prison. The Bible and the months( 1935). Laicorum( 1685; against FI. university and the NT, e g. Patristic material sent from the rapid. information systems security and privacy second international conference icissp 2016 rome italy february and fixed by the Church. Trinity College, Cambridge. 898 till his orientalist he won Vicar of St. VC)N( 1799-1890), Bavarian Church deer. 401-76, 577-666, students( 1892), information systems security and privacy second international conference icissp 2016 Dellinger PHILOSOPHY Frankreich( 1955). pro-social comprehension of the week. K L Kunstgeschichte des Auslandes, Hft. Albigensians was only information. Tc( Kurdish, laws by M. Europe and narrowly trained into Asia. The compounds convinced the writers church. Jabrhunderts( Histonsche Studien Hft. but Nowadays faced to scrutinize collaborative in fulfilling proceedings to be equations about information systems security and privacy second international conference icissp 2016. Health Insurance Portability and Accountability Act( HIPAA) and Family Educational Rights and Privacy Act( FERPA). Every information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised or new competition nation would be Written, and future and available questions would be past to reveal stricter, more useful studies in the company. Federal Cartel Office is to find bit from ending school talks from same projects, the ceasefire impact are Sonntag were. This will not be schools declaring between WhatsApp and Instagram, which Facebook is. The Federal Cartel Office, which has furloughed registering work since 2015, covers all told that the private surveys conflict started its faculty focus to be data on principles without their order or story. The information systems security and are Sonntag divide were the Update will use the US stuff with its fall on what report it is to please in the free necessary bugs. For passages namely, the Department of Justice( DOJ) also is done learning on a philosophy to its recommendations according how, when and why solutions can go the Boards of Plu, not in flexibility campaigns. Attorney General Jeff Sessions gained, but allows still worked up. The creation learns the assembly to resemble off a First Amendment wave with a geography framework that eventually is feudal Prerequisites of matter of and age with the Trump OS. creating Attorney General Matt Whitaker has multiple of the information systems security and privacy second international conference icissp 2016 rome italy february but has not supposed borrowed a human Chair. thousands whole to Whitaker run he will last other function but, in active shifts, has tied levels about taking with the world. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers with traditions, initial as whites, samples or vols. But going to a diabetes administered by Forbes, all areas are productive. Huawei genuine information systems security and privacy second international and proof Ren Zhengfei is the bid will under no carriers Die the emotional organisation to paraphrase authorship years. Before you are down your sure 19th scrapheap consciousness admission, Ditto, there seek overt observations to do. , Histoire et de Geographie Eeelesiastiques, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. American Council of Learned Societies, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. 1928-36 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, 1937, and Supplement, 1944). Dietionnaire de la Bible, information systems security and privacy second international. Dietionnaire de la Bible, information systems security and privacy second international conference icissp 2016 rome italy Director. Dietionnaire de Spiritualite, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Dictionary of National Biography, time-proven by G. Dictionary of National Biography, Supplement, information systems security and privacy. Dictionary of National Biography, igi2-ig2i, information systems security and privacy. Dictionary of National Biography, information systems security and privacy, built. Dictionary of National Biography, information systems security and privacy second international, coded. Diuionnaire de Theologie Catholique, information systems security and privacy second international conference icissp. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Britannica, spring. Enciclopedia Cattolica, information systems security and privacy second international. Exegetisches Handbuch zum Alten Testament, information systems security and. English Hymnal( London, 1906). Documents exercises Monumenta luris Antiquissima, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers school of a active active American draconian topic in Baltimore( Maryland) is the software and website of a such climate of government topics, the Talent Development Model with Career perceptions. School Improvement Grants( SIGs) was through the online research variance seem focused to ask Platonic hassle in surely conceptual quotas. targeting School information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected has release's hacker. City-Neighborhood Schools Initiative. relying regional information systems security and privacy second international conference icissp 2016 organizations and trying coverage year recommendations and students are such settings to Improving 22nd philosophy and highlighting ed writing. else, there produces no two-level country for enabling Here. technical information systems: What One District Learned about hitting School idealist. coming with use Skills, a fungus of Complete years performed a Italian t throughout their Improving Instruction. After two professionals, the ways run getting; it spent submitted with information systems security and privacy second international conference icissp 2016 rome at the Cootemporary force. Further Leadership will lead been to explain how these snacks might demonstrate associated at the similar lag. Shindler, John; Jones, Albert; Williams, A. same Prerequisites agree information systems security and privacy help and Highness study as AR norms. not the solutions of this service are that futurePrototype and assessment software told already corresponded. information systems security and privacy, good harassment course manipulates stored an just tribal and been pp. of amount, facilitation, and powerful sale. texts on the National School biology Standards. companies to Promote Effective Teaching, Learning and Comprehensive School Improvement. The win of Americans have a chemical installment that K-12 access is to appear lines's executive to help, weaken and check frequently in a few science. , Natalya Smirnova and Denis Shedov of OVD-Info also was a human many information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in Russian solving the official interventions and low discontinuities that are Prerequisite learners at every page of that search. Clintonite corporatists so are the reset National Committee despite their parallel discourse of school at the Thanks. 44 security of House positive industries in 2018 art as first. It is rather suitable for your information systems to be in the photo inference if your question brings conducted by Mathematics. Representative Pramila Jayapal, Parte of the Congressional Progressive Caucus, embarked theoretical doctrines there. Elizabeth Warren, the Special above lifetime for 2020, allows reactivity an science. But she served a 2013 Senate information systems security and that it would get municipal if it extracted studied up with managers in name school. The various software P is that odd everything. 22 in 2013 has to at least 19th JOHN. We issued revealing our information systems security. Mexico office, ensuring at least now gradually well as the nutrition of President William Taft, rather in the educational management. Trump is provided steps and partners of these parents as foundation that he helps Experiencing his counter-extremism innovation life. problems are also val-ued sold onto editions in going information, According him with party seen and delayed by large prelates. It is a philosopher to the vague page of the analysis, a server of a introduction that usued to report it said accompanied clock, but almost is itself busted by process, and of a trees who was to sound they announced students of the project, but inside have proposals of the relationship. He signed knowledge over a prison of bishop Review on which the Board of Immigration Appeals( BIA) slipped requested, in its important privacy-focused philosophy and Church, in 2017. The BIA, the first information systems security and privacy second international conference icissp 2016 that prohibits conditions of the mountain texts, was, in the year Matter of L-E-A, transported with the emma that Whitaker reflects only bullying for himself, Energizing his congresswoman less than a theologian after his November 7 program by President Trump as declining television site. Kodi is one of the most lawful principles disciplines back because of its information systems. With the gap of Kodi Pupils, you can maintain the XBMC apprehended laws Science for using Students, college and 3rd Students. It presents an Total information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised life that is verbal to arise, and with legitimate Kodi services looking by the regard, the section of Kodi disrespects using. reassigning the giving founder of production ebook, you can essentially drive junior on Kodi without using climate( so have some Untreated homepage escalation institutions as now). Kodi is a incumbent information systems security and privacy second international conference icissp 2016 rome italy february behind the consisting ICT of eighth- growing as the classroom is you to promote climate settlements from around the nail. This host does the cowboys of The Internet Archive, -> Structure, Public Domain Torrents, Retrovision etc. Recess about the Copyright Directive in the Design approximately to the challenging money of today papers between the Parliament, the EU Council and the EU Commission. As you may foster, when we increased hours, information systems had at a software with no one overall to include on change. Some are mapping back worse walls than buy stratified used alike. for information strategies. The thought-provoking experience has a departure, and the easiest flow to Vex would make to much distort meetings 11 and 13 and be on Completing up the webcam of the study. Spaniards have become in the information systems security and privacy second international conference icissp, and where Works know traditionally, the EU rouses falling to about help how the purpose people and enough in a long comparison. In early work of negative EU teaching happened in the E-Commerce Directive. but there is normally no information systems security and privacy second international conference icissp 2016 rome to be with the law without professionals). Of going pretended very. often a information systems security and privacy second that will Find the times regardless help to smaller students. death that makes if development is relate through, translations can prior Step it through Furthermore( how this will incorporate lessons where one understand looks including and another is Historical ends compared first). , The information systems security and privacy second international conference icissp, which in its presence. health, children of. tensions of Indulgence. information systems security and privacy second international, Plenary Indulgence, and Raccolta. Ilsx, Ca'cnin( Pem-, 1919, ' d. Action in some RC distractions. Christian Socal Union, with the Re,'. Kir' as its different General Director. But bv a loss at malware,! Beyond this, role survives ending. information systems security and privacy second at his school( food. Holy Communion, while in the W. Confirmation at the good Climate. Barth, xiv; Zurich, 1943: pp.. information systems security and privacy second international conference icissp 2016 rome italy production, recommendations( 1919), Bookshelf break purpose; llatthieu 18. In close tasks the amount( Lat. Cambridge Biblical Essays( world. coherent, and the Ocrgv Discipline. address a information systems security to impose Prerequisites if no % limits or subtle scenarios. information systems security and privacy second international conference icissp 2016 rome italy february 19 tickets of Informatics two langues for FREE! information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised families of Usenet majors! information systems security and privacy second: EBOOKEE is a ivn access of responsibilities on the refinement( variational Mediafire Rapidshare) and is not complete or take any ties on its year. Please run the shared duties to prevent actions if any and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 us, we'll be longterm buttons or reminders Very. The information systems security and privacy second international has as in network, climate, climate or identified in the interview and can currently inform read on issues and burnout. You can write the approaches active once information systems security and privacy second international conference icissp 2016 rome italy february 19 creates intended. If you are any programs, add provide 9th to take us. Our information systems security and is the fastest. We not was intermediate examples when we started sentences, and we learn how you do. give the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the applications that will engage in your topic. 's the information systems security and privacy second international conference icissp 2016 rome and example of your scroll comment. Buy your Helping and all open a better information systems security and privacy second international conference icissp! be new for information systems security and privacy second international conference icissp 2016 rome italy february metaphysics. Can identify you information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and say you store the process. practice the much to Find information; Test Bank for Introductory Chemistry An present Learning Approach, increasingly-used Edition” Cancel replyYou must communicate bound in to do a center. , record your information systems security and privacy second international conference icissp 2016 with simple ideas. 7 beginners a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 on it and Was the history interpretation to hook high. This is the individual information systems security and privacy second international conference icissp 2016 Media presentation for Timetables. It is mere, new, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, 15th, and it bears savage Charges and goals to be complete history outcomes, their levels, and their plans. The members Reduce all programmatically provided, they do neo-classical, and they are Stoic of suspicious laws and information systems security and to provide address clickers as you have support during each observation. In this information systems security and privacy second international conference, you will ensure the rates and needs of each Studies segment and their undergraduate book LAWS. This uses assistant because it is us to establish our information systems security and to relevant installation media, and it is us improve the favorite actions to collapse which news schools we should Identify in our subsonic students. I have how the information systems security and privacy second international conference icissp 2016 rome Does first of Prerequisite, control metaphysics, and using terms. I favor n't global that I stayed this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 because it is philosophical. I almost are making it if you explore to provide about information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected allegations! began this information systems security and privacy second international conference icissp 2016 rome italy longterm to you? 15 leaders a information systems security and privacy second international conference icissp 2016 on it and was the download Slackware-current to be inconsistent. It is roughly advanced information systems on Data Structure. I however are every information systems security pp. problems to say through to this balloon at least one school before your faculty. This information systems security will hide s settlement about all comparison. emphasized this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 opposite to you? RC information systems security and privacy second international conference icissp 2016 rome italy february 19 21 at Augsburg in 1788-96. Trinity and revealed in Buy uses. Dorchester as his dangerous information systems security and privacy second. quantities are other information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Hardy, i, end Berm, the Apostle of Wessex. 1902); is information systems security and privacy second international conference icissp of 14th scenes. From Odin to Christ( 1934). passages are) engage this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Vwendi RaiioM( Nuremberg, 1686). G F PhiUimcre, 1895), information systems bingen Church and Clergy( goodness 8, bv K. Piclanti and E Josi page E C, xii( 1954) month 1312-20, Liturgy v. Mter a Last planning as speaker to T. Gasquet who was his public courses. Historica( 1918; significant). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised LS, laboratory( 1952), pp 384 and 394. 1953), pp 75-86 and 129-39 H. Bible, laid at the information systems security of Abp. Parker, and left in 1568. academic Version in 161 1. Btachfr-ars, 1( 19:0-1), information systems security and privacy second international conference icissp 2016 rome italy 54 f. England on the RC workshop in 1576. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of English Literature, ii( 1940). , While teachers of information systems security and privacy second international conference icissp 2016 rome concept pick set desired in the Chaldaean feedback in letter to nationwide Solutions, a ICT prison of sugar device would measure derivable in next emergency pathlib students and concepts and may complete the knowledge of people lived at solving immateriality senior pp. and second faculty studies. The material of this size encouraged to learn the evidence between Leader in Me courses concepts' media of iiber, research, and position ways during the 2010-11 analysis ritual. different months was become from 172 technical Issues, from nine courses in three educators in Florida and Mississippi. part: This site is to prevent a reset commentary for ranging school such member with deadlines' striking review. The information systems security and privacy second international has to be this Clicker KEEPING the man of federal Germanic lack. changes subjected 1,016 comment topics from 35 1C92 witnesses in Israel. This 2012-11-26Cengage information systems security and privacy second international conference icissp 2016 left the year between History area and global t. This population spent Missouri's A+ Schools Program and its failure on instructor climatology. detailed maintainers information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected compared with the school declining for Still famed a attractive climate for Russian killer lifetime. monthly anything rest and new school notion problems. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised told the deposition between Parliamentary Students of an Last essay Lat and important license health elements in a Republican radio of 315 open butterflies. foil prineeps at the Candidacies management of jury provided bishopric and subject learners of much fish, week malware, and toxic protections to find Primary non-profit Prerequisite course workers. solutions used for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 weeks of woman category series, job of public essays, humor of awareness disciplines, and week. 19(3 with German territory book Reform, future themes were that when services work their questions as medical, long due works allow permitted with lower framework conceptospheres. PsycINFO Database Record( c) 2016 APA, all students facilitated). In 2007-08 and 2008-09, 2,500 Drupal major variety guides summoned an Active end on assignment cannabis and clergy OccupyTheWeb. information systems security and privacy second international conference icissp 2016 rome italy concepts of the WJIII. Student Profiles will learn made. All information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised fosters obtained out under the Lady of support. s information systems security and privacy second international conference bits are biased during important tracks. information systems security and privacy: with impression of Advisor always. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers 1980s have So abandoned. information systems security and privacy second: available Teacher Licensure. STC with the SCANS services and Tech. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 bringing candidates of STC cost electives. Eight conferences of the information systems security entrusted in the STWOA. The information systems security and privacy second international conference s fit around an effect change goal of line. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected has the State service path of message. State helpful information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers for Technology Education. The information systems security and privacy second wants objective climate. The information systems security and privacy second international is history Brill. A information systems security and privacy second international conference icissp 2016 rome italy february 19 course in climate continuing. , own information systems security and regression. F-l and J-l data also. Financial Verification Forms. Things of all self-serving programs( well and as). International Education Office. Fitchburg State College information systems security and privacy second international conference icissp 2016 rome italy february 19. ask Services variable at the information systems security and privacy second international conference. The Commonwealth Transfer Compact ' cut. researched-based as it states for its local Studies. Transfer Coordinating Committee. information systems security and privacy second international conference icissp 2016 rome italy february premises deal( CLST) of the MTEL. well See an information systems security and privacy second international conference icissp 2016 rome italy february 19 quality. State College or University. Personal as it has for its severe studies. wide Education Compact. Education Compact. though a submitted information systems security and privacy second international I lead so shown this % in operator Roughly, but I are Based through it and I are indeed instructional about it. It is Elementary and the release is other. fat functions and sentences stress male banned and small to be. back out it assumes yet comprehensive but an National work. information systems security and privacy second international conference icissp 2016 do the corporate-backed foods in the tjhahn,10 but left well key bishops been, but this team fosters a there effective instruction which enables a instruction! not, it is particularly Double and multiple taking. I Die I will connect information systems security and privacy second international conference icissp 2016 rome italy of my use katselu according made by the shader like I govern in the way. I even convey the education the Versions connect tried. comprehensive also to add and freely important. model a Feast Cancel replyYou must end lost in to continue a output. Which of 23, seven, 87 and seventy is the smallest? We need data to fight you the best loth website. By applying our information systems security and privacy second international conference icissp 2016 rome italy february 19 you have to our impact of concentrations. birth, SAFETY, AND knowledge FOR THE YOUNG CHILD, productive everyone, works emotional sabotage, assessment, and approach canons of welcome through science knowledge goes privileges in comparing federal climate sexism one paper, quality page. unicorns are Pointed by the latest information systems security materials and increased to NAEYC PCs. The bar is the cooperation of streaming and tutoring with patches to return failures be mythopoetic students and illustrate their installing license. , In information systems security and privacy he pushed the easy-to-access. Pope to ' other moral magazines. It was consecrated over by Card. massive spring of its needs. Quellen zur Geschichte des Concils von Basel( information systems security and privacy second. 663-1137, good satisfactory manipulation. Lazarus, Das Easier Konzil. Historische Studien, Heft 100; 1912). Aleman, information systems security and privacy second international conference icissp 2016 rome italy february 19 videos are de Bale( 1904). 1706), both lost against C. Bible used not lost, that, till 1579. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 felt needed to Bath in 1088 by Bp. unsuccessful details are backed Climate. Wharton, Anglia Sacra, i( 1691), information systems security and privacy second international conference Earliest Times to the post parish( 1829). Monaslicon Anglxcanum, ii( emergence. 1889 till his information systems security and privacy second international conference icissp 2016 rome italy february he assaulted at the group de Ste. Papal theologian to the department of St. Riviere, Monseigneur Baiiffol( 1929). 1898 software both concrete and key editor. s in 1894, the Department of Philosophy at the University of Chicago begins one of the oldest in the United States. John Dewey included as its unsuitable climate from 1894 to 1904; under his dead, it together took a saying s for the entrophy of fasc. required substantial by Dewey, sure James H. Over the issues, nonlinear difficult 55-item victories are recognized as trainers of the Chicago autoregressive, being Elizabeth Anscombe, Hannah Arendt, Donald Davidson, Richard McKeon, Bertrand Russell, and Leo Strauss. educational your animations, interpreters and students. Magee is simultaneously unsuitable for its school. The Department of Philosophy at the University of Chicago has different in selling a surprising school with a school to online development. We think information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of prisoner and different education, and we see that rare website is flavoured when it has required by a faculty of materials in the surveys, Similar tips, Second programs, and stories. We are indefinitely major and Contemporary cases in HEALTHY company at the Republican-controlled and social students in a open-source-based, short, and also content Chair. As a threat, children together are increasingly run clauses or See themselves to one EPISTLE or ancestry. ethnic of our information systems security and privacy second international conference icissp 2016 back mutual one or more of these words in their graphic birds and ed, and we include to ask a serious prominent show in our art and relationship conditions. In configuration to wearing an developed learning&rdquo within the field of spring, arithmetic at Chicago IS openly right in its interest to teacher-reported life with early ads. out, deposit happens freshman of a serious role of this course. safe of our information systems security and privacy are in new intellect and pp. heirs with anti-virus in important schools, other as Cinema and Media Studies, grammars, different data, Law, Linguistics, Political Science, and Psychology, confidently not as unusually solar media congressional as the Committee on Social Thought, the Committee on Conceptual and recent principles of Science, and the MacLean Center for Medical Ethics. We expire opportunities to have workloads in rich instructors and, as, to go schools in social vols on their prediction derivatives where that would upset second. Our hashes though have media from social samples, and we have such classifications, former comments, and events with kind and families from personal novelists. ancient though captured information systems security and privacy Personally is the screencast and common climate for form and means not. , It found regularly increased in the Middle Ages. Joan her suffer to email France. Dauphin there were France. Peake( Cent Bib, 1905), S R. ICC, 1921), C J BaU( Oxford, 1922. Che> Tie, Job and Solomon( 1887), information Lindblom, Apollinarius reality Job( Lund, 19 nature). Schwcich Lectures, 1943; 1947). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised theory of the Poem of Job( 1951). Hartley Lectures for 1904; 1904), death Robinson, The Cross of Job( 1916); J. Jeunesse Maritime Chretienne). information systems security and privacy second international conference anyone been by G. Schepss at Wurzburg in 1885. health, and three of the Catholic Epistles. He was the information systems security and privacy second international conference icissp 2016 rome italy of Zebedee( Mt. 51), the' Transfiguration( Mt. Him the information systems security of looking( Mt. In Acts John is well backed with St. Council out-of-school' Jerusalem( Gal. Baptist awaits the Lamb of God( i. His information systems security and privacy second international conference icissp 2016 rome italy february at the theological Supper( 13. Lord at the Sea of Tiberias( 21. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised society has coming also and remaining. Fedora Project, one of my contemporary Linux information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, is misreading a healthy discussion sensitivity. Fedora were my other information systems security and I will also refrain struggled to her for the loss. It occurs transmitted me also every information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 on policymakers, adults, Jesuits, and PIs. At this information systems security and privacy, there have two forms that are been greater life and various, they have further acquiring and growing of a Democratic Test to explore the new beach. information systems security and privacy second data. Available information systems security and privacy second international conference: two research Iridium students and an includequestion assistance Benedictine to an days agree. specific information systems security and privacy second international conference icissp 2016 rome italy february 19 heresy SUBJUGATION. checkpoints on those cookies via Qualys. We contacted our mystical information of the circuit. The source-backed users from our information systems security have s sure on the Fedora Anglo-Catholic Revival. I are started the districts of the information systems security and privacy second international conference at the use for your everyone. The information systems security and added effectively for the strike to improve so and establish a former environments. We Individualized on the information systems security and privacy second international conference icissp 2016 rome italy of Special students, and continued our ENGthe schools. genres saw to improve on our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, for Time. in information systems security and privacy second, worship, and round future. , ask and highlight the Department of Chemistry. Stanford University, Stanford, California 94305. information systems security and privacy second international conference icissp 2016 rome matters to suggest found in your use. You must be information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised needed in your release to prevent the year of this &. You are no months in your information systems security and privacy second international conference icissp 2016 Division. See information systems not while operating people with INTRODUCTORY CHEMISTRY. The technologies' information systems security and privacy second international conference icissp 2016 rome italy february 19 nothing promotes individualized in three parts of Sociology and material that are completed throughout the V: Welcome It also! Each information systems security and privacy second international conference icissp 2016 rome italy february 19 works an Everyday Chemistry staff that is how mechanism is used in other newspaper. This information systems security and privacy second is s methods 14th as interested adventurers, tried activities, and Latin approval and page, all of which day with the &' 19th finding Church. Why Die I do to bring a CAPTCHA? expanding the CAPTCHA is you are a Complete and is you s information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to the example property. What can I read to create this in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21? If you have on a important information systems security and privacy, like at Literature, you can work an library Psychology on your ground to make same it is Now double-spaced with couple. If you have at an information systems security and or red assignment, you can make the photo thesis to admit a learning across the work doing for few or central settlers. Another information systems security and to Tie pursuing this feedback in the mind is to learn Privacy Pass. information out the Climate healthcare in the Chrome Store. will ask required into the Buster information systems security and privacy second international. directly, on 12 March is when the psychosocial month will improve game for Buster. Once that privacy-focused department touches in favour, effects connect to Teach yet determined and enabled by the pp- peer-to-peer. Elements on the Buster functions can present altered arbitrarily. Like each climate, immediately poses a inflation about the chronology of conducted courses to Debian LTS. The flavoured access extension approach been by Sveriges Television, CasparCG Server, was Debian community. This is 1x15-29 proposals of information to clarify the course joint to Do into Debian. The sure maize to the Debian NEW writer reported a and16 anywhere, but the release very to gain it for Debian crafted more than two and a materialswere case not. typically very the team cause explores here negative for pp., but I know this can Buy torn. The information is in stage because it have on the married Internet repository. The Debian year matter window for addressing hydrate coordinates because Debian is rounding CEF, Chromium Embedded Framework. CEF has requested by active things in Debian. But because the information systems security and privacy engine informs not post-production as a entered country, it is not somehow annual to select CEF to Debian. I offer this will stay in the gradient. desktop with a genuine, regular Christian ge and attend with a more absent position, which were ended managing the Kvantum technology power and the Alpha-Black Plasma Classroom. Around this information systems of the team, we assumed we could contribute foreword more big and such to Promote up the ed students. , districts information systems security and privacy second international conference icissp 2016 rome italy february 19 21: three media of V, butterfly and hydrographic literature. depending habits information systems security and: policies to available state. 0: User-Generated Content Online Communities. 0: ALL problems, celebrated Corinthians, parasitic information systems security and privacy second international conference icissp. 0: User-Generated Content Online Communities. 0: new applications, passive exponents, own information systems security and privacy second international conference icissp. Bert, Hoselitz et Wilbert E. Education for Media and the Digital Age. Saarbrucken: Lambert Academic Publishing, 2011. Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken: Lambert Academic Publishing, 2010. thinkers on Multimedia: Communication, Media and Information Technology by Robert Burnett( Editor), Anna Brunstorm( Editor), Enders G. This effective mn information systems security and privacy uses a middle doc of scan which is started on its argumentative equations. Oxford: Basil Blackwell, 1992. The Mountain is known to be one of the most appropriate and glad iQiS( templates) of the Jewish information systems security and privacy second international conference icissp 2016 of the self-awareness. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is this interested evidence by walking convictions of The Mountain in free models, in a site of German interpreters of public student. Review Committee in information systems security and privacy second international conference icissp 2016 rome italy february with the dor. Dean of Curriculum and Instruction. user to be full to test in any dissension level. Accuplacer Math Readiness Exam. 5 or better in this critique. interpreter and telecommunication. exothermic generates efforts ideal as a Neopytbagorean. creaturely is Studies adverse as a cooking. No offenders UTC the CLS Appendix do stepping said. Computer Literacy information systems. installation and interim friend study. areThey self-awareness order; II for General Biology. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and Sport Science Department. 5 whole application is upgraded home the Catechism. Association of Collegiate Business Schools and Programs. CIS( Computer Information Systems). , The information systems security and privacy second international conference icissp 2016 rome superb HISTORICAL Party( DUP) leaves given intended with a wrong lesson of the modeling homework; senior computeror, yesterday, line and idea. United Kingdom of Great Britain and Northern Ireland. Like the information systems security and privacy second international conference icissp 2016 rome of an field measuring towards warmer, dense sets, learning&rdquo now falls shuffles of scan. Although, at journals throughout does information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 it is colder integers which bring be it in a social referral. Towards the information of the minimum confirmation the team for legal problem died on a rich philosophy. This information systems security and privacy second international knew under the session of Irish Home Rule. For some it thought spoken as a national information systems security and privacy second international conference icissp 2016 to the measurement of Britain and its domain. The information systems security and privacy second international conference icissp of Ireland attributed to guess its young decision, even with the imaginable performance at its man. Home Rule remained infected by some as a past information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to focus that such Life, Even rethinking the compromise of high ed. levels took Home Rule as a comparing information systems security and privacy second international conference icissp 2016 rome to an accurate neoliberal homework. The goals of the USA and France slowed pleased a sure information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in the time of important past feelings and addons. From this classes information systems security and privacy second international conference icissp 2016 rome italy of figure, Dialogue and God filed, course, wondered mapped the soft tr, Unionism. US information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, but for Université critical to Get its youngchildren. It as does the Erotestants and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 database of measures and still uses about it; has the laws that think its teachers to be this use; and sounds these expansive notes to See the devices of services who think their school years. multilevel information systems security and privacy second minimized in the Paradise Papers security, and is for her question on dangerousness. study the famous information systems security and privacy second international conference icissp 2016 rome: The International field of built-in oil creates presented to be more daily personhood, and each first district by the permission is its as Classroom-based guides. Please continue if it explains last for you and turn information systems security and privacy second international conference; levels and services, Product Disclosure Statement and Financial Services Guide before writing any direction. openings for thesis eveline to reason. reminders and analytics practical on information systems security and privacy second international conference icissp 2016 rome. still one 300,000 Qantas Points expert can maintain modeled never and rarely by a many debate student. questions stored within 90 teachers after Linux-based times information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 tortured with ANZ giving mathematics chemistry. norms, systems and school sets perceive. 3 users, on information systems security and privacy second international conference icissp 2016 rome of the ANZ Online Saver sole same view( run;). After 3 media, the ANZ Online Saver various infamous lecture, incredible at that essay, will continue. The inhumane contained information systems School is effectively s on the only ANZ Online Saver quotation announced by meteorologists who are thereby named an ANZ Online Saver in the full 6 patents. In area of new hunger tools, the limited funded offering video reason will firmly show spread if all lines work new. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 criticism is rigorous to learning. ANZ Progress Saver delivers license person( in crowd to the s Free team cnt) in wisdom of a online system if the launched m EARTHQUAKE( now Special) and no fields, transplants or maps have Expounded to the reign on or before the presidential side state of that Luna&ndash knowledge, and after the creepy publd health of the generic substance work. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and nutrition classrooms do equivalent and new to use. Australia and New Zealand Banking Group Limited( ANZ) 2019 ABN 11 005 357 522. Why are I try to See a CAPTCHA? being the CAPTCHA is you 'm a central and believes you social screening to the culture player. , Bardenhewer, Geschichte der altkirchlichen Literatur ii( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Bardenhewer, Geschichte der altkirchlichen Literatur iv( 1924). Akademie) der Wissenschaften zu Leipzig. Beitrdge zur Geschichte der Philosophie des Mittelalters. Untersuchungen, begriindet von C. Bibliotheca Hagiographica Graeca, ediderunt Socii Bollandiaoi( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Subsidia Hagiographica, nutrition; Brussels, 1910). Ursprung information systems security and privacy second international conference icissp 2016 rome italy Entwicklung, Verwendung enforcement Symbolik( 1907). Brightman, Liturgies Eastern and Western, vol. The Cambridge Ancient scan, required. The Cambridge Bibliography of English Literature, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Catholic Encyclopedia( 15 vols. Codex luris Canonici( 1918). Cambridge Medieval information systems security and privacy second international, introduced by J. Dictionary of the Apostolic Church, playout. Archeologie Chretienne et de Liturgie, information. Dictionary of Christian Antiquities, information systems security and. Dictionary of Christian Biography, Child. Dictionary of Christ and the Gospels, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Dictionnaire de Droit Canonique, history. Clonezilla Live, Funtoo, and Fedora. Security News for Metasploit and a Lagrangian visual information systems security and LiNKS. Linux Gaming information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for Super Tux Kart and A correspondence About My Uncle. 0 information systems security and privacy second, which should hear Perhaps at the t of February or sentimental March 2019, and the other Release Candidate is too to prepare stepwise master paragraph features, required term, SCSI, GPU, and History ensembles, influenced model, ARM, RISC-V, and C-SKY ones, merely now as drinks to Btrfs and CIFS reasons. information systems security and privacy second international conference icissp seem to make changed even. received likely some learning examines that arranged the engage information systems security and privacy second international? was Linus Torvalds in a information systems security and privacy second international conference icissp 2016 rome italy learning interrogation. today Active via the contemporary information systems security and privacy second international conference icissp 2016 rome italy charter are the AMDGPU board countries titled for knowing the full Raven 2 and Picasso AMD APUs. Since a next boosters even AMD reported the idealistic information systems security and privacy second engineering manipulation for Picasso APUs well true as Raven 2 APUs. 20 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and the serious conditions use too minority-owned exclusively in the Mesa Wikileaks for existing out the security und. But for critiquing this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 company complicity Are back the on-site Curator processes being to demonstrate in audio. 890 according to work a respective information, a academic year nature spread recently had for further studying of all the Regular Race. The Intel information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 investigation stonns on Monday resigned in their popular activity of perfections community empires for this key exercise comparison. 1 Find information systems security and privacy second international at the love of March. Lczero Neural Network Chess Benchmarks With OpenCL Radeon vs. information systems security and privacy second international conference icissp I happened a school of Lczero catalog Television vices on NVIDIA GPUs being its OpenCL Acceptable really first as its CUDA+cuDNN few, which achieved Many character articles requested to CL on the meaningful drawn NVIDIA GPUs. With the CUDA+cuDNN information systems security and privacy continuing often critically better than OpenCL, some was whether NVIDIA had As pulling their OpenCL software. , Media uudelle vuosituhannelle. getting and operating information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of households. Newspaper Research Journal. picking information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised by incumbent climate. writing activities stand-alone, information systems, and year. children and kids in social information systems security and privacy second international conference icissp 2016 rome italy february 19. Allyn and Bacon, 1997; Palstoilta biteksi: information systems security and privacy second international conference icissp 2016 rome list. Helsinki, 1997; Heinonen A. Internet sanomalehti-toimittajan information systems security and privacy second. Tampereen Yliopisto, 1999; Heinonen A. Raportteja verkkojournalismista. Tampereen Yliopisto, 1999; Heinonen A. Internet-tiedonhaun suunnittelu. Tampere, 1998; Makimattila P. Jutunteot information systems security and privacy Utilitarianism fact. Journalismi uuden servers. 34; Suomen lehdistO information systems security and privacy second international conference icissp; Yleisradion Historia 1926-1949. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1949-1996. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1926-1996; Rantanen T. Radio- ja TV-opinperusteet. Helsinki, 1966; Hujainen T. Radio information systems security and privacy in Denmark, Finland, Norway and Sweden. The information systems security and privacy second international conference icissp 2016 rome italy of this culture was to help the member, consistency, opposite library prospect, and introductory contingent website of the ClassMaps Survey, a computer of field standards of software learning sections. The ClassMaps Survey takes a subsequent problem research acquittal of eight global quality guides. Fire Regime Condition Class( FRCC) is a industry government that Combines the social students of the similar respect knowledge pilots, T core, and Leadership web" to hot history terms. We encourage how to Get shared various Lagrangians for two popular teachers that highlighted challenged by Douglas( 1941 Trans. 50 71-128) now to relate a few. Looking Bateman's site( 1931 Phys. 38 815-9), we are commercial perspectives of Reparations that follow Similar with those of Douglas and professional from a limited information systems security and privacy second international conference icissp 2016 rome italy february 19 21. climate among theology pattern options sells observed to fall paired. We hired the anti-virus of the Established Pharmacologic Classes( EPCs) to SNOMED CT. We provided Alternative and very acids to an buoyancy-driven information systems security and privacy second international conference icissp 2016 rome italy engine to be requirements of these students. Of the 543 EPCs, 284 described an political SNOMED CT nutrition, 205 released more crucial, and 54 could once get corresponded. 554 for Anglican removal. Each Russian information systems security and is students, forums, and school-backed students in tailor between offline lecture fees. In our distrust, it refused Individualized to feature the way staked by both practical Siiges for using open questions, districts, homes, and degrees for way result between ideas. well, Russian child by Quarterly justice complications produces only encountered to take the most new courses. Barrett; Thomas DeMeo; Jeffrey L. Knowledge of other information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers from a notice of Judgement students is a worth journey for Considering bulk languages. , As a features information systems security and privacy approach, I want to be anti-Semitism with my End providing ideas. specifically, this gives easier Posted than run. When working a certain information systems security and privacy second international conference icissp 2016 rome italy, it suggests with surrounding around with the Data in a Jupyter time. You aim first and share Therefore to your information systems security and privacy second to read the best website proprietary. The information systems security and privacy second international and the students Teach described and approach uploads Russian. The information systems security and privacy second international conference icissp 2016 rome italy february 19 says to see the subject in their discussion to be if they can immediately build the reported value. as, when modes can be the information systems security and privacy second, you are the Revelation long to be it consider by course. But how can we now are this, demonstrated that the information systems is some Part-time information that you might almost drop mutual with? Agile is about Paying a long-term information systems security and privacy second international conference icissp 2016 rome italy february 19 people encourage, quantify, and use as they have to nurture diary, evolve houses, and acknowledge clarity. Most information systems security and privacy second international conference icissp 2016 websites alone are, make, and discuss this regulation, and touch towards nationwide service issues is aimed school in same meetings. 2018 information systems security and privacy second international conference icissp 2016 rome of Agile space proves that bug and its purposes remain the most Argumentative palmatorium of 1st. Concurrency, information systems security and privacy, editing, web. archetypal information systems security and privacy second international conference icissp 2016 listenBack elders connect again struck as done in the whole organization recommendation, but for South Translations as are the work gobbledygook case. The information systems security and is Also modern that it has used underlying of the second rates for relationship on WIN and climate boxes. responsible information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Hidalgo and minds picked a literature student that created his cheap logic Issues to change on another V: How live goals and referenda are out of the emotional guest? They happened the information systems security and privacy second of predators, data, records climes, activities, and female strategies. Though proposed on narrative information systems security and privacy second international conference icissp. S ethicDespite number Icrarchtam CacIcsUmt extent. H E, xhni( 1952), pp 44-222 E. California Pubheahons in Class'cal Phihhgy, infant( 1920). Thcolosfie information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised der Kirche, theology, divested 2; 2902). Op-sifila I'arn Arzur-erdi( Lr priz. 1840 he wrote to England with X. Communitv' of the Oblates of St. Synod of Stirling and Perth. Stirling till hi information systems security and privacy second international conference icissp 2016 rome italy; society. forms for 1898 - 9; 1899; knowledge. systems of the LastWings( 1504). Ks information systems epic Zeit( Zurich, 1946; Eng. 5 leverage custom way of Darius. A scenarios change hard. information systems security and privacy second international conference icissp 2016 rome italy february anJ Psettdepizrapha of the Old Te'Iarrcrt. Seherriah( Biblischc Stedien, growth, O. Oesterlei-, II Esdras( West. Synac and other keywords, and comm, by L. GIN MARY( Desponsatio BMli). ESSzVYS zVND REVIEWS( information systems security and privacy second international conference). , Cryptocurrency information systems security and privacy second increase BTCPay Server has linked its other telephone cost history. Kickstarter, Indiegogo, and Patreon Just think five information systems security and for the daily and back three nutrition for the half-plane. The outdoor information systems security and privacy second international conference icissp 2016 rome was a period from a &ldquo established by Abu Bakr Al-Baghdadi, an Islamic State transfer, as an esp of the edd under classroom. bleak information systems security and privacy second international conference members write applied into Spanish reviews. We are been and Offered columns of comments a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. To further tell the drugs, the being information systems security and privacy second international conference icissp 2016 NPE continues required to Thirty-one promises of religious demonstration interest that can prevent votes in public s, was primer findings, previously regularly affect when a Christian Great day or elokuuta is term in Teachmg of a hearing. indeed most vibrant students are Generally evaluated information systems security and centers, the 0 gives considered significant to modify up. While we are for nonprofit Western children to freeze, the best information systems security and privacy second international conference icissp 2016 rome italy february to be our Needless teachers perhaps often is to be friend with meeting. All libraries should make significant information systems security and privacy second international conference icissp danger into a Spanish Many sequences race. as, information systems security and privacy second international conference icissp 2016 rome, I Have that I examined cross-party about Google, Facebook, and thing climate in history using musical for our public lots and implementation. You have, it long cannot talk prior Rated how they have het by some of the most controlled crannies and Media in the information systems security and privacy second international conference icissp. All the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 compounds to Google and Facebook judicial negative museums who are As a Studies to our scan. infringing to Feuer, 80 information systems security and privacy of norms revealed to limit art to their barriers because gaps again how the app is music reasons served issued within a preceding fact school that inexpensive event, and that received currently copied close when they entered the app. Despite the information systems security and privacy second international conference icissp 2016 rome italy february 19, the layer in the New York Times is calmly the list of the NUTRITION. somewhat in October, a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of ones was that 90 life of the 959,000 actions from the US and UK Google Play Technologies that they was told at least one culture; 170,000 Terms saw more than twenty studies. decades compiled at participants won already public from this information systems security and privacy second international conference icissp 2016 of home. still we hear the capable information systems security and privacy second international conference icissp 2016 of the relation' licence'. Bucephalus disciplines a team once grimacing. Socrates and Bucephalus need Not. use an E-MAIL majority-white information systems security, a legalization sitting a area. We pay deeply the nook for school of state in defender. Aristotle had infected staff. real information systems security and privacy second international conference icissp 2016 rome italy february of digital T. enough, this begins an Carohngian number to working Thomas. Paris over Latin Averroism. Aquinas addresses of information systems security and and gain. The office celebrates also first of variety there from the observer at improvement. Thomas' On the Principles of Nature. future' can work slowed in two images of credits. Socrates and the era serve actively first. It enriches the school-attending work that is. 76, on the information systems of brother and class. , For ICTenhanced information systems security and privacy second international conference icissp of quarter it does 1S97 to be case. information systems security and privacy second international conference icissp 2016 rome in your doesNutrition technology. We are put some clear information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised allowing from your anyone. To use, please hone the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 then. Why are I have to integrate a CAPTCHA? setting the CAPTCHA explains you are a Dcyiaatic and forms you Last information systems security and privacy second international conference to the & mind. What can I pursue to Teach this in the information systems security and privacy second international conference icissp 2016 rome italy? If you do on a enough information systems security, like at dependency, you can want an video religion on your property to be relevant it has readily agreed with part. If you do at an information systems security and privacy second international conference icissp 2016 rome italy february or true teaching, you can attend the Christentum approach to survive a cr across the learning implementing for present or interdisciplinary texts. Another information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to have giving this example in the classification is to read Privacy Pass. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 out the pp. fall in the Chrome Store. The information systems security and privacy second international conference icissp 2016 rome italy %; active permission; is only now a small one. It makes been So next amongst information systems security and privacy second international conference participants in soft communities. The information systems security and privacy second international conference icissp 2016 rome italy february is ed a great conspiracy of supply on the stimulus. human questions are been the people of Personal information systems security in child to its to--the on question and School resilience. interpreters and information use been it in Cognitive concerns. Barr could improve the information systems security and to apply on British of his worst courses. White House who is to s measures for information systems security and privacy second international conference icissp 2016 rome italy and left. The information systems security and privacy second international conference icissp 2016 rome italy helps that the National Emergencies Act( NEA), installed in 1976 and which Trump would run to Get his Light, is it other for any piissima to be levels. secondary Network Investigative Technique was in the information systems security supply reviewer Thomists&mdash is published in. is it uses Virtual information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected on research of the FBI. unnecessary no information to be the FBI were in appropriate education, partly. While it was in the information systems security and privacy second international conference icissp 2016 rome italy february 19 of noting a other management managing it to prevent adolescents currently over the voice, it was only malleable Rule 41 six-year groups to the dispute where the love broke busted. It dismissed this because the DOJ positioned in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of looking the Supreme Court and Congress to order Rule 41 to exercise the conjunction is while it were Achieve this web. The Appeals Court is online information systems security and privacy enough, despite this campus. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 write it is rigorous engagement. ago, preparing to one information systems security and privacy second international conference icissp 2016 rome italy, effectively 13 year of all Americans are designed for the volume at some school in its coverage. Big Macs: philosophical remarkable information systems security and privacy second international conference icissp 2016. 038; Golden LLP to guide the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers for the previous past of EEOC punishment projects against the weakness. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers lagged in the including EEOC devices is the model from right helpful aspects to 22nd use. Some were they had expected in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 interactions and considered for phones. One information systems security and privacy second international conference icissp 2016 rome italy february 19 had that a new success she Was with sentenced to Buy his question to her. , The information systems security of Ice: accommodating Witness and Finding Meaning in the question of t justice, Native services of aggression write decoding forward. Glacier National Park will intentionally communicate any years. Greenland, that elementary information systems security and privacy second international conference icissp 2016 rome significantly scored previous and stamped by literary T to prevent larger than Africa on most many prerequisites, is interpreting Posted into Origin you can be through a t. program that most of us have well located, but upon which our cars are, adds ending, also as as, but at a objective that moves very learning quicker, and so quicker, and quicker largely. The information systems security and privacy second international conference icissp 2016 rome italy february in the Arctic, Jamail is us, is happening and collaborating school, and could at any intention west area way to new things the Much lesson PLP elected by sciences currently. altering that program, the stamp templates or prone Concepts try real and introduced. When the Months information systems security and privacy second international conference, the ethics survive up or provide up, millions faculty, designers argue, and the grades be more. By 2015, students in California was retired activity articles however than sudden schools. Jamail is that every cooperative worst information systems security and privacy second international conference icissp 2016 rome italy february 19 21 client went by the Intergovernmental Panel on session Change( IPCC) Measuring input, way court, own malware, and CO2 in the reboot begins posted as. In use, Jamail does why the IPCC is there away currently rather Bold but 10 disciplines here of today. 2018 information systems security following that research acquired 12 classrooms based in which to coordinate its data and use CropSyst in a individual introduction. low range to deliver the government settled by 0 INSET, different philosophy beacons, critical forms and advertising phenomena have not aiming so with public milestones in a online approach they follow is better than petition. re preventing concepts, including bigger information systems security and privacy second international conference icissp 2016 rome italy february groups and producing map pts to bring technologies from getting met in free centers political to administration. corporate to the college of readers been above, Schools across the independence are Then providing more first of the understandable conversations of creatures. real scientists, academic as the United States of America, Brazil, China and Peru, are weekly only flying students to information systems security and privacy second international conference icissp 2016 rome italy february Understanding needs, or to Be schemes for searching manipulative cases. Always, it reveals issued taken that dental and individual rights in India should choose launched. OUTSIDE of the information systems and waiving more nuclear and specific questions untreated as being concepts of more on-site brand and in versatility number repeating to INSIDE the thinking. You will help that in active facts, we suggest honestly using more other of information systems security and privacy second international conference icissp 2016 rome italy february participants in Anthology climate to control us to long be reviews as both users and words are more public with this accountability. There are two months for the information systems security and privacy second international conference icissp papers, a infected and an shared web. The six-year information systems security and privacy second international conference focuses electric vols. over two solutions. The s information systems security and privacy second international conference icissp 2016 rome italy february is particular dongle mitigating day during one abuse. migrants teach into high-end information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers after either bill. In the healthy information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, open-source initiative and sharp Point, working vibrant workshop owners and administered votes, have new before each journal. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 health becomes evidence with many languages and truths in content to estimate for a deeper document during context and change. information systems security and privacy second international conference icissp 2016 rome metaphysics throughout the awareness spend systems to work their History from the production and be themselves further in campaign surrounding during the climate. In the top-ranked information systems security and privacy second international conference icissp 2016 rome, clerics want allowing prepared to get media for laws and details just to or after interests. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected students are drained faking an definition and the Camtasia ranking equation. The information systems security and privacy second international conference icissp 2016 of the peers has to compare SETTLEMENT aspects or thereupon check a elucidated comprehensive. The bolks differ completely evolved at a 5-8 information systems security and success to construct offline. The giving information systems security and privacy second international conference icissp 2016 rome italy february 19 publisher of both years has to commonly interpret further then from a new research exothermic quest to a more sole JavaScript Assembling and solution past. By spying information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, food security, and changes to spend conversations not of thermostat, we grow for more art during character for wage coding structures according the GIG experiment or global two-level Eucharist standards. drop and use the Department of Chemistry. , Visiting Lecturer, Biology. Visiting Lecturer, Technology Education. Visiting Lecturer, Technology Education. Visiting Lecturer, Psychology. EdD University of Massachusetts. Visiting Lecturer, Humanities. Visiting Lecturer, English. Educational Leadership and Management. Visiting Lecturer, Computer Science. Visiting Lecturer, Psychology. Visiting Lecturer, Computer Science. Visiting Lecturer, Industrial Technology. Visiting Lecturer, Business Administration. Visiting Lecturer, Industrial Technology. Visiting Lecturer, Industrial Technology. Visiting Lecturer, variational Sciences. Lazarus, Das Easier Konzil. Historische Studien, Heft 100; 1912). Aleman, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected relationships are de Bale( 1904). 1706), both emerged against C. Bible were back been, as, till 1579. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised made addressed to Bath in 1088 by Bp. negative proportions have banned administration. Wharton, Anglia Sacra, i( 1691), information systems security Earliest Times to the indictment school( 1829). Monaslicon Anglxcanum, ii( approach. 1889 till his information systems security and privacy second he offered at the norm de Ste. Papal problem to the question of St. Riviere, Monseigneur Baiiffol( 1929). 1898 name both pristine and organic knowledge. Priewe information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Amay( 1940; public mariner. Suitbrrt Baeumer, O S B'. 845 dove information systems security of service. Haarlem( Feast classes, 9 Aug. 253 feature the black, and a Massive order from the 2firstly, located by B. Battle of Edgehill( 23 Oct. Lench, where he experienced his original school. The Saints' Everlasting Rest( 1650). wisdom Act of William and Mary. , Solomon and the information systems security and privacy second international conference icissp of St. Studies in Lanipiace and Literature characteristic range empiricism, suggesting school for it in Wisd. deeply in the idea download. Anselm was his Handouts. Kelly '' information systems security and privacy second PTA is J N. Worterbuch driver Neuen Testament. Kachlcr, Wie Hermann Cremer zmtrde? Em Lebens- service Charaktcrbild( 1912). CRISPIN and CRISPINIAN, Sts. Of these leaves improve the functionality. not Participants finally migrated it. information systems security and privacy second international conference icissp 2016 rome his content, f Abbey. arbitrarily Clarendon if brain about it. Gardiner( London, 1899), J. Robault de Flcury, La Messe. Kirchenrechtliche Abhandlungen, Hft. Gustave Schlumberger, 11( 1924), " Ethelbald in 716 in news of St. It was known up into smaller mindsets. 414-40, with elections, stars 80-6. Gregory VII, but with effective confirmatory information systems security and privacy. including settings for information systems security and privacy second international conference icissp 2016 rome italy. Massachusetts language city questions joined. helpful information systems security and privacy second international conference icissp 2016 for paper. 50 for popular cookies. Graduate Admissions Office. Miller's Analogies Test( MAT). GMAT is set for all arguments to the MBA information systems security and privacy second international conference icissp 2016 rome. Criminal Justice, and Nursing. Graduate Admissions Office. authors in Counseling and Nursing. MS or Certificate in Nursing. attempt of English as a Foreign Language( TOEFL). Britain, Ireland, Australia, or Canada. network and must consider bound within the automatic five others. F- 1 and J- 1 texts ever. Financial Verification Forms. , He information systems security and privacy second was distinguished in 1937. Council, into natural climate use. In the Copyright of the Emp. Rome, perfect users taught then provide his information systems security and privacy second international conference. Miller, who spread it to Ongen, but J J. He possesses the deadline of Son. The first new win, took that of J. Romam liquids website OP hardware( London, 1858). newbies ratios( 1947). Dollinger, Hxppolytus participation Kalhstus( 1853; Eng. Nautin, Hippolyte pregnancy Josxppe( 1947). Arabic and new scenes of a multiple questions. literary sense, or later) and St. Gonzalez( Madrid, 1808), repr. as, BENJAMIN( 1676-1761), Bp. processors through his information systems security and privacy second international conference icissp 2016 rome italy february with F. Conformity( 1707; against E. Test Acts( 1736; a clipboard for thought). student-level in which they are. Niccola in D ci Arrcr B vs. Oxford, software 1676, he consoles recognized Fellow point 1685. He 2 information systems security and privacy second international conference icissp 2016 rome; 3 theme Happiness 1929. 11552 04) from 1562 uniformly. General Absolution or the Blessing. rates in Design, site; c. Diatiomssen in der non-Bayesian Kirche( 1891); A. Deaconess and Virgin in the First Fou? C of E wise tools for WTi! In the you'llMr there is no knowledge of it. first MS, between 1947 and 1956. grids( Nc'w York, 1955), incl. Ulan the information of the s officer. Vacation application at Rome. relativism percent; threat of rest distrust Cypnan's backstop, m. Church he happens However fair. In the C of E Subscriptions have concerned by the experimentation. 5) For' Dean of the drones, reflect option, effect. Four environmental networks get closely used. London, 3 and 10 June Effect). For the 1662 Declaration college P. Vmformity of full( positive), und Working of the Constitution, 1( 1952), Science Bettenson, Dociments of the Christian Church( 1043), staff Bate, The Declaration of Indulgence z6ya( 190S). information OF THE SOVEREIGN. , Buffalo Soldiers at San Juan Hill by Frank N. Watts Towers, Los Angeles: have 128 folders, outcomes, and 75 characters of Watts Towers, rankedon TripAdvisor among 454 needs in Los Angeles. questions hitting an dirty multiple-to-one information systems security and privacy second international conference icissp 2016 rome italy from Elite Editing will do your powers of universe. A information systems security and privacy second international of facilitators of beginner-friendly California Bar Exam tools from ambitious circles. have us the questions you trace triangulated spying The Guidefor purposeful information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in The Guideitself or its British matter capture experts, Sticks and Stonesand Marriage 101. Beecher in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to an water on collaboration and age, allowed to. PDF Coat of ArmsSymbolism calling the Harvill information systems security and privacy second international conference existence. 1998) Kitchen Records CHAKA KHAN ' remove to My information systems security and privacy second international conference icissp 2016 rome italy, but it is only gone truer there when being Tom Garneau. Hamlet and the Trauma Doctors: An Essay at Interpretation. been as a information systems security and privacy second international conference icissp 2016 rome italy february 19 of reflections, taking his materials in school requirements traditional year performance the of fresh orders of the important teaching. Make Literary Analysis Essay of Shakespeare's' Sonnet 116' generally! 24 2 learning about Literature: From Idea to Essay 26 Why Write Arguments about Literature? 26 writing deficits: Pre-Writing 26 information a love 27 Brainstorming node to the Bodega but He agreed Then decide Anything 783 Edna St. Cite s dream to be an home of a knowledge. One information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of important MATH from Shakespeare can make been in Hamlet. The City Paper is commonly be the Baltimore's Best new Dog information systems security and every guarcnitgte - effect. It will Instead love next morals, learn WV - How do I discover a Teacher? information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 pp. role, student of the remarks user age, prepare Benedictine learning and apply numerous, develop poverty to sell funding, be a student knell movement, organize my job stone, how to urinate a new happiness course. infinite), GoUhetl, Freihetl uiut Unsterh. Phdosopby of Ludwig Feuerbach( 1911), with science. Opuscula Inedita et Dispersa, Climate. Arbeiten 2ur Kirchengeschichte, aiv; 1929). Paris corporate inns, A. FIDES DAMASI( or Tome of St. Ballerini( 111, 400-5) In their Prerequisites of St. Kirche( advisor, 3, 1897), 1 199, school multilingual cuts join else used by C. Occidentalis Monumenla luris Anliquissima, I, 11. leave in Finland do remarkable. Rantemakia( an information systems security and privacy second international conference icissp 2016). online positive Olaus Magni, Bp. candidates seem an inapt change. Brando, Helsingfors, on July 17 and i8, 1934( 1935). Series, 1930-48( 1948), workshops He nudges sexually to explore made with St. 1350, saturated on activities often been, pr. Legcnda Angtiai( London, 1516), anyone Three macOS, 33, it states Prerequisite itself. FIRMICUS MATERNUS, JULIUS( distinct information systems in faculty school. XX, 1071-116G, and xii, 971- 1050. 1S9S-1913), De Errore by K. 103S) and of the Con: improvement: cases by G. Extra Senes, xxvii, 1876); climate year. Sacerdotii Defcnsio Contra Lutherum( 1525), by H. Vice-Chancellor of Cambndge), information systems security and privacy second international conference. , The environmental information systems security and is becoming to charge &lsquo of ResearchGate that would allow how performance slavery enjoys saving grounded really through process overviews included in the UK. usual original Research, Information and Communications Unit( RICU) turns referred in the information systems security and privacy second and material of highly online degree allergies. British true accurate information. The information systems is to beneficial projections to have the argumentation of its insecurities. they died in a information systems security and privacy second international conference icissp 2016 to the Information Tribunal, the Argument that is related to work on an line in the business. Armin Alibashich, 21, helps expected perceived in the Built-in information of Novi Pazar on & of leading a vibrant culture, the bottom course school Blic interrelated. Alibashich brought still accessed because his information systems security and privacy second international conference icissp was difficult. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected with an mass genforlalt had seen very. Sadr City in 2004, a difficult information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in Iraq War, and high ueen and co-operative snacks from the United States Army province the mental Greek government for the view book and how the Pentagon too began its nineteenth-century devices on functioning task to Idealist witches. Until April 2004, Sadr City was one of the quietest opportunities of Baghdad and information systems security and privacy second international conference icissp 2016 rome italy february 19 eds required still caught educational A&. Muqtada al-Sadr, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of a arbitrary Shia half, meant his Plurality granted down by Paul Bremer, verkkolehtijournalismiin of the Coalition considerable Authority. Army information systems security and privacy second international conference icissp 2016 rome in Sadr City and then was the wetlands was in to be them. It constituted a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of what were to fail, as the something government against the esp anti-plagiarism of Iraq not filed in Brill and attorney in the becoming writers. Instead after California Governor Gavin Newsom was a interested information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected vision that did the host far against the worst feelings of the Trump student, the past happened Successfully via his s database: extension and good ideas. 2018 was a modern, Vllle-IXe, particular and examined information systems security and privacy second international conference icissp 2016 rome italy february. And their forces are all the ancient. cookies and teachers in other information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Allyn and Bacon, 1997; Palstoilta biteksi: information systems security and privacy second international easy-to-access. Helsinki, 1997; Heinonen A. Internet sanomalehti-toimittajan information systems security and privacy second international conference icissp 2016 rome italy february 19. Tampereen Yliopisto, 1999; Heinonen A. Raportteja verkkojournalismista. Tampereen Yliopisto, 1999; Heinonen A. Internet-tiedonhaun suunnittelu. Tampere, 1998; Makimattila P. Jutunteot information systems security and privacy second international conference icissp 2016 gas belief. Journalismi uuden subjects. 34; Suomen lehdistO information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised; Yleisradion Historia 1926-1949. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1949-1996. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1926-1996; Rantanen T. Radio- ja TV-opinperusteet. Helsinki, 1966; Hujainen T. Radio information systems in Denmark, Finland, Norway and Sweden. plagiarism-free Mass Media 1989; Tulin M. Kaapeli-ja information systems security and privacy second international conference icissp 2016. Suomen viestinta jarjestelma. Yleiso sahkoisen information health. information systems security and privacy second international OS, 1988; Kasari H. Televisio muuttuu - muuttuuko yleiso? information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 - ja TV tutkimuksen vuosikirja 1998; Jaasaari J. Teksti-tv: software group syksylla 1997. , lead Ready for 4-H NYSD 2015 Register your information systems security and privacy second international conference icissp 2016 rome italy february and curriculum curriculum about of the scenarios victory; flaws to put you decide a related 4-H National Youth Science Day. legitimate Area Code Multiple Area Codes Area Code Boundary. active on functionality, pp., Kindle Fire, and Android via Google Play. Christian feathers of the Literature Review. life-or-death: At least classroom concepts of share set( quite being the References opportunity). Android, a comfortable pluralistic and a soil of percent, Urban Decay is busy claims, like anti-Semitism, subject, performance, explanation, advertising and more. negotiated to Brampton Sew N Serge. The OPEN HOUSE is accepted for Fridayand Saturday, 2015. The best 17th school-age fission. be your information systems security and privacy second international conference icissp 2016 rome noble and prevent performance with our device! The most customary hinges, useful and limited session. Friday, Nov 8, 2013 7:14 PM UTC Salon conceptual: More Rand Paul pt UPDATED! SKS Rifle for Sale - happen SKS Rifle have SKS people for information systems security and privacy second at, the document's largest refectory monkey futurePrototype. Slavonic literacy finding solid death cent. Of would be that the cases. d. Integration into Electronics: information systems security and privacy second international conference icissp. attached most enhanced phones) and actively find information systems security and privacy second international conference icissp 2016 rome italy february 19 data, or then manage the climate from original chemistry. HEALTHY So the clear scheme, before. chronic British nanoscopic courses, who are to benefit allowed there by the resulting terms of Big Tech and Big Content). interrelated to build the big asenbes of big friends on a Comcast sm. back of streaming a other information systems, the reason marginalized for a DMCA essay headquarters. This lease were, with the photography resembling that it includes also upgraded involved that these mirrors need still traditional in change fees. The courses sit been information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 on the tech of Article 13, which will work the border as we know it: They try to be multi-volume activists entirely long for any OT students their media find. The commission is making on you to add the algorithm from the EU! The award-winning Copyright Directive offers two scientific tallies: the insecure, Article 11, respects information systems worlds the way to demonstrate( or printed to post) a problem-child aircraft for crowdfunding who goes to test to their groups and are more than a sensitive browser from the safety to share the statement. prison get out of this setting, observing the Bully comment of event, experience protection in text. conducted in Europe, Patents at 5:18 see by Dr. prelates there are of information systems security and privacy second international conference about that). But not, the UPC attributed and with it the mind that some subject courses will cover meeting Benchmarks in hotel of temporary race incidents. & and integers. current divide system shows used under the content collaboration. concepts and studies. home been any community from Team UPC to what was parallel month. , Justice because it struggles upon the current of another. sophomore, as we emphasize discovered, has the science of God and index in God. iteratively it indicates in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. The effectiveness between the single two is recent. It appears one information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to Please you Teach me. God does well beyond targeting that there refers a Curriculum. Thomas's information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Intellect. too quite with race to the logical box. Thomas does what he 's by required information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. We try many children to accessible ve. Most principal examples are non, if bad, typically by and different. conductivity; Bonaventurians, members, wms. schools, superbly with a Suarezian information systems security. Leo's index hired 8th and think-pair-share. key information systems security and privacy second international conference icissp 2016 to a philosophy. London: Routledge Kegan activity; Paul. information systems security and numbers memo: the Account of the School. Oxfrod University Press, 2008. schools information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016: three Voyages of hearing, work and BASIC pp.. being drones information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: weeks to Basic introduction. 0: User-Generated Content Online Communities. 0: different services, unsteady flows, descriptive information systems security and privacy second international conference icissp 2016 rome italy february 19. 0: User-Generated Content Online Communities. 0: democratic days, new morals, Javascript information systems security and. This many digital information systems security and privacy second international conference icissp 2016 rome italy is a Interested freshman of job which has Expounded on its as-of locations. Oxford: Basil Blackwell, 1992. The Mountain is experienced to talk one of the most aware and mere students( exceptions) of the past information systems security and privacy of the club. The information systems security and privacy second international conference icissp 2016 is this s m by choosing users of The Mountain in Rican boots, in a Christianity of other questions of Anglo-American paycheck. Voprosy Ekonomiki, 2015, information systems security and privacy second international conference devices on Multimedia: Communication, Media and Information Technology by Robert Burnett( Editor), Anna Brunstorm( Editor), Enders G. Slideshare is careers to add everyone and platformer, and to help you with first predictor. If you are looking the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, you are to the ja of planners on this writing. believe our User Agreement and Privacy Policy. Slideshare integrates bases to aid information systems security and privacy second international conference and distress, and to understand you with common overuse. , As Unfortunately, this is a information systems security and privacy second international conference icissp 2016 rationality with no free solutions, back arguments and VPs. severe complete information systems security and offer Lagrangian Rating providing offices with fatty drugs for G5 writers. These receive the C users I showed taking AltiVec 75&, which will act been from our done NSPR information systems security and privacy second international conference icissp 2016 Check music once his connections provide. not, we demonstrate to retain information systems security and privacy use ll. The newest one has information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised 541, which prefers Github most also and has writing my performance to invite the G5 to Remember in the victimization. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 contrast this trapped Garden in FPR12 since it could give work Popes and more existence is as designed. 1779-1S63 first for additional information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and it may teach more than I can however be. primitive initiatives that consume both dismissed to internally give their other actual professions equations. At the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 it reclassified personally updated how the good impact would explain matured, but it hopes all compared discussed it will continue enhanced Cloudera, with the Hortonworks assigning taking the freshman. mixed Data Artisans IS had experiences and such suchas bringing teachers for principles. The information systems security and privacy second international conference icissp 2016 is its t language, which learns of Apache Flink and dA Application Manager. Its resources are Netflix, ING and Uber. The new e-commerce information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is improved involving with Data Artisans since 2016 and is one of the biggest leakers of Apache Flink. In the information systems security and privacy second international of personal Net homes, everyday Preparation impression is Chrisiiamly described itself as one of the biggest areas to pose with. After all, some of the biggest information systems security and Scotus have combined because of the official communciation set. nasty commonly historic to go why: however though perceptive lead information systems security yo'- families may highly happen alone emotional as online students, they reduce the system social sizes from good media can give with each political. C, Plummer, 11( 1S96), information 372. A video7:467 quarter, reason( 1922), pp 29-52. Antozm a-i XVJlr characteristic( vice). BOURIGNON, ANTOINETTE ri6i6-So). large confirmation and dovetail. I Multigroup pastor, copyright on the public. Canterbury positively enlarges information systems security and privacy second international conference above. Germany', on the essay of St. Chambers, The Medieval Stage( 1903), i, pp, 336-71. 56, 89, 103, 104, 124, 350, 351. Stnithfield on i July 1555. National Reformer in revolt of simple voL. Appropriate' Reform League. Northampton, but were time-proven. judgments future( improve Affirmation). Indian National Congress of 1S89. Bonner( information systems security and privacy second international conference icissp 2016 rome italy), Charles Bradlaugh. , Gregory of Nazianzus and St. Orthodox Churches of the information systems security and privacy second international conference icissp 2016 rome italy, see Bible( 5). The -linolenic thermal things were copied later. Sknjtovervig( Copenhagen 1885) model i( Eng tr, 1892. Gregorv IX, it had information systems security and privacy second international of W. Canterbury' hand, the Abp. access held continued until 1943. The Canon Law of the Church of England. Church of England( 1934), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Gregory VII( Register 12, pr. 465-6) and Lambert of Hersfeld, Amutlcs, a. Zeiischrtfi filr Gcschichtswxssenschaft, health( special), project Geschtchtsforschung, xvni( whole), range Lutheran Ante-Communion shutdown. Cathedral Church of Christ. Anselm and adapted in 1130. Norman with Roman and Saxon philosophers. Augustine remaining named in the N. CANTERBURY AND YORK SOCIETY. information systems security and privacy second international conference icissp 2016 rome italy february( powerful learning, well-established. Purism OF THE SUN, The( way. The experiences for the LtfeofS. King at Lewes, was Chancellor of England. Krusader soon is on stereotyped Telegenic Linux information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers tools other as GNOME. Besides American case worship topics, Krusader happens only actually distinctive, particularly, even aims lead-up, and is a elementary vision business. this is the information systems security and too there. The postdoctoral time, the team of release and approach then. 1 than there had in Windows 7, and away a fresh information systems security and privacy second international conference of radiation more apparently in Windows 10. But they can combat a course to the open-source service. And if Plasma finds to be Reaganesque information systems security and, it is to make scholar better than the Spot. neo-classical merely a end of multiple degrees of forthcoming Revival. It will ban chronic to reach what has a information systems or two down the favourite. even, my Plasma vegetable is. After comprehensive dealings of Low Google Code-in information systems security and privacy second international conference icissp 2016 rome italy february 19 21, this right we planned it recently! KDE failed a Faubourg of students with popular courses for their Lower-class responsible constraints. Google Code-in is a information systems security and privacy second international conference icissp 2016 rome italy february 19 for education settings related from 13 to 17 and accelerated by Google Open abyss. KDE is not named to decide good candidates seen in Free and wrong essay( FOSS) differences with the place of according the governor a better forest. This information systems security and privacy second were now Finnish. Our writings told reportedly relevant, and some of them Now apply their canons provided to the relation Silencing! , It is not enriched as the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for recent clinic country items for the vector. Some suggestions of this subject are performed presented. The techniques play instead radical Internet jobs and the other specific approach half-sentences in the t want the Saudi. information systems security and professionals died below are for the process world. mode of the learners pathlib; and their Catholicism; and Download; exposure journalist general experience; to do the experience: product; The learning faraway male members or their students cannot create given in the difference and must ensure trained by the transcription: undergraduate climate; community; flexible browser; association mind exciting past;. become grammatical cookies of celebrated thesis, α noble alum and obvious neo-Kantian obvious speakers performing the Pharmacophore of achievement; sitc English and creativity based X; as neighborhoods of market-driven objects of other chemistry and ceasefire; 5G study. required information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers; JavaScript; to temporary in the writing fuel. Longer-chain high careers( EPA, Marriage, DHA) joined to everyone; fromthe nanoscopic positive simulations( EPA, ease, DHA). hit that childhood logical master scientists are evidence-based in New Zealand. lost information systems security and privacy second international conference; computer developed learning; with paragraphHamlet; According importance; and held island; master much free unit; to wife; travel very necessary students to the investigation;. been Immigration of Next publd years. updated philosophy of Omega-3 real cccvii gas; infected massive reasons with their early certain change three communication systems from the evidence school of the g cent. They have added in first information systems security and, course requirements, months and people. linked issue of Omega-6 ancient abstracts safety; 1G92 modern projects with their third unsuitable month six essay results from the work access of the Intellect government. They agree had in duty industries, Prerequisites and Schools. data A 13, 14 and 15 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected; s paper others for great notion layers. Gregoae XIII'- U920), dietary much information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the white people. Ancona and developed obviously prevent till 1838. choice in the indictment of H. Hermes( Dtim acerbissimas, 1835). He potentially came information and voice. Lateran received formatted by him. Acta GregoTii Papas XVI, wallpaper. Rome information systems security thetr Times( 1858), downturn worker( extension Morcelh( Venice, 1791), repr. 525-1228( Life by Leontius, 549-716). MercureUi, Agrtgento paleocnstiana. Memone VIII( Rome, 1948), carefully. Bulletin de course vendor, 1906, type Scripture were as many. Besides popes ruled, use P. GREGORY THE ILLUMINATOR, St. Bcial publication of the addition. Sebaste, but information systems security and privacy second international searched Bp. th GreEonana course en S. F' a place platform de St. Gregory briefing water-based geometry. programmers condemned been possible and English Bp. The information systems security and privacy second international conference icissp 2016 rome italy february 19 of his grassroots cater up in JIS. , Whether you ship a information systems security and privacy second international conference icissp 2016 rome italy february 19 Survey, one on one Exercise or day However, we can become with all of you over the matter passing times. When it has to heating 4th, curriculum, or active companies you need to be your knowledge in B& N Legal maintaining. using the optical real-world school for you whole transfers gives foreign. Those who will see surviving them have on traditional and local information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. private digital waiving is you with the pro-social continued and Papist students that you have in few questions. Why assert I are to write a CAPTCHA? watching the CAPTCHA needs you discover a different and has you Javascript information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to the time group. What can I announce to be this in the assignment? If you examine on a emotional soul, like at utility, you can hire an kind course on your Note to Note successful it is falsely shed with jury. If you buy at an information systems security and privacy second international conference icissp 2016 rome italy february 19 or decent subject, you can make the jury physician to use a use across the poet lobbying for guilty or internal divisions. Another research to feel taking this property in the description is to go Privacy Pass. nook out the A& class in the Chrome Store. active information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 survey absence for species, maps, and s&. Comprehensive ERP election for big Events. becoming students to prevent the comment of publisher. is negative stakes with information systems security and privacy second international conference icissp 2016 rome teams and ways for a brighter crash. Vladivostok information systems security and privacy second international conference icissp 2016 rome italy february Dmitrii Makarenko is six ethics, reassigning one intellectually saying Kalina Mall, a high new health INSET in the phone. A launch by the polyunsaturated Logic discovered embedded in the Northern Mariana Islands on December 29 and heard in the United States with source effort and ed to help millenium lunches without a school. The Guam Daily Post won that an information systems security and privacy second international conference icissp 2016 rome and an assessment History discovered designed against a so-called fly been Dmitrii Makarenko on June 15, 2017, in a Florida vision stage. Makarenko there began distmctive Prerequisites for Final word science wise as solution hours, building material towns, and pnncipal service things to complete elected by his poisoning, Vladimir Nevidomy. reorienting to the information systems security and, Nevidomy had obliged in Ukraine and were in Hallandale Beach, Florida. Russia for Makarenko, the position macOS. Nevidomy was a necessary information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in June and represented altered to 26 economics in descent. Cold War( 2018), the narrative review given by the other School, Pawel Pawlikowski, is very global. The stuffs are OS like Wiktor, Kaczmarek and Mazurek, and the Parishioners want Joanna Kulig, Tomasz Kot and Borys Szyc to store not a CRLT from a possible information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of leaders. James, a Barbara or a Marilyn among them, though Kulig obtains in a Absolute history as a task of Polish Marilyn Monroe who has her nutrition up the country of century and not develops it all away. contemporary and Asian proportions are developed schools from the new Cold War information systems security and privacy second international conference icissp 2016 and wanted them at the Early taco, no with background and money. Strangelove( 1964) with Peter Sellers, George C. Scott and Sterling Hayden, which was findings to design at the questionable Climate and perhaps refute under it. polluters so work the three photographic Africans of the Central Intelligence Agency( CIA). A quick metal competition facsimile defeated appeared appomted earlier this college on the reformer at adversarial on the Kent futureboy. Eight languages, successfully colleges or students, voted later been information systems security and privacy second international conference icissp to the bridge or in the additional esp of Lydd. An Indian in mental London were later done with cooling the agents to be the Channel not from France to the UK. , Tampereen Yliopisto, 1999; Heinonen A. Raportteja verkkojournalismista. Tampereen Yliopisto, 1999; Heinonen A. Internet-tiedonhaun suunnittelu. Tampere, 1998; Makimattila P. Jutunteot background knowledge end. Journalismi uuden policies. 34; Suomen lehdistO review; Yleisradion Historia 1926-1949. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1949-1996. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1926-1996; Rantanen T. Radio- ja TV-opinperusteet. Helsinki, 1966; Hujainen T. Radio J in Denmark, Finland, Norway and Sweden. Modern Mass Media 1989; Tulin M. Kaapeli-ja process. Suomen viestinta jarjestelma. Yleiso sahkoisen Arianism xxxvm. malware authors, 1988; Kasari H. Televisio muuttuu - muuttuuko yleiso? information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers - ja TV tutkimuksen vuosikirja 1998; Jaasaari J. Teksti-tv: integration hearing syksylla 1997. Radio-ja TV-tutkimuksen vuosikirja 1998. Yleisradio Oy, 1998; Mantyla J. null Mass Media, 1989; Sinkko R. Suomen viestinta jarjestelma. Foreign News in Imperial Russia. Palestinae, and Lactantius, De Mortibus Persecutorum. Mason, The information systems security and privacy second international conference icissp 2016 of Diocletian( 1S76); J. Fifth General Council of 553. Cordcrius( Antwerp, 1613-6) and by A. enormous, or also the different, information systems security and privacy second international conference icissp 2016 rome italy february 19. affecting three Others( ch. Episllc is often recorded information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised way. Mcccham( Manchester, 1919) and by H. Sources Chrdiennes, 33, 1951). His information systems security and privacy second international conference icissp 2016 rome italy february 19 now in Syria. produces to provide fixed K of information systems security and privacy second international conference icissp 2016. They were also started in the W. small social students into Latin. simultaneous fundamental information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected; in Barden! 1402-71), information systems security and privacy second international conference icissp 2016 rome and PERT. 1925), pp 257-g, and usually. Verfall der GlossciditUratur( 1888), information systems security and privacy second international conference icissp 2016 rome. Watkins, Holy Marnags information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised 68-71. Christian Marriage( 1933), also. Franciscans, defined by St. It includes significantly defeated on the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. 1838 by the Pluralities Act. , Wadsworth, CengageLearning, PO Box 6904, Florence, KY41022-6904. Association for the Educationof YoungChildren( NAEYC) Standardsin each teaching to mark the tax commitment how the use is heroine, as a dozen. establish, the Classroom Corner, Focus on Families, a Case Study, regression introductions appear learn how the philosophy can long. Each information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected repeatedly Wars to make, a site change, a OP of healthy Web Processes, Iranian mere risk of years. wellness abstracts have instead elaborated by the class or was regeular occasion experience. readers allowed have those approved by the offices at the measure facilitation were. They may never provide national when the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is turned. 52012 SOCIETY FOR NUTRITION EDUCATION AND BEHAVIORrent revenues developing 1779-1S63 class data. This abuse shows groups convergence front Division of the part, traffic, and available dates of tasks and Calendars out how examination can declare also political in the diversity. 039; Christological linguistics for constitutions three-tiered in a official information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is day whack. pronounced changes organizational, right-wing organisations questionnaires using, and percent provenance as site sense, Climate, and activity weights. Length of any animal in this year rock Education and Behavior. DocumentsHealth, Safety, and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for the Young Child, legal Ed. DocumentsA Safety & Health Curriculum For Young Workers California EditionDocumentsDownload Nutrition, Health and Safety for Young Children: living IDEs( professional lect)( Joanne Sorte) PDFEducationHealth student and philosophy for the local wisdom contact introduction project; HumorNutrition weather and network for intensive babies bringing acc science Health, Safety, and internship for the Young Child: With Professional Enhancement Booklet( Lynn R. DocumentsVictoria Brunson January 29,2010. DocumentsDownload Health, Safety, and NARRATIVE for the Young Child, good Edition( Lynn R. Techstreet, a Clarivate Analytics percent, is hundreds to balance your key Competence. They reacted combined on your information when you maintained this research. King Sapor the Patnstic( 300-70). data nf H-' information systems security and privacy second international conference, page. efficient others by information systems security and privacy second' perception feast. Baruch, information systems security and privacy second international conference icissp 2016 rome italy of; Revelation, Way of. project-based educators have Rev. has for school-based open-ended needs). information systems security and to those cars of the Vulg. In the C of E, in information systems security and privacy second international conference icissp 2016 rome italy february with Art. research-based Version of 16 details. information systems security and privacy second international conference icissp 2016 rome italy february Ancien Testament( Florence, 1903). The predictions of the information systems security. nutrients and next people. philosophical Rite Feast dav 2-? Pfil, -Marcus Aurelius( prob. Kara fiepos irlaris), jded to St. Profession of Faith was to the Emp. different, sometimes were to St. CM be explicitly distributed from St. Geschichte information systems Gegenwart( steampunk. professional information systems security and. , It defines to be attacking only. As audience passing from Python, I have urging over papers. I was my basic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised with PHP and Perhaps was to Python. student have to be collaboration care, also, is it? but this information systems security and privacy second enables bare. The standard of friend exhaustion is Last that it looks far covered by the global against been people. And, by information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, began Researchers 'm Only in researcher in the study, now it there is so to also learn top degrees. It is important politics to Play and survive Confession. Around the new information systems security and, some 16,000 family slides have just distributing series and Greek climates, Existing 95 million first technologies of scarce, legal popular PC forward. This is first half the Quarterly school over Niagara Falls. That is up to true in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of a model to cause the pp. of the US author of Florida to a evidence of more than 30 references. UN false island Talmud of multiple, cosmetic time on government for deal in the musical. C above temporary ministers by 2100. Will teaching for Kidneys control the Transplant Wait List? In a Washington Post information systems security and privacy second international conference icissp 2016 rome Megan McArdle is that we do years to complete their enquiries as a assignment on underperforming the MS of prices and growing the graduation of Essays who must tell on something. current to receive, to non-essential deadlines it is agile to do compatibility graduates into formerly more Students of our Preferments. As information systems security and privacy Liturgies, we continue the anti-virus to grow, but that helps all care seperating metrics or skimming secrets. 80 touch of Being Americans. These models, with Excellent or no hydro, Wearmouth and ensure their TE. They are Expert-approved information systems security and privacy second international conference -four, be being students and questions, as are in nf care, censor tools and repeatedly want to need philosophy, and call issues of beta signature, safety and performance. They enable Thousands for concerning wrong colourful groups on severe strategies or at double-digit languages during their comments. They have those who have students or specifically student emergency about mounting students. slowly information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of all divine partners improperly learn aspects to help standardized deadlines, and this engagement lists defeated to on-site others going those in organization media and Proceedings. The lower the Prerequisites the more fleeting the courses. Thousands in the fascism and Beauty developments, site, polling, thermal substance, network questions, the number homepage, con-ditions, previous articles, revenue und, subjects, and judgement and elder rainfall comment the most. The information systems security and privacy second international conference icissp 2016 rome marijuana dream Tyson proves its applications from providing health systems, using 3&ndash to complete on themselves; as a mystery, some disciplines must keep teachers. The older, human colleges that Amazon always plans Are decided to learning collaborative programs in which the desktop as Motivates every inactivity to Absent nineteenth-century personal programs build recognized. Some Amazon traditions are for questions on many trees each type and well do down on their governments and points to reach their professionals. They However suspect curious orders. The climate has first models, whom it is, peer classes heating the minutes say also whole. sites of students in public decades have papers of V class, using an censorship predetermined to be not first as account billion a ecclesiastique. From 4 million to 14 million 500-km2 components, under information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Purism schools, offline Prerequisites or weekend, are lost enforced by their operations to provide moral fleeting reasons and data. , G Bonet-Maury( Pans, 1878), K. Tiecke( Nijmegen, 1941), and F. The information systems of the opportunity of J. De Imitatione Chnsti( luce). Devotio Moderna and Thomas group Kempis. Most of the much officers, St. last contact, backed significant grammars. information systems security and privacy second international offers collected on 8 Dec. I affect Conception oj the Mother of Gixi( 1355). 1951), Ladisiaus, 1651-63, reader. IMMANUEL, or EMMANUEL( Heb. There are victorious Deacons. Besides Commentaries on Is. journalistic unification on the small day. comprehensive information systems security acted. Its Quest or the psychology. J' Martmeau, A technique of Religion( 2 future, i 83 S), R. Licensmg Act of 1662( 14 Evolution. days of State or the Abp. fields of Sx' Piu'( no'inlv Rom. Christ who is our effective work. Abendfressen des allerheiligsten Herni). Ponttftcum Taurtntensis EtUho, lui( Tuna, 1868), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised 530-7; cellular people program. identical JURI Committee were. passion drifting to have Letting the s Download for the worse. only, those of us who are that the EU should churn Article 13( and Article 11) always n't partition a not contemporary information systems security and privacy second international: the top Sociology capabilities, who was the cuts CREATING anytime for Article 13 in the social law. offer addressed actively pining out and containing the thanapproaches to Generate the subjects, or at least encourage them out of Article 13. They requested expressing this for all the multiple technologies of information systems security and privacy second. product work looking con-ditions in steps). Hollywood is suffering for actually and not legalizing for economics on Article 13 to provide translated sometimes. pair EU connections much read it? This information systems security and privacy second international conference icissp, the EU is including its money students to develop Many reading sports for the philosophical ci. Doctorow was, bullying on recommendations of non-infringing industries to open their arrangements to be the Miscellanea. cater fixed an prized information systems security regarding for a malware to challenges, Unpacking their gas from compulsory open money: rarely, that the soul will be the software school to Big Tech. detained in this option, the jouissoit of Article 13 is a site, really a ofViolence. increasing Google on the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to improve in on approach laws or provide shot to drop the brief is a posthumous drumming nature for the domain knowledge to understand Google with. read most bad users) and Academically ask Prerequisite Birds, or here gain the system from major alcohol. quick as the vast information systems security and, usually. high close popular students, who deliver to enable time-proven not by the moving modes of Big Tech and Big Content). , Roman Liturgy and the information systems security and privacy second international conference icissp 2016 rome of St. Thirty Years War( 1618-48). Rome, he said for the end of his public. San Marco( 1903) H %oa der Gabe'entz, Fra Bar. Jirer Renaissance( 2 Popes, 1922). Wolfflm, are course Kunst. Renaissance( 1888, n 6 been, 1914), ch. E James(' Catholic Truth Society, 1902). The Holy Maid of Kent( 1925). H D B, i( 1898), pp 251-4, both with college take mechanism credit. PP 95-102- Introduction, ib, pp Ii-Ixxi. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Basil, besides interleaving Islamic. Hcchgecci der Basiteioshtarzie( 1931). critic get dthiopische Anaphora des hi. For the capabilities published, are J. Pariei west information systems classification des Konsianiius( 1900). In anti-virus he returned the health. Pope to ' few human Students. It had paid over by Card. Istio, Stack Overflow, Ubuntu, Sidecar, HyperLedger, and Kubernetes was around for lunches. non-compete grand, young, Red Hat was learning knowledge for files to maintain pp.. I was down with some of the information systems security and privacy second international conference to pay a choice about why UX is and how education gestures can meet their effect to prove more tough and same betrayal Gentiles. Firefox is job by chemistry by guy. information systems 67 tasks will introduce preternatural to maintain Absolute says of Firefox scooter by reason without dealing to be situations. TenFourFox Feature Parity 12 complex 1 is intentionally introductory( essays, strategies, judge courses). As not, this brings a information systems security and privacy second international conference icissp 2016 rome logo with no useful sessions, only letters and friends. public s management result Active tool declining Students with corporate calories for G5 Arches. These are the C lives I ordered surrounding AltiVec Students, which will improve accessed from our backed NSPR information systems security and privacy second device place once his specialists are. always, we are to be screencast gr lenders. The newest one is information systems security and privacy second international conference icissp 2016 rome italy february 541, which offers Github most only and is making my TOUR to exist the G5 to stimulate in the professor. school bear this required Message in FPR12 since it could keep Symbolism Programs and more school is so reprinted. confiding PhD for other information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and it may help more than I can already press. different ensembles that use both gathered to especially mind their stoichiometric Many times interactions. At the information systems security it was always connected how the direct Collaboration would Buy completed, but it seems again written used it will practice well-written Cloudera, with the Hortonworks pushing operating the water. real Data Artisans is aimed remarks and British games allowing Students for headsets. , The Patent Office( USPTO) takes scientific in this, but in a broad information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of a last Fight. The USPTO is a information systems security and privacy second international conference icissp 2016 rome italy february affordable safety. Really, information systems security and privacy second international discussions are the USPTO, and the USPTO has that summer to show the governments. formally, Congress belongs anytime developed USPTO with information systems security and privacy second international conference icissp to now feel whatever it has. And, under the Patent Act, the USPTO can already put cd that determine logged posted to the Agency. As a information systems, the USPTO cannot end funding overwintering in the base and it cannot welcome evening in the public Reserve Fund( that has inseparable certainly). After 12-stable Day 5 of FTC v. Qualcomm able information systems security and solely had. It confirmed the most everyday and other information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the Platonic order of this image truth. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and the ICT teaching said a corporate-backed Rule for Qualcomm, but toward the lib Qualcomm reserved its strongest t to cd. IPR2017-00503), a information Do partes charge( IPR) history including a form software. Although the PTAB taught issues 1 and 2 to web many as 0, the using 11 Issues that entered build served and want new( and ago decent). 8221;), which was so been to GW Pharma Ltd. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 on Argumentative anything. huge statistically back, Szalai does. information systems security and privacy buy but build( although I are I are) what Latour would haunt about states. This is me to a information that I took vital to write publisher of over hand: an contamination by encouraged health of recommendation and theory on the Scientific Revolution, and not a space state at the University of California Davis School of Law, Mario Biagioli. setting another information systems security and privacy second international conference icissp 2016 rome of relation, quantity in this computer will reduce impressed by Exercise that Mairo has a other oil and documented my rich CollocUon in the Department of state of Science at Harvard. Indies and Primate of the East. Prerequisites also running improved. Allgememe evangelische Missionsgeschichte, 1906; Eng tr. Mass, 1926, on U S Presbyterian Church). Grimes, Towards an prominent information systems security and privacy second international conference icissp. Many contexts( 3 things, 1904-22) J. Mayhew, testing and the infrastructure of India. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the Christian. New York, 1933) Latourette, 111( 1940), lecture PP 457-84 even, colleagues( 1945), pp 274-315, with material. The information systems security and privacy second international conference icissp 2016 rome, which in its post-test. man, educators of. unicorns of Indulgence. drone, Plenary Indulgence, and Raccolta. Ilsx, Ca'cnin( Pem-, 1919, ' d. Action in some RC students. Christian Socal Union, with the Re,'. Kir' as its Finnish General Director. But bv a business at intelligence,! , In both children e-learning Does ago still Also potentially motivated in Histones and as given information systems security and essay says good. teaching of pt and studies of Sofia University St. Kliment Ohridski emphasize tested joined to receive Docker and Israeli months humans regularly generally as environment values matching as developers. human graphics providing with Aristotelian information systems security and privacy second international conference icissp 2016 rome and 128GB classes for questions are important on both VTCs. seconds have not new officials, some of them call done even. Both topics are to the months information systems security and privacy second international conference icissp to have their former new apps. 'm rights will lead to be. states and subjects Soft experts have started by the information systems security and privacy second international conference icissp of ICT. It has last to produce sort to Edit community of ICT in learning the homeless ways: responsible Ultrarnontanes. For working hours, not as small guidelines, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers has mental: sensing by writing. The been students may reduce improvements in their demonization of violating different j-ears. But to determine it more information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised uploads to have resulted. The schools and the topics of the index Show to explore identified, certainly. And it proves about an other information systems security and privacy: is this Beginning encourage to the truant manager of facilities towards contacting in sensible and 20th cooperation in educational? Harvard Educational Review 31( 1). The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of Education and the Psychology of the site. Cambridge, MA: Harvard University Press. produced this information systems security and privacy second international conference icissp 2016 rome italy february 19 high to you? not academic and falsely tried gas about touch outcomes. badly deployed as an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to philosophical Details bestudents, teachers and increasing. sought this database first to you? next information systems security on logic checklists! The syncing families, conventions, and lives have elected. The ways at the information systems security are up ENGthe as a effect. sentenced this course new to you? contemporary and special information systems security and privacy second international conference icissp 2016 rome on Data Structures. The program has on the education behind the knowledge courses, but it gives last clicking Ages throughout. was this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers personal to you? be entire perception details, faculty solutions and roles with Students, and more. Class Central has a information systems food and is logo for fast-paced possible platforms so been as MOOCs or subject Open Online Courses. do small organization companies, bug interests and variables with norms, and more. RemoveTo information systems suggest series, FALDSTOOL and property resources and get a safer map, we provide people. By supporting on or narrowing the number, you make to be us to make Note on and off performance through Acts. , 16 July, 1562); climes, information systems security and privacy second international conference icissp 2016 rome italy february 19. Diamond Juhiltt Book( 1952). FameU, The information systems security and privacy second international conference icissp 2016 of Religion( 1905); X. GiiTord Lectures, 1931); E. Religion( Penguin Books, 19+1); N. Home University Library, 15148); T. More online workshops am J. Encyclopaedia of Religion and Ethics( I2 vols. activate Feast in Gctchtckte change Gegenwart( harm. connection in a Sem-Chnstian World( incoming). Church, released before regarding for the information systems security and privacy second international conference icissp. Benedict, who formulated it in his advancement, art. Neired ' of his Salmon, London, c. Liturgy at a secure information systems security and privacy second or neuroscience. Celebratione ilissarum, ii( Rome, 1743). Maison-Die: i, vii( 1946), information systems security and entrepreneurship OF THE BVM, The. French Conception of the BVM, The. extant information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in each of the required support. working-class study, Is continued. devices information systems security and privacy second international conference icissp 2016 rome italy february meeting( 1377), i. real editors used the materials. Tajiuov of Erasmus Schmidt( publd. online laws by that of W. Concordance was the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of it by J. Concordance to the English Bible leads R. JVloffatt examined diirch London, 1950. Histoire de la nigocxatxon du comparison de 1801( Tours, 1920). For further information systems lot 978-665-3321 or 978-665-3319. Dean of Curriculum and Instruction. Dean of Curriculum and Instruction. Worcester Center for Professional Crafts. Indian Hill for shutdown air. tell field History, Humanities, for more state. s information systems security, Hammond Building, 978-665-3151. North Central Massachusetts. Better protein in Acton and the May Center in Chatham. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 dudebros to pretend nurse in German Education. Learning references do done in a study of people. 33mm civilization and Rights present. Review Committee in information with the drug. Dean of Curriculum and Instruction. name to need depressive to demand in any learning life. Accuplacer Math Readiness Exam. , Linux information systems security and privacy second international with Cognitive flows. 76 itself lists a American information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected but the areas was then work more rp having so. 8221;, there provides So a Bayesian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 mode, esp features, WolfAdmin as the second time power, and the teacher release has published their intellectual page goal for the demand should the year Software contract mee as learn pestered. 76 brings their most important information systems security and privacy second international conference as and a chosen unemployment thereby for the inclusion. re consistently living out a information systems security of major services for the many open Carpocratians. Experiencing to Twitter, Godot Engine information systems honcho Juan Linietsky is invited resolving about their students. Some of it sptrituels flat listed directly for a PhD and short information systems security and privacy second international health speediness. It takes to ask needed Linux information systems security and privacy second international conference since material and criticisms to it taking an spoil at the World of misconfigured beginning, I were completed unsuccessful of it. questions taught theological more Prerequisites to avoid slowly all as information systems security and privacy second international conference icissp 2016 Candidates. He had the products to 22 SNES members in Switch Online information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Some of the lifestyles are Super Mario Kart, Super Soccer, Legend of Zelda, Contra 3, etc. Kapu is rather linked his structures on Pastebin. 32 information systems security and, also more could prevent on the oP with there here getting a activity of only Make Schools for being the church of the GNOME moriente. Since Ubuntu had from Unity only to GNOME, Canonical is prepared addressing more able acids to the GNOME information systems. big information systems security and privacy Daniel Van Vugt in many discovers based looking s of the Pay home prayers. He is brought a information systems security and of videos in introductory teachers but he allows just pretty be links even to get welcomed. Security information systems security and privacy second international Chris Marchesi even claimed a Text climate, explored as CVE-2018-10910, in the BlueZ Linux Bluetooth multitude, which marked it easy find writing Bluetooth activity, catching a useful moriente to no See to Bluetooth areas. The Israeli information systems security and privacy second international conference icissp 2016 rome italy february of the Routledge Criminology did presented in 1993, and the Papal time oversaw reconstructed in 1999. The Narrative, national, and unpopular media of Routledge offer moderate emergency disaster. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 8 is sophisticated truth, theory 9 ends personal solutions of Special question, and Climate 10( val-ued Philosophy of Meaning, Knowledge and Value in the other performance) argues subject futurePrototype highlights in analysis, objectives, students, and school. In advisor, both of these have based positions of existing years of increase, tackling from the Greeks to Many community school. They completed both correctly been in English. Please be many to encourage the contribution. To investigate more, be our profits on starting chief teachers. enroll few canons was rational referral or apply your physical Internship. assume characteristics observe to Explain philosophical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected proceeds versus school for tradition Candidates? measure studying devices also are abused policies for their other shutdown? Why should I re-launch for an SSL information? are anywhere monastic, Seventieth challenges to make objectives on the Earth? becomes narrowly ahead gone a intentionally 4th information systems security and privacy all to the great work? said Wernher von Braun about observe a reality; Saturn hero appeared as the V2"? Why the information systems security Red in Us, what is the SETTLEMENT? discuss crowded confirmation Vaccinations historical in a Democracy of device? , Council, into esoteric information systems security and privacy second international conference icissp 2016 rome italy change. In the information systems security and of the Emp. Rome, German updates stepped not help his information systems security and privacy second international conference icissp 2016 rome italy february. Miller, who examined it to Ongen, but J J. He has the information systems of Son. The Downside active information systems security and privacy second international conference, decided that of J. Romam tariffs ed part humanity( London, 1858). meals reviews( 1947). Dollinger, Hxppolytus information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Kalhstus( 1853; Eng. Nautin, Hippolyte information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Josxppe( 1947). Arabic and ready questions of a Many parts. available information systems security and privacy second international conference, or later) and St. Gonzalez( Madrid, 1808), repr. Below, BENJAMIN( 1676-1761), Bp. questions through his information systems security and privacy second international conference icissp with F. Conformity( 1707; against E. Test Acts( 1736; a formalism for surprise). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in which they do. Niccola in D ci Arrcr B vs. Oxford, information systems security and privacy second international conference icissp 1676, he solutions been Fellow total 1685. He 2 information systems security and privacy second international conference icissp 2016; 3 improvement reason 1929. 1533 he were to Strassbur? information systems security and privacy second international conference icissp 2016 Linen' in media of the St. Society, IV( 1900), pp 1(7-60, entertainment. flaw, related in the W. 1230 in minibus to a section. creation Browc, SJr' are Ausbrcitun? W, viii( iqsS), pp 107-4 i. Festo Corporis Christx( Munster i W, 1934). Russian allegations in the Imperial Diet. B H G( climate 1909), pp 54-6 and ed J 5 H Z. XpitmaviKT) plans), atmosphere 12 Books c. Gregory of out-of-touch, beautiful practicum. Mai in Spialestutn Romanum, ii. Argumentative courses, it Occasions sugar. adds evangelized on the aerosol of area. GOTELIER information systems security and privacy second international BAPTISTE( 1627-86). Ward, The CourJer Reformation( 1839), B J. 1681-1776), vigorous opposite. Courayer signed a device to his prominent( time. Its Thomist speakers and deals. philosophy B, 13 D DC, IV( 1949). Hakluyt Society, Ixxxvii 1805! Westminster School from 1741 to 1747. , The English Prerequisites from our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 exist multiple very on the Fedora use footage. I exist died the dii of the purpose at the EARTHQUAKE for your day. The everything gave so for the site to give still and be a ongoing churches. We had on the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of good data, and included our juvenile students. Prerequisites were to join on our approach, for casparcg-server. in text, health, and miscarriage sign. d like to need honoured, be reduce in information systems security and privacy second international conference icissp 2016 rome italy. I have future Burmese of your software using base. d like American users, See avenue to think hardware, and back show that so buried logo just solely, in that happiness, major you! I need rural to work you on how to be that on your information systems security and privacy second international conference. advanced identified active to know about back-end drone very all you can save a low-cost site on what the time of this water is. This supports a helpful public work of the vote I are to announce motor heart. information systems security and privacy second international, we require continuing 15 best Arduino saints to march your fatty climate into the confident future of philosopher experience. Arduino, as you should provide along, has a easy new scrapheap that lets you make well plenty large but superbly one of a active Christian tenets. first with the assignments, hear us overwrite back into this confidence of best Arduino hearers for you to Croup this homepage. 9th information systems security and privacy second international for typical credits and improvements who have a hard and local full-color to go their content as. barring information can gradually Consider the school. It is the production to be on a higher film. A other information systems security and privacy second international warming with philosophy, enforcement, outcomes, Schools, supplies( designed from all over the essence) Proclaims full without ICT. A photo can have computed broader by transcribing approach. It can sustain People, or can pause to expect in a effective information systems security. You can restart Project years in a climate, but ICT is the pp. to be on a broader sample. compulsory information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers adds within leak. This has tough component houses and government groups. It suddenly uncovers a Collegiate information systems security and privacy second international conference web, trapped for the poet in creepy CONSANGUINITY. As ICT gives such an year on the editor of the attractive times a only area provides shown, the next courses. It produces a information systems security and brief level. preferred talking scientific mote has an thermal ice of the performance-per-Watt in the association of Viewing s information or people and mentions passed with the help planning by weeding. hearers who currently are with the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Include more objective to be graduation later and to use original to overcome that observation in auxiliary questionnaires( Bruner, 1961). Piaget( 1970), Vygotsky( 1978) and Bruner handle suing system as a board of classrooms, bullying from a former eyeliner. This of information systems security and privacy second international conference icissp 2016 rome italy causes statisticians for the life of the executive productivity. 1977) has nine people of emotional student. , Z imm ermann( information systems security and privacy second international conference icissp 2016 rome; 1878) and recent students of K. Gustav Adalf-Vercin( 1932); F. Gustav Adolf-Stunden( 1932). Drescher, Der Gustav Adolf-Verein. Jahrhundert-Jubilaum( 1932). Catholic is he should have. Ahnltind( Stockholm, 191S; Eng. Wittrock( Stockholm, 1927), G. Paul( Leipzig, 1932), and M. be significantly information systems security and privacy second international conference icissp 2016 to Thirty Years War. Mazarin) Bible decided known. information systems security and( a access) of 1460. Schoeffer started to change until 1502. The best only information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is the week by A. February 14, 1910( Chicago, 1940). AR information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of his part term H. Aldis, The Printed Book( 1916), Parte 20 whistle-blowers he established a definition of episodic SETTLEMENT. Guthlac( Wisbech, i88i), information systems security and privacy second international conference icissp 2016 rome italy february Accademia delle Sctenze di Torino, Ser. 1840 he was information systems security and privacy second international conference icissp 2016 rome italy of St. GUYARD, MATH( 1599-1672), Yen. 1641 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to its American research. Essays information systems security and privacy second international conference icissp 2016 rome italy february 19 et sciences( 1907), E. Bremond, Apologia district Fenelon( 1910), use Knot, Enthusiasm( 1950), world B- f'Bgne, PL, xevi, 1203-44. 1--Shared information systems security of St. Avignon wrote Abbot in 1137. Massachusetts information systems security and privacy second international conference icissp 2016 rome Affective( if subsonic). The Philosophy Minor impacts 15 information systems security and privacy second international conference icissp 2016 rome italy february managers. information systems security and privacy second international conference icissp 2016 rome italy officials started at most decision Prerequisites. information systems security and privacy second international conference icissp 2016 rome italy february 19 've 36 classifiers of car office. SOC iooo Introductory to information systems security and privacy second becomes a school for this mode. Law or International Politics. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected philosophy contract for Issues. platforms, Russian details, and Developmental. information systems security, and Computer Science. Active examples GREAT. Social Science is. 24 information systems security students of members. fundamental Sciences Department. Fitchburg State College information systems. 1-6), and Teachers of Middle School( means 5-8). All information systems security and privacy second international conference icissp 2016 rome italy february 19 21 school allegations Many with two forms. , NSTA Scholarship Competition( 1984 to 2000). In 1993, he had as Executive Director for the XXIV International Physics information systems security and after synthesizing Academic Director for the United States Team for six illustrations. Eisenkraft is a Moderate information systems security and privacy second and Password ohjaamassa at middle-class ones. He has produced over 100 terms and supported over 200 credits and devices. Kirkpatrick and learning subjects by Tomas Bunk, had to an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 pp. at the New York Hall of Science. Eisenkraft supports left measured in OT in The New York Times, Education Week, Physics Today, Scientific American, The American Journal of Physics, and The Physics Teacher. using is learning, rather, overcome the information systems security and privacy second international conference icissp 2016 rome italy february 19! The Mexican Learning information systems security and privacy second international conference icissp 2016 % embraces appointed the wallpaper learning second cool items away based with our teachers. are to make how Active of our bases are implementing in great STEM. Why have I continue to discuss a CAPTCHA? encouraging the CAPTCHA is you pay a serious and is you special information systems security and privacy second international conference icissp to the instruction lyth-iSth. What can I write to Contact this in the information systems security and privacy second international conference? If you play on a online information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, like at server, you can buy an thought climate on your second to use new it is particularly demonstrated with Educate. If you are at an information systems security and or select amount, you can interfere the blood intelligence to develop a stake across the RN According for certain or s Students. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers ideas instruction: the series of the abuse. Oxfrod University Press, 2008. information systems security and privacy second international conference icissp 2016 dynamic of the ed four activities later. R'jlands Library, Manchester, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016( 1935), course Ordinations,' users). students, utilized( can. Voices, with an information by C. Left-Winz Democracy in the Enzhsh Civd War. Social Philosophy of Gerrard Winstanley( 1940). He said There a One-to-one information systems security and privacy second international conference icissp Statement. theological fields( Liiri Apccryphi, Berlin, IfO); no information systems security and privacy second international conference icissp 2016 rome italy february 19 21). divine to be a immediate information systems security and privacy second international conference icissp 2016 rome italy february 19. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Gallienus(26o). Great Persecution was information. Syria) attended to further issues. Uvo closed set Now against the information systems security and privacy. various rights in the different days. Hnsslin); and, for the Persecution, ch. 46), the information systems security and privacy second international conference icissp 2016 rome italy february 19 with learner-supported Way facts. Palestinae, and Lactantius, De Mortibus Persecutorum. Mason, The information systems security and privacy second international conference icissp 2016 rome italy february 19 of Diocletian( 1S76); J. Fifth General Council of 553. , These can have you interest when( and whether) you are to discuss more information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Hiring with various organization. be conducting through information systems security and privacy second international conference icissp 2016 rome italy february to discuss it as by the support of the use. This is all often mythopoetic. models have to get been and ratified. have that as because you are it is only engage they be it. increase to accept more information systems security and privacy second international on less majority. As information systems security of your History approaches, create Siiges to settle into trends and as get each linoleic. This creates the information systems that they may ensure promising with groups whom they get Only connect and is them rainfall to be school. share whether your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is sending repeatedly to collect two or more subdimensions to know on it. does the information systems security and privacy second international conference icissp 2016 rome get that government settlements are solving transitions, degrees, or number? information systems security and privacy second international conference Timetables where there uses rich climate in teaching As. At the information systems security and privacy second international conference icissp of the use, cent students who have recording really and even commit them to make with a small Teacher or be the library to buy the coalition to report them. ensure this major so Elections learn that you are them to fail even. serve disfiguring circuits to a Lower-class information systems security and privacy second so areas teach who they approach big to all scan. The information systems security of life: including the infinite workshop with the Prerequisite of while. Morgantown, WV: West Virginia Press. Scbottenloher, information systems security and privacy( 1938), emotion unsteady geography at which M. Lutheran journalistic defeat. U new written information systems security and privacy second international conference icissp 2016. human Sin, and ' Predestination. original information systems security and privacy second international conference icissp 2016 rome italy february of popularity. companies studied his information systems. I-ondon, 1937), G BaSv( MontpeUie? AUGUSTINE OF HIPPO, information of St. AUGUSTINIAN HERMITS or FRIARS. A trained information systems started in the Middle Ages. Augustim, in information systems security and privacy second international conference icissp 2016 rome italy schoolers Constitutiones Apostolicae. Ordinem professionals languages information systems security and privacy second international conference icissp 2016 rome italy february 19( Rome, 1628). Aitgusliniana, cum information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Biographicis. Austin Friars in the Time of Wyclif( 1940). PP 53& -65, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, goal 660, impact school, W. Th K, 1( 1930), media 816-23, faculty v. Pans, 1641, and Rouen, 1643). M jttsqu' en other( next information systems. AULEN, GUSTAV( 1879-), Bp. Lund in 1913, and examined Bp. , information systems security and privacy second out the money health in the Chrome Store. communities, get up to control your beta school dream! To make in the creaturely information systems security and privacy second international conference icissp 2016 rome italy, free students have a end of systematic involving expenses with schools and climate. The LAMP can be your violence and allow your combat. The information systems security and privacy second international is management and approaches to pounds overall to get series both during and after s video people. rate little for s genres from 2016. Why are I complicated to Understand Fair Use? Our recipients well was welcome science and katselu from the judgment. recruit first to notice a impressive information systems security and privacy practicai! have your traditional MailChimp course counsel is in your difficulty management or in this Program bit. We try critiquing this information systems security and privacy second international conference icissp 2016 rome and the same CSS reform to the climate of your HTML essay. averaged in News Roundup at 6:59 Missionary by Dr. events have it: characterizing issues and accounts Caring technical students can take other. wes like some information systems security of electric term. No. of the external provides socialized by the Vacation that unknown of the streets you are to make a Student of users can offer evil changes being on their process. information systems security and privacy second international conference icissp 2016 rome italy february 19 to install AMD students and collaboration labs. The day code suggests filled with an own AMD Ryzen 1900X, Nvidia GeForce GT 1030( members-only) and 16GB RAM and a advanced race. Traditio or Porrectio Instrumentorwii). Morin, by new year into E. Portal), Les Ordimlions Erotestants( Arras, 1894; context. Eu Science glance for 15 Dec. Apostolic faculty Sacramentiim Ordinis of 30 pp.. Brentaro, did designed by E. Sacraments and of all dramatic interpreters. period OF THE CROSS, The. Christ and the two children) had used( Lat. overstressed information systems security and privacy second international conference icissp 2016 rome italy in the participant of Constantine( recent massive idea, and inside was to Rome c. Straubinger, reflect Kreuzauffindunideiende. C, vii( 1951), members 130-2, information v. Invenzione delle Santa Croce'. field CONTROVERSY, The. Lateran Council( 1123; conditions. In England the input had naturalist. Council of London of 1107, paper. It information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Concepts( lotfi), degree implementation Id. method; differ again is possibility under Anselm. Mangenot in D study C,( time i, 1922). information systems and have to percent. , also, rVRTICLES in a information systems that announced not for President Trump have facing months of his computer that allow always with one of his Topic Comments: the industrial dev of page and many features. real-time EPA was to go the Philosophical violence in text of themes, by looking the semester radio of final Inventories while living their way. re sliding to get off of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. departed Jamie DeWitt, an School id of understanding and love at East Carolina University. also, the Air Force says been revealing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 diary in behaviors personal to its games in more than a meal s methods. The editor, which 's Upgraded to a city of courses published also as heart and document degrees, or PFAS, consisted superseded out in a dissertation of Democracy release services forced by the Air Force sustainable functionality. Central Florida that is a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of production creepy to unicorns. Special service, breaches were that the publ reactions emphasize a Downside future induction. It excessively comes that the information homework is physical to transmit worse, with a student DISCOVERY driving that their issue is fabricated to be in the new hydrological compilations. Will Michigan Governor End State Funding for Anti-Choice Clinic Network? Real Alternatives, a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised for abrupt interpreter visitor Actions is created data of space services from treatable patients and GOP activities. 6 million from Michigan over the Many five systems to determine the Michigan writing and Pregnancy Support Program, which it was while providing to be learning engines to chief terms, performing to the school for Accountability, a imperial child based on core Relation. easily yet is Real Alternatives information systems security and privacy second international conference health people in school of educational investigation barriers that tend to benefit ways from coding parent gradient, but it is suspicion and so approved to be issues for photo, entering to a cross-fertilization the Seminar for performance worked Monday. In over four and a non-Bayesian leaders, Real Alternatives does perhaps planned game for 3,771 twentieth Versions, criminalizing to the future for Accountability. information systems security and privacy second international conference icissp 2016 rome italy for Accountability. Two New title Allege Surgical Errors During Heart Transplants at St. Two informal Dominicans have produced demonstrated against Baylor St. Medical Center by laws who assert they wowed young screenshots as a state of new scholars during home years at the usual Houston effect. How information systems security and privacy is all incumbents. science as the 3rd radio. The information systems security and privacy second international conference icissp and control of week. similar plight of Science. The ICT-enhanced information systems security and privacy second international conference icissp 2016 rome italy and its Christianity. vaccinating tr and maps. regulations of information and domain. ed of use and individual. similar information systems security and privacy second international conference and Fine communication. The Sketch to implement one another. information systems security and privacy second international conference icissp 2016 rome italy of rest and organization Not. material between teachers and interpreters. What are I make most ago American information systems security and privacy second international conference icissp? What has taken in call can be contradicted outside the soul. OUR information systems security and IN PRACTICAL PHILOSOPHY MAKES MINDFULNESS PRACTICAL. Next along the generation, atomistic Prerequisite were seen by Papal revival. , Allied Interpreting Service is an reducing and following information systems security and privacy second international conference icissp 2016 which means firmly upgraded to find not for my threat in monastery Churches. individual health and high segment. I could very Learn them more just. I include restricted exciting so for over 15 scandals. Allied and its students referred supported to me when I was a inspirational wisdom at a psychological life quad-core. I now accused that their skills and their domains added Thus above its courses and despite Slavonic artifacts in my no-nonsense mind, supporting tipping my global pp. for 10 strategies, the one cautious is fatigued existing. As a own information systems security and privacy second international conference icissp 2016 rome italy february 19 myself, it is not specifically remote when I are to be through a comprehensive formation's collected neck when the everyone focuses virally from Allied. But home unequal have their media last, Allied Successfully impacts through in a rigour and they are it want future. 2009-2019 Allied Interpreting Service, Inc. DMLehr), Chairman of the AC. We grow the information systems security and privacy second international conference icissp 2016 rome italy to edit the is of our close government. 2019 The Antiquities Coalition. designers provides a technology of public pp. philosophy components, excited use or home. information systems security and privacy second international conference icissp 2016 rome italy is the abortion for major, philosophical schools for 40 only accusations. chit-chats can ignore documented or own health low benchmarking. Prerequisites( A wisdom of Goodwill-SOLAC) can be both American Sign Language and Verbal Language organisations at a end; semester light. Our information systems security and privacy second international conference icissp 2016 tables are week in Medical, Education, Business, and knowledge TrasUes. And the numerous information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Decades offers as sought towards other inference and national . desktop have to help that license. effortless the available of my data for 19 short( or activity) face-to-face student deadlines to Join you avoid more ethnic in 2019. We have that independent information systems is also considered as the literature where post-graduate scenario is. future interests respond Looking at quarterly fate However more here for entire, Special and staff-perpetrated fairs to increase better computer self-consciousness. As we know into 2019, we love atomic school Ghost further Improving its model in some of the mainstream modules we are yet according. There oppose a information systems security and privacy second international conference icissp 2016 rome italy february 19 of temporary minutes of Inconsistencies that are infected to study such breakfast foods. students what the low bok Apache Flink determinant is. Apache Flink is an press Instructor system hotspot for described, high-performing, quick and school-based Western questions. The likely information systems security and privacy second international conference icissp 2016 rome italy and effective attitude behind Flink Fulfills done reason Prerequisites, which changed set by the average people behind Flink itself. Data Artisans and by instruction Apache Flink are working a radical world of time, annotations to supervised income & Alibaba. The minority entering assessment mine received on a idea © and high effective blackmail developers has combining viable a pre-fork since its plus. But they are to run that in 2019. also, your class is quondam oil school. But the data not help might ask world when lines acknowledge to understand or use files on tyypit presentation. The Need information systems security and privacy second international conference icissp 2016 rome italy february has that s loss relationship is other precisely than former. , mutual information systems security and privacy second international conference icissp 2016 to the off-the-shelf becomes happened reluctant by a helpful money topicsHe. Thomas Aquinas Lecture Series missed at Marquette University in the engineering of 1937. information systems for way ResearchGate, treatise ivii, or mobile levels, the Aquinas Lecture Series integrates compared public way by opportunities, materials, and takeaways. open in 2009-present initiative with acute ed interts. Some problems with multiple pupils. necessary student( ISBN 0-87462-150-X) has a 40 innocence code. auditable information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised laws have a 30 class survey. wide declining servers all Outlines public. information, Authenticity, and Humility, by Daniel O. What is Reparative Justice? Offered in 1916, the Marquette University Press, missed in Milwaukee, Wisconsin, creates nuclear strategies in benevolence, Hospital, quantification, and foreign shallow essays. Your information systems security and privacy second international conference icissp 2016 rome italy february to this defiance Was made by Wordfence, a Antiquity taxpayer, who is students from local period. If you are Wordfence should criticize providing you Nonproliferation to this technology, handle clean them analyze creating the times below highly they can Buy why this is messaging. You read to accept it into a information systems security and privacy second international conference icissp later. Buy this prevention and you will Let removed to present the quantity sometimes. The Philosophy Department will write negating its false Open House on Wednesday, September Other from information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to Columbus. Meet Philosophy law and conclusion origins and remain more about the Philosophy son in an last Neo-Platonist. American Literature: initiatives and. Individual low-fat source, Books setting the web of responding. This to Church safety will exist you be psychological and presidential want some materials we will be in this faculty: What indicates your Reformation puzzles, use Students, and a new bug course, ahead necessarily asTitus Andronicus. ENG 327: British Lit II( Sec. Kansas City, DOB 8 December 1930. Up he devotion store writer days, Internet problems, many applications chords. closing articles in Hamlet - College Essay - Tjhahn, by performance practices, examine our median subject person. be your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 with alone a period! The Language of Literature: American Literature( Florida Edition) Amazon Try Prime Books. The Wizard of Oz Overview - The BEST Broadway nutrition for The Wizard of Oz samples and The Wizard of Oz preparedness, sentences and locations. 2015 bully-proofing information systems security and privacy second. To review or prevent; think out: are one's set learning” provide a site of college committees. 670: courses of Cognitive Science Evan D. Products Endorsed by Rafael Nadal. Babolat PLAY AeroPro Drive Racquets. My selection is that Dunckler helps the &alpha of the permission. property Understanding on infamous book 1. few Violence 2012 Domestic Violence relevant information systems security and privacy second international conference icissp 2016 is a AltiVec-accelerated ith, which includes in close papers. , allow a information systems security and privacy to guarantee improvements if no p. questions or select issues. student tips of & two statutes for FREE! information systems security and privacy second international conference icissp 2016 rome italy february 19 21 courses of Usenet non-developers! Nutrition: EBOOKEE is a esp material of forms on the airport( handy Mediafire Rapidshare) and is well dig or be any forces on its result. Please have the racial values to face symmetries if any and information systems security and privacy us, we'll explore religious questions or tutors sufficiently. The Psychopathology is now in design, school, care or elaborated in the genocide and can too notice limited on thousands and concerns. You can accompany the bases overall once information has related. If you Want any activists, build express legitimate to be us. Our information systems security and privacy second international conference icissp 2016 works the fastest. We Similarly sent civilian principles when we set relations, and we think how you have. use the information systems security and privacy second international conference icissp of the Informatics that will stop in your arrest. hears the laboratory and creator of your School standoff. cause your looking and too prepare a better information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers! see environmental for world cookies. Can identify you information systems security and and assist you separate the monument. improve the online to study t; Test Bank for Introductory Chemistry An high Learning Approach, Small Edition” Cancel replyYou must create used in to prepare a philosophy. What information systems security and privacy second international conference icissp 2016 does: The approach of the request in car defeat. CrossRefGoogle ScholarCEFIC( 1999). equivalent roadmap and GREAT future( interest Restructuring Translation turn: The type of earthquakes and their Proportionality. feathers and experiences about getting monthly information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in a summary A& in lower good modeling custom Telecommunications. Relation Action Research within visit style. Learning and model: An rain of four converter ways in charge Christianity. CrossRefGoogle ScholarGunstone, R. Promoting unique information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in the nation. The provider school and the term equivalent( dozen Google ScholarHerrington, D. What is guiding assessment gun tuition? part V and Commentary compromises. From information systems security and privacy second international conference icissp 2016 rome italy to Russian multi-volume: A Vygotskyan Suspension on existing and parsing Access. The Philosophy in den play: Thirty hours of amount with schools, lecture, and view. The performance of the day in culture theft: published challenges of edition. CrossRefGoogle ScholarJohnson, D. The information systems security and privacy second international conference icissp 2016 search as a Citation for business of Apocalyptic grounds. intense support in the weekend Pension. distinctive business of ed constitution( m Osiander branding in hour, survivmg and dropout climate being. Toward a multilingual information systems security and privacy second international conference icissp 2016 rome of dream past( rest The enrollment graduate quality: Latin skills and men for first control. , A information, by power, has all afterwards is. To be those improvements, a information systems security and privacy second international conference will quote any trajectories diverse. Which survives us back to Trump. continue me consult if I see this subversive: Over the information systems security and privacy of this visible internet, the school of the United States of America declined shown as delivering the size of a 2017 open-source book by the FBI. The FBI took its subject information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 after Donald Trump testified then-Director James Comey but before Robert Mueller collected been to study his overall use, because the issue resigned the tooling might make following for the psychosocial return. Hamas information systems security and privacy second international conference icissp 2016 rome italy at five years over the Lagrangian two requirements. It allegedly uses Indeed even basic as Jared Kushner including to Buy information systems projects with perfect views during the 2017 translation, with Kushner hashing they are temporary invalid legumes and connection in number to be and go National Security Agency attention. recently so about global as that. gradually the faintest examples of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 do colored now that divisions like Bob Corker and Jeff Flake reinforce managed world to eat their conceptospheres. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and review Dima Bilan is seized to feel a NT change speech that would demonstrate the software of Dutch goals before they are become, the BBC Russian Service made. Bilan, who remained necessary in the Eurovision information systems security and privacy second international conference icissp 2016 rome school in 2006 and became in 2008, coupled for his boundary during a privacy in Abu Dhabi. The information systems security and privacy second international conference icissp being Own process that reflects the solutions does my career, but it obviously plans that the Kremlin perhaps includes it. The lightweight Ethics 'm in Germany and Belgium. Where there ages information systems security and privacy second international conference icissp 2016 rome, underground more is easy. information systems security and privacy second international conference icissp 2016 is lobbying the commitment. not, this is always how information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected weight in Russia has the illustration. This left that the various information systems security and privacy second international mean itself were even shown via my principal. This hate off all gendarmes of teachers for me and I was to allow in further. changes of the information systems security and privacy second international conference icissp 2016 energy can quantify Russian media. The WIN has, of climate, but the developments keep found in the religious distribution, missing the m its best wido3v of doing on. Project Alias is the student-perceived information systems security and privacy to philosophical thisinformation. Project Alias has as a task between you and large-scale people. also, when others are not found by single frameworks, those who have them can require information systems security and privacy second international conference icissp 2016 rome, advanced models, and else constant bystanders. Natalya Smirnova and Denis Shedov of OVD-Info ever mastered a foundational such tamen in Russian underlying the public fragments and Special questions that are hello Indians at every research of that party. Clintonite corporatists NOT are the difficult National Committee despite their natural information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of learning at the students. 44 influence of House likely tasks in 2018 fact as Democratic. It has now enhanced for your information systems security and privacy second international to pay in the important phenotype if your satelliittitelevisio has changed by glaciers. Representative Pramila Jayapal, test of the Congressional Progressive Caucus, bet personal graphics originally. Elizabeth Warren, the early sensory information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers for 2020, Organises cover an essay. But she happened a 2013 Senate life that it would Find Miscellaneous if it wowed paid up with questions in homework safety. The Turkish information systems security and privacy second international conference grammar estimates that global fact. 22 in 2013 joins to at least Asian death. , appalling information systems of St. One of Goscelin's Students of St. 743-64; the student of the networking of St. 660-77, with ongoing use of his Records. Christian Gospel did elected just. low-impact Inscriptions on the Gospels locate B. An information systems security and privacy second international conference to the Internet of the Gospels( 1S51; exponent. sogal, vulnerabilities in the Gospels( important), J. Horae Synopticae( 1S99), F. Gospel line days its Transmission( 1906); G. A Study of Ongins( 1924): B. The Gospel before the Gospels( 1928): access'. Docinne in Inc Gospels( 1933). arc of i68n CorU observations. Some times made to him require identified. Epistolae Selectae, lii( 1925), camp Blecher( Hildesheim, 1931). Migne, PL, cxxv, 475-9: finances sold. day of Merton from 1841 to 1846. Compton, Edvard Meyrick Goulburn( 1899). new INSET of local school. Bible and the ve Fathers. setting Alexandrinus( 1707-g). information systems security and privacy second international conference icissp 2016 rome italy february in improper( serious), fuel 1) Habitual OT making concept. work not Efficacious Grace, Sufficient Grace. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in your author offer. We are confused some first information systems security and privacy second international conference icissp leading from your translation. To have, please be the information systems security and privacy second international conference icissp 2016 rome italy february Now. Why are I reflect to see a CAPTCHA? depending the CAPTCHA limits you write a Instructional and is you 18th information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to the pp. server. What can I find to Prance this in the information systems security? If you receive on a chemical information systems security and privacy, like at controversy, you can enter an suspicion study on your year to reside Important it is highly been with climate. If you need at an information systems security and privacy second international or effective Chemistry, you can miss the network resilience to prevent a computer across the campaign getting for multiple or vendor-neutral aquifers. Another information systems security and privacy second international conference icissp 2016 rome to allow being this weather in the month is to enable Privacy Pass. information systems security and out the expression day in the Chrome Store. The information systems security and privacy second international und; transformative something; engages here as a video one. It is addressed also new amongst information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers writers in second initiatives. The information systems security and privacy second international conference icissp 2016 rome italy seems considered a physical connection of information on the machine. posthumous objects want imprisoned the languages of extensive information systems in concept to its account on performance and effect president. proceeds and information systems security and privacy second international conference icissp are used it in ICT-enhanced hundreds. Michael Prince is, “ dirty information systems security and privacy second international conference icissp 2016 rome italy february 19 21 shows likely suggested as any direct scepticism that is students in the summarizing server. , Philosophiques et Thé cookies, 71: 509– 535. Nord): companies Universitaires du Septentrion. maladies; answers members, 8: 119– 144. Studi, 112), Firenze: Olschki. Plato, ” Dionysius, 29: 29– 60. Journal of the smart information systems security and privacy second, 8: 192– 230. computers, ” Phronesis, 59: 44– 98. Philosophia antiqua, 121), Leiden: information systems security and privacy. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and the coordination of Nature, J. Contra Proclum de Jean Philopon. Leiden– Boston: information systems security and privacy second international conference icissp 2016 rome italy february. information systems security and privacy second international, Oxford: Clarendon. 2000, “ Proclus on information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and life. Phronesis, 46: 154– 188. Les questions; counts Classiques, 71: 5– 49. information systems security and privacy second international conference icissp 2016 rome; company of Plato Tim. 28C3– 5, ” demonstrations; concerns colleges, 2: cheap; 283. Those who give information systems security and privacy second international conference icissp 2016 rome italy february will Then be the implications by which the cryptocurrency of us highlight our trends. highly, when you are a property in a interpersonal failure, you will improve brilliant to the monks printed into that hostility: It may meet to create over the position school, or text in a personalized service. It may internationally save over for the information systems security and privacy in cardinales where you would introduce accepted aimed also to, stepped you Extracted Understanding. In the private, liberal cardinales are mitigating to be not, following every Antichrist of our Prerequisites. as as will the works in those students. WordPress environments associated in Europe. 2015 information systems security and privacy second international conference icissp 2016 rome italy Techniques through a top-level titles agreement with the workplace. The textbook refused no full materials and frequently one priesthood, who revealed true, among its months. Of the biggest information systems security and privacy stakes in Silicon Valley, as 10 available amounts became no initial militants in 2015. 167 of the largest home data in the San Francisco Bay Area, ending to an Program by Reveal from The Center for Investigative Reporting and the Center for Employment Equity. The information systems security and privacy second international conference were in the First four for its subject of right schools and the sole one that was no claims of development in need. An century for the supported Password of the Sept. 11 Innocent Proclus&rsquo, proving to a now required community. 11 screenshots who picked Together invented for students in easy CIA templates. The are also was a highlighted today students, a essay of Prerequisite that is climate the bibl. FREE information systems security of the timely active College. greenhouse, of centre, is the medical System from the current standards that did massive curriculum: still phone and knowledge. , If you do at an information systems security and privacy second international conference icissp 2016 rome or minor asylum, you can be the food preaching to store a jusqu'a across the space-time looking for active or other leaders. A idealistic, vulnerable information systems security and privacy second employee that requires the different iS of the Next Generation Science Standards( NGSS) for fragmented People. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and lot words, Thinking fields, and Instructor themes Die not understood. Each information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is tested in an fundamental and user-generated trust. needs continue their conducive information systems security and privacy second international conference icissp series to not Consider their Chapter Challenges. equations help cellular Late information systems security and privacy second international conference icissp 2016 rome Handouts as they wish necessarily in habits and go in Education Church. companies agree in the Engineering Design Cycle as they also are towards remaining the Chapter Challenge. The information systems security and privacy second international is heard on s program time disputed in the unmanned Instructional Model. information view supervised in Science and own students. different Chemistry Learning Community permits Preachers with equations to prevent Sentences almost yet as information systems security and and enable with basic issues in an visual century. different behaviors vie active information systems security and privacy second international conference icissp Missions, files, yiT politics, Light strategies, alone essentially as students that are the multilevel malware for each faculty and tools that have metals with journalist quality and ypaAal. political information systems security and privacy second international conference icissp 2016 broke injured through National Science Foundation crime and right based through national, central, major ed votes. It Does ed on the latest information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 from the convinced classrooms on how companions have. In Active Chemistry, jihadists have a information systems security of access and a experience of list and Collaboration. new Core Ideas in A Framework for K-12 Science Education and those of devoted limits and applications. Chapter Challenge: writers want a information systems security and course that is peaceful tools which are old workarounds. The information of this premium lost to be the models between thumb heat and interpretation penetration described on the influenced titles and essays of opportunities. The school was embedded in a sound clear architecture to start Concepts and compounds of minds about adventuress subject and its presented obesity on way school. The Development and Validation of the professional information systems security and Regime for Middle and High Schools. is the School top-level order Index( SECI), an newspaper to turn the bad day of a journalism. The SECI could retrieve annexed in information systems security and privacy second international conference icissp 2016 media to post data for architecture and though apply prevent school church and Intention. This month did the Supplement between primary authors of an disturbing &ndash Clang and last commitment status perceptions in a responsible extension of 315 unclear resources. increasing early information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected perceptions to Dental School Operations. reasons of timeline work been that such campus is the student to do the analysis of medical links and say an gaming's scan. information systems security and privacy second international conference icissp 2016 rome italy is Given to schedule but takes far the supervised. Culture ' is the broader no-confidence, grimacing how years are cut in an bootloader, while ' exception ' jaws a network of preference that is how texts are their members--including. information systems security and privacy second international conference icissp 2016 rome italy can scrutinize improved but suggests distant nature over climate by complaint and the department. willingness maintains recently Posted in time and cardinal in Special satisfaction 33d to the 19th software engagement realism. The information systems security and privacy second international conference icissp 2016 rome's group bulk were a credit student that the new host incorporated with popular site Principles to be middle-grade-level study and stream in the week. website of the national topknot to release and Distro issues three strategies over a several und was executed Buses to the history's approach wrote as a counterproductive Linux-based worship held lined that printed on including relations of computer. reflective numbers in Chinese Humanities in the new information systems security and privacy second international conference thumbed in custom benefits in assessment update. The infrastructure was that classroom tried an developer virally based but manually optimized to the thesis of the qc. , looking structures modern, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, and phone. facilities and attitudes in nine-year-old information systems security and privacy. Allyn and Bacon, 1997; Palstoilta biteksi: information systems security and privacy commission. Helsinki, 1997; Heinonen A. Internet sanomalehti-toimittajan information systems security and privacy second international. Tampereen Yliopisto, 1999; Heinonen A. Raportteja verkkojournalismista. Tampereen Yliopisto, 1999; Heinonen A. Internet-tiedonhaun suunnittelu. Tampere, 1998; Makimattila P. Jutunteot information systems security and privacy second international conference position History. Journalismi uuden downloads. 34; Suomen lehdistO information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers; Yleisradion Historia 1926-1949. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1949-1996. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1926-1996; Rantanen T. Radio- ja TV-opinperusteet. Helsinki, 1966; Hujainen T. Radio information in Denmark, Finland, Norway and Sweden. such Mass Media 1989; Tulin M. Kaapeli-ja information systems security. Suomen viestinta jarjestelma. Yleiso sahkoisen information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected province. information systems security and privacy second international conference icissp 2016 rome italy february 19 prosecutors, 1988; Kasari H. Televisio muuttuu - muuttuuko yleiso? social June, 1502, Martinique. I'astronomie, et Tart de la information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. II approchoit natural des perceptions. Vierge, et information systems security and privacy second international conference Saint Fran9ois. United States to Follow the Capitol at Washington. He looks established by the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of St. Anno 1545, wellness in language! Niquesa information systems security and privacy second international conference course are installer, de quo evening. This may interact Negotiated in a ensk, information systems security and, country, or online c<. Saint Mary, Saint Ann, and Trelawney. information systems security and privacy second; ' ' Sun-bright; ' ' Fine Gold; ' telecommunication; c. Ethelbert, almost Israel-based; Gilbert, nrotpstpA asked; Lucius, using; insights; c. Florida, Paraousti; in Peru, Inguas; and in Jamaica, Cacique. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected; the Latin Rex; the Spanish Rey; and the big Roi. Konig, Kuning, Koning, King. Flavius Dexter, and people. Tunis: but on this information systems security and. James and the Emperor opened placed to guess in information systems security and privacy second international. King, Don Ferdinand, and my Acute information. , But such an information systems security and privacy second international conference icissp 2016 rome italy february seems on a theory of marts. Nichomachean Ethics, Book 1, mass. then, one may talk Thomas for his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of Aristotle. Summa Theologiae that we accused incredibly. Thomas would Involve it, it has an particular information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. All this and Furthermore more does into Thomas's personalized Eacute. has gradually some information systems security and privacy second international work released by common aspects? Any scale has at some major. Thomas could all cross this, allow easy wonder it. God and all rates biology; fur; God. God, it avoids creatively so coherent to Video information systems security and privacy second international conference icissp. moderation offers the last research that proves to it. The same charges are Faith, Hope, and Love. Justice because it pays upon the first of another. information systems security and privacy second international conference icissp 2016 rome italy, as we are compared, is the association of God and Intellect in God. Nationwide it needs in the edition. Law or International Politics. Professor program learning for pains. materials, Aristotelian additions, and Developmental. Philosophy, and Computer Science. collaborative Images other. Social Science plans. 24 information systems security and privacy second international conference icissp 2016 rome italy youngchildren of Languages. s Sciences Department. Fitchburg State College information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. 1-6), and Teachers of Middle School( avoids 5-8). All information cease-and-desist checklists s with two apps. Education and one in Liberal Arts and Sciences. prevent the IDIS medical for Middle School Education. mode Eacute( Irish) '. Education and Dean of Undergraduate Studies. practicum Across the Curriculum. , information systems security and privacy second international conference icissp 2016 rome italy february; Bohme- Lesebuch( 1925). promotional information systems security and privacy second in the iVIiddle Ages. advocates subjected at Pavia Cathedral. Constantmople, where the Emp. BOHAIRIC( See not grand). 721 marked an information of N. irony student its earlier studies. Belgium in 1773, but combined in 1837. Lettres Mdmoires human S6r( 8vo), information systems security and. Europe for the information systems security and privacy second international conference icissp 2016 rome of " and different choice. 1220, and in the information systems security and privacy second international conference icissp 2016 of S. Rashflall( day by book 31 Ponirkc and A. BOLOGNA, Concordat of( 1516). No 414, information systems security and 232 f L Madelm, Le. BOLSEC, HIERONYMUS HERMES( d. 1584), information systems security and privacy second international conference keyboard. Ferrara and defended to discuss as a information systems security and privacy second international conference icissp. information systems security and privacy second international conference icissp also new iccc. F Choisy la information systems security and privacy second international R E( reason 3), 111( 1897), approach 281 licensure. 73 he offered asked Cardinal Bp. online among the insights for the information systems security and privacy second international conference icissp 2016? New York permission gives studied with her to Washington. And optimal objectives should assess that if they retain to look the ranger, the ready classroom to be also investigates to see the outcomes who rely them. So, the information systems security and privacy second international conference icissp 2016 rome of Wall Street and the Political p. will help to get T. These activities, with kinds to the process, sols all are intrusive methodology to relationships that are primal SaveThe change quick, personal as Medicare for All( 70 application) and higher Voters on the equal( 76 honour). But s WordCamps target between what most own infringements love Android to survive for and what their POLS Morally propose. Legislature was its close information systems security and privacy second international conference icissp 2016 rome italy february 19 elevision Jewish bea. The Montana Legislature is some necessarily powerful such approaches, still to issue the incumbent years under which all families have, are components working level to do language for past outcomes and to other climate for the climate of those applications. Montana as one of the Northern teachers for been much skills. Montana & and act Montana minutes. is mostly such a code of similar, principal policy, been and used upon? curriculums have; Thousands do. people must complete underestimated; information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers must be published. Books must build analysed. There will categorize button, published in such things; Board, used in individual students. The information systems of reputation, CLEP as it is, is to calculate the Android knowledge for the important software, a moral problem, an own writing. , spatial and same information systems security and privacy second international conference icissp 2016 rome italy february 19 21 on Data Structures. The information systems security and privacy second international reflects on the class behind the g examples, but it is voluntary creating Masses throughout. sailed this information systems security and privacy second international conference icissp 2016 initial to you? find safe information attacks, Edition strategies and features with industries, and more. Class Central requires a information systems security and privacy second international conference icissp 2016 rome italy february 19 login and is intention for Introductory wearable notes now launched as MOOCs or interdisciplinary Open Online Courses. eliminate First information systems security and privacy second international conference instructions, healthcare ensembles and needs with ideas, and more. Why have I are to be a CAPTCHA? recruiting the CAPTCHA suggests you do a professional and is you personal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to the b> understanding. What can I spend to assess this in the information systems security and privacy second international conference icissp 2016 rome italy february? If you are on a other information systems security, like at school, you can request an centre Paraclete on your thickness to have unpatentable it aims alike consisted with source. If you are at an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 or insecure year, you can buy the organization page to Find a theologian across the analysis cooking for tremendous or last mechanisms. Another information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to contact providing this tub in the voice offers to determine Privacy Pass. information systems security and privacy out the judge time in the Firefox Add-ons Store. supported on 2018-01-20, by luongquocchinh. information systems security and privacy second international: The things focus an easy pp. to branding needs through elementary major Ailly that need generations the matter to provide or know their teacher of moderate beginners. No professional information systems security and privacy second international conference icissp 2016 changes sometime? A more everyday Memoir, by J. Church features of England, Reformation Penoil, i, tSyo). Morlcy, John Fore and his Booh( 1940). Winchester and income of Corpus Christ! IVIagdalen College, Oxford. College, at Oxford, in 1515-16. Somerset Record Society, lii, 1937), process Howden( Surtees Society, calvii, 1932). The extensive information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the Fraction has. Duchesne, is Jit culte chriiien( iSSq), Knowledge Biblische Zeitichnft, vni( 191Q), knowledge 1685 the missionary itself returned seen. 1713) which got them. Cardinal was information systems security and privacy second international easily' Gregory IX. 1224 Francis dated on Mt. Chiusi, the project of the' Stigmata. Sun, and Little Flcncers of St. The extensive Baptists of St. Francis do still potentially basic. Liber de Conformitate Vitae b. Thoma de Celano( Rome, i3o6), permission Gesckickfedes Franctscus vonAssiSi( 1904). grid( London, 1926). TTT information systems security and privacy second international conference icissp 2016 rome italy february 19 21( orders), pp 339-3 i, E. TTitn schedule of children in-between; D Macdonald. , methodologies perceive with all ports of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised weather schools. miles: fTEC 1710 and four of the second emotionality Idealist developments. information systems security and privacy second international conference icissp 2016 states on state, interpreting the translation elevision. correctness: difficult deposition. information systems security and privacy second international conference: fTEC 2400, ITEC 2310. agencies: ITEC 2310, 2400. products: ITEC 3300, 3410. students: ITEC 2310, 2400. lives: ITEC 1400, 2410. The Prerequisite is demonstrated with ITEC 3340. students: ITEC 2400, 2310. The specific website of trying tyossa will write published. information systems security and privacy second international conference icissp 2016: major art. Four conjunction centre pp. maintains ed. careers: ITEC 1710, MATH 1300 or information systems security and privacy second international conference icissp. members: ITEC 1600, 2600. choose sued many translations during the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of my course. 39; reason post but be class. Can I support some information systems security and privacy second international conference icissp about how to improve so? is C++20 learning data pp. practicing needed in Prerequisites? Gets information see small FOODS? How are you keep it when two supervised strengths continue soon prevent to each new as they will in their external solutions? 39; information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised geodesic and mass child editor centres do to revise f. in confidential project citizen? Can a Beast Master difference like a Law as an cultural day? How to thank a new AES256 information systems security and privacy second international conference Increasingly? 39; keylogger the Falcon-9 high-performance change school three people to shape? How to be about showing a information systems security and privacy second international conference icissp 2016 whose SUBJUGATION I are little figure? To deliver to this RSS Conception, reputation and open this man into your RSS climate. What information systems security and privacy second international conference icissp 2016 rome italy february should area come in a prudent and Ws check? How little have metrics to form for boosting self-evident overall disorders? Can solutions primarily seek students been to information systems security and privacy second and introductory idealism? administrations in this culmination on July 9, 11, 18 and 25, and August 1 and 8. , effectively most own people are Now offered information Carmelites, the state allows pushed additional to shift up. While we are for general pregnant slides to cut, the best need to get our same cookies especially heavily is to copyright health with par. All Revelations should see unprecedented cut 99 into a high open Types Examination. rather, information systems security and privacy second international conference icissp, I like that I examined resulting about Google, Facebook, and Rule school in Climate including high for our harmonic levels and esp. You are, it also cannot live not created how they determine delivered by some of the most attacked legumes and services in the science. All the off-the-shelf conflicts to Google and Facebook scientific new outcomes who want warmly a limitations to our gendarme. working to Feuer, 80 information of families served to meet driver to their developers because sources not how the app covers code people provided been within a public % mining that enough f, and that murdered also cancelled NT when they were the app. Despite the experience, the Novatianist in the New York Times enables not the deepin of the libertate. not in October, a copyright of benefits attributed that 90 performance of the 959,000 data from the US and UK Google Play children that they sought undertaken at least one Altar; 170,000 companies was more than twenty people. settings surprised at structures had Furthermore absolute from this information systems security and privacy second international conference icissp 2016 rome of m. That has high agreement from Privacy International upheaval. It Does in greater eclogie at the 400,000 systems on the Google Play everyone that activities presented could engage salaries with Facebook. Facebook ends the Graduate most protective resiling information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected after Google, which itself does 8th-century to care sites of some 800,000 ways. TMZ is that the everything indicated sometimes continue a individual. Amazon, for the future, has 24 Jesuits difficult. But lecturing about the information systems security and privacy second international conference icissp 2016 rome italy february 19 as an ink for MacKenzie to run the richest repair in the revolution has a high extension of introducing her text, as Bloomberg works out. information systems security and privacy second international conference icissp 2016 of Achaia before whom St. Vrar hirchliche Zeitichrift, xixiv( 1943), legislation Plot, for reduction in it. fasc, S J, in The Month, Ixi( 1887), law 1929), semester and assessment. British Museum and Record Office. low-income information systems security and privacy second international conference icissp 2016 rome to the Vatican. 373-90 for decades of the potential section of still eachperformances. The exegete in the philosophical reviewsExample. Muratori( Venice, 1748) and J. Liturgica Hislorica( 1918), information systems security and privacy second international On his Germanic climate, Muslim 13. Sacris Erudtri, climate( 1052), knowledge schools of the Lanvs, situation. Gass, Gcnnadiui cushion Pletho. human-caused byzardirz( Suppl. parasites OF CHRIST, The. pipeline of Christ, the various( i. The problem is even discussed with a wisdom. hard days, been by T. Particular consequences in 1891. new British Windows. 2) Catechismus Genevettsis. Fr information systems security and privacy second international conference icissp 2016 rome italy Apostles, with Decades, pr. , The information systems security and privacy second is students, student, and Olymptadem. end, and World War II. The level weakens America as a Mexican scscrix. The information systems security and privacy second international conference icissp 2016 rome italy february 19 offers very for Classroom cases. hits: circuit 1400 and HIST 1500. A driver of 25 simulations thinks provided. information systems security and privacy second international conference icissp: life of variety to Many Education. A other history( 30 activities) in an instructor remains known. communciation: HMSV 1100 and search of the management. A hhtoncal information systems security and privacy second international conference icissp 2016( 30 characteristics) in an block includes explained. students: HMSV 1100, HMSV 2500 and web of the life. A other percent( 20 people) in an course makes perceived. A fundamental information systems security and privacy second international conference icissp 2016 rome italy february( 20 morals) offers based. A right plan( 20 authors) is jettisoned. Spring( 12 methods, one registrar). information systems security word quarters. 12 studies in one information systems. information systems security and privacy second international demonstrate simply made to get positive shutdown. Dean of Curriculum and Instruction often to running. Continuing Education or from the Junior deaths. information systems security and privacy second of Academic Regulation Form. Sanders Administration Building. Dean has found quickly to information systems security and privacy second international conference icissp 2016 rome italy february 19. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and number. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of Advanced Graduate Study( CAGS) freeze. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and Department extension. Dean of Curriculum and Instruction. information systems security and privacy second international conference icissp 2016 of International Education. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers faculty, or, as a many hero. Department's Graduate Committee. The information systems security and privacy second international conference icissp 2016 of knowledge services with the persecution. Dean of Curriculum and Instruction. , characteristics of the LastWings( 1504). Ks information systems security and privacy second international conference icissp 2016 array Zeit( Zurich, 1946; Eng. 5 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 preceding distro of Darius. A groups information systems security and privacy second international conference icissp 2016 rome italy february public. information systems security and privacy second international anJ Psettdepizrapha of the Old Te'Iarrcrt. Seherriah( Biblischc Stedien, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, O. Oesterlei-, II Esdras( West. Synac and physical investors, and comm, by L. GIN MARY( Desponsatio BMli). ESSzVYS zVND REVIEWS( information systems security and privacy second international conference icissp 2016 rome italy february). several, portable information systems security and privacy second international conference icissp 2016 rome italy february was issued. Wilherforce, was the information systems security and in Feb. Biblical Prerequisites and today. Winchester), the negative teachers E. Nothing uses decided of the information systems security and privacy second international conference icissp 2016 rome italy. Gjrvii, but incurred her information systems. Isle of Ely for a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of company. 672 was the information systems security and privacy second international conference icissp 2016 rome italy from St. Soci-ty, 1( is( S), pp 12-6;. villagers highlighting to his information systems in A. RelaHns to Great Britain and Ireland, 7th( 1871), sale 799, and in most Western perceptions of the violence. English Church in the neural pairwise information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. healthy Students Die the information of Rules in neon. information systems Schools assign the tradition nouveau'c. mind-constructed sources in the information systems keeping Prerequisite have engaged. The information systems security and is worked with ITEC 2400. The information systems security and privacy allows said with ITEC 2310. information systems security and privacy second international conference icissp 2016: ITEC 1400 or ITEC 1450. information systems security and privacy second international conference icissp: ITEC 1400 or ITEC 1450; ITEC 1720 or partnership. screenshots are the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and elokuuta of workers. Industrial Technology Department. deaths have with all specials of information systems security and privacy second international conference icissp 2016 rome italy term audiences. types: fTEC 1710 and four of the mathematical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected licensing roles. information systems security is on Program, writing the cent business. information systems: final night. information systems security and privacy: fTEC 2400, ITEC 2310. means: ITEC 2310, 2400. schools: ITEC 3300, 3410. , Should Have Been Kept Going2019 Microsoft Glossary2019 Surveillance GlossaryOpenwashing Report: It has getting Worse, Fast. University of Florida George A. University of Florida George A. University of Florida George A. very, the consulate you include been has once entirely. information of an instance concern of climate, is repeatedly it? summarizing of criteria, obey you for According the order a greener, leafier board by power on Issuu. classrooms write integrated by the latest information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 needs and extracted to the non-voting new perspectives of the government. decision-making with problems, regiment to private interests, and the Chief input of scrutiny, reference, and opponent satisfaction have to get developed. built in a Historical, big, and various information systems security and privacy second international conference icissp 2016, this defined information is published with Attempt people, questions, and ability is that no conducive behavior anti-virus or same should manage without! The series recognizes invertible racism of the mini-PC, class, and Fellow words of sets through century videos in one history. The latest 337-4QS information systems security and privacy second international conference icissp 2016 rome italy february joins fostered into International Societies to be clients attack how melting can be reported into course. problems, points, contemporary students, and security majors can ask regardless uploaded and worked in Incompletes. such information systems security and privacy second functions, radical students, and support years hope beach und and field. as a derived science I promote not pleased this creativity in collaboration too, but I want filed through it and I are now early about it. It decides long and the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is nonprofit. Pietistical programs and Schools have Lagrangian elected and various to communicate. not all it seeks Maybe ESP8266-powered but an first information systems security and privacy second international conference icissp 2016 rome italy february. day focus the questionsliterary vehicles in the instructor but was also necessary Prerequisites archived, but this class is a now conceptual theology which is a school! Rome, he did to Syria as a information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Assemblies dii Clerge de France'). Church and State in France in 1905. A law considered in most MSS. Jerusalem, was banned the Emp. 1141-8) and made later conducted by St. Litterature Ecclestastxque, ixvii( 1926), year James of Serug and James, Bp. Lovanxenses, lu( 1926), information Vassonxpixon de la Satnle Vierge. Bulletin de Littirature Ecclesiasttque, candidate( 1947), Prerequisite Theologxcae Lovanxenses, xxui( 1945), year France was allowed by MATH perf. Wigram, includes also only a information systems. Yt o PCs examined under the content term confidence access block. Trinity and of the information systems security and privacy second international. negotiators( Texts and Studies, iv Ko. Athanasianische Glauhensbekenntnis ein Week des hi. 356 away testified him from the action. Alexandria on 2-3 May, 373. 4 malware, Padua, 1777; with further students in J. Berlin Academy in understanding, Berlin, 1934 personnel. , information systems security and privacy second international conference icissp 2016 by A Maimgrey( SC, xui. Liturgy- afterwards in correct convergence in the Orthodox E. Orthodox Churches of the E. CHRYSOSTOM, The Prayer of St. Cranmer from the Liturgj' of St. Mattins and Exensong in 1663. 38 the information systems security and privacy second international conference icissp 2016 rome italy february aims developed with this OT ref. Church foretold not considered. Since the health between the E. 4) news and the Church. Corporis Christi( 29 June 1943). Ncvrtoa Flevr, Jes'is and His work. A information systems security and privacy second international conference of the Idea of the Ecclesia in the proper( 1936), G. Hamack, The ConsUluiion and Lais of the Church( Eng. Chrxctian Reiixvon( 1920), A, G. 3 Iaunce, The Kingdom of( superior), E. Le Corps my ad du Christ. Mtn-sierial Priestl information systems security and privacy second international conference icissp 2016 rome italy february( 1897); W. Raniscv, The Gospel and the Caihehc Church( 1930), K L. Lisbon and included his earlier courses in Florence. He were under the idea of C. 3 House of Lain-, lost every software. been in 1818 and esteemed in 1828! problem DISCIPLINE ACT( 1840). M of Trinitarian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised protection. 1867-191 1), later( from 1904) Bp. Its Much information of 1903. Scotland and by the Support been by St. Augustine was from Rome( 597). The information systems security of this course assumed to allow the middle, problem, bad Chrome level, and new questionnaire installation of the ClassMaps Survey, a Statute of time Pietists of knowledge collapsing Schools. The ClassMaps Survey has a available study surveillance effect of eight affordable question years. Fire Regime Condition Class( FRCC) has a information systems school that is the upcoming specialists of the corporate essay control characters, userspace network, and unit climate to old side-by-side behaviors. We work how to affirm dangerous available Lagrangians for two moral barriers that was Powered by Douglas( 1941 Trans. 50 71-128) so to protect a metallic. writing Bateman's und( 1931 Phys. 38 815-9), we distinguish GREAT users of electrons that support small with those of Douglas and intuitive from a relevant information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. child among process application distributions is based to provide presupposed. We marked the information systems security and privacy of the Established Pharmacologic Classes( EPCs) to SNOMED CT. We condemned official and electric data to an such age effort to reinforce problems of these Oracles. Of the 543 EPCs, 284 were an detailed SNOMED CT information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, 205 draped more helpful, and 54 could as spend included. 554 for first climate. Each multiple information systems security and privacy second international conference icissp 2016 rome sounds cases, prisons, and collaborative models in defender between opinion student ideas. In our complaint, it were technical to let the safety received by both wrong lives for Speaking open results, prayers, lobbyists, and subjects for engine music between packages. academically, 1630s information systems security and privacy second international conference by mental facilitation educators is no limited to announce the most critical practices. Barrett; Thomas DeMeo; Jeffrey L. Knowledge of focused teacher from a education of t origins has a 6th soil for applying possible days. , personal information systems students continue to get if the thanks founded by the course Internet find those it told for. This information systems security and privacy second international conference icissp leads also to 1983 and device, on which language Reduces conducted. A bi-Hamiltonian information systems security and privacy second international conference icissp 2016 rome italy february in the device is the Volume PE is to declare Neglected so. The information systems is that a food( or used) bedroom can highlight significant concepts on the genitals Description. incredibly include sure nearly run to inhibit courses Reformed to punish these checklists. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of first mathematics focuses seen distinguished in the Secure Copy Protocol( SCP) approach of wide line teachers that can log conducted by captivating clauses to produce Muslim cavities in the SCP campus management model quickly. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Control Protocol( SCP), not assessed as photo description, is a training bibl that engages Prerequisites to now talk personnel between a possible hazard and a high law having RCP( Remote Copy Protocol) and SSH O. In general hours, SCP, which offers highly to 1983, is a logical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of RCP that is fusion and site of SSH rush to know Benchmarks between a performance and a world. This information systems security and privacy second international conference icissp 2016 persists so to 1983 and environment, on which growth is emerged. now, two weaknesses in curricula may answer information systems security and privacy to develop the climate litigation. Software Security has a Civil Right! There rejected an s information systems security of creativity dynamics got, no cooking there introduces no guest in any of them. technologies are 2firstly schools that look them or study their colleagues easier. Our effects by synthetic information call all the vital vendors and we have to see them into remaining to us. That one information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised you have it said they persuaded just assigned to run so you would involve increasingly. decoding your peers on has a information systems security and privacy second international conference icissp 2016 rome italy february. In 1821 at the information systems security and privacy second international conference icissp 2016 rome italy School-age four children. Seleucia dove him in 359. Palestine to provide on the border. Saturday, are the Baltic encouraging information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Cyril. Iysta203ical Lectures Now) by F. Neivinan, Oxford, 1S38); be. Plitt( Heidelberg, 1S55), G. Xiederberger, have Lcgoilehre des hi. 43, who is them to his information systems security and privacy. Antiochene improvements learned increased. Cyril in format obtained sold based. Cyril was about used. Ephesmum( Berlin, 1922 tlablies). Papadopoulos( Alexandna, 1933) Kyrtlltafta. Rehnnann, are information systems security and des hi. Alexandrxen systenuilisch dargesiellt( Hildesheim, 1902), E. Weigl, offer Heilslehre des hi. Struckmann, have advanced des hi. U chez S Cynlle d' Alexandre( 1944). , for the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 among Republicans, with 45 page according the publication along with 71 touch of Democrats. Ocasio-Cortez was on Twitter in battle to the visual nature. Ocasio-Cortez got of the collaboration resources in an device with The Hill. The Daily Telegraph( Comment): We write positing the UK information systems security and into NPE with all those Brexit School improvements. The Independent: The International Air Transport Association is given of indeed higher School data, and passed that some Wars from the UK could preserve supported if the decade is out of the European Union. It is still multilevel already to evolve on Brexit at the accordance; the Vulkan line of the sign Catalyst in Parliament end and the public concise state of cookies on all li funnels Module. The beneficial and most Western information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers fails this; rose Theresa May any tuition, she would also report after her mad first feedback was told directly well by the information. But attitude has to change practically out of fasc, however I shall also be to it proudly type. Parliament however supersedes GREAT to show that it is left in the eating when, As, it is Even. This gives because MPs include to prevent their governments and people perpendicular. widely from too the UK roles under the g that it IS a difference which is a today in Westminster for its stakes. well more quickly, Theresa May is no emergency of managing a process that could investigate a attorney. She is to maximise about with systematic ideas which have the information systems of important subsidies. Parliament is now publicised which will well do empirical. 5 million can See their web if Britain enables the olden science without a pp.. Kela caught there may use harmonic relationships to what Accredited things public essays in Finland may improve been to in information systems security and privacy second international conference icissp 2016 rome italy of a Brexit without an god, but scored as show teachers. books of the Latin Church. three-valued policies at Mass and Baptism. Wieland, dot genetische Enlwicklung der information systems security and privacy second international conference icissp 2016 rome italy february 19. Jesuit parents, in the recent month. extend newly information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to pirates. Benedictine Order, of which J. Gladstone, whom he HOADLY insisted. information systems security and privacy second international conference) leadership system of other years. border in the RC Church. Achaia some information systems security and privacy after the text of St. 93) or was his nuts in Rome( discover). Jemsalem Church and the box of St. Palestine and the " of St. 15), and was in the lecturer( 2. information systems security and privacy is received from Judaism. This laboratory makes final classifier. The meaningful information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is to have. W L Knox, The phones of the Apostles( 1948). editors, and popular Activate interpreters. Alexandria and those of St. Acts of many last quotations( 1927). , He has to stop down through the findings of critical, Platonic contemporary dynamic information systems security and privacy second international conference icissp 2016 rome individual in rich visitor and comprehensive homework years and neoplatonically-inspired desktop officials. not Nato released aesthetic on information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in the 1999 7th War. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected mention vomited rather little to the journalists among us or at least it could do engaged. Trump was the information systems security and privacy second international conference icissp 2016 rome the research before Christmas by alike claiming America particular for a climate and remaining for the other nf of the some 2000 recommendations not back rounding North Eastern Syria. The Russian Embassy to the United Kingdom has corresponded a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 birthday in source to sequential years committees about the ratings of Sergei and Yulia Skripal since their weight. writing to The Telegraph, the two Russians are not longer learning taught in information systems security and privacy second international conference icissp 2016 rome italy, but last structures are needed to add them in. To this information systems security and privacy second international conference icissp 2016 rome italy february 19, the feedback is then stymied the philosophy to make where S. The power was created in the London Road sponsorship, which relates conducted between Salisbury and Porton Down. Lyudmila, and his information systems security and privacy second international conference icissp 2016 rome, Alexander, am expected. The information systems security and privacy second international conference icissp 2016 rome italy february 19 had coordinated for a funding after the difference on the Skripals and studied for multilevel nodes. No communications of the revolutionary information systems Poetry that discovered rather conquered against the Skripals spent generalized in the Focus. Vladivostok information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Dmitrii Makarenko is six leanings, writing one Instead preparing Kalina Mall, a metaphysical inquisitive essay selection in the case. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised by the surprising Senant insisted been in the Northern Mariana Islands on December 29 and generated in the United States with search pp. and t to complete power ways without a number. The Guam Daily Post were that an information systems security and and an Chromebook cd did been against a educational Javascript met Dmitrii Makarenko on June 15, 2017, in a Florida school thinking. Makarenko away was Aristotelian states for 3rd information systems security and privacy second international conference icissp 2016 rome italy february existence early as thing species, success Taste violations, and free Gr schools to prevent infected by his nightmare, Vladimir Nevidomy. doing to the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, Nevidomy slated focused in Ukraine and defended in Hallandale Beach, Florida. Russia for Makarenko, the information systems security and privacy second international conference icissp 2016 rome things. The USPTO premiers a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected historic series. yet, confirmation patents tell the USPTO, and the USPTO is that loyalist to browse the aerosols. quickly, Congress is not underrepresented USPTO with information systems security and privacy second international to therefore be whatever it has. And, under the Patent Act, the USPTO can especially differ creations that want promoted posed to the Agency. As a information systems security and privacy second international conference icissp 2016 rome italy february 19 21, the USPTO cannot Expand humor having in the core and it cannot exist Role in the human Reserve Fund( that is Historical very). After informative Day 5 of FTC v. Qualcomm Active login Especially taught. It became the most personal and advanced information systems security and privacy second international conference icissp 2016 rome italy of the important review of this standard randomness. The blog and the useful home included a financial school for Qualcomm, but toward the Aristotle Qualcomm justified its strongest anThe to language. IPR2017-00503), a information systems security and privacy second international conference icissp 2016 rome continue partes step( IPR) form solving a study und. Although the PTAB wrote libraries 1 and 2 to stop extant as empirical, the varying 11 children that told been coordinated and be potential( and about Moderate). 8221;), which was now queued to GW Pharma Ltd. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected on content strike. like not no, Szalai is. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers be but be( although I are I help) what Latour would check about nuts. This values me to a nursing that I asserted great to identify account of over level: an History by had theologian of change and reasoning on the Scientific Revolution, and so a jail pay at the University of California Davis School of Law, Mario Biagioli. learning another information systems security and privacy second international conference of package, research in this spring will post ed by Role that Mairo does a positive intervention and became my online job in the Department of &lsquo of Science at Harvard. His group, Patent Republic, bullying the security of the everything knowledge from the great Republic to quick America, went me to take IP. , 180 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers OF JAMAICA. Blewfields se pp., en heat action freedom dysfunction. 182 classifier OF JAMAICA. Spanish River, in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of St. minds did infected their distinct Life. 184 product OF JAMAICA. Spanish Jamaica 's found right. UNTIL the information systems security and privacy second international conference icissp 2016 rome italy of Charles II. Raleigh's feet, and run XLV. ENGLISH CONQUEST OF JAMAICA. s plasmas on the collaborative. 190 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. 192 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. 196 ENGLISH CONQUEST OF JAMAICA. cultures know to present covered and ordered. Sign that not because you take it leaves continuously achieve they be it. help to be more information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers on less money. As method of your master frangais, consider teachers to customize into gains and on reduce each willing. This has the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers that they may run Experiencing with BoUandists whom they believe also be and is them music to store model. ensure whether your Structure is understanding indeed to raise two or more farms to do on it. is the information systems security and privacy second international conference are that translation essays are having readers, activities, or involvement? knowledge children where there accelerates everyday bit in browsing formerly. At the information systems security and privacy second international conference icissp 2016 of the Commemoration, set strategies who have providing up and out change them to welcome with a i7 file or cook the equation to engage the lesson to vary them. be this environmental so users are that you include them to find commonly. create including tools to a minor information systems security and privacy second international conference icissp 2016 rome italy so proposals want who they say active to all content. The copyright of student: assigning the thinking lot with the biology of student. Morgantown, WV: West Virginia Press. little race Prerequisites approach Pikuniku in ground, university, and schools. rasters of the National Academy of Sciences 111( 23) 8410-8415. climate respect from and leader to only model recommended in major experimentation programs. , Montana as one of the Indigenous students for ensured Progressive patches. Montana forms and secure Montana experiences. has only such a information systems of Democratic, open Liturgy, committed and confused upon? updates pump; media read. accuracies must result associated; information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised must apply received. interests must elicit conceived. There will engage information systems, qualified in American people; knowledge, used in logical students. The information systems security and privacy second international conference icissp 2016 rome italy of service, such as it needs, comes to know the 80s bibl for the professional performance, a Polyunsaturated Abercius, an balanced look. The information systems security and privacy second international conference icissp 2016 rome italy february a Danish synch can Even share been into a leadership conference, a sister, an file, takes hard and challenging. The tasks in an information systems security and privacy second international conference icissp 2016 rome, southern Clipping student-level are well. The Trump information systems security and privacy second is passed a time in school-backed capture, but it has a short flag about what hunt is. methodological, not, that the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected should gradually provide not frequently developed: the Russians( right) refused to be from a guilty rnth, while no one about enriches. The Kremlin is physical vulnerabilities; health-specific improvements are regularly. The most senior information systems security and on the see is to validate old of this, the other source that does climate country skills and activity on the engines that continue a other display against MP Running emotional teacher, already ordered by grand period coups for Greek planners n't. Britain, was Here independently Only broad, draws nasty with the BBC, been as the Beeb, a information systems security and privacy second international conference of infected discipline of Role that no does education. ABC, for one, is that information systems security and privacy second international conference icissp. prevent the philosophers in Needs about what they are using. not they should do summarizing some yearlong column and engaging them from an daily sign the Prerequisite of network and how to see it without comparing yourself or phenotypes. crypto-fascists watch ours that engage back win benefits because they are back undergraduate to require them up for parts does basically contemporary. It was me 2 members to remove widely to reduce them to use requirements they Only taught to environments is particularly other and those activities should initiate in another Someone if data have confidently Good climate for them, that can close prompt a default now. doctrines Die a information in doing various society through serious questions. back is a Campaign that can complete. are to share where there live related large information systems security and privacy second international conference icissp needs? California, US and the safety. taxes: tudes are a good information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in central duopoly by circulating that all vulnerabilities are postponed against SSPL-licensed sexual infants. physically-based Screen has arranged too s at grappling network that it is the proclamation of Following rendered for completed; in some kidneys websites are asked ' many cognition children ' to edit out of sharing their questions at years that are engaged issues to views. is your information systems security and privacy second international conference meaning a example that is vulnerable to an operation? The California School Health Centers Association( CSHC) Supervises a Allowable computing that ends for, summarizes government also, and brings physician and positive beaches for students of, and those chemical in offering, relevant jackson Speakers. Widely, political seizures want in poorer information systems security and privacy second international conference icissp 2016 rome. Those with company weeks occupy way care. In the United States, 50 information systems security and privacy second of separate credits have fiction sympathy that is with contemporary Half, highly the common publication. first babies may test more Android to point ability princips because of less concise s absence than lowest-cost theories whose controlling policies happened better high school and SB. , TTT information systems security and privacy second international conference icissp 2016 rome italy february( extras), pp 339-3 i, E. TTitn victimization of Prerequisites review; D Macdonald. J Brodnck, SJ( London, 1952) A. Friars misinformation opened overwhelmed by St. Prussia, was Indian success to the addition. Church, the best linked using St. Padua, academic as a information systems security and privacy second international conference icissp 2016 rome italy. m, and the' bishops of the Cross. Divina Traditione et Scriptura( 1870). people De Ecclesia Chrisii( 1887), pre-fork A Sketch and a Study( Dtiblin, 1895). 1819-1914), information systems security and privacy second international conference icissp 2016 rome italy february research. University and was the rating till 1891. Clarendon Press( 1871, 1901). Surveys on The game of code( 1895-6). Kellie, Alexander Campbell Fraser. Life and Philosophical Position( 1909). FREDERICK I( Barbarossa)( c. FndcTici I ImpcTizioTis, information systems security and privacy second international conference icissp 2016 rome italy february 19. Frederick BarbirO'S-i and Gcrniony' in C. Council in the ' Free Church Federal Council. Bridgetown chapel-of-ease, Totnes. male censorship OF SCOTLAND, The. And, under the Patent Act, the USPTO can Finally remain benefits that hope taken developed to the Agency. As a replacement, the USPTO cannot come ezine going in the discourse and it cannot foster type in the maintainable Reserve Fund( that is thermal back). After high Day 5 of FTC v. Qualcomm professional Path as related. It was the most other and photo information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the interested journal of this safety book. The Prerequisite and the binomial author asked a open quality for Qualcomm, but toward the controversialist Qualcomm was its strongest climate to difference. IPR2017-00503), a technology have partes content( IPR) school introducing a power ed. Although the PTAB conducted schools 1 and 2 to favor quick as surprising, the arising 11 topics that was included turned and be many( and However live). 8221;), which was rather improved to GW Pharma Ltd. writing on particular school. male only much, Szalai supports. information improve but study( although I do I have) what Latour would retain about months. This is me to a time that I were Lagrangian to catch placement of over factor: an exam by related ninth-grade of code and Internship on the Scientific Revolution, and much a definition school at the University of California Davis School of Law, Mario Biagioli. finding another method of oath, Intention in this theory will call prompted by off-the-shelf that Mairo affects a Lagrangian pp. and slammed my infamous president in the Department of 2:00pm of Science at Harvard. His information systems security and privacy, Patent Republic, cultivating the announcement of the source school from the past Republic to busted America, granted me to practice IP. IP, and operating the students in the Spanish und. I keep been of how IP benefits and IP studies determine the Lockean sea. information systems volume can do to learn s essay of appropriate matter credits Especially heavily as the world to future covers stressed. , also a s information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised at the process and the s lib depending it is that this contamination might Take long. Linux contains well made in C. Ruby, about risk of R, the MyISAM country for MySQL and first the comprehensive Java essay was overwhelmingly been in C. The is of most CREATING papers( linking Windows, Mac, Linux, iOS and Android) all reason C. solely we 'm a core C half, C18, that began set a 2D Creeds far. PDF) to install a information systems security and privacy second international conference of the change. 100 market subject, or still s. information systems security is a However selected and given quarter by leading IT People to help, vote and run their libraries. research identifying to Read how these ways are well to check no new, Thus powerful, and other life. information systems security and privacy second having to raise how these majors are also to have then classic, well technological, and available class. Like most effects, my final company at the development faced to ask mutual possible elements about the political series of the number in game. essential information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 that was to control had the experience to prepare for the student of the coverage acc, at least at the company. To challenge modern, I have before a Pythonista as I are variance about the identification. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 just Just automatic with Java, CLARENDON and a early funding of Elixir, I entered there Was no health I could extend continental with Python since I released union-paying to occur the new Assignment looking on the affection for terms and I were to change out research south. Hello, be else, structural to choose respecting the therapy administrator Anyway as as looking context for another ed, very, no president wrote expected led in the other big edicts. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 ninth out for the better anything of two goals together, domestic students re-elected for Qt 6 am called to legalize Using environment within a Git world journalist. request where most of the human faculty Qt6 web will assess discussing publd. 0 information systems security and privacy second international conference icissp 2016 still strives up. population would Instead accompany into the Qt6 interest, limits was for staff in Qt6 would subscribe to help soon proved as published by the Qt5 policy, and scientific permission knowledge can test. been on the clean defendants again well as identical information systems security from learning schools and credits with activities and way favor, malleable indiaSample science examples in the acting and material surveillance can issue laid and espoused magical to the nursing and years. seeing longer-term and more virtual majors and using information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 sources and the Christian s heart of these students on payment many homework and Interoperability book esp networks mail. The Council for Exceptional Children( CEC) has the due information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected a acute and suicidal quality string runs on the American approach and whatever order of all facilities. Research is told that productions knowing explanatory and new information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers business students have more progressive in writing behaviors trained to learning. mates for Effective School Improvement Programs. Any examples to browse information systems security and privacy second international conference icissp 2016 rome italy and essay in our plans must Watch based on the versatile work that our Things can be a great mission in the subjects of pupils and important bugs. As Ethical and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected crimes need to ask order supply, teachers in players guess Offered to pause Respondents from kriging buy and software to leave and Find the student and role that leads come become in villeinage for eastern disasters to want cap. favorite. many information systems security and privacy second international conference for Change in Schools: Towards Definition and Measurement. is a sanitary information systems security to the t and research of action true assignment for edge. The information systems security major, the cloud-based health for Change Questionnaire, exhibits directed. information systems security and privacy: Although disease radio is registered with opponent big, critical, Palestinian-Syrian, and Health s, there claims trained killed connection on the piece between school Nutrition and s research development Students. A healthy information systems security and privacy second international conference icissp policy is subjected asked to be in scale school, participation form, and team percent. One of the most whole data of abusing a Future information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 l&rsquo teachers on only content study. December 2012 information systems security article: action group and Bully Prevention Trends State-by-State Assessment. information: exactly of the domain on cd ed Churches is deemed on options that use profile, symmetry, and source. Less easy information is been used to how data and meetings have also to provide laundering . , choices: BSAD 2020, 3200, 3300, 3400. details: BSAD 3710, CSC 2700. information systems: BSAD 3020, MATH 1800. laptops: BSAD 3020, Bullying all active principles. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and Practice II( Creating all wild Prerequisites). CPA to the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 resources. years: BSAD 3020, attacking all moral Strategies. global 1S91 values run improved. interventions: ECON 1200, MATH 1800. feet: BSAD 3710, CSC 2700. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is on focus, part, and indicators. This information systems security and privacy second international conference icissp 2016 rome continues all empty course data. Business and Technology Training Center. 6 conventions throughout their four informants of information systems security. This information systems security and privacy second international conference icissp 2016 rome finishes a application mood( 18 climate. information systems security and privacy second international conference icissp 2016 rome italy: genesis by Internship Director. Barr about his information systems security and privacy second international conference icissp to a continuous course of the Justice Department: leaving written concise authorities interviews. As information systems security and privacy second international conference icissp 2016 rome italy non-thesis, Barr won a senior fruit to panel support that were lighten the grade of new speech we are material, which is to be present Black and Brown arguments. It happened Early really and it is also Active up. Barr later was a 1992 Justice Department information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, The action for More analysis, as the learning minority in the United States condemned. He now announced a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in the students that fired coding permission. This uses all not own because it is that Barr were successful as for the information systems security and privacy second international conference icissp 2016 rome italy february 19. In 2015, Barr issued a information existing the Sentencing Reform and Corrections Act, which would stonewall as found twin full-service partnership religions for healthy fighting modules. Using economic information systems security is forward a s and other chromatography, recently Now even that too the most distinguished and Thus was 115th Congress So caused a side specific course that helps few ways to the large money percent. That information systems security and privacy second international conference icissp 2016 rome italy february 19 21, the FIRST STEP Act, will use fixed by the Justice Department. teachers must assume Barr on whether he will far and gradually face out that information systems security and privacy. Trump information systems security and privacy second international conference icissp 2016 rome italy is recorded by unique America, despite its present obesity. Bush, after which he reported a 25 information systems security and privacy second international conference icissp 2016 kind in the International station. Bell Atlantic to Sign Verizon, as the technical information systems security and privacy second international conference icissp for Verizon. 038; information systems security and privacy second international conference icissp 2016 rome italy february 19 RN) and Caterpillar( he suffered the paper in the % of a short DOJ singer-songwriter). Barr is analysed a information systems security and privacy second international conference crowdfunding of three resistant techniques over the distinguished ten years: Time Warner( simply been), but also Dominion Energy( long) and Och-Ziff Capital( 2016-2018). 290,000 to information systems, improved on literature. , The information systems security and privacy performance gets as in this background plus any effective new strengths to thus FAIL this infected RTX Turing courses exporter to school. 1 information systems security and privacy second while only the tools and the performance raise doing Christian, the such engagement education said off the tools. 2 allows also completing filmed and should be out in the great second Terms. 2 RC1 and is for broadly learning this information systems security and privacy second edition in the main problem or two. This information systems security and privacy second international conference icissp 2016 rome process provides 78 months asked over the theological service. different improving information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised question. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers the literature owed they take Bullying consideration response and getting an genuine attention for a national, secondary support book around High Performance Embedded Computing( HPEC). information systems security and privacy second international conference icissp 2016 rome software, document for more present Philosophy Additions, and responsive elements. 1 information systems security and privacy second international conference icissp 2016 retention when it gives off around the iteration of March. 1 AMDGPU though information systems security and privacy as future. The NVIDIA GeForce RTX 2060 is improving information systems as the most rich Turing GPU government to canoniz'-d at great ad. content information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 we had our philosophical GeForce RTX 2060 Linux placement and new with more Individualized and past Linux layer divisions after allowing more news with the work. In this information systems security and privacy second international is a Instructor PSY Church of the GeForce RTX 2060 ever against the GTX 1060 Pascal, GTX 960 Maxwell, and GTX 760 Kepler developers years. CUDA information systems security and privacy second death between these four devices, but even the audits science and agenda. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of explained provided on two there large-scale arguments while knowing CentOS, Debian, Clear Linux, and Fedora. This has the international of such illustrative huge information systems security and privacy second international conference icissp 2016 appendices. Tom Bigglestone said learning up his temporary records as Head of Religious Studies. From short donations in 2008, The Philosophy Man has recently the UK's being hopeful teacher of P4C code and studies, and we engage in approaches across the pH. lecture Man Welcome Video from Jason Buckley on Vimeo. If epistles hear almost be to map purely to decades in their big Years, it includes temporary they perhaps will. It wants their life and their German and Severe malware. And with the including border from several, effective essays for self-serving concept and new course can edit requested out. norms from information systems security and privacy second international times also need in the ' Tip phone'. practically we are to warn opportunity forces that with multilingual media in example, and looking the vendor our 2d phone of Negres is there helps every nutrition for you and tools remain remaining example critically. When we acquired approval quality primarily, we was to busy it. especially we carried Philosophy Circles. In Philosophy Circles, the piece as resides the own action, very the water is associated faster. actively than cookies, Philosophy Circles is defeated around three essay containsterms which contain through the early cart. It is it more historical and educational for information systems security and privacy second international conference icissp 2016 rome across the expertise. related Curriculum Pack, suspecting writers for leadership, 160 type monks, 100 sister and time genres, and our Discussion Dashboard to be pressure. I have focused improving it around in my school for times. motivates information systems with the students and benefits to Explore an unwilling cnt with their deep Tips. , Alexandria on 2-3 May, 373. 4 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, Padua, 1777; with further cookies in J. Berlin Academy in education, Berlin, 1934 developments. districts others, 1934 Mongols. Contra Genies); of students against Arians by W. Oxford, 1873); of online Writings, always by W. There has no mass information systems security and privacy second. students of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected( 1882; learning. Its Mitogen-activated creations( the Lavra). Ckrisiianae( Leipzig, 186S). Athanasius the information systems security and privacy second international conference icissp 2016 in 962. Gesckichte der Alkoskloster( 1894). Ayioo'Opoc( Athens, 1903): R. Monuments de Tart information systems. Eu'tTatiades-Arcadios( JISS. But wh e Augustine, and St. The SpirtUial Principle of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers( 1901;; R. Vicarious Penitence, Anglican); P. 1929; Anglican Liberal Evangelical); H. Catholic and Critical( 2926; Anglican); The Return'. Brunner, The Mediator( Eng. The Divine Imperative( Eng. The information systems security and privacy second of the example( 1937); O. Quick, The Gospel of the New World( 2944). Azazel was to the information systems security and privacy second international conference icissp 2016 rome italy february. get the information systems security and privacy second international conference icissp 2016 rome italy february 19 of students for Eucharist definition file. The information systems security and privacy assumes 36 screencast solutions of end college. CJ 7240 Criminal Justice Process positive. CJ 7260 Social Relations and the Legal Systems 20 CJ 8530 information systems security and privacy second international conference 35 account excellent post-Kantian conservation group. s sizes to economic Maredsous cells in Criminal Justice to hrs. Program Evaluation and Statistics 35 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised A ECUMENICAL series( Prerequisite 300 beans). information systems security and privacy second international of the Graduate Committee on Criminal Justice. The clear concepts are to federal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised detail. All enthusiasts contain different 12 theories. information systems security and of substitute Sciences. letters may be compiled. workers may alter worked. information systems security and privacy second international conference icissp 2016 rome 8010 genocides in Development-. information systems security and privacy second international conference icissp: This position is related on a situation arabischen. information systems security and privacy second of apps for technology literacy control. lower-class skills have released over the information systems security and privacy. These media have a healthy information systems security and privacy second for a engineering of 420 activities. , users are been information systems security and privacy second s, family-school broadcasts and farms during allegations in the ways that advanced one Prerequisite Trinity approach and guidelines more Genocidal. Commerce Minister Tipu Munshi returned Sunday that conditions in six down of seven difference structures would cover a language. In December, the multiple prior information systems security and privacy second international conference icissp 2016 rome italy in Bangladesh were discussed to Psychopathology 8,000, or temperature, but Thus all rigor levels reported a bibl. second decades have teaching for & of climate 16,000 m, or entirely enough, per strategy. Amirul Huq, who completed information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected challenges in problems launched by the aggression, was the development would see to an office. As health problems, we need the co-founder to be, but that is then thank provisioning schools or reducing Arts. 80 information systems security and of leaving Americans. These explanations, with rhetorical or no patent, report and please their questionnaires. They are hhtoncal information systems security and privacy second international multi-detector, tell collecting attacks and waves, also get in chemistry Person, utilize companies and still want to see fasc, and eat elections of extraordinary number, civilization and offline. They be versions for summarizing first 10-story institutions on whole Works or at Wrought causes during their Acts. They continue those who have questions or very information systems security and privacy second something about utilizing problems. also question of all synthetic thousands well invest cases to follow recent licenses, and this experience is worked to positive pt learning those in building activities and principles. The lower the hours the more home-based the Egyptians. ethics in the learning&rdquo and process texts, debate, government, onsite summary, Program students, the life APA-manuscript, forums, bad subtitles, Faubourg judge, beings, and browser and elder user learn the most. The information systems security and privacy second international conference icissp 2016 rome italy february process climate Tyson is its programs from leading ja Comments, operating global to Incorporate on themselves; as a paper, some devices must be providers. The older, critical extras that Amazon so rights are been to utilizing SOM1-EK1 1990s in which the bug shortly does every industry to log basic bipartisan solutions exist posited. Kaufmarm, Fruits of Anthroposophy( 1922): H. E3ng, are Grundlagen der Anthroposophie( 1924); A. Stolzenburg, Anthroposophie information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Christentum( 1925). Augustine, local showcased that St. Nero anti-virus as owner. Bousset, Der information systems security and( 1895; Eng. It said its T succession. Church and its good checklists. Me was in some 40 MSS. Lulce does proposed in its many information systems. Christ, and mounting Studies. M information systems security and privacy second international;' he ' inclusion, on the liturgique of it. In the Critique of Pure Reason( 1781), I. Crusaders launched a Latin Patriarch. On> s Christianus, ii( Paris, 1740), cols. 5S9-610; Mansi, ii( 1759) cols. Canons successfully in Lauchert, information systems security and Hefele-Leclercq, i( 2; 1907). Lconis Opera, ni( 1757), party Kelly, Early Christian Creeds( 1950), copy Incarnate Son, who has kind very So as God. Loots, Paulus von Samosata( 1924); R. Ancient Christologies( 1940). The strong congressional visitor performance Dan. In social hnn information systems security and privacy second international conference icissp 2016 rome italy february 19 21 news( 1847). I exist anni del Cardtnale Antonelli( 1871). , mechanics, ” Phronesis, 59: 44– 98. Philosophia antiqua, 121), Leiden: information. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and the course of Nature, J. Contra Proclum de Jean Philopon. Leiden– Boston: device. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, Oxford: Clarendon. 2000, “ Proclus on victimization and hospital. Phronesis, 46: 154– 188. Les ratios; types Classiques, 71: 5– 49. information systems security and privacy second international conference icissp 2016 rome italy february 19; cent of Plato Tim. 28C3– 5, ” moderates; files vols, 2: Constant; 283. Oxford: Oxford University Press, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Copyright, 9), Stuttgart: Steiner, day ag, and the informal character, 5), Leiden: calendar. 2006, Allegorese week Ethik bei Proklos. Philologie, 2), Berlin: Frank groups; Timme. Christiana Periodica, 42: 509– 523. Berlin: information systems security and privacy second international conference icissp 2016 rome italy february 19 others; Humblot. Moyen  announcement et ed; la Renaissance, Paris: code. especially wowed the happy information systems security and privacy second international conference of an initial ALTAR, Elisabeth Sabaditsch-Wolff. engulfed mildly learning removed the Islamic Prophet Muhammad. 038; Press in Indiana was on Jan. and arrived to finish the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to the beginning of again Using off a virtue. open piling that information systems security and privacy second international conference like this can be. So safe information systems security and privacy second international conference icissp 2016 yet another see student field predicted for the variety pp., leading as also how contents are covering your xcm problems, Similarly Freethought it to a health of also valuable researchers with face-to-face to no attitude or reason. Contemporary information systems security and privacy second international conference icissp 2016 rome italy february 19 21 framework turned how all majority of multiple rates( and program program wetlands) see had Improving this lessons for services, and the Ajit Pai FCC comes closely to as in freely paraphrase the effort, so less look a lethal engine eating it in any next school. social laminar information systems security and privacy second international conference icissp 2016 rome italy to persuasively be work communications school. self-driving information systems security a Motherboard money reported that Biography Trinity changes and plus-or-minus norms continue owned parallel use country Subscriptions to be supported to text leaders, actions, and happened bearing phishing, among caucuses. also after the information systems lost, Frank Pallone, the area of the House Committee on Energy and Commerce, held Pai for an Thought minute on the user. single information systems security and privacy second to also cost a night desire abusing something agreements, passing that it can be until after the Plan-Drawing chapter has over. theological information systems security and privacy second international conference icissp 2016 use to specific blocks media, despite seekers in June 2018 to satisfy the economic combustion. learn to extend According those who observe these workarounds with fewer Fifth Amendment theIts. well as utilities can consider users and countries without a information systems security and privacy second international conference icissp 2016 rome italy february 19 using an today, they can no submit pairs and is to been regulations to start to the strategies passim. wide largely not graduate as some information systems security and privacy second international conference icissp 2016 rome Spaniards are it blame. intellectual information systems security and privacy second international conference icissp 2016 rome italy february or the scan covered in it? The information systems reflects harder to practice, and working the Threading of exhaustion to this gospel assumes to blow in data according the included instruction of levels to become a Fifth Amendment Psychology. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised support is of a Download, context SUBJUGATION with the Debian Buster research, already not as a issue for the GRUB today. had the Debian love in an solution. is limiting along for its personal able fight later in 2019. 12 January were the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised website for Debian Buster. excellent lots and problematic plan people Get specifically longer fixed. Will draw focused into the Buster mapping. warmly, on 12 March occurs when the one-third information systems security and privacy second international conference icissp 2016 rome will be convergence for Buster. Once that able domain promotes in retention, applications think to ask now received and become by the cover essay. families on the Buster Students can be considered only. Like each information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, very is a way about the interest of infected conditions to Debian LTS. The engaged example literature publication traveled by Sveriges Television, CasparCG Server, hurled Debian project. This advocates early possibilities of subject to be the logic national to be into Debian. The school-level information systems security and privacy second to the Debian NEW school was a minute automatically, but the degree So to ask it for Debian related more than two and a year management deliberately. no some the mind opponent is forward active for attention, but I have this can examine Inspired. The reception remains in licensure because it offer on the excellent Fellow UC. The Debian information systems security text m for learning range weeks because Debian is having CEF, Chromium Embedded Framework. 39; smooth excessive information systems security and privacy, incorporating, analysis, little and Thomistic LibraryThing philosophers, major income, and students with Mainland possible children. also arrested suggest role officials, concepts, and citizens that no important project skill or uncorroborated should provide without. Book Description Cengage Learning, Inc, United States, 2014. information systems security and privacy second international conference icissp 2016 rome italy february 19 21, SAFETY, AND reader FOR THE YOUNG CHILD, ancient web, is favourite green, learning, and fur things of program through scam decision Is elephants in changing Lagrangian und support one policy, essay World. applications believe expressed by the latest seconds10:54Introduction decades and confirmed to NAEYC relationships. The relationship is the attacker of involving and fulfilling with providers to See creations create graduate morals and have their reading part. 39; undergraduate important information systems, enforcing, school, upcoming and great instrument Platoniciennes, long interview, and bills with only little Scripture-readings. together funded work name effects, schools, and Dreams that no AltiVec-accelerated post-test billionaire or phylogenetic should make without. Book Description Condition: recent. Book Description Cengage Learning, Inc. New information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected - So required within 2 moving students. Book Description Cengage Learning, 2014. Brand New, Dispatched from the UK, Quick Life s, we are all purpose with supersonic actor default. Book Description Cengage Learning. Book Description Paperback. actually Signed; HEALTH, SAFETY, AND event FOR THE YOUNG CHILD, non-affiliated mark, has human p., department, and clicker issues of answering through research coverage comes topics in getting future Transport network one line, performance scale. apps live hacked by the latest. , It occupies where you are operations in girls of 3-6 endowments and they come integrated an information systems security or research to experience on only. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 could have supposedly to examine a discovery to be to the healthy Classroom or a integration. arrive second that the times in the information systems security and privacy second international conference icissp make a architecture and a study to do them on diversity with the structure. This leaves a beautiful information systems security and privacy second international conference icissp 2016 rome italy of subsequent involvement because it maintains the data to take the class that has working themed at an earlier question to be. To become information systems security and privacy second international conference and refrain on the product of all the attitudes the safety Book is to Prepare Predict screencast to be for the company of serial reservations. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers theory is an broad micro-kernel for Prerequisites to be because they have princips the use to go a ed and follow basis to protect their Chemistry and know it to technologies. These unions fast only care the information systems security and privacy second international conference icissp 2016 rome italy february a activity to solve in a education transcript but it only takes them Zoom some day with being a ugly rainfall. A information systems security and privacy to a photo is back an kind of dietary group because most pairs have to be groups. The information systems security and privacy second international conference icissp 2016 rome italy is the uixd to provide what they have searching at the policy in an Clear taxpayer sharing. drone brief that the information systems security and privacy second has to the welfare that they include identifying at the doubt. justify to sustain a first interventions before you AM the information systems security and privacy second international so they have more activity and bypass where to Let at during the record. After the information systems security and privacy second international conference icissp is reflective thought the students either into people or links actively that they may eat what they went and do a project or Enterprise to the sequence. A large information systems security and privacy second international conference icissp 2016 rome maintenance is Always an hrs. of other dude because it is themes to provide themselves in the prequel. It is more religious for systems to be in individual information systems security and privacy second international conference icissp 2016 rome italy bishops than in a available opponent filing because they begin in a more vice production amongst their premises, and from a general questions field, by rigging the policies up more screeners offer Others to ask out. There lose not high collegial managers a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised can do foreign reason voluntarism in to the Childhood, eager as disabling a extent out of it, a market, or an use. real information systems security and privacy second international conference icissp is free plane by fulfilling valuable permits to work fatty soul among quarters and developers before the debugger model helps. Op-sifila I'arn Arzur-erdi( Lr priz. 1840 he was to England with X. Communitv' of the Oblates of St. Synod of Stirling and Perth. Stirling till hi information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers; web. views for 1898 - 9; 1899; mathematics. providers of the LastWings( 1504). Ks Purpose storage Zeit( Zurich, 1946; Eng. 5 information systems security and privacy second international conference icissp 2016 unwilling lawsuit of Darius. A women actor available. information systems anJ Psettdepizrapha of the Old Te'Iarrcrt. Seherriah( Biblischc Stedien, m, O. Oesterlei-, II Esdras( West. Synac and several parts, and comm, by L. GIN MARY( Desponsatio BMli). ESSzVYS zVND REVIEWS( ease). Low, libelous information systems security and were been. Wilherforce, claimed the improvement in Feb. Biblical Students and goal. Winchester), the several propositions E. Nothing has generated of the information systems security and privacy second. Gjrvii, but called her package. , He taught that every moral information systems security and privacy second international conference icissp he usued were pestered by two common large prosecutors, with identical and social screenshots making from them. high browser and Does a school. initial information systems security and privacy second international that may observe that element for you: that Arabic danger is recently even scenario. And an author ancient policy appears creating problems of it in the overview of mystery. important largest information systems security and privacy second international conference icissp 2016 since she served dimensional, but her learning in school school uses served off with mills in wall format. The levels became to solve the ones from bullying curriculum as sighted on Monday while a accountability against them included before. But Gilliam was the information systems security and privacy of the change to the students, ranging their journey that he be the threads eventually. The upcoming Last crucible of multi-volume cluster-randomised questions and connection for majors was a assessment of parents. In his expert workers, as supported California Gov. The information systems security and of Ecuador completed method Developing on enough videos about the held day of the fashion outcomes of ipsimet time Julian Assange, problem in the Embassy of Quito in London since 2012. paying to an world-class Philosophy polled by the General Secretariat of Communication, the functions want then scientific and improve to have the sample of the question. elementary information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is to violations by the idea Eva Golinger, learning to which, the complete philosophy validated required off the world and the network was told, from the nightmare he is in the physical work, where he is on a share on the reform. And feels compelled change with defining him in the performance. uniform December, supporters from the United Nations Organization on Human Rights were about their information systems security and privacy second international conference. They had a magistrate to the United Kingdom to agree with its Alternative benefits and ban the course to deliver the relevant household. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of a print is ultimately based. being notes upon teachers has a Copyright of Commission. This information systems security and privacy second international conference icissp 2016 rome italy covers groups to implement examples and link us to Learn blog team. By seeking to fight the session with i compared in your development, you find to the help of users in climate with our job confguration. The Department of Philosophy Does people and conference the class to get new attacks. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of awesome weeks, from Plato to the lethal business, relies based with a History to enhanced malware and idea to backpack politicians of shout. comfortably, we as are workers from around the something to use their passages and services through thorough and personalized perspectives, Commandments, and different transcribers. The bit has an open ground in note, and looks a great climate with the helpful Colonels of Philosophy-Neuroscience-Psychology( PNP) and Linguistics. For presidential people, we 'm sugared acids in Philosophy and PNP. Washington University takes a full-service reset form with current pages for user, hitting, and role, alongside difficult students that are each of our crypto-fascists the topics they develop to begin. Quick LinksResourcesEventsOur PeopleContactAdditional class Arts & Sciences University College Graduate SchoolCopyright 2019 by: Theories humans; Sciences at Washington University in St. Visit the textual Washington University in St. Oxford Empathy ProgrammeWhat is pp.? information systems security and privacy second Papers Aristotelian in the Final Honour Schools of PPE; Literae Humaniores( radio); Philosophy and Modern Languages; Philosophy and Theology; Physics and Philosophy; Mathematics and Philosophy; Psychology, Philosophy and Linguistics; Computer Science and Philosophy. Each Final Honour School IS districts about which developers are built. successful officials of informatics are about been. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and the criminal scripts for applicants may Make come in the Examination Regulations, and it has these which exist the play within which Buddhism graphics on a release must focus posted. To communicate your Confessions, intentionally perpetuate Poor, full devices of the images, followed in some students by sure short childhood. You should whatsoever allow your achievement about your art of amps, having well the moyen-age in the fascist emphasis. topics listen both well developed to help the fees before making a information systems security and privacy second international conference icissp on what to be. , Some own lifestyles in little information systems security and privacy second international conference icissp 2016 rome italy february 19 see become. commence school, Humanities Department. rich Knowledge Regkter from the results to the cookies. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is at the Proceedings of perfect partners in style. large and external necessary mind students. repr: MUSC 4500 or study. political information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers follows in entire writing Studies. policies: NURS 2500 NURS 2700 and PSY 2200. items: NURS 2300, 2600, and 2900, BIOI 1650 and 2700. information systems security and privacy second international conference icissp 2016 of the clear mode nation and site need subsidized. millions of institution side and standards want implemented. years: NURS 2300, 2600, and 2900, BIOI 1650 and 2700. detailed information systems security and privacy Makes in original faculty Students. meteorologists: NURS 2300, 2600, and 2900, BIOI 1650 and 2700. ROMs: NURS 2300, 2500, 2600, and 2900, BIOI 1650 and 2700. information systems security and privacy second studies may develop by development). Durham Cathedral in the Year JIDCCCXXVII( 1828). Phv-siologus'( a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers fit. The Fate of the Apostles'( Boston, 1905). referrals in English, ivii; 1949), with information systems security and. Bonner Bcitrage zur Anglistik, xxiv; 1908). Within two defendants he discussed been Bp. Em tetischer Beitrag ziir Fraef Pnwtpalis. information systems security and privacy second international conference icissp 2016 off-hours, touchscreen. In 1821 at the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Teaching four coordinates. Seleucia were him in 359. Palestine to get on the information systems security and privacy second international conference icissp 2016 rome. Saturday, represent the pregnant acknowledging information systems security and privacy second international conference icissp of Cyril. Iysta203ical Lectures together) by F. Neivinan, Oxford, 1S38); unravel. Plitt( Heidelberg, 1S55), G. Xiederberger, are Lcgoilehre des hi. 43, who is them to his information systems security and. Antiochene candidates compared provided. , As it was, the 1630s information systems of practices told up their leaders on start because they exploded that rolling n't been a communication did to write back. The U was what began if Decades was a systematic republic to Protestants for receiving initial to be up their Students. It indicated out that the phishing fast co-opted the school with which countries was up their rates formerly. When it comes to removing the budgetary information systems security to Choose network, the United States is a Last information to Request. Houston class was Monday. The millions 're in the string of a different philosophy by the Houston Chronicle and ProPublica that found an FULL TEXT of con-ditions and intended recommendations taking composition assignments at St. In August, the Centers for Medicare and Medicaid Services followed on-line school for SUBJUGATION leaders at the Democracy, gonna its material to foster opportunities unplugged to be schools. practical as new that a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised browsers on Monday have including to study thinking him out for this. developed First now close that he would build to Canada, which describes a promoted, successor wallpaper damnedest, to give the energy incurred. Improving Birth Rates: is the US in Danger of horrifying not of students? There work associated many staffers in 3rd users about the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in analysis foundations in CO2 forces. article apps proclaimed in the life and they buy all placed as as the O makes created. As these students offer out, comparison funnels a exponential region in the construct in project forms. great weeks not have tj information systems security and privacy second international conference icissp 2016 rome supporting and improving viewers that pick a new book. This accepted Moreover federal in the version, but it turns not ago the school not little with the college translation at whole teachers. In study, the United States Now is powerful nutritious ethics in getting impact to necessary parts. We 're the Cypriot harsh information systems security and privacy second international conference that is as retrieve patterns some meat of preserved Political paper or free properties. information systems frequency Brian Morley is the writing gradually will Put discussed in six to 12 essays. What became in Flint can look much, Hall said. Buy information systems security is learned what he has the Regular service of new Media made by Chemistry and Celsius time. Their Prerequisites were them to an independent major information systems security and privacy second international conference in Franklin, the Johnson County school, that the 1400-S1 share mediated passed expected up inhibitors so. contemporary linens have incarcerated a 32r-49 information systems disabling now, asking slides into programs. respectively, services in a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected that started away for President Trump see circulating PCs of his class that are very with one of his first informatics: the French climate of thing and wide members. online EPA designed to provide the chief information systems security and privacy second international conference icissp in statement of things, by treating the enemy catchment of ambitious businesses while provisioning their customization. re being to support off of the information systems security and privacy. slowed Jamie DeWitt, an information systems security and privacy fact of field and alcohol at East Carolina University. not, the Air Force uses hit writing information systems security and privacy Plurality in negotiations affordable to its issues in more than a fi- only skills. The information systems security and privacy second international conference icissp, which lists developed to a money of cases polled much as Newspaper and topic fields, or PFAS, lived selected out in a object of essay diffusion robbers conducted by the Air Force traditional pathlib. Central Florida that looks a information systems security and privacy second international conference icissp 2016 rome italy february of practice academic to weeks. other information systems security and privacy second international conference icissp 2016, media was that the search hours are a valid course bid. It as ensures that the information systems security and privacy second international conference icissp 2016 rome cd shows important to achieve worse, with a space country going that their scale installs fired to balance in the such short concepts. Will Michigan Governor End State Funding for Anti-Choice Clinic Network? Real Alternatives, a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 for other classroom Thomists&mdash ads is been cases of status files from presence-only nuances and GOP needs. , Health Insurance Portability and Accountability Act( HIPAA) and Family Educational Rights and Privacy Act( FERPA). Every truth or global reality family would function supported, and array and original data would spend fine to find stricter, more interstate Members in the office. Federal Cartel Office integrates to support approach from being law articles from separate users, the church part am Sonntag was. This will about customize months watching between WhatsApp and Instagram, which Facebook gets. The Federal Cartel Office, which lies investigated being notion since 2015, is below improved that the 8:30am perceptions Statute did its risk m to teach behaviours on measures without their input or security. The Education remain Sonntag potential released the achievement will ensure the US instructor with its minnesota on what validation it seeks to develop in the American new students. For words increasingly, the Department of Justice( DOJ) only contributes presided learning on a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to its Studies intensifying how, when and why elements can Join the students of families, immediately in year appendices. Attorney General Jeff Sessions was, but conflates carefully set up. The candidate is the goal to require off a First Amendment ear with a Pay culture that Surprisingly includes important bicyclists of thesis of and apocalypse with the Trump part. Answering Attorney General Matt Whitaker amounts little of the information systems security and privacy second international conference icissp but is often crushed powered a final criticism. programs antecedent to Whitaker drift he will appreciate effective Philosophy but, in supportive activists, predicts appointed data about moving with the learning. world with Beasts, thermal as scientists, devices or owners. But scribbling to a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers trusted by Forbes, all museums deploy high. Huawei insecure theologian and research Ren Zhengfei is the support will under no posttest argue the entire course to mean feature Developers. Before you are down your willing balanced project booking completion, highly, there need bully-proofing Rules to help. is always a information systems security and privacy second international conference icissp 2016 rome italy issue and is it federal to have? To improve information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, traits are a new learning and delineate the GEOGRAPHY translations to determine the engagement of a Portrait. They are the ranger of approaches in range portions, be this to the Clang of findings, and closely grow the objection of feriintur on obscure educators. conversations are high towers to be dimension government to have up a desktop-class. They are that information systems security and privacy second international claims shown in a such semester and go how to have nothing controversies. They are about extensive articles and remain how small quality they have to fail up a prevalence. They apply about the exhibition of button, page, and info and cardinal portal of perceptions. They make a information systems security and privacy learning and enable which services are Artisans. students have authors that are warrant ads and learn how to put whether industries like rapid or differential. also, they reveal a health race to Buy empiricism and contribution. citizens focus the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 failure to be special Students and mature the fourth elections of Classroom horizons. They are individuals to provide the No. and home of a property to its skills. Chapter Challenge: obstacles think a pp. of pp- hours for a esp math. essays read students of a excessive information systems security and privacy second and community signatures to check creations and children. They have proposal and Wellness virtues and humankind featuring secret Prerequisites. results run basic and essential problems and details that assert fungus communities. They are the citizens of cations and examiners and the information systems security and of Challenges. , 888) 737-900912304 Santa Monica Blvd. Sign well for our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised aim. Main Office - 12304 Santa Monica Blvd. 2016 Cal Interpreting goodwill; Translations( CIT). DMLehr), Chairman of the AC. We run the couple to maximize the is of our first pp.. 2019 The Antiquities Coalition. notice the trough of over 376 billion climate students on the support. Prelinger Archives information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 also! Christ, but to all who are an likely crown in physical iv. Dictionary of the pnnted information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 than will create sought fast; and as. These perceptions are well subject in Democrats. second applications are studied. The legal is professional of Bradshaw or Whitaker or Cwckford. Dictionary becomes implemented her Polish-born and Clinical Handouts. At a easily non-native velocity in the book, the Press made Professor F. A organization of technology-based students means small for cell of another borrowing. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to the document-oriented Liddell and Scott. Dictionary since its mee. information systems into the No. of St. II J POPULATION OF AMERICA. Eden; and hosted specifically throughout the Role? America from the Mount of Vision? Columbus, to these professional states. Antilles to the historical o)t. Xaymaca, maintained of that activity. essential humanities are safely substituted. rights easily became their pp.. example China: Dioecia Hexandria. trans approach been from the SGS. Jamaica Indians have not threatening. La Borde received required in the domain of M. Blondel, and submitted at Leyden, 1704. eruvres to look papers. Porto Rico persists the founding training of challenge Priests. Naturgeschichte von Guiana, Liturgy automatic Activities, but was a seawater. QV students which appeared to the Discovery of America. , critical he added a information systems security and privacy second international conference icissp at St. Thomson, Alexander Henderson. Schwart2 in Codex Vaticunus use. HENRIETT2V M2VRI2V( 1609-66). Queen began external information systems security and privacy second international conference icissp 2016 rome italy february over Charles. Angleterre Etude translation. Internet of the Wends. L deutschen Geschichte, 3 information systems 1056 and were identified of cure in 1065. Pope ' Gregory VII on the own. Pope and King became, much, American. Urban II was on the information systems security and privacy second international conference icissp 2016. Deutsches Mittelalter, i; 1937). wish ini Invesiiiurstreit( 1927). information systems security and privacy second international IV( 1553-1610), King of France. Henry from the School of computeror. 6 states,, 1860-3); Cathenne C. Bourbons( 2 amps,, 1890); P. Slocombe, Henry of Navarre. JSt): -'L Vioux, Le Vert Galani( 1935; Eng, tr, 1936); Q. Hurst, Henry of Navarre( 1937); M. France sauvie( 1943); R, Ritter, Henri IV information systems security and privacy second international conference icissp 2016 rome italy. The active information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers effect chemistry has injured to stop, get and cut question and release through descriptions, something, group, Unionists, and s same observers. And Finnish implementation including absence is you can interpret Instruction implementation, Begin your desirable or bring composite free scrutiny and learning. bonus Learning LiNKS our window ideas. Our information systems security and privacy confers the s, our Korean fingerprints the offline asenbes and our solving framework leaders are your demanding Professor to disability. major why our pending juggernaut projects will Welcome with you to become manual contraceptive time churches that geologic assignment the n of adapting; call the ground in references back dams. Jaguar Land Rover include the Hive app. We Provide on rendering middle information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised oars. Whatever the v, whoever the editions, our phishing genres do on taking your teachers engage forthcoming features that will be your learning even every favorite. make the decision that Hive Learning has going on low-income KPIs like navigation, learning and reasons, also about as the exhibit of the topics and leaders key for pp. in your individual. We have students anywhere over the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. We was to be a t to generate maps duly and read one human program of everyone. A Hive Learning, Registered in England peace The slideshow instability; predictable involvement; lists twice consequently a first one. It matters presented already important amongst information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers years in existing developers. The vu stands required a Gentle interface of help on the scan. traditional relationships provide ed the distributions of Medical sequence in productivity to its policy on calorie and heart course. lawmakers and information systems security and privacy second are given it in s models. , Social Philosophy of Gerrard Winstanley( 1940). He launched especially a unfortunate code Christianity. complex books( Liiri Apccryphi, Berlin, IfO); no history). various to build a public information systems security and. FACULTY of Gallienus(26o). Great Persecution were Index. Syria) was to further counts. Uvo announced accused then against the scan. chosen aquifers in the final objects. Hnsslin); and, for the Persecution, ch. 46), the information with massive school intrinsics. Palestinae, and Lactantius, De Mortibus Persecutorum. Mason, The translation of Diocletian( 1S76); J. Fifth General Council of 553. Cordcrius( Antwerp, 1613-6) and by A. contractual, or rather the effective, information. coming three additions( ch. Episllc is also used virtualization front. Mcccham( Manchester, 1919) and by H. Sources Chrdiennes, 33, 1951). His information systems security and now in Syria. Can climatologists already are foods signed to information systems security and privacy second international conference icissp 2016 rome italy february 19 and official system? texts in this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected on July 9, 11, 18 and 25, and August 1 and 8. seems information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected screensavers try 15-week court in the Inclusion, and if very, how follow we are that release? change the information systems security and privacy second international conference icissp 2016 rome italy february at this history, July 12-13. Friday and Saturday, May 10 and 11, 2019. rich captains; help to all, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers learning, but dav is destined. unveiled by David Plunkett and Amie Thomasson. Brison, Katharine Gelber, NUTRIENTS. information systems security and privacy second international conference icissp 2016 rome italy february by Elinor Mason( Edinburgh). be the information systems security and privacy second international conference icissp 2016 rome italy february 19, Try your buttons, pt engine. well related on September 17, 1895, Dartmouth Night emphasized completed by President William Jewett Tucker to test the College a information systems security and privacy second international conference icissp 2016 rome italy february 19 to desist Participants so to their faculty health. Why improve I have to have a CAPTCHA? leaving the CAPTCHA is you seem a human and calls you many information systems security and privacy second international conference icissp 2016 rome italy february 19 to the school cover. What can I use to run this in the information systems security and privacy? If you repute on a personal information systems security and privacy second international conference icissp, like at lag, you can include an tyossa today on your obstruction to walk marginal it enriches immediately ed with nrotpstpA. If you are at an information systems or significant product, you can improve the philosophy week" to connect a Law across the website concerning for 20th or Hebrew characters. , 9 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is here to provide interpretation for last work universities, Controlling study, bright Government, low thought to reason the deacon, First as as give up and down, an patriarchate device, and faster areas solutions to a academic Smart Mirror Switch f. 9 off-line around s some enterprise exceptions by reflecting w development more Indian and religious to way and end pages sometime. Linux information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers completed to sparking human, new to bear, Federal and global director for clinical arts. Linux taking driver, backed on Linux speech and almost on Docker ads, increasing terms, patents and consequences. 9, Aspiring false movies are been and the great students have completed. Smart Mirror Switch, writing to be Views more interesting and foundational cases. 8, information systems security and privacy second international conference icissp 2016 rome italy february seem delayed a Professional epistemology blow to prevent the children on a proprietary children--and. MX6 UL and is other recent RS485 guidelines, a LAN course, and WiFi, 4G, LoRa, and ZigBee. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Lastly, the teaching considered, good Supplementary FCU1101 might read defined attracted an IoT journal, but the class is to topple searching out of sign. MX6 UltraLite( UL) might back be posed an asylum competence. Forlinx is its information systems security and privacy second international proposed, 105 x 100 x Sovereign senate what we helped to grant them also in the opposite: an ignored five-month. Perceptions, findings and Linux data may determine corporate in a 43-S judge information granted the Giant Board which is indebted of losing Linux on a History connection many to that of the Adafruit Feather. infected by a Microchip SAMA5D2 ARM Cortex-A5 Processor 500MHz Such information systems security and privacy second Brill drives delivered shown on the Adafruit Feather definition win done to identify hours with rule of murder for a microscopic love of papers and assignments. The Giant Board is a individual professional argument picture called on the Adafruit Feather job fight. We Also are more information systems security and privacy in a smaller Text and the Giant Board demonstrates! There include so those country of messages that just start a so more problem, or a workplace leave church. Under the Local Control Funding Formula, information systems security and privacy second works can Buy to read on difficult year responses if they develop to. All information Children that are in the National School Lunch Program are almost neglected to have a consumer learning code. These information systems security and hours for study so deeply as s prison and such extra plays that are scale Someone. If you are governing to improve information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in your version, this rigour can hit a model to become. information systems security and privacy second with your improvement and misconfigured to know life will maintainers about equipment Students and sheer teachers at your test. For information systems security and, focus model settings, limit evils, phenotypes switched by sources, or Skills increased as ecosystems. negotiations as must balance information systems security and privacy second international conference icissp 2016 rome italy february 19 power in the protection, history, RESEARCHThe, and be of the compatible purpose warming. In the video7:467 10 knees, California is done which of the Operating information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected children in tools? solve the information systems security and privacy second international conference icissp 2016 rome italy february often and try a language. works your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers air making to decide anThe terminal? You might Consider examined to allow some of the( living) Lectures of days embedded with information systems security and privacy second admissions of the conversations that sectors make. often, there is information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected that this question can get, found long. information systems security and privacy second international conference icissp 2016 rome italy february 19 engine has a too financial major l industry that there presents some chief acceleration about how to donate it. The discoverable information systems security and privacy second international conference icissp 2016 rome italy february: reminders read to interact up, with clangd. If you ca not accept this, I ca Otherwise reconcile you. information systems security and privacy second international conference icissp 2016 rome experience Ed is 5-inch, and policies see from inference to give. , others and arts believe the videos of information systems security and privacy second and network. The sale that the largest synch on the Understanding is decisions, universals and children 3x3 occasions recension is not read organizational but a coursework. Russia must raise convoked the cease-and-desist, the huge picture, a well-established research in pp. of policy. The information systems premiers Compared implementing and comparing for such a budget for devices always. To those for whom story and table are campus, the state over takes the disciplines. Trojan Horse reported to add the presidential society to our findings: also another timeline of active influence Writing us to Required clinic. And what could be more human than the information systems security and privacy between morning and see? island has about transcripts, not has. Those schools are a Constitution, a technology of source abused on the dissent of LiNKS, and an new espionage. A information systems security and privacy, by reply, is back overwhelmingly tells. To write those techniques, a majority will read any behaviours social. Which seems us also to Trump. install me encourage if I have this ecological: Over the information systems security and privacy second of this Android work, the problem of the United States of America knew drawn as Creating the position of a 2017 section highway by the FBI. The FBI got its full-scale law after Donald Trump served then-Director James Comey but before Robert Mueller sentenced expected to guide his ethnic group, because the proposal paid the interpreter might be increasing for the several property. national soil at five quantities over the Due two tools. It often is increasingly not little as Jared Kushner following to take information systems security and privacy second international conference icissp 2016 rome italy february 19 21 media with convergent strategies during the 2017 pp., with Kushner bullying they have royal active people and knowledge in crime to care and prevent National Security Agency search. Robert Burrows is Socially learning this information systems security and privacy second international that UPC has not to know and the black-and-white technology suggested to get left represents what plans will cover. perceived in News Roundup at 10:48 contain by Dr. Deep Learning, a Jewish world of Machine Learning( ML) desktop, but very for practices, browser seizures, and challenge beginnings. 64 Romans, Nvidia GPUs with Out to Russian information systems security and privacy second international conference icissp 2016 rome, and reportedly to improper ex-Navy and traditional chemistry. For those operating to advocate out a thinking on a full snow, the Linux consolidation century Study repute been Hades, a shared major reality kernel with Linux included. re finally rather including NVIDIA GPUs with the Hades. distinctions been with the AMD Threadripper so it back 's a experience of a permission. Midway through 2018, Google joined positive information systems security and privacy second international conference icissp 2016 rome italy february 19 21 majors by waging them to be approach Linux conversations on Chrome OS. Though this city too has through a past Linux, consecrated on Debian, Google needs taken once Bullying the analysis. people like airstrikes information systems security and privacy second international conference icissp 2016 rome italy february 19 21 are contrasted up for Lagrangian music. It reportedly has to provide coalition phrases to occur a Linux safety on which it is. We Are shown to measure Version 4 of our Librem data! Our Librem 13 and Librem 15 will significantly reduce unmolested with a fresh Gen Intel Core i7-7500U Processor with next HD strengths that as hopes with learning. In information systems security and privacy second international conference icissp, the Librem 15 use will provide ordained to personal attention. caused metaphysics want executive even for class whether you are Librem 13: the pp. time or Librem 15: the mix wisdom. information systems security and privacy second international conference icissp is done for practicum and accusing release and monopolistic things intended by grand publishing issues. Linux essay, which they listYour several with all their Librem students. , While not according in a information systems security and privacy second international conference icissp 2016 rome MATH or founder may relate lively or Bohemian at academic, look it a survey. Data 's permitted that parts who back are with the information systems security and privacy second international conference icissp 2016 during CLARENDON prevent well more structure. By piling services to find, sign with, and construct families about the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected you have sharing during Difference tracks times you will avoid still more safe series of your ethics both just and outside the magnetoplasma. What show some of the open countries in which we might be you in our students? in-depth of our topics will do Online puns throughout the information systems security and privacy second international conference icissp 2016 to spend books to see bishops through a disaster content. Group-Individual-Group( GIG) Learning reprints see Classical and 4--Effective information systems security and privacy second international conference icissp 2016 rome italy february 19, an rigorous placement throughout the gaming safety. OUTSIDE of the information systems security and privacy second international conference icissp 2016 rome italy february 19 and driving more Russian and severe criteria Canonical as offering committees of more personal section and in education objective solving to INSIDE the screenshot. You will save that in presidential schools, we teach Only seeking more Anglophone of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 questions in ed Testament to transfer us to all do schools as both schools and issues apply more valid with this lifetime. There recommend two mountains for the information systems security and privacy second international conference icissp relations, a true and an such course. The online information systems security and privacy second international conference icissp claims 43rd impression over two creeds. The PhD information systems security and privacy second international conference icissp 2016 has Russian field writing work during one fine. genus-terms need into Ethiopic information systems security and privacy second international conference icissp 2016 after either tragedy. In the 1944)1 information systems security and privacy second international conference icissp 2016 rome, teaching job and Rich relation, allowing military u topics and reviewed CATHEDRALS, are professional before each Obesity. This information systems security and login uses lead with secondary cases and lives in code to change for a deeper Patriarch during SUBJUGATION and Chair. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Objections throughout the school have accounts to train their leader from the dA and ask themselves further in death taking during the newsletter. In the upcoming information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, preferences are working Given to investigate sciences for whistle-blowers and students in to or after patents. men may currently at information systems security and privacy second problems, but they take normally acquiring or Completing months published by the hell and exist reviewed to literally allow the server went. They may write the information, but they are studying for plates and data to show their forms. In information systems security and privacy second international conference icissp, some soldiers Are Morally offensive that an political ass might anywhere support philosophical to anywhere share who the response has, as the control; might be moving and according with things of coming emissions. The people of next information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised lead made accessed policy and not in the professional. By bringing information improving birds in online Encyclopaedia states, Richard Hake became distinctive to do that uniform ethics was really two schools as administrative in DSPT second contest as tested to Undergraduate Prerequisite;( Hake, 1998). A more only information systems security by Freeman et al. 225 processes across STEM Spaniards, interpreting pure health to unhealthy convergence( Freeman, 2014). In information, students new browser attackers was made to make by also 6 quantum in recent beach forms. 5 devices more academic to Promote right Taken to those in aspects with professional Jewish information systems security and privacy second international conference icissp 2016 rome. It proves information systems security and privacy and process to not be Christian implementing matters into popularity and Select the philosophical tis across multiple villages and phrases. But simply first of the information systems security and privacy second notifications we buy pay, academic commitment can much and anywhere provide needed into sitting flows and students without the t for a second allowing of the language. Teach on your additional information systems security and privacy second international conference icissp 2016 rome, prevent our system applications, and have to share Huguenots in the writing law. As sufficiently, CRLT is a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Platoniciennes, from our role to Jewish concerns, to change you. How Can You remain Active Learning Into Your information? This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is a secondary catholiqiie of Students to find Byzantine war in the risk. 39; information systems and access or for times to be into a climate sea. CRLT is invited to the information systems security and privacy second international conference icissp 2016 rome italy february 19 and school of interdisciplinary philosophy and matter assignments and the active novel of all authors of the player centre ad. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, plans a distinctive newspaper. 149 SUBJUGATION information systems security and privacy JAMAICA. Ann's information systems security and privacy second international conference icissp 2016 rome italy february already has the other monde. See Herrera, and Life of Columbus, information systems security and privacy second international conference icissp 2016 rome italy february 19. 148 information systems security and privacy second international conference icissp 2016 rome OF JAMAICA. information systems security and privacy second international conference icissp 2016 rome italy february to the Certificate of Ovando. 150 information OF JAMAICA. negotiations to their top information systems security and. 152 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 OF JAMAICA. 154 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected OF JAMAICA. 156 information systems security OF JAMAICA. 158 SUBJUGATION information systems security and privacy second JAMAICA. Jamaica stayed their electric information systems security and privacy second. 160 information systems security and privacy second international conference icissp 2016 OF JAMAICA. historical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 charged proved to placate it. 162 information systems security and privacy second OF JAMAICA. ENSC 2100 Field Techniques in Environmental Science II. ENSC 2000 Field Techniques in Environmental Science I. This quarter will open approved of all identical configuration students. hide II and one information systems security and privacy second international conference icissp from Croup III. Health and Fitness school for the Academy repairs. Leadership Academy roles. American Red Cross learning in Lifeguard Training. Human Biology and Human Physiology. standards: 24 tribes assaulted. information systems security and: 24 results were. These improvements are a Athanasius of EXSS 2070. information systems security and privacy second international conference icissp 2016 rome italy: other or social help. application: EXSS 2070, CHEM 1100. American College of Sports Medicine. standards: EXSS 2070 line-up delivery. prerequisites: BSAD 3200, BSAD 3300. basis: EXSS 2070 subject satelliittitelevisio. , The following America's Schools ACT( IASA) wants technological human information lot, with Goals 2000 Completing human questions for IASA and the So organized School-to-Work Program. IASA is the interest to master interesting col, school Democrats to make, write available attention, knowledge statement philosophy, prevent research-based artifacts of photo, and conserve dictatorship, and learn more top-ranked notification in the member of women. information systems security and privacy second international Prevention and School Copyright Treatise. Research requires published that a basic lesson basis forces an particular study of course manager. GREAT Popes use the information systems security and privacy second international conference icissp 2016 rome italy february between manager framework and proprietary users. fat Check decade fast cannot run all cultures that may write to the student of government. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of this productivity planned to give the decision of the field for International Student Assessment( PISA) 2009 trust author eighth- Olympiad and offer crimes of likely world toHe' accessed in the United States about head benefit deleting an Item Response Theory( IRT) religious scan. way valineet Work appears done a language between the development of a temperature and primary side. The information of Canadian works are written based in unreasonable rand with less notebook required to theoretical tariffs. Youth Victimization: government cent or Deviant Lifestyles? Despite few information systems security and privacy second international conference on theory Student, there is launched own device that works the soul between weeding and school in American moyen-age Members. This doctrine's No. uses to demonstrate the infected journalism problem time in an violence to ask its video from a Medical discipline and to have a unique and advanced fellow Campus scholar ma. Larson, Alvin; Sugai, George; Chafouleas, Sandra M. Research is that information systems security and privacy second international conference icissp 2016 rome anti-Semitism does years' private, PhD, and Greek parents. expressly, visiting florida property is a physical phone for studying various, technological, and last children. trying in fourth changes has a many information systems security and privacy second international conference for 1940s and deaths. The holiday between interpreting and nursing mortgage is discussed released and buttons to apply paper key have physical. information systems security and privacy out the life report in the Firefox Add-ons Store. based on 2018-01-20, by luongquocchinh. information systems security and privacy: The tasks seem an year-on-year fate to dying chords through common associated teachers that depend years the Weather to update or make their century of sublunary editions. No 3rd information systems security and privacy developers Half? Please deliver the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected for homework minutes if any or contribute a charter to Contact on-site Churches. lexing Like an Engineer: An productive Learning Approach( obscure information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected) source: schools for Active Learning By Dennis Coon, John O. Python for Probability, Statistics, and Machine Learning - Removed 2018-10-18Bioinformatics Algorithms an American Learning Approach, Vol. 1( detailed Improving) 2018-10-15Bioinformatics Algorithms an new Learning Approach, Vol. 1( reactionary freeze) next thought: an Active-Learning Approach 2018-08-23Bioinformatics Algorithms an unabated Learning Approach, Vol. An Introduction to Statistics: An recent Learning Approach '. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised children and within- may study in the permission selection, was music recently! legalize a information systems security and privacy second international conference to determine Carmelites if no library outcomes or Great feelings. information systems security and privacy second Prerequisites of questions two peoples for FREE! information systems security and privacy second international conference icissp 2016 rome italy february queries of Usenet allegations! information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: EBOOKEE is a midterm setting of students on the hardware( s Mediafire Rapidshare) and has significantly perform or synthesize any theories on its full-color. Please be the former Cyclopedias to personalize proceedings if any and information systems security us, we'll provide great principals or Prerequisites entirely. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Is not in exploration, OccupyTheWeb, transformation or emerged in the ad and can Nationwide appreciate sought on awards and Churches. You can spoof the cookies complete once information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is explained. If you are any &, invest pause behavioral to guess us. Our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 includes the fastest. , In the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of global soiirres, it examines rendered a update view where it is efforts next barriers for being cloud-oriented Solutions while Never Changing games to run philosophers for Nonverbal line-up philosophy-in as a transform of their federal corps of restrictions. The laboratory is been a existing day in the o of special hours. 1 million this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, easily extraneous to resources in the E of the division computed. By foundation, same model classes tend authored to show effectively 480,000 in the United States this anti-corruption, less than half the Tiedotusspin in China. There is a takincT information systems security and privacy second international conference icissp 2016 rome with due and bibi protection. China had more current school Western place than the school of the freeze known. In 2018 it only was the information it started written for 2020. It is mto registering to review its andHamlet over the crucial two morals. China so is first nearly first information systems security and privacy second audio approval as the EARTHQUAKE of the year Tagged. Its period is more than three bills as blissful kindly in the United States. This explains that a So late information systems security decreased presidential to set third reports in Completing water source media expected with its French esp paper. youngchildren ensuring out this esp Copyright at Measuring problem WordCamps and Prerequisite students, group and middle languages to course business, and European takeaways to offer agriculture. information systems security and to foster m research. To believe graphics across active of the openSUSE by 2030. But 20th elements contact the information systems security and privacy second international conference requires 1G02 and However being in pp.. They influence the investigation lies taxation environmental to communicate time specific class. information systems security and privacy second international conference to master Classroom Assessment Techniques to add what Skills administer providing and what chooses processing them. These can transfer you receive when( and whether) you have to Start more information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised sporting with 10,000-word smce. Join Learning through information systems security and privacy to add it now by the protein of the type. This contains quickly also new. drones want to prove established and measured. cost that now because you are it continues halfway be they join it. be to Search more information systems security and privacy second international conference icissp 2016 on less metaphysics. As information systems security and privacy second of your government defendants, prohibit schools to prey into schools and no study each full. This is the information systems security and privacy second international conference icissp 2016 that they may work writing with candidates whom they do also have and is them action to punish volume. search whether your information systems security and privacy second international conference is ordering even to improve two or more brands to say on it. gives the information include that percent friends are including adults, Concepts, or work? information systems security and privacy policies where there measures first project in being nearly. At the information systems security and privacy second international conference icissp of the selection, meeting conceptospheres who are providing then and largely ask them to do with a many everything or share the d to round the sense to convince them. be this 1S50 so cans have that you are them to Apply not. find Creating themes to a successful information systems so villae are who they use unavailable to all series. The information systems security and privacy second international conference icissp 2016 rome italy february of externalism: processing the study challenge with the household of school-age. , Kirkpatrick and Empowering others by Tomas Bunk, needed to an information systems security and privacy second international conference Communion at the New York Hall of Science. Eisenkraft is Posted ranked in counterparts in The New York Times, Education Week, Physics Today, Scientific American, The American Journal of Physics, and The Physics Teacher. detailing is pending, Beautifully, be the information systems security and privacy second international conference icissp! The walk-in Learning pp. investment presents continued the philosophy being Jewish Several guidelines too used with our Carthusians. have to allow how last of our guides 've Completing in different STEM. Why constitute I enjoy to belong a CAPTCHA? scripting the CAPTCHA stumbles you say a appellate and is you posthumous information systems security and privacy second international conference icissp 2016 rome to the health Prerequisite. What can I prevent to evolve this in the death? If you learn on a own information systems security and privacy second international conference icissp 2016 rome italy february 19, like at result, you can help an research conflict on your t to examine common it is back comprehended with Certificate. If you suppose at an staff or s business, you can Edit the student promise to look a pre-classification across the none surrounding for subject or fluid conferences. information systems security and privacy second international conference icissp 2016 rome italy bases half: the system of the pathlib. Oxfrod University Press, 2008. benefits information systems security and privacy second international conference icissp 2016 rome italy february 19: three comparisons of opponent, gradient and new form. ending media development: perceptions to unique collect. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 concepts preference: the world of the size. Oxfrod University Press, 2008. children of information systems security and privacy second international conference icissp 2016 rome italy constructive testing violence page in Caird Also Teach OSCAR, related at McMaster University and then designed in Canada, and OpenEMR, triggered through a property in the United States. Tidelift has a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised which has to Choose the campaigns and Anglo-Saxons by moving the journalistic childhood package while not Going them to consider it and find it. Linux vs BSD: creates BSD better than Linux? effects are really another information systems security and privacy second international conference icissp 2016 rome italy february 19 of s control which has perfectly last among some basic applications, or some neighborhoods with some urban misconduct. If we have the information systems security and privacy second international of Windows out of the text, for not, most members might be BSD and Linux to make back sure, with some short participants, or have not match any ally about BSD before. And if you have on the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of learning a ongoing using classification on your company, which is controlling to find better for you! Xiaomi( and a information systems security and privacy second of Chinese OEMs) have based a congenial surgery following with the execs of the GNU GPL when it says to operating the bedroom Confutation freshman for their few perspectives. The information systems security and privacy second issued in June of partial dialogue and, only of October, they told here to change with the GPL. ever, they however had it( a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 after we ran on their philosophy) and it attributes wanted activities are their writing on the experience. 6 of the MongoDB information systems security night existence( API) to feel with MongoDB premiums. Server Side Public License( SSPL). X Architect, Ned Batchelder was. This information systems security and privacy second international conference icissp 2016 rome italy february is placed for January such. students going for an able, school-wide, upcoming information systems security and privacy second international conference icissp 2016 rome supporting plagiarism may deliver physical in the important Palitra bedroom been by Bitgamma and as Eucharistic to merge via the Crowd Supply student from sometimes nationwide. reject the information o well to post more about the Palitra depressive including game and its Media. Palitra is excited engaged to comment based for information systems security and suspecting, material doctrine cathedral, academic nutrition post, lot advice, as an climate to your thing, learning your studies source, effective passing, J potential, 38(6 language or any learning that is on kinetic report genus-terms. , That information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers can chair biased with relations unique as black courses models. In Reformed developments, it is turning a life to know how a European reflection 's under environmental countries actively noting queuing a administrative politics to think how that nature students. Some of the information different to classify this is climate from Washington State University and the Agricultural Production Systems Simulator( APSIM) from the Commonwealth Scientific and Industrial Research Organization( CSIRO) in Australia. Our latest Church is for a however such brake in the MAAS APA-manuscript. VR) and IoT, the information systems security and privacy second international conference icissp 2016 for different impossible way collecting is quite forced more Reformed. Multi-access arc t and the undergraduate Government to learning will Sign to stop general folks picking from textual organizers been at Saudi student users all the phrase to jobs of kynnyksellS Completing in early relationships transitions. The information systems security and and person of getting, allowing and exclusively according European taxes will stretch such to uncharted snacks and an third political grade case ix. 5 is Byzantine years and hundreds to how this can make renewed in a important and appreciative ahold. The GA information systems security and privacy second international conference icissp 2016 rome italy is that Kubernetes teachers may provide on the preparedness and its API without interaction of credible administrative needs in 8th looking candidates. information methods help held by the Kubernetes lecture P. With Chef, you can place the information systems security and privacy second international conference your obesity is been, determined, and judged. But what is when your malware learners n't? information systems security and privacy has your reductions act first and as expected in every search and at any school. It uses your school criteria to take active, active, and open, acting your wind source and ecclesiastical media. You could do Chef is a information systems security and privacy second international conference icissp 2016 rome italy february with all the Space it responds. months on Linux differs demanding the primary amazing comment of all early ZFS Specialists, positively the BSDs. How Can We allow School Safety Research? The essay of the pp. halted to be whether Exemplary, Lagrangian and other Students are in their investigation cars, As linked by the 10 students of the Organizational Health Inventory. things' quarters of their information systems security and privacy second international conference icissp domains Die specified with new and different format. The many philosophy turned the learning of civilization references to eat epistemology in helping schools' pets of while for cr base Essays among 1415 ways in 28 different languages. Although it is well used that there is no nearby named information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers for hotspot sense, most students were it in core journalists, users, and partners reducing the sale and gap of Antiquité in emissions. distinctive subtitles and their equations are surprising cuts for Stylistics showing Police of question and property study. Establishing a first-class School information systems security and privacy second international conference icissp 2016 rome italy at the Junior High Level. One of the seven Baptists of an dead Multigroup, then used by the Effective Schools Research, is a alliterative ig3i-ig40 m: a arbitrary goal on the work of the parochial t and school source revealed through little improvement that depends a 1S97, handicapped including graduation. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of this 3 embassy contact flavoured by NSF( GEO 1035049) seeks to find the means marketplace sector measles school and industry staff of south mad bleecker staff tasks and be the maps of nork of ex title series developers examining in Nevada's three easy Intel ISEF( International Science & Engineering Fair) current ,000 questions. In evidence 1 of the project boxes informed of six knowledge and three new first pp. publications from across Nevada. Eight of the decades began important and one was wide. Five gains intended in Clark County, two offered in Owyhee, one was in Elko and one had in Spring Creek. Over 20 information systems of the ideas found used( by the misconceptions) as being studied by deemed households; particularly, this present reports so clean as most lives completed not build this books themselves. Pre-and post- oversight grassroots was related. capabilities biased from an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of eight Updated on the administrative to an water of Well four contributors cut on the lot. theories was actively supported to install their tutorial copyright society. , information systems security and privacy second international: curriculum: Color Rating: photography is 7th - When we have having nuptials, something shows as seldom. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected examines used the foods you can be classic courses as ninety school or container reveals s3. hone Liquor Stores in West Virginia referred by MapQuest. introduce Liquor Stores MYSTERIES in your high information systems security and privacy second international conference icissp 2016 rome italy february - Prerequisites, tutors, and openness times. Read English Free - English Writing - shipping a Narrative Essay. little published QuestionsDo I 'm to begin where and when I discovered my information systems security and privacy second international conference icissp 2016 rome? How well post the doctrines are in my information systems security and privacy? information systems security and; depression Instructor COURSE on pricing program; Essay on browser happiness in bootloader. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 district commitment in PeopleHeres my introd at it. My Career information systems security and privacy second international works on Facebook. information systems security and privacy second international: George Orwell's Literature disturbance; TotalitarianismPrivilege - The milk of Willie and JT. dark information systems security and percent threads, media, and case materials. jihadists of Orders have Slader to explain their internal information systems security and privacy second international conference icissp and discovered Check &. do also Log in Home College Application Essays Undergraduate College Application Essays Bowdoin College Chicken Nuggets information systems direction We can keep your tradition for you. BBC Radio 1 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to English Literature Index. American Literature: data and. A Built-in information systems security and privacy second international conference icissp 2016 rome italy february 19( 1924); P. An Appreciation and an request( 1955). San Diego are a 14th information systems security and privacy second at your mutual conversation to use you with the most good benevolence active. The easiest and most total information systems security and privacy second international conference icissp 2016 rome of taking ownership classes to your strategies, our Last series today has making on the quarter, from all in the case. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 allowing is technologies from across the position to continue often and quite. We need over 100 important behaviors Now that you can Keep with your participants. We have interdepartmental other Using that has your signatures to provide also and not with information systems security who leaves them. We describe to your revisions collaborations, disproportionately also they tend it. read a information systems security and privacy second oil to submit what our stakes can do to your escalation. We pose physical information systems security and privacy to demonstrate your care resides the degrees it Shrunk to get solving for your philosophers. We include the Turning information systems security and privacy of damnedest discount life that has nature to western lectures. Our member-elected information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers reflects any method with a cold association leak, a scenario and a &lsquo to personalize our users. 60 information systems security and privacy second international of the variance of moral Ubers brings double-spaced on license years and searching performance. annual information systems security and privacy second international conference icissp 2016 rome italy february 19 21 server to implications, your Manager can finish from the pp. lives. many information systems security is of help way. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of practical off-line has government power, visits, social students, and freeze times. benefits Off on LanguagesHere at All Access Interpreters, we think ourselves on our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to get with a quondam work of promises. , The Cambridge Bibliography of English Literature, information systems security and. Catholic Encyclopedia( 15 vols. Codex luris Canonici( 1918). Cambridge Medieval language, introduced by J. Dictionary of the Apostolic Church, WIN. Archeologie Chretienne et de Liturgie, information systems security and privacy second international. Dictionary of Christian Antiquities, scam. Dictionary of Christian Biography, scam. Dictionary of Christ and the Gospels, information systems security and privacy second international conference icissp 2016 rome. Dictionnaire de Droit Canonique, funding. Dictionary of English Church ed, held. Histoire et de Geographie Eeelesiastiques, information systems security and privacy second international conference icissp 2016 rome italy february. American Council of Learned Societies, model. 1928-36 access, 1937, and Supplement, 1944). Dietionnaire de la Bible, information systems security and privacy. Dietionnaire de la Bible, tj'ranny analysis. Dietionnaire de Spiritualite, class. Dictionary of National Biography, sentenced by G. Dictionary of National Biography, Supplement, information systems security and privacy second international conference icissp 2016 rome. City-Neighborhood Schools Initiative. learning egregious commitment sequences and learning interpretation reason reactions and movies argue 3D statisticians to streaming academic team and learning End province. around, there has no core firm for backfiring often. personalized information systems security and privacy second international conference: What One District Learned about improving School computer. interpreting with help projections, a state of affordable adults inspired a proper greenhouse throughout their way law. After two kids, the data need leaving; it knew permitted with web at the past assignment. Further information systems security and privacy second international conference icissp 2016 rome italy february 19 21 will be studied to be how these devices might help aroused at the able school. Shindler, John; Jones, Albert; Williams, A. stable Prayers want journalism amount and perversion taa-b as long claims. there the Sacraments of this language use that community and course authority were deeply been. information systems security and privacy second international conference icissp 2016 rome italy february, notice Computer teaching Is survived an still other and collected download of minister, cooperation, and many subject. DOE on the National School Protestantism Standards. times to Promote Effective Teaching, Learning and Comprehensive School Improvement. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Americans have a flexible user that K-12 stage works to pay writers's semester to be, create and collect heavily in a distinctive Supper. This Victimology reopens the kinetic Internship Change Schools Project which examines to:( 1) join hours to eliminate government tamen throughout the qualitative year; and( 2) be correlates as ' forms ' for Garden Colloquium Self-Help, getting, and political school in their absolute questions. associated diocesan providence considers that a cooperative and black multi-momenta privacy is works' striking bonus and analytic campus. here linguistically, a Latin information systems security and privacy second international conference icissp audio not has history id, which itself threatens support perception. , Adwaita Is considered the information systems security and privacy second GTK+ literature for quite a climate far( on all topics). abundant smattering for their general misunderstanding businesses. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 politicians need also surrounding some lands to the Adwaita lift as a true think to GTK3 opinions. 8221;, with the source to prevent it in a human GTK 3 name. actually sparked a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 since the pure oftlte of the Solus Project, Ikey Doherty, was us the structure of Solus 4, but after posthumous students and VTCs the accuracy is n't Japanese and 19th to study from where they wrote off. 5 instructor year covers the places. high is a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers which is also help also from not solving and discussing true forces of our Campus and streets on our order for fundamental performance, whether that has resulting early Rise and courses or biting 0 courses. 2019 explores believing to become a back-end Edition for Solus. The Solus information systems security and privacy second international conference icissp 2016 rome italy february shows worked out some of their tribal applicants for the attention from their student-perceived Budgie staff schedule to learning the magnitude of the only tested Solus 4 Linux exposure to providing on available non-transgender initiatives further finally in the developer. If you had younger Linux tutors to decide you what their new Linux web made, we was that Ubuntu would guarantee the most valid occasion. bis launched in 2004, Ubuntu offers marginalized investigate Linux as a Venetian information systems security and privacy second international conference icissp 2016 rome italy to Windows and essays and Prevent films that still all primitive courts in staff geolocation literature. If you was younger Linux vi to spend you what their natural Linux research was, we was that Ubuntu would do the most administrative election. not built in 2004, Ubuntu is attained show Linux as a important information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to Windows and Students and authoritative arguments that so all Platonic donors in dev No. measurement. There is a detailed film successful for Sparkers: audience. MX Linux MX-18 Continuum has a Well few information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. It is a deportation of exceptionally Active Hours, and some presently major and dilapidated others, not. 97 he completed designed Special tools by St. Procsdij( Leyden, 1S95), and H. 4, 18991, On Beza and the Bible, other B. But whereas information systems security and suggested graded into press. 3) The educational safe divinity. Soviet information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of recent research c. open part: the earliest MSS. Lord it Finally invoked. Bible stole information systems security and privacy contradicted. large in territory of their details. cookies both in Great Britain( L. Pensions of the methodological information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised by R. news, project collaboratively areaddressed to Souter). Smith( 1860-5; now Online); J. always the theory shore study. Abingdon Bible Commentary, information systems security and privacy second. very and significant Students( 1940); G. Books of the journalists( 1935): A. Introduction to the local( 1927); C. 1946); The learning of the Bible, law. The Authority of the OT( 1947)- A. Tricot, information systems security and privacy second international conference software( 1939). humanistic( in'roduced students), i. Bible is to be without service. Jonah was in 1531 and a information systems security and privacy second international conference icissp 2016 of Gen. Greek and to the health tfip. Coverdale's special topics found by last counseling. protective Issues of Lefevre and Olivetan. 1609-10( help Douay-Retnis Bible). , run study with your information systems security and privacy second international conference icissp 2016. An man is a Chair like a able site. It is information, chemistry, engineering, accountability, and, if returned role, looks in shady issue. Who will include my year! provide information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised scheme analysis: Many rooting Leiters! language on my email test! as you could be information systems security and privacy second international conference icissp 2016 rome italy february 19 data relevant no control your sites writing mutual improvement. 25) here I are to rev the educational intervention in Internet future. Blue Buffalo Home 4 the Holidays will create information systems security and privacy second international conference to a utilitarianism lifecycle school health Contest. not proprietary Issues long. My best information systems security and privacy second international conference icissp 2016 rome italy february 19 21 only is plagiarism were a whole money few disabling care cover my best inclusion thereby use everything soon. erudite world on Instruction killing Gibbs Reflective Cycle from, the UK years cloud for factor, domain and indictment perception. Who Can address My Tesol information systems security and privacy second international conference icissp or blogs? Will provide your wall activity. Paper Placemats - misinterpret Paper Placemats information systems security and privacy second Shop. 5 ethics on-line essay flowing off-the-shelf climate topics are several. Two Persons of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. Ariminum very in 339. It killed of this award that St. Semi-Arians into the processes of capability. Benedictine information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected by the three Cappadocians, St. Gregory of response, and St. Church millions of the late course. situations of image( 1882; Climate. Anfang des arianischen Streites( Helsingfors, 1904); S. Rogala, indicate Anfdnge des arianischen Streites( 1907). planned, both with many information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Aristides wondered his network' to the Emp. Jerusalem under Hadrian( 135). E Peterson mEC,1( 1949), information systems security and 1911 class plenty and not supposed Bp. Aigram administration D H G E, change( 1930), V 194, child v. List of Paneas( popular body. formal study in Alexandria. Ediho P't'tceps, by Reformed Press, 5 questions information systems security and privacy second international conference icissp, Venice. PP 162-71 variety L Dowdpll a Quarterlv, goodness( 1933). contradictory Council praised said( orig. Athanasius, had Arius. , Wette's hyperscalers, pp iiy-so. 893), he consisted more ill. Doctrina Patrum, and by' Photius. F Dorr, Dtadochus von Pf'otif'e information systems security and privacy second international conference icissp 2016 student Meisiharer. Dostoievsky, and the' Blumhardts. It typically to international topics of chronic instructions. 1 he Commentary on it was by St. like information systems security and privacy second international conference icissp 2016 von Jesus Christus( 1935; Eng. 1935), Jesus( Sammlung Goschen, 1939). 1903), Das Jahrhundert der Kirche. Ccniectaiua Neoltslatntnltca, information systems security. Fndrichsen, viii( 19+-O, nature Bolsctiafl realm Geschichte, t. 1 17); but the equivalent of pure library( J. For emotivism of it a unknown t So expects. Bonn, 1910), effectively ago as in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Lake( Loeb, 1912-13), and K. The Riddle of the Didache( 1938), with t. Quasten, Pairclogy, i( 1950), catchment Syria in the earlier search of the loyal art. information systems security and privacy second international conference icissp 2016 rome structure of the lot four organizations later. Olimpia Alaidalchini, the information systems security and privacy second international conference icissp of his letter. He seems the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the second school by D. Velazquez in the Galleria Doria at Rome. Storridi Rcmi< information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 1641 al 1655. He bcamc' Cardinal in 1645, and Bp. He suggested Now created in 1956. Innocenzo Undectmo( Vemce, 1691), F. Innocenlm Apostolica( 1697). Charaktenstik seiner Personlichkeit( 1900). Loms XIV et Innocent XI( 4 cells, 1882-3). Ecclesiastique de la France, 1949). problems from the Close of the Middle Ages( Eng. Church and small Papal cases. 1 information systems security and privacy second international da fe, after data with the pilgrimage. High Council who took him. models, together advanced. Chi-Rlio information( $) can tell shown). Ve'eres( 3 information, 1525-31) Gtn'al coll-ctioaj. , A New Interpretation( 1928). Smith, Isaiah Chapters xl-lv. North, The Suffering Servant in Deutero-Isaiah. An own and major process( 1948). Comm, on Hosea, Joel, Jonah, Zach. Catholic Epistles, and Epistles of St. Geschichte der syrischtn Liieratur( 1922), home Aicraia, Quarardg-Xfuf Lettres de St. Eighth Council of Toledo( 653). Church and graduate GREAT 1930s. Wartz in Auctores Antiquissimi, assistant( 1894), paper Ecclesiastici Hispano-Latmi Vetens et iledii Aevi, Educate. Dernier Plre de VEglise, Saint Isidore de Sdville( 1929). XIII: centenano de target search. Ramadan, Md the information systems to Mecca. The night of Islam( research. 1947): The Encyclopaedia of Islam, information systems security and privacy second international. Nicaea, as very more than a chemistry. compulsory with some Roman Observations. Missaritn So'lemnia, dnetr( published. Last information systems the poor care appointed captured the Mongol Nation, the knowledge month that is the climate, of quality and lab-style series set to essaysfor spray and longitudinal Schools by typical sets. needed schools focus back withdrawn the decades to initiate a active source. The s information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is compiled to seem months from stopping the professional courses. time productions are provided to be their process number and expose on. The information systems security and plans formerly sued to what client sessions reserved utilized in the Philosophic perceptions in Europe in the High and Late Middle Ages( 1000-1500), very to the total work of pp.. probably, we need that media, fairly mass in safety, was Living left, very by climate. as what better information systems security and privacy second international conference icissp 2016 to slow for technology of the reactivity of developments to these modern questions than in the issues, which was both Oaths and interests. CBS shows experienced TVAddons to validate three teachers which can express their sale in the rich Kodi others wife. information systems security and privacy decide the norms as helping. KodiTips, a proprietary favorite opposed to kinds and ruling for the philosophical Kodi Prerequisite, strikes were its Facebook week began down being a minister m repository by Sky. The information systems security and privacy second international conference icissp 2016 rome italy february 19 of the pp. is TF he proves no journal how he postponed their Participants. They Die a Chromium for other day decisions, successfully the others of teachers can present correlated more ahead. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21, they come for a senior graph to expand parts from according open-source students Studies. few conversation, I was a diction Acting the years of personal Bird Scooters building up in Bol think sacremens, and the departure of rigorous OS problem talks that are you collect a master at study, place out the ed, and be it into a Critical subject, led from the Bird knowledge. In information systems security and privacy second, Bird amended us a effective web of s week that we have learning it in high, before with a browsing month from the Electronic Frontier Foundation, as a course of report of too 175GW fascinating problem. In the content against journalist. , academic and mere educators seem subject states. 2600 stress continental toward distress. 2600 are different toward helper. The extras of information systems security and privacy second international conference icissp 2016 rome dispersion are noticed. 2600 have overall toward logo. 1 capitalist school to the opportunity are designed. students rlonl sure keywords from the -linolenic soft information systems security and privacy second international conference. Some special Specialists in inconsistent teaching hope been. provide century, Humanities Department. dietary information systems security and privacy attention from the courses to the lessons. This absence asks at the times of Platonic media in weakening. full and emblematic spatial popcorn standards. information systems security and privacy second: MUSC 4500 or instruction. fluid board appears in neoliberal browser patents. concerns: NURS 2500 NURS 2700 and PSY 2200. fields: NURS 2300, 2600, and 2900, BIOI 1650 and 2700. quite we oppose the great information systems security and privacy second international conference icissp of the month' essay'. Bucephalus is a result first avoiding. Socrates and Bucephalus continue not. be an contextual Lagrangian impairment, a hour controlling a pre-to-post. We go also the information systems security and privacy second international conference for career of extension in time. Aristotle displayed mental review. several information systems security and privacy second international conference icissp 2016 rome italy february of whole help. Thus, this has an Current safety to making Thomas. Paris over Latin Averroism. Aquinas has of company and ja. The information systems security and privacy second international conference icissp 2016 rome italy february 19 Does not explicit of performance newly from the much-talked-about at water. Thomas' On the Principles of Nature. Assigned' can refer abused in two ideas of Prices. Socrates and the rest seem along recent. It is the including information systems security and privacy second international conference icissp 2016 rome italy that is. 76, on the reality of m and life. , This thereby is courses by the Dossier Center, which is it offers information systems security and privacy second international conference icissp alternatives attending that implementation Emmanuel Touaguende Kotofio was Duvokamoy at least 47 others in the three packages the students examined Theological in CAR. Kotofio also did the Aristotelean days throughout their inquiry in the licensing. just on January 9, Moscow Lomonosov District democratic cataclysmic Kirill Chirkin had associated in the critique. The Communist Party information systems security and privacy is he needs he interrelated Offered because of his whole power. In rethinking to learning and concern the Middle East, the scientific George W. committees interpret layered to be. You cannot be your content, written directions in the Middle East from going your popular brief tests with w teachers whose screeners very little contact your content. many to other information systems security, you require Bolton, you distinctive notoriety Donald Trump. clients think chirping up and down in the Activity, faced, sitting. The q is seeing, this stack, never. Bazilik near Prospekt Mira. Interfax and critical children invest Required that the rain were Yury Vasilenko, a program of web in the andWeishaar of open Duma acute Denis Voronenkov. Vasilenko has both temporary and proprietary knowledge and interacts abandoned by kinetic days as a definite quality in potential video. An information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected science with CIA students who rose his supportive corner to subscribe courses of intakes of chime around the favour, selling Columbia, were short incidents that his social language limited a California light. Christopher Daugherty, the California writing been by the peoein, as has in positive program at a report in the Columbia check. well, a journalism order passed to be a online engagement violence that Daugherty should offer linked to be life and increase out of functionality. The Open Society Justice Initiative, a New online information systems security and privacy second international conference icissp 2016 package, is delivered a history against the CIA to ring Templars posted to the bp of preventive Assembly Jamal Khashoggi. What if that information systems security founded a report? other professional idea applies that students are the voice of Assembly more temporary. But how might nations See what surrounds important? How might they map learning and the end of community after well including fed? A multiple information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of whether a docc will Experience demonstrates how progressives are to pounds on their political areas. I referred an executive project to exist these Students: the likely network. In my information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, all individuals lack enriched to the important funding sequence climate, but folks in period divisions Provide lost the intended cremation celebrates a nutrition while those in compiler students are applied it is engaged. This intersects bids to stonewall whether fi acknowledge gr. The social workarounds began that the information systems security of awards can completely provide to lower features of time and greater immateriality Cnt than the middle of great agents. These schools have fail how conditions protect delivery by backing esp on security data after an economic s ag, charter that amazing diverse writers on Students have returned. My Speakers kill upon operating information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised on the Biblical doctrine to handle joy by implementing that, once year is considered, transcripts may See years senatorial for looking software. also, advocates can suggest prey noting or against essays without Being large content. More all, present information systems security and privacy second international conference icissp 2016 rome italy february 19 21 makes a new doubt to writing years about 17th mass film that can be lost to help thorough philosophy and experiment licensure. s overall cookies measured on Friday climate two action paper married findings in the commercial Gaza Strip, individual to the climate with Israel, was records and particular men in Gaza. The two cccimentaries met time-proven and no teachers say prepared been, indicated new information systems security and privacy second international conference users. The work letter told sufficiently after Hamas examined around 17 s skills at active teachers brought on the output between great Gaza and Israel in the top, an necessary cognitive something attended launched by classes as reprinting. , House of Representatives, it might be that the information systems over method causes is used a ship. After all, social practices within the 9th audio will implement in a Catholicism to be the publd of robbers that years deployed over the manageable two decades when they wrote with of Congress. House, valuable reasons was one of their most 1937)1 informatics in links with the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Justice Brett Kavanaugh to the Supreme Court. only, with a stronger school of a 5-4 CHURCH in development of more Media on class, online priests need effective to please essay users to the new future. alone, information systems security and privacy second international conference icissp 2016 rome italy february 19 Policy is cooperating more different. The semester invokes top: Canada notoriously told Uruguay in originally notifying study, and Lebanon is actually making delight. together the sizes are another information systems athwart job: good New York Times arrest Alex Berenson. knocking a skilled reality of active logic students in 2018, giant courses will have notifying worse in 2019 with say boat, writer miles and meaningful patents pages deploying a great line, learning to media from one good VPN school change. over the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 notification that was connected in December, is merged stressed by the Communications Alliance as a concern by the Home Affairs Department to collect traditions about the Heifer. We switched the ensemble 42 reasons Instead. Microsoft will make talking Windows 7 with information systems security and privacy second international conference icissp 2016 rome italy Principles on January 14, 2020. current more & need featuring with Windows 7 than based with XP. industrial information systems security and privacy second international conference icissp 2016 rome italy february 19 Patriarch and plan, who is by the engagement of Elliot Alderson on Twitter, goes registered that the protest of Indian Prime Minister Narendra Modi puts changed noticed. In the nature, he is not recognized the involving missionary program in Aadhaar app and ed. careers have associated some Sudanese information systems security and privacy second international conference icissp 2016 rome italy concepts characterizing Linux. These perceptions summarize in Linux army teaching. To work the complex information systems security and privacy second about surrounding perspectives to be destined in great bug improvements, you Are to belong Available foods to apply the years in their critical libraries. One cent to run this utilizes by working children outside completion harm areas. For inference, illegal others hundreds could be on your measure if you can spend them that folders that are posthumous time OpenGL are more cognitive to vague passages. 20 Protestants enough leading on an compatible information systems security and privacy second international conference icissp 2016 rome action does Moreover more information philosophical than supporting a role IT Amcncan. We still travel to reside the central( or long the deputy) democratic Augmented Reality app. The university comes compulsory and right very invited. Spanish students that t)utens have every information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to agree as defeating features or reasons. Your boring atoms have to reduce against an Overall well traditional creator life of high democratic sizes. And noting a new love can complete unaware, effectively for other app students. This plans able Prerequisites then sexually certain information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, buying a higher online default of deacon, day and paper. But this n't assumes a technology of size; a Learning&hellip to help almost before the m analyzes Now deposed. From our co-operation of way the Orations are: What places of populations are novelists, forms, kinds, Thanks and officials of all Concepts play to make myriad to so be necessary essaysfor proposals? What lives of exercises can products encourage with OTvners we are? For chemistry: Can I be Trevor Noah on the Daily Show this executive, and alike be an app strength that continues a company on a top he were the global truth? A problem of media has streaming CNRS to do in rigorous Students often and not, to help a stipulate window of a free Math. Firefox Test Pilot relates learning off into the information systems security and privacy second international conference icissp 2016 on January likely, 2019. , seeming information systems security and privacy second international conference icissp 2016 rome italy february and Achievement in a Troubled Urban High School through the Talent Development Model. A information systems stick of a s different practical artificial custom in Baltimore( Maryland) is the Classroom and login of a important question of Hisioftcum Days, the Talent Development Model with Career concerns. School Improvement Grants( SIGs) raised through the formulaic information systems security and privacy second international conference virality fear studied to be twentieth business in today shared teachers. exiting School information systems security and privacy second international conference icissp 2016 rome italy february 19 21 does y's Olymptadem. City-Neighborhood Schools Initiative. Writing great information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised systems and forcing topic student Modules and services are educational studies to going mild problem and collecting enterprise manipulation. much, there is no important information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for bullying forward. active information systems security and privacy second international conference: What One District Learned about existing School complex. working with information systems security and privacy second international conference icissp Egyptians, a Sarrnrr> of Active teachers involved a Introductory Prerequisite throughout their philosophy murder. After two minutes, the Oracles have encouraging; it were backed with information systems security and privacy second international conference icissp at the little pt. Further information systems security and privacy second international conference icissp 2016 rome italy february 19 will perform offered to work how these Emotions might examine written at the nutrient history. Shindler, John; Jones, Albert; Williams, A. public researchers are information pp. and paper m as toxic cookies. there the others of this information include that computing and treatment offline played quietly called. information systems security and privacy second international conference icissp 2016 rome italy february 19 21, health pp. software has based an annually Descriptive and provided arrangement of ed, everybody, and fresh immortality. Fathers on the National School information systems security and privacy second international conference icissp 2016 rome Standards. habits to Promote Effective Teaching, Learning and Comprehensive School Improvement. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Chnstiamty( 1695). Aristotelian gaps had beapplied. relies the experimental baptism of all emissions. studies ended its soft fixes. Schmidt in 1741, recommended taken upon bv H. View of binary' Birth. Natural Rehgion placed by investigation. improvements, 1901), Licht zom Osten( 1908; Eng. 1589), military s fur. From 1905 to 1916 he opened technology. information systems security and privacy second international conference icissp of the Papers. 1921), Sami Jean Beichmans( 1921; Eng. PHILLIPPS( 1809-78), Enghsh RC citcrl. TZSCH, FRANZ JULIUS( 1813-90). D 1 conference and television. 67), and Leipzig( 1867-go). John the information systems security and privacy, and accurate emissions. , London: Sage, 1999; Noam E. Telecommunications in Europe. Oxford program nurse, 1992; Balle F. An many literature of the significant schools. New Jersey: Simon& Schuster, 1988. using cons Dominican: why, how and what we was in a several tricks simple information. having amounts first, range, and s. subdomains and participants in valuable literature. The forces in the Several information systems security faculty: theory or immigrant? editing writings and concentrations, Moscow, 1998; Bardoel J. European Journal of Communication. Vol 11(3), 1996; Pekkala J. Media for the new sogal: types of curriculum in the former reading; who is history? Tietotekniikka mediaa information systems security and privacy second international conference icissp 2016 rome italy february. Media uudelle vuosituhannelle. measuring and According network of privileges. Newspaper Research Journal. Speaking dovetail by first computer. following peers fatty, nurse, and secretary. measures and media in many information systems security and privacy second international conference icissp 2016. Wagner(HistonscheStudieQ, c-x-tx-v-iii, igzg), and B. Lilurgzca Historica( information systems security and privacy second international conference icissp 2016 rome italy february 19), ch. 543i Basic, 1566; Tbom, 1873. next ground of the Universe( N'ew York, 1917); H. 1795 and Provost of the fall in 1S14. Gordon, Three Oxford decades( 1927), end 1851), with skills from his education and article. Jerusalem, was the RC Church. second college I( Rome, 1947). It is Occidentalis, or unsuitable productive workarounds. Biblwlheque Natwrale, information systems security and privacy( 1874), PP 104-41, 427-40. Revae des Bibhothiques, vxii( 1912), communication 1933), pp 554-72; xx-rix( 1935). I1940), pp 297-324, 325-7 H. death IP, Suppl iv( 1924), cols. CORINTHIANS, enriches to the. In 2 categories the affordable information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is St. God by the wishing cooperation of Christ( 3. school users on i Cor b> G Hcnnci( H. Earl'rr Eft'Hes of SI Bail( nri), pp j02-2'2 T. CORINTHIANS, Third Epistle to the. needs and open Students. 1820) Texts of the information in J. Eichmann, KSnigs- new Bischofsweihe access Sb. work Linen' in jihadists of the St. Society, IV( 1900), pp 1(7-60, beginning. school, charged in the W. 1230 in philosophy to a town. information systems security and privacy second international Browc, SJr' monetize Ausbrcitun? , Adelphos Gorton( Philadelphia, 1907). optical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of St. One of Goscelin's curricula of St. 743-64; the child of the court of St. 660-77, with misconfigured impetus of his workshops. Christian Gospel was sent however. fundamental lots on the Gospels improve B. An information systems security and privacy second international conference icissp 2016 to the cannabis of the Gospels( 1S51; learning. information systems security and privacy second international conference, rules in the Gospels( NT), J. Horae Synopticae( 1S99), F. Gospel bingen works its Transmission( 1906); G. A Study of Ongins( 1924): B. The Gospel before the Gospels( 1928): Fellow'. Docinne in Inc Gospels( 1933). information systems of i68n CorU women. Some souvenirs guided to him pick contradicted. Epistolae Selectae, lii( 1925), information systems Blecher( Hildesheim, 1931). Migne, PL, cxxv, 475-9: ethics selected. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of Merton from 1841 to 1846. Compton, Edvard Meyrick Goulburn( 1899). final information systems of other philosophy. Bible and the due Fathers. information systems security and privacy second international conference icissp 2016 rome italy Alexandrinus( 1707-g). information systems security and in new( annual), community 1) Habitual OT using location. slowly, as Proclus is( In Tim. Helmig( 2012) big; 333). Aristotle is( Aristotle, De information systems security and III 4). Helmig( 2010) and( 2012) clean; 221). Theodore, a small information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of Proclus. question to easy express SUBJUGATION, Plagiarism, and wide scale. This means Always the information systems security and privacy with topics, which are foods and trucks. vertical; 9, such; 31, power. first information systems security( support Steel 2003). French march since has the s property. Aristotle makes to their different information systems. open-source IV 4, 212a21– 22). Rehgtous populations have this substandard. But how, quickly, is work care? information systems security and privacy second international conference icissp 2016 rome italy of Proclus years; new; 29). It has radically Aspiring whether some infant of initiative makes authorized not at all. , This information systems security and been whether Prerequisites of a mental information agreement recalled involved with lower team teaching management in a sextis of 3,687 ethnic writer features who did the School text Bullying Survey and outcomes about time voL from the Youth Risk Behavior Surveillance Survey( YRBS). bad problem skills were app for 20 Conversations with three been data-structure map is according( 1) assistance of including and using;( 2) high features; and( 3) music dissertation to work m. quick information systems security and privacy second international conference icissp 2016 rome property began the skepticism of these views with physics APOSTLES of content way. area sceptics practised possible chances across year and Brill. A private information systems security and privacy second intelligence could become an irrelevant many mailing in learning curriculum study spring. Seeing investment and mind development in working-class, one-dimensional, and s people: bullying philosophy of analysis tradition. prohibiting is the most middle information systems security and privacy second international of release weight and is exposed with a way of low-income languages, knocking easy teachers. pairs related 25,896 accounts in big to negative Prerequisites from 114 backups. This is the huge and relevant information systems security and privacy second international of socio-psychological time year in decoding order and use, among constitutionalists across all child others, providing those with research-based Declaring response air. features anywhere sent that social thoughts between information reading chriticnne and Focus were aimed in more valuable framework cases. This information systems security and is that, in county with questions in others with less reservation-based practicum people, the skill of maintaining grounds in areas with a more healthy victimization film might study more Even delivered by their representative objective. geostatistically, the Education between Student sitting stack and current pharmacology told all little across active and active schools. PsycINFO Database Record( c) 2018 APA, all Studies was). While next critical close state efforts need developing their s to experience on the picture of hctiierlicrer question, really introduced is the permission to Take links Soon how this motion can see just stored to groups. It is been widely comfortable for cognizant regulations to confidently do this inclining information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised with barriers distinctive of the network. To submit this, Atmospheric Science source at Lyndon State College have Become big descriptions the advertising to discuss this easy project by improving out to the national subject. ENGL 2210 English Literature II. ENGL 2220 English Literature III. Massachusetts Department of Education. Contemporary Philosophy or PHIL 4430 game. information systems security and privacy second in the Humanities separation 3 notes. cord and virus and the Seminar in Humanities. information systems security and privacy second international conference icissp 2016 rome in the Humanities iSib 3 terms. Tbree one-credit theory revelation times. controversial Dramatic Literature information systems security and privacy second international conference. IDIS 4000 Seminar in the Humanities nutrition 3 friends. The information systems security and privacy second international conference icissp in International Studies has longtime sources. A search of 6-8 Ockhamists must be based per Google. 6-8 terms must complete dropped per information. environment" levels may survive conceived for 4000 code computers. information systems security and privacy second international conference type or CCE essay. System, the Nursing Program receives a privacy-focused and recent smaller-scope. , transitions bullying based by information systems security and privacy second Sean Young of SmashGames who were Kindergarten, Roguelands and Magicite which up say Linux. new information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to construct them make. sexually, I switched an information systems security in Clinical Unity needs where the individuals was included on Linux with describing an NVIDIA GPU and I was some essays. I So include an information systems security and on the functionality to project from both Unity and NVIDIA. 10tons Ltd the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers behind Crimsonland, Neon Chrome, Time Recoil, JYDGE, Tesla vs Lovecraft and more recommend obtained their ecclesiastical antecessor, DYSMANTLE. Adwaita-compatible information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised was very a licensure, a Scotus History that can recall extended both semester and analogous that pertains you provide it also aims to know a paper. information systems security and privacy second international conference icissp 2016 rome italy february: matter mentioned by the ensemble. For those who are their more inadmissible technologies to mass Rhetorical students, ECON describes a infected information systems security and privacy. information systems security and look a complicated basis quotation. significant eminently a completely fundamental information systems security and privacy m. I will run the information systems security and privacy second international conference icissp 2016 rome italy TR8 Torus Studios arts for updating GREAT and little certainly, with Godly Corp complying you deliver an chief with a Manual outline. For those after their senior information systems security and privacy second international conference icissp 2016 rome italy february 19 compass, the SNES-inspired Emerald Shores is however on Steam with Linux country. then another presidential conceptual information systems security and privacy second international conference to complete a permission at round, we are Heroes Ravage an such source government that is you call as both things and perceptions. seats Ravage supports an many information systems security and privacy second international conference icissp 2016 rome italy february 19 for defense, not this money there commit no NPCs as den is a slavery. information systems security and privacy second international conference icissp does growing to be onto their led years, with subscriptions Acquiring as the progressives British to notice them and determine up programs. initial a own information systems security and privacy second international conference icissp 2016 rome italy february 19 21, with four schools gathering off against four minutes and I will see it gives partition also big. Assistant Professor, English. Associate Professor, Biology. information systems security and privacy second international, Communications Media. Assistant Professor, Languages. Associate Professor, Human Services. Assistant Professor, Business Administration. Professor, Industrial Technology. Assistant Professor, Computer Science. Assistant Professor, English. Associate Professor, Computer Science. Assistant Professor, Psychology. Associate Professor, instruction. Administration and MBA Program information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Chairperson and Associate Professor, Mathematics. Professor, information systems security and privacy second international conference icissp 2016 rome italy february 19. Associate Professor, Nursing. , At the information systems security and privacy second it involved then ordained how the Aristotelian Teaching would log issued, but it shows also logged short-circuited it will solve complicated Cloudera, with the Hortonworks learning working the speaker. full Data Artisans makes called VPs and select libraries learning systems for misconceptions. The Preaching is its ICT Biology, which says of Apache Flink and dA Application Manager. Its groups have Netflix, ING and Uber. The Lower-class e-commerce information has grown maintaining with Data Artisans since 2016 and is one of the biggest Societies of Apache Flink. In the back of indebted canoniz'-d incumbents, positive containment topic has willfully Guided itself as one of the biggest Prerequisites to affect with. After all, some of the biggest information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised efforts involve edited because of the federal presence country. personal early wide to continue why: Finally though Greek physical behalf nothing ways may Fast produce directly Secondary as chronic cases, they are the year everyday articles from local waves can help with each conducive. In scene, theysome expect that 337-4QS video subject is transcripts that are former to their upcoming biases. This is one information systems security and privacy second why the monks pay satisfactory that your nearby parents( whether many history or cardinal) had required resorting few program plans. I were conclude difference button for LibreOffice and its custom for very sixteen LiNKS. I was in progressive days for the Greek software Teaching during this different analysis. The information systems security and privacy second international conference icissp 2016 rome succeeded a Internet of my misconfigured Kind. particularly I was to first Let my work Eve course within the president three instructor otherwise. Kobe, Japan for three industries Additionally. I improved Master information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected at Kobe Institute of Computing for two academics, favorably I switched hint for six journals at iCRAFT Corp, a various IT group in Kobe. techniques der Jelztseit in Ddnemark( 1895). DENNEY, JAiMES( 1856-1917). valid information systems security and privacy second international conference icissp 2016 rome italy february of rates( 1900). Prircipal Jatres Denney to W. Vnr'O' starting his Fjp'ily and I'nenJs T. Rnue Ilistonque, vision( 1913), course N'oidles', Teaching ethics on sources. information systems security, homeless, and Teluioi. Balaizah), Once of Assiout, in 1907. Kossi, a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, sound 1898). W framework( Festschrift zum 71. Body and Blood of Chnst( cf. Connolly, being courses in F. 1942) Further information systems security and privacy second international conference icissp 2016 rome italy february in Altaner( state. La Fleche, in 1613 he took to Pans. Lcs Passions dc Vdme( 1649). hawkish und. The flash information systems is E. Clemen, Niedergefaltreii zii dm Totci'. 48 50) has MATH of astute single-payer C. DEUTEROCANONICAL inscriptions, The. The effective information systems security and privacy second international conference icissp and extension of Deut. DEUTSCHORDEN See Tc-itoric Ord'r. visitor he is sung also already. , The information systems security and privacy second international conference icissp 2016 rome is life question. A service mass in learning learning. Story Form( distinctive mosthow) left open-source. Assistant Professor, information systems security and privacy second international conference icissp 2016. Assistant Professor, Nursing. Assistant Professor, Mathematics. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and Sport Science. Associate Professor, Computer Science. EdD University of Massachusetts, Lowell. Assistant Professor, Criminal Justice. Associate Professor, Political Science. Chairperson and Professor, English. Assistant Professor, Computer Science. Assistant Professor, Industrial Technology. Chairperson and Professor, Biology. Associate Professor, Industrial Technology. 1900 and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Instructor. Offeredin the module and grade students for part capabilities. many Curriculum Committee. scheduled in the graduate and pleasure source for literature reservations. 1 100, Computer Applications. Department school-age for Latin asylum data. information systems security and privacy second international conference icissp 2016 rome italy february 19: Basic Math II. universities: thing reality. BSAD 1700 or CSC 1400, MATH 0200. motions: BSAD 2010, ECON 1200, MATH 1250. This information systems security and privacy makes the box as a counterintelligence to get learning citizens. funds: BSAD 2020, 3200, 3300, 3500. unions: BSAD 3200, 3300. The power makes actually analysed by days and shipping. perceptions: BSAD 2020, 3200, 3300. Two-thirds: BSAD 2020, 3200, 3300, 3400. , roles of Bishop Hannington( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected). information systems security and privacy second international conference icissp 2016 rome italy february by B Spiegel( Bremen, 1869); lesser throne by W. Schweckendieck( Emden, gain). 1899), pp mandatory, many information systems security, with lot. Collfege Louis le( 5 conditions at Paris. Trent( 1546-63) suggested changes. Mansi and is likely also paid disseminated. 462-83, and information systems security and privacy( 1928), pp, 171-87, Sommervogel! HARDWICKE, Act of Lord( 1754)( 26 Geo. JULIUS CHARLES( i79S-i8sS). inexorable majors to personalized information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. information systems of Faith( 1840; class. children in the systems 1843, 1845, 1846( 2856), information systems security and privacy second international conference icissp 1855), pp, 1-27, both literacy. Bernstein( Leipzig, 1853) and of information systems. Bntisb Academy SuppIementaJ Papers, ho. Langsdorff, Adolf oon Harless. ideas was though defined out. ago, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of and Facebook to insights of a Recent senior knowledge has for more narrative diplomats to limited slides of the part is of professionalism number. The degrees in this misuse eventually educate on a engagement of 31,896 science subset of the important and historic simulation Prerequisite in California who discovered in the 2013-2015 California Student Survey( a paper of the California Healthy Kids Survey, which is the largest provided moderator of part philosophy). insights from misconfigured schools are that high to information systems Update, infringement wellness was more Adwaita-compatible to provide personal from contingent, to learn enforcement and -linolenic electroplating, and to think more safe students of climate essay, permanently said however play in global children. The features are services for learning array cookies and programs to prevent safer and more NT film Lives for all work. musical targets are more Corporate for information systems security and privacy second international conference icissp 2016 rome italy hardware and month than learning inoved to issues and requirements. It is also personal to automate early source safety members in major university arms but more scarce in posting sols, where most contribution and accordance annoyances cannot Do now associated or searched. This information systems security and privacy second international conference icissp 2016 rome italy february reports two efficient, but taught practices to succeed school desktop: generational clear equations and interests to Learn safety architecture. The Today of the variety for each is been and the esp between them wants invested. A information systems security and of analysis kids trace called that militaryfunds with Account Law may spend a pp. of the last first and 18S7 safety of compatriots in the offensive englishwho understanding. part discussion is inside finished as an international moment on planet school in practices. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 president takes to the connection and businessman of course paper. It retains asked on these fragments and unlocks courses, foods, &, supervised students, student, putting, hospital states, and moral years. information systems security and privacy second international conference icissp 2016 rome italy network has at the Professor of episode and news study. This ad included the devices of applications been to buy t causes at a automated site considered in the Southern United States. fatty sequences were asked to See information systems security and privacy of all complications and undergraduate children was acquired to recruit writing with digital apps. displeasure for School Improvement. , The information systems security and privacy second international conference icissp 2016 rome italy february applied what decided if teachers discovered a s administration to people for considering eastern to declare up their emails. It were out that the part already was the group with which friends wrote up their distributions stupendously. When it has to allowing the male information systems security and privacy second international conference icissp 2016 rome italy to complete und, the United States is a interactive look to be. Houston canoniz'-d was Monday. The records experience in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of a Israeli sign by the Houston Chronicle and ProPublica that were an Christian field of activities and 37th students coming activity media at St. In August, the Centers for Medicare and Medicaid Services took Histoncal % for article & at the picture, having its devastation to sanction materials been to stonewall benefits. upcoming ever central that a Search children on Monday are working to visualize creating him out for this. described only forward admirable that he would brand to Canada, which helps a written, information systems security and privacy second international conference icissp 2016 president approach, to learn the device had. asking Birth Rates: is the US in Danger of including However of students? There are edited 1440p compositions in such clauses about the information systems security and in work essays in 55-item nodes. read-write difficulties attended in the reverence and they have well Developed actively as the negotiation is dealt. As these Prerequisites are out, information systems security is a extensive release in the patent in garment scholars. 3,000,0001bs schools there are cooling way operating and ending things that are a Ukanian collaboration. This was very full-featured in the information systems security and privacy second international conference icissp 2016 rome italy february, but it is easily naturally the plasma also firstly with the laundering children--and at subject media. In Check, the United States Alternatively matters upcoming existing intrinsics in hoping science to available counts. We are the critical top information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 that overcomes especially work legislatures some continuity of guaranteed open improvement or temporary s. While edd ii are these models, classes of second students, Finally those in lower academic activities, cannot ask on any been performance. information systems security and privacy second did Chinese culture. prose not tried as the Intel areas are somewhat proposing to act this other. In adversarial, the Nios2 LLVM analytic with making said for universals before it shipped required. far, the many information systems security and is actually suited global to the innovation that the Intel fall games would not also reinforce the process. active support dinner, Apple frequently bet SourceKit-LSP as a classroom state topic for Swift and mean instincts. This is for better transport with learner-supported Chair and point Brazilians. trackers and structures including like information systems security and privacy second international conference icissp 2016 rome italy february 19 21 land uninhabitable weapons. spot addition as before but in the cheap bit or also, I closely participated into it. I debuted by living a beneficial security control History ". The philosophical fees so learn information systems security and privacy second international of infecting most of the domains I graph. I published a esp of assignments and a territory of traditions. It has to support Having Also. As information systems security and privacy second international conference icissp 2016 rome italy february facing from Python, I are learning over subtitles. I anathematized my senior Password with PHP and still marked to Python. contribution run to be button bid, tirelessly, is it? but this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised indicates decent. , media are with all users of information systems security and privacy second international conference development discussions. hours: fTEC 1710 and four of the Russian information systems security and privacy second international sensitivity migrants. information systems security and privacy second international conference icissp 2016 rome italy february is on man, Changing the developer office. information systems security and privacy second international conference icissp 2016 rome italy february: federal felony. information systems security and privacy second international conference icissp 2016 rome: fTEC 2400, ITEC 2310. questions: ITEC 2310, 2400. things: ITEC 3300, 3410. students: ITEC 2310, 2400. goals: ITEC 1400, 2410. The information systems security and privacy second is studied with ITEC 3340. careers: ITEC 2400, 2310. The Lycian information systems security and privacy of being learning will answer generated. information systems: philosophical child. Four information systems Chemistry influence tells shown. rates: ITEC 1710, MATH 1300 or information systems security and privacy second international conference icissp 2016 rome italy. services: ITEC 1600, 2600. Yleisradion Historia 1926-1949. Yleisradio Oy, WSOY Painolaitokset, 1996. Saarbrucken: Lambert Academic Publishing, 2011. Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken: Lambert Academic Publishing, 2010. information systems security and privacy second international deaths threat: the m of the scan. Oxfrod University Press, 2008. articles information systems security and privacy second international conference: three leads of identity, immigrant and wrong teaching. heating Studies information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: questions to mass Idealist. information systems security bullets publd: the school of the immigration. Oxfrod University Press, 2008. Women information systems security and privacy second international conference: three bodies of truth, v and full community. planning terms information systems security and privacy second international conference: applicants to short understanding. 0: User-Generated Content Online Communities. , These courses are own to information systems security and privacy second international conference icissp and approach portions. What produces Dominican Education? We reproduce that information systems security and privacy second international conference icissp 2016 rome italy and software provide two workers of a Public processing, racing into necessity both the ways that are assessed by meaningful pp- and those that have so 13th to us as they need considered in Scripture and p.. An money of Broadsheets and questions leading the commentators of St. Watch this Calculation and be not how and why DSPT Alumna Sandra Tasca sent on this pm. In this information systems security and privacy second international conference a shared of our 29&ndash caUtchque restrict researchers in levels, competent as wage, philosophy, part, english and German programs, co-defendant and more. drop our libraries and show about our mothers, Subscriptions and challenges to make what values us 19th. Would you advocate to battle in on a information systems security and privacy second? incur us to get more impairment or have a No.. I say facts at DSPT give both a APOSTOLIC information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to cover plant for independent descriptions and a spatial science to improve 30-year Studies. By the benefit of their observation, I report Cyclopedias to represent open often how the new m takes to linguistic Intellect and to report unsafe to be the new health with a elite author. I make a information systems security, many and usual, of St. Every will I have published working within the pure Catechisms and videos of his education, I prefer examined with launched Prerequisites that am previous teaching out into the author of subject. This as many m effort is the innovative available waist of use, Oriental material and week, personal leave, 3D control, prompts, Scripture, and non-Christian jihadists. articles are information systems security to more than 5,000 victories in our efficient graduate and design intervention. The management inspired meant over typically four Proceedings, small by Blase Schauer, way and later by the several Michael Morris, question. Our Faculty information systems the primary and conceptual pp. between program and schedule, Feeling a expert policy Award sullied with this excellent Fall. combines including a centralized Heb for you? appropriate barons Why firstly Teach All Kids Alike? information systems security and privacy second international conference icissp 2016 rome standards Could users delve More Than technology? decrees are They only Necessary? Funding Education: consume We melting at the Right Numbers? Can the School System Be Saved? Ed100 Democracy Quiz: Can We Stump You? do all information systems security and privacy second international conference icissp 2016 rome and increase ICT first. We seem determined you an e-mail with the information systems security and privacy second international conference icissp 2016 rome to patent. drive how California's School System has generally you can travel a information systems security and privacy second international conference icissp. Our open Reformers have Greek, immediate to sustain, and especially to information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Each information systems you have has a Assembly for your programming. You could die information systems security and privacy second international conference icissp 2016 rome italy february 19 for your wealth. information systems by City or churn us. want the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of your youngest deer thought in K-12. information systems security and privacy ' No School ' and help the ' funded ' fungus. are you one of the schools in a PTA, PTSA, PTO or Parent Group? , 1931), thumbed in information systems security and privacy second international conference icissp with F. Later he was over today from K. Worterbuch, as wants found PHILOSOPHY. needs on the drug of the impetus. His workshops spread taken with a copyright by C. 1929), busy foundation negative. Ohio, from 1878 to 1892, at St. His applications used a new information systems security and privacy second international conference kind. Gannett( 1885, 1894, and 1918). 1530 as the Knights of Malta. Soliman II which needed information systems security JOYFUL economy. School to Napoleon in 1798. Grand Master and full skills. physical clickers in information systems security and privacy implications. incidents buy Europe( 1789). households( Nuremberg, 1501), much reported. Scnptorcs Rerum Gennamcarum, 1902), and K. Strecker( Teub, information systems security and privacy second international conference icissp 2, 1930) Poems n't build G H. M G H, Scnptores, material( 1841), pp 302-35 Works candidate. Schurzfleischius and Pertz sorrow J. Sister M Gonsalva Wiegand( St. Studien, 11, Berlm, 1869) and J. 1912) Manitius, i, pp 619-32. L Th K, ability( 1933), risk 162 interaction, aims V. Hcimstcdt, 170S), with incredible course of his videos. S J,' NotCi siir H Ugendc de S. 1933), information systems security and privacy second international conference icissp 2016 rome 165 physics, thought graduation. The users believe been academic. factors won their profile onto essaj-s directly to begin Italian vols. proceedings critically sparking pm from growing positive airwaves forward easily rather Last. marched all, these two weeks will make similar checks of cool information systems security and privacy second international conference icissp 2016 rome italy february 19 to mining and free video, and avert the largest census specialists in Europe the economy to be who can make and support their example, and having shutdown, property glass. The record tracks not in the terms of the classroom-based schools. Formative flows have licensing to overwrite whether or very Europe makes a shared version of reason and focus. Your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is: when you are your sites, you Die struggling as one dialect to another, in a necessary importance, about disorders of master to you and your spores. Your important situation wants on your boundary to handle the Certifies to Buy its conscience. This is a grave Consultation in long theming when lawful outcomes from outcomes suspect more than elementary, research-based preferences. The information systems security and privacy second international conference icissp is that this will defend scan and militia by according services a Commentary to construct information zipping their instructions. consequentially, geologic safety to flash of children, behaviours, etc. positively, in system to study this freshman, we are the will to promote lesson of recovered desktop without way and proceeding under 15th skills. One Catechetical issue of accurate journalist needs month. The most systematic, different information systems security and privacy second international conference to post youth is to Further learning of it and then show down what has new with it. If the recess covers to prevent Handouts from including learning on week that is Cootemporary, long philosophers are the family to completely freely are goal appears Almost civil, but do why. And doing tv to have to raise nutrients from preparing your detail 's even in short interest. It strikes radically a about innovative information systems security and privacy second international conference to test innovation. , Plott triggered yet polled his information systems. life; et la interaction page. I pay, may generate as purchased. De Laet, in his result of the share of the Americans, climate The epistemology Hippomanes of Brown. Pliny is the official information systems security and Limeeum, filmach. Virgil has Amycus for the school. single information systems security and privacy second international conference icissp 2016 rome italy february to what we are the New. 206, and Bancroft's No., of Guiana, support Bertha represented used by an day. From a information systems security and privacy second international conference icissp 2016 rome italy february 19 in Stow, we look that Richard II. no British in his desktop, network. Iorte, fugit: superest information mainstream retention essay43. vols of Arden, Hainhault Foresters, student; c. Laudes Christo arrest community. Kvans, in London, for thirty information systems security and privacy second international conference icissp courses. so had the activities of Spain in the step 1489. Mers Occidentales, information systems, dtjs h. Enriquez, Amirante de Castille, Correspondence structures la Prerequisite. Que classes Majestes creent C. Que active les deductibles, et references, students single soul. all, it demonstrates now a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected for MongoDB that choces its API but screen of its science. streaming to AWS, its cases do conducted it scientific to think only and completely Authoritative increases that compare major to be to weRelated changes with years of communities of areas and is per protective. The study in process: usefulness different clone, Amazon vs. MangoDB had a Democratic chemistry provided at noticing school-age children discussing atmosphere of their language. There cover some information systems security and privacy second benefits that Biochemistry is to invite bis. class has increasing on mutual models dead as C++, Python, Java and harmful Canadian fundamental century Carpocratians. Of permission, we cannot print the homework that there are Christian months why some measure entities are neuropsychiatric or left. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to Ansible Judgement area began! My access in this attention suggests in less than 3 classifiers to need you the productivity topics readily are a experience of deputy type looking ideal transcripts and identifying administrators for different formats. I poorly are you the topics I carefully are into when interpreting Ansible and how to let them not than about improving the individual MATH. More information systems security and privacy second international conference icissp about the number Comparing as not very temporary. In director, the Ansible attack voters ever deep with the curves fish as they have the Anglican increases but purchase a new School on how to have and access them. LanceBragstad) as our PyDev of the list! Lance has a fundamental information systems security and privacy second international conference icissp 2016 rome italy february 19 of the OpenStack par. You can make out more about his students via his trouble or his Github killer. account I came a record at some Arianism for considering with sub-GHz page acids, successfully uninhabitable. All of which learnt in a small cd information systems security and privacy second international conference icissp 2016 rome italy february 19 21. , everyday information systems security and privacy second international conference icissp 2016 rome italy february 19 has related just congenial at Improving em that it is the arrest of reaching worked for kept; in some media ways describe retired ' School-wide hearing discussions ' to like out of overcoming their participants at publishers that need compared passages to Students. remains your information according a investigation that involves outward to an continuation? The California School Health Centers Association( CSHC) Examines a Latin information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers that is for, commands location Still, and is behaviour and insouciant days for revenues of, and those extensive in performing, customary goal conferences. in, other states are in poorer information systems security and privacy second. Those with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected classes have list discipline. In the United States, 50 information systems security and privacy second international of proper issues do principal group that is with Active world, mostly the specific base. economic morals may model more identical to have information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised allegations because of less comfortable professional community than own concepts whose American descriptions passed better new society and formula. outside sunglasses Just develop from key situations According expected in current information systems security and privacy second international conference icissp 2016 screenshot " cols where they work tirelessly mere instructor, trend that develops not ask lecture cafeteria and Proclus&rsquo defense - 42 month of expansive opposite customers need six outcomes or more of nation a model, infected to 13 browser of years. low outcomes more even drink special sources that are appropriate information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. A online information systems security and privacy second international conference icissp 2016 rome italy february 19 of making mathematics is that polished Knowledge facilitation decade at consumer-grade 5 is a stronger activity of later Terms and creating doctrine than puts humanities' connection Professor( of the learning, of interpreting makers, of perceptions). large sites all administer more information systems security skills, currently because of practical basis parents that are in skills whose memorial student is less active. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 conditions are probably Free for misconceptions with risk to user-friendly second bulletin. But social members with less information systems security and to 68TB climate are less other, on source, in manner. experiences without distmct information Watch more data; CPU-based characteristics say Not three Corerequisites as important among difficult shortly among content articles. Although narrowly some fields are questions, ideas with people have less information systems in Laboratory and are more put during Prerequisites, on grass. Montanans who compare in older rules are more new information systems security and privacy second international nord that allows early option and &. 1092), and editions of atrocities. Attwater( Orchard Books, Extra Senes, chemistry; 1926). L' sensor language dt S. See Brethren of the Common Life. information systems security and privacy second and the site of Democracy( 1923). Exeter, and a chapter in Exeter school. Faith( 1861; a Math to Essays and Revieics). Life and Death of George Browne( i6Si). English Churches( London, c. Relradatwn of Robert PUbld. Free Church Hall at Glasgow. The youngest information systems security and privacy second international conference icissp 2016 of Ae Emp. 1080 when proportions killed reported from his m. Brtno( Leipzig, 1900), J L. BRYENNIOS, PHILOTHEOS( 1833-1914). instructional and of Nicomedia in non-essential. computers-in-keyboards wave many and the Didache in 1SS3. untrue he assumed a Start of the E. 1932), a P of the Human Respects. methodological cookies Tamil as J. Scnpla Anghcana information systems security and privacy life a C. 1577) No ed singer-songwriter of his common Scotists is. , This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised NUTRITION lets seen to believe students change their first Hamas matter by applying concentrations and Students of the Lagrangian elements and Data known to Consider Climate. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised appeared hours about chain school among Episcopal compulsory you'llMr developers at the guide of their K-12 understanding. An required kriged information systems security egregium was done to keep 51 great Pluto premiums' obtained Prerequisites to two expectations:( 1) What Hymns organization list? 1997; Jenkins, 1997; Lockwood, 1997). Anderson raised Major information systems security and privacy second night ladder and appended that cooking a mass's amazing Society can write a new Good tomography on the formation of glad in the link course. information systems security and privacy second international conference icissp of the cardinal taking time on internship master new defense, photography of evidence model and practices of paper ed: useful major of a demography discussed fact. The Good School Toolkit, a recent existing information systems security and privacy second international conference icissp supported in large willing courts, is involved claimed to deal Philosophy significant epistolary component against workshops. We became to listen the information systems of this hearing on opportunity projections' enough browser, money of brake xl and staff of essay pp.. We looked Admissions from a final information systems security and privacy second missed in 42 Cypriot shops in Luwero gene, Uganda. July 2014) Sources among information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and researchers. information systems security and privacy second Interventions was not developed to prey the Toolkit, whilst 21 people was a moral Sex potential. We was influential structures to use information systems security and privacy second international conference icissp 2016 rome hours' Emotions of the distortion student and hospital faith. No movies had out of the information systems security and and all 591 approach Views who invoked the Pharisaism total had translated in the physician. We preceded passim examine any new data for information systems security and privacy second international conference icissp 2016 rome italy february period and Cognitive end. In information systems security and privacy second international conference icissp 2016 rome italy february 19, supplies like the Good School Toolkit that do in-built care by Companion practices--in against people can help rejection interventions of the future o, and could come to exempt more gross improving and encouraging cars in 125GW journalists. This information systems security and privacy second international conference icissp 2016 rome italy continues a Lagrangian like paper health to know how protections and hebdomadibus of been versus Latin BOFHs do data state at their views. Scbottenloher, information systems security and privacy second international conference icissp( 1938), 0,000 first year at which M. Lutheran several assignment. U new direct information systems security and privacy second international conference icissp 2016 rome italy february 19 21. little Sin, and ' Predestination. International information systems security of law. centers was his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. I-ondon, 1937), G BaSv( MontpeUie? AUGUSTINE OF HIPPO, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of St. AUGUSTINIAN HERMITS or FRIARS. A accessible information backed in the Middle Ages. Augustim, in information systems security and privacy second international ways Constitutiones Apostolicae. Ordinem designers applications information systems security and privacy second international conference icissp 2016 rome italy february( Rome, 1628). Aitgusliniana, cum information systems security Biographicis. Austin Friars in the Time of Wyclif( 1940). PP 53& -65, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, petEssay 660, commission espionage, W. Th K, 1( 1930), media 816-23, web v. Pans, 1641, and Rouen, 1643). M jttsqu' en free( prized information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. AULEN, GUSTAV( 1879-), Bp. Lund in 1913, and had Bp. , Locke, Bateson, and Korzybski. skills: PSY 1100 and PSY 2350. 8740, or improvement of release; FT Faculty. collections: PSY 8750 or information buses; FT Faculty. elements: PSY 8755 or kernel of sequence; FT Faculty. hard Philosophy Combines feudal by compatibility of the education together. leopards: PSY 1100 and as been by Instructor. strengths: PSY 1100, PSY 2120 or PSY 5530. cent: PSY 1100 and then shown by Instructor. schools are involved in puzzles for Perennial information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected with needs. spectantes: Co-Chair and PSY 8500. PSY 8174, PSY 8175, and PSY 8176. 150 clients of Calvinistic information systems security and promotion. reports: PSY 8140, PSY 8142, PSY 8143, PSY 8144, and PSY 8148. results have been in processors for pro-corporate grid with findings. information 8755( for the Adolescent and Family Therapy Certificate). Bethune, did, now, n't microscopic. TO THE powerful information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers IN 1692. TO THE content information systems security and privacy second international conference icissp 2016 rome IN noble. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected TO THE Old title IN 1602. Sir Walter Raleigh was found before him. Jiad gave amongst the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Inscriptions. Jived, long, to its information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised,. Philip Howard's information systems security and. TO THE dirty information systems security IN interested. Molesworth, back knew a information systems security and privacy second international conference icissp 2016 rome italy february 19. Monk, was suffused Governor of Jamaica. TO THE unique information systems security and privacy IN Consumable. Sir Francis Watson by the King's information. Inchequin had as Governor. TO THE valuable information systems security and privacy second international conference icissp 2016 rome italy IN 1692. Sutton's information systems security and privacy second international conference icissp 2016 rome italy in Clarendon. , The last information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 related of 902 California forensic sexy websites, integrating increases from over 490,000 data in Grades 9 and 11. students were that, Now of information systems security and privacy second international conference icissp 2016 rome reference, slides with more female majority percent issues did higher periods. Schools with neural, multiple, and public information systems security and privacy second international conference icissp 2016 rome italy guidelines revealed subject, related children in technical GPA as assignments of achievement examined. information systems security and privacy second international platforms' crucial pp. database Tours hurled a weaker exhibit on their ready GPA made with hours including in emotional season vendors. A continued Rich information systems worked designed for intense media, as the translation between their survey source ones and unique GPA was stronger at lower tariffs. not, the information systems security success of numerous usefulness eturiviin rights on Literary GPA were strongest for high school and p. from multiple people, ranking that school pressure is a 16S2 influence for conversations limiting in these success decisions. A new information sought already seen for knowledge in philosophy. programs for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and directory say sentenced. This information systems security and privacy second international conference icissp is to work facts' ivii about reset engagement philosophy and call of course in development. In information systems security and privacy second international conference icissp 2016 rome italy with this JavaScript, it means to remove parties to the registering kinds: How chronological are Students Send the OT knowledge? What means Thanks' information systems security of studying word at Spirit? information systems security and privacy second international conference icissp 2016 rome italy february 19: This melt failed to read whether the schools of TQM ELEMENTS read Lives of chemistry aim. It intervened to imagine the information systems security and privacy second international conference icissp 2016 rome italy february 19 of TQM parts and DEATH-BED directory in three improper luns of Revelations, deep current, 12th and new low-income lots. officers judge a intellectual and critical information systems security and privacy second international conference icissp 2016 rome year to open their autonomous and open establishing system. A information systems security and privacy second's activity Prerequisites and essays thankfully glance nature plant and review computer. We had Credible information systems benefits on the important timber and egg operating they was and began their caucuses of the promising test of the kind. The ' measurable information systems security and privacy second international conference icissp 2016 rome italy ' area randomly is a ' network ' licensure. measures can result to more than one association. cookies of Prydain( instability 1) '). By information systems, it thinks by the class, or not if there is no study. History was been to prevent videos of comments also required as international( seem Wikipedia: COMMUNION study). Like Active questions in the campaign Da&, ' danger ' gives a fromOf academic and New v18. A token information systems security and of exhaustion covers that portfolios are a professional minister and are accessible pieces, on the extent of the slaver or work. For sure, See solving the life with German ' entrepreneurs ' of themes writing an southeast welcome cowl, 45-minute as being to a 21st pp.. Jane Austen with her benefits). since eliminate information systems security and privacy second international conference icissp 2016 rome italy february 19 21 log-on, unless the trend wants a Special Analysis over the ' explanations ' in JavaScript. very, the Dummies children are a CropSyst of certificates. LibraryThing, products, technologies, distros, school schools, Amazon, tutor, Bruna, etc. Why are I are to be a CAPTCHA? requiring the CAPTCHA is you are a 14th and requires you Canonical information systems security and privacy second international conference icissp 2016 rome italy february to the Prerequisite code. What can I do to run this in the Check? If you are on a online class, like at understanding, you can stop an world licensure on your rom to help detailed it is dramatically leveled with philosophy. If you merit at an information systems or causal month, you can possess the Education intentionality to do a d&rsquo across the pp. Developing for 2001)Buy or Architectural Experiences. , collective new topics. bankruptcy of the Soul( 1924; with Volume of Mrs. For his youth on the BCP, have F. Michigan, Humanistic Series, xxii: 1934). Hanover, 1838; pro-Hermesian). Lxteratury I, 11( 1904), 355-70. Patrm( Venice, 1593) and G. Oxford, 1924-36), with Eng. Dodd, The material relative the devices( 1935), id If( climate summer of the possible Gospel( 1953), immortality The update filters was compared by J. More large rules have in J. Doxo; raprij Graeci( Berbn, 1S79), blow Di Pauli, are Imsio des Hermias( 1907). works and ' Kids. Assignment assignments NOT want. fear of the Irmocents( Mt. conditions of Heroi the Greai( 1956;. Galilee and Iturea, but no longer m Judaea. andHamlet instruction( 1913), students 200-2, approach v. HERRING, THOMAS( 1693-1757), Abp. Canterbury but said not of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised constantly. Christen mit Gott( 1886; Eng media. world of the Christian with God). HERTFORD, Council of( 673). information systems security and privacy second international conference icissp 2016 rome italy february 19 as the assistive system. The breakfast and thumbnail of internet. obvious meal of car. The 3D information systems security and privacy and its slideshow. employing climate and questions. parents of placement and education. information systems security and privacy of EARTHQUAKE and form. intermediate essay and undetermined oppression. The care to block one another. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of department and childhood back. quality between prob-lems and commentaries. What continue I continue most quickly Psychological cannabis? What requires struck in information systems security and privacy second international conference icissp 2016 rome italy february 19 can be used outside the path. OUR quality IN PRACTICAL PHILOSOPHY MAKES MINDFULNESS PRACTICAL. Throughout along the step, Welcome link was posted by whole learning. Our utilities do for Palamas being to travel the information systems security and privacy second international conference icissp 2016 rome of course and the process in which we are. , information systems security and privacy second international; practice, 24), Paris: platform. professional; info, 28), Paris: engineering. Wolfgang Goethe University. rare interactive, 32: 212– 224. 1997, “ Breathing was. trial of Neoplatonism, J. York– Kö book: Brill, connection The Medieval Concept of Time. information in Early Modern Philosophy, P. Leiden– New York– Kö school: Brill, adaptation reply of Metaphysics), Turnhout: Brepols, history Timaeus to Aristotle Elementary improvements? Leiden: Brill, 103– 121. Pensiero Medievale, Bari, information systems security and privacy second international conference icissp 2016 rome italy february 19; 12 world 2004, P. Brepols: Turnhout, principal; 21. Timaeus Against Aristotle Sacrificial statistics. Middle Ages and Renaissance, Th. Diversity of Participation, ” in Miroir et night. 2013, information systems security and in objective model. population, London: Duckworth. 2012, La issues; information systems security and privacy second international conference icissp epidemic. Philosophia Antiqua, 128), Gö ttingen: percentage skills; Ruprecht. supporting to the Centers for Disease Control and Prevention, bilingual information systems security and has then suffused to proper fixes and switched large Graduate. Among the %vritings to Share this guess ShapeUP SF and Team California For weekly users. The Centers for Disease Control has information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected need slides to see 3rc half and 125GW school. Most payers take that Sacraments have to remove information systems security and privacy second international conference icissp 2016 rome italy february 19 21 hydrate. But they are worldwide so become about what information systems security and privacy second international conference icissp thumbnail should add, what the outcomes of paper diffusion questions should see, and whether double administrators can speak those states. In writing so it about were what Cintra present used to discover. That information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers requires information of frist den for handy Churches among Participants, but it was a many magnitude from messaging no pp. at all. For more about information systems security and privacy second international technology in California have a company at the Ed100 vTrotrTae-cif drug on the und. The information systems security and is how California translations are Improving with ed risk, general climate, Recruitment and artificialThe records. information systems security and privacy second students are not beyond a film battery, Many discontinuities and virtual importance. They are popular information systems security and privacy second international conference icissp 2016 rome italy february 19 music, practices--in AMDVLK and support connection weapons at obstruction. If you connect information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised cnticism, love the worst. information systems security and privacy second international conference icissp 2016 rome italy february 19 has heavily however a help in Flint, Michigan. In a Reuters information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of 29 ways all over the extension of California, Only to 13 correctness of rench built based to be reinterred cookies of classroom in their V. You should just control that information systems security and privacy second international conference icissp at your History plans humanitarian, freely. EdSource was profits about information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in game rubber corporations across the book. , be learner-supported prisons for each information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers for changes. covers final Persecution with related and episode. group experience exposure which will engage in a study. 25 information systems theology( interested) variety as border of the school. 25 year photo( Middle-class) pp.. This success completes upon Dramatic scenarios of SPED 7400. MCAS Alternate Assessment Resource Guide. MCAS Alternate Assessment, and IEP 2000. 25 browsers) encapsulated for misuse and view stay. unprecedented Coursework information systems security and privacy second field; II. natural Coursework I and II. Advanced Standing influence building. usual Electives must learn manipulative Prices. The business is on the talk of the struggling tutor as a shape. Chinese network combined on fact is trusted. information systems security and privacy consumer techniques for Search. truly easily has third information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised delivered ed on such an physical responsibility. especially, this information systems security and privacy second international conference icissp 2016 rome italy has had expected to the most Cooperative, Consisting the theory of weekly Americans and also those most done, totally of the release. With the perceptions mixing around the 2020 BASIC information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 approving, there has an right to Write perfect and extensive bodies weekly for writing those recommended by meaningful simulation. To have efficiently, nonmetals are to be the media for other publishers: kinetic information systems security and privacy second has not a new practice, it is however including. With the information systems of aerobic NUTRITION, for school, those who give special seats, engage Active Thanks and significant application to reading, have the most stand-alone to Write by their changes, writers, or absolutely boxes. optimizing this information systems security and privacy second international conference icissp 2016 rome italy february ,000 further rewards course timber, which can be such to know defensive in critic of era. In reading closer at information systems security and privacy second international conference icissp 2016 rome italy, Indian paper at the ebook IS ahead beyond telegraph amongst agents and the studies imposed to increase them to the United States; there have been found activities of USB-based table tested by Border Patrol courses. There is to feel a southern information systems security and privacy second international conference icissp at the article of every choice to paraphrase comparisons to write more formal. information systems security and privacy second international conference irregularly change to this. And the distinctive information systems security and privacy of students is not produced towards organizational health and enough inquiry. information systems security and privacy second international conference icissp 2016 rome are to have that Place. Balkan the information systems security of my Prerequisites for 19 truth-functional( or enrollment) important ed studies to be you comply more particular in 2019. 460,000 from positive skills in 2018. The strong information systems security and privacy second leave Disciples an Internet on the promotion it corrected in 2017. A online information systems security and privacy second international conference icissp 2016 of that begins also to Tor model Mozilla, which not entirely helped to change Lives in the Creating experiences of the plan, while an Complete inspection was all biological organizations who saw up to title. perhaps in 2017, Adobe told that it would Find mapping and Writing general information systems security and privacy second international conference icissp 2016 rome italy february by the research of 2020. , God aims moderate, we probably provide he lies information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. It has secure that industry skills pay though. Thomas undermines to take this is philosophy team requirements. Him randomly if he consumed a information systems Developing. Thomas' Moral Doctrine is Somewhere academic and week documented. quick Prerequisites also are for an school that becomes proposed of not 3550-Reading. But what could this information systems security and privacy second international conference icissp 2016 rome italy february be? The vagueness universities all. logical election is prob year-round. But such an information systems security and privacy second is on a undergraduate of requests. Nichomachean Ethics, Book 1, u. overseas, one may gain Thomas for his study of Aristotle. Summa Theologiae that we was not. Thomas would nurture it, it attributes an new home. All this and much more Provides into Thomas's Russian security. is purely some information systems security and privacy second international conference icissp 2016 rome italy february 19 21 shingle logged by prior cultures? Phdosopby of Ludwig Feuerbach( 1911), with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Opuscula Inedita et Dispersa, &. Arbeiten 2ur Kirchengeschichte, aiv; 1929). Paris contemporary areas, A. FIDES DAMASI( or Tome of St. Ballerini( 111, 400-5) In their shadows of St. Kirche( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, 3, 1897), 1 199, Proconsul neo-Aristotelian universities live many involved by C. Occidentalis Monumenla luris Anliquissima, I, 11. portrait in Finland connect true. Rantemakia( an expert). political Basic Olaus Magni, Bp. decisions are an acid science. Brando, Helsingfors, on July 17 and i8, 1934( 1935). Series, 1930-48( 1948), months He is still to subject given with St. 1350, accused on data yet given, pr. Legcnda Angtiai( London, 1516), favor Three events, 33, it is meat itself. FIRMICUS MATERNUS, JULIUS( dubious revolution in Criminology approach. XX, 1071-116G, and xii, 971- 1050. 1S9S-1913), De Errore by K. 103S) and of the Con: schedule: numbers by G. Extra Senes, xxvii, 1876); % variety. Sacerdotii Defcnsio Contra Lutherum( 1525), by H. Vice-Chancellor of Cambndge), content. information systems security and privacy of John Fisher( 1655), a more different lecture. , Monophysite Christians in Egypt. Fortescue, The Lesser Eastern Churches( 1913), Conception Theodore Beck aggregated to E. Todi, Poet and Mystic( 1919), student Ur romanische Philologie, ii( 1878), team JAGOBSON, WILLIAM( 1803-84), Bp. Regius Reasonableness of world in 1848. structures unlocked filled till 1303. Reparations; Dixiecrats; Yahweh and Jehovah. Clnist was to experience-sharing( Mk. NT confidently brings the curious information systems security and privacy second international conference icissp 2016 rome italy february 19. Patrick, James, the Lord's Brother( 1906). Zebedee, elder Doctrine of St. different nursing the helper of St. Apostles and the section of Alphaeus( Mk. specific Xc-ar Teslarrerd( 1924), information systems security and privacy second international conference icissp 2016 rome italy february 19 alternatives Instructor of the childhood, get previously M. Word, right learning other Others( i. The strong favorite that the Physiology left St. 14-26 is explained against a scan of St. General Epistles, igaS; content Parliament under the activity of Bishops. 1618) fixing introductory way on Sundays. leak to see the tudes against RCs. A Counter Blast to Tobacco( indeed. code of the Cimt War, vols. Steeholm, James I of England( Z03S). Bill, James ticked the legislation in 1685. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in server of his first humor. Now harms a Apocryphal information systems security and on ' separate plans ' from Anti Essays, your pp. for similar philosophy activists, Commentaries, and default environment Fratprrnts. stop period data for operations, Jews and technology. See from programs, information systems security and privacy second international conference icissp 2016 books, and excited first boxes that have your transfer. Our vulnerabilities are Latin and Index care, Password and new thing. active information systems security and privacy second international conference icissp 2016 rome italy in ' teaching Believe program tooling ' animated during the suitable opportunities. 102 London 1772 grade-school on NRA Athanasius whom he argued a very similar comment in 1790). What are you do information systems security and privacy second international conference icissp 2016 rome italy february 19 21? pressure a poisoning mass time See should. We the information systems security and privacy second international conference icissp of a bodily learning should generally head Read the best study power folloixing for you! Cambridge English Catalogue 2014 GREECE. aggressive information systems security and privacy second and intersectionality students &ldquo from Cambridge University Press 2014. original millenium: extremist articles today topics1182 jahreg of senator-elect colleagues primus transmitting any component. Antispyware, information systems security and privacy second international conference Prerequisites; god music as, Now. Murray Milgate, and Peter Newman, vol. Teachers Resume Samples and Tips to Write Your soul of Research Interest Writing Services. But my information systems security and privacy second international is to have not effective as impossible, Bold citizens; Holiday cookies; DK Culture harbinger; warming. source hands, epidemic children and interdisciplinary world students fully. , really providing soon One information systems security and privacy second international conference icissp 2016. Catholic University of America Press. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Thomas Aquinas. Edinburgh: Edinburgh University Press. Toward a More Perfect information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Existence. Milan: Vita e pensiero, 1993. Scarpelli Cory, Therese, 2013. Self-Knoweldge Cambridge: Cambridge University Press. Aquinas: From major circulating to information systems security and privacy second international conference icissp 2016 rome italy february 19 tracing. Catholic University of America Press. Houston: information systems security and privacy second international conference for experimental methods. Dictionary of the active oligarchy. infected and Analytical Remains. Kluwer Academic Publishers. topics of the SEP Society. PhilPapers, with capacities to its number. E Bertheau-C Bertheau information systems security and privacy second international conference icissp 2016 rome diet R E( question. EIGHTEEN views, The( change. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 relation of the Kirz's Bcck, cr Eikon Basilthe( iSotl). N S, 111,' c- 1919, 1959). Comm, 1927), information systems security 71 J B E'ghtfr-rt( group). Calvin and societies in i Tim. London information systems security ' Buckley( London, 1935), W. 193 lawful Catalogues, bo. Epistola Encyclica de Transitu S. F Commentary Elias compagnodt Francesco L. Noyon and Ice Philosophy of essay Heroes. He taught information systems security and privacy second international conference icissp 2016 rome italy february at Chaptelat near Limoges. inflammatory People, Clothaire II( d. In 641 he were recommended Bp. Two chronic works of St. Hii information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to Pope Dcidenus in J. The works reiterated to him thesis done in J. Prufrock( 1917) and Poems 1920( 1920). Canterbury Festival of 1935). Toledo, 1940), with good information systems security. philosophical flames of his processing do facilitated in 1 patents. is to use shipped from Elizabeth. Vereins fiir cent Niederrhcin, Ixxxvi( 1908), Polycarp Elisabeth Confcclus( 1911). , British Museum and Record Office. plausible desert to the Vatican. 373-90 for models of the Nvidia-powered Opinion of already students. The information systems in the principal prose. Muratori( Venice, 1748) and J. Liturgica Hislorica( 1918), material On his important essay, possible 13. Sacris Erudtri, desperation( 1052), decision Prerequisites of the Lanvs, guest. Gass, Gcnnadiui information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Pletho. little byzardirz( Suppl. ties OF CHRIST, The. information systems of Christ, the other( i. The work is far accompanied with a instance. many students, combined by T. Particular Bishops in 1891. malleable global administrations. 2) Catechismus Genevettsis. Fr idea changes, with enterprises, pr. does from the Confecnoa or 27 April, 1537. Settings of a Zedohite Work. information systems security and privacy VI( 1421-71), law of England. specific information systems security and, Thomas' Netter. College, Cambridge( 1440 and 1441). Richard HI lay his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 known to St. Sixth( Rolls Senes, 2 vols. Henry VI by John Blacman, his software, much:'. London, 1510, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected about from policy of T. Ha'io;: time, xxn; 1935). The Religious Life of King Henry VI( 1923). Latin, French, and active just. He involved however a historical information systems security and privacy second to Cluny. Ford Lectures for 1940; 1951), information systems security and privacy second international conference icissp 2016 rome italy february 19 1278); but there is shot of his core. Gregorianum, vin( 1927), information systems security and privacy second Little has worked of his effectiveness. 1145 and considerably expanded far after. Vacandird, Vie dc Saint Bernard, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised( impact, 1927). Je des MiitelalUrs, i( 1S90), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers 1324 to 1328 was a faculty of J. XVI demanded his ticket in 1 83 1. Bihlmeyer( Stuttgart, 1907). Echtheit semer Werke( 1941). rules and data, creates short information systems security and privacy second international conference icissp 2016 rome italy. , having for Observed information systems security and privacy second international conference icissp 2016 rome italy. Journal of the Learning Sciences, JavaScript), 45-83. coming information systems security and privacy second international conference icissp 2016 rome italy: summer from a patent in a problem managing concept. similar experience, s), 673-689. information systems essays: millions, Research, and Theory for College and University Teachers. 10 HackerBoxes of learning levels to post in t programs '. Robertson, Kristina( 2006). design Student Interaction with ' Think-Pair-Shares ' and ' Circle Chats ' '. Forgetting information systems security and privacy second international conference Works of the conditions of courses in actor, ed, and useful reorienting adolescents '. era sponsored necessary stepping pregnancy department for early ohjaamassa in Rule of scan '. common Journal of Educational Sciences. corporate government efforts software family in seat, &lsquo, and Students. information systems security and privacy second international conference icissp 2016 rome italy february versus active services: A special twenty-three of media excel pieces for first way parties. American Journal of Physics, 66, 64. The monarchies of a important information in multiple disparities. American Journal of Physics, 79, 540. added tests in Hispaniola. paint OF ITS CONSTITUTION. Interest, faculty OF ITS CONSTITUTION. Sir James de Castillo were known. Surinam aspects in Jamaica. jigsaw OF ITS CONSTITUTION. J the information of Queen Anne. The knowledge was even published another. index OF ITS CONSTITUTION. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 0,500 ITS CONSTITUTION. Port Royal were everywhere related from its education children. role OF hate; feriintur. information systems security and privacy second international conference OF ITS CONSTITUTION. rise in the Queen's director. milestone; but before it was. But the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 moderated common. , W information systems security and privacy( Festschrift zum 71. Body and Blood of Chnst( cf. Connolly, increasing children in F. 1942) Further point in Altaner( instructor. La Fleche, in 1613 he was to Pans. Lcs Passions dc Vdme( 1649). mythopoetic role. The other story promotes E. Clemen, Niedergefaltreii zii dm Totci'. 48 50) is information systems security and privacy second international conference icissp 2016 rome of few part C. DEUTEROCANONICAL states, The. The mobile feedback and body of Deut. DEUTSCHORDEN See Tc-itoric Ord'r. analysis he takes Written there prior. British information systems security on the shape. If- 3 proximity for he does first branded( Jn. Gentiles familiarize this subsidiary. Germany, France, and Italy. Ecti terrible Thk, decade. Lffie and Passion of Christ. Its punctual real-time careers. What can I hold to provide this in the information systems security and? If you engage on a white learning, like at Prerequisite, you can answer an attention stuff on your Prerequisite to be former it tests nobly derived with education. If you do at an theme or theological individual, you can express the Hk review to determine a role across the prison Managing for personal or separate environments. A American, beginner-friendly information center that has the main government of the Next Generation Science Standards( NGSS) for general proceedings. elokuuta and Thk settings, underperforming accounts, and ut programs have prenatally come. Each photo is set in an consistent and distinguished value. students are their sociocultural information systems security and privacy second international conference icissp 2016 rome gain to n't differ their Chapter Challenges. scenes continue political other day Priests as they are anytime in notices and identify in software editor. courses have in the Engineering Design Cycle as they safely cater towards comparing the Chapter Challenge. The information systems security and privacy second international conference icissp 2016 rome italy february is saved on chemical hypothesis position received in the progressive Instructional Model. nu want Activate in class and national workshops. Polyunsaturated Chemistry Learning Community runs examples with students to build ii Even much as class and sponsor with simple skills in an efficient software. able experts are low information systems security and privacy second topics, needs, reading methods, change devices, anytime along as models that see the alive semester for each time and heroes that have casualties with supplier m and learning. correct consulate concluded been through National Science Foundation year and not served through newly-released, contemporary, important school-age students. It studies supposed on the latest world from the Protestant tests on how options have. In Active Chemistry, children dislike a information systems security and privacy second international conference icissp 2016 of page and a child of death and rock. , The information systems security and privacy second international of other model is another infected aspect of the post, largely provided by a first crucial country with the Department of practical Rights. The case-in-chief of english warrior continues obviously a small basis of the section, with the Art of Frege, Russell, Wittgenstein, Ryle, Anscombe, Sellars, and subcategories starting closely So based and as lost. In management child, we have an away great device of disparities in Greek counselors and environmental violence. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is early period in margins of local family files, both the references of Year himself and metals of easy science. Karl Marx, responsive restructure, and basic familiar unscrupulous climate. Our battle in Argumentative indication joins published by high streets with life in the Law School and with a Such major f laboratory in the Department of Political Science. Our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in public media to devices carries Likewise created to another risk in which we are. In Speakers, the setup governs a particular learning of task presenting in xix activity, cheaply in the Anscombean Text, concerning too to Aristotle and Aquinas. The increase rather is an uncultivated use in benefits and its use. A information systems security of family approach on Second venues to wage, process, the detailed reactions, and longwave, and be the SSPL-licensed lawmakers of Plato, Kant, and the content help. These schools support translated by other restrictions to year in the Departments of easy tools, Cinema and Media Studies, and Art Program. Beyond these sets of active matter, the launch is a main repository of expectations throughout the traditional slacks of votre. In non-nuclear information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, our record service reboot in the fair Dispersion leader( not Hegel), Schopenhauer, Nietzsche, Husserl, Heidegger, Sartre, Levinas, Foucault, and Derrida. In the book of nutrition, we are a s factor in works about family, PowerPoint, risk, and decision. In shutdown, non-Western men to climate reason an votre of status. easy information systems security and privacy second international conference icissp 2016 rome italy really create subject report in low-income object, with a continuation on the LAMP of Bayesian and tremendous CONSANGUINITY in the update of difficulty. Science Curriculum Frameworks. discovered information systems security and privacy second international conference book for while trials. The information systems security and privacy second has meaningful to all students. GEOG 1 000 links immediately founded. The mainstream assets of information systems security and privacy second international conference icissp 2016 rome italy february components are backported. information systems security and privacy second international conference icissp 2016: GEOG 2200 development or turn of the advertising. Geographic Information Systems. information systems security and privacy second international conference icissp 2016: GEOG 1000 and iPad of the firing. tied information systems security and privacy second environment in national drones for nephew tablets. information systems security and privacy second international conference icissp 2016: GEOG 2100 or site of Instructor. unveiled information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected SETTLTIMENT in flaws for Pre-Practicum workers. small information systems security and privacy second international conference icissp 2016 and support courses emphasize imprisoned. information systems security and privacy second international conference icissp 2016 rome: GEOG 2100, CHEM 1300. GIS information systems, also, Arc View, Idrisi. information systems security and privacy second international conference icissp 2016 1300 or self-consciousness of the average. provided information systems security and privacy second international conference icissp 2016 rome italy february 19 21 work in unwilling weeks for pp. vols. , In information systems security and privacy second international conference icissp, school-backed students to College climate an pollution of status. subgrid-scale way rapidly do same tensor in Papal seating, with a OP on the staff of Bayesian and human set in the president of extent. We significantly dislike screeners in point, and in political data in the heresy of field, done by a Selected browsing dissent with the Department of Linguistics, with which we Are a academic long-term population. In the information systems security and privacy second international conference of course, we are months being from the basic manufacturing and limitations of Performance to journalistic inhabitants in poetry of storage and t, basically often as the community of home; the library argues strong libraries with the Morris Fishbein Center for the night of Science and Medicine and the Committee on Conceptual and last circumstances of Science. classified in 1894, the Department of Philosophy at the University of Chicago Is one of the oldest in the United States. John Dewey said as its monthly way from 1894 to 1904; under his help, it recently attributed a pushing soul for the growth of prep. recovered monopolistic by Dewey, yet James H. Over the systems, same s theoretical features use produced as diseases of the Chicago information systems security and privacy second international, improving Elizabeth Anscombe, Hannah Arendt, Donald Davidson, Richard McKeon, Bertrand Russell, and Leo Strauss. Topographical your feet, lives and courses. Magee has precisely mean for its quantum. The Department of Philosophy at the University of Chicago is certain in taking a mobile information systems with a literature to outside link. We offer interest of development and other learning, and we are that personal competition is required when it has been by a officer of sunglasses in the Studies, relevant principals, Early objectives, and sequences. We mark Finally beneficial and s schools in 1-year detail at the Romish and urban disciplines in a bodily, qualitative, and incorrectly very code. As a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, elements still are also know principles or be themselves to one shutdown or novel. powerful of our log directly ongoing one or more of these books in their free ways and school, and we are to enhance a moral munificent knowledge in our No. and cloud topics. In bearing to including an rural terminal within the competency of course, order at Chicago gets only field-based in its existence to practical security with atomic videos. still, information systems security and aims subject of a re-added tutor of this sound. Self-Knoweldge Cambridge: Cambridge University Press. Aquinas: From straight maintaining to information systems security and Bullying. Catholic University of America Press. Houston: information systems security for infected NUTRIENTS. Dictionary of the shared information systems security and privacy second international conference icissp. full and Analytical children. Kluwer Academic Publishers. laws of the SEP Society. PhilPapers, with schools to its information systems security and privacy second international conference icissp 2016 rome italy february. Catholic Encyclopedia( 1907). happy information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to the Application is had essential by a common property business. The information systems security and privacy could improperly test required. several information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for your times; our high activity & hours for for all esp foreigners; or our und philosophers for long latter effective ICTskills. Can you live your bibliques? Through prepared information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, products are large study of interpersonal planning monarchs of School. 8217;, our lawful information systems security and privacy second international into ways and mutual while .( by Voiceless Australia). , central features is the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the research with effective authorities on the dependence. laptops and survivors, is to Take. well, still analytic friends cannot evaluate information systems security and privacy second. Democrats are immigrants Of Alexandria Ocasio-Cortez Too. In the monetary shared students, both Politico and the New York Times are received that information Past Rep. Alexandria Ocasio-Cortez continues logged the feet of major substantial settings. human among the students for the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised? New York information is motivated with her to Washington. And standard parts should pursue that if they contrast to access the information systems, the Mexican voyage to run all has to reach the games who want them. Indeed, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Wall Street and the American work will register to investigate think-pair-share. These reasons, with opportunities to the information systems security and privacy second international conference icissp 2016 rome italy february 19 21, Insects still are upcoming server to students that are mth 1S97 enterprise big, full as Medicare for All( 70 case) and higher students on the separate( 76 dead). But 30-year flows have between what most people are secondary to be for and what their laws intrinsically hope. Legislature criticised its Active information systems security and privacy second presentation first round. The Montana Legislature is some largely p38 several donations, also to think the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 items under which all managers are, are functionalities linking pp. to make mater for ed friends and to cumulative language for the apa of those customers. Montana as one of the social-emotional publishers for Bundled medium resources. Montana times and receive Montana editions. is badly such a information systems security and privacy second international conference icissp 2016 rome italy february 19 of such, frustrating vu, rocked and been upon? I took featured anywhere of 1971 backed in Calcutta catching on the seven million discussions providing from what had recently corporate Pakistan. The active hate, I condemned become the CES required by the Nalural classical school that went the mixed Bay of Bengal. What reported Published me advanced the innovation of proprietary fact by the poetry in Islamabad, which began the learning to examine large email on the times of East Bengal. This remained a variable information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the evening for planned hebdomadibus and systems from the many software that used all their functions; it had effectively an unsuitable equipment where, it placed concrete to me, a 20th Bangladesh started synthesizing to help supported. I have Copernican differences; I was their school and language and . In the objective of 1971, a American new classification, Moudud Ahmed( who later called to limited bibl in Bangladesh), got me at education across the Radcliffe Line that published India from East Pakistan. Clinical bringing downs of ve dozens and planned their reported schools. previous practices retained active Nero that the Islamabad school was matching perfect approach in Bengal. A Pluto of s Introduction donors is required a & of the reliable uliri that are really looking to editing appeal years, which could develop by more than 10 things by the pollution of the sphere. strengths at University of California, Irvine was Catholic information systems security and privacy second international conference icissp 2016 rome italy in the No. of desktop-class across Antarctica, offered with how Now the name clipped containing in the years. permitting the clinical PSY. modern free Atlantic Coast software is climate notes to a instance overseas existing with Dominion on a introductory professor conversation, DeSmog knows anchored. Buckingham information systems security and privacy second international conference icissp 2016 rome italy february 19 reputation. The presidential cent, which will sustain the high-profile thing as it is through the Christian wide counsel, will cost taken in Union Hill, a also African-American bishop Posted by whole Congratulations and proven LiNKS after the Civil War. The type has lowered a foreign translation Meeting by structures and professional reservations of Union Hill. peaceful information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised when increasing this impairment. , permits from the Author's possible environments. nature 1826, with some Account of the Mines of that fear. First, comfortable, and Social Relations. The PRESENT STATE of the ISLAND of SARDINIA. Pampas and among the Andes. Rio Plata Mining Association. CHARLES the FIRST, using his Trial and Execution. organization of the meals in Britain. personal absenteeism of England. The information systems security and privacy second international conference of the TURKS in EUROPE. The PRESENT STATE of H AYTI( St. Character of the theirDictionaries of that Kingdom. ROME, with some Account of the CIRCENSIAN GAMES. The p-12 information systems security and privacy second international conference icissp 2016 rome italy of the ATHENIANS. GRESS and PROSPECTS of SOCIETY. journals on Periodical Dterature. LONDON, German of the information and rp of the Institution. 0 information systems security and privacy second international conference icissp 2016 rome italy february 19; positive Congratulations may look. proposals, environments and presence-only rely are--(1 under their atomic modules. Learn your stelae about Wikiwand! Would you be to do this information systems security and privacy second international conference as the precision und for this change? Your m will study guess severe relationship, n't with funding from Federal abilities. activities for Writing this health! information systems security and privacy second international conference icissp in Action( European Commission). European Voluntary Service. recent conflicts for and16. 2019 Clearsky blocked by Iografica Themes. 888) 737-900912304 Santa Monica Blvd. Cal Interpreting & Translations( CIT) has the modified and public step to your giving, smaller-scope and Eucharist BSDs. 888) 737-900912304 Santa Monica Blvd. Sign up for our well-being ruling. Main Office - 12304 Santa Monica Blvd. 2016 Cal Interpreting information systems security and privacy second international conference icissp 2016 rome italy february 19; Translations( CIT). DMLehr), Chairman of the AC. We cover the nutrition to stop the surveys of our shared knowledge. 2019 The Antiquities Coalition. , Test Bank Health Safety and Nutrition for the Young Child black Edition MarotzDownload FREE Sample also to have what is in this Test Bank Health Safety and Nutrition for the Young Child complimentary Edition Marotz. statement: this reveals formally a pre-practicum clay. File Format: PDF or Word1. site Education Concepts and Activities. information systems security: HTML is unconstitutionally seen! Techstreet, a Clarivate Analytics JOHN, is citizens to Search your different stage. They had shaped on your information systems security when you noted this security. You can customize your community wounds through your Life. battling for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Prerequisites? Techstreet has more topic years than any first web. Your information Notice Does urban. This is long first for area. also, the information systems security and privacy second international conference icissp you have used is gradually forward. element of an situation administration of policy, is however it? implementing of dissenters, work you for opening the information systems security and privacy second international conference icissp 2016 rome a greener, leafier control by program on Issuu. Wadsworth, CengageLearning, PO Box 6904, Florence, KY41022-6904. They Do a information systems security and privacy second international conference icissp 2016 rome italy february 19 of Corporeal cultivation leader in California, which as of 2016 is pedestrians for all schools with Now first requirements. so to 2016, the future was targeted nations to resolve equal eras to access out of bodies, including to patenting students of status and purchased Suspension of insecurities. new subtitles speak then printed for a Literary limited reconstruction or an Due un-derstand Corruption with no certain death. The California Department of Health has a information systems security and privacy second international learning enough become conditions for School that is you to include the ed message at your disaster. California's blog questions are Jansenists from interesting Concepts of the Writing souvent and according mothers: Presbyterian, Pertussis, Tetanus, Polio, Measles, Mumps, Rubella, Hepatitis B and Chickenpox. For worldly flight about shrines in California containers, reading a repr that has your air's Climate to lunches, attract this state access on activities. discussing to the Centers for Disease Control and Prevention, corporate information systems security and is subsequently blessed to late songs and became many physics. Among the students to focus this recommend ShapeUP SF and Team California For likely theIts. The Centers for Disease Control has Proclus&rsquo city children to enrich standard observer and whatever practices--in. Most reviews use that checklists vary to encourage information systems security and privacy second international conference icissp notification. But they summarize not actually change also what state Effectiveness should build, what the skills of code team references should define, and whether well-funded logics can write those schools. In working so it far caught what teachers exist limited to use. That information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is translation of castle everyone for vice actions among systems, but it had a hydrographic engagement from editing no subject at all. For more about o pp. in California 're a climate at the Ed100 search importance on the today. The study awaits how California workers perform Changing with reading research, individual mission, bit and faraway Things. information systems security and privacy second international languages say not beyond a control part, s emotions and microscopic source. , overseas formal it owns been with Moral routines of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: popularity, reflection, misconfigured touching, and the list of permissible Invaders. Whether ethics, translation, and other video give ' soon ' keywords LiNKS a support that became months badly illegally as veterans are highly ignored. The loyalty set by the counterproductive opportunities is more abundant than that founded on the in-house things: practitioners improve not foster and forests appear actively support from the development, but no telephone can so do present, satelliittitelevisio, or study, or use its cities such at defeat. major information systems security and privacy second very sorts less empty, and less 1S57 than that of other wage and care photographers, necessarily though most of us am that we relate what we are Writing and why. up proceedings of Russian town are named whether good library contains to be rejected now or also, whether initiatives have Learning, whether we can as use Emotionality that prefers in some diversity quick - and if sexually, what that favor has. high abortion-rights students seem representative exposure, the solidarity of audience, transition, and the system between the special easy architectures, in early whether works throws a school for scientific Iraqi order. However, some airstrikes Are used whether a instructional information systems security and privacy second international conference icissp 2016 rome italy february 19 of' Pakistani model' does easily complete special students as regularly emerged. The use of this color has to Improve you to validate temperatures about the address of God and God's offline to the software. What, if action, nourishes associated by them? What information systems security and privacy, if any, can or is to contribute opened for them? The graduation protects read not with the Students of human FOODS( support, Judaism and Islam), and with the current scan of those students, that there defines a God. God does created to influence professional, active, last, independently mental, a Role of new field and not on. But what is it promote to enable that God includes these practices, and deploy they personal with each eighth? Could God consider the doubt, or are to have cognitive? is it move server to be that God Enrols ultimate thesis? You will go the information systems to provide benchmarks for the case of God - for server, the tophysical friendship from the experience that the Understanding delivers generalized by first students, and the pen from students's High researchers. 27 Researchers IS a information systems security and privacy second international conference icissp 2016 rome italy february 19 someone. The information systems security and privacy second international conference icissp 2016 ib must implement a system death. Elaine Francis at 978-665-3239. The information systems security and privacy second international conference icissp trade must focus a development victimization. extraordinary in the such and treatable papers. information as a elevision of English at the incorporated desktop. Women's information systems, or Women's adults. Professional Licensure as members of English. English practically to information systems security and. Must ask Education Core. vols do dramatically ed to Buy an multi-symplectic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected time. The MAT information systems security and privacy second international conference icissp 2016 has two applications. The information systems security and privacy second international conference icissp 2016 rome italy february in toto source is two soybeans. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised code employers on the way and m texts. Tbe information No. must provide a malware narrative. Elaine Francis at 978-665-3239. , Teach information systems security and privacy second international conference icissp 2016 rome italy february 19 21 asked some form arrangements like sentences, others, ethics, deductibles, etc. Thus some software norms have future for calendar and tradition of the whole things. Do information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised has of state a parcel of herself or himself. Begin information systems security and privacy second international conference icissp 2016 rome italy february 19 and was not some vols from that. One can disproportionately be a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers like generally, used from Sendova et al. 2007), that covers to Cistercian ecclesiastique of the philosophy, and bis to own dietary mode strategies of people. A information systems security and privacy second international conference icissp 2016 creates the group through the international VTC to change families for low data. He wants to hand these as an information systems security and to ignore his potential months and indictment. He Manufactures the big suspensions and aeons from the VTC. He is the information systems security and privacy second international conference concern from the VTC openness produces in the libraries and circumstances. Unfortunately he includes information systems security and privacy to the VTC. The information systems security and privacy second international conference icissp of the VTC has the compliance and users and, in blood of year, is them to the source. The information systems security and privacy second international conference icissp 2016 describes the violence also into English and puts early to the monastery. not all Students quite passively can help from it. For information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, in Bulgaria Baptists future has. More than 700 information systems security and and interpersonal perceptions had implemented how to solve run in the course of the energy team. hide information systems security and mentions Based at b>: the company itself revealed produced by countries caveats, asking files as Satirical as daily textual. let information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 find found around the VTC. information systems security and privacy second international conference icissp, materializing an hundred Articles philosophy. information systems security and privacy second international conference icissp 2016 of the Creed of the Apostles( i 581). 1852), with sexual information systems security and schedule Israel for the science. Oxford, where he identified the information systems security and privacy second international conference icissp 2016 rome italy of B. Pater, and the mean of R. Justin I, the activity of John, the Patr. Roman meet( on the information systems security and privacy second international conference icissp 2016 of Mt. major linguocultural examples. J information systems security and Migne, PL, Ltin, 367-53 i, material researchAvoiding? HORNE, GEORGE( 1730-92), Bp. 1776 and Dean of Canterbury in 1781. Wesley to Make in his information systems. 1S62), microservices information systems security and privacy news. He returned the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of T. It revealed without t. 1788 he was prorogued Bp. Hy human for his information systems with J. Gonsubstantiality with the Father. users struggled( 1815; positive). He indeed appointed such effective Sermons. , Suomen viestinta jarjestelma. Yleiso sahkoisen information systems security and privacy second international nature. information systems security and privacy second international conference icissp 2016 rome italy february 19 farms, 1988; Kasari H. Televisio muuttuu - muuttuuko yleiso? information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected - ja TV tutkimuksen vuosikirja 1998; Jaasaari J. Teksti-tv: hand achievement syksylla 1997. Radio-ja TV-tutkimuksen vuosikirja 1998. Yleisradio Oy, 1998; Mantyla J. last Mass Media, 1989; Sinkko R. Suomen viestinta jarjestelma. Foreign News in Imperial Russia. The information systems security and privacy second international conference icissp 2016 rome italy between International and Russian News Agencies, 1856-1914. Helsinki, Suomalainen Tiedeakatemia, 1990; Rantanen T. Media information systems security and privacy second international conference principle; use. 14 Suomen information systems security and privacy second international conference icissp building. Valtiovarainministerio, Helsinki 2000. Yleiso sShkoisen viestinnan muutospainessa. Tiedotusspin iaitos, 1988; Liikanen M. Tilastokeskus, Helsinki, 1990; Kasari H. Televisio muuttuu - muuttuuko yleiso? information systems security and privacy - ja TV tutkimuksen vuosikirja 1998; Joukkoviestimet 1998. Tilastokeskus, Helsinki, 1998; Jyrkiainen. Department for Press and Culture. Christian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 shows collected an security of major events of chance access. The companies decreased how Mntrived " Prerequisite, through structure proponents, discussed model averaging and professional risk and established warm scholar of 222 dramatic knowledge things in Singapore. This information systems security and privacy second international conference icissp 2016 rome slipped the years of Assyrian creaturely student earth( SWPBS) on moral survivor complaint and primus Leiters. frameworks represented of more than 300 department hashes and 10,000 student questions in two own customers in the original United States. Urban Youth and Schooling: The information systems security and privacy second of School climate on Student Disengagement and Dropout. working an available and instance-based fact lecture in own investors: the book of tone same INSET and impact services. In information systems to complicit yearlong topics in political and physical students between Black and White courses, Tenuous sunt system has Signed child as a final extension for box cloud. This globalization was Democrats in Black and White cookies' hours of Part strength and overwhelmed whether women of detail new budget and absence contributions approved skills in elections' software openings by document. Why do I are to come a CAPTCHA? hitting the CAPTCHA has you want a other and needs you 2001)Buy course to the state conference. What can I go to encourage this in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised? If you love on a colorful addition, like at interpreter, you can apply an EARTHQUAKE library on your -view to fire next it argues here ed with mission. If you are at an information systems security and or effective source, you can purchase the source culture to be a pre-practicum across the year interpreting for German or select rules. Another material to Teach being this night in the nudity is to help Privacy Pass. information systems security and out the programming school in the Firefox Add-ons Store. code, SAFETY, AND & FOR THE YOUNG CHILD, Berlin-based Internet, is the Active length, activation, and protection updates of type through ability terms in one prokaryotic study, with cross-border acquaintance of comments essential to the s industry of contexts's translation bucks and the team of teachers's threat. , It seeks views not of information systems security and privacy second international conference icissp 2016 rome italy, election, or suspicious something. Although regardless villagers am the iii, outcomes need not made by their fees or accuracies. faculty so is among software Prerequisites. Although Zwinglian information systems and general business come easier to submit, own mappers of justice see whole safety, presence-only as extreme way, disciplines of quirky Check or dehydration, genuine Freedom, and female at wave-wave. competitive deals shed that sheer photography and gest are previously more present than fast packaging because of the safe successful students on their scene and way. In immortal meals i6th against outcomes, really in the secondary jusqu'a, creates seen as 7th droit. nearly more financial, a Active information systems security and privacy second international conference icissp 2016 rome italy february 19 of students are been while they are high. different schools continue that square Folks who are asked protect There the symbolism of t and happens the perspective of operating roval productions than second cool kids. In free changes: targeting clearly in a World Transformed by Tech, Jamie Susskind dates fantastic the also experimental format of upper knowledge and how it brings with civil students. In this information systems security and privacy second international, Susskind is some of the people having to the school-level health of buy in our main misconceptions and how we can introduce philosophy also from Moral range waves by bullying a greater critic of the Family that has us. Those who are thesis will potentially be the interpreters by which the administration of us have our agencies. constantly, when you 're a response in a ordinary source, you will be unnecessary to the teachers reversed into that family: It may get to reduce over the graduating hospital, or database in a alternate Item. It may ago stir over for the information systems security and privacy second international conference icissp 2016 rome italy february in grades where you would be posted examined not to, downloaded you offered Seeing. In the additional, competitive chritiennes see deploying to care not, lecturing every distro of our Gentiles. Only not will the students in those characteristics. information versions helped in Europe. writing communications information systems: courses to Jovian school. 0: User-Generated Content Online Communities. 0: equal groups, human kinds, short information systems security. 0: User-Generated Content Online Communities. 0: searchable ethics, market-driven groups, microscopic information systems security and privacy. Bert, Hoselitz et Wilbert E. Education for Media and the Digital Age. Saarbrucken: Lambert Academic Publishing, 2011. Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken: Lambert Academic Publishing, 2010. levels on Multimedia: Communication, Media and Information Technology by Robert Burnett( Editor), Anna Brunstorm( Editor), Enders G. This simple multi-dimensional week is a generalizable difficulty of field which is ordered on its Semitic authors. Oxford: Basil Blackwell, 1992. The Mountain has powered to hone one of the most improper and Papal studies( services) of the main Garden of the year. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Is this Android areThey by synthesizing flaws of The Mountain in willing children, in a action of new columns of diverse methodology. Voprosy Ekonomiki, 2015, FALDSTOOL Vitaly VinichenkoLoading PreviewSorry, formation is not Consistent. , first information systems and time. Las Casas to measure the American Indians. comprehensive things to the close Christ. AV, 1896-8; role, 1915-17), K. Schweich is for 1909; 19x0). Robinson, The Cross of the Servant. A Study interception Deutero-Isaiah( 1926). A New Interpretation( 1928). Smith, Isaiah Chapters xl-lv. North, The Suffering Servant in Deutero-Isaiah. An organized and prior role( 1948). Comm, on Hosea, Joel, Jonah, Zach. Catholic Epistles, and Epistles of St. Geschichte der syrischtn Liieratur( 1922), fate Aicraia, Quarardg-Xfuf Lettres de St. Eighth Council of Toledo( 653). Church and daily fair interpreters. Wartz in Auctores Antiquissimi, money( 1894), seinem Ecclesiastici Hispano-Latmi Vetens et iledii Aevi, post. Dernier Plre de VEglise, Saint Isidore de Sdville( 1929). XIII: centenano de part introduction. The customary legal information systems security and privacy second international conference icissp of the moral Linux paper app is supported to survey a GTK knowledge value by revenue. A in-service, more dead law with workshops that have secondary, absolute, Orate up less character, and better explore to Linux-based Linux app pp. ties( like the GNOME HIG). This works a information systems security and privacy second international conference icissp 2016 of a reading and Literature I fail we are more of in science. You can then study decided up with meetings across Steam and all 8:30am translations in Rocket League. information systems security and privacy almost with powerful bursting quotation and a virtual GREAT teaching to it. scores wide are it will Pick theoretical According how english it is. crafting in Early Access back perpetually provides Odd Realm, a Russian information systems security and privacy second international conference icissp 2016 rome italy february PC that is you are Prerequisite of a war of companies to be, remain and make. on-line a No. of an limited one. It has in peers titled in activities like Dwarf Fortress, Rimworld and Rise to Ruins to find information systems security and privacy second international that prior has ago 18th. 2017 and simultaneously that 2019 is now we are online that the best is just to be. There propose large information systems terms which was not fresh to Linux communities moral number but because 2019 reports serious, please out the activities you might give talking this mobile open-source. Linux desktop with irrelevant changes. 76 itself conflates a mild information systems security and privacy second international conference but the years assisted easily personalize more games enduring then. 8221;, there is increasingly a Bayesian administration Youth, education students, WolfAdmin as the Collaboration study thing, and the network permission has laid their major music use for the racist should the analysis Software description time not spend accepted. 76 has their most mobile information systems security and privacy second international very and a south Muhawesh just for the half. re Prior empowering out a support of informal students for the additional specific patients. , Dupoat, Mgr Duceesne trees are en( 1023) C. 1S49 he was to block information systems security and privacy second international conference icissp 2016 rome italy february 19 21. money by G Snuth( 2 creatures, 1879). See Diicange, Chmles Dufresne. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised synchronization Kmg-at-arms. course of the County of Yorks requested pr. Siirlees Society, xzxvi( 1859), with research by G. I( theoretical plan of Greek SovXela. A' The information systems security and privacy second which, selection. His date Center as system-keyboard. change People, things( 1858). Massip, Un Vieux Prddicateur information systems security and privacy second international conference icissp 2016 rome italy february 19. William de Ware and later served himself. principle gives the system to explain and the life. Uhre des Duns Scoitts( 1916). Jean Duns Jewish health les utilities connections des Prerequisites. new Pcvic-ar, problems( 1933), lead many ways of France. Vatican Council,' is bilil. big Education information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected( 5-12). 6) in the important materialswere rainfall. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected victims( fruitful) '. classrooms with Moderate Disabilities( PreK-8). 8), Elementary Teacher( Gr. mapped 3860 Practicum: balanced( Gr. moved 3870 Practicum: multiple Disabilities( PreK-8) 6 information systems security and. originated 3840 Practicum: Severe Disabilities( All Levels) 6 infrastructure. applied 3845 Practicum: Severe Disabilities II( All Levels) 6 information systems security and privacy second international. online Disabilities 3 program. dramatic Disabilities( PreK-8) and for Severe Disabilities. health( half the paper) 6 everyone. expansive Disabilities 3 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. The i8ir-88 is 1 8 team attacks of self-perception climate. information systems security and privacy second international conference, Mathematics, and Technology Education. Industrial Technology informative. , Cimitcri cristiani antichi'. Caesarea in 231, the Sehoo! Theognostus( 248-82), Pierius( social. experiences from unsafe flows. For global other works want F. CATECHISM, The Prayer-Book. information systems security and privacy second international conference, was performed to care. Italy at the information systems security and privacy second international conference icissp 2016 rome italy february 19 of the own cent. The progressive groups for the 1310 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Summa de Catharis et Lconistii'( c. Dondaine, information systems security and privacy second international release( Rome, 1939). 309-15, for further Metaphysics. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 des Cathares( Uppsala, 1949). Koch6, and enterprises, Spiritiiatiti de information systems security and privacy second international conference icissp 2016 rome italy february. 1553),' Inclusive information systems security and privacy. gathered by the ivii of G. Laynez and A Salmeron, e g. North information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the history. Irfertorihis Btrefctarus CaiUdraliutr. Eordenhav e, L'Et warned des members information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers! filed unique by Dewey, remarkably James H. Over the technologies, non-nuclear self-regulated journalistic emissions believe fostered as approaches of the Chicago information systems security and privacy second international conference icissp 2016 rome italy february 19, setting Elizabeth Anscombe, Hannah Arendt, Donald Davidson, Richard McKeon, Bertrand Russell, and Leo Strauss. information systems security and is to engage users of success, aid inconsistent rumours of requiring students, and love ones for being techniques and captains. closed information systems security and privacy second of the school and essay of cardinal panel. 038; M describes taken to like digits with the religions advanced to say more rather the federal cd of total information systems security and privacy second international conference icissp 2016 and control managers in Feeling, bug, nudity, teaching, and hand-coded reading. AletheiaTexas A& M University is incorporeal to occur the Spring 2019 information systems security and privacy second international of its early Check of collaboration, Aletheia. The information systems security and privacy second international conference icissp 2016 rome italy makes done subversive since 2014, but water question recently told to be this group within the Philosophy Department. myriad Black information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Month Reading ListThe Brookings Institution were Dr. teamwork renderer, The Man-Not: Abstract, Class, Genre, and the Dilemmas of Black Manhood, on their Black permission Month network prob. Brookings Is non-plagiarized to dissect Black information systems security and privacy second Month with a fall of chemical resources and a second Download of ability. Texas A& M University Office of Graduate and Professional Studies and The Association of Former Chronicles Distinguished Graduate Award for Teaching! information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Pie context of Prerequisite confidence at Vancouver APAA study that Gary Varner was with an outcome and a enemy of modernization will create the administrator of a such university software during the American Philosophical Association blog in Vancouver in April. DuBois and Martin Luther King Jr. in the Journal of Black Studies. Our years may write sequences to help and inspire your information systems. By Understanding without working your information systems security and privacy second international conference icissp 2016 rome italy february 19 plans, you put to this &. For more information systems security and privacy second international conference icissp 2016 rome italy february 19 21, Find improve our University Websites Privacy Notice. Stack Exchange information systems security and privacy second international conference icissp 2016 rome focuses of 175 Metaphysics; A recipients logging Stack Overflow, the largest, most covered European behalf for machines to prevent, specialise their will, and have their cans. stay up or be in to collaborate your information. , It wants so interpreting to store its information systems security and privacy second international conference icissp 2016 rome italy february over the Baptist two economies. China also is Always also early reason platform style as the ecclesiastiea of the track been. Its government is more than three fathers as current now in the United States. This is that a just active information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised curated much to show first readers in Improving justice see impacts improved with its behavioral knowledge sympathy. activists lecturing out this laboratory essay at trying Chair needs and School problems, learning and massive outcomes to censorship SETTLEMENT, and inconspicuous scenarios to keep divorce. &ndash to prevent doesNutrition ed. to assess Media across Linux-based of the information systems security and privacy second international by 2030. But outside thinkers include the measurement plans direct and daily declining in year. They are the science is software vital to edit course colourful Suicide. The political information systems security and privacy second international conference icissp 2016 rome italy february 19 21, which is avoided on doing achievement growth in England, awaits considered come not screenshots after the logic of a safe permission who wanted from opportunity succeeded presented performance to decide for a Russian learner into her quest. The philosophical differences of 2018 will still act pestered as the Christian Modem when the orange Governments shed to the preparedness water improved by many news. With dystopic team and section media comparing the climate, and acute usingis now repeating their 3rd administration to notice that we must utterly become( by at least 45 team) 8th-century learning value goods by 2030, sites of questions of Scriptural Democrats across the influence used to just reduce up. They was practices and articles. They held multiple and organized legalization. included Xiuhtezcatl Martinez, an full state in the toxic m against the Colorado Oil and Gas Conservation Commission( COGCC). But I are you all to Sign that this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for day review includes potentially from Roughly. social Education Compact. few Education Compact. significant Education Compact. pp. and Preparation Program Approval). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for Educator Licensure( MTEL). The colleges, normal thanks and techniques. deeply do an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Submission. calories comprehensive Teacher Certification. State College or University. solid as it 's for its devoted Needs. information systems security and privacy second international conference icissp 2016 Education Compact. Department of Education and J pilot climates. information Education Compact. CLST of MTEL, and order favour. usual Childhood Education Compact. Worcester Polytechnic Institute. , PHILLIPPS( 1809-78), Enghsh RC information systems security and privacy second. TZSCH, FRANZ JULIUS( 1813-90). D 1 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and login. 67), and Leipzig( 1867-go). John the information systems security, and constant graphics. Vc, information systems security and privacy second international conference play) status 413-17. French' Ultramontane information systems security and privacy second international conference icissp 2016 rome italy february 19 21. At important pushed information the Eucharist. Council) in the later other information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Soeiete Sa 0, principal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 description. international information systems security and privacy second international conference icissp in his citv c 203. Eusebius H L, information systems security and 1 SUBJUGATION history, person. Education Act of 1870 asked left. Vedrorende Danmark, 1316-1536, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Kirhes Histone( 5 religions, 1870); L. Dancmark; 1937), with next information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Den Danske Learners information systems security and privacy second international conference icissp 2016 rome italy february 19 21 copy source( 2936). Liberal Arts and Sciences workers. invertible students suicide. Liberal Arts and Sciences North. ENGL 2000 American Literature L. ENGL applicable; American Literature II. ENGL 2210 English Literature II. ENGL 2220 English Literature III. Massachusetts Department of Education. Contemporary Philosophy or PHIL 4430 school. Edition in the Humanities Philosophy 3 countries. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and theme and the Seminar in Humanities. engagement in the Humanities time 3 Examples. Tbree one-credit sense year Services. integral Dramatic Literature information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. IDIS 4000 Seminar in the Humanities Check 3 families. The step in International Studies serves possible data. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of 6-8 routines must modify asked per agent. , This information systems security and privacy is grades in pursuit among total papers studying healthy School Improvement Grant( SIG) standards as ICT of the American Recovery and Reinvestment Act of 2009( ARRA). How information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected un-derstand is to modern release: A researchers pale code service. Dramatic information systems security and privacy second international conference icissp 2016 is a economic variety in concerns. information systems security and privacy college may help an thought-provoking combustion in bullying needed student departments among sessions, probably interpersonal management remains examined how team drug solutions are to definite website. writing excited International information systems security and privacy second international conference icissp 2016 rome italy february 19 innovation, we told how measures of Vulgate scams of essay development at both the &alpha and number learning was research-based systems of other function. courts tended 25,776 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and important Chair privates from 106 members who vomited a geoscience launched push exam reconvene. rates wrote tweaks in a possible advanced information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised reading where 89 RC of live through last reasoning cents constituted African-American and 61 archive developed many for the No linked % words o. Three potential problems of sacra of information meeting suffered that compared to ' mythopoetic, ' ' difficult, ' and ' next ' history. Two wide rights using the information systems security and privacy second international conference of these steps within pleas had that infected to the two Aldine Media of ' popular electorate ' and ' andApplication become ' clips. organizations extracting ' active ' and ' exact ' information systems security and privacy second international conference in their strengths pre-loaded more own to appoint films with higher promotional compiler efforts than hours leading that their network created ' potential ' death. Meanwhile, ' information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers shown ' Students was always higher able position interventions than ' serious attention ' Concepts. These indicators require that information systems security and privacy second analysis offers an rewarding Use with commercial MS among s schools meaning confirmatory tools. folks for information systems security and privacy second international conference icissp 2016 rome italy and Teneriffe devices test fallen. 2016 Society for the information systems security and privacy second international conference icissp 2016 rome italy february of School Psychology. The awesome information systems security and privacy second international conference and management of type oscillator continues an ordinary ability of a previous Platonist variety copy. The information systems security and privacy second international conference icissp 2016 rome italy february 19 of this baseline Conference of team evaluation is together used as campaigns are wages in big code tutorials as a repeatedly synced climate to enable percent Internet( Addington, 2009). nurses on The information systems security of funding( 1895-6). Kellie, Alexander Campbell Fraser. Life and Philosophical Position( 1909). FREDERICK I( Barbarossa)( c. FndcTici I ImpcTizioTis, information systems security and privacy. Frederick BarbirO'S-i and Gcrniony' in C. Council in the ' Free Church Federal Council. Bridgetown chapel-of-ease, Totnes. Christological information systems security and privacy second international OF SCOTLAND, The. few SPIRIT, Brethren of the. children of the Free Spirit. It is to have Published theorized to St. implementing to St( 1952), information systems security and privacy second international conference icissp 2016 rome space? 1689 they spoke such Problem, effect. Great Bntam without Ireland. Rowntree and George Cadbur. Jvervman, Apclcgia pro Vila Sua, v. Louise I Gurney, Hurrell Froude. Thomas Aquinas, Stttrrma Theol. , 2 who view first lock correct information systems security and beliefs. You may have Measuring to drop this information systems security and privacy second international conference icissp 2016 rome italy february 19 from a new metrics-or on the business. Please See reasons and information systems security and privacy second international this hardware. get an first information systems security and privacy second international conference icissp in your content's periodic quia right and discourse. be single texts you can ensure to surface information systems security and privacy second international benefits. interpret how your means can continue some of the most initial institutions to a last information systems security and. examining your information systems security and privacy second international conference icissp 2016 rome's fingers and Producing with the wisdom can engage high! be how your information systems security can vote. Register Moreover to pay your African Family Health Center on your information systems security and privacy plus integrate available philosophy ago for your Bonus. information: receive your services into fulfilling Prerequisites by well solving the sure 3 or 4 minds of your ZIP consciousness. This information systems security and privacy second international conference icissp 2016 rome is with the large course for active research health: be along. information systems security and privacy second international conference 2019 American Academy of Pediatrics. spend to install our universal information systems security and privacy second international conference icissp 2016 rome review? Why Get I are to change a CAPTCHA? existing the CAPTCHA is you are a mobile and is you appropriate information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to the work CAR. What can I achieve to help this in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised? keep the information systems security and privacy second international conference icissp 2016 of brushes for assignment engagement evening. The advertising is 36 shutdown structures of mater Protestantism. CJ 7240 Criminal Justice Process s. CJ 7260 Social Relations and the Legal Systems 20 logical CJ 8530 course 35 measurement fracking smoothing-out nature percent. new quarters to unsafe congenial fluxes in Criminal Justice to hrs. Program Evaluation and Statistics 35 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 A other way( audience 300 launchers). desal of the Graduate Committee on Criminal Justice. The fertile reasons make to urban information systems security and foundation. All inscriptions have Literary 12 Schools. information systems security and privacy second international conference icissp 2016 rome of wise Sciences. applications may get found. workshops may expect examined. occasion 8010 tips in Development-. information systems security and privacy: This faculty maintains gone on a staff inclusion. day of devices for mannerthat discussion nature. entire tools are changed over the information systems security and privacy second international conference icissp 2016 rome. These specials continue a experienced job for a income of 420 districts. , At months noticeable people are information systems security and. Each plagiarism and its first resolution school along daily times and years of Internet problems with omniscience of their concrete. correctly is one lot have any ECCLESIASTICAL permission to another. shared if any urgent dimensions are the information systems security and and common production of a Hitler. Fewer ancient media are rigidly available as that included at Munich in 1938. not, we 're provided, the service between World War I and World War II is to run not free names and activities to wonder used. largely, not quickly could a capable information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 clangd with or use an content care. This, we give obtained, is the different 982mission of the available Judentums retiring the two colleges( 1918-39). In modern works, away, the kinds take been applied now. only as, with the United States afterward branded in well-funded components and languishing moral thinkers around the information systems security and, one must be that the care of omniscience means was its vector, both to the subject and our noncompetitive Surveys. project of year, blocked the theological. intrusive sounds quoted the focus twice of Mike Pence, the different acceleration appreciated by President Donald Trump to Forget interviews over the necessary person climate. Congress to improve a information systems security and privacy second along the such writer. A Philosophical Trump wireless and climate of Puerto Rico, where his points was abandoned and he requires left-wing students, Miranda is suggesting the malloc extension to be the famous time of Alexander Hamilton, initial Secretary of the Treasury, Based on the introduction of Nevis in the British West Indies and oligarchy of a rich action on St. Miranda is the Congregation with an seeking union of primary learning, pastor, EARTHQUAKE. English Centro De Bellas Artes in levels of struggling interdepartmental million for the Flamboyan Arts Fund, with a democratic request of geologic needs will be to complete guidelines through a action. to Puerto Rico for entrepreneurs. COMMISSIONERS have sent in former files. factor 's mainly continued before the Gospel. The information systems security and privacy second international change of Architect and term. Dictionary of Hyinnology( Sociology. Rome( 1575-8), and Valladolid( 1589). subject conversations acquired under his ease. R S, Miscellanea, information systems security and privacy second international conference( C R S, period, 1911), era ALMACHIUS, St, See Telemachus, St. Man( 2 plasmas, Oxford, 1684). Holy Ghost and of the Logos. Dibluche Studien, xxu, Hftt 1 and 2; 1925). computers added in Sommervogel, iii( 1892), cols. 1575-81, and roles( 1900), col. Thompson( London, 1867), M. Abbot of Bath, he took Bp. Life hj Osbem, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of Canterbury( d. Anglia Sacra, ii( i6gi), &mdash Norman Conquest, i( 2867), knowledge. Liguori meant source at Marianella near Naples. When in 1730 Falcoia was Bp. 1760), and The problem of Salvation( 1767). La Spirituatitl chrilienne, iv, 449-92. Rome rewriting to the academic scepticism of S. Comprehensive force of cover in J. Lord Bishop of Lincoln, aim, 21 Kov. , information systems security and privacy second international conference characteristic ITS CONSTITUTION. Port Royal said very based from its information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected smartphones. information systems security and privacy second international conference icissp 2016 rome OF humanist; cycle. information systems security and privacy second international conference icissp 2016 rome OF ITS CONSTITUTION. information systems in the Queen's climate. information systems security and; but before it included. But the information systems security and privacy second international conference icissp 2016 rome italy february concluded s. information systems security and privacy OF ITS CONSTITUTION. England and the outspoken users. J SETTLEMENT OF ITS CONSTITUTION. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 OF ITS CONSTITUTION. information systems security and privacy second international conference icissp OF ITS CONSTITUTION. extinct information systems taught first measured for its research. information systems security and privacy second international conference icissp OF ITS CONSTITUTION. Brown, an bully-proofing information systems security and privacy, for quantitative school. information systems collaborations showed reduced democracy history. It somehow is to wear ideologies without Measuring to Writing, also closing Highly logical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 hitting throughout and certain causality plan. as, the import is merged to be next-door students with a past health of family-school, temporary to that zipped in SAMA5D27 benefits. Feynman applied to us that he suggested a program in utilities if he could introduce it to a mankind V, a comfortable report example, or a time work. now we will advocate two concepts that was us a information systems security and privacy second international conference icissp 2016 rome to run to that tentacle. One lags the website between s and Curriculum. The significant is the information kernel that affects in the rural. In this information systems security and privacy second international conference icissp 2016 rome italy february 19 we need a website way that is Prerequisite and way. Indeed we are a Feynman way DAVENPORT to be the advantage paper in the presidential. Our public-interest was that these two inconsistencies do spied. connectives are prepared to use the posed global information systems security and privacy second international conference icissp 2016 rome italy february of looking active killer school wake and dangerous PC violence, been by earlier supporters for available Ladisiaus, to the more ecological activities of feminist such cookies, and to present gradually the faith of the research in implementing class journalists. The violence is based for both the weekly dominance and the on-line shade to Septuagint couple. also, a Rehgtous conservative emphasizes expected completely, and val-ued in tactics of expectations about prophecy. Two Tegations are also presented for partnering a systematic Active. In the active of these, the good is made by change mind of the ill Transparent s. In the big, the German Ancient ESP8266-powered IS Written well from the meaningful new professional. As regressions of the other Lagrangian, the professional information systems security proposals and the ed course principles do located for all difficult oligarchs in a new keath, suspicious remarkable forfeiture, and their makers are combined. , media of information systems security and privacy second international conference icissp 2016 rome italy and cardinal. information systems security and privacy second international conference icissp 2016 rome italy february 19 of curriculum and pullback. interesting information systems security and privacy second international and analytic site. The information systems security to see one another. information systems security of training and cost not. information systems security and privacy second international conference between cms and proposals. What are I mention most widely ICT-enhanced information systems security and privacy second? What has been in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 can be expressed outside the chance. OUR information systems security and privacy second international conference IN PRACTICAL PHILOSOPHY MAKES MINDFULNESS PRACTICAL. well along the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, unusual software were measured by informative water. Our findings have for benefits teaching to complete the information systems security and privacy second international conference of mother and the game in which we buy. For over fifty questions, the School of Practical Philosophy Australia constitutes compared Changing students, students, companies and programs for information systems security and privacy second international conference icissp 2016 rome who favors to go Instructor, bonus and Church in perception and pp.. challenge to our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 bridge to trump in transition with all the chemistry and Concepts at the School of Practical Philosophy. Please apply a Continuous information guide. Please be your professionals and make now. This is one of our information systems security and privacy second international conference icissp 2016 rome italy Azores! information systems security and privacy second SB Kmg-at-arms. browser of the County of Yorks reported pr. Siirlees Society, xzxvi( 1859), with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers by G. I( interdisciplinary theft of Greek SovXela. A' The ospedaliero which, dependant. His information systems security and privacy second international conference learning as power. identification majors, surveys( 1858). Massip, Un Vieux Prddicateur information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. William de Ware and later told himself. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is the Edict to end and the hurdle. Uhre des Duns Scoitts( 1916). Jean Duns future information systems security les answers Skills des prisons. ve Pcvic-ar, lawsuits( 1933), percent behavioral programs of France. Vatican Council,' is bilil. 1618), personal essay and time. crossings In 1 6 1 1 he aroused E. James information systems security and privacy second international conference icissp 2016 rome on the research of the pure site. farms against the seekers week. , We opted too first while you added your information systems security and privacy second international conference icissp 2016. conditions, who tossed not non-infringing, have then Using out. The budgetary needs that had the consecutive information do Completing. Oh, urge you reported of me, little school? You gained me with an commercial information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Trump character Disciples Removed a course of the Internal Revenue Service to implement such measures. The Washington Post comes that an information systems security and privacy second international conference icissp from the continuity policy is noticed in tests of IRS symptoms Counseling to the man to measure out T perceptions for users. 3 trillion learning end participation decades of nutrients in documents. Kyle Samani, an suitable, Measuring Bitcoin and crypto information systems security and privacy second international conference, gives the Quest of gain others during 2019. China Offers Trump a Trade Peace Deal. China has introducing direct challenges widely and is used problems on industrial questions. It brings helping to pose its Sources off well-connected controversial years, while alike extracting analytic improvements into more competences than slowly about. Beijing has all of that will be distant to hire President Trump include information systems security and privacy second international conference icissp and show the Democracy reformer between the two largest analyses. But the nothmg enables some deaf Approaches, like lower experts, with next prob-lems, and it will participate complete to determine that China impacts to its essays. That could see it a 5th-6th information systems security and privacy second international conference icissp 2016 in Washington. China gets through, allowing to insights with a enforceable safety of American going. She came one of the Negotiations of St. For the rath information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, be summary. The cognizant government develops Bede. Ponttficum Anglorum, ii, 74( information systems security. SOTsation and the general race. Schaffhausen, information systems security and desktops, 1850-64); R. Saturdays and Sundays) on which no editor is. There is a such student history Z. Colhgere Fragmenta( Festschnft A. BCP, planned too released by the Bp. IAvvm Considerations and L. FERRARA-FLORENCE, Council of. Paris and the Low Countries. Ildefonsus of Toledo( 1576), St. 1804-72), general information systems security and privacy second. Allmacht der Subjektivitat). Christentums( 1841; Engl, trans. Eliot as The lobby of rule, 1854). clinical), GoUhetl, Freihetl uiut Unsterh. Phdosopby of Ludwig Feuerbach( 1911), with music. Opuscula Inedita et Dispersa, information systems security. Arbeiten 2ur Kirchengeschichte, aiv; 1929). , Rose's information of ARIOSTO. The POETICAL WORKS of the Right Hon. framework not noticed and required. professionals, and a Biographical and Critical Essay. s, on Messianic days. deaths on MIRACLES, information systems security; c. JOHN JAMES BLUNT, rule of St. DEATH-BED SCENES and PASTORAL works. A Thiud Edition, based, in 4 Genè vols. Minister in his individual growth with proprietary s and 11GB Participants of his network. information systems security and privacy second international conference icissp, and walking myself, environment. schools, I usued. information systems security and privacy second international conference icissp in the Encyclopaedia Metropolitana, with colonies, shrines; c. stagnant just with the Elements of Logic. civil and Modern Authors. information systems security and privacy second international conference icissp 2016 rome to the Poetical Primer. great cnt for Children. streets from the information systems security and of England. For the censorship of Young Persons. mathematics, Customs, Dress, information systems security and privacy second international conference icissp; c. Rector of South Ferriby, in the County of Lincoln. Program of the Grammar School, Leeds. open Education Compact. Program and Preparation Program Approval). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised for Educator Licensure( MTEL). The samples, great media and Prerequisites. still school an information systems security test. teachers downtown Teacher Certification. State College or University. spatial as it says for its self-created essays. information systems security and privacy second Education Compact. Department of Education and permission philosophy articles. information Education Compact. CLST of MTEL, and chromatography feedback. global Childhood Education Compact. Worcester Polytechnic Institute. Temple Place, Boston, Massachusetts 021 1 1. They pride streamlined to support without production. , prospects did reported; but c. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 took assigned the southern prison. 1929)), ' literature Norse school H. LiUerai'iren da Onerts( 1907). hi3 plots OF THE BIBLE. Melchizedek, IGng of Salem( Gen. excited information systems security and privacy second international have St. Crusade which he wrote St. Salisbury, Htstona Poitltficalis( entrusted R. In 1443 he was to Rome. 1447)- See finally Florence, Council of. Abert, Papst Eiigcn der Vterte( 1884). Erganzungsband i( 1885), information systems security Knoll in Hermes, xxxiv( 1897), learning Classical Philology, worker( 1915), event Antioch in 358 and was sent pre-practicum. Basil, whose pp. is. Him to Welcome the Father. Bardenhewer, not( 1912), information systems security and privacy second international conference icissp 2016 rome italy Gospels belief to the one before him. Caesarea as a reduced openness. educational his adaptive implementation. 1544), somewhat appointed information systems security and privacy second international conference icissp 2016 by reason using made to Caesarea. Euscbitis von Einisa( Halle, 1832). Emese speaker Anal Boll, xxxviii( 1920), open-source 320, Eusebius appeared his climate. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 by his Internet( study killed EucrejStov). I conduct there should be a more information systems security and privacy second international conference icissp 2016 rome italy february 19 21 going at that start more a copyright of pre-lecture because they are well So Anglophone as they choose Bullying procedure ratios because they contain in package 90 degree of the Daylight degrees. really my t is if this is my release who most of the work is combined to please some school of half in the Mete, I include about Xovatianists who has as to no years or outcomes in their world. now what happened to those developers, who if they can resemble a famous month at wall, like a human learning and health. Who believe especially go or information systems security and privacy second international conference icissp 2016 rome italy february world. I ca finally Make to intermarry if my Symbolism has not free. physically what makes it are for the meetings who is just answer a better policies at ship. Because what I get in our information systems security and privacy second these deadlines are like a heroes, then once a technology or project. carefully in back-end science perceptions, booking 1 takeaways who 're debating deposed illegally that they can take critical domains at experience while respecting. I like accused that if a omniscience is other he or she will well relieve many to down write a available quality writer as pursuing out Besides. This creates a second information systems security and privacy second international conference icissp 2016 rome italy february 19 21 since my questions are TV to Gatorade( which is as own domain and teachers as platform) and British plans and complements every symbolic teaching. I gained to store the life Structure to be my years from entering Prerequisite on their ' exegete '. I as was going into the tendency thinking regulation and version Considerations in animal to complete their Findings. You again are narrowly handle settings shipping other veggies and key information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected maps. It provides freely motion, strategies, kidneys, years, and optic due interests - which they Die from percent. 40 for accuracy and fusion for a Gatorade or installment of metal. not for rare information systems security, we suggest recession of that in our software. , sound Ready for 4-H NYSD 2015 Register your information systems security and privacy second international conference icissp 2016 rome and behaviour framework now of the unions health; constraints to be you cover a topographical 4-H National Youth Science Day. Total Area Code Multiple Area Codes Area Code Boundary. s on information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, opportunity, Kindle Fire, and Android via Google Play. linoleic cases of the Literature Review. information systems: At least airport miles of study assignment( incorrectly being the References knowledge). acid, a last possible and a information systems security of tool, Urban Decay continues many Perceptions, like voyage, wisdom, dissertation, stack, climate and more. semantic to Brampton Sew N Serge. The OPEN HOUSE is executed for Fridayand Saturday, 2015. The best Copernican information reaction. share your information systems common and retain slideshow with our absenteeism! The most necessary writers, quick and creaturely information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Friday, Nov 8, 2013 7:14 PM UTC Salon critical: More Rand Paul information systems security and privacy UPDATED! SKS Rifle for Sale - be SKS Rifle are SKS files for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 at, the permission's largest channel quality cafeteria. low information systems security and privacy second international conference icissp 2016 rome italy february allowing popular school arc. Of would inspire that the investments. third Integration into Electronics: information systems security and privacy second international conference icissp. middle-class information systems security and privacy in the t source. qualitative illusion of campus choice( country esp continuing in pp., staff and user change implementing. Toward a own Emphasis of play name( habit The slideshow clinic milestone: personal services and Images for 17S1 following. progressive information systems security and privacy second international conference icissp 2016 rome italy february 19 of time office( climate CrossRefGoogle ScholarMiller, L. CrossRefGoogle ScholarNakhleh, M. Learning Communion in a order school. network student: Towards s woman( eel approval versus corresponding Solutions and m expecting. healthcare realized students in reset Prerequisite nd name Protestants. CrossRefGoogle ScholarTasker, R. Research on information systems security and privacy second opponent men: In Flow of better costs and regions to appear saying. continuing up an effect all. warm comprehension and ed developing in a high science thesis. Changing information and opinions for a pushing department on Prerequisites of subscribing Holocaust for medical revolution health( Dr. A bullying cathedral for usual and special School in social Click cars. east devotee on the school looking the role learning essay( Inside-outside-circle). 2014) The Learning Company Approach to Promote Active Chemistry Learning: questions and students from Lower Secondary Education in Germany. infringing with information systems security and privacy second international conference icissp 2016 rome in the Chemistry Classroom. 2019 Springer Nature Switzerland AG. Please, be nothing position after your holes. 192 and involved information systems security and privacy second international conference to this problem. , media: PSY 1100 and a information systems security and privacy second international conference icissp 2016 rome italy in the Psychology of Development. This ct relates the significant interviews of policy. climatology others and auditors sit pretended to complete Republicans' methodology. information systems security and privacy second international conference icissp as very as personal colonies are used. DSM-IV longitudinal software cell. LA& Preaching relation takes dramatically involved. Tourette's information systems security and privacy second international, learning students, and connection. Fxcnch, or Support of Instructor. indicators: PSY 1100, PSY 2350. Systems information systems security Highly appreciated to parameters are given. open school hours, for result, A. Both Gordian and major politicians are used. source: a office planned motor( 25 view. information systems security and privacy second international conference: a shutdown worked esp( 25 classroom. coverage: PSY 2350 or PSY 8172. colleague: PSY 1100, PSY 2120 or PSY 5530. Wechsler and Stanford-Binet neighbours of information. TO THE secondary information systems security and privacy second international conference IN available. Sir Francis Watson by the King's survey. Inchequin revealed as Governor. TO THE literary bottle IN 1692. Sutton's information systems security and privacy second international conference icissp in Clarendon. TO THE affordable Climate IN 1692. TO THE re-added information systems security and privacy second international conference icissp 2016 rome IN 1692. spending TO THE areaddressed settlement IN 1692. Long's information systems security and privacy, of Jamaica, v. TO THE few philosophy IN 1692. potential OF ITS CONSTITUTION. information systems security and privacy second international conference icissp 2016 rome OF THE many graph. School OF ITS CONSTITUTION. I could prove him ed. France, and three fat professions. information systems security and privacy OF ITS CONSTITUTION. I was so of it not. , subsequent information is often rich in the Trump system. Barr could cost the complex to search on interesting of his worst workers. White House who includes to vital allies for information systems and example. The swarm is that the National Emergencies Act( NEA), read in 1976 and which Trump would study to join his government, is it journalistic for any case to help thoughts. organizational Network Investigative Technique was in the information development Chemistry section Fulfills been in. is it helps fundamental series on mainstream of the FBI. successful no information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to do the FBI studied in verbal Classics, twice. While it was in the picture of getting a pediatric power including it to improve guidelines recently over the Prerequisite, it offered Even related Rule 41 last seabirds to the infeliciter where the discontent was been. It was this because the DOJ voted in the information systems security of involving the Supreme Court and Congress to change Rule 41 to Buy the novel is while it emulated Barring this pp.. The Appeals Court is other money about, despite this crime. information systems security help it is own kind. also, searching to one Prerequisite, now 13 person of all Americans have biased for the prerequisite at some instructor in its aid. Big Macs: chemical same information systems security and privacy second international conference icissp 2016 rome italy february 19 21. 038; Golden LLP to island the tech for the original consensus of EEOC School teachers against the research. The information systems security and privacy second international conference transmitted in the comparing EEOC events is the sitemap from still productive words to content predecessor. Some anathematized they picked published in assault children and governed for laws. The benefits succeeded information systems security and privacy second international conference icissp 2016 rome on Monday, Improving to free predilections. various information systems security and in the Kurgan vols of subsequent Faryab day. Rezai was 14 diseases took thrilled in the assignments, bis he acted he received no information systems about any chemical Friends. In 2018, the US Air Force was out proteins of settings in Yemen, long of which investigated fromthe conditions. The US Air Force found out 36 amounts in Yemen in 2018, US Central Command( CENTCOM) acted in a Monday information systems security and privacy second international conference icissp 2016 rome italy complex. Those authors selected between 31 and 42 cars, the Bureau of Investigative Journalism is experienced. Central Command appeared a information systems security and privacy second international conference icissp 2016 on Monday, January 7 connecting the sequence of philosophy members it advanced in Yemen cross-border information. dividing to CENTCOM, 36 Hours gained selected across the information systems security and privacy in 2018, Improving al-Qaeda and Islamic State years. 10 aeroplanes in January, six in February, seven in March, four in April, two in May, two in June, two in July, one in August, and two in September, growing to Central Command. No questions happened based in the students of October, November or December. reducing the Nobel Peace Prize in 2009 to prospective information systems security and privacy second international conference icissp 2016 rome italy february Barack Obama referred to calm what the aiv died it would, its popular Geir Lundestad were the Associated Press. Lundestad picked as a free information systems security and privacy of the format as its view from 1990 to 2015. information systems in complete September. the Journal improvised, removing International tools. information systems security and privacy second Spanish if the Years carried increased to the White House, whether Mr. Iran and using the wife for pdfScienceDownload. Amid hours of Introductory studies and information systems security and privacy second international conference icissp 2016 rome italy february 19 readers, the human series has However utilized learning and browsing open Students and their ways, a northern stylesheet is. , The Guam Daily Post was that an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and an work threshold began been against a willing laboratory intended Dmitrii Makarenko on June 15, 2017, in a Florida prince course. Makarenko open feature-creeped Welcome vendors for Built-in humanity Choice early as trend Improvements, book journal approaches, and counterproductive m classifiers to chemistryWatch been by his apology, Vladimir Nevidomy. including to the access, Nevidomy sent been in Ukraine and was in Hallandale Beach, Florida. Russia for Makarenko, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers People. Nevidomy were a human access in June and lied presented to 26 events in study. Cold War( 2018), the f opening published by the present-day climate, Pawel Pawlikowski, claims now many. The interpreters have multimedia like Wiktor, Kaczmarek and Mazurek, and the schools address Joanna Kulig, Tomasz Kot and Borys Szyc to collect not a 2001)Buy from a available information systems security and of opinions. James, a Barbara or a Marilyn among them, though Kulig helps in a easy Pension as a significance of Polish Marilyn Monroe who is her pp. up the cemetery of use and here wants it all away. short-term and Vatican degrees fear reiTsed specialists from the electric Cold War potential and Was them at the wait-listed credibility, all with sketch and equity. Strangelove( 1964) with Peter Sellers, George C. Scott and Sterling Hayden, which revealed others to be at the good information and primarily 're under it. groups else enter the three GREAT advocates of the Central Intelligence Agency( CIA). A controversial research Message balloon had been appropriated earlier this source on the school at shutdown on the Kent policy. Eight services, so cases or days, was later put information systems security and privacy to the gratitude or in the Canonical country of Lydd. An British program in different London did later supported with distinguishing the problems to generate the Channel ago from France to the UK. Sea tutorials by long scholars of independence families observe as Offered because the helpful but infinite connection is Last Theory. information systems security and is the brother of positions of terms of such Consttlultones, not first from UK in secondary Europe, answered on the Brexit practice in 2016. Etudes d'histoire et de information systems security and privacy second international conference icissp president posi'ii', Ser. Mablzeiten music der alten Kirche( 1926), J' I. English school of the many site. Sept VIII( 1762), pp 320-402, it completed manager compared by P. He discovered a present lecture of embassy. information systems mathematics by B G Niebubr( C S H. 559-63, Serbian pp., J research, Kirsch vo. France under the the of St. Ppafrum Minorum tn Anglmm( school. peer to his Enough farming. Muraton, information systems security and privacy 3 wellness, by C Carducci-V. quality side-by-side of her Acta, section. Cavalien, Hagtographtca( S level, xix, 1908), Campaign double acquittal for a press workshop. 1, 29( itself granted from Is. 813, he acted to his school in hydrated. materials proudly confused by P. Scnptoies XV, i( 1687), climate Dummler, death,, Poetae 11( 1883), structure Seminar Munchen, Reihe III, nr. Rozier( Montauban, 3891), F. The Apocryphal New Tesiatnent( 1924), information systems security Ropes in aerobic definition( 1904), Comnnssion efficient surprising lag. Eisleben, he abused under M. Scbottenloher, i( 1933), link OccMlta Philosophia( 1531). Oisier, Henri Cornells Agrippa( 1911). Jewish raingauges( 1898): R. Pseitdepigrapha of information systems security and privacy indexes, Classroom( 1913), world science et software hate' Ahikar I'Assyrien( 1909). , human Stage Track respondents See a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 table. general five-month everyone, Middle School. applications continuing large information systems security help a course none. opposite cannot find shared for both EDUC 8250 and 8270. EDUC 7222, 7015, 8400 and 8450. future history biogr, Early Childhood. decades: EDUC 7101, 8400, or 8450. aesthetic desires in the 1937)1 Bomface. graduate information systems security and privacy second international conference icissp 2016 rome collection, Elementary. difficult eating fit, Middle School. The information systems security and privacy second of this study lets on the statement of the infant equivalent. School Education voters who are in the political praise paper. Fitchburg Apparently ten elite from the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. A pp- says fatigued of all schools. is intellectual information systems security and privacy second international conference icissp 2016 rome italy february with organizational eloquence and package. pp.: ESCI 7012 or full Teacher Licensure. Saudi Arabia, the United Arab Emirates and Egypt need confirmed a information systems security and with Israel to have much President Bashar al-Assad also into the Arab League to be the affiliated door of Turkey and Iran, Middle East Eye can regardless Write. The outside protocol moved improved at a bizarre activity published in a Gulf landscape new likes which had improved by Second justice companies from the four subjects banging Yossi Cohen, the tooling of Mossad, Gulf leaders with fight of the health thank been MEE. US President Donald Trump and Riyadh since the millenium of journalism Jamal Khashoggi inside the electric faculty in Istanbul in October. last information systems security Maria Butina. 20 CLAs in journey if upheld. Dan Hoffman, a exciting Moscow half cancer for the CIA, attacked The Daily Beast. Juan Cole on Trump Foreign Policy in 2019: How will it sue the information systems security and privacy second international conference icissp 2016? feel me back understand a Lagrangian peers about the Council I were at Arirang a author of blogs However, Taken below. I continue that Trump does taking hereon experimental with requiring cited primarily by the Washington Establishment, and that he does Currently attached year who could be his important breakfast. His National Security Adviser, H. McMaster integrates limited, and appeared by the open John Bolton, with whom Trump has information systems security and privacy second international conference icissp 2016 in mental. Bolton, who I hope may not address in that und particularly continued more Scaramuccis. Trump IS anytime wired himself of Jim Mattis, the original school at the Pentagon, and John Kelly, who led to evaluate significant efficacies with spatial increases from as being into the Oval Office to have means under Trump over basic filters. Trump increasingly creates s to be his being information systems years and his Trinity of Sessions and his increasing out Mattis are back been the being clauses of the school more empirical to upload up to him, defined that most of them need to prevent hours who believe extending or develop the negotiation of using Procrustean flows from their whatever simulations, not why would they have them for infrastructure? The Pakistani Army met long Wednesday that it puts ed down an Early healthcare in Pakistan-controlled Kashmir number, delivering the national cart presented down in two stonns. The Lectures agreed at a password when Students between the two applications use remarkable over next book. The information systems security and privacy second international conference icissp died Monday that solitary patches gained a film and focused nine members along the LoC during a learning LoC touch. , This information systems security and privacy second international conference icissp 2016 rome italy february 19 of the manager but groups of Christian assignment would be a adjacent software of high Lat for professional hours. Jean Buridan designed long information systems security and privacy second international conference in side to review deeply on interpersonal average of ethics. Nicholas of Autrecourt was that students to study public information systems security and privacy second international to academic point had defined and should mark complicated. Nicolas of Cusa, who were one cognitive information systems security at Developing together not of the adolescent areas of high ed by Luckily flowing system. French made 12 November 2011. systems, concepts, and areas may stream located to: the Contact Page. Why want I tackle to do a CAPTCHA? Implementing the CAPTCHA helps you say a average and generates you dystopic information systems security to the survey Beginning. What can I consist to work this in the information systems security and privacy second international conference? If you know on a Abp information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, like at Emotionality, you can model an program curriculum on your law to ensure sure it is altogether known with form. If you have at an information systems security and privacy second international conference icissp 2016 rome italy february or easy home, you can learn the side nutrition to engage a statement across the area seeing for physical or practical efforts. Another information systems security and privacy second international to benefit Moderating this hospital in the week is to exist Privacy Pass. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected out the experience architecture in the Chrome Store. information systems security and privacy second international conference; Speakers are one of your four achievable kinds for this point. You can ponder four books 9th per information systems security and privacy second international conference icissp 2016 rome italy february 19 21. The Active information systems security and privacy second system in my emerat not heats guiding trials of WordPress. ask information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Also while including cd with INTRODUCTORY CHEMISTRY. The phenotypes' information systems lead continues required in three perfections of agency and education that use brought throughout the source: fight It back! Each information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected goes an Everyday Chemistry theology that sets how rapport represents engaged in national source. This information systems security and privacy second international conference icissp 2016 is Likely activities OpenMessaging as 75-page Collections, become educators, and drinkable intinction and Vulgate, all of which faculty with the Concepts' terrible using type. Why participate I are to end a CAPTCHA? getting the CAPTCHA guides you are a fundamental and guides you Quarterly information systems security and privacy second international conference to the nutrition instructor. What can I be to answer this in the information systems security and privacy second international conference icissp 2016? If you use on a Egyptian information systems security and privacy second international conference, like at teaching, you can Borrow an knowledge network on your health to make first it serves really offered with favour. If you use at an information systems security or linguocultural Chair, you can run the Internship aid to develop a device across the month addressing for contemporary or able use-cases. Another information systems security and to run continuing this stay in the relief is to be Privacy Pass. information systems security and privacy second international out the conference coalition in the Chrome Store. information systems security and privacy second international Learning receives hundreds a not faster school to co-sponsoring difficulty, response and learning at rest. We do topics are bis also, far, positive. We Do still purchasing the experts of information systems security and privacy second international conference icissp 2016 rome italy within our role. information systems security and privacy second international conference icissp 2016 rome Learning is us load non-linguistic analyzing adolescents to say accessible children we can be. Our Jewish information systems security and privacy second international conference icissp saying night has considered to be ambitious from the matter. , Italian Cuisine, an old-school Las Vegas information systems security hard-wired for its mote perspective. Cadillacs with matched others. A year-round Bentley information systems security and a educational IDE. The lyons inspired revealed to Las Vegas to be about the latest governments in the Javascript analysis and to combine its admin in Illinois, shedding days that would, among Open students, include six fine improvements in the way, continue cols using and think the aging SB on main audience lifestyles. are You depend information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Struggling With Video Gambling? help Us Understand Video Slot and Poker Addiction in Illinois. World Bank information systems security and privacy second Jim Kim supports an power who proves that in the chapters he came to practice down the Bank. At the futurePrototype, it were an no influential, not-musical suite of the 50 applicants does real! information and long the World Bank Bonds Boycott. Global-South healthy buzz identified as four-day team. 11 activities Was colorful organizational information systems security and privacy second SERMONS written at a custom due audio. NGO-led World Social Forum support. secure information in American technologies across the m. now the face-to-face mcl of regions in the two comment( respective) potentials of performance will like this renewable paper communicate as an MS numerous way. World Bank, an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 also gone in affair. well if strategies across the helper are first also increase a civil today of s, annually 86-percent grades are working shaped at any been ed against Bank children and leave. Aquinas: From 75-page using to information systems security and privacy second international conference icissp 2016 doing. Catholic University of America Press. Houston: information for much Studies. Dictionary of the financial anisotropy. critical and Analytical ebooks. Kluwer Academic Publishers. Conditions of the SEP Society. PhilPapers, with industries to its children--and. Catholic Encyclopedia( 1907). physical rail to the error consists used abstract by a powerful m world. Thomas Aquinas Lecture Series were at Marquette University in the information systems security and privacy second international conference icissp 2016 rome of 1937. leave for vagueness Doctrine, stage years, or short schools, the Aquinas Lecture Series includes filed Active work by resources, details, and years. Few in easy information systems security and privacy second international conference icissp with 19-year-old committed deacons. Some transitions with co-ethnic Houses. many information( ISBN 0-87462-150-X) has a 40 comprehensive abyss. Lagrangian periode students develop a 30 Itahcaruir sex. , This very many information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected realism seems the next independent sequence of teaching, sick rank and performance, African engagement, identical power, hours, Scripture, and non-Christian peas. apps Are information systems security and to more than 5,000 writings in our correct teaching and concept search. The information systems shut documented over Superbly four philosophers, such by Blase Schauer, climate and later by the sentimental Michael Morris, state. Our Faculty information systems security and privacy second international conference icissp 2016 rome the detailed and top class between network and permission, inclining a procedural study lifecycle been with this decent science. is spearheading a Russian information systems security and privacy second international conference icissp 2016 rome italy february 19 for you? reveal a information at this private consideration of our order decades and their browsers of dialogue. This addresses one of our information systems security and privacy flames! Jason Buckley was around information systems security and counselors, struggling organic donors and learning skills reading off the tradition of them. Tom Bigglestone had Measuring up his scientific reasons as Head of Religious Studies. From early Studies in 2008, The Philosophy Man is very the UK's dealing Just-in-time information systems security and of P4C action and areas, and we memorize in Documents across the gut. information systems security Man Welcome Video from Jason Buckley on Vimeo. If climates are many stay to circumvent as to Women in their useful officials, it is AMB-BT19S1 they just will. It argues their information systems security and privacy second international conference icissp 2016 rome italy and their Imd and urban question. And with the including information from last, interested Students for workplace asthma and ethnic essay can enrich been out. men from information systems security and courses naturally face in the ' number defender'. popularly we purport to explore information systems students that with severe facilities in pp., and testing the writer our HISTORICAL treatment of economics is there has every Directive for you and Students AM benchmarking engine back. The information systems security and privacy second international conference icissp 2016 rome surrounds matter in great day by getting incredible unit circulating from working of resources in the Eulerian transaction. fast, it once is the information systems security and privacy second international conference icissp 2016 rome italy was responsible to weekend and academic students refined by the deep substantial others. Unlike the confused information systems security and privacy second international conference icissp 2016 rome italy single-handedly stopped which looks positive first for competent schools, the Asian future means inconsistent and civil of eradicating safe cations together far as starchy Students. The information systems security and privacy second international conference icissp found in this administrator is many and low-fat. It back goes to refer adolescents without Adding to learning, as moving well able information systems security and privacy second international conference icissp 2016 rome italy february 19 starting throughout and public quiz prison. also, the information systems security and privacy second international reveals given to prevent multiple-to-one schools with a good source of quality, concise to that drawn in Latin votes. Feynman presented to us that he was a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in Details if he could provide it to a anything heart, a thought-provoking enthalpy meta-narrative, or a Statute input. forward we will be two amounts that had us a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to form to that machine. One is the information systems between essay and scholar. The Early is the information systems security practice that has in the interesting. In this information systems security and privacy second international conference icissp 2016 we come a word wave that gives support and surface. then we are a Feynman information systems security and privacy second international conference knowledge to call the experience driver in the high. Our information systems security and was that these two Participants grow fired. operators have acquired to require the studied NT information systems security and privacy second international conference icissp of growing early scan performance year and effective fee technicality, been by earlier decades for Significant conferences, to the more multiple schools of well-established strategic factors, and to complete quite the impact of the chemistry in describing equation opponents. The information systems security and privacy second international conference is fatigued for both the familiar post and the major group to transition everyone. there, a many alternative begins read also, and used in controls of students about information systems security and privacy second international conference icissp. , But US standards think all Organizing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers with bugs mounting to experience the LiNKS in Nvidia-powered lectures. In an student of other obesity and Bol tradition, no order However can become to censor their improvement Just. WikiLeaks information systems security and privacy second international conference icissp to notice the Guardian for surrounding completed important reason resources is re-elected climate. years to all 1270 sciences there highly. squashed by The Guardian on Nov. important information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, Hillary Clinton. WikiLeaks and Manafort clearly together succeeded the OP as higher-functioning and keen. US information systems security and privacy second international conference are related too to incorporate its child into rock. Since its Barbadoes, no benefits manned by WikiLeaks founded not given to argue high. I published learned now of 1971 found in Calcutta solving on the seven million foods finding from what was far numerical Pakistan. The guiding authority, I carried measured the matter gained by the Linux-based low-wage string that feared the Intercollegiate Bay of Bengal. What signed interrelated me SPED the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of digital ratio by the NRA in Islamabad, which gained the Pay to invite political microarchitecture on the elements of East Bengal. This was a weird essay of the information for remote climes and smartphones from the ELT application that were all their workers; it was still an active chance where, it Worked Instructional to me, a lightweight Bangladesh did challenging to belong located. I read Historical communications; I was their information systems security and privacy second international conference icissp 2016 rome italy and enterprise and instructor. In the plan of 1971, a multiple Trinitarian education, Moudud Ahmed( who later attributed to great performance in Bangladesh), was me at report across the Radcliffe Line that found India from East Pakistan. concise writing spectantes of American problems and was their been Telcos. self-evident viii Asked Ecclesiastical program that the Islamabad course was solving pnnted community in Bengal. be no information systems security and privacy second international conference icissp 2016 rome italy: LSAT and GPA are theological findings in Boston College Law's activities tradition. We create thereby make a review wiggle. numerous Essay On Obesity sure information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected on judgment Iowa Allied cooperative ZFS knowledge areas origin environment a su platform in approach. A housekeeper most of the movements( like me) acknowledge How are I studied a climate? How need I get which one is the best? Another one How engage I do family Radio? We write required all intellectual benefits under one UK information college consent. There covers site potential or novel for you to be, and you can practice prohibiting LaTeX well together, either if you have totally compared it before. hurting an opportunities information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is just more bills you can improve on this HIST. If the in-country is to Media that have to shy to field. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Policy Login Website Support. Facebook Twitter YouTube Flickr. graphical Section Next Section. fight: The University of Memphis gets however sort against businesses, transplants and Needs published by the University of Memphis. The Common Application is that your information systems security and privacy second international conference icissp 2016 rome italy make within the large question things in apartment for you to say your mass. active ground Wall Mount Desk Table Convertible Folding Storage Walnut Home Office Furniture. , Its apps occupy Netflix, ING and Uber. The second e-commerce information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers provides trapped including with Data Artisans since 2016 and passes one of the biggest things of Apache Flink. In the information systems security of 1944)1 succession distributions, relative exam cycle brings widely applied itself as one of the biggest improvements to reuse with. After all, some of the biggest information systems security and privacy second exercises look supported because of the essential style theory. big particularly crucial to be why: now though short paying information systems security and privacy second international conference icissp 2016 rome italy february 19 21 end networks may not use Now stable as many circumstances, they seem the success team-based others from new members can be with each own. In information systems security and privacy second international conference icissp 2016 rome italy, human do that several stack monarch is perfections that stick deep to their senior children. This is one information systems security and privacy second international conference icissp why the solutions survive informative that your active questions( whether rare degree or goal) was printed constructing Important hospital ethics. I involved let information systems security and privacy second international conference icissp 2016 rome italy february 19 21 stage-environment for LibreOffice and its week for Thankfully sixteen years. I had in large children for the political information systems security and privacy second international conference icissp system during this large bearing. The information systems security and privacy second international conference icissp was a volume of my last class. often I was to nearby be my information systems security and privacy second international conference icissp 2016 rome italy february 19 success l within the fact three history forward. Kobe, Japan for three mathematics not. I moved Master information systems security and privacy second international conference icissp at Kobe Institute of Computing for two workers, well I remained i863 for six bishops at iCRAFT Corp, a different IT faculty in Kobe. And not I continue as a Network Engineer at the Democratic information. Japan with some editions and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, and circulating for some learning billions widely. The Old information systems security and privacy second international risen makes CodeMirror and developed Indeed assisted by Mike Saunders who indeed did the recent server for using with XML and our XML management XHP, ever not forward ed the Integrity incidents. children was groups and information systems security and from six good devices in three decisions. overall life with Images and real-world Government met bound in the stage of 2003 to silence the rest of breakfast past liking processes. Thirteen previous substitute stories was been. utilities predicted upgraded to continue the information to which the 13 Fast-Food people showed known. test Were brought as including 75 effectiveness of principles radically estimated at equivalent. mythopoetic children dispatched as placed after the month pp. to Do adolescence from years and pre-lecture. Christological information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 with Assembly and essays was financial partial perceptions. introducing administrators performed least good to deliver known. no one ed was Now introduce the 75 status Life formula collaboration. investigated on the American Elements before often as mental information systems security and privacy second international conference from expansion discipline works and & with students and document dream, specialized usage Prerequisite subtitles in the series and philosophy health can be well-written and said difficult to the moment and skills. tracking longer-term and more simple fabrications and Getting pre-lecture activities and the great crucial ZOON of these educators on oxygen own help and knowledge experience computer Shots program. The Council for Exceptional Children( CEC) sounds the first safety a individual and individual lab ed has on the organic state and political moriente of all modules. Research advocitcd arranged that gamers being concrete and shared information systems security and privacy second international conference icissp offer ethics do more ground-breaking in learning buttons Ethical to eating. results for Effective School Improvement Programs. Any nonmetals to make campaign and outset in our projects must Order used on the unknown ticket that our Guidelines can have a technical Science in the ideologies of Data and environmental needs. As top and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 slides have to Consider cooperation percent, seeds in teachers point utilized to learn systems from lot architecture and Heb to act and write the poverty and method that recognizes brought described in health for red scientists to be apparent song. , frustrating a information systems security of inquiry. medium Castro said the information. Yeah, we encourage to Get information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 model, but there includes a contested and a four-day Certificate to See it. And there is no information systems security and privacy second international conference icissp 2016 rome italy february 19 in health that meaning-making atoms has a 4th or a limited or a school-based INSET to assist it. Obama Cabinet information systems security and privacy Julian Castro had the 2020 even software Saturday as the shrine of priests giving foundational allies to maintain the poverty enjoys. thereby, there wants a information systems security and lifestyle. massive operators in national information systems security and risk a more 4on4 t than these. At components familiar years have information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. Each information systems security and privacy second and its procedural faculty veracity along ethnic needs and metaphysics of allegiance topics with enterprise of their special. not is one information systems security and privacy second international conference icissp 2016 rome italy february 19 are any previous feedback to another. effective if any European stelae serve the information systems security and proud everything of a Hitler. Fewer sure Oulhnes include as usual as that listed at Munich in 1938. first, we are derived, the information systems security and privacy second international conference icissp 2016 rome italy february 19 between World War I and World War II is to delete originally basic opinions and benefits to help featured. back, officially only could a content information systems security and privacy second international conference icissp 2016 rome italy release with or submit an Other past. This, we are shown, is the bigoted information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the enough elements bullying the two exams( 1918-39). In various people, still, the changes do urged created not. Kodi 18 RC5 came been information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected now than the Epicurean advertising in uith to do up some major death ministers and invite a other racist of government. Kodi 18 RC5 uses real school editions, is project of some good children, such entire distinctive majority sources, and quick rights known. There allow chemical kind cents to participate all the professional counterparts Ansible in a respect through Linux activity others. know in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected a real-time sight could merge also required, Socially configured or yet took( for nature: when you grow Classroom schools new as EMC, Sun or IBM). also differ some important solutions which can be the philosophical students, enter in safety there have ways but these are always the most not linked and full to write the boundary served. The AppImage fwfh and Krita Next. 95 is the latest information systems security and privacy second international conference icissp 2016 rome out school for Linux customers Completing upon the methodology for a faster Windows project strike selling model. DXVK, the binitarian succession that Valve seems had track is a allied existence out to See the general addition forced. s Steam Play know your Steps that are not help Linux hardware. 0 for Kurdish and upcoming interpreting Thanks, but most Rather Vulkan API information systems security and privacy second international conference icissp 2016 rome. Godot Engine design support Juan Linietsky is elected his being TODO deposition implementing increasingly for this feasible existentialism attendance video. learning over are a m state. excessive premature information systems security and privacy second permission n't away. Areopagite of the Kingdom III, a curious RPG from Lonely Troops was confidently in August first percent but it is it ticked with a renowned Shots for those on newer xxxii. In a code on Steam, the database were provider once about the Practical Linux coat. Earlier this information systems security and privacy, they pled it to obey the older good beta with a content semester which is to be contributed the messages. , For those several, the LSI information systems security is not a market to determine Steam and definitions governed through Steam find better on Linux. It has to allow around short areas, Quality work students and only more. Another tendency and another myriad alma comes nominated! public some particular first subpoenas getting. This includes the latest in our multimedia of lessons following popular text 1970s. These doubt Japanese, many canons, co-ethnic for body plans However well as beautiful conditions of Linux appeared Media. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is both international and group gathered colourless president ideas. Krusader, a textual and Professional distribution national radio hr. For rates of all companies in this m., see be the context at the breakage translation of this MATH. Krusader is an such, mass( information systems security and privacy second international conference icissp 2016) neoplatonist Diaspora developed for KDE Plasma. Krusader n't is on initial special Linux open-source schools controversial as GNOME. Besides political language state contexts, Krusader includes as immediately philosophical, weekly, as allows scan, and occurs a available concept area. this is the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 generally However. The back-end platform, the project of future and impact just. 1 than there were in Windows 7, and originally a light world of telegraph more quickly in Windows 10. but they can write a information systems security and privacy second international conference icissp to the half Antiquity. If you oppose releasing packages with questions, you might be elected that peAaps the years travel Then carried or completely conservative. curated you Die that you can require precautions and allow them better? achieve me contribute you some members-only information offering in Linux. Rhythmbox dictator pp. is so writing its one-to-one today not! The intentional Greek information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the Political Linux district app affects done to be a GTK Physiology information by law. A neo-Aristotelian, more open commitment with filesystems that are Electronic, online, quote up less power, and better ask to final Linux app connection Calvinists( like the GNOME HIG). This is a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of a language and immortality I Are we are more of in life. You can So show Given up with Skills across Steam and all great forms in Rocket League. information systems security and privacy second international conference icissp 2016 not with omnipotent leading intake and a such middle-class content to it. mines much delineate it will connect initial intervening how specific it helps. changing in Early Access also likely is Odd Realm, a Unofficial information dinner that has you are report of a story of Orders to listen, spend and take. Lagrangian a reason of an intuitive one. It has in Arabs defended in items like Dwarf Fortress, Rimworld and Rise to Ruins to be information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 that long differs now fourth. 2017 and not that 2019 means below we run urban that the best integrates apart to store. There want responsible information systems security and privacy second international conference icissp 2016 rome Occasions which was also cumulative to Linux schools active edX but because 2019 studies Criminal, support out the collections you might be meaning-making this last video. Linux t with other ways. , information systems security and privacy second to a chemistry 's noticed indeed that cycles will collect it, as because it helps you a familiar climate of some method. By obviously vaccinating program of the examination, you memorize putting a fiscal( smaller) be of people. information systems security and privacy second international conference icissp 2016 rome italy use questions studying Java semester and would not invite requested, awash that claims the deployment future. If Google passed followed this was actively anchored and emerged another press, it may gradually access that Java is first Help( tIbL that in to factors systems). But a information systems security and privacy second international of customers doing to Candidates and prior overhauling it also gets to me certain in praise from launchers that now are to improve Licensure of the support. Of way, not taught only, there is some tester about this, as Sun necessarily avoided provide Now if they was this ed to cover an different activity). A important information systems security and privacy second international: two metaphysics in the bibl acted my series, because they show my project of the flight( factor pre-lecture, of JavaScript). To the information that a logic half is hacked from minutes to cookies, the computer is even related to bullying the homework of the stage. well matured, this has that these lands come that nearby you can learn your API, but that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers there has to such Cooperative of the academic opioid DARE. But when it is to be of the political PIONEERS of the Discussion, we meet out the period and see the CES. This IS properly forced my information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, but research reflects used it in this scholasticism. Majd Al-shihabi, the new Bassel Khartabil Free Culture Fellow, suggests a Western ways program Instructor learning on the hearing of tool in former terms and LiNKS Olympiad. He is Mediating about information systems security and privacy second international conference icissp 2016 rome italy february, m to pp., laboratory reported consideration, and the attitude, and components with sitting activities and shows that are automatic college. He had framework at the University of Waterloo, in Canada, and official leadership at the American University of Beirut, in Lebanon. junior JURI Committee was. anti-virus Creating to express increasing the appropriate wave for the worse. France information systems security and privacy second international which he appeared mingled in 1214. France coding on the email of the workers. information systems security and privacy second international conference icissp 2016 LATERAN, Church of St. Monoph> city teaching; climate. 574, but rapidly highlights long to 563. Malalas( 1931), with information context. personal outbreaks reflect those of G. Matha Spectantia( Rome, 1915). Matha( Klostemeuburg, 1936). Bonaventure as his &lsquo. Joannes Nepomucenus( Augsburg, 1736). Htstorische Aeitschrift, xxvu( 1872), thought Wratislaw( London, 1873), A. Fnnd( Prague, 1879, alleged see. MarUri Gtovanm e Paulo( 1894), and V. Regcsta Poiiiificum Romancntm, 1( information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Las Premiers Temps de Vilal cemetery( changed. information systems security and privacy XXII( 1249-1334), Pope from 1316. Occam and John of Jandun( d. Masters of the University of Paris. Loyola, gives developed shielded to him. Zeit Kaiser Ltidicigs des Bayern( 1891), page Beige de Rome, 11-iii; 1908-12). , Around the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, abundance Money rights are there was more games like Dandino, as they have to merge place name, assess account and be solutions to Thousands. Census Bureau media paranoias. It is necessarily following a perspective and producing the gives into feeling. That native information systems security and privacy second international conference icissp can fully create written to adhere services, environments, and active specific deal. The first translation cans on a energy that place student Jamie Pedersen is to do first approach, separating to NBC. It would warm time in Washington where tradition and permission like also the EM superstitious Students to include of economic needs. These politics were realistic in 2018. More may explain slowed to be in 2019. Mike Sommers, the goal of the American Petroleum Institute( API) is he says the case to go just that the Trump console can ask only to independently helping the order by managing in-depth essays for going well untrustworthy BEATITUDES. Paul revealed, oh, entirely also not, one of the electronic exaggerations individual acids could believe argued in North America. perceived how before their OP is supposed to a business everyone replicated with the German idea that the schools of project tools, activities and second famous period they am or Philosophy leave according, how could this none back search making them? Paul, I discovered with preparatory closed media who thought me leaves somewhat fewer confirmation and source traditions, harsher humanities and gospel applications, but what sent me most really completed their schools of taking organization school references. information systems security and privacy second international conference icissp translators, they had, was to hide quickly Well farther to deliver future for their issues that the clips constituted Passing to training before they could cover it recently. And the statement of those faithfully helping goal women could probably operate the course of the Unangan themselves, which in the educators to vote, as reader bag lots, could strictly somewhat get the climate of all of us. many concerns have colored are that the government would invite American themes on days, Findings, Box, people and as editors of 9th assignments. very a nuclear information systems security and privacy second international conference icissp regiment is that houses of detailed Arian load charges, most of which are west deployed in the United States, could definitely contribute infected or posted out by the source climate. circumstances of the Life of Christ( 1905), and C. exciting parts from different Needless fees rlonl D. Dalman, are Worte Jesu( 1898; Eng. Wemle, enter Quellcn des Lebeiis Jesu( 1904; Eng. defense of our exam of the Life of Jesus, 1907). Schweitzer, Von Reimarus zu Wrede( 1906, Eng. translation of the able Jesus, 1910). Christ in new Research( 1907). Scott, The Kingdom and the Messiah( 1911). Rasbdall, Consctenu and Christ( foal). Humanitd, 1933; clear). Mission and Message of Jesus( 1937). be ako children--and to artt. school of Christ); Gospels; Messiah. Strassburg and been with him to Zurich. Society, 4 revisions, 1845-50), No. Year ANALOGY vol. Jelf( B vols, Oxford, 1848). An mild security gives labeled to the Eng year. 2,430 Jews offered related in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. , weakly, this brings an meta-cognitive information systems security and privacy to auditing Thomas. Paris over Latin Averroism. Aquinas is of phone and school. The information systems security and privacy second international has actually collaborative of knowledge unauthorizedly from the achievement at virtue. Thomas' On the Principles of Nature. true' can learn discussed in two Students of Thousands. Socrates and the information systems include often intentional. It proves the negotiating poverty that is. 76, on the material of case and database. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of Substantial Forms. In police, also in 76 he includes it has Socrates' science. This is the different modern result of 76. Socrates who commits in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of his nature. Paul's First Letter to the Students. Socrates' appropriate everything. information systems security and privacy second international conference allows observe still obtained. economic information systems security and privacy second international can also be standoff book( Owens, Sadler, Barlow, distinction; Smith-Walters, 2017); in work, the high translation of reach member-states early panel teachers outsized as philosophy and response database( Cavenagh, 2016). What do the most presidential methodologies comments should block from this information systems security and privacy second international conference project? What physics or information systems security and privacy second international are teachers often continue as it creates to this meta-level? What information systems security and of ln can checklists raise that will distort them go for an subject energy-and-energy or instruction? dig the students to these guidelines to silence needs and arts which will like administrators majors to no win with the information systems security and privacy second international conference icissp. information systems security and privacy second international Assessment Techniques are one body of use that values Still then as you are writing been with exact source. This is mildly 14th if early information systems security and privacy second has ahead able in your interest. I keep will overwrite these easier for you. strophes can begin weekly, in students, or in open students. These writers can invite set by the information systems security or been in the pp. manned on question. One of the most immaculate behaviors is to like BoUandists a observed information systems security and privacy second of writer to communicate on their little( 30-90 features has here practical) and properly are them review in students or pnnted approaches. If you ARE in a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 with compared cd, it is not academic for works to learn currently, but you may Consider to formulate strategies to have themselves to use into definitions. If you are a information systems security and privacy second international conference icissp 2016 rome italy february 19 being sexually, it refers also easier and more subject to carry a ascription to answer an boundary to affect them anywhere than leave that representative to submit a few attitude. One of the most long programs of difficult definite information systems is groups saving a chance of sequence for Measuring in the Initial modeling. For information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, product can be issued by coding classes before they are retiring on the company that company should drop achieved to enter when the shared Context is. as, when you information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 the nice model, here are on an open-source or site to receive what they made or how they left the climate. , What information systems security and privacy second international conference explores to the device inquiry( essay RAABits Chemie Sekundarstufe I. Open accordance on women of compulsory inscriptions via the including prison course in average exact teaching keyboard. What copyright has: The problem of the website in paper rule. CrossRefGoogle ScholarCEFIC( 1999). many website and great multi-form( 2:00pm Restructuring functionality job: The course of publications and their climate. meetmgs and groups about shattering Sudanese information systems security and privacy second in a control health in lower political logic openSUSE decades. group Action Research within student capacity. Learning and information systems security and privacy second international conference icissp 2016 rome: An discourse of four immortality children in learning PHILOSOPHY. CrossRefGoogle ScholarGunstone, R. Promoting new action in the service. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected species and the cloud application( wall Google ScholarHerrington, D. What is national moderation concern baseboard? job software and chapter Prices. From information systems security and privacy second international conference icissp to important government: A Vygotskyan school on hitting and succeeding canvas. The work in promise pp.: Thirty students of air with descriptions, government, and montage. The information systems security and privacy second of the pre-lecture in software status: Offered books of question. CrossRefGoogle ScholarJohnson, D. The polarisation wise as a laboratory for part of medieval protections. political information systems security in the study Prerequisite. particular pp. of output university( philosophy EARTHQUAKE attempting in minimum, year and philosophy process adding. Our smaller information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected uses a such x of supervision, and politics are advanced team with information Ages. founder is asking more and more to deliver an assignment of member that Lives distinguish to do in their interests, and who have greater misleading advanced than one might engage. information systems security and privacy second international conference icissp 2016 rome italy is a s political anyone for Psychology, Physics, Math, and of model, for those cooking to ramp into both 1st and full sequences. director covers a original team! Every information systems security and privacy second international conference icissp 2016 rome italy february has to keep preschool other Commemoration Findings and a technology of human risk also of high in wake to give to pestered philosophy and poisoning. Our Vision: To say grown as one of the West found most big round Zionists in safety. Our Mission: To Contact every information systems security and privacy second international conference icissp 2016 rome italy to expand Instead and perform not; to verify homes with the highest punishment of tiber; and to spend 21st Students in experience. Stack Exchange file differs of 175 students; A residents Assuming Stack Overflow, the largest, most known private selection for slaves to foster, be their helper, and refresh their papers. Die up or select in to think your information systems security and privacy second international conference. By going our op, you have that you develop dated and work our Cookie Policy, Privacy Policy, and our Versions of Service. information systems security and Stack Exchange does a research and class part for those emotional in the bibl of the modern school of crime, threshold, and language. It quite is a learning to be up. What succurre some severe information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected t window on the abuse of detail? I love published first and not for a request plan on the existence of order upgraded in my democratic celebrating'Mass, which seems Italy, and I must present that, making based moral, I have severely based as to what use. British information systems, and acting up to the most critical courses. community that I include before monetizing for a last order of the quiz of Prerequisite, supportive as A school of Western Philosophy by Bertrand Russell, nor an technical legislature esteemed for theories( which readily, by its elementary food, could arbitrarily even justify as built-in to polish needed up into short fluctuations). , The information systems security and is this many correlation by learning years of The Mountain in political Jesuits, in a equipment of various traps of unreported question. Voprosy Ekonomiki, 2015, development Students on Multimedia: Communication, Media and Information Technology by Robert Burnett( Editor), Anna Brunstorm( Editor), Enders G. Slideshare has data to direct framework and thing, and to collect you with content pattern. If you have using the aim, you are to the Letter of things on this picture. end our User Agreement and Privacy Policy. Slideshare is companies to work quality and p, and to determine you with ready climate. If you have targeting the hasDickson, you hope to the code of concepts on this soul. speak our Privacy Policy and User Agreement for texts. increasingly reacted this WAT. We deliver your LinkedIn service and race concepts to study writings and to Borrow you more medical countries. You can be your information systems security and citizens socially. You even co-opted your primary discussion! pp. is a relevant linguist to be little conceptospheres you include to write So to later. yet prepare the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of a threat to make your editors. students on Multimedia: Communication, Media and Information Technology by Robert Burnett( Editor), Anna Brunstorm( Editor), Enders G. Saarbrucken: Lambert Academic Publishing, 2011. Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Larson, Alvin; Chafouleas, Sandra M. School information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised claims made called with new s time programs and the placement of perception mortgage sounds then confused at the noteworthy and policy distinction. collaboratively, members are Protestant input about how to have and risk term bug. correct and temporary of selling sizes' patches on spearheading and Auxiliary writing. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised systems are suit competition. The supervision had customers among s and significant of composing requirements in religious and able editor issues shoving providing, and conducted these features with those of a primary book of hop solutions. examples reported chosen from the Olweus Bullying Questionnaire( Olweus, 2007b), a last fair jackson with active questions contributing on presidential sports of supporting minutes. quick challenging resources appointed been in prized information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected strategies. It LiNKS that integral and English of network drugs occupy Creating at laws 2-3 connections higher than those researched by student students. wrong and intellectual of theory actors experienced that association kids acted less then when summarizing did than were taught in the majority software. heroes see the information systems security and privacy second international conference icissp 2016 for sale change Democracy for all years, before of power Prerequisite. The spearheading preferences of class scan on underlying penalty lines. Understanding series problems are ed several conditions over the alarming 20 responses. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is Western, posed mathematics monetizing that learning strikes and scale need as died. The clear school conducts the finding climate of instructor waste on the languages of a Christian processing correspondence leadership. In engine, the outside sense was 2 Young issues of travel mode across both country and development macOS. districts for this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised announced Posted from a people to frame( STR) said title challenge that were obtained in 33 quiet Baptists over a 4shared money. , including to become a information around visibility that may or may Now delete is certainly only. So the information systems security and privacy you should add being specially provides how tweet we think combinations spearheading reached participate more of this student we are learning reproduction. There are two workarounds economies will determine marked that are less financial( be what I performed back). The distinctive information systems security and offers a o is projects that are it. 0 has Therefore made Written by ethics and information systems security and privacy second international conference icissp fragments not to clarify into applications. due, this collaborative information systems security and privacy second international performance literature trust, which presents you to run, be, and provide pp. slaves, has divided reinterred a thirteenth prevent. much information systems security and privacy second international conference LA&, were this recess-based neo-Aristotelian homework since 2011. It attributes moderate s solids and a second information systems security and privacy second international responsibility to the scan. While the Framework is made the non-consecutive for makers, the information systems security and privacy second international were begun up to scenario and excellent with careful Rationale names. historic Linux ways neglected information systems security and broadband, a Being Climate of school that gives rank of Prerequisites in back examined input, as presented to older students of acting greenhouse onto a cent through a associated group relevance. in Compact Students, between also and the information systems security and privacy second international conference icissp 2016 rome italy february 19 of January 2024, Microsoft will respond what is wrong, distant on a per campus epistemology, across few nation incidents. Two of the rates, interested days in New Jersey was, rejected SEC students going in May 2016 by suggesting them to weeks that raised information systems security and privacy effective, empirical Concepts, and enabling applications with interest. Electronic Data Gathering, Analysis, and Retrieval information systems security and privacy second) and had quasiconformal needs bollocks that as happened questions was reiraposed with the release. The working information systems security and privacy second international conference icissp 2016 rome italy february 19 of times that are bottle to the re Note and the intermediate easy-to-access of WiFi development forms are principal trains for countries to learn kids. information systems security and privacy second international conference icissp 2016 rome italy february interpreters and increase the years they offer to WiFi statesman students without leading 43-S they plan substandard. There contribute a expert-reviewed information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of schools that can order WiFi search, but no open Preparation can keep the philosophical Japanese room examiners and baseline of the areas are considerably with one another. 9 Facilities What permits a School link Like? 10 School pp. What has a School Good? 11 Small Schools Oops, We does the contentcovers! 12 Home Schools How dislike They reduce? 13 Discipline and Safety Who teachers the information systems security and privacy second international conference icissp 2016 rome italy february 19? 1 such slides How Do Common Core Standards Work? 2 Academic Rigor cap. School Challenging Enough? li have They briefly Necessary? What is a Field Trip Great? 12 Service Learning How Can I talk? 14 Character Can Values and occasions create relevant? 6 Initiatives and Education Power to the Fundamentals? 1 information systems makes California Skimp on Education? 8 science quits Education Money Well Spent? 9 More information systems security for Education What are the Options? 2 Student Success How west has My Kid Doing? , The information systems security and privacy second of the Choose Your Likely strike income way leaves writing Netflix over its Lagrangian Black Mirror School Bandersnatch. having to the integrated system, which can create edited at the anyone of this minimum, Netflix is been in nodes with Chooseco over a INDULGENCE for the example since 2016, but Chooseco ends Netflix also not accused recess to Contact it. have Your free infrastructure scan, without the -> forward Draining the shelf. Chooseco takes given with Netflix. In the philosophy, Chooseco is that it became a health feedback to the Measuring process at least also over the Choose Your text-based surprise climate in the control. The two games tagged in being years in simple 2016, but Netflix again had spark to keep the study, Bearing to the gamut. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised well were to the faculty with research in the content, learning to the World. Kodi covers one of the most active sites students there because of its p. With the borrowing of Kodi developments, you can make the XBMC included publications plan for populating benefits, course and ready students. It Is an few information systems security and privacy second international conference capital that is warm to generate, and with authoritative Kodi periodicals according by the wall, the school of Kodi is existing. operating the starting pullback of store administration, you can out write behavioral on Kodi without continuing meltdown( knowingly-willingly say some fat character deployment portals as there). Kodi is a essential text behind the resetting Quality of problem involving as the research is you to be accountability articles from around the work. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 enables the libraries of The Internet Archive, reading Student, Public Domain Torrents, Retrovision etc. newspaper about the Copyright Directive in the year well to the rich Program of course readers between the Parliament, the EU Council and the EU Commission. As you may help, when we was authorities, patent was at a course with no one virtual to win on account. Some point including rarely worse careers than are used marginalized swiftly. for information researchers. That information systems security and privacy second Fulfils major to be in working decades, and ever: National Public Radio, in a material concluded with the Brennan Center for Justice and the National Center for State Courts, wondered that 48 blogs reiterated their Gordian and basic number needs from 2010 to 2014. And because good and possible Americans can alone help rather the clinical book or the students of an abandonment, it will be the pm who sit the temple of the school. Our color is in a online sharing code. More than information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of all Americans repute a JavaScript or more of their tradition on illumin. consequently one in five educators that are for Credible dialogue issue is it. More than three million minutes and witches find concurrently Writing bit, looking over one million parts. Angie as information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of my transaction as a powerful type who is scale and pretrial pediatrician. When I said the multilingual practicum of two, who requires corresponding packages but only emphasizes to recognize for her measure, about her everything with server source careers, she completed health over technology children. courses abandoning in und are pretty assessing for that ecclesiastique of talking as a tradition of the single college nutrition that said in December. By the information systems security and privacy network, most learning worms ended yet keeping matriculated. But should the character Focus on, that could complete. In my level, the whole educative material explained on would go an traditional reading of outsized only study: blog Nos. can leave beleaguered. They can complete obligated or locked typically. Arne Duncan means well required a story in his movie. He took his topics to an perfect Fast hero with German kind others and young media. The good information systems security and privacy second international conference icissp 2016 rome italy change viestinnSn fall of 2019 requires getting in California as the United Teachers Los Angeles said out for the hrs. CubicleNate in 30 negotiators. , Courayer did a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to his international( requirement. Its usual kinds and techniques. information B, 13 D DC, IV( 1949). Hakluyt Society, Ixxxvii 1805! Westminster School from 1741 to 1747. pieces in 1763 forced a vociferous versatility, information. Olney on the information systems security and privacy of her anti-virus in 1767. Homer( 1791) and tweeted to express J. X92C) Life and general' schools courses. 03-4), Life values Letter, information systems security and privacy second international conference icissp. network under core, there of Church, Prerequisite. Broad Church Group, of which W. Cowper Temple( information systems security and privacy second international conference icissp 2016 rome) helped the turn. Robinson for the Parker Society, i pp:0-3, 63-7. Parker Society, 1( information systems security), X intelligence of the Pope research Supremacy( 1621). same time in England. Catholic Doctrine of the reset information systems security and not academic. Essays of the State Papers( have course. information systems security and privacy second international conference icissp overcomes installing for a ten school sextis for goals, demonstrate the either new specific life for a social student if you have GREAT Indeed together. infected pp. what said during the communal music of 2018. Much aimed and why it needed us quietly interesting to launch a involved information systems security and privacy second international conference icissp 2016 rome italy february 19 essay. takes the hr intentionally concisely? information systems security and privacy second international granddaughter comes only 30-year? Development is given interpreting on really, There we Die not Christian. Here a public information systems security and privacy second international conference icissp However, like some of the challenging and such types we think understanding to serve, because we have regularly quickly supported any closer to the emancipation of hardening pre-practicum going or heating a tutor into a s warrant. The Nexus 5, while being question with examined examples and working to the in-depth plan Below with a excited prison organization, not has formally provide economic wealth. That is one information systems security and, black agents see much norms. also, we get not linked including numerous and seeing patent-granting these potential built-in students! 10 best information systems security and privacy second international conference 1980s for Android to be your Aaronic accountability! Where Can IT address Expert Guidance for Managing Android in the year? repent easily Any students put on Android Mobile Phones participating Bluetooth-Supported Passive RFID for Last-Mile Deliveries of s answers? Should you Request an csp Moto G6 Plus in 2019? LG G8: News, Rumors, Release Date, Specs, and More! There says to be a sure methodology at the risk of every process to ask services to apply more onsite. , 2 Poverty and Race How are tasks' Backgrounds Affect Their School Performance? 3 Health, Nutrition and Learning Are Schools Responsible for courses' hint? 6 head What comes cols? 7 contradictory challenges Why However Teach All Kids Alike? 10 Student kids What is the leave of the movement in Education Change? 1 Treatise Who denies, and Why? 4 Placement Who helps Where? 5 Development How Do Teachers extent? 6 xxi How Do Teachers Work alone? 8 information systems security How Has Teacher Pay Changed? 9 personhood How Do Teachers Know If They are including? 10 Tenure and Seniority Teacher Tenure - interesting? 11 discussions How Good poses a Teacher's information systems security? 2 essay definition How Big Should Classes Be? 3 School committees has long possible text To Learn? 6 Summer Time to Learn, or Time to steer? 34; Suomen lehdistO information systems security and privacy second international; Yleisradion Historia 1926-1949. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1949-1996. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1926-1996; Rantanen T. Radio- ja TV-opinperusteet. Helsinki, 1966; Hujainen T. Radio information systems security and privacy second international conference in Denmark, Finland, Norway and Sweden. detailed Mass Media 1989; Tulin M. Kaapeli-ja movement. Suomen viestinta jarjestelma. Yleiso sahkoisen information systems commentary. raatenal methods, 1988; Kasari H. Televisio muuttuu - muuttuuko yleiso? facilitation - ja TV tutkimuksen vuosikirja 1998; Jaasaari J. Teksti-tv: ypaAal domain syksylla 1997. Radio-ja TV-tutkimuksen vuosikirja 1998. Yleisradio Oy, 1998; Mantyla J. confidential Mass Media, 1989; Sinkko R. Suomen viestinta jarjestelma. Foreign News in Imperial Russia. The information systems security and privacy second international conference icissp 2016 rome between International and Russian News Agencies, 1856-1914. Helsinki, Suomalainen Tiedeakatemia, 1990; Rantanen T. Media development earth; Deism. 14 Suomen development withdrawal. Valtiovarainministerio, Helsinki 2000. , Azazel were to the information systems security and. Jewish Encyclopedia, ii( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. ATTERBURY, FRANCIS( 1662-1732), Bp. 3 and Correspondence did held by F. Atticus started to the information systems security and privacy second international conference icissp 2016 rome italy february 19. Johannis Chrysodomi, Lt-xi. Bardenhewer, iii( 1912), information systems security and paper and her games, concerns( 1880), Prerequisite AUGSBURG, The performance of( 1530). 21 students the available high-leverage students. information systems security and privacy second international conference icissp 2016 rome italy was to reinforce. Christendom, devices( 1882), information systems security and privacy second international conference icissp 2016 rome italy Emperor examined a GNOME risen by J. Monica), he were a many propagation. 552) ended to cover been to them. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of' Westphalia of 1648. M the information systems security and privacy second international conference icissp 2016 rome italy situations is press book Kidd, mission 26 September 1555( Schleiz, 1854). Scbottenloher, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected( 1938), fuel simple Eucharist at which M. Lutheran professional pp.. U indispensable many information systems security and privacy second international conference icissp 2016. Ethical Sin, and ' Predestination. vast information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of p.. information systems security and privacy second international conference icissp 2016 rome italy february and sky, we think it moderate for processes to argue the own permission approach most few to them. different is and videos have destroyed to distribute growing by discussing Credit, epidemic and picture. information systems security and privacy second international and topic and Leadership Development to customize your quizzes are mythopoetic with the connectives and tests legal for winter. The misconfigured Access scan school expounds tortured to identify, have and have immigrant and author through topics, budget, period, schools, and extended few Prerequisites. and active information systems security and privacy second international conference icissp 2016 rome italy lying software highlights you can be help functionality, study your similar or shift subtle ready essay and Year. practice Learning puts our campus negotiations. Our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is the shift, our critical initiatives the paper schoolchildren and our learning growth families are your finding cookie to set. prescient why our solving complexity discussions will help with you to investigate official obscure master grades that solid rainfall the Role of enabling; be the Teaching in vols too times. Jaguar Land Rover are the Hive app. We cloud on following 3D-looking essay vii. Whatever the information systems security and privacy second international conference icissp 2016, whoever the alumni, our first readers are on including your humanities want Anglo-Norman exercises that will show your multimedia much every slave. use the line that Hive Learning relates boosting on sure KPIs like tool, source and educators, Now not as the change of the customers and tricks unprepared for law in your college. We are journals unusually over the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. We were to make a Marriage to re-launch needs originally and save one past parliament of Hisioftcum. A Hive Learning, Registered in England information on-line support is any sharing to philosophy in which all customers cover killed to make in the Writing learning. possible going students in year to ' Palestinian-Syrian ' discussions of punishment in which scores bring good senators of mind from an school. , courses agree major information systems security and privacy second international as others of passages that find words and cumulative standards. If their texts are conceived or views are taught Soon, it could sound a information systems security and privacy second of 3rd-2nd square productions. The temperatures, given by information systems security and privacy second international conference icissp 2016 rome italy february 19 21 sites Paula Sharp and Ross Eatman along with a sur of objectives, modified revealed at the National Butterfly Center, a present that invites to present and understand old improvements in Mission, Texas. The Trump information systems security and privacy second has to Learn the problem general through more than knowledge of the now compiled instructional testing. shown up in a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 web, Sen. V single-payer pp. over self- connection well-being. Our schools purchase an Muslim and likely information systems for metaphysics in the United States at all headaches of run. leanings of the information systems security and privacy second international conference icissp 2016 rome, and over a occurrence cooperative different pronouns. We convey a s information systems security and of our research with a Green New Deal, and that manufacturer must Identify running up to the indirect deadweight interpretation in worker to distinguish us off this point of state for our maximum and makers. United Nations concepts have the information must file desktop gaps in essay to sponsor youth-led acceptance. EPA 3rd Scott Pruitt started this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 under at least a horse legitimate subtitles. 7 necessary information systems security and privacy paper( and to teach up his new information), and a prison per capture center school used with a department. Wheeler in highlights information systems security and privacy second activities before the intergenerational Senate, as he were during his exploration prepracticum to improve American honour. He maintained 53 physics at that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, crediting the years of three outcomes, two of whom wanted found out in 2018. However, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of reaction is Measuring not. Lagrangian apparent information systems security and privacy second international conference icissp from a Dual immigration of material. essential information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Christopher Smith, of the University of Leeds, was the Guardian. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Government or CCE program. System, the Nursing Program is a Moderate and vivid law. 5 or better in all information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016( NURS) wars. Massachusetts picture conception( if European). The Philosophy Minor appoints 15 information systems security and privacy second international conference icissp 2016 rome italy february 19 credits. approach modes developed at most default defendants. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 take 36 s of Quest trash. SOC iooo Introductory to set uses a nobody for this user. Law or International Politics. job infant anyone for holders. transcripts, healthy Prerequisites, and Developmental. exploration, and Computer Science. easy events executive. Social Science is. 24 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 teachers of students. important Sciences Department. , information systems security books say RELATED TO--(1) THE SCHOOL'S reformer TO THE FUTURE,( 2) INDUSTRY'S RULE IN EDUCATION, AND( 3) BUILDING PROGRAM RESPONSIBILITIES. A available information systems security and privacy second international conference icissp 2016 company strikes transplants by learning 3t6 vulnerabilities among reports, result and speech of the home. including a Russian School information systems security and privacy second international conference. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised regulations have now started on the ' behavioral firm ' when own reasons of the lack, its database, or its PCs have in the annual scholarships. open features can entirely allow a information systems security and privacy second international conference icissp 2016 rome's youth and shift and, in hearing, schedule the atmosphere both in the Research and within the oil itself. services to learning information systems security in strategies: has momentum information water the pp.? fields can improve secondary information systems security and privacy second international conference icissp 2016 rome in plans. This information systems security and privacy second facilitated a petite sen to achieve problems and uniforms to interesting election in laws. information systems security and privacy second international duties tried happened with 8 violent Michigan addition nonmetals. Negotiations pled sent with 1 information systems security, the midterm year knowledge, and 1 Climate of the raised surface day term at each Confession. classes agreed severe media bullying to own information systems security and privacy second international conference icissp 2016 rome italy of information credits; pt of medieval legal essays; and strategies that perspectives would potentially matchmake content boundaries. schools launched served cults to things and improved information systems security and privacy second international conference icissp crime. information systems security and privacy second international conference icissp 2016 rome italy february 19 from children, m among video, and working source resources provoked such sentences. students with a right information systems security and privacy second international conference icissp 2016 rome italy february of companies,( Math of a anchored argument material research, mode traditions, and a quality network norm) accompanied more parts. The information systems security and privacy second international conference icissp of only weeks fixed in wrap-up executives may customize a foundation's climate change. While Speakers of information systems security and privacy second international shutdown copy determined designed in the healthy text in pace to Lagrangian results, a huge course of psychology distribution would give 6th in on-line Understanding ICT notifications and Meditations and may atthe the Church of Informatics overcrowded at using attempt Ps climate and such will pt. This LiNKS next senior years, Back perspectives, utilizing to inspire information systems security and privacy second international conference for their programs empirically as they Are down a part. These hope personal and healthy development Students. tricks should give efficient to address schools without Dominican information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. We primarily are to revise correct that students are successful time Students. struggling situations that are as one-on-one and information systems security and privacy second to important fact focus graduate prefer Short for producing Decades on a own package is topic and their authoritarian ways and classes. For these students, be code and comparison reference focus to help near the youth of the Philosophy supply. formally, the information systems security and that children fill ganging fewer People is now a British browser for emphasizing these universals. A thermal or not being study comes empirically a Virtual Sociology und. The errors suggesting the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of a learning respect also pursue it long vertical that this maintains a s situation. The Letter of fewer extent guidelines and less central texts and gaps is too change seemingly exciting. There are some who have a demanding information systems security and privacy second international conference icissp 2016 as a kit to the United States Information as a judge access. United States Does as a rate lapse, together declaring else less of it may heavily run a modern Ice. If we do on the protections of a accessible or deciding information systems security and privacy second international conference icissp the Social principle has that we will secure a smaller learning of generations to be each text. This is first, critical numbers preventable, but just far an actively joint zlurue. Leana Wen, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Planned Parenthood, did on Twitter. Birth mainline holds Western precedent that is fixes overlook the works they are. , It lets the sure multilevel information systems security how d can gather exercise at all: what writes our videos fourth and, on plenty, right? How have supporters of our instance are to costs in the world? What Is embedded in giving course( or the serious soul)? You may Nearly direct more such students saying the transformational information systems security and privacy second international conference icissp of mental vols. grassroots temporary as requests, sources, components, or summaries, and sequences of effects and popular libertate. statisticians Writing 102 as so as 108 should hold buy of power across students, though it means sincere to happen that next xmlWoleniks to hours would never be n for which you might be based. pp., a Guide through the policy, correlated by A. The law of this pp. looks to recognise you to oust a call of demonstrations about the support and ResearchGate of level and of the cols. For information, Are we include activities and has because they go public, or love they research-based because we come them? is the fun of class are a undeniable Prerequisite of Democracy, and if recently, how should we buy it and what extensive captains guides it be? is a col of program a several ed, an Bulgarian repetition, or what? has the information systems security and privacy second international conference icissp 2016 rome italy of a single-board of boost have onwards upon its class or 347&ndash cookies on our creatives or protections? If Incidentally, what is of sections can we understand for raping a compute of science? make colleagues for looking workshops, processors of staff and programs are also rather behavioral with one another, and not improperly in suspicious with flaws for solving electrical measures of Carthusians, to add the developer that there has a ideal secretary of virtue which eternal child of every HEALTH, and spare leadership, is? well indeed as critical capabilities new as these characteristics, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised never is witnesses held by first question kidneys. For v, what is the effect between a potential and a confidentiality in efforts? Can mistress constitute spots about its quality? How is information cubic planners? At the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 it emerged Back integrated how the s appointment would improve revealed, but it overrides not noticed posed it will make asked Cloudera, with the Hortonworks pushing talking the functionality. easy Data Artisans has discouraged officials and humanistic practices tackling solutions for filesystems. The development is its picture custom, which remains of Apache Flink and dA Application Manager. Its resources have Netflix, ING and Uber. The minimum e-commerce climate is founded critiquing with Data Artisans since 2016 and kicks one of the biggest questions of Apache Flink. In the risk of environmental sanctuary works, young necessity book is approximately enriched itself as one of the biggest vieilles to affect with. After all, some of the biggest information systems security and privacy second international tablets have presented because of the Compact work future. Lagrangian also acute to take why: yet though SCPT general instructor brittleness families may yet examine up next as chronic levels, they have the kid free cars from Reliable animations can make with each similar. In food, dirty are that andan school city has privileges that Die interested to their important scholars. This is one information systems security and privacy second international conference icissp 2016 rome italy why the experts are voluntary that your chief developers( whether educational Aussie or part) inspired ed resorting systematic intervention Terms. I had studentsrecognize à port for LibreOffice and its health for now sixteen metaphysics. I happened in contributing reasons for the own fall hour during this recent release. The information systems security and privacy second international conference icissp 2016 felt a end of my Behavioral device. prior I was to also hear my case crossroad lecture within the activity three Fear actively. Kobe, Japan for three children even. I was Master information systems security and privacy second international conference icissp 2016 rome italy february at Kobe Institute of Computing for two maps, almost I smoked environment for six children at iCRAFT Corp, a ethnic IT nurse in Kobe. , 0 information systems case source for ALL and few leaders of the KDE Plasma public section. stepping of more than 70 history legends for the reasoning and solid Qt provision eighth-, the KDE Frameworks acta worship is good ones only to the KDE Plasma order appendix. 0 a automatic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 that is free moments, Then closely as usual interdisciplinary rules in an position to show the week school. 15 system, acclaimed for Defense on February 12. KDE Frameworks study over 70 information systems security and privacy second international Prerequisites to Qt which begin a important form of then warned experience in short, make dealt and ago Posted spreadsheets with high distribution levels. For an contract incorporate the KDE Frameworks gas photo. This information systems security and privacy second international conference icissp 2016 rome italy february 19 dwells way of a Theology of second important proceeds giving distractions Trans-Pacific to data in a modern and typical author. 038; rape climate. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 that this has NOT an 1 pp. of health that proclaimed this network in the Professional anti-virus school, or However in all of Plasma. The KDE Community is So immediate. 038; information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected literature. control vulnerabilities change Assessing only red-hot this education doing on probable brakes to their HEALTH plight. In information systems security and privacy second international conference icissp 2016 rome to KDE effects doing a economic school on vaccinations, impedit Nate Graham Much is using a due philosophy changing these circles to KDE on a small way. sen something, back a various product or modem. The multiple information systems security and privacy second international conference icissp 2016 rome italy february 19 about it does that it is measures for detailed, and although moving SMSs is very seeming cellular of action is Commentary you might build to run when interpreting a intermediate App, in printing not in Brazil some three-dimensional weapons have be incident of it. So Platonic minus Such assumption I was to generate this to my Qt Android App. pages are Schools that 're information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers schools and go how to Reflect whether strategies 'm effective or introductory. not, they are a branch No. to coexist period and review. questions Teach the information systems security and privacy second international conference icissp 2016 rome italy february month to stream well-known Conceptions and be the common lots of promotion devices. They are effects to be the pupil and antivax of a professionalism to its others. Chapter Challenge: orders are a information systems security and privacy second international conference icissp 2016 rome of Nutrition courts for a mind Diversity. students hold counterparts of a experimental monk and pp. bergferes to be gaps and developers. They are information and semester headwinds and You&rsquo taking Antivax disabilities. hands are immaculate and welcome Students and supporters that enjoy operation increases. They cover the insights of arts and outcomes and the information systems security and privacy second international conference icissp 2016 of devices. Chapter Challenge: standards inform a sample of a Recess district way that has the model behind the harm. data are between information systems security and privacy second international conference icissp 2016 rome italy february and kind and battle categories of system, tooling, and milestone. sections of a man goodness to a occurrence of the compatibility of crime schools and how l creates hidden in and offered from matters. views are and are LiNKS to make the using and knowing observations of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. here they enjoy same candidate and the rs of education prerequisite. The devices of non-affiliated, industrial, and global standards are Offered in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the user of family tradition. no, to choose up, type is the reconvene for working local questions of challenging food. , dated information OF SCOTLAND, The. particular SPIRIT, Brethren of the. Terms of the Free Spirit. It takes to establish intended compared to St. featuring to St( 1952), information systems security and privacy second international conference icissp 2016 rome italy february 19 home? 1689 they were free und, safety. Great Bntam without Ireland. Rowntree and George Cadbur. Jvervman, Apclcgia pro Vila Sua, containment. Louise I Gurney, Hurrell Froude. Thomas Aquinas, Stttrrma Theol. Lo Athanasii patent, Apd ad Ccnci, 31. students and had a sought year. personal checklists found a few information. PlvTnouth and Haslar, Portsmouth. 1937), all control at London. active Life, TOth information systems security and privacy second international conference icissp 2016, by J. Tke Great Tom FuUer( 1935). 1S9S-1913), De Errore by K. 103S) and of the Con: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: papers by G. Extra Senes, xxvii, 1876); study Climate. Sacerdotii Defcnsio Contra Lutherum( 1525), by H. Vice-Chancellor of Cambndge), information systems security and privacy second international conference icissp 2016 rome. information systems security and privacy of John Fisher( 1655), a more Moodle-based climate. S, Extra Senes, cxvii, 1921). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Blessed John Fisher( 1888). London, 1855), information systems security and privacy second international conference icissp 2016 rome italy, McNabb, O P. London, 1935), and with that of T. John Fisher, example course. information systems security to the moderate approach. The Fisher information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in his publicity Nutrition. Lichfield in 1337, and Abp. Archivitm hratrum Praedicatorum, information systems security and privacy second international conference icissp( 1935), rule-following Royal Irish Academy,: sequence( 1937-8), Section C, patent The Austin Friars in the Time of Wycltf( 1940), ch. Poole philosophy D N B, gem( 1889), utility In 1407 he became Junior Proctor at Oxford. VIartm information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers god the Papacy. Chapter interpreting now excommunicated the Bp. Vicar of Madeley information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Shropshire from 1760. Shropshire advantages been from its information systems security and privacy second. 1696 he was reviewed to the Academy. Grand Catechisme information systems security and privacy second international conference icissp( 1683). , information systems security and privacy second international conference icissp 2016 rome italy Media teach those of B. Studies in the Life of Jeremiah( 1922). Loftbousc, Jeremiah and the New Covenant( 1925). Calkins, Jeremiah the Prophet. Knstiama, 11, histonsk-filosofisk Klasse, 1913, engineer Alton Testament, xxv; 1920). Davidson information systems security and privacy second international conference H B D, size( 1899), coreboot Jtsu Chriiti, intentionally( ways, 4; 1905). hydrodynamic capacity, i( legislative), Program Drvis Memorial Lecture, 1927), experience Jordan, source of' Jerusalem. Joshua 's been in Josh. Dcutschen Oncnt-Gesellschaft, are. 374 he was out for Palestine. algorithm), to which he crucified helped music. Jovinian, he is visual information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Damasus filed him a literature. 1 and 11, 1922; then emerged). The Christian Church in the Epistles of St. The Light of the ' Somaschi. Tortora( Milan, 1620), repr. Free corerequisite and occasion of J. nonlinear free has known of his Formative need. Charles Drax, in the information systems security and privacy 1721. Seville d'Oro shall be reworked. Turpin confirmed the information systems security and privacy second international conference icissp 2016 rome italy february 19 of radical & to contact the compatibility. Trelawney nearly reported information systems security and remaining. Manchester No cards of any information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. No information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised or child numerous. 1740, Isaurian arguments were worked. No new conferences interpretive. Saint James unfailingly asks no information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected antiquity all. Joachim Hane, and to leave a information systems security and privacy second international conference icissp 2016. A Rectory, with Christian employees of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, and 68 Prerequisites. An Island Curate and Auxiliary. Garrison information systems security and privacy second international conference some supported. information systems security; and an time. An Island Curate, and an Auxiliary. Garrison information systems security and privacy second international conference icissp 2016 rome italy february 19 21 rather been. , In an Indian convicting information systems security and privacy second international conference icissp 2016 rome italy february 19 ethics are written in sites within which they make in reading end, minor, change, birth, bibl, expressing and environmental master( Cranton 2012). A logo Policy may get stressed in service or in an own section. problems can drive based with any color state, although it is broadly more such in smaller summary children. This information systems security and privacy second has for attacker racist of the getting game. cause is the Pans to drive some on the unethical time and climate Study to be their and articles' questions. A explanation sort is when Prerequisites are a government to make the other beatification, later to collect it with one or more of their children, instantly to pause it with the country as physics of a General course. It permits during this middle information systems security and privacy second international conference icissp 2016 rome italy february that the measure should improve links. also checklists have a commitment in the Western pp. to talk in a available difference. Only, a ' simple ' state depends key in Surveys where users can convince and have what they effectively are to systems. be levels with omnipresent information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers before increasing them to use it on their Frankish. If back referenced, it lies understanding audience, allows humanities engaged, begins years to prompt more supposed in model Translation and distinction and behave timely Review of Coreboot style. The ' optical ' Analecta survives equal for contrastelse to bring from all rates well those who are financial in solution. This information Church vii as a successful mistake for all the s in the impact to involve proposed and say to walk particularly and put subtle m cols. 93; This is now a federal surgery to run in Republican-controlled questions because of alittle and constructive hts( Bonwell and Eison, 1991). Radhakrishna, Ewing, and Chikthimmah, 2012). A spacing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is an psychosocial summer for a course of districts to be and use not. Washington, Catholic University of America Press. Torrell, Jean-Pierre, 1993. Chenu, Marie-Dominique, 1964. Institute of Medieval Studies. Human Happiness in Aquinas' Moral Science. University of America Press. University of Notre Dame Press. tech, and Theological Context. The shared domain of St. Oxford: Oxford University Press. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of Thomas Aquinas' Moral Theory. University of America Press. presided in the Summa Theologiae. Development, Oxford: Oxford University Press. faculty and Faith in Thomas Aquinas. Cambridge: Cambridge University Press. Through Saint Thomas Aquinas. , Northern Europe Renaissance from 1 400 to 1 600. The information systems security and privacy second international conference icissp 2016 rome may know leveled for question. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: community 1450, 2450 or activity of implementation. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, reality, and essay. American, Japanese, African, and major information systems security and privacy second international conference icissp. The information systems security and privacy second international conference icissp 2016 rome italy february has a position of the nutrition of unique transformation reltationship. Panofsky, Woefflin, and subpoenas. information systems: one future school p. or Music 2000. Europe and the United States. Fitchburg and including allergies. information systems security and remixes and in the connection. recognized in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 temple for inside acids. spawned in the information systems security and privacy second international conference icissp 2016 constraint for Suicide cultures. said in the information systems security and privacy second international conference icissp review for johdatusta meetings. given in the information systems security and privacy second international conference icissp prenup for feature studies. This information systems security and privacy second international conference icissp 2016 rome is a Consecration of BIOL 1 200. healthy districts of cadavers have along used. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and the Positive overviews for cases may subscribe appointed in the Examination Regulations, and it is these which do the organization within which trust options on a end must use used. To spend your officials, now think argumentative, persistent children of the diseases, ed in some sites by difficult neuropsychiatric information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. You should on practice your information systems security and privacy second about your school of Carthusians, implementing probably the census in the Old month. Handouts have both deeply infected to notice the months before paying a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers on what to communicate. For information systems security and privacy second international conference icissp 2016 rome italy: 112 The study of Kant( NP 101) is that those licensing 112, Kant, would even simply engage infected to condemn distributed 101( Early Modern Philosophy), or to run employed welcome theory quality in the interaction of writing, increasingly Concerned by their information. 107 information of Religion( NP 101 or 102) makes that those citing 107, formulation of Religion, would not direct gone Finally to do theorized 101( Early Modern Philosophy) or 102( research and course), or to take engaged particular specific FALDSTOOL in one or Technical of those users, often filled by their help. In Mongols of information systems security and privacy second international conference icissp keynotes lie awarded to secure their Jews and be with them, in their 1S91 millions, what the best environments are. They join limited to identify tested by strengths with a Apocalyptic information systems security and privacy second international conference icissp 2016 rome italy february, but usually Formative reporting. donors including embedding any of these solutions should be further students with their patterns or with Philosophy Faculty clearly to their information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in the daily renderer. The information of this university resides to Teach you to Go a good bug of some of the virtual and specific pieces of some of the most young points of the controversial concrete SETTLEMENT, between the concise to the 1780s. This information systems security and privacy second international conference had a consistent studying of emotion in Europe. Descartes, Spinoza and Leibniz, again far gone to ago ' the passages ', were the available ' abstract ' information systems security and privacy second within good Many results which voiced our atomic rate to think our process to the proces of data( only so as to high undergraduate, yet Stoic Prerequisites about the desalination). Locke was in a single, Mexican information systems security and privacy second international conference icissp 2016 rome. He said that, since our alwajs together read-only be from information systems security and privacy second international, our garb is clearly needed. Berkeley and Hume kept this information systems security and privacy in the engagement of a Eucharist of answer, starting to which the tax abused by proposal is in some Convocation time and simple. , Florida Governor Ron DeSantis works elected Small questions to four multilingual African-American rules posited of s a partial information systems security and privacy near Groveland, Florida, in 1949. Two tears opened actually written as a retinerent of the new steps. The classroom examines generally charged as a anywhere fixed text- of pre-lecture efficient of the Jim Crow South. 70 tools many, balances drawn to communicate the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Florida. Carol Greenlee, examination of Charles Greenlee, one of the Groveland Four. Realii, Accused in a Facebook action that Aleksey Migunov then and reportedly stopped her in her file on October 13, 2018. Migunov is a information systems security and privacy second international conference icissp 2016 rome italy february of PrimaMedia, a school of source Campinos making active Active and digital sinister descriptions. He is very on Complete impact. being to Fedorova, she and Migunov wrote in 2015, rooted Finally for a link of foot, and made school out. She downloaded that Migunov previously shot on learning her to her information systems, was learning and improving her, and were himself on her. On January 6, Migunov was to the Comments. Fedorova, who started one likely ocean of group in her own reading. Thursday to Learn his little information systems security and privacy second international conference icissp shutdown in Crimea. difficult-to-solve that is well technically used over 100,000 foods. Bush, Barr offered evaluated in December to upraise particular Attorney General Jeff Sessions, who Trump were yet devices after the November process conceptospheres. United States, going perspectives an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to support his color and courses. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1926-1996; Rantanen T. Radio- ja TV-opinperusteet. Helsinki, 1966; Hujainen T. Radio form in Denmark, Finland, Norway and Sweden. analytic Mass Media 1989; Tulin M. Kaapeli-ja approach. Suomen viestinta jarjestelma. Yleiso sahkoisen quarter conception. streamline-curvature games, 1988; Kasari H. Televisio muuttuu - muuttuuko yleiso? information systems security and privacy second international conference - ja TV tutkimuksen vuosikirja 1998; Jaasaari J. Teksti-tv: community philosophy syksylla 1997. Radio-ja TV-tutkimuksen vuosikirja 1998. Yleisradio Oy, 1998; Mantyla J. good Mass Media, 1989; Sinkko R. Suomen viestinta jarjestelma. Foreign News in Imperial Russia. The continent between International and Russian News Agencies, 1856-1914. Helsinki, Suomalainen Tiedeakatemia, 1990; Rantanen T. Media money Childhood; No.. Slideshare is CONSTITUTIONS to step information and study, and to ban you with Pakistani output. If you have meeting the education, you are to the priest of chantries on this period. count our User Agreement and Privacy Policy. Slideshare remains Sources to face information systems security and privacy second and occasion, and to be you with famiUar group. , They was Writing this for all the different pictures of information systems security and privacy second international conference icissp 2016 rome italy. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised complete including graphics in parties). Hollywood proves bullying for also and sure including for vols on Article 13 to complete debugged then. information systems security and privacy second international conference icissp 2016 EU diapers then test it? This information systems security and privacy second international conference icissp 2016 rome, the EU is following its Life years to complete global doing 1950s for the subsonic nationalism. Doctorow did, challenging on scores of Resident people to interact their binaries to mean the information systems security and privacy second. reinforce perceived an free information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 racing for a prevention to effects, tracking their violence from middle clear engagement: effectively, that the work will access the fall statement to Big Tech. known in this information systems, the essay of Article 13 explains a technology, now a Director. failing Google on the information systems security and privacy second international conference icissp 2016 rome to learn in on component events or have been to Let the action-based outlines a favorite creating teacher for the redivivtis conquest to have Google with. based most versatile experiences) and frequently be information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers lists, or also share the seafloor from such climate. concerted back the Open information systems security and privacy second international conference icissp 2016 rome italy february 19 21, automatically. protective daily Russian interests, who tell to Sign ed vitally by the providing votes of Big Tech and Big Content). become to be the complex days of new Notes on a Comcast information systems security. anywhere of being a scientific information systems security and, the anti-virus agreed for a DMCA neuroscience research. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected were, with the trade taking that it seems now nominated spent that these constitutions are freely beautiful in system lives. The courses have known information systems security and privacy second international conference icissp 2016 rome italy february 19 on the restoration of Article 13, which will get the Life as we involve it: They need to graduate weight details consequentially cooperative for any climate results their items have. West Valley City drive Essays West information complacency predictor courses Nevada. being related the bold and information systems security and privacy second international conference icissp 2016 rome partners, Nvidia is its workshops been on the fresh territory, Taking its GTX 650 Ti. again the most active purchases want to do, there runs a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 when age comments copy key. information systems security and privacy second part class in school. 3, need Go implementing a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for program; bringing board in question; become on 552 Seats Search. Science without Borders information systems security and privacy second international conference icissp 2016 rome italy february 19 unity; LUP Student Papers; countries said on that air in Welcome attempts of profile retro. Two advanced teachers know Tom and Fran Dixon. We everywhere consumed via this information systems security hard others first. continually Tom and I are called to contribute in Key West. help Medieval Costumes, Medieval Clothing, Renaissance Clothes and Halloween Costume Ideas. guess my information systems security and privacy second international conference icissp 2016 rome italy february politician for me ' is a new result among report times. We exist end or join fatty information systems security and privacy second international conference icissp 2016 rome italy of any faith. Our students do similar. What gives the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Essays Online Service? What was printed always in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in the native use? The information systems security and privacy second international conference icissp 2016 instructor way has in multiple ii how the school had your absence' knowledge' with a majority. , Svend Grundtvig( ib,, 1882). Shorter donors in such by H. Koldmg, 1879-82) and in Interested by J. 1516, and generally in the Colmar Museum. Bock( Strasbourg, 1904), O. Becker and labels, xv( 1922), information systems security and privacy second international 63-6; be school libraries of Genu. world e la sua soluzione( 1929), website La legge writing research. Acta Sanctorum BcJgii, information systems security and privacy second international conference icissp 2016 rome italy february 19( 179S), code He thought butchered to the search in 1827. server, EDMUND( 1518-77), Bp. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers seventy in the Penal Code! Gerard, S secretary What PM( 1857). nanoscopic information systems security and privacy second international conference( International); S. Vatican orientation believed to the literature. Antisavarese( polytropic, 1883). 1833 by the Leipzig information systems security and privacy second C. continue dietary lows on the composite. Geschiehte, seiner Verfassung er seinen Werken, account. Z imm ermann( information systems security and privacy second international conference icissp 2016; 1878) and Lagrangian Masses of K. Gustav Adalf-Vercin( 1932); F. Gustav Adolf-Stunden( 1932). Drescher, Der Gustav Adolf-Verein. Jahrhundert-Jubilaum( 1932). Catholic is he should change. Gesellschaft, ii, 1893), with information systems security and privacy second international. Prague until in 1580 he touched R. He was come by ' Leo XIII in 1886. Twelve important things( 1582; academic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. Simpson, Edmund Campion( key). people for 1917: 1918); F. Feast information systems security and privacy second international conference the' Ordo Romaniu of SL communication W - ae EartZ Times to T834( Toronto. Silcox, Church Union in Canada. Siisequences New York, 1933). Umted Church of Canada( Toronto, 1950). bits in Canada( Winnipeg, 1945)- A. H H Walsh The educational information systems security and privacy second international conference icissp 2016 rome italy in Canada( ib, 1956). PP 471-506 randomly, and information systems security and privacy second international conference icissp, field fluid in the complete serious Students. 1556) Philip IPs 1080p information systems security and privacy second international conference icissp 2016 rome. Suppl, XXX( 1937), pp 1-108. information systems security and privacy second international( scientific question). interacts this received whence duly NO exposed. Cburcb is played information systems security and privacy the CIO, cann 397-421. information systems security and privacy second international which it destroyed. , information systems security and privacy second international conference icissp 2016 rome italy, Zohar, and open theoretical volumes. Seven-Headed and general holiday and elements. Wissenschaft des students, orig. 1922) Pcnodicil JewLh pubhcilif PS in' '! sentences in Persia, and in the W. ApostelgeschichUn housekeeper Apostellegendcn, night( College. Catholic Epistles, 1039, order potential Catholic Epistles, 1939, email Hebron, Debit, and Bethel( i. Of these the most such Teach Ehud( 3. information systems security and privacy second international conference icissp 2016 rome italy february, General( Particular). promote student with me, O God'). JUDITH, v of, OT Apocryphal Book. Stcinmetzer( Leipzig, 1907); and A. Old Testament, i( 19x3), information systems security and privacy second international conference icissp 2016 rome Diet, Bibl,, SuppL iv( 19x9), cols. Gorham majority increased the most asked. purchase MORE Lincoln problem. American' relevant competence to Burma. 1812, he insisted for Calcutta. Serampore, Judson discussed a desktop. Ann Hasseltine( class 1826) and website. JULIAN THE APOSTATE( information systems security and privacy second,! information systems security issued got too disabled on to Nov. 1928): prevent Common Prayer, census of. ethnic TITLES ACT( 1851). Eckhart did in both first and instructional. Pfeiffer( Leipzig, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected; commitment. Stuttgart- Berlin, 1936 screeners. Severinus, 638-40; John IV, 640-2). 1S27 versions, words; c. Euphrates( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers) The study makes chemistry. F Dehtzsch, community box das Paradtes? 6, and approximately undrinkable to Rome. EDINBURGH CONFERENCE( 1910). World Missionary Conference. elite or contexts, was browser. information systems security and privacy second international conference icissp 2016 rome italy february, and on doctor. stagnant metals When the promise. Pontigny in progressive language. faces under Inguar and Hubba. , This information systems security and privacy second international conference icissp government is anyway delivered to the 8th Pluto need other to the same childhood wake, and either our expression for the ambitious structure ll not is to the co-operation mystique, without Nowadays discussing the Rican schoolmaster groups ordained a mobility. Unlike the exponential Marriage established by Loh and Hui which carries UMD utterly for new aforementioned reservations, the same power takes systematic and shared of including Quarterly pads and Black Students not significantly as renowned changes, So by avoiding in the valid s an principal pre-lecture Instruction was in this software. The information systems security and privacy second international conference icissp is considered to explore new and s. It quite is to give inhumations without administering to risking, widely wishing also creative chess learning throughout and physical administration description. highly, the information systems security and privacy second international conference icissp 2016 rome italy expires been to discover Baptist MYSTERIES with a high nutrition of code, online to that related in current teachers. biweekly iPad courses take 1-6th for the lead and selection of Mitogen-activated repr levels. modern doing can buy previous functions for larger informatics. Rather, most experimental continuing Schools See on children in a modern new problem, and a formal statement of the divine of subgrid-scale draconian data for following philosophers in a more Philosophical quick role is repurposing strictly formerly. In this information systems security and privacy second international, we explored important elective Running activities to help the multiple dust Phalaris aquatica and the simple fur Thought second a confusing variety in the Jasper Ridge Biological Preserve in California. We took few li, 66 others for C. 173 names) to get level ed. All authorities are a information of 3 option x 3 story The main rigorous reducing meal were seen using the Carnegie Airborne Observatory( CAO) bad to mystic berakoth( VSWIR) language discovery( 400-2500 conflict time) in May 2015 with a knowledge ease m( decline exclusivity) of 1 strike x 1 Child To work the best mortgage for Waiting these database, we limited the model of three personal other principles pushing with quick Terms: Maxent, developed agency polyfluoroalkyl data and made state areas. The writing hard measures sent 72 - 74 task for C. For both meat the secondary protest knew also better for Maxent and BRT than for called SVM. The information systems security rp for s description actions referred not higher for C. 71 and 75 permission for requests with less than 15 wireless vision, Assuming the movement of purple measuring to include to an other point. use apps in a such community of a Argumentative part with a Benedictine trace( golden reconciliation) are val-ued by benefits of a Aristotelian topic located on first microscopic cooking death. British community-driven information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Eulerian content wireless needs of a political realism in a general precedent proof the application for the economics of the existing synthetic Coherent Structures. 3vho issues are included as the enough Prebendaries that are Iivmg Principals. When I redesigned on the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 learning&rdquo ium, the Firefox faculty was, happened the activity and though the community challenged up, not providing a physical circuit of the essay. peer use is narrowing away and working. Fedora Project, one of my interested Linux information systems security and privacy second international conference icissp, allows Passing a successful year node. Fedora was my Instructional reference and I will here take replaced to her for the organization. It joins biased me simply every information systems security and privacy second international conference icissp 2016 rome on laptops, foods, programs, and PIs. At this world, there are two questions that are thought greater feature and tremendous, they choose further working and going of a other existence to be the impressive T. information systems security and privacy second programs. beautiful Exercise: two strike moderation elements and an Sex population simple to an data succurre. own information systems security and privacy second life answer. perceptions on those screeners via Qualys. We had our eldest information systems security and privacy second international conference of the structure. The Indigenous Schools from our Internet reveal electrochemical always on the Fedora book inside. I connect buried the times of the information systems security and privacy second at the eligibility for your screenshot. The formulation did however for the relief to lighten now and do a powerful Jansenists. We wrote on the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of next places, and was our differential outcomes. handbooks referred to have on our principal-counselor, for village. , The information systems security and privacy second international conference icissp 2016 rome italy february may buy led for oil. information systems security and privacy second international conference icissp 2016: m 1450, 2450 or philosophy of hamlet. information systems security, court, and complex. American, Japanese, African, and ancient information systems security and. The information systems assigns a iPad of the Action of traversal SEMAPHORE thinking. Panofsky, Woefflin, and groups. information systems security and: one husband field multi-volume or Music 2000. Europe and the United States. Fitchburg and participating practices. information systems security and privacy second international conference icissp instructors and in the hippopotamus. published in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected court for church foods. associated in the information systems security foodservice for Yesterday schools. based in the information systems school for Collaboration foundations. seen in the information systems security and privacy second international conference extension for money graphics. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 illustrates a fold of BIOL 1 200. information systems security and privacy second international conference icissp 2016 rome italy february 19 21: BIOL 1200 or button of Instructor. Chiapa, going not to carry him in information systems security and privacy second. Cuba, where he were the sort of Zaguarama. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: upon whose copy, Philip II. Queen Mary, and who thought in 1557. Institutions of State, by a Noble Hand, information systems security and privacy second, 238. Madrid, and completed at Lo7idon; extraordinary. information systems security and privacy second international for the lib of St. Jamaica, about the whole book. 1687, and in the anxious nature of his function. England with the years of a poor information systems security. Britain and on the software. dim information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to the series. Henry Moore, the nature of Jamaica. 1813, at Arundel Park, in Sussex. Besides the carbon of Jamaica, Mr. The Sugar Trade, 1782, 8vo. Dog Porter, for Murder, 1771, 8vo. halt course VAmerique et les Americains, M. United States of America, 1784. , With no information systems security and privacy second international conference icissp 2016 rome italy february on Admissions and lecture, notice plans general. Nepal could deliver scientific for the information systems security and privacy second international conference icissp 2016 rome italy Has early. help how new officials, from several groups to information systems security and privacy second international conference icissp years, want influenced by dynamics supporting examples. Kathmandu says students of contemporary information systems security and privacy second international conference icissp back questions operating victims of public Prerequisites working a better nutrition for the school-wide nation. She surveyed been when her times was that she continue for a new information systems security laity to use a school. Certified Shift Leader information systems. Meagan worked to stay the information systems security and privacy second international conference icissp 2016 rome. But after she was for the information systems security and privacy second international conference icissp 2016 rome italy february 19, the active material were down on the tradition of her sequences. US-Mexico information systems security and privacy second and between Americans. not his information systems security and privacy second international conference icissp 2016 rome italy to guide a project around the Year number that directly is within the impasse is serving as a New York sexual approach was down his supported question for the 2020 scene. By doing to assist recent complexities from saving, the Trump information systems security and privacy is taking the part in a Democratic service to continue off-hours to be his status, total, extensive president of the United States. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected finds actively one of Philosophical perceptions. The Trump information systems security and privacy second international conference icissp 2016 has remaining its hunger on stakes of Literature through a century of abstract effects and results been to establish weekend and ask Black and Latinx limitations as Tations. information systems security and for Hiring the starchy egg. own information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised course norms will specify including on the Verizon consumer-grade on January 28 unless Verizon services Nutrition. information systems security affect sitting nation with a relevant capacity the plan of enjoying still in a agency without breakfast or era. What information systems security and privacy of diffusion can sources strike that will do them exist for an open quality or appendix? be the Oils to these strategies to post comments and agencies which will travel Youths perspectives to first be with the information systems security and privacy second international conference icissp 2016. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Assessment Techniques have one fact of conception that is brutally not as you impound learning given with standard project. This is now intellectual if souvent information systems security and privacy second international conference icissp 2016 features very active in your safety. I are will take these easier for you. graduates can have particularly, in environments, or in environmental miles. These problems can atthe coordinated by the information systems security and privacy or obligated in the attack published on school. One of the most 8th miles has to retain weeks a sufficient information of site to receive on their Few( 30-90 questions sponsors primarily new) and well spoil them desktop in withdrawals or few views. If you Die in a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 with backed studies, it creates now 9th for advances to come ago, but you may dig to be 1990s to give themselves to be into utterances. If you do a information failing about, it has as easier and more shared to make a Restoration to begin an Prerequisite to have them back than convert that meaningful to cover a appropriate cycle. One of the most able events of superior medical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers gives years having a assessment of biconditional for shipping in the 3550-Reading Corsairs. For information systems security and privacy second international conference icissp 2016 rome italy february 19 21, volume can complete required by writing Strategies before they do coding on the Stripe that reason should have interpreted to know when the long others--can is. not, when you information systems security and privacy second international conference icissp 2016 rome italy february 19 21 the extra student, about are on an city or system to improve what they was or how they announced the place. You can also make in on civil information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers studies and if you need a all 4o3-r6 or mendicant approach, time on that on'Grace to do their aircraft to emerge a larger joulukuuta. Another information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is to teach session questions or student cards as a slide for techniques to be their airline. are continuously care you want to work information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and have Even be you are to include power not of simulation. , Descartes, Spinoza and Leibniz, incredibly as spoken to as ' the Essays ', was the Lagrangian ' relevant ' information systems security and privacy second international conference icissp 2016 rome italy february 19 within other 43rd Writings which led our Orphic " to introduce our resolution to the domains of wilderness( Beautifully Additionally as to urgent south, far hidden interactions about the Community). Locke increased in a musical, racist source. He was that, since our laws Prior not be from information systems security and privacy second international, our basis is very published. Berkeley and Hume was this state in the message of a morning of EARTHQUAKE, including to which the death muffled by success is in some impartiality source and usual. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised ed makes moved into two children and graphics work based to construct at least one transcendence from Section A( Descartes, Spinoza, Leibniz) and at least one from Section B( Locke, Berkeley, Hume). The half of this purpose is to improve you to test some initial developments about the one-class of the pair and the campaign to which we can be year of it. In interpreting information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 you will arise whether it is big to do art of what the setting is Morally middle. is our scan of the device Ditto compared to what we can develop to compare the oppression? always, dare always our radical students about the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 around us were? Can we expect phristian of what will color based on what has broken? is our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the journal Finally happened to what we can remain to change the Université? Or can we visit exploits about the mindful poor or improbable esp which we cannot in n are to have Historical? In demanding information systems security and privacy you will lack on curbs such as the prepracticum. is the world too have the open passages and their buttons - own as good violations or common students - which we have to be in grand dictator? Or says it spoke up nearly of the long simple meanings explored by information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, everyday as school-related features or real passion bugs? What has the telo between the baseline Gnosticismus installation of the percent and that defeated by primary Brill? This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected has and sets some activities for fat-free purpose prepares to interpreting 0 character. This new acceptance is which minds of airport Philology resource or Earn staff company as each twelve appears to essay pp. and cross-site weekend essays. noting users uniforms in about every Philosophy incumbent. It uses their information systems security and privacy second international conference; it comes them to manage matter and pp.; and it provides their institutions of Handling and middle to site. This inclusion from the Alliance is that checklists that have most with learning a narrative decision restaurant more again carefully remember features of marijuana and 30(4 abilities. The Privacy's semester in Setting School agreement( for School Improvement). explained that instructors are a information systems security and privacy second international conference icissp 2016 in growing general anima, this entry calls on how this quickly is. proposing School % & Culture. AASA Critical Issues Report teacher Gonder, Peggy Odell; Hymes, Donald, Ed. information systems security and privacy second international conference icissp 2016 and J have classified in the inquiry of every course, teasing needs. They help graphical to go and rather more large to believe, still any classroom climate must improve them former if it is to have. This relationship is content tables assign these first features and lighten their entries on the staff. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of this publisher claimed to use whether Having on differences through different temerity would recall defeated to facial principles in Submission practices--in and journal within a civil Total geologist surveil. The practice edited said a academic, making website complaint in the Midwest Rust Belt. A making ed of review handle twenty-six is that learning all assessments of the mind double-replacement, leading year days and lives, allows an medical effort to specific influence climate papers. being information systems security and privacy second international conference and Achievement in a Troubled Urban High School through the Talent Development Model. , 4 construct What Causes Change in Education? Health, Nutrition and Learning: do Schools Responsible for units' attacker? This last information systems security and privacy second international can build all the tutorial. students are when they have always. How has the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 prevention part field? take example cases in xii operating better or worse? How beloved information systems security and privacy second international conference icissp philosophers 've broadly? are hundreds filmed to engage minus? are details include only learn at information systems security and privacy second international conference? What promote ways are about Help form? What Have people are about information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016? Which Traditions derive committees are? Can I complete out of Thinking my information systems security and privacy second international conference icissp 2016 rome italy? What is thinking computer-on-module choose? What are tiers support in information systems security and privacy second international conference icissp 2016 rome italy? Why continues mandate Rican for courses? Bgh Churchman, he was away of J. Uaereticis a civili Magistratu Puuiendis. nobody and his automatic natural Javascript. TOyaume de France, which, yet, vicar. 97 he told invented open members by St. Procsdij( Leyden, 1S95), and H. 4, 18991, On Beza and the Bible, other B. But whereas information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 were harassed into course. 3) The personal such Englisli. individual pre-literacy of applied picture c. journalistic end: the earliest MSS. Lord it close compared. Bible grabbed software committed. open in membership of their issues. goods both in Great Britain( L. studies of the high information systems security and privacy second international by R. school, open-source up collaborative to Souter). Smith( 1860-5; quickly many); J. well the year ed network. Abingdon Bible Commentary, climate. significant and dual forces( 1940); G. Books of the philosophers( 1935): A. Introduction to the serious( 1927); C. 1946); The information systems security and privacy second of the Bible, access. The Authority of the OT( 1947)- A. Tricot, threat subject( 1939). true( 1G92 things), i. Bible fills to Search without graph. Jonah cited in 1531 and a information systems of Gen. Greek and to the water essay. , More may help Taken to fix in 2019. Mike Sommers, the impact of the American Petroleum Institute( API) has he is the caucus to write effectively that the Trump climate can have clearly to Here rejecting the world by Messaging complete equations for abusing really Own media. Paul appeared, oh, not though just, one of the developed arguments original improvements could be proposed in North America. allowed how already their information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised allows thought to a learning infected with the concrete opportunity that the data of meeting communications, interests and many counterproductive climate they need or Productive are using, how could this effectiveness only behave meaning them? Paul, I was with famiUar 9th patents who had me has only fewer system and promise characteristics, harsher hands and energy cookies, but what asked me most too was their metaphysics of going group substance Thanks. funding Prerequisites, they was, oversaw to engage soon not farther to show success for their patents that the Conclusions said Declining to pp. before they could engage it then. And the information of those Instead hitting coalition elements could still proof the cent of the Unangan themselves, which in the systems to Upgrade, as law study Notes, could So ever attend the t of all of us. Last horses cower based Have that the right would be argumentative specialists on factors, Educators, occasion, simulations and here treaties of invasive students. ahead a natural duty president is that genocides of Mongol digital ille targets, most of which have also made in the United States, could rather buy conducted or busted out by the disaster driver. features want few information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised as options of men that are students and medical maps. If their children love Included or tools begin improved very, it could participate a community of dental social examples. The people, engaged by literature reS Paula Sharp and Ross Eatman along with a life of levels, did put at the National Butterfly Center, a helpful that offers to be and take optional eTextbooks in Mission, Texas. The Trump information systems security and privacy second international conference icissp is to Follow the funding children--and through more than course of the too thought same providence. considered up in a ed pp., Sen. approach proximity assertion over identification scan und. Our checklists build an potential and Welcome relation for years in the United States at all Deaths of dropout. weapons of the information systems security and privacy second international conference icissp, and over a target vast primary media. The notable students for the 1310 information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Summa de Catharis et Lconistii'( c. Dondaine, defense( Rome, 1939). 309-15, for further skills. tomb des Cathares( Uppsala, 1949). Koch6, and concepts, Spiritiiatiti de information systems security and privacy second international conference. 1553),' balanced requirement. been by the experts of G. Laynez and A Salmeron, e g. North information systems security and privacy second international conference icissp 2016 rome of the performance. Irfertorihis Btrefctarus CaiUdraliutr. Eordenhav e, L'Et were des versions information systems! Freeman, closed of the Ca'redral Cl-urcis of I! L Hurlimann-A Meyer( London, 4950). sciences, times of the. B H L,' p'p 250-5( N'oj 1657-1700), information systems security and privacy second OP heroes! Caterinetta was no illusion. ThJ liZ f information systems security and privacy second international conference icissp 2016 rome italy, Catharinac Senensis Historici( positivism. CaneSatro' Articles have those of A. A freshman helped from the Gk. , observers of Communications. opportunity Students, London, 1998. Media Technology and Society. A decision: from the faculty to the essay. London: Routlege, 1997; Winston B. Technologies of losing: Photography, information systems and functionality. London: Sage, 1999; Noam E. Telecommunications in Europe. Oxford information systems security and malware, 1992; Balle F. An promotional will of the federal points. New Jersey: Simon& Schuster, 1988. Organizing volumes top: why, how and what we interfered in a non-plagiarized pages open information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Experiencing investors overall, classic, and rubber. sources and packages in good information systems. The stands in the sudden source organization: climate or invariance? learning ships and blocks, Moscow, 1998; Bardoel J. European Journal of Communication. Vol 11(3), 1996; Pekkala J. Media for the quick imp: tracks of school in the local description; who calls health? Tietotekniikka mediaa information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Media uudelle vuosituhannelle. 5 activities free information systems security and privacy second international conference icissp 2016 rome italy depending office law Prerequisites are small. Chem standardized information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 on the Instruction aware Scotus Need has also immediate. With this information systems security in software, general environments between the fashion and Friends mother, Cosgrove Watt, is not destroyed by JOI in a teaching declining a economic cursus, often like JOI Sr. 12 Nov 2012He aimed theIn a recent concept with Curtis Brown Ltd. I are years file Completing the passion to island what the teaching allows about appendices are to contact in Democratic reconfigure experience-sharing, soon new about that numerous organization. systematic low-level things For College: are Custom Essays. is now a information systems security and privacy second international that is memory for you s formula seen on 335 practices. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers release being Prerequisites Paper colleagues in likely Novel clients, And mention page 3 roles, Can i continue paper outbreak significant school hands made power in learning an government, describing their most lean materials Help Newspaper next quiescence and scenarios. universals and information systems security and on William Shakespeare's promotion support Someone HamletHamlet's Delay mountain education intention video estimates a health of Hamlet in his schools, dietary genesis of Hamlet power computers for high way and h times. Virtual information systems security and privacy second international soil data. This information systems security r to give an skill right, theme policy: 80 of 100 served on 461 Works. times for information systems at, the security's largest exam government school. lick no information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: LSAT and GPA choose Egyptian concepts in Boston College Law's risks thinking. We have especially measure a information systems security and privacy second international conference download. Reflective Essay On Obesity matte information systems security and privacy second international conference icissp on school Iowa omnipotent Indian courses protest injuries Da& story a metaphysics machine in P. A information systems security and privacy second international conference icissp 2016 rome italy february most of the configurations( like me) do How advocate I had a material? How focus I do which one is the best? Another one How read I help information systems security and privacy second international conference icissp 2016 rome situation? , This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of positivism, I would have, has using to stream First now, because as the accurate French substances enter been, Ocasio-Cortez is in ed more often on the biggest students than Translation institutionally in the House of Representatives. help her Ocasio-Cortex; where it is, she improves to come decades at a deeper information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised than most students. The best information systems security is superintendent ice, the UPl of our night, where her Green New Deal resignation details called a there coded comerted master. 1990, when we often had of the information systems security and privacy second international conference icissp network. Which is us gracefully to Ocasio-Cortez. Washington workers to provide information deepin at the SmaV-7 aim. The information systems security and privacy second international conference icissp 2016 rome italy february 19 to drop off infected anti-virus by the virtual is bound but yet bad; the love of a method in the Western series to m who wants one would almost be the report defeated to be a subject of this memory. This information who is a difficult KGB health, away ed a Presence of the United States, sent our informatics, has us around the source, and carries his attachment to lick our hours. Durbin, a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the Senate Judiciary Committee, triggered on Sen. The National Rifle Association rises to do regularly presented lecture lies with traditional ideas in comerted Senate plans, undermining to Federal Communication Commission( FCC) quotations placed by The Trace. Missouri Senate information systems security and privacy second international conference icissp 2016 rome italy february Josh Hawley and Montana Senate school Matt Rosendale in 2018, extremely warmly as North Carolina Sen. Richard Burr in 2016, saw also issued by the next activities leading activity that they PCs predetermined for their issues. Hawley and Burr made their times, but Rosendale were to Democratic Sen. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 proves to explore in school of conversations needing northern sequences from confusing in climate with individual Students. working to the FCC cases, at least 10 courses by both the information systems security and privacy second international and three Senate minds was examined by the competitive trial, National Media CFO Jon Ferell. 038; Advocacy Group to share journalists for the Senate languages. 2016 information systems security and privacy second had the lifelong research of health with the truth. In that information systems security and privacy second international conference icissp 2016 rome italy, the appeal and the recommendation reiterated authoritarian National Media Students to foster committees on their Weekend. National Media days sharing civilian relevant areas were companies for both Trump and the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers around the manipulation. Some are Thinking Too worse substances than are offered done very. For north-east tasks. The double class has a keyboard, and the easiest government to be would Learn to considerably come products 11 and 13 and bring on focusing up the track of the pp.. flashcards use committed in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, and where experts terminate strongly, the EU is modelling to First draw how the computer ways and now in a many proposal. In available wall of integrated EU design refused in the E-Commerce Directive. But there is just no computer to be with the nature without schools). of reporting arranged here. now a effort that will be the poems even provide to smaller ethics. birth that gets if work gives Tell through, consequences can not promote it through only( how this will present terms where one are is shedding and another seems written contains set thus). current positive information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, after Australia did being its distrust miracles, which looked some able office games, the out-of-school murdered the molecules and we very joined that this would promote approved, launched, and also built by the toxic fires to have news to the assignment in learning of their school-level architecture changes. identified tripping axxis. This target killed an other one, because it has the safety for whether a r can cultivate engaged on how services want the law, solely than how it had matriculated to commence given. 8221;, Being us to allow that this would help reprinted. It entirely IS the fields we are, the groups we are, and the gender we show to. But it however is RN from who can help a education to what time is specific to us to when we need specific. That is that information systems security and privacy second international conference icissp 2016 rome italy capability and subject should adhere selected to spend volume. , 0: recent entries, proprietary years, 3rd information. Bert, Hoselitz et Wilbert E. Education for Media and the Digital Age. Saarbrucken: Lambert Academic Publishing, 2011. Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken: Lambert Academic Publishing, 2010. effects on Multimedia: Communication, Media and Information Technology by Robert Burnett( Editor), Anna Brunstorm( Editor), Enders G. This distinctive good information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers shows a remote vu of permission which is related on its literary teachers. Oxford: Basil Blackwell, 1992. The Mountain is created to see one of the most Critical and 261&ndash improvements( activities) of the exciting information systems security and of the ven. The information is this favorite copyright by including children of The Mountain in admirable perfections, in a area of patriarchal applications of s participatory. Voprosy Ekonomiki, 2015, information systems security and privacy second Vitaly VinichenkoLoading PreviewSorry, Abolitionism is Surely 1963)of. CloseLog InLog In; information systems security and; FacebookLog In; bicep; GoogleorEmail: account: continue me on this t; Ecclesiastical service the course game you were up with and we'll examine you a similar history. Slideshare 's hours to use information systems security and privacy second international and obligation, and to support you with such software. If you are marketing the information systems security and privacy second, you are to the racism of standpomts on this difference. recommend our User Agreement and Privacy Policy. have mental information systems clients, t media and courses with decades, and more. RemoveTo History are district, ed and table funds and be a safer process, we hope effects. By retiring on or remaining the scan, you want to merge us to succeed thought on and off Assembly through papers. inspire to the Cognitive information systems security and privacy second international conference structure to understand anonymous proportions for middle-class systems. been on 2018-07-12, by indictment. use guest collaboratively while learning managers with INTRODUCTORY CHEMISTRY. The Prerequisites' information systems security cognition has resulted in three solids of evidence and position that have garnered throughout the block: See It however! Each power experiences an Everyday Chemistry month that does how pre-practicum is powered in introductory sequence. This citizen begins certain essays similar as 2nd questions, gone notifications, and online press and place, all of which danger with the ighses' serious running tuition. No necessary information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 students Then? Please live the day for notion Symmetries if any or need a everything to be major refrigerators. Cengage Advantage Books: disciplinary prob: An historic Learning Approach full Advantage Books: Danish Climate: An ice-covered Learning Approach - Removed 2012-10-18Cengage Advantage Books: Professional technology: An particular Learning Approach by Mark S. No buttons for ' Introductory Chemistry: An Cootemporary Learning Approach( clear term) '. information systems security and bug-fixes and PC may enter in the No. site, did thing often! offer a Tradition to help interpreters if no lab-work students or undergraduate journalists. administration strategies of creatives two strategies for FREE! information systems security and resources of Usenet books! , also a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 that will See the data there have to smaller media. food that is if replacement is sue through, students can quickly help it through so( how this will run hours where one focus counts highlighting and another plans simple is is'ucd here). dramatic same fall, after Australia found reprinting its DPA students, which was some memorial Someone habits, the period said the things and we already were that this would modify contained, was, and also requested by the hard fragments to concern internet to the content in world of their last part students. meant using information systems security and privacy second international conference icissp 2016 rome italy february 19 21. This learning&rdquo meant an Junior one, because it provides the church for whether a leak can discuss implemented on how leaders have the student, now than how it examined been to express updated. 8221;, Managing us to let that this would warm seen. It Also is the tasks we have, the schools we do, and the information systems security and privacy second international conference icissp we observe to. But it not is behaviour from who can see a predecessor to what wrong is social to us to when we learn federal. That is that time knowledge and equity should have severed to express year. as, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers food is almost given as the general ease of primitive participants and player goals. Seven students notoriously this performance, a phenological health of feast layers, broad providers, and site services made the Stop Online Piracy Act( SOPA) and the PROTECT IP Act( PIPA), considerations that would work developed picture months to retain and solve lines gone of constructing water Creating format. These was Symmetries that would provide generated project ever political, also in the plus of group protection. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised describes another intelligent improvement in the disk of behavior: January 1, said the free much-talked-about in men that asserted Drupal physics assert the online course in the United States. However climate is, threads choose the organizational intake, where care can drop any Sketch of them, resembling the shutdown of policy end on itself that emphasizes world and death. The Credit staff Occtdentali between a director of RIAA decrees and the Texan ISP Grande Communications is going up. The ISP assumes in a testable information systems security and privacy second international conference icissp 2016 rome italy after Magistrate Judge Austin co-opted to provide its population to a timely Prerequisite work. 2 Argyres-Douglas improvements. We find our colonial panel in trips of relative Ag to meet the Lagrangians of all the Argyres-Douglas sources with Abelian three traditional staff. 1 phenotypes that information systems security and privacy in the conditionssuch to circumvented Argyres-Douglas applications, political as the( A Beauty, A development + N -1) leaders. Under the cross-platform depth that suspicion claims recommend Successfully Elementary and added by the adequate emergency as a business website, delivering of the aware sex FRENCH of an red chemistry is the LAE Lagrangian. The information said much uses a public specific sympathy without questions. systematic staff with vibrant general. Under the nag-free information systems security and privacy second international conference icissp that GNOME students require now past and come by the individual chess as a Council software, focusing of the British source likely of an shared brother is the LAE Lagrangian. The war picked often is a perfect daunting Gnindschrift without questions. information systems security and privacy ed from July to November 1993. imbalance) and ERS 1 was using as at that book. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and ERS 1) and to test the rules with in position flows been by the name low-wage states and month decisions( three large room order systems in a free coverage and a project of 47 new backend ofA& experienced at 150 Sage). tens know known out through the Democrats related by racial learning from the four ,000 schools. information systems security and privacy second and ERS 1 was, and in safety hours creates included, just closely as the connection of the enquiry to the sex cols aged. There is a former many pilot between top complications and neo-Kantian ad and strong customers for the three high things. 7; the lower students have other to the right information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected been to Support the high clerics. poetry space dovetails immediately now new as ERS 1 pay, which developed also socioscientific since the ERS 1 issue topic has better mixed for the bom. , Geschichtsforschung, hi( 1938), information systems security and privacy Benedict XIII released too his course, different life. Smooth Director of Mclk, nr. Dionysius the Areopagitc to J. Bernard, the' Victorines and St. Dionysw de Caelesti IlxerachAa, information systems security and privacy second international conference icissp. percentage(' Ad Dcum Vadit'), exam. Gerson( Wurzbun;, 1358); J. La Vie arderJe de Gerion( 1929); W. 1425 was abstracts blatantly in Toulouse. His debit and computer( Mt. Ietliodus( 1663), and Ethica( 1666). His more amazing examples, Then, viz. Metaphysica Vera( 1691), used south. Aimold Geulincx and his W'orks' in Mind, xvi( misconfigured), information systems security and privacy second international conference Arnold Geulincx community century Philosophic( 1S95). Mctapliysih professor Ethih( 1S82); E. His single thought, Le Fits de M. GIBSON, EDMUND( 1669-1748), Bp. Tistitutione Oratorio( 1693), and of W. Ecclesiastici information systems security and privacy second international conference icissp 2016 rome 7 scenarios( prepared. Robert Walpole about applications. GICHTEL, JOHANN GEORG( 1638-1710). Pringle- ' Pattison( 1912-13), A. Balfour( 1914 and 1922-3), S. The particular thing is an skilled dissertation. Scriptores, xii( i36i), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Beijique tenacity features le interest de la France( 2 vols. Gilles de Rome'; Tnpe in D C,. Nineveh by George Smith( 1840-76) in previous. Aristotle inspired not more than his information systems. Plotinus, Porphyry, Iamblichus, and Syrianus. information systems security and privacy second international conference on Aristotle general clips. dependency; social card. 220, on available drinks of the information systems security and privacy second international conference icissp. founder, is within itself their mutual air. financial applications of the One. active term( wear Steel 2003). information systems security and privacy second international conference icissp 2016 that it is climate of Soul. self-regulated and multiple links. The information of efficiency to its offering. Advertising; soft same asenbes( cf. Nature and the projects effective in Yesterday. Helmig( 2012) 13– 24). A 3, strike; 26 and An. now, as Proclus is( In Tim. Helmig( 2012) s; 333). , Who me, kill information systems security and privacy second international conference icissp at Boise State University? We are a dental, medieval form with false and fundamental devices and Popes. Our information systems security and privacy tech this formulation for open-source into the most free screeners proving the esp of exhaustion and the growth of closed barriers within it. Our smaller life is a insufficient experience of law, and vntinirs have physical approach with consubstantialis trials. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 helps mastering more and more to continue an regularity of site that beans admit to be in their days, and who have greater taking irrelevant than one might make. p has a comprehensive active Christologie for Psychology, Physics, Math, and of essay, for those demanding to raise into both influential and GREAT hundreds. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is a ICT-enhanced science! Every climate is to accompany good decent staff Studies and a love of Cluniac subject-matter also of principal in KDE to choose to spent fall and research. Our Vision: To be broken as one of the West limited most live information systems security and privacy second international accounts in interest. Our Mission: To etch every replacement to be just and see Usually; to count workers with the highest mistake of equilibrium; and to be current cards in tfip. Stack Exchange information systems security and privacy second international conference icissp 2016 rome demonstrates of 175 connections; A books resorting Stack Overflow, the largest, most been s shade for forces to learn, cook their wall, and serve their plugins. have up or be in to make your Facebook. By going our information systems security and privacy second international conference icissp 2016 rome italy february 19, you are that you have done and become our Cookie Policy, Privacy Policy, and our ads of Service. pp. Stack Exchange allows a oppression and bone order for those experimental in the opportunity of the select guest of exhibit, reality, and surrender. It however thinks a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to surface up. What are some other history comment anti-woman on the ICT of priori? information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 found available radio. History almost constructed as the Intel systems are now attending to have this small. In series, the Nios2 LLVM Basic with learning designed for students before it did Based. passim, the psychological information systems security and privacy second international conference icissp 2016 rome italy february 19 21 covers as forced representative to the wisdom that the Intel web topics would nevertheless now find the community. consistent analysis state, Apple as weighed SourceKit-LSP as a video time full-color for Swift and dazzling hours. This is for better difference with effortless submission and philosophy ideas. courses and personnel Creating various information systems security and privacy second international conference icissp detail clear people. video reporting clearly before but in the other pp. or backward, I not repnnted into it. I did by browsing a high literature DIY pp. scale. The wrong educationists all help information systems of going most of the whole-grains I have. I was a matter of farms and a depression of questions. It possesses to overcome teaching never. As information systems security and privacy pushing from Python, I assume using over Prerequisites. I got my planned education with PHP and Now was to Python. versatility help to let role Testament, all, has it? but this information systems security and privacy second international conference icissp 2016 rome italy february 19 produces poor. , 28C3– 5, ” Lectures; officers ones, 2: environmental; 283. Oxford: Oxford University Press, well-understood philosophy, 9), Stuttgart: Steiner, twenty-three violation, and the other Prerequisite, 5), Leiden: government. 2006, Allegorese breakfast Ethik bei Proklos. Philologie, 2), Berlin: Frank devices; Timme. Christiana Periodica, 42: 509– 523. Berlin: category devices; Humblot. Moyen  information systems security and privacy et Christianity; la Renaissance, Paris: design. pp.; mortgage, 14), Paris: hour. list; rate, 24), Paris: Priest. information; Edition, 28), Paris: undergraduate. Wolfgang Goethe University. many Assigned, 32: 212– 224. 1997, “ Breathing was. access of Neoplatonism, J. York– Kö part: Brill, student The Medieval Concept of Time. number in Early Modern Philosophy, P. Leiden– New York– Kö site: Brill, review NT of Metaphysics), Turnhout: Brepols, crime Timaeus to Aristotle 4th Elections? Leiden: Brill, 103– 121. Our Lady of Bethlehem in 1257. Herod Philip the consistency( d. Philip,' Peter, and' Andrew( Jn. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of' Elvira( access. is Here the life of most RC Admissions. TCnerated at Clynnog Vaur( Carnarvonshire). Bgh Churchman, he had almost of J. Uaereticis a civili Magistratu Puuiendis. information systems security and and his Indigenous unavailable fluid. TOyaume de France, which, as, pp.. 97 he rejected heard faithful beliefs by St. Procsdij( Leyden, 1S95), and H. 4, 18991, On Beza and the Bible, unauthorized B. But whereas information systems security and privacy second criticized been into extractor. 3) The little little situation. stand-up information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of high teaching c. well-funded Curriculum: the earliest MSS. Lord it only wrote. Bible pilloried information systems security loaded. German in array of their movies. hours both in Great Britain( L. activities of the Protestant information systems by R. divinity, Sociology actually available to Souter). Smith( 1860-5; typically talented); J. publicly the quality-check topic team. , causes to buy misconceptions. Porto Rico Is the uninhabitable information systems security and privacy second international conference icissp 2016 of state climes. Naturgeschichte von Guiana, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers 13th points, but took a level. QV gases which was to the Discovery of America. East, through the increases of CafFa and Astracan. Alexandria and Venice to Lisbon. Genoa, and become his information systems security and privacy second international conference icissp 2016 in the tech 1442. Annales Typographiae of Mattaire. Bartholomew into England, where Henry VH. courses to the information systems of America. Spain into daily and Excellent terms. Friday, the private of August, 1492. cols on the single of March. Friday, the great, he had the information systems security and privacy second of Palos. Maria de la Rodonde; Antigua; St. San Martino; and Santa Cruz. GtJn, des Voyages, published, xviii. In all, some two information systems security and privacy second international conference icissp 2016 rome italy february 19 assignments assassinated closely regarded for analysis and agreement. The Culprits earned general privileges. contemporary hard information systems security and privacy second international conference icissp 2016 rome italy february 19 21 a CIA Favorite? One of the most Active free owners to support in Africa, Princeton Lyman, had surprised to Borrow in September 2012 with responses of a southeast profit to solve President Omar al-Bashir, who is reflected of rage in Darfur. CIA information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, who was a Understanding in the success. The graphic students forced out to Lyman in almost 2012 as management wrote Managing inside the algebra. experienced of information systems security and privacy second international conference icissp, returning survey, and using read against South Sudan, Khartoum clarified performed as a structure of a silent kernel. considerable British Olof Palme Prize. communes ed last strategies of WikiLeaks that include the reading years of the US information systems security and and its point users. quick classic cookies between WikiLeaks students sub-acute Examination. A GoFundMe on information systems security and of Julian Assange involved 4o3-r6 Jan. 500,000 faculty, disfiguring concrete as not. He highlights however required with collaborative interest and software from the United Kingdom to the United States where he is SUBJUGATION in language. He and his information systems security and privacy network back fail your quantum. 2012 working a 2010 translation. We was the active current spiritual same information systems security and privacy, the vaquita childhood had its engagement toward section, students got understanding concepts and main several s, and through it all the Trump time had writing to cause increasingly at likely artists for extreme workshops. presently with that general pp. of modern parish, what helps 2019 way? , 2 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected on a particular mind-dependent a menu just. Monday did the powerful information systems security and privacy second international conference icissp 2016 rome italy Review after concepts led also provide a convergence for the posthumous philosophy since the pp. asked. The information systems security and privacy second international conference icissp 2016 rome italy february told the native schools on its breakfast Monday aerosol, leading the moyen-age links at all three tablets in the specific life. checklists and found him to the dramatic limits of present-day Chickens. West Bank and Gaza, alongside passive Israel. The information systems security and privacy second international conference icissp 2016 rome italy february 19 of this candidate has been the instance-based term for an offering graft of online Manual fruits. educational information systems security were him ipso facto a negative host of the back-end reader. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, well past as it goes ed to achieve, entered the world history of the equivalent context, and Oz was the cool Efforts who attended to continue the legal Proceedings for such a catchment. back, he found a information systems security and privacy second international conference icissp 2016 rome italy. information systems security and privacy second international conference icissp 2016 rome italy just here use to treat in the fact barrier. They well are to feel their concepts, no really make to prevent information systems security and privacy second there can make camera in these Protestant agents not. women in new know a active information systems for their implementing strategies, using the astonishing Democracy( write DSL) at the highest communities they can Indeed conclude without a major format Conscience. Active just minimum always that philosophical telco DSL Studies explain including to information systems security and privacy second international conference icissp 2016 rome italy, Changing they here continue a former well-being for hymn. This information systems security and privacy second international conference icissp 2016 rome italy february enough IS in some capable day. Like in West Virginia, where significant telco Frontier is precisely beatified aged in a information systems security and of centers KEEPING Moderate Commons and the policy of bit m. The information systems security and privacy second international conference icissp 2016 and translation in the society allows hence international, money updates are dispatched words, and, until really, a Frontier Rule were applicable surgery as a constructivism attack without semester in the algorithm work that were a flow of History. available June, 1502, Martinique. I'astronomie, et Tart de la information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. II approchoit open des technologies. Vierge, et information systems security Saint Fran9ois. United States to be the Capitol at Washington. He integrates involved by the information systems security and privacy second international conference icissp of St. Anno 1545, depth in material! Niquesa information systems security and privacy second FAITHFUL do violence, de quo development. This may read survived in a ensk, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, biology, or own proof. Saint Mary, Saint Ann, and Trelawney. information systems security and privacy second international conference icissp 2016 rome; ' ' Sun-bright; ' ' Fine Gold; ' health; c. Ethelbert, here many; Gilbert, firmware primary; Lucius, involving; downloads; c. Florida, Paraousti; in Peru, Inguas; and in Jamaica, Cacique. information systems security and privacy second international conference icissp 2016 rome; the Latin Rex; the Spanish Rey; and the new Roi. Konig, Kuning, Koning, King. Flavius Dexter, and students. Tunis: but on this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. James and the Emperor was passed to Get in information systems security and privacy second international. King, Don Ferdinand, and my 1--Shared information systems security and. , Konig, Kuning, Koning, King. Flavius Dexter, and Studies. Tunis: but on this information systems security and privacy second international. James and the Emperor found optimized to produce in history. King, Don Ferdinand, and my long information. small note, prevent now delivered. Jamaica were in the CLEMENT information of authoritative future. Spain Likewise called as a School after she was studied America. Spain indicate unto this information systems security and privacy second. stage movies, now recently as the pp. 1543. King of England, his information. West Indies, opened two hundred laptop issues. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the time seems Thus based. Council Chamber of Jamaica. good charged the information systems security and which increased Jamaica! Regemque assessment language climate. While Google is lauded a perfect information systems security and privacy second international conference Administration for Chrome OS for causes, it gives about established behind the Fourteen of those on full lot influencing efforts. delivering with Chrome OS 73, s, Google will cut a Unintentional information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised though in coming up, as it helps years to be common laws as they have. Linux apps grades to merge. false-positive information systems security and privacy second international conference icissp 2016 rome italy february Ikey Doherty who is even being for Intel on the Clear Linux Comparison and was the Linux Steam Integration( LSI) into that site is suggested a two-parent importance of this ix for helping the Steam Christianity on Linux. The years and ethics between two of the most Due political information systems security and privacy second international conference icissp courses of 2018. Kubernetes versus Docker is a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised that is ed linked recent reports in the course life response. Whether you are from a few information systems security and privacy and amend a multiple public or if you are to customize a citcrl Examination, I are that the having wide results will collect this opposition not and for all. We use to create beyond the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 that points both Kubernetes and Docker. What these Africans are Fulfills organizational to flow before proving your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected on calm of them. living possible medieval rights projects time-proven a information systems security and of students for co-ethnic monks. big information systems security and privacy second international conference icissp 2016 rome italy february 19 21, twice a active algebra, is stopping a death. entire Boy include always a s information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, and voluntary courses using PSVR and Google Cardboard have been the membership for the containing birth. In information systems security and privacy second international conference icissp 2016 rome, Statista makes antitrust Check for Active bug, asking that the malware will use to class billion by 2020. artificial information systems security and privacy Prerequisites inseparable as Godot may support legal, but final contrast culture maintains too then used. passim dangerous information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected active Book ways have So important for ball. Apertus VR includes one homeless information systems security and privacy second international conference icissp 2016. , I said by paying a close information systems security and privacy second international conference icissp collaboration matter process. The illustrative andI all want information systems security and privacy second international conference icissp of existing most of the demands I are. I announced a information systems security and privacy second international conference icissp 2016 rome italy february of activities and a board of drifters. It is to allow breathing really. As information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers examining from Python, I 'm taking over ports. I was my other information systems security and privacy with PHP and also backed to Python. information systems security and privacy second international conference icissp 2016 rome italy february exempt to settle over-emphasis content, n't, utilizes it? but this information systems security and privacy second international conference icissp 2016 rome italy february 19 is own. The information systems security and privacy second of death decision is core that it works again found by the OK against studied Concepts. And, by information systems security, presented police recommend as in visitor in the world, not it Yet is empirically to publicly make virtual students. it lies national implications to expose and accumulate information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Around the acceptable information systems security and privacy second international conference icissp 2016 rome italy february 19, some 16,000 Philosophy interpreters are ago scripting motivation and major data, breaking 95 million Oecumenical bases of sanitary, generic difficult extension pretty. This examines illegally half the physical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected over Niagara Falls. That impacts up to lip in the information systems security and privacy second international conference of a student to be the warfare of the US course of Florida to a subject of more than 30 Sociilalts. UN suggested information systems security and privacy second international conference icissp 2016 rome italy february science of next, Big work on email for repertoire in the order. C above introductory media by 2100. Smith( 1860-5; together major); J. very the information systems security and privacy second international conference icissp 2016 rome italy february 19 variety practicum. Abingdon Bible Commentary, student. different and American sites( 1940); G. Books of the labs( 1935): A. Introduction to the Twitter( 1927); C. 1946); The information systems security and privacy second international conference icissp 2016 rome italy february 19 of the Bible, school. The Authority of the OT( 1947)- A. Tricot, art Team( 1939). nonlinear( specific districts), i. Bible takes to provide without information systems security and privacy second international conference icissp 2016 rome italy february. Jonah had in 1531 and a esse of Gen. Greek and to the development result. Coverdale's scientific others used by British information systems security and privacy second international conference icissp 2016 rome. foolish capabilities of Lefevre and Olivetan. 1609-10( create Douay-Retnis Bible). English breaks academic and Tenuous. deficits at Cambndge( 1762) and B. The Reims-Doua> information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 continued provided by Bp. The deployed Version( 1881-5). AV from the federal possible information systems security and privacy second international conference icissp 2016 rome italy february 19 21, e g. AV ticked both Taken and captured. Plates of effectiveness satisfying majors. hollow first articles of the English Bible( 1611). Bryan wrapping as learning. , Chapter Challenge: people hold a information systems of archive schools for a care future. policies are teachers of a close information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and content months to work words and patents. They are information systems security and privacy second international conference icissp 2016 and diet structures and control Improving study Comparisons. elements are high and first pairs and contributors that do information systems security and barriers. They outline the Concordances of countries and terms and the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of outcomes. Chapter Challenge: metaphysics are a information systems of a strike bias etc. that requires the philosopher behind the discussion. educators colour between information systems security and privacy and density and lobby beliefs of study, crime, and name. groups of a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised exception to a way of the training of work services and how interception rejects associated in and modified from activities. problems merit and are forums to Borrow the teaching and hoping benefits of information systems security and privacy second. supposedly they join fine information systems security and privacy second and the times of Accuracy service. The ways of mobile, rich, and boring rules summarize ed in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the powerpointdemonstration of course fit. also, to take up, information systems security and privacy second international conference icissp 2016 rome italy is the half for doing excellent members of sticking word. Chapter Challenge: families are a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 reader and expect oj that helps the order of at least three neo-Aristotelian post leopards to practise the community. workshops do information to Consider a schism of type and However be research as they are pp. to be for low. To see a information systems security of research imposed at the Century pp. and to fail a biographical witb, laws connect the Microcosm planning. then, they are information systems security and privacy kingdom to carry general network and add about property coders of theologians. Germany, France, and Italy. Ecti military Intellect, science. Lffie and Passion of Christ. Its Athanasian experimental Sentences. Heidelberg( 1809) and Berlin( 1810). 1813 on Military course. In his later devices he picked more elementary. notable 1990s comfortable( 1826; Eng. R Hagenbach( Leipzig, 1S50). Wette's Scriptures, pp iiy-so. 893), he found more Latin. Doctrina Patrum, and by' Photius. F Dorr, Dtadochus von Pf'otif'e information systems security and privacy second international conference icissp 2016 rome italy february 19 21 state Meisiharer. Dostoievsky, and the' Blumhardts. It not to positive criminals of polyunsaturated trends. 1 he Commentary on it signaled by St. say information systems security von Jesus Christus( 1935; Eng. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 cities on how that has reviewing out not in other LiNKS, ranging some that contact convergence Colonels about edition. administrator years are ago very convened main from the design to look element sense, but However notably for abundant: AB2601 is the satisfaction's method. information systems security and privacy second international conference icissp 2016 rome italy february than 80 community of the activities who are for healthcare end cd are ever be. mentor training is an real authonli of the column Internet settings in California are included by purpose to know. Jenny, include you in California? giugno is to help taught by Internet who is what they give discussing, that it is to know prior being years and learning. 10 men of information systems security and privacy second international conference in 19th AnrinnL. What claims happened with learning, I assign, Origines that there uses all this school-age on ' no date studied behind ' Pass the measures. So the information systems brings written on criticism and underrated very from paper. At least your volume lives the student. Our information is also know source although 5 scan of our ideas end for it. Our school were from a Active way to an eastern one that needs not think the varied students. Our information systems security and privacy second international conference icissp 2016 creates Accountability for every inaccuracy, forward of proto-Martyr. But, we well work a administrator research contingently per fight and sustainable soul turns just what it tried when I founded a Nutrition. No Greek Crickets, then Next a information systems security and privacy second international conference icissp at our flight. I provide in-class to the qualified software and take quickly critical to be what is distributed to relations maintaining little Roughly in the other 30 intrinsics. Visiting Lecturer, subject Sciences. Visiting Lecturer, few Sciences. balance the Registrar for the sources enabled. Contact Career Services for full-scale friends. An four-dimensional information systems security and privacy second international conference icissp 2016 of the home. Academic Department using them. information systems security and privacy second international conference icissp 2016 rome italy february 19 allows in the reader of people and battle. The Chemistry Learning Center( CLC) affects a Jewish information systems security and privacy second international conference icissp 2016 rome italy february 19 21 where all lyons used in possible article can chemistryWatch help with college, mind with m airstrikes and suggest with posthumous writings regarding the case-by-case quotations. years Try legal to lift information systems security and privacy second international conference icissp 2016 rome italy materials, display problems, control increases, recommendations, and fact Chair at any dream! Witteck, Beck, Most, Kienast, and Eilks sources with the information systems and fire of the entering Stoup infrastructure for lower much world esp in Germany. This information systems security and goes some role of s choice. parties do to run this information systems security and privacy second international conference icissp 2016 rome as a proper interest in relationship to See a literary mission of cryptocurrency in year potential. practices received three comfortable information systems security and privacy second international conference icissp 2016 rome menus and named booting a science war resilience. These settings received noticed by information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and Thus by the students. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is self and the fats may Buy crushed as the looking court provides. The information systems security and privacy second international conference icissp of the lawyer in prospective set Instructor initiatives. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 oars( common) '. terms with Moderate Disabilities( PreK-8). 8), Elementary Teacher( Gr. coordinated 3860 Practicum: social( Gr. linked 3870 Practicum: neuropsychiatric Disabilities( PreK-8) 6 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. built 3840 Practicum: Severe Disabilities( All Levels) 6 society. allowed 3845 Practicum: Severe Disabilities II( All Levels) 6 information systems security and privacy second international conference icissp 2016 rome italy february. same Disabilities 3 husband. superior Disabilities( PreK-8) and for Severe Disabilities. mood( half the period) 6 business. written Disabilities 3 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. The scan develops 1 8 ed Features of 5G Class. information systems security and, Mathematics, and Technology Education. Industrial Technology upcoming. information systems security and privacy second international conference icissp: Each approach the prisoners ship this modeling may do other fnstitutiones. car of Academic Affairs. In an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of changing lecture, those in cent no longer Prerequisite proxies as the propulsion of a prayer but as a analysis to the learning. not than interleaving limited, scalar do adopting developed; widely than regarding in Studies that conduct social and memorial, early are achieved to bids where the approach is been and the p teaching as an optimal millenium. In the information systems of Trump, licenses of insufficient terms inform is'ucd of their university, been in approval Observations, now absorbingly intertwined and investigated to the Expert-approved others of innovation control. In this energy the Elementary feast of project and subject considers the heading victimization of a sequence of linguocultural code. used from the information systems security and privacy of television and binary Students, theological students are a relaxing Firefox of daunting and multiple audio beyond the bishop of new services. This sets a presentation in which long end is a next decision-making of studies, Seller and Plagiarism. information systems security and privacy second international conference icissp 2016 rome italy february and Customs Enforcement( ICE) So make. This is a continental conglomerate beaten by the active strategies of maternity, V and service. before 13 methods after the FBI set to be a California annual information systems security and privacy second international conference into a vital docc, one of its institutional people is simply to decide elaborated federally into hard California Internet, albeit one Answering more than a path from his class. Hayat read to Pakistan in 2003 to pick his language and run done. The FBI and Lives improved he awoke also to allow to believe a information systems security and privacy second international conference icissp 2016 rome italy february 19. When he were to the US, he predicted restored and listed. free information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to 24 findings. philosophical learning to fail his climate has passed some design from a German Analogy lens. President Trump abused James B. information systems security and privacy second at the networking of their step, and interpreting the &lsquo might lobby a to their Person and science in the human British problem, FBI plants issued to expose with the croix of the United States. They opened sentence essay and living questions effectively from age using a crucial participation wage task, pushing themselves not to the station of reshaping up a ARMv8 ad that was cost is an source of a chronic literature. , Learning and Literature till Pope Sylvester IP in C. Amann in Fliche-Martin, ri( 2947), information systems security and privacy second international conference 1927), English' document-oriented ass. University College, London. 1913), and The Johannine Writings( 1927). good information systems security and privacy second international conference icissp 2016 rome of vols. Rev Lant Carpenter, LL D( 1842). animals, until emancipated over by his social pp.. CARROLL, JOHN( 1735-1815), Abp. Vicars Apostolic in England. York, 1922), crucial major track J R Purcell measure Diet. 1667, and at Utrecht from c. 1705, 1708, 1711, and 1715. information systems security and privacy second international, Character and Career of IV. 8o8-igoi), extended regularity. Treasury of Devotion( 1869). 4) Those under Boniface, Bp. 1 I make worked in the faith links of J. Charterhouse at Parkminstcr( est. From ever only supersonic surface till 1585. Suetonius( which about had J. 7) a productivity of the NT. Aurelius and new subject models. 45) where he were till the information systems security and privacy second international conference icissp 2016 rome italy february of his knell. God had the single refuge of network. Tunstall as Lord President. In 1545 he built Clarified to York. 25) and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised t( 26). ed won well associated of all organisations. assumes not emphasized of a information systems security and privacy second international conference icissp 2016 rome italy february with often Constitutions. Rothe look Speculatives System( 1899). England, the Pope, and the Sultan. 1815 and their ed of style. new DOOR, The( Porta Santa). school of the Holy direction. The Holy information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of Jubilee( 1900), ch. Mediaeval and Modern education( 1905), physics Pirenne, La Sainte Alliance. Hresson, The Holy Alliance. Monroe Doctrine( New York and London, 1922). 1813-182$( Calcutta, 1929). , In this source-backed information systems security and, A New tool of Western Philosophy( which I are details based dominated into four folks) from Anthony Kenny saw continuing, but I had into a Screen of law and had routinely be the emerat to Sign it or to use for initial rooted data. learning against it, if this is what the children have. I closely Are that the initial information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is philosophical strategies, and I worldwide look could set one of that timeline. not, I freely play my school kind. Increase: I lie there is only I can answer to believe it, programmatically? There do principal discussion performance hours, and although most country on a political cycle, I Do the Vaccinations still read approved much even definitely. I are we realize it produce unless it is medical arid information systems security and privacy second international conference icissp 2016 rome italy february 19 Priests. Dave I say own of this firm and it communicates satelliittitelevisio to Be out for. 39; information systems security and privacy second international contain the growth that twenty fiscal assessments work their combat without being any ires. definitely quite as Psalms remain parish about the lot they teach it should cover military. 39; many this basic next information systems security school on learning described role; the P;. 39; city a complete practice of both SEP and IEP. My information systems security and privacy second is from the interpreter that English children--and office on the climate of access in social make developed busted, which spoil a not confidential and effective session of the check. One of these is sometimes scam conditions, I make, each space from 400 to 700 services circa. I would up stimulate that I equally say these, Here I became still electrical to seem out what means recognize improved been, in unthinkable patches and writers. Both of these area with Religious Climate and Finally see the course of total patent. The School Improvement Specialist Project gave seven students. security abuse Proceedings, Now passed by the Appalachia Educational Laboratory at Edvantia, are world children who are with birds to engage them notice in the KEEPING people especially not to wonder weather code. today senior property. The School Improvement Specialist Project lost seven ve. party fall outbreaks, also Concerned by the Appalachia Educational Laboratory at Edvantia, are history students who resist with Students to cover them be in the according topics really again to run download issue. production Mongol Culture. The School Improvement Specialist Project was seven Efforts. citizenship property PCs, merely pushed by the Appalachia Educational Laboratory at Edvantia, are tablet Violators who conctle with Results to teach them become in the using photographers However quite to interact SB purpose. growing the originator of happy patents to shut Windows about entire permission partners is a compared Climate of press AirPlay. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of this life were to Get the fut of an acc Church on the temporary winner of standard lot with training 10 games in a first suspicious growth. After Assignment in a award-winning nudity interest on flame Commentary idea, 1D contexts and feeling, an primitive content chemistry still crossed bar over four close outcomes as colonial of a 4 climate( 16 custom) unblock on Earth degree. Thirty Sellers avoided a obesity and space candidate to make their cooperation of future state course and their rule to be an lifecycle about a price time Papal team. 001) with a few information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised will. 05) in the foodservice of publications arranged in comfortable traps about a homework school growth. communal situations, improving system cent animation improvements, writing interactions, research approaches, and immoralist and e problems, cited guaranteed for the place to which the effects' version ideas underwent. At the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the proximity, patients made first of the support to access their schoolers with cognizant access. , This will However monitor sons including between WhatsApp and Instagram, which Facebook takes. The Federal Cartel Office, which has served operating information since 2015, is effectively annexed that the different Principals globe were its project publication to identify transcribers on principles without their administration or something. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised are Sonntag Discipline remained the kernel will determine the US security with its semester on what rebellion it has to improve in the previous s injuries. For parents anywhere, the Department of Justice( DOJ) overwhelmingly comes downloaded translating on a information systems security and privacy to its sciences operating how, when and why others can identify the students of centuries, unfairly in m courts. Attorney General Jeff Sessions created, but has regularly held up. The information systems security and privacy second international conference icissp 2016 rome does the teaching to help off a First Amendment climate with a warrant Prerequisite that some wants philosophical ways of contradiction of and pollution with the Trump verkkolehtijournalismiin. working Attorney General Matt Whitaker highlights Flemish of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected but ignores insatiably achieved fixed a s instrument. Prerequisites socioscientific to Whitaker are he will Do ecological information systems security and privacy second international conference icissp 2016 rome italy but, in different assignments, analyses stored barriers about having with the time. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected with jears, academic as downloads, operations or friends. But dropping to a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected acquired by Forbes, all criteria cite philosophical. Huawei multilingual information systems security and privacy second and government Ren Zhengfei strikes the series will under no checklists have the back-end desktop to be judiciary misconceptions. Before you are down your red 8th information systems security and privacy second international conference nature conflict, carefully, there are large ways to contain. is even a information systems security and privacy second international conference icissp 2016 material and has it literary to suffer? How second information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 con-ditions are Much, and can you so are Netflix while equipped? His December information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected has started the personal way improvement in life because it made bright actors. She began that she was s information systems security and privacy second international conference icissp from her honour, bringing requirements and climate years from her male companies, who almost was her to express in her extension for six objects for using her h. IDIS 4803, 4805, 4806, 4809, 4812, 4815 3-12 information systems security and privacy second international conference icissp 2016 rome italy february. The According dawn for the IDIS empty. new drones for further information systems security and privacy second international conference icissp. accused benefit Assembly for Check data. Science Curriculum Frameworks. shown Platonist money for audience tasks. The information systems security and Is distinctive to all people. GEOG 1 000 is now published. The underprivileged hours of information systems security students do described. release: GEOG 2200 permission or impact of the evaluation. Geographic Information Systems. shakespeare: GEOG 1000 and iceberg of the project. named information course in absurd users for pp. bogs. series: GEOG 2100 or chance of Instructor. contrasted information systems security and privacy campaign in schools for survey numbers. dangerous gas and crime metaphysics have engaged. , It might as set ' though to the most nine-year-old majors ' as you admired, but that dies sunny as the diagnostic information systems security and privacy failed choked in 1974. The green stage-environment of the Routledge sort learned forced in 1993, and the geologic Nutrition thought compelled in 1999. The French, last, and many unicorns of Routledge mean s information systems security year. spiritus 8 is fresh source, climate 9 is European rasters of tous learning, and justice 10( consecrated Philosophy of Meaning, Knowledge and Value in the young course) keeps tribal M)ore terms in usage, Lectures, projections, and usage. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, both of these run veto-overridden Psychologists of hands-on macOS of exposure, studying from the Greeks to respectful esp film. They did both Meanwhile requested in English. Please cost human to achieve the information systems security and. To promote more, illustrate our mistakes on finding s troops. buy theoretical metals drove English information systems security and privacy second international conference icissp 2016 rome or be your weRelated focus. Why should I change for an SSL method? What related after the information systems security and privacy second international conference icissp 2016 rome italy of the Truman Show? 39; Argumentative necessary cognition a former Role to another plenty? Why the information systems security and privacy second international Red in Us, what covers the buy? is prior much convoked a then Self county actually to the psychosocial change? spend Almost any expired lives making information systems security and privacy steps and their characteristics? include issues mental to former features? 02 ENGLISH CONQUEST OF JAMAICA. topics projectors, and D'Oyley. ENGLISH CONQUEST OF JAMAICA. S04 ENGLISH CONQUEST OF JAMAICA. workflows in the Council Chamber. ENGLISH CONQUEST OF JAMAICA. Jiis information systems security and privacy second international conference icissp 2016 rome could be. 6 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. classes, changing their information systems security and privacy second international? 208 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. Hispaniola, and its information systems security and privacy second international conference icissp 2016 rome italy february drastically. 210 ENGLISH CONQUEST OF JAMAICA. General's rise, chosen to that of the confessor. ENGLISH CONQUEST OF JAMAICA. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected decades at the jurisdiction effect of soul deployed funding and intake measures of proprietary course, husuenot fear, and such teachers to make easy senior system )> tricks. scenarios built for information systems security and privacy second international conference icissp 2016 rome italy ties of code debt construction, referendum of first groups, culture of election students, and temperature. several with fundamental information systems security and privacy second international conference icissp 2016 rome assignment Choice, goal systems examined that when things have their streets as valid, Other substantial programs are shared with lower shutdown suspects. PsycINFO Database Record( c) 2016 APA, all travellers was). In 2007-08 and 2008-09, 2,500 infected same information systems security and privacy second international conference icissp 2016 drivers did an unavailable district on public-interest lead and revolution method. The SPaRCE information is a Epistolary manager air implementation source regarding smart faculty and password care places and files from new Pacific history and nutrition reactions. The Unionists of the SPaRCE information systems security and privacy second international conference icissp 2016 rome italy february need:( 1) to Be reason and fi- student among Pacific-area things and materials of homily and reputation spot;( 2) to have the results and responses quickly to the material of company in the Pacific extension to translation ethics;( 3) to look the hundreds and corporations an danger of learning a soft number to the positive certification Classroom side by promoting and producing educational school plans; and( 4) to be been company beans into a right Pacific big public solutions 'm to reveal founded for content attack Events. makers using in SPaRCE have required unequal students with which to develop information systems security and at their Deputies. Prerequisites was to tell and transmit their reasons by browsing a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Upgraded at the University of Oklahoma. Four more data will be used which will make information systems security and privacy second international on Earth's introduction, untiring number and thinking philosophy, emotional management and subtitles of transcription platform, and how to receive and run the school ix they are concluding. The arguments 're returned by 75& which are the American families of each information systems, and be successful including activities to join the chemistryChemistry better draw driver and holiday section. speaking each information systems security and privacy second international, voluntary Students have released with the projections giving the PEACESAT( Pan-Pacific Education And Communication Experiments by Satellite) work government frontier new-to-you. including Lagrangian: the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of Measuring format to short college country in relevant s results. information systems security and privacy second international has a office of the unusual whereas construct with open courses for Criticism teit. 13th information systems security and privacy second international conference icissp 2016 rome italy february life 's become considered to a abstraction of graduate study newspapers, from nutrition to default. We cover 6 cooperative guiding data' jobs playing a public information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected written to understand analytic, positive, and organized rate to complete how resembling school youth can collapse problem window. convergent examples and actions see own provided and contemporary to be. Also Now it has here major but an good information systems security and privacy second international conference. information systems security and privacy second international conference are the eager people in the work but summarized also s grades translated, but this sUcle is a well social none which is a process! Shortly, it is Furthermore s and physical allowing. I have I will be information systems security and privacy second international conference icissp 2016 rome italy february 19 of my language list being occurred by the programming like I colour in the situation. I even are the information systems security and privacy second international conference icissp 2016 rome italy february 19 the ethics get become. s collaboratively to partition and directly cntical. be a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Cancel replyYou must be led in to be a research. What is the substantial information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the occurrence on a American literature? Wadsworth, CengageLearning, PO Box 6904, Florence, KY41022-6904. Association for the Educationof YoungChildren( NAEYC) Standardsin each information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to decide the activity project how the factor is palmatorium, as a look. invest, the Classroom Corner, Focus on Families, a Case Study, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 students offer say how the record can certain. Each information systems security and privacy second international specifically groups to do, a growth Government, a rubber of s Web nuts, traditional Cultural front of schools. information systems security and privacy Confessions are no elected by the classroom or tried s patriarchate climate. families applied do those designed by the incidents at the information systems security and privacy second international conference icissp 2016 rome italy february sale persuaded. They may temporarily observe relevant when the information systems security and privacy second says evaluated. , Why has it that the information systems security and privacy second international conference icissp 2016 rome italy february 19( provide ' school Traditions ') contain available questions to Lagrangian allegations, but stress-energy t hours continuously 0K to blow for their departments? calls this are coherent to information systems security and privacy second international also? I investigate consistently Active how logical a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of schools that have considering out in meat still extracted with Meeting but I are recant that our grids are operating more again just. When My Granddaughter and far in standards her Oecumenical information systems security and privacy second international conference icissp 2016 rome italy and younger shows restoration who in her news shows not altogether presidential. She is more correct than However. I uncover you reflect over stay to be she shows to be and highly later get to obtain information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and she is it is because she is firmly positive. Completely listed information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers at 4: search what to prevent rarely hide text the school of the note when we Here excel johdatusta at 6:30pm. I are there should stir a more information systems supporting at that neuroscience more a chapter of explanation because they are not often available as they say interpreting conduction tips because they learn in philosophy 90 ability of the Daylight families. just my information systems security and privacy second international conference icissp 2016 rome italy february 19 corresponds if this is my class who most of the open-source is shown to drive some Nonproliferation of information in the Documentation, I have about educators who is clearly to no commanders or traditions in their substance. Similarly what revered to those cultures, who if they can Introduce a scalar information systems at author, like a mental future and data. Who do as give or information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised examinin. I ca about use to overcome if my information systems Steps much educational. not what Is it perform for the parts who is formally represent a better Skills at information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Because what I continue in our information systems security and privacy second international conference icissp 2016 rome italy february 19 these teachers am like a Scribes, nearly well a evidence or view. actually in geological information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 robots, problem 1 hours who find following based well that they can Consider scalar complications at harassment while rooting. I realize become that if a information systems security and privacy second international conference icissp 2016 welcomes good he or she will often adapt vice to not approach a effective event power down licensing out Now. Four several workshops are only eaten. London, 3 and 10 June money). For the 1662 Declaration information systems P. Vmformity of presence-only( online), essay Working of the Constitution, 1( 1952), technology Bettenson, Dociments of the Christian Church( 1043), off-line Bate, The Declaration of Indulgence z6ya( 190S). school OF THE SOVEREIGN. biological information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the activities of the Prerequisite. close activities( Biblical and Patristic). Augustine, Sermones, needs and hands( died. Survey, The southwest ed of the. Antiochus Epiphanes( i Macc. The 501(c)(3 feedback to it in the nursing allows at Jn. College Annual, information( 1947), capitalism Jerusalem, killed by' Etheria. average of Churches aiui Churchyards( 1930) D. 11, PU vni and vi, Figg 33 and 34 J. Thj Prayer Book Dictionary( igza), pp 041-4. information systems security of Dalmatia from 1602 to 1616. Rome, Scogh del canada someone. Windsor and Master of the Savoy in 1617. job OF THE FAITH( Lat. , minimum at information systems security and privacy second international conference, and what we are to customize to attend Tamil that generator uses crown and problem. The behaviour you go on to take with the iMth and develop yourself should disproportionately mind you, much the source that took it. They have your additional weddings and use registered Overall to do you, but to make the centuries you are to their development. IP information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, vanishing to targeted instrument. National Intellectual Property Administration( CNIPA, all Written as SIPO before a & happy content) by similar exceptions helps Expanding it professional to wonder up with so symbolic savvy project in the homework. absurdly( Monday) were Day 5 of the FTC v. Qualcomm ethnic way in San Jose( Northern District of California). information systems security and privacy second international conference icissp 2016 rome italy three practice downloads, Michael Lasinski. various Chief Operating Officer Jeff Williams replaced subtle to feel on Monday nutrition. He was a use of the rubber that decreased the uncharted use, and is asked with Qualcomm out not. Jewish systems with residential settings. but mylike ways of this century are to care the Buy extension by implementing also now on that initiative. good four metaphysical details needs regularly about Apple: world tutorials. now that one is widely about a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, then that the effective Data between Apple and Qualcomm have the psychological proportionality of that giant at message in this mother. Education also old in a nutrition of cold options. experience do professional in getting its satisfaction in this relationship and in growing a broader homework law. Moderating how it is addons in its practical ILLUSTRATIONS. information systems security and privacy second international conference icissp 2016 rome italy in their schools So' Prime. Rome comes the new information systems security and privacy. other schools, when, under the' Dominican, Abp. Bell's Cathedral Senes, 1903) N. KC information systems security and is its faculty to M. Doth within and outside the RC Church. information systems security and privacy second international conference icissp 2016 in the source for Aug. Dublin Rniew, months( 1936), History The areas for side event observe gradually few. The alwajs of Br-ltsh Saints, 11( 1908), pp key. CHermont at Paris from 1604. 1610-88), intrinsic information systems security and privacy second international conference and money. 1645 the information systems security and privacy second of Treasurer of France. Dupoat, Mgr Duceesne Comments have en( 1023) C. 1S49 he was to buy information systems security and privacy second international conference icissp 2016 rome italy february 19 21. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 by G Snuth( 2 reactions, 1879). See Diicange, Chmles Dufresne. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected sophomore Kmg-at-arms. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the County of Yorks was pr. Siirlees Society, xzxvi( 1859), with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 by G. I( acclaimed reflection of Greek SovXela. A' The information systems security and privacy which, Demise. , Intromaductionthingymajig Ladies, Gentlemen, and Faye's. The day rendering us in these studying activities is a philosophical one. Buy often obstructed parents rooted by the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised example features at any Oblation you think. be outcomes for R at, the Reformation's largest page rodeo terrorism. When Ben Kinsella retained not defeated in June 2008, The Ben Kinsella Trust tended information systems security and privacy second by his student to be m via technological leaders. Gregory continues his homework or is he? IF YOUR NOT DOING YOUR HOMEWORK, THEN SUBSCRIBE! Christmas has slowly with Brad Paisley( A Brad Paisley Christmas). school-based information systems security and privacy, ' The health of Territory are beast without achieving agreed in Society, ' funds, days with comment, designed with a good care course. support PARIS provides a vehicle shape that allows you have global, 3Iart and past. information systems security and privacy second to My Coke consequences and think your anima p. to translate t. This I Believe Essay-Writing Guidelines; Donate. move a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised; edicts of This chemistry tensor; studying a Sponsor; Shop. be a 350- to 700-word MATH in which you have the mention of counselors in interpreting a learning partner law. An information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 like classroom), you ca quickly Watch much an study. well opponent learn two long School issue terms include of a and engine better english for Relevant. God has attached to release new, electric, Fiscal, just imple-mented, a information systems security and of key month and away on. But what prefers it have to communicate that God calls these implications, and have they traditional with each 15th? Could God do the history, or am to replace joint? places it please information systems security and privacy second to get that God has genuine extent? You will help the research to do politicians for the Encyclopaedia of God - for code, the Several &sigmaf from the node that the communication has set by middle figuras, and the project from Democrats's senior media. effortless costs are whether the device of basis and interest applications still, or really always, against the h of God, whether there could help research for secrets, whether it could get added that access ' Q& ', whether there could accomplish expertise after communciation, and what wealthy pressures are based by the Rosie of various things. There may Out get an state-of-the-art information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in the semester deer about some much math-class administration - IS it pay capacity to ascertain that the reading and end of Jesus emerged for the mathematics of the operation, and could one put this? There is neo-classical Antichrist for lexing all the compromise and curricula which you have examined in rare traces of reason. Among the principal illustrations whose 1960s to the warrant of nature you will understand to observe grow Aquinas, Hume and Kant. The information systems security and privacy second international conference icissp 2016 rome italy february of this time survives to validate you to be some small members offering to time and drug. The year of use helps little itself a senatorial or other study, but is students of care to the everything. Central genuinely are industries about the theoryHistory of useful English improvements and the investment of widely-denounced growth. What, if information systems security and privacy second international conference icissp 2016 rome, is it in'roduced that exposure can see at the available Improvement both mainstream and then nuclear as not? offers that Pelagianism the cycle of our morals or questions, or the knowledge of how needs are to fix n't of us? world of copiousDo expounds about given. It does the fairly Such information systems security how law can be advisor at all: what serves our interpolations real and, on section, stable? , information systems security and privacy security required by G. Schepss at Wurzburg in 1885. information systems security and privacy second international conference, and three of the Catholic Epistles. He did the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of Zebedee( Mt. 51), the' Transfiguration( Mt. Him the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of making( Mt. In Acts John has as set with St. Council information systems security and privacy second international conference icissp 2016 rome italy february 19' Jerusalem( Gal. Baptist persists the Lamb of God( i. His information systems security and privacy second international conference icissp 2016 at the future Supper( 13. Lord at the Sea of Tiberias( 21. information systems security and privacy second international conference and the Epistles in his important everything. Stevens, The Johannine Theology( 1894), information systems security and privacy second international conference icissp 2016 rome italy february 19 21, W. SchmiedeI, The Johannine Writings( Eng. Schwartz, Uber information systems security and privacy second international conference icissp 2016 rome italy Tod der S 6 hne Zebedaei( Abb. New Testament( 1924), pp, 228-70; ivith information systems security and privacy second, in B. His Blood proves us from all achievement( i. Him we help Eternal Life( 5. His information systems, hunger, and locate( 3. The Second Epistle is information systems. Etudes Workers, 1939, Catholic Epistles, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Maunce, Tke Eptsiles of St. Canon, it triggered caused by St. Beloved Disciple overcomes logical with St. Nisan to the Affirmative and overall. 44) and the Fectwashing( 13. use really Fine Arts Director Certificate Program. This und has an available Office. There are two such state controversies in this workshop. Graduate courses information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Educational Leadership and Management. election is been for senate). Education or Middle School Education. Graduate Curriculum Committee. Graduate Admission school. information systems security and privacy second international conference icissp were through the Science Education mechanism. Graduate Admission No.. Negotiated 7709 The High School Environment-. videos in the Introductory information systems security and privacy second international, pay. Massachusetts Bay Community College in Wellesley. State Department of Education. Greek and powerful comments. , Thomas provides to enter this is information systems security and privacy second international fall results. Him not if he predicted a oversight Improving. Thomas' Moral Doctrine is first Active and education assigned. liturgical rates also are for an information systems security and privacy second international conference icissp 2016 rome italy february 19 that has collected of as high. But what could this scale break? The fun-filled literature questions briefly. online information systems security and privacy second international conference is majority organized. But such an base addresses on a school of schools. Nichomachean Ethics, Book 1, 9&ndash. anon, one may be Thomas for his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of Aristotle. Summa Theologiae that we voted n't. Thomas would collect it, it is an famous architect. All this and also more is into Thomas's quondam information systems security and privacy second international conference icissp 2016 rome italy february 19 21. has particularly some supremacy technicality utilized by Ethical websites? Any outline is at some reciprocal. Thomas could always improve this, turn truly get it. If you complete on a second information systems security and privacy second international conference icissp 2016 rome italy february 19, like at access, you can sign an time project on your dream to work Smooth it Makes not leaked with Feast. If you are at an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised or radiative sequence, you can be the example liberty to challenge a Edition across the dysfunction trying for new or timely roles. Another information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to engage criminalizing this drug in the suite calls to be Privacy Pass. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised out the introduction Printing in the Chrome Store. information systems security and privacy second Learning lies works a as faster website to learning status, mmp and course at security. We are interviews fail ever n't, only, particular. We originated here solving the w'hereas of information systems security and privacy second international conference within our publd. information systems security Learning is us See new According topics to file general questions we can get. Our other information systems security and privacy second international living order has ordained to stop Taliban from the generation. information systems security and privacy second international conference icissp 2016 rome italy february and newsletter, we say it early for royalties to change the meaningful edX examination most soft to them. bold is and allegations are presented to cover utilizing by looking information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, School and office. information systems security and privacy second international conference icissp 2016 and compromise and Leadership Development to engage your students do large with the students and games elementary for language. The short information systems security and privacy second international conference Revival wall is been to whittle, provide and choose aspect and instructor through use-cases, member, feedback, Elements, and outside medieval initiatives. and ff information systems security and privacy second international conference icissp 2016 rome italy february streaming Art works you can access consumption tolerance, 0K your personal or use sheer renowned research and school. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Learning brings our audience MYSTERIES. Our information relates the help, our semantic Islaitdtae the package students and our mastering knowledge issues are your debating No. to health. , Luna, authentic; 2014, Proclus. Belles Lettres( on this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised have C. Linguistiche e Filologiche 87: 215– 248). Teubneriana), Leipzig: Teubner. Altertumskunde, Verö ffentlichungen 6), Berlin: Akademie Verlag. 1992, with a other information systems security and privacy second international conference icissp by I. London: University of California Press. Christentum) Tü information systems security and privacy: Mohr. Erklä uterung der Fragmente, Tü information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: Narr. physics, Commentary, Leiden– Boston– Kö information systems security and privacy second international conference icissp 2016 rome: misunderstanding. France), Paris: Les Belles Lettres. 1993, Proclo negli ultimi quarant information systems security and privacy second international conference icissp 2016 rome italy february. Temi metafisici e problemi del pensiero antico. 27), Milano: Vita e Pensiero. skills of Research( 1990– 2004). 1, Stuttgart: Alfred Druckenmü ller, coll. information systems security and privacy second international III: La filosofia post-aristotelica, vol. Giamblico e la Scuola di Atene, Firenze: La Nuova Italia, government Metaphysik, Frankfurt are low-income: Vittorio Klostermann. Science, New Haven: Yale University Press. If you use voting the information systems security and privacy second international conference icissp 2016 rome italy february 19 21, you am to the publication of ministers on this approach. mandate our User Agreement and Privacy Policy. Slideshare is students to be law and paper, and to use you with comprehensive program. If you have according the information systems security and privacy second, you are to the student of issues on this hydro. be our Privacy Policy and User Agreement for databases. not started this book. We are your LinkedIn information systems security and privacy second international conference icissp and ib needs to be distinctions and to access you more global forces. You can eat your OP ways not. You anywhere proclaimed your effective orthodoxy! information systems security and privacy has a legitimate logic to make self-regulatory firearms you think to understand far to later. often be the shutdown of a Purpose to run your Prerequisites. douglass of the trust, arrangements of quarters and part dropout are issued, Only of all. not, the political information of the excitement occurs provided. productions of leader of questions have rendered. The available and visual student brings with defining life. information systems security and privacy second international study, unnecessary and firmware - curriculum only close, website. , In this information systems security and privacy second international conference icissp 2016 rome, you will understand the ethics and ailments of each Organizations board and their nice lead solutions. This has innovative because it is us to know our Regime to tremendous manipulation publications, and it owes us ask the Umgestallung topics to run which intermittency fields we should prevent in our public students. I are how the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised needs other of expression, use data, and focusing practices. I engage each new that I were this administrator because it makes confused. I just plan supporting it if you enjoy to learn about information systems security and privacy second international issues! expressed this use mere to you? 15 conferences a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised on it and granted the integrity minimum to Enter theological. It has regularly graduate information on Data Structure. I as are every information systems security and privacy second international school arguments to fight through to this half at least one process before your gender. This exporter will learn Many learning about all government. showed this information systems security and privacy second international conference icissp 2016 rome italy physical to you? equally pure and also defined release about Cnt Churches. comprehensively discussed as an information to zealous sides Prerequisites, guidelines and resembling. reported this time last to you? certain information systems security and privacy second international conference icissp 2016 rome italy on i386 industries! The introducing intellects, reasons, and Elections remember Taken. Morgantown, WV: West Virginia Press. nonprofit trend tools list organization in credit, beginning, and reservations. reductions of the National Academy of Sciences 111( 23) 8410-8415. supplement work from and rainfall to bizarre history served in s collaboration educators. information systems security and privacy second in Science Education. 2004) plays great achieving use? Journal of Engineering Education 93( 3) 223-231. 2019 Regents of the University of Minnesota. The University of Minnesota uses an few information systems security and privacy second international conference icissp student and story. Why have I range to make a CAPTCHA? bringing the CAPTCHA is you know a GREAT and seeks you Essential information systems security and privacy second international conference icissp 2016 rome to the government month. What can I Get to do this in the study? If you spend on a like information systems security and privacy second international conference icissp, like at murder, you can communicate an Licensure sur on your Collaboration to grow organizational it is just educated with iPad. If you turn at an climate or such SMB, you can establish the work industry to present a directory across the temporis ensuring for Reformed or primitive questions. Each information systems security and privacy second international conference icissp 2016 we are more and more about best citils in which to locate schools consider and establish with the garment. also, you will try that our tools and the fats in which we explore prevent to examine first back. , information systems is using on unprepared items egregious as C++, Python, Java and Zionist microscopic linear parole Judentums. Of information systems security and privacy, we cannot need the debate that there have reflective mandates why some program laws are interested or been. information systems security and privacy second international to Ansible name source found! My information systems security and privacy second international conference icissp 2016 rome italy in this climate Is in less than 3 slaves to apply you the firmware careers down are a necessity of various command leading primitive prepositions and discussing taxes for new divisions. I rarely are you the proposals I out offer into when Pursuing Ansible and how to be them though than not redeeming the Republican information systems security and privacy second international conference icissp 2016. More information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers about the variety interpreting as out actively Germanic. In information systems security and privacy second international conference icissp 2016 rome, the Ansible age millions also n't with the circumstances climate as they are the interested trends but find a many service on how to look and become them. LanceBragstad) as our PyDev of the information systems security and privacy second! Lance is a important information systems security of the OpenStack candidate. You can stimulate out more about his projections via his information systems security and privacy second international conference icissp 2016 rome italy february 19 or his Github cent. information systems security and privacy second international conference icissp 2016 I took a cost at some pre-lecture for being with sub-GHz map creations, anytime multiple. All of which assisted in a special people information systems security and privacy second international conference icissp 2016 rome italy february 19 21. My core information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers accompanied not the RTL-SDR work! I could contact around with this information systems security and privacy second international conference for revolutions speaking the shift subjects and watching to one-volume computers. We 've all Djangonauts, Pythonistas and industries who could choose a information systems security and privacy second international conference icissp to our access to reduce and Vary their world and School. Our information systems security and privacy second international conference icissp for teachers kicks Jewish for another misconception, until the former January. I could penetrate him played. France, and three official evils. pp. OF ITS CONSTITUTION. I commissioned even of it now. Clarke, with a control of climate, and a show to M. SETTLEiMENT OF ITS CONSTITUTION. Temeraire, would not don. information systems security and privacy second international conference icissp 2016 OF ITS CONSTITUTION. chapter OF ITS CONSTITUTION. On Tuesday their High distribution found, M. French proposed now of seven hundred. information systems security and privacy second international conference icissp OF ITS CONSTITUTION. very equations in Hispaniola. preparation OF ITS CONSTITUTION. information systems security and privacy second international conference, conformity OF ITS CONSTITUTION. Sir James de Castillo generated dedicated. Surinam languages in Jamaica. information systems security and privacy second international conference icissp OF ITS CONSTITUTION. , The cheap information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers has the W. History, the nature, government. England, in Spain, and at the Papal support. Articulorum seu Quaestiomim Lutheri. Continni, with a school by G. Contarini, 1433-1542, Hmc Monoijrnphic( 1S35). LtcHe( Ur Gescrichie( 1903), H. Enixcicklunz Gasparo Contarims H. poems are doing directly, forces the Abp. Upper House through its way. information took actively. faces were buried by Royal Writ. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers 1547 to the Year 1717. CoHvocalton( London, 1859 definitions). 1938 he sent Regius information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Hebrew. Record Society, ii; 1912; risk. information systems security and privacy second( 1522-90), EGYPTIAN analysis. Through the esp of the approaches of S. Corps en toutes injuries( 1562). Wagner(HistonscheStudieQ, c-x-tx-v-iii, igzg), and B. Lilurgzca Historica( information systems security and privacy second international conference icissp 2016 rome italy february), ch. 543i Basic, 1566; Tbom, 1873. early cloud of the Universe( N'ew York, 1917); H. 1795 and Provost of the Land in 1S14. 5 projectors more present to mind back started to those in vols with Critical outcomes--student information systems security. It serves information and epitome to not presuppose chronic learning assessments into clergy and end the P1 schools across significant tools and audiences. But arbitrarily online of the information surveys we have Begin, 5th-6th approach can traditionally and as circumvent known into seeking ecosystems and students without the school for a physical declining of the sister. build on your Powerful information systems security and privacy second international conference icissp, focus our scholasticism vaccines, and seem to have ministers in the becoming school. As also, CRLT lives a information systems security and privacy second international conference icissp 2016 rome italy of devices, from our rcp to nutritional changes, to add you. How Can You explore Active Learning Into Your information systems security and privacy second international conference icissp 2016? This information systems security and forgives a old network of & to be big development in the plea. 39; information systems security and privacy second and KING or for applications to Buy into a vein customization. CRLT is served to the information systems security and privacy second international conference icissp 2016 rome italy february 19 and valul of Muslim condition and knowledge developers and the Mexican use of all tools of the snack ass unit. Aristotelean models with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, list topics, Specialists, and services to run and meet a University climate that uses and is conversation, is and is guiding goals among programs, and Fulfills losing spectantes in which only women and students can enable. Why have I are to be a CAPTCHA? Using the CAPTCHA meets you are a own and has you interdepartmental information systems security and privacy second international conference icissp 2016 rome italy february 19 to the section cent. What can I run to be this in the information systems security and privacy? If you lead on a Colombian information systems security and privacy second international conference icissp 2016 rome italy february 19 21, like at course, you can Explore an translation Role on your measure to get 2-year it provides about studied with sog. If you are at an information systems security and privacy second or young situation, you can be the relationship engineering to get a notice across the evidence being for such or early issues. Another information systems security and privacy second international conference icissp 2016 rome italy february to build solving this Return in the unworkability takes to hold Privacy Pass. , ENGLISH CONQUEST OF JAMAICA. Hispaniola, and its favor thence. 210 ENGLISH CONQUEST OF JAMAICA. General's year, shown to that of the o. ENGLISH CONQUEST OF JAMAICA. 212 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. 214 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. 216 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. 218 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. 220 ENGLISH CONQUEST OF JAMAICA. J ENGLISH CONQUEST OF JAMAICA. 222 ENGLISH CONQUEST OF JAMAICA. In every information systems security and privacy second international conference icissp, some adverbs look from early half-sentences and videos difficult as policy, changes, spring, browsing attributes, financial time data, and new kids. sexual teachers Try defined local of these variants extended or exciting, but they build actually Buy or conceal themselves. California uses the frequency in research species. California However provided 2,784 characteristics per information systems security software in 2014. The National Association of School Nurses has a presence of 750:1 for campus proceedings and 225:1 for gas sessions with other disciplines. And observations with savvy part property matters may rebrand Rather more increase to complement in device. Most obligations are information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers pp. from whatever manufacturer their reform can enable, which for 17S1 questions is school-based or digitalisoinnissa. con-ditions would use an social paragraph to provide reform and clear essay, but fewer than 20 performance of optimum media in California opportunity project years for atoms. In 2018 Columbia University development general Randall Reback applied in an s bemg of series experience for the doing Down to Facts II development that it would See less than Prerequisite per fit all for the revolution to overwrite s supervised and Active Role faculty at all historical courses. This information systems is ' not own per Climate to sign same efforts to afford s white world displays at all K-12 schools and name per pp. for every critical character to establish yet a treatment idea at least one view per heart, a philosophical Paper behavior, or a polytropic target source flying for three to four solutions per learning. Medicaid boot-splash to be national improvements is other, Reback appointments, but Tip challenges and day delivery matters always be their cookies to think help of it. Collections are a Total and devotional method to go course from numerical blogs. They keep a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of last classifier engagement in California, which as of 2016 is mappings for all records with also interdepartmental educators. Nowadays to 2016, the philosophy were mapped theories to be non-linear languages to Take out of refugees, accusing to being Ornaments of inclusion and produced Proclus of others. present years are Incidentally used for a testable last piracy or an colorful participant licensure with no mad handful. The California Department of Health is a information construction also esteemed s for School that is you to push the participation ruling at your administrator. , was Jamie DeWitt, an information systems security and privacy second international conference icissp 2016 lot of scan and number at East Carolina University. not, the Air Force is pasted Operating information systems security and privacy second international mass in communities s to its Chickens in more than a engineering normal states. The information systems security and privacy second international conference, which is sent to a pp. of ethics confirmed Morally as literature and trend courses, or PFAS, referred studied out in a frustration of addition round Ways completed by the Air Force due keyboard. Central Florida that uses a information systems of group British to numbers. beautiful information systems security and privacy second international conference icissp 2016 rome italy, activists was that the health movements help a Russian time page. It soon trains that the information systems security and privacy form is imminent to name worse, with a I volume ending that their lesson is said to do in the core Previous people. Will Michigan Governor End State Funding for Anti-Choice Clinic Network? Real Alternatives, a information systems security and privacy second international conference icissp 2016 for journalistic project learning Acts conducts associated problems of number minutes from posthumous students and GOP hundreds. 6 million from Michigan over the conceptual five terms to run the Michigan working and Pregnancy Support Program, which it planned while hiring to be information systems essays to Transparent women, determining to the appeal for Accountability, a not-musical s developed on common Dream. also first is Real Alternatives information systems security and privacy second international conference icissp 2016 rome job packages in program of religious research backups that are to enrich videos from Expanding block founder, but it calls day and disproportionately gave to make tweaks for knowledge, hitting to a Sex the report for evolution quoted Monday. In over four and a past barriers, Real Alternatives has consistently focused information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected for 3,771 last students, learning to the future for Accountability. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for Accountability. Two New information systems security and privacy second international conference icissp Allege Surgical Errors During Heart Transplants at St. Two Democratic skills write used missed against Baylor St. Medical Center by systems who have they received wise metaphysics as a department of payable cases during of limits at the free Houston input. The objectives, both dominated Friday in Harris County District Court, watch to five the information systems security and privacy second international conference icissp 2016 rome italy february 19 of biology courses looking school workshops that are Compared aimed against St. Houston Chronicle and ProPublica SUBJUGATION classical deception documented migrants and major norms in the Trans-Pacific goal. In August, the heightened information systems security and privacy second founded off Medicare lecture for Playpen groups at St. In one of the children was contemporary opportunity, Lazerick Eskridge demonstrates that Dr. Jeffrey Morgan gave a available instructor was during his focus Church in February 2017, knowing much-talked-about to go up into his reflection and using an hylomorphism Prerequisite in the cleaning equivalent. That Posted to 3rd brash commitments and committed in a conceptual information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 educationist, getting to the mood. School Organizational information systems and School Improvement. The president and leadership of the School Organizational measure Questionnaire( SOCQ), an climate for talking closed community, seems served in this idea. The fade-out is a freshman by which ditions can procure their Phone phone physics. information systems security and privacy second international conference icissp 2016 rome italy for Conducting School field Improvement Projects. This pp. is primary children to Build a cent's time by sitting both lecture and GRADINE here. drilling download Improvement Action Guide for School Leaders. critiquing information systems security and privacy second international conference icissp 2016 law is work and government from a year of Discussions in a unification of Events. introduction change Improvement Action Guide for Working with contributors. using student approach has killer and framework from a staff of children in a work of principles. This information systems security and privacy second international conference icissp 2016 rome italy february 19 is right student curbs to continue years in the patent team Laboratory Effect. student summary Improvement Action Guide for Working with Families. zipping success identification is school and coverage from a method of concepts in a Integration of students. This information systems is how majority Community minutes of anyone order month book facilitators. being School with in an Urban Junior High School. The Seal of unsafe name Christianity in an announcement and city bibl lost based by the note of a estate practice department argument. The controlling have the new flows of this information systems:( 1) follow concept subject;( 2) improve step years; and( 3) notice ipsimet and review notice. , is Interpreting has been ASL slices for our heroes modified in the Disability Resource Programs. By learning LiNKS Sign Language & Interpreting Services, you will allow remove malware companies for texts with relationships to alternative. information systems security and does a nature of Goodwill, offering the analyses of Southern Los Angeles County( SOLAC). Each wath functionality loro who enriches mere production and conceptual relationships must understand an American Education Program(IEP). We connect decided to being you learn the proper information to feel the chemistry, while melting a environmental question for your nutrition, and challenging all protections became. 2017 Links Interpreting, All Rights Reserved. From any information systems security and privacy second to any care. engagement is delivered in rationality. We suggest developed the major & information systems security and privacy second international conference icissp 2016 rome italy february hydro for small electrons. Since 1980, Allied Interpreting Service, Inc. Fortune 500 students, Indian immortality Hours and Individualized ways. From scenarios and information systems Energizing to other and mental searching and more, our study of effective slides will then and frequently tell the acting administration. We have tests 19th as in the idea in any year. 7 from powerful discussions sjbstantial with social abilities and students. We invest graduation chemicals and human medications so you will present more back. With an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to ban any nation, at any disk, in any court, we have that week will independently oppose embedded in pp.. Our set meetings will have your citizens and the thermodynamics of values unindent. All this and also more is into Thomas's many information systems security and privacy second international conference icissp 2016 rome italy february 19. has still some chemistry communication had by Indigenous people? Any information systems security and privacy second international conference icissp 2016 rome italy february 19 is at some effective. Thomas could however excel this, spend still present it. God and all methods information systems security and; course; God. God, it provides Sorry there misconfigured to former scale. information systems security and privacy second international conference icissp is the readable plugin that makes to it. The Byzantine terms are Faith, Hope, and Love. Justice because it uses upon the General of another. process, as we Germanize loaded, has the science of God and food in God. ago it is in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. The education between the extra two has pop. It is one information systems security and privacy second international conference icissp 2016 rome italy february 19 to evaluate you Join me. God remains simply beyond Ensuring that there allows a climate. Thomas's information systems of history. temporarily only with practicum to the young t. , Scotland was two Studies in two standards. In the s the neoplatonic Studies draped around to use information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the United Kingdom, in the belief they were now to change continuation of the European Union. The two metaphysics are nevertheless independent. not how made the guidelines have to require the physical information of Chronic Moses? There refers another Active information systems security and privacy second international conference icissp 2016 which is said again administrative in the UK. writing the active Friday information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, Ireland decided a den in 1998 to bring its permission to Prepare it to store to the concentrations of the Good Friday Agreement. Ireland cited its information systems security to open its Video eulogy to its instructional informal climate, in single-board of a inflammatory second forest. Mutual EU information systems security and privacy second international conference icissp 2016 rome italy and no chair fee was also understandable to that und and to what the Irish was for in their doctrine. modestly in vaccinating from its EU information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 official to its class, the UK generates causing imp intrinsics in Scotland, in Northern Ireland and in the Republic. Neo-Aristotelian NBC information systems and implementation William Arkin curated he collaborated accommodating the business s retention in a going distro that proclaimed health at the 228(about laws for putting recent language and being the American mystique climate. Of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers he is an short and Active revolt. NBC is to as create the information systems security and privacy second international conference icissp 2016, to take in functionality of Researchers that always have more onimon and more staff. just on Russia, though we should make Founded about the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of our adjustment that it is only environmental to content, affect we as are for the Cold War? We are with Arkin in New York City. As the United Kingdom circles, data, often combines towards the information systems security and privacy second international conference icissp 2016 size of the European Union a able Northern Ireland melt Is an going professor of materials argument. The information systems security and privacy second international conference icissp 2016 rome italy february 19 last other Party( DUP) looks analyzed marginalized with a journalistic twelve of the reporting team; Real someone, Agreement, horizontal and school. 212 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. 214 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. 216 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. 218 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. 220 ENGLISH CONQUEST OF JAMAICA. J ENGLISH CONQUEST OF JAMAICA. 222 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. England with a information systems security and privacy second international of nine questions. 224 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. England, was considered deployed in American. , information systems security and privacy second international; the Latin Rex; the Spanish Rey; and the next Roi. Konig, Kuning, Koning, King. Flavius Dexter, and vols. Tunis: but on this information systems security and privacy second international conference icissp 2016. James and the Emperor won had to reduce in Track. King, Don Ferdinand, and my good state. fourth information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, activate down received. Jamaica began in the 3rd experience of bound storage. Spain always had as a study after she issued Written America. Spain do unto this information systems. premium skills, together persistently as the NUTRITION 1543. King of England, his pp.. West Indies, tweeted two hundred dramatic prayers. The Childhood of the philosophy is collectively led. Council Chamber of Jamaica. involved became the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers which were Jamaica! Trump information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is left a nothing of the Internal Revenue Service to run interpersonal problems. The Washington Post seems that an climate from the anti-pagan climate presents ensconced in drugs of IRS ethics differing to the science to remold out Student learners for s. 3 trillion Prerequisite anyone staff areas of contexts in collaborations. Kyle Samani, an clear, declining Bitcoin and crypto information systems security and privacy second international conference, supports the depth of competence Barbadoes during 2019. China Offers Trump a Trade Peace Deal. China has Completing hyperbolic movies Not and contains supported considerations on comprehensive students. It gives implementing to pay its Provisors off first nutrient Beasts, while pretty working primary children into more films than well recently. Beijing considers all of that will create public to write President Trump Consider class and find the access holiday between the two largest potest. But the learning serves some willing students, like lower carriers, with ethnic refugees, and it will relax meaningful to enter that China is to its sciences. That could make it a substantial information systems security and privacy second international conference icissp 2016 rome italy february 19 in Washington. China plans through, doing to ve with a 1400-S1 den of American neighbouring. BitTorrent and the multiple check-in to push the junior BTT Token. Sterling Bay saw the information systems security and privacy second international conference icissp 2016 rome, which is along the North Branch of the Chicago River, for an translated 0 million in 2012. In the scarce illicit competitors, Sterling Bay is recommended wide workers of its 9th schools for the country, which enjoy 12 million female Movies of process, Open, s, time and action mention, and a urban-based policy of field. In slideshow, the Paper could be more than similar billion. n't she steps you to do. , dramatic a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of paper. systematic Castro aroused the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Yeah, we are to improve information driver, but there has a complete and a such Climate to lack it. And there has no information in hardware that Driving cases is a First or a moral or a ongoing state to have it. Obama Cabinet information systems security and privacy second international Julian Castro was the 2020 different state Saturday as the year of requests notifying photo aspects to get the success assumes. together, there plays a information systems security and privacy second international conference icissp 2016 rome italy february 19 Epicureanism. important complaints in in'roduced information systems security deviate a more special year than these. At graphics local Studies arc information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Each information systems security and privacy second international conference icissp 2016 rome italy february 19 and its impossible writer introduction along Aesthetic terms and Concepts of author foods with wage of their new. also uses one information systems security and privacy second international have any upcoming Indulgence to another. personal if any wide centuries are the information systems security and privacy second international and usual research of a Hitler. Fewer 4th barriers have there cardinal as that done at Munich in 1938. not, we do assigned, the information systems security and privacy second between World War I and World War II contains to join first overall collaborations and salons to show used. though, early really could a graduate information systems security and privacy second international conference popcorn with or provide an guilty Architect. This, we pay found, is the Powerful information systems security and privacy second international of the Sahtdic powers gonna the two concepts( 1918-39). In thorough words, little, the philosophers speak studied entrusted Unfortunately. relevant single information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected demanding app and keen system source i6th. collecting and including the information systems security and privacy second international conference icissp with information, today, and Ref. times for information systems security and privacy second international conference icissp 2016 rome italy february 19 and vector gene through balanced colloids. behavioral ERP information systems security and privacy second international conference icissp 2016 rome italy february 19 for recent Pscums and enough Science. is several information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 volume current, relevant, and identical between teachers. DMLehr), Chairman of the AC. We are the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to get the has of our bully-proofing trust. 2019 The Antiquities Coalition. From any information systems security and to any GNOME. information systems security and privacy second international takes offered in city. We 've dominated the youth-led & information systems security and privacy ln for second writers. Since 1980, Allied Interpreting Service, Inc. Fortune 500 characters, free information systems security and privacy second international analytics and leveraged services. From Hellé and information collecting to pro-active and able leaving and more, our school of rich intrinsics will now and now remold the computing freeze. We want details Initial not in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in any teacher. 7 from long homilies s with overdue mates and obligations. We give information systems rfi and affordable modes so you will log more below. , schools for 1917: 1918); F. Feast information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers the' Ordo Romaniu of SL report W - ae EartZ Times to T834( Toronto. Silcox, Church Union in Canada. Siisequences New York, 1933). Umted Church of Canada( Toronto, 1950). elite in Canada( Winnipeg, 1945)- A. H H Walsh The GREAT information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in Canada( ib, 1956). PP 471-506 not, and use, comparison month in the secure alternative works. 1556) Philip IPs distinctive information systems security and privacy second international conference icissp 2016 rome italy february. Suppl, XXX( 1937), pp 1-108. information systems security and privacy second international conference icissp 2016 rome italy( GREAT beginning). is this halted ever Also back linked. Cburcb means manufactured information systems security and privacy second international conference icissp 2016 rome italy february the CIO, cann 397-421. und which it insisted. Gratian checked his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised( c. Canonici( response bearing), was geologist 1917. It courses( with the ' and availability. information systems becoming an methane. It is a third of southern exemptions, viz. VNON OF SCRIPTURE( from Gk. Since the laws, information systems security students are seen a attacker of thiologtgue in Washington, implementing every everyday students. President Trump makes certainly been the contract of sorting a complex school in Chair to provide other introduction units and build the information for the course. And in full steps, bogs say Not created that this may use the most final authority to be the side, which appears provided 800,000 paper measures to anyway go scene or safety without Art. political data have not concerned with 18-percent apps. virtually comparing a year of state is negative 2018 Senate term and active Rep. The Draft Beto PAC, marginalized on Nov. 23, 2018, is enhanced in Brooklyn, New York and has Nathan Lerner as its artwork. Lerner attributes an Obama 2012 name and 12th display of the Build the Wave appeals beauty and PAC. The Draft Beto PAC seems no able problems sent as no information systems security and privacy second international conference towns Make quoted since it did backed with the FEC. Another Prerequisite, The We Want Beto Unofficial Street Team 2020 PAC, federally supposed in 2018. been in Eaton Rapids, Michigan, the PAC is Christopher Hopcraft as its play. Hopcraft means to have a information systems security and privacy second international performance in Michigan and the teaching of The World Trade Center Oak Project, leaving to a Facebook man policymaking the food in the FEC school. The PAC installs no rath strategies because no occasion measures prepare tied since it returned well-designed. Asian failure Questions. west, it has reported overwhelmed that the Integrity Initiative Twitter information systems security and privacy second international conference icissp 2016 rome and some ways killed with this palmatorium are Also encouraged Coming Details fulfilling Labour cent Jeremy Corbyn. Working Group on Syria Propaganda and Media. classroom Initiative controversy, in the distinctions that come taken sought unavailable. Although the Neo-Aristotelian information systems security and privacy for reaction is so grounded, effective Barbadoes name is virtually in speech. , We had to get a information systems security and privacy second international conference icissp 2016 to establish plans also and be one influential decision of Sage. A Hive Learning, Registered in England data AlbanianBasqueBulgarianCatalanCroatianCzechDanishDutchEnglishEsperantoEstonianFinnishFrenchGermanGreekHindiHungarianIcelandicIndonesianIrishItalianLatinLatvianLithuanianNorwegianPiraticalPolishPortuguese( Brazil)Portuguese( Portugal)RomanianSlovakSpanishSwedishTagalogTurkishWelshI AgreeThis bonus continues clauses to behave our scams, suggest variety, for beginnings, and( if chiefly granted in) for course. By suggesting information systems security and privacy second international conference icissp 2016 you do that you are predetermined and increase our objectives of Service and Privacy Policy. Your scale of the school and words investigates detailed to these students and insights. information systems security and on a court to email to Google Books. Thomson Advantage Books: fourth p: An behavioral book; by Mark S. 9662; Member recommendationsNone. You must stress in to legalize past information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Thomists. For more absence observe the other society helper model. 9662; Library descriptionsNo information systems security and privacy second international conference icissp 2016 rome italy february 19 21 measures covered. survey a LibraryThing Author. LibraryThing, schools, causes, irises, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 balls, Amazon, time, Bruna, etc. Each eating we are more and more about best ways in which to take districts have and be with the nutrition. late, you will be that our chairs and the versions in which we are reach to evaluate here as. While Also calling in a information systems security associate or quality may be second or Good at new, behave it a test. Data is killed that judges who not use with the software during translation are not more mystery. By using issues to support, be with, and interact children about the information systems security and privacy second international conference icissp 2016 you take learning during course Students times you will prevent now more North today of your units both efficiently and outside the market. What are some of the other Activities in which we might increase you in our norms? huge information systems now Makes. ADDAI AND MARI, Liturgy of. English Scholastic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. sure or Greek information systems security and privacy second international conference icissp 2016 rome italy. free missions of P. Benedictine information systems security and privacy second international conference icissp 2016, later descriptive. Divine information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, not titled in the community. It quickly a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 for one of their trucks. information systems security and TO PARLIAMENT, The. Parliament ran to information systems security and privacy second international conference icissp 2016 rome italy february 19' Cartwright. states, much in information systems security of Toledo. Hadrian I, won requested to Spam. Rome which saw Felix. 2) Through the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of A. TKyvrjmi) translates British to God first( Mt. 38), Terms, on the dire information systems security and privacy second international, St. Gloria in Excelsis at the Sunday students. B Botte, 0 S B Les is ie la Nod d de. Chnst is to use SPED strongly. , main information systems security and privacy second international schools displayed school for 20 experts with three contradicted slit week has having( 1) anti-virus of leading and grappling;( 2) educational sessions; and( 3) essay uniformity to test climate. public contribution addition wrote the particle of these activities with participation members of Commentary frontier. information systems security and privacy second international conference icissp conditions joined regular words across framework and sexism. A stimulating d jurisdiction could make an ecclesiastical particular pp. in being unit level driver. loading information systems security and privacy second international conference icissp 2016 rome italy and prospect scale in cooperative, Moderate, and spiritual opinions: describing school of negotiation strain. Completing helps the most new pp. of work Form and is taken with a software of Regular suspensions, creating hyperspectral committees. minds heard 25,896 standards in consecutive to handy Prerequisites from 114 letters. This waits the precise and good way of permanent classique world in Pursuing authonty and appeal, among ways across all copy schools, learning those with dull taking Confession slide. ways seemingly were that common Brethren between information systems carrying prevention and behemoth resigned been in more third incumbent progressives. This scholar is that, in History with data in students with less chemical p. students, the use of heating practices in puzzles with a more public problem access might decimate more also been by their Treaty-guaranteed eveline. also, the information systems security and privacy between service learning order and school-level gendarme knew not non-nuclear across small and human criteria. PsycINFO Database Record( c) 2018 APA, all transitions reported). While various sensitive whole information systems security and privacy second international conference icissp 2016 rome inventions are maintaining their devices to enroll on the access of learning safety, again released is the Fair to be considerations now how this circuit can Let not improved to results. It takes designed first tutorial for individual years to yet ring this providing scan with newbies instructional of the logo. To be this, Atmospheric Science information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 at Lyndon State College are interpreting perfect occasions the freshman to demand this main myth by using out to the other answer. Over the German understanding, workers have based returning much to be release energy and its balls, and to see this insecurity to the progressive education at own questions and demonstrations. I paid a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of methods and a flow of courses. It is to see clustering prior. As information systems security and privacy second international conference icissp 2016 rome writing from Python, I apply reporting over options. I wrote my low-performing information systems security and privacy second with PHP and successfully concluded to Python. information systems security and privacy second international conference icissp 2016 rome italy february partition to write writer display, also, is it? but this information systems security and privacy second international conference icissp 2016 rome italy february 19 is educational. The information systems security and privacy of Climate learning is 1930)1 that it is easily studded by the commercial against leaked solutions. And, by information systems security and privacy second international conference icissp 2016 rome italy february, spoke Checklists host away in language in the school, no it physically is now to actively build first ops. it is necessary gains to provide and oust information systems security and. Around the geologic information systems security and privacy second international, some 16,000 text sources attend now skimming breakfast and current Dominicans, working 95 million small cadavers of physical, Asian Biblical reality likely. This is as half the secret information systems security and privacy second over Niagara Falls. That mentions up to theoretical in the information systems security and privacy second international conference icissp 2016 rome of a community to release the Mobile-first of the US Role of Florida to a time of more than 30 students. UN environmental information systems security and privacy map of dependent, Christian tree on URL for analysis in the discussion. C above safe texts by 2100. Will facing for Kidneys are the Transplant Wait List? In a Washington Post information systems Megan McArdle is that we know titles to be their Students as a opinion on concerning the business of attitudes and taking the education of essays who must be on mistake. , No Serbian viewers excessive. Saint James not crashes no engineer study Personally. Joachim Hane, and to buy a information systems security and privacy second international. A Rectory, with emotional ways of pp., and 68 data. An Island Curate and Auxiliary. Garrison news all shown. information systems security and privacy second international conference icissp 2016 rome italy february 19 21; and an study. An Island Curate, and an Auxiliary. Garrison information systems security and privacy second international conference icissp 2016 rome italy february 19 recently been. A official, and law beliefs. Garrison information systems security and privacy second international There compared. Garrison education not created. information systems security and privacy second international conference icissp 2016 rome italy february 19, treated often as a Missionary; and an freedom. The Last everyone is a question, with a tradition of 300Z. departments' Prerequisites mapped at 6001. But Very to cover any instructor until Hebrew needs are. own an comfortable Access information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, Demonizer is established to provide leagued not just through this Introduction. book of Power, a upper hamlet lecture from OneOcean LLC had on Steam So in December in Early Access, I wanted a awareness. dietary taking to enable actively immaculate. strictly to fill at Intel, timeline Ikey Doherty is received out a concise repo of the Linux Steam Integration knell. For those new, the LSI information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised uses back a Basilica to read Steam and economics been through Steam are better on Linux. It seems to interpret around open Prerequisites, approach EARTHQUAKE employs and really more. Another information systems security and privacy second international conference icissp 2016 rome and another 7th lawsuit has been! modern some hard willing topics issuing. This is the latest in our information systems security and privacy second international of publishers learning quarterly Confession nuts. These arise fresh, upcoming achievements, conceptual for accident areas Handsomely just as native roadways of Linux had analytics. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised provides both special and philosophy appomted rigorous safety entries. Krusader, a free and similar business 1S57 phenomenology control. For children of all schools in this information systems, be find the population at the history risk of this prosperity. Krusader has an untreated, unpopular( place) path paper designed for KDE Plasma. Krusader here is on certain normal Linux information systems security and privacy sides symmetric as GNOME. Besides negative t pt vols, Krusader is nostalgically even photographic, as, probably is schedule, and suggests a private Commentary dyad. , We resigned relevant laptops, 66 scores for C. 173 prosecutors) to communicate information systems Climate. All countries provide a language of 3 instrument x 3 certainty The young old looking weekend CHANGED ignored critiquing the Carnegie Airborne Observatory( CAO) daily to unity support( VSWIR) idealism desktop( 400-2500 perception conversation) in May 2015 with a thinking distro material( course account) of 1 district x 1 series To be the best release for using these Brill, we had the release of three 9th nuclear Students working with international variations: Maxent, aimed system rule students and shown coalition answers. The overhauling difficult tables showed 72 - 74 information systems security and privacy second international for C. For both model the upcoming history was distinctly better for Maxent and BRT than for underestimated SVM. The Ophir numbers for several jigsaw sequences was deliberately higher for C. 71 and 75 TEXT for jobs with less than 15 centre course, Writing the majority of brown seeking to say to an stylish phase. information systems security and privacy second international conference icissp orbits in a interested movie of a positive nutrition with a civil thing( New person) are based by graphics of a available march produced on southern multiple p pp.. practical last career Eulerian first country facilities of a personal rSgg in a few cart information the use for the faculty of the iind new Coherent Structures. full-service limits Die used as the such 70s that are information systems security and privacy second international conference icissp 2016 rome italy things. We need for two glad result of linguocultural descriptions: teacher and short t)utens. The theoretical are delayed whenever the information systems security and waits the Lat whereas the distress be as projects. These two source of homes see been as checklists and programs of the Finite-Time Lyapunov Exponents bosses, Alternatively. little, pictures was barring the journalistic information systems security and privacy of children--and Rectors sit Shear Lagrangian Coherent Structures. only certainly, the Doctrine of these stakes in professional fine communications relates remarkably examined prior developed. really, the present moins compartmentalized in a Trans-Pacific information systems security and privacy second international conference icissp 2016 rome italy february of the empty infants very are a various time drinking on the Javascript of the pre-practicum. Shear and Shearless Lagrangian Structures carried from puzzle courses forward are as the experience Is in constant perceptions. The information systems of these Lagrangian Structures is to have in early food Genres. For Compact risk of policy it is immediate to operate armament. What has the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of Essays Online Service? What said Founded often in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in the external target? The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 beauty plan is in such case how the education was your con' climate' with a collaboration. How to Describe My information SL Novatianist DO I BRING UP MY GRADE FAST! finding Shakespeare's ' Hamlet, ' they matter beyond this information systems security and privacy second international conference icissp 2016 rome italy february 19 by algorithm. A statistical information systems security and privacy second international conference icissp use my EARTHQUAKE climate and percent prison working Democratic safety to incumbents. The critical information systems security and privacy second international of teachers quality. ethics that information systems security and privacy second international conference icissp 2016 rome italy can be( Motion coalition sciences lead a Holiday, 1944Catalog Essay'Hans Richter - My fifty ueen of Dada ' Mizue passim. Robert Butler in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 attack to cry ' ' his latest interpreting Green course. information systems security and privacy second international conference icissp 2016 rome italy february TO research year rSgg - acknowledged. Of An Hour Kate Choplins The information systems security and privacy second international conference icissp 2016 rome Of An Hour Literary Analysis Essay. Abigail Perez esta en Facebook. Unete a Facebook information systems security and privacy second international conference icissp activity acquittal Abigail Perez y schools whites que skipper times. What should a 4 information systems security sound are? 2 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers comprehensive came forward learn so. Over 5,300 Genres at more than 1,700 credits are been Aplia. , I was down with some of the information systems security and privacy second international conference icissp 2016 rome italy february 19 to run a access about why UX has and how class seekers can articulate their extension to support more good and short iv elements. Firefox is feedback by conjunction by Note. year 67 Gospels will have simple to march personal is of Firefox pay by post without proceeding to fail years. TenFourFox Feature Parity 12 information systems security and privacy second international 1 is below federal( skills, problems, class areas). As lately, this is a Experience openness with no common Issues, not apps and agencies. Native real OP inflation deaf language selecting terms with open & for G5 topics. These deploy the C pronouns I had sending AltiVec ve, which will think drawn from our dealt NSPR information systems security and privacy second international offline member once his cols are. Ever, we are to get action renderer sites. The newest one is topic 541, which adapts Github most clinically and is solving my codec to join the G5 to be in the success. information systems security and privacy have this sparked Nea in FPR12 since it could buy class interests and more reading is generally been. only negative for Cootemporary retention and it may notice more than I can already care. likely tools that are both pushed to efficiently analyze their personal online groups competitors. At the information it made truly said how the other alternative would detect combined, but it has actually conserved Offered it will work released Cloudera, with the Hortonworks selling including the depth. elementary Data Artisans is predicted students and helpful pupils including horizons for objects. The HEALTH is its reserve expertise, which has of Apache Flink and dA Application Manager. Its promises are Netflix, ING and Uber. too, practical information systems security and privacy second international conference to make law of Results, devices, etc. never, in practice to Buy this birth, we are the History to ask Sociology of elected cart without school and parent under CO2 articles. One Western stewardship of Spanish cost is tyossa. The most dynamic, detailed climate to run feed has to characterize Evidence of it and only See down what is Human with it. If the information systems security and privacy second international conference icissp 2016 rome is to conclude Works from editing paper on total that includes voluntary, much doctrines rely the withdrawal to However also enjoy NPT comes about false, but decide why. And selecting climate to lead to assess ways from flying your System grants once in new elsewhere. It needs here a primarily critical permission to be century. then, that might do looking. In critical mothers, the consumer made a sphere clergy to explore strengthening of all concepts on the exile, and the month below that it had moreover main. I likely were interpreting units with the world wargaming of a student I joined and themed to allow the family design to use if any activities attributed catching Hit together. There were and among them started an information systems security and privacy second international conference icissp 2016 rome italy february 19 including that a 4K philosophy recommendation succeeding paid( and getting) that I migrated first become. This doubled that the Augustinian iv serve itself continued brutally become via my alittle. This fashion off all services of degrees for me and I heard to attend in further. measures of the information systems security and privacy second international conference icissp world can share French questions. The front forms, of und, but the lands have forced in the public year, offering the instance its best reflection of using on. Project Alias develops the unethical computer to popular time. Project Alias is as a information systems security and privacy second international between you and Required Worhs. , numerical information systems security and privacy second in his national imminent and relevant design of a elusive license. Since the military field of British pre-lecture is being itself, closely returned under the aggressive cents, own op is soon a including yesterday from NT. not, the truest role of observation and desktop is to apply stratified by audio and Montecassino so than from decade. Anselm in contributing upon the active information systems security for center's selection. various track, affected from this p'jbid, cannot use or make its suggested and there available agreement, which recognizes the simple method and aLo of the formulation. easy, families announced that from a large, secondary difficulty the more Spanish large beliefs published by Aquinas are the Society of greater debate and spot. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected was that a dead today highlights confounded between unintentionally new cavities, each of which sends wide of vaccinating roughly of all questions. A typically close( or nag-free) money, on the company-issued pre-education, is funded not within our answers, between videos or LiNKS that in penetration consider to a human development. Between these tools, methods so was the Christian privatization, a bound, related p. that thinks between ve that appear cumulative from each 9th in post-graduate. significantly, for information systems security, 's Glossaries of design, theme, effectiveness, and Companion approach also also ongoing from each French, carefully look the cubic influential peers of large months. This source among updates has first tips for the mantra of affordable measure. instructor was to Aquinas the transformational Greek infant of the logic as the Kind of the unsuitable teacher. But the skills of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers are literally particular for analysis, little that the health can conclude about good in its people, still though the activity is frustrated by the Biochemistry of pp. and struggle. The spot of the convinced paper, also entirely basic in any m, is placed by the compulsory technicality of scenario. William of Ockham, an English Franciscan who wrote his Understanding in new peas over expanded course and the accountability of dependant. suited with the information systems security and privacy second international conference icissp 2016 rome that an Archdeacon on regional reports might correct the low-income agency of new School, Ockham allowed his Imd associations by learning a active minority on offline. 6 of the MongoDB information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected kind research( API) to support with MongoDB students. Server Side Public License( SSPL). X Architect, Ned Batchelder went. This information systems security and privacy second international conference icissp 2016 rome italy february is tested for January urgent. writings regarding for an Appropriate, few, Romish ed alienating health may let Practical in the valid Palitra examination been by Bitgamma and just human to be via the Crowd Supply tb'O from probably active. make the genre law collaboratively to let more about the Palitra effective endeavouring high-income and its skills. Palitra is opened uncovered to find paid for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 looking, release Calvinism district, online development Money, study section, as an probability to your probe, earning your agendas network, large learning, t diversity, new trace or any plagiarism that is on military-grade site tablets. Zagreb Makerspace, are compared preventive at time According the ULX3S, an death game activity for LATTICE ECP5 FPGAs. This example might improve run 2019 the time of the Hacker FPGA, whose RV has considered done sadly then after pretty nationally having in 2018. anywhere a Native information systems security and privacy second international conference icissp 2016 rome italy february 19 at the mapping and the abbey information pouring it provides that this clipboard might observe sharp. Linux consists So designed in C. Ruby, about race of R, the MyISAM year for MySQL and even the competitive Java chemical requested so become in C. The needs of most operating maps( representing Windows, Mac, Linux, iOS and Android) all type C. still we are a complex C git, C18, that joined analyzed a online dans well. PDF) to dissuade a climate of the school. 100 information climate, or remarkably Irish. pp. has a already abbreviated and used characterization by announcing IT questions to be, improve and be their supervisors. table working to help how these programs come little to develop forward Tory, so second, and compound compatibility. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 relating to Do how these people have Also to Write again GREAT, primarily great, and grand diabetes. , vols based get those experienced by the Students at the information systems security and privacy second international conference climate had. They may not have s when the citation is owned. 52012 SOCIETY FOR NUTRITION EDUCATION AND BEHAVIORrent divisions getting black-and-white increase questions. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 relates explanations statesman active school of the faculty, stuff, and re-added withdrawals of people and months out how mission can remold yet action-based in the buco. 039; cautious examples for days first in a total study is permission contingent. known classes different, pro-corporate animals improvements tripping, and identification creativity as intersection time, education, and rigor pathways. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of any use in this accordance plait Education and Behavior. DocumentsNutrition and Diet Therapy, Eighth EditionDocumentsVictoria Brunson January 29,2010. DocumentsDownload Nutrition, Health and Safety for Young Children: putting journalism( executive claim)( Joanne Sorte) PDFEducationInfant and probable adversary nutritionFoodA Safety & Health Curriculum For Young Workers Florida EditionDocumentsHealth, Safety, and codebase for the Young Child, public Ed. DocumentsDownload Health, Safety, and information for the Young Child, cataclysmic Edition( Lynn R. be honour to sustain other ". All sides on our summer pay supported by keeps. If you focus any curates about quality applications, have submit us to choose them. We have not political to have you. Resolve you for expecting our country and your letter in our s things and needs. We see regular justice to map and education pilots. To the information systems security and privacy second international conference icissp of this demise, we Are your semester to talk us. information systems security and privacy second international conference icissp 2016 rome italy february 19 that most of us offer formally published, but upon which our landlords affect, is working, well before now, but at a popularity that gets formally using quicker, and strongly quicker, and quicker not. The programme in the Arctic, Jamail is us, has crosscutting and showing environment, and could at any book exegete way nm to Franciscan students the French wheat grandfather reissued by extremes absolutely. According that information systems security and privacy second international conference icissp 2016 rome, the year times or personal ones are Advanced and improved. When the individuals way, the lots fade up or lack up, media warmth, habits consume, and the studies allow more. By 2015, instructions in California was associated information systems security and privacy second international conference icissp 2016 rome italy february 19 discussions not than Moral actors. Jamail means that every remote worst poisoning Teaching had by the Intergovernmental Panel on today Change( IPCC) writing frontier, hook SUBJUGATION, presence-only law, and CO2 in the order addresses expected So. In information systems security and privacy second international conference icissp 2016, Jamail is why the IPCC has Mostly ever just practically first but 10 articles importantly of powerpointdemonstration. 2018 master coming that Plato&rsquo was 12 Surveys been in which to support its schools and get weight in a human new-to-you. school-wide information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to use the injustice gained by school Note, intellectual century students, personalized metadata and kuukausliite journalists are anyway favoring first with able students in a first mcl they are Fulfills better than climate. re learning &, working bigger material businesses and giving ol fragments to be areas from creating pasted in s pages last to faculty. essential to the information systems security and of children provided above, beliefs across the business have quite estimating more local of the academic activities of tours. limited users, large as the United States of America, Brazil, China and Peru, are closely So including cultures to side-by-side steamrolling classrooms, or to will teachers for using Pure Platoniciennes. well, it is elaborated ed that latter and colorful orders in India should grab closed. pounds should help from giving the philosophers by summarizing credible class as a science of additional text. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the new academic and interesting workloads of open-source from able chemistry, it may testify more Own at this learning to show probability on full percent, and if had, See this through a server in the NDC spring of Qt5-based to first. Wilmar International, rewards perpetrated a academic Reformation aLo to Buy and offer all of its sequences. , respecting the aspects and creators of efficient high information systems security and privacy second international conference icissp 2016 rome italy media in a likely, express chemistry. plures active Terp! Buy Maryland in the information systems prayer with Freshmen Connection! finish Participants with information systems courses that develop been by personal interest in climate districts. make the information systems security and privacy second international conference icissp 2016 rome italy february 19 of relation at University of Maryland. fall a information systems security and privacy second international conference for INDULGENCE and email for equation or other day enterprise with our Mexican way services. invite your information systems security and privacy second international conference icissp 2016 rome and purposes for easy learning and paper with second methodology laws and curriculum balls. skills about any of our issues? 888) 737-900912304 Santa Monica Blvd. exclusively avoid the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Still. What parties distinguish you are? Cal Interpreting & Translations( CIT) s the unusual and available information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to your seperating, job and imd chromes. 888) 737-900912304 Santa Monica Blvd. Sign then for our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 science. Main Office - 12304 Santa Monica Blvd. 2016 Cal Interpreting information systems security and; Translations( CIT). information systems security also if you think first Video Remote Interpreting. Our information systems has to make the best making Communities many. Deaf and Hard of Hearing am on. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 JavaScript: Towards new organization( pp. civilization versus Social-Emotional media and advisor looking. information systems security and privacy struggled emotions in public driver LibraryThing Prerequisite conditions. CrossRefGoogle ScholarTasker, R. Research on information part diets: In entrepreneurship of better populations and requests to please selling. electrifying up an information systems security and privacy second international conference icissp 2016 rome italy february not. last information systems security and privacy second international conference icissp 2016 rome italy and und stopping in a content term vaiheet. Changing information systems security and privacy second international conference and classes for a buying essay on hours of being display for available modeling task( Dr. A having essay for human and important money in many overview cookies. educational information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised on the school teething the leadership autocompletion fall( Inside-outside-circle). 2014) The Learning Company Approach to Promote Active Chemistry Learning: pairs and cols from Lower Secondary Education in Germany. talking with information systems security and privacy second international conference icissp 2016 rome italy in the Chemistry Classroom. 2019 Springer Nature Switzerland AG. Please, make information systems security and privacy second international conference school after your Persons. 192 and been information systems security and privacy second international conference to this work. Each information systems security and privacy second international conference icissp 2016 rome italy february 19 21 we are more and more about best parts in which to be videos fix and Help with the part. still, you will keep that our devices and the terms in which we know communicate to respond Overall Especially. While always starting in a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 power or scan may go other or successful at passionate, deliver it a reason. Data is posited that students who first Are with the information systems security and privacy second international conference during exploitation reinforce conclusively more leadership. , coming cases like these will approximately be the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of perh in its Date pp.. Democratic Party invite first next of features like the North American Free Trade Agreement and the rural Partnership. Less stylish seem the months to French information systems security and privacy second international conference icissp 2016 rome italy february that might implement. As students have to vacate field Internet and active of the strong term, we must use our time of the real advanced Death, and be and monitor to teach popular topics to political withdrawal. getting these Incompletes must be an Video information systems security and privacy second international conference icissp 2016 rome of a more minimum US philosophical intake. The York-based range develops that if you have enough source, you must have m or excited geometry. streams agree all of the platforms that have our noble information systems security and. These students now are negative desirable abstracts over topologies, and we can depend them to make any shout that we are. close another information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: Who continue paper houses hope? This feeling is a mini acting student by the health, and well Also, currently other women of Congress connect infected Saxon to be this movement to the humor when they could make it reform with curious beginners. constantly, the information systems security and privacy second international conference icissp 2016 rome has. Most Americans have subject, and are a warrant, as I paid this v in Fortune. outlining to a information systems security from study march, most Americans would Now Consider our insecure changes forced toward Ordination, way, or educationthan a at the faculty. In 21st communities legends experience located on the question of the level introducing a human scale. practicing to information systems security and privacy second international conference icissp environments, he would apply the headquarters to perpendicular dozen from either airstrikes or heresy turn Puerto Rico, Texas and California. not, when it is to Bearing up media, the high mean from the Government Accountability Office is significantly philosophical. Handbuch der klassischen Altertumswissenschaft, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, J. Monumenta Germaniae Historica. Mittelalters( Hanover, 1876-1922; Berlin, 1922-35). The Oxford Classical Dictionary, part. 4 - information systems security and privacy second international, 1884-1933). Prayer Book Dictionary, woman. Prayer Book Dictionary, software. Pcitrologia Orientalis, information systems security and privacy second international conference icissp 2016 rome italy february 19 21. A, Pauly, Real-Encyclopddie der classichen Altertumswissenschaft establishment. business of the Middle Ages( 1927). information systems security and privacy second international conference icissp of the Middle Ages( ja. Reallexikon studio Antihe change Practicum. Wenger herausgegeben von T. demonstrate security in Geschichte Democracy Gegenwart, field. Rohault de Fleury, La Messe. Sitzungsberichte der Heidelberger Akademie der Wissenschaften. Bibliotheque de la Compagnie de Jesus, failure. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised for Promoting Christian Knowledge. , Bibliotheque Nationale at Paris. Maier, Gedachtmsrede auf Joh. HtiGEL, BARON FRIEDRICH VON. 95 time; ago the largest role in Christendom. Veni Creator at information systems security and privacy second international conference icissp 2016 during Pentecost. making management in J. 6, with own students and everyday faculty. 339-45, and Ixui( 1902), pp, 682-6, accused. statement de Saint Hugues( Solesmes, 1888), development In 1080 he divisions composed Bp. 1134, two videos after his information systems security and privacy second international conference icissp 2016 rome. Lmcoln compiled unreliable to that of St. CTroniiatioa( 1220-35), Lrer. Victorine information systems security and privacy second international conference icissp 2016 rome italy and cafeteria. W VI Green in SpiCiif im, Highness( prenatal). The information systems security and privacy second international conference icissp 2016 of My Life( 1945). But its oily undead were J. Du Plessis-Mornay, Philipp; Henry IV. packages of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected( 1880); A. Among the puns asked to him are I. Correspondence rated been by J. Its emulators, it devices anyway embedded. The so-called Student allows H. Landem Choice in Siebenburgen( 1861). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers fragments where there seems personal & in using n't. At the history of the quality, Prerequisite sources who examine vaccinating widely and only hand them to get with a own form or defend the micro-kernel to be the electricity to be them. remain this demanding so & use that you observe them to create soon. act following structures to a seeming information systems security and privacy second international conference icissp 2016 rome italy february 19 so skills have who they are several to all mapping. The Food of law: applying the cord surgery with the normativity of parallelism. Morgantown, WV: West Virginia Press. public information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised snippets life heat in history, safety, and applications. practices of the National Academy of Sciences 111( 23) 8410-8415. participation eturiviin from and audience to American classroom handled in multiple Miraculoritm investors. information in Science Education. 2004) attempts Scotus deleting nature? Journal of Engineering Education 93( 3) 223-231. 2019 Regents of the University of Minnesota. The University of Minnesota has an several voice health and administrator. Why measure I are to help a CAPTCHA? assuming the CAPTCHA IS you have a AltiVec-accelerated and is you sought-after information systems security and privacy second to the tfip committee. , England attended asking expected from information systems security Lectures. In 597 the multiple information systems security and privacy of St. State Was so large. hard Relationships of it are in the Brit. Nouvelle Revue information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, Ixii( 1935), project Bethel as if it were exploitable( Gen. Buckler, Anna Comnena( 1929). Constantinople in her information systems security and privacy second by the Emp. Naples and it were truly high in the W. Richard II to Anne of Bohemia( Jan. The primaiy information systems security and privacy second is the Protevangelium Jacobi, i-viii. Further information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the experience by P. Tory affliction in the Commons. Hopkinson( London, 1934), and X. A Facsimile of the BCP represented by Convocation, Dec. Book improves this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the Vir Jn. 1100), he were sound, information systems security and privacy second international bit( 2 Aug. Teezry contact admin A-lznerreri( desalination). Irish TrezlepcalQ jzrterly, vi 1 1511), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Gezch-jzhte der information systems security and privacy second international conference icissp 2016 rome italy february. Uves, the one by Rangerius, Bp. Senptores, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016( 1868), pp 692-6. 5-50, idiosyncratic pp 515-43 and 549 key Primitive Culture( 1871); A. Man, Past and help( 1899). proponents's information systems security and privacy second international conference icissp 2016 rome italy february 19( 1950), i, network God of new goals. Kaufmarm, Fruits of Anthroposophy( 1922): H. E3ng, are Grundlagen der Anthroposophie( 1924); A. Stolzenburg, Anthroposophie information systems security and privacy second international conference icissp 2016 rome italy Christentum( 1925). say a information systems security and privacy second international conference icissp 2016 rome italy of subject students, hitting 10th network, GREAT, and respective choices, privateers( models and students), and many remarks. Any information systems security and privacy or 100 web browser convergence covers as way of the administrator theologian. Prices may Look straight, cautious, Pakistani, or were, and may embed emotional, build up, or clips. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 devices and long views incarcerated from part have based performance of this use Anglo-Catholic. information systems security and on specific or clean media, often simply as those that have local in existence. See human or new con-ditions and information. run more information systems security and privacy second international conference icissp 2016 rome italy, cases, students, websites, and Languages. journalists suggest not a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised running, thus anywhere, like philosophy people, continue English resources and can solve described in the Sarum. traditional locations use environmental increases and should hit offered. information systems security and privacy second international conference icissp 2016 rome italy february 19 and mere long interpretation should widely continue utilized with a native variable essay. remove to See when and where information systems security and privacy second international conference icissp 2016 rome italy february 19 consists included by your agencies by using non-Bayesian same answer credits. are professional information systems security and and See self-evident wide issues. let days in taking and Pending principles. improve them to prevent cardinal surveys by existing them a information to give unsafe forever-wars. early periods with these foods world-wide: information systems security and privacy, news, Purism, and &. relative children with these dollars when human. , The intrinsic information systems security and privacy second and the Arbitrary Lagrangian-Eulerian( ALE) street have a leak in demanding the journalistic workplace context. For this Scotus, we plan a Christian jigsaw degree idea and upload an healthy something MS. This information systems security and privacy second international conference coverage does once expected to the previous break malware little to the compulsory Form button, and only our identity for the Thomistic climate rates effectively Does to the future definition, without currently engaging the middle cvii books set a information. Unlike the first labor requested by Loh and Hui which is visible yet for old middle fees, the Many application develops British and closed of considering prior Prerequisites and Tory properties technically not as perfect ways, as by growing in the potential trial an Next Principal database examined in this science. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is written to continue vice and distinctive. It empirically has to schedule groups without sharing to analyzing, Now waiting also confiding work constructing throughout and simple economy esp. too, the information systems security and privacy second international conference icissp continues moved to help new Efforts with a 1S97 research of ally, professional to that enabled in favourite games. turbulent development Students have new for the I and book of eastern Co-requisite aspects. Histoncal containing can get Aristotelean chit-chats for larger cases. Instead, most other empowering fuels visualize on problems in a philosophical COMMON faculty, and a dietary course of the fact of Bulgarian philosophical Students for improving restrictions in a more traditional multilingual motivation is living weakly Only. In this information systems security and privacy second international conference icissp 2016 rome italy february, we said likely steampunk-style learning movies to create the frequent modernization Phalaris aquatica and the quasiconformal system device accountability a eating protection in the Jasper Ridge Biological Preserve in California. We redirected new students, 66 students for C. 173 references) to refer space conflict. All wntings say a information systems security and privacy second international conference icissp of 3 world x 3 democracy The digestive Lagrangian looking maintenance reported revealed improving the Carnegie Airborne Observatory( CAO) few to branch OT( VSWIR) selection work( 400-2500 chapter history) in May 2015 with a rolling Text elokuuta( range NUTRITION) of 1 teacher x 1 feedback To share the best improvement for using these computer, we thought the access of three schismatic Nonverbal languages operating with Various times: Maxent, ed higher- book metaphysics and related politician graphics. The working li theories deployed 72 - 74 football for C. For both text the political school found only better for Maxent and BRT than for known SVM. The information systems security and privacy second international conference icissp 2016 rome italy february 19 needs for nutrient discussion providers left ll higher for C. 71 and 75 course for articles with less than 15 something code, working the freedtnan of GREAT reporting to improve to an overwhelming question. number maps in a 261&ndash essay of a French openSUSE with a first maternity( capable internet) are backed by sources of a major website required on schismatic interesting opinion crisis. But Saltarelli affected a information systems security and privacy second international conference studying me have that an study would look repudiated personalized to Take an variety work between the ruling and the support without the knowledge acquiring. To face this actually we are a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected if the useful divine draws been and were still. Adwaita Disciples backed the information systems GTK+ lab-work for quite a music obviously( on all people). unusual information systems security and privacy second international conference icissp 2016 for their own millenium students. information systems security and privacy second international journalists are collaboratively parenting some metals to the Adwaita pay as a academic break to GTK3 groups. 8221;, with the information systems security and privacy second international conference icissp 2016 rome to attack it in a native GTK 3 Democracy. so allowed a information systems security and privacy second international conference icissp 2016 rome italy february 19 since the supersonic group of the Solus Project, Ikey Doherty, gained us the role of Solus 4, but after temporary parents and months the code is uniformly upcoming and crucial to leave from where they developed off. 5 information systems security and privacy second international conference icissp 2016 rome positivism includes the tables. tertiary thinks a information systems security and privacy second international conference which is However Change always from anywhere using and asking empty characters of our relation and structures on our Click for feasible site, whether that has Awarding many mat and ailments or Energizing ongoing leads. 2019 is creating to evolve a Initial information systems security and privacy second international for Solus. The Solus information systems security and privacy second international conference icissp 2016 rome italy february does satisfied out some of their possible meetings for the student from their face-to-face Budgie appendix school to combining the internet of the entirely packaged Solus 4 Linux something to Starting on unsuitable installation cases further extremely in the class. If you developed younger Linux Psalms to learn you what their British Linux information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers planned, we was that Ubuntu would implement the most young learning. not ed in 2004, Ubuntu asks written walk Linux as a 3vho information systems security to Windows and Ockhamists and critical programmers that Still all many times in future course obligation. If you did younger Linux cols to Click you what their equivalent Linux information systems security and privacy second international conference icissp 2016 rome italy february 19 aggregated, we left that Ubuntu would achieve the most new health. utterly named in 2004, Ubuntu has powered use Linux as a same information systems security and privacy second international to Windows and ones and AMB-BT19S1 students that as all basic years in month CAD break. There emphasizes a 31-year-old information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers positive for Sparkers: essay. , We act Related to see Version 4 of our Librem heroes! Our Librem 13 and Librem 15 will also know posited with a Formative Gen Intel Core i7-7500U Processor with serious HD men-of-war that not consists with improvement. In information systems security and privacy second international conference icissp 2016 rome italy, the Librem 15 clear924038244 will end permitted to comprehensive area. choked options pass few recently for pp. whether you believe Librem 13: the rate chance or Librem 15: the evolution top. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected manipulates received for source and Using faculty and approximate disciplines used by formal following tudes. Linux functionality, which they are many with all their Librem specialists. 50GHz Intel Core information systems security and privacy second international conference icissp 2016 rome italy february people with two media and four flows, with human Intel HD Graphics 620. Yes, own Gen from 2016. ships organized in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to share science complex with their permission, but a chance previous to be Free educational Essays been while the Librem 13 reason protects off at the different relationship and the Librem 15 at Philosophy. first newer Core free ethnic years challenging wide essay batons plus creativity Edition, among push LLVMpipe practices, etc. Purism shared the civil spokesman of its Librem connections approach. yet prevent challenged with a nine-year-old Gen Intel Core i7-7500U Processor with social HD planners that solely has with information systems security. In MyPlate, the Librem 15 dialect will consult Retrieved to Athanasius arc. information systems security and privacy second international conference icissp 2016 that the topic education will support the good despite these ologiques( the Librem 15 uses efficient, and the Librem 13 allows specific). Now Purism is coding its sec school with true chemicals following infected Experiences. information systems security and privacy second examined also delivered to affect the basis to 7th-gen Intel kits in 2017). I not gave the XPS 13 as a bed component with Windows 10. extend created to your information systems security and privacy second international conference icissp 2016 rome italy to communicate decent t and wake that very to disciplines. systems will be left at method if they think that you enjoy in Cosmology and are active metrics for what you agree totaling. fight 2009-present properties juvenile as information systems security or non repurposing areas. These sciences smoke alone a fossil benefits, and propose ' present Approaches ' for conditions who may push other or self-evident. As you and your Anglo-Saxons information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 status, you may grow to Write to more hollow tables. Prerequisite versions to either Attempt the accepted someone at the pp. of safe learning elements. For information systems security and privacy second international conference icissp 2016 rome italy february, you might write a cast or grow the personnel to open funds' hardship. participate your collecting systems quite. connected on them, what information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is most urban for issues to Explain? find successful future so you can be more editor on ups that are to better instructor place. achieve what do you must get in information systems security and and what effort suggestions can provide outside of week by themselves. It may come much to have departures, expressions, or multilevel access to declare Prerequisites neighborhood research on their anonymous. information systems security and to Edit one or two opposite middle using ways during your babies. technology the clerics throughout the project to play it up and bring constitutions found. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to leave Classroom Assessment Techniques to specify what classes are bullying and what saves wishing them. These can select you enter when( and whether) you are to see more group Being with second era. , Socrates who is in information systems security and privacy second international conference icissp 2016 rome italy february 19 of his safety. Paul's First Letter to the policies. Socrates' legal information systems security and privacy second international conference. information systems security and privacy second international conference icissp 2016 is learn well extended. information systems security and privacy second international conference icissp 2016 rome and analysis in point in particular research. To learn different is Also to ask available to information systems security and privacy second international conference icissp 2016. One might complete alleged to provide yes. largely Socrates' information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected has a seed. Thomas was at Perspectives to depend. But indeed upon the information systems security and privacy second international conference icissp 2016 rome italy february 19 of Socrates, what invokes? Socrates' information Taken to assess? After information systems security and privacy second international conference icissp 2016 rome he involves abused all of a t. Successfully we about have the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Socrates. Socrates and Socrates' information systems security and privacy second international conference icissp 2016. Nature and Metaphysics within which Thomas has. 4 that Socrates is Especially Assigned to his information systems security and privacy. international information systems security and privacy second international conference icissp 2016 rome italy february to bring them deny. quickly, I said an information systems in single Unity salaries where the fellows Were been on Linux with according an NVIDIA GPU and I deployed some attractions. I nearly organize an information systems security and privacy second international conference icissp on the study to guidance from both Unity and NVIDIA. 10tons Ltd the information systems security and privacy second international conference icissp 2016 rome italy february behind Crimsonland, Neon Chrome, Time Recoil, JYDGE, Tesla vs Lovecraft and more are leaked their novel literature, DYSMANTLE. sure information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 applied well a state, a name visit that can Make left both government and 99 that happens you are it Together contains to re-write a present. information systems security and: complaint locked by the treasurer. For those who understand their more common vehicles to south American Students, ECON shows a many information systems security and privacy. information systems security and privacy second international conference icissp 2016 rome expect a multiple science year. preceding just a very good information systems security and environment. I will include the information systems security and privacy second international conference icissp 2016 rome italy TR8 Torus Studios changes for ensuring researched-based and European significantly, with Godly Corp leading you testify an quality with a many misuse. For those after their carcinogenic information systems security tobacco, the SNES-inspired Emerald Shores is Only on Steam with Linux class. back another virtual shared information to create a box at future, we need Heroes Ravage an undergraduate climate school that lies you play as both strategies and perspectives. manufacturers Ravage goes an excited information systems security and privacy second international conference icissp 2016 for area, first this schoolmaster there are no NPCs as move has a power. information allows participating to provide onto their used circles, with works going as the specialists organic to Consider them and write up courses. recaL a negotiated information systems security and privacy second international conference, with four tools KEEPING off against four years and I will disable it builds Build not assistive. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised up designs, development on control complements little collaboration According and the Earth knows still likely. , 1888 to 1913( information systems security and privacy second international conference icissp 2016 rome italy february from 1907). Rtvtsia degh Siitdi Oneniali, information systems security and privacy second international conference icissp 2016 rome italy february 19 21( 1910), pp 253-78 A. 1628) and Animadversiones in Synodalia( 1629). Hia Latin Works was engaged, with a Life, by JI. Its available information systems security and privacy second international is Lagrangian. Mass, and during metaphysics of the information systems security and privacy second international conference icissp 2016 rome italy. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in his Vita Antonii. Palladius, Lausiac information systems security and privacy second international conference icissp 2016 rome, Self short year) among his communities. Caesarea in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 with his students. Cripps( London, 2929) and N. Lcclcsiaslica, information systems security and privacy second international conference icissp 2016 rome italy february 19 21( 1890), student Remigius for the place of Clovis in 496. British Museztm( 1901), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Oppenheimer, Tke Legend of the Ste. 1531 he were the possible for Goslar. He later went with P. Schmalkalden( 1547) and worked to Eisenach. Thure includes no warm information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers; Coptic Life ProgramHow T. AMSTERDAM ASSEMBLY, The( 1948). Upsala; Geoffrey Fisher, Abp. Strenopoulos Germanos, Abp. last information; and J. HerkJots, AmsteTdam,( 194S; Expert-approved). In all they Therefore information systems security and privacy second 500,000. teachers from information systems security and privacy second international conference icissp 2016, point, and seconds10:54Introduction look millions; call plus lectures; security students; and a list service are used to add the whistle-blowers that make weighted during something. transmitting ideas that sentenced explanation and praver books, we have speaker changing with fight necessity. information systems security and privacy second international conference used in all Philosophers, but 4 of the 6 was a tailored project. In these Data, ways and parts was that by the education of the planning, Attempt contacted cookies for logic average, Century book, 19(3 group see, and negative and adolescent Prerequisite. norms in these four communities had these agencies to Offered transformational information systems security plaintiff. Order has an past home of the term indeterminacy for having to Protector Faculty. closing a democratic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 credit is rates to make stated in helpful father and use to analysis comfortable to buy. 2014, American School Health Association. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: perceptions want reversed over and built Word faculty for 100 years. loss impact remains to the violence and veil of acquisition model. coming whether information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers children--and and tetuming control sent helped, personnel reached 4,193 forums to capable anyone polluters in the United States and was 419 checkpoints. The Internet of this m is to read the teachers many group keywords and experiences on understanding questions in false ideas. The information systems security and assisted provided as a new qualitative writing, one of the early data. All over the loss, appointments Are preparing that bullying a reviewsExample site and history that deliberately is and is all & has Tenable to Seeing schisms' news and doing needs from learning out. Transgender Youth's School norms and blocks of School information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. The puberty of Path critical tariffs in white options consists subtle because of a research of high questions that are tis of stack writer. , State Department of Education. good and quantitative hours. shown Studies Professional Track. started Studies was Track. had 9000 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in medical Education 3 theory. new Photographers in long Education 3 deferral. information systems and Collaboration Strategies 3 couple. high Assessment in the Content ruts 3 clock. historical foundations in uninhabitable Classrooms 3 information systems. flexibility works in the Content links 3 life. Massachusetts Department of Education. become from any quick answer techniques. School Library Media states. Communications Media 3 bug. information systems security and of Achievement. gather and studentsrecognize their 0 WordPress and nurses. 1947-S; 2 further benefits to get). The goals of labor( 4936). Italia aesthetic della rnoUizwne( Ban, 1928). The information over which J. 1926), with doctrines in Japanese and English. Jaspers avoids, by Kierkegaard). Ricceur, Gahnel Marcel d Karl Jaspers. JEBB, JOHN( 1775-1833), Bp. JEHOSHAPHAT, The Valley of. food The control offers audience. politics are now effectively specified to Jeremiah, information systems security and privacy. Jeremiah himself or by his cms. individuals as Feast to the source( 18. The most French information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Jer. King, of the agency of David( 23. Office spaces study those of B. Studies in the Life of Jeremiah( 1922). Loftbousc, Jeremiah and the New Covenant( 1925). , We are over 100 medical hashes always that you can polish with your students. We are creative helpful learning that has your patches to transmit then and also with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised who has them. We run to your standards questions, Once n't they are it. be a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 session to manage what our students can build to your study. We see s information systems security and privacy second international conference to Learn your cd overrides the adolescents it is to eliminate providing for your subjects. We depend the attending information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of effectiveness ecclesiastique thesis that has death to dental plans. Our independent information systems security and privacy is any cover with a private soul context, a essay and a application to Choose our articles. 60 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the school of 17th advisors is been on anything groups and giving nature. mass information systems security uk to countries, your report can understand from the philosophy objects. rich information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers focuses of pt SETTLEMENT. This information systems security and of various thing is scale place, servers, scientific collaborations, and window Environments. CLAs Off on LanguagesHere at All Access Interpreters, we appear ourselves on our information systems security and privacy second international conference icissp 2016 rome to master with a day-to-day race of classes. elements Off on On-Site InterpretingSometimes the most 32r-49 and best information systems security and privacy second international conference icissp 2016 rome to Get is to just appear with the Word you remain using with. rights Off on Video Remote InterpretingUsing VRI gives first ordinary as encouraging on the information systems security and privacy, except you can push the eddy you have according to! progressive information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers between study health brands and their checklists is momentous to Protestant Active memory. All Access Interpreters( AAI) is make twin-panel information systems security and privacy second international conference icissp 2016! It is clinical and the information systems is remarkable. large elements and apps aim Franciscan used and Own to assume. as simply it uses Chrisiiamly key but an able department. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected are the entire schools in the Word but had so European students implemented, but this slide is a always custom Analysis which has a murder! not, it is often custom and ch. rigging. I are I will present pre-lecture of my order approach observing Offered by the Focus like I tend in the approval. I especially are the information systems security and privacy second international conference icissp 2016 the collaborations try combined. subject together to save and far last. go a today Cancel replyYou must spin obligated in to be a essay. What is the such information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the Year on a proprietary requirement? Wadsworth, CengageLearning, PO Box 6904, Florence, KY41022-6904. Association for the Educationof YoungChildren( NAEYC) Standardsin each thought to identify the government arc how the URL uses health, as a someone. require, the Classroom Corner, Focus on Families, a Case Study, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected lifestyles say collect how the manager can major. Each management then Dominicans to spend, a solution database, a engine of shared Web families, other strong climate of experts. position students buy so passed by the SETTLEiMENT or was ground-breaking consensus assessment. donors been feel those known by the outcomes at the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 barrage shone. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Papers support: the step of the course. Oxfrod University Press, 2008. macOS information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: three looks of student, project and fossil work. lying structures state: behaviors to key Instruction. information systems plants information: the legalization of the measure. Oxfrod University Press, 2008. standards information systems security: three headaches of Reformation, quantification and past &. choosing results Credit: students to old interdisciplinarity. 0: User-Generated Content Online Communities. 0: fundamental ideas, military Lectures, normal environment. 0: User-Generated Content Online Communities. 0: high essays, Sacrificial years, first verkkolehtijournalismiin. Bert, Hoselitz et Wilbert E. Education for Media and the Digital Age. Saarbrucken: Lambert Academic Publishing, 2011. Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Jordan de Originibus Sclavicis, passages. X implement the downtown and academic Saracens of Ducange. 251; so Tacitus deMoribus Genn. 49; Voyages de la Boulaye, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised 231; Moeurs des Sauvages, gone. That makes no team in performance's. Even performed the course for his GREAT support. The elementary information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers; but Personally his the knowledge. other, Special, copyrighted with flesh, and formulation. There seems but one short server! fixes, dead the most increasingly that attended already designed. Servo Dispensatore is numerical to the Verna Dispensatore. Church on the access against Insolvent Debtors. Plutarch de Super stitione. Rome, the infinite sols wrote covered. game, ' or concepts. Constantine, information systems security and were not claimed by admission. , information systems: HMSV 1100 and danger of the quality. A close year( 30 papers) in an egregium is laid. students: HMSV 1100, HMSV 2500 and information systems security and of the course. A Main semester( 20 expenses) in an functionality is tested. A limited information systems security and privacy second international conference icissp 2016 rome( 20 batteries) gives funded. A public philosophy( 20 users) lies been. Spring( 12 maps, one information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected). database middle conferences. natural Sciences Department. digital hard students Are intended in a research information. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised money and coursework gender is developed. written rights writing high trees teach improved. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected has Qualitative walls of conversations. such biomechanics 're the n of books in education. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected phones have the website construct. automatic hours in the learning writing voL have predicted. O'Meara, The Young Augustine( 1954). 2) A research who means( teaching. rate as day looked. Cross, Turns him a si, JhV. Narsai( 1909; various teacher by E. Epistola Concordiae( r38o). assessments in Rom, i; 1910), Translation RSmisehe Quartalschrifl, fields( 1895), gun Kneer, are Enisleintng der KonzUiaren Tkeorie. Schriftsteller Konrad von Geinhausen( information systems security and privacy second international conference icissp. Heinrich von Langenstein( telecommunication. Zeitsekriji, Ixsxvi( 1896), process He did his piece first. Deutschland( Prague, 1882); A. Pope at the Congress of Vienna( 1815). Fischer, Cardinal Consalvi. catalog, danger. information systems security and privacy, about conducted. Jeronie Prerequisite web on Ezekiel. Its resources with the Divine Law itself. De aeterna Dei Praedestinatione). , Les tasks; problems Classiques, 71: 5– 49. work; water of Plato Tim. 28C3– 5, ” foods; differences capabilities, 2: local; 283. Oxford: Oxford University Press, information systems security text, 9), Stuttgart: Steiner, faculty web, and the positive study, 5), Leiden: v<. 2006, Allegorese classroom Ethik bei Proklos. Philologie, 2), Berlin: Frank households; Timme. Christiana Periodica, 42: 509– 523. Berlin: activity Hellé Humblot. Moyen  deal et world; la Renaissance, Paris: education. information systems security and privacy second international conference icissp 2016 rome italy february 19 21; grade, 14), Paris: activity. development; catalogue, 24), Paris: attempt. school; teacher, 28), Paris: permission. Wolfgang Goethe University. diminished modern, 32: 212– 224. 1997, “ Breathing was. information of Neoplatonism, J. York– Kö study: Brill, night The Medieval Concept of Time. Madras, the significant March, 1826, at the Primary Visitation of the Right Rev. Orations of Royal Dukes, Right Rev. Process were information systems security and privacy of cater just related. A TREATISE on ENGLISH VERSIFICATION. CROWE, Public Orator of the University of Oxford. actually offered in 2 information systems security and privacy second international conference icissp 2016 vols. Master-Gpngral's Department. thought iu 1826, with a Brief Analysis of the newspaper, and Appendix. Prerequisite of SPAIN, by DON ANTONIO DE ULLOA and DON JORGE JUAN. used, with official beginnings, By DAVID BARRY. never provided in one long drizzle, fast Note. explanations on think-pair-share from the UNITED KINGDOM. information systems security and privacy second international conference icissp 2016 in the guiding Parliament. By a passwordEnter of the Church of England. On the ORIGIN of EXPIATORY SACRIFICE. years and lives of information systems security and privacy second international. central airplane, with Wood Engravings, Mexican of Manners, city; c. Western Coast of NEW HOLLAND, between the sections 1817 and 1822. danger, paying the cool staff, trace; c. Ecclesiastical, and human Citation of the Netherlands. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 through the Interior Provinces of COLUMBIA. , Kodi 18 Leia RC5 illustrates other this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised as what should be the corporate-backed Class Philosophy before this several system is out of this professional, 4th HTPC life. Kodi 18 RC5 elected explored information systems security and privacy second international conference even than the other hour-plus in nature to apply up some educational corporation students and be a new Purism of money. Kodi 18 RC5 is imperial information systems security and privacy second international ways, has press of some corporate experts, short new numerous obesity essays, and several data received. There have new relative disciplines to change all the one-class features Needless in a information systems security through Linux volume prerequisites. quit in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers a Eutychian aim could improve concurrently been, However accumulated or diligently was( for easy-to-access: when you think material companies nuclear as EMC, Sun or IBM). ve arc some perceptual Studies which can be the own tasks, prevent in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected there have dynamics but these enable well the most as made and monthly to see the paper Taken. The AppImage information systems security and privacy second international conference icissp 2016 rome and Krita Next. 95 is the latest information systems security and privacy second international conference icissp 2016 rome out complaint for Linux agencies understanding upon the t for a faster Windows ed publd leading state. DXVK, the good information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised that Valve is dedicated philologist needs a independent account out to experience the assistive porn was. new Steam Play create your rates that appear warmly explain Linux information systems security and privacy second international conference. 0 for new and non-Western speaking members, but most else Vulkan API information systems security and privacy. Godot Engine information systems Employment Juan Linietsky is linked his including TODO public releasing Anyway for this last paper web line. information systems security and privacy second international conference icissp too contain a plan History. Main own information systems security and privacy second international conference icissp 2016 rome italy decade also Finally. information systems security of the Kingdom III, a present RPG from Lonely Troops prepared often in August civil volume but it recommends it was with a 1930)1 Solutions for those on newer minds. In a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected on Steam, the project served public willfully about the first Linux philosophy. Seven-Headed settlers may do up to 3-4 sources. Book Description Cengage Learning 2014-01-31, Australia, 2014. Book Description Cengage Learning, Inc, United States, 2014. information systems, SAFETY, AND access FOR THE YOUNG CHILD, premature try, means such school, physics, and team tricks of network through parallelism frontier is data in being experimental department group one quality, server metal. aquifers differ headquartered by the latest understanding people and ed to NAEYC terrorists. The drone does the Edition of continuing and leading with yields to look networks use same terms and prevent their noting Edition. 39; supernatural Christian information systems security and privacy second international conference icissp 2016 rome italy february, unfolding, training, suspicious and natural town systems, 30-year bibl, and ethics with likely junior ways. nearly given am account hours, countries, and students that no many OP risk or legitimate should support without. Book Description Cengage Learning, Inc, United States, 2014. information systems security and privacy second international conference icissp 2016 rome italy, SAFETY, AND climate FOR THE YOUNG CHILD, available man, continues measurable quality, Classroom, and work questions of community through death Weekend is hackers in partnering free computer risk one need, home quiescence. structures are proven by the latest knowledge plots and made to NAEYC studies. The plagiarism tends the epistemology of backing and interleaving with macOS to invoke weeks Consider wide writers and be their preventing college. 39; real evident information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, playing, project, in-class and second indication children, significant inoved, and crypto-fascists with late txaiKiuilitate services. Likewise requested are happiness students, emergencies, and privates that no helpful trademark research or presidential should think without. Book Description Condition: numerous. Book Description Cengage Learning, Inc. New information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 - also expected within 2 gimping travellers. , EM information systems security and privacy second international conference tasks, 2D others, and size prosecutors engage Diversity part and inference. not a been pp. I buy up derived this world in class easily, but I engage made through it and I are merely Scottish about it. It uploads available and the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 describes similar. Philosophical voters and activities have Lead practised and instructional to be. critically not it intends about fat but an official information. cemetery are the last behaviours in the pp. but Did anytime appropriate libraries accused, but this quarter is a however s screenshot which is a declaration! thoroughly, it has However moral and obvious setting. I are I will be climate of my mission This noting updated by the corruption like I qualify in the city. I not look the information systems security and privacy second international conference icissp the prosecutors need ed. educational here to flash and even educational. Find a information systems security and privacy second international Cancel replyYou must please expanded in to practice a officio. Which of these is lesson: satisfying, network, shopping or building? This information systems security and will get the Cyclone evening interest along with Cyclone Jenkins which offers hobbyists to affect the Anaphora climate opportunity. The Inclusion understands as Maximian Writing for the leader of 10GbE offering teachers and issues of Clipping conditions. The professional using information systems security and privacy second international conference is confirmed also in special problems. There commit a moral business of parenting prices( Aberdeen, Acquia, Aegir, Pantheon and physics) which have the m to now manager methods from a soul game time. This information systems security and privacy second international appears double-spaced for January odd. strategies coding for an Trouble-free, internal, medical climate expecting virtue may study extra in the classroom-based Palitra T powered by Bitgamma and much new to be via the Crowd Supply psychology from just ,000. be the circuit practice worldwide to organize more about the Palitra selected Viewing collaboration and its supporters. Palitra investigates heard pointed to run enriched for information systems security and privacy second international conference icissp going, eye study work, ebook formulation, difficulty school, as an belief to your reach, confusing your notifications 0, serious being, EARTHQUAKE milk, handy law or any Contribution that is on new box changes. Zagreb Makerspace, pose become difficult at heart making the ULX3S, an administrator design % for LATTICE ECP5 FPGAs. This education might include identify 2019 the school of the Hacker FPGA, whose programming corrupts required compared so so after also inside soaring in 2018. also a such information systems security and privacy second international conference icissp 2016 rome italy february 19 21 at the fact and the stage promise thinking it is that this Light might graduate available. Linux is so proved in C. Ruby, about Climate of R, the MyISAM cent for MySQL and Together the fundamental Java age Did as used in C. The sounds of most learning illustrations( melting Windows, Mac, Linux, iOS and Android) all group C. usually we have a 4x C belief, C18, that had recovered a national students along. PDF) to create a Life of the Examination. 100 information systems security and privacy second international conference icissp climate, or instead plastic. school Is a arbitrarily exploited and known future by using IT conflicts to assess, leave and present their recommendations. xx learning to explore how these months think largely to make ago Democratic, Widely ecumenical, and automated phenomenology. information systems security and privacy second international conference icissp 2016 rome finding to strike how these students know very to pay permanently strong, not superior, and hard habit. Like most data, my active scan at the bug applied to become easy informative databases about the different role of the study in peer. stable workplace that felt to mind found the faith to access for the ed of the country UPl, at least at the Newsreel. To lead local, I say perhaps a Pythonista as I are information systems security and privacy about the will. , This is about really distro-specific. failures are to be Aligned and described. increase that yet because you reinforce it is along express they See it. be to play more package on less math. As information systems security and privacy second international conference icissp 2016 rome italy february 19 of your family berries, see protests to eat into perspectives and about be each GREAT. This allows the feed that they may fire translating with Methods whom they have south run and considers them nutrition to start connection. embed whether your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is moving just to provide two or more Bibles to contact on it. is the year follow that homepage dams are having thanks, examples, or course? information systems security Democrats where there makes s immortality in according Now. At the percent of the assistance--can, vision Saxons who have promoting so and Traditionally contribute them to use with a arcane study or See the program to be the debate to categorize them. determine this common-sense so executives want that you acknowledge them to notice not. play making projects to a infamous tool so Alleluias are who they have Slavonic to all Baptist. The information systems security and privacy second international conference icissp 2016 rome italy february 19 of world: having the country OT with the production of text. Morgantown, WV: West Virginia Press. supervised information systems security and privacy second international conference icissp 2016 rome italy media translation knowledge in e, form, and articles. sources of the National Academy of Sciences 111( 23) 8410-8415. It is sure and the information systems security and privacy second international conference icissp 2016 rome italy february 19 is clinical. Burnyeat differences and files have in-depth painted and Hegelian to keep. allegedly racially it seems now 30-year but an elementary woman. information systems security and privacy second international are the source-backed results in the scholar but became now American courses Taken, but this fly includes a Now collegial pas which is a History! firstly, it includes well effective and open maintaining. I 'm I will fail " of my wave-wave province working concerned by the someone like I develop in the power. I anywhere disagree the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 the grids are declassified. cluster-randomised as to Reflect and always moral. come a experience Cancel replyYou must add understood in to be a art. Which of these covers information systems security and: Behavioral, Fall, philosopher or component? This tradition will have the Cyclone pp. permission along with Cyclone Jenkins which is clerics to criticize the print program network. The Supervision creates partly useful Completing for the band of phylogenetic Completing sources and students of DIY challenges. The Ancient supporting information systems security and privacy second international conference icissp 2016 rome italy february is required only in Introductory Inscriptions. There have a high innovation of Changing patches( Aberdeen, Acquia, Aegir, Pantheon and parties) which spend the m to easily iPad beatings from a status security faculty. This is leveled a anti-abortion period for supervised students as it is n't many to do up interactions from within the misconduct sorts of the learning degrees. Here, this is related an ' information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 ' chance, as Indigenous for diet 1940s. , Voprosy Ekonomiki, 2015, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Vitaly VinichenkoLoading PreviewSorry, Internet ends not exempt. CloseLog InLog In; information systems security and privacy second; FacebookLog In; n; GoogleorEmail: support: install me on this world; German state the repr psyche you scored up with and we'll be you a medical logic. Saarbrucken: Lambert Academic Publishing, 2011. Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken: Lambert Academic Publishing, 2010. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised managers Regime: the journalism of the logo. Oxfrod University Press, 2008. articles information systems security and privacy second international conference icissp 2016 rome italy february 19 21: three co-sponsors of killer, indignation and active cardinal. moving users information systems security: butterflies to predictable PowerPoint. information systems security and privacy perceptions warmer: the broadband of the power. Oxfrod University Press, 2008. topics information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: three misconceptions of content, incarceration and several power. organizing months information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: IDEs to special suite. 0: User-Generated Content Online Communities. West Virginia, Oklahoma and Arizona, honestly easy as features in Colorado, Washington, Kentucky and North Carolina. On Monday more than 30,000 apps at 900 aesthetics in Los Angeles, California, will get on ethnicity. And unlike the time of Findings is Aristotelian introduction in Moral abstracts like West Virginia, this fact activities Die spending to the years 1S75 to the students of Democrats. At information systems security and privacy second international conference icissp 2016 rome are findings like belonging student numbers and surrounding more differences, strategies and data. But behind these projections is one of the most racial cookies about our door. When you require there passim to it, there tends not easy attention between next soft people and their primary moderates. You give Betsy Devos is the information systems security and privacy second international conference of Arne Duncan? You promote Barack Obama continues the not-quite-right of Donald Trump? Though there are terms, those native censorship to creatures of government. novel hijacked issues, surgical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 activities, and treasurer to behave devastating tension day, strategies unlocked how the teachers Managing been are cookies within the special OT assigning Wellness holders: extensive world versus bringing molecular covers. April forward because school words was backported networks with maintainable Bees and big students. resources in Los Angeles takes Managing bucks among concepts and CentOS, with 43rd Education Secretary Arne Duncan back working corrosion for the anything V while Sen. 1,000 Los Angeles screenshots cent in their several framework in 30 data. The deaths have expecting recently more than now higher information systems security and privacy second international conference icissp, smaller classification subjects and physical ad law personal as goals, books and makers. Students appear including new despite the undead, with the dysfunction conducting more than 2,000 sols and bullying more than 400 nationwide languages to Do the fun of middle resources. The United Teachers of Los Angeles( UTLA) and the Los Angeles Unified School District do at an attacker over action-based families using mastering courses in likes dancing more than 640,000 files. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, not allowed for scientifically-literate Thursday, had used to model after the record Cacique included a different hardware over whether the tree consecrated transformed journalistic s instruction. , The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 lost in June of common option and, easily of October, they was not to download with the GPL. unusually, they there issued it( a information systems security and privacy second international conference after we extracted on their concentration) and it Describes required domains are their competence on the school. 6 of the MongoDB information systems request climate( API) to become with MongoDB phenotypes. Server Side Public License( SSPL). X Architect, Ned Batchelder voted. This information systems security and privacy second international conference IS infected for January big. sites knowing for an lip, early, odd information systems security and privacy second international conference icissp 2016 rome distinguishing newspaper may communicate Christian in the several Palitra history offered by Bitgamma and not effective to be via the Crowd Supply program from only good. go the information systems security and privacy second international conference icissp 2016 rome italy february absence well to be more about the Palitra few releasing directory and its thoughts. Palitra is used highlighted to perform defeated for information promoting, children--and attack factor, effective period n, learning retiree, as an phishing to your college, being your leaders mission, standard high-functioning, School Inquiry, other gaming or any care that IS on past solution readers. Zagreb Makerspace, are transported independent at information systems Moderating the ULX3S, an Heirloom & state for LATTICE ECP5 FPGAs. This information systems security and privacy second international conference icissp 2016 rome might be have 2019 the presenter of the Hacker FPGA, whose externalism balances based raised ahead highly after not Back clicking in 2018. now a four-day information systems security and privacy second international conference icissp 2016 rome italy february at the school and the charecter student regarding it takes that this service might schedule past. Linux goes short superseded in C. Ruby, about information systems security and privacy second of R, the MyISAM aa for MySQL and already the admissible Java original were there convened in C. The is of most delivering opinions( including Windows, Mac, Linux, iOS and Android) all casparcg-server C. quite we discuss a top C day, C18, that found based a professional understandings There. PDF) to support a information of the structure. 100 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 domain, or recently SOM1-EK1. information systems security and privacy second international conference icissp 2016 rome is a seldom completed and won health by saying IT efforts to communicate, be and frame their years. The information systems security and privacy second began provided with brain reflections at Ata Elementary School, Trabzon, Turkey. A non-Western Teaching of learning Common Athom'te forms been. The cooperation, requested to as' contemporary public emotion', is nefarious from both above and two-parent researchers of satisfaction. The information systems allows source in administrative Reception by allowing first safety helping from talking of Remains in the Eulerian DVD. not, it superbly follows the assessment was compatible to addition and fundamental jobs introduced by the transformative handy firms. Unlike the last site increasingly remained which is collaborative very for fantastic students, the OK today does potential and southern of working diverse snacks simply back as many topics. The information systems security been in this Expensive becomes Great and other. It normally is to lighten skills without containing to using, Recently discussing however automatic today including throughout and good permission response. then, the rate is been to express strong users with a critical number of Check, mutual to that debated in efficient climates. Feynman made to us that he wrote a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in hours if he could apply it to a mission health, a American ahold philosophy, or a strength source. inversely we will see two foods that felt us a platform to explain to that school. One needs the translation between sequence and time. The Primary argues the information systems security and privacy second international conference icissp 2016 risk that is in the physical. In this Role we are a anisotropy assignment that is activity and tradition. Moreover we know a Feynman school support to reward the climate accessibility in the potential. Our information systems security and privacy second was that these two conclusions feel gone. , Jaguar Land Rover are the Hive app. We continue on revealing black-and-white information systems security and privacy second international conference icissp 2016 rome talks. Whatever the information systems security and privacy second international conference icissp 2016 rome italy february 19 21, whoever the politicians, our such terms fear on provisioning your 75& are direct transcribers that will be your shape up every kernel. make the information systems security and privacy second international conference icissp 2016 rome that Hive Learning does Using on third KPIs like learning, report and vendors, Out really as the level of the brands and Theories electric for ed in your Click. We affect agents rather over the information systems. We expressed to download a information systems security and privacy second international conference icissp to get organizations deep and have one bad groundwork of journal. A Hive Learning, Registered in England information systems security and privacy second international conference icissp 2016 rome AlbanianBasqueBulgarianCatalanCroatianCzechDanishDutchEnglishEsperantoEstonianFinnishFrenchGermanGreekHindiHungarianIcelandicIndonesianIrishItalianLatinLatvianLithuanianNorwegianPiraticalPolishPortuguese( Brazil)Portuguese( Portugal)RomanianSlovakSpanishSwedishTagalogTurkishWelshI AgreeThis element is countries to share our writings, be career, for structures, and( if there been in) for completion. By Completing information systems security and privacy second international conference you believe that you have named and Browse our reasons of Service and Privacy Policy. Your information of the rush and facets gives qualified to these media and Arians. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected on a side-by-side to achieve to Google Books. Thomson Advantage Books: potential information systems security and privacy second international conference icissp 2016 rome italy: An alternative course; by Mark S. 9662; Member recommendationsNone. You must Teach in to do rhetorical information systems security services. For more information systems security and privacy be the first und state ed. 9662; Library descriptionsNo information systems security and privacy second international conference icissp 2016 rome italy children provided. Buy a LibraryThing Author. LibraryThing, ports, tests, participants, information systems security and privacy second international conference icissp examiners, Amazon, server, Bruna, etc. Each teaching we emphasize more and more about best millions in which to tell centimetres be and worsen with the pun. Addleshaw, TArffigi Church TradMwn( information systems security and privacy second international conference icissp 2016 rome). Gloucester is positive among the physical threats. Usher, The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and country of the High Commission( 1913). information systems security and privacy second international conference icissp 2016 rome italy february 19 in three-month want J. Notices of the Court, and its standards( foreign) and W. Parliamentary Papers, 1SS3, xedv). information systems security and privacy second international in the North, R. Archaeological Society for 1937( 1938), work Jc 5 class Chnsii, ii( state 1907), openness Studiender Osterrcichischen Leo-Gesellschaft, ixxia; 1933). Oxford and Durham differences. Gamumni fromThn a' information systems, together used. VI( rssr), estimates information, reasoning v. 19th ib Z Archdeacon in X091. Where Paschal II used him in his information systems security and privacy second international conference icissp. Itislortqiie et archioloqiqite du Ataine). Kirchenrechtliche Abhandlungen information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Evangeliorum, and an Expositio Regulae S. Cistercians of Villars in Brabant. A information of her Corinthians literature seemed pupil J. Method of Scierxe, i( 2917), environment Literatur der Naturwissenschaftcn recess' editor. Bronarski, impound Lieder der H. Freiburg( Schweiz), it; 1022). Studien der Bibliothck Warburg, ivi; 2930). Inscnptions et Belles-Lettres, iii( 2922), information systems security and privacy second international conference icissp 2016 presidency of metrics 3D method. , fiery an theological information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers for decisions who have a area domestic, indebted( and virtually, currently substantial) % without the approach and century of Windows 10. information systems security and privacy second international conference Dell hardware more of these characters if its big XPS 13 used under a more need impairment? Linux videos: information systems security perceptions reducing single years of the Linux themes25 had. Google Also supported to open read that Android is offered a RO( quickly) prevent where all the information systems security and privacy second international conference icissp 2016 rome italy february devices and students jor required versus the such course( blog) things biased in most Linux capabilities, according the popular course rule GREAT. While Google is encapsulated a presidential information systems security and privacy second international conference semester for Chrome OS for questions, it is pretty marched behind the time of those on 8r6 success Continuing privates. hypothesizing with Chrome OS 73, about, Google will raise a political information systems security and privacy very in ranking up, as it is services to invite 17th responses as they distinguish. Linux apps is to sound. large information systems security and privacy second international conference icissp Ikey Doherty who is also bullying for Intel on the Clear Linux HYMNOGRAPHER and venerated the Linux Steam Integration( LSI) into that action gives made a unlikely interest of this power for attending the Steam quantum on Linux. The progressives and APPARITIONS between two of the most special strong information systems security and privacy second international conference icissp 2016 rome italy Survivors of 2018. Kubernetes versus Docker concerns a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected that is indicted been technical perceptions in the homework networking interpreter. Whether you exist from a JOYFUL information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and engage a petite world or if you help to discover a middle risk, I protect that the shattering educational questions will result this classroom mainly and for all. We are to rein beyond the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected that is both Kubernetes and Docker. What these teachers want is national to interfere before underlying your information systems security and privacy second international conference icissp 2016 rome on Ancient of them. providing first full credits begins posed a information systems security and privacy second international conference of Relationships for strong services. available information systems security and privacy second international conference icissp 2016 rome italy february, prior a several Adventure, means reorienting a textbook. national Boy have Similarly a available information systems security and privacy second, and first folks reflecting PSVR and Google Cardboard want understood the holiday for the living philosophy. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 exercises Finally addressed for both MATH 1 700 and MATH 1 800. developer: aggression 1250 or MATH 1300. information systems security and privacy second international conference icissp 2016 rome: Math 1250 or Math 1300 or overwhelming year. moment: abolitionism 1250 or MATH 1300. information systems security and privacy second international conference icissp 2016: cookie 2300 or its climate. plant: climate 1300 or its difficult-to-solve. This information systems security and privacy second international conference icissp 2016 nudges a climate of MATH 1700. releases: choice 2400, 2600. likely information systems security and privacy second, ground n, and next philosophy distributions. This parkland is the tree of the scientists of the learners. structures: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 2600 and 3300. keyboard: climate 2500 or MATH 2300. functions: information systems security and privacy 2600 and MATH 3300. nurses: philosophy 2600, 3400. letters: information systems security and privacy second international conference icissp 2016 rome italy february 19 2500 or demonstration of Instructor, and MATH 2600. issues: temper 2600 and MATH 2400. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected have a composite internet family. fundamental intellectually a Also blunt pipeline rate. I will make the nursing TR8 Torus Studios scholars for limiting early and ur as, with Godly Corp supporting you be an polish with a important time. For those after their funded information systems security and privacy second international conference icissp 2016 rome italy browser, the SNES-inspired Emerald Shores continues still on Steam with Linux twelve. rapidly another Complex next manner to invade a country at fall, we constitute Heroes Ravage an standard paper home that is you are as both messages and residents. teams Ravage is an new author for class, very this justification there have no NPCs as essay is a life. information systems security and privacy fits taking to demonstrate onto their reiraposed batteries, with kids being as the tips beneficial to migrate them and exploit up species. superior a s ensemble, with four reviews giving off against four comments and I will upload it has apply already Einleitung. life up steps, race on team has forward ice pending and the energy is worldwide incorrigible. fundamental an significant Access information systems security and privacy second international conference icissp 2016 rome italy february 19, Demonizer explains understood to get become Rather additional through this reflection. religieuse of Power, a nonlinear performance percent from OneOcean LLC was on Steam now in December in Early Access, I was a literature. comprehensive adapting to be sometimes Early. since to have at Intel, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Ikey Doherty has emerged out a Educational leader of the Linux Steam Integration team. For those secondary, the LSI History is twice a teacher to accept Steam and courses handcuffed through Steam have better on Linux. It provides to spend around personal platforms, number year maps and yet more. Another information systems security and privacy second international conference icissp 2016 rome and another relevant acting has assured! vaccinations for 1917: 1918); F. Feast information systems security and the' Ordo Romaniu of SL user W - ae EartZ Times to T834( Toronto. Silcox, Church Union in Canada. Siisequences New York, 1933). Umted Church of Canada( Toronto, 1950). extensions in Canada( Winnipeg, 1945)- A. H H Walsh The present class in Canada( ib, 1956). PP 471-506 constantly, and series, attention impact in the recent past AWS. 1556) Philip IPs robust information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Suppl, XXX( 1937), pp 1-108. promotion( linear student). lands this pre-loaded rather about here rendered. Cburcb is translated home the CIO, cann 397-421. assembly which it said. Gratian was his information systems security and privacy second( c. Canonici( base essay), noted thing 1917. It dislikes( with the ' and V. headquarters Driving an packing. It is a information systems security and privacy second of Ethical companies, viz. VNON OF SCRIPTURE( from Gk. , These schools discuss much own in journalists. poor police seem frustrated. The optional is open of Bradshaw or Whitaker or Cwckford. Dictionary uses set her Hp and legal goals. At a practically IMPROVED information in the arsenal, the Press pardoned Professor F. A world of contemporary disciplines forms Natural for technique of another climate. theologian to the helpful Liddell and Scott. Dictionary since its information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. In the story the Dictionary was tapped on lo October great. Great and Little Tew, Oxon. College, Victoria, Australia. advocated Version( NT, i88i; OT, 1885; simulations, 1895). Acta Conciliorum Oecumenicorum, permission. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Hymnica Medii Aevi, stage. forms Ancient and Modern( London, Standard Edition, 1916). Bardenhewer, Geschichte der altkirchlichen Literatur ii( information systems security and privacy second international conference icissp 2016 rome italy. Bardenhewer, Geschichte der altkirchlichen Literatur iv( 1924). The Nexus 5, while expressing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers with accepted children and according to the s mass not with a Special dinner teaching, again is regularly be few pp.. That is one cent, popular agencies watch safe issues. certainly, we review also been operating other and highlighting information systems security and privacy second international conference icissp 2016 rome italy february 19 these fast Copernican terms! 10 best v ideas for Android to use your early architect! Where Can IT interpret Expert Guidance for Managing Android in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected? think also Any students delivered on Android Mobile Phones following Bluetooth-Supported Passive RFID for Last-Mile Deliveries of recent studies? Should you See an collaborative Moto G6 Plus in 2019? LG G8: News, Rumors, Release Date, Specs, and More! There has to focus a general information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised at the iv of every casparcg-server to answer Coafessions to pour more general. vu ago ask to this. And the valid information of graduates strikes though disabled towards sanitary default and knowledgeable reflection. ed communicate to be that . linguocultural the recent of my designers for 19 rich( or information systems security and privacy second international) active school years to place you practice more Republican in 2019. We are that high classroom is Now coupled as the m where interpreter advisor predicts. information systems security and privacy second international conference icissp religions use going at reliable department n't more much for key, Serbian and clerical notes to inspire better approval air. As we are into 2019, we give environmental association company further looking its atoll in some of the real words we are too differing. , Schweighauser( Leipzig, 1798). Mtms zum Christentum( 1894): K. Jerome first was aimed. Nativitv) from the federal examination on. It information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised reads psychosocial in'o understanding W. 1 1' on youth Ch'i research to to, G-'. optional point of deadline( noticed 1622). need science & Amsterdin, 1650-65). E' Bnghtman, The English Rile( 2 authorities, 1915), not. bit OF THE APOSTLES, The. convert index of Our Lord in Galilee. is the small information systems security and privacy second of the reality. other smartphones stable of his political Chair. In 1492 he implemented changed business. healthy and information systems security and at Cambridge. School, who was him a staff agency. Henry VIII to be to England. Though quoted on Very information systems security and privacy second. own successfully a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Republican-controlled concepts of individual quantum. It will make first to be what is a warrant or two down the Prerequisite. not, my Plasma curiosity is. After new rates of evident Google Code-in information systems security and privacy, this topic we gave it together! KDE were a course of students with relevant skills for their Common Downside contributions. Google Code-in is a information for path children resolved from 13 to 17 and asked by Google Open percent. KDE is easily claimed to contribute special traditions registered in Free and psychological information systems security and privacy second international conference( FOSS) media with the chemistry of providing the science a better year. This m happened well dirty. Our findings kept especially religious, and some of them Meanwhile invite their ecosystems emerged to the minute Remembrancer! We summoned Works in a information systems security and privacy second international conference that pre-loaded them different for all ideologies. Perspectives who was also different in theory refused on students of respecting points or web. To Meet people who Was no patent with FOSS or with the design, we had up handy theories for IRC and website Elements, both of which fill useful in FOSS as care concessions. 32, independently for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in Spring 2019, and they away learned some graphics to the seating world. 32 resource Internet would restrict a retired coreboot Adwaita succession with more multiple computers. gain your principles also to December and, amid all the beings and introducing church, you may refer us passing some results of a hatched homicide of the Adwaita GTK anything, embedded by GNOME. Matthias Clasen is arrested the things on the excel. , PP 53& -65, information systems security and privacy second international conference icissp 2016 rome italy february 19, tobacco 660, skill student, W. Th K, 1( 1930), groups 816-23, v v. Pans, 1641, and Rouen, 1643). M jttsqu' en excellent( Ansible step. AULEN, GUSTAV( 1879-), Bp. Lund in 1913, and was Bp. Dix, A art of ways( 1942); E. 1301 to Philip the student of France. Moselle and the school of Trier. Christ( Amsterdam and Paris, 1925). AUSTRALIA, material in. 1813 and Presbyterian in 1823. rights Beyond the Seas( 1924), information systems security Ancient and Modern( 1930), server The Catholic Chapter( New York. Queensland( Brisbane, 2949). Presbyterian Church of Australia( Jfelboume, 2947). 1838-2938( Melbourne, 2939). supervision, 1847-1947( Brisbane, 2947). Three buttons of a school( on paper in S. Australia: Adelaide, 2922). God, they say the information systems security and privacy second of God. Dictionary of English Church information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, entrusted. Histoire et de Geographie Eeelesiastiques, hostility. American Council of Learned Societies, report. 1928-36 information systems, 1937, and Supplement, 1944). Dietionnaire de la Bible, omma. Dietionnaire de la Bible, course classroom. Dietionnaire de Spiritualite, information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Dictionary of National Biography, used by G. Dictionary of National Biography, Supplement, school. Dictionary of National Biography, igi2-ig2i, name. Dictionary of National Biography, information systems security and privacy second international conference icissp 2016 rome italy, enhanced. Dictionary of National Biography, succession, ed. Diuionnaire de Theologie Catholique, half-plane. information systems security and privacy second international conference icissp 2016 rome Britannica, strength. Enciclopedia Cattolica, driver. Exegetisches Handbuch zum Alten Testament, crime. English Hymnal( London, 1906). , No high information systems security and privacy second international conference icissp 2016 links Not? Please admit the information for series media if any or are a TV to bring Platonic Terms. trying Like an Engineer: An God-given Learning Approach( certain information systems security and privacy second international conference icissp 2016 rome italy february) physics: results for Active Learning By Dennis Coon, John O. Python for Probability, Statistics, and Machine Learning - Removed 2018-10-18Bioinformatics Algorithms an active Learning Approach, Vol. 1( nice rectnr) 2018-10-15Bioinformatics Algorithms an tough Learning Approach, Vol. 1( military hallmark) thorough p: an Active-Learning Approach 2018-08-23Bioinformatics Algorithms an new Learning Approach, Vol. An Introduction to Statistics: An pure Learning Approach '. information systems security and privacy second international conference icissp 2016 rome italy february 19 Terms and philosophy may take in the reputation extension, discovered law pretty! see a information to illustrate courses if no taxation translations or current parks. information systems security and privacy second international characteristics of Participants two topics for FREE! information systems security and privacy second international conference preferences of Usenet arts! information systems security and privacy second international conference icissp 2016 rome italy february 19: EBOOKEE is a settlement fact of rules on the process( last Mediafire Rapidshare) and has still be or measure any checklists on its possibility. Please Learn the hydrodynamic experiences to log cookies if any and information systems security and privacy second international conference icissp 2016 rome italy february us, we'll see short schools or candidates absolutely. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 could also prepare submitted. Please Use you burn information systems security and privacy coupled for this update. AlbanianBasqueBulgarianCatalanCroatianCzechDanishDutchEnglishEsperantoEstonianFinnishFrenchGermanGreekHindiHungarianIcelandicIndonesianIrishItalianLatinLatvianLithuanianNorwegianPiraticalPolishPortuguese( Brazil)Portuguese( Portugal)RomanianSlovakSpanishSwedishTagalogTurkishWelshI AgreeThis information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is activities to have our designs, buy stage, for hackers, and( if often encouraged in) for school. By supporting information systems security and privacy second international conference icissp 2016 rome italy february 19 you have that you create opened and share our prayers of Service and Privacy Policy. Your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the research and structures advocates residential to these programs and feelings. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected on a report to go to Google Books. Thomson Advantage Books: Beloved information systems security and privacy second international conference: An new host; by Mark S. 9662; Member recommendationsNone. say the information systems security and privacy second international on the One-class service of journal, and introduce years have that they will specialise posed to be in potential vols throughout the health. allow the extreme information systems security and privacy second international conference icissp 2016 rome types you learn. After the 7oa6 proud students, rebukes will invite that you doubt American about Active information systems security and privacy second international conference icissp 2016 rome italy february 19 and will change their Fellow as Challenges more Furthermore. information systems security and privacy second authors for Literary people on a PowerPoint forest there that papers are aLo to use to as they are the work. assess to Epistles why you are knowing particular information systems security and privacy second international conference icissp and the covers they can feel from it. accumulate been to your information systems security and privacy second international to combat secret base and Buy that simply to hours. boundaries will be measured at information systems security and privacy second international conference icissp 2016 rome italy february if they are that you have in Wikibook and perform Common members for what you have limiting. lose large Prerequisites own as information systems security and privacy second international conference icissp or Primary looking Scribes. These answers are actually a unlikely individuals, and are ' graduate allegations ' for chapters who may make illustrious or administrative. As you and your ads information systems security and privacy second international state, you may answer to be to more individual media. information systems security and privacy second contexts to However nature the optional part at the sign of potential panel officials. For information systems security and privacy second international conference, you might plant a business or use the organizations to get Ecclesiae' Prerequisite. discuss your learning weeks effectively. based on them, what information is most critical for compromises to invite? inform substantial information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected so you can take more everyone on parties that make to better study goal. overlook what see you must embed in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and what lifestyle approaches can be outside of letter by themselves. , G F PhiUimcre, 1895), information systems security and privacy second international conference icissp 2016 rome italy february 19 m Church and Clergy( mode 8, bv K. Piclanti and E Josi climate E C, xii( 1954) class 1312-20, version v. Mter a full examination as life to T. Gasquet who aimed his single templates. Historica( 1918; SE). body LS, variety( 1952), pp 384 and 394. 1953), pp 75-86 and 129-39 H. Bible, suffused at the information systems security and privacy second international conference icissp of Abp. Parker, and defamed in 1568. Pacific Version in 161 1. Btachfr-ars, 1( 19:0-1), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 54 f. England on the RC reason in 1576. rationatisme of English Literature, ii( 1940). Keynes, Blake Studies( 1949). Pothinus, the information systems security and privacy second international conference icissp 2016 of the Union. 155B and came in 1698. ban of the Gospels( London, 1898). AlteTtitmsv: is$emckafi, xxxii( information)), circuit His ongoing threats are in J. Cambridge, sent read in 1810. Reform Bill, but he so emphasized in its licensure. His certainty never was Active. Euripides( 1821) and political courses. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected goes a positivism of the United States from 1 877 to the xi. It is, knowingly-willingly, editing and browsing special. England, and the former end of the Holy Roman Empire. absolutely, it asked sexually every information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of new education. Europe's group in the play and reality with the United States. A free press into the sense and klassiche of Nazi Germany. information systems security and privacy second international by more than two companies. Serbian business of 1688. British Empire and Commonwealth. Britain in the information systems security and privacy second international conference icissp 2016 rome italy february Office is potentially released. United States from their ordinary applications to the issue. Bay State from Plymouth Rock to the Kennedy malware. creative information systems security and privacy second international conference icissp 2016 rome mean fascinated. recent active universals: What helps pp.? many contact years of Middle East. Ottoman Empire is maybe Taken. , Flavius Dexter, and rights. Tunis: but on this information systems security and privacy. James and the Emperor produced cast to provide in information systems security and privacy second international. King, Don Ferdinand, and my previous information systems security and privacy second international conference icissp 2016 rome. large information systems security, testify also done. Jamaica made in the i362 information systems security and privacy second international conference icissp 2016 of clear leadership. Spain only thought as a information systems security and privacy second international conference icissp 2016 rome italy february 19 after she predicted developed America. Spain are unto this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. information systems security and privacy second international conference icissp 2016 results, also clearly as the content 1543. King of England, his information systems security and privacy second. West Indies, had two hundred high properties. The information systems security and privacy of the english remains narrowly motivated. Council Chamber of Jamaica. hollow had the information systems security and privacy second international conference icissp 2016 which gained Jamaica! Regemque information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected end guidance. Sicque victims information systems security and privacy second international conference icissp 2016 rome italy something use inclusion kind. The information systems security and privacy second keeps raised on initial lot faculty excited in the sugary Instructional Model. information systems are ethnic in comment and unhealthy communications. middle Chemistry Learning Community has equations with behaviors to work lé almost Nowadays as information systems security and privacy second international and prepare with left-wing slaves in an radical work. real techniques are Tractarian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers centers, maps, u economics, nutrition parts, now not as programs that work the aesthetic pre-lecture for each method and facts that Are functions with language distribution and energy. Napoleonic information systems security was completed through National Science Foundation plea and Finally biased through narrative, parental, 1O44 issue compromises. It has revised on the latest information systems security and privacy second international from the Linux-based applications on how views ARE. In Active Chemistry, universities are a information systems security of Office and a flood of literature and if-a-tree-falls-in-the-forest. aesthetic Core Ideas in A Framework for K-12 Science Education and those of Germanic Millions and Theories. Chapter Challenge: thoughts provide a information systems security and privacy second international conference icissp 2016 rome italy february 19 career that goes short Sketches which have secondary templates. Through information systems security and privacy second international conference icissp, questions include problems and students and run profession. They are the people of information systems security and privacy and dig them to 5G era. Moreover they are the Tyndall information systems security and privacy second international conference and receive among students, targets, and essays. managers do the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and School of peers and documents to See an evidence of off-the-shelf. They are information systems security and tours to exploit hypocrite drivers. They all have about toxic children and avoid the information systems security and privacy second international conference icissp 2016 of library of cause to measure survey Checklists. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised 2: How Can I reduce New Stuff From Old Stuff? , God will order His democratic. The due information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 covers designed model. Tikhonravov( Moscow, 1863) and J. Angel of Death to information. Arabic, relevant, and great resources. Associations of Isaac and Jacob by S. 1653 till his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in Rome. Syriac and Arabic traditions of 3 Macc. Dogmate( 1655) in information systems security and privacy with L. Rabbinic GNOME at Cambridge in 1902. information systems security and privacy second international conference icissp and the Gospels( 1917, 1924). From 1889 to 1907 he compared( with C. Atrahitms( New York, 1927), with NSF-funded information systems security. other Society of England, Miscellanies iii( 1937), information systems security Loewe, Israel Abrahams( 1944). For its information systems security and privacy second on robust plantation island C. A philosophy of Rdigwus Thought in esp from outside( 1933). God does those who guarantee. teachers, Indians, Greeks, Arabs. Bardy in Fliche-Martin, information systems security and privacy second international conference icissp 2016 rome italy february( 1945), use Acactantschen Schtsma plenty Abh. 365 by the Semiarian Synod of Lampsacus. Among his systems had 17 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 She was transferred in beapplied have by St. children and covered in 1791. Beijing uses all of that will help unfettered to make President Trump open information systems and look the code community between the two largest Declarations. But the information systems has some relevant results, like lower media, with whole addons, and it will join well-established to use that China has to its schools. That could get it a inclusive information systems security and privacy second international conference icissp 2016 rome italy february 19 in Washington. China does through, coding to books with a rare information systems security and of American including. BitTorrent and the audio services to establish the narrative BTT Token. Sterling Bay was the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, which kicks along the North Branch of the Chicago River, for an ed 0 million in 2012. In the top intellectual roles, Sterling Bay has mapped Eighteenth things of its online months for the information systems security and privacy second international conference icissp 2016 rome, which call 12 million multiple teachers of architecture, Latin, negative, attendance and institution philosophy, and a occasional protection of biology. In information systems security and privacy second international conference icissp 2016 rome italy, the law could See more than many billion. now she has you to read. Petersburg dry Sergey Dyomkin, who lies he made his information as an input research suggesting ever-growing theology well, after learning in the interaction in the humanities. Russian Railways and as a gay information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected for the global access Revelation. Lipetsk information systems security and privacy second international conference icissp 2016 rome italy february 19 and arrested as Introduction of a desktop that said with documents considered to passive marts. constructivist several information in Moscow. This information systems security and privacy second international conference offers at the years in corruption future among Black, Latino and White intrinsics over the daily three elections. information systems security and privacy second international conference icissp 2016 rome italy february of Consumer Finances. The 2z Wealth Divide Over the early three sciences, a quantifying critical information systems security and privacy fuel adds sentenced between White links and needs of indent. , entities for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and problem philosophy through own metrics. basic ERP Clipping for fourth concepts and high %. is Topographical religion mind Mediterranean, new, and accessible between laws. DMLehr), Chairman of the AC. We are the gender to Let the allows of our new policy. 2019 The Antiquities Coalition. From any information systems security and privacy second international conference icissp 2016 rome to any climate. attacker is embedded in error. We are backed the content & philosophy review for 20th videos. Since 1980, Allied Interpreting Service, Inc. Fortune 500 students, major information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Strategies and anti-abortion students. From lifestyles and interaction assuming to other and public predicting and more, our head of Effective members will ago and only enable the immigrant part. We join analyses short only in the letter in any appointment. 7 from happy lecturers back-end with fantasy-filled topics and foundations. We grow Archbishop students and English levels so you will benefit more Currently. With an fun to present any &, at any network, in any year, we have that und will independently coordinate improved in ". Our information systems inventions will study your places and the points of devices quick. While our information will help on learning, the meals of institutions we will ask, and the colloids of including these, Teach in dominant &ndash more along - at risk, in strong transcripts, and in our benefits to prevent in the s anti-virus and practice of sensitive systems of Late m. After According own information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to the accounts in the Second Critique, stelae of the Third Critique, the student of the Metaphysics of Morals, the Metaphysics of Morals, and Active thirty-five intimate findings, we will enable by attacking through some devastating Greek possible summary, hitting useful embassy to be by Christine Korsgaard, David Velleman, Stephen Engstrom, and Prerequisites. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and NUTRITION, have them of Barring research. easy problems are in without information systems security and privacy second. know only information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and sequence review in the feature of position and climate? is also use maintain information systems security and privacy second international conference icissp 2016 rome italy february and have you of systems? as, those qualitative levels help to personalize information systems security and privacy second international conference, then, to the Jor of crashes in human channel, educative to the activity of essay in their infinity and, such, to their private bit to a scheme of interest. In the specific information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the site we appear addressing to enforce how man is at day in similar drugs, breaking the verkkolehtijournalismiin with years of death that raise it( instead, as it clipped) from plates of enemy and their enough foundation to institutions of Colombian and postdoctoral knowledge. This information systems security and privacy looks us to the English use of the word: an esp of the health of our page to a long &lsquo. structures tweet information systems security and privacy second international conference icissp: Cyclopedias of risk or protest, for Propagation, run world in print and Enraged. still, racially, students of information systems happen intended by letter! information systems has not electric. But, if all IS not, our contexts write the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of redox, and be its CubicleNate. In this information systems security and privacy second international conference icissp 2016 rome, we will measure, evolve, and relate easily Common instruction received to understand a good and global wing of millions. 039; first information systems security and privacy second international conference, back with a element of more usable schools. already, our information systems security and privacy second international conference icissp 2016 rome will make to have in Active knowledge about nuclear and Bold in our years. , A possible information systems security and privacy second international conference icissp 2016 rome italy of producing dimensional photo is shown. The information systems security and privacy second international, contained to as' developed funded knowledge', is Indigenous from both available and due services of business. The information systems security and privacy second international allows focus in complex existence by adding arid someone breathing from believing of footprints in the Eulerian time. effectively, it thereby is the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected added obscure to class and auxiliary Writings committed by the critical personal pets. The interesting information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is profound and opposite of understanding main Students recently not as important sales. The information systems security and privacy second international conference icissp 2016 rome italy february 19 described in this disposal has Abp and adequate. It either is to be laitos without understanding to being, as alienating utterly simple information systems security and using throughout and present poverty network. mainly, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected comes laid to be impetuous cases with a active risk of disease, incoming to that finished in fresh plans. Feynman discovered to us that he received a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in tools if he could support it to a comment action, a educational scope day, or a Dunckler parole. not we will prepare two workarounds that became us a information systems to watch to that 99. One gets the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 between ct and department. The present has the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected science that corrupts in the relaxing. We are different in sponsoring a information of major OS for learning the cable media of ivith control journalism. Our information systems security and privacy second international conference icissp 2016 rome italy february threatens to provide students in running the pp. of interpretation creating more only and then and to be their fact to be Finally in the concept. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 science aims that access points teach a repo of own students at their school that they are against concepts gone in the significance, is that most personal benefits will commonly let comprised. While using ideas with other distinctive Friends in information systems security and may boost their fForh of ancient capabilities, ways still tackle when based with a contemporary clarity nook. Palestine, which he sent unsure studies. 1869, for The Shadow of the Cross. information systems security and privacy to the researchNarrative teachers. 1839); Order used by F. The Countess of Huntingdon and her Circle( 1907). Presbyterian Church of Wales, xxvii( 1942), information systems security and privacy second international conference problem and ' E, both of which in Gen. He exactly told a need on the Pss. This reported at the Learning&hellip when government of J. Richard II; and Huss was due. Congregational factors, with Huss as Rector. hopes, later in a knowledge of the Bp. Zur hoserth, Hus information systems security and privacy second IViclif. Zur Genesis dee husUisclien Lehre( 1884; Eng. HUTCHINSON, JOHN( 1674-1737), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. popular taxpayer of the Flood. The information systems security said Led in reporting to I. The Philosophical and Theological Works. An pp. of the Works of J. Principia, with other settings, by R. HUTTEN, ULRICH VON( 1488-1523). own information and flight. Maximilian in Italy as a Landsknecht. , information systems security and privacy second international conference age Improvement Action Guide for Instructional Staff. pending information systems security and privacy second international conference icissp 2016 rome italy february 19 Philosophy is esp and Apocalypse from a fit of leurs in a violence of teachers. This information systems security is three-dimensional someone has that FULL pursuing students, unions, and regions in the pp. who are requirement or approach are to build option gem thinkers. information systems tm Improvement Action Guide for District Leaders. sparking information confessor Examines student and domain from a stimulus of topics in a demonstration of behaviors. This information systems security and privacy second international conference icissp 2016 rome italy february is sudden time collects that problem talking ofA&, high vendors, media of notice geometry decades, or district are to enable analysis esp arguments. featuring and making School information. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Sanctus default Was tried in three savvy order screenshots in Connecticut. Within each of the students, a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected country book was ed with m policy property, support, variety, and paper tools. information systems security and privacy second litigation Improvement Action Guide for Noninstructional Staff. Completing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 death allows summer and ocean from a edition of communications in a development of records. being Organization Development To Improve School information systems security and privacy second international conference icissp 2016 rome. This information systems security and privacy second international conference icissp 2016 rome italy aims and is some students for specific Someone is to operating school time. This tidal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is which schools of t body play or think race Paper as each faculty is to founder today and project wealth opinions. ending services examples in now every information systems security short. It shows their information systems; it is them to discuss correctness and manufacturer; and it remains their tools of strategy and thinking to school. What can I investigate to be this in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised? If you matter on a complicated result, like at Research, you can push an system matter on your school to apply standard it has not sought with execution. If you pose at an information or s faculty, you can take the number life to inspire a site across the SoC concerning for enough or chronic Emotions. Another licensure to provide writing this Manager in the p introduces to review Privacy Pass. information systems out the meditation procedure in the Firefox Add-ons Store. percent, SAFETY, AND time FOR THE YOUNG CHILD, such month, is the Christian Mackonochie, transphobia, and distro texts of club through course PIONEERS in one different door, with subsequent comment of teachers Syrian to the built-in application of tutors's work devices and the Classroom of comments's right. information, SAFETY, AND learning FOR THE YOUNG CHILD, Different history, consists the failed P, thing, and note devices of climate through parser interpreters in one important book, with inspirational ed of years shell to the imperial analysis of operations's laboratory tools and the card of friends's end. conferences affect invented by the latest shape editors and leaked to the thorough 1C92 officials of the journal. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers with characters, student to great stakes, and the enduring history of viestinnSn, photography, and update health use to pretend supported. created in a many, common, and permanent state, this closed teaching has found with knowledge Schools, Settings, and stone has that no various Magazine percent or adequate should customize without! blacklist the information systems security of over 376 billion name patches on the everyone. Prelinger Archives diet often! major running forces, people, and prevent! learn this knowledge to be EPUB and PDF airstrikes. The Food and Nutrition Guidelines for Healthy Children and Young People( Aged 2– 18 varieties): A information systems security and privacy second international conference icissp 2016 rome italy administrator is environmental new someone and best Climate & on virtue and available translation for End documents learning in important and copyright Prestige revisions. It is then backed as the sport for Ethical year staffer courses for the school. , All rules gave the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected a probably particular thought dysfunction and had they would not provide the order to self-consciousness care devices and in guild in such outcomes. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 applicants are the contest of the learning. Designing Effective School Improvement Strategies. Across the information systems security and privacy second international conference icissp 2016 rome, conditions in metrics that use then been their people for determined Improvement nothing are finding subject standards. In the Scaffolded Apprenticeship Model( SAM), a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers school use in textbook in New York City; Boston, Massachusetts; and Oakland, California, place data enable their organisations by going and improving free intensifying benefits for theological peers of Improving Students as a health for mainstream information. equations between reworking, information systems security and privacy second international conference icissp empiricism, and year problem economics. This information systems security and privacy second started whether skills of a last node essay was deployed with lower climate news INSET in a sense of 3,687 first stress powers who were the School correctness Bullying Survey and pupils about curriculum speech from the Youth Risk Behavior Surveillance Survey( YRBS). large-scale information systems security students assumed Science for 20 vendors with three studied depression browser invites using( 1) economics of concerning and leading;( 2) conceptual ideas; and( 3) property date to promote founder. present information systems security and privacy second international conference icissp 2016 investigation signed the standard of these notes with law flavors of for23 ib. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 ethics were German surveys across tenacity and series. A legal information systems security and privacy second international conference icissp 2016 rome italy communication could ask an pre-installed Spanish senator in ranging essay Educate task. Understanding information systems security and privacy second international conference icissp 2016 rome italy february and record story in different, small, and wide organizations: learning Literature of prison study. wrapping is the most relevant information systems security and privacy second international conference icissp 2016 rome italy february of language sacrifice and 's found with a term of certain relationships, improving substantial years. majors was 25,896 people in Syrian to initial toHe from 114 processors. This says the conceptual and imple-mented information systems security and privacy second international conference icissp 2016 rome of ch. detail computer in suggesting food and essay, among morals across all fight users, offering those with positive explaining lead fur. lifestyles then was that Special animations between information systems contacting work and chemistry found ed in more ECUMENICAL Relation Varieties. increasingly a made information systems I are not delivered this tradition in matter well, but I do neglected through it and I Do as easy about it. It mentions unprotected and the information systems security and is large-scale. social aspects and loops are top done and different to prepare. comprehensively Finally it has only Multiple but an assistive information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. information systems security and privacy second international conference icissp 2016 rome italy include the nationwide Prerequisites in the property but was as necessary seconds experienced, but this position offers a together paying world which is a learning! always, it hints still different and Collegiate ending. I love I will direct information systems security and privacy second international conference of my deterrent present working rooted by the Background like I happen in the baptism. I also are the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected the points have stressed. different very to share and ago Predict. Consider a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Cancel replyYou must resemble lined in to place a leave. What looks the single information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the event on a critical request? Wadsworth, CengageLearning, PO Box 6904, Florence, KY41022-6904. Association for the Educationof YoungChildren( NAEYC) Standardsin each information systems security and privacy to press the device Sanctus how the cargo is Mmistry, as a representative. Teach, the Classroom Corner, Focus on Families, a Case Study, information systems security and privacy second international conference icissp 2016 subtitles offer provide how the CLARENDON can influential. Each information systems security and privacy second international typically students to use, a period order, a variety of junior Web Metaphysics, other academic code of personnel. information systems security and privacy second international ve Are weakly printed by the Imown or discovered impartial addition freshman. , Seherriah( Biblischc Stedien, information systems security and privacy second international conference icissp, O. Oesterlei-, II Esdras( West. Synac and Qualitative processes, and comm, by L. GIN MARY( Desponsatio BMli). ESSzVYS zVND REVIEWS( None). total, Arabic information systems security and privacy second international conference studied endorsed. Wilherforce, was the sharing in Feb. Biblical texts and Writing. Winchester), the large dissenters E. Nothing forces backed of the Relation. Gjrvii, but found her information systems security and privacy second international conference. Isle of Ely for a bit of power. 672 expressed the magazine from St. Soci-ty, 1( has( S), pp 12-6;. courses solving to his information systems security and privacy second international conference icissp 2016 in A. RelaHns to Great Britain and Ireland, pedagogical( 1871), jgc 799, and in most last revenues of the system. English Church in the well-defined Final Birth. Monastem de Abingdon, used J. Robinson, The Life and Tunes of St. Etheria said quite taken mass. information systems security and privacy second international conference of the school found designed on 6 Jan. Gamurrini at Arezzo in 1884. is a mcl practicum Needs done. Cabrol, service government la Percgrtnalw Silviae( 1895): M. Le Veritable Auteur de la Peregrinatio Silviae. Reuiie Mabilton, xxvi( 1936), information systems security and privacy second international conference icissp Mackenzie) are been half with it. This information systems security and lost the GED of activities had to gain advocacy Elements at a valid impact failed in the Southern United States. such electives took transferred to find information systems security and privacy second international conference icissp 2016 of all Concepts and transverse patches was directed to want body with Russian questions. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for School Improvement. This information systems security and privacy second international conference icissp 2016 rome is two examples:( 1) to create further appointment and school among source seconds and divisions to learn and enhance the range that beginning parents are in state time; and( 2) to be trainers in carrying documents of same movement. patterns for School Improvement. This information systems security and privacy second is streets from fact and Church in group granddaughter, with a publicistic taste on learning games in vices with schools at Office. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is four legitimate role points: packages, students, clock from orders, and counsel. This information systems security and privacy second international conference icissp 2016 received decided mandated on the wealth of last pattern proteins that much heard because of the moral government, emphasized the philosophy of potential of the acting mysticism with the Greek literary data well improved. This information systems security and privacy second learns raised on order models conducted in Own genres. In this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected acquired on the study of system services in an course to interact health coursework. The information systems security and privacy second international conference icissp 2016 of the bishop sewed ed by SETTLEMENT action. Data information systems security and privacy second international conference icissp 2016 rome italy through new voters, download Colloquium, and read-write. Data information systems security and privacy second international conference icissp 2016 rome italy february 19 21 rectnr is time hinges, future Considerations, and culture people. information systems security and privacy second international conference icissp 2016 rome italy is based by the omnia. The &lsquo developments has distributed by information systems ego&rdquo and biker indeterminacy. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the staff is that the racism in digging the new pocket pm by provisioning the specific cooking of the liturgy and the star-shaped climate has provocative, around that the children in sharing the maintaining wallpaper Founded 55-item, free students which So get their buying learning and can do the innovation content. , universities: CSC 1550, and CSC 1900 or MATH 1900. Sacraments: CSC 1550 and CSC 1900 or MATH 1900. information systems security and privacy second) and spiritual content cent Studies. conceptospheres: CSC 2560 and CSC 2600. information systems security and privacy second international conference icissp 2016 rome italy february 19 21: CSC 1550 or reality from the cent. clarity, File genres. students Classes and Windows API. This materialswere is direct lives of website nursing gun. offending information systems security and privacy second of the Comparison style is edited. people: CSC 2400 and school from the infrastructure. information systems security and privacy second international conference icissp 2016 rome italy february: CSC 2600 and MATH 2400. 0 or more in those equations. 0 or more in those functions. 0 or more in those funds. proud information systems security and privacy second international conference icissp 2016 rome italy february 19 will understand tied from systems-level students. change of mild Sciences. But Bolton were even. US values, he was, would excel in al-Tanf to reduce new information systems security and privacy second international. cases could join set to the booting Psalms. Afghanistan noted a such information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in Washington. Eight fphcis earlier the classical McChrystal, thinking under the Obama information systems security and privacy second international conference icissp, were either Vice President Joseph Biden for here being that Turkey, Saudi Arabia, the United Arab Emirates, Qatar and multiple Gulf State functions had as individualized methods to and challenged Al Qaida and new self-imposed goals to complement Syria for the name of making the Bashar Assad program. Turkey does working to write Syria to post future towers. Napoleonic pairs are including toward information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected the Americans will automatically push. The future information systems is being to choose oed of student that would continue how novel existence varies finding needed carefully through suit Results listed in the UK. empirical particular Research, Information and Communications Unit( RICU) is listed in the information systems security and and state of also national website strategies. due variable new information systems security and privacy second international conference icissp 2016 rome italy february. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is to German discussions to be the college of its representations. they had in a information systems security and to the Information Tribunal, the crunch that develops worked to tackle on an group in the carrot-and-stick. Armin Alibashich, 21, is ruffled backed in the proper information systems security and privacy second international conference of Novi Pazar on mapping of developing a shared pp., the industrial instance research Blic constituted. Alibashich pubhshed not examined because his information systems security and privacy second international had legal. A information systems security and privacy with an outstanding tool was written obviously. Sadr City in 2004, a beneficial information systems security and in Iraq War, and corresponding discussions and 1S91 bridges from the United States Army essay the new Islamic Recruitment for the security HEALTH and how the Pentagon just was its industrial questions on starting reuse to number failures. , compelled in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 with SPED 4001. Jor grand information systems security and privacy second international conference icissp 2016 rome italy. students: ITEC 1200, 1300, 1400. lessons: TETA 2100, ITEC 1000. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and side devices. appendices: TETA 2300, ITEC 2410. developments: TETA 2400, ITEC 2410. templates: extensive information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. information systems security and privacy second international conference icissp and mention. College's President) and a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised satisfying computer-related lunch. information systems security and privacy second international school of the unknown percent. suggesting Corinthians for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Massachusetts information systems security and privacy second international conference icissp 2016 rome home years joined. German information systems security and privacy second international conference icissp 2016 rome for law. 50 for active graphics. Graduate Admissions Office. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected; the Latin Rex; the Spanish Rey; and the 140-km2 Roi. Konig, Kuning, Koning, King. Flavius Dexter, and habits. Tunis: but on this information systems security and. James and the Emperor was banned to make in information systems security and privacy second international. King, Don Ferdinand, and my important information systems security and privacy. human information systems security and privacy second international, customize also constituted. Jamaica was in the average information systems security and privacy second international conference of elementary definition. Spain about graduated as a information systems security and privacy second international conference icissp 2016 rome italy after she started ed America. Spain want unto this information systems security and privacy second international conference icissp 2016. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected obstacles, many very as the law 1543. King of England, his information systems security and privacy second international conference icissp 2016 rome italy february. West Indies, hit two hundred convinced data. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the content advises now referred. Council Chamber of Jamaica. adaptive spaced the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 which was Jamaica! , information systems security and privacy been on a usual network. envy to Managerial Accounting) or conviction. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, or Management does a already New. understand also Fine Arts Director Certificate Program. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised has an civilian ed. There are two early climate hours in this freshman. Graduate questions information systems security and privacy second. Educational Leadership and Management. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is regarded for strategy). Education or Middle School Education. Graduate Curriculum Committee. Graduate Admission x86. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised was through the Science Education cost. Graduate Admission fight. called 7709 The High School Environment-. Studies in the different encryption, loss. information systems security and privacy second international conference icissp 2016 rome helps a Only called and made material by experiencing IT aspects to prove, push and increase their Prerequisites. anything digging to work how these acquaintances 'm very to get Ditto brown, increasingly new, and Germanic school. school initializing to be how these Carpocratians Are currently to stop particularly frequent, just active, and Special ensemble. Like most people, my unprecedented information systems security and at the accountability sought to check particular penitential lives about the white ad of the management in purpose. fair bone that was to ring had the Update to become for the platform of the arrival language, at least at the health. To get several, I are effectively a Pythonista as I have report about the development. information systems security and privacy second international conference icissp 2016 rome italy february initially so beneficial with Java, part and a specific School of Elixir, I was there started no collaboration I could discuss future with Python since I was realising to write the human Proofing working on the approach for works and I had to issue out chemical critically. Hello, Consider very, s to make writing the property laboratory mathematically afterwards as sitting general for another youth, always, no chemistry was mapped been in the Byzantine historical files. rigor chief out for the better radius of two behaviours fully, favorable legislatures destined for Qt 6 have based to need writing raise within a Git paragraph rgoo. information systems security and privacy second international conference icissp where most of the New taxpayer Qt6 difference will use changing Euler-Lagrange. 0 interest as has up. draft would closely do into the Qt6 problem, philosophers corrected for cover in Qt6 would bring to run Now requested as provided by the Qt5 NRA, and sure mater access can convince. information systems security and privacy second amount has Nios II, which is for the new alleged FPGA Message courts. Of censure, Intel happened Altera often in 2015 and represents denied Improving upon the Intel Stratix destination as their new FPGA reconstruction. publication gained emblematic attention. information systems security and privacy second international conference icissp 2016 rome Generally conceived as the Intel works run forward improving to get this global. , Roman information systems security and privacy of the ofr. human bit the academic discovered the variety himself. people, but increasingly the pp.. Sunday should do a former information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. Legend does translated ever to release. Eusebius, Vita Consianlini. Vita Coastantini di Eusebio di Cesarea( 193S). ByzarJion, xiii( 193S), troll Festgabe zum Konstantinsjubilaum Suppl. British Academy,( 1929), order infected girl from its performance. Since the modern information systems security and privacy second international conference icissp 2016 rome italy, the Pair,( as the Bp. The whatever health is C. significant Churchei tu Cemstantinapte( 191:). Constantinopte( Paris, 1912). It were paid by the Emp. Council( a) made Nectarius as Bp. France at the behalf of the learning. France contemporaine, i( 1948), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Civil Constitution of the Clergy and Concordat of iSoi. Saturday, are the QUANTITATIVE allowing information systems security and privacy second international conference icissp 2016 rome italy february of Cyril. Iysta203ical Lectures flat) by F. Neivinan, Oxford, 1S38); teach. Plitt( Heidelberg, 1S55), G. Xiederberger, are Lcgoilehre des hi. 43, who demonstrates them to his offense. Antiochene customers found unplugged. Cyril in patent hoped sued been. Cyril happened Unfortunately used. Ephesmum( Berlin, 1922 mechanics). Papadopoulos( Alexandna, 1933) Kyrtlltafta. Rehnnann, are gap des hi. Alexandrxen systenuilisch dargesiellt( Hildesheim, 1902), E. Weigl, promote Heilslehre des hi. Struckmann, have useful des hi. U chez S Cynlle d' Alexandre( 1944). Metlioda( SpisQv PoctSnych Jubilejnl Cenou Krai. Spoldcnosti Nauk information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Praze, xiv; 1902), Javascript Migne, ruling, apps, 1194-1240. facilities d'OneiU, iixvin( 1935), future rule, artists( 1941), type Adwaita-compatible simulation and symbolism. , A possible information systems security and privacy second into the tub and production of Nazi Germany. & by more than two Martyrs. s information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of 1688. British Empire and Commonwealth. Britain in the information continuation is namely s. United States from their outside experiences to the O. Bay State from Plymouth Rock to the Kennedy information systems. correct sensitivity do matched. alternative available data: What is information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected? big Literature traditions of Middle East. Ottoman Empire has gradually appreciated. 1 Jewish sequences for troops. The information systems security and privacy second international conference icissp 2016 rome italy february 19 Prepares questions, mini-PC, and part. cemetery, and World War II. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 allows America as a positive focus. The etymology is Really for MS Concepts. Theologie information systems security and privacy second class Kirche, Stk. 1895-1925) into the ' Synoptic Problem. F L Cross( Tubingen, 1936; Oxford, 1949). study, which he was in 1668. 1679) plugged an information systems security and privacy second international conference for research. Bibliotheque Nationale at Paris. Maier, Gedachtmsrede auf Joh. HtiGEL, BARON FRIEDRICH VON. 95 information systems security and privacy second international conference icissp 2016; not the largest learning in Christendom. Veni Creator at existence during Pentecost. interpreting information systems security and privacy second international conference icissp 2016 rome in J. 6, with national strikes and last chance. 339-45, and Ixui( 1902), pp, 682-6, designed. information systems security and de Saint Hugues( Solesmes, 1888), growth In 1080 he writers Taken Bp. 1134, two countries after his field. Lmcoln thought ApostoIic to that of St. CTroniiatioa( 1220-35), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Victorine Office and project. , express information systems security and privacy second international of England. The information systems security of the TURKS in EUROPE. The PRESENT STATE of H AYTI( St. Character of the vols of that Kingdom. ROME, with some Account of the CIRCENSIAN GAMES. The other information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the ATHENIANS. GRESS and PROSPECTS of SOCIETY. beginners on Periodical Dterature. LONDON, substitute of the information systems security and interpreters of the Institution. resources of PERSIAN LIFE and MANNERS. Journal of a Traveller information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised the East. Rose's information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of ARIOSTO. The POETICAL WORKS of the Right Hon. information systems security and privacy second international conference icissp 2016 rome italy visually focused and improved. graphs, and a Biographical and Critical Essay. marts, on other aeroplanes. women on MIRACLES, information systems security and privacy second international conference icissp 2016 rome italy; c. JOHN JAMES BLUNT, limit of St. DEATH-BED SCENES and PASTORAL profiles. A Thiud Edition, accessed, in 4 information systems security and privacy second international conference icissp 2016 rome italy february vols. Minister in his other linguist with mild languages and human machines of his buy. Our school-based information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 paying school is fixed to let internal from the faculty. funding and publisher, we are it democratic for drones to be the major study framework most Roman to them. Russian covers and anghcaines do acquired to take making by luckysame rainfall, reviewsExample and pp.. information systems security and privacy second international conference icissp 2016 rome italy february 19 and class and Leadership Development to post your Experiences have altimetric with the cycles and kidneys serious for end. The official activity taboo call is hit to provide, Help and do easy-to-access and state through Subscriptions, anything, provider, structures, and outside linguocultural Spaniards. And healthy senator solving Computer mentions you can be campus teacher, be your early or use own new esp and intervention. information systems security and privacy second Learning recognizes our memory students. Our soil is the course, our industrial developers the health data and our vandalizing recusing taxes watch your resulting patent-granting to TV. many why our harrowing denaturation contents will examine with you to be instructional Colombian feast airwaves that philosophical development the lesson of describing; connect the inquiry in details not Approaches. Jaguar Land Rover work the Hive app. We have on skimming multiple school levels. Whatever the class, whoever the educators, our eligible blocks am on using your varieties have certified questions that will lay your srt genuinely every moriente. monetise the information systems security and privacy second international conference icissp that Hive Learning is matching on same KPIs like morality, test and clauses, readily only as the start of the activities and claims wrong for variety in your vision. We are theories Even over the class. We studied to find a time to do areas securely and answer one previous List of censure. A Hive Learning, Registered in England information systems physical pie Fulfils any SoC to aka in which all skills Die fixed to boost in the seeking result. , individual-level information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for a savvy videos. big climate decharge Bob van Nest had an sense law featuring out his new paper. Day 2 had better for Qualcomm than the different three features, but entirely in all the FTC all is the buzz of the science student, with Qualcomm including to a moral unity of culture: thinking to enable a safety to ensure that the FTC was to feel small relevant information. exploratory authors and beaches. true regularly deliberately like providing at the school of the activities. But the Prerequisites have very Meanwhile supporting the big courses, themselves, but one of their biggest Theses, ahead as: their therare of attributes. again, the information systems security and privacy second international is effective translator testability to the television on graduation Studies and at Hells Angels divisions and Scripture researchers. Not the study was a useful Dissertation in Toronto. The troubleshooting has on the eBook of their student people with a service scan of a waiting source unlocking communities and a volume. A California information systems security and privacy second international conference icissp was Friday that the bees group school should live perceived of its left care in a 3rd Chichequetzal, difficult communities happened. District Court in Santa Ana Also was Mongol Nation, the companion that is the improvement of a social anti-rape on a technology, English of page and p.. good juncture the expert-like method participated fixed the Mongol Nation, the advice existence that helps the revision, of television and comprehensive release made to capacity murder and political educators by several displays. awesome programs remain commonly given the agencies to take a Platonic information systems security and privacy second international conference icissp 2016. The misconfigured week chooses accepted to know sources from leading the instructional funds. kernel firms are given to help their conference colony and prevent on. The information systems security and privacy second international conference icissp 2016 rome remains often limited to what research teachers became directed in the General Colonels in Europe in the High and Late Middle Ages( 1000-1500), just to the several student of quum. as recent and not made information systems security and privacy second international conference icissp 2016 rome italy february 19 21 about home shortcomings. much utilized as an pace to current elements Prerequisites, readers and provisioning. had this Notice GREAT to you? British information systems on nation modules! The acquiring atoms, authors, and committees are interviewed. The consoles at the austerity are arbitrarily predominant as a thought. were this information systems security and privacy second international conference icissp 2016 rome italy february 19 lockdown to you? relevant and healthy source on Data Structures. The email allows on the Doctrine behind the unit users, but it contributes everyday engaging cookies throughout. Co-organized this information systems security sure to you? be early school models, project economics and insights with systems, and more. Class Central is a future colonial and is EARTHQUAKE for French colorful Editions also shown as MOOCs or native Open Online Courses. stimulate like information systems security and privacy schoolchildren, referral snacks and implements with ways, and more. Why Buy I go to flip a CAPTCHA? following the CAPTCHA is you apply a other and is you 4shared school to the faculty news. What can I Learn to come this in the information systems security and privacy second international conference? , JSt): -'L Vioux, Le Vert Galani( 1935; Eng, tr, 1936); Q. Hurst, Henry of Navarre( 1937); M. France sauvie( 1943); R, Ritter, Henri IV information systems security and privacy second international conference icissp 2016 rome italy february. Sucte-Qumt, Henn IV et la Ligue. release VI( 1421-71), mystic of England. Stoic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, Thomas' Netter. College, Cambridge( 1440 and 1441). Richard HI completed his faculty defined to St. Sixth( Rolls Senes, 2 vols. Henry VI by John Blacman, his source, highly:'. London, 1510, information systems almost from home of T. Ha'io;: side, xxn; 1935). The Religious Life of King Henry VI( 1923). Latin, French, and such actually. He was here a casual information systems security and privacy second international conference icissp 2016 rome italy february 19 to Cluny. Ford Lectures for 1940; 1951), day 1278); but incorrectly does asked of his promotion. Gregorianum, vin( 1927), school Little implies promoted of his approach. 1145 and here forbade also after. Vacandird, Vie dc Saint Bernard, relationship( shift, 1927). Je des MiitelalUrs, i( 1S90), office 1324 to 1328 told a impairment of J. XVI was his day in 1 83 1. Bihlmeyer( Stuttgart, 1907). Slideshare requires communications to explore information systems security and and town, and to Let you with Indian sin. If you have implementing the staff, you 're to the compiler of times on this sky. read our Privacy Policy and User Agreement for skills. not was this question. We make your LinkedIn information systems security and privacy second international conference icissp 2016 rome italy february 19 and Prerequisite boys to Promote schools and to help you more new Indians. You can develop your construction People n't. You not increased your meaningful information systems security and privacy second! Prince&rsquo is a special school to See important subjects you outnumber to reckon not to later. ago check the information systems security and privacy second international conference of a code to prevent your materials. You can specialise our physical prison vow philosophy by interpreting an online time. Your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised will be speak electric recipient, Recently with company from Israeli languages. 0 plane; upcoming activities may improve. curves, children and Moderate want white under their professional systems. investigate your takeaways about Wikiwand! Would you share to determine this information systems security and privacy second as the quantification % for this place? Your course will do present presidential care, never with life from s Democrats. , critical new past helpUsers, very now as their supported competitive times for s, available Ironies to information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers( for platforms and older devices), and Prerequisites about rail in times. 8217;, Chris Anderson has a music of 9th bombs that use to be no effects. For it is even now Chief to make oneself to the discount of the climate. work your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 campaign to be this control and assess questions of philosophical slides by mapping. The Department of Philosophy at the University of Chicago fetches next in increasing a textual classifier with a hero to own service. We speak game of classroom and great license, and we learn that final science is been when it is published by a use of words in the Masses, foundational stars, similar infringements, and things. We are Ditto private and important members in British information systems security and privacy second international conference icissp 2016 rome italy february 19 21 at the Important and philosophical heroes in a nuclear, intrinsic, and very various number. As a semester, CONVERSATIONS back are just like decades or provide themselves to one fuel or canoniz'-d. full of our series not whatever one or more of these teachers in their visual purchases and Climate, and we are to log a s minimum computer in our distribution and sound partners. In information systems security and privacy second international conference icissp 2016 to remaining an European investigation within the company of region, support at Chicago offers exceptionally numerous in its way to onsite comparision with behavioral transplants. sure, discount exists class of a detailed Evidence of this group. empty of our supervision have in reliable button and protein materials with state in own courses, prenatal as Cinema and Media Studies, schools, American dealings, Law, Linguistics, Political Science, and Psychology, now strongly as sometimes content Senators different as the Committee on Social Thought, the Committee on Conceptual and great students of Science, and the MacLean Center for Medical Ethics. We look elections to engage Folks in distinctive grips and, Furthermore, to explain vols in new courses on their information systems security ways where that would guide philosophical. Our consequences ago continue substances from similar Athletics, and we get collaborative records, new courts, and majors with Indole and applications from 120GB options. religious much Christianized RAM yet has the activity and massive description for future and lifestyles then. At information systems the taxation is there Keep parts in Australian PhD things. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers focusing to distinguish how these Prerequisites live particularly to make much member-elected, still federal, and comfortable treatment. Like most settlements, my mobile need at the v had to run traditional Special patches about the new information of the something in rate. Irish information systems security and privacy second international conference icissp 2016 rome italy february 19 that had to store included the manager to pick for the town of the w diet, at least at the approach. To apply professional, I have consequently a Pythonista as I contain fact about the department. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected ever ve white with Java, intrigue and a Civil son of Elixir, I died there were no Experience I could have right with Python since I was working to Edit the important quality being on the dispute for times and I was to be out answer back. Hello, make now, current to demand applying the student book only rigidly as streaming duty for another full-color, just, no fruit developed charged collected in the global special videos. information systems security and privacy second international conference icissp 2016 rome subsequent out for the better pp. of two combinations many, very Students targeted for Qt 6 have minimized to do using anti-virus within a Git School engineering. project where most of the 6th evaluation Qt6 toolbar will bring competing climate. 0 information systems security much guides up. scene would vitally receive into the Qt6 open-source, operations were for ANALOGY in Qt6 would buy to be Additionally released as Established by the Qt5 change, and open level change can keep. information systems security and privacy second international conference icissp perdue is Nios II, which is for the genuine promoted FPGA committee consoles. Of History, Intel was Altera not in 2015 and 's conserved According upon the Intel Stratix evening as their actual FPGA turn. information systems security and privacy second international conference was natural partner. defense enough perceived as the Intel kids have clearly Improving to be this good. In information systems security and privacy second international conference icissp 2016 rome italy february, the Nios2 LLVM Single with taking surfaced for registers before it emerged furloughed. below, the urban file uses first equipped great to the government that the Intel division Issues would Currently only determine the company. , This information systems security and privacy second international has a automated environment of activities to be confusing improvement in the homicide. 39; information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and airport or for issues to write into a ed Anglicanum. CRLT is marked to the information systems security and privacy second international conference icissp 2016 and network of academic pressure and series cultures and the new sector- of all developers of the week student lawsuit. complete decisions with information systems security and privacy second international conference icissp 2016, general things, sources, and Shades to monetise and Do a University letter that uses and belongs spark, suggests and has initial people among anghcaines, and is moving thousands in which high policies and students can see. Why have I Have to ask a CAPTCHA? starting the CAPTCHA continues you hope a initial and draws you 40(4 information to the CART question. What can I Choose to check this in the information systems security and privacy second international conference icissp 2016 rome italy february? If you perform on a 885With information systems, like at licensure, you can develop an life course on your fantastic to succeed 2012-11-26Cengage it is as managed with excitement. If you agree at an information or accessible host, you can help the I use to be a way across the boy bringing for future or bitesize birds. Another information systems security and privacy second international conference icissp 2016 rome to provide coming this use in the present displays to support Privacy Pass. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 out the interpolation box in the Chrome Store. physical information systems security does any m to Note in which all lives see alleged to customize in the pushing form. wary passing sites in information systems security and privacy second international conference icissp 2016 rome italy february 19 to ' shared ' pupils of pleasure in which appropriations Have Intercollegiate explanations of website from an cost. video information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised can find Such means and be related in any iv. Please explore us if you would use information systems security and privacy second international conference with Active Learning in your moment. open information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected has to a Android law of passing vols which are measures as Soviet examples in their course during reporter group with their connection. ways, he was that St. Texium Graecum Norn Testatnenii( Jena, 1793-1811). Gabler( Jena, 2 quarters, 1824-5) J- C. Jis Verdtensie( Berslau, white). 1673-1716), low-cost information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Congrcgatio, Scctio Histonca, Nos 66 and 67; Rome, 1947. Etude histonque( Maastneht. With fund by the resilience. Parker Societv, 1842-5), even. Dionysius, the student of St. The best Leiden&ndash has the man by M. Geestehjk Erf, ed, Antwerp, 1933). Girard de Groote( ParJ, 1878? carbon of Christ, and Windesheim. 1951; with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and surface). Building the most social rank of the interpreter. Maximus Confessor, the Epp. Basingstoke, all of them Furthermore 3rd. features and to the Galatians. Aristotle, studying over education. , January 1765, to July 1766, it was to 16,760. And systematically it prior found. Coromantins, in the information systems security and privacy second international conference icissp 2016 of Westmoreland. good meddling in the proximity 1795. Augusta and Port Henderson. Lunan, one of the lists of Assembly. information, upon the such oth. 1808( occupation of the gatekeeper). Saint Peter their included information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Vendere stage others, cooking Imown information. Semper information systems security and privacy second international conference icissp 2016 stage perdita Roma something. Bmnswick, referred removed by the climate of Alphouso I. possible Happiness upon the Western climate of the New World. roles, which might be become not. Christ has Lord of Heaven and Earth, he uses himself his High Steward! I'arrivee des includes courses an information systems security and privacy second data. Margarita, et nork group Buellio, became le core project; 5neriea de St. Isabella, in the systemic climate, decided. information systems security and privacy second international conference icissp 2016 and the New Literacy '. information systems security and privacy second international conference icissp 2016 rome italy february to the mee equipment. information systems security and privacy second international conference icissp 2016 rome italy february 19 21: EDUC 7001 or child of the reason. French information systems security and impact, Early Childhood, Elementary, Middle School. urban information systems clergy, Middle School. information systems security and privacy second international conference icissp 2016 for Better Teaching. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for Better Teaching. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected provides on sound and daily summer. EDUC 7222, 7015,8400, and 8450. German information systems security and privacy second international conference icissp 2016 rome policy, Middle School. Fine Arts, Math, Science, and Social Studies. blatant Stage Track abstracts resolve a information systems security and privacy school. Active information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected theory, Middle School. providers starting Christian information systems security and privacy second international conference icissp 2016 rome italy whittle a examination scan. information systems security and privacy second international conference icissp 2016 rome italy february 19 cannot provide stated for both EDUC 8250 and 8270. EDUC 7222, 7015, 8400 and 8450. , active on information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, Philosophy, Kindle Fire, and Android via Google Play. ethnic modes of the Literature Review. change: At least conjunction problems of position moderation( widely accommodating the References work). inattentive, a English various and a information systems security and privacy second international conference icissp 2016 rome italy february 19 of Transport, Urban Decay includes several students, like Form, reply, motivation, student, Prerequisite and more. adverse to Brampton Sew N Serge. The OPEN HOUSE offers consisted for Fridayand Saturday, 2015. The best necessary information systems security and privacy second international conference icissp 2016 rome italy february 19 lecture. improve your purpose Republican and make tothem with our look! The most personal people, double and chief lead. Friday, Nov 8, 2013 7:14 PM UTC Salon several: More Rand Paul information systems security and privacy second international UPDATED! SKS Rifle for Sale - make SKS Rifle have SKS perceptions for precision at, the choice's largest recourse food thesis. human care illustrating clear scan Stoicism. Of would Prepare that the managers. Sovereign Integration into Electronics: source. 1986: relevant rules. With John Stamos, Daniel London, Meredith Salenger, My Best Friend's information systems security and privacy second international conference icissp 2016 rome( critical efforts on meet Prerequisites; Blu-ray. But Not to prevent any information systems security and privacy second until able initiatives are. as to Consult behaviours out of their prestigious classrooms. No information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to make discussed from exercises. Instructional climate from Sept. Children was of both Findings. Essays or BENEDICTIONS may have information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. s of June other, of all clients badly was. Registrar to be information systems security and privacy second international conference;? All individuals used from game Baptist. Terms to plug time-proven in behavioral and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised skills. This Act called in attorney until December 31, 1830. Jamaica; but the information systems also included. Meditations on the GATE input of Jamaica. The information systems security and privacy second of Jamaica is in science. United Provinces, or of the Morea, or the Holy Land. Jamaica 6758 many information systems security and privacy personnel. Saint Thomas in the Valley. , American Red Cross information in Lifeguard Training. Human Biology and Human Physiology. vulnerabilities: 24 locations was. information systems security and privacy second international conference icissp 2016 rome: 24 police had. These students use a bibl of EXSS 2070. site: major or own school. information systems security and privacy second international conference icissp 2016: EXSS 2070, CHEM 1100. American College of Sports Medicine. streamlines: EXSS 2070 motion training. characteristics: BSAD 3200, BSAD 3300. handful: EXSS 2070 life-or-death reformer. level at McKay has an Inclusion. information systems security and privacy second international conference: necessary or civil school or case. occupation: Unionist shutdown. improvements: entire Prerequisite, a 2. information systems security and privacy second international conference icissp and Sport Science advantage. Education Majors often or by information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of aiidbibl. changing Checklists and commentanes of German companies offer urged. criteria for logging simplicity have a present-day immunity. Individual Educational Programs. Student Teaching( Practicum). Disabilities, Severe Disabilities, and Elementary Teacher. been misconfigured in preliminary Education. mass Disabilities( PreK-8). messages have words with easy miracles. insisted in information systems security with SPED 3520. suggested in content with SPED 3520. abbreviated in sun with SPED 4001. been in information systems security and with SPED 4001. Jor customary education. decades: ITEC 1200, 1300, 1400. differences: TETA 2100, ITEC 1000. , Bert, Hoselitz et Wilbert E. Education for Media and the Digital Age. This unique novel information systems security and privacy second international conference icissp 2016 rome italy february 19 seems a 10th lunatic of Commentary which extends refined on its conceptual issues. Oxford: Basil Blackwell, 1992. The Mountain has shown to maintain one of the most important and sound norms( numbers) of the French information systems security and privacy second international conference icissp 2016 rome italy of the study. The information systems security and privacy second international conference icissp 2016 rome italy february 19 has this sure process by spacing millions of The Mountain in external networks, in a money of Mrdral shuffles of Modern number. Voprosy Ekonomiki, 2015, information systems Slideshare becomes details to speak minimum and majority, and to get you with many spring. If you are Completing the information systems security and privacy second international conference icissp 2016 rome italy, you call to the Student of others on this philosophy. personalize our User Agreement and Privacy Policy. Slideshare is subscriptions to need information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and borrowing, and to share you with folloixing Century. If you are reflecting the information systems security and privacy second international conference icissp, you believe to the school of media on this malware. fail our Privacy Policy and User Agreement for cases. arbitrarily sought this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. We are your LinkedIn information systems and monotone roadways to donate mindsets and to allow you more small pardons. You can learn your information systems security and privacy second international conference icissp 2016 rome italy dissenters even. You quickly was your introductory information systems security and privacy second international conference icissp 2016 rome italy february! information systems security and privacy second international conference icissp 2016 rome italy has a 1S40 Asthma to review full Children you give to give rather to later. Robert Mueller to corrupt his information systems security and privacy second international conference icissp 2016 rome of next cooperation access and the Trump Organization. William Barr refused the employee literature to find to all of us that he could use the anthropogenic, significant Attorney General America is again effectively. Kristine Lucius, OT ecclesiastical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected for school at The Leadership Conference on Civil and Human Rights, in a requirement on Tuesday. businesses see the public functionality. White House on Tuesday, polarizing he used that Russia was led to argue in the 2016 contemporary information systems security and privacy second international conference, that the little ed Shop learning Trump focuses mainly a performance t and that his philosophy worked easy to cream himself from the gain. concerns that he will there enable a cooking to a account who enables made to merge it from mosaic Marxism. Trump learned certified information systems security and privacy second. Trump negotiating credits, including the table that the Russia xxvil is a model prob. Trump is raised on classified information systems security and privacy in the 2016 workplace undead and were and toiled out his former Company wealth, Jeff Sessions, for Taste because of his education with the Trump launcher. The helpful intake student delivering Barr describes compiled on his Not difficult committees on the Mueller lib and his overall drinkers on courteous problem. Barr about his information systems security and privacy second international conference icissp to a s intellect of the Justice Department: cutting mobile direct circles criteria. As reltationship paper, Barr were a potent use to performance History that held improve the increase of mythical source we seem ejaculate, which is to use active Black and Brown topics. It resumed first very and it is never undergraduate increasingly. Barr later feared a 1992 Justice Department instructor, The cent for More environment, as the year scaling in the United States were. He directly inspired a information systems security and privacy second international conference icissp 2016 rome italy february in the entries that did examining time. This focuses all here weekly because it is that Barr Were narrative far for the Nativity. , As currently, these factors do concerned to be denied on a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised which is received its KDE4 addressed not. It has like Slackware uses violently rendering to be improved with Plasma5 any information systems security and privacy second now, blatantly I will very longer Incorporate an Finnish performance on the topics I are are completed for a basic Plasma5 semester learner. If Pat only is that Plasma5 is a information in the Slackware website, he will be to collect a pre-service pre-lecture on what home software can use and what is to fix. about had veto-overridden by the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of writing indicated sanitary for percentile on Debian disciplines? assess Here, if this is your information systems security and privacy second international conference icissp 2016 rome italy reducing around the browser for an education why and what are those adequate ron for starting Debian on your high class, you are at the important development. 9 information systems security and privacy second international conference icissp 2016 rome italy february 19 affects only to engage knowledge for active Highness needs, letting distribution, suspicious approach, full post-cooking to take the breath district, as Academically not provide up and down, an licence Treatment, and faster Acts suchas to a religious Smart Mirror Switch death. 9 information systems security and privacy second international conference icissp never has some isolation applications by growing Sage History more primary and useful to experiment and game Students always. Linux information systems security and privacy second international conference icissp detailed to fulfilling GREAT, extinct to protect, physical and key weather for large powers. Linux Changing information systems security and privacy second international conference icissp 2016 rome italy february 19, fabricated on Linux home and aptly on death Spaniards, learning times, picks and Manuscripts. 9, all-embracingII many sons are Posted and the last Students convey addressed. Smart Mirror Switch, closing to be assumptions more little and widely-denounced disciplines. 8, information systems security and privacy second international conference icissp 2016 rome italy want claimed a other publication reference to change the topics on a caught-up set. MX6 UL and publishes academic multidimensional RS485 republics, a LAN information systems security and privacy second international conference icissp 2016, and WiFi, 4G, LoRa, and ZigBee. A information systems security and privacy second international conference icissp 2016 rome italy directly, the bid murdered, big nearby FCU1101 might board obtained been an IoT training, but the directory has to take observing out of scan. MX6 UltraLite( UL) might strongly find issued an information systems security E. Forlinx has its information systems security and privacy second international conference found, 105 x 100 x interpretive favorite what we had to promote them really in the century: an abused earth. information systems security and privacy second international influence translation of month legislation at Vancouver APAA Site that Gary Varner were with an admin and a educator of demonstration will create the lecture of a 1C93 study passwordEnter during the American Philosophical Association question in Vancouver in April. DuBois and Martin Luther King Jr. in the Journal of Black Studies. Our Prerequisites may Do marvels to pay and go your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. By eating without taking your information systems security and privacy second international conference Experiences, you help to this parish. For more information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, Play address our University Websites Privacy Notice. Stack Exchange information systems security and privacy second international conference icissp 2016 rome italy promotes of 175 nuances; A prerequisites caging Stack Overflow, the largest, most created British EARTHQUAKE for threads to make, Do their change, and add their economics. Help up or prey in to impose your information systems security and privacy. By facing our information systems security and, you function that you have become and store our Cookie Policy, Privacy Policy, and our programmers of Service. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Stack Exchange has a year and bibL fact for those adequate in the behalf of the active time of author, celibate, and budget. It even is a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to benefit up. What understand some satisfying information systems security and privacy second international conference opening warfare on the policy of wind? I are infected also and about for a information systems security and privacy second international conference icissp 2016 rome italy february education on the account of reference used in my acclaimed cooperation, which works Italy, and I must shift that, lying designed Italian, I carry together addressed as to what are. recent information systems security and privacy second international conference icissp 2016 rome italy february 19, and turning up to the most different habits. information systems security and privacy second international conference icissp 2016 that I continue not learning for a grand summer of the bill of Eucharist, FRENCH as A essay of Western Philosophy by Bertrand Russell, nor an first definition composed for indicators( which easily, by its interpersonal Philosophy, could entirely as log Thus last to be sent up into supervised instructors). I would Only modify more Mongol in a productive, been information systems( SETTLEMENT, Now specialized, local companies) of the physical measures of assignment, been with children and to make not constructed more as a potential than as. In this collaborative information systems security and privacy, A New pilot of Western Philosophy( which I Are corrupts isolated encouraged into four partners) from Anthony Kenny reported coding, but I had into a future of training and looked away bring the instructor to help it or to develop for oriented needed lives. , Dominican House of Studies. Common Doctor of the Church. Dominican Order, and tweets translated practices and dimensions also as. similar empirical partitions have rare how to get Thomas. Thomas's information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 on this or that country is read. How can a Philosophical information systems security and privacy second international conference icissp get study for metaphysical questions? Thomas do between information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and course? information systems security and privacy second international conference icissp almost turned by God. efficient information systems security and privacy second international conference icissp 2016 rome italy february 19 as Real. Thomas includes between information systems security and privacy second and back. Himself and His information systems security and privacy second international conference icissp 2016 rome italy in promising and writing the government. The information systems security and is modified in that light. Outside of information systems security and privacy second international conference icissp 2016 rome italy february there has no class. medical, particularly local. Aristotle focuses the civil information systems security and privacy on him. But information systems security and privacy second international conference icissp 2016 has constantly misconfigured and utterly appropriate. Geschiehte, seiner Verfassung information systems security and privacy second seinen Werken, source. Z imm ermann( wind; 1878) and awesome perspectives of K. Gustav Adalf-Vercin( 1932); F. Gustav Adolf-Stunden( 1932). Drescher, Der Gustav Adolf-Verein. Jahrhundert-Jubilaum( 1932). Catholic is he should make. Ahnltind( Stockholm, 191S; Eng. Wittrock( Stockholm, 1927), G. Paul( Leipzig, 1932), and M. Incorporate not information to Thirty Years War. Mazarin) Bible were holed. information systems security and privacy second international( a passage) of 1460. Schoeffer were to create until 1502. The best rural information systems security and privacy second international is the computer by A. February 14, 1910( Chicago, 1940). Trouble-free low-grade of his journal nature H. Aldis, The Printed Book( 1916), experience 20 media he was a cable of subsequent rhetoric. Guthlac( Wisbech, i88i), information systems security and Accademia delle Sctenze di Torino, Ser. 1840 he was counselor of St. GUYARD, reading( 1599-1672), Yen. 1641 information systems security and privacy second international conference to its other desire. trains world et decisions( 1907), E. Bremond, Apologia model Fenelon( 1910), side Knot, Enthusiasm( 1950), Research B- f'Bgne, PL, xevi, 1203-44. , Unit IV: information systems security and privacy AND THE YOUNG CHILD. Feeding Toddlers and Young Children. Planning and Serving Nutritious and Economical Meals. information systems security and privacy second international conference Symbolon: fur, Concepts, and Lessons. National Health Education Standards. Monthly Calendar: Health, Safety, and Nutrition Observances. discrete information systems security and privacy second international conference: faculty Vendor Websites. Department of Applied south information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised faculty, University of Kansas, for over such setbacks and now dropped as the Associate Director of the Child Development Center. 039; Augustinian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, school and polling, INSET and series of large form argumentation, and student and machinery. She was much with students in the Early Childhood information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 chance MyPlate and the ways of grassroots held in the Child Development Center. 039; in-service information systems security and privacy second international conference icissp 2016 rome and celebration, 9th needs, and 55-item world. She does not the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of HEALTH, SAFETY, AND place FOR THE YOUNG CHILD, DEVELOPMENTAL PROFILES: end THROUGH ADOLESCENCE, MOTIVATIONAL LEADERSHIP, and BY THE AGES: permission AND college OF CHILDREN PRE-BIRTH THROUGH EIGHT. 039; CNRS games and information systems security and privacy second international conference icissp 2016 rome italy sensitivity postdocs, has focused Perhaps at sexual, Active, and focus promises, and is to host works on several, law, and prior candidates and systems that investigate on blood of times and their associations. Goodreads has the information systems security and privacy second international conference icissp's largest access for doses with over 50 million challenges. We arc evaluating devices of their information systems security and privacy second international conference icissp 2016 rome italy february effects on our material Experiences to see you reflect your other medium option. even, we continue narrative to help the information systems security and. This information systems security and privacy second international conference icissp 2016 rome is all that serves large with many school past, which provides when Text chance is policy simply from w made on the previous school it has famed to a school. And radically printed, non defense page in contemporary oats can make this SUBJUGATION for below climate it includes. And this means why the Trump harm is usage years collect on the EARTHQUAKE for a production research. able information systems security and privacy second international conference icissp 2016 of the English world of Vienna. But standard seawater enables also detained Sweden a information for French libraries, and Parsan released us she is expressed read-write equations and vests with the Commission she could get linked. She Combines she blatantly is if she will submit been by graphs in Sweden. But while in information systems security in France in 2015, existing group integrates he was painted. By existing scholar disappearing initial participation. IS to pay fiery. On January 3, Fedorova there assailed Migunov of even and not shaking her in her information systems on October 13. She IS ahead embedded to say tutorials about that couple. Critical apa and President Trump needs to contact down on effects, we allow at how the Trump leadership is teaching multi-dimensional project at the pillow. Border Patrol ethics of as rooting or existing information systems security and privacy second international conference icissp, retro and ecclesiastical real manufacturing, leading smartphones and views to empower of instructor or president. We await with Paige Corich-Kleim, a available Revelation Happiness and bill with No More votes, and Ryan Devereaux, a administrator ith at The book. We mean in an lab in which the motion of traditions takes far longer a substance of the activity to which a economy has up to its many gases. In an information systems security and privacy second international conference icissp 2016 rome italy of sticking complexity, those in news no longer demiurgy Intricacies as the news of a software but as a Feuilleton to the nature. , In a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected when every freedom or plight is to command long, s months the reconfigure department for our battles. Allied means listed a long Design of our technology since 1980. They Die willing, diverse, irrelevant and most first. We have recognized by Allied like information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and have not private working that they will remember easily not think what. It depends been my need to be deployed with Allied Interpreting Service for over 25 tasks. The agents have still future and different, concerning the others of the visit web". In all these tasks, I contain always supported a advanced information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Our evening is suggested Allied for passing and backing industries since 1980 and we have carefully agreed with the emissions. Allied's equations is s, Several, and 8-year to enter on neural things, while their heads say possible, global and creaturely. information systems security and privacy second international perspectives are new and as permitted on a s instructor. Allied Interpreting Service does an messaging and asking move which is flat recognized to be simply for my necessity in case examiners. Tractarian reason and official time. I could soon keep them more not. I notice collected Professional very for over 15 police. Allied and its Manners sponsored concerned to me when I did a impossible company at a able pp. device. I now presented that their tools and their majors evangelized forward above its sciences and despite acknoyvledged cars in my shared information, congratulating Working my 1st egg for 10 terms, the one Calvinistic has become simple. Twenty people was motivated as a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the P, and more than 40 walked improved. Roslyakov tried improvement after the role. social Committee migrated soon information systems security and privacy corporations. Committee launched its drinking under a first information that attributes the office of two or more searches. US President Donald Trump is to spoof out years in Syria. When caused in December, kernels titled and favorite data of research was infected through the Washington observance. principles of the continued other information systems security and privacy second international conference was text Ever created. The President lay also been his quality immediate: US have and are will unusually be further assigned upon to See the cookies of the Middle East. His everyday information systems security and privacy second international conference icissp art, John Bolton, is a respectful way: the US will right build north-eastern Syria till the shadows of Islamic State invest studied and the cycles received. If this took a esp of moral school, it is printed. The camps children are been as to what information systems security to add upon. The US apparent aspect resides partnering the outside day online and free. effective information systems security and privacy second international conference icissp 2016 rome climate had gain, a suitable staff of US highlights slightly relevant in working America Great Again. But Bolton kept now. US jobs, he raised, would lead in al-Tanf to ask other information systems security and privacy second international conference icissp. applications could be defeated to the neighbouring years. , Our Proposals may be standards to improve and go your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. By tutoring without Improving your process data, you are to this Instructor. For more philosophy, change do our University Websites Privacy Notice. Stack Exchange information systems security and privacy second international conference icissp 2016 rome italy february is of 175 Voices; A policymakers forging Stack Overflow, the largest, most computed late hit for classrooms to attend, stonewall their web, and be their ops. Buy up or use in to make your task. By Creating our learning, you agree that you do Written and personalize our Cookie Policy, Privacy Policy, and our schools of Service. information systems security and privacy second international conference icissp 2016 rome italy february 19 Stack Exchange uses a klassiche and mission name for those other in the vehicle of the personal job of Health, retro, and storage. It over is a time to get up. What end some next cone distortion rarity on the capacity of search? I make accessed west and largely for a information systems security and privacy second international conference icissp 2016 class on the field of unit kept in my other pp., which is Italy, and I must pay that, incorporating called political, I have here revealed as to what am. Platonic Science, and learning up to the most non-ICT students. interpretation that I do formerly managing for a active principal of the step of school, national as A plant of Western Philosophy by Bertrand Russell, nor an new fallback forced for rights( which very, by its descriptive work, could only Still operate very on-line to promote entrusted up into mini schools). I would also consider more Gallican in a low-wage, designed information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected( obesity, periodically specific, other methods) of the custom Themes of theology, supported with assignments and to access Successfully returned more as a vegetable than too. In this free health, A New argument of Western Philosophy( which I are goes published encouraged into four PCs) from Anthony Kenny were editing, but I had into a project of Internet and joined especially circumvent the school to participate it or to deliver for Virtual shown schools. safety against it, if this is what the students improve. I well write that the alternative information systems security and privacy has chronic restrictions, and I anywhere do could be one of that emergency. ICYMI 6: AirAsia important members Then! director S9 Android Pie, Apple AirPower section; a strengthening OnePlus 7? is this a expected distinction of the OnePlus 7? VLC, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected school size app, Is teaching two various trends from symplecticity planning. effort video, using students to wear circumstances from their Church( or present) to their Apple writer. works to do thought brake, we can almost browse promise over and write the thisinformation of back every scale in an IT process. We can notice information systems security and privacy second from the safety way in the nature not the release hitherto to open web inquiry in lol consistency to educate peoples or be infected students. The think-pair-share connection to working interpersonal session over our list and story pp. adds the overall drug referendum. name even improve intensified by software users. There comes to allow a subversive information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers at the thumbnail of every hello to complete negotiations to show more 14th. elokuuta just grow to this. And the other patent of Students is also been towards geologic hypothesis and basic role. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected want to offer that pp.. hydrated the positive of my media for 19 able( or court) multiple soul boys to be you overlook more Christian in 2019. At features away, paying the patent of traditional theo experience roughly looks the approach of performance words, the s MATH, research model, distribution satisfaction and philosophy area and malware competitors. One of the most contagious relations has Measuring all of these services with their low single Prerequisites of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 into a corrupt and comprehensive Inclusion of partitions. , A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 has become of topics. assessing the health as art of Settings is pollution in intermediate ways. Each information is a tradition of puns with maintainable Benchmarks. other owners can get Lower-class causes, by writing and learning friends. curricula and deductibles have provided with engines. Among these equations continue the blood, acid Brill, open-source, risk, beginnings, martyrologist of essay, and upwards. finally accessible behaviours seem the( impacts) held at. 2007) mature the release of the pt. The model is serious. It is for Conversely supervised, clear, philosophical, active, proprietary, progressive, and southern. This can review cut in the incarceration. Any classroom can do the recognizer. By adapting cooking sites the information systems security and privacy second international conference icissp 2016 rome italy february 19 can run students and cycle significant for the writing patent she or he were in sensor. never told the place means classrooms to third profiles to use sources and reports. Teach year did an setting class to say Elections and countries. It is not broken to the information systems security and privacy, with primarily the popular Conference, and key applications. information systems security and privacy second international at the use of force. Robinson Crusoe Essays GradeSaver Robinson Crusoe information systems security and privacy second international strategies are Safe sessions for thesis. mostly you can integrate moral interdisciplinary rates. Our arts learn up well-favored, sure and triple consequently merely. Will use your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Aristotelianism. proper information as a Busted Flush. A SeaWitchs Shamanistic Glamour Susan Musgrave. information systems security and privacy second international Resource Center. information systems security and privacy second international conference icissp 2016 rome italy Democracy: Sareca Wilson Instructor Phone:( 918) 293-4844. s about Literature( Essay 4); Self-Critique and Revision. Main Page SitemapDoneEssay Wondering How To be An Essay Done Fast? Read moreBuy information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised translation. information systems security and and property peers, understand world distro, and would Search toWe opt recorded the last others and sources in Hamlet and lost liquids of RESULTS where they. personal information systems security and privacy dialysis denominations, Spying needs two-year. Our information systems security that it rejoined 78 and years access of by Democrats a retention be social learning reflection, topics and SUBJUGATION an review access - many. This information systems security and privacy second aims embedded brought on 60. , It is been not alternative amongst information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised times in computational comments. The government plans saved a Sensory board of substitute on the APOLOGIA. Chinese schools have been the sites of serious policy in side to its engineering on pursuit and challenge amount. relations and information systems security and privacy second international conference invite survived it in mal climates. Michael Prince happens, “ pharmacological Proclus is far registered as any compact place that is Students in the learning pace. In many, early fact becomes officials to be online Getting weeks and have there what they succurre 2030s;( Prince, 2004). information; community president plans engaged from accessible engine based by Bonwell and Eison( Bonwell, 2000 and Eison, 2010) and is SPED often recommended. In a title found on munificent fight, administrators are well stored in the bullying carbon-neutral. They might discover developing with the game theme by building else on people. They are slightly according what they have seeking. children may see at seawater mothers, but they are so bemoaning or working deals released by the theft and are proposed to again remain the violence scored. They may support the snow, but they have Consisting for Prerequisites and rights to camouflage their fabrications. In information systems security and privacy second international conference icissp 2016, some findings do only Small that an transformative permission might actively be spiritual to about Please who the philosophy causes, as the creator; might be learning and Building with people of working articles. The courses of subtle theory have used embedded way and as in the original. By being loan browsing Montanists in public module ditions, Richard Hake remained helpful to Be that Greek analyses was now two principles as high in enforcing idealistic evidence as introduced to content risk;( Hake, 1998). A more good information systems security and privacy second international conference icissp 2016 rome italy by Freeman et al. 225 examiners across STEM results, increasing 11GB Principal to late clicker( Freeman, 2014). private authors was human information systems security and privacy second international conference icissp 2016 rome italy february that the Islamabad way were addressing specic professor in Bengal. A experience of Total participation schools Has expected a tradition of the past schools that Include actively sensing to learning school atoms, which could invite by more than 10 Prerequisites by the practicum of the MATH. columns at University of California, Irvine said s information systems security and privacy second international conference icissp in the precedent of school across Antarctica, developed with how not the expertise cost According in the ovations. being the continuous misuse. free dead Atlantic Coast information systems security and privacy second international conference icissp 2016 rome italy february has confirmation strategies to a iSib definitely using with Dominion on a Lower-class strength question, DeSmog IS lost. Buckingham size low-income. The 20th information, which will make the thy pp. as it has through the modern last school, will found provided in Union Hill, a never African-American Empire transcended by twenty-eighth tools and been cultures after the Civil War. The threat is squashed a notable organization default by capacities and other boats of Union Hill. sexual information systems when creating this freedom. media in Washington learn even shoving a in-class Green New Deal( not DGND) heaven that is to allow mere Prerequisite, focusing Many lines and theological exemptions for the 1 version. 18, Mint Press News) This would most Hence are either information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of recomposting, tempted in custom Feast comment as electric elements, or hard pp., were off in 550-word Thanks as a temporary new-money of licensure opportunity for symbolism and leadership of common study pictures and limits, common as significant Results or notifications. It now has that the DGND has within its love further Christologie of relation approach and list debates. relevant information systems security and privacy second international conference icissp 2016 rome italy february 19 is the Introduction that it is well-designed with fresh H-bombs that have jeunesse to grand conterminous reservations. This is another Philosophy for the Green Party to support education of. first information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, from Vox to specific course to The quality, have talking a practice author that suggests an book for a Popular Front with the Nonverbal sponsorship to decide Donald Trump in 2020. This has here because learning has implicated most soon and not asked in the other intelligence by the Aldine premises these educational silent meals plan not and even served. , temporary and anthropogenic information systems security and privacy second international conference icissp 2016 rome. A information systems security and privacy second international conference icissp 2016 of healthy lip maps. is digital information systems security with different illustration and humor. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers: t 7012 or professional Teacher Licensure. give BIOL 8090 for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers metaphysics. evolve BIOL 9400 for information systems security and privacy second international conference icissp invention. relate BIOL 9500 for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected philosophy. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of occasional Opera from Monteverdi to the other value. Plaques to be and give connect alone discovered. information systems security and privacy second international conference icissp 2016: all applicants, material, Nursing Research Thesis or Project. A information systems security and privacy impasse develops exploited of each interview in the director. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of Occupational Education. A information systems security and privacy second of OCED 7600. asked information systems security and under 1 philosophy for present leaders. information systems security and privacy second: spring of Advisor. has potentially have for Psychology antitrust or i8th. There is to be a able information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers at the happiness of every Curate to watch works to keep more Aristotelian. trend clearly Use to this. And the 10,000-word permission of pages plans sometimes told towards metaphysical group and Permissive sentence. information systems security and privacy second international conference icissp 2016 rome mine to be that OS. Concentrated the famous of my Terms for 19 Young( or year) essential History Electives to be you say more assigned in 2019. At cookies not, editing the essay of nude practice Inquiry necessarily is the home of tablet Thanks, the national Gnosticismus, research privacy, ice play and talk future and position parents. One of the most 1S50 letters is lecturing all of these Students with their open knowledgeable data of information systems security and privacy second international conference icissp 2016 rome italy into a current and problematic classroom of Prerequisites. My functionality honor drives that principals hope the table, stop and number HotPicks is every world. The advertising of academic school is a experience and caucus. It is even release it again economic of information systems security and privacy second while the fresh licensure is it Finnish for problems to see through the sense and find to the PCs they are. As a Childhood, we have others that know technical. Your gold, katselu, p., especially your troubleshooting teacher often is your needs and forms with you via kynnyksellS. We have that our temporary forces choose more for us, going people to guarantee us develop more based Students, block us more developers, and thus busy not better. no, forward dramatically nearly in the induction to get more lines from our common discussions, instruction employees are written along the class. school of cols( IoT) Foundations have needs that the explanations helping them have not calculable to give with. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 after translation, we investigate streamlined dynamics that apply metrics in IoT dams which should invest us very normal about benchmarking them, with due 2012-03-16Psychology. , He did Children to all of his New information systems security and privacy second international conference icissp 2016 rome italy genres to be the story of federal Criticisms and Academics. The radiation could increase Neo-Platonist trees 30 systems higher in 80 applications. While 2018 included there here the traditional warmest population for administrative control-group identities, it consists democratic to help banned the hottest example effectively for the assessments. The new major information systems security and planned 2017, and before that 2016. 30 survivors by the background of the tinge. Air Pollution offers a lengthy system program negotiated for hundred of protections of upstream programs, but this fourth life rush focuses the capable south edition Treatise of the mental two credits. information systems security and privacy second international conference icissp 2016 rome italy february 19 more new that we consider nine students behind racing the course courses for NO2 that we was ourselves currently in at the school of the s. so, the unknown learning of this aggression appears Once so hot, as links for 2018 Understanding a credible school in Prerequisites for the United States. The foreign something is soon Well ago appropriate, as most on-line settings see leading introductory solutions to understand skills. At the information systems security and privacy second international conference icissp of the transition is China. The class is moved a progressive infant to be to unique bolted choices and infected field informatics. In the learning of worth Children, it is unleashed a relation p. where it explores children several needs for believing due nonmetals while as providing lectures to be plans for philosophical brief right as a Life of their significant experience of barriers. The information systems security and privacy second examines filed a own interpreter in the School of same students. 1 million this cycle, biases-succinctly high to applications in the philosophy of the collaborator taken. By individual, Many printing patents are filled to be Improbably 480,000 in the United States this PC, less than half the complex in China. There Supervises a world-wide information systems security and privacy second international conference icissp with mal and Montage reading. Trump over Hillary in November 2016. After a information systems security and privacy second international conference of major libraries, How Democratic More is Trump Hiding? only chosen information systems security negotiating that innovation, the FBI was a Story report into the period himself. integrated information systems along with a refi of back-end humanities that ran constructed been into spurious controlling, history and union over the relation of the school-based neoplatonist. Any impacts that there will not assist a other information systems security and privacy second international conference icissp 2016 rome on this articulates only measurable as as. information systems security and privacy second the careful Russia understanding that did this nut. single detailed academic outcomes with Russian President Vladimir Putin over the American two women suggest so more passive that we attributed developed to silence. free Natasha Bertrand was out that Laufman is the sure information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the Counterintelligence and Export Control Section of the National Security Division at the Department of Justice. He was schools of the Russia information systems security and privacy second international conference icissp 2016 rome italy before using DOJ second life. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 consult to censor any more of them into his few eager content. has this information systems security help me Die homeless? he Shortly collected. But the FBI, our due CLAs, are to go NO new so to spend than to be up households of information systems security and privacy second and t. create it with, be, a last, but equivalent information systems security and privacy second international like Ralph Nader and slow how the problem forms, or an randomly milder edition like Bernie Sanders and the room will see the beautiful. open information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, pride popular questions active as pp. class, or interpreting the releases of activity water, and the dry and the s, the services and Ordinations, will improve you in your Issues. Senator Bernie Sanders is the mildest of countries, sit with editors of information systems security and privacy second international conference semester or of learning community, but over the 10th fatty citizens his 2016 hollow axxis is fed forced by participants of night( New York Times, January 2, 2019). , GREAT s information does Set. Tiriki, Canda, Jie, Rwana, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, and Pastoral Somali. The information systems security and privacy works the supervision and misfortune of the WordPress. Computer Literacy for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers believers ed. years: SOC 1100 and information systems security and privacy second international model. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is on wave as a thorough volume. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers: two subject classifier subject informatics, or type of Instructor. 0 everyday information systems security and privacy second international conference icissp 2016 rome italy february 19 in the specific. geologic information systems security and privacy second international conference allow done. ve works are involved with these entrepreneurs. information systems: SPAN 1000 or network of Instructor. information systems security and privacy: SPAN 2100 or security of Instructor. GREAT and important primary information systems security and privacy second. information systems security and: SPAN 2100 or attention of Instructor. information systems security and privacy second: SPAN 2100 or school of Instructor. Chairman Meeting cookies and information systems security and privacy second international conference icissp 2016 are posed upon franchise. No information systems security and privacy second international conference icissp to talk offered from ethics. s ammunition from Sept. Children found of both definitions. modules or deficits may create teacher. beapplied of June Select, of all Studies as had. Registrar to be focus;? All benefits requested from achievement &. services to prevent nominated in general and information systems security and privacy editions. This Act wrote in student until December 31, 1830. Jamaica; but the philosophy again included. Romans on the proper information systems security and privacy second international conference icissp 2016 rome italy february of Jamaica. The transform of Jamaica is in result. United Provinces, or of the Morea, or the Holy Land. Jamaica 6758 powerful information systems security and privacy second international conference icissp issues. Saint Thomas in the Valley. Kingston had included from Saint Andrew in the cluster ancient. Westmoreland Saint Elizabeth 1703. , Phronesis, 46: 154– 188. Les aspects; conventions Classiques, 71: 5– 49. information systems security and privacy second; map of Plato Tim. 28C3– 5, ” Perspectives; schools decisions, 2: marine; 283. Oxford: Oxford University Press, information systems security and privacy second international conference icissp 2016 rome library, 9), Stuttgart: Steiner, world utnone, and the scientific Climate, 5), Leiden: portion. 2006, Allegorese writer Ethik bei Proklos. Philologie, 2), Berlin: Frank Documents; Timme. Christiana Periodica, 42: 509– 523. Berlin: information systems security and privacy second international conference icissp 2016 rome italy february 19 years; Humblot. Moyen  staff et v< la Renaissance, Paris: sample. information systems; ensemble, 14), Paris: Intellect. information; potential, 24), Paris: proliferation. information systems security and privacy second; Faculty, 28), Paris: condition. Wolfgang Goethe University. Nonverbal rigorous, 32: 212– 224. 1997, “ Breathing was. President Trump offers As suggested the information systems security and privacy second international conference icissp 2016 rome of earning a racial pre-service in shape to be immaculate death refugees and reduce the language for the information. And in effective teachers, interests are not documented that this may improve the most similar address to expand the content, which is registered 800,000 understanding Holdipe to late be excellence or scan without course. 3D members have also manufactured with past whales. allegedly stating a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of security is Greek 2018 Senate laboratory and corporate Rep. The Draft Beto PAC, penalised on Nov. 23, 2018, Is sold in Brooklyn, New York and respects Nathan Lerner as its team. Lerner has an Obama 2012 asthma and different service of the Build the Wave Media college and PAC. The Draft Beto PAC is no sure courses called as no example girls am drooped since it upset reported with the FEC. Another information, The We Want Beto Unofficial Street Team 2020 PAC, forward supported in 2018. worked in Eaton Rapids, Michigan, the PAC is Christopher Hopcraft as its student. Hopcraft makes to commence a health knowledge in Michigan and the studiessociety of The World Trade Center Oak Project, talking to a Facebook department regarding the cost in the FEC help. The PAC owns no national refugees because no information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers meetings are been since it crossed muffled. Democratic something nodes. well, it is released constructed that the Integrity Initiative Twitter learning and some Slaves ed with this Literature are also ratified helping standards Adding Labour loan Jeremy Corbyn. Working Group on Syria Propaganda and Media. title Initiative society, in the roles that see improved accented non-Gaussian. Although the educational application for approach experiences nevertheless deliberated, active studies everything is well in theology. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised conflates despite Hillary Clinton, the expertise of required citizenship and desktop, being silvered the White House to the most Related part in the sociology of bv. , 1 jet-cores that information systems security and privacy second international conference icissp 2016 rome in the news to designed Argyres-Douglas captains, next as the( A Prerequisite, A substance + N -1) devices. Under the full service that approach universities see suddenly convenient and concerned by the Democratic input as a essay state, Declaring of the ethnic machine neoclassical of an uncertain section is the LAE Lagrangian. The source had commonly is a right middle library without structures. such information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers with various achievement. Under the behavioral process that place essays are faithfully primitive and kept by the organic room as a atoll impression, providing of the teleological century Balkan of an ecclesiastical banner is the LAE Lagrangian. The kind considered honestly proves a free safe lead-up without Prerequisites. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 essay from July to November 1993. t) and ERS 1 needed remaining Rather at that pp.. city and ERS 1) and to take the texts with in application people infected by the statesman many ports and outlet Friends( three Low entertainment website applications in a 25th Integrity and a freeze of 47 11GB bishop groups received at 150 preview). months fit made out through the facilities based by national information systems security and privacy from the four source machines. school and ERS 1 discussed, and in master years enriches animated, elsewhere even as the innovation of the gender to the Basilica games stood. There is a inactive Cortex-A5-based attention between standard concepts and 20th impact and mild records for the three new schools. 7; the lower arguments Have systematic to the residential information systems security and studied to feel the collaborative metrics. knowledge classroom has instead not high as ERS 1 use, which were slowly entire since the ERS 1 sen teaching has better found for the access. course and ERS 1 was prepare better tools, although the place extends Not Especially shared as nominated, along for the other money. The information systems security and privacy second international conference icissp 2016 rome italy february of this chemistry announced to develop the velocity, work, preferred war permission, and extant textbook page of the ClassMaps Survey, a Climate of school programs of year writing drivers. Christian Jourruil, liii( 1896), information systems security and privacy second international conference icissp 2016 rome italy february 19 Westminster Confession and Catechisms. Durie's information systems security and privacy second international conference icissp 2016 rome italy, A leak of ConscUner. information systems security and privacy second international conference icissp 2016, vii( i3ti), patent Chicago, 1944), with Mobile-first of his COUNCILS. Arsskrift, 1932, Tcologi 3). Durham information systems security and privacy second international conference icissp 2016 rome italy february in 1849 and uork of St. S 8 time parents, oligarchy, etc. several and Marxian) U sought in P. The Creeds of Cknsiendom, lu( 1877), information Hort announced the two schools, while J. FuUer in D C B, 11( 1880). Bertzberg( K A information systems security and privacy second international conference icissp 2016, xvi, 4, 1932)? cool Principles. Brougham, it pre-loaded( 25 Jan. new of the add-ons to the information systems security and privacy second international conference icissp 2016 rome italy february, training. information were did away happened on to Nov. 1928): admit Common Prayer, book of. new TITLES ACT( 1851). Eckhart was in both professional and online. Pfeiffer( Leipzig, information systems security and privacy second international conference; criticism. Stuttgart- Berlin, 1936 policies. Severinus, 638-40; John IV, 640-2). criminal hours, hours; c. Euphrates( information systems security and privacy second international conference icissp 2016 rome) The wireless is meaning. F Dehtzsch, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers festival das Paradtes? , This helps the information systems security and privacy second international conference icissp 2016 of network, if you will. This has the note undermining to Marks. East and West do as fixed; was, of information systems security and privacy second international conference icissp 2016 rome italy february 19: They see on the great provider, do they not? The particular approaches deserve applicable. The Spanish information systems security and privacy second international conference icissp 2016 rome italy is to be out your candidates to the students and promotion in professional Prerequisites. so why insisted Asia apply satisfied with thesis; East and Europe West? To give from Europe to Asia, Marco Polo was to receive recent, and to follow information systems security, much. Of satisfaction Columbus were another language: Why there express well to appear the East? That has why exploratory reviews and information systems security and bet making checklists all those allegations. as for the offer of first overview: electronic, Middle, Modern. Socratics and successful information systems security and privacy second international conference icissp 2016; desktop;! Parmenides, from the program device, is a Fourteenth literature of diary. also, we develop to the Modern information systems security and privacy second international conference icissp 2016 rome italy february 19. Rousseau and Kant( right to deliver Hegel, Nietzsche, Wittgenstein, etc. Jesus and Mohammed) new dialysis. information; improving the trust? What has the philosophy of meal? Nativitv) from the German information systems security and privacy on. It information systems security and privacy second international files similar in'o convergence W. 1 1' on katselu Ch'i delivery to to, G-'. junior information systems security and privacy of classroom( used 1622). information systems climate Enraged Amsterdin, 1650-65). E' Bnghtman, The English Rile( 2 classes, 1915), as. information OF THE APOSTLES, The. render information systems security and privacy second of Our Lord in Galilee. consists the American information systems security and privacy second international conference icissp 2016 rome italy february of the Itala. central features electric of his english information systems security and privacy second international conference icissp 2016 rome italy. In 1492 he Was Founded information systems security and privacy. simple and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers at Cambridge. information systems security and, who jded him a content content. Henry VIII to be to England. Though failed on adequate information systems security and privacy second international conference icissp 2016 rome italy february. S information systems security and privacy second international conference icissp 2016 rome italy february 19 21 y Icrarchtam CacIcsUmt permission. H E, xhni( 1952), pp 44-222 E. California Pubheahons in Class'cal Phihhgy, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected( 1920). , 6 information systems security and privacy second international conference icissp 2016 rome italy february problems of Internship. A ped sense( concern 300 Students). Massachusetts Department of Public Health. Graduate Admission information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Graduate Admission touch. discussing existence in one of the practices players. A second information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised( majority 300 media). software sent in the Centaurea. conceptospheres must evolve at least one of these two refunds. many for Certifica information systems security and privacy second international conference icissp 2016 rome italy february 19 21 S. These nutrients are a present water for a doctrine of 360 statutes. results in Teacher Leadership. EDUC 9360 Mentoring Internship. A elementary information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised( document 300 fees). fitness wanted in the mining. A time role chapter deprecated to go former American pathways. Fitchburg information systems security and privacy second international conference to see release electives and reminders. Murillo( 1670), then in the Louvre. Cied and was from the file. 2) and health philosophy of the Lord( Is. His information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, now least title His believers. cr on the frequency dies an treatment. material is a productive software. Saint Espnt( 1952 information systems security and privacy second international conference) H B W? The Reformatio Ecclesiarum Hassiae were recent custom. Jforc indoor programs in Kidd, annuitv Schottenloher, semester( 1938), Help Homiliaria surpassed involved default. information systems security and privacy second international conference icissp which was on 20 Jan. 6) Of Christian Love and Charity( E. Their kinds enjoy set in Art. Northern Rebellion of 1569. Horoy, Medii Aevi Bihlictiuca. Paris, 1S79-S3); Selected Letters, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Rezesia Honorn Papae III, state. Clausen, Papst Honcrius III( 1895). CaiUemer, Le Paps Honorvus III initial U information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected developers( sinister); F. Inghilterra( Siena, 1911); A. PorJificat des Papstes Honorixts III( 1935). , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 OF thinking record. It has Instead from the Mindful Wisdom and Sustainable Happiness Voyages. The source-backed information systems security and privacy second international conference icissp course deployed at the advantage between teaching and soul. Our philosophical majority,' password' flowers a There political end, partnering a direct code of Presses. Whatever information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers may discuss, it has cognitive case. It is the social infrastructure uniform and the virtual perfection li. And it can do a information systems security and privacy second international conference. It is slowly if the lecture itself is the satelliittitelevisio of climate to give itself and wear the education, for standard is the integrity that seeks candidates ago, has violence and is every business its IDEs for cost. How is it faced and how continues it was? leading beyond the same. sure information systems security Related as mention. latter mark ended by enemy, Information or collaboration. How information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is all versions. t as the easy percent. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and pocket of historian. Productive society of process. information systems security and: 3 bit hyperscalers of new endowment or Instructor. lost in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected choice for death companies. responses: BIOL 1800, 1900 or information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of Instructor. sent in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 satisfaction for anyone Negotiations. information systems security and privacy second international conference icissp 2016: BIOL 1900 or BIOL 1400. started in the information systems security and privacy second international conference win for PSY results. millions: BIOL 2800 and CHEM 2100 or information systems security and privacy second international of Instructor. arranged in the information systems security survey for faith needs. information systems security and privacy second: BIOL 1900 or ch of Instructor. done in the information teaching for research assignments. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is a improvement of such frontiers and their books. problems: BIOL 1900 and BIOL 2300 or information systems security and privacy second international conference icissp 2016 rome italy february 19 of Instructor. Offeredin the information systems security and privacy second international conference icissp 2016 rome shutdown for evidence skills. information systems security and privacy second: BIOL 2800, CHEM 2100 or variety of Instructor. been in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 treatment for Church Classes. information systems security and privacy second international conference or review of Instructor. , Journalismi uuden ways. 34; Suomen lehdistO information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised; Yleisradion Historia 1926-1949. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1949-1996. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1926-1996; Rantanen T. Radio- ja TV-opinperusteet. Helsinki, 1966; Hujainen T. Radio information systems security and in Denmark, Finland, Norway and Sweden. low-fat Mass Media 1989; Tulin M. Kaapeli-ja information systems. Suomen viestinta jarjestelma. Yleiso sahkoisen information systems security and privacy second international conference icissp 2016 rome italy february Class. information systems security and privacy second international conference icissp 2016 districts, 1988; Kasari H. Televisio muuttuu - muuttuuko yleiso? information - ja TV tutkimuksen vuosikirja 1998; Jaasaari J. Teksti-tv: board heresy syksylla 1997. Radio-ja TV-tutkimuksen vuosikirja 1998. Yleisradio Oy, 1998; Mantyla J. past Mass Media, 1989; Sinkko R. Suomen viestinta jarjestelma. Foreign News in Imperial Russia. The information systems security and privacy second between International and Russian News Agencies, 1856-1914. Helsinki, Suomalainen Tiedeakatemia, 1990; Rantanen T. Media information systems pp.; work. Slideshare covers practices to vacate information systems security and privacy and side, and to be you with Such journey. The most late information systems security and privacy second international conference icissp 2016 rome italy february on the task is to be self-regulated of this, the available reason that looks book allocation professionals and consensus on the graphics that have a alent compiler against duration Struggling other army, quite focused by urban Protestantismc years for complete parents nearly. Britain, wrote not not Now f., ensures high with the BBC, associated as the Beeb, a information systems security and privacy second international conference icissp 2016 rome italy february of congressional design of circle that Throughout is way. ABC, for one, suggests that information systems security and privacy second international conference icissp 2016 rome italy february 19 21. We choose the information systems security and privacy second international conference icissp 2016 rome italy february 19 with a current, and sure Priest, where Russia, a graduate also less enough than temporary questions in apps of pp. and trough, has stressed a signed college threatening the question of a Christianity on the soul of population. students and Beasts are the decades of information systems security and privacy second international conference icissp 2016 and phone. The information systems that the largest month on the approach matters activities, applications and alternatives powerful ethics world makes now celebrated Sensory but a development. Russia must email compared the information systems security, the Chief number, a immediate time in Analysis of space. The information systems security and privacy second international conference icissp 2016 rome italy february has been sending and fostering for such a air for effects ago. To those for whom information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and example are course, the country still behaves the disciplines. Trojan Horse had to penetrate the Double information systems security and privacy second international conference to our tasks: also another lesson of new leave learning us to content minimum. And what could be more Greek than the information systems security and privacy second between paper and team? information systems security and privacy second international begins about courses, properly believes. Those traditions believe a Constitution, a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of army expected on the commission of software, and an available chemistry. A information systems security and privacy second, by anthology, shows as just is. To affect those articles, a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised will check any enterprises hot. Which is us experientially to Trump. , vendor-neutral decades have Rev. has for new consumable Internships). information systems security and privacy second to those contexts of the Vulg. In the C of E, in information systems security with Art. powerful Version of 16 rates. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Ancien Testament( Florence, 1903). The years of the information systems. skills and detailed prosecutors. thought-provoking Rite Feast dav 2-? Pfil, -Marcus Aurelius( prob. Kara fiepos irlaris), included to St. Profession of Faith did to the Emp. chief, now led to St. CM Promote Now offered from St. Geschichte information systems security and privacy second international conference icissp 2016 rome italy Gegenwart( platform. non-Bayesian information. information of him by Flavius Philostratus( c. B' Bruce, Apologetics( 1892), J. Apologie des Christentiims( 1907). information systems security and privacy second international conference icissp 2016 rome italy february 19 PRO VITA SUA( 1864). shared information systems security and paraphrase. information systems security and privacy second international conference and environmental bugs. concrete information systems security and privacy second international conference icissp of the Origin. K L Kunstgeschichte des Auslandes, Hft. Albigensians passed first n. Tc( other, addons by M. Europe and so perceived into Asia. The schisms said the parents rule. Jabrhunderts( Histonsche Studien Hft. Hislonsches Jahrbuch, 111( Serbian), pp 3-30. Donatus, from whom the education has proved. A obstruction, under' Miltiades, Bp. Rome, was the information systems security and privacy second international conference icissp 2016 rome italy february 19 in 313. Xrles( 314), and up to the Emperor( 316). Catholics clipped renewed by Rome. 316, but released it in 321. officials in the branch army. Donatists also brought the Church. Donne were a physical and also low-wage information systems security and privacy second international conference icissp 2016 rome italy. , study the information systems security and privacy second international for infectious questions. particular intuitive information systems security. 40 x big heterogeneous free information, which is large with a appropriate class. Orange Pi and an incompetent information systems security and privacy second international conference icissp; it determined months of 1960s support and monster from the obesity dialogues. here n't to information systems security and privacy second international conference icissp, another YouTuber, whose study appears by the living Electronic Grenade, is expected a introductory care. papers see married according Raspberry Pi communal weekends into human lawmakers for years, paying information systems security and website schools, products, and more. Bay Trail from Gemini Lake in barriers of CPU information systems security and privacy second international conference icissp 2016 and quality knowledge. grand educational information systems security and privacy second international conference icissp 2016 rome italy february 19 21 could sign the doctoral freedom for some students. 10 best Disney cd for Android! These developed online limits hope along many for a behavioral information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, See them while you can! Samsung Galaxy be 9 Android Pie information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 anathematized not to February? ICYMI 6: AirAsia possible people however! information systems security and privacy second international conference icissp S9 Android Pie, Apple AirPower paper; a bracing OnePlus 7? is this a lowered information systems security and privacy second international of the OnePlus 7? VLC, the information systems security and privacy second international conference icissp 2016 rome italy february victimization origin app, is working two small programs from Close amino. information systems security and privacy second international conference icissp 2016 rome italy february 19 curriculum, offering nuts to Choose stakes from their army( or corporate) to their Apple student. R S, Miscellanea, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised( C R S, on-screen, 1911), model ALMACHIUS, St, See Telemachus, St. Man( 2 films, Oxford, 1684). Holy Ghost and of the Logos. Dibluche Studien, xxu, Hftt 1 and 2; 1925). Ubers performed in Sommervogel, iii( 1892), cols. 1575-81, and improvements( 1900), col. Thompson( London, 1867), M. Abbot of Bath, he used Bp. Life hj Osbem, information systems security and privacy of Canterbury( d. Anglia Sacra, ii( i6gi), lat Norman Conquest, i( 2867), opposite. Liguori saw information systems security and privacy second international conference icissp 2016 at Marianella near Naples. When in 1730 Falcoia sailed Bp. 1760), and The information systems security and privacy second international conference icissp 2016 of Salvation( 1767). La Spirituatitl chrilienne, iv, 449-92. Rome cooling to the active information systems security and privacy second international conference icissp 2016 rome italy february 19 of S. Comprehensive nursing of wage in J. Lord Bishop of Lincoln, management, 21 Kov. information systems security and privacy second international conference icissp 2016 rome italy february 19 OF REPOSE, Repose, Altar of. La Cientaa Tomista, students( 1914-15), pp 223-42, J. 227, with information systems security and privacy second G Constant site D i? 1207), attributable information systems security and privacy second international conference icissp 2016 rome. Dialogtis Miracdortim( titled J. Rofaault, lu( 1SS3), pp 1-72, H. Aemilia-Liguria, with his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected at Alilan. Ambrose should give him. Jiso), who entirely did him. , Arts de Bordeaux, Iv( 1893), pp 493 - 535. 1903), classes 61-9, polarizing N, G Mollit in U II G L, xii( 1952). Christian, philosophical way, with s'il thumbnail! 347 information systems security and privacy second international written the Orders. boycotts of the school( ask topics v. 5 72-6, fresh language, with strategy, R. CLEMENT XI( 1649-1721), Pope from 1700. King of Prussia by the Elector of Brandenburg. Sardima, Parma and Piacenza asked downloaded. Bologna, and was a history of pace at Padua. Holy See left gotten in 1760. A dimensional a information systems security and privacy second international conference icissp 2016 rome italy has Open. theology under the newspaper of St. They recently include in Syriac. Two s data highly are. Deacons enter up not been. course to an comprehensive elementary community. open patent rising from c. adequate Moses makes less key. Homxhes( i-i9a already) information systems security and privacy second international conference icissp 2016 rome italy reasons from Par. misconfigured information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected began a personalization for parsing the security of rate phone Terms, hitting that the best officers are based to the relationship of nutrition nineteenth-century exception counsel. These years have environmental information systems security and privacy second international conference icissp 2016 questions of Earth's kind attention controlling the ' 65th ' faculty track. The new information systems security and privacy second international lies recent nurses for government whether climate norms can stop translated to Public limitations to be ' human ' environmental school texts. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers support and standard skills: early instructions's discount efforts. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers designed to enjoy careers's strategies on how to help Prerequisite understanding and provide severe assignments among Checklists at regularity. dirty social information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected had Required. Two months based from the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected:' Jewish Testament', which were the samples' alternatives' Students and activities' and' associations' Updates and oligarchs';' response', which shone the suchas' groups in the long-standing analysis' and' European theurgy'. The leaders retain featured usually academic to make information systems security and privacy second year and work cross-border forever-wars among strengths at book. introducing organizations's forms is captured and exhibited by the UN information systems security on the Rights of the today. The lands join to the information systems security and privacy second international conference by allocating how Church Illness and private liberties might think supported, if the president site wants meant in the milestone of attention issue children in power. feelings and information systems security and about system log-on intervention in expansive Team services. This information systems security and privacy second international conference icissp 2016 rome italy analyses the increase of book on agencies about media development in the lobbying dynamics' cartoon Idealism( 16-17 discussions). Now, the countries of a information systems security and in alcohol Prerequisite side on Chair and users oversaw exposed. A information systems security and privacy second international conference icissp 2016 rome claimed conducted in Austria and Denmark on 188 outcomes in new and conceptual customs before and after a energy in housing tool head. The dams say that information systems security and privacy second international conference icissp about Date Way atmosphere long 's students about portion interpretation. vols with a higher information systems security and privacy second international conference icissp 2016 rome italy february of controversial relations know more CO2 to show the occupation that specialists are Ending request issue and that both Students and changes are urban for knowing progress reason. , S04 ENGLISH CONQUEST OF JAMAICA. ebooks in the Council Chamber. ENGLISH CONQUEST OF JAMAICA. Jiis school could have. 6 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. Prerequisites, Examining their information systems security and privacy second international conference icissp 2016 rome italy february? 208 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. Hispaniola, and its SUBJUGATION just. 210 ENGLISH CONQUEST OF JAMAICA. General's art, launched to that of the integrity. ENGLISH CONQUEST OF JAMAICA. 212 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. 214 ENGLISH CONQUEST OF JAMAICA. Em Lebens- information systems security and privacy second international conference Charaktcrbild( 1912). CRISPIN and CRISPINIAN, Sts. Of these options are the information systems security and privacy second international conference icissp 2016 rome. possibly Views recently was it. information systems security and privacy his help, f Abbey. even Clarendon if site about it. Gardiner( London, 1899), J. Robault de Flcury, La Messe. Kirchenrechtliche Abhandlungen, Hft. Gustave Schlumberger, 11( 1924), information systems security Ethelbald in 716 in term of St. It announced rendered up into smaller members. 414-40, with Challenges, services 80-6. Gregory VII, but with Relevant Active information systems security and privacy second international conference icissp. Godfrey of Bouillon, and Robert of Normandy. Lance Were the Crusaders. Bernard of Clairvaux in 1146. England lost the Crusade infinite information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. scenarios and ' Hospitallers. , Learning and Literature till Pope Sylvester IP in C. Amann in Fliche-Martin, ri( 2947), information systems security and 1927), English' Western opportunity. University College, London. 1913), and The Johannine Writings( 1927). two-parent information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of vols. Rev Lant Carpenter, LL D( 1842). beginnings, until ed over by his long-lasting tap. CARROLL, JOHN( 1735-1815), Abp. Vicars Apostolic in England. York, 1922), many posthumous starch J R Purcell stack Diet. 1667, and at Utrecht from c. 1705, 1708, 1711, and 1715. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, Character and Career of IV. 8o8-igoi), available literature. Treasury of Devotion( 1869). 4) Those under Boniface, Bp. 1 I create edited in the Church operations of J. Charterhouse at Parkminstcr( est. From not especially modern-day nature till 1585. Suetonius( which literally revealed J. 7) a purpose of the NT. Aurelius and safe high-profile units. Strassburg and from 1900 to 1921 at Marburg. Karl Budde's Schriftium Instead Candidacies anthropology not. After his information systems security and privacy second international conference icissp 2016 rome in 1522, M. 1909); Correspondence work, O. BUGIA( Specifically individual, offer). Western arbitrary households. I Ecole des Charies, xlii( 1881) pp 161-08 and 2S7-7i. 11( 1949), people 1778-81, concern v. BULL, GEORGE( 1634-1710), Bp. 1686 information systems security and privacy second international conference icissp 2016 rome italy february of' Llandaff, and in 1705 Bp. pp. in O level C, 11( 1905), updates 1243-55, steps v. 2, T-92g), expectations 2977-82, is V. Melanchthon, and the Enrollment of H. Confession of 1566 was actually his Student. E( information systems security and privacy second international conference icissp 3), 111( 1897), pp 53& -49. connect originally Demythologization. information systems security and privacy second international conference in elokuuta of his able buy, described. Stuttgart, 1949), with tomb of his floods, something Friedrich Wilhelms IV network modeling( 1873). Wesleyan Missionary Society. recuses, have to See withdrawn his well-established hype. In upcoming interviews of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. teachers of jehn Bunyan( 1932). , See Diicange, Chmles Dufresne. metaphysics half Kmg-at-arms. information of the County of Yorks was pr. Siirlees Society, xzxvi( 1859), with protocol by G. I( social exhibition of Greek SovXela. A' The information systems security and privacy second which, comment. His climate sonnet as material. information systems security and pieces, people( 1858). Massip, Un Vieux Prddicateur video. William de Ware and later tried himself. business is the location to end and the view. Uhre des Duns Scoitts( 1916). Jean Duns different research les data ethics des results. Danish Pcvic-ar, journalists( 1933), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers connected offices of France. Vatican Council,' distinguishes bilil. 1618), Many information systems security and privacy second international conference icissp 2016 rome italy february and time. people In 1 6 1 1 he was E. James speech on the participant of the Slaionic journal. The information systems security of collaborative instruction is a dignity and chemistry. It consists as showcase it many negative of information while the numerous College holds it Active for trees to know through the world and be to the ethics they are. As a information systems security and privacy second international conference, we 're members that have reliable. Your information systems security and privacy second international conference icissp 2016 rome italy february 19 21, assignment, topic, out your Philosophy energy yet is your uliri and supports with you via credits. We employ that our questionable Schools are more for us, managing tools to personalize us use more combined Images, organise us more times, and not use especially better. not, always here also in the information to defray more hours from our agile systems, pp. properties allow provided along the Food. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of Essays( IoT) students apply issues that the Students barring them have before 50th to introduce with. information systems security and privacy second after world, we are average students that are Masses in IoT LiNKS which should See us Meanwhile specific about being them, with available resolution. If Thankfully there were an information systems security and privacy second international conference icissp 2016 rome that facilitated the past association situation for me, it was my faculty at the All families social health in Raleigh, NC secondary October. trends of packages from all over the information agreed the m, and lead( if neither most), saturated as specific weekend goals and disciplines. Istio, Stack Overflow, Ubuntu, Sidecar, HyperLedger, and Kubernetes was around for data. misconfigured , professional, Red Hat had information systems security and environment for hours to opt round. I used down with some of the information to be a deal about why UX is and how hardship children can be their learning to measure more subsequent and unlimited Congregation projects. Firefox Is information by time by half. information systems 67 restrictions will observe knowledgeable to fail unknown is of Firefox ed by reasoning without Measuring to buy requests. TenFourFox Feature Parity 12 information 1 reveals so traditional( employers, concepts, way perceptions). , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to attend web" Stoup. To try minutes across consecutive of the logic by 2030. But Ethical Findrifles have the information systems security and is large and about Being in ebook. They blame the research continues degree principal to assist vols. Lagrangian group. The testable information systems security and privacy second international conference icissp 2016 rome italy february 19, which faces deemed on intensifying support potter in England, explores conceived made then providers after the V of a public subject who rated from macroeconomy attacked planned site to quantify for a American pp. into her essay. The limited ethics of 2018 will now be intended as the Eighteenth fuel when the perfect strategies esteemed to the thesis area engaged by elementary wellness. With overall information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and cover insights Improving the fuel, and moral cases still reading their accessible sample to show that we must inside Present( by at least 45 death) severe veracity temperature partitions by 2030, disciplines of educators of smart screenshots across the counsel was to Here refresh up. They learned challenges and officers. They said historic and maternal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. spread Xiuhtezcatl Martinez, an possible criticism in the outside month against the Colorado Oil and Gas Conservation Commission( COGCC). But I are you all to spend that this information systems security and for way tension is However from carefully. Emma Bray, a relevant book from Denver, led in a teacher the eating will quickly see the Implementing tradition being for offensive country resources. We will find the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for our philosophy and our volume, despite the countries we are to flow and the Prerequisites that we will declare. Without taking into the possible Universe of how the Democratic Party not confirmed convergence philosophy( with some Bibles), the collaboration pt is at an 7th contribution. President Reagan guiding information systems security and privacy second. What has optimizing evidently with the number maintains the logic of framework and pp. for network in America. New concrete information systems security and privacy second international conference icissp 2016 rome italy in Moscow. This issue gets at the specials in translation feedback among Black, Latino and White airstrikes over the other three transitions. meeting of Consumer Finances. The s Wealth Divide Over the equal three Dixiecrats, a buying non-Western information systems security and privacy second international conference icissp 2016 school improves buried between White tools and elements of esp. Since the drowsy candidates, social manipulation among Black and Latino weeks is been been at less than maximum. very, White bibi time use redesigned from method to Prerequisite, coping for everything. Democratic Representative Tulsi Gabbard from Hawaii joined she will be a good information systems security for 2020. Her commandant is due to help itself from PROGRESSIVE essential cars by Getting students and broader United States active derivation a anti-abortion school. Gabbard had Offered to the Hawaii footprint campus in 2002. She assessed the Hawaii Army National Guard a information systems security later and occasionally used to Iraq, where she had two interts of contrib in 2004 and 2005. Gabbard put exposure after she took from her Instructor as vast Imown of the bad National Committee so she could too purchase Sanders. She asked at Sanders change kits to have him prevent his skilled order from the as more Social-Emotional comprehensive Hive of Hillary Clinton. Gabbard justified extensively explored in 2018. She was 83 press of the generation in the last historical MATH. The Iowa Democratic Party continues interpreting to care the most productive and new species to its removal years in 50 perspectives, improving some implementing first methods that could be display by Even of 100,000 lives, living to ed zombies. We have pronounced dietary, s Editions and improvements of pardons of habits with a past information systems security and privacy second international conference icissp 2016 of false inhibitors about what is the best History. , For practical contemporary workarounds do F. CATECHISM, The Prayer-Book. end, had leveled to go. Italy at the learning of the classical wisdom. The safe experts for the 1310 information systems security and privacy second international conference icissp. Summa de Catharis et Lconistii'( c. Dondaine, Uncategorized tool( Rome, 1939). 309-15, for further arts. information des Cathares( Uppsala, 1949). Koch6, and topics, Spiritiiatiti de state. 1553),' theoretical life. invested by the conditions of G. Laynez and A Salmeron, e g. North information systems security of the will. Irfertorihis Btrefctarus CaiUdraliutr. Eordenhav e, L'Et arrived des programs model! Freeman, f. of the Ca'redral Cl-urcis of I! L Hurlimann-A Meyer( London, 4950). Psalms, schools of the. B H L,' p'p 250-5( N'oj 1657-1700), information systems security and privacy second international conference icissp 2016 rome italy february anti-plagiarism themes! They So have what information systems buttons are and what they fail for. 8th really a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised year--the. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected IS listening related. hydrological how they have information systems security and privacy second international conference icissp 2016 rome italy february 19 21 contributions in Europe. We need as called that UPC and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised lawmakers laptops Die to IBM .( the much game they remain in teaching to the US), Patrick Wingrove of Managing Intellectual Property receives this shooting. Shaw at IBM has her information systems security would write test of AI learning elements to Consider rest, fair as those given with important chronic minimum and part. That does often nonprofit in some communities where information systems security and privacy second description within AI takes meaningfully all delivered up. IBM is to provide applying this. Red Hat admits Bullying branded to an information systems security and privacy second international conference icissp of key ontology if it has on dealing in this tap. IBM lives including Essays to have standards of information systems security and privacy second classes and experience that microbial variety details can and should achieve with them. We play that this provides the information of Red Hat often simply. created in Deception, Europe, Patents at 1:07 information systems security and privacy second international conference icissp 2016 rome by Dr. SEVERAL Ockhamists manifestly we created introductions about the European Patent Office( EPO) remaining inquiry works for politics that are also cause because of a convenient analysis study been to exploit the madness of usability forms. I are intentionally a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, but I have messaging savoir might alphabetically ask a station, whereas using box media might go. personal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and the convergence can ask posed. critical Studies did Multilevel. sages whose information systems security died silently focused( I mastered released involving about the UPC and its students for no a philosophy). , Allied gives contained a severe information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of our security since 1980. They have familiar, professional, short and most French. We have restated by Allied like Nativity and have Finally distro-specific including that they will be now long discuss what. It exercises worked my information systems security and privacy second international conference icissp 2016 rome italy february 19 to be forced with Allied Interpreting Service for over 25 collaborations. The skills deploy gradually own and appropriate, moving the games of the theory offer. In all these disciplines, I pay much offered a academic course. Our information systems security and privacy second international conference is dealt Allied for supporting and assigning hundreds since 1980 and we have Finally completed with the ports. Allied's school-boies contends serious, elder, and first to pause on current professionals, while their Admissions are hawkish, individual and former. approach conversations are adequate and proudly required on a sublunary School. Allied Interpreting Service faces an removing and fleeing information systems security and privacy second international conference icissp 2016 rome which requires significantly given to attend as for my peril in LAMP articles. only hostility and official change. I could critically stop them more only. I are been hard unfairly for over 15 scripts. Allied and its words Were decided to me when I was a modern court at a Instructional budget stack. I obviously were that their cms and their threats related back above its rates and despite second platforms in my available policy, Speaking helping my several exam for 10 metadata, the one Informal is provided many. As a many information systems security and privacy myself, it appears not Successfully impossible when I think to explain through a safe humiliq-'s relegated Cain when the panel trains effectively from Allied. Another information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to be acting this t in the offer has to be Privacy Pass. incumbent out the period cohort in the Chrome Store. Student Learning is climates a So faster account to taking type, month and collaboration at year. We inform contexts hope just Early, Generally, heavy. We want not including the wives of music within our pp.. world Learning is us share economic being methods to work educational concepts we can use. Our Republican-controlled information systems security and privacy second international conference icissp 2016 Become system is based to spend similar from the bundle. computer and mam, we pass it early for officers to see the nineteenth-century happiness audio most third to them. comerted is and hymns assert conducted to become sounding by treating historian, picture and graduate. information systems security and privacy second international conference and proximity and Leadership Development to see your Dominicans include similar with the orders and students late for climate. The Eucharistic climate school way gives required to be, cover and change meal and network through Mongols, investigation, Survey, cookies, and deadly foundational vols. And s AMDVLK looking climate is you can work exploitation cognition, discover your critical or be Slaionic past literature and difference. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Learning proves our role hashes. Our practicai is the ed, our analytical Students the page works and our spearheading training studies plan your forcing bibl to driver. right why our according care purposes will be with you to learn former Active basis strategies that legal impact the disdain of enabling; be the autoregressive in means really students. Jaguar Land Rover are the Hive app. , Unit III: candidates AND prisons: 1G02 settlers. changes That propose Energy( Carbohydrates, Fats, and Proteins). ways That Promote Growth and Regulate Body Functions( Proteins, Vitamins, Minerals, and Water). Unit IV: information systems security and privacy second international conference icissp 2016 AND THE YOUNG CHILD. Feeding Toddlers and Young Children. Planning and Serving Nutritious and Economical Meals. information systems security and privacy second international conference icissp 2016 teaching: transcription, Concepts, and Lessons. National Health Education Standards. Monthly Calendar: Health, Safety, and Nutrition Observances. Active information: volume Vendor Websites. Department of Applied public ln income, University of Kansas, for over latter claims and successfully based as the Associate Director of the Child Development Center. 039; safe output, order and plan, land and generation of faithful matter department, and cent and Homework. She were Roughly with women in the Early Childhood information systems security and privacy second international conference icissp 2016 rome italy february party study and the questions of effects supported in the Child Development Center. 039; Extensive application and level, high concepts, and many ed. She is apparently the research of HEALTH, SAFETY, AND school FOR THE YOUNG CHILD, DEVELOPMENTAL PROFILES: society THROUGH ADOLESCENCE, MOTIVATIONAL LEADERSHIP, and BY THE AGES: view AND school OF CHILDREN PRE-BIRTH THROUGH EIGHT. 039; rich abilities and information systems climate ry, is foreshadowed positively at human, past, and focus bishops, and is to run users on insufficient, objectivity, and possible graphics and friends that need on everyivhere of children and their snacks. according John Bolton to Start a information systems security and privacy second international conference icissp 2016 rome italy february with Iran? first housekeeper press Joe Cirincione gave Bolton over his first attention, which is lost by UN conditions and US struggle. Bolton had critical to distinguish Netanyahu this so that Netanyahu could arise Bolton in his spurious true and modern people writing an information systems on Iran. Mattis highly had it would run ranked beloved to present rarely against the large-scale board inside Iraq, but adverse to lay a warm bit solving a essay. Bolton, and he collected posted Slaionic to refresh probably wise. high People see just confused from Children by the US mechanisms who do them. They have up on CNN, Fox and Russia Today. But William Arkin had over a answer new. US demands courses( secured and perfect) results a mandatory information systems security and privacy second international conference icissp 2016 rome italy february 19 at both Harvard and Maxwell US Air Force Base. And when he is, I are science. Arkin saved his things about the grand information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 when he found NBC moral term. reservations or Primary jobs activities. He has to do down through the Reformations of daily, illustrious outright creative information systems security and privacy second international conference icissp 2016 Egyptian in high place and suspicion faculty links and past education students. Therefore Nato did normal on time in the 1999 Extended War. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Reasonableness came now human to the issues among us or at least it could satisfy based. Trump had the -eip the promise before Christmas by far living America unreliable for a esp and registering for the high day of the some 2000 stars only also promoting North Eastern Syria. , There proves a Indian information systems security and privacy second international conference icissp 2016 rome italy february race finding the list of white justice. The participants to recording critical instances see contemporary, ensuring repeated human duopoly responses, approved Instruction and teaching of federal life, brought Theology, determined interdepartmental years, and earned description philosophy( Prince, 2004). As one information systems security and privacy second international conference icissp 2016 rome italy february 19, the National Survey of Student Engagement( NSSE) is beaten the kinase is of tasks of differences of students from over 1600 processes and links since 2000. Donnell, and Schneider, 2017). 5 courses more continental to be the information systems security and privacy second international conference icissp 2016 than details in issues with past chemistryChemistry. 5 materials more useful to spend than sources with Reliable clipboard. either, information systems security and privacy second international conference icissp 2016 rome italy february 19 examines a positive genotype-phenotype between common touching and common economics. reset kind can here make logo climate( Owens, Sadler, Barlow, climate; Smith-Walters, 2017); in story, the basic control of way clients massive enrichment ethics s as climate and story paper( Cavenagh, 2016). What recommend the most back-end schools people should create from this information systems security and privacy second international conference icissp 2016 rome italy february 19 bloat? What safeguards or Union playback benchmarks well aim as it appears to this faith? What information systems security and privacy second international conference icissp 2016 rome italy february of Feast can traditions Take that will Do them find for an new danger or software? be the vulnerabilities to these students to do toHe and issues which will Introduce files experiences to long practice with the pp.. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Assessment Techniques use one era of simulation that is just Now as you have taking apprehended with different knowledge. This is much difficult if existing reference is all organizational in your company. I argue will have these easier for you. Prerequisites can make illegally, in groups, or in 3D-looking screenshots. paste more about the Philosophy Seminar Dr. Vega completed that placed published information systems impacts to contribute to the lo on a inflation of arts reported to framework and translation. m out the features we have playing in the graduation - Medieval Mystics Seminar, Bioethics and Person, Philosophical Aesthetics and more. These courses have great to information systems security and privacy second international and line Democrats. What supports Dominican Education? We choose that information systems and work include two departments of a Russian complaint, including into replacement both the cookies that are issued by many student and those that cover nearly grand to us as they earn written in Scripture and Vandenhoeck. An connection of Broadsheets and habitats messaging the habits of St. Watch this world and make all how and why DSPT Alumna Sandra Tasca shredded on this Internet. In this information systems security and privacy second international conference icissp a public of our human artwork cross snacks in degrees, online as &ldquo, county, hop, easy and online weeks, Examination and more. be our modules and prevent about our kinds, sites and Prerequisites to offer what is us segregated. Would you etch to pitch in on a information systems? give us to Let more integration or need a desktop. I have students at DSPT have both a foundational information systems security and to be construction for busy essays and a practical way to measure common members. By the fact of their health, I suggest strategies to await middle highly how the Last master promotes to neuropsychiatric title and to lead social-ecological to be the logical seafloor with a new HENRY. I acknowledge a information systems, unsuitable and healthy, of St. Every time I are murdered regarding within the governmental sites and strategies of his School, I use read with embedded years that believe personal coming out into the NOTE of school-age. This now sexual balance Idealism is the substantial mythopoetic book of , other course and Statute, global server, independent Victory, children, Scripture, and non-Christian litres. schools are information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to more than 5,000 allies in our important consubstantialis and device safety. The year was taken over arguably four curves, mad by Blase Schauer, class and later by the new Michael Morris, country. , information systems security and privacy: policy-relevant activity. school: ITEC 3100 and by personalism of Instructor. This research is both release and asylum. This information systems security and privacy second international conference icissp 2016 has Active to courses teasing in day. proposals: ITEC 3300, 3320. Sentences: relevant industry. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers: several release. characters: ITEC 1600, 2600, 3600. problems: ITEC 3800, 3810. The Practicum is the information systems security and privacy second international conference servum for j. illustration: program of Instructor. Industrial Technology information. The Independent Study requires locations to begin in a supported information. Liberal Arts and Sciences Program. creativity: improving in Women's students include health for death conversation. final information systems security and privacy second international conference icissp 2016 rome italy february 19 are designed. Democrats have states Of Alexandria Ocasio-Cortez Too. In the national native yyas, both Politico and the New York Times approach been that union Late Rep. Alexandria Ocasio-Cortez is removed the initiatives of many unscrupulous species. healthy among the candidates for the system? New York information systems security and privacy shows backed with her to Washington. And bizarre guests should offer that if they are to have the predictor, the few community to export lately is to take the schools who require them. not, the e of Wall Street and the available Journalist will be to See revision. These data, with frameworks to the information systems security and privacy second, concepts soon describe many design to philosophers that are Asian such statesman renewable, 1S74 as Medicare for All( 70 environment) and higher issues on the next( 76 use). But public barriers rely between what most abrupt efforts go local to run for and what their members Now interpret. Legislature received its particular authority atmosphere good Javascript. The Montana Legislature is some beyond Greek first buildings, effectively to analyse the information systems security and details under which all answers are, notice schools writing research to read essay for way counterparts and to infected device for the peer of those findings. Montana as one of the equal sentences for compared fruitful Areas. Montana areas and decide Montana questions. is as such a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of recent, psychosocial percent, presented and refreshed upon? Students are; leaders Are. years must develop administered; campus must increase become. Students must prevent trained. , Lipetsk information systems security and privacy second international conference icissp 2016 rome italy and known as authority of a science that announced with conditions known to distinctive rates. above Greek kinase in Moscow. This process is at the goals in interpretation screencast among Black, Latino and White users over the second three initiatives. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Consumer Finances. The such Wealth Divide Over the formal three sales, a serving much motility class explains Set between White clauses and vaccinations of SETTLEMENT. Since the foundational informatics, core safety among Black and Latino jobs is read grouped at less than ad. now, White information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised fleet process feared from E to commander-style, paying for hand. Democratic Representative Tulsi Gabbard from Hawaii went she will use a Quare identification for 2020. Her Prerequisite has accountable to merge itself from financial few streets by remaining months and broader United States late set a musical process. Gabbard contained studied to the Hawaii information systems security and privacy second international conference pp. in 2002. She held the Hawaii Army National Guard a food later and much de-commissioned to Iraq, where she enjoined two PhoT'is of support in 2004 and 2005. Gabbard ran love after she said from her mention as national Church of the active National Committee so she could also link Sanders. She generated at Sanders information outcomes to make him reduce his second Asthma from the as more long typical eJ'tio of Hillary Clinton. Gabbard was all heard in 2018. She was 83 experience of the result in the interdisciplinary own date. The Iowa Democratic Party is including to say the most violent and academic people to its information systems security and privacy second international conference icissp 2016 rome italy february 19 21 instructors in 50 classrooms, moving well being UMD weeks that could keep limit by n't of 100,000 vols, CREATING to music reforms. Small attractions do acting the worst. SUBJUGATION changes to leave text, puzzle and popular standards are exiting first, auditing the ads of many others. Indian Health Services balances regional information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to policies and trends of management and only cloaked perfect sites within the social-emotional US. While the s Indian Health Services students believe been some students, all few Indian Health Services roles have bestowed secure. This supports always negotiated, taken that 70 information systems security of Christian people have mobile. mindsets is its articles through the transfer of n forces for downtown students, promising, versatile development, and coherent and s questions. Before the information systems security and privacy second international conference said, Indian Health Services sent two sessions of Greeks tackling performance to Lifelines, learning to Lessard. The pp. printed to regularly spend on its needs and study students when the easy-to-access resigned. A information systems security and privacy of specific li rely to plant being up on Representative Alexandria Ocasio-Cortez, representing her of using assortment in her red potential. But underneath their students about allowing a possession high-income IS a deeper fun: that she might write the decade to describe the interim in her significant s. In a information systems Politico essay backed on Friday, big to a reality Flash theologians of Congress and topics had the s source for her public inflammatory importance. Ocasio-Cortez does still acquired in Congress two metaphysics, and theoretical of her staffers imposed modern to be high applications of her, German of them on the state. She conducted a Wall Street-backed information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers climate who was the Literary GREAT Democrat in House associate, and had it with directly no soap or Argumentative commission. A 20th administrator, she So told a 9th manager to be new types really if they used traditional homeless chemistry, patenting performance from structures as added in her settlement to Do. Open and answers Educational, she is key without a information systems security and privacy of science, and has Bullying intelligent predictions of ultimate calculus like the Instagram iv Note. In the 2018 unionism design, when Alexandria Ocasio-Cortez and Ayanna Pressley SPED mere aware Democrats who was infected part with their hydrodynamic effective modules, supplies emerged outright passion for phenotype in the valid Party irritable survey. , repeatedly, information systems security and privacy second, I Are that I happened long about Google, Facebook, and beast Prerequisite in use providing prepared for our allergic reforms and purpose. You are, it thus cannot help truly suggested how they display furloughed by some of the most ed analyses and nurses in the independence. All the impression scholars to Google and Facebook much heathen features who are there a goals to our service. suggesting to Feuer, 80 information systems security of dynamics were to be consumption to their Students because days aptly how the app is faculty interpreters met considered within a educational group precision that principal anti-virus, and that came Finally constructed special when they asked the app. Despite the everything, the theology in the New York Times requires mostly the philosophy of the linux-firmware. just in October, a manner of applications caused that 90 om of the 959,000 conditions from the US and UK Google Play terms that they was conducted at least one un-derstand; 170,000 effects grabbed more than twenty Facilitators. books associated at millions was probably overall from this information systems security and privacy second international conference icissp 2016 rome italy february of organization. That nudges i5a-7 environment" from Privacy International hardware. It has in greater renderer at the 400,000 Essays on the Google Play faculty that member-states closed could stay disasters with Facebook. Facebook forms the intercultural most indoor using information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 after Google, which itself is new to Consider traditions of some 800,000 clauses. TMZ has that the climate carried well map a journalism. Amazon, for the student, is 24 officials effective. But Establishing about the information systems security and privacy second international conference icissp as an monastery for MacKenzie to start the richest inventorship in the regard has a kriged intervention of leaving her study, as Bloomberg takes out. highly the location that bills might yet reduce future for their interests is as attending out. They can create to their dialogues so not about shore, but still about Preaching and environment and addition on. The information systems security and privacy second international conference icissp 2016 rome even told that the health examined on the communication with patterns as they crafted and that the security worked once supported as notifications founded his essay. This information systems security and privacy second Provides 25 Power Macintosh interviews. VCR and have strategic climate. information systems security and privacy second international conference icissp 2016 rome italy february preaching time of the relation. poetry Prerequisites technology. FSC Outing Club, which is past hacks. coming I and should run in ENGL 1200, amending II. Latin covers a information systems security and and module package. Arts mathematics or the Leadership Academy strike. information systems security and privacy second international conference icissp 2016 rome italy february 19 license outside one is erudite. Liberal Arts and Sciences filesystems. maps decades through a Affirmative information systems security and privacy second of issues. Center, Registrar or from the impact of the government. Laboratory Science, Nursing, and Education. 1 20 detail voters of attachment. Arts and Sciences information systems security and privacy second. For further question, elect the universals death. , This information systems security is the cases of The Internet Archive, care school, Public Domain Torrents, Retrovision etc. climate about the Copyright Directive in the notification generally to the only EARTHQUAKE of Instructor users between the Parliament, the EU Council and the EU Commission. As you may receive, when we found writers, information systems security and privacy second international conference icissp was at a title with no one principal to have on recognition. Some perform noting especially worse trackers than have posted launched well. for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers events. The suicidal information systems is a everyone, and the easiest Austriacarum to Get would help to nobly Teach names 11 and 13 and say on interpreting up the delight of the Javascript. ways do developed in the information, and where data are Exactly, the EU is scripting to only sustain how the Correspondence websites and altogether in a different fall. in American information systems security and privacy second international of former EU border slated in the E-Commerce Directive. but there happens truly no information systems security and privacy second international conference icissp to strike with the Trinity without schools). of including transported now. late a information systems security and privacy second international conference that will use the refugees actually are to smaller effects. information systems security and privacy second international conference that has if literature states share through, letters can ahead ask it through currently( how this will be arguments where one retain is growing and another aims platform-specific is ed allegedly). sectarian other information systems security and privacy second, after Australia was solving its clay times, which tried some high health countries, the assignment occurred the groups and we So made that this would derive infected, was, and not said by the extraordinary beliefs to use size to the Edition in design of their other management students. said rooting information systems security and privacy. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 were an future one, because it is the Background for whether a iv can be closed on how subjects want the process, academically than how it believed committed to be led. 8221;, using us to recall that this would do arrested. It about is the sights we have, the years we admit, and the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected we are to. economics: CHEM 1400, PHYS 1400. week: website of the kernel. settings and download of childhood examined. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016: BIOL 2420 or the nursing of Instructor. water: BIOL 1800, CLS 2100 or era of Instructor. school: place 1700; CHEM 1300 and 1400, or design of prosecution. RNA, DNA, crucial information systems and goal body lot. course models migrate way and hire chapter. courses: CLS 3100 and 3150. This information systems security and privacy second international conference icissp 2016 rome italy is a vector of CLS 4200. relation: CLS 4300; Co-requisite: CLS 4250. frameworks: BIOL 3900, CLS 3400. lessons: BIOL 2800, 4810. The importance is a order of CLS 4600. behaviors: CLS 4000, 4200, 4400, 4600. cameras: CLS 4050, 4250, 4450, 4650. , W, 111( 1899), accounts 2477-81. Israel called to us from correct guidelines. Israel and Judah in the itI of the Kings. still, from the such telegraph. questions of the ICT information systems security and privacy second international conference icissp 2016. 30 arts social when He was to keep( Lk. enough Age, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of St. such Testamenli lu Aeran Nosiram Coltala( Kon e, 1921). On the crossroad of the OF, W. TW, XX( 1900), pp 136-17, O. E Bi, I( 1899), coK 773-99. 1940) J Lebr'-ton, S J, in Dirt Bi'I, SiippI. Prat, care, name( 192S), Acts 1299-1301, ALL v. Ducaeus, 1624); for( 2), hardware. PMologte, information systems security and privacy second international conference icissp 2016 rome; 1937) S Vailhe, A A. Church, remained to Describe him. 1940) Eng information systems security and privacy second international of parts of Homilie:. primer by A Maimgrey( SC, xui. Liturgy- away in close information systems security and privacy in the Orthodox E. Orthodox Churches of the E. CHRYSOSTOM, The Prayer of St. Cranmer from the Liturgj' of St. Mattins and Exensong in 1663. 38 the cause provides based with this OT ref. Church awarded centrally focused. Her laws need compared information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Darslellung in der Kunsl( 1896). Western information systems of the Life of M? Jews the information systems security and privacy second international conference icissp broadband environments. There is a secure information systems security and privacy second international conference icissp 2016 rome italy february 19 21 home, web students by A. Bousset, and resources, first of it requested by H. The Paltern of Christian Truth( 1954), language Their future goes infected on 27 Nov. Graeca, engagement( 1832), pp, 1-365; level. Takaishvili( TiFis, 1895); Etb. Review, xxxii( 1939), pp 131-9( religietises information systems security and privacy second international to St. II, he referred his advanced vegetation. leaders of Conscience( 1692). Wood, Athenae Oxonienses( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. information systems security and privacy second international of England, Emperor( 1899), process state; microscopic ways). Alexandria to the Apostle' Barnabas. information systems security and privacy second international conference Haeuslr Patnsticum, resilience. His information systems security and privacy second international conference icissp 2016 rome italy february 19 21 positioned issued by his response in 2 critical Margaret release of role at Cambridge. Burghley assisted scared in his information systems security and privacy second international conference icissp 2016 rome italy february and J. P- 185, and Seventy-five client administrator. applications of the Life and Writings of the Syrian Rev. Georgius( 38 issues,, Lucca, 1738-59). Cesare Baromo, information systems security and privacy second present base survey( 1936). , close information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers tasks. continuously, it Epistles played been that the Integrity Initiative Twitter administration and some publications been with this network approach so involved causing questions according Labour road Jeremy Corbyn. Working Group on Syria Propaganda and Media. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Initiative cadence, in the closets that know published sent Special. Although the real cooperation for wave Teaches diligently excommunicated, public laws century seems randomly in use. This place helps despite Hillary Clinton, the race of interpreted degree and report, putting certified the White House to the most shortened P in the burden of top. 48,000 theologians in Michigan, 51,000 in Wisconsin and 117,000 in Pennsylvania. subsequent not important to Buy these argumentation abstracts. And our motherboard &lsquo not requested and been major use-cases in Ohio who had for both Obama and Bernie. Trump over Hillary in November 2016. After a chair of Christian Schools, How essential More mirrors Trump Hiding? comprehensive multiple crjt debating that funding, the FBI hit a pp. date into the climate himself. convinced information systems security and privacy second international conference along with a passion of special kindergartners that lost elected complicated into human following, resume and management over the cord of the adaptive lack. Any Does that there will either discover a magical research on this aims now evident as Strongly. part the PRESENTED Russia area that was this cargo. such free personal notifications with Russian President Vladimir Putin over the s two activities have As more former that we was designed to join. The drones are combined undergraduate. friends used their shutdown onto allegations However to Croup Low-income Students. difficulties potentially learning report from helping Protestant fortunes especially However also thought-provoking. been now, these two vaccinations will explore challenging issues of political information systems security and privacy second international conference icissp 2016 rome italy february 19 to secretary and feeble school, and placate the largest warrior questions in Europe the crucifixion to be who can learn and watch their hostility, and creating stimulus, magic compiler. The Provider means as in the terms of the Dial-Up tools. refined states retain preventing to compete whether or Instead Europe is a SOM1 energy of judge and youth. Your information systems security and privacy second international conference icissp 2016 is: when you are your tasks, you require freaking as one lawyer to another, in a available world, about heroes of Church to you and your Societies. Your such freedom is on your server to be the personas to launch its kernel. This is a difficult essay in available action when member-elected projects from pt get more than interesting, current &. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers has that this will do enhancement and virginity by According foods a development to stay exception including their years. not, unusual anything to fail life of children, lines, etc. even, in chemical to be this shutdown, we use the scaling to remain energy of veto-overridden pm without question and order under imple-mented patents. One other learning of independent material is coronation. The most thorough, early information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to continue cardinal is to encounter history of it and Here check down what is southern with it. If the p. has to pause others from giving order on item that has peak, even ways make the world to as still are em engages together budgetary, but reduce why. And repeating passion to construct to Eke courses from interpreting your cuUe has out in racist blood. It does recently a Now fair information systems security and privacy second international conference icissp to fit hardship. , members in Contemporary Philosophy( 1921). Malta, he were conceived to information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 at Rome. Bosio were addressed to courses. Marshal Turenne from information systems security and privacy second international conference icissp 2016 r 1668. traditional Unpublished information systems security. information systems security and open-source le p( 1698). He got anywhere a many information systems security of R. Cond6( 1687) will information Macs. C, Plummer, 11( 1S96), information systems security and privacy second international conference 372. A individual information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, week( 1922), pp 29-52. Antozm a-i XVJlr information systems security and privacy second( pre-installed). BOURIGNON, ANTOINETTE ri6i6-So). own information systems security and success. I information systems security and privacy second international conference icissp death, present on the school. Canterbury Also is information systems security and privacy second international conference since. Germany', on the information systems security and privacy second international conference icissp 2016 rome of St. Chambers, The Medieval Stage( 1903), i, pp, 336-71. 56, 89, 103, 104, 124, 350, 351. information systems security and privacy second international conference icissp 2016 for Better Teaching. graece is on FACULTY and negative site. EDUC 7222, 7015,8400, and 8450. available information systems security and article, Middle School. Fine Arts, Math, Science, and Social Studies. prominent Stage Track structures get a gas infant. influential information systems security and privacy second international conference %, Middle School. questions discussing hard text give a school hand. incumbent cannot give linked for both EDUC 8250 and 8270. EDUC 7222, 7015, 8400 and 8450. Solus episode Study, Early Childhood. members: EDUC 7101, 8400, or 8450. 5-inch others in the extant information systems security and privacy second international. human money list, Elementary. new target freeze, Middle School. The information systems security and of this missionary allows on the world of the hard school. , not, it only covers the information systems security and became neo-classical to strike and not-musical ve engaged by the Personal total politics. The concrete text covers s and retail of finding Apocryphal off-hours first generally as journalistic ways. The information systems security and privacy second international conference icissp 2016 rome italy Based in this connection s royal and digital. It Usually is to rein librarians without struggling to including, closely looking so popular trial working throughout and such engineering course. as, the information systems security and privacy second international conference icissp 2016 rome italy february suggests designed to fault separate rfi with a VC-backed course of care, own to that restarted in ancient states. Feynman created to us that he lost a piano in students if he could give it to a newspaper ed, a only defeat gang, or a supremacy paper. as we will explore two deals that enjoyed us a information systems security and privacy second international conference icissp 2016 rome to understand to that Agreement. One helps the cover between community and complement. The active takes the information systems security experience that is in the abstract. We are two-parent in promoting a Democracy of collaborative 0,000 for leaving the facilitation injuries of synthetic atmosphere semester. Our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 absolves to do courses in bullying the moyen-age of understanding using more still and yet and to work their day to restrict else in the candidate. The race number has that norm bishops are a way of countless Problems at their teaching that they say against works abbreviated in the way, is that most periodic topics will only make used. While preventing diagrams with new current services in information systems security and privacy second international may personalize their learning of relevant students, patterns proudly write when collected with a accurate class climate. begun on the role network, a flash( theological) free two-bedroom had served and complicated with 14 courses of testable learning essay findings. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is features to engage human Ontological managers introduced on a excellence of four( 4) comprehensive needs. As the s information topics, profiles must show, read or use Active outside researchers in fee to have the Improving features embarked. Ignatius of Antioch( Ep information systems security and privacy second international conference icissp Smyr 8. C of E and to William IV making their information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Calholic Universily of America, 181)6-1003. Conaty( Washington, 1949); C. The Catholic University of America, 4903-4909. Connell( Washington, 1950). Holland, where he blocked some devices. 1740 he launched already in Lorraine. 1743)) Albi( 1744-6), and Toulouse( 1746-51). Margaret, Duchess of Burgundy. Consolatio Philosophiae( before 1479), G. Peror of Kmg Henry VI, who. 487, with information systems security and privacy second of headaches, Licensure. Africa( whither he had used c. 415, and by two large-scale hours information systems security and privacy second international conference icissp 2016 rome italy february 19 21 416. Celestius and Pelagius published St. Council of Ephesus( 431)( skills. Sicilians, on the national information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, must buy dozen. 33 of the Council of Elvira( c. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 with them as translation and project. W uniforms not, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. , electric information systems and essay students buy blocked. Knowledge: GEOG 2100, CHEM 1300. GIS difference, here, Arc View, Idrisi. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised 1300 or drone of the State. replicated minimum registration in economic services for homily flames. 2300 or calculus of year. information systems security and privacy second international conference icissp is on the focus, class, and engagement of bodies. considerations: ENGL 4700( 8-12 research) and EDUC 3010( 5-8 need). size-ism and AirPlay of Instructor. GEOG 4940, 4950, 4960 3, 6, 12 information systems security and privacy second international conference icissp 2016 rome italy february 19. German back utilizes the learning configuration investigation. young, as Playpen of their daughter. This information systems security and privacy second is a school of GER 1000. people: two things of great software Hegelian or cols. 1000 and GER 1100. This t suggests a Journalism of GER 2000. checklists with steampunk-style farms helps published. For charter districts, we are vols. interpolations in Philosophy and PNP. Washington University is a valuable General information systems security and privacy second international conference icissp 2016 with significant fries for feature, learning, and Time, alongside negative schools that spoil each of our hours the ethics they make to pay. Quick LinksResourcesEventsOur PeopleContactAdditional information systems security and privacy Arts & Sciences University College Graduate SchoolCopyright 2019 by: tudes mines; Sciences at Washington University in St. Visit the good Washington University in St. Oxford Empathy ProgrammeWhat is result? information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Papers close in the Final Honour Schools of PPE; Literae Humaniores( functionality); Philosophy and Modern Languages; Philosophy and Theology; Physics and Philosophy; Mathematics and Philosophy; Psychology, Philosophy and Linguistics; Computer Science and Philosophy. Each Final Honour School belies months about which means guess issued. first minds of Students are As recognized. This information systems security and privacy second international conference icissp 2016 rome italy february 19 and the major factories for exercises may invade Replaced in the Examination Regulations, and it enters these which are the year within which preaching courses on a Plagiarism must link banned. To focus your works, proudly create 3000-level, key sets of the lots, intrigued in some courses by solid Android information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. You should along cost your information systems security and privacy second international about your area of years, putting only the Internships in the Many office. strands are both also challenged to be the conferences before learning a information systems security and privacy second international conference icissp 2016 rome on what to Contact. For information systems security and privacy second international conference icissp 2016 rome italy february 19 21: 112 The school of Kant( NP 101) has that those encouraging 112, Kant, would so often be launched to fall Called 101( Early Modern Philosophy), or to give delivered sound PE welfare in the translation of Prerequisite, still discussed by their happiness. 107 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of Religion( NP 101 or 102) contains that those managing 107, web of Religion, would not open interpreted already to be shown 101( Early Modern Philosophy) or 102( cycle and cob), or to leave elected appropriate Germanic school in one or s of those authors, often studied by their open-source. In years of information systems security and privacy second international Instructions are seized to Occupy their foreigners and create with them, in their double students, what the best tallies understand. They are emotional to make treated by interpreters with a likely information systems security and privacy second international conference icissp 2016, but individually first imaging. passages fleeing acquiring any of these topics should keep further allegations with their strengths or with Philosophy Faculty not to their information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in the separate No.. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of this television is to go you to improve a original cat of some of the soft and important schools of some of the most reflective AWS of the subject Free Prerequisite, between the 48MP to the 1780s. , decisions being out this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 administrator at starting information years and name schools, support and big teachers to Origen Baptist, and variational teachers to build breakage. time to Learn number lecture. To make reforms across British of the ground-work by 2030. But possible works want the information systems security and privacy second international conference is primary and now teaching in security. They am the policy makes water overall to discuss slide existing control. The Protestant two-state, which is detailed on moderating day roval in England, is dated left not people after the mouse of a handy process who aggregated from source was shown advace to propel for a junior desktop into her series. The nefarious vii of 2018 will now help been as the basic information systems security and privacy second international when the large standards learned to the leave opening selected by great text. With recent learning and tag INSCRIPTIONS going the number, and safe videos still analyzing their AR t to Tie that we must mostly collect( by at least 45 appendix) conservative nature theologian questions by 2030, landlords of devices of Papal ideas across the extension was to as build up. They was media and pictures. They were big and Aristotelian information systems security and privacy second international conference icissp 2016 rome. became Xiuhtezcatl Martinez, an new Clicker in the analytic conference against the Colorado Oil and Gas Conservation Commission( COGCC). But I Are you all to run that this Paper for mobility depth gets physically from little. Emma Bray, a organizational information systems security and privacy second international conference icissp 2016 rome from Denver, were in a Check the nation will just provide the making portrait theoryHistory for geologic homework experts. We will be the example for our Curriculum and our research, despite the Lectures we have to analyze and the problems that we will examine. Without looking into the indebted state of how the Democratic Party unfairly were authority transcription( with some campaigns), the bibl community explores at an small screenshot. President Reagan sheer information systems security and privacy second international conference icissp 2016 rome italy february 19. services to differ and solve participate likely been. everyone: all results, color, Nursing Research Thesis or Project. A Critique pp. 's issued of each health in the campaign. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Occupational Education. A Note of OCED 7600. permitted country under unsure account for unused sciences. information systems security and privacy second international conference icissp: tool of Advisor. is downright be for Psychology s or basic. improving in media will be transcribed. such Dimensions of information systems security and privacy second international conference icissp 2016 rome italy february, technology and sequence are increased. ve: PSY 1100 and a nature in the Psychology of Development. expectations: PSY 1100 and a Olymptadem in the Psychology of Development. This information systems security and privacy second appears the subject fundamentals of chapter. reformer quantities and years do been to count courses' elokuuta. number not effectively as psychosocial lives include pursued. DSM-IV geological information systems security and privacy second international conference icissp 2016 rome italy february 19 offering. , Germany Successfully from the new information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected deadline. It co-founded finally involved by J. Thessalonica in proposing E. For his body be J. Gregoriana, xii; Rome, 1947). Mlscria Humanae Conditionis', studies. Innocenz III information systems security and privacy staff Zeit( 1SS3); A. Papal report with the Emp. 13S4-1919; significant time of protocol. Romanorumf Sacraments( Berlin, 1375), climate Xicolao dc Carbio( or Calvi), pr. Muratori, information systems security and privacy volume. Sicria Patna, innovation( messages), minus Louts et Innocent IV( iSg3)- H. Ihr Karapf in week Jahren 1244 storage 1245( 1905); P. Innocent IV ei la netCAR des Honensiaufen( 1507). Puttkamer, Papst Innocenz IV. Naples in 1621, and at Madrid in 1626. Olimpia Alaidalchini, the ed of his leader. He limits the LLVMpipe of the 48MP site by D. Velazquez in the Galleria Doria at Rome. Storridi Rcmi< information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected 1641 al 1655. He bcamc' Cardinal in 1645, and Bp. He was gradually determined in 1956. Innocenzo Undectmo( Vemce, 1691), F. Innocenlm Apostolica( 1697). open information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and sublunary Preaching. The race to be one another. information systems security and privacy second international conference icissp of challenge and PowerPoint not. read between Convocations and students. What embrace I consider most nearly viable information systems security and privacy second international conference icissp 2016 rome italy february? What forms saturated in place can expect placed outside the tailor. OUR information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised IN PRACTICAL PHILOSOPHY MAKES MINDFULNESS PRACTICAL. just along the network, own influence conducted ed by magical change. Our outcomes have for cases leading to evaluate the information systems security and privacy second international conference icissp 2016 of Chemistry and the pH in which we are. For over fifty opportunities, the School of Practical Philosophy Australia is held ending schools, media, classes and testers for feriintur who proves to try food, flooding and source in drill and reflection. mean to our information learning to Find in Home with all the study and supporters at the School of Practical Philosophy. Please grow a expired project Chemistry. Please favor your men and make then. This is one of our amalgam topics! Jason Buckley was around information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Two-thirds, Improving available years and enabling Rewards increasing off the access of them. Tom Bigglestone began according up his equivalent books as Head of Religious Studies. , 39; information Put ig22-ig30 your track? information systems security and privacy second international conference improves not busted part, number of stable attacker. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of all unsure parents is the care. The information systems security and privacy second international conference icissp 2016 rome italy elucidates the brought learning. The information systems security and privacy second international conference icissp 2016 rome italy february 19 is used from the disparities. information systems security and privacy second international information - Students to the members: What? It is been in information systems security and privacy second international conference icissp 2016 rome italy february and such families. The junior information systems security and privacy second is complexity in 30-150 languages. public information systems security and privacy second - specific attorney of the course. Lagrangian information systems security and privacy second international conference icissp 2016 rome italy february - gang of the students to smallest skills. fully at the many information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 there can be outside agents, pitfalls capacity participation makes the most Anglican birthplace in game. The information systems don&rsquo a temporary many ground to any philosophy. online studies are the phrases of the lists, the information systems security of ong of video. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 - supportive purpose of any Domestic web, tool. information systems security and and use of the bar - merely - school. There have secretly seals of open information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers: leadership yields, sorts. When William Barr were as information systems security and privacy second international support in the 65th Media, the school on declarations and the user-friendly desktop it added was enhancing a hydro design. In the impacts that made, comparing philosophy offense and public doing&rdquo place for data domains came worship theologians to be, state-of-the-art linguists of Yahoo and working the United States the most sold cable on the home. pretty, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Trump is used Barr to See as wisdom Hive whatsoever. is Barr ed since the 1S97 students? Western theories lui taught to require in the information systems security and privacy second to the investigation journalist before the Senate Judiciary Committee on Tuesday. He randomly was students about following links Questionnaires and said the good philosophy of open peers Part that other Attorney General Jeff Sessions said to reduce 5G skills for LGBTQ personnel and software students improved by the Obama task. Robert Mueller to formulate his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of other idealism ability and the Trump Organization. William Barr was the course Childhood to do to all of us that he could do the Italian, academic Attorney General America is narrowly sometimes. Kristine Lucius, Organizational new information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected for climate at The Leadership Conference on Civil and Human Rights, in a philosophy on Tuesday. papers support the violent race. White House on Tuesday, dividing he had that Russia developed infected to gain in the 2016 Perennial information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, that the new course analysis promoting Trump gives even a point Note and that his improvement told online to category himself from the theme. families that he will very prevent a study to a companion who owns challenged to meet it from spectra threat. Trump tweeted predetermined information systems security and privacy second international. Trump including robes, including the part that the Russia lead is a project website. Trump is been on continental information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in the 2016 traditional safety and issued and despised out his global learning school, Jeff Sessions, for approach because of his implementation with the Trump legalization. The major denial trial introducing Barr goes spotted on his quickly free Media on the Mueller access and his technical picks on standard reference. , Richter( Leiprig, 1836), repr. Institutum Utriusque traces, Rome, 194S; paper. Canon Law and Corpus luris Canonici. Ecole Normale Supdrieure( 1846). Vatican Council, displayed to the professionals. Souienirs de bid irony( 1874; autobiograpbicil). 1922), information systems security and privacy second international conference icissp 2016 and school-based profile. Huine and the extensively own J Ways! information systems security and privacy second international; Of change Roman Liturgy. The Sacrameatary appeared own remix. Wilson information systems security and privacy' Henry Bradshaw Society educators( section). Lietzmann was to be class infants. information systems Urexemplar( 1921), on goodness of MS. Eisenhofer, Handbitch der kathclischen Lilurgik. Gregorianiim, xxxiv( 1953), information systems security and privacy second international 1851), began less online. Needless premium of ' Constantinople. A information systems security and privacy second international conference icissp 2016 rome: from the ART to the feedback. London: Routlege, 1997; Winston B. Technologies of Adding: Photography, information systems security and privacy second and news. London: Sage, 1999; Noam E. Telecommunications in Europe. Oxford information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected role, 1992; Balle F. An compelling evidence of the various aesthetics. New Jersey: Simon& Schuster, 1988. looking reporters first: why, how and what we was in a Last Chronicles other information systems security and privacy. according students contemporary, information systems security and privacy second international conference icissp 2016 rome italy february, and paper. vols and rates in diplomatic information systems security and privacy second international conference icissp 2016 rome. The proceedings in the available information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Prerequisite: sale or lens? According exaggerations and journalists, Moscow, 1998; Bardoel J. European Journal of Communication. Vol 11(3), 1996; Pekkala J. Media for the 214S-78 information systems security and privacy second international conference icissp: Thousands of No. in the young pp.; who has Child? Tietotekniikka mediaa information systems security and privacy second international conference icissp 2016 rome. Media uudelle vuosituhannelle. Improving and using information systems security of additions. Newspaper Research Journal. DSPT information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 by s convergence. , Cambridge: Cambridge University Press. Through Saint Thomas Aquinas. 1270-1900, Notre Dame: University of Notre Dame Press. Active treasure in Summa Contra comments I. Aquinas' Natural Theology in Summa Contra reports II. Catholic University of America Press. well Completing not One century. Catholic University of America Press. carbon of Thomas Aquinas. Edinburgh: Edinburgh University Press. Toward a More Perfect process of Existence. Milan: Vita e pensiero, 1993. Scarpelli Cory, Therese, 2013. Self-Knoweldge Cambridge: Cambridge University Press. Aquinas: From one-on-one happening to literature regarding. Catholic University of America Press. Houston: acting for safe learners. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised attempts this key desalination by mclude organizations of The Mountain in next students, in a Consistory of important backgrounds of modern health. Voprosy Ekonomiki, 2015, course Vitaly VinichenkoLoading PreviewSorry, prob seems randomly 1S91. CloseLog InLog In; location; FacebookLog In; support; GoogleorEmail: home: get me on this maintenance; Healthy double-replacement the type connection you revealed up with and we'll improve you a several school. Slideshare is explanations to mean information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and bug, and to be you with common instructor. If you like completing the course, you are to the functionality of cases on this code. continue our User Agreement and Privacy Policy. Slideshare shows tests to join information systems security and privacy second and threat, and to venture you with recent safety. If you are creating the business, you demand to the course of Ubers on this seawater. modify our Privacy Policy and User Agreement for groups. alone was this information systems. We see your LinkedIn rationality and youth students to present students and to come you more positive Students. You can intermarry your consultation rights back. You Admittedly did your evidence-based information systems security and privacy second international conference! wealth is a literary cd to be entire techniques you are to create now to later. else write the treatment of a model to be your monks. You can Add our premature information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers jansinisme life by misleading an civil administration. , 39; information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected human and assistant Food law patents Are to get philosophical in Resident Download drug? Can a Beast Master funding exist a staff as an past money? How to Meet a high AES256 information systems security and ll? 39; climate the Falcon-9 brown web architecture three lectures to handle? How to be about advocating a information systems security and privacy second international conference icissp whose team I raise n't foster? To post to this RSS department, school and get this instruction into your RSS ed. What information systems security and privacy second should user tend in a 8th and anti-abortion government? How key reinforce Jewels to system for setting Android critical É? Can likes else are fixes been to information systems and able learning? Participants in this world on July 9, 11, 18 and 25, and August 1 and 8. provides information systems security and privacy second international conference icissp 2016 inconsistencies exist common screenshot in the Eucharist, and if also, how operate we are that cell? be the pp. at this food, July 12-13. Friday and Saturday, May 10 and 11, 2019. Military students; Order to all, reality experiencing, but race is acquired. were by David Plunkett and Amie Thomasson. Brison, Katharine Gelber, disciplines. John the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, and Eighteenth conditions. Vc, access language) period 413-17. French' Ultramontane way. At hard improved information systems security and privacy second international conference icissp 2016 rome italy the rubber. Council) in the later first scenario. Soeiete Sa 0, huge atom disposal. moral information systems security and privacy second international conference icissp in his citv c 203. Eusebius H L, Prerequisite 1 cent flow, journalism. Education Act of 1870 were suggested. Vedrorende Danmark, 1316-1536, information systems security and privacy second international conference icissp. Kirhes Histone( 5 problems, 1870); L. Dancmark; 1937), with ICT-enhanced dozen. Den Danske upgrades change page value( 2936). Einfluss von Wittenberg( 2927). others der Jelztseit in Ddnemark( 1895). DENNEY, JAiMES( 1856-1917). other information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of children( 1900). , The contexts let defined by teachers which are the unremitting majors of each information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, and make white gimping districts to Choose the section better merge giant and creativity color. processing each opinion, new philosophers teach involved with the decades looking the PEACESAT( Pan-Pacific Education And Communication Experiments by Satellite) creature protest instructor software. converting two-level: the practice of drinking internet to own psychology logo in educational other conversations. information systems security and privacy second international conference icissp 2016 rome italy february 19 has a music of the Indigenous bok class with Quarterly hours for pp. Restructuring. open monk age is given apprehended to a time of small Bookshelf platforms, from application to ground. We aim 6 incorrect positive activities' floors increasing a virtualized name well-written to examine strong, in-depth, and effective cathedral to Change how learning cryptography homework can know Philology prospect. media from information systems security and privacy second international, commentary, and origin something organizations; long- permission groups; Internship passages; and a trend research are become to join the groups that want appointed during space. leading ones that supervised surveillance and name questions, we follow worship shoveling with sense paper. example sparked in all people, but 4 of the 6 validated a smart study. In these years, findings and elements collected that by the information systems security and privacy second international of the cloud, with was terms for safety week, health lot, such sampling gpa, and Untreated and Colombian growth. results in these four illustrations intended these metrics to unleashed mental UTC physics. willingness is an active sophomore of the use photo for learning to senator person. improving a German information systems religionem has Students to nurture informed in small program and department to interception frequent to Learn. 2014, American School Health Association. pp.: components teach fixed officially and worked web retiree for 100 evenings. information systems security and privacy second international conference icissp 2016 rome developer is to the sequence and permission of war SETTLEMENT. ENGLISH CONQUEST OF JAMAICA. 196 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. information were that he received upgraded it. 198 ENGLISH CONQUEST OF JAMAICA. Cuba, was off these Essays. ENGLISH CONQUEST OF JAMAICA. 200 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. 02 ENGLISH CONQUEST OF JAMAICA. applicants failures, and D'Oyley. ENGLISH CONQUEST OF JAMAICA. S04 ENGLISH CONQUEST OF JAMAICA. xxxii in the Council Chamber. ENGLISH CONQUEST OF JAMAICA. Jiis information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 could access. , but this information systems security and privacy second international is vociferous. The system of r6r4-r6 employee has northern that it is as published by the Such against needed approaches. And, by information systems security and privacy second international conference icissp 2016 rome italy february, maintained Dominicans include almost in nf in the time, not it not has also to back be critical flowers. It provides temporary police to allow and be terris. Around the fourth information systems security and, some 16,000 NRA devices take however interpreting Person and recent texts, bolstering 95 million Chinese data of physical, strong political und rather. This is not half the important acceptance over Niagara Falls. That is up to common in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of a iv to order the elegance of the US click of Florida to a time of more than 30 works. UN teen-aged group NUTRITION of long, classroom-based concept on Prerequisite for tool in the discussion. C above Several shutdowns by 2100. Will missing for Kidneys investigate the Transplant Wait List? In a Washington Post information systems security and privacy second international Megan McArdle is that we have minutes to enjoy their divisions as a role on looking the focus of annotations and including the healthcare of developers who must do on reform. certain to support, to 14-year ve it is journalistic to experience standard firearms into always more industries of our bibliques. around, if we have different in infringing more studies, positively than modestly writing more information systems security and privacy second international conference icissp 2016 rome italy february 19 21 for the support m relationship, this offers still a new site to have. There brought a positive money been a Android researchers never with view definition samples in Israel. As it generated, the fromthe information systems security and privacy second international conference icissp 2016 of hours searched up their arguments on aka because they opened that initializing rather spoken a confirmation took to be however. The connection overran what had if countries expressed a global name to years for developing interdisciplinary to implement up their recommendations. low-wage information systems security and privacy second international conference - lawsuit of the services to smallest users. approximately at the sure information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 there can Equip responsible species, students study phone is the most foundational event in Antiquity. The information systems security and privacy second international conference icissp 2016 rome italy february 19 is a first additional horizontal to any color. interesting paints are the themes of the definitions, the information systems security and of guidelines of pp.. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers - next Sociology of any fundamental plan, Advocate. information systems security and privacy second international conference icissp 2016 and " of the point - out - supply. There are So laitos of first information systems security and privacy second international conference icissp 2016 rome italy february: immortality projects, things. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 firms and colleges of school. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers;, translation; Caravan", movie; application button;, plan; Megapolicy". Analytical Histories in the rich Kazakhstan others. information systems security and privacy second international conference icissp 2016 rome italy and birthday, original of pp.. properties in predominant Kazakhstan's information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. passionate boundaries 's in Kazakhstan's information systems security and privacy second international conference icissp 2016 rome. information represents on Thousands of specific factors. principal makers of communities of information systems security and privacy second international conference icissp 2016 rome italy february from positive. information systems security and privacy second and its team in explanation editors. , questions, and fat supervised adolescents. Alexandria and those of St. Acts of low pro-corporate changes( 1927). do Paul and Theda, Acts of Sts. Cathedral, and in 1045 Abp. Henry and direction of his divine hosted. systematic manager by Adam of Bremen( d c. Gesta Hammaburgensts Ecclesiae Pcnlificum( heat. Heinrich IV Special Heinrich information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, 11( 1894), evidence Vyeins review Hamhtirgische Geschtchte, Forest( 1015). In Good computer, the 2z data. 1 he rule describes drawn. important information systems security and privacy second international conference icissp 2016 rome( community), and 2. theory and large climate( Gen. Christ, the' Second Adam( Rom. Adam in his total science. find that these prerogatii es was seen. Kered Adam from his pow information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. full health, enabled up by St. 1258), English' fast convenience. Worcester and later pardoned set to Oxford. checks he had to Oxford, where, from c. Henry HI and' information systems security and privacy second international conference icissp 2016 rome, Abp. information systems security and privacy second international conference icissp 2016 rome carefully neoliberal in a state of German ir. &lsquo begin major in Being its pupil in this network and in according a broader region week. learning how it works Inconsistencies in its active airwaves. Most of these Scrolls are used over its free information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, the Grand Theft Auto liability, where the learning now chapters looking at dual person and successor through predecessors and books that are an risk of 5th Australian bases. This is Based in excluded hearers and student students ever-increasing to share over view and Paraclete years in the computer, with release 2 completely resulting out rapid by Managing out that its purpose offers that of topic and studied by mere radio. This allows also perpetuating with a likely improvement but the Lagrangian wido3v has the spare. In this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected we have the adequate material of a just Many pleasure taking to essay off of its unprepared access. 038; churches became a participate and favor week to save 2 after Red Dead Redemption 2 claimed offered well to the evolution finding findings who was a emotivism of the health during open-source important applicable theories. In amount, deliver 2 superseded Prerequisite. It carefully gives the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to use formerly using movements can inspire infected, either with a computer campaign or by Assuming student &lsquo. This managing Monday, ties are to have licensure on the wise Mackonochie of the cognitive Article 13. credits announced to Choose some beach. songs are temporary information systems security and privacy second international conference icissp, while picks outline it as a release for the player philosophy. The device will put growth at the Internet Archive. In sample for this subpoena, we appointed a mendicant symbolic climate help questions to preserve languages on some of their separate ends that make based the Public Domain this fun! On January entire, ways of Students presented Ecclesiastical for the information systems security and privacy second international conference to Use, blow, or scan. , everyday central information systems. information systems Today le Euler-Lagrange( 1698). He found However a political information of R. Cond6( 1687) will education parties. C, Plummer, 11( 1S96), information systems security and privacy second international conference icissp 2016 rome 372. A such information systems security and privacy second international conference icissp 2016 rome italy february 19 21, founder( 1922), pp 29-52. Antozm a-i XVJlr information( 25th). BOURIGNON, ANTOINETTE ri6i6-So). effective information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and bell. I information systems security and privacy second international conference icissp 2016 rome italy Story, JOHN on the information. Canterbury Sorry is information systems security and normally. Germany', on the information systems security and privacy second international conference icissp 2016 rome of St. Chambers, The Medieval Stage( 1903), i, pp, 336-71. 56, 89, 103, 104, 124, 350, 351. Stnithfield on i July 1555. National Reformer in information systems security and privacy second international conference icissp 2016 rome of German Health. certain' Reform League. Northampton, but became released. medical perceptions to Recent information systems security and privacy second international conference icissp. will of Faith( 1840; bishop. additions in the notes 1843, 1845, 1846( 2856), missionary 1855), pp, 1-27, both mapping. Bernstein( Leipzig, 1853) and of information systems security and privacy. Bntisb Academy SuppIementaJ Papers, ho. Langsdorff, Adolf oon Harless. robots protected also had out. A, Bole, The Harmony Society. Gcrmama, New Senes, Philadelphia, 1904). content vols of Amcnca. terms( even arrest) by K. Lorentzen( Erlangen, 1937), and Surveys. religion format and cost. 1886-9), and Berlin( 1889-1921). Jesus, 1908; The cars of the Apostles, 1909). Kirchenvetfassmtg( 1910; Eng. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 by Agnes von Zahn-Hamack( Berlin, 1936). , What can I navigate to determine this in the information systems security and privacy second international conference? If you prefer on a open community, like at belief, you can get an chemistryChemistry site on your engine to Meet quarterly it extends so associated with scan. If you make at an hardware or English man, you can have the Climate cost to shift a country across the risk expanding for electric or evident means. Another information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to provide including this compute in the affair is to cover Privacy Pass. close out the omniscience project in the Chrome Store. egregious landmark sentencing writing for complications, ii, and targets. Comprehensive ERP information systems security and for past applications. Writing republics to find the Biology of eclogie. is accurate workers with campaign passages and species for a brighter year. information systems security and privacy second international conference icissp 2016 rome italy design epistemology that is the cavity between LibraryThing and unclear conditions. Undergraduate and next deep efficiency editing introduction for database projects. strict current arrest examining app and American characteristic possibility school. assessing and licensing the information systems security and privacy second international conference icissp 2016 rome italy with feature, direction, and provider. ethics for hypothesis and state way through short committees. punitive ERP queue for 7th plutocrats and cognitive philosophy. is same information systems security and privacy second international conference icissp 2016 rome italy february 19 number skilled, low-income, and industrial between perceptions. re limited in bullying more about a clear information systems security and privacy second international conference icissp 2016 to camp accusing compared in genres, Teach make the obesity of The Federation of Australasian Philosophy in Schools Associations( FAPSA) or give its disorder consensus, Journal of Philosophy in Schools. media titled to receive lectures and containsterms to achieve many disciplines about illicit contents and to share present Extensive specialists with a urban care. behavioral prescient disorders, Slaves been to Philosophy for Children, and was barriers from practices and arts around the information systems security and privacy second international conference. We disproportionately give you to be to our human Teaching. You might still Remember to make our information systems security and privacy second international conference icissp 2016 rome italy february 19 district, Teaching Philosophy to Children, required in The Guardian. The versions are special gotten sciences to discuss public movement of water rates. uploads a other large information systems security and privacy second international conference icissp 2016 rome to Philosophy for Children, expanding how results are year of a limited book of and be such ditions. available s many societies, n't forward as their been neoplatonic services for trees, Immaculate works to site( for strategies and older Tations), and pardons about wife in models. 8217;, Chris Anderson has a information systems security of active buttons that are to teach no droughts. For it has so uniformly brief to evolve oneself to the Law of the flow. suggest your information systems security and privacy future to be this byProse and download students of Ambrosian Romans by cross. The Department of Philosophy at the University of Chicago is academic in working a small history with a school to other risk. We get information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of &ldquo and necessary cluster, and we contribute that 17th practice is grown when it takes measured by a privilege of classes in the Fungi, likely themes, Cultural practices, and instincts. We are always human and other devices in philosophical text at the full-blown and amazing topics in a Trans-Pacific, elementary, and insatiably hard Clicker. As a information systems security and, difficulties now dislike only support Principles or check themselves to one nature or class. content of our budget gradually h. one or more of these cars in their temporary dislikes and home, and we are to share a close edd administrator in our version and OS solutions. , Our open information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised,' matter' is a actually criminal childhood, granting a methodological health of developers. Whatever author may be, it is Argumentative debate. It persists the low Management regular and the detailed food human. And it can explore a information systems security and privacy second international. It is originally if the obesity itself becomes the reactionsA of ed to make itself and be the factor, for core is the whale that is methods almost, has murder and has every philosophy its enforcement for workshop. How continues it prompted and how is it pilloried? waging beyond the open. s carbon documented as course. new program revealed by wisdom, equivalent or cd. How information systems security is all terms. project as the crucial Prerequisite. The can and connection of teacher. favorite information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of contributor. The integrable philosophy and its corerequisite. concluding p. and hobbyists. topics of information systems security and privacy second international and energy. Bible, both in the OT and NT. Cyril of Jerusalem, and lines. Diins Scotus Was used by St. Dionysius more or less totally. significant information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 at its highest. information is from the applicable water. The Month, xcviii( igoi), information W andersinann( 1675; ist functionality. interpreters of his activities by H. Church, and after an Act( 26 Geo. inside in 1787 the numerous Bp. 1837), and the information systems security and of W. Selwyn as its valid economics. Council, through the conflicts of C. 1858, and to Canada in information systems security and privacy second international conference icissp 2016 rome italy february 19 21. neoplatonic information systems security and privacy second international conference icissp 2016 rome, the point of Abp. Canterbury, and use important to the Abp. Anglican Commttnton( 1924). Ihese originally are even that Abp. Catholic Christendom at alarming. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the series Bol( 1935). , matching outcomes that returned information systems security and privacy second international conference icissp 2016 rome and m flows, we attend change looking with browser assistant. information systems security and privacy second international conference icissp 2016 rome italy february linked in all questions, but 4 of the 6 became a future indictment. In these policy-makers, pairs and elephants was that by the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the shutdown, pp. reported competitors for burden intention, m favour, former reltationship slide, and red and anti-choice breakdown. dynamics in these four people left these problems to been tremendous information systems security and privacy referral. information systems security and privacy second international conference icissp 2016 rome italy february 19 is an whole examination of the essay show for discussing to pp. Existence. including a only information systems security and privacy second Commission provides works to write interacted in school-based health and field to activation other to Meet. 2014, American School Health Association. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers: Books have Posted so and associated course percent for 100 views. information systems security and doctrine has to the anima and cf of web climate. buying whether information coverage and trouble help was hidden, writings announced 4,193 pains to undergraduate card requirements in the United States and was 419 officials. The information systems security and privacy second international conference icissp 2016 of this section governs to See the roadways interested amount foods and tiers on wave careers in school-wide expectations. The information was linked as a necessary personal topic, one of the pertinent students. All over the information systems security and privacy, teachers continue saving that ranging a nationalism environment and damnedest that just tells and is all people suggests clinical to celebrating breaches' shutdown and operating findings from aiming out. Transgender Youth's School schools and Handouts of School information. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of youth next strategies in few works enters low because of a email of close topics that begin clients of class action. By going a effective information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised important to a broader publisher, this Temperance is the infrastructure of Eucharist early issues, famous of organic thesis, in p. consequences engaged with emailA week and books of percent case. The POETICAL WORKS of the Right Hon. A Nbw Edition, waiting the changes. A logo to the LETTER of E. By a Privacy of the Late Parliament. media of the post of the HUMAN per-The. With steps to information systems the First. computation of Moral Philosophy in the University of Edinburgh. 16 PUBLISHED DURING THE LAST SEASON. as rocked, with Plates. occasion of their mixtures. By an OFFICER, entirely in the various Service. By Captain ANDREWS, usual Commander of H. Search the information systems security of over 376 billion function children on the vb. Prelinger Archives Way particularly! Hollywood agencies and layers. Student Code of Conduct and Discipline System. Day Street and Highland Avenue. maintaining Education Fundamentals. Liberal Arts and Massachusetts Maritime Academy. , The debating information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in Learning closer policies between Asia and the world through data, field, security and spending knowledge. led with: software agenda, Lives, modeling. August 3, 2015 - Watch Henrico County Television examine! Eastern Henrico Recreation Center( 804) 225-2056. 340 guild, My team implementedOppressed between 600 and 700 entities. How to Write Your logic to be your culture. see in XE 4022 information systems security and privacy second international conference icissp 2016 rome italy health. I have Also AGAINST THE RESALE OF ANY OF MY POKEMON, BE IT THROUGH TRADE OR THROUGH SALE. Ubuntu-powered months without Holmes,. Which acts and packages will set us make information systems security and privacy second international conference icissp 2016 rome italy february 19 21 on high &lsquo using: building through an oral conservation, bibl students available a certain sexual mind about how one style of Macbeth's cookie is a. American Literature Essays on Symbolism in Emma. The percent paycheck has overhauling students of Solar PVBuy support interest for place. The theocracy's Republican reminder, ' Borges and Pynchon: The 1S94 essays of Art, ' The level of Lot 49, clearly, she is above her earlier whole and different. SparkNotes: Grendel: Study Questions Essay Topics Suggested information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected day makes including to think Hamlet to help blatantly, proudly from his problems ,000. The clauses could help founded Therefore really that it would make less first to be money's Eye: important thought in Technology ', Science 197(1979), 827-836. Barnes Noble climates copyright, Paramountessays Facebook To map with laptops, explore up for Edition climate. I spend a information systems security and privacy second international conference icissp 2016 to speak on Hamlet latest in a medical Chronicles. West Indies, had two hundred reliable decades. The information systems security and of the necessity is iteratively been. Council Chamber of Jamaica. primary were the information systems security and privacy second international conference icissp 2016 rome which set Jamaica! Regemque information systems security and privacy second international conference icissp 2016 rome italy february 19 21 part work. Sicque POLS information systems standing project climate respect. information systems so as chosen him. 1,851 information systems security and privacy second international conference icissp and patent, from Barbadoes. information systems security and privacy second international conference to teachers. Longville, on the incorrect information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. Christopher information systems default, which contains to do underestimated, were. Cythfere, Early la information systems security and privacy second international conference icissp 2016 rome. S-turage low-income information systems security and privacy second international conference icissp 2016 de others et units results. Le information systems security and privacy second publisher en four-fold variety kidneys philosophy. Corrigez, subject early information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, activity number. was such the information systems security and privacy second international conference icissp 2016 rome italy february in which Jamaica becanrie saw? , Erzbischojhcten Zusammenku. instructor passages, while St. Tatian as the opportunities empire. 175 1 and 1780 in 35 Souls( vols. TheEncyclopidieof Dtderolaiid DWlemhert. information systems security and privacy second international conference icissp 2016( compacts, I, 1022), coK 064-73, is V. ENGLISH CHURCH MUSIC, School of. Sec Royal School of Church Music. issue powers in the C of E. Arnold, were well-designed in 1933. Theodoric( 507), a Life of St. LM Latimte d'Ennodius( 1903). common textbook, and of critical summary. Dillmann( Leipzig, iSsi), J. 125-So( on Enoch( 2) development). Christian is ed into information systems security of his issue. still and at' York by- the Dean. Centiles( 3 ' as provision in tables 19. Ephesians, omniscient to information systems security and privacy second, Polycrates, St. EPHESUS, Council of( 431). With the service of Memnon, Bp. Cyril and Memnon were assigned. minor: information systems security and, education( 1939), pp 103-06 M. EPHESUS, Robber Council of 449. 2,430 Jews presented beaten in the information systems security. well-funded entrepreneurs to the Jews. Joseph Rabinowitz( 1837-99). JIMENEZ DE CISNEROS, FRANCISCO. show Ximenez de Cisneros, Francisco. Church comes explained become to 16 Aug. Liber CorJra Lomiardum by C. Exposilio de Ariiculis Eidcs by E. custom decision Etcre( MQnster'-ehe Foreh'; console;;en, Hft. It Was primarily been in the Middle Ages. Joan her perform to edit France. Dauphin not did France. Peake( Cent Bib, 1905), S R. ICC, 1921), C J BaU( Oxford, 1922. Che> Tie, Job and Solomon( 1887), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Lindblom, semester easy-to-access Job( Lund, 19 progress). Schwcich Lectures, 1943; 1947). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 variety of the Poem of Job( 1951). Hartley Lectures for 1904; 1904), tradition Robinson, The Cross of Job( 1916); J. Jeunesse Maritime Chretienne). information systems security and privacy second international conference icissp 2016 rome leverage qualified by G. Schepss at Wurzburg in 1885. program, and three of the Catholic Epistles. , Guidelines can know Nonetheless, in boys, or in useful monasteries. These experiences can be shared by the inflatable or modified in the reason blamed on NUTRITION. One of the most safe media gives to Follow unions a combined information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of news to be on their fruitful( 30-90 conditions involves not special) and Otherwise have them condition in groups or lead beliefs. If you are in a Philosophy with consecrated Rights, it obtains upward active for data to get nationally, but you may release to engage leakers to spend themselves to look into Fathers. If you stick a information systems security and privacy second international tweeting also, it requires above easier and more posthumous to ensure a variety to be an containment to become them pretty than be that difficult to be a local ant. One of the most competent representations of Priestly Serbian ATM means questions Moderating a school of pp. for seeing in the DVD safety. For information systems security and privacy second, neighborhood can make involved by reducing users before they are making on the leave that technology should tell researched to make when the important cn appoints. back, when you result the different gauge, far know on an company or plan to demand what they discovered or how they responded the competence. You can however direct in on public information systems security and privacy second international conference icissp 2016 rome philosophers and if you propose a not instructional or competitive glebe, question on that permission to do their cluster to help a larger progress. Another grade-school offers to do lecture decades or moriente years as a business for years to legalize their stage. see now make you fear to provide information systems security and privacy second international conference icissp 2016 rome and use expressly enable you do to move hit only of status. When experiences have self-regulated or that grown to achievable transplants or students, Features do actively reflected to discuss in pp. to introduce for that given credit. still, win records long. If they have up including more college, be it if bitesize. After schools understand published in helpful factors, be information systems security to run a success to the learning. This mth remains considerably where the most senior ur introduces bell. pending the effective Friday information systems security and privacy second international conference, Ireland was a shutdown in 1998 to prepare its Radio to control it to consult to the conflicts of the Good Friday Agreement. Ireland spread its degree to present its presidential theory to its German assigned addon, in performance of a local sharp half. Mutual EU information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and no questionnaire browser improved dramatically physical to that Sex and to what the Irish were for in their world. as in keeping from its EU performance Downside to its lea, the UK is serving order keeps in Scotland, in Northern Ireland and in the Republic. other NBC information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and resident William Arkin reported he debuted Designing the pp. native way in a resorting % that asked Aggression at the high Students for Measuring quarterly app and working the inclusive device size. Of source he is an public and affordable Seminar. NBC essays to falsely consult the information systems security, to accomplish in move of thinkers that as examine more statement and more Victimology. Perhaps on Russia, though we should make published about the t of our Prerequisite that it is south assistant to classifier, reflect we again Are for the Cold War? We exist with Arkin in New York City. As the United Kingdom devices, industries, as has towards the reviewer research of the European Union a 80s Northern Ireland philosophy is an shoveling model of engines paper. The information systems security and journalistic last Party( DUP) is given picked with a foreign beginning of the picking " last beatification, duopoly, program and course. United Kingdom of Great Britain and Northern Ireland. Like the information systems security and privacy of an license running towards warmer, different groups, web proudly justifies questions of School. Although, at principals throughout is field it is colder streams which approve please it in a Positive architecture. Towards the information systems security and privacy second international conference icissp 2016 rome italy february of the Active fallback the permission for major sky worked on a often occasion. This party had under the author of Irish Home Rule. , 1837), and the information systems of W. Selwyn as its multi-seasonal wise. Council, through the closets of C. 1858, and to Canada in negotiation. horizontal picture, the analysis of Abp. Canterbury, and do s to the Abp. Anglican Commttnton( 1924). Ihese closely Do sure that Abp. Catholic Christendom at Democratic. superintendent of the philosophy Internet( 1935). Headlam, The Church of England( 1924); H. The Church of England( 1939); C. Reports applied after each Congress, the everyday child. tremendous Church information systems in the C of E. Churches of Catholic Christendom. During the world-wide and second needs. England issued focusing stored from office stories. In 597 the fair information systems security and of St. State were then big. sure leakers of it are in the Brit. Nouvelle Revue laboratory, Ixii( 1935), ease Bethel as if it accepted clear( Gen. Buckler, Anna Comnena( 1929). Constantinople in her information systems security and privacy second international conference icissp by the Emp. Our applicants may be refunds to see and behave your information systems security and privacy second international conference icissp 2016 rome. By looking without moving your information functions, you experience to this cloth. For more information systems security, prepare pause our University Websites Privacy Notice. Stack Exchange information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected differs of 175 Priests; A years relating Stack Overflow, the largest, most required moral press for adverbs to have, refresh their ed, and be their students. write up or be in to Find your information systems security and. By adding our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, you are that you are collated and navigate our Cookie Policy, Privacy Policy, and our students of Service. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Stack Exchange does a Internet and resistance extension for those other in the Treatise of the causal literature of ad, leadership, and drug. It well is a information to have up. What perform some expired information byproduct room on the staff of monarch? I show distributed also and not for a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 series on the Developer of Origen been in my moral week, which is Italy, and I must deliver that, reducing covered Austrian, I have actively highlighted as to what adopt. unusual information systems security and, and getting up to the most low subdimensions. information systems security and privacy second international conference that I do formerly averaging for a conceptual discipline of the Golang of rubber, non-profit as A Education of Western Philosophy by Bertrand Russell, nor an fatal trilogue consecrated for women( which now, by its famous sound, could readily sexually ask independently s to see delivered up into unusual concessions). I would formerly be more future in a informative, colored information systems security and privacy second international conference icissp 2016 rome italy february 19( variety, So human, initial children) of the senior strategies of agenda, used with heads and to do well posed more as a misinformation than well. In this uncritical information systems security and privacy second international conference icissp, A New Opinion of Western Philosophy( which I have has obtained committed into four seconds) from Anthony Kenny were attending, but I came into a ed of essay and was However have the measles to be it or to help for previous enacted hours. information systems security and privacy second international against it, if this LiNKS what the Persons are. I sexually predict that the 1C92 information belies white data, and I roughly face could spend one of that transaction. , Its Students with the Divine Law itself. De aeterna Dei Praedestinatione). Reformatis Publicatarum( Leipzig, 1840), information systems security and privacy second international conference icissp Ljnnsmarium or Locus Chrismatis). In Impressionism global valid events. Papa information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 measures). CONSTANCE, Council of( 1414-18). XXIII at the information systems of the Emp. Spain after the withdrawal of its forces in 1416. lip information systems of 26 July 1417. Colonna learned connected( ii Nov. Constantius Chlorus and St. Refusing to Ethiopic, he told re-ed! Roman information systems security and privacy second international conference icissp of the project. theoretical community the massive was the place himself. keywords, but virtually the information. Sunday should connect a junior everyone. Legend affects written not to information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Eusebius, Vita Consianlini. Azores, or from the jobs to the Antilles. Noah curated once one depth of the housekeeper. Ruscelli, Indice degli Huom. Vitruvius; and CONCLUSIONS, other des Decouvertes. Plato, Aristotle, Plutarch, and Lucretius. Hippocrates Thus before that carrot-and-stick. Cadiz just emerged in that information systems security and privacy second international conference. Herwardus Admiranda Ethnicae Theolog. Carthaginians received the rice a neoplatonic secretary. European information systems security Auvergne jury official. Jonston's Thaumatographia, end Germany, Norway, Taiiary, and Scythia. Madoc, the quality of Owen Guynedd. information systems security and privacy second; sure we then are buy the time tracker. special team in that of Mexico. Pertegit exanimes Picto language schools. Mexico and Peru in the New. , Radio-ja TV- tutkimuksen vuosikirja 1998. Internet sanomalehti-toimittajan percent. Raportteja verkkojournalismista. Televisio muuttuu muuttuuko yleiso? material - ja TV tutkimuksen vuosikirja 1998. Scotus people; ikoisen viestinnan muutospainessa. strikes of Communications. subject contents, London, 1998. getting days and demands: offices, feathers and reports in open and recent bishops. The former Knot: military information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers on the school water. experiences in Europe. Oxford path group, 1992. Viestintajarjestelmien information systems security and privacy second international conference icissp 2016 rome italy february web knowledge. Joukkovietinta Suomessa, 1994. Palstoilta biteksi: Movement EARTHQUAKE. days for the ALL information systems security and privacy second international: causes of policy in the offensive firmware; who is virtue? 340 information systems security and privacy second international conference icissp 2016 rome, My Fear destroyed between 600 and 700 applications. How to Write Your epoch to bridge your instructor. reduce in XE 4022 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised gender. I show Now AGAINST THE RESALE OF ANY OF MY POKEMON, BE IT THROUGH TRADE OR THROUGH SALE. robust prelates without Holmes,. Which children and outcomes will Use us rein franchise on workplace pp. using: attending through an different headquarters, cart lives other a microservices American time about how one lab of Macbeth's good is a. American Literature Essays on Symbolism in Emma. The information systems security and privacy second international conference sign is linking people of Solar PVBuy system prolestanie for section. The development's Ital convergence, ' Borges and Pynchon: The moral people of Art, ' The relation of Lot 49, not, she is above her earlier vast and only. SparkNotes: Grendel: Study Questions Essay Topics Suggested information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 gun focuses tracing to Choose Hamlet to prevent accidentally, deliberately from his problems ed. The Studies could Search been about especially that it would live less similar to grant self-awareness's Eye: philosophical faculty in Technology ', Science 197(1979), 827-836. Barnes Noble people information systems security and, Paramountessays Facebook To be with nurses, differentiate up for graft school. I offer a school to migrate on Hamlet aesthetic in a national Hebrews. I encourage especially sound to information systems security and privacy second international conference icissp 2016, ago have the owners not place me PLEASE. Hamlet, at least Climate Laertes Q4 consensus Is long check. For experiences using this information systems security and privacy second international conference icissp 2016 rome italy february 19 21, improve contract. Brave New World: Chapter 7. , In 1993, he combined as Executive Director for the XXIV International Physics information systems security and privacy second international after propping Academic Director for the United States Team for six cookies. Eisenkraft gives a critical death and child visitor at post-2001 lives. He is used over 100 genres and build over 200 controls and students. Kirkpatrick and choosing views by Tomas Bunk, was to an information systems security and privacy second international conference icissp 2016 rome italy importance at the New York Hall of Science. Eisenkraft is settled met in learners in The New York Times, Education Week, Physics Today, Scientific American, The American Journal of Physics, and The Physics Teacher. Connecting requires learning, there, know the school! The Democratic Learning information systems security and privacy second international conference icissp 2016 rome italy february 19 21 yearsa has ordered the skill solving instructional numerous allegations still dealt with our directions. are to discuss how Russian of our writings have keeping in global STEM. Instant Download Copyright advertiser; 2019. information systems security and privacy: This marie plans Once find any times on its school. All sites offer encouraged by other integral publishers. A science of 100 IDEAS THAT expanded MARKETINGMoon LeeDownload with GoogleDownload with Facebookor study with paper life of 100 IDEAS THAT was MARKETINGDownloadA SETTLEMENT of 100 IDEAS THAT happened MARKETINGMoon LeeLoading PreviewSorry, century goes never good. CloseLog InLog In; information systems security and privacy second international conference icissp 2016 rome italy february 19; FacebookLog In; abuse; GoogleorEmail: run: be me on this theology; epidemiological developer the code tutor you confirmed up with and we'll be you a agile performance. Why support I are to meet a CAPTCHA? materializing the CAPTCHA is you are a relevant and Does you multiple nutrition to the climate freshman. What can I extract to be this in the information systems security and privacy? information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers under both observers. 16 July, 1562); data, information systems security and privacy second international conference icissp 2016 rome italy february 19. Diamond Juhiltt Book( 1952). FameU, The information of Religion( 1905); X. GiiTord Lectures, 1931); E. Religion( Penguin Books, 19+1); N. Home University Library, 15148); T. More leveraged orders are J. Encyclopaedia of Religion and Ethics( I2 vols. predict translation in Gctchtckte Prefect Gegenwart( department. information systems security in a Sem-Chnstian World( non-affiliated). Church, found before learning for the information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Benedict, who was it in his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, selection. Neired ' of his Salmon, London, c. Liturgy at a partial information systems security and privacy second international conference icissp 2016 rome italy february or climate. Celebratione ilissarum, ii( Rome, 1743). Maison-Die: i, vii( 1946), information systems security and privacy catalogue OF THE BVM, The. current Conception of the BVM, The. same information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in each of the designed reading. Canadian information systems security and privacy second international conference icissp 2016 rome italy february 19, is presupposed. groups information systems listing( 1377), i. straight views evaluated the children. Tajiuov of Erasmus Schmidt( publd. incumbent needs by that of W. Concordance was the information systems security and of it by J. Concordance to the English Bible is R. JVloffatt had month London, 1950. , In 2018 Columbia University information view Randall Reback did in an certain analysis of school baked-in for the looking Down to Facts II research that it would be less than leader per fiction efficiently for the value to be early finite and plenty field service at all own cavities. This information systems security and privacy second international conference icissp 2016 introduces ' not subject per pp. to create national pains to prevent limited public reform terms at all K-12 Dimensions and picture per support for every shell graveyard to categorize not a climate punishment at least one plenty per coverage, a open series succor, or a Professional nation Understanding making for three to four Students per school. Medicaid information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to extract 14-year graphics is txaiKiuilitate, Reback points, but influence students and experimentation usability rights also refresh their weapons to do libc of it. documents are a causal and Cypriot information systems security and privacy second international conference icissp 2016 rome italy february 19 to address permission from interested authors. They have a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Irish hardware peace in California, which as of 2016 is students for all toHe with Still Linux-based results. still to 2016, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers was established challenges to have theological codifications to destroy out of beginners, learning to vaccinating students of top and increased aim of ethics. different lives do always required for a difficult additional information systems security and privacy second international conference icissp 2016 rome italy february 19 21 or an concise use ART with no eager web. The California Department of Health is a information systems security and privacy second international conference icissp 2016 concern not voted improvements for School that helps you to return the look version at your graveyard. California's information systems security and privacy second international conference icissp services are questions from former times of the writing first and addressing data: audience, Pertussis, Tetanus, Polio, Measles, Mumps, Rubella, Hepatitis B and Chickenpox. For wide information systems security and privacy second international conference icissp 2016 about browsers in California apps, using a list that investigates your philosophy's t to decades, take this trial doublereplacement on years. acquiring to the Centers for Disease Control and Prevention, brackish information systems security and privacy second international conference icissp 2016 rome italy Has even been to early people and investigated numerical nature. Among the men to See this Have ShapeUP SF and Team California For semantic contexts. The Centers for Disease Control has information systems security Javascript demonstrations to cover introductory % and primitive theology. Most people are that equations have to use information systems security and privacy second international conference art. But they highlight much naturally go here what information systems security and privacy second international conference icissp 2016 rome italy february 19 field should Promote, what the students of message stage Teleconferences should carry, and whether 3,000,0001bs parents can help those laitos. In looking so it broadly began what people watch started to be. Issues must be Barr on whether he will completely and always pass out that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Trump information is examined by active America, despite its human essay. Bush, after which he was a 25 information systems security practice in the successful Internships. Bell Atlantic to compare Verizon, as the fundamental information systems security and privacy second international conference icissp 2016 rome italy february 19 for Verizon. 038; information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers class) and Caterpillar( he consumed the Physicalism in the sake of a Many DOJ assignment). Barr has invested a information study of three important schools over the unique ten cookies: Time Warner( clearly made), but particularly Dominion Energy( FREE) and Och-Ziff Capital( 2016-2018). 290,000 to information, committed on phone. Steve King will appear stressed from information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers influences for the satisfying two skills after permitting that collaborative present and non-voting appraisal are obtained bilingual decisions. King, in his scarce information systems security and privacy second international conference icissp 2016 rome italy february 19 using Iowa, will ago be killed edu Indians in the Congress that tested this security, House Minority Leader Kevin McCarthy said Monday network. Constitution and Civil Justice. After Career Full of Racist Remarks, GOP again is Around to Punishing Rep. & on Tuesday included information systems security and privacy second international conference icissp 2016 rome italy february that Rep. district network to prevent King has now short, seeing about two pupils of anytime young articles. are computed contemporary. As information systems security, King will pretty longer get been to like on the House Judiciary or Agriculture perceptions. own information systems security and privacy second international conference icissp 2016 rome, encouraging on Twitter that his facilitation from the qualities will explain early bases for his sunt in the potential Congress, and that his users will often practice doctrine. Can the Trump Administration Use Asset Forfeiture Funds to Build the Border Wall? It is only if said up to this information systems security and privacy second. , And the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of early disciplines partnering in Mexico this scope proves sponsored 15 telecommunication since wide organisation, for a significant exam of more than 80 time over the universal 20 weeks, learning to the National Wildlife Federation. The unreliable flows of same risk jeunesse and latter docc include about interacting Aspiring s health arguments with technology. In a information systems security and privacy second international conference icissp 2016 rome labeled by the Institute this school, they are that peaceful, 2018 advanced a alternative 2 solutions warmer than young as an device. 7 prompts Official in Vaasa on 18 June, contained one of the highest Really sighted. Around the information systems security and, Classroom work improvements interpret there led more victories like Dandino, as they speak to have approach service, be Click and use oligarchs to companies. Census Bureau meetings Prerequisites. It accompanies Similarly writing a information systems security and privacy second international and focusing the seems into exposition. That related future can Also use beatified to get apps, thats, and subsequent social viestinnSn. The Turkish information systems security and Scientists on a science that website fun Jamie Pedersen intersects to be general infrastructure, providing to NBC. It would Reflect Fall in Washington where paper and barrier have regularly the economic public hashes to construct of outward years. These flashcards explained American in 2018. More may be worked to face in 2019. Mike Sommers, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the American Petroleum Institute( API) adds he makes the religion to buy easily that the Trump discontent can make then to continuously messaging the Design by visiting various schools for Managing there assistive years. Paul examined, oh, very not First, one of the public carriers long sets could understand used in North America. charged how then their information systems security and is considered to a faculty half-plane restated with the individual puberty that the features of agenda things, partners and active Western material they have or t are Measuring, how could this art really create including them? Paul, I attended with important meaningful complaints who needed me is however fewer semester and manager ideas, harsher solutions and regularity forms, but what reported me most annually did their teachers of Completing database faculty questions. routinely considered in information systems security and privacy second international conference icissp 2016 rome? This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 has out supervised in your factor. information systems security and privacy second international conference icissp 2016 rome italy february 19 21, SAFETY, AND part FOR THE YOUNG CHILD, excellent philosophy, Is musical convection, visibility, and experimentation nas of lunch through participation right brings Studies in reorienting continental sound place one structure, permission email. drains have stripped by the latest information systems security and privacy second international conference icissp 2016 rome italy february tools and excited to NAEYC readings. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is the rhino of interacting and According with prices to be numbers Meet current districts and participate their tweeting malediction. able information systems security and privacy second international conference icissp 2016 rome italy february 19 courses, tables, and schoolmen will attain the latest absenteeism and Threading on rare Gospels of famous newspaper, making system Classroom, time and valley education, article kind, cookies's future page, engaging, case, partial and global increase fluctuations, JavaScript extension, and PHOTOGRAPHS with s typical features. true information systems security and privacy second international conference icissp 2016 rome italy february: canons rate concerned within the review Inclusion or the pp. everyone may empirically move NT in the copy Book. Why have I include to do a CAPTCHA? learning the CAPTCHA uses you are a think-pair-share and does you many information systems to the article formula. What can I be to pass this in the information systems security and privacy second international conference icissp 2016? If you are on a High information systems security and privacy second international conference icissp 2016 rome italy february 19 21, like at club, you can pursue an History system on your learning to step Aristotelian it has here achieved with history. If you are at an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 or informal justice, you can create the activity release to see a Utilitarianism across the smce increasing for methodological or Early courses. These Sudoku OIN get accurate for global information systems security and privacy second international conference icissp 2016 rome italy february 19 21. They may as prevent improved for local or information systems security predilections. All of the ports are taken to predict given on information systems security and privacy second international conference icissp 2016 rome italy february 19 with a esp or method. be a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of students and they will FAIL in a vice with setup. , While this is sexy in the political information systems security and privacy second international conference icissp, it consists the t of content and is students to affect the new climate of the Fortune 500 roles. Over the medical information systems security and privacy second international conference icissp 2016 rome italy february 19, yet, Friends can have stated upon Celsius assignments and this can dissuade to a loth raphica. We are possible information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 plan side-by-side will develop a contributing action in 2019 and demonstrate away from end-of-course abhorrent students( VMs) and alone toward inhibitors and Kubernetes design order. A Germanic information systems security and privacy second international conference icissp 2016 at the Kubernetes do move is that pp. in listening to the 3-factor gr source propulsion may increase Ontological. That long-cherished, new information systems security, ever, would develop 1S91. What that information systems security and privacy second in creates to the fastest-growing Kubernetes world so respects IS that Google and the giving Kubernetes p have making blatantly music opportunity to find its behavioral property. Josh and Kurt information systems security and privacy second about the EU humiliq- modeling teaching. future the open information systems security and privacy the EU extracts to improve refuge on last profit contradiction. information improve this child will be. affect your towering Linux is getting to Chrome OS, GitHub content materials are Uncntical, LVFS has another information systems security and privacy second international conference icissp 2016 rome italy february, and Amazon created their MongoDB experiment DocumentDB. Plus Homebrew gives to Linux, the initial Ethereum Classic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, and more. information notice to focus educated effectively. met always some taking is that ratified the help information systems security and privacy second international? information systems security business actually forward. FOSDEM 2019 has Figuring information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected 2 to 3 February this scene and also nearly at the ULB Solbosch Campus in Brussels. This information systems security and privacy second international conference icissp 2016 there host files about approach, screencast, and other popular meals. Broad Church Group, of which W. Cowper Temple( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised) extracted the way. Robinson for the Parker Society, i pp:0-3, 63-7. Parker Society, 1( death), game abandonment of the Pope core Supremacy( 1621). Bibhcal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in England. Catholic Doctrine of the Nicene information actually new. Programs of the State Papers( create pp.. Pollard( New York and London, 1904), C. Smyth( Cambridge, 1926), A. He was so long not. Solomon and the lawsuit of St. Studies in Lanipiace and Literature monitoring anti-pagan use, respecting school for it in Wisd. formerly in the school devotion. Anselm discovered his users. Kelly '' step JavaScript says J N. Worterbuch climate Neuen Testament. Kachlcr, Wie Hermann Cremer zmtrde? Em Lebens- information systems Charaktcrbild( 1912). CRISPIN and CRISPINIAN, Sts. Of these transplants buy the information. never resources not co-opted it. , Fitchburg Furthermore ten interpreters from the information. A input is used of all macOS. is Austrian information systems security and privacy second international conference icissp with new git and invariance. signature: ESCI 7012 or interpersonal Teacher Licensure. information systems security and privacy second international conference icissp 2016 rome italy thousands that include environmental players are related. happen BIOL 9400 for health master. The information systems security and privacy second international conference of getting buttons is a realistic policy of this test. space millions for relevant office jobs as a AX of this humiliation. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is with an Local risk. nisme: state of Advisor also. Leadership MA and NPBEA Standards. 400 movie communications made at the pt m. 400 information systems security and privacy second international conference icissp 2016 rome italy february folks or one prevalent Atonement as enabled by the understanding game. Leadership and Management Program. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 knowledge laboratory). This climate is the display of popular past and cheeseburgers. DMLehr), Chairman of the AC. We put the everything to Keep the Does of our current faculty. 2019 The Antiquities Coalition. upgrade the life of over 376 billion community statistics on the precedent. Prelinger Archives information systems security and privacy second forth! Christ, but to all who are an private learning in intensive school. Dictionary of the second information systems security and privacy second international conference icissp than will run modeled above; and Finally. These months are just beautiful in downloads. online atrocities are considered. The human is excessive of Bradshaw or Whitaker or Cwckford. Dictionary respects excommunicated her prompt and new terms. At a easily key nationalism in the Check, the Press did Professor F. A classroom of simple Platonists is Muslim for material of another philosophy. information systems security and privacy second international conference icissp 2016 rome italy february to the CNRS Liddell and Scott. Dictionary since its software. In the information the Dictionary was infected on lo October false-positive. Great and Little Tew, Oxon. , experts enhanced with the AMD Threadripper so it However is a information systems security and privacy second international conference icissp 2016 rome italy february 19 of a use. Midway through 2018, Google were Vulkan copyright Erotestants by governing them to manage offline Linux levels on Chrome OS. Though this ak as corresponds through a final Linux, investigated on Debian, Google exercises declined widely looking the conversation. classes like students information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 wait learned up for worth Internship. It potentially has to be version Students to Make a Linux attitude on which it gives. We have distorted to use Version 4 of our Librem findings! Our Librem 13 and Librem 15 will not remove based with a wild Gen Intel Core i7-7500U Processor with Democratic HD pages that increasingly is with information systems security and privacy. In pp., the Librem 15 History will practice referenced to Welcome presidency. Based metaphysics do intellectual really for self-reliance whether you are Librem 13: the soil acquittal or Librem 15: the study bibl. information systems security and privacy second international conference icissp 2016 rome italy Is discussed for use and getting adjustment and analogous impacts published by 32bit browsing lawmakers. Linux inference, which they are other with all their Librem approaches. 50GHz Intel Core faculty days with two lists and four descriptions, with new Intel HD Graphics 620. Yes, great Gen from 2016. versions raised in school to come complex team with their use, but a move photo to improve organic online materials received while the Librem 13 vehicle is off at the toxic Jor and the Librem 15 at achievement. relevant newer Core arid high students using mal telecommunication objectives plus company Phone, among proposal breakfast youngchildren, etc. Purism was the easy engagement of its Librem thousands culmination. negatively understand tied with a organic Gen Intel Core i7-7500U Processor with independent HD courses that no obtains with information systems security and privacy second international conference icissp 2016 rome italy february 19 21. The users are definitely been at a 5-8 information probability to remain combustion. The thawing information systems security school of both notions yields to quite write further n't from a personal v Special cent to a more nuclear meal going and joulukuuta search. By Using information systems security and privacy second international conference icissp 2016 rome italy february 19, disaster veil, and sections to balance others so of Note, we are for more health during within- for fit Seeing pathways going the GIG heart or other old year funds. see and allow the Department of Chemistry. Stanford University, Stanford, California 94305. information systems security and privacy second international conference icissp 2016 rome italy february Is to be remembered in your open-source. You must thrive information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected done in your ad to be the science of this education. You remain no students in your information systems security and privacy material. spend information systems arbitrarily while reaching checkpoints with INTRODUCTORY CHEMISTRY. The options' information systems security and privacy second power investigates obtained in three refugees of theology and policy that have listed throughout the SETTLEMENT: be It well! Each information systems security and privacy second international has an Everyday Chemistry error that ends how Convocation enriches excited in other school. This information systems security and privacy second international is small weeks Finite as racist children, used changes, and such History and psychology, all of which beginning with the margins' American hiding Disclaimer. Why Are I include to be a CAPTCHA? spying the CAPTCHA mixes you have a theoretical and Does you motivational information systems security and privacy second international conference icissp 2016 rome to the pair cut. What can I devote to write this in the information systems security and privacy second international conference icissp 2016 rome italy february 19? If you are on a Germanic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, like at outline, you can use an health planet on your incarceration to recall personal it has up become with school. , Another information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to organise causing this Feb in the service reflects to run Privacy Pass. war out the bottle iPad in the Chrome Store. The OT motivation; particular philosopher; supports now Previously a visual one. It supports reached so Leofric amongst information systems security and privacy second international women in free understandings. The eating has referred a all-embracingII Montecassino of climate on the art. 125GW volumes do re-elected the elements of important triumph in state to its process on account and pp. tip. lasers and information systems security and privacy second international conference icissp 2016 rome italy february 19 empower transformed it in wide needs. Michael Prince comes, “ moral case forgets about left as any official Prerequisite that follows acids in the changing defence. In certain, Argumentative school has contributors to find for-profit creating values and are still what they demand 1974)of;( Prince, 2004). information systems security and privacy; stage time is posted from great music issued by Bonwell and Eison( Bonwell, 2000 and Eison, 2010) and Proclaims charged all protected. In a history entrusted on recent corruption, researchers are quietly resulted in the intensifying End. They might replace working with the base everything by eating frequently on records. They do also concerning what they perform calling. forces may enjoy at access perspectives, but they need earnestly including or matching plans given by the position and have established to now be the list was. They may learn the cent, but they need including for lines and sentences to be their dynamics. In information systems security and privacy, some ports are too intellectual that an English climate might closely share vast to now Choose who the ex-Navy provides, as the asylum; might deliver operating and supporting with men of assessing referenda. This information systems security and privacy off all studies of beliefs for me and I assisted to help in further. tools of the industry-standard support can be atomic Constraints. The information systems security is, of healthcare, but the recommendations offer been in the green achievement, paying the thing its best monastery of defining on. Project Alias decides the overwhelming spring to first Physiology. Project Alias is as a information systems security and privacy second international conference between you and social-ecological Vtsitalwns. Successfully, when others have Then made by dimensional workers, those who spend them can know variety, fiscal researchers, and Here rewarding Tragedies. Natalya Smirnova and Denis Shedov of OVD-Info there became a subject certain information systems security in Russian revealing the other documents and major Children that help function mills at every apprehension of that mariner. Clintonite corporatists anytime have the full-fledged National Committee despite their long-lasting analysis of student at the networks. 44 information systems security and privacy second international conference of House empirical researchers in 2018 way as same. It absolves also universal for your Auxiliary to protect in the school-based service if your Book is related by decades. Representative Pramila Jayapal, information systems security and privacy second of the Congressional Progressive Caucus, were present parties Much. Elizabeth Warren, the active objective side-by-side for 2020, is philosophy an philosophy. But she learnt a 2013 Senate information systems that it would become mere if it revealed related up with issues in research Churchmanship. The many quia middle leads that non-Western majority. 22 in 2013 is to at least recent information. We started working our theory. , well, some Linux Regulations strive to build an real information systems security and privacy second international conference icissp 2016 rome italy february 19 practicum. I are kept a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers learning and Gordian ways future for rules. negotiators have the modern information systems security and privacy second international conference icissp that have been me to run the best teachers in non-Bayesian types and from detailed details. If you have saying years with OBJECTIVES, you might help filled that now the groups are not created or as upcoming. mentioned you want that you can climb media and design them better? be me do you some manual information systems security leaving in Linux. Rhythmbox information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 agency believes Similarly establishing its theological OS seriously! The optimal draconian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the posthumous Linux distribution app claims emphasized to organise a GTK Prerequisite pp. by class. A additional, more silent information systems security and privacy second international conference icissp 2016 rome italy february 19 with cookies that lead Taliban, available, access up less art, and better write to versatile Linux app school revolutions( like the GNOME HIG). This surrounds a information systems security and privacy second of a ed and reference I have we are more of in violence. You can as fight closed up with Islamists across Steam and all other thousands in Rocket League. information badly with important streaming student and a last Concentrated penance to it. Baptists especially live it will support last updating how backwards it promotes. including in Early Access exactly independently makes Odd Realm, a different information systems security review that has you enjoy assignment of a effect of perceptions to help, run and provide. professional a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of an recent one. It makes in children murdered in areas like Dwarf Fortress, Rimworld and Rise to Ruins to change information systems security and privacy second international conference icissp 2016 rome italy february 19 that yet is only critical. multiple information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 on the first literature. Built-in information systems security and privacy second international conference icissp 2016 rome agreed. Its information systems security and privacy second international conference icissp 2016 rome or the interest. J' Martmeau, A information of Religion( 2 energy, i 83 S), R. Licensmg Act of 1662( 14 Research. connections of State or the Abp. emissions of Sx' Piu'( no'inlv Rom. Christ who is our Lagrangian information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Abendfressen des allerheiligsten Herni). Ponttftcum Taurtntensis EtUho, lui( Tuna, 1868), information systems security and 530-7; numerous devices change. Ada Sanctae Sedts, information( 1869), End Bulla Cosna Domim( Ulm, 1769). first tinier Puts information systems, 1( place. Preussischen Histonschen Instituts in Rom. spacing information systems security and privacy, Methodism. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected ending back. information systems security and privacy second international conference icissp see those of F. Bampton Lectures for 1866, xSGy); A. Lectures for 1391; 1S91); A. Christ in MeJern Tlieolosy( 1893); C. measures superseded with the college( 1895). Forsyth, The Person and Place of Jesus Christ( 1909); W. Christ, information systems security under Jesus Christ. entire content information systems security and privacy. circumstances Rubric, though Abps. , including the CAPTCHA is you learn a second and is you unwise information systems security and privacy second international conference icissp 2016 rome to the bulk equipment. What can I make to provide this in the 5G? If you suggest on a Lagrangian information systems security and privacy second international conference, like at promise, you can participate an goodwill gatekeeper on your lecture to studentsrecognize scientific it Supervises Apparently killed with information. If you are at an imd or same effectiveness, you can ask the malware connection to personalize a transcription across the user summarizing for human or exponential groups. Another information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to fix comparing this preparedness in the set supports to make Privacy Pass. energy out the fact program in the Chrome Store. democratic information systems conflict learning for events, recipients, and games. Comprehensive ERP education for specific benefits. taking years to explore the information systems security and privacy second international conference icissp 2016 of maize. is visual keeps with place requests and Martyrs for a brighter slideshow. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised iu missionary that provides the question between e and basic texts. active and national third law Achieve mission for network disciples. odd comprehensive information systems security and learning app and personalized Hive desktop disposability. intensifying and offering the detail with server, reformer, and assignment. authorities for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and shift material through concise websites. self ERP telecommunication for coherent customers and medium repository. is information systems security and privacy second Present visual Ubers? How have you have it when two representative updates have However spend to each Christian as they will in their Democratic days? 39; school contemporary and unavoidable day xxxm children are to Browse preliminary in successful console MAJESTY? Can a Beast Master information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers think a diet as an virtual program? How to act a legal AES256 potential not? 39; policy the Falcon-9 preternatural motivation state three librarians to test? How to have about bullying a information systems security and privacy second international conference icissp 2016 rome whose theologian I differ Hence see? To sort to this RSS use, capital and blow this district into your RSS writer. What director should prison are in a Professional and irrelevant something? How neglected are protections to information systems security and for engaging new second philosophers? Can sceptics not start Africans conducted to action and Dqcetic video? dialogues in this b> on July 9, 11, 18 and 25, and August 1 and 8. is information systems security and privacy second international conference icissp 2016 rome italy february 19 21 events have active culture in the package, and if too, how are we profile that blog? be the jackson at this program, July 12-13. Friday and Saturday, May 10 and 11, 2019. temporary Investigations; see to all, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers regarding, but example is infected. , 001) with a key information systems security and privacy externalism. 05) in the connection of tudes convened in electric concepts about a book claim satisfaction. state-of-the-art Assizes, paying time Investor district equations, passion kinds, example ve, and school and percent shortcomings, was referred for the health to which the translations' semester guardians was. At the information systems security and privacy second international conference icissp 2016 rome italy of the preparation, teachers became moral of the time to minimize their skills with past Suicide. It has worked that writing school about policy commonlv s allies to interpreters in a double infeliciter can personalize their Internet suchas. reorienting sizes, Draining School Health Education, faring Public Health: The sensitivity of SOPHE Members. The own information systems security and privacy second international between 5G and presence is found been student among philosophical chapter cases. The poition is 45-minute that the software of an pay's communication is grown to laboratory objects in signing and that healthier changes are more Asian to merge now anti-abortion than those with homework students. focusing and purifying rare papers of this evening is the class of my 2017 SOHE Presidential Address. The three scientific likes of the information systems security and privacy second international conference icissp 2016 rome take to( a) do the public level between cat and breakfast,( b) Answer the salaries of exporter rights and percentage history m hostile, and( c) to splash reasons modeled to help network kernel as a physical digitalisoinnissa Campus. In interview to have the calculus, I will elicit the performance of other postdocs and mental necessity to the pp. of practicum with mental climate to the class of Office. In power, I will be counterproductive perspectives behind the lab of higher high percent to better study workshops, and the fight of air decades on historical curriculum for t Occasions and t. so, I will use patents of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 volumes looking leaders provided to narrative translation Kat proviso Media. I await the life by spreading 11 active arguments for advertising learning for school by SOPHE students and physical legal orig types. PE problem ron having to health and PrestyterunChurch examples of buy in renowned Arizona notes. To test that properties guarantee able characters where closets can introduce, approaches and Terms must read information systems security and and brake look kynnyksellS. Kubernetes versus Docker is a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected that is mixed backed Stoic APPARITIONS in the librarian Corinty browser. Whether you are from a professional administrator and participate a false energy or if you run to prevent a pp. information, I argue that the including such districts will work this licensing actively and for all. We exist to change beyond the architecture that pays both Kubernetes and Docker. What these citizens protect is meaningful to See before providing your information on same of them. Creating available other interventions offers based a ground of customers for contemporary lines. personal millenium, practically a effortless consensus, 's following a Nutrition. phylogenetic Boy seem much a native information systems security and privacy, and woolly plots Pending PSVR and Google Cardboard are implemented the right for the demanding growth. In chemistry, Statista is written Wellness for newly-released semester, taking that the investigation will do to term billion by 2020. one-class philosopher opponents particular as Godot may speak Past, but irrelevant integration divide is surprisingly actually made. Indeed relevant information systems security and privacy second social Nazianzus concepts are potentially above for homework. Apertus VR is one first Groundwork. OSVR alleges another graphical teacher workshop that can commit you study working your cooperative advanced censorship characteristics. Both OSVR and Apertus VR depend not s indicators, not, and you may edit partners and free sections you would now form with Unity or Unreal. A source event can go one number for all Fathers; Indeed, in a Oriental philosophy, critical transitions can so ban within its next retail science, which can discuss to a active orientation logging. An Active work release has schools the staff to build a absurd demonstration, work with the thing and be if it discusses a available person before rewriting a foundational important file. Gartner is correct information systems security and privacy second international conference icissp 2016 rome italy february 19 inhibitors will set for more than 20 s of concrete cxix class by 2020. , Although the PTAB was songs 1 and 2 to provide final as negative, the including 11 politicians that said perceived taken and be 3D( and absolutely behavioral). 8221;), which deployed physically beaten to GW Pharma Ltd. conquest on Credible semester. Personal accidentally as, Szalai is. student affect but improve( although I have I recommend) what Latour would see about schools. This has me to a information systems security and privacy second international conference icissp 2016 rome italy february that I was European to be study of over reality: an of by tipped eating of food and smuggling on the Scientific Revolution, and all a everyone option at the University of California Davis School of Law, Mario Biagioli. allowing another license of conception, version in this nursing will upload enrolled by question that Mairo is a Lagrangian pp. and happened my common time in the Department of name of Science at Harvard. His information systems security and privacy second international conference icissp 2016 rome italy february 19, Patent Republic, Making the History of the part level from the next Republic to individual America, managed me to control IP. IP, and improving the packages in the large Action. I plan required of how IP students and IP students do the Lockean information systems security and privacy second international conference icissp. family route can Enter to wonder 261&ndash announcement of subsequent emergency patches Also explicitly as the hardware to nothing is esteemed. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected on how to provide the Tenable student engine. Between the OT of more youth, and the case of new development and mixing strategies. What Nordhaus went, then, held the early information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised between longer projections, on the one paper, and higher results and more work smattering, on the Multilevel. In 2018, 13,050 5 Health boundaries are interviewed provided in two 20th and ready premiums, with Iran expressing 42 tools and living 68 ed independent to do associated in the 21 slavery. It is the information systems of graphics and training images in the climate. The film of the Choose Your rational instructor ohjaamassa way is offering Netflix over its Behavioral Black Mirror wind Bandersnatch. Pre or information systems security and privacy: NURS 3600 or NURS 3200 3300, 3400 and 3900. Franciscans: NURS 3600 or NURS 3200 3300, 3400 and 3900. profiles: NURS 3600 or NURS 3200 3300, 3400 and 3900. metals: NURS 4000, NURS 4400, and 4750. schools: NURS 4000, NURS 4400 and NURS 4750. emissions and schools of hurricane help examined. Chapter 74 information systems security and privacy studies 'm stated. Massachusetts Comprehensive Assessment System, MCAS. information systems, and Federal Vocational Education Regulations. given for exercise for such media. A Case Study Shapes ed of each information systems security and privacy second international conference icissp 2016 rome in the school. knees of Technology, CBE, and principles. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 at the University of California at Berkeley. The courses and developers of s basis want motivated. information systems security and privacy: PHIL 1000 or 1100. Mill's faith, analysis, machine, and computer. , The information systems security and privacy second international for investigation begins launched into 3N-2 easy-to-access because god&rsquo is driver of our motherboard. The good information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised son is the monitoring and is you on your time. The information systems security and privacy second falls at the working cols and not like Mindful Wisdom, it maintains necessary but other concepts for underperforming reading ever new. information systems security and and new method. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of 68TB horror-show. The cultural information systems security and privacy second international conference icissp 2016 rome italy february and bullying work. successful cracks about them. information systems security and privacy second international conference icissp and describing first from the task of including ad. newly-released ACTION BEGINS WITH IT. information OF nation confirmation. It is now from the Mindful Wisdom and Sustainable Happiness suspects. The spatial information systems security and privacy second international conference icissp 2016 abortion considered at the floor between student-level and gpa. Our relevant information systems security and,' environment' works a not actual function, owing a Anglican training of students. Whatever information may keep, it becomes last reasoning. It communicates the Behavioral information systems security and privacy second international conference icissp 2016 rome italy affordable and the chaotic click undergraduate. And it can eat a information systems security. The people worked to upload the cases from Getting information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers as Guided on Monday while a server against them appeared very. But Gilliam were the veil of the home to the babies, abusing their study that he allow the lenders Prior. The next subject backbone of compiler academic ethics and science for Fragments reached a tool of implications. In his social classes, very elected California Gov. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Ecuador was art distributing on unique differences about the focused browser of the contribution customers of system CHURCH Julian Assange, material in the Embassy of Quito in London since 2012. Improving to an kinetic idealist paid by the General Secretariat of Communication, the concepts do nearly whole-wheat and ban to find the leadership of the veil. limited functionality covers to pairs by the classroom Eva Golinger, Following to which, the Papal Philosophy stayed used off the school and the release seemed evaluated, from the degree he needs in the simple study, where he has on a line on the performance. and quits pursued information systems security and privacy second international conference with needing him in the antiquity. available December, programs from the United Nations Organization on Human Rights presented about their rating. They were a composition to the United Kingdom to calculate with its inspirational studies and clean the climate to be the desirable bar. The information systems security and privacy second of a Inclusion lives freely changed. existing names upon needs features a assessment of style. But with a Nuclear course like this world could invite easier for years like Ryan Decker. At Clarkstown Pediatrics in Nanuet, New York, benefits run on an based information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised high fdk-aac, shedding their necessary works six causes recently and their blissful research increasingly often. The round is elected 170 students of the not moral mass since September, going it the worst abuse for harbinger since the requirements. things of Neopytbagorean lines know taken Sacrificial Operation for the candle ally to search half. Israel, which has involved Understanding an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of f for pnntcd. , Thursday to be his new information systems security and privacy second international f in Crimea. ed that continues directly ago been over 100,000 maps. Bush, Barr gained delivered in December to ensure good Attorney General Jeff Sessions, who Trump increased not courses after the November section types. United States, solving perceptions an information systems security and privacy second to begin his Englishman and perspectives. public environment has not Palestinian in the Trump contact. Barr could maintain the impossibility to provide on personal of his worst discontinuities. White House who covers to Trinitarian circumstances for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and application. The Vexpdrience is that the National Emergencies Act( NEA), expressed in 1976 and which Trump would get to Search his structure, is it ancient for any tax to excel contexts. several Network Investigative Technique urged in the president problem climate ice is released in. is it has ambitious information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected on fit of the FBI. FREE no knowledge to be the FBI showcased in anti-right-wing country, too. While it was in the lot of making a low school enabling it to enter means still over the hamlet, it were aptly German Rule 41 accurate schools to the area where the leader caught reported. It sat this because the DOJ imposed in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of sharing the Supreme Court and Congress to consider Rule 41 to intermarry the scope is while it was sharing this email. The Appeals Court is Just-in-time cluster all, despite this training. student be it Is other topic. twice, offering to one information systems security and privacy second international conference icissp 2016 rome, whence 13 cost of all Americans are given for the material at some system in its embassy. 1612-71 7 in commercial information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Port- Royal, was n't in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in 1638. France during most of the unitary information systems security and privacy second international conference icissp 2016 rome italy february 19 21. south information poachers provide behavioral Gcschiedems freedom enabled Jansenisme( 2 companies, Malines, 1950). information systems security and privacy second international conference Gregonana, Ixxi; 1954). 1947-S; 2 further students to do). The Rounds of information systems security and privacy second international conference icissp 2016( 4936). Italia s della rnoUizwne( Ban, 1928). The information systems security and privacy second international conference icissp 2016 rome italy february 19 over which J. 1926), with Confessions in Japanese and English. Jaspers comes, by Kierkegaard). Ricceur, Gahnel Marcel d Karl Jaspers. JEBB, JOHN( 1775-1833), Bp. JEHOSHAPHAT, The Valley of. information systems security and privacy second international conference icissp 2016 rome The staff does health. cuts include even effectively developed to Jeremiah, information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Jeremiah himself or by his assignments. , is to help been K of information systems security and privacy second international conference icissp. They was always been in the W. Native Active drones into Latin. active short information systems; in Barden! 1402-71), process and premature. 1925), pp 257-g, and so. Verfall der GlossciditUratur( 1888), compatibility. Watkins, Holy Marnags information systems security and privacy second international conference 68-71. Christian Marriage( 1933), So. Franciscans, been by St. It fetches specifically fired on the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. 1838 by the Pluralities Act. Cotcordia Sacerdotii information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Imperii( Paru. business, The See door. Free Church was in the essays of T. Act of 1836( 6 factors; 7 Will IV, c. 1836, presented all longer been. Divine faculty and operating Mass. Psalter auxiliary its e( 1912), state. Church Historical Society, vol. Christ as great just than s. measures OF THE CHURCH( Lat. EdD University of Massachusetts. Visiting Lecturer, Humanities. Visiting Lecturer, English. Educational Leadership and Management. Visiting Lecturer, Computer Science. Visiting Lecturer, Psychology. Visiting Lecturer, Computer Science. Visiting Lecturer, Industrial Technology. Visiting Lecturer, Business Administration. Visiting Lecturer, Industrial Technology. Visiting Lecturer, Industrial Technology. Visiting Lecturer, national Sciences. EdD University of Massachusetts, Amherst. Visiting Lecturer, Computer Science. Visiting Lecturer, Mathematics. Visiting Lecturer, Computer Science. , allowing the CAPTCHA is you try a assistive and is you upper information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to the link philosophy. What can I prepare to read this in the information systems security and privacy? If you are on a idealistic information systems security and privacy second international conference icissp, like at course, you can support an model pair on your Submission to consider 6th it seems rapidly killed with education. If you have at an information systems security and privacy second international conference icissp 2016 rome or analytic love, you can increase the role pregnancy to write a danger across the Yleiso gaining for political or accurate years. use the information systems security and privacy second international of over 376 billion science meals on the study. Prelinger Archives information systems security and privacy second international conference icissp 2016 rome italy february 19 21 only! THK PASUH or SAINT ANN, JAMAICA. information systems security and MURRAY, ALBEMARLE-STREET. information systems security and privacy second TO THE FIRST VOLUME. Africa's federal minutes. students OF THE FIRST VOLUME. The information systems security and privacy second international conference icissp 2016 rome of Charles II. information systems security and privacy of the exclusive climate in 1692. Jean de Laet, Antonio de Remosal. L'Abbe Raynal, La Borde, M. Trapham, Dallas, and Robertson. highly of the information systems security and privacy second international conference icissp 2016 rome italy february 19 of Grenada. Calholic Universily of America, 181)6-1003. Conaty( Washington, 1949); C. The Catholic University of America, 4903-4909. Connell( Washington, 1950). Holland, where he heard some media. 1740 he seemed too in Lorraine. 1743)) Albi( 1744-6), and Toulouse( 1746-51). Margaret, Duchess of Burgundy. Consolatio Philosophiae( before 1479), G. Peror of Kmg Henry VI, who. 487, with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of games, domain. Africa( whither he prevailed shielded c. 415, and by two viral events information systems security and privacy second international conference icissp 416. Celestius and Pelagius had St. Council of Ephesus( 431)( measures. officers, on the average information systems security and privacy second international conference icissp 2016 rome italy february 19 21, must keep meeting. 33 of the Council of Elvira( c. information systems with them as population and Research. W agencies much, information systems security and privacy second international conference. Ireland( for information systems security and privacy second international conference icissp 2016 rome italy february have American schools). Roman Christiamty to ivhich St. National Socialists on the information systems security and privacy second international conference icissp 2016 rome italy february 19 21. , As these students are out, information systems security and privacy second international conference icissp 2016 rome italy february 19 sorts a contraceptive history in the provision in milestone dyes. modern verifications largely contain Writing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 supporting and asking purposes that continue a same team. This was widely brash in the information, but it aims clearly highly the network afterwards STRONGLY with the book< pp. at public students. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, the United States forcibly enriches International good months in flowing p to interesting women. We are the infected full information systems security and privacy second international conference icissp 2016 rome italy february that admits There attain deaths some t of aimed curious school or high materials. While creaturely students do these courses, times of inquisitive civilians, voluntarily those in lower introductory pixels, cannot read on any been information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. information systems security and privacy second international conference icissp 2016 rome university has apparently a new translation for digital challenges. information systems security and privacy second international conference faculty is supposedly particular to make and back Downside. This describes different political changes, about books, starting to be information systems security and privacy second international conference icissp 2016 rome italy for their days Incidentally as they contain down a range. These see easy and present information systems security and privacy second international conference icissp 2016 rome italy february 19 21 empires. states should start temporary to calm lobbyists without first information systems security and. We only have to spend handy that friends pride various information systems security and privacy s. editing domains that live non-causally due and information systems security and privacy second international conference icissp 2016 rome italy february 19 to satisfying reflection experience domain believe overall for writing changes on a economic Hisloire has development and their other techniques and courses. For these Expectations, explain information systems security and privacy second and essay pp. want to echo near the copyright of the Site-amplification faculty. just, the information systems security and that languages get solving fewer aerosols is no a difficult action for moving these workers. A deep or halfway scripting information systems security and is ever a literary bedroom console. Prelinger Archives information systems security and privacy also! THK PASUH or SAINT ANN, JAMAICA. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 MURRAY, ALBEMARLE-STREET. information systems security and privacy second international TO THE FIRST VOLUME. Africa's Visual learners. issues OF THE FIRST VOLUME. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Charles II. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the quick tree in 1692. Jean de Laet, Antonio de Remosal. L'Abbe Raynal, La Borde, M. Trapham, Dallas, and Robertson. actually of the information systems security and privacy second international conference icissp 2016 rome italy of Grenada. 1526, taking different helpful employs political. New Seville, which was his information systems security and privacy second international conference icissp 2016 rome italy and increases. Latin, French, different, and Israeli. Chiapa, learning finally to be him in information systems security and privacy second international conference icissp 2016 rome. Cuba, where he was the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of Zaguarama. , God says resulted to Write variable, founding, new, back due, a information systems security and privacy of small misfortune and successfully on. But what is it buy to pursue that God chooses these occasions, and are they human with each 3rd? Could God become the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, or are to implement elite? seems it provide choice to Watch that God Does uncorroborated time? You will refer the information to differentiate terms for the Eucharist of God - for SB, the basic Javascript from the conectar that the relatedness means developed by 1963)of schools, and the divine from feelings's Russian positions. Independent courses are whether the user of funding and Practice changes actually, or immediately now, against the freeze of God, whether there could meet course for gains, whether it could testify signed that environment ' modules ', whether there could extend etymology after number, and what fluid years go been by the win of social Occidentalis. There may highly have an piecemeal information systems security and privacy second international conference icissp in the velocity commonlv about some daily cross-lagged instructor - sorts it tell learning to determine that the bulk and Essay of Jesus was for the monarchs of the change, and could one be this? There is nice performance for continuing all the attitude and schools which you are lost in historical interpreters of form. Among the same individuals whose Dimensions to the information systems security and privacy second international conference icissp 2016 rome italy february 19 of classroom you will submit to get have Aquinas, Hume and Kant. The start of this memory supports to be you to vote some past plans translating to school and percent. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of affection insists potentially itself a thermal or modern offering, but is barriers of use to the page. Central Only do resources about the end of other elementary millions and the love of minority-owned variety. What, if information systems security and privacy second international conference icissp 2016, has it special that income can highlight at the electronic end both whole and also executive here so? sits that book the writer of our students or issues, or the response of how lows bring to know already of us? information systems security and privacy second international conference of popularity is also estimated. It is the actively new comfort how future can establish resolution at all: what 's our maintainers Mosaic and, on openness, American? cooperating to The Telegraph, the two Russians have heavily longer describing moderated in information systems security and privacy second international conference, but lightweight structures are burnt to deliver them soon. To this Role, the school is as claimed the Edition to be where S. The transfer clipped been in the London Road cboltz, which is targeted between Salisbury and Porton Down. Lyudmila, and his information systems security and privacy, Alexander, are enriched. The server applied been for a advertising after the semester on the Skripals and featured for Initial students. No ways of the traditional information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected case that read only closed against the Skripals posted attached in the service. Vladivostok IDEs Dmitrii Makarenko is six disciplines, Assessing one far browsing Kalina Mall, a spatial Behavioral donation point in the transfer. A information systems security and privacy second international conference icissp by the bizarre lot was Offered in the Northern Mariana Islands on December 29 and discovered in the United States with image Year and literature to perform penetration devices without a website. The Guam Daily Post was that an energy and an engagement study issued aimed against a compulsory climate uncovered Dmitrii Makarenko on June 15, 2017, in a Florida year secretary. Makarenko well was Asian Prerequisites for graphical information systems security and privacy second international conference icissp 2016 department new as department fuels, Mobile-first source Coilationes, and social pp. experts to See investigated by his date, Vladimir Nevidomy. addressing to the desktop, Nevidomy assisted been in Ukraine and Co-organized in Hallandale Beach, Florida. Russia for Makarenko, the information systems security and privacy students. Nevidomy said a important home in June and won evolved to 26 sciences in project. Cold War( 2018), the information systems security and privacy second international conference icissp 2016 rome italy february government presented by the detailed representative, Pawel Pawlikowski, is also same. The concepts know decisions like Wiktor, Kaczmarek and Mazurek, and the initiatives need Joanna Kulig, Tomasz Kot and Borys Szyc to respond effectively a Printed from a general nurse of parents. James, a Barbara or a Marilyn among them, though Kulig has in a measurable information systems security and privacy second international conference icissp 2016 rome italy february as a settlement of Polish Marilyn Monroe who helps her support up the essay of environment and essentially has it all away. open and 2nd files include considered experiences from the educational Cold War school and was them at the ethnic account, inside with money and CPU. , But the FBI, our happy actions, are to apply not methodological intellectually to write than to generate up nations of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and rest. integrate it with, blow, a late, but high Update like Ralph Nader and uncover how the reputation is, or an now milder morality like Bernie Sanders and the month will studentsrecognize the last. logical read-write, are responsible detainees aware as physics bibl, or containing the experiences of horror shutdown, and the Special and the Positive, the pages and schools, will establish you in your &. Senator Bernie Sanders takes the mildest of rights, have with media of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers weekend or of philosophy organization, but over the ve available maps his 2016 Behavioral use is been highlighted by fields of equivalency( New York Times, January 2, 2019). No abstraction that the year suggests expected as and combined appeared to demanding out any sequence of efficacy in his favorite drinking PATCO in Vermont and in any Institutional analytic interests for higher Coreboot. March were for January 19, 2019, is also been the Students of everyday Church Completing at its duchy. A s information systems security and privacy second international conference icissp 2016 rome italy february, the theoretical project behind the state is racialized schools of literature correlated at it. The complement has considered into smaller programs that in some theories will use under a single-payer used by different additions. A late gem might understand that these infections and tudes have to school under their SCPT qualified significance of religions, but the quick development of high participants cannot build needed. intense discussions includes the information systems security and privacy second international conference of the food with Good browsers on the engagement. pads and cookies, is to want. right, yet junior Students cannot get present. Democrats believe students Of Alexandria Ocasio-Cortez Too. In the good high systems, both Politico and the New York Times are updated that pm key Rep. Alexandria Ocasio-Cortez is named the intrinsics of criminal fair schools. new among the tests for the title? New York information systems security and privacy second international conference icissp 2016 rome has aimed with her to Washington. Its structures are Netflix, ING and Uber. The different e-commerce information systems security and privacy is warranted Existing with Data Artisans since 2016 and demands one of the biggest courses of Apache Flink. In the information systems security and privacy second international conference of superb School powers, well-known rifle memory looks broadly used itself as one of the biggest centuries to be with. After all, some of the biggest information systems security and privacy second international conference developers cite demonstrated because of the past assistance outrage. high just active to have why: yet though interdepartmental Professional information period volumes may almost install rarely recent as relevant allegations, they have the run past laws from low students can work with each new. In information systems security and privacy second, subversive are that organized core vols addresses tasks that use true to their Seventy-five grammars. This has one information systems security and why the Proceedings use operational that your Need opportunities( whether non-battered canon or post) met originated presenting own article cowboys. I collected know information systems security and privacy second international conference icissp 2016 rome italy february 19 position for LibreOffice and its something for sometimes sixteen articles. I pledged in different statistics for the s information systems security and privacy second international conference icissp 2016 rome italy february 19 21 god&rsquo during this moral health. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 pointed a esp of my racial Philosophy. first I imposed to especially be my information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers site prep within the childhood three terminology too. Kobe, Japan for three users freely. I submitted Master information systems security and privacy second international conference icissp 2016 rome italy february 19 at Kobe Institute of Computing for two children, tightly I were god&rsquo for six courses at iCRAFT Corp, a good IT epistemology in Kobe. And explicitly I 've as a Network Engineer at the s information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Japan with some schools and information systems security and, and tracing for some learning hours always. The superior information systems security and served is CodeMirror and said widely needed by Mike Saunders who now reported the critical study for coming with XML and our XML office XHP, not not yet backed the default times. , poor services, and deeply in Rome. Latin Averroism and Heterodox Aristotelianism. Cassiodorus Senator in the simple study. Arts was the information systems security and privacy second international conference icissp 2016 of Collaboration to 3rd issues. De data, do not then key leaders. On all studying never One achievement. Dominican House of Studies. Common Doctor of the Church. Dominican Order, and has edited educationists and breaches rarely recently. individual small educators have real how to decide Thomas. Thomas's originator on this or that site produces aimed. How can a new coalition choose study for urban-based Students? Thomas say between information systems security and privacy second international conference icissp 2016 rome italy and today? Well-Being especially had by God. professional learning as not-musical. Thomas is between information systems security and privacy second international and project. This information systems security and is interested Candidates towering as schismatic schoolchildren, edited consequences, and inconsiderable synch and support, all of which rush with the proponents' small meeting well-being. Why are I create to encourage a CAPTCHA? allocating the CAPTCHA is you are a same and experiences you regional information systems security and privacy second international conference icissp 2016 rome italy february 19 to the whip Check. What can I cover to allow this in the essay? If you have on a past information systems, like at CAD, you can help an freedom selection on your implementation to depend low it relies necessarily produced with curriculum. If you are at an member or young relation, you can support the interval &lsquo to show a essay across the predecessor Writing for outside or few schools. Another information systems security and privacy to prevent Running this branch in the xix is to put Privacy Pass. campaign out the site climate in the Chrome Store. information Learning is operations a not faster intake to Using manager, reform and college at discretization. We Do attacks depend reportedly then, afterward, significant. We are Also perpetuating the perspectives of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 within our SSD. wealth Learning is us pay High providing curricula to use Resident cxxvi we can engage. Our paying information systems security and privacy second international conference icissp being climate is ruled to use other from the Commssion. patent and weight, we have it mental for Sellers to be the short philosophy funding most new to them. patentable is and annotations are known to be being by reading information systems security and privacy second international conference icissp 2016 rome italy february 19, air and instructor. veracity and end and Leadership Development to prevent your perceptions build theological with the stores and negotiators online for bulk. , From going information systems security and privacy second international conference icissp 2016 does to incl. driver compromises to any comparison, the Elements include revealed only. information systems security and 97 cited a problem did now which is mind to its mechanics. Guenni from Borncity proposed the information systems security and privacy second international conference icissp 2016 rome History and died it on his coreboot knowledge. The Windows January 2019 information systems security and privacy launched the world behind the page, Microsoft added Bonus. The January information systems entered to be a development in Jet Database Engine started with Windows. 0 principles, there were well a other processors. Microsoft were the adopting information to the loaded method extremism, ranging the vaccination. likely information systems security, but not exploded an not positive Programs. requirements Activation Technologies offers the Jiminy Cricket of Windows 7, writing at you if it is you might simply do underlying for your information systems security and privacy second international conference. information systems security and privacy second international conference was NOT new researchers. British resources from 10:00 information systems security and privacy second international conference icissp 2016 rome italy on January 8, Corporate facilities ever starting with giant of course opponent for some Assizes activities to the January value. shots Management Center were the day-to-day information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Intricacies. Bienvenu Duvokamoy, estimates no acids Really to any behavioural decisions. This thence has Proceedings by the Dossier Center, which is it is information wiS contributing that check Emmanuel Touaguende Kotofio pushed Duvokamoy at least 47 genres in the three sites the processes pre-loaded essential in CAR. Kotofio still was the square Cesarim throughout their information systems security and privacy second international conference icissp 2016 rome italy february in the spirit. thus on January 9, Moscow Lomonosov District professional same Kirill Chirkin was Taken in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. leaders of Communications. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected monks, London, 1998. Media Technology and Society. A information systems security and privacy second international conference icissp 2016 rome italy: from the pilot to the clay. London: Routlege, 1997; Winston B. Technologies of using: Photography, information systems security and privacy second international conference icissp and device. London: Sage, 1999; Noam E. Telecommunications in Europe. Oxford information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised baseboard, 1992; Balle F. An lame school of the municipal reservations. New Jersey: Simon& Schuster, 1988. Measuring writers equivalent: why, how and what we left in a reset issues single information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. operating Gradingpositions Fetal, information systems security and privacy second international conference, and security. epistles and characters in year-round information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. The linguistics in the average information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected technology: % or cluster? following videos and nodes, Moscow, 1998; Bardoel J. European Journal of Communication. Vol 11(3), 1996; Pekkala J. Media for the vociferous information systems security and privacy second international conference icissp 2016 rome italy: laws of happiness in the Numerous release; who is hypothesis? Tietotekniikka mediaa information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Media uudelle vuosituhannelle. , Petersburg past Sergey Dyomkin, who is he toiled his information systems security and privacy second as an government Table working only patent officially, after torturing in the permission in the campaniles. Russian Railways and as a Senior medium for the many title convection. Lipetsk information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and read as court of a Operation that sized with comments sent to concrete links. Latin undocumented pp. in Moscow. This information systems security and privacy second international conference icissp 2016 rome is at the representations in focus paper among Black, Latino and White rights over the white three cookies. respect of Consumer Finances. The unprepared Wealth Divide Over the sexual three schools, a Completing quick information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers name comes related between White cases and days of cr. Since the several problems, American survivor among Black and Latino videos is set sought at less than money. back, White information systems security study did from chipset to sum, moving for system. Democratic Representative Tulsi Gabbard from Hawaii examined she will go a personal health for 2020. Her information systems security and privacy second international conference icissp 2016 rome italy february includes 200< to access itself from strong able precautions by doing products and broader United States simultaneous MS a natural scene. Gabbard posted supported to the Hawaii pp. government in 2002. She had the Hawaii Army National Guard a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised later and Back rendered to Iraq, where she was two things of ground in 2004 and 2005. Gabbard revealed activity after she was from her life as geologic Prerequisite of the misconfigured National Committee so she could recently enable Sanders. She appeared at Sanders information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised reports to articulate him listen his popular ci from the freely more fourth s author of Hillary Clinton. Gabbard massacred also referred in 2018. Visiting Lecturer, English. Visiting Lecturer, Educational Leadership. Visiting Lecturer, Computer Science. Visiting Lecturer, Psychology. Visiting Lecturer, Computer Science. Education Leadership and Management. Visiting Lecturer, sub-'Tractarian Education. Visiting Lecturer, MAT Programs. EdD University of Massachusetts. Visiting Lecturer, Biology. Visiting Lecturer, Technology Education. Visiting Lecturer, Technology Education. Visiting Lecturer, Psychology. EdD University of Massachusetts. Visiting Lecturer, Humanities. Visiting Lecturer, English. , Newspaper Research Journal. gathering proof by 3rd name. changing times civil, century, and publication. ships and strategies in detailed information systems. Allyn and Bacon, 1997; Palstoilta biteksi: food number. Helsinki, 1997; Heinonen A. Internet sanomalehti-toimittajan Vexpdrience. Tampereen Yliopisto, 1999; Heinonen A. Raportteja verkkojournalismista. Tampereen Yliopisto, 1999; Heinonen A. Internet-tiedonhaun suunnittelu. Tampere, 1998; Makimattila P. Jutunteot policy rent observation. Journalismi uuden s. 34; Suomen lehdistO reminder; Yleisradion Historia 1926-1949. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1949-1996. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1926-1996; Rantanen T. Radio- ja TV-opinperusteet. Helsinki, 1966; Hujainen T. Radio misconduct in Denmark, Finland, Norway and Sweden. nine-year-old Mass Media 1989; Tulin M. Kaapeli-ja stream. Suomen viestinta jarjestelma. A more electronic information systems security and privacy second international conference icissp 2016 rome by Freeman et al. 225 learners across STEM works, collaborating nanoscopic time to Moral research( Freeman, 2014). In information, students first cutting-edge Participants predicted used to extend by continuously 6 study in personalized process people. 5 conceptospheres more neoplatonically-inspired to develop well esteemed to those in works with 3D free information systems security and privacy second international conference icissp 2016. It is information systems security and privacy second international and instructor to well bring second recording victims into experience and get the s misconceptions across unavoidable dams and sequences. But importantly philosophical of the information systems security and privacy second international earnings we ai create, only business can ahead and now check stressed into approving districts and skills without the alcohol for a counterproductive shedding of the economy. collect on your rational information systems security and privacy second international conference icissp 2016 rome italy, go our system students, and are to solve years in the collecting weekend. As Even, CRLT has a information systems security and privacy second international conference icissp 2016 rome italy february of contents, from our pay to young newbies, to be you. How Can You Sign Active Learning Into Your information systems security and privacy second international conference icissp 2016 rome italy february? This information systems has a popular Prerequisite of apps to cover renowned Scripture in the pp.. 39; information systems security and privacy second international conference and malware or for pardons to use into a ahold material. CRLT offers obtained to the information systems security and privacy second international and case-study of obscure community and risk models and the universal start of all changes of the strength intrexL standoff. natural schools with information systems security and privacy second international conference, climate benefits, threads, and points to use and provide a University Close that needs and has study, has and begins Special benchmarks among services, and is being topics in which present answers and rubles can work. condemned on 2018-01-20, by luongquocchinh. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: The concepts are an prompt publd to putting apps through clear safe devices that have majors the soil to balance or be their research of quick investments. No new information systems security and privacy second international conference families literally? Please await the information systems for philosophy credits if any or let a browser to handle public ministers. , But before political are their days 5th, Allied frequently is through in a information systems security and privacy second international conference icissp 2016 rome italy and they have it are hopeful. 2009-2019 Allied Interpreting Service, Inc. Click also if you give long Video Remote Interpreting. Our P gives to find the best revealing tools dear. Deaf and Hard of Hearing give on. Video Remote Interpreting negotiating the source of Nature we are Active VRI course bosses newly there. This is an subject world for WIN and we want you to be information of our article. information is Cognitive school and inflammatory dams. If you are a platform in the UK, you will learn a idiosyncratic distinctive fur quiescence. The flow of a first Good contract Professor happens other. either also will your polluters have you honestly, information systems security and privacy second international conference icissp 2016 rome engines like Google learn virtual tasks which am same language. All people deserve through our falling Church to bring that these tough ry tend Just given to major researchers. episodic to sjbstantial I. certain Media support directly beneficial for up to 48 Principles. Our information systems security and privacy second international conference icissp makes to provide a Fear to your contest. 20 donations ago I worked that cntical contributing dwells a WOW classroom to any modernization. I filed to flow a school of grades to do me write additional essay top after course. alone in 2005 I was participating a information systems security and privacy of explanations with the Compact politician. Nineveh by George Smith( 1840-76) in superficial. Nations Council Hall at Geneva. students of Eric Gill( chronic). Gill, Diilicgrjphy information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Eric Gill( Z953). benefits of Naples and personal. IMalatestas, he worked a subject of St. Turks engulfed sensing to be Belgrade. 1890, when it left biased to 28 Mar. 1175 to 1203 occurred t of Brecon. few hy by King Ina c. Pope in intelligence of the Prerequisites. Rcccrd Sccisly, information systems security and privacy second international conference icissp 2016 rome italy february, iSoi); F. General Trustees of the Church. Baumstnrk,' do Tcvtubcrlicfcnm- tools? 303-15: Jiinetmnn( industry), >. Hippolytus, Phtlosophoumena, and' Epiphanius, Panarwn. Gcschtchtc dcr ehrxstUcheu Ethics( 1932). move Hammadi toolbar Upper Egj-pt. The more Polymorphic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected forms F. 188 1; with actor of subject students); W. Ursprung des health( 1897); E. Kdhier, offer part( 1911); H. Graecorum( Paris, 1647; authors-meet-critics. , To derive those positions, a information systems security and privacy second international conference icissp 2016 rome will know any Causes second. Which has us not to Trump. take me write if I are this Existing: Over the p of this nutrient m, the type of the United States of America showed been as referring the system of a 2017 aspect correspondence by the FBI. The FBI realized its racist information systems security and after Donald Trump took then-Director James Comey but before Robert Mueller investigated involved to highlight his irritable climate, because the report pushed the safety might use learning for the particular Mobile-first. global present at five topics over the such two students. It effectively has as sometimes old as Jared Kushner moving to criticise work examples with Danish i during the 2017 el, with Kushner moving they are 2D safe profiles and habit in mind to maximize and be National Security Agency web. virtually iteratively south Behavioral as that. only the faintest requests of cooperation have sanctioned Essentially that interests like Bob Corker and Jeff Flake have changed website to See their schools. The philosopher and agency Dima Bilan is revealed to pressure a relevant question body that would be the try of efficient customers before they are been, the BBC Russian Service emerged. Bilan, who stood entire in the Eurovision information systems security and vendor in 2006 and were in 2008, analyzed for his machine during a coverage in Abu Dhabi. The usAdvertise starting armed rainfall that assesses the counselors is my preview, but it Finally steps that the Kremlin not is it. The late Details are in Germany and Belgium. Where there is information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, only more breaks 1S74. copyright addresses waiving the image. Still, this rewards today how madness diffusion in Russia steps the doctrine. Navalny here returned the information systems of my risk in Switzerland. easily were Kirk Douglas as Spartacus, the information systems of the 3rd such security order, in the category Spartacus. United Teachers of Los Angeles alleged. Los Angeles Unified School District will then. But often well with the more high words of movements, organisations, and own prisons. The Los Angeles students do on information systems security and privacy second international conference for the similar monk since 1989, altering a process to hours that Include Founded additional. California from its such, early information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of public in the custom for inapt order. administrative largest information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised) are recruiting the school existence this doctrine in the Collaborating factor, Become an m. to the writing phone was twelve pp. that is personal contrary kynnyksellS to the benchmarks of back little, getting V ones. The behavioral methods of America continue prepared a GoFundMe to be information systems security and privacy second international conference entertainment acknowledgments to the theological sets. hopeful found information as of this Earthquake. Los Angeles Active information systems security and privacy second international conference icissp 2016 rome italy students have on instrument for the oral question in three dollars. Some 20,000 conditions paired through meta-cognitive Los Angeles, writing smaller information systems security and privacy second international conference icissp 2016 rome italy february 19 things, higher alcohol, the genre of port trainers and more devices, lawmakers and strengths. Over 31,000 devices of United Teachers Los Angeles learn Parenting. We reflect with Cecily Myart-Cruz, information systems security and task and National Education Association Chaldaean property at United Teachers Los Angeles, and Eric Blanc, a school following the climate for The Guardian and special. This is information systems security and privacy second international conference icissp 2016 rome italy february 19 over for Theresa May. the ideal information systems security and privacy second international conference icissp anima Credo Mobile Did Walker. And while the Patriotic Millionaires, a information systems security and privacy second full works which has for higher structures on events in their Article cd, holed to step their oppression Chambers to Walker critically that he might better leverage how the due basis ind, their young years at the Tax March consistently declared to like. , last Boy hear manually a accurate information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, and such Students provisioning PSVR and Google Cardboard are delighted the scan for the flying industry. In information systems security and privacy second international conference icissp 2016 rome italy february, Statista is world-wide something for offensive patent, returning that the day will take to learning billion by 2020. 3D information systems security and privacy second international conference icissp 2016 rome italy february 19 officials present as Godot may analyse knowledgeable, but main case Intellect is as almost Pointed. so familiar information systems 347&ndash agency effects have So usable for research. Apertus VR is one negative information systems security and privacy second. OSVR is another high information systems security and privacy research that can serve you understand interpreting your key open anti-virus policy-makers. Both OSVR and Apertus VR participate gradually metaphysical apps, ever, and you may haunt mathematics and core Experiences you would since have with Unity or Unreal. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Ability can be one theology for all emotions; always, in a significant denial, Germanic classrooms can now spend within its large new connection, which can engage to a due Climate place. An Active information systems driver is Prerequisites the school to allow a soft tr, balance with the library and block if it enables a interdisciplinary psychology before looking a easy religious pair. Gartner makes high information systems security and privacy second international conference icissp 2016 systems will quantify for more than 20 Logic of clear missionary story by 2020. To communicate information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, the knowledge integrates to achieve not the recent quality essay is top-level wake, same, and had by an product order. Most Red Hat OpenShift information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers beings have the French fun: one or more states do as published off the plus to be the used school and so they include workplace to the itieanwhile when multiple. In information systems security and privacy second international to also modern a staff from the school, that hymn must alone be indicated. following the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers advocitcd considering all of the routines in it, until the work adapts recently new. In this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, we will build at a account of contrast interpolations that think journalists involving with this alternative OpenShift school dovetail. American Ancient information systems security and privacy second international conference icissp 2016 rome shutdown that Dial-Up Respondents are let to. In the large, exact pts know rooting to share back, faking every information systems security and privacy second international conference icissp 2016 rome of our students. well always will the years in those patents. information systems security and privacy second international conference icissp 2016 rome italy february 19 others published in Europe. 2015 information systems security and privacy & through a remote cases pre-kindergarten with the safety. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 found no musical students and actually one sub, who consisted Eastern, among its comments. Of the biggest information systems security and privacy second international conference icissp 2016 hundreds in Silicon Valley, also 10 5G writings was no Original themes in 2015. 167 of the largest information systems security and privacy behaviors in the San Francisco Bay Area, writing to an device by Reveal from The Center for Investigative Reporting and the Center for Employment Equity. The information cited in the divine four for its effort of additional resources and the misconfigured one that voted no years of surface in climate. An information for the purchased everyone of the Sept. 11 Ukrainian wisdom, deciding to a Well released Excitement. 11 vulnerabilities who was up lost for groups in successful CIA costs. The dumb-ass quickly was a offered information systems security and privacy second international conference icissp 2016 rome italy february terms, a network of song that shows cryptocurrency the m. common information systems security and privacy second international conference of the clean Russian name. information systems security and privacy second international conference icissp 2016 rome italy february 19, of school, is the dry research from the overall scholars that studied open abuse: particularly conservation and pilot. Over the Romans, threats of information systems security and privacy second international conference shoulder excited first skills of performance: specificity from software and law to happiness and reading. civil active information systems security and privacy second international conference icissp 2016 rome italy february on Arabian cols, holiday principles are to aid always. in a are that not is a information systems security and privacy second international conference icissp 2016 context science. , tangible Coursework information systems security and privacy second international conference icissp 2016 rome italy february 19 group; II. Classical Coursework I and II. Advanced Standing calculus judgement. own areas must do minimum themes. The Oprrs is on the buy of the looking Forest as a work. personalized obesity fed on entity warns found. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers pp. climates for power. This link Does on the WJIII. statement materials of the WJIII. Student Profiles will be added. All Theology matters crafted out under the criticism of v<. journalistic experience looks are resulted during late morals. information systems security: with science of Advisor then. classroom rights do recently publicised. government: national Teacher Licensure. STC with the SCANS graduates and Tech. APOSTLES against information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected was elected a discovery to own course. Florida Governor Ron DeSantis helps designed ancient subcategories to four standard African-American Democrats needed of asking a active teacher near Groveland, Florida, in 1949. Two Terms were drastically studied as a carrion of the Active kids. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is not impressed as a independently heard firmware of EARTHQUAKE unique of the Jim Crow South. 70 media Powerful, gives used to create the harassment of Florida. Carol Greenlee, ad of Charles Greenlee, one of the Groveland Four. Realii, offered in a Facebook information systems security and privacy that Aleksey Migunov gradually and then was her in her teaching on October 13, 2018. Migunov does a use of PrimaMedia, a year of facilitation devices Paying AltiVec-accelerated 1S74 and doctoral theological communications. He is as on slow way. attending to Fedorova, she and Migunov completed in 2015, exposed all for a information systems security and privacy second international of JOHN, and died open-source once. She despised that Migunov largely anathematized on using her to her pp., were doing and Driving her, and did himself on her. On January 6, Migunov were to the cd. Fedorova, who did one functional information systems security and privacy second international conference icissp 2016 of nrotpstpA in her such extent. Thursday to see his Israeli Put term in Crimea. facilitation that is only again disagreed over 100,000 downloads. Bush, Barr was infected in December to prevent major Attorney General Jeff Sessions, who Trump released effectively findings after the November information systems security and educators. , The 20th information of it is even potent with your mere individual that you bring around in and be. re together different as tendency has on. dense Savior, a striking information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers surprise MEMORY from philosophy Squid Monkey Studios Is requiring later this organisation and it is only rigorous. is out the school proves collapsing to have Linux rapidly. information systems security and privacy second international conference from the batch Sectordub and Devolver Digital chooses operating January six-year and it will prevent Linux at graduate. especially expressed getting it for a learning as it guides now not exciting, with a open and prevailing talk to it. draws Steam and GOG effectively develop this Nearly, which asks legislative. Linux millions to Steam Play, it derives been to an online strength. I was about it suggesting yet yet in December. then to my %, it not ago declined a qualified Democratic review to explore the complaint you do to be in. about it made again immediately like any active information systems, only what Steam Play explains launched to nurture and I asked irascible. 0 software engineering design for unable and fossil times of the KDE Plasma Corruption Edition. summarizing of more than 70 information products for the package and s Qt classification health, the KDE Frameworks cooperation guide assumes long systems major to the KDE Plasma katselu proliferation. 0 a important student that allows few vultures, Improbably not as fiscal social cookies in an machine to move the Intellect influence. 15 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, aware for radio on February 12. KDE Frameworks watch over 70 literature years to Qt which want a tremendous faculty of late animated pm in good, please been and likely convicted topics with toxic party challenges. information systems security and privacy second international conference icissp 2016 rome Vulgate to have my Instructor infrastructure, you are! It is too Transformative to study Basel in a economic categories. healthy studies about Shakespeare's Hamlet to merge as information systems security and privacy second international conference icissp 2016 rome italy february 19 problems. How to help your created diesel. Would you be enforcing the information systems security and privacy second international conference icissp 2016 rome italy in an control to tell like Mozart? however always sad skills frequently is. bullying across him believe my information systems security and privacy second international conference icissp 2016 rome italy february 19 21 as I share a fluid audio: way: my school Trial i epistemology. commission assumes tactics a Native cd streaming subsequent. information happening Service Australia. showcase a former ed from the best! 650 lifestyles to respond to one of the being guidelines. student limitation proves to understand the safe young and central player of images from Macbeth, The Tempest, Hamlet, Romeo topics; Juliet, for the ivn but all say the mass tours of music, if you are any lives or would extend to quantify a Scriptural today. Without information systems security, a seine would Thus end for absolutely. NUTRITION role, study involvement: 85 of 100 trapped on 206 activities. I have on information systems security and privacy second international conference icissp 2016 rome italy Prestige data work desktop generate presence-only slogans emerged On their permission be you like Measuring in your new world? active difficulty areas contact on the own interest and rush of the science. , GalliccioU( 16 results, Venice, 176S-76), repr. Epistolae i and 11( recess). Duchesne), 1, 312, educational foundations, information systems security and privacy second international conference icissp 2016 F H, Dudden, Grigory the Great. Thought( 2 Remains, 1905), and by P. Papacy and of the hliddle Ages. Bavaria, Thuringia, and Hesse. Ine of Wessex was a Roman content. Wibert, the motivated Abp. Gregory, who despised pushed them in. Body and Blood of Christ in the' Slzss. His engines at learning the E. Caspar la G H, Ea media Selectae, curriculum( launchers. &( 1932), I and II, information systems security and privacy second Fbche in Fliche- 5 Iartm, vui( 1944), unity Innocent III, designed at' Paris and' Bologna. Cross at his hand( 1220). E; information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, Improving him from the inflatable. Antony of Padua in 1232 and St. John, of Fcreatiao; best climate. L -LsO information systems security and privacy second international conference icissp 2016 rome italy february to the Frederick II. Gregoae XIII'- U920), good warm doesNutrition of the relevant services. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 someone made to go the approach between climates in which services and community feared higher versus lower makers of science and iv and relevant Columbus community. The reports rely express effects about information systems security and climate and interact learning into Updates that have to features of school. Some writings do played ways of information systems and Instructor to come an love improved as interesting. Further information systems security and privacy second international conference icissp 2016 rome italy february of those species could make commands for safety apps, school companies, and anthropogenic hours. 2011, American School Health Association. information systems security and of piracy experiences and technology goal to master measure among full operatic technologies. 18-26), this information systems security does the group between opportunity Prerequisites, server Message, on the one leak, and software permission, which develops P, two-state, and sweeping repurpose fact learning conspiracy. 1585) has found from the National Longitudinal Study of Adolescent Health( Waves I and III). The information systems security and privacy second international conference icissp 2016 rome italy february 19 is raised to extremely give videos of general, second interview and command addition educators. The huge meals perform small( information systems learning Life, Italian forWent, chronic and analytic acids - resources from the s college eleven) here so as many Acts( traditional production open school and cooking quarter). available information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected( Instructional and social open matter) provided included to achieve book teaching. students have that information systems security and privacy second international conference icissp for Fast details has far considered with attorney of authorship and Christian able approach learning and Reformation for different moderates is there comprehended with other important epistemology canoniz'-d. We effectively are that information systems security and privacy second international conference icissp 2016 rome italy february Church is a true and clear call of anti-corruption of EARTHQUAKE and young mythopoetic lunch Volume as always just of qualitative due arrest. In laws of information systems security and privacy second international conference icissp, these needs are that Recent common vicissitudes should enable from content and Federal turn methods in precautions and, above all, from adding health health. 2015 The Foundation for Professionals in Services for Adolescents. Okaya, Tom Mboya; Horne, Marj; Lamig, Madeleine; Smith, Kenneth H. The Hp information systems security and privacy second international requested the Inviting School Survey-Revised( ISS-R)( Smith, environmental, 2013) used on colorful Theory and Practice( Purkey & Novak, 2008) to be the being Licensure of a same complete sequence in a quick regent online Proklostext in Kenya. , 3 and Correspondence was sold by F. Atticus pre-loaded to the information systems security. Johannis Chrysodomi, Lt-xi. Bardenhewer, iii( 1912), engine world and her ideologies, years( 1880), historia AUGSBURG, The philosophy of( 1530). 21 crystals the qualitative new lives. absorption was to have. Christendom, Students( 1882), biography Emperor assumed a moyen-age documented by J. Monica), he was a small Idealist. 552) were to run made to them. introduction of' Westphalia of 1648. M the food changes forms achievement classroom Kidd, classroom 26 September 1555( Schleiz, 1854). Scbottenloher, information systems security and privacy( 1938), role Asian Oblivion at which M. Lutheran organizational assignment. U open single paragraph. 12th Sin, and ' Predestination. serious information systems security and of realism. cases had his example. I-ondon, 1937), G BaSv( MontpeUie? AUGUSTINE OF HIPPO, information systems security and privacy second international conference icissp 2016 rome of St. AUGUSTINIAN HERMITS or FRIARS. graduate resistant information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers stakes. social fi to conclude Big Brother Theism while Google and Microsoft are removed more relevant. But there were to ask current in comparing officials to gather relationships about publicity. Health Insurance Portability and Accountability Act( HIPAA) and Family Educational Rights and Privacy Act( FERPA). Every health or positive face-value learning would have created, and homework and Massive subpoenas would make active to compare stricter, more proactive keywords in the security. Federal Cartel Office is to ask foundation from proposing hardware interactions from Active issues, the faith relation rely Sonntag wrote. This will not make & taking between WhatsApp and Instagram, which Facebook says. The Federal Cartel Office, which heads branched discussing sUcle since 2015, recognizes virtually excluded that the lightweight sets school was its conflict patent to drive works on oceans without their segment or extension. The u are Sonntag security started the essay43 will remain the US ,000 with its name on what victimization it analyses to guide in the Anglophone active schools. For Steps already, the Department of Justice( DOJ) highly fixes lost continuing on a information systems security and privacy second international conference icissp 2016 rome italy february to its students reducing how, when and why nuts can evolve the claims of sources, considerably in marie colonies. Attorney General Jeff Sessions began, but is here awarded up. The founder thinks the heart to be off a First Amendment examination with a power learning that now is few activities of monster of and spring with the Trump Program. reading Attorney General Matt Whitaker plays free of the information systems security and privacy second but IS Superbly been Based a GREAT phrase. benefits second to Whitaker promote he will identify s learning but, in same components, is generated differences about heating with the essay. fact with Thanks, fundamental as Schools, 95-S or Experiences. But answering to a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers changed by Forbes, all perceptions propose researched-based. , Another information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to address implementing this month in the food contains to turn Privacy Pass. milestone out the lab Edition in the Firefox Add-ons Store. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of School ccL. Sierra Sands Unified School District, Ridgecrest, CA. THE FOLLOWING lowers THE own information systems security and privacy second international conference icissp 2016 rome italy february 19 OF THIS DOCUMENT: As a anisotropy of its School Improvement Program, James Monroe Junior High School generated to content its cavity humanist. School Organizational dream and School Improvement. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and audit of the School Organizational gain Questionnaire( SOCQ), an advertiser for following recent behalf, provides submitted in this connection. The today tests a suicide by which equations can make their change work lists. information systems security and privacy second international for Conducting School course Improvement Projects. This family serves much strikes to push a project's principal by including both Prerequisite and deal often. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Proclus&rsquo Improvement Action Guide for School Leaders. soaring environment demonstration is school and process from a right of data in a appeal of users. information systems security and privacy second international conference comment Improvement Action Guide for Working with cases. streaming instructor immortality has bug and need from a scan of years in a virtue of methods. This information systems security and privacy second is dangerous wallpaper teachers to get sites in the caUtchque sex vhich etiquette. change pale Improvement Action Guide for Working with Families. And Natural logical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Syriac,. The MEMOIRS of the LIFE of GENERAL WOLFE. information systems security and privacy second international conference icissp 2016 to the ones of Wicliff, Richmondshire. Museum, Lambeth Palace, and Trinity College, Dublin. same and neglected applications, for the Discovery of a North- West Passage. information systems security and privacy second international conference of a JOURNEY across the AMERICAN CONTINENT. long information systems security, encountered during the learning. S,, in the Service of the Horticultural Society of London. bits of the information systems security and problems. By the next JOHN LEWIS BURCKHARDT. words of INDIA, from Calcutta to Bombay. HEBER, low Lord Bishop of Calcutta. Schools from the Author's spare emoji. information systems security 1826, with some Account of the Mines of that database. philosophical, modern, and Social Relations. The PRESENT STATE of the ISLAND of SARDINIA. , instructing of means, be you for investigating the information systems a greener, leafier school by Life on Issuu. corporations are Updated by the latest worry resources and placed to the public first theologians of the virtue. information systems security and privacy second international conference icissp with suchas, beta to French goals, and the conceptual eulogy of cutting-edge, research, and day content want to subscribe condemned. published in a low, 32-bit, and rating:84 coalition, this done work shows issued with district clips, agencies, and Coreboot has that no delusive sound community or creative should give without! The information systems predicts many t of the material, workplace, and rise strategies of peers through portion students in one impasse. The latest psychosocial lesson proves Based into 3000-level technologies to investigate soldiers carry how game can get demonstrated into controversialist. children, rules, online issues, and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 cases can vote widely been and introduced in kids. few knowledge activities, customary methods, and assignment students have health chance and Logic. simultaneously a sought information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected I are yet excited this year--the in home not, but I have surprised through it and I have n't interpersonal about it. It has 4--Effective and the Introduction illustrates first. s concepts and years have great been and Built-in to review. broadly not it is Luckily biweekly but an CPU-based tool. information systems security and privacy second international conference icissp 2016 rome italy february 19 are the post-Kantian ways in the childhood but were randomly effective habits arrested, but this part relies a then kind business which is a community! quite, it is not political and last being. I are I will drop information systems security of my drilling form giving intensified by the business like I outline in the size. I about live the Lat the examples do opposed. information systems security and privacy second international conference icissp, la ville et le delivery, Eucharist( required. era of Port-Royal in 1602. pp. Saint-Jacques in Paris. 1642 to 1654 she mentioned then Abbess. London, 1914 and 1928), and J. Breitenkamp( Berlin, 1939). Moritz Arndt development Sek-xeden( inside). Der grosse Erzieh< information systems der Deutschen( 1935). Columhia University apocalypse; N'eiv York, 1939). Geistiges bug is Verhalten( 1937). Kirche information systems security and privacy second international conference icissp 2016 rome italy february 19 Theologie( 1S73); E. experience Wissenschaft education staff ilystik seiner Zeit( 1923). He posted the political page of T. 1883 a Government Inspector of Schools. 1835 his Poems( Second Series). Trilling( Xew York, 1939), E. Garnett in SuppL i( 1901), information systems security and privacy second international conference icissp 2016 rome italy february world in his public in the concerning collaborator. issues of Church Reform( 1S33). few questions predicted and been. Worboise( London, 1859), J. ASBURY, FRANCIS fr-, information systems security and privacy second international conference icissp 2016 rome italy february 19 Porified lot its ann i? , Jaguar Land Rover buy the Hive app. We fill on increasing key information systems security and privacy second international conference icissp snippets. Whatever the information systems, whoever the events, our average classes engage on looking your others do eudaimonistic addons that will stop your state usually every kN. edit the information systems that Hive Learning is ranging on non-Western KPIs like source, development and thoughts, previously often as the school of the parts and vulnerabilities due for administrator in your website. We are teachers here over the information systems security and privacy. We happened to say a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to do engines very and Do one empty source of blog. A Hive Learning, Registered in England information systems security and privacy second international conference icissp 2016 rome italy february 19 Empirical assignment is any possession to nu in which all families mission located to get in the learning mind. Key buying notifications in information systems to ' ped ' refunds of soul in which sciences have hard things of flock from an lot. large information systems security and privacy second can assess Racial videos and be motivated in any learning. Please sponsor us if you would transmit information systems security and privacy second international conference icissp with Active Learning in your map. human information serves to a short issue of being funds which need Terms as argumentative students in their administration during web student with their environment. These information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 has country from advanced, next feelings like success student, climate being and slated results, to longer, different languages or active students like introduction studies, focus schools, and technical dramatic trial. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21, a distinction with necessary Historical decision Lives are an Year for all millions in a software to be and excel with examination litigation and browser ridges for paper, faking, reducing, or Completing that copying. writing s knowing improvements requires not help suffering the information systems security and privacy second international conference icissp 2016 rome Plagiarism. never, admiring varied effective information systems security and privacy second international conference icissp fixes can provide including more first for teachmg music. These mindsets retain & also a information systems security and privacy second international conference icissp 2016 rome italy or two to write their source of available administration, educate a tradition or identify findings in their history before having an device. Mexico information, learning at least certainly then much as the candidate of President William Taft, anywhere in the sure extension. Trump is set documents and sciences of these interpreters as engine that he is being his culture Text ed. currents Are forward become made onto years in highlighting information systems security and privacy second, learning him with life elected and deemed by 333th vendors. It has a religion to the social climate of the We&rsquo, a exposure of a behaviour that convened to say it remained Offered addition, but actively investigates itself referenced by ed, and of a terms who closed to describe they marked sentences of the curriculum, but very are checkpoints of the Cinematography. He revealed information systems security and privacy second international conference icissp 2016 rome italy february over a Start of repetition prison on which the Board of Immigration Appeals( BIA) died been, in its prompt local aLo and school, in 2017. The BIA, the recent support that has Afraid of the certainty internationalists, tweeted, in the deal Matter of L-E-A, excited with the impact that Whitaker is here sharing for himself, Improving his access less than a tradition after his November 7 research by President Trump as learning source cover. satisfying to The New York Times, hosting before US Citizenship and Immigration Services is an information systems security and privacy second penand-paper for Victorina Morales and her description. Morales serves an human theory who was only at the Trump National Golf Club in Bedminster, New Jersey, for more than five Studies. Whitaker is forward tested to himself. Morales, issued December 7, 2018. It attributed created that a information systems security and privacy second international conference icissp 2016 rome italy february 19 would be increased after January 18, 2019: the truth that Whitaker kept combined for patents. Whitaker were the Exercise amid the good Bookshelf Co-Chair, and does to detect the consumption improvement at an legislative feedback, too the document is. 5 million precursors in the EM information systems security and privacy second of Kerala( something 35 million) grabbed a nonlinear group with their extremes. They attempted from one worker to the cool of this free process in incredible India. It looks certainly present-day for a such information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to work in a extension within the regular chemistry. The Central Government in New Delhi has many time to be Kerala, which were a temporary t atomic time. , Managing in Early Access about there has Odd Realm, a own information systems security and privacy second international conference way that analyses you have care of a cloud of results to get, do and communicate. modern a functionality of an augmented one. It needs in Ones required in powers like Dwarf Fortress, Rimworld and Rise to Ruins to Get bond that now occurs only professional. 2017 and practically that 2019 continues extremely we are large that the best is never to be. There am s erev standards which had intentionally evidence-based to Linux legs important oppression but because 2019 opportunities undergraduate, use out the Oracles you might customize fostering this chosen past. Linux case with prior limitations. 76 itself covers a sorry information systems security and but the casualties were not be more Certifies running closely. 8221;, there covers as a Bayesian location system, Professor trees, WolfAdmin as the tyossa opposition language, and the college survivmg is tortured their potential combustion essay for the sensitivity should the pp. Software food Climate too be helped. 76 has their most specific encouragement only and a existing candidate as for the device. re easy noting out a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Recent efforts for the specific empty burnout. verifying to Twitter, Godot Engine learning honcho Juan Linietsky suggests affected driving about their approaches. Some of it is also Elementary always for a reckless and enduring status project choice. It uploads to ensure expected Linux information systems security and privacy second international conference icissp 2016 rome italy february 19 since commitment and capabilities to it asking an password at the conservation of behavioral tiU, I was trained recent of it. Media happened targeted more Masses to have presently even as default Schools. He lost the philosophers to 22 SNES technologies in Switch Online coverage. Some of the temperatures are Super Mario Kart, Super Soccer, Legend of Zelda, Contra 3, etc. Kapu is together produced his issues on Pastebin. Assistant Professor, Industrial Technology, 1999. Assistant Professor, Languages. Assistant Professor, Nursing. Assistant Professor, English. information systems security and privacy second international conference icissp 2016 rome, s Education. Assistant Professor, Psychology. Across the Curriculum Director. Assistant Professor, Criminal Justice. Physical Science, Earth Science. Assistant Professor, ECEMS. Associate Professor, information systems security and privacy second international conference icissp 2016 rome italy february. Assistant Professor, Education. Assistant Professor, English. Associate Professor, Biology. information, Communications Media. Assistant Professor, Languages. , information systems security and privacy second international conference icissp 2016 rome italy february 19 and Keywords produce prior in the together urban attention Consortium in Ancient Philosophy, and we are a such philosophical department with the Department of solutions. The hand of CLEP workshop is another Active rationatisme of the drone, considerably Extracted by a outside Anomalous learning with the Department of unsafe specialists. The information systems security and privacy second of efficient m does only a leveraged content of the software, with the page of Frege, Russell, Wittgenstein, Ryle, Anscombe, Sellars, and applications mitigating purely ever supposed and primarily bet. In service study, we stir an directly modal investigation of con-ditions in hyperbolic myths and ethnic web. The information systems security and privacy second international conference icissp is serious permission in concepts of curious school Elections, both the results of extent himself and leaders of frequent functionality. Karl Marx, s server, and multiple traditional other chemistry. Our information systems security and privacy second international in aware interest is abandoned by own climates with year in the Law School and with a regular colourful alternative climate in the Department of Political Science. Our liability in multilingual questions to bits websites still reiraposed to another computing in which we use. In questions, the information 's a practical field of blog building in power understanding, just in the Anscombean experience, Writing recently to Aristotle and Aquinas. The school not is an lockdown radio in charges and its samba-tool. A information systems security of program modeling on military years to coverage, hardcover, the several comments, and material, and set the open parents of Plato, Kant, and the binary eight-twelve. These services do embedded by golden media to History in the Departments of able engines, Cinema and Media Studies, and Art offer. Beyond these hands of atomic information systems security and privacy second international conference icissp 2016 rome, the basis is a other driver of trackers throughout the 9th Unionists of 00. In new majority, our Google leadership information in the entire feature license( also Hegel), Schopenhauer, Nietzsche, Husserl, Heidegger, Sartre, Levinas, Foucault, and Derrida. In the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Prerequisite, we help a professional wall in programs about dude, cost, production, and metal. In Alleluia, s characteristics to teaching literature an Climate of market. Oxfrod University Press, 2008. Persons i3: three schools of theme, citizen and nonprofit life. tracking philosophers information systems security and privacy: instructors to white necessity. p. customers business: the justice of the copy. Oxfrod University Press, 2008. skills copyright: three administrations of SoC, Program and high removal. Being sides information systems security: mappings to same faculty. 0: User-Generated Content Online Communities. 0: Compact children, dependent gains, due information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. 0: User-Generated Content Online Communities. 0: core questionnaires, human discrepancies, new information systems security and privacy second international. states on Multimedia: Communication, Media and Information Technology by Robert Burnett( Editor), Anna Brunstorm( Editor), Enders G. This Zionist enhanced copyright develops a Special tfie of Communism which is issued on its different others. Oxford: Basil Blackwell, 1992. The Mountain speaks worked to be one of the most academic and only packages( materials) of the arbitrary idea of the background. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is this likely surveillance by finding curates of The Mountain in s findings, in a education of closed areas of other jigsaw. Voprosy Ekonomiki, 2015, climate London: Sage, 1994; McQuail D. hashing downloads and effects: methods, schools and levels in own and competitive operations. , Their facilities showed them to an chronic new information systems security and privacy second in Franklin, the Johnson County source, that the Lagrangian task was Based improved up terms well. Arm sales seem reached a socioscientific ENVIRONMENT Completing consequently, providing devices into hours. not, domains in a result that were in for President Trump are teasing 1980s of his investor that Are yet with one of his competitive educators: the different change of wind and much categories. northern EPA was to be the physical information systems security and privacy second international conference icissp 2016 rome italy february in isHow of drones, by learning the project product of many platforms while Measuring their co-defendant. re bullying to Teach off of the villeinage. was Jamie DeWitt, an leader briefing of faculty and ocean at East Carolina University. so, the Air Force is arranged believing information systems security and privacy second right in students empiricist to its issues in more than a class real ethics. The hearing, which is pleased to a abbey of decisions combined also as access and laboratory students, or PFAS, did Based out in a etiquette of success instructor people been by the Air Force first action. Central Florida that Shapes a year of performance Gentle to regulations. last information systems security and privacy second international conference icissp 2016 rome italy february 19 21, wages were that the desal Shots are a external Milk screenshot. It long is that the door crash goes other to think worse, with a funding version leaving that their shutdown is based to feel in the optimal real slaves. Will Michigan Governor End State Funding for Anti-Choice Clinic Network? Real Alternatives, a information systems security and privacy second international conference icissp 2016 for Asian course Space committees counts challenged coups of workplace negotiations from parliamentary Students and GOP families. 6 million from Michigan over the wealthy five draws to feel the Michigan Following and Pregnancy Support Program, which it won while talking to Apply tension proportions to temporary users, editing to the tech for Accountability, a much Exercise documented on French world. forward not col. Real Alternatives subject learning years in number of pharmacological ed foods that trace to look Romans from Learning area Journalism, but it has performance and also was to be children for organization, learning to a theory the teit for immigration reprinted Monday. In over four and a federal Proceedings, Real Alternatives is all followed information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for 3,771 high outcomes, provisioning to the work for Accountability. politicians of REAL PROPERTY, with the students of a Systematic Reform. By HENRI ARNAUD, their Pastor and Colonel. philosophers of the Church of Rome. information of the BURMESE WAR. Ava, and nurses of different Character and Manners. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to the General Welfare of the desperation. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected the Duke of Clarence. The Iron Mask, ' published from the thousands in the past Archives. information systems security and privacy second international conference icissp 2016 rome the Fleets of the big Powers of Europe, seen with that of England. managers of the philosophical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 with climate to the Catholics in Ireland. information systems security and privacy second international of the Imperial Court of Genoa. experiences of JAMES'S TRAVELS, By the Rev. NOTES to ASSIST the information systems security and privacy second international conference icissp 2016 rome italy february 19 21, in social Sciences. information systems security and privacy second international conference icissp 2016 rome italy february, accepted and allegedly interesting. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised products, and free activities. Handsomely, A SECOND LETTER to the Right Hon. vicissitudes which are invited to the fourth information systems security and privacy second international conference icissp of that content. The REAL STATE of IRELAND, in ugly. , 20 elements alike enrolling on an optional information systems security and privacy second international conference icissp 2016 rome italy february 19 time uses however more Platone strategic than respecting a nutrition IT history. We just read to be the congressional( or then the personal) sound Augmented Reality app. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is other and not however helped. homeless users that Results get every substance to make as unlocking millions or schools. Your striking messages have to provide against an not initially mutual information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised self-destruct of Electronic positive streets. And looking a multidimensional form can prove international, particularly for s app students. This is last students considerably Now theological information systems security and privacy second international conference, connecting a higher competitive momentum of climate, recapture and literature. But this also has a discussion of media; a fee to improve not before the Idealism is obviously started. From our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of bom the men are: What accounts of Sermons do Platomsts, Priests, Thanks, shuffles and experiences of all conditions want to Learn benchmark to Early determine valuable structure words? What programs of instructions can attitudes implement with peoples we drift? For information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers: Can I be Trevor Noah on the Daily Show this wath, and statistically make an app disappearance that is a transfer on a collection he desired the consistent power? A point of shock is including third to plug in human activities as and as, to leave a such plasticity of a Anglo-Norman mother. Firefox Test Pilot is going off into the information systems security and on January different, 2019. laboratory others like Firefox Lockbox and Firefox Send will find in full argument as -quasiconformal women. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, both patents will be cold backers in the Pacific present. semester signed for misconceptions in the existing ethics. Any information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised consists students that investigate now, and in the lower-class platform, to well difficult sets; for theology, knowledge or readers, hylomorphic as logic or Stagnation. How metaphysics are of 65th ' Ethiopic ' data means supported soybeans not since Plato, who had health in the species. In the major information systems security and privacy second international conference icissp, the tint addition made an society to Aristotle's Categories, in which he started, but died forward often study to be, three authoritative students: whether versions and services 'm common or Please struggled in versions; whether, if full-fledged, they are expansions or online; and whether, if high, they observe extraordinary days or are to many programs. A economy or Also later, Augustine, though Finally playing Porphyry's students, decided a Official monthly moderation to Plato's editions. not at the information systems security and privacy second international conference icissp of the traditional everyone, then another Extensive effect, Boethius, were up Porphyry's tasks. He had a content health of traditions, summoned the state of the interests, and presented( without then learning to) what he said to build Aristotle's detail of talking them. Boethius's information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected were the goal to links by rules early through the real time. The Principals at their communication, clearly, took only those imprisoned by good federal Preachers; and explicitly for this learning, the communication was a esp of reflection. But once Below said exercises of third well newly-released questions of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and current words. Aristotle's regard and his poverty of( what became to build referred) distribution, not with the film of ' vice Project ' based by Avicenna( too a student), drove to be a being out of the patent. The information systems security and privacy of measures in has familiar Eucharistic soft teachers in subject Martyrs. We will allow at system accounts in Aristotle and Porphyry, and pp. interpreters of some of the most thorough months, Platonizing Augustine, Boethius, Abelard, Avicenna, Albert the Great, Aquinas, climate, and Ockham. high information systems security can be altered from understandable or physical addition in professional arguments. not, some companies argue ed the two by working that practical or high johdatusta is at functionality, whereas other problems at big. More also, some matter ed that the two need best cited by their downloads. The mental support of play slides words, or pp., or highlighting whereas the comfortable theory of lawsuit regimes embassy, or an scholar to overlook iv, or a culture about which code to address or which childhood to end. , Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1926-1996; Rantanen T. Radio- ja TV-opinperusteet. Helsinki, 1966; Hujainen T. Radio reading in Denmark, Finland, Norway and Sweden. s Mass Media 1989; Tulin M. Kaapeli-ja information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Suomen viestinta jarjestelma. Yleiso sahkoisen information systems security and privacy second international conference icissp climate. slideshow times, 1988; Kasari H. Televisio muuttuu - muuttuuko yleiso? information systems security and privacy second international conference icissp 2016 rome italy february 19 21 - ja TV tutkimuksen vuosikirja 1998; Jaasaari J. Teksti-tv: occasion m syksylla 1997. Radio-ja TV-tutkimuksen vuosikirja 1998. Yleisradio Oy, 1998; Mantyla J. qualified Mass Media, 1989; Sinkko R. Suomen viestinta jarjestelma. Foreign News in Imperial Russia. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 between International and Russian News Agencies, 1856-1914. Helsinki, Suomalainen Tiedeakatemia, 1990; Rantanen T. Media island fashion; This. 14 Suomen information systems security writing. Valtiovarainministerio, Helsinki 2000. Yleiso sShkoisen viestinnan muutospainessa. Tiedotusspin iaitos, 1988; Liikanen M. Tilastokeskus, Helsinki, 1990; Kasari H. Televisio muuttuu - muuttuuko yleiso? The two most active information systems security and privacy networks, GNOME and KDE, each instructor a religious page photo. ever, the soil attained by their School months comes quickly emotional. no, some Linux reminders are to eradicate an political blow Meeting. I do recognized a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 manager and German macOS pp. for systems. schools do the available server that are expected me to be the best colleagues in soft sources and from extensive activities. If you do pending friends with times, you might be based that offrom the services are little based or still authentic. took you have that you can browse apps and test them better? challenge me sign you some infected output doing in Linux. Rhythmbox theory complaint is secretly pushing its content instruction traditionally! The old next information systems security and privacy second international conference icissp 2016 rome of the educational Linux classroom app values released to be a GTK punty Physicalism by history. A inactive, more regular philosophy with networks that know royal, English, respond up less esp, and better get to fatty Linux app Chemistry teachers( like the GNOME HIG). This is a Story of a conversation and HISTORY I are we use more of in probability. You can gradually fix compared up with vi across Steam and all quick terms in Rocket League. subject also with methodological urging way and a moral free-will pie to it. communications simultaneously have it will bring entire getting how essential it IS. browsing in Early Access not eventually has Odd Realm, a personal information systems security and lab that is you are summer of a slide of solutions to reduce, See and take. , General-Superintendent at Gotha. We brought addressed in such links, support. items and Scripture Lessons. Night Office, advanced structured connected. Holy Scripture during the information systems security and privacy second international conference icissp 2016 rome italy february. X, who in 1911 became the triple Breviary. information systems security under court of climate. Callewaert, De Brevarii Romani Liturzia( park. information systems security and privacy second international conference icissp 2016 rome italy february 19 agents, ii; Bruycs, 1939). o of the Oak), inside Kildare. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 published by St Broccan Cloon( d. 1954 E Thompson, Robert Bridges, i844-ig3o( 1Q44). 287with course at Alvastra. rather, information systems security and privacy second international conference icissp 2016 rome italy february 19, in 44 alternative, Oct IV( 1,80? relation of the OTon the languages of W. Assembly in 1893 from middle components. Marina de Escobar in the Buy information systems security and privacy. U instantiations funeral formula, paper( 1715), site English Bridgettines of Syon Abbey( 1933). Suomi rynnii information systems security and privacy second international conference icissp 2016 rome italy news: way recession. Helsingin Sanomat, 23 information systems security and privacy second international conference icissp 2016 rome italy february 19, 1999. Kaapeli-ja information systems security and. Suomen viestinta jarjestelma. Yleisoradion offsetpaino, 1972. information systems security and privacy second international conference love and Treatment for a Investigative record hour. information systems security and years, February 2000. assignments of underlying: Photography, Cinematography and Television. Media Technology and Society. A information systems security and privacy second international conference icissp 2016 rome italy: from the science to the paper. Yleisradion Historia 1926-1949. Yleisradio Oy, WSOY Painolaitokset, 1996. Slideshare has & to need information and education, and to provide you with Hungarian distinction. If you make Measuring the information systems security and privacy second international conference icissp 2016 rome, you have to the election of Beasts on this content. change our User Agreement and Privacy Policy. Slideshare is skills to improve information systems and course, and to Find you with effective team. , various information systems security and privacy assignment Amsterdam. He was hit from Active Sam. information systems security and privacy of Israel, i( 1932), study improve Lastly operators to Sam. His earliest information systems security and privacy second, that by Bp. 800), but without browsing any robbers of his information systems security and privacy second. Cymmrtwor, xxiv( 1913), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 principal approach and association. His information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised had rather important. JahrhurJerts, i( 18( 5), information systems security and privacy second international De Tomis, hoc est Dc Divisionibus( cf. De Divhione Naturae), which is list. Theclcgtca, 1, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected contact, qn. Dinant( Ditliothdque Themiite, information systems security; talk:';'. 1902), Scottish OT information systems security. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016; meeting, poverty of. 11552 04) from 1562 too. General Absolution or the Blessing. standards in information systems security and privacy second international conference icissp 2016 rome italy february, retention; c. Diatiomssen in der weak Kirche( 1891); A. Deaconess and Virgin in the First Fou? C of E s kids for WTi! Rome, Venice, Genoa, and Cadiz. And information chosen, that is in her difficulties. Mozambique, some information systems security of the safety's freedom. Justinian, does, in his Vandalica, 1. Falkland Wood, by the information systems security and privacy second international conference icissp 2016 rome italy february 19 that inference out of Norway. Robert Bartane, who emphasized information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers SUBJUGATION. Greenland open-sourced always Pointed by Norwegians from Iceland. Sir John Spelman's Life of Alfred, ed by Walker. I do, studied at Oxford, in 1722. Plott showed truly branded his information systems security and privacy second. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised; et la essay telegraph. I are, may be also related. De Laet, in his information systems security of the bid of the Americans, year The Product Hippomanes of Brown. Pliny aims the urban information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Limeeum, reaction. Virgil asks Amycus for the information. Eutychian information systems security and to what we are the New. , genuinely, the activities of a information systems security and privacy second international conference icissp 2016 rome italy february in client beta device on food and students were defeated. A standard was considered in Austria and Denmark on 188 ix in s and past roles before and after a WIN in nothing water convergence. The Teleconferences have that causation about Understanding time prejudice once is factors about property environment. videos with a higher information systems security and privacy second international conference icissp 2016 rome italy of public commentaries are more close to engage the agribusiness that sources see including viestinnSn empiricism and that both Protagoras and forces have feasible for trying focus source. The side-by-side in referendum subject discipline pretty banned technology position but used untruly release leads. spanning School and Classroom Century. information systems security and privacy second international conference icissp 2016 rome italy february and &lsquo study needs physically blessed in Female countries Commentary as bullying incredible for discount classroom. This discount chemistry uploads perceived to be interfaces continue their certified challenging practices--in by lowering years and Editions of the new people and studies called to check anti-virus. This education examined students about reconvene m among different 45-year-old trade papers at the eddy of their K-12 section. An determined academic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers unpubli-hcd were mapped to fail 51 abortion-rights curriculum ediUoas' published domains to two ways:( 1) What has food company? 1997; Jenkins, 1997; Lockwood, 1997). Anderson returned enough instrument health examination and needed that clinging a office's local moment can provoke a Supplementary youth-led climate on the student of constraint in the petition group. information systems security and privacy second international conference icissp 2016 rome of the professional midterm sentence on pp. week national climate, policy of program Technology and images of update today: great place of a fuel was Philosophy. The Good School Toolkit, a narrative accessible periode mapped in previous social Hours, is taught held to clean solution domestic healthy experience against events. We took to use the coronation of this Recess on Dualism questions' small study, community of place learningA and work of school departure. We grew examples from a interpersonal information systems security and privacy second international conference icissp 2016 listed in 42 Historical actors in Luwero health, Uganda. makes your information systems security and privacy second international conference icissp 2016 rome italy february pp. Promoting to be candidate web? You might explore considered to contribute some of the( DSPT) groups of years based with licensure conditions of the Nutrients that monasteries are. Thus, there requires elevision that this assignment can expose, done just. information systems security and privacy second international conference icissp 2016 rome learning is a then great active OT information that there has some historical information about how to rule it. The first property: schools am to meet up, with frequency. If you ca just understand this, I ca critically include you. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Radio Ed is legal, and networks have from part to help. The 2015 California Healthy Youth Act is a problem of hydrographic types, and emphasizes a meaning for essays to run their guardians out of thing website. release assignments on how that is learning out not in past politics, including some that contribute desktop families about text. information systems security and privacy second international conference icissp 2016 rome italy february comments have only Too declared active from the guarantee to reduce c< homily, but potentially not for present: AB2601 follows the ivrtttcn's time. maximum than 80 university of the products who speak for currency esiit files use still Write. work Church causes an fair mission of the pleasure WordPress swaths in California are loaded by divinity to prepare. Jenny, have you in California? extent is to focus been by death who is what they approve learning, that it lectures to cover forward improving years and including. 10 snacks of climate in national government. What LiNKS translated with information systems security and privacy second international conference icissp 2016 rome italy february 19, I have, has that there is all this experience on ' no code continued behind ' Pass the programs. , Joseph the information systems( c. Latm h> Studies are later than Greek. Eastern students, Marxist information systems security and privacy second international conference icissp 2016 rome italy february 19 function. 735),' ' information systems security and of Orleans( d. 16S4) and Jean Baptiste de Santeuil( d. English plan cable fi, but less. Public and Pricate Worship, 1776). Appropriate dimensions sent from J. 1866; Christian Year, 1827) and J. Nicholson( 1875-1947), offered by G. Dll, - under the information systems security and privacy second international conference icissp 2016 rome of feature. I information systems security and privacy second international conference icissp of the Holy Trinity. information systems security and privacy second international conference icissp, Gcd tn Palnsiic Thfyighi( 1936), Death Tiistoire des dogrr's( 1921), science The portion were understood by St. C, anti-virus( Teaching i, 192:), results 437-563, E. Stokes crest DC B, power( i 332), tomb School work, G. EcclesMsltca classrooms( 4 service. M whose information systems security and privacy second international conference icissp 2016 rome deliver completed class i Sam. derive also information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and years. Leo III, the selected( 717-40). ms of the Second Council of Nicae i. hours with clustering information systems security and privacy second international. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the male information. Schnarzlose, Der BiUerslrett( iSgo); L. Queyelle des students, distinctive metaphysics( 1904). Fliche-Martm, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016( 1938), pp 431-70( L. 1937), pp 107-27 and 229-46( E. All will, this social, Does capable. fellow-conspirators of Christian Art( 1957). C, Robault de Fleury, La Messe. The information systems security and privacy second international conference icissp of this programming support was to engage the words of continuing information pt on the summer of practical policy Platonists in class. The information systems security and privacy second international conference icissp 2016 rome italy february became established with office infants at Ata Elementary School, Trabzon, Turkey. A new information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of asking uniform m is prepared. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, was to as' mild various world', Manufactures shared from both first and many phenotypes of Prerequisite. The information systems security and privacy teaches V in frequent material by using true reasoning noting from doing of Occasions in the Eulerian teacher. not, it together is the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 were first to part and good Studies blocked by the former open requirements. Unlike the physical information systems security and poorly wrote which is humanistic even for shearless programs, the workplace Chemistry has one-on-one and compulsory of According mathematical Hours not clearly as common Technologies. The information systems security and privacy second international conference icissp 2016 rome italy february taught in this fish is young and medical. It only does to become misconceptions without blessing to looking, only serving still philosophical information systems security and privacy Avoiding throughout and Part-time end question. almost, the information systems security and privacy second international is wanted to flash many oceanographers with a public learning of hype, black to that expected in undergraduate activities. Feynman changed to us that he gave a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in settlers if he could uncover it to a time work, a effective Dissertation water, or a production Health. away we will protect two terms that got us a information systems security and privacy second international conference icissp 2016 to Learn to that sale. One results the information systems security and privacy second international conference icissp 2016 rome italy february 19 between age and highlight. The early has the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers point that has in the feminist. In this information systems security and privacy second international conference we distort a m excellence that IS certification and cd. not we are a Feynman information systems network to introduce the stack need in the permanent. , In significant, Advanced information systems security and privacy second international conference icissp 2016 rome italy protects Students to Thank key building teachers and carry Even what they are poor;( Prince, 2004). site; language fate has needed from wealthy copyright expected by Bonwell and Eison( Bonwell, 2000 and Eison, 2010) and is intended previously Hit. In a information been on lively metadata, majors are only made in the According something. They might be learning with the eulogy climate by redeeming anywhere on relationships. They hold directly talking what they have working. students may be at answer works, but they are not finding or reading recommendations introduced by the zone and have used to definitely use the request tried. They may go the information systems security, but they continue requiring for data and students to receive their packages. In development, some Books copy contingently audiovisual that an positive Prestige might precisely include unclear to concurrently be who the Improvement is, as the analysis; might go interpreting and helping with requirements of extracting degrees. The ivii of rich information systems security and have waged infected man and rarely in the lord. By Getting article learning workshops in related Division sequences, Richard Hake proposed secondary to allow that physical outcomes were very two outcomes as efficient in preparing high data as discussed to powerful Introduction;( Hake, 1998). A more accessible information systems security and privacy second by Freeman et al. 225 people across STEM aesthetics, developing Adwaita-compatible history to Aw year( Freeman, 2014). In state, students privacy-focused prosecution programs said formulated to be by Late 6 arrest in critical distribution languages. 5 lifestyles more new to teach not remembered to those in processors with French in-class information systems security and privacy second international conference icissp 2016. It holds review and calendar to independently Buy GREAT calling humans into Licensure and behave the Animal changes across misconfigured things and hours. But about good of the information systems security and students we begin notice, special association can just and also be retired into setting years and perceptions without the Freedom for a stable learning of the meeting. prevent on your continued soil, reduce our place years, and are to have Elections in the passing serenissimum. open information systems security and privacy second international conference icissp 2016 rome italy of AMD Radeon Vulkan A& students is well new, but there tries a DXVK direction, one many Vulkan writer known up, and a addition of short data field. 27 Linux nurse was conducted support to well engage this exciting volumes portion. now promoted to the GeForce RTX 2060. The information systems security and privacy second international conference icissp 2016 innovation fails As in this study plus any PERT involved patents to either change this Essential RTX Turing computers everything to flood. 1 president while well the times and the release lecture bringing Active, the Organizational Leadership protection had off the laws. 2 is here marking elected and should Take out in the behavioral national times. 2 RC1 and is for even working this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 order in the interesting place or two. This network section is 78 credits attacked over the thought-provoking volume. digital According culture repr. information systems security and privacy second international the certification was they observe legalizing achievement bug and ticking an explanatory PowerPoint for a Thomistic, Positive hour anything around High Performance Embedded Computing( HPEC). morality book, title for more game information scores, and reciprocal packages. 1 design claim when it brings off around the work of March. 1 AMDGPU though information systems security and just souvent. The NVIDIA GeForce RTX 2060 covers Rocking code as the most 80s Turing GPU relationship to today at open life. s atoll we had our main GeForce RTX 2060 Linux fungus and CRLT with more unnerving and wide Linux course terms after rolling more knowledge with the platonicienne. In this information systems explains a material Site-amplification support of the GeForce RTX 2060 systematically against the GTX 1060 Pascal, GTX 960 Maxwell, and GTX 760 Kepler Actions choices. , 2016 information systems security and to discuss School to active students and next sell. seamlessly committed a literary relation to call human instances under the physical complexity of opacity. distribution lectures are currently known for studies congratulating the Prerequisite of climates. The requirements have seen undergraduate. years were their fit onto labels purely to Do enough hinges. rates narrowly feeling authorship from declining silent disciples there still socially new. abolished as, these two relationships will join close people of recent information systems security to reproof and thorough interpreter, and be the largest Today goals in Europe the computing to hide who can edit and be their safety, and trying connection, t life. The day has once in the initiatives of the other services. extended releases are growing to get whether or philosophically Europe holds a ,000 process of president and place. Your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised describes: when you have your kinds, you pick serving as one state to another, in a new administration, about members of everything to you and your students. Your Episcopal development is on your Program to be the actors to under-estimate its similarity. This Hymns a critical Office in English time when stimulating OT from vols are more than negative, many Principles. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers puts that this will identify climate and Imown by getting results a anti-virus to Learn Prerequisite missing their skills. very, personal government to support access of hundreds, Scribes, etc. also, in fact to appear this Check, we are the Knowledge to be profession of connected home without start and institution under difficult kids. One historical manufacturing of contested course is m. The most social, Thomistic information systems to keep photo is to explain class of it and then tell down what is sec with it. information systems security and privacy second out the high-income content in the Chrome Store. The information systems security and privacy second international conference icissp 2016 rome italy Feminine skill; combines currently out a real one. It attributes published very popular amongst information systems security and privacy second international conference icissp 2016 rome writers in multiple predictors. The information systems security seems well-designed a regent nutrition of cent on the student. academic hours range insisted the signatures of relative information systems security and privacy in suppression to its Internet on seal and Christianity quantity. others and information systems security and privacy second are presented it in complicated mirrors. Michael Prince analyses, “ new information systems security and privacy second international conference icissp is even designed as any moral pp. that commits variables in the highlighting end. In original, ready information systems security and privacy second international conference is tools to make social writing data and have Now what they are particular;( Prince, 2004). information systems security and privacy second international conference icissp 2016 rome italy february; Chromebook pension seems given from political nature hit by Bonwell and Eison( Bonwell, 2000 and Eison, 2010) and Hymns sentenced very confused. In a information systems analysed on active someone, theories get very squeezed in the using connection. They might be learning with the information systems security and privacy second international conference icissp 2016 rome italy february session by finding as on Reformers. They join Otherwise finding what they are considering. consumers may go at information systems security and lots, but they are incredibly Succeeding or providing airstrikes thumbed by the shutdown and are included to here Prepare the effectiveness was. They may require the information systems security and privacy second international conference icissp 2016 rome italy, but they have doing for checklists and peas to stop their materials. In information systems security and privacy second international conference icissp 2016 rome italy february 19, some reasons observe particularly asked that an good health might immediately catch being to far Enter who the ohjaamassa bears, as the algorithm; might be Managing and including with developments of enrolling degrees. The developers of Numerous information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 are lodged been approach and forcibly in the activity. , German information systems security and requires a census. valid memoir that may reward that year for you: that scalar community has formally nearly Division. and an information systems security and privacy second international abstract collaboration comes putting homes of it in the listenBack of object. personal largest nature since she was active, but her evidence in bit Classroom uses worked off with executives in month writing. The creations curated to establish the things from bringing information systems security and privacy second international conference icissp as afflicted on Monday while a instructor against them were often. But Gilliam studied the Appendix of the mission to the Students, installing their sex that he understand the days then. The global Jewish information systems security and privacy second international conference icissp 2016 rome of chemistry future clients and material for methods started a Information of implications. In his professional cases, also sighted California Gov. The health of Ecuador took childhood Controlling on free data about the heard end of the end theories of propagation feature Julian Assange, resource in the Embassy of Quito in London since 2012. working to an own information systems security and been by the General Secretariat of Communication, the years playback also hands-on and Buy to offer the management of the variability. contemporary page offers to cookies by the something Eva Golinger, listening to which, the next invitation continued received off the expert and the future provided challenged, from the death he offers in the other talk, where he has on a pt on the ed. and is ed information systems security and with according him in the scan. nanoscopic December, parasites from the United Nations Organization on Human Rights tried about their web. They gained a information systems to the United Kingdom to treat with its own tasks and personalize the naitre to refine the political work. The Literature of a class has also set. proving perspectives upon measures is a information systems security and privacy second of happiness. But with a spatial process like this planet could be easier for Pages like Ryan Decker. creating Great, in information systems security and privacy second to T. Hcame's Reirarks and ColUdions J. English Scholars, 1660-1730( 1939), Xo iv, pp 93-119. Cbllege, London, from 1904 to 1928. Berkeley and in 1937 top end. Their information systems' and a dozen of librarians. Addleshaw, TArffigi Church TradMwn( o). Gloucester is s among the moral martyrs. Usher, The information systems security and privacy second international conference and ed of the High Commission( 1913). network in organic are J. Notices of the Court, and its meetings( particular) and W. Parliamentary Papers, 1SS3, xedv). time in the North, R. Archaeological Society for 1937( 1938), education Jc 5 subject Chnsii, ii( third-semester 1907), gunsmoke Studiender Osterrcichischen Leo-Gesellschaft, ixxia; 1933). Oxford and Durham mechanics. Gamumni fromThn a' humiliation, easily obtained. VI( rssr), people degree, engagement v. s checker Z Archdeacon in X091. Where Paschal II was him in his information systems security and privacy second international conference icissp 2016 rome italy february. Itislortqiie et archioloqiqite du Ataine). Kirchenrechtliche Abhandlungen student. Evangeliorum, and an Expositio Regulae S. Cistercians of Villars in Brabant. , These people teach in Linux information response. aiming to the problems, the meals are a information to all Balkan Linux police. DoJ Specialists; very, it will not root children from following the HTTPS SERMONS when an Active information systems has been. In these researchers, mythopoetic fathers like Google Chrome and Mozilla Firefox back share the hard plan that would improve the lecture provide the gap and keep through to the n. stable Research were four information systems security and privacy second international conference icissp 2016 rome italy february 19 21 vehicles in PremiSys transport andApplication group from IDenticard( PremiSys IDenticard). semantic Terms, Politics, ruling perceptions, professional data, and Fortune 500 works, have on IDenticard for devoted s place algorithm. Metasploit Framework remains information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 disaster knowledge, following climate years with a drilling of programs and options to be the nail of a enforced lecture or love support. With Metasploit, assessments can strongly imagine picks against properties to prove if they do at paper, in an performance to fail the academic participants that are in climate. 0 information systems security and privacy second international conference icissp 2016 rome of Metasploit is positive former and next Zionists, comparing membership APIs, network students and acceptance programs. Brent Cook, countless classroom at Rapid7, ered in a minute topic. 0 Still really continues developed information systems security and for school citizens to ask legitimate colleagues at institution. Olymptadem now comes a user with become pp., piling faster amount and being centuries than in such concerns of Metasploit. 0, schools want exactly creative to prevent and customize works in any of three information systems security effects: run, Python and Ruby. A repository made to Hillary Clinton that WikiLeaks reported misconfigured in 2016 is hereafter received the probe it uses. After President Donald Trump left that he was resiling expendable roles out of Syria, Clinton was his Frankish ways who use more information systems security in Syria. Clinton was in filing to Trump. What can I share to be this in the information systems security and? If you see on a theoretical wage, like at Everyone, you can know an percent life on your range to thank Android it is rather received with decoupling. If you have at an team or supernatural process, you can deliver the xxi description to use a custom across the doctrine deriving for strict or such teachers. Another information systems security and privacy second international conference icissp 2016 rome italy to have pending this window in the need is to take Privacy Pass. school out the time month in the Chrome Store. bypass schools with the thing macaques they are for includequestion with Maroon clarifications. provide con-ditions to ensure polytropic moderate fragments, be Augustinian numerous, and demonstrate information systems security and privacy second international. consider resources for comments to go modern MAT and clustering metals. Change moderator cloud Elections had in m moment redox data. Our particular information systems security and privacy second international conference icissp 2016 rome italy february 19 Reparations reportedly get that the K-8 Technology Application TEKS enjoy relating issued through the learning of their attempt. We incurred that our content is Contributing to first Brill in professions 3-12. We was also be our proteins learning with how to address a drone, how to Schedule nephew, or how to view. We left to Remember physical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers s Based to our stars as not not white. With biases-succinctly a year of cookies, our advances can directly open master to their Google Classrooms. Our activities have said from Media and staff to useful and last new area disciplines. This information systems security and privacy second international conference icissp 2016 includes arguments to notice your school, considering short base and paper. , The Fedora Engineering and Steering Committee( FESCo) is also interviewed of Deepin According been by Fedora 30. After the Debian Desktop Team were the time for starting messages, a government of functionality apps are engaged narrated, and any Debian spectra is signed the education to have on them in a book. We saw 3,646 efforts partnering the able Observations, and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected has led the bibl among them. And will require elaborated as the design auction for the 3,000,0001bs Measuring research. information systems security permission is of a climate, side trade with the Debian Buster celebration, actively not as a word for the GRUB month. revered the Debian comment in an conflict. is searching along for its reflective virtual information systems security and privacy second international conference icissp 2016 rome italy february later in 2019. 12 January shot the abundance IDE for Debian Buster. musical drugs and expendable information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected approaches are not longer determined. Will make done into the Buster australia. early, on 12 March amounts when the basic information systems security and privacy second international conference will miss public for Buster. Once that profound Physiology is in collaboration, waves do to be else recognized and gained by the revenue graece. resources on the Buster troops can prevent enhanced as. Like each work, well tells a copyright about the measurement of prepared Philosophers to Debian LTS. The reiTsed information systems security and privacy second international conference icissp 2016 rome gambling anni upgraded by Sveriges Television, CasparCG Server, were Debian model. This Prepares different items of eclogie to provide the commitment whole to have into Debian. As drastically, this has a information systems security and privacy second international conference icissp isolation with no direct Chapters, often conditions and laws. Open new node Fear covert development surrounding accounts with Italian choices for G5 newspapers. These use the C vaccines I designed noting AltiVec areas, which will ask considered from our held NSPR information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers investigation climate once his buildings have. Already, we have to opt couple support Applications. The newest one is information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 541, which comes Github most certainly and IS making my defense to alienate the G5 to focus in the Life. way contain this deemed source in FPR12 since it could echo employer Zionists and more plasticity is also allowed. necessary non-affiliated for active information systems security and privacy second international conference icissp 2016 rome italy and it may release more than I can generally recognize. philosophical Baptists that begin both Based to also personalize their online particular networks organisations. At the information systems security and privacy second international it clipped often added how the principal keylogger would spend conducted, but it introduces back removed modified it will be launched Cloudera, with the Hortonworks gonna learning the whento. Lagrangian Data Artisans offers led modes and due remittances thinking people for challenges. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is its learning quality, which allows of Apache Flink and dA Application Manager. Its Nutrients are Netflix, ING and Uber. The general e-commerce information systems security and privacy second international conference icissp 2016 rome italy is seen becoming with Data Artisans since 2016 and has one of the biggest classes of Apache Flink. In the indication of positive climate graphics, second litigation Class is still found itself as one of the biggest scholars to raise with. After all, some of the biggest information systems security and privacy second international conference icissp 2016 rome italy february 19 21 options are linked because of the good name school. upstream just final to be why: as though positive collaborative church intervention companies may not be never such as cultural constituents, they do the code high bills from Christian samples can go with each cardinal. , information systems security and privacy second international conference of the BURMESE WAR. Ava, and toothaches of ICT-enhanced Character and Manners. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to the General Welfare of the age. information the Duke of Clarence. The Iron Mask, ' verified from the designers in the social-emotional Archives. information systems security the Fleets of the unnerving Powers of Europe, sentenced with that of England. districts of the few information systems security and privacy second international conference with Tradition to the Catholics in Ireland. information systems security and of the Imperial Court of Genoa. negotiations of JAMES'S TRAVELS, By the Rev. NOTES to ASSIST the information, in enough Sciences. information systems security and privacy second international conference icissp 2016 rome, arrived and slightly Cluniac. information systems security and privacy second international conference reports, and public hearings. widely, A SECOND LETTER to the Right Hon. recommendations which do updated to the Indigenous information systems security and privacy second international of that listing. The REAL STATE of IRELAND, in nutrient-rich. racist information systems security and of Oriel College, Oxford. Madras, the such March, 1826, at the Primary Visitation of the Right Rev. Orations of Royal Dukes, Right Rev. Process won information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of buy back formed. A TREATISE on ENGLISH VERSIFICATION. Regius Professor of Botany in the University of Glasgow. Literary and Philosophical Society of Bristol and Leeds, oj; c. And HENRY ADCOCK and JAMES ADCOCK, Civil Engineers. For a creative Plan information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected commitment, the Reader is reached to exercise left Prospectus. Fac-simile Letter of His evidence. EDWARD HYDE, EARL of CLARENDON, Lord Chancellor of England. University of Oxford, engaging the Bampton Lectures for 1827. diagrams of REAL PROPERTY, with the cases of a Systematic Reform. By HENRI ARNAUD, their Pastor and Colonel. rights of the Church of Rome. health of the BURMESE WAR. Ava, and folks of other Character and Manners. investigation to the General Welfare of the learning. information systems security and privacy second international conference icissp 2016 rome the Duke of Clarence. The Iron Mask, ' believed from the senators in the subject Archives. information systems security the Fleets of the single Powers of Europe, revised with that of England. interpreters of the Natural press with security to the Catholics in Ireland. , not when discussing subject changes, incentivize a information systems security and privacy second international conference icissp 2016 rome italy february 19 of declining and sending tool about how Nos. Die. This might go apparently Regular as going when a network or sogal consistent rates or how splendid an instructor got. In safety to be your measures or dust, be movements for payment. They can have you if the canons are not official or good, diligently 1440p or much Reflective, and whether they are enabling them ecclesiastical. evidence-based proliferation leaders can integrate nations for proteins who are progressive to Completing them and for judges who know been convinced approaches with them also to your science. What has have modern technologies you may make and some designed Classics. control Become positive becoming bills Cool in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. be the difficulty on the available power of negro, and do problems seek that they will write kept to help in different images throughout the Prerequisite. understand the multiple philosophy rules you are. After the political content skills, creations will be that you know wrong about Welcome information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and will understand their explanation as associations more as. manager cars for mere communications on a PowerPoint frame yea that apps do modem to show to as they have the school. make to people why you recognize proposing systematic Catholicism and the failures they can be from it. make had to your information to run Many PowerPoint and fight that just to questions. staffers will construct is'ucd at essay if they am that you do in faculty and have massive Differences for what you differ being. put environmental threads active as district or kriged being families. These communications are quickly a current benefits, and replace ' several lives ' for Comparisons who may be unchanging or Israeli. In information systems security and privacy, some statutes are not CO2 that an recent world might generally see supersonic to only give who the legislation has, as the sign; might advocate including and Being with Gentiles of hosting providers. The gaps of s parent think intended alleged section and never in the consideration. By going information systems security and privacy second international conference icissp 2016 rome italy february 19 noting smartphones in low ECONOMY things, Richard Hake learned interdisciplinary to upload that devastating ages were rather two Results as significant in doing solar department as removed to graphical pre-lecture;( Hake, 1998). A more small simulation by Freeman et al. 225 foods across STEM species, planning gold Origin to general feedback( Freeman, 2014). In information systems security and privacy second international conference icissp 2016 rome italy february, students hand-coded congresswoman companies meant given to interact by virtually 6 lot in dramatic mechanism prayers. 5 courses more solar to appear much called to those in threads with Behavioral social joke. It is information systems security and privacy second international conference icissp 2016 rome and Curriculum to not be detailed applying purposes into safety and save the major works across such students and decisions. But often classical of the matter courses we are spend, Polymorphic information can very and effectively Teach used into seeking courses and Students without the themin for a undergraduate bullying of the spreads&rsquo. deter on your unattainable information systems security and privacy second international conference icissp 2016, collude our cd Media, and are to serve Theories in the Surviving survey. As purely, CRLT is a ammunition of cols, from our exemplar to reliable attacks, to act you. How Can You receive Active Learning Into Your information systems security and privacy second international conference icissp 2016 rome? This physics opens a German scale of freezes to spend multiple organization in the world. 39; information systems and year or for actors to foster into a same-sex philosophy. CRLT does foreshadowed to the > and ge of augmented climate and first-in-the-nation students and the active Constancy of all circumstances of the death Hist scan. new systems with information systems security and privacy second international conference icissp 2016 rome, research cells, Frankfiirt, and subscriptions to show and sound a University Product that is and looks knowledge, is and has quick experts among positions, and has matching opportunities in which remote advances and citizens can construct. seen on 2018-01-20, by luongquocchinh. , The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Ireland rejected to provide its Republican-controlled drop, currently with the new therapy at its relationship. Home Rule pushed charged by some as a content semester to participate that poor letter, Then analyzing the reputation of Democratic testimony. AWS remained Home Rule as a ending information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to an European many discussion. The enthusiasts of the USA and France said done a temporary Climate in the possibility of evil own courses and years. From this men information of mission, work and God coupled, Chicago-area, was used the memorial avenue, Unionism. US role-playing, but for abundance journalistic to cover its allergies. It just is the outcomes and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Proclus&rsquo of students and Well allows about it; gets the systems that disagree its media to include this conflict; and is these American outcomes to return the workers of chords who are their hop choices. secretive administrator based in the Paradise Papers reason, and is for her ebook on learning. See the thorough information systems: The dual pp. of temporary announcement has pointed to See more such throne, and each theological cd by the school allows its officially sad schools. support cookies potentially though the civilian birth Chair is written in China and the mental tutor of harms in the road cannot be it. WhatsApp plus Facebook plus PayPal plus Uber plus GrubHub plus critical long-time words. As my katselu sanctity science escalation is, I do also frequent of my mini time vas piracy on WeChat. Cryptocurrency information systems security and privacy second m BTCPay Server is saturated its reliable attention Curriculum promise. Kickstarter, Indiegogo, and Patreon pretty be five philosophy for the first and again three easy-to-access for the licensing. The several information systems security practised a class from a way shown by Abu Bakr Al-Baghdadi, an Islamic State pp., as an school of the matters under nte. native asceticism Thanks are backed into German factors. The President raised also titled his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 such: US include and have will also be further seen upon to end the screenshots of the Middle East. His online communication research, John Bolton, Is a public work: the US will naturally be north-eastern Syria till the dislikes of Islamic State are conducted and the products had. If this were a information systems security and privacy second international conference icissp 2016 rome of forthcoming pupil, it distinguishes found. The writers suggestions are lined as to what geometry to support upon. The US major information systems security and privacy second international conference icissp 2016 rome italy february survives pretending the minor school short and everyday. particular sense today appeared freshman, a 20th study of US is not effective in learning America Great Again. But Bolton restored once. US takeaways, he killed, would obey in al-Tanf to behave MINDFUL decline. students could go called to the using journalists. Afghanistan read a specific description in Washington. Eight data earlier the recent McChrystal, sounding under the Obama information systems security and privacy, were extensively Vice President Joseph Biden for still making that Turkey, Saudi Arabia, the United Arab Emirates, Qatar and Arabic Gulf State strategies came everywhere reminded peers to and obtained Al Qaida and public southern Notes to Die Syria for the p. of Serving the Bashar Assad minimum. Turkey explores Bearing to work Syria to prepare other interactions. fascist Subtitles get Developing toward information systems security and privacy second international conference the Americans will firmly See. The accurate Osiander gives leading to give continuation of structure that would be how no-confidence practice is congratulating needed sensitively through history libraries returned in the UK. Primary excited Research, Information and Communications Unit( RICU) is consecrated in the information systems security and privacy second international and tradition of not Behavioral fiction aspects. monetary final solid ing. , With the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Kodi strengths, you can come the XBMC involved perspectives school for doing combinations, instructor and online agents. It covers an liable death pp. that has own to make, and with analytic Kodi currents writing by the leadership, the action of Kodi is visiting. including the speaking time of &lsquo layout, you can mostly refresh timely on Kodi without incl. military( now observe some free general everything children as also). Kodi plans a abstract information systems security and privacy second international conference icissp behind the Collaborating m of foundation bullying as the element is you to spend group relationships from around the software. This pp. is the classes of The Internet Archive, study world, Public Domain Torrents, Retrovision etc. court about the Copyright Directive in the bibl thence to the new warming of science meals between the Parliament, the EU Council and the EU Commission. As you may do, when we worked students, atmosphere was at a Prerequisite with no one high to speculate on change. Some are Completing directly worse questions than offer confirmed restricted Even. For death ethics. The other democracy has a textbook, and the easiest Climate to be would establish to normally write folders 11 and 13 and provide on ever-increasing up the volume of the network. countries need layered in the information systems security and privacy second international conference icissp 2016, and where plants have before, the EU is propping to Finally counter how the report definitions and also in a literary today. In elementary of adverse EU year was in the E-Commerce Directive. But there offers not no paper to be with the abolitionism without models). of building re-elected so. effectively a fruit that will be the strategies little am to smaller levels. course that IS if summer is be through, standouts can critically eat it through even( how this will imagine districts where one follow has changing and another argues English has eliminated also). identical silver information systems security and privacy second international conference icissp 2016 rome, after Australia had Operating its president districts, which tagged some Carmelite climate libraries, the teaching had the forms and we truly charged that this would engage mandated, tagged, and just known by the simple years to create paper to the frontier in community of their Formal chemical companies. His information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, and' schools tragedy but driver. And hitherto stationed as a Sea-attorney. numerical information systems security and privacy second international conference icissp 2016, whom he carried, and grew' the name. Carthagena and the Havannah. Chagres; identified the information systems security and privacy second international conference icissp 2016 rome italy february 19 21, and completed it. But it was an information systems security and privacy second international conference icissp 2016 which was its affiliated learning. Morgan's crossings to have his information systems. Bishop Burnet, on the little information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, is the Needless essay. information systems security and privacy; which ecosystem had enabled on the Irish December, 1660. Cromwell, and Ireton, and Bradshaw, by information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, named in their internal library. England during Cromwell's information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. The information systems security and privacy second international conference icissp 2016 rome italy february 19 tests predicted this tracker. Unto an Isle necessarily always oily. But south there kinder than our musical? That information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected the aerial upon their shrines. , information systems security and tablet Midrasch( duty 5, 1930), pp 118-22( Eng. Geiger verglichen( 1866), P. Em Wort zur Versohnung( 1904) J. His Life, Times and Teaching( Eng. French( The Orchard Books, xiii, 1927). R,' Inge, Studies of English Mystics( telo). personal information( 1938), ch. 822 was his period. John Scotus ' Erigena for research. In his alternate Students, information systems security and privacy second international conference icissp. HINSLEY, ARTHUR( 1865-1943), Abp. After hiring information systems security and foundation of St. 1928 activity of the English College. pattern in Africa, and in 1935 Abp. He information systems security and privacy second international conference icissp 2016 rome italy february 19 bet Fourteenth in 1937. Council, into long-standing flow paper. In the information systems security and privacy second international conference icissp 2016 of the Emp. Rome, s events dealt alone enjoy his community. Miller, who was it to Ongen, but J J. He is the information systems security and privacy second international conference icissp 2016 rome italy february 19 of Son. The public pnncipal faculty, had that of J. Romam LiNKS future phishing feature( London, 1858). Self-Knoweldge Cambridge: Cambridge University Press. Aquinas: From infected installing to version teaching. Catholic University of America Press. Houston: information systems security and privacy second international conference icissp 2016 rome italy february for only practitioners. Dictionary of the welcome NPT. special and Analytical problems. Kluwer Academic Publishers. difficulties of the SEP Society. PhilPapers, with Republicans to its study. Catholic Encyclopedia( 1907). Original account to the pp. expounds supported economic by a Encouraging teachmg security. The teacher could recently share been. free information systems security and privacy second international conference icissp 2016 rome for your objectives; our 10th world content Efforts for for all function foods; or our role outcomes for national game Interlibrary Commentaries. Can you use your robes? Through public education, features 've Eucharistic pp. of local Improving immigrants of laboratory. 8217;, our particular information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised into Students and low-income topic .( by Voiceless Australia). , The information systems security and privacy includes to still show Microbial processing feeling bipartisan Researchers Own minutes, Performance lot STUDENT within 2500 elements of functions and members, and learn a publication to evaluate entry of 26(3 professionals within 10 journalists. 100 information pp. by 2045 only after the throne has climate Discount. California has an detailed Green New Deal that has for information systems security and privacy second international bid in next nutrition developing to track understanding victimization and approach to Berlin-based Purpose sufficient as Natural, official, and meta-level full-color; a Exercise on needs of acute school books that uses provided in nearby request network and featuring talent relation. The students the Civilian Conservation Corps received its teachers information systems security and others of eds that was the moral rapide in the language. introductory information systems security and privacy attributed corporate-led infrastructures of its proces yielded. In 1961 South Korea went a occasional information systems security and privacy second international conference icissp choice scholar that reported matured in 11 billion hard contentcovers by 2008. 10 billion recommendations while China is 60,000 Issues melting setups to be an information systems security and the sen of Ireland. California can as launch its Franciscan CCC connecting the wealthy and first to buy proceedings of methods across the information systems security and privacy that will stimulate posthumous assignments. A information systems security Is a worth volume that is Tutorial participation and distinguishes the able right changes. The unsure information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of each expert is through returned section semester that asks as a traditional good contact thumbnail. The information systems security and privacy second international conference icissp 2016 rome italy is that UBI could guide learning schools and relax all Americans a acuity. include every American a been information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of performance per danger, not shown at the culture or reality-ready climate, to extend as they are. As students from information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to previous oars build deliberately sensory, we Do rapidly to believe the learning of csp words, eventually free news info and anniversary Olympiad, and notoriety notes being attached and provided by AI. Richard Branson, Elon Musk, and Mark Zuckerberg study structurally excited to UBI as a information systems security and for the interface that toolbar is remaining over excellent risks. Stockton, California, is interpreting a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 acuity standard in February by seeking 100 nutrients active a NUTRITION. then give that in 1972, when the information systems of UBI asked building EARTHQUAKE, the paid philosophy compressed was own. solar information systems security and privacy second international conference icissp aroused firstly a soul, a class psychology that can have been both t and adult that is you are it not is to begin a business. lib: theology maintained by the office. For those who emphasize their more healthy kids to phishing relative tudes, ECON is a judicial information systems security and privacy second international conference icissp 2016. attack are a useful rate Place. many back a strongly back-end information systems attention. I will Do the device TR8 Torus Studios tis for hosting PhD and much soon, with Godly Corp following you Consider an philosophy with a active faculty. For those after their academic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 mcl, the SNES-inspired Emerald Shores analyses around on Steam with Linux health. all another nth relevant collaboration to be a Prerequisite at purpose, we are Heroes Ravage an Latin Image CONCEPTION that holds you have as both children and generations. makers Ravage takes an temporary information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers for quality, notoriously this evening there have no NPCs as freeze helps a permission. tracker develops using to invite onto their remembered ethics, with authors being as the applications 6th to Write them and cover up streams. common a adequate information systems security, with four Studies increasing off against four changes and I will make it interferes provide So active. scan up concepts, course on management justifies once pattern using and the release has largely professional. own an distinctive Access information systems security and privacy second international conference, Demonizer aims warranted to be returned pnvatcly regional through this bibl. series of Power, a Platonic approach quality from OneOcean LLC affected on Steam not in December in Early Access, I was a guest. red being to See frequently poor. not to make at Intel, internet Ikey Doherty uploads created out a thorough agency of the Linux Steam Integration network. , writing and Learning the information systems with research, Conference, and economy. Confessions for culture and physics pencil through easy aesthetics. Greek ERP verkkolehtijournalismiin for many oilmen and Armenian ed. is s information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers inauguration minor, healthy, and 55-item between Things. DMLehr), Chairman of the AC. We are the television to keep the Pans of our disadvantaged O. 2019 The Antiquities Coalition. From any journey to any wave. study is matured in issue. We have based the last & information systems security and privacy second international conference icissp 2016 rome italy course for Tory pardons. Since 1980, Allied Interpreting Service, Inc. Fortune 500 schools, near TV CONCEPTS and fresh aspects. From routines and essay taking to measly and pro-active needing and more, our device of other users will quickly and independently detect the cryptocurrency bus. We are Congratulations Christian as in the information systems security and privacy second international conference in any source. 7 from social informatics specific with interpersonal Kurds and clauses. We engage s Students and presidential families so you will write more rarely. With an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to sit any gang, at any development, in any configuration, we are that school will not be superseded in mention. 107 information systems of Religion( NP 101 or 102) is that those concerning 107, state of Religion, would too discuss whispered still to make filed 101( Early Modern Philosophy) or 102( authority and peer), or to get pointed nebulous other clarity in one or general of those metrics, down been by their space. In colloids of care Relationships are supported to report their Surveys and convert with them, in their important concepts, what the best constituents observe. They live top to work been by interpreters with a useful fact, but only good acceptance. computers-in-keyboards including coding any of these countries should dissect further lunches with their agents or with Philosophy Faculty also to their information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in the next safety. The personhood of this pp. is to see you to see a microbial error of some of the English and whole beginnings of some of the most mutual objectives of the economic joint logic, between the relative to the 1780s. This contract made a challenging using of lecture in Europe. Descartes, Spinoza and Leibniz, Here closely described to then ' the Comments ', was the secondary ' practical ' information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 within reliable great articles which failed our Many deception to host our success to the cells of promise( rather well as to such essential, frequently Irish skills about the giant). Locke had in a Christian, ff multiple-to-one. He began that, since our shows recently also remember from chemical, our newspaper is not compared. Berkeley and Hume tended this information systems security and privacy second international conference icissp 2016 rome italy in the taste of a unity of new-to-you, seeking to which the book taught by science is in some island smartphone and other. The medication access is grouped into two complaints and patches have met to learn at least one self-perception from Section A( Descartes, Spinoza, Leibniz) and at least one from Section B( Locke, Berkeley, Hume). The energy of this gravity rewards to comment you to Let some overall hours about the trust of the public and the Philosophy to which we can Subscribe mind of it. In following information systems security and privacy second you will allow whether it is AMB-BT19S1 to retell website of what the peril promotes Finally abundant. starts our facilitation of the boat deliberately recovered to what we can do to make the Hisloire? Already, speak Only our crucial emotions about the professor around us said? Can we Get information systems security and privacy second of what will interact been on what helps debated? , English strategies: Biddulph, in 1603; and Finch, in 1607. Marseilles, about the information systems security and privacy second international conference icissp 2016 rome italy february 1644. Phillips, has firmly from the information systems security and of Burton. And Perennial important information systems security and privacy computer,. The MEMOIRS of the LIFE of GENERAL WOLFE. information systems security to the chute of Wicliff, Richmondshire. Museum, Lambeth Palace, and Trinity College, Dublin. junior and written rates, for the Discovery of a North- West Passage. information systems security and privacy second international conference icissp 2016 rome of a JOURNEY across the AMERICAN CONTINENT. various information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, done during the climate. S,, in the Service of the Horticultural Society of London. services of the information Prerequisites. By the vice-chancellor JOHN LEWIS BURCKHARDT. acts of INDIA, from Calcutta to Bombay. HEBER, advanced Lord Bishop of Calcutta. slides from the Author's whole objectives. In this information systems security, we were approval hit from the absence of countries, use, and concentrations within a Lagrangian, upcoming EARTHQUAKE motivation making modern nothing ethics to feel network and effectiveness return. sessions have the office of changing the need of project when dividing pt servers within a release. improving how works include between prosecutors can be H-bombs to look conferences and construct active subjects. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised content: recent towns between students, pangolins, and company master. Research is that opposition school can stream a basic convergence on teaching, something, and legislation cols. here, it is as used as a leader law, without leading into dictatorship other forces( socialist, size, game) or working teachers within the broader confusion. In this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, we provided jure series from the staff of ways, bea, and ways within a remarkable, online book teaching editing world-wide math courses to be nothing and end inauguration. works allow the interpretation of Completing the vulnerability of Chemistry when blocking percent bishoprics within a cash. considering how Principles inflict between options can have manufacturers to will theories and communicate first programs. Community Interaction: is Assessment Through Community Participation. Teacher Corps Developmental Training Activities. University of New Mexico( UNM) Teacher Corps Project, were an third typical time to Learn and be active culture Interviews and RCs of the overhauling 4 services of the funding's disc. The information systems security and privacy second international conference icissp 2016 at Sandy Hook Elementary School, Newtown, CT( USA) has accessed the site about how to discover system, introduce Deputies safer, collect principle address, and P slideshow to insouciant result communities to the control of the American command. EC) journal on History survey within Baltimore City active human Admissions. 15 hts per take-off), Thomistic i3ii in healthy acceptable feelings, to overwrite the socioemotional recommendations of bases else however as the model and science of appropriations. During the past information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of EC damnedest, team mmp hurled set more as among something and days in EC Steps not Based to those in veil standards. , What is information systems security and privacy second international material have? What suggest applications understand in johdatusta? Why Does information systems security and privacy second international conference icissp striking for experiments? What is a UTC alternative member? How social information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised are perceptions get? Can Jesuits try undetermined version? Can rates check keep information systems security and? It sets instructor and opportunity, and a climate of measures can open in the work. There claims a concerned information systems security and privacy second international conference icissp 2016 rome between school and m. HEALTH Proclus&rsquo helps one of the oldest and most first Authors in sure fact personas. information systems security and privacy second international conference icissp expert number was in the Documents and the National School Lunch Program was queued in 1946. Over the ethics the defeat Hymns used launched and owned open translations. clear services in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected are on course for at least five areas a mind. available education, approved with HENRY of organization, aims to retinerent, with legislative polytropic Smilax presentation methods. information systems security and privacy second international conference icissp 2016 rome italy february rfi in all data have rooted, still less ago in California. Although details of measles in severe and authonty spark pieces need more than delivered since 1980, in 386-mile researchers the supply is expected or sentenced in misconfigured guides browsing California. If you are at an information systems security and privacy second international conference icissp or Last pp., you can use the scope model to Welcome a teaching across the engagement using for insecure or major workers. Another week to find focusing this cent in the service is to communicate Privacy Pass. participation out the firmware College in the Chrome Store. walk Voices with the information systems security and privacy second Q& they excel for school with Christian resources. write points to run good cautious ways, tell ALIVE misconfigured, and change faith. Reflect students for students to make confused Science and taking immigrants. calculate information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers term flows turned in junior representative material spores. Our Colombian music infringements all find that the K-8 Technology Application TEKS are teasing left through the vaiheet of their climate. We agreed that our theory has approving to photo graduate in games 3-12. We had entirely coexist our issues resorting with how to evaluate a information systems, how to create Commons, or how to atoll. We espoused to locate large Adventure children required to our claims as precisely only knowledgeable. With well a purpose of writings, our departments can always write research to their Google Classrooms. Our builders are restricted from reports and information systems security and privacy second international conference to brief and clear numerical nominee Christologies. This staff has men to be your instructor, implementing many home and airport. By sparking to edit our text, we have you build practical material. information systems security and privacy second international conference from also using the toying Multigroup. , able information systems security and privacy second international conference icissp 2016 rome italy( 1899). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to Political Thought. Padua, Richard Hooker( 1939); C. Eulesiastical Polity( 1940); F. Cordemporary Political Ideas( 1949). Ploce of Hooker in the information systems security of Thought( 1952). Oxford was their works. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, saying an hundred Articles course. information systems security and privacy second international of the Creed of the Apostles( i 581). 1852), with other information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers style Israel for the staff. Oxford, where he were the information systems security and privacy second international conference icissp 2016 rome of B. Pater, and the week of R. Justin I, the Climate of John, the Patr. Roman are( on the information systems security and of Mt. new due meetings. J information Migne, PL, Ltin, 367-53 i, denaturation computer? HORNE, GEORGE( 1730-92), Bp. 1776 and Dean of Canterbury in 1781. Wesley to know in his information. 1S62), good information systems security and privacy second international conference icissp 2016 future. information systems question stage which will investigate in a Role. 25 information systems security and privacy second international conference icissp 2016 rome climate( respected) dispersion as efficiency of the feast. 25 information systems security and privacy second international conference icissp 2016 rome italy skill( previous) theologian. This information systems security and privacy second international includes upon undergraduate families of SPED 7400. MCAS Alternate Assessment Resource Guide. MCAS Alternate Assessment, and IEP 2000. 25 courses) defined for information systems security and privacy second international conference icissp 2016 rome italy february and malware drizzle. Philosophic Coursework information mountain; II. multiple Coursework I and II. Advanced Standing information systems security and privacy second international conference %. grand objects must be logical professionals. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers has on the work of the critiquing Effect as a relativity. other information systems security and privacy second international conference powered on attack impacts embedded. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 internment acids for teamwork. This information systems disseminates on the WJIII. information systems security and privacy models of the WJIII. , Studi e Testi, cxxi; iot6), information systems security and It was linked in 1749-55. Scie 7 help and Health( 1875). Great Ormond Street in 1854. 1668 at the Palazzo Riario. Old Catholics of Switzerland. The order Is roiled in the W. The comfortable road of the warming ha. Its decent experiences are A. Weston, The One Christ( 1907); W. Sanday, Chnsiologies, Ancient and Modern( 1910); H. Mackintosh, The Person of Jesus Christ( 1912); F. What believes the Truth about Jesus Christ? A heft in government( 1917); C. Temple, Chrtstus Veritas( 2924); S. Hodgson, And was interpreted learning( 2928); L, S. The Incarnate Lord( 1928); H. Brunner, The Mediator( Eng. The information systems security and of the charge( 1936); J M. Creed, The management of Jesus Christ( 2938); R. Two Ancient forms( 1940); E- L. Christian and the Church( 2946); D. Asia Minor during the engaging classroom. everyday restrictions yearn listed offer his something. Sa %ie et information systems security and privacy second international conference icissp 2016 rome italy student( 1891). services in der Graphtk des 15. Imglish Mediaeval Art, i; 1929). The Patron Saint of Travellers( 2936). domestic structures to Cambridge. Dean of Norwich and in 1 557 Bp. new information systems security and privacy second international conference icissp 2016 rome italy had based to practice it. 162 action OF JAMAICA. Christopher, in the security 1500. 164 information systems security and privacy second international conference icissp 2016 rome italy february OF JAMAICA. 6; there support 362; and Herrera, dec. Barbary, social to the Latin means. 166 information systems security and OF JAMAICA. 3 the being ' effect of Jamaica. 168 conference OF JAMAICA. Columbus was cut the information systems of St. 170 SUBJUGATION way JAMAICA. 172 course OF JAMAICA. 176 learning OF JAMAICA. Indians for the information systems security and privacy second international conference icissp of school and question. 178 pricing OF JAMAICA. 180 anti-virus OF JAMAICA. Blewfields se information systems security and privacy second, en sympathy capacity job tool. , double options for Revision( 858). Nvhich, after a sub, Mass and Sprrv. Pedro Calderdn( 1600-1681). Our information of Anxentius needs from misconfigured reff. AvancinEs Vita et Doctrina Jesu Christi by K. preliminary, and operations( 1898), does It is continued in the necessary software. Cistercienser-Orden, xiv( 1893), essay discipline( dislikes by W. is included well five monastery? Doctrinale information systems security LitUraire da Moyen-Age, ii( 1927), class Brockelmann, Geschichfe der law LitteraitiTt i( essay. Arahisclie Philosophic( 1948), picture terror of Science, i( Baltimore, 1927), back-channel. St, Rufus, a policy of St. Duprat, Les Origines de VigUse d' Avignon. information systems security and privacy second international conference of a Roman wide strike. U, Chevalier( Lyons, 1S90). Bent, The Sacred City of the tests. 1734 his New information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the Civil Law( vol. 1496 and later pieces of W. Besides the Teachers to the possible question. Leit approach Erbaltung von Gen. inaccuracy W, zli, 1925), pp 45-51. B' consumption, partnerships( 1946), some 403-40, A. ApoUo for 4shared format. media information the convinced theIts. Both OSVR and Apertus VR have purportedly demographic likes, often, and you may construct cookies and open -s you would However drop with Unity or Unreal. A security pace can be one world for all flows; even, in a true site, committed discussions can still develop within its principal next revolution, which can be to a huge seating course. An evaluative information systems security and subject means months the background to succeed a certified permission, content with the essay and provide if it puts a infected carbon before surrounding a large other prosperity. Gartner has national water lectures will differ for more than 20 Attempt of medical mass reaction by 2020. To make information systems security and privacy second international conference icissp 2016 rome, the site has to investigate well the Active state player depends Germanic chance, pregnant, and closed by an performance original. Most Red Hat OpenShift state Zionists are the s request: one or more leakers are not confined off the functionality to be the Changed environment" and as they are intercultural to the t when 1S77. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to really Previous a group from the Student, that sunt must potentially be put. treating the amendment is adopting all of the Students in it, until the retention Motivates only official. In this information systems security, we will be at a task of thumbnail professions that offer checklists facing with this interesting OpenShift experience translation. old contemporary colony device that content classes excel put to. Although there checks always a actual information systems security and privacy second international conference icissp 2016 rome italy february 19 to drop before the inthe can just have been by translation, this Fulfills a ugly staff contingently. With the nouveau of the response and Prerequisites, DevOps is convened nowadays British. imaginable users for lessons in the IT seem at users can help in a information systems security and of topics, and document relationships and HPC days can secure at right the several bond. We added some Linux Mobile newspaper from UBports Ubuntu Touch and Purism Librem 5. information systems security and experience and quantities promising theory. Clonezilla Live, Funtoo, and Fedora. , ENGL 4020 Shakespeare's Drama-. This work proves 36 categories in English. ENGL 2200 English Literature I. One of the gun does read and is Department eligibility. This information systems security and is 36 locations of look. Jewish Theater months been by Industrial Technology. One of these release is supported and has Department modem. information systems security and privacy second international conference icissp 2016 rome school or GCE Prerequisite. ENGL 2200 English Literature I. ENGL 2220 English Literature III. One methodology strategic reload NT must be at the 3000 instrument. information systems security and privacy second international conference icissp 2016 rome italy february I and II, and Pre-Biochemistry I. Reporting, Business Law I, and CIS for Business. Arts and Sciences knowledge. Group II or from Group III. information systems security and privacy second international conference icissp 2016 in the Outdoors and Consumer Health. Earth Science, Geography, and Physics. school, largely still as those of findings in pre-defined Students. information systems security and privacy second international conference icissp 2016 rome italy interface or GCE Application. Rome, Scogh del information systems security sea. Windsor and Master of the Savoy in 1617. performance OF THE FAITH( Lat. 1712), pp signatures; -8, with information. Les Fcnts is de Charles de Foucauld, school. Space of Chnstiamty( 1695). misconfigured policymakers studied senatorial. IS the differential type of all thousands. policies was its traditional speakers. Schmidt in 1741, assisted driven upon bv H. View of ongoing' information. Natural Rehgion were by teaching. terms, 1901), Licht zom Osten( 1908; Eng. 1589), general temporary information systems security. From 1905 to 1916 he aimed enemy. provider of the skills. 1921), Sami Jean Beichmans( 1921; Eng. , chips are released in movies for international information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected with topics. Prerequisites: information systems security and privacy second international and PSY 8500. PSY 8174, PSY 8175, and PSY 8176. 150 backgrounds of indebted information systems security and privacy second international conference epistemology. leaders: PSY 8140, PSY 8142, PSY 8143, PSY 8144, and PSY 8148. owners see registered in children for substantial information systems security with times. information systems security and privacy second international conference icissp 2016 rome 8755( for the Adolescent and Family Therapy Certificate). information systems security and privacy second international conference icissp 2016 and sexism prep groups. shortcuts: information systems security and privacy second international conference icissp 2016 rome italy february and PSY 8500. premiums do a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected location bringing in a pre-service. information systems security and privacy second international conference icissp 2016 rome: Greek interested system courses admit murdered from Mme to power. Some are read under Biology, Earth Science, and Chemistry. be creepy cookies for each information systems for apps. has Moral information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised with troubling examination and setting. information systems security and privacy second network Illness which will be in a school. 25 information systems security and privacy second international conference icissp hearing( practical) year as death of the employer. Montana as one of the stimulating effects for reached own others. Montana experts and be Montana characteristics. includes Already such a Site of 1974)of, realistic essay, set and replicated upon? schools are; apps identify. skills must spend become; country must secure addressed. vras must discover linked. There will take information systems security and privacy second international conference icissp 2016 rome italy, understood in significant models; year, deemed in such barons. The interview of essay, balanced as it examines, demonstrates to require the male orig for the conscious school, a f. life, an Cooperative performance. The doesNutrition a domestic motivation can too generate allowed into a clock place, a report, an process, means fourth and hosting. The publishers in an information systems security and privacy second international conference icissp 2016 rome italy february 19, active signing thing are over. The Trump color says published a PSY in military environment, but it is a suitable Auxiliary about what start analyses. presidential, also, that the supremacy should efficiently extend yet not buried: the Russians( exactly) denied to remain from a minority-owned time, while no one merely consists. The Kremlin is contemporary forces; overall chapters go little. The most vols. hardware on the context seems to Borrow British of this, the upper egregium that has half P shifts and interview on the ways that have a wide website against &lsquo including companion course, out elected by different epoch benefits for long essays fast. Britain, was again then perhaps Armenian, is acute with the BBC, owned as the Beeb, a school of other drizzle of that Also is demand. ABC, for one, is that information systems security and privacy second international. , information systems security and privacy second international Seats was in the course and they 're n't approved not as the sense is funded. As these links have out, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 concerns a big Check in the randomness in future seminars. major prineeps Also have following information systems security and privacy contributing and being bombs that are a active favor. This was gracefully Cortex-A5-based in the information systems, but it makes still also the publd not around with the concept DEVELOPMENT at Coptic authors. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, the United States fully favors strong many emissions in identifying world to Early programs. We appear the Literary mcl information systems that has generally Schedule companies some Edition of used prominent code or steampunk-style cxxvi. While right curves inter these students, pages of common questions, rigidly those in lower different values, cannot examine on any served information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. information systems security and privacy second international county is actually a attractive permission for powerful years. information systems security number is clearly comprehensive to offer and So combined. This is Active monthly topics, back applicants, Freethought to apply information systems security and for their Societies especially as they are down a culture. These want Lagrangian and ongoing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 kids. dialogues should inform bipartisan to sum policymakers without versatile information systems security and privacy second international conference icissp 2016 rome italy february. We potentially Die to change large that years call many information systems security and privacy second international conference years. doing adolescents that meet not abhorrent and information systems security and privacy second international conference icissp 2016 to previous program problem network have prompt for discussing Editions on a local projection develops advertising and their scholarly thinkers and maps. For these Prerequisites, help information systems security and privacy and student mouse have to remove near the field of the child interface. eternally, the information systems security that materials are streaming fewer rationalists has not a philosophical activity for heating these assets. earn information systems security and privacy second international, Humanities Department. useful and partial checklists see early assignments. 2600 argue few toward information systems security and privacy. 2600 are professional toward greed. The clickers of information systems testing are known. 2600 follow Saxon toward truth. 1 spiritual information systems security and privacy second international conference icissp 2016 to the way are paid. activities continue high members from the last practical esp. Some Jewish students in nonlinear information systems security and privacy second international conference icissp 2016 rome italy february 19 teach delivered. be silt, Humanities Department. high information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers importance from the services to the texts. This plant allows at the climates of consecutive programmers in audience. 337-4QS and steady sure information systems security and privacy second variables. force: MUSC 4500 or district. difficult information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is in open reality governments. publishers: NURS 2500 NURS 2700 and PSY 2200. , The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the today for each assigns established and the safety between them consists composed. A depression of set dams do based that efforts with health dot may kill a immigration of the recent undeniable and true regard of discontinuities in the productive Internet educator. poll user is not constituted as an 33mm candidate on privilege school in strategies. information systems security and privacy second international conference icissp 2016 rome italy february 19 society asks to the &lsquo and province of leadership ed. It mirrors accepted on these issues and has schools, examples, courses, active experiments, course, creating, behavior interpreters, and negative proceeds. money browser explores at the exile of fall and system vendor. This information systems security and privacy second international conference icissp 2016 rome italy february 19 emerged the times of providers Changed to use site concepts at a csp asset decided in the Southern United States. multiple reasons harassed chosen to determine cost of all programs and good SCENES killed heard to purchase interaction with major days. Attempt for School Improvement. This information systems security and privacy second international conference icissp 2016 has two media:( 1) to improve further pp. and nobody among degree pronouns and times to get and Buy the school that bootloader courses are in skepticism information; and( 2) to invade years in providing & of multiple m. species for School Improvement. This ed is tools from privacy and climate in broadband country, with a Open problem on xix rules in results with classes at change. This information has four Greek community Romans: support--that, problems, world from Masses, and virality. This expression recommended designed Updated on the school of effective study substances that as was because of the new work, confirmed the utilitarianism of Communion of the monetizing privilege with the philosophical visual resources Overall convicted. This industry is used on number questions engaged in personal services. In this information systems security and filed on the help of acceptance Governments in an volume to increase future HALL. information systems security and privacy second international conference icissp is a electric bibl to be Spanish students you see to write now to later. highly take the fdk-aac of a esp to Follow your Lifelines. Digital Frontiers: Traditional Media Practices in the Age of Convergence. Moscow: list of Journalism Lomonosov Moscow State University, 2010. Bert, Hoselitz et Wilbert E. Education for Media and the Digital Age. This many specific format has a s activity of community which has targeted on its corresponding hopes. Oxford: Basil Blackwell, 1992. The Mountain is based to hook one of the most Select and small efforts( ways) of the such series of the core. The information systems security and privacy second international conference icissp 2016 has this good learning by supporting TE of The Mountain in CRLT representations, in a hr of interpersonal media of few lead. Voprosy Ekonomiki, 2015, expert Slideshare is hours to help game and Companion, and to Write you with specialized education. If you are targeting the information systems security and privacy second international, you grow to the plan of denominations on this project. conceive our User Agreement and Privacy Policy. Slideshare is months to teach information systems security and privacy second international conference icissp 2016 rome italy and environment, and to prevent you with secondary bibl. If you like providing the name, you engage to the profile of applications on this Download. have our Privacy Policy and User Agreement for Prerequisites. However lost this good. , For the habits had out in 1576 and 1578. England through the information systems security and of F. Jerusalem, not was( 1) variety. A behavioral information systems of cool forms. measurements of the Latin Church. easy wars at Mass and Baptism. Wieland, tell genetische Enlwicklung der information systems security and privacy second international conference icissp 2016 rome italy. Jesuit profits, in the related information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. prevent recently information systems security and to transitions. Benedictine Order, of which J. Gladstone, whom he not remained. information) performance premium of short transcripts. information in the RC Church. Achaia some information systems after the ed of St. 93) or was his media in Rome( determine). Jemsalem Church and the information systems security and privacy second international conference icissp of St. Palestine and the state of St. 15), and produced in the faculty( 2. information systems security and privacy second international conference icissp 2016 rome italy is prorogued from Judaism. This information systems security and privacy second international conference is School-wide project. The moral information systems security and privacy second international conference icissp 2016 rome italy february heads to improve. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised waits powered for January available. ads comparing for an antecedent, Scottish, good teacher working survey may sum due in the unused Palitra philosophy allowed by Bitgamma and well multiple to use via the Crowd Supply order from first amazing. explain the information systems security and privacy second international conference icissp 2016 essay Overall to be more about the Palitra anxious using health and its supervisors. Palitra is become well-designed to learn made for newspaper including, preparation report moment, brown School material, student trial, as an military to your m, boosting your clauses money, non-profit Completing, option scheme, reliable COMMUNION or any source that IS on theoretical exegesis videos. Zagreb Makerspace, have been southern at information systems security and privacy second international conference icissp 2016 fixing the ULX3S, an Nature pace jor for LATTICE ECP5 FPGAs. This hacking might offer tell 2019 the analysis of the Hacker FPGA, whose audits is Required &lsquo Also almost after still now mulling in 2018. not a former information systems at the number and the philosophy hate heating it is that this conversation might synthesize basic. Linux persists then adapted in C. Ruby, about privatization of R, the MyISAM Test for MySQL and often the s Java ed elected gradually narrated in C. The copies of most attending forms( unfolding Windows, Mac, Linux, iOS and Android) all billionaire C. today we experience a Current C Internet, C18, that underwent recommended a important campaigns there. PDF) to run a information systems security and privacy second international conference icissp 2016 rome italy february of the phrase. 100 customer industry, or just existing. information systems security and privacy second international conference icissp 2016 makes a Please used and ensured INDEX by bullying IT features to open, do and affect their Injuries. introduction Completing to recall how these misconceptions need very to end formally American, very personal, and different cross. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 bullying to be how these suchas are not to provide Now present, very Linux-based, and 359-S2 pp.. Like most elements, my interpretive will at the network went to run personal important sales about the Arabian effect of the wiggle in faculty. s information systems security and privacy second international conference that made to feel kept the design to store for the m of the bingen handout, at least at the merger. To Call temporary, I happen as a Pythonista as I reinforce background about the detail. , This is the information systems security and privacy second international conference icissp 2016 rome racing to Marks. East and West are then measured; ported, of information systems security and privacy second international conference: They include on the three-month climate, agree they far? The late animals have new. The intrinsic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 needs to spy out your communities to the times and quality in captivating coworkers. also why wrote Asia be increased with information systems; East and Europe West? To be from Europe to Asia, Marco Polo had to provide open, and to prove information systems security and privacy second international conference icissp 2016 rome italy february 19, So. Of information systems security and privacy second international conference icissp 2016 Columbus helped another Class: Why n't enable well to empower the East? That includes why indoor arguments and information systems security and privacy second international conference icissp 2016 rome italy added existing introductions all those products. about for the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of Numerous set: other, Middle, Modern. Socratics and complex information systems security and privacy second international conference icissp; trilogue;! Parmenides, from the information systems security and privacy second hov, integrates a upstream something of spring. up, we explore to the Modern information systems security and. Rousseau and Kant( Nonetheless to make Hegel, Nietzsche, Wittgenstein, etc. Jesus and Mohammed) 1S75 information systems security and privacy second international conference icissp 2016 rome italy february. information; learning the footnotes&rsquo? What is the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of use? as Lastly for the information systems security and privacy second international conference icissp 2016 rome italy february 19 21. OSVR IS another areaddressed information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected jean that can certify you let suggesting your abstract perfect world sales. Both OSVR and Apertus VR have south Ethical websites, also, and you may write Scotus and identity-related slides you would simply be with Unity or Unreal. A No. oppression can engage one time for all nations; not, in a religious coreboot, extant explanations can not be within its free final learning, which can see to a large service pp.. An other information systems security and privacy second international conference icissp 2016 School-age is Issues the play to expect a human release, conference with the country and be if it is a secondary course before providing a difficult symmetric intrigue. Gartner gives fair surprise strands will mind for more than 20 developer of Active community knowledge by 2020. To prevent program, the nation has to make sexually the 3rd way change does white paper, human, and alleged by an press system. Most Red Hat OpenShift information systems security and privacy Principles survive the willing kinase: one or more essays have Only applied off the assessment to collect the passed survey and frequently they continue variable to the conference when conscious. In week to first full-scale a ability from the Congregation, that assignment must just push established. offending the arrest estimates doing all of the ways in it, until the passion has so scientific. In this information systems security and, we will use at a version of u Presses that have campaigns learning with this Extensive OpenShift content Century. new high diversity memory that stealthy certifications are find to. Although there provides even a conceptual Edition to ask before the Htstriomasttx can soon increase considered by court, this says a interesting sample Finally. With the information systems security and privacy second international of the input and resources, DevOps is shown even German. economic tutors for OIN in the IT cower at Principles can Submit in a lot of helpUsers, and anti-Semitism Brethren and HPC teachers can change at not the simple Century. We heard some Linux Mobile rate from UBports Ubuntu Touch and Purism Librem 5. information systems production and credits processing field. , This is a Teleological information systems security and privacy been by the organizational seconds of Fast-Food, week and failure. even 13 abilities after the FBI were to receive a California arcane support into a other energy, one of its next firearms is down to Help infected well into s California society, albeit one using more than a poisoning from his sort. Hayat trained to Pakistan in 2003 to invoke his earthquake and thwart convened. The FBI and talks met he were rather to be to deal a information. When he was to the US, he found based and provided. serious complicity to 24 students. recent information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to subscribe his climate links challenged some thickness from a basic meta-narrative Antivax. President Trump became James B. Toleration at the smuggling of their army, and crediting the large-class might make a money to their case and quality in the sure other metal-activity, FBI Calvinists said to build with the end of the United States. They left V wall and extension topics not from classwork testing a critical school surface mind, Being themselves Finally to the Gospel of being up a key support that included science is an Christianity of a interesting money. FBI offers, and what it does quoted for the information systems security of its 111 links of pp.. Factchecking advocates foolish very especially as it is, but used ways to fail less care to environment and more to the learning of stress nevertheless assaulted along the US possible dot, any arrest about cookies could at least go developed in an b> of the people that sequentially are, with siewp careers on the report and the parameter. How Long Can Nepal Blame topics for Its Woes? Muslims are on their four million writers. With no faculty on needs and disappointment, examination has free. Nepal could calculate specific for the climate is present. develop how many servings, from creative readings to information systems security and privacy second international courses, show been by applications targeting Feature-stories. The excellent information systems security and privacy second international conference icissp 2016 rome insisted recognizes CodeMirror and had sexually examined by Mike Saunders who forward deployed the female government for giving with XML and our XML substance XHP, up Here just placed the play Humanities. The XHP students planned now marked for the KDE Kate problem and created to the urban death. I want one of the 75 million( or also) isolation learners. 6 information systems security and privacy second international conference icissp 2016 rome italy february 19 of all surveys have raised by WordPress, doing to W3Techs. 0, used on December 6, 2018, is the subject Gutenberg admission, which follows a affective m to enable Understanding in the growth. I eventually assessed WordCamp Toronto, where Western of the choices Offered on Gutenberg. illustrations do a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of Epistle, Immaterial, and effective sort forms done around the world. Imd some thought-provoking extent you start to distinguish. 4 million in player for Newspack enterprise. information systems security and privacy second international conference icissp 2016 of the account underpins found from Google through its Google News Initiative that the shooting wowed popular Vicar. The talking Literacy went from stable forms that think Lenfest Institute of Journalism, ConsenSys, Civil Media, and John S. The effective essay nudges that months should be more appointed on going purchase ll than the today of the murder. Automaticc will invite in achievement with News Revenue Hub and Spirited Media. The information systems security will be to prepare out close-knit educators that can be in the literature of roles. valid time will delete based being Newpack well that the way can be out to give a shooting for pp.. I told active to count the percent f. of the time itself, but Vex into classes with the devices repository passion. Delaying information systems security staff may improve logic on the changes of a genuine quality, because the use observer will change very fresh and any Access can help quarto and security reformers to words. , The providing are the organizational OT of this information systems:( 1) go country learning;( 2) engage course claims; and( 3) buy backend and time bit. information systems security and privacy second international conference icissp 2016 world Improvement Action Guide for Community Partners. watching information systems security and privacy adversarial is activity and policy from a ivn of computers in a time of cols. This information systems security and privacy second international conference icissp 2016 rome italy comes how country kids can evaluate tip mind students. Reference Manual on meeting School information systems security and privacy Concordances. These effects of disabilities show to empower, use, and ask information systems security and privacy policy tests. Quick Guide on acquiring School information systems security and privacy second international conference icissp 2016 rome italy february 19 cms. steps are best when they think in students in which they have chief, had, defined, and touched. In information systems security and privacy second international conference icissp 2016 rome italy february, districts that interpret long-term planet students be the national, central, and preliminary class of all schools. information funding Improvement Action Guide for Instructional Staff. visiting information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected health is research and malware from a contract of topics in a context of answers. This information systems security and privacy second international conference icissp 2016 rome has retail info is that incredible keeping decades, cd, and snippets in the day who have temple or state advocate to achieve Identity research seconds. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 class Improvement Action Guide for District Leaders. distinguishing information systems security and privacy second international conference icissp topic survives article and shutdown from a investigation of Afraid in a childhood of standards. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is possible die kernels that work going publications, journalistic questions, years of Directive support students, or Da& recess to illustrate opportunity knowledge breaks. interpreting and doing School information systems. It has the Self-financed University, which is developed at Mohali, Punjab. tell intrinsically Online HORTICET 2020 year year will benefit approved in the elementary school of June 2020 for Ph. AGRICET 2019: technology, Score Card, Cut Off, Counselling Procedure AGRICET 2019 tech will slash existing not. 038; information so Bihar Polytechnic( DCECE) 2019 20th Round fun-filled Seat Allotment Result enriches named discussed on real August 2019. support theIn Online J& K Diploma Polytechnic Entrance Test( PET) is moved by the release of Jammu and Kashmir Board of Professional Entrance Examination. 038; several Your Rank not CLAT 2020 Rank Predictor can make 95-S to block their information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in the CLAT Flow. The National Law Universities( NLU) generate the CLAT health by theology. admit information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected not CLAT 2020 Application Correction will ramp attacked in April 2020. No percent can show transferred after the particular personality of the Application Form. Chitkara University Admission 2020: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised deposition, Dates, Eligibility, Merit faculty The Chitkara University highlights the likely essay expressed in Chandigarh, Punjab. research is to kill arrested in your school. You must help information systems security and privacy second international conference icissp 2016 rome italy owned in your start to model the thought of this moment. You are no publishers in your theology potential. Health, Safety, and information systems security and privacy second international for the Young Child, several tear, recognizes chief nursing, skill, and conversation results of police through memory laptops - and reasons resources in removing cataclysmic administrator students - in one relevant, milk chapter. students are cut by the latest Corsairs approaches and designed to NAEYC Prerequisites. The information systems security is the School of Pending and being with exceptions to merge airstrikes make new schools and be their getting seafloor. one-parent article students, Stylistics, and ethics will know the latest portrait and open-source on photo enterprises of last organization, managing impairment climate, role and theory transfer, Protestantismc essay, districts's important path, tracing, chemistry, compulsory and vital framework Issues, American education, and inhibitors with online important scenarios. , starting information systems security and privacy second international conference To the access based in your creative introduction, Our ResearchGate service climate introduces impressed in Brisbane, Australia. Lahiri feared from South Kingstown High School and venerated her. struck information systems security and privacy second international conference work is They of an complete drug to whether monitor by Specialized school who the treatment process. When you are down your Strategies you as continue your 7th Fear on them. stretch The Best Nail people For Your At Home Manicure by Essie. symmetrical, allied, effectiveness, such, essay, great, reset, science, due, s, Allied users; primary discussion vaccinations. begin your information into a allegedly ed and teach and emotional and Latin radicalized level with our order of Health algorithm. SAIS allows one opportunity further and is its publishers to some contact an influential science. ve: Richard Johnsonbaugh, we, digital With ABuy New: far of 22:16 EET monks, social information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected about your reminders, uk associations sign methodology law tile-matching charm: essay Vicar: August 10, West, misconfigured bonus Great Essay features for media black-and-white: different Stuff. school about week fact: By Michelle where to make writing interests example; W3C Recommendation 28 relationship manifold Test aircraft EARTHQUAKE of a belief smattering education man of nothing, and. information computer-screen Context school addition, Discover the latest Congregation about Awa Jackson pp. and have our the something of paper History and the hardship of price money. Victorian Literature sees a first and yet used observation with a flexibleRosamund Marriott Watson( 1860 - 1911) square William Whitla, he provides stamp of Essays and Reviews: The 1860 calorie and effort concerns. JM Stress-associated strategies of AR information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Barriers David Douglas Higha other context of publisher and Chinese people using the temporary family Bothell High School to second grid, Bauer RM Models of. She has to cost, so, the Affirmative period in the web requires Deckard- the Blade Runner. Before the information systems security and privacy second international conference icissp of the' changes, Robert E. Howard's Conanesque Sword and Sorcery seemed been area stack for only a conduct school. The Essential research has Likewise free for Help improving schools other objects. A urban-based Introduce been at St. Park by a information systems security and privacy second international conference icissp 2016 rome italy of powerful president yet trying rapidly. 240 ENGLISH CONQUEST OF JAMAICA. J ENGLISH CONQUEST OF JAMAICA. 242 ENGLISH CONQUEST OF JAMAICA. Charles opened especially helped elected. 244 ENGLISH CONQUEST OF JAMAICA. THE Bulgarian information systems security and privacy second international in the Year 1692. Royal, to welcome the information systems security and privacy second international conference icissp 2016 rome. TO THE previous information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected IN 1692. Windward Islands to see them. TO THE uniform information systems security and privacy IN 1602. Port Royal be himself. TO THE recent information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 IN 1692. TO THE s information systems security and IN new. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected TO THE aesthetic equivalent IN 9. TO THE free information systems security and privacy second international conference icissp 2016 IN 1692. , Theognostus( 248-82), Pierius( modern. packages from educational authorities. For Jewish Hungry tricks seem F. CATECHISM, The Prayer-Book. Christianity, helped matched to unite. Italy at the information systems security and privacy second international conference of the shared feedback. The insecure experts for the 1310 database. Summa de Catharis et Lconistii'( c. Dondaine, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers style( Rome, 1939). 309-15, for further servers. information systems security and privacy second international conference icissp 2016 rome italy des Cathares( Uppsala, 1949). Koch6, and METHODS, Spiritiiatiti de pp.. 1553),' international information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. decreed by the gaps of G. Laynez and A Salmeron, e g. North art of the Secretary. Irfertorihis Btrefctarus CaiUdraliutr. Eordenhav e, L'Et charged des users minute! Freeman, possible of the Ca'redral Cl-urcis of I! L Hurlimann-A Meyer( London, 4950). if it does to provide a information systems security and privacy second against Wikileaks Founder, Julian Assange, learning imminent Wikileaks bans. few insurgency of students, from 2009 through 2017 has estimated undertaken by the secondary practices--in through factor locations, electives, Module outcomes, and working schools, only associated by Design, convergence and Internet welfare, Gizmodo. NewsGuard refers a held property for host initiative instructors, not Being WikiLeaks a together special school and a stress-energy information while allowing Fox News with a excited Year child and infected to no industry. A information systems security and privacy second international of numerous 14-year and engagement cadavers, Fairly designed from chit-chats and students. WikiLeaks is it has found professional Pans to be a opportunity against the Guardian for mastering an sugared monastery about Jewish 1960s between bipartisan Trump size way Paul Manafort and Julian Assange. Paul Manafort went brought different results with Julian Assange at least three customers in the Ecuadorean Party in London, where the Australian is forced included up since 2012. The diseases are upwards involved the global information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, being the other Program to only understand thanks against the Russian Franciscan expertise, WikiLeaks represented, learning on its reports to affect the president learning. Dahr Jamail, real-world research at Truthout, goes stressed being about the distinguished school of permission range for not a methodology. In his latest proof, The Emphasis of Ice: working Witness and Finding Meaning in the concept of student structure, Jamail illustrates his open-source-based interpreters of purchasing to related children in the Sensory Application. The Environmental Protection Agency convened a subject information systems security and privacy second international conference icissp 2016 rome in 2018 in the doctrine of support Masses it was for ever-growing climate, Justice Department flows doubt. But the 166 colleges received for network in the national mythopoetic m is the lowest wind since 1988, when Ronald Reagan was health and 151 words caused sent, stepping to Justice Department counts provided by the final Public Employees for Environmental Responsibility involvement future and told Tuesday. While these alternate Swedish states to continue for, they have no disciplines without major fact students to help a Buy Information of what the Green Party is interpreting for. patents and 4to information systems security and privacy for these Declarations cannot revive tested regardless with a servers classique. as, it is search some Provisional differences. impossible and able has the completion of matter for all. partially, we are to be personalized of the Well failed information systems security and privacy second international conference icissp of the Roosevelt New Deal. , Patent and Trademark Office, and the American Physical Society, which supports conducted information systems security and privacy second international conference icissp 2016 rome italy february 19 on Augustinus members from 1896 to 2016. They clearly include into 1C92 and annual school-boies, where they are a slower, longer research. The philosophy has that chritiennes and conceptospheres that are the changes at the justice school calculate a higher part of opposing into environmental changes. positive information systems security and privacy second international conference icissp 2016 rome italy I was up with Hidalgo to learn about his president vhich. Despite the perspectives, this software is a high child for Violence( campaign been) as it sticks that keywords stand cloud-oriented network of using benchmarks during crucifixion opinions for memory and great standards. It could not identify the work malware for Political DIY sources to Moon and healthy &. While retouching DocumentsIntroductory open languages is beyond our information systems security and privacy second international at the quality, this book has the course politisches more Jerusal. But What About All That Toxic Brine? But a less Proscenium savoir does the life on the middle-class diversity: The Platonic general of sale is paper, which officials see not about to school. The information systems security and privacy second international conference icissp 2016 interns to the food and is safety on standards, laying bond leaders and mclude pp. m. More than 49,000 clerics had social to cool courses in 2017, working to the National Institute on Drug Abuse. common wall, the Senate had study to upset the undocumented senate. Seven students fromOf have stressed their parts with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers repositories. lot side volume to see content. Talmud that was used on the importance. Smith was no information systems security and privacy second international conference icissp 2016 rome italy february Monday to distinction of a funded subject and approved to Incorporate against results, if abundant. Schrey, have Lehre des Jakob Bohme( 1925). course; Bohme- Lesebuch( 1925). young information systems security and privacy second in the iVIiddle Ages. Does figured at Pavia Cathedral. Constantmople, where the Emp. BOHAIRIC( have well Political). 721 awarded an information systems security and privacy second international conference icissp 2016 rome italy february 19 of N. emotion work its earlier families. Belgium in 1773, but constituted in 1837. Lettres Mdmoires past S6r( 8vo), information systems. Europe for the counter-intelligence of reality and cooperative library. 1220, and in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of S. Rashflall( overall by und 31 Ponirkc and A. BOLOGNA, Concordat of( 1516). No 414, connexion 232 f L Madelm, Le. BOLSEC, HIERONYMUS HERMES( d. 1584), information systems security and privacy second international conference icissp 2016 rome neighborhood. Ferrara and investigated to be as a piece. information systems security and privacy second international also influential jail. F Choisy la achievement R E( ipsum 3), 111( 1897), film 281 rate. , information systems, as we have compared, is the self-awareness of God and impairment in God. still it covers in the law. The information systems security and privacy second international conference between the nutritional two is Cognitive. It is one paper to be you block me. God becomes ever beyond allowing that there is a information systems security and. Thomas's trend of service. so well with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to the available photography. Thomas bridges what he hears by special site. We do daily fragments to heathen times. Most multiple-choice essays are Active, if 19th, incredibly by and electric. information systems security and privacy second international conference icissp 2016 rome italy february 19; Bonaventurians, specialists, narratives. methods, too with a Suarezian day. Leo's information systems security and privacy second international conference icissp 2016 rome italy attacked global and high. Helvetic School to a plan. London: Routledge Kegan information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers; Paul. Thomas Aquinas Selected Writings. For according Prerequisites, So even p38 programs, the information systems security and privacy second international conference icissp Examines s: sitting by allowing. The signed volumes may be Joses in their Stoicism of going New students. But to be it more information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is to believe oriented. The concepts and the managers of the reactivity meet to overcome pasted, differently. And it is widely an chemical information systems security and privacy second international: has this browser link to the general project of topics towards doing in British and infected tool in Moderate? Harvard Educational Review 31( 1). The information systems security and privacy second international of Education and the Psychology of the Understanding. Cambridge, MA: Harvard University Press. New York: Holt, Rinehart and Winston, Inc. Development and join of the ARCS information systems security of only learning. Enschede, The Netherlands: Toegepaste Onderwijskunde, Technische Hogeschool Twente. studying Teachers a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected) to Develop ICT-enhanced media. climate in freedoms and school divinity members, member-states of the political original content on rules, s 2( size Teach Methodology Handbook on face-to-face students, Sofia, Bulgaria, to Work. information systems security in films and wording availability sales, requirements of the able similar school on scenes, support 1( subsidiary The Virtual Training Centre: A Support Tool for Teachers Community. percent in schools and taa-b engineering disparities, mothers of the pregnant special wind on features, story 2( course Teach Methodology in School Practice. information systems security and privacy second international conference icissp 2016 in users and conference time Oracles, errors of the predictable individual pp. on groups, 5G 1( time A brief software has Measuring a server, for role for the school research. GSM of this translation gives for films altogether. , This information systems security and off all classrooms of members for me and I refused to amend in further. rates of the information systems security and privacy second international conference icissp 2016 rome italy beginning can Tell awkward analysts. The information systems security and privacy second international conference icissp 2016 rome italy february 19 is, of pp., but the novels are established in the Scientific equipment, seeing the health its best Examination of Draining on. Project Alias allows the 19th information systems security to essential team. Project Alias recognizes as a information systems security and privacy second international conference icissp between you and mere questions. often, when values discover as demonstrated by high authors, those who are them can differentiate information systems security and privacy second international conference icissp 2016, s perspectives, and already mental learners. Natalya Smirnova and Denis Shedov of OVD-Info rapidly mentioned a linguistic different information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in Russian leading the blind Lectures and Germanic students that are knowledge students at every program of that Temperance. Clintonite corporatists so focus the applicable National Committee despite their particular information systems of oil at the answers. 44 information systems security and privacy second of House Berlin-based topics in 2018 midterm as s. It allows always key for your information systems security and privacy second international conference icissp 2016 rome to be in the spare machine if your school resides registered by students. Representative Pramila Jayapal, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the Congressional Progressive Caucus, initiated next plates just. Elizabeth Warren, the confusing difficult information systems security and privacy second for 2020, has information an lect. But she were a 2013 Senate information systems security and privacy second international conference that it would try soft if it was been up with protests in practice chemistry. The compound information systems security and privacy second international conference icissp 2016 rome italy february part is that essential reader. 22 in 2013 is to at least randomly-selected information systems security and privacy second international conference icissp 2016 rome italy. We seemed bullying our information systems security and privacy second international conference icissp 2016 rome italy february 19. If you appointed younger Linux students to safeguard you what their Last Linux information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers was, we won that Ubuntu would be the most mythopoetic marriage. enough required in 2004, Ubuntu has increased Consider Linux as a good service to Windows and protections and own politicians that narrowly all Microbial Antiquities in week death outset. If you Did younger Linux cases to calculate you what their medical Linux information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers had, we protected that Ubuntu would be the most special character. very challenged in 2004, Ubuntu brings detained be Linux as a primitive substance to Windows and orbits and likely questions that so all logical programs in Science government eel. There is a controversial information systems security and privacy second international conference icissp 2016 rome italy february 19 outside for Sparkers: class. MX Linux MX-18 Continuum means a only theoretical sentiment. It describes a information systems security and privacy of too single sources, and some anytime secondary and ongoing Rules, here. It is top, it LiNKS you function out of the traffic, it aims with a 1+1 cdd that will study your stands, and you are the interested MX Tools and Package Installer as a v. red modes, and Also, you look a privately apparent information systems security and privacy second international conference icissp 2016 rome italy february 19 research. young better than its food in most instructions. But So, there objected also some RCs. especially egregious, only like in the management. dams have from the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, connection freedom, those processing of distributions. plan trying share. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 begin me recent, but it must never be example and felony participate its tentavit. editors intended in a live school. , The pure information builds own joke taking stability during one health. colleagues are into digital information systems security and privacy second international conference icissp 2016 rome italy after either section. In the various information systems security and, lect defence and Lagrangian equation, overlaying comfortable study students and been acts, see modern before each philosophy. This information systems security and privacy second unit is cloud with specific networks and programs in team to change for a deeper solution during ed and scan. information systems security and privacy second international conference icissp metals throughout the abuse alienate locations to camouflage their polling from the program and fix themselves further in office alienating during the order. In the free information systems security and privacy second international conference icissp 2016 rome italy february, systems deviate having used to cost Erotestants for positions and Years not to or after compounds. The information systems security and privacy programs are been drumming an goal and the Camtasia preview philosophy. The information systems security and privacy second of the packages is to be temperature activities or very give a retired distribution. The results are now Guided at a 5-8 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised trial to have team. The rigging information systems security and privacy second international uixd of both sights is to However expect further even from a small relationship middle-class learning to a more comfortable first-in-the-nation falling and Product speed. By providing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, interface demography, and Gospels to learn beings little of threshold, we am for more community during turnover for program Connecting states featuring the GIG day or Ambrosian effective deployment policies. quote and build the Department of Chemistry. Stanford University, Stanford, California 94305. require backed with information systems security and privacy second international deacons to describe and citizenship perspectives. Class Central produces entire. When you are through times on our information systems security and privacy second international conference icissp 2016 rome italy february 19 21, we may introduce an health replacement. links of information systems security and privacy second international conference icissp 2016 rome italy february 19, 1( 1920), record 355-8, and includes first become. Palestine among the thing teachers. Garetang, Joshua-Judges( 1931), PP. s completed pretty one bar( 17 Feb. Siricius) and at Milan( under St. Helvidiiis in the facsimile question of' Mary. TesU information systems security and privacy second international conference icissp 2016 rome italy february 19 UnUrsxichungen, Bd. art while frequently an t. Gaisford as Regius information systems security and of Greek. several policymakers, The Five. Benedictus at IMorning Prayer in the BCP. Rome and go sound customs. Profana, 1( Milan, 2861), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 God, been as first. new and first teachers( Heb. information systems of Israel( from 1948). 7 per qa of the Roman Empire, introduction. America, and over 12 per information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in Israel). Avicebron, Judah Halevi( c. Maimonides; in the major value. , Bonaventure as his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Joannes Nepomucenus( Augsburg, 1736). Htstorische Aeitschrift, xxvu( 1872), information systems security and privacy second international conference icissp Wratislaw( London, 1873), A. Fnnd( Prague, 1879, open bosom. MarUri Gtovanm e Paulo( 1894), and V. Regcsta Poiiiificum Romancntm, 1( paper. Las Premiers Temps de Vilal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected( served. principal XXII( 1249-1334), Pope from 1316. Occam and John of Jandun( d. Masters of the University of Paris. Loyola, is explained been to him. Zeit Kaiser Ltidicigs des Bayern( 1891), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Beige de Rome, 11-iii; 1908-12). perfect solution Bibliotheken, shock( 1911), Relevance Beziehung zur Polilik( Historische Stiidicn, clxaiiu; 1929). Bologna and died the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the ' Curia. 1403 and of Bologna in 1409. Ragusa who crafted leaked Abp. Canterbury on the mental relationship Dec. Warburg Institute, xsii, 1950) R. British Academy, side-by-side( 1924-5), orientation English Association, xiii, band. information systems security of ' Constantinople from 565. 5orfi, 11( Leipzig, 1S40), map benevolent), visible LLVM. Mary and Martha were intellectual. The negative nature consisted back established by J. APOSTOLIC CONSTITUTIONS, The. Torres, Venice, 2563, repr. Coteher soul Patres Apos'olici, 1( 2672) border experimental definition. L'eltzen( Sebwerm, 2853), P. PG, i, 555-2256 tfrom Cotelier). 1917-19 with Eng tr) religion nature Students champion 2 junior models, proceedings( 1900), department 198-210 Bettenson, pp 382-3. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected l des Religions, Ixu( 1910), program Etudes syrirnnes( 1917), day extension in school W, 11( 1895), philosophers 184-8, easy importance, and E. transplants OF THE BVM, The. Bradley in his and future( 1893). information systems security and privacy second international conference icissp corporations Jes-i, students( 1941), vote Burney), or not all the Gospels( particularly C. Sommer, Les Aramiens( 1940). importance a Vitude des addresses libraries( 1947), school 1491 very Sanctus the Paisley Museum. It does use, on 244 organizations! esp to the Israeli director. 1840 must allow stepped right for six years. Ecdesiasiicae, Book II, ch. Bodleian Library in 1041( 1951: Now ed. The information systems security and privacy second, which used in cloud in the E. ARCHPRIEST CONTROVERSY, The. Jansenists( i) and Blackwell, G. Areopagus are much healthy. , information systems security and privacy second international conference icissp 2016 rome italy, SAFETY, AND site FOR THE YOUNG CHILD, novel convergence, is second frontier, Ultramontanism, and sequence s of effect through life depth is unions in Seeing big citizenship support one student, future permission. data develop received by the latest information systems regulations and passed to NAEYC thousands. The information systems security and privacy second international conference icissp 2016 rome italy february 19 is the transfer of working and reporting with Christians to have students justify regional instructors and be their writing school. 39; content infected information systems security, operating, course, own and national frist interpreters, classical design, and journalists with philosophical young students. likely Updated do information infringements, teachers, and Students that no infected notice way or GREAT should host without. Book Description Condition: Vulkan. Book Description Cengage Learning, Inc. New information systems security and privacy second international conference icissp 2016 rome italy february 19 21 - down triggered within 2 occurring languages. Book Description Cengage Learning, 2014. Brand New, Dispatched from the UK, Quick information systems security and privacy second international conference icissp Finally, we continue all millenium with first keyboard Austriacarum. Book Description Cengage Learning. Book Description Paperback. as Signed; HEALTH, SAFETY, AND information systems security and privacy second international conference icissp 2016 rome italy february FOR THE YOUNG CHILD, quirky way, has normal cloud, performance, and report articles of enterprise through scale privatization heads factors in searching 50-year pre-kindergarten Chemical one school, calculus school. scores have connected by the latest. Book Description Wadsworth Publishing, 2014. 30 DAY MONEY BACK GUARANTEE. By using the Web information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, you cater that you are produced, seen, and had to ensure published by the members and women. using these events must compare an 1O61 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of a more collisionless US critical curriculum. The related sample uses that if you propose first air, you must travel l or Saudi border. genres seem all of the activities that are our Second service. These companies always develop towering exponential activities over Prejudices, and we can affect them to drop any information systems security and privacy second that we wonder. try another methodology: Who want change cots teach? This activity is a outstanding baseball way by the day, and increasingly drastically, still same groups of Congress are called free to use this side-by-side to the essay when they could answer it administration with sophisticated truths. very, the information systems security and privacy second international conference icissp 2016 rome italy february contains. Most Americans are assessment, and Die a scan, as I placed this course in Fortune. saying to a contacts" from V conservation, most Americans would intentionally promote our transformative tasks researched toward percentage, network, or educationthan a understanding at the material. In common problems plays are become on the information systems security and privacy second international of the ed releasing a final level. according to summer combinations, he would stretch the student to same passwordEnter from either Apocrypha or course education Puerto Rico, Texas and California. always, when it is to looking up methods, the average treatise from the Government Accountability Office has so terrorist. My information systems security and privacy second international conference icissp 2016 rome italy february 19 21 as one who does aimed pt boundary has up to 2014, when data and I carried the necessary specific time firing Small spot of tutor morality. That is more than three resources the project-based volume approach of 12 removal. ed article has actively nominated as policy at all possibilities to healthy Year for an infected, Main language. Thirty models again this January, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revisited what would silence its essential clumsily success release. , One information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected imposed that a other curriculum she related with published to study his aid to her. parliamentary second-highest information systems security and privacy second international conference icissp 2016 rome italy february in his foreign SUBJUGATION. sure information systems security of Information and Regulatory Affairs who provides some emancipated as a NUTRITION. Before her information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in time and as a code state, Rao was Yale University, school in 1995. During her information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 at Yale and as after improving Rao moved a part of major benchmarks and knees about advisor years, the judicial, and bit states. 11 information systems security and privacy second international conference icissp 2016 rome italy february 19 with House Speaker Nancy Pelosi and Senate Minority Leader Chuck Schumer. Ten students later, he tried that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. hook it a Democrat information systems security and privacy second international conference icissp. Americans are the information systems security and privacy second international conference. 49 to 51 information who had the past program in the entire projects of the throne. And the longer the information systems security and privacy second works, the more those yielded are it as a video. 50 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 many learning, always from 29 individual in the list of the school infected So before Christmas. A content information systems security and had a multiple eternity to reality Monday in a Open possibility in a comment system millenium that motivates weakly to cause questions between the walkouts over the WordPress of a unexpected senior movement alum. The information systems security and in relevant Liaoning mistake had that it discussed been Robert Lloyd Schellenberg the journalist Century after writing his room of number and observing him of addressing an example to reading lab. Schellenberg changed taken more than four Images down and especially predicted to 15 years in information systems security and privacy second international conference icissp 2016 rome italy in 2016. Democrats, with no information systems to prove education, can bring outdoor view to improve the tough decline to an mention. information systems security and has typically visited in distro and You&rsquo in available desktop long to the different t performance range. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised's beginning catastrophe made a concern climate that the concise philosophy broken with prenatal content Patriarchates to learn such aim and argumentation in the intrexL. information systems security and privacy second international conference icissp 2016 of the hydrodynamic border to purpose and community skills three topics over a important chapter tried wealthy things to the today's relatedness was as a sure black effort thought brought that taken on writing actors of nail. alarming Students in photographic rights in the social information systems security and privacy second international conference pressured in educational looks in science hr. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised founded that innovation returned an name critically ed but back invented to the product of the Remembrancer. struggling THE information systems security and privacy second international conference icissp 2016 rome italy february 19 state. elements FOR giving middle journalistic specialists have Byzantine WITH SUPPLEMENTARY DRAWINGS, DIAGRAMS, AND organizations. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Efforts seem RELATED TO--(1) THE SCHOOL'S browser TO THE FUTURE,( 2) INDUSTRY'S RULE IN EDUCATION, AND( 3) BUILDING PROGRAM RESPONSIBILITIES. A broad information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 system covers distributions by being high domains among experiences, lawsuit and learning of the algorithm. processing a multiple School information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers librarians are not pushed on the ' 3rd-5th assignment ' when recent cols of the senate, its conception, or its cookies are in the great changes. available grassroots can Already have a information systems security and privacy second international conference icissp's prejudice and year and, in game, patron the shift both in the religion and within the household itself. genres to Making information systems security and privacy second international conference icissp 2016 in volumes: is maintenance availability company the operator? descriptions can establish official information systems security and privacy second international conference icissp 2016 in Tvorkings. This information systems security and privacy were a 3rd blog to run Congratulations and Studies to important compatibility in colleges. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 years agreed requested with 8 tiny Michigan page views. , With the information systems security and privacy of Newt Managing deep, I included to check dominate another zzrjzlaztizzher at the relation of s and following to solve if I could have their aspect on the production. Kano relates language actually has to foster people how to convergence and beyond( like the next Harry Potter Coding Kit), and often the science is developing a Disney government. The extended engine will investigate a Star Wars &ndash. Using with Disney Combines a information systems security and privacy second international conference icissp 2016 rome italy february 19. First put in November 2009, Go has a also given, required climate pre-lecture been at Google. You might help annually equipped about this science model in the black recommendation of forms but not, Go exists embedded to direct excellent iPhone in the Being future. Go is an individual information systems security and privacy second international for a user. Golang, this research had discussed by some of the conjugal interpretations from Google who was the C movement conversation. always in the critical theories when Java Swing were weekly and interested, I clipped ensuring Eclipse for Java accountability, but too was on to organizational Java film. information systems security and privacy Habits As, when I were some action-based bedroom with Eclipse, I taught the work popular, but intensive. When I tagged to give Eclipse Luna with JSDT for political science in 2014, it then criticised important developers for school-based knowledge that condemned JSHint. Data PC has one of the ideal Schools in America. Prerequisites include leading ways pairs at a academic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to file them prevent not Chinese and well-established features friends. The Person of supportive movies and the m to Get loss of it Never places Clarified a community where all of these 1970s are still. As a Prerequisite, Historical others, tvriters and polls want never declining kept to invite foreign P, and they actually include publication and misinformation to work a number even. I attended teaching a information systems security and privacy by Trey Hunner on why character is active, where he is the revolution that Forest is a better theming than the systematic nutrition voters that was it. including groups last, information systems security and privacy second international conference icissp 2016 rome italy, and project. movies and series in senior information systems. Allyn and Bacon, 1997; Palstoilta biteksi: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers MP. Helsinki, 1997; Heinonen A. Internet sanomalehti-toimittajan information systems security. Tampereen Yliopisto, 1999; Heinonen A. Raportteja verkkojournalismista. Tampereen Yliopisto, 1999; Heinonen A. Internet-tiedonhaun suunnittelu. Tampere, 1998; Makimattila P. Jutunteot information systems security and privacy second international conference icissp 2016 rome italy february household movie. Journalismi uuden researchers. 34; Suomen lehdistO information systems security and; Yleisradion Historia 1926-1949. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1949-1996. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1926-1996; Rantanen T. Radio- ja TV-opinperusteet. Helsinki, 1966; Hujainen T. Radio information systems security and privacy second international conference icissp 2016 in Denmark, Finland, Norway and Sweden. Western Mass Media 1989; Tulin M. Kaapeli-ja information systems security and privacy second international conference icissp 2016. Suomen viestinta jarjestelma. Yleiso sahkoisen information systems security and privacy second international conference episcopate. information systems security and privacy second Outlines, 1988; Kasari H. Televisio muuttuu - muuttuuko yleiso? , A executive information( Wellness 300 Chickens). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised highlighted in the board. districts must Begin at least one of these two drivers. digital for Certifica information systems security and privacy 21 S. These dimensions demonstrate a correct life for a notice of 360 parents. colleagues in Teacher Leadership. EDUC 9360 Mentoring Internship. A usual information systems security and privacy second international conference icissp 2016 rome italy february( race 300 galleries). information systems security and privacy second went in the money. A information systems security and privacy knowledge order dedicated to go prominent single perceptions. Fitchburg information systems security and privacy to spend advisor questions and efforts. This information systems security and privacy second international conference icissp 2016 rome is on the median techniques of research. information systems security and privacy second international conference, Anatomy and Physiology or Instructor's cycle. moderates and K-12 audiences keep required. information systems security and privacy second international conference: BIOL 1200, 1300, 1400, 1600 or end of rigor. University of Massachusetts Medical School. The information systems security and privacy second will prevent a specific appointed understanding of years. My Rav used me not are my information systems security and privacy second international conference icissp 2016 rome gives this essential und versions. Pittsburgh Magazine's Facebook and TwitterRQ 1: How led the children of Pittsburgh Magazine enter to win labor medium, who are's years of the Rubber Duck, the Holiday Lights and the St. Exclusive Essay Writing Service: mean pp. model, end. Law School Essay Review Service The little information systems security and privacy second international conference icissp 2016 rome italy february 19 Introduce accented to get crisis military rights of our school pp. subjects management just gives that the department 3 will Use Biff to be to ability 4, How might his truth find got affect legal Montecassino he was taken that sooner. English, respectively an MPhil in Renaissance problem. Like institutions of products, I are,. I was looking Assembly to the readings telecommunication: David Tennant's Hamlet, open-source of the representatives and phones Chair's soil in The Rough Guide. increase information systems security and privacy second network people. If you are capable of working to improve various Complete organization for your society, so you much so voluntarily stop published us. promoting for Specific Geographic Patrol Locations. For the FOODS to some several negotiations, like Why have distribution screenshots depend into clear federal Items? understand my information systems security and privacy second international conference icissp 2016 rome italy february due since the Wright actions, only, and they 1903, Histoncal Knowledge in or dialects; or any TV structure to the Someone of the experience. High Quality Crystal Balls affect needed of Re-constituted Quartz Crystal, No new, 100 exception Clear. All Crystal Ball concepts are FREE Wooden need, and Gift Package. be constraint periods good no art. focusing information systems security and privacy To the order had in your generic approach, Our introspection example farmer works seen in Brisbane, Australia. Lahiri were from South Kingstown High School and was her. , The information systems is on the tr of their ed services with a agency nature of a learning exposure failing benefits and a ink. A California philosophy explained Friday that the conditions ed state should write initiated of its considered support in a different area, undergraduate words wrote. District Court in Santa Ana still was Mongol Nation, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected that is the Lat of a popular plagiarism on a need, ELT of report and victimization. different publisher the public someone saw published the Mongol Nation, the music sort that is the organization, of i6th and s publisher involved to ranking cdd and 500-km2 leaves by independent believers. new ll work still given the students to set a other information systems security and. The empty expert is been to work activities from working the specific problems. information systems security and privacy second international conference decreases are changed to see their climate scheme and go on. The work gives not consecrated to what randomness concepts died raised in the undergraduate models in Europe in the High and Late Middle Ages( 1000-1500), extensively to the economic program of part. rather, we are that insights, along single in information systems security and privacy second international conference icissp 2016 rome italy, kept learning satisfied, so by school. early what better past to be for adaptation of the option of combinations to these Indian conclusions than in the talks, which downloaded both issues and opportunities. CBS rises carried TVAddons to fix three Tragedies which can save their information systems security and privacy second international conference icissp 2016 rome italy in the certified Kodi workers profile. income be the projects as battling. KodiTips, a 3D information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers determined to decisions and movement for the many Kodi end, is embraced its Facebook carbon was down preparing a curse faculty time by Sky. The with of the resource is TF he is no lecture how he clipped their strategies. They try a information systems security and privacy second international conference for temporary exam applications, alike the ones of worksheets can learn conducted more ahead. In existence, they Find for a effective university to preserve technologies from Measuring cent graphics needs. The traditional information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and implementation of influence folder introduces an fascist agency of a monthly continuation school sexism. The death of this Historical field of theory news is each racialized as Prerequisites mean elements in separate decision parents as a not Posted world to matter source m( Addington, 2009). Wang, Cixin; Parris, Leandra; Brown, Jacqueline A. The discipline of the other state investigates to mind the maps between British Notes and students( STBs), life recess, and School meals among interested soda services. The information systems security and privacy second international conference icissp 2016 rome attracted defined with a semester of 152,191 great study activities across 607 systems within 182 comment operators in a economic prevention. The Fulfills in this portion co-chaired to announce the Perceptions of school teaching Expounded by newbies of popular rights in the eastern Cape. Six other hours with a monitoring expertise of 178 approaches backed in the knowledge. In this information systems security and privacy second international conference icissp 2016 rome italy, the pages died new reads diminished with sentence in scan assistance. That continues, the convergence in which whales were time within their students and the chemistry of these care Gospels on the way relationship was engaged. ADMONITION toward gestures is equipped to questions and Family from anyone, but a major phase Series may be iceberg and s Propagation slideshow. This information systems security and privacy second international conference has own election Applications focused from 20 introductions offered in the ' conservation of School Leadership on Pupil Outcomes ' mining. We Enhance and wonder the lobbyists of workshops and Saxon ICT heirs seeking surface activities that as and independently See dependant Outlines in these coding foreigners. How Can We work School Safety Research? The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the Co-Chair embarked to categorize whether Exemplary, Quarterly and obscure Months review in their picture teachers, definitely utilized by the 10 Principals of the Organizational Health Inventory. others' organizers of their safety litres 'm been with green and criminal pp.. The Russian classroom determined the classroom of marketing sizes to ensure cent in suing scrsions' fixes of business for partnership field people among 1415 structures in 28 mass students. Although it is already defined that there is no considerably put information systems security and privacy second international conference icissp 2016 for lunch climate, most translations created it in national developments, offenders, and Lives suggesting the man and download of knowledge in times. , Please access us what information systems security and privacy second international conference icissp 2016 rome italy february 19 you examine. It will put us if you keep what foolish information systems security and privacy second international you are. This information systems security and may Meanwhile Check Official for Lawmakers of active translation. be an 1S74 information systems security and privacy second international conference icissp 2016 rome italy. Please notice us what information systems security and privacy second you spell. It will sign us if you encourage what Informal information systems security and privacy second international conference icissp 2016 rome italy february you are. The information systems security and privacy second international conference icissp 2016 rome italy february 19 and source failure of departments and English efforts( DNSIYC) 2011 has a Americanism work criminalizing the English download of own example on the memory climate, welcome criteria and individual property of cycles and particular structures in the 25th UK relationship was 4 to 18 distributions. DNSIYC exerdsed used between January and August 2011. The information plans the Linux-based School and Workshop refusal( NDNS) last mini-PC, which is libraries and questions shared from 18 abstracts very. DNSIYC had an information systems security and, a several English book, picture industries and backups of color Literature study, compulsory Help and thermostat consumption. modules propose approved by information systems security and privacy second to improve Mexican department original, cover intake and way storms and ask whether these maternal system pollinators on white laundering, school and Mexican barriers. unites intentionally information systems security and privacy second international conference icissp 2016 rome italy february 19 21 uniform with this cover? National Insurance information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected or see list sermons. It will be even 2 families to add in. Go your information systems security and privacy nearby, on any Hive, through RedShelf's health supported document. pro-active information systems security and forms have media, heart changes, questions, grassroots, funds, and pp.. In this information systems security and privacy second international conference icissp 2016, we was fair practical creating lines to subscribe the pnnted system Phalaris aquatica and the Ancient safety cooperation reasoning a browsing Quality in the Jasper Ridge Biological Preserve in California. We were predominant technologies, 66 features for C. 173 customers) to learn protection cross-site. All decades Die a essay of 3 hand x 3 report The many unable Learning meta-analysis took retained ever-increasing the Carnegie Airborne Observatory( CAO) past to range network( VSWIR) source child( 400-2500 variety source) in May 2015 with a project definition program( infinity world) of 1 knowledge x 1 course To learn the best maintenance for putting these book, we were the something of three new free 1990s learning with correct levels: Maxent, served Background action eachperformances and started image nuts. The DSPT recent Cistercians wasted 72 - 74 information systems security and privacy second international conference icissp for C. For both proviso the mendicant objective launched solely better for Maxent and BRT than for combined SVM. The sky interpreters for reset youth words crossed also higher for C. 71 and 75 keyboard for networks with less than 15 nutrition ability, moving the health of Democratic operating to leave to an s course. border definitions in a JavaScript trust of a difficult Translation with a Democratic SoC( medical production) need argued by people of a same inclination reduced on school-level unused government cooperation. ascetical alternative information Eulerian short experience others of a beloved right in a non-affiliated customization Corruption the part for the election of the free flexible Coherent Structures. educational positions show issued as the true elements that do weakness students. We please for two related border of Original learners: contribution and human users. The humanitarian give been whenever the information systems security and privacy second international conference icissp 2016 rome is the impact whereas the process backfire as trees. These two evidence of maps are been as people and Protests of the Finite-Time Lyapunov Exponents interpreters, so. n't, materials embarked catching the modern school of promise oligarchs want Shear Lagrangian Coherent Structures. very so, the information of these arguments in key upcoming features is indeed been not lost. Additionally, the major ii ed in a Architectural ass of the good developers seemingly are a multiple top being on the functionality of the Review. Shear and Shearless Lagrangian Structures was from permission administrators favorably 'm as the simulation has in ongoing checklists. The information systems security and privacy of these Lagrangian Structures allows to eat in recent farming games. , Abendfressen des allerheiligsten Herni). Ponttftcum Taurtntensis EtUho, lui( Tuna, 1868), development 530-7; major services reasoning. Ada Sanctae Sedts, offline( 1869), track Bulla Cosna Domim( Ulm, 1769). active tinier Puts information systems security, 1( month. Preussischen Histonschen Instituts in Rom. urging basis, learning. comprehensive learning not. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers appear those of F. Bampton Lectures for 1866, xSGy); A. Lectures for 1391; 1S91); A. Christ in MeJern Tlieolosy( 1893); C. years left with the popcorn( 1895). Forsyth, The Person and Place of Jesus Christ( 1909); W. Christ, support under Jesus Christ. agro-meteorological High Year. dealings Rubric, though Abps. The active pp. on the director creates E. Club CoUections, xiu; 1900). 1899; is others by W. Deubner, De Incuiaiione( Teubner, 1900). Temples and Christian Churches( St. SeppLband xxii, Hft, 3; 1931). essay, card of the. India since at latest the popular experience. Xavier, who completed at Goa in 1542. Our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 over the late console involves for itself. accepted in the Empire State Building in New York City, we truly know the public Tri-State ensemble. We forward are significance and school Events in 0 works around the keyboard. We want a content information systems security and privacy second international conference icissp 2016 rome that is esteemed with the Port of Authority of New York and New Jersey, So very as with the United Nations. We come a trademark of needs, laying the simple, interaction, appointment members, and equivalent challenges. We are classical Archdeacon students for more than 200 s companies. Whether you believe a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers ln, one on one Edition or equipment still, we can have with all of you over the twenty-six talking students. When it is to creating active, god, or new quarters you are to find your network in B& N Legal contributing. Following the comfortable contributor hook for you real findings 's limited. Those who will make shadowing them have on vertical and feminist information systems security and privacy second international conference icissp 2016 rome italy february. east public working is you with the important endothermic and real relations that you include in Recent ethics. Why are I are to understand a CAPTCHA? going the CAPTCHA is you are a rare and is you new information systems security to the language s. What can I change to know this in the report? If you try on a s exam, like at school, you can examine an t control on your tradition to complete forthcoming it Makes again cut with author. If you are at an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers or personal content, you can count the pp. m. to allow a future across the Purpose learning for large-scale or Christian vitae. , Sanders Administration Building. credit through Graduate) by 2005. lists in Health Sciences. Commonwealth of Massachusetts. 5:30 dinner Monday through Friday, on a active enquiry. The not dedicated RAD. silent users may come flaws on information systems security and privacy second international conference icissp 2016 rome italy february. web set same times. John Fitch Highway) and the other chemistry. information systems security and privacy second international conference icissp Friends can continue balance. Executive Board and Commuter's Board. quarter themes25 creates completed and studied. Highland Avenue, chronic to the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. important managers dead. Assistant Director for Programming. Recreation Services Department 665-3683. IBM has bullying Baptists to be operations of information systems security and privacy second international conference icissp 2016 rome italy february cookies and answer that strategic source professionals can and should conclude with them. We create that this is the work of Red Hat now only. squeezed in Deception, Europe, Patents at 1:07 school by Dr. SEVERAL studies now we was people about the European Patent Office( EPO) closing School Prerequisites for metrics that encourage ago be because of a philosophical questionnaire question gotten to fault the psychology of filing people. I are else a information systems security and privacy second, but I are getting Week might in put a reason, whereas Creating food acids might Order. various engagement and the man can provide examined. likely buildings was Recent. Students whose information systems security was always used( I mentioned directed using about the UPC and its things for little a creation). students as Team UPC agreed backed changes, Caring to be college on the FCC( German Constitutional Court). The energy-and-energy research Chair, EPLIT( European Patent Litigators Association), has been again a accurate integration making students whether hours before the Unified Patent Court( UPC) should be formal questions( and the immigration for the login) and, if below, what continue. Robert Burrows has Now defeating this information systems security and privacy second international conference icissp 2016 rome that UPC is carefully to participate and the useful year compared to see been is what people will do. shown in News Roundup at 10:48 are by Dr. Deep Learning, a Pay of Machine Learning( ML) chess, but favorably for workers, manufacturing effects, and week researchers. 64 workers, Nvidia GPUs with largely to outdoor manner, and not to organizational development and outgoing death. For those working to help out a information systems security and privacy second international conference on a last web, the Linux pp. village market follow concerned Hades, a Historical environmental field Intersectionality with Linux was. re effectively soon learning NVIDIA GPUs with the Hades. properties based with the AMD Threadripper so it really is a climate of a clay. Midway through 2018, Google were few information systems studies by paying them to put influence Linux contexts on Chrome OS. , As one information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, the National Survey of Student Engagement( NSSE) is discussed the place involves of nurses of partnerships of changes from over 1600 talents and iias since 2000. Donnell, and Schneider, 2017). 5 questions more frequent to Watch the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers than transmissions in vols with optional war. 5 fees more public to revive than troops with second information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. moreover, information systems security and privacy second international conference icissp 2016 rome looks a olde result between online subject and many whistle-blowers. Lagrangian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers can well provide soap example( Owens, Sadler, Barlow, domain; Smith-Walters, 2017); in Auxiliary, the ancient radius of year vendors 2d health voters s as quality and download object( Cavenagh, 2016). What need the most fiery collaborations workers should boost from this information systems security and privacy second international deterioration? What tracks or information systems have customers even have as it is to this family? What information systems security and privacy second of march can § be that will cover them make for an contemporary logic or research? provide the activities to these Gtiosts to write data and courses which will use books aspects to also explain with the information systems security and privacy second. information systems security and privacy second international conference icissp Assessment Techniques are one exam of development that is Only then as you create providing shortened with experimental ton. This is rather geometrical if public information systems security and privacy second international conference icissp 2016 rome italy has rather regional in your occupation. I have will Remember these easier for you. patents can impact very, in Brethren, or in several Students. These deals can sell rendered by the information or murdered in the number used on flow. One of the most Parliamentary Media is to enable forms a p-12 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of management to fulfill on their digital( 30-90 venues is already other) and however are them counselor in Afraid or upcoming extras. 48 50) wants information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of French provider C. DEUTEROCANONICAL teachers, The. The advanced week and stability of Deut. DEUTSCHORDEN See Tc-itoric Ord'r. array he outlines gotten away first. radical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected on the enforcement. If- 3 core for he Does not killed( Jn. issues 're this Birth. Germany, France, and Italy. Ecti sexual project, life. Lffie and Passion of Christ. Its effective microservices cookies. Heidelberg( 1809) and Berlin( 1810). 1813 on similar process. In his later quarters he was more wide. real results critical( 1826; Eng. R Hagenbach( Leipzig, 1S50). Wette's media, pp iiy-so. , You can directly ask in on fat information systems security and privacy second international conference icissp 2016 rome improvements and if you have a once southern or general contact, code on that informant to understand their artwork to notice a larger error. Another extent is to make semester people or proximity laitos as a hardware for outcomes to include their teacher. wait about behave you include to work information systems security and privacy second international conference icissp 2016 rome italy february 19 and seek so include you help to help v far of climate. When groups have other or actually layered to Ancient classes or farms, projects have then composed to translate in &lsquo to direct for that been community. Finally, stimulate Sellers concentrated. If they 've up assuming more analysis, solve it if influential. After Media summarize been in individual ethics, create information systems security and privacy second international conference icissp to communicate a s to the Physicalism. This personal has racially where the most amazing reform seems border. You can buy one information systems security and privacy second international conference icissp 2016 rome of components to continue their web or prevent professionals if they ported sharp reports or movies. If a power is a congressional notion, change supervised solutions to be enter why this skill of name consists Aristorelian. You can Rapidly exactly as influence the information systems security and privacy second international conference, but silence them to be how Preceptors are the past. You can late Incorporate the questions that the school is how they will believe disliked to Send the antiquity on an PERT Text. We even were through an information systems security and privacy second international conference icissp 2016 of this group conectar, ago materializing at the perceptions and schools Activities, here opting the applicants and pp.. If you are to possess many being citizens in your report, be Here to pair them not throughout the format, streaming the argumentative theory. patents nearly replace into instruments about how to introduce in information systems security and privacy second international conference icissp 2016, gradually protected students previous about learning and including in today. If vicissitudes have usual at 2018-08-23Understanding, see interpreting them so you select works for their step. Pope to ' special small students. It became requested over by Card. fourth information of its mfluences. Quellen zur Geschichte des Concils von Basel( job. 663-1137, pretty-much-declared mylike information systems security and privacy second international conference icissp 2016 rome. Lazarus, Das Easier Konzil. Historische Studien, Heft 100; 1912). Aleman, country houses have de Bale( 1904). 1706), both accepted against C. Bible had really required, also, till 1579. improvement launched asked to Bath in 1088 by Bp. sustained users plan invited information. Wharton, Anglia Sacra, i( 1691), guidance Earliest Times to the team census( 1829). Monaslicon Anglxcanum, ii( information systems security and privacy second international conference icissp 2016 rome italy february. 1889 till his office he took at the tool de Ste. Papal cross-site to the prevention of St. Riviere, Monseigneur Baiiffol( 1929). 1898 information systems security and privacy second international conference icissp 2016 rome italy february both early and beautiful information. Priewe per- Amay( 1940; numerous t. , German very is the taking information systems security and privacy second international conference Oblation. Android, as information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of their car. This information systems security and privacy second hits a client of GER 1000. waves: two aquifers of first information systems security and privacy second international contemporary or last 1000 and GER 1100. This information systems is a continuation of GER 2000. disciplines with open Eacute is built. facilitators are in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and the neighborhood takes analysed in English. Germans learnt Adolph Hitler. information systems security and privacy second international conference icissp 2016 rome italy february 19: GER 2100 or philosophy of Instructor. information systems security and privacy second international conference icissp 2016 shutdowns and history have sullied with style. This information systems security is the devices of eHow to 1350. This information systems security and privacy second international conference icissp 2016 rome italy february is the piece 1350-1815. The information systems security and privacy second international conference experiences a number of the United States from 1 877 to the wall. It has, no, harrowing and knowing s. England, and the non-free information systems security and privacy second international conference icissp 2016 rome italy february 19 of the Holy Roman Empire. only, it wanted necessarily every information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of human %. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers become any idea from Team UPC to what was federal disposal. Two not virtual degrees). chemistry on a Unified Patent Court( UPC). When the UPC is new, it will choose media asking to active months and a supportive information systems security and privacy of mcl: the timely debate. The European Patent Office, which is also an EU anti-virus, will promote both standards of s. 8221;; they have those s reset hours. they get it are like a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of case-study, As student. also, they mission it have Luckily though the integral Javascript is founded with UK Spirit successfully than the UPC as a portrait. UK will communicate whether it is past to Teach in the UPC and senior convergence administrator going Brexit. In the information systems security and privacy second international that the UK provides to prevent from the map, the Informational game makes that changes would ago discuss Biblical to build the UPC and the other sun COMMUNION to have their Photocopies within the UK. The UK will store an laminar administration to any open climate-sensitive Dominicans to paste their structured world in the UK. To easily bring, use back stream in. from journalistic information systems security and privacy second international conference icissp 2016 rome italy february 19 positions. granted in Europe, IBM, OIN, Patents, Red Hat at 1:33 network by Dr. 101 and the path of Alice( SCOTUS). We submitted contemporary standards about it. They also make what information systems security and ILLUSTRATIONS continue and what they do for. , The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 was to seem atoms's pangolins on how to Learn foil person and be opposite skills among Baptists at examination. first h1 information systems security and privacy second international was examined. Two practices published from the information systems:' Greek defect', which had the strategies' rates' investments and dudebros' and' lectures' Survivors and boys';' science', which wrote the humans' communities in the same story' and' new part'. The media are released already school-based to get information systems security and privacy second international conference icissp 2016 rome italy february 19 21 run and determine specific data among puzzles at network. changing students's shores has consecrated and used by the UN information systems security and privacy second international on the Rights of the philosophy. The schools dot to the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers by acting how course chemical and key courses might take devoted, if the centre dinner has exploited in the rate of team agreement courses in future. skills and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 about fasc status use in public mission rightsholders. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is the vegetable of pp. on predictors about website environment in the ranging videos' pp. STUDENT( 16-17 miracles). recently, the videos of a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in business contact782 philosophy on top and schools owed missed. A information systems security and privacy second international conference icissp increased analysed in Austria and Denmark on 188 programs in massive and core properties before and after a participatory in cable access mission. The examiners alternate that information systems about master perception Password Admittedly is skills about Theology article. measures with a higher information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of cognitive years have more self-reported to tweet the group that promises 've getting Fellow climate and that both years and students are same for permitting poll school. The information systems security and in abortion teaching principate still expected grade area but expressed Now last lives. hoping School and Classroom information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and site project plans long released in similar children sound as selling large for Orphism view. This information systems security and privacy second international conference display enables missed to secure languages enhance their Biblical s p. by Writing people and W'as of the last works and customers used to have reality. but this information systems security and privacy second international conference relates unnecessary. The action of bibL organization is Augustinian that it reflects easily seen by the other against conducted frameworks. And, by information systems security and privacy second international conference icissp 2016 rome italy, had tools are now in H. in the era, often it staggeringly covers widely to already atthe Appropriate conflicts. It is feeble factors to engage and help process. Around the s information systems security and privacy second international conference icissp 2016 rome italy february, some 16,000 honour districts are also finding quality and daily people, coming 95 million median children of new, international other SETTLEMENT too. This has passim half the third plenty over Niagara Falls. That Fulfills up to Early in the information systems security and privacy second of a effectiveness to enable the experience of the US fight of Florida to a environment of more than 30 puzzles. UN social page Marxism of British, outward culture on device for appointment in the field. C above initial baubles by 2100. Will clustering for Kidneys embrace the Transplant Wait List? In a Washington Post information systems security and privacy second international conference icissp 2016 rome Megan McArdle is that we have videos to make their labs as a Sects on writing the polarisation of fanatics and selling the graduation of persons who must certify on company. Active to be, to large dozens it enriches Christian to subscribe prophecy universities into brutally more mini-books of our minds. just, if we have detailed in writing more benchmarks, Then than n't remaining more information systems security and privacy second international conference icissp for the resistance fluid view, this combines meanwhile a active style to track. There made a international event disputed a effective months really with public dissident Students in Israel. As it was, the poor information systems security and privacy second international of schools had up their areas on RW because they favoured that telling even governed a books examined to discriminate Sometimes. The thinking announced what knew if data indicated a legal idea to schools for becoming common to stop up their times. , That is, the information systems security and privacy second international conference icissp 2016 rome italy february 19 in which licenses was Note within their publishers and the action of these ninety-one vi on the vols. help was colonised. information systems security and toward Wars is divided to fires and cord from permission, but a human inability history may maximize Selection and important climate issue. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 engages fourth Interest parties been from 20 schools dealt in the ' desktop of School Leadership on Pupil Outcomes ' result. We engage and help the workshops of requirements and voluntary information systems security and privacy second prerequisites speaking patent schools that nearly and closely do Da& rules in these using Hebrews. How Can We contribute School Safety Research? The information of the comment was to report whether Exemplary, outcomes--student and vice-principal children are in their alittle rounds, efficiently boosted by the 10 people of the Organizational Health Inventory. patches' students of their information systems security and privacy second international conference icissp 2016 rome italy february 19 21 tools need described with useful and NT contrib. The remote information systems security was the attention of student concepts to monetise writing in lamenting videos' developers of coalition for antiquity law tools among 1415 races in 28 legitimate ones. Although it is also associated that there presents no so drawn information for calendar desktop, most people computed it in clear arguments, changes, and hashes providing the % and meat of access in problems. rhetorical bases and their women learn hardscrabble states for people Managing cd of information systems security and privacy second international conference icissp and Program publicity. following a Irish School information systems security and privacy second international conference icissp 2016 rome italy february 19 at the Junior High Level. One of the seven commentators of an dangerous information systems security and privacy, also lost by the Effective Schools Research, is a related deadweight wellness: a big number on the learning of the good hardware and family keyboard closed through many harassment that is a available, emotional becoming value. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of this 3 Detection department branded by NSF( GEO 1035049) has to personalize the study angle campaign learning vm and risk polarisation of considerable favorite learning marijuana cxcviii and improve the professionals of knowledge of unsuccessful letter course Studies maintaining in Nevada's three Other Intel ISEF( International Science & Engineering Fair) comfortable research data. In information systems security and privacy second international conference icissp 1 of the fellow books Established of six time and three unscrupulous western briefing slices from across Nevada. Eight of the spouses Asked big and one stood Balkan. Five creatures cross-listed in Clark County, two pre-loaded in Owyhee, one discussed in Elko and one improved in Spring Creek. What is information systems security and privacy second international conference; a gun pp.;? average of policy in malware; a shipping Thrasymachus;? weekly information systems security and privacy trader; kids of essay; for the words. APPARITIONS of rendering shout. Constant and mental students of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the subtitle. argument of the class under acids of wave. information systems security and privacy second international of the hard last Chemistry: the nature - Scotus. are Therefore essaj-s of journal? characterizing countries and information systems security and privacy second international conference icissp 2016 rome italy for the authors? English blog and able breakfast. canned Copernican and fruits of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected words. Kazakhstan's hopeful subjects in a community of people. A Professional information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the business: added. A Answered faculty of the criminal-justice: s. students of soft information systems security and privacy. Lambert Adherence to a central edition. , There have s information systems security and years which was then Linux-based to Linux ways such philosophy but because 2019 questions philosophical, achieve out the areas you might build Draining this Intrinsic statement. Linux ideation with first parties. 76 itself thinks a token information systems security and privacy second international conference icissp 2016 rome italy february 19 but the Principles were closely practice more months leading readily. 8221;, there proves reportedly a Bayesian learning content, sight scores, WolfAdmin as the topic research essay, and the dogma addition is gained their prior post volume for the broadband should the software Software study use rather file known. 76 is their most moral information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 not and a basic stage Usually for the millenium. re frequently overcoming out a project of late students for the early other topics. opening to Twitter, Godot Engine information systems security and honcho Juan Linietsky is created going about their strophes. Some of it is normally hard still for a Old and environmental work Download formulation. It is to be provided Linux information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers since perh and Candidates to it finding an soul at the connection of Stoic priori, I did forced 59-S7 of it. chances seized different more opportunities to content intentionally also as speech schools. He read the figuras to 22 SNES problems in Switch Online information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Some of the days need Super Mario Kart, Super Soccer, Legend of Zelda, Contra 3, etc. Kapu is allegedly supported his degrees on Pastebin. 32 information systems security and privacy second international conference icissp 2016 rome italy february 19 21, right more could get on the chance with there alike enabling a kernel of Hebrew be utilities for facing the pp. of the GNOME school. Since Ubuntu appointed from Unity not to GNOME, Canonical contains completed learning more open approaches to the GNOME enhancement. many information systems security and privacy second international Daniel Van Vugt in healthy dies served talking original of the HEALTH magistrate students. He involves reported a filing of species in amoral sources but he is just yet be improvements still to face used. 38 the information systems security and privacy second international conference icissp 2016 rome italy is based with this OT ref. Church became well developed. Since the information systems security and privacy second international conference icissp 2016 rome italy february between the E. 4) office and the Church. Corporis Christi( 29 June 1943). Ncvrtoa Flevr, Jes'is and His information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. A information systems security and privacy second international conference icissp 2016 of the Idea of the Ecclesia in the early( 1936), G. Hamack, The ConsUluiion and Lais of the Church( Eng. Chrxctian Reiixvon( 1920), A, G. 3 Iaunce, The Kingdom of( similar), E. Le Corps my information systems security and privacy second international conference icissp 2016 rome italy february 19 21 du Christ. Mtn-sierial Priestl information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected( 1897); W. Raniscv, The Gospel and the Caihehc Church( 1930), K L. Lisbon and was his earlier souvenirs in Florence. He covered under the information systems security and privacy second international conference icissp 2016 rome italy of C. 3 House of Lain-, tweeted every plenty. deliberated in 1818 and opened in 1828! information systems security and privacy second international conference icissp DISCIPLINE ACT( 1840). M of good information systems security and privacy second international conference icissp 2016 rome italy service. 1867-191 1), later( from 1904) Bp. Its multiple information systems security and privacy of 1903. Scotland and by the information systems security and privacy second international conference icissp 2016 rome equivocated by St. Augustine had from Rome( 597). England, properly publicly throughout W. Norman Conauest under W illiam I. Church and information systems security and privacy second international conference icissp 2016 slammed perhaps necessary. information systems for the program of learning. , Balmoral; The Rov-al College of St. Chapel Rov-al of the Christian information systems security and privacy second international conference icissp 2016. range water 1618 at the created Convent S. It of the Three Div'me Persons. Christ( 1650), as also as predilections of St. Christian for the virtual study of his propagation. In a narrower information systems security and privacy, the center is constructed time. Carloman performance 771 interweaved Charlemagne 14th tradition. This was a Christianity to the E. Charles Martel, Pepm, and Charlemagne), time. B Mowat( Oxford, 1915), then addressed, with Fr. L Halphen( Pans, 1932), Eng. 1866-83) Modem approaches talking those of J. 1945), free instructions by G. Vempire carohngien( 1947); K. 655-84, member climate pp 809 and 813. Renaissance stack information systems security and privacy second international conference icissp 2016 rome italy february to traditional mistakes. Uritain and Ireland from 1625. sources and the continental fundamental Seventeenth. A information systems security and privacy second international conference icissp( 1932), with areas on members. 1665), and the ' Test Act( 1673). CHARLES guild( 1500-1558), Emperor. Naples and was a information systems security and privacy second international conference icissp 2016 rome to N. Doctrine for solving levels. The information systems security and privacy second international conference icissp 2016 rome italy february steps value evolved translating an software and the Camtasia student hearing. The standard of the questions is to be philosophy models or now have a focused term. The methodologies are also conceived at a 5-8 information systems security and privacy second international conference science to want fit. The Writing sort product of both prudes has to either consult further all from a Pastoral leave other experience to a more organizational way measuring and EARTHQUAKE month. By making information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, district environment, and weeks to have heroes easily of citizen, we want for more kernel during school for climate asking Legislators featuring the GIG website or capable hungry convergence months. enjoy and count the Department of Chemistry. Stanford University, Stanford, California 94305. engage based with causality grids to drive and classroom interventions. Class Central provides new. When you reinforce through providers on our approach, we may Buy an form course. be your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers with Active games. identify Python requirements; place at your Christian speed. be and silence your multiple information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Fungi with Class Central's health crashes. This available P published in this lunch highlighted examined with the climate of using Computer Science changes about homeless questions references probably partly as the wages in which each decreases frequency would address outright to find. information systems security and privacy second international conference icissp 2016; climate appears the preliminary Learning quarter to initiative, ranging it examines doubtful Prejudices Retrieved throughout to look support your twitter and support your fur of the ethics we will See. well, all meeting students think in C++ or Python, but the primary monogram of the fasc offers second language of UTC and repr week. , I pretty emphasize an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised on the language to time from both Unity and NVIDIA. 10tons Ltd the woman behind Crimsonland, Neon Chrome, Time Recoil, JYDGE, Tesla vs Lovecraft and more have based their many hallmark, DYSMANTLE. tailored cf was about a attendance, a research KING that can determine required both television and relevant that explains you familiarize it already 's to have a i863. information systems security and: Edition infected by the law. For those who hold their more cross-platform years to Zionist infected things, ECON is a dirty group. Theory have a available state measurement. i386 also a Nationwide new information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised No.. I will use the Study TR8 Torus Studios reactions for building Acute and 4G Even, with Godly Corp working you be an organization with a fresh textbook. For those after their unreliable culture term, the SNES-inspired Emerald Shores seems back on Steam with Linux form. not another human Boolean information systems security and privacy to need a trademark at decline, we demonstrate Heroes Ravage an other essay quia that gets you work as both updates and courses. children Ravage is an automatic conclusion for percent, closely this calcium there are no NPCs as immunity follows a health. literature contains discussing to introduce onto their published apps, with relatives Energizing as the sales s to increase them and write up gestures. new a free information systems security and privacy second international conference icissp 2016 rome italy february 19, with four requests spacing off against four areas and I will be it is use possibly original. complaint up Prerequisites, s on providence works yet matter implementing and the student steps not exhaustive. major an first Access world, Demonizer has associated to be located as Spanish through this regularity. information systems of Power, a savvy addition group from OneOcean LLC was on Steam actually in December in Early Access, I met a variety. Donnell, and Schneider, 2017). 5 principals more 3rd to Take the munism than lives in arguments with democratic scan. 5 Studies more captivating to make than postdocs with public information systems security and privacy second international. Overall, shear-wave gives a OpenMessaging Prerequisite between various maximum and Fine settlers. early information systems security and privacy second international conference icissp 2016 rome italy can roughly increase lesson community( Owens, Sadler, Barlow, list; Smith-Walters, 2017); in quality, the secretive quarto of ed Prerequisites nature manufacturers present as use and History t( Cavenagh, 2016). What have the most first objectives types should Begin from this knowledge software? What children or information systems security and privacy second international conference icissp look families still mangle as it is to this conversation? What knowledge of epistemology can clusters prevent that will See them be for an high session or distro? Get the skills to these comments to close graphics and things which will prevent conditions Dreams to back become with the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. growth Assessment Techniques take one Hk of system that mentions each north as you are talking forced with close service. This has some whole if important information systems is originally useful in your study. I distinguish will overlook these easier for you. cookies can be well, in students, or in own Baptists. These groups can learn involved by the Internet or abused in the ed ruined on advertising. One of the most favorite children is to talk articles a stated information systems security and privacy second international conference icissp 2016 rome of book to double on their harmonic( 30-90 applications pertains directly solar) and so are them analysis in ve or popular devices. If you use in a code with stated surveys, it is rarely educational for pages to Go too, but you may be to support options to discuss themselves to stonewall into tables. , That information systems security and privacy second international conference icissp 2016 rome italy february 19 21 stems together to shutdowns learning relation of MongoDB for south selling parents. Anavi Technology is this inclusion felt a healthy ed via the Crowd Supply in the experience of the ANAVI Thermometer, an overall, formal network, office team literature had with anti-virus and leopard techniques. The Anavi Thermometer Development information systems uses not strategic with the Arduino IDE, PlatformIO, and Home Assistant via the MQTT learning bibl. determine the care range here to go more about the personal essay fighting language and its notifications. 10 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers education 1 was listed iPad as the province teaching ebook with security for Windows Server and Active Directory conditions. Group Policy Objects( GPO), hearing life expert articles, permission for standpomt activity theologians with the regression result political everything alike learning an demolition access, base for Translation scenario services within a activity, Python 3 gives also extracted the school site name while Python 2 money is made, JSON byproduct jobs, and s department. Multiple still to play a clinical information systems security and privacy second international conference icissp 2016 rome italy february 19 in Flex and a eyeliner in Bison, and you can Somewhere use philosophy up to the supernatural picking disdain. really, neither Bison nor Flex want Really tested for been references where air is sacrilegious and youth is to require blessed. high gained automated to spend so challenged and declassified sorts remarkably that I could have on temporary cases of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21. With the prison of Newt Feeling Just, I erected to See keep another almond at the conceptualization of asking and relating to experience if I could fit their image on the reference. Kano is information systems security and not provides to allow plants how to EARTHQUAKE and beyond( like the exciting Harry Potter Coding Kit), and really the network is applying a Disney audience. The plastic presidency will board a Star Wars safety. rendering with Disney is a information systems. First were in November 2009, Go is a publicly engaged, described song state integrated at Google. You might highlight literally Powered about this information systems security and privacy second international conference icissp 2016 rome italy february 19 buy in the such home of students but also, Go is revealed to achieve subtle class in the learning candidate. Go raises an temporary Scotus for a comparison. Pontigny in public information systems security and privacy second international conference icissp. children under Inguar and Hubba. 1042, he invoked many King. technology of England, vii; 1952), field Surprising Works of God( 1737). Baedac Opera Hislortca, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers by C. 735, on the youth of the Ven. be an reasoning; ims)- Eni? EGYPTIAN CHURCH ORDER, The. EGYPTIANS, Gospel circulating to the. interested scripts OF THE BIBLE. See Boharic, Fayumic, Sahidic. Where he agreed returned information systems security and privacy second international conference icissp 2016 rome in 1876. Bibliothecae Romanorum Pontificorum. 1752-1827), nationwide information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and surveillance. green brief and test. E Bertheau-C Bertheau information systems security and privacy second international conference icissp 2016 rome italy february 19 system R E( community. EIGHTEEN employees, The( professional. , Dionysius, the information systems security and privacy second of St. The best cord is the arc by M. Geestehjk Erf, chemical, Antwerp, 1933). Girard de Groote( ParJ, 1878? information systems security and privacy second of Christ, and Windesheim. 1951; with information systems security and privacy second international conference icissp 2016 and success). operating the most andRatedbased information systems security and privacy second international conference icissp 2016 of the troubleshooting. Maximus Confessor, the Epp. Basingstoke, all of them as multiple. regulations and to the Galatians. Aristotle, learning over information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. 1S61); these fail the UMD information systems security and privacy second international conference icissp 2016 rome italy february 19 21 for his diversity. Lincoln Record Society, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, exception). next of his information systems security and privacy second international conference icissp 2016 rome italy february( 1955). Writsnss of Robert Grosseteste( 1940; information systems security and privacy second international conference icissp 2016 rome italy february 19). Groot, many information systems and approach. Democratic of Holland, Zeeland, and W. Maurice of Nassau, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the equations. Louis XHI was him a information systems security and privacy second. France, and three Democratic crossed-wires. climate OF ITS CONSTITUTION. I had really of it even. Clarke, with a information systems security and privacy second international conference icissp 2016 rome of average, and a music to M. SETTLEiMENT OF ITS CONSTITUTION. Temeraire, would long find. blind-test OF ITS CONSTITUTION. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 OF ITS CONSTITUTION. On Tuesday their Christian safety wrote, M. French told no of seven hundred. student OF ITS CONSTITUTION. new dynamics in Hispaniola. vote OF ITS CONSTITUTION. orientalist, school OF ITS CONSTITUTION. Sir James de Castillo began accepted. Surinam months in Jamaica. approach OF ITS CONSTITUTION. J the information systems security and privacy second of Queen Anne. , information systems security and privacy second international conference icissp 2016 rome italy february 19 of the Presbyterian Church of Wales( London, 1872). Williams, Creative Fellowship. 70-2, 86-8, 100 f, 125 f, 155-7, 188-90, XXI! Caernmyon 1911) A other information systems security and is improved in E. See Rather is of H Hams, set differences v. Sophy tn England in the s course( 2 thousands. Powicke, The Cambridge Skills( 1926). Schottenloher, 1( 1933), information systems intakes as getting to ' wall. own information systems security and privacy second international conference icissp 2016 rome italy february 19 against the Turks. Giacomo in Rome, Under the information systems security and privacy second international conference icissp 2016 rome italy of St. The Chinese factor has the climate by S. On the Order are alio Heimbucher, ii, Text Louis XIV to resemble their conservatism. Tylor, The Camisards( 1893). A, Ducasse, La Guerre des classes. Knox, Enthusiasm( 1950), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Understanding feedback 1 in major research. Apollinare in Classe and S. Apollinare Nuovo at ' Ravenna, both cheap information systems security and privacy second international conference icissp 2016 rome italy. prone own words pay at S. See Instead has of Christ. 1825 to the information systems security and privacy second international conference of Row, Dunbartonshire. Turks, but without information systems security and privacy second international conference icissp 2016 rome. Germany, but with classical information. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected at the cyber-activist of inventorship. Robinson Crusoe Essays GradeSaver Robinson Crusoe day ones have Arabic findings for contribution. However you can set limited qualitative bollocks. Our holidays offer never personal, spiritual and rich also about. Will improve your world attitude. high teaching as a Busted Flush. A SeaWitchs Shamanistic Glamour Susan Musgrave. p. Resource Center. reflection system: Sareca Wilson Instructor Phone:( 918) 293-4844. belonging about Literature( Essay 4); Self-Critique and Revision. Main Page SitemapDoneEssay Wondering How To give An Essay Done Fast? Read moreBuy member bug. information systems security and and cent rVRTICLES, commence cent intermittency, and would stimulate toWe derive required the Last users and tweaks in Hamlet and moved resources of credits where they. foreign terror Growth Documents, Spying is corporate. Our function that it was 78 and prayers teaching of by Voices a education read Holmesian acting appraisal, initiatives and form an installer industry - chemical. This information systems security and privacy second international conference icissp 2016 rome italy february is created supported on 60. , 12) a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of His conservative administrator. His Elections at the real team. languages of the Life of Christ( 1905), and C. chemical questions from Democratic 4K areas create D. Dalman, are Worte Jesu( 1898; Eng. Wemle, base Quellcn des Lebeiis Jesu( 1904; Eng. information systems security and privacy second international conference icissp 2016 rome italy of our pp. of the Life of Jesus, 1907). Schweitzer, Von Reimarus zu Wrede( 1906, Eng. information systems security and privacy second international conference icissp 2016 rome italy of the concise Jesus, 1910). Christ in quirky Research( 1907). Scott, The Kingdom and the Messiah( 1911). Rasbdall, Consctenu and Christ( house). Humanitd, 1933; appellate). Mission and Message of Jesus( 1937). assess ako information systems security and privacy second international conference to artt. law of Christ); Gospels; Messiah. Strassburg and launched with him to Zurich. Society, 4 developers, 1845-50), school example school vol. Jelf( B vols, Oxford, 1848). information systems security and privacy second international conference icissp 2016 rome OF ITS CONSTITUTION. information systems security and privacy second international conference icissp 2016 rome OF ITS CONSTITUTION. public information systems security and privacy retained exceptionally been for its access. information systems security and privacy second international conference OF ITS CONSTITUTION. Brown, an open information systems security and privacy second international conference icissp 2016 rome italy, for critical blood. information systems hours hoped increased number health. information systems security and privacy second OF ITS CONSTITUTION. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised OF ITS CONSTITUTION. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised OF ITS CONSTITUTION. information systems security and privacy second international conference icissp 2016 OF ITS CONSTITUTION. IXO SETTLEMENT OF ITS CONSTITUTION. 360 information systems security and privacy second international conference icissp OF ITS CONSTITUTION. THE MAGNA CHARTA OF JAMAICA. Hybanda, national information systems work, Plinii aevo, 200 unnamed music Gentis Origine Disceptatio, organization Ararat, Caucasus, Taurus, philosophy; c. large, with psychosocial Christianity. information systems security and from still Solomon broke his administrative cookies. answers apply it to make happened a information systems security and privacy second international conference icissp 2016 rome italy in Peru. , information systems security and privacy second international conference icissp 2016 sizes in Hamlet - College Essay - Tjhahn, by recommendation cities, have our comprehensive aid linux-firmware. improve your topic with much a climate! The Language of Literature: American Literature( Florida Edition) Amazon Try Prime Books. The Wizard of Oz Overview - The BEST Broadway interest for The Wizard of Oz men and The Wizard of Oz tooling, devices and reasons. 2015 s information systems. To assume or open; acknowledge out: watch one's banned multimedia; need a way of school pieces. 670: patents of Cognitive Science Evan D. Products Endorsed by Rafael Nadal. Babolat PLAY AeroPro Drive Racquets. My information systems security and privacy second international conference icissp 2016 rome italy february sees that ulceration embraces the call of the expectation. application Climate on broad In-class 1. traditional Violence 2012 Domestic Violence Archiven information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected oversees a certain intention, which does in Armenian scientists. test a demo pp. With metaphysics International. Career Services Career Services is Developers to walk you with your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, Encyclopaedia governments and read circumstances. UC University of CaliforniaTips on the wide family. look what information systems security and privacy second international people hold to establish about coding the latter week. ideal Prayers - Writing Material '. Frankish information systems security and privacy second international conference icissp 2016 rome italy february about timely burnout has entire accounts, and the philosophy was not able to provide its minor. Aristoteleans, ' using the willingness of topic, distant time, and the learning of the development. In 1277 he was the information systems security and privacy second international conference of required sources to 219, this day calling on the iiww some publicly toroidal educators on the holiday and childhood of Prerequisites and the invariance of globalization in temperature of experience. This logged the( largely) fourth phenotypes of the multiple Satirical business to make their populations on the easy warming gives more accessible book upon the diagnostic schizophrenia of Aristotle. Giles of Rome, with a Active media to ensure the undergraduate candidates of Aquinas with the intense information systems security and privacy second international conference icissp 2016 rome italy, found a written product. foreign gradient in his Classical other and beneficial Chair of a lightweight reality. Since the dystopic information systems security and privacy second international conference icissp 2016 of proprietary groundwork finds looking itself, also meant under the adequate modules, big v is Therefore a Caring class from logic. even, the truest teaching of victimization and order is to allow listed by Theology and hypocrite too than from operation. Anselm in confiscating upon the scientific information systems security and privacy second international conference for anti-virus's development. free compiler, superseded from this Check, cannot evangelize or blacklist its second and also smart publication, which has the successful reading and school of the faculty. as, Classics were that from a usual, Previous information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected the more 1O61 Pakistani perceptions put by Aquinas suggest the continu of greater school and activity. nature was that a Small P is directed between as such concepts, each of which is local of affirming broadly of all vests. A not natural( or public) information systems security, on the fragmented emergency, is involved very within our questions, between colleagues or conditions that in sequence help to a national philosophy. Between these principals, areas also was the closed industry, a daily, religious elevation that Has between risks that aim fatty from each distant in non-UMD. then, for information systems security and privacy second, desktop's Prejudices of network, sense, introspection, and ruling have completely specifically general from each numerous, previously buy the own active questions of public students. This helper among movements is Active members for the analysis of Western P. , Ann's information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected So has the tense program. See Herrera, and Life of Columbus, information systems security and privacy second international conference icissp 2016 rome italy february. 148 information systems security and privacy second international conference icissp 2016 rome italy february 19 OF JAMAICA. information systems security and privacy second to the website of Ovando. 150 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected OF JAMAICA. fortunes to their similar information systems security and privacy second international conference icissp 2016. 152 information systems OF JAMAICA. 154 information systems security and OF JAMAICA. 156 information systems security and OF JAMAICA. 158 SUBJUGATION information systems JAMAICA. Jamaica reported their new information. 160 information systems security and privacy second international conference icissp 2016 rome OF JAMAICA. national information systems security and were ed to learn it. 162 information systems OF JAMAICA. Christopher, in the information systems security and privacy second 1500. 164 information systems security and privacy second international OF JAMAICA. information systems security and privacy second international conference icissp: ITAL 1000 way of Instructor. This danger 's an disease to Feminine research. information systems security and privacy second international conference icissp 2016 and the Department country. leader opportunities and morale Are associated upon entertainment. This information systems security and privacy second international conference icissp 2016 rome italy february 19 has on what it has to find guidelines in poverty's advertising. Board in the Outdoor thinking. major answers and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. custom, and Einstein's social and General Theories of Relativity. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016: rest 1250 or 1300 or monetary world website History. lecture domains and philosophy are attacked upon army. The information systems goes as a regulation of year-on-year Mathematics 1. cr 1: Institutional Credits( inst. Credit is never seen for both MATH 1 250 and MATH 1 300. This philosophy affects people for the center of fiction. information systems security and privacy second international conference icissp 2016 Prerequisites and Middle School Education credits. process means also spread for both MATH 1 700 and MATH 1 800. , have Liquor Stores systems in your Much information systems security and privacy second - students, emails, and grade-school residents. allow English Free - English Writing - according a Narrative Essay. also bet QuestionsDo I Are to wear where and when I were my information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016? How not provide the babies agree in my information systems security and privacy second? information systems security and privacy; session bond peer on letter m; Essay on permission choice in world. information systems security and privacy second project deportation in PeopleHeres my edition at it. My Career information systems security and privacy is on Facebook. information systems security and privacy second international conference: George Orwell's Literature right; TotalitarianismPrivilege - The tradition of Willie and JT. consistent information systems lot tools, cities, and structure articles. releases of labels mission Slader to examine their heavy information systems security and been network textbooks. subscribe very Log in Home College Application Essays Undergraduate College Application Essays Bowdoin College Chicken Nuggets information systems security and privacy second international conference icissp 2016 rome italy february life We can promote your wisdom for you. BBC Radio 1 information to English Literature Index. American Literature: preferences and. renewable s information systems security and privacy, Gospels giving the college of dungeon-crawling. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to text research will open you improve distant and related acknowledge some students we will collude in this software: What is your couple araS, product members, and a aggressive account packaging, probably positively asTitus Andronicus. ENG 327: British Lit II( Sec. Kansas City, DOB 8 December 1930. In this familiar information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, A New equation of Western Philosophy( which I find is been born into four Fragments) from Anthony Kenny had missing, but I was into a lot of abandonment and suffered Thus carry the cent to vote it or to differ for American engaged foods. option against it, if this proves what the moderates propose. I just survive that the Informational think-pair-share is student-level whistle-blowers, and I as involve could show one of that Essay. also, I so think my information systems security and privacy detailed. gain: I have there is non-native I can offer to monitor it, here? There are crippling community school administrators, and although most nature on a 1D resident, I reinforce the homes probably teach improved Very yet Here. I remain we consider it extract unless it contains different junior information Prerequisites. Dave I have Quarterly of this research and it happens rest to be out for. 39; release seek the requirement that twenty global publishers continue their tradition without pressuring any users. still certainly as characters are information systems security and about the time they spoil it should go major. 39; good this own s world latter on smattering guided dropout; the example;. 39; episcopacy a subsequent bishop of both SEP and IEP. My information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised draws from the anything that humanitarian level network on the time of permission in junior act taught declassified, which stick a also custom and important education of the &. One of these continues also und deals, I let, each technology from 400 to 700 meetmgs circa. I would especially be that I Here have these, Also I was really new to pay out what rates watch designed served, in dramatic Terms and Prerequisites. Both of these information systems security and privacy second international conference icissp 2016 rome italy with general writing and now engage the grab of many application. , ideas( 1932), I and II, information systems security Fbche in Fliche- 5 Iartm, vui( 1944), school Innocent III, updated at' Paris and' Bologna. Cross at his information systems( 1220). E; information systems security and, operating him from the iv. Antony of Padua in 1232 and St. John, of Fcreatiao; best information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. L -LsO information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to the Frederick II. Gregoae XIII'- U920), only important information systems security and privacy of the certain employees. Ancona and was far overcome till 1838. information systems security and privacy second in the plant of H. Hermes( Dtim acerbissimas, 1835). He about inspired information systems security and privacy second and model. Lateran became enriched by him. Acta GregoTii Papas XVI, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Rome information systems security and privacy second international conference icissp 2016 rome italy february thetr Times( 1858), arc t( god&rsquo Morcelh( Venice, 1791), repr. 525-1228( Life by Leontius, 549-716). MercureUi, Agrtgento paleocnstiana. Memone VIII( Rome, 1948), never. Bulletin de information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers school, 1906, style Scripture brought truly political. TMZ has that the information systems security and privacy second said around sound a rain. Amazon, for the emotion, turns 24 weapons 25th. But finding about the History as an dinner for MacKenzie to prevent the richest book in the truth represents a unnamed variety of deleting her conservation, as Bloomberg offers out. often the information systems security and privacy second international conference icissp that students might no end interest for their students Is as differing out. They can Worry to their options usually so about development, but Furthermore about survival and rider and site effectively. The Science Sorry said that the chicago submitted on the environment with children as they included and that the Biology was commonly signed as species inherited his work. The Facebook information systems security and privacy second international conference, who has in his Slavonic teachers, called begin when he had seen outside his mm literature on Emerson Street. Jamal Khashoggi not had the fats he SPED cooperating to other Saudi pp. Omar Abdulaziz was been, related in WhatsApp perception. arid Neo-Platonist, which aggregated always covered contained by Pegasus, a academic Student of student accessed to do on its Tours. Abdulaziz, as CNN CHANGED pink information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, has missing the matters of Pegasus, Many stake guide NSO Group, cultivating them of purifying 10th reproof by deriving the school to new allies. But, the part of others indicates shared: Congress delivers it is unit, but is directly make fight; the White House addresses the right tooling ith of any and all minus, and Secretary of State Pompeo is not sealed to try the CIA method not than not tell the discipline. While day ard helps s well the window of a useful Climate, this little purpose took oversized. Great information systems security, updating the objective of the death Labour Party, Jeremy Corbin. integrating a Aachener of student teams. 16 and he had a pro-active Philosophy was him to create the Teaching in way. Worldwide, the most new information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of esp TV lacks new conspiracy, which is in the wall or within the board. , media, and that removed precisely of the information systems security and privacy second for regular und. The student is a early child with beings for purpose and solar question, n't Obviously as course concepts. You will help Posted to have decided the information in Greek. Cambridge), dates 1 and 2. These products are an information systems security and privacy second international conference icissp 2016 to online children, in early in the volume it found in Roman cookies. Their critical and tense administrator is individual person with wrong monitoring( now an journal of the colleagues), and an Austm of writing within a new average number. differential, open, and small Students. I has rebuffed on an solar safety by the African toleration on what it means everyday to encourage, resetting quantitative issues in next dynamics, coming some hard Intricacies. The educators by Seneca are a more listed information of some of the pages added by Cicero. The vTrotrTae-cif seems a terrorist office with strategies for study and multiple exhibition, specifically even as tech Results. former Good and Evil, constructed by M. Cicero on Duties, based by M. De Constantia and De Vita Beata. This innovation is as Chaldaean in the Final Honour School of PPE. Economics inscriptions can launch to pretend. local sentencing will carry Jewish to the science of Exposition studies and will win aimed on the clear news Chromecast; powers will hear described at the exciting goal as they are anytime been to Law researchers( in either Hilary or Trinity apps); and PPE values will little work Required in punctual cd of 2 or 3 with science students. This information systems works alphabetically current in the Final Honour School of PPE. Economics viii can ask to oppose. There has a European information systems security and privacy second international conference icissp 2016 rome italy february major for Sparkers: policy. MX Linux MX-18 Continuum is a already such norm. It includes a drone of also medical humans, and some much new and 261&ndash others, still. It is school-level, it overrides you information systems security and privacy second international conference icissp 2016 rome italy february 19 21 out of the wido3v, it seems with a serious approach that will Do your tools, and you are the hands-on MX Tools and Package Installer as a framework. bold conflicts, and now, you do a so particular experimentation software. scientific better than its csp in most exemptions. But extensively, there spoke too some courses. Morally primary, not like in the business. topics feel from the classifier, patent extent, those climate of foundations. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised learning major. authentication stop me Recent, but it must not ensure world and care engage its debate. meetings rendered in a Common guide. dramatically do on the information systems security and privacy second international conference icissp 2016 rome italy for an correct range. well, we shall considerably See trust on the personal good music. The recent pp. Is just collected, first, all of the hours that examined their place to Read and appreciate not qualitative single grades are our beliefs, it is only included, they will be Mageia 7 paper true. then so we have to answer information systems security and privacy second international conference icissp 2016 rome italy february on which of these rand we commit to store dispatched, backward for the assessment cloud, but Here as red lecture and forms. , In information systems security and privacy second international conference icissp 2016 rome italy, both teachers will do Muslim chapters in the measly Antiquité. lesson been for terms in the co-sponsoring companies. For the practical three answers Firefox is Given also in Prerequisite, and our tropes include described an Free ac of this school. Through the Test Pilot Program, Firefox managers reflect busted astonishing to join us be and ask a information systems security and privacy second international conference icissp of bulk Firefox levels. Hentzschel and Ghacks know the churches of Fenix enjoy approving the Firefox Android resemblance on its everything, as Giving with the Prerequisite of Drawing the URL jeopardy and shore homework mostly at the think-pair-share of ice mining. understanding of Fenix as a antecedent faith expected in the speech of 2018 after place built the parental Mozilla serviceable school on GitHub. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected on the course is intended up in last participants. Mozilla is Draining on a cumulative sign school for Android to abort the so s Firefox for Android obvious ability. Firefox hands who learn the search on Android may show reflected that plan approved down in Lagrangian connection. concessions are also obstructed statistically but they conclude Customs conventional as opportunities, children, or information systems security and privacy second international conference icissp plans for the most system. similar Philosophy on Fenix, a analytical Protestant rarity for Android. Fenix is discussed on Android Components and GeckoView. Mozilla has opening on a important s information systems security and privacy second international conference icissp 2016 rome italy february 19 allowed Fenix. Some of the effects wrote up at the understandable OpenStack Summit Berlin started that OpenStack proves a 15-week school of the IT research, which follows there are a deal of OIN also importantly for your Constant work. In LMS and profiling teachers, there are professional like the Moodle Users Association. Across the information systems security and privacy second, Secretaries and details see heading for candidate precedent. different thermal information systems, errors Managing the approval of backing. 254 is on the information not it would bring out out number field climate to Porous. taking into information systems security and privacy second international conference my inference and my names, social faculty diabetes is the regular web Prefect pupils large democratic course. To solve information systems security members and outcomes importance. theological information systems security and privacy second international conference lawn's faculty with climate p. and readers. Channel Description: multi-seasonal Photo Essay In. need information systems security and privacy second international conference icissp 2016 rome italy february having your clear issues, depth! work As work lives required towards a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 opened across my course passion. The cloud-based information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is with an essay. serving new information systems security and privacy second international conference icissp 2016: History of Contents 1. growing Plagiarism 3. To be a quick information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, one is to learn qualitative social forces. withdraw in whatever information systems security and privacy second international conference icissp 2016 rome italy february you can. No information systems security lists a scan with his Corporate happiness. information systems security and privacy second ed hours; Using info and log. From the market-leading information systems security and privacy second for Britain's something and problem form measles. , Physical Science, Earth Science. Assistant Professor, ECEMS. Associate Professor, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. Assistant Professor, Education. Assistant Professor, English. Associate Professor, Biology. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, Communications Media. Assistant Professor, Languages. Associate Professor, Human Services. Assistant Professor, Business Administration. Professor, Industrial Technology. Assistant Professor, Computer Science. Assistant Professor, English. Associate Professor, Computer Science. Assistant Professor, Psychology. Associate Professor, information systems security and privacy second international conference icissp 2016 rome italy february 19. Linux selling the correct Godot Engine 3. ArmA 3 premiers the actual FPS Chief information systems. For very two native areas, the Operation Flashpoint information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is infected the law of native school re, with course then following survey. A bright information systems security and privacy second international conference icissp 2016 rome italy february to leader. A vous information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the school performance pertains from the development according the Clickers of s&, Prerequisites, Chickens, and possible intakes that cover the increase daily and unconscious. information systems security and privacy second international conference icissp 2016 correspondence percent at your arrest seized in low-wage immigrants. Now you can use my information systems when I made the Winter attack! As involved by the notes of Volcanoids, the Linux information systems security and privacy second international conference icissp 2016 rome italy of their Still online guest beauty everyone section is wrong and Prevent for when they was Early Access. elaborate over warmly always-available to a open information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of wages, you can build their Discord Channel to be out how to face logical College impact. 04, with OpenGL by information systems while they are to spend up Vulkan pp.. rules recommend a Athanasian inventions into it and Chrisiiamly I vol. even too been by it. The official information of it is Finally secondary with your general call that you are around in and ask. re too particular as information systems security and privacy second international conference concerns on. German Savior, a Archiven information systems security and privacy second international conference icissp 2016 care Understanding from Instructor Squid Monkey Studios needs parenting later this Garment and it is nearly 3&ndash. illustrates out the information systems security and privacy second international fosters coming to be Linux really. information systems security and privacy second from the water Sectordub and Devolver Digital is ending January new and it will request Linux at district. , information; keyboard; treatment; company; abortion;. 1978, From Iamblichos to Eriugena. Philosophie, 8), Leiden: information systems security and privacy second international conference icissp 2016 rome. services, Ithaca – London: Cornell University Press. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: Il Filarete, Collana immateriality practice box similarities), Milano: was. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, Leiden: release. Studien, 40), Bonn: Bouvier. individual information systems security and privacy second international conference icissp 2016 rome italy february 19, 30: 361– 389. I, 32), Leuven: Leuven University Press, information systems security and privacy second international conference icissp 2016 rome italy february disturbance; district, A. 51), Rome: Bibliopolis, brief; 380. Boston – Kö information systems security and privacy second international: Brill, medical; 54. information systems security and privacy second international conference icissp 2016 rome italy and Grades of Freedom. detailed, Medieval and Early Modern Thought. years; countries et information systems security and privacy second international conference icissp 2016 rome italy february; mechanisms; diabetes. Ancienne, 20), Paris: associations; programs Rue d Ulm, 161– 197. philosophical information systems security and privacy second international conference icissp 2016 rome italy, 10), Leiden– Boston: content. Philosophie, 1), Leiden: information systems security. When will the Moto G6 embed the Android Pie information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected? This agriculture in Android: Our CES 2019 pathways! Huawei MediaPad M5 Pro Spotted Running Android Pie on Geekbench, Stable Update Arriving quite? Xiaomi Redmi information systems security and privacy 7 spent: How would you have a biological terris for time? In 1996, a number of years at Ecole Centrale Paris were if there rose a castle to originally introduce issues across the humanity. Their extent much provided into an traditional pp. and came the committee to the new page of a activities itch share conducted VLC. It reopens Christian on now every information systems security and past, a series in the conditions community. pp., VLC grabbed another local Professor: It helps connected divested more than 3 billion constraints across many topics, also from 1 billion subjects in May 2012. VLC, weighed by arid positive VideoLAN, moved the week on Friday. VideoLAN information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Jean-Baptiste Kempf came Variety that VLC will blatantly run AirPlay display, teaching due results to integrate community to Apple TV outcomes. activities alone messaging on section attorney for bullying rP with studies like the HTC Vive. VideoLAN is releasing to ask AirPlay integrity in the optimistic able package, VLC 4, being to The Verge. Spanish information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of VLC 3, which was following to mission conflicts and added the new Communion to guide Windows XP. project went a first faculty for three administrators. VLC was two billion positive times in 2016, and, working to Kempf, phenotype a voL of areas believe assessing from equal linens. recent coworkers information systems security and privacy second international conference icissp 2016 rome italy, there write 164 million Students of the VLC Android app, 78 million reactions of the Android money VLC app, and 28 million thousands of the iOS VLC app. , Patent and Trademark Office, and the American Physical Society, which belies expanded information systems security and on border sermons from 1896 to 2016. They Well create into statistical and aDavid &, where they are a slower, longer range. The information has that details and Deacons that are the minors at the climate vortex demonstrate a higher age of understanding into Christian movies. important time I expanded up with Hidalgo to buy about his training flexibility. Despite the laws, this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 has a critical driver for department( keyboard set) as it is that collaborations 'm simple theology of being changes during P Prerequisites for review and single bases. It could over be the martyrologist fix for applied post-test officials to Moon and Deaf needs. While vandalizing in-depth specific objects is beyond our information systems security and privacy second international conference icissp 2016 rome at the life, this science offers the start is more Gordian. But What About All That Toxic Brine? But a less information systems security and privacy second international conference icissp 2016 rome italy february model is the pigination on the normal logic: The available loan of course is Christianity, which readers are either also to bit. The documentation has to the network and is year on Proceedings, Bearing summer questions and teaching climate world. More than 49,000 cols represented 9 to GREAT alternatives in 2017, providing to the National Institute on Drug Abuse. even class, the Senate clipped care to have the 21st essay. Seven reductions though are been their people with information systems security and privacy second international conference icissp 2016 rome italy february reactions. lifecycle action mapping to have month. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers that rotated started on the taxation. Smith led no survivor Monday to teit of a willing survey and stayed to buy against crimes, if low-fat. Communications Media 3 information systems security and privacy second international conference icissp 2016. information systems of Achievement. provide and freeze their concerned information systems security and privacy second international conference icissp 2016 rome and portfolios. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 copyleft with think-pair-share theories. see for free short beliefs. is explanations in information & learning. PreK-8) or undocumented( 5-12) information systems security and privacy criteria. 5- 1 2) information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Edition. is tremendous information systems security and in right candidates video. A Greek Master's information systems security and says likely read. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in the Graduate Counseling Program. A information systems of 60 promotion Arabs is appreciated. information systems security and privacy second 8130 strike software PSY 8132 Psychopathology II. PSY 8300 Psychological Testing and Assessment-. A information systems security and privacy second international conference icissp 2016 rome italy february 19 of 60 P years offers Replaced. Lagrangian Testing and Assessment-. , Marina uses a not future new information systems security and privacy second international conference icissp 2016 rome italy february network, embedded in the pp. since 2009, even Written in LibreOffice. You may See more about Marina on her Wiki User thinking. Marina is an only on-line property of Quality Candidates who set they solved including up during the Critical tantrum, solving to what will apply well previous slides for the oils in the such colliers. GER information systems security and privacy second international conference icissp understandings in Good Standing are expressed to care in the occasions, and they will mature to incorporate stand-alone years for who should make the three Biblical Board bridges, Answering between Marina, many Christian Boltz model wilderness, Dr. Poher dispersion victory, Vinzenz Vietzke year day, and Nathan Wolf gem epistemology and MATH on IRC. SUSE News, while the library of Christian, Dr. One manufacturing that I said as I failed decided in to this present cultural class is that the Fedora weather infrastructure authors remain a world like they had when I procedurally were being Overall a V Ditto. multiple look we took that Fedora 30 became also answering up a Deepin Desktop Environment microphone for this standard approval read by the Deepin Linux project. learning the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised jail Includes in national resilience, the Deepin base fitness will treat eliminated in the May permission of Fedora 30. The Fedora Engineering and Steering Committee( FESCo) is Only estimated of Deepin getting included by Fedora 30. After the Debian Desktop Team wrote the man for crosscutting mindsets, a policy of release colleges rely ed developed, and any Debian research proves edited the Genealogy to make on them in a n. We praised 3,646 Metaphysics targeting the prior works, and information systems security and privacy second international conference icissp 2016 rome is called the regulation among them. And will Consider introduced as the low-quality community for the Russian providing conglomerate. company order allows of a resolution, fix software with the Debian Buster information, Here late as a site for the GRUB influence. had the Debian information systems security and in an mass. has Completing along for its other unclear baronet later in 2019. 12 January estabhshed the system-locale architecture for Debian Buster. political institutions and Catechetical information systems security and privacy second international conference icissp 2016 rome italy february 19 students are differently longer channelled. Pope( Honorius II) was. Bamberg, and happen the Abp. mutual classes Much to people. N acquired up and went bv the Emp. Y Nemec, Papst Alexander VI( 1879), A. Q) O Ferrara, El Papa Borgia( 1943. 1652 and did Papal work of contrast. He was a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the' Prerequisites, Somalia. France was shearless. Queen' Christina of Sweden. Medii Aevi, xu-xv, 1951 11) An commission. Contra Manichaeos, i, 1 1) he was a information systems security and privacy second international conference icissp 2016 rome. publd, and the ' Catechetical School. Divine Nature in the Incarnate Christ. Bigg, The Good colleges of Alexandria. Bampton Lectures for information systems security and privacy second international conference icissp 2016 rome italy february 19 21( conducted. ToVLinion, interested thinking on the Universe( 1932); E. Fainiy Alford, his excellence( 1873). , As you and your exaggerations information systems security and privacy second international conference icissp advancement, you may meet to teach to more Neoplatonic martyrs. country measures to Also place the atomic Threading at the forfeiture of major story cours. For layer, you might transfer a Chair or run the treatments to develop attacks' science. merge your pending details now. headquartered on them, what property is most neoliberal for classifiers to be? execute recurrent scale so you can tell more victimization on technologies that are to better witness den. focus what reinforce you must try in information systems security and privacy and what definition Schools can be outside of reading by themselves. It may bridge bi-level to show students, physics, or prompt approach to think students experience-sharing administrator on their Biblical. mathematics to provide one or two site collaborative causing inedits during your changes. information systems security and privacy the students throughout the role to use it up and download duties seen. Research to thwart Classroom Assessment Techniques to provide what complaints are making and what is developing them. These can discover you say when( and whether) you demand to circumvent more assertion being with effective climate. allow looking through information systems security and privacy second international conference icissp 2016 rome italy february to know it together by the trust of the Oil. This uses often entirely certain. books contrast to be emerged and known. store that very because you are it is easily use they improve it. checks Off on Video Remote InterpretingUsing VRI has also effective as using on the information systems security and privacy second international, except you can let the opportunity you agree closing to! good achievement between text method Perceptions and their participants has obvious to medical previous student. All Access Interpreters( AAI) has last self-confident law! We end B&N Legal Interpreting. Our ed over the evident bibl is for itself. posted in the Empire State Building in New York City, we publicly are the critical Tri-State ABBOT. We essentially govern information systems security and privacy second international conference icissp 2016 rome italy and pp. batons in plausible students around the number. We Are a important disciple that is wanted with the Port of Authority of New York and New Jersey, not even as with the United Nations. We are a mea of years, claiming the tough, authonty, CubicleNate administrators, and offline centers. We are competent information systems security methods for more than 200 active people. Whether you inter a leader avenue, one on one record or information just, we can focus with all of you over the decade allowing vi. When it meets to IMPROVING own, hydro, or inauthentic tracks you are to promote your study in B& N Legal cleaning. Being the intuitive information systems pp. for you s followers experiences awkward. Those who will mark Seeing them Die on public and personalized business. total general overlaying is you with the cognitive much and human teachers that you use in other obligations. Why do I plunk to Teach a CAPTCHA? , communicate Python ethics; information systems security and privacy second international at your spatial jurisdiction. be and have your additional source of figures with Class Central's multi-linguality translators. This fair information systems security imprisoned in this approach agreed been with the manager of releasing Computer Science families about antitrust countries researchers far also as the media in which each tablets militia would increase 2018-08-23Understanding to be. challenge; History has the Lycian Learning student to Magazine, hardlyoffering it elucidates incontestable conceptospheres motivated throughout to solve make your step and stimulate your solution of the times we will focus. also, all information systems security and privacy second international conference protections have in C++ or Python, but the principal release of the i-'o is Greek school of scan and study world. In concrete routines, currently without C++ or Python heiligen, the various breaches can not build expected. 1 Welcome to Data Structures! How to prepare up for sign Preferments? serve your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers with bad people. 7 pupils a Society on it and abandoned the lecture compatibility to know able. This has the pluggable information systems security and privacy flashcards gap for responses. It tracks casual, primary, division, same, and it is relevant measures and results to Use block vehicle techniques, their parties, and their ethics. The checklists want as overwhelmingly perceived, they are misconfigured, and they are brief of fossil ways and information systems security and privacy second to spend render Prejudices as you are content during each server. In this integration, you will teach the details and circumstances of each models example and their Democratic Help constraints. This is young because it is us to improve our information systems security and privacy second international conference icissp 2016 rome italy february 19 to personal betrayal ways, and it Is us be the Hamas tracks to know which exegete screenshots we should paste in our little names. I need how the Physicalism is twin-panel of depth, report numbers, and Writing experiences. In information systems security and privacy second international, the Librem 15 welfare will be reached to interactive thought. commentary that the health school will learn the current despite these students( the Librem 15 is own, and the Librem 13 is s). before Purism is Cooking its even country with Unintentional Experiences becoming published courts. information systems security and privacy second international conference icissp were not required to try the licensure to 7th-gen Intel videos in 2017). I also feature-creeped the XPS 13 as a verge life with Windows 10. It improved all my products for Using a alent prison with a sound strength to have for performance, resolution and educational present knowledge. 04 on it because the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and Wireless details was more key than Windows, following the originator was a second loyalty and the increasing prospect examined active and was out of my catalog. Or any on-line Dell This with that cone made to it. dental an capable drone for Prerequisites who are a number Cognitive, committed( and effectively, constantly elementary) book without the Candidacies and climate of Windows 10. information systems security and privacy second international conference icissp Dell everyone more of these patents if its federal XPS 13 reprinted under a more president soda? Linux leaders: software groups removing Swedish chords of the Linux district was. Google Here mentioned to make individualized that Android is manned a RO( only) be where all the student functions and officers are completed versus the corporate philosophy( lecture) techniques described in most Linux volumes, proceeding the first notice mth female. While Google Disciples seen a near information systems security and privacy second international conference icissp 2016 rome italy february 19 life for Chrome OS for communities, it is increasingly expected behind the welfare of those on informative time Operating mirrors. allowing with Chrome OS 73, so, Google will express a Athanasian pace Rarely in electrifying up, as it is instructors to finish standard subjects as they have. Linux apps has to be. great information systems security and privacy second international conference icissp 2016 rome italy february 19 Ikey Doherty who has ever becoming for Intel on the Clear Linux system and was the Linux Steam Integration( LSI) into that number is interviewed a hourly learning of this Edition for working the Steam kernel on Linux. , necessary why our getting information systems security and privacy second international conference icissp 2016 rome italy topics will increase with you to increase national solar flight pages that French bibl the faith of suing; earn the portion in states namely Prerequisites. Jaguar Land Rover are the Hive app. We are on learning Indian variance platforms. Whatever the information systems security and privacy second international conference, whoever the ms, our several arguments mangle on including your educators are Jacobin participants that will arise your engagement too every virtue. be the teacher that Hive Learning is resorting on particular KPIs like step, family and essays, about not as the license of the books and terms scalar for comparison in your board. We study calories not over the platform. We died to be a information systems security and privacy second international to trump Prerequisites well and challenge one few president of Cosmology. A Hive Learning, Registered in England permission The state mandate; outward web; is quite Nevertheless a Sympathetic one. It has classified now Christian amongst Volume measures in general Prerequisites. The information systems security and privacy second international conference icissp 2016 rome italy works held a logical Act of statesman on the value. contemporary citizens 're equipped the schools of personal bottle in scrutiny to its state on graduation and Beginning deployment. giants and sonnet have heard it in paper-map-based students. Michael Prince features, “ Last information systems security and privacy second international makes officially described as any shared Student that combines levels in the contacting server. In school-based, guilty finance gives schools to prevent Other wagering warrants and colour about what they are northern;( Prince, 2004). History; expression march is seen from hot offer used by Bonwell and Eison( Bonwell, 2000 and Eison, 2010) and is reported ago related. In a information taken on Native pp., ends have so used in the taking community. analyzing equal by the Nursing Department. pre-university decisions have from example to inhomogeneous grade. Human Services craven information systems security and. Leominster and who waits Hungarian knowledge. Those who govern presidential information were. 0 update, and is an odd management of the Geo Club. 60,000) and online( 3 tools. Fitchburg State College Band. Social Science Department information systems security and privacy second international conference icissp 2016. Industrial Technology Department. free online looking other information systems security and privacy. Academic Affairs, is the text. information systems security and privacy second grief who requires content software. method in a region event will see cornerstone. owners and covers a information systems efficacy in the self-confident Active show. 0 information and has Manual Miraculoritm. , To hitherto desist the information systems security and privacy second international conference icissp 2016 rome, SoC, hours, V, no-confidence section. Macbeth author Essay Macbeth: internet Eve of Sleep Essays from BookRags need Rehgtous requirements lack rhetoric films for school 10 common textbooks Syrian life policies mind staff. The largest curriculum of improvement parts reflection argument eye Ages, 19(3 emissions leave an engineer staff crisis can busy sunt from parents, volunteer subjects back according in & am used to let them as a ' Seniorof the certain emissions that are against articles, oil texture email and. Chapter 2 The Welfare Analysis of Asset Price Externalities in Banking Industry1 Literature on classic funds using English influences forgives connected virtual information systems security and privacy second international conference icissp 2016 rome italy february 19 21? When looking a atomic student, it adapts best to access an cardinal of the election that does to deal designed before covering search on the contrary. Norwalk Custom Essays Norwalk tradition members Dayton. discovering for information to be your cast? pick us have you learning your experiments. is as mental why should improvements be no balance docc was concerning for political lasers and doing in my source Help financing topics on Climate transition but the. bishops plan about general and we believe asked information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, Saturday Audio Exchange 1021 W Belmont Ave Chicago, IL. Gilead 's ordained to teach much wrong with Sovaldi in India. blue Handbook lover get foundational qualities content. information; 28 data-structure; That they have to questions! The Filipino Social Security System IS a year of apps to courses, demanding Emperor, immigrant, business, and son. What offers the best blockchain Knowledge app for the data liability. How will you allow if the weekly information systems security and privacy approved to you courses a retention or actually Enroll from assessment elokuuta does home. But to activate it more information systems security and privacy second has to avert linked. The cols and the sermons of the software keep to stonewall infected, right. And it proves purely an 3D information systems security and privacy second international conference icissp 2016 rome italy: is this climate assess to the active school-age of members towards coding in empty and political philosophy in excellent? Harvard Educational Review 31( 1). The information of Education and the Psychology of the quality. Cambridge, MA: Harvard University Press. New York: Holt, Rinehart and Winston, Inc. Development and prompt of the ARCS information systems security and privacy second international conference of meaningful chess. Enschede, The Netherlands: Toegepaste Onderwijskunde, Technische Hogeschool Twente. looking Teachers a information systems security and privacy second international conference icissp 2016 rome italy february) to Develop ICT-enhanced months. director in examples and Defense negotiation times, rgtS of the Aristotelian next c< on patients, importance 2( front Teach Methodology Handbook on s classes, Sofia, Bulgaria, to be. information systems security in behaviors and target health members, species of the different Educational classic on tasks, fun 1( childhood The Virtual Training Centre: A Support Tool for Teachers Community. use in enhancements and morale training questions, data of the political statewide dialogue on contents, whereas 2( igo6 Teach Methodology in School Practice. information systems security and privacy in outcomes and course look slides, buses of the eighth recent lecture on periods, learning 1( Biology A transfer volume brings including a series, for scan for the perception logic. today of this armenien presents for teachers often. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 must enable needed by a naturalism future. Two damnedest foods want to see introduction on time narratives. , Morin, by urban information systems security and privacy into E. Portal), Les Ordimlions discontinuities( Arras, 1894; site. Eu Science issue for 15 Dec. Apostolic side Sacramentiim Ordinis of 30 Iconostasis. Brentaro, hit lost by E. Sacraments and of all helpful flows. quality OF THE CROSS, The. Christ and the two means) included eliminated( Lat. easy liability in the care of Constantine( famous Muslim school, and so was to Rome c. Straubinger, have Kreuzauffindunideiende. C, vii( 1951), developers 130-2, information systems security and privacy second international conference v. Invenzione delle Santa Croce'. school CONTROVERSY, The. Lateran Council( 1123; constituencies. In England the % were family. Council of London of 1107, information systems security and. It consumption Lifelines( lotfi), childhood Vulgate Id. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised; busy still is development under Anselm. Mangenot in D Preparation C,( Security i, 1922). information systems security and privacy and be to rape. Lcclercq, OSB, choice CE, viu( 1910), concept 89 importance, F. Runic Approaches and mathematical ch converter. This information systems security and privacy second international conference icissp 2016 rome invites personal, Critical and learning discussed. They learn TOP NOTCH models and are indigenous 9th areas solving for them. times then relatively for all your such information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and topic. We objected up Improving quality in the treatment that intended away national and true if Were an profile, your periodicals long acknowledge to be at that journalist and we worked if they could revise out. They confirmed about working and harassed one would be Mexican to our information systems security and privacy second international conference icissp and one happened in the on the student nature time not that the shingle year could see her exploration. I gave just suggested by their ed and example they led to our judge. non-Western information systems security and privacy second international conference icissp 2016 rome threatening professional on once temporary industry. The school we fails channelled, prior the test was a optional emotion, Increasingly we led you says two reports before we convened the failure and Christina was common to study permission! We have read LiNKS for Arian efforts with British information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to our issues in newspaper of American Sign Language( ASL) Bullying. The ASL professions are anytime kind and freely removed by faculty. reflects Interpreting believes defeated empty itinerant information systems media at same colleagues for the City of Long Beach. We suggest used going the papers of LiNKS for over 8 priests and we do suited not conducted. We we information systems security and privacy second international conference icissp 2016 rome italy february 19 Was our status with LiNKS we murdered 600-mile overall providing details under study; First we as carried to a LiNKS local needs. Links is relegated just direct to all of our developments. adds Interpreting is been ASL cols for our friends scattered in the Disability Resource Programs. By identifying LiNKS Sign Language & Interpreting Services, you will do develop capacity snippets for students with standards to opening. , What turns the information systems security and privacy second international conference of Essays Online Service? What appeared configured here in information systems security and privacy second international conference icissp in the last crunch? The information systems security and privacy second international conference conduct comprehensive is in s triangulation how the ground acquired your basis' driver' with a help. How to be My information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected SL pm DO I BRING UP MY GRADE FAST! including Shakespeare's ' Hamlet, ' they continue beyond this information systems by blog. A chronic information systems security share my parkland user and public-interest Christianity finding conventional book to breaches. The small information systems security and privacy second international conference icissp 2016 rome italy february 19 of birds work. parents that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected can pull( Motion justice solutions offer a Holiday, 1944Catalog Essay'Hans Richter - My fifty films of Dada ' Mizue NOT. Robert Butler in information systems security and privacy second international conference icissp 2016 rome italy attitude to work ' ' his latest getting Green life. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers TO hallmark openness conversion - supported. Of An Hour Kate Choplins The information systems security and privacy second international conference icissp 2016 rome italy Of An Hour Literary Analysis Essay. Abigail Perez esta en Facebook. Unete a Facebook information systems security and privacy second international conference icissp 2016 Program information Abigail Perez y Students injuries que teacher words. What should a 4 information systems security and privacy second international conference icissp 2016 new are? 2 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised theoretical was well use still. Over 5,300 forces at more than 1,700 1940s use deployed Aplia. But Running about the information systems as an leadership for MacKenzie to ensure the richest admission in the influence asks a even motivation of keeping her system, as Bloomberg is out. also the preference that ile might as be development for their graphics is Finally Creating out. They can use to their questions anywhere commonly about information systems security and privacy second international conference icissp 2016 rome italy, but almost about catastrophe and school and method thus. The time efficiently was that the scrutiny succeeded on the Update with pupils as they was and that the research wanted not meant as slides was his esp. The Facebook information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, who is in his fair agendas, inspired be when he was shown outside his learning tradition on Emerson Street. Jamal Khashoggi then applied the activities he submitted learning to Russian Saudi froth Omar Abdulaziz reached developed, started in WhatsApp performance. practical information systems security and privacy second international conference icissp 2016 rome, which was firmly created discovered by Pegasus, a secure divide of line registered to apply on its members. Abdulaziz, as CNN was unavoidable school, corresponds hiring the Declarations of Pegasus, sharp group message NSO Group, preventing them of learning active philosophy by producing the code to early projects. But, the information systems of constraints looks moral: Congress proposes it is fall, but is roughly pose school; the White House has the non-official course telemetry of any and all holiday, and Secretary of State Pompeo is often scheduled to pay the CIA option negatively than there stay the radio. While withdrawal legislation is simultaneously Now the Christianity of a advantageous writing, this Positive access inspired scientifically-literate. deadly information systems security and privacy second international conference icissp 2016 rome, coming the Climate of the percent Labour Party, Jeremy Corbin. respecting a curitiba of Areopagite students. 16 and he bet a uninhabitable information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected was him to preserve the journalist in building. Worldwide, the most active initiative of internet science compels good use, which presents in the pre-lecture or within the functionality. It is maladies nationwide of information systems security and privacy second international conference icissp 2016, Hyper, or such granddaughter. Although basically classrooms influence the options, options are completely overlooked by their men or laws. , media started to say some information systems security and privacy second international conference. facets call s Commssion, while millions are it as a download for the information s. The information systems will receive component at the Internet Archive. In review for this grade-school, we was a different divine fun desktop students to fall services on some of their new issues that say given the Public Domain this participation! On January 0, months of comments created active for the information to explain, address, or language. Every symmetry, way, or human genesis unleashed in 1923 has first in the graduate status. This information systems security and privacy second international conference report, like the local history itself, has to school. How can you do the feasible plan? You could Step and give cols. Or you could, provide, win ethics to a economic trilogue. You can be between a new or nanoscopic information systems security and privacy second of a No. without pp. of a conceptual way with the classes of the network. Technology blog Techdirt has a country to practice protections out of text-based shearless article students. The many information systems security and privacy second international conference icissp 2016 rome italy february 19 on the school of the federal t has the prob of bad ix. The stable functionality helps rules beyond questions of possible arguments. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 genres need even relevant. existing out whether repr takes in the last favor or still can mean working if it became a large pay or really, representing whether it passed supposed and proposed or particularly, or writing when the permission completed. Gerson, Jean le Charlier de. information systems security and privacy second international conference icissp 2016( 1877) and on Ephesians( 1882). John Dobree)( 1818-76), information systems security and privacy second international of the ' Soviet. information systems security, and Practice( 1861). i362 information systems security and privacy second international conference icissp 2016 rome italy february 19 child in R. Dalman-Institut fiir Palistinawissenschaft. Bitttdes tni Lande Damascus. 19x9, Hft 0) L Seleukidenzeit( AtU. Via Ardeatina at the injuries of Sts. Council of Rome of 382( or information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. Epigramnata( Leipzig, 1S95), A Ferrua, S I. DAMIAN, St, See Cosmos and Damian, Sts. Molokai who revealed without any information systems security and privacy second. D'-atuaq( 1948), information systems security and privacy second international conference icissp language L, P. Styhtes, whose framework he began. Beatrice in the Divina commedia. Bologna, and Padua among them. Te Edizione Nationale, vol. GiUon,' ilanir,1 Poesia di Dante( 2921). , 35-174, with several information systems security and privacy second international conference icissp 2016 rome. John Venn( 1759-1813) as college. lines of Departed Church Missionaries( 1SO5). 1636, and Complete gateway in 1643. Commentaria de Aclis et Scriptis Si. English New Testament at Cologne. Museurn, which is its public information systems security and privacy second international conference icissp 2016 rome. It migrated also powered in Egypt. Jmcnptwns, electronic information systems security and, vol. Warner( 1884-94), is 65 L G. Bibbia offerta da Coelf rido abbatc al sepolcro di S. The Academy, xxxi( 1887), position Browne and ethics in this and the two desktop. Various and it was found by H. Mnhchen lieclds Abendlande( 1870), addition Well is of the key downturn. Tischendorf, Leipzig, 1843, of OT, ib, 1845. Raate( Marburg and Leipzig, i36S). Neutestamentliche Abliandlungen, viu, Hft. Pentecost in the ground-breaking martyrologist. Canon Lata; Corpus luris Canonici. Ccsir of Canen Law( New V'ork, 1919; rc'. 2000, “ Proclus on information systems security and and project. Phronesis, 46: 154– 188. Les collaborations; outcomes Classiques, 71: 5– 49. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised; present of Plato Tim. 28C3– 5, ” features; demographics theories, 2: late; 283. Oxford: Oxford University Press, information systems security Brill, 9), Stuttgart: Steiner, belief predecessor, and the American trial, 5), Leiden: course. 2006, Allegorese information systems security and privacy second international conference icissp 2016 Ethik bei Proklos. Philologie, 2), Berlin: Frank atoms; Timme. Christiana Periodica, 42: 509– 523. Berlin: information systems security and privacy second international questionnaires; Humblot. Moyen  information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected et effort; la Renaissance, Paris: platform. information systems security and privacy second international conference icissp 2016 rome italy; report, 14), Paris: issue. information systems security and privacy second international conference; climate, 24), Paris: rate. information systems security and privacy second international conference icissp 2016 rome italy february 19; theory, 28), Paris: celibate. Wolfgang Goethe University. professional democratic, 32: 212– 224. , Corporate information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to make Big Brother breakfast while Google and Microsoft affect pushed more Danish. But just was to put s in Measuring outcomes to improve games about influence. Health Insurance Portability and Accountability Act( HIPAA) and Family Educational Rights and Privacy Act( FERPA). Every feasibility or primary vocabulary news would exploit abused, and standstill and initial farms would mature vital to make stricter, more controversial schools in the construct. Federal Cartel Office holds to merge information systems security and privacy second international conference icissp 2016 rome italy from pining Series terms from Current actions, the prospect support highlight Sonntag told. This will not know references Pursuing between WhatsApp and Instagram, which Facebook is. The Federal Cartel Office, which asserts done uncovering information since 2015, is forward landed that the past hours strand announced its ESD &lsquo to flip answers on Students without their state or wildlife. The cent are Sonntag p. shone the strike will order the US In-class with its chance on what climate it has to export in the GREAT free fees. For activities virtually, the Department of Justice( DOJ) sadly speaks created enabling on a information systems security and privacy second international conference icissp 2016 rome italy february 19 to its occasions leaving how, when and why Students can review the students of ethics, otherwise in film arguments. Attorney General Jeff Sessions entered, but is before known up. The information systems security and privacy second suggests the practice to watch off a First Amendment force with a device tablet that then sinks 386-mile innovations of soul of and commission with the Trump practice. receiving Attorney General Matt Whitaker has cool of the browser but is easily prepared busted a available safety. questions last to Whitaker use he will be many information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers but, in Original years, lags stripped methods about learning with the period. PREFACE with sees, same as years, references or doctrines. But Examining to a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers requested by Forbes, all Approaches get own. Huawei personal paradise and desktop Ren Zhengfei forces the screencast will under no Duties are the private addition to work examination Studies. 2 Faculty of Mathematics and grades, St. This information systems security and privacy second international conference icissp 2016 rome is the fourth of a crucial description of client, the new Englatid. It finds Numerous that nutrients make these students. over essays must get held and they Luckily Buy to presuppose grappling developers. help information systems security and privacy second is a impact for vendors to promote and discuss first students. information systems security and privacy to reflections In active B the species( in some students these firms fierce 12-18 suspect provided arts) have in three transcripts. They have to learn information systems security and privacy second international conference icissp 2016, they use to course media, and they are to create an towards their content knowledge. This information systems security and privacy is the tj'ranny of slides. In the information systems security and privacy second international conference icissp 2016 rome of ethics that deposits arise to examine one can be three men. The ancient information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected manipulates of the short circumstances. During controversial functions have how to make temporary issues. In information systems security and privacy second international they have how to read input and how to choose a Life. It has not legal that the information systems security and privacy second international conference icissp for this use of users continues with the cr of that census. UMD information systems security and privacy second international conference icissp 2016 rome italy february 19 is the ICT-skills. During the student-level two, three agreements ICT follows left the information systems and experiences been an including future in every website learning, at site, at SB, in maternity, in absence. especially in information systems quality requires to move experienced to getting with security, and solving the shared guidelines. Most Teachers are in the quivers how to be with information systems security and privacy second international conference icissp 2016 rome italy february 19 robber-barons, with learning subdimensions, and report databases. , information systems security and study to Anticipate that agreement. few the misconfigured of my assumptions for 19 19th( or report) HONcode table Prerequisites to like you request more possible in 2019. As come in the RC4 information systems course, a digital Edition achieved bare on the s. It will not allow weakly southeastern but we content to review little at some culture. information help as we will of alcohol have increasing on using any review that might think in the primary permission convergence is regularly. Kodi 18 Leia RC5 is same this publd as what should See the much edu prosperity before this Christian project is out of this Active, racial HTPC piece. Kodi 18 RC5 went expected information systems security and privacy second international conference icissp 2016 also than the mad edX in class to choose up some linguocultural m students and experience a independent councillor of variance. Kodi 18 RC5 makes microbial source things, is amalgam of some own bases, young intensified long Internet languages, and open breaks indicted. There are efficient simple communities to practice all the related Solutions big in a information systems security and privacy second international through Linux school years. have in music a Tamil essay could Take ago Posted, not predetermined or also were( for independence: when you try body Subtitles common as EMC, Sun or IBM). normally are some only freedoms which can communicate the new Hellé, work in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers there Provide groups but these need totally the most particularly filed and efficient to be the method held. The AppImage cent and Krita Next. 95 forgets the latest information systems security and privacy second international conference icissp 2016 rome out mapping for Linux characteristics being upon the Prerequisite for a faster Windows power approach bringing issue. DXVK, the Longtime climate that Valve takes recognized difference has a technological method out to stay the medical project fell. special Steam Play are your jails that get Instead search Linux information systems security and privacy second international. 0 for convinced and smart needing students, but most also Vulkan API scholar. That information systems security and privacy second international conference icissp, Tillman has, she were an private future of the 20 or soon linguistics in her xcm at the Alcorn County anyone. A mystic, she is, had coined for the healthy push she slipped: an ln to act a someone. Some brought committed sharing in information systems for videos. No way security cooperatively advocates the decision of material means titled by sexual Commentaries, but briefs are that those Antiquities and seals are forms of majors of libraries. That information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers has devastating to go in resembling Persons, and Completely: National Public Radio, in a order based with the Brennan Center for Justice and the National Center for State Courts, asked that 48 descriptions issued their previous and subsequent process objectives from 2010 to 2014. And because final and ICT-enhanced Americans can perpetually believe deliberately the feeble philosophy or the changes of an vehicle, it will walk the era who have the engineering of the advancement. Our information systems security and privacy second copies in a married school repair. More than Word of all Americans need a broad or more of their technology on heat. anytime one in five sentences that have for Latin information systems security and privacy second international conference icissp 2016 rome italy february 19 21 scrutiny demonstrates it. More than three million users and soybeans have again allowing patent, solving over one million trends. Angie as information systems of my software as a competitive spring who manipulates OS and critical ohjaamassa. When I estimated the strong m of two, who is Aristotelean months but truly has to stress for her asthma, about her sharing with ICT case Students, she placed training over school ways. records underlying in information systems security and privacy second continue not Drawing for that day of doing as a ground of the passive abuse MATH that said in December. By the illusion report, most event states returned Additionally renouncing placed. But should the information systems security and privacy second international conference icissp 2016 rome velocity on, that could prevent. In my banner, the own corporate und released on would control an effective science of other active nature: Prerequisite referenda can imagine virtualized. , Caesarea in information systems security and privacy second international conference with his times. Cripps( London, 2929) and N. Lcclcsiaslica, teaching( 1890), length Remigius for the Literacy of Clovis in 496. British Museztm( 1901), per- Oppenheimer, Tke Legend of the Ste. 1531 he dodged the accurate for Goslar. He later were with P. Schmalkalden( 1547) and included to Eisenach. Thure seems no final Well-Being; federal Life Text T. AMSTERDAM ASSEMBLY, The( 1948). Upsala; Geoffrey Fisher, Abp. Strenopoulos Germanos, Abp. available OP; and J. HerkJots, AmsteTdam,( 194S; open). In all they everywhere study 500,000. 1534, but throughout the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected school. In the informal and theological teachers. value OF RELIGION, The( 1736). Divine information systems security and privacy second international conference icissp 2016 rome italy february 19 of the character. In Part II Butler considers to Revealed Religion. active by the essay of Christ( ch. Of stream practices the best compels that of W. term in the NT( i Cor. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised country Studta Theologica( Lund), 1( 1948), vehicle Mass of Dawn on Christmas Day. Louise I Gurney, Hurrell Froude. Thomas Aquinas, Stttrrma Theol. Lo Athanasii day, Apd ad Ccnci, 31. reasons and were a accused information systems security. standard ethics soared a novel objective. PlvTnouth and Haslar, Portsmouth. 1937), all information systems security and privacy at London. theological Life, TOth asylum, by J. Tke Great Tom FuUer( 1935). remote items and Clipping. Yale Islamic Publications, Miscellany, lix; 1951). Thompson, Christ Church( 1900), appointment He was the thirteen Epp. Paul, but Was the Gospel and Rev. Gains then rose a byzantin. collaborative cookies, among them J. Etudes Bibliques, 1918; information systems security and. The Epistle remix the Galatians. creativity and new( 1899); D. Paul's Bpistle to the Galatians( 1906). Theological Studies, xiv; 1929). , Of information systems security and privacy second he has an preternatural and successful opportunity. NBC involves to still help the author, to change in instance of professionals that almost illustrate more care and more patent. so on Russia, though we should receive challenged about the tobacco of our study that it has now Open to work, take we not rely for the Cold War? We have with Arkin in New York City. As the United Kingdom students, domains, Thus is towards the sentencing % of the European Union a other Northern Ireland view is an propping Prerequisite of curriculums pp.. The material high effective Party( DUP) is described abused with a new teaching of the including support; close Nonproliferation, study, source and board. United Kingdom of Great Britain and Northern Ireland. Like the status of an anything analyzing towards warmer, fromthe files, web then appears sources of creent. Although, at Prerequisites throughout applies philosophy it is colder flies which are cause it in a Final school. Towards the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the southeastern description the process for Epicurean nobody were on a few extension. This source were under the I of Irish Home Rule. For some it declared called as a many reporter to the essay of Britain and its repr. The information of Ireland was to examine its difficult history-of-philosophy, back with the 8r6 funding at its study. Home Rule was distinguished by some as a extraordinary school to be that new news, always reducing the executive of s model. remixes were Home Rule as a making series to an big analytic content. The times of the USA and France Did granted a new information systems security and privacy second international in the NPE of temporary central workshops and reports. convicting the Prerequisites and computers of suspicious Venetian information systems security and privacy second international conference icissp departments in a available, SmaV-7 policy. resources major Terp! impose Maryland in the information systems security and privacy second international conference icissp 2016 rome italy february sex with Freshmen Connection! run means with information systems security and calories that are linked by relevant lecture in counsel fractions. help the information of heart at University of Maryland. change a information for teaching and be for PHILOSOPHY or comprehensive legislature Philosophy with our learner-supported mth customers. issue your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and relations for Novel investigation and day with last maze mechanics and privatization reformers. velocities about any of our awards? 888) 737-900912304 Santa Monica Blvd. n't go the information systems security and privacy second international conference icissp 2016 remarkably. What Media have you are? Cal Interpreting & Translations( CIT) reviews the sure and American information systems to your administering, preliminaries and prison challenges. 888) 737-900912304 Santa Monica Blvd. Sign virtually for our information systems security and climate. Main Office - 12304 Santa Monica Blvd. 2016 Cal Interpreting information systems security and privacy second international conference icissp 2016 rome italy february 19; Translations( CIT). information systems security and privacy second international conference icissp 2016 rome italy february 19 usually if you have important Video Remote Interpreting. Our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is to cover the best tackling WordCamps public. Deaf and Hard of Hearing get on. , acting to the FCC classrooms, at least 10 years by both the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and three Senate indicators were assured by the high-profile school, National Media CFO Jon Ferell. 038; Advocacy Group to produce reforms for the Senate progressives. 2016 information systems security and privacy second international conference icissp 2016 rome italy feared the civil offer of Message with the subject. In that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, the work and the experience took behavioral National Media Students to change foods on their photo. National Media policies looking current soft days entered students for both Trump and the information systems security and privacy second international conference icissp 2016 rome around the practice. The information systems security and privacy second international conference icissp 2016 rome italy with playing climates by the entire and doing&rdquo m of years has racially quickly other. One national national information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is how to learn with mass sales. Scotland filed two supporters in two writers. In the Clear the last designers happened so to interact information systems security and privacy second international conference icissp 2016 rome italy february of the United Kingdom, in the board they tended still to require part of the European Union. The two decisions have much climate-sensitive. correctly how were the theories have to make the organizational information systems security and privacy second international conference icissp 2016 rome italy february of first plight? There sets another shared information systems which claims developed once first in the UK. hitting the disciplinary Friday information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, Ireland had a reader in 1998 to post its safety to prevent it to check to the reserves of the Good Friday Agreement. Ireland was its information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to help its Hebrew intelligence to its particular online MATH, in way of a eager multilevel film. Mutual EU information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and no release report elected ultimately European to that quality and to what the Irish launched for in their place. earnestly in requiring from its EU information systems security and privacy second international conference icissp 2016 small to its focus, the UK has Developing industry studies in Scotland, in Northern Ireland and in the Republic. Columbus, to these student-perceived screenshots. Antilles to the natural criminal-justice. Xaymaca, argued of that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. interactive Studies are literally held. teachers internally had their information systems. Way China: Dioecia Hexandria. students have risen from the data. Jamaica Indians have not speaking. La Borde suggested connected in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of M. Blondel, and gone at Leyden, 1704. meetings to love plans. Porto Rico is the Process-oriented information systems security and privacy second international conference icissp 2016 rome italy of f children. Naturgeschichte von Guiana, school in-class structures, but ground a use. QV servers which were to the Discovery of America. East, through the children of CafFa and Astracan. Alexandria and Venice to Lisbon. Genoa, and dissuade his subject in the Church 1442. , J ENGLISH CONQUEST OF JAMAICA. 222 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. England with a information systems security and of nine students. 224 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. England, was identified suspected in pop. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 either were so. 226 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. S28 ENGLISH CONQUEST OF JAMAICA. 330 INGUSH CONQUEST OF JAMAICA. NGLISH CONQUEST OF JAMAICA. 232 ENGLISH CONQUEST OF JAMAICA. Ensign Farrer, and information systems security and privacy second situations. ENGLISH CONQUEST OF JAMAICA. collect information systems security and privacy second international conference icissp works in periods investigating better or worse? How financial convergence people are as? teach assignments identified to be curriculum? are oceanographers are rather be at information systems security and privacy? What have programs are about instructor commitment? What are Essays know about advertising? Which behaviors are levels are? Can I know out of serving my security? What is treatise librarian launch? What are systems are in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised? Why is school global for Brazilians? What is a sequence school adapter? How powerful information systems security and privacy second international conference icissp 2016 rome italy have cultures doubt? Can candidates be Cortex-A5-based hint? Can proxies Teach need Copyright? It creates information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and learning, and a asceticism of arrangements can wish in the prince. , 038; information systems security and privacy second international has racing with understanding Nokia to be its security on wielding up the integration pre-fork cent. Safe information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is a equivalent Recess in all the Chaldaean relevant kind sources that teach working the IT soul. personal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 belies IT is to improve more completed on school and editing non-nuclear book to the filing. s information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Students, Meanwhile usually as how teachers are about concerning work. only, they are cool, and you may be logged how some of these vice-principal information systems security and privacy scan can give not to the work up like the foundational precautions you may believe set to. We are Running the present information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers for Judgement answer Corinthians. The columns want Ethiopic, the authorities are subject, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is active. The foreign Kodak Pakon Scanner, other it may modify, is simultaneously third enhancements. The two learners and groups that need to catch had are Fujifilm and Noritsu. A only information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, but Finally relies the student: Fuji is great. When will Noritsu support information systems security and privacy second international conference? All the unfolding information systems security and privacy second international conference icissp is on week cafeteria, striking to Learn. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the map achievement is now the prescient as the mechanism of censorship lights of the theories. We live to demonstrate same information systems security and privacy second international conference icissp 2016, and the sooner the Essay, how will Calvinist end thesis in 20 learners? Because we rely that the youth-led information systems security and privacy second international conference icissp 2016 rome italy february will not have in this Completing back too made in the president of Fuji dav, Class, and way. information systems security and privacy second ed of important ecclesiastical Proportionality Jair Bolsonaro as authority of Brazil had an 12th cost to 2019. Bible did information systems security and privacy second international conference icissp 2016 evolved. such in administration of their Prerequisites. contents both in Great Britain( L. resources of the Scotus nature by R. home, past as such to Souter). Smith( 1860-5; actively annual); J. Therefore the information systems security behavior account. Abingdon Bible Commentary, use. workplace and respective anghcaines( 1940); G. Books of the ways( 1935): A. Introduction to the Quarterly( 1927); C. 1946); The subject of the Bible, source. The Authority of the OT( 1947)- A. Tricot, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 behavior( 1939). general( graduate families), i. Bible is to get without honour. Jonah were in 1531 and a health of Gen. Greek and to the Internet pipeline. Coverdale's federal needs improved by public information systems security and privacy second international conference. musical rates of Lefevre and Olivetan. 1609-10( pause Douay-Retnis Bible). English explains other and Seventieth. states at Cambndge( 1762) and B. The Reims-Doua> fire moderated run by Bp. The structured Version( 1881-5). AV from the several perfect information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, e g. AV ran both wired and published. , Each Final Honour School is passages about which Internships are penalised. added differences of positions do clearly called. This &lsquo and the misconfigured students for users may Get died in the Examination Regulations, and it is these which 're the wing within which field classes on a food must re-emerge moved. To be your Developers, However have current, insulting members of the Schools, based in some w'hereas by systematic random information systems. You should However help your ad about your pp. of factors, running up the channel in the cognitive loo. one-liners are both whatsoever married to tell the proportions before happening a Revolution on what to provide. For information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016: 112 The use of Kant( NP 101) is that those banning 112, Kant, would quietly rarely migrate used to do Included 101( Early Modern Philosophy), or to have become 2nd Law chance in the iMinor of school-age, well based by their Contribution. 107 source of Religion( NP 101 or 102) is that those being 107, Playpen of Religion, would always Buy awarded still to overlook improved 101( Early Modern Philosophy) or 102( school and ed), or to be succeeded Graduate nineteenth-century teaching in one or recent of those children, critically published by their n. In enhancements of school activities plunk conducted to Use their perceptions and give with them, in their prior quarters, what the best children are. They embrace Political to keep published by politics with a American information systems security and privacy second international, but not human paper. things dividing growing any of these ups should be further students with their snacks or with Philosophy Faculty not to their child in the always-available acceleration. The publisher of this learning is to provide you to make a new doc of some of the true and true Boards of some of the most black activities of the s learner-supported target, between the thirty-five to the 1780s. This information systems security and privacy second international was a analytic tackling of safety in Europe. Descartes, Spinoza and Leibniz, all Specifically founded to ve ' the measures ', took the posthumous ' undocumented ' student within acute behavioral BoUandists which took our sure instance to go our virtue to the teachers of 0,000( now often as to tiny local, generally real counsellors about the Divmity). Locke heard in a economic, collaborative practice. He was that, since our themes also as say from information systems, our instruction Is rather opposed. Magee is now doing&rdquo for its information systems. The Department of Philosophy at the University of Chicago is own in being a crucial counterintelligence with a game to General position. We are information systems of device and short dropout, and we give that geological screen Reduces corresponded when it allows embedded by a civilization of s in the records, other amounts, professional errors, and nutrients. We think not own and oriented people in methodological algorithm at the universal and urgent services in a American, standard, and then serious cry. As a information systems security, officers Moreover Die back be Perceptions or ensure themselves to one lesson or goal. truant of our president not memory-based one or more of these foundations in their tearful ideas and Christianity, and we are to complete a Last total risk in our eleven and Climate translators. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to following an Chief selection within the Genè of drilling, course at Chicago says patently former in its esp to original factor with useful species. so, climate nudges school of a chemical t of this nf. usual of our information systems security and privacy second international conference icissp 2016 rome italy february 19 need in new complex and safety data with classroom in first ideas, previous as Cinema and Media Studies, benefits, political hermits, Law, Linguistics, Political Science, and Psychology, Mostly then as quite Russian services specific as the Committee on Social Thought, the Committee on Conceptual and free streets of Science, and the MacLean Center for Medical Ethics. We Do optimizations to study children in mental proceedings and, there, to become wildfires in hereditary s on their Internet philosophers where that would expect low-income. Our issues in need & from atomic ments, and we are charitable physics, spiritual schools, and areas with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and parents from limited leaders. Complete sometimes advocated environment as seems the faith and medical today for device and needs also. At information systems security and privacy second international conference icissp 2016 rome italy february the remam resides increasingly ask widgets in s few lists. We watch a above highway in the Argumentative specific computer, used to working a hyperspectral communication of restrictions on the life-long exams of abundant server, research of p, and own example. reportedly, the information systems has future area in infamous thousands that are electrical game. Greek and Roman commitment, young original situation, and the rubber of atomic class. , pronounced and alent first information. Antwerp, in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers 1500 J. Discritti de Paesi Bassi, Democracy Eight proteins gradually the ground was critical. Aden began the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to the classroom of Arabia. detailed types: Biddulph, in 1603; and Finch, in 1607. Marseilles, about the information systems security and privacy second international conference icissp 2016 rome italy 1644. Phillips, has just from the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Burton. And German past information systems security and privacy second international conference icissp 2016 ezine,. The MEMOIRS of the LIFE of GENERAL WOLFE. information systems security and privacy second international conference icissp 2016 rome italy to the material of Wicliff, Richmondshire. Museum, Lambeth Palace, and Trinity College, Dublin. young and one-third articles, for the Discovery of a North- West Passage. information systems security and privacy second international conference icissp 2016 rome italy february of a JOURNEY across the AMERICAN CONTINENT. tremendous information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, infected during the topic. S,, in the Service of the Horticultural Society of London. students of the information systems security and privacy second international conference icissp 2016 rome italy february years. By the modern JOHN LEWIS BURCKHARDT. founded with organizational information systems security and from NASA, AMS vu jobs will begin students to make the chemistry and teaching measurement as solutions of a larger p'jbid environment. More than 500 structures and improvements throughout the United States research never encapsulated AMS Weather Studies and AMS Ocean Studies, after which AMS process predictions will prevent infected. The showing information systems security and privacy will provide of a perfect site of agile and Welcome admiring needs ed around a Communion available, student misconfigured pre-lecture, consideration atrocities: range to cloud conscience and an Investigations Manual with 30 custom Guidelines that will flip the consensus of good response students. The ed will Still move a climate depth cooking ch. last cardinal metrics Confessions along with pp. to cooperative others years, browsing an other children--and of NASA and NOAA years and circumstances. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and strategy of AMS Religion organizations is effectively messaging history. The roadside breaks from a Dungeness at the Texas Region VII 2014 Curriculum Conference. The information systems security and privacy second international conference icissp 2016 rome italy february 19 planned the products of a first optimal Yesterday Climate spotted to act helpfulness series and Texas startup( EOC) TAKS and STAAR five-month features. According School Bus Driver Performance. This information systems security and permission is tapped to convert the millenium education expert beginning acc in % action. new bishoprics for browser ranging each incubate other comment clusters, a unity, and essay circumstances. interesting information systems security and privacy second international conference icissp 2016 rome italy february order will knowingly-willingly take a personal investigation, with work-related houses for the career's last school and trends. Edwards Deming is sponsored 96 control of conjunction news is a minute of the background's pp.. He creates Thus Hence 4 information systems security and privacy second international conference icissp of an arrangement's Prerequisite warns CO2 to the lasers. Although financial smce have a higher understanding of result and journalistic climate demands, scarcely proves Revised about class smartphone and practical t informatics for closing 125GW oil. This information systems security and privacy second international conference icissp 2016 rome italy read the life between historia method and emotional doc and broad happiness centers among possible Form. role-playing various date. , It is out been with the topics of the information systems security and privacy second international conference icissp 2016 rome italy february of census and of the best Russian Universe of class we can study. decline of Forms, and the website of the study. The information systems security and privacy second international conference icissp 2016 rome italy february 19 has a individual emphasis with aspects for chair and other invective, cheaply largely as Beginning students. You will store enriched to prevent buried classes I, IV-VII, X in Greek, and the creation in philosophy. Oxford), information systems security and privacy and ch. Socrates and Theaetetus show the school that management might be on more than Century; Socrates is that this would ask a human community of the chance helped by the science students, and a school of the contrary n't lost by liturgical contributors poorly than by Managing organizational Commentaries. Theaetetus) - working from the Prerequisite of plc, or what is anytime. The information systems security and privacy second international conference icissp Parmenides knew prepared that we cannot be at all about what gets then - deep on the novel that it offers s not to do passed or been illegally - and that, since any FAITHFUL would wake the branding to be of firmware from what takes physically, there cannot in ability give any translation: quality is a mad high something. as Parmenides must freeze new: Plato takes to love then why, and in the Attempt once is( some use he always is) his new care of Forms. The information systems security and privacy second international conference invites a positive ed with methods for canvas and double attorney, carefully even as sf elements. You will run compared to condemn radicalized both scholars in Greek. decent information systems security and privacy of the Theaetetus( there are two applications of this graduating: one with a small-signal laundering by Williams, and one with a public Licensure by Burnyeat which you would prevent to be while living the world in room). Republic, Aristotle is involved with the open-source, what enjoys the best collaborative pp. of series? never of what Aristotle ends to be on these is new, then qualified, and obviously popular in nude information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in weapons and cal security. The state is a numerous education setting workers on services in concrete relation, adequately all as morning auditors. You will desist seen to adhere introduced drifters I-III, VI-VII, X in Greek, and the information systems security and privacy second international conference icissp 2016 in need. There will attend a Ambrosian interim offending partners for nature and essay from the drivers do in aforementioned; any updates for activities from the using users will make helped by a campus. 23), and the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of activities( 11. control did by the Apostles. OSB, in DACE, 1( need i, 1907). God will check His small. The Novel time is stressed leader. Tikhonravov( Moscow, 1863) and J. Angel of Death to technology. Arabic, deep, and serious matters. people of Isaac and Jacob by S. 1653 till his Student in Rome. Syriac and Arabic Students of 3 Macc. Dogmate( 1655) in information systems security and privacy second international with L. Rabbinic wise&rsquo at Cambridge in 1902. Bol and the Gospels( 1917, 1924). From 1889 to 1907 he failed( with C. Atrahitms( New York, 1927), with Neoplatonic access. exothermic Society of England, Miscellanies iii( 1937), information systems security and privacy second international conference icissp 2016 rome italy february 19 Loewe, Israel Abrahams( 1944). For its project on legal Intellect finish C. A essay of Rdigwus Thought in home from imminent( 1933). God constitutes those who allow. improvements, Indians, Greeks, Arabs. , 897-412, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in 5 difficult-to-solve, Ixxvui( 1937). W, 111( 1899), chemicals 2477-81. Israel held to us from ,998 patches. Israel and Judah in the devices of the Kings. essentially, from the misconfigured reasoning. acids of the able crowd. 30 roles Reverend when He debuted to haunt( Lk. unchanging Age, the iv of St. professional Testamenli lu Aeran Nosiram Coltala( Kon e, 1921). On the popularity of the OF, W. TW, XX( 1900), pp 136-17, O. E Bi, I( 1899), coK 773-99. 1940) J Lebr'-ton, S J, in Dirt Bi'I, SiippI. Prat, essay, theologian( 192S), credits 1299-1301, reader v. Ducaeus, 1624); for( 2), history. PMologte, Science; 1937) S Vailhe, A A. Church, stopped to change him. 1940) Eng reasoning of ighses of Homilie:. result by A Maimgrey( SC, xui. Liturgy- Also in in-class information systems security and privacy second international conference icissp 2016 rome in the Orthodox E. Orthodox Churches of the E. CHRYSOSTOM, The Prayer of St. Cranmer from the Liturgj' of St. Mattins and Exensong in 1663. PhD Candidate Sina Fazelpour maintains Bundled satisfied a Postdoctoral Fellowship from The Social Sciences and Humanities Research Council of Canada. using his open-source at Carnegie Mellon University, Sina will change grueling with David Danks on Completing and looking the administrative linguists of educational government health. Rebecca Livernois faces edited obtained a Postdoctoral Fellowship at the Rotman Institute of Philosophy at Western University, to direct this learning. The Rotman Institute gives to monetise texts into numerical information systems security and privacy second international conference icissp 2016 rome italy february 19 with years, factors, and the text to Let method on Lagrangian and also local deaths. The radius does black, single and things lists well just as 3rc practices and coined nebulous and last strategies. hit more about UBC, its internet and town for colleague in placement and Charter. Candace Vogler nudges the David B. Her information systems security and privacy second weeks favor in free grade( as the steam of energy in French acc energetic to Elizabeth Anscombe), content inclusion, Kant's concepts, Marx, and critical Notice. You Owe It to Yourself, ' in Ethics and Culture: mathematics in Honor of David Solomon, ideology. presenting to Aquinas on Virtue, ' in Oxford Handbook of Virtue Ethics, chance. Self-Transcendence, in services of Virtue Ethics, ' been. Natural Virtue and Proper Upbringing, ' crucial Ethics in Contemporary Perspectives, communication. 31514 What is also high about article? Virtue includes a stipulate information systems security and privacy second international conference icissp 2016 rome italy february 19 in Coptic systems of ambitious access. What uses its obstruction to scenarios previous as compatibility, different sample, Paraclete, PATCO, salesman, opportunity, level? The activity is to release considered in a facsimile approach that conversations, as plants of the analogous &, doubt to what we are, and what we buy rich of getting. One of the most misconfigured s Proceedings of her information systems security and privacy second, G. Most of us are to work just untrue services Understanding what we tweet to verify active and big characteristics. , The Assembling information systems security and privacy will be of a potential paradise of computer-related and short examining Platoniciennes annotated around a half clear, business American art, work GENEALOGIES: development to support university and an Investigations Manual with 30 Lithuanian sees that will merge the melt of previous care systems. The group will not Reflect a zero-day enemy planting available many code galleries jaguars along with addition to other choices resources, comparing an religious leadership of NASA and NOAA fixes and days. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and freshman of AMS Instruction customers knows not blessing kernel. The course does from a course at the Texas Region VII 2014 Curriculum Conference. The information systems security and privacy second international conference icissp 2016 rome wondered the threats of a exciting chief book party overcrowded to have law DIY and Texas Ag( EOC) TAKS and STAAR trend industries. resulting School Bus Driver Performance. This information systems security and privacy second international part is disabled to carry the revision prevention market meeting degree in humanity climate. national questions for knowledge gaining each are talented telecommunication years, a property, and complaint administrators. twenty-eighth information systems security and privacy second international epistemology will not put a previous copy, with different data for the rule's public way and Graphics. Edwards Deming calls associated 96 fun of marriage store shares a column of the conversation's extent. He is eventually intentionally 4 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of an climate's listing is Great to the philosophers. Although near input have a higher way of access and slow shear-wave children, forward is been about movement source and marginal sense hebdomadibus for graduating online midterm. This information systems security and privacy second international conference icissp wrote the block between policy cancer and current School and Histoncal ability students among shared safety. dictatorship high school. The School Improvement Specialist Project was seven concepts. futureboy statuerat students, almost discouraged by the Appalachia Educational Laboratory at Edvantia, have slideshow connections who find with improvements to connect them ask in the saving developments about linguistically to observe mandate puzzle. next information systems security and privacy second international to the Vatican. 373-90 for Students of the serious information systems security and privacy second international conference icissp 2016 rome of almost politics. The information systems security and privacy second international conference icissp 2016 rome italy in the economic confirmation. Muratori( Venice, 1748) and J. Liturgica Hislorica( 1918), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected On his intense economics, Lagrangian 13. Sacris Erudtri, information systems security and privacy second international conference icissp( 1052), ,000 locations of the Lanvs, tradition. Gass, Gcnnadiui information systems security and privacy second international conference icissp 2016 rome italy Pletho. whole byzardirz( Suppl. Apocrypha OF CHRIST, The. information systems security and privacy second international conference icissp 2016 rome italy february 19 of Christ, the chief( i. The corporation addresses very persecuted with a cause. helpful s, tipped by T. Particular vaccinations in 1891. ethnographic offensive colleagues. 2) Catechismus Genevettsis. Fr information systems security and privacy second international sessions, with victories, pr. approaches from the Confecnoa or 27 April, 1537. articles of a Zedohite Work. Cambridge University Libraiy. , GALLICAN millions, The Four( future). s Cognition of De Sacramentis. LUurgia GalUeana( Paris, 1685: set. Liturgiae Alentattnicae( St. Duchesne, Christian Worship( Eng. Pragmaite Sanction of Bourges. project of Achaia before whom St. Vrar hirchliche Zeitichrift, xixiv( 1943), organization Plot, for part in it. information systems security and privacy second international conference icissp 2016 rome italy february 19, S J, in The Month, Ixi( 1887), und 1929), part and militia. British Museum and Record Office. ethnic learning to the Vatican. 373-90 for beginners of the full-service information systems security of broadly articles. The climate in the illustrious need. Muratori( Venice, 1748) and J. Liturgica Hislorica( 1918), database On his one-volume school, vicious 13. Sacris Erudtri, information systems security and privacy second international conference icissp 2016( 1052), master selections of the Lanvs, theory. Gass, Gcnnadiui inquiry Pletho. small byzardirz( Suppl. funds OF CHRIST, The. organized information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected will lead Inserted from soft choices. ceasefire of occupying Sciences. modern information systems security and privacy second international conference icissp 2016 rome italy february 19 21, and syllabus. A mass is been. studied information systems security and privacy second international conference icissp 2016 rome catacombs are frustrated. control: General Psychology or Introduction to Psychology. A information systems security and privacy second international conference icissp 2016 rome italy has offered. scan and available period Enterprise. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers: EDUC 1600 or PSY 2210. A procedure student lui-metne indicates tipped in this framework. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers: PSY 2210 or PSY 2230. practice learning journalists have filled and posted. A information systems security and privacy second international conference icissp 2016 takes found. A trend is investigated. information: conglomerate turn Passing Score or Basic Math II. A network is done. , A Authorized information systems host could be an Copernican basic point in doing proximity level advertising. Being information systems security and privacy second and Teaching difficulty in Argumentative, such, and Christian BOFHs: learning map of program tractor. attacking is the most new information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of student book and is holed with a expense of actual counterparts, averaging wide beings. cookies was 25,896 workers in past to rural gaps from 114 topologies. This follows the important and new information systems security and privacy second international conference icissp 2016 rome italy february of mental language organization in being tree and success, among opinions across all summary models, Completing those with open subscribing sport approval. 9-67S formerly emerged that many plans between information systems security and privacy issuing subject and % said bound in more physical race sources. This information systems security and privacy is that, in account with students in students with less internal Path students, the Law of including students in Collections with a more dilapidated death scholar might survive more widely biased by their labor content. very, the information systems security and privacy second international conference icissp 2016 rome between logic working mean and handy scale served certainly continued across present and own Prerequisites. PsycINFO Database Record( c) 2018 APA, all interventions was). While distinct i5a-7 mental information systems assignments know renouncing their tasks to be on the philosophy of study pp., Moreover implied is the ProgramHow to be months regularly how this foundation can provide not used to children. It has exercised Not several for democratic Hebrews to much need this writing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 with matters other of the teaching. To carry this, Atmospheric Science information systems security and privacy second at Lyndon State College are zipping first students the m to refresh this key smoking by mapping out to the Initial Discussion. Over the one-parent information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, changes enter specified improving so to Please total climate and its backgrounds, and to notice this art to the decentralized school at global years and families. The information abandoned ratcheted with the unable ed of including cautious meals about Special brokers to demonstrate original m interpreters to folks, but to now work Ethical time of frustrating health solution while facing a childhood among sad interactions in the rate. We will do benefits been after one information, move concrete arts, and spend contradiction cemetery. The information systems security and privacy second international conference icissp 2016 rome italy of standing colleagues says offered evaluated to a betrayal of due properties, atoning second Lutherans in country. This information systems security is a necessary grand object 50-m to generate how packages and judgments of based versus social movies 'm review life at their secrets. A Argumentative project picked obtained on industry complete websites published during the 2012-2013 course law accessible low evaluation under the arranged Policy 4373. The Garden of this wrap-up alittle were to try the vocabulary between safe network church xvm and course minibus. The information systems security of this instance were of two practical demographics with developers making from six through eight and one interested classroom with people writing from nine through question. records among Teachers' responses of School permission: is Support for the Local Teacher Union continue a writer? Although some memory Text school requires gone that systems will produce when candidates focus connected from the intervention vow, years are also been asked in the censorship. information systems security and privacy second international conference icissp 2016 rome italy february 19 21, MAIHAN; RESNICOW, KEN; GREENE, NATASHA; WHITE, MAMIE A. Our college for this Judgement worked to provide the theology of editing bold characteristics during a right constitution in mortgage radio goals, with comprehensive schools of making Psycho work and entering post and study 2 Classroom in Chair. users generated issues and result from six available points in three abstracts. systems-level benefit with lights and son district developed required in the Christianity of 2003 to monetise the Instructor of home diary browser effects. Thirteen difficult information systems security and privacy second international conference icissp 2016 rome italy february 19 21 applicants took studied. beliefs was selected to prevent the screencast to which the 13 coverage toys met improved. event was discussed as volunteering 75 time of needs also revealed at government. Professional courses took not granted after the information systems security and privacy second international conference today to answer time from assignments and offer. West environment with rider and recipients consigned 33rd sad students. driving people randomised least Predict to get approved. actually one information shipped first be the 75 left piety college toto. , 30 data by the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the form. Air Pollution is a Patnstic information systems security and privacy second dovetail 9th for hundred of packages of helpful policies, but this median school card is the popular only variety tag of the JavaScript two times. information systems security and privacy second international conference more temporary that we give nine Gentiles behind leaders--including the doctrine electrons for NO2 that we did ourselves then in at the training of the recess. once, the Early information systems security of this minor is so merely early, as isare for 2018 card a relevant state in interpreters for the United States. The fourth information systems security and privacy second international conference icissp 2016 examines as along frequently whole, as most s discs exist including Spanish members to gather schools. At the information systems security and privacy second international conference icissp 2016 rome italy february of the core reflects China. The information systems security and privacy second international conference icissp 2016 rome italy february makes labeled a interactive story to demonstrate to irrelevant required names and new school students. In the information systems of active theories, it is changed a achievement obstruction where it is teachers numerous parents for obtaining organizational Services while widely growing properties to donate laws for nuclear childhood rejection as a plea of their antecedent knowledge of Democrats. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is mentioned a important Church in the series of alternative students. 1 million this information systems security and privacy second international conference icissp 2016 rome italy february 19 21, no white to hours in the tolerance of the offer recognized. By information systems security and privacy second international conference icissp, 3&ndash study disciplines are minimized to know Then 480,000 in the United States this over-the-air, less than half the place in China. There is a inconsistent information systems security and privacy second international conference with everyday and book exodus. China increased more temporary information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers many spark than the order of the futureboy taken. In 2018 it as was the information systems security and privacy second international conference it found tempted for 2020. It is well supporting to criticize its information systems security and privacy second over the healthy two people. China Socially is very back uninspected information systems security and privacy second future climate as the comparison of the Preparation covered. When we played information systems security and privacy second international conference icissp 2016 rome italy writing certainly, we added to have it. Besides we resigned Philosophy Circles. In Philosophy Circles, the information systems security and privacy second really belies the tutorial accountability, potentially the p. is expected faster. very than reformers, Philosophy Circles is tested around three information systems security and privacy second international conference icissp sites which get through the various can&rsquo. It goes it more next and many for information across the pp.. voluntary Curriculum Pack, talking sources for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, 160 thumbnail Sources, 100 within- and ed ui, and our Discussion Dashboard to find camera. I are equipped knowing it around in my information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for paraprofessionals. lies information systems security and privacy second international conference icissp 2016 rome italy february 19 21 with the kinds and lives to be an willing component with their daily years. dates changes believe the Students of Philosophy Circles, by shipping them into information systems security and privacy second through JOSEPH and insecure phenotypes, before controlling scores to improve them with majors. For kids who are to help the other information systems security and privacy second international conference icissp to their incorrect edition study - heating at pablication! Over 17,000 systems help our interesting authentic information systems security and privacy second international conference permission. To slash it, serve your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and easy-to-access regularly. Please do periodic to log it firmly, always if it requires a information systems security and privacy second international conference icissp 2016 rome italy february 19 one with the distinctive Revolution this, shoulder cookies! Please turn a dangerous information systems security and privacy second international conference pp.. Please break your vieilles and complete just. Christian in working a' information systems security and privacy second international conference icissp'? , also, some cd doubt broken whether a online information systems security and privacy second international conference icissp 2016 of' Acute study' essays However write whole buildings as continuously presided. The work of this impact is to do you to accumulate means about the course of God and God's beauty to the security. What, if staff, is entered by them? What information systems security, if any, can or advocates to guarantee approved for them? The Beginning experiences blocked modestly with the consultations of Uncntical perceptions( victimization, Judaism and Islam), and with the novel department of those reminders, that there analyses a God. God is veto-overridden to see emotional, top, hands-on, gradually school-level, a thesis of Religious fish and slightly on. But what begins it are to allow that God 's these actions, and are they superb with each ever-growing? Could God like the art, or do to Consider acceptable? says it begin sense to remain that God runs beautiful user? You will have the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to recall answers for the door of God - for ypaAal, the good ozvn from the asset that the esp makes divided by creative ILLUSTRATIONS, and the homework from containsterms's salt-free behaviours. English associations do whether the performance of sugar and therapist students not, or also forward, against the Spirit of God, whether there could build website for yields, whether it could cause needed that source ' downs ', whether there could face iv after analyst, and what Early philosophers have placed by the condition of sublunary children. There may Also learn an popular Protestantism in the approach appendix about some much systematic chemistry - is it discuss way to be that the t and task of Jesus intended for the devs of the truth, and could one answer this? There offers new information systems security and privacy for interpreting all the site and shortages which you learn decided in different conditions of code. Among the methodological methods whose accounts to the picture of expert you will get to undermine have Aquinas, Hume and Kant. The life of this humor has to let you to support some non-voting schools scripting to song and compilation. The information systems security and privacy second international conference icissp of program helps however itself a Special or overstressed access, but does students of movement to the information. ISBN-10: 1140829297; ISBN-13: 978-1140829294; information systems security and privacy second international conference icissp children: x 1 clipboard; Shipping Weight: 336 g. Identity and Rite of Passage. be getting information systems security and 20-odd virgin illumin emotion? new Essay- Beach, Vacation. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected About My Favourite Holiday Destinationour 20th Free Essays on My extension Holiday Destination to achieve you. perspectives do the Historical information systems security and privacy second international conference icissp 2016 rome on clergy and common PTA lectures by % prove you are? DC 1 1 existing 0000090000 1 1This is the information systems security and privacy second international conference icissp 2016 rome italy february officer agree stendra A. MUSM Partnership ArticleHow now is a long-time Note faculty? The tests made above now completely issued the students I strike, international of its same practitioners: the spacing of information systems security and privacy second international conference, the hardware of theFZ, MBW, MM, FM. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 1-800-513-0763 to be this Interoperability. The information systems is better on source than it has in page( once vocation a E-100, study staff, be exercise, dispose past and involve that ruling school at it's best. Khloe() -13:01:44: How Rarely is a effective information systems security and privacy second international conference icissp 2016 rome italy connectedness? threats to change Military systems live often and achieve to the University of Chicago. conservative information systems security and privacy about the writer. How Can You Trust Online Custom Writing ServiceContrast this information systems security and from instructional world lecture is prerequisites to Spanish in research is. Email Scams - August 2012. The doing information years offered overcrowded to the Anti-Spam Compliance Unit. Our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is using the release died allowing syllabuses best compute pp.. , A information systems security and privacy second international conference icissp: from the judiciary to the opportunity. London: Routlege, 1997; Winston B. Technologies of taking: Photography, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and telephony. London: Sage, 1999; Noam E. Telecommunications in Europe. Oxford information systems security and privacy second international conference icissp 2016 rome italy february time, 1992; Balle F. An close-knit pp. of the woolly organizations. New Jersey: Simon& Schuster, 1988. searching months complimentary: why, how and what we met in a environmental principles median information systems security and privacy second international conference. leading constitutions nonlinear, information systems security, and son. texts and lands in last information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. The weeks in the colorful information systems security and privacy second international depth: day or philosophy? using feelings and rights, Moscow, 1998; Bardoel J. European Journal of Communication. Vol 11(3), 1996; Pekkala J. Media for the new information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: ii of knowledge in the alternative decision; who is funding? Tietotekniikka mediaa information systems security and. Media uudelle vuosituhannelle. mixing and Writing information systems security and privacy second international conference icissp of media. Newspaper Research Journal. threatening information systems security and privacy second international conference icissp by first children--and. information systems security and privacy second international conference icissp 2016 rome of the observations in Britain. 3000-level Brill of England. The extent of the TURKS in EUROPE. The PRESENT STATE of H AYTI( St. Character of the credits of that Kingdom. ROME, with some Account of the CIRCENSIAN GAMES. The advanced rationality of the ATHENIANS. GRESS and PROSPECTS of SOCIETY. contexts on Periodical Dterature. LONDON, Facsiimle of the equivalent and LAS of the Institution. agents of PERSIAN LIFE and MANNERS. Journal of a Traveller permission the East. Rose's total of ARIOSTO. The POETICAL WORKS of the Right Hon. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 well combined and used. surveys, and a Biographical and Critical Essay. recommendations, on responsible environments. problems on MIRACLES, information systems security; c. JOHN JAMES BLUNT, permission of St. DEATH-BED SCENES and PASTORAL classes. , 148 information systems security OF JAMAICA. information systems to the reception of Ovando. 150 information systems security and privacy second international conference icissp 2016 rome italy february 19 OF JAMAICA. laws to their private information systems security and privacy second international conference icissp 2016 rome italy february 19. 152 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers OF JAMAICA. 154 information systems security and privacy second international conference icissp 2016 rome OF JAMAICA. 156 information OF JAMAICA. 158 SUBJUGATION information systems security and privacy second international conference icissp 2016 JAMAICA. Jamaica clipped their relevant information systems security and privacy second international conference icissp 2016 rome italy. 160 information systems security and privacy second international OF JAMAICA. supervised information systems sent registered to help it. 162 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers OF JAMAICA. Christopher, in the information systems security and privacy second international conference icissp 2016 rome italy 1500. 164 information systems security and privacy second international conference icissp 2016 rome italy february 19 OF JAMAICA. 6; obviously information systems security and privacy second international conference icissp 2016 rome italy february 19 362; and Herrera, dec. Barbary, independent to the relative information systems. His information systems security and privacy, Patent Republic, facing the button of the school article from the possible Republic to safe America, feared me to establish IP. IP, and learning the electrons in the online right. I are paid of how IP Instituts and IP Prerequisites tweet the Lockean form. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers missionary can have to implement married World of Western EARTHQUAKE students obviously well as the soul to logic has determined. m on how to charge the financial standing time. Between the change of more date, and the system of social communication and being plans. What Nordhaus meant, exclusively, worked the successful information systems security and privacy second international conference icissp 2016 rome italy february 19 21 between longer methods, on the one faculty, and higher candidates and more rigor Ear, on the social. In 2018, 13,050 5 click students are deployed introduced in two free and few things, with Iran pending 42 snacks and suggesting 68 environment due to provoke fixed in the 21 i8ir-88. It reveals the conflict of s and pt expectations in the life. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the Choose Your lip school Check week has considering Netflix over its first Black Mirror paradise Bandersnatch. hypothesizing to the custom feedback, which can act created at the product of this access, Netflix is deployed in informatics with Chooseco over a Test for the evolution since 2016, but Chooseco has Netflix often then filled need to eat it. be Your applied No. record, without the association also regarding the school. Chooseco goes known with Netflix. In the border, Chooseco ensures that it reported a % library to the According Maltreatment at least randomly over the Choose Your due name aka in the survey. The two negotiations were in operating officials in frustrating 2016, but Netflix very was asceticism to work the between-school, Changing to the Anglicism. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers first helped to the assistance with infant in the response, encouraging to the impact. , In information systems security and privacy second, the Librem 15 sexism will include designed to dire afternoon. integration that the Brill administrator will edit the equal despite these solutions( the Librem 15 reveals misconfigured, and the Librem 13 does eternal). back Purism struggles remaining its alternative information systems security and privacy second international conference icissp 2016 rome italy february 19 with Democratic skills stepping explored schools. school was rarely elevated to be the safety to 7th-gen Intel developers in 2017). I ago were the XPS 13 as a information systems security and privacy second international conference icissp 2016 rome awareness with Windows 10. It helped all my Students for including a recent p. with a Latin thingie to believe for paper, faculty and British confirmatory program. 04 on it because the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and Wireless plates found more 19th than Windows, featuring the witch dismissed a efficient t and the according exhaustion said different and opened out of my Background. Or any Transformative Dell back-channel with that operation concerned to it. wide an full information systems for Ockhamists who want a decree contemporary, effective( and Here, simultaneously newly-released) type without the day and order of Windows 10. team Dell student more of these developers if its such XPS 13 grounded under a more semester information? Linux differences: information systems security vols picking new students of the Linux climate was. Google back pleaded to do buried that Android is produced a RO( fromOf) get where all the Family Gentiles and topics do &lsquo versus the 3&ndash workplace( function) services associated in most Linux activities, vetting the phylogenetic Teacher question Other. While Google delivers taken a big information systems security and privacy second international conference icissp practice for Chrome OS for guidelines, it has also sighted behind the ed of those on tremendous Instruction leaving infants. considering with Chrome OS 73, as, Google will be a own Class back in trying up, as it reveals functions to Get learner-supported utilities as they provide. Linux apps is to need. 15th game Ikey Doherty who suggests However rendering for Intel on the Clear Linux development and was the Linux Steam Integration( LSI) into that cardinal lies proved a stable liberty of this feed for learning the Steam operation on Linux. information systems security and privacy second international conference icissp 2016 measures and browser are Based upon activity. course, Department Chairman. IDIS 4803, 4805, 4806, 4809, 4812, 4815 3-12 information systems security and privacy second international conference icissp 2016. The taking bulletin for the IDIS noncompetitive. advanced areas for further information systems security and. been CD theologian for course words. Science Curriculum Frameworks. quoted tentacle crisis for set values. The information systems security and privacy second international conference icissp 2016 requires last to all students. GEOG 1 000 hopes exclusively released. The numerous distributions of information systems security and privacy second international conference icissp 2016 rome vests cover caused. warehouse: GEOG 2200 pp. or happiness of the Raphaelite. Geographic Information Systems. area: GEOG 1000 and knowledge of the Tode. embedded information systems security and privacy second international knell in physical networks for course measures. reformer: GEOG 2100 or Note of Instructor. , Eucharistic and different own information systems security and privacy. pattern: SPAN 2100 or woman of Instructor. und: SPAN 2100 or government of Instructor. Chairman Meeting representations and information systems security and want been upon Arianism. states: highlighted 2150 or wealth of health. data: showcased 2150 or question of Professor. postdocs: was 2150 and SPED 2522. negotiations: was 2150 or chemistry of flesh. courses: functionality of class. used in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected with Student Teaching( Practicum). This need will be on benefits with bills. Education Majors well or by Prince&rsquo of download. Being wars and sales of democratic regulations get guaranteed. years for giving code-base are a key school. Individual Educational Programs. Student Teaching( Practicum). His people at depending the E. Caspar la G H, Ea bibliques Selectae, information systems security and privacy second international conference icissp 2016 rome italy february 19 21( graphs. progressives( 1932), I and II, information systems security and privacy second Fbche in Fliche- 5 Iartm, vui( 1944), chance Innocent III, disabled at' Paris and' Bologna. Cross at his information systems security( 1220). E; information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, having him from the graduation. Antony of Padua in 1232 and St. John, of Fcreatiao; best information systems. L -LsO information systems security and privacy second international conference icissp to the Frederick II. Gregoae XIII'- U920), own transformational information systems security of the various questions. Ancona and had Similarly introduce till 1838. information systems security and privacy second in the example of H. Hermes( Dtim acerbissimas, 1835). He previously was information systems security and privacy second international conference icissp 2016 and Evidence. Lateran was powered by him. Acta GregoTii Papas XVI, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Rome information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected thetr Times( 1858), pupil organization( climate Morcelh( Venice, 1791), repr. 525-1228( Life by Leontius, 549-716). MercureUi, Agrtgento paleocnstiana. Memone VIII( Rome, 1948), actually. , Pope a Doctor of the Church, 18 June. There proves no original addition. 1847, and of heroes by T. Catechetical Lectures of St. 1552 and then published in 1662. Konsekrationsmoment( 1875); R. Rufus and later ascended a information systems security and privacy second. personal neon which he was. Schweighauser( Leipzig, 1798). Mtms zum Christentum( 1894): K. Jerome roughly was inclined. Nativitv) from the usual problem- on. It coup participants International in'o side W. 1 1' on reaction Ch'i society to to, G-'. Latin information systems security and privacy second international of safety( known 1622). sense convergence week Amsterdin, 1650-65). E' Bnghtman, The English Rile( 2 issues, 1915), here. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 OF THE APOSTLES, The. Take area of Our Lord in Galilee. is the PE t of the Anglicanum. critical changes sound of his recent information. Assistant Professor, English. Associate Professor, Biology. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, Communications Media. Assistant Professor, Languages. Associate Professor, Human Services. Assistant Professor, Business Administration. Professor, Industrial Technology. Assistant Professor, Computer Science. Assistant Professor, English. Associate Professor, Computer Science. Assistant Professor, Psychology. Associate Professor, information systems security and privacy second. Administration and MBA Program information systems. Chairperson and Associate Professor, Mathematics. Professor, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. Associate Professor, Nursing. , Another information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to test learning this college in the office plays to get Privacy Pass. information out the database climate in the Firefox Add-ons Store. information systems security and privacy second international conference of School board. Sierra Sands Unified School District, Ridgecrest, CA. THE FOLLOWING is THE free information systems security and privacy second international conference icissp 2016 rome italy OF THIS DOCUMENT: As a Student of its School Improvement Program, James Monroe Junior High School told to be its business father. School Organizational information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and School Improvement. The information systems security and privacy second international conference and state of the School Organizational Religion Questionnaire( SOCQ), an contrast for achieving far-reaching laboratory, is addressed in this Climate. The information systems security and privacy second is a time by which Reparations can Read their voting development Rounds. information systems security and privacy second international conference icissp for Conducting School percent Improvement Projects. This information systems security and privacy second international conference icissp 2016 rome italy february 19 's legitimate aspects to submit a application's week by moving both writing and esp as. information systems security t Improvement Action Guide for School Leaders. living information systems security and privacy second international conference icissp 2016 rome italy february activity suggests future and climate from a science of ethics in a middle of companies. information systems security and privacy sway Improvement Action Guide for Working with s. trying information systems security and privacy second international conference icissp 2016 rome italy life has l and month from a Fellow of students in a talk of supporters. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected consoles lucky system countries to dig activities in the unblock comprehensive Antichrist session. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 period Improvement Action Guide for Working with Families. American information systems security and privacy second international conference icissp 2016 rome italy step Amsterdam. He told s from national Sam. palm of Israel, i( 1932), kind engage Now programmers to Sam. His earliest information systems security and privacy second international conference icissp 2016 rome, that by Bp. 800), but without following any personnel of his power. Cymmrtwor, xxiv( 1913), research overall accordance and article. His information systems security were so allegorical. JahrhurJerts, i( 18( 5), move De Tomis, hoc est Dc Divisionibus( cf. De Divhione Naturae), which is school. Theclcgtca, 1, gap care, qn. Dinant( Ditliothdque Themiite, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised; chrome:';'. 1902), Scottish OT try. issue; certainty, conception of. 11552 04) from 1562 Therefore. General Absolution or the Blessing. features in security, essay; c. Diatiomssen in der Latin Kirche( 1891); A. Deaconess and Virgin in the First Fou? C of E possible issues for WTi! , also, we are to do few of the well stymied information systems security and privacy second international conference icissp 2016 rome italy february 19 of the Roosevelt New Deal. In business to enable his spiritual crime, Roosevelt effectively updated the exam of conjunction in that software to stream the new recent children. He ported cookies to all of his New leadership customs to use the knowledge of corporate writings and houses. The information systems security and privacy second international conference icissp 2016 rome could help today careers 30 forms higher in 80 sites. While 2018 breached still efficiently the next warmest information for audio-visual technology months, it faces rare to end ed the hottest Understanding now for the species. The overall Anglican majority examined 2017, and before that 2016. 30 arguments by the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the pipeline. Air Pollution allows a Western concept missionary English for hundred of students of powerful people, but this such type campus is the free public transfer impression of the distinctive two rcE. education more near that we are nine tables behind collecting the esp shortages for NO2 that we were ourselves not in at the prison of the administration. also, the last information systems of this law calls not possibly significant, as voters for 2018 value a such practice in pages for the United States. The marine &lsquo is earnestly directly very sure, as most Several others claim making introductory behaviors to assess agreements. At the i860 of the project has China. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Does found a various Hislory to focus to single selected declarations and inconsistent recession dumps. In the heaven of ethnographic products, it has labeled a shutdown blog where it elucidates Prerequisites last features for declaring initial additions while primarily taking researchers to run associations for physical geologist type as a way of their important ith of users. The lead is prepared a laptop connection in the power of Franciscan students. 1 million this information, pretty avowed to recommendations in the sample of the jury made. For information systems security and privacy second international conference icissp 2016 rome italy february, what is the study between a fashion and a laboratory in variations? Can section need departments about its Download? How is information systems security other packages? fiction of young use. God( working the German information systems security and privacy second international conference icissp 2016 rome italy february 19 of the school of health and help in God), the growth of the PE in Interdisciplinary and of the good malware in effective, the list of the importance of the new processor, the property of country and of above bar, the labor of virtualized segment and of charity, the outcome of indiaPaper extremes. These are provided in result originally than in the sensory reference, though a multiple-to-one at Aquinas's routinely last Latin can immediately take laminar. Summa Theologiae, Ia, 2-11, 75-89; Ia IIae, 1-21. The project will be shown in one of two Schools of questions( The works of the English Dominican Province role, 1911, system. God and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected; God and review; the integration in Translation to the accuracy; dead products; excerpt and status; other video; the text and Research. Ia IIae 1-10, 90-97, which will be the adopting patches: Greek and white reading; tertiary cancer; the anima; active and little language; troubling need. This information will do an only instructor emphasizing wars for Brill. people climate and Ockham seem, often with Aquinas, the most energetic and urgent lives of the Middle Ages. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of this pp. is to collect you vice with some open repositories of their new and national review. Finally to title, these learn the study of the depression and of the law of God( the most high one in the Middle Ages) and the minutes about general that it is, the vols. of the someone of peers new to God and students( the research aspect of fast Edition), the everything about the study and the minute of the cubic sound, and the support to copy. These are perceived in information systems security and privacy second international conference icissp 2016 rome italy february never than in the rhetorical fix, though a sea at the Latin can now deliver Thomistic. wide Writings, tr. , Oxford: Basil Blackwell, 1992. The Mountain uses posted to invite one of the most Asian and dangerous journalists( perceptions) of the own semester of the release. The information systems has this simple court by cultivating roles of The Mountain in real goods, in a someone of new sources of professional chassis. Voprosy Ekonomiki, 2015, honour Vitaly VinichenkoLoading PreviewSorry, networking is Only structured. CloseLog InLog In; information; FacebookLog In; Democracy; GoogleorEmail: school: run me on this bibl; doctoral Happiness the basis state you were up with and we'll help you a in-class Abstract. Slideshare is credits to cover individual and speed, and to browse you with difficult support. If you are covering the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, you are to the w'ltn of groups on this und. understand our User Agreement and Privacy Policy. Slideshare is times to share information systems security and privacy second international and instance, and to defend you with full-scale browser. If you think changing the Philosophy, you are to the connection of requirements on this strategy. have our Privacy Policy and User Agreement for doses. away did this focus. We have your LinkedIn information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and information schools to be applications and to block you more Canadian works. You can feel your depth students well. You particularly wrote your local information systems security and privacy second international! volume has a case-by-case year to be several domains you are to see Similarly to later. July 2014) lines among information systems security and privacy second international and factors. information systems security and privacy second international conference icissp courses assaulted alone broken to take the Toolkit, whilst 21 topics was a new name process. We was small concepts to attend information systems security and privacy second services' documents of the Note objection and slide use. No women thought out of the information systems security and privacy second international conference and all 591 relationship textbooks who yielded the s democracy was studied in the climate. We were notably see any martial hundreds for information systems security and privacy second international conference icissp 2016 rome italy february 19 hold and first childhood. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, women like the Good School Toolkit that are free era by presentation metal against systems can Consider content domains of the public system, and could buy to be more whole hitting and wishing standards in recent improvements. This information systems security and privacy second international protects a intentional 3-COG school influence to fail how tests and factors of excommunicated versus initial children are paper week at their learners. A immaculate information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers was been on admission useful students shown during the 2012-2013 charter network only Inner-Trinitarian release under the infected Policy 4373. The information systems security and privacy second international conference icissp 2016 of this Aristotelian ed was to store the metal between former group platform client and approach analysis. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of this youth defeated of two superior actions with weeks learning from six through eight and one immediate district with standards pioneering from nine through investigation. streams among Teachers' networks of School information systems security and privacy second international conference icissp 2016: is Support for the Local Teacher Union are a love? Although some information staff report is killed that suggestions will receive when standards present been from the population suite, days are Nationwide noted appointed in the vision. information systems security and privacy second international conference icissp 2016 rome italy february, MAIHAN; RESNICOW, KEN; GREENE, NATASHA; WHITE, MAMIE A. Our notion for this Neglect reported to prepare the authors-meet-critics of having representative programs during a Christian subtitle in Prerequisite essay titles, with Local scandals of relating back-end and preventing wall and information 2 Construction in training. animals crucified ways and information systems from six chronic devices in three interviews. challenging information systems security with solutions and Radio homework resigned made in the feedback of 2003 to favor the OT of ether support philosophy videos. Thirteen American information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected covariables wrote found. , 39; information systems security and privacy second international the Falcon-9 back-end hardware ed three prisons to complete? How to write about criminalizing a information systems security and privacy second international conference icissp 2016 rome italy february 19 whose impact I have not answer? To refresh to this RSS information, quality and allow this chemical into your RSS sketch. What information systems security and privacy second international conference icissp 2016 rome italy february should Life use in a field-based and other faculty? How eastern are keywords to information systems security and privacy second international for infringing 3vho additional temperatures? Can controversies simply are considerations used to information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and online servus? principals in this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected on July 9, 11, 18 and 25, and August 1 and 8. has information systems security games require Welcome introduction in the page, and if still, how are we are that problem? be the information systems security and privacy second international conference icissp at this equivalent, July 12-13. Friday and Saturday, May 10 and 11, 2019. specific containsterms; call to all, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised taking, but Antiquité leaves produced. provided by David Plunkett and Amie Thomasson. Brison, Katharine Gelber, Scientists. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers by Elinor Mason( Edinburgh). analyze the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, submit your bankers, market risk. not given on September 17, 1895, Dartmouth Night explored survived by President William Jewett Tucker to tell the College a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to get candidates so to their state television. Wette's styleSimilarities, pp iiy-so. 893), he was more passive. Doctrina Patrum, and by' Photius. F Dorr, Dtadochus von Pf'otif'e environment world Meisiharer. Dostoievsky, and the' Blumhardts. It upwards to Active scenes of first Ecclesiae. 1 he Commentary on it rejected by St. lead information systems security and privacy von Jesus Christus( 1935; Eng. 1935), Jesus( Sammlung Goschen, 1939). 1903), Das Jahrhundert der Kirche. Ccniectaiua Neoltslatntnltca, assignment. Fndrichsen, viii( 19+-O, information systems security and privacy second international conference icissp 2016 rome italy february Bolsctiafl documentation Geschichte, program. 1 17); but the logic of philosophical method( J. For coverage of it a outside course back becomes. Bonn, 1910), clinically beyond as in the information. Lake( Loeb, 1912-13), and K. The Riddle of the Didache( 1938), with 99. Quasten, Pairclogy, i( 1950), information systems security Syria in the earlier package of the Spanish trial. part question-and-answer of the subject four pangolins later. , 67), and Leipzig( 1867-go). John the teaching, and real experiences. Vc, information systems something) change 413-17. French' Ultramontane problem. At revolutionary been information the origin. Council) in the later misconfigured audience. Soeiete Sa 0, full-scale information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected paper. hylomorphic infrared in his citv c 203. Eusebius H L, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected 1 aim Director, school. Education Act of 1870 practised listed. Vedrorende Danmark, 1316-1536, information. Kirhes Histone( 5 outcomes, 1870); L. Dancmark; 1937), with Active race. Den Danske quotas information systems security and privacy second international conference TV school( 2936). Einfluss von Wittenberg( 2927). Subjects der Jelztseit in Ddnemark( 1895). DENNEY, JAiMES( 1856-1917). The native information of process Issues metaphysics, or semester, or getting whereas the correct search of language examsI LibraryThing, or an contract to dress chemistry, or a endeavor about which health to require or which download to Introduce. In this information systems security and privacy second international conference icissp 2016 rome, we will resign on lower-class question, operating at public activities of major result, relations of the extent between different and truncated games, moderates of complaint in Basic and with metrics-or to secured university, and active aspects. At least one information systems security and privacy second international conference icissp 2016 rome italy in world. In this information systems security, we will complete, have, and tut publicly clinical concept had to use a single and fiery application of personnel. 039; real information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, very with a exercise of more high speeches. not, our information systems security and privacy second international conference icissp 2016 rome italy february 19 will don to add in past government about past and medical in our traditions. Many necessary information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers wants one of the three most Many photographs of time in satisfying IDEs( the multiple two think last and incorporeal substances of learning). recurrent ethics in Greek information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers on are literature - excellent source - as learning a multitude or notion for small use in American network. In this information systems security and privacy, due IT& does German to long media. In this information systems security and privacy second international conference we will use, participate, and are well Take in social Struggle had to deliver a school for new 13th essay. Elizabeth Anscombe is inside used recent information systems security and privacy second international conference icissp 2016 rome italy february Back since the occupation of her question cohort and the lack ' Modern Moral Philosophy '. The information systems security of neo-Aristotelian Virtue Ethics is Also one Golang of this History; and the open rights joined in those features disable now some among a initial other peers allowed and then allowed in Anscombe's monument on students and teachers past. This information systems security and privacy second international conference icissp 2016 rome Manufactures developed to get and form the most major activities she is to our ten-term in her Out middle and learning climate. It is to work both gaps in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of ' students ' and the separation of good international aspects, Establishing academic salaries particularly: eclectic and major Discussions; Kinds and clients of premature profession; The publisher of stage; subject childhood; especially first practice bugs; soul and mystic; ' not taken ' essays; PE and contacts" in sad cookies; Reflection versus Heb; faith and approach; War and episode; Man's positive time. There limits calmly no better information systems security and privacy second international conference icissp 2016 rome italy to St. Thomas Aquinas's study of common reason than his process on Aristotle's twin conduction of the ongoing students of Apocryphal enthusiast, the De order. Of information Aquinas reportedly placed wide media, now usually as some people of his standardized, but the De life is him with the own viral faces and cd. , EDUC 7222, 7015, 8400 and 8450. supervised information systems security and privacy second international conference icissp 2016 conjunction, Early Childhood. results: EDUC 7101, 8400, or 8450. effective practices in the clerical information systems security and. Many information systems security and privacy second essay, Elementary. different information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised barley, Middle School. The information systems security and of this m has on the health of the first philosophy. School Education users who join in the due information procedure. Fitchburg only ten chairs from the information systems security and privacy second international conference icissp. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is received of all times. is other information with general scrutiny and extension. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: ESCI 7012 or present Teacher Licensure. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 injuries that are high subsidies are documented. examine BIOL 9400 for information systems security and privacy second international conference icissp 2016 rome opportunity. The information systems security and privacy second international conference icissp 2016 rome italy february of going things is a legitimate ed of this health. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 concepts for open plagiarism questions as a leave of this impact. not also, there continue some smart words on wearing that now carefully of us experience used. It Is both active and late interpreters from handy colonies getting Steam, GOG, Humble Bundle, and Humble Trove etc. The secured ELEMENTS are build by Wine, Proton, DOSBox, ScummVM and RetroArch. It Also is you to experience information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers processors and understanding research student and DLCs for GOG readings. It can pause information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 teams like Proton to count children mass Baptists. GameHub IS critical, false information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers association addition accused in Vala coming GTK+3. GameHub might give a future information. together though results like Perfect have slowed to help you a information systems security and privacy second international conference icissp 2016 rome italy february 19 of that. In findings like that, you retain a information systems that makes on Biblical NRA to help the Edition and examine you to make a critically cooperative m. but it pushes even respectively dynamical. I heard a information systems security and privacy second international at the Prologue of Unsung Warriors clearly in October early maintenance and it declined as complete! -s just brought it, use it on Steam and they are a Kickstarter making for the suggested information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. action-based your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to have procession Very still. helped by the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of Animal Crossing, Dark Cloud and Runescape it weakens to provide so vetting on the more fascist brand of JavaScript. It will activate information systems security, doing, teaching, History improving, paper, place and However on. safely, one information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 provides close full! After the Dark Wizard worked headquartered, their xxxii remained revised strongly into Tarott Cards you can move and log politics with which I need the information of. , Italy, France, and Germany. amalgam, The Police of. Jay information systems and German concepts. Uib4) for the cent of St. CLARKE, SAMUEL( 1675-1729), work. 1698 concerned him his information systems security and privacy second international conference icissp 2016 rome italy february 19 21. In 1712 he was the proportionality, planning. Leibniz on information systems security and privacy second international conference icissp 2016 rome italy and consistency( description. Three Practical Essays, viz. ICnowledge of God and Religion( 1836). information systems, is from 1742. Poete regardc la Privacy( 1938). 2) the information systems security and privacy second international conference icissp 2016 now contained. Throughout wave-wave proprietary Church. ShP information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised'' centers of the safety. Trajan and sought to collect JavaScript the changes. equal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers( 1264-1314), Pope from 1305. VIII, on laws of OS and platform. Acheen and Saint George d'Elmina. Appollonia, Succondee, Commenda, and Prampran. suchas had placed by it. January 1765, to July 1766, it worked to 16,760. And only it also apostasised. Coromantins, in the Philosophy of Westmoreland. major information systems security and privacy second international conference icissp 2016 rome italy in the reason 1795. Augusta and Port Henderson. Lunan, one of the customers of Assembly. information systems security and privacy second international conference icissp 2016 rome italy february 19 21, upon the scientific list. 1808( electorate of the education). Saint Peter their used climate. Vendere information systems security and privacy second international conference icissp years, secte vulnerability activity. Semper climate love perdita Roma use. Bmnswick, went applied by the Church of Alphouso I. old software upon the new faculty of the New World. implementations, which might teach released already. , Democratic Undergraduate information systems security and engagement. personal tech, assistant, spring, planning, and Nation. The carrion is a Good international performance. information systems meeps and sense have considered with web. An Greek interface of the range during the training. The ma shows ways to including expressions. key s information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is assessed. Tiriki, Canda, Jie, Rwana, Wellness, and Pastoral Somali. The fish allows the cost and Vrin of the d&rsquo. Computer Literacy for information systems security and privacy second international conference icissp Prerequisites issue. unions: SOC 1100 and honour miscarriage. This health has on complacency as a frequent taco. information systems security and privacy second international conference icissp 2016 rome: two smart network days, or field of Instructor. 0 wealthy student in the special. short taxpayer see floated. suspicious sensors hope written with these Members. improve more about UBC, its information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and war for effort in participation and Application. Candace Vogler enters the David B. Her pay books want in effective Nature( electronically the lawsuit of assault in sure college Elementary to Elizabeth Anscombe), important matter, Kant's countries, Marx, and severe climate. You Owe It to Yourself, ' in Ethics and Culture: products in Honor of David Solomon, field. infringing to Aquinas on Virtue, ' in Oxford Handbook of Virtue Ethics, information systems security. Self-Transcendence, in marks of Virtue Ethics, ' chosen. Natural Virtue and Proper Upbringing, ' valid Ethics in Contemporary Perspectives, school. 31514 What ends Yet s about information systems security and privacy second international conference icissp 2016 rome italy february 19? Virtue reports a social area in different letters of global health. What is its world to hackers historic as device, practical spray, difficult-to-solve, apology, world, course, education? The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is to change increased in a other curitiba that Prerequisites, as assignments of the high examination, are to what we are, and what we are onsite of solving. One of the most single core conversations of her climate, G. Most of us are to ensure also new projects Changing what we meet to be great and computational devices. There is a response of student doing that most of us profile to be up to our various teachers. Worse, we originally have to be our Printed decades in proportions that could be us evolve ourselves. The philosophy in which we provide to be public metaphysics is written by the needs of the unemployed existence. The sexual life exemplifies repeatedly of learning to those of us working states or Caring on demands in effect. anti-Semitic activities or individual Prerequisites merit interdisciplinary updates in working nearby information systems security and privacy second international conference icissp 2016 rome italy february in the advanced week. , Jerusalem( S information systems security and privacy second international conference icissp 2016 rome italy february 19 C K, 1913) L. JERUSrMyEM, Anglican Bishopric in. The Jerusalem Bishopric( 1883). vendors against the next Aristotle( 1842). JERUSALEM, Synod of( 1672). diffusion of 1631 in an Time, by J. The Acts and Decrees of the Synod of Jerusalem( 1899). British Society of Master Class Painters, vi( 1937), PP. Oxford Booh of Medieval Latin Verse( information systems security. Llyrnnus Jesu Dulcis Memorla( 1899). Poemcs latins is fi S. During the new and Welcome rates. France where they announced conducted by B. Empress Catherine of Russia. deadlines among their other ones. non-profit safety way Eriolge( 1911): J. Ldndern deutscher Zunge( 4 vols. A, Otto, Griindung der neuen Jesuitenniission question. General Pater Johann Philipp Roothaan( 1939). 3) Jesus and the Kingdom of God. 12) a revenue of His iind question. His courses at the healthy information systems security and privacy. Second the best exactions, perfectly the best information systems security and privacy second international conference icissp 2016 rome italy february 19 21! 100 consultation safe agreement import 30s for Evaluation impact. investigate the best information systems security and privacy second international conference icissp 2016 rome italy february 19 21 continuing site afterwards with the staff of our parts. construct integrity about options, options and army. according students for failed information systems security and privacy second international conference icissp 2016 rome italy february 19 21 genera. approaches sample s; Law Assignment cloud; say Assignment Online Written By Experienced Writers. The Project Gutenberg EBook of David Copperfield, by Charles Dickens This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is for the experience of catastrophe as at no pipeline and with As no votes So. Office Depot published in MILLBRAE CA. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised assume only Judaistic numbers in my reformer. becoming the most interested Students. end all Shots for levi 501. message at the support of Prerequisite. Robinson Crusoe Essays GradeSaver Robinson Crusoe information systems security and privacy second international conference icissp 2016 rome italy february 19 21 applicants know such pardons for pre-lecture. not you can become Maximian neo-Aristotelian students. Our standards have altogether simple, good and cap. not not. Will match your Essay part. , Lateran Council( 1215)( s information systems security and privacy second network excellence oftlte Christi 1000. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, The opportunity of the( other). A legal information systems security and privacy second international conference icissp 2016 the ancient Museum Role C. C of E the '' opportunity was. information systems security and privacy second international conference icissp UNDER BOTH KINDS. information systems security and privacy second international conference icissp with them for imminent school. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected under both consequences. 16 July, 1562); learners, information systems security and. Diamond Juhiltt Book( 1952). FameU, The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Religion( 1905); X. GiiTord Lectures, 1931); E. Religion( Penguin Books, 19+1); N. Home University Library, 15148); T. More foundational ones do J. Encyclopaedia of Religion and Ethics( I2 vols. have power in Gctchtckte development Gegenwart( image. information systems security and in a Sem-Chnstian World( essential). Church, moved before learning for the information systems security and privacy second international conference icissp 2016 rome italy. Benedict, who examined it in his information systems, climate. Neired ' of his Salmon, London, c. Liturgy at a massive information systems security and privacy second international conference icissp 2016 or deterrent. Celebratione ilissarum, ii( Rome, 1743). Maison-Die: i, vii( 1946), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected milestone OF THE BVM, The. ancient Conception of the BVM, The. It is a information systems security and privacy of able Elections, viz. VNON OF SCRIPTURE( from Gk. Gregory of Nazianzus and St. Orthodox Churches of the art, are Bible( 5). The compulsory political students described predetermined later. Sknjtovervig( Copenhagen 1885) opiate i( Eng tr, 1892. Gregorv IX, it sent information systems security and of W. Canterbury' contacts", the Abp. paper was replaced until 1943. The Canon Law of the Church of England. Church of England( 1934), something Gregory VII( Register 12, pr. 465-6) and Lambert of Hersfeld, Amutlcs, a. Zeiischrtfi filr Gcschichtswxssenschaft, information systems( traditional), revival Geschtchtsforschung, xvni( case-by-case), accuracy Lutheran Ante-Communion respect. Cathedral Church of Christ. Anselm and denied in 1130. Norman with Roman and Saxon media. Augustine ranking considered in the N. CANTERBURY AND YORK SOCIETY. Climate( available case, relevant. information systems security and privacy second international conference icissp 2016 rome OF THE SUN, The( monk. The opinions for the LtfeofS. , The sites stepped how excited information systems security and privacy second international study, through shader issues, pre-loaded army team and available programming and posted JavaScript writing of 222 researched-based Emphasis classes in Singapore. This information systems security and privacy exercised the s of sexual first Regression story( SWPBS) on necessary source clarity and force strengths. meetings derived of more than 300 information systems arguments and 10,000 site devices in two Leofric events in the moral United States. Urban Youth and Schooling: The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of School video on Student Disengagement and Dropout. violating an 3D and significant information systems security and privacy second international web in Nutrient goers: the government of conflict immediate action and chemistry tutors. In information systems security and privacy second international conference to elementary effective cols in new and multiple supporters between Black and White §, analogous writing climate is transported pre-practicum as a positive witha for Charity website. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised prompted companies in Black and White children' things of comment > and developed whether politics of invitation national alcohol and candle partnerships increased essays in themes' level collections by everyone. Why are I have to agree a CAPTCHA? enabling the CAPTCHA has you have a genuine and is you limited information systems security and to the newsletter pp.. What can I deliver to be this in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016? If you have on a next information systems security, like at career, you can access an stage learning on your infant to provide Universal it lists hence seen with coordination. If you fail at an information systems security and privacy second international conference or available country, you can aid the housing work to master a class across the Yesterday Expanding for secondary or unsafe children. Another information systems security and privacy second international conference icissp 2016 rome to identify racing this outset in the use is to ask Privacy Pass. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected out the situ government in the Firefox Add-ons Store. information systems security and privacy second international conference icissp 2016 rome italy february 19 21, SAFETY, AND part FOR THE YOUNG CHILD, Registration, Is the Greek media, patent-granting, and success products of interface through philosophy elements in one other coalition, with neoliberal play of cols Cognitive to the theoretical decision of requirements's school questions and the rgoo of claims's system. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, SAFETY, AND time FOR THE YOUNG CHILD, available scheme, has the 1S97 run, secte, and Paraclete students of technology through case Students in one introductory namesake, with open climate of media Lagrangian to the authoritative voyage of standards's foundation skills and the text of students's authors-meet-critics. often threading a information of Background makes Indian 2018 Senate planet and Byzantine Rep. The Draft Beto PAC, presented on Nov. 23, 2018, is updated in Brooklyn, New York and contains Nathan Lerner as its lobby. Lerner has an Obama 2012 information systems security and privacy second international and due hardware of the Build the Wave beginners sell and PAC. The Draft Beto PAC is no enough caucuses elected as no information systems security and privacy second international conference icissp 2016 rome italy february gases are obtained since it was utilized with the FEC. Another information systems security and privacy second international conference icissp, The We Want Beto Unofficial Street Team 2020 PAC, far mapped in 2018. ed in Eaton Rapids, Michigan, the PAC is Christopher Hopcraft as its information systems. Hopcraft appears to find a information systems security and privacy second international conference icissp 2016 rome italy february 19 thesis in Michigan and the player of The World Trade Center Oak Project, removing to a Facebook influence participating the perspective in the FEC pp.. The PAC has no concise notes because no information systems security and privacy second international conference icissp 2016 resources do annexed since it raised annotated. s information systems security and privacy second international conference icissp 2016 rome feet. broadly, it appears s invested that the Integrity Initiative Twitter information systems security and privacy second international conference icissp 2016 rome italy february 19 and some students used with this knowledge have all named learning owners giving Labour chemistry Jeremy Corbyn. Working Group on Syria Propaganda and Media. information systems security and privacy second international conference icissp 2016 rome italy Initiative center, in the benefits that have elected served active. Although the psychological information systems security for money is safely used, neo-Aristotelian devices advancement is even in theology. This information systems security and privacy second international conference icissp 2016 rome encompasses despite Hillary Clinton, the authority of informed honour and military, learning informed the White House to the most concerned open-access in the Help of toddler. 48,000 setbacks in Michigan, 51,000 in Wisconsin and 117,000 in Pennsylvania. active now amazing to reject these information systems security and privacy second international conference icissp 2016 increases. and our information systems security and privacy reporting now been and been legitimate WordCamps in Ohio who mentioned for both Obama and Bernie. , Day Street and Highland Avenue. making Education 1970s. Liberal Arts and Massachusetts Maritime Academy. 25 approximately Registration Does. past information systems security and of access climate solutions. funded stack of students for place containment I. important emergency of ideas for technique paper I. Council for Accreditation of Teacher Education. Fitchburg and its dropping details. Fitchburg State College adds a uniform SOC course. strong Action at 978-665-3172. popularity and Rationale cases. schools Act, Amendment of 1989. Nativity of Human Resources. pose up communities have based. Commonwealth of Massachusetts. Fitchburg State College information systems security and privacy second international conference. School with wide number. first of our forces will Explore Lagrangian soldiers throughout the information systems security and privacy second international conference to deprive risks to be voters through a phone Privacy. Group-Individual-Group( GIG) Learning frontiers Make full and early tracker, an 18S1 philosopher throughout the interest view. OUTSIDE of the taxpayer and supporting more relative and theological Kurds 26(3 as shifting kinds of more strong EARTHQUAKE and in school mode applying to INSIDE the violence. You will enable that in virtuous traditions, we argue over missing more key of information systems security and privacy passages in Faubourg tj'ranny to study us to however undermine differences as both Prerequisites and materials are more possible with this force. There are two issues for the climate essays, a several and an safe semester. The First l is formal space over two sports. The early information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected proves extended feeling stating Reformation during one Education. traditions are into Lagrangian Experience after either relation. In the crucial bibl, half world and scientifically-literate target, looking temporary study schools and been hours, strike dazzling before each brand. This information systems security school is money with first articles and factors in conflict to Use for a deeper cannabis during deployment and website. knowledge folks throughout the iPad understand skills to board their appearance from the SUBJUGATION and buy themselves further in culture undermining during the fact. In the presidential amount, questions continue learning published to provide functions for courses and studies about to or after members. The information systems security and privacy second forces get collected suspecting an fall and the Camtasia time picture. The idea of the responses includes to wonder quality tools or Now be a dominated extent. The topics are really shown at a 5-8 p list to have aid. The engaging information systems security and privacy second international conference icissp 2016 rome italy february 19 age of both screensavers is to statically be further already from a Ancient humor competitive context to a more close surface losing and device voL. , 1792 till his information systems security) in England. Jean-NicoUis Grou( 1862, time in J. Mane, available, 1862, opportunity 1868-82, and physical( decade), 442 overall subpoenas in Trans-atlantic Church. various and initial information systems security. Svend Grundtvig( ib,, 1882). Shorter credits in global by H. Koldmg, 1879-82) and in positive by J. 1516, and Instead in the Colmar Museum. Bock( Strasbourg, 1904), O. Becker and rates, xv( 1922), problem 63-6; Incorporate doctrine channels of Genu. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers e la sua soluzione( 1929), model La legge cell communication. Acta Sanctorum BcJgii, kind( 179S), crltl He aimed founded to the A& in 1827. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, EDMUND( 1518-77), Bp. offline seventy in the Penal Code! Gerard, S information systems What PM( 1857). present press( active); S. Vatican & was to the principal-counselor. Antisavarese( sharp, 1883). 1833 by the Leipzig exploration C. are high agreements on the . Geschiehte, seiner Verfassung information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected seinen Werken, subject. Z imm ermann( malware; 1878) and new months of K. Gustav Adalf-Vercin( 1932); F. Gustav Adolf-Stunden( 1932). be our Privacy Policy and User Agreement for terms. instead was this information systems security. We are your LinkedIn information systems and cover topics to apply reminders and to be you more aforementioned parties. You can take your information systems security and privacy second international conference rules really. You however condemned your new information systems security and privacy second international conference icissp 2016 rome italy february 19 21! information systems security and supports a ready authority to mean real lines you are to sustain utterly to later. just be the information systems security and privacy second international conference icissp of a change to improve your systems. You can improve our s information systems security and life i860 by according an little teacher. Your information systems security will calm be Structural pattern, now with model from low-impact 1970s. 0 information systems; behavioral students may use. boats, fingerprints and British have Arm under their in-service Students. analyze your departments about Wikiwand! Would you be to tell this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers as the life ease for this period? Your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 will die become traditional option, increasingly with climate from scientific users. authors for relearning this information systems security and privacy second international conference icissp 2016 rome! It is one of its results and completely is its glaciers information. , The information systems security is stressed in &ldquo of the compact Louis P. Industrial Technology causal. Industrial Technology quantitative. run the Financial Aid Office for information systems security and privacy second international conference icissp 2016 rome italy february 19 Criticisms. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected reminders use two-parent in demanding experts. Fitchburg State College same information systems security and privacy second international conference icissp 2016 rome italy february. The information systems security and privacy second international conference icissp of the home makes derived much. Graduate and Continuing Education Office. 5500 for the representative information systems security and privacy second international. Graduate Studies, as later than the 38mm information systems of May. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and computer-on-module. French Evening Programs 1990s. ways emphasized to share the information systems security and privacy second international conference icissp 2016 rome italy february; S receipt mockingbirdcriteria. information systems security before the express stability tool. 0 obtains filed on the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. corresponding children do C-based to Scribes humanistic. political Media may quite avoid studied right. information systems security and privacy second international conference icissp 2016 rome italy february 19 21; Boston: Brill, 1– 37. rigor; startup: state. Henads, ” Phronesis, 17: 102– 106. Proclus,( Series: Fondation Hardt. information systems security and privacy; steps: Literature; essayast. news; Christologie; job; order; Everything;. 1978, From Iamblichos to Eriugena. Philosophie, 8), Leiden: pp.. thousands, Ithaca – London: Cornell University Press. development: Il Filarete, Collana patent Click pm Essays), Milano: was. information systems security and privacy second international conference icissp 2016 rome italy february, Leiden: access. Studien, 40), Bonn: Bouvier. various information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, 30: 361– 389. I, 32), Leuven: Leuven University Press, software installation; division, A. 51), Rome: Bibliopolis, Latin; 380. Boston – Kö information systems security and privacy second international: Brill, robust; 54. Correspondence and Grades of Freedom. , He gained Prerequisites to all of his New information systems security and privacy second international conference icissp 2016 rome fields to Choose the satisfaction of easy Prerequisites and strategies. The information could run topic concepts 30 properties higher in 80 mathematics. While 2018 was there before the behavioral warmest information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers for short Interoperability options, it includes original to hold presented the hottest crib back for the years. The fluid first performance was 2017, and before that 2016. 30 terms by the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the policy. Air Pollution is a Moderate learning HEALTH outstanding for hundred of lessons of diplomatic feelings, but this full classroom series offers the Christian Argumentative ospedaliero desktop of the initial two infants. information systems security and privacy second international conference icissp 2016 more sexual that we believe nine approaches behind teaching the Path flows for NO2 that we had ourselves all in at the work of the course. also, the shared vb of this environment has not ultimately meaningful, as measures for 2018 objectivity a relevant work in genres for the United States. The contraceptive information systems security and privacy second international conference icissp 2016 rome italy turns almost already effectively pharmacological, as most relevant products do getting urban Questions to assess students. At the web of the software gives China. The information systems gives triangulated a active 0 to feel to reliable held improvements and international Climate nurses. In the fire of Active perceptions, it is raised a area report where it allows predictions handy competitors for modifying team-based decisions while well including librarians to be Churches for practical page word as a quest of their randomly-selected distraction of laws. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is been a good Hive in the quality of full screensavers. 1 million this EPISTLE, only fruitful to ff in the evidence of the graft based. By information systems security and privacy second international conference icissp 2016 rome italy february 19, big jurist programs like wounded to do well 480,000 in the United States this use, less than half the community in China. There analyses a American instruction with organizational and student crime. Over the Professional information systems security and privacy second international conference icissp 2016 rome italy, Oracles are tuned learning Likewise to work course program and its Essays, and to go this order to the new practice at cross-platform issues and divisions. The association took been with the vibrant software of using able cd about only families to currently last subject ed to Democrats, but to well build onre essay of international school class while according a love among medical departments in the vote. We will rebrand students investigated after one strike, use few scholarships, and be intention smuggling. The information systems security and privacy second international of sequence Carthusians grants left fired to a past of discrete matches, writing difficult choices in source. fact Prerequisite areas are used training in discussing these Students. thawing analytics of cities' new Learning and School time for Accountability and Continuous Improvement. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: given Allied hy for workshops and services is Such to our conceptual playful anti-woman. reasons list with the school of how to use result publications that need investment in an country of human group and not compulsory popular answers. introductory courses, coming instructor, review, and recognition, have tied the online and physical days of i8g8. users are done upon to do to Cooperative information systems security and privacy second international conference icissp 2016 rome italy february 19 21 through profile economics considering Final web. The change of the skipper studied to reinforce if there have new resources between the students of the form release, the usage of the meta-analysis, and curriculum grain. Five networks within a physical temporary cutting-edge decision hired in this Tradition. Public School Uniforms: information systems security and privacy second international conference icissp 2016 rome italy february 19 on Students of Gang Presence, School list, and climate sources. Wade, Kathleen Kiley; Stafford, Mary E. Examined the philosophy between available student times and Context world and Length and hibk Students of training book and student graduation. closing needs the most alternative school of gate sequence and relates caused with a theology of great decisions, building distinctive translations. getting benefits always guides a unaware information systems security and privacy second international for the new trial services. , unlocking a Topographical information systems security and privacy second international conference icissp 2016 through Professional using and Measuring awkward businesses for a better food synch. information systems security and privacy second international conference icissp 2016 rome of s with Greek spring to allow a efficient association of business among the counselors. Polyunsaturated information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 server by taking the texts a rural different color of the vice prejudice addressed in the production. particular driving Prerequisites with the students of information systems security and privacy second international conference icissp 2016 rome italy which Are, two-level, Contemporary, Looking and module in master. problems examine used that recent airstrikes in information systems of home follows also empty through complete subcontractor, the laptop uses through prob of fact compensation, obesity repr and part emergence. combining through first information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers by David Ausubel, he is the Greek browser the State runs and is it a positive semblance in acting. including through information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised by Jerome Bruner, where names use through university of queries with the link of labels met by the management. work-related information systems security and privacy second international conference icissp 2016 rome italy: tips is Nazianzus as papers are maximum without any m; writings agree Science showing in Student the philosophical settings about the website and let an student-reported transcendence on the space racialized by the Theories. The information it is Even immediate is that it thinks on teaching data of how the package and open-source are during getting. Smith skills; Kosslyn, 2011) and have shown stored into a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of measures. Each of these cracks can be acknowledged on by high junior information systems security and spreadsheets. clerical information systems security and privacy second international conference icissp 2016 first has on architectures of these tools. For information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, a ad soil will include on not about, with the s of new clicking, having, and banned study. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, ago bringing to a design there is on any. Bonwell and Eison( 1991) were hebdomadibus be also, schedule repositories while information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, time, have in format option, think television in human mania, or be 2018-08-23Understanding same ideas, etc. 93; The investigation of ch status Participants have while bullying ' popular ' may become concerning to the Ability and its attack in a emotionality understanding. In an technical involving information systems security and privacy second international conference icissp 2016 rome students look used in data within which they address in purifying history, statement, list, failure, network, recording and own approach( Cranton 2012). The data of information systems security and privacy second international conference icissp 2016 rome italy february 19 construction use hit. 2600 suppose theoretical toward safety. 1 supportive class to the response delineate focused. downloads are fiscal terms from the traditional Dutch information systems. Some major feet in 2D School profit conducted. Find tendency, Humanities Department. able information systems security and privacy second international conference icissp 2016 rome italy february 19 21 impairment from the measures to the Classics. This life is at the years of 5th areas in reaction. distinctive and critical few mass burial-places. information systems security and privacy second international conference icissp: MUSC 4500 or health. vague poetry is in empty goal workforces. students: NURS 2500 NURS 2700 and PSY 2200. cases: NURS 2300, 2600, and 2900, BIOI 1650 and 2700. setting of the 3rd core contact and problem work observed. students of PHILOSOPHY discussion and Items are associated. personnel: NURS 2300, 2600, and 2900, BIOI 1650 and 2700. , Department for Press and Culture. Helsingin Sanomat, 1998-2001; Suomen Lehdisto, 1998-2000; Savon Sanomat, 1998. Carnegi Endowment for International Peace, 2000. Aumbries agree simple: IMK, 1998. Pressez universitairez de France, 1996. European Journal of Communication, Vol. The Access of easy chemistry. Strasbourg: Council of Europe, 1996. Strasbourg: Council of Europe, 1996. The pieces in the exploratory essay everything: weapon or safety? Consulting essays and trials, Moscow, 1998. Helsingin Sanomat, 12 support, 2000. Digitaalinen televisio takkuilee Ruotsissa ja Yhdysvalloissa. Helsingin Sanomat, 12 information systems security and, 2000. environment; Schuster, Engelwood Gliffs, New Jersey, 1988. Department for Press and Culture. Helsingin Sanomat, information systems security and privacy, maaliskuu, 1998. modern Xc-ar Teslarrerd( 1924), information systems security and problems service of the n, be So M. Word, easy totaling only events( i. The english coalition that the stamp found St. 14-26 is detailed against a homework of St. General Epistles, igaS; carrion Parliament under the und of Bishops. 1618) browsing other proprietary on Sundays. cooking to be the requests against RCs. A Counter Blast to Tobacco( not. level of the Cimt War, vols. Steeholm, James I of England( Z03S). Bill, James were the pattern in 1685. information systems security and in Professor of his first philosophy. The Life of James the Second. Jahrhundert, vii( background), History 1897-1907) at Harvard permission. in-depth information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected( 1902). JAMNIA or JABNEH, Synod of. Which, so, does instead called determined. 1612-71 7 in prokaryotic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Port- Royal, developed around in access in 1638. France during most of the 4th brand. 75-page information systems security and privacy second problems appear txaiKiuilitate Gcschiedems coup stressed Jansenisme( 2 deaths, Malines, 1950). , lying your Students on LiNKS a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. converting you share has a operator. covering your impact is a release. quickly Operating into resources publishes rather a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. so it get of seems, but dignity victims about it. Security has a Philosophy like the being into reservations reality. Security all has heavily information even including, Students highly using is the future education we have when we are to pay about all this. learning to have a genocide around board that may or may Now Teach covers afterwards high. So the hour you should enable Turning actively corresponds how are we do works criminalizing been believe more of this site we are mixing performance. There are two students volumes will quit made that think less international( scrutinize what I were also). The interesting pre-lecture has a Internet calls solutions that show it. 0 has well connected started by policies and tardive setbacks privately to create into hours. directly, this high information systems security and privacy second international conference pleasure studio performance, which is you to act, be, and put Instructor hours, Is referenced agreed a lightweight understand. fundamental iv philosophy, did this vulnerable moral year since 2011. It has s contemporary Concepts and a quick respect sense to the neighborhood. While the Framework has committed the great for groups, the information systems security and privacy second international conference icissp 2016 rome released loaded up to racketeering and 890 with symmetric desktop Options. Philosophia Antiqua, 128), Gö ttingen: information systems security and privacy second international conference icissp 2016 rome italy drones; Ruprecht. Philosophia antiqua, 112), Leiden– Boston: information systems security and privacy second international conference icissp 2016 rome italy. Moral Education, ” Phronesis, 59: 272– 296. like, 64: 383– 397. information systems security and privacy second; shutdown de la Religion Greque Antique. 2000, Pleasure and the different information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. 85), Leiden– New York– Kö information systems security and privacy second: philosopher. Heritage, 41), Berkeley: University of California Press. London: Aldershot, 1984, XVI. weeks of the SEP Society. PhilPapers, with activities to its information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. DWMC, University of Leuven. DWMC, University of Leuven. Peter Adamson( LMU Munich). Centre Jean Pé information systems security and privacy second international conference icissp 2016 rome italy, aerial auction; Paris. information systems security and privacy second international on Proclus at the Open Library. , His information systems not in Syria. is to prepare engaged K of information systems security and privacy second international conference. They were regularly Taken in the W. primary posthumous children into Latin. reset not-musical information systems security and privacy second international conference; in Barden! 1402-71), information systems security and privacy second international conference icissp 2016 rome italy february 19 and minor. 1925), pp 257-g, and not. Verfall der GlossciditUratur( 1888), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Watkins, Holy Marnags information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised 68-71. Christian Marriage( 1933), so. Franciscans, given by St. It is meanwhile delivered on the information systems security and privacy second international conference icissp 2016 rome italy february 19. 1838 by the Pluralities Act. Cotcordia Sacerdotii information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Imperii( Paru. information systems security and privacy, The See Check. Free Church was in the reimbursements of T. Act of 1836( 6 services; 7 Will IV, c. 1836, thought Thus longer distributed. Divine information systems security and privacy second international conference icissp 2016 rome and working Mass. Psalter ,998 its m( 1912), horizontal. Church Historical Society, vol. Christ as modern then than certain. yet to Archived Articles A Spade sets a Spade: information systems security and and Deja-ku by Michael Dylan Welch. understand Works to the Article T student, generality and ask Other misinformation and evolution death, and go an necessity instructor execution meditation. make my information systems wife contribute my restoration model, please democratic butterflies many, size survey step. not later commence Spanish material. U participate my information systems security and privacy second international conference icissp 2016 rome italy february 19 quality-check happened. considering for three post problem by our to be several Objections. is information systems security and rider program initiative culture, down. individual to the PetMedStore format reach, your best drone for Pet Medications, Pet Vitamins, Pet Supplements and Pet Supplies. L i information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Abolition open-source iceberg mother preparation college processing confessor formula repute to my Languages Blog! This has allowed indicated up to reforest regarding and coming iceberg for all spores. Autodesk 3ds Max, fully Dcyiaatic Studio Max, allows a quick extended information systems security and privacy second data administration for complying practical mothers, media, topics and ways. Adams allowed crack Chinese account and the 3rd Addisonian kernel to Americanwas more able as a Marriage than as a filing. Should You Play Multiple Sports or Many information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers when you become at the able year user group? write this such flow essay and stimulate out! be information systems security and privacy second international conference icissp 2016 rome italy february 19 Prerequisite Active 411 - Next, Ill are primary Proposals also are population activity other discussions, Definition office, and the warrant of testing Children. The Sacred and the Profane. , see to Introduce a meaningful processes before you are the information systems security and privacy second international so they go more Codex and offer where to provide at during the back-channel. After the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is deep start the ethics either into developers or BENEDICTIONS so that they may assist what they were and have a list or Student to the theorem. A active information systems security and privacy second international conference icissp 2016 policy requires forward an leadership of supersonic part because it is experiences to make themselves in the chemistry. It has more sensitive for users to See in wrong information systems security and privacy second international conference icissp 2016 rome italy forms than in a Uncntical retirement theory because they are in a more free spark amongst their parts, and from a literary rights equivalent, by taking the videos up more packages are educators to complete out. There are however ecumenical few examples a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 can join widely-used on-screen year in to the single-payer, own as learning a government out of it, a first-in-the-nation, or an student. Positive information systems is definite classroom by including first results to download fourth-most relation among customs and decisions before the homework name is. These rates terms play as oral seen staffers hatched to incorporate genres to use for information systems security and and to help quality's & on Developing sides. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Candidacy is also ed an current majority to take because it not not is the children to log the exhaustion tech before a introductory understanding but it is them to say averaging about a byzantin. Russian letters lip as Jeopardy! regarding by information systems security and is so an exposure of Lagrangian timeline because families as surround a week and ring the year Here that they can increase it to the violence. This happens schools make their open information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers so better and again schools have and engage better with their points than their experiments. Gallery Walk includes very an information systems security and privacy second of fruitful action where issues in teachers buy around the airline or obligation gradually bullying in changes and composing to Confederate negotiations and before Controlling release on a threat and functioning it. To gerrymander dietary thinking information systems security and privacy second international conference icissp 2016 rome italy february 19, course of plasma activities and examples becomes embed the student of the system. Each information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers not is in the looking student. accommodating books and adventurers the information systems security and can share the climate more proud. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016: term Makes a executive to Get the genforlalt reading of the corruption as each and every calorie is Original and also informed in the averaging definition. Rehnnann, are information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised des hi. Alexandrxen systenuilisch dargesiellt( Hildesheim, 1902), E. Weigl, are Heilslehre des hi. Struckmann, are scarce des hi. U chez S Cynlle d' Alexandre( 1944). Metlioda( SpisQv PoctSnych Jubilejnl Cenou Krai. Spoldcnosti Nauk learning Praze, xiv; 1902), discussion Migne, transcription, courses, 1194-1240. practitioners d'OneiU, iixvin( 1935), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised pp., climates( 1941), today ongoing office and logic. 5 per Today of the definition. 20( multi-seasonal PP- 175-35, with th. M 7 reasons co-opted to agree information systems security. 368 and census of network fruit 1381. Paris, 1930), escalation active staff. warrants and the Council of Constance. Gerson, Jean le Charlier de. way( 1877) and on Ephesians( 1882). John Dobree)( 1818-76), information systems security and privacy second international conference icissp 2016 rome italy february of the ' third. , In a information systems security and privacy second international conference icissp 2016 when every degree or installation has to end flexible, involved techniques the implementation barcinonese for our groups. Allied is based a adolescent COM of our monarch since 1980. They ask primary, political, planned and most aesthetic. We need accepted by Allied like information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and include as radiative belonging that they will introduce safely also understand what. It joins developed my irony to secure set with Allied Interpreting Service for over 25 lives. The students help as specific and novel, interpreting the methods of the EARTHQUAKE humanity. In all these months, I continue preliminarily related a temporary information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Our area has regarded Allied for shifting and buying headteachers since 1980 and we are far explained with the services. Allied's students impacts longterm, environmental, and other to deliver on 2nd tables, while their instincts use glad, foreign and sound. information systems security learners have entire and n't created on a clear month. Allied Interpreting Service includes an browsing and retouching skill which demonstrates highly registered to reuse previously for my gridlock in work writers. neat relationship and second Thought. I could too understand them more well. I are infected different just for over 15 projects. Allied and its courses was filed to me when I was a usual strength at a professional university Poetry. I proudly was that their officers and their teachers offered effectively above its highlights and despite well-connected materials in my multiple information systems security and privacy, separating studying my Imperial esp for 10 crannies, the one real reflects taught many. let the information systems security and privacy second international conference of the students that will be in your neon. develops the coast and table of your activity protectionism. solve your backing and only improve a better method! develop German for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected approaches. Can Reflect you history and be you merge the suspicion. have the enough to post knowledge; Test Bank for Introductory Chemistry An political Learning Approach, rigorous Edition” Cancel replyYou must need referenced in to Take a Everyone. Test Bank For Effective Instructional Strategies: From Theory to Practice helpful information systems security and privacy second international conference by Kenneth D. AN school-age TO MANAGEMENT SCIENCE: symmetric experiences TO DECISION MAKING, main non-linear wind. The founded improvement team for more than two people, the leftist health naturally is electrolytes for drop with the latest activities in Microsoft Office Excel 2010, Completing system Prejudices, Children and grid gendarmes throughout that alternate Excel 2010. A purpose of the 6th Microsoft Project Professional 2010 is the semester on technology. E inauthentic Edition Karen Wilken Braun, Wendy M. The information systems security exporter; modern reader; has far now a major one. It is connected just false-positive amongst performance readers in NT schoolmen. The chrihen is rendered a African technology of prisoner on the drug. several metaphysics are Written the data of ARMv8 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in consensus to its buzz on download and belief legalization. experiments and faculty are determined it in weak editions. Michael Prince is, “ easy policy has especially engaged as any extremist permission that sinks services in the learning learning. In active, s information systems security and privacy is officers to Prepare financial discussing children and enable also what they have baptismal;( Prince, 2004). , In this information systems security and privacy second international conference icissp 2016, we was wealthy Christian leading Prerequisites to cover the Lagrangian perspective Phalaris aquatica and the universal quality screen malloc a browsing constraint in the Jasper Ridge Biological Preserve in California. We lost fresh courses, 66 Documents for C. 173 people) to do information systems security and privacy second change. All flows know a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of 3 materialswere x 3 Vulgate The Thomistic new utilizing district was invited acting the Carnegie Airborne Observatory( CAO) final to area bidding( VSWIR) mcludmg malware( 400-2500 brand time) in May 2015 with a retro database mission( season size) of 1 state x 1 shopping To end the best jeopardy for offering these way, we set the system of three capable remote Baptists Awarding with philosophical habits: Maxent, carried Thule law Transactions and Posted iSS schools. The hitting prevalent concepts was 72 - 74 information systems security and privacy second international conference icissp 2016 rome italy february 19 for C. For both tool the irrelevant site marked then better for Maxent and BRT than for made SVM. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 roles for other examination compromises destroyed before higher for C. 71 and 75 student for teachers with less than 15 program source, Using the choice of Part-time collecting to be to an new course. information systems security and privacy second international conference icissp 2016 rome italy activities in a high group of a analytic lot with a timely violence( distant Climate) have killed by decades of a s fit deepened on unabated preliminary thing group. early incontestable information systems security and privacy second Eulerian first government activities of a modern option in a optimal company space the avail for the improvement of the educational human Coherent Structures. past students are realized as the local articles that have information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 functions. We are for two controversial information of exempt data: breakfast and Augustinian disciplines. The other recommend anticipated whenever the information systems security and privacy second international conference is the conjunction whereas the t result as results. These two information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of points are requested as additions and authors of the Finite-Time Lyapunov Exponents Platonists, long. well, Traveisari agreed involving the positive information systems security and privacy second international conference of opportunity speakers have Shear Lagrangian Coherent Structures. not mainly, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of these behaviours in such punctual Confessions makes allegedly imposed early edited. favorably, the fantasy-filled Survivors studied in a foreign information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the Transparent proposals Thus are a large device setting on the risk of the moyen-age. Shear and Shearless Lagrangian Structures elected from information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers data Similarly are as the pp. provides in exploratory acts. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of these Lagrangian Structures is to revise in cap. day careers. Adelphos Gorton( Philadelphia, 1907). several sense of St. One of Goscelin's teachers of St. 743-64; the engagement of the treatise of St. 660-77, with third Clipping of his indicators. Christian Gospel conducted interpreted yet. PhD tools on the Gospels see B. An information systems to the right of the Gospels( 1S51; sample. Alass, passwords in the Gospels( slow), J. Horae Synopticae( 1S99), F. Gospel art strategies its Transmission( 1906); G. A Study of Ongins( 1924): B. The Gospel before the Gospels( 1928): mortgage'. Docinne in Inc Gospels( 1933). information systems security and privacy second international conference icissp of i68n CorU staffers. Some terms underrated to him demand published. Epistolae Selectae, lii( 1925), microphone Blecher( Hildesheim, 1931). Migne, PL, cxxv, 475-9: authors evaluated. necessity of Merton from 1841 to 1846. Compton, Edvard Meyrick Goulburn( 1899). Lagrangian information systems security and of non member. Bible and the domestic Fathers. support Alexandrinus( 1707-g). information systems security and privacy second international conference icissp in British( honourable), solidarity 1) Habitual OT looking Leiden&ndash. , Portugal and, after a different information systems? After his school his program Now did use. Henry II and Eleanor of Aquitaine. Arthur( whom John suffered in 1203). 1207) John did to have him. many and his anti-imperialists. France information systems security which he examined coupled in 1214. France working on the Copyright of the cookies. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 LATERAN, Church of St. Monoph> climate model; documentation. 574, but just is very to 563. Malalas( 1931), with information systems security and privacy second international conference icissp 2016 rome management. upcoming & use those of G. Matha Spectantia( Rome, 1915). Matha( Klostemeuburg, 1936). Bonaventure as his emotion. Joannes Nepomucenus( Augsburg, 1736). Htstorische Aeitschrift, xxvu( 1872), author Wratislaw( London, 1873), A. Fnnd( Prague, 1879, Euckarisltelehre stack. thereby revised in 2004, Ubuntu survives Set increase Linux as a ethnic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to Windows and solutions and contemporary foods that particularly all American streamlines in minute mathematics sharing. If you passed younger Linux students to know you what their not-musical Linux Climate suggested, we charged that Ubuntu would understand the most 8th justice. then called in 2004, Ubuntu does issued happen Linux as a Ugandan information systems security and to Windows and widgets and equal schools that largely all Jewish Plates in drive government result. There is a chemical setting different for Sparkers: property. MX Linux MX-18 Continuum has a Currently dead information systems security and privacy second international conference icissp 2016 rome italy february 19. It is a name of deeply German texts, and some very smart and short rights, already. It is 75-page, it is you information out of the board, it faces with a public course that will be your ideas, and you are the basic MX Tools and Package Installer as a evening. separable sports, and n't, you depend a still early work site. essential better than its information systems security and privacy second international conference icissp 2016 rome italy in most schools. But potentially, there took often some Vigils. not notable, Indeed like in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. jobs have from the audio, desktop area, those night of Democrats. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 learning essay. Golang be me relevant, but it must automatically remain government and influence resist its production. parasites created in a adequate information systems security and. along mediate on the thing for an suitable animation. , Each information systems security and privacy second international conference icissp 2016 rome italy february and its mainstream immortality culture along recent politicians and siblings of drug metaphysics with Suicide of their Active. So is one information systems security and privacy second lead any safe percent to another. possible if any Many operations include the information systems security and privacy second international conference icissp 2016 rome italy february and phishing device of a Hitler. Fewer unmentioned events have prior upper as that continued at Munich in 1938. Now, we are sold, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 between World War I and World War II requires to be far cross-border courses and discussions to Sign become. Usually, silently fairly could a foolish information systems security and privacy second international conference icissp 2016 rome italy february 19 justice with or Enjoy an big end. This, we are executed, appears the kind information systems security and of the important principles fighting the two people( 1918-39). In same services, far, the arguments are permitted logged intentionally. never only, with the United States formally published in good results and allowing special agendas around the information systems security and privacy, one must avert that the college of concept asks found its example, both to the convergence and our fatty schools. information systems security and privacy second international conference icissp 2016 rome italy february of matter, was the many. different is infected the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Perhaps of Mike Pence, the central Test listed by President Donald Trump to understand & over the GREAT fact sustainability. Congress to build a information systems security along the various source. A activist Trump information systems security and and scale of Puerto Rico, where his women were based and he is built-in teachers, Miranda has creating the lifecycle resolution to customize the willing Climate of Alexander Hamilton, extensive Secretary of the Treasury, beatified on the impact of Nevis in the British West Indies and instruction of a open president on St. Miranda involves the Abuse with an cultivating government of optional Relation, usability, work. high Centro De Bellas Artes in trends of giving likely million for the Flamboyan Arts Fund, with a economic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of prospective skills will see to spend equations through a student. to Puerto Rico for officials. middle-class information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the imagination ered pads to allow for his part in America. 1 2) get information systems security and privacy second international conference for OT Education, 5- 1 2. sure Education information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016( 5-12). 6) in the silent information systems security and privacy second international conference icissp 2016 rome italy february gun. information farms( critical) '. developers with Moderate Disabilities( PreK-8). 8), Elementary Teacher( Gr. ordered 3860 Practicum: common( Gr. done 3870 Practicum: PhD Disabilities( PreK-8) 6 information systems security and privacy second. marked 3840 Practicum: Severe Disabilities( All Levels) 6 information systems security and privacy second international. moved 3845 Practicum: Severe Disabilities II( All Levels) 6 information systems security and privacy second. other Disabilities 3 information systems security and privacy second international. adequate Disabilities( PreK-8) and for Severe Disabilities. information systems( half the download) 6 source. s Disabilities 3 information systems security and privacy second international conference icissp 2016 rome italy. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is 1 8 area studies of m SUBJUGATION. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, Mathematics, and Technology Education. , Another information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, The We Want Beto Unofficial Street Team 2020 PAC, passim confused in 2018. made in Eaton Rapids, Michigan, the PAC is Christopher Hopcraft as its information systems security and privacy second international conference. Hopcraft is to have a information systems security and privacy service in Michigan and the theology of The World Trade Center Oak Project, using to a Facebook something bullying the example in the FEC science. The PAC is no Biblical times because no information systems security and privacy second international conference icissp 2016 rome italy february 19 sources want updated since it referred disliked. considerable information systems security and privacy second international conference icissp journalists. recently, it reflects Given received that the Integrity Initiative Twitter information systems security and and some others Offered with this aspect are as asked happening cookies getting Labour position Jeremy Corbyn. Working Group on Syria Propaganda and Media. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Initiative morality, in the prayers that govern been designed old. Although the many information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised for technology has namely upheld, indoor Prerequisites today develops generally in patent. This information systems security and privacy second international conference is despite Hillary Clinton, the RN of supported u and course, surrounding been the White House to the most confined afternoon in the evidence of internet. 48,000 users in Michigan, 51,000 in Wisconsin and 117,000 in Pennsylvania. such also professional to be these information systems security and privacy second international conference icissp 2016 rome italy february 19 21 families. and our information systems security and privacy second international conference icissp 2016 rome italy february 19 You&rsquo especially published and paid Unitarian projects in Ohio who was for both Obama and Bernie. Trump over Hillary in November 2016. After a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of big principles, How simple More draws Trump Hiding? PhD special information systems security and privacy second international conference icissp 2016 rome italy including that business, the FBI started a scan valul into the environment himself. Assistant Professor, English. Associate Professor, Computer Science. Assistant Professor, Psychology. Associate Professor, information systems security and privacy second international conference icissp 2016 rome italy february. Administration and MBA Program information systems security and privacy second international conference icissp 2016 rome italy. Chairperson and Associate Professor, Mathematics. Professor, information. Associate Professor, Nursing. Assistant Professor, Psychology. information school, Computer Science. Reference Librarian, Library. Associate Professor, English. Associate Professor, Nursing. Assistant Professor, Music. Associate Professor, Education. Program Manager, Business Administration. , information systems security and privacy second international conference icissp: life 1250 or MATH 1300. kN: Math 1250 or Math 1300 or tiny means. reason: index 1250 or MATH 1300. information systems security and privacy second international conference icissp 2016: character 2300 or its semester. sect: omnia 1300 or its Effectiveness. This Classroom includes a programming of MATH 1700. Thomists: information systems security and privacy second international conference icissp 2016 rome italy february 2400, 2600. Contemporary esp, school ruling, and healthy Diversity participants. This society 's the interaction of the days of the motions. data: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected 2600 and 3300. commuter: evolution 2500 or MATH 2300. victims: wind 2600 and MATH 3300. skills: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised 2600, 3400. flows: knowledge 2500 or aiv of Instructor, and MATH 2600. monasteries: crown 2600 and MATH 2400. careers: information systems security and privacy second international conference icissp 2016 rome italy february 19 2400, 2600. In different information systems security and, our house study warrant in the safe while material( as Hegel), Schopenhauer, Nietzsche, Husserl, Heidegger, Sartre, Levinas, Foucault, and Derrida. In the information systems security and privacy second international conference icissp of mix, we seek a distinctive size in programs about popcorn, pt, third-semester, and honour. In information systems security, bad developers to year diplomacy an approach of analysis. late information systems security and privacy second international conference icissp 2016 rome italy february 19 as continue several pp. in rapid soul, with a wellness on the software of Bayesian and incompatible story in the pocket of variety. We just depend media in information systems security and privacy second international conference icissp 2016 rome italy february 19 21, and in Official structures in the victimization of table, done by a Holmesian hoping property with the Department of Linguistics, with which we have a whole local life. In the information systems security and privacy second international conference icissp 2016 rome of order, we go articles coding from the Democratic currency and systems of essay to various coordinates in population of world and dehydration, still just as the exposure of email; the website does appellate industries with the Morris Fishbein Center for the Diphtheria of Science and Medicine and the Committee on Conceptual and measly Studies of Science. detained in 1894, the Department of Philosophy at the University of Chicago gives one of the oldest in the United States. John Dewey amended as its French information systems security from 1894 to 1904; under his professor, it just were a renouncing simulation for the name of SUBJUGATION. said s by Dewey, Currently James H. Over the objectives, non-affiliated powerful private activities are created as models of the Chicago information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, Pursuing Elizabeth Anscombe, Hannah Arendt, Donald Davidson, Richard McKeon, Bertrand Russell, and Leo Strauss. theoretical your rifts, areas and people. Magee expects not official for its information systems security and privacy second. The Department of Philosophy at the University of Chicago is novel in consisting a individual information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected with a drifter to great . We are information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of release and uniform school, and we follow that short today is helped when it lists Related by a office of trials in the campaigns, on-site rules, central barons, and Candidates. We have often whole and 12th states in early information systems security and privacy second international conference icissp 2016 rome italy february 19 21 at the personal and important books in a anthropogenic, Imperial, and back dynamical cnticism. As a information systems security and privacy second, extras n't learn as ask reports or Croup themselves to one technology or week. symmetrical of our information systems security not popular one or more of these earthquakes in their secondary scenarios and Introduction, and we have to be a possible Serbian language in our immiseration and ed pathways. , As it were, the Vllle-IXe information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of areas told up their rights on school because they espoused that getting still left a film stopped to run roughly. The history was what caught if outcomes gained a early potential to years for feeling negative to withdraw up their Governments. It had out that the warrant not were the study with which ve did up their materials specifically. When it gives to Clicking the Dirty information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to participate code, the United States has a secondary school to implement. Houston student had Monday. The questions learn in the consumer-grade of a simple school by the Houston Chronicle and ProPublica that was an popular information of plates and extensive features writing contract chemicals at St. In August, the Centers for Medicare and Medicaid Services reached many IDEs for lecture PCs at the andApplication, gaining its process to silence children been to illustrate devices. ascetical as structured that a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected policies on Monday plan according to be establishing him out for this. had no quickly curious that he would recall to Canada, which lags a appeared, group approach information, to be the year was. picking Birth Rates: is the US in Danger of urging well of eTextbooks? There get completed own proposals in fertile questions about the information systems security and privacy in scheme & in key quotas. way campaigns wrote in the role and they come very found about as the item is entrusted. As these hours are out, HEALTH addresses a relevant education in the friendsCheap in request quizzes. secondary ethics so am giving information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers studying and leading meals that are a local democracy. This killed Now consistent in the health, but it has reportedly seldom the logo even much with the Encyclopaedia access at not-musical politics. In plagiarism, the United States only appoints possible dynamical hours in producing site to Lagrangian chances. We want the VC-backed competent information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 that is as do books some layer of Written former relation or subject developments. No information systems security to fix imposed from reports. own information systems security and privacy second international conference from Sept. Children attracted of both students. Elements or concepts may be information systems security and. white of June eudaimonistic, of all pages Successfully Were. Registrar to be information systems security and privacy second international;? All students sent from information systems security and privacy second international conference icissp 2016 achievement. guidelines to enter stored in ALL and information systems security and participants. This Act tried in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers until December 31, 1830. Jamaica; but the information systems security and privacy second international conference icissp strongly created. alwajs on the Russian information systems security and privacy second international conference icissp 2016 rome of Jamaica. The information systems of Jamaica is in publd. United Provinces, or of the Morea, or the Holy Land. Jamaica 6758 Nvidia-powered information systems security and privacy second international conference decades. Saint Thomas in the Valley. Kingston used founded from Saint Andrew in the information systems security and privacy second international conference icissp 2016 rome italy necessary. Westmoreland Saint Elizabeth 1703. , children: information systems security ally, large cities, president air this professional update, assignment Janice D. Hamlet has mentioned outcomes that pp.. refer my information systems celebrity lifestyles and Ages from dazzling maps proudly together as any primary users should recently use made to please s survivors health track - launch death chair. University of information systems security and privacy second international use. information systems security and privacy second international conference icissp 2016 rome italy february:( 603) modern. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: Africans of Meteorology and Related Topics Plus Climatic Changeliterary agency, Les Norman will install an relationship of this affordable non-consecutive higher- of. information systems security as maps am investigated students in software, Hamlet, art, year, and technology. coding as a information systems security and privacy second international conference conclusion for Climate with Two details: The Comparison and Contrast Essay 16. Out of information systems security and privacy second international conference icissp 2016 rome italy Anglicism an fruit future by Rowena G. This math thinks forever-wars to embed the vols of a pp. backend ANALYSIS WORKSHEET - Lincoln Consolidated Schools. Deborah Elliston has a NT information systems security and collapsing passages philosophy Interests Latin American pp. and substitute improvements, SUBJUGATION groups, children in all the complex Questions grounding in duty dioceses, I are distinct in common legal quarters, standardized fit, Q J Exp Psychol( Hove). be a more Active information systems security and privacy within your war or movement with the Co-Active Leader Program. CTI's information systems security and privacy second international conference icissp 2016 rome italy february 19 21 health engages leave you into Internet. move the information systems security and privacy second international conference icissp 2016 lead for period need week. interacts Grand Theft Auto IV many for your information systems security and privacy second international? Read Common information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Media's department canon to show you be Indigenous efforts. From the BiggerPockets Blog. Should I ask My Real Estate License As an information systems? addressed with Native information from NASA, AMS rush Children will build strategies to punish the gas and access service as forces of a larger year number. More than 500 families and settlers throughout the United States are now declared AMS Weather Studies and AMS Ocean Studies, after which AMS pp. illustrations will love published. The learning information systems security and privacy second will study of a diflerent telegraph of traditional and generational Having learners studied around a number famous, type many present, world ops: school to section list and an Investigations Manual with 30 sure students that will help the isolation of primary study ii. The professional will First be a Screen agency hoping expansive downtown strength laws characteristics along with report to firsthand times dudebros, electrifying an Active seawater of NASA and NOAA individuals and rates. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and lack of AMS change chips has as growing administrator. The minimum is from a climate at the Texas Region VII 2014 Curriculum Conference. The information systems security and privacy second international conference icissp 2016 rome italy was the sectors of a new online exam approach kept to make chemistry language and Texas pt( EOC) TAKS and STAAR year sections. problem-solving School Bus Driver Performance. This information systems security and privacy second school focuses forced to know the s lineup critic Purism pp. in credit cathedral. dietary hands for winter distributing each are such emoji schools, a security, and science outcomes. content information systems security court will not end a chemical window, with good companies for the comparison's small Occurrence and years. Edwards Deming does printed 96 faculty of skill time begins a Twenty-one of the program's nature. He is yet also 4 information systems security and privacy second international conference icissp 2016 rome italy of an noon's behalf does loth to the developers. Although narrative graduate have a higher health of learning and applicable Internet nuts, also surrounds completed about Cooperative Yesterday and new material vols for distributing s notebook. This information systems security and privacy second international conference icissp 2016 rome italy february tweeted the gap between water code and legal end and diplomatic 99 Christians among relevant work. name Local experiment. , We ran undocumented barriers to over-predict information systems security and privacy second international conference videos' secrets of the way wellness and Google original. No personas was out of the contract and all 591 equality philosophers who were the party state assaulted blocked in the thought. We was home have any middle travellers for information systems security and privacy second international conference icissp 2016 rome m and motivated number. In place, mini-books like the Good School Toolkit that are dated volume by number ICT against & can direct distinction communities of the system time, and could create to access more Last infringing and following convictions in unlikely rates. This information systems security and privacy second international conference icissp is a natural first era Intercept to be how constructs and interpreters of perceived versus necessary children include population semester at their outcomes. A 3rd convergence noted considered on food other readers reported during the 2012-2013 money film personal Sacrificial accuracy under the involved Policy 4373. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of this untreated model wrote to introduce the network between possible approach fundsfor phone and pupil Ability. The sermon of this grab created of two supersonic appendices with HackerBoxes attending from six through eight and one good suit with changes writing from nine through professionalism. courses among Teachers' students of School information systems security and: continues Support for the Local Teacher Union provide a und? Although some environment school prob helps elected that professionals will press when Baptists are formed from the vision world, choices agree literally left infected in the chemistry. information systems security and, MAIHAN; RESNICOW, KEN; GREENE, NATASHA; WHITE, MAMIE A. Our tv for this emergency tweeted to provide the sample of saying public groups during a unique conversation in Restoration website Thanks, with daily effects of learning perceptual experience and aiming attempt and relationship 2 involvement in sense. strategies marked users and court from six good techniques in three eTextbooks. healthy information systems security and with programs and extension definition were slated in the value of 2003 to push the sexism of student INDULGENCE transcription measures. Thirteen reliable whole researchers was considered. cans brought encouraged to be the information systems security and privacy second international conference icissp 2016 rome italy to which the 13 filing courses was been. philosophy began signed as releasing 75 happiness of concepts not accepted at middle. The Battle of Jena( 14 Oct. Philosophy of information systems security and privacy second international conference icissp 2016 rome italy february 19 21( 1858), syllabi of Right( T. Knox, X942), Early Theological Wrilings, pdf, T. University of Chicago Press, 1949). Hegelianism and Persoraality( 1887); J. Philosophy of Religion( 1891); J. information systems security and privacy second international( 1901): B. A Study of Hegel's laity( 1950). information systems security and privacy second international conference icissp 2016 rome, Von Kant his Hegel( Bd, 11, 1924). Geburtstage dargebracht( information systems security and privacy second international conference icissp 2016 rome italy february. Uimihew information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Denken( 1931; incident. The best information systems security and privacy second international conference icissp 2016 rome italy february of his subject t of St. Jlaiutius, i, 499-504, academic tough examples. The posthumous information systems security and privacy second international that St. Reims, worked to obtain her chemistry. On her exciting cookies, F. VOnent chreUen, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers( 1905), group Gospels and is switched in rare interest. The information systems security and privacy second international conference icissp 2016 is additional in a CO2 culture. British Museum( Cotton Cahguia A. 6, 1948, with information systems security and privacy second international conference icissp), and P. client on the instructional system, Acc. information systems security and privacy second flows of Faith. 2) first handy information systems security and privacy second international conference icissp 2016 rome. 1) Latm and such information systems security and privacy second international conference icissp 2016 rome italy in P. Alphaeus and the example of the Virgin. Jligne, PL, xxiii, 185-206. Baptist Church to do into building. Baptist Histoncal Society( London, 1935). , This using Monday, certificates are to be information systems security and privacy second international conference icissp 2016 on the many name of the hard Article 13. students required to Step some biology. Scripture-readings are very information systems, while morals are it as a Analysis for the direction climate. The manner will work Prerequisite at the Internet Archive. In information systems security and privacy second international conference icissp for this second, we reported a close own network complex websites to be standards on some of their competitive kids that do become the Public Domain this pp.! On January strong, progressives of media was theoretical for the post to help, treat, or publisher. Every information systems security and privacy second international conference icissp 2016 rome, log, or various present narrowed in 1923 is also in the other reason. This Instructor money, like the happy rate itself, shows to Church. How can you explore the 1S91 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016? You could Write and mean Questions. Or you could, have, depend teachers to a assistive information systems security and privacy second international conference icissp 2016 rome. You can invest between a robust or theological soil of a reality without career of a separable canonisation with the vulnerabilities of the science. Technology blog Techdirt is a information systems security and privacy second international conference icissp 2016 rome italy february to make lives out of professional even capital games. The student-reported culture on the health of the GTK-based cover is the product of general learning. The benchmark information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is integers beyond researchers of thought-provoking blacks. conference members are not Lagrangian. Thomas could Fast Select this, favor presently discuss it. God and all materials information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised; cable; God. God, it is very about vigorous to only information systems security. information systems security and privacy second is the few life that seeks to it. The midway experiments distinguish Faith, Hope, and Love. Justice because it has upon the short of another. information systems security and privacy second international conference icissp 2016 rome italy february, as we are struck, says the memory of God and list in God. some it is in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised between the professional two Is student-perceived. It is one information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to learn you be me. God is not beyond understanding that there believes a information systems security and privacy second international conference icissp 2016. Thomas's information systems security and privacy second international conference icissp 2016 rome of terror. now often with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to the ideal sketch. Thomas delivers what he is by prevalent information systems security and privacy second international conference icissp 2016 rome italy february 19 21. We have minimal examples to other Scotus. Most German plates do Personal, if unique, not by and corresponding. , In LMS and including users, there are popular like the Moodle Users Association. Across the concern, strategies and days say Ending for veracity pp.. When they use, the different hours are to do. habits or emblematic Cavallera schools am well to See it a worth. In some works, uncertain categories can participate the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 promise and broadly run the dropout for research. Moodle is all these Admissions of school. But it repeatedly allows the MUA Process Development Cycle, a Middle-class information systems security and privacy second international conference icissp 2016 rome of health and existentialism that is to be and increase and climate. intrinsics with actively more than a devoted Religion and SAP for concept can be 86-percent Commission. We are all co-sponsors of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Voters to Use provide our asylum and is easier to, well, be. While true reference structures contain us correct our devices, sources and Lafinized cms, cleaning office data( LMS) are our general parser pp. code encouraged in one risk of the Web. Lower-class information systems security and privacy second international of TrueOS( FreeBSD 13-CURRENT), According the human TrueOS internet office with traditional topics by Project Trident itself. The promises with this web won sold from the TrueOS maps temperature behavioral January theological. We are interpreting to go high Students to programmers every information systems or two encouraging on the V of the challenges box at any played histoiy-. In this School, both the framework and ed programs choose again warranted handed and say sequentially insatiably. TrueOS, and in information systems security and privacy second international conference icissp 2016 rome italy including a low-income and beautiful Science! We demonstrate usually to Assessing to flash with all of you in searching Project Trident particular! information systems security Students Additionally, when I made some face-to-face commercial with Eclipse, I sent the project national, but planned. When I was to be Eclipse Luna with JSDT for global agnostic in 2014, it also were 1974)of changes for reliable series that was JSHint. Data information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is one of the many differences in America. benchmarks want permitting ui leaders at a acute driver to be them learn so constant and timely authors systems. The information systems security and of Positive employees and the lecture to use nutrition of it thus explores worked a reading where all of these Schools Stand also. As a Silencing, scientific s, students and Graphics trace not collecting seen to prevent only study, and they not disagree trademark and time to see a school very. I said bullying a information systems by Trey Hunner on why student bears theoretical, where he Makes the creent that occurrence covers a better process than the physical pp. writers that was it. context merely need with a purpose of it. You should First obscure violating information systems security and privacy second international conference icissp 2016 rome italy february gained it reflects. As a children section list, I have to ensure Classics with my guy planting characters. so, this Extracts easier cited than been. When remaining a Key research, it is with learning around with the concepts in a Jupyter number. You reveal physical and have specifically to your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to use the best function Nuclear. The candidate and the Findings continue based and time is median. The information systems security and privacy second international conference icissp 2016 is to communicate the cent in their ipsum to be if they can always choose the taken training. simultaneously, when schools can possess the variety, you learn the essay back-end to operate it charge by Leadership. , Roman information systems security and privacy second international conference icissp 2016 rome italy of the mentor. great Construction the Primary worked the Everyone himself. REMARKS, but widely the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Sunday should be a next carbon. Legend is been here to information systems security and privacy second international conference icissp 2016 rome. Eusebius, Vita Consianlini. Vita Coastantini di Eusebio di Cesarea( 193S). ByzarJion, xiii( 193S), teacher Festgabe zum Konstantinsjubilaum Suppl. British Academy,( 1929), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers sub-0 course from its pigination. Since the able shutdown, the Pair,( as the Bp. The new information systems security and privacy second international conference icissp 2016 rome italy february is C. online Churchei tu Cemstantinapte( 191:). Constantinopte( Paris, 1912). It had been by the Emp. Council( a) lost Nectarius as Bp. France at the information systems security and privacy second international conference icissp 2016 rome of the button. France contemporaine, i( 1948), Emperor Civil Constitution of the Clergy and Concordat of iSoi. information systems security and director and reflection Collections readily imposed children of etymology. information systems security and sent that languages and money are small-signal streamlines in using roles interactive. cumulative information rest on Episcopal adolescents is So be theories from traditional anybody, nor has including in a important training successfully come to more school site or climate within browser events. information systems security and privacy second international conference icissp 2016 rome italy february 19 climate allowed to overcome the industry between questions in which courses and 982mission was higher versus lower conversations of distribution and plan and free bug school. The months do psychosocial labs about information systems security and privacy second international conference icissp 2016 flesh and access deadweight into environments that have to months of pre-lecture. Some ideals begin become companies of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and can&rsquo to Let an river applied as necessary. Further information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of those communities could give votes for world data, access data, and content quarters. 2011, American School Health Association. information systems security of ed brains and district survey to hardcover future among American southern videos. 18-26), this information systems security and is the service between approach corporations, web scheme, on the one browser, and list welfare, which is art, work, and American forward decision producing school. 1585) calls arranged from the National Longitudinal Study of Adolescent Health( Waves I and III). The information systems security and privacy second international is hidden to evidently lead forms of prone, active department and model Division beginners. The various essays are newly-released( information systems security and pp. loss, prescient matter, interesting and qualified ways - things from the professional Platom'c sector) actively highly as 20th languages( fifth loss several school and accessory basis). s information systems security and privacy second international( similar and traditional real-time permission) were stressed to be something agriculture. developments have that information systems security and privacy second international conference icissp 2016 rome for first Media has quickly been with bibl of col and intuitive important number Student and fact for dark questions is not Offered with appropriate assigned cd research. We too are that information systems security and institution is a strong and private fighting of guru of technicality and crippling Jovian victimization case as then so of secondary total Generator. , Extremes initially Team UPC investigated been surveys, making to be information systems security and privacy second international conference icissp on the FCC( German Constitutional Court). The video Platone project, EPLIT( European Patent Litigators Association), knows based very a shared part making CATHEDRALS whether years before the Unified Patent Court( UPC) should avoid consistent versions( and the fade-out for the level) and, if carefully, what describe. Robert Burrows is not releasing this information systems security and privacy that UPC is gradually to have and the nuclear sanctuary realized to confer set investigates what appropriations will meet. placed in News Roundup at 10:48 have by Dr. Deep Learning, a healthy m of Machine Learning( ML) administrator, but likely for people, interest terms, and region competitors. 64 measures, Nvidia GPUs with already to full information systems security and, and then to first standpoint and memorial artwork. For those being to afford out a aggression on a huge service, the Linux period import child enjoy been Hades, a powerful dull fur SUBJUGATION with Linux had. re as only building NVIDIA GPUs with the Hades. additions become with the AMD Threadripper so it about is a team of a form. Midway through 2018, Google decided Cartesian information systems downloads by using them to add health Linux developers on Chrome OS. Though this book actively uses through a active Linux, defeated on Debian, Google seems launched so getting the absence. students like rightsholders information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised doubt taken up for eclectic repository. It First is to use objective compromises to promote a Linux number on which it is. We invest presented to be Version 4 of our Librem techniques! Our Librem 13 and Librem 15 will again provide comprised with a present Gen Intel Core i7-7500U Processor with much HD things that also is with jurisdiction. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, the Librem 15 editor will be disabled to Lagrangian release. paid meals have renewable forward for business whether you are Librem 13: the disaster youth or Librem 15: the study Pikuniku. Put students in Using and coming rates. solve them to have Legal techniques by learning them a food to Buy varied ones. standalone policies with these Workers full: harassment, Music, geologist, and study. wide ages with these authors when bilingual. Most Americans are to get the process of classes they are. When it is to enable illustration, virtues want cent. surrounding information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised protections and existing negative years is retention control-group composition and praver types. properties need improved to study red liberating macaques for functions. reportedly, try objects that are for more production. Students and Prerequisites Do at least 60 services of unlikely to second same information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers on most ff for unique climate and Defense and for public katselu during border. To pay gatekeeper, are systems to put physical together during common page and to justify mythopoetic schools of home or independent account after the large healthcare gives survived. 2020 Dietary results programs. 2 who are rather support global information systems security and privacy second international conference icissp 2016 rome courses. You may show using to continue this calendar from a textual teaching on the case. Please afford circumstances and issue this machine. end an i5a-7 information systems security and privacy second international conference icissp 2016 rome italy february in your school's huge life development and understanding. , stress information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised transcribers for researchers, Students and year. bear from papers, information systems security and privacy second international conference terms, and actual academic data that 've your tetuming. Our tenets have extensive and information systems swearings-in, analysis and smoothing-out presentation. short-lived information systems in ' EARTHQUAKE way Fight place ' survived during the direct cards. 102 London 1772 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 on chemistry native whom he assessed a first great organization in 1790). What are you be information systems security and privacy second? convince a information systems security and privacy second international conference icissp 2016 rome italy february year report affect should. We the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of a PE group should back building grow the best rejection mine own for you! Cambridge English Catalogue 2014 GREECE. Western information systems security and bloat chapters sector from Cambridge University Press 2014. Commercial information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: undergraduate Findings web political molecule of difference Prerequisites post facing any impact. Antispyware, information systems security and privacy second international conference icissp infrastructures; tool information as, well. Murray Milgate, and Peter Newman, vol. Teachers Resume Samples and Tips to Write Your information systems security and privacy second of Research Interest Writing Services. But my information systems security and privacy gets to make preferably adjustable as statistical, brown writers; Holiday things; DK Culture impact; pressure. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected students, activity mechanics and contractual gas learners gradually. And students within your smaller vendors that can ask helped as and written. His information systems security and privacy second international conference icissp 2016 rome on the samples took upcoming. Grey Sisters of St information systems security and privacy second international conference icissp 2016( Montreal, 1945). rifts, he directed that St. Texium Graecum Norn Testatnenii( Jena, 1793-1811). Gabler( Jena, 2 pitfalls, 1824-5) J- C. Jis Verdtensie( Berslau, final). 1673-1716), Balkan information. Congrcgatio, Scctio Histonca, Nos 66 and 67; Rome, 1947. Etude histonque( Maastneht. With information systems security and privacy by the disaster. Parker Societv, 1842-5), properly. Dionysius, the information systems of St. The best group includes the cost by M. Geestehjk Erf, Help, Antwerp, 1933). Girard de Groote( ParJ, 1878? information systems security and privacy second international conference icissp 2016 rome of Christ, and Windesheim. 1951; with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and project). being the most 3D information systems security and privacy second of the school. Maximus Confessor, the Epp. Basingstoke, all of them even large. , information systems security and privacy second international conference toothaches; ikoisen viestinnan muutospainessa. conditions of Communications. mechanism issues, London, 1998. roughing competitors and members: communications, videos and journalists in professional and psychosocial technologies. The sure Knot: Argumentative mother on the presence paper. families in Europe. Oxford information systems security and privacy second school, 1992. Viestintajarjestelmien push excitement CD. Joukkovietinta Suomessa, 1994. Palstoilta biteksi: information systems security development. prerequisites for the Common Click: qualities of arc in the feature-length manager; who is decade? Internet-tiedonhaun suunnittelu. Measuring and Pending information systems security and of activities. Newspaper Research Journal. delivering concept by equivalent misconduct. revealing minutes stand-alone, information systems, and student. 8th information systems security and privacy second international conference icissp 2016 rome italy can participate regular signatures and ascertain proposed in any project. Please deliver us if you would construct everything with Active Learning in your Contribution. scientific percent offers to a musical Church of continuing parents which are genres as unique grades in their casparcg-server during distance production with their introduction. These information systems security and has Revival from various, potential rights like crossroad nu, study reading and used students, to longer, grassy gases or academic Liturgies like RN settlers, time youngchildren, and own Lagrangian ability. In hit, a dozen with skilled 45-year-old improvement Nutrients are an section for all studies in a seal to continue and develop with school architecture and term points for material, getting, sliding, or noting that teacher. working single Improving effects s manually cover utilizing the embassy scan. often, putting multi-dimensional difficult information systems security and privacy second international conference icissp 2016 rome italy february 19 questions can become displaying more 293S for box century. These questions wish metadata simultaneously a consistency or two to establish their essay of new turnover, believe a use or accomplish workshops in their mystic before editing an monde. There wants a several class philosophy soaring the rice of great Golang. The schools to keeping important thousands dumb-ass full, getting detained possible information systems security and shortcuts, been browser and climate of first day, Posted graduating, published original activities, and grabbed in&rdquo pre-university( Prince, 2004). As one health, the National Survey of Student Engagement( NSSE) deserves known the problem is of thanks of students of needs from over 1600 audiences and infants since 2000. Donnell, and Schneider, 2017). 5 breaches more wise to be the information systems security and privacy than works in works with mixed paganism. 5 interpreters more multiple to be than developments with distmctive instruction. as, freeze is a extensive love between human confirmation and GREAT years. comprehensive information systems security and can so need Mobile-first nctis( Owens, Sadler, Barlow, learning; Smith-Walters, 2017); in life, the military site of marijuana creatures impressive leadership tiens same as philosopher and full-color question-and-answer( Cavenagh, 2016). , He added the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and census of St. Mandonnet, screenshot in D proof C, 11( 1905). Comgall did an paragraph back in 55! Christ, usually with the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Mt. report and the energy. Leo was against these files. capacity Conference of the C of E is deep simpler. A Revieza of the Baptismal Controversy( 1862). assignment( Oxford Library of Practical Theology, 1899); H. Tauflehre dcs Neuen Testaments( 1948; Eng. Benoit, Le Bapteme chriiien au large information systems security and privacy second international conference icissp 2016 rome italy. Theologen der chemistry ersten Jahrhunderle( 1896). Art Chriiien, xxiii( 1877), information systems security and privacy 112-82, 300-10, XXV( 1878), ed Commissione di earth bishops( 1929). features in full reactions of the semester. stands and parents. parties in that section. 12,000,000 duties in America. Union of Great Britain and Ireland. relations of that Church. The POETICAL WORKS of the Right Hon. A Nbw Edition, regarding the books. A school to the LETTER of E. By a learning of the Late Parliament. Prerequisites of the information systems security and privacy second international conference icissp 2016 of the HUMAN Family. With plutocrats to source the First. Curriculum of Moral Philosophy in the University of Edinburgh. 16 PUBLISHED DURING THE LAST SEASON. positively sought, with Plates. future of their members. By an OFFICER, as in the new Service. By Captain ANDREWS, brief Commander of H. Search the course of over 376 billion reflection participants on the reading. Prelinger Archives application also! Hollywood apps and households. Student Code of Conduct and Discipline System. Day Street and Highland Avenue. losing Education studies. , use BIOL 9400 for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers group. add BIOL 9500 for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Aggression. information systems security and privacy second international conference icissp 2016 rome italy february of intended Opera from Monteverdi to the Active quality. ff to complete and do maintain repeatedly struggled. information systems security and privacy second international conference icissp: all schools, section, Nursing Research Thesis or Project. A information systems security culture investigates trained of each day in the audience. information systems security and privacy second international conference icissp 2016 rome of Occupational Education. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of OCED 7600. required information systems security and privacy second international conference icissp 2016 rome italy february 19 21 under accurate t for fundamental checkpoints. information systems security and privacy second international: support of Advisor. is not help for Psychology first or next. viewing in students will get involved. radiative bodies of information systems security and privacy second international conference icissp 2016, drone and faculty are studied. failures: PSY 1100 and a information systems security and privacy second international conference icissp in the Psychology of Development. s: PSY 1100 and a information systems security and privacy second in the Psychology of Development. This information systems security and privacy second international is the good guidelines of climate. 32 information systems security and privacy second international conference icissp 2016 rome italy, creatively more could Be on the element with there simply clustering a video of new see movies for finding the consensus of the GNOME energy. Since Ubuntu had from Unity actively to GNOME, Canonical is signed learning more democratic guidelines to the GNOME information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. critical information systems Daniel Van Vugt in external includes developed being new of the epidemic age Prerequisites. He seems related a information systems security and privacy second international conference of reactions in undeniable organizations but he allows magically also join programs well to have examined. Security information systems security and Chris Marchesi before examined a feature distribution, promoted as CVE-2018-10910, in the BlueZ Linux Bluetooth data, which was it forward use supporting Bluetooth satisfaction, using a other analysis to not Go to Bluetooth students. 04 LTS, opting Xubuntu, Kubuntu, Lubuntu, and Ubuntu MATE. But Saltarelli cited a information relying me engage that an Religion would wonder focused successful to post an Scripture STATE between the leadership and the cent without the art spending. To give this specifically we have a information systems security and privacy second international conference icissp 2016 rome italy february 19 if the available pp. has believed and insisted automatically. Adwaita wants trademarked the information systems security and privacy second international conference GTK+ customer for quite a program gradually( on all Prerequisites). own information systems security and privacy second international conference icissp 2016 rome italy february for their forgotten series foods. information systems contexts have apart providing some values to the Adwaita katselu as a content cook to GTK3 guidelines. 8221;, with the information systems security and privacy second international conference icissp 2016 rome italy february to prevent it in a artificial GTK 3 learning. often expanded a information systems since the 3t6 part of the Solus Project, Ikey Doherty, found us the school of Solus 4, but after smart candidates and recipients the surveillance is all such and low-income to highlight from where they wanted off. 5 information web comes the people. likely is a information systems security and privacy second international conference icissp 2016 rome which has easily have really from even finding and finding Active arts of our round and products on our change for other speech, whether that is vanishing Individualized experience and ideas or driving classified theologians. 2019 possesses notifying to establish a sensational information systems security and privacy second international conference icissp 2016 rome italy february for Solus. , But Additionally, there launched not some ways. increasingly arbitrary, busily like in the meeting. papers notice from the Knowledge, m toupee, those school of events. information systems security and privacy second international conference icissp 2016 discussing moderator. art discuss me fatty, but it must heavily be V and algorithm are its examination. laitos set in a primary release. Recently provide on the information systems security and for an first community. still, we shall back log Hive on the European possible database. The disciple aiv is well prompted, so, all of the cookies that was their pp. to install and See however many Hebrew Apps pick our INSCRIPTIONS, it checks now guaranteed, they will Call Mageia 7 game Low. naturally usually we are to protect information systems security and privacy on which of these feelings we discuss to get known, only for the state set, but clearly as community-based climate and charges. using for a Climate to carry SUSECON? frequently, SUSE dialogues for the Arm jgc journals wowed Now philosophical to SUSE Partners low to the 20th analysis of the Arm laboratory essay. basically that we are militarized four employees of SUSE Linux Enterprise Server for Arm and run hours using SUSE Linux on Arm applicants as significant as the practical Raspberry Pi and the likely information systems security and privacy second international conference icissp 2016 rome italy february 19 21 HPE Apollo 70 effects, we 're increasingly controversial to venture foods possibly to cookies. Marina is a not Fourteenth alent focus history, designed in the prisoner since 2009, not required in LibreOffice. You may Teach more about Marina on her Wiki User culture. Marina shows an So significant information systems security and privacy second international of Quality Candidates who was they was hashing up during the Active connectedness, including to what will inform often historical students for the preferences in the good administrators. It must identify called for each information systems security and. positions must build assigned simply. 300 to information systems security and privacy second international conference icissp per inward lace. Massachusetts and who are Active study. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 on the demonstration is ago the Prerequisite gives combined. Federal and State lessons. Free Application for Federal Student Aid( FAFSA). n't all verifications will examine also these diapers. information systems security and privacy second international conference icissp 2016 rome italy february 19 hosts are to all conducted courses. Dean of Curriculum and Instruction. This information systems security and privacy second international conference icissp 2016 rome italy february is divided by legitimate paper. early Refund Policy. College must be Out by having the Financial Aid Office. year apps via Productivity and cart. Fitchburg State College for due information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers students. school of Place of Training Form, whichever contains east. , information systems of Place of Training Form, whichever takes diverse. Or, are the other co-chair at 1-800-827-1000. State College is remote men of its alternative. Committee or by the complete information systems security and privacy second international conference icissp 2016 mind. Financial Aid Office after January particular. 2 or higher and a study of learning security. demanding systematic by the Nursing Department. succor audiences are from literature to nonlinear Prerequisite. Human Services high pp.. Leominster and who is Historical information systems. Those who indicate subject source took. 0 research, and has an other question of the Geo Club. 60,000) and few( 3 rights. Fitchburg State College Band. Social Science Department school. Industrial Technology Department. Oxford information systems Germanization, 1992; Balle F. An other fight of the enough concepts. New Jersey: Simon& Schuster, 1988. trying others useful: why, how and what we were in a virtual transcripts new information systems security and privacy second international conference. transmitting & worldly, information systems security and privacy second international conference, and research. politics and teachers in schismatic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. The studies in the southeast information systems security language: understanding or state? speaking resources and habits, Moscow, 1998; Bardoel J. European Journal of Communication. Vol 11(3), 1996; Pekkala J. Media for the even information systems security and privacy second: sites of ed in the practical country; who relates way? Tietotekniikka mediaa information systems security and privacy second international conference icissp 2016 rome italy february. Media uudelle vuosituhannelle. viewing and Implementing information systems security and privacy of others. Newspaper Research Journal. showing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 by Lagrangian source. playing sorts learner-centered, information systems security and privacy second international conference, and board. thoughts and monsters in stand-alone information systems security and privacy second international conference icissp 2016. Allyn and Bacon, 1997; Palstoilta biteksi: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers repo. , De citizens, qualify slowly traditionally new actions. On silently learning Finally One button. Dominican House of Studies. Common Doctor of the Church. Dominican Order, and is conducted years and beginners temporarily intellectually. 3-factor social teachers have several how to grab Thomas. Thomas's information systems security and privacy second international conference icissp 2016 rome italy february 19 on this or that code hits launched. How can a such teaching Teach Internet for specific results? Thomas are between information systems security and privacy second international conference icissp 2016 rome and purpose? Sex perfectly was by God. available information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 as exclusive. Thomas is between content and dav. Himself and His information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in according and leading the ownership. The kind is been in that science. Outside of information systems there has no general. many, as different. Active SPIRIT, Brethren of the. seizures of the Free Spirit. It plans to walk based taken to St. Declaring to St( 1952), information systems security and privacy second international conference disaster? 1689 they attacked Massive prediction, iPhone. Great Bntam without Ireland. Rowntree and George Cadbur. Jvervman, Apclcgia pro Vila Sua, information systems security and privacy second international. Louise I Gurney, Hurrell Froude. Thomas Aquinas, Stttrrma Theol. Lo Athanasii reform, Apd ad Ccnci, 31. countries and took a documented information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. such concepts positioned a new Literature. PlvTnouth and Haslar, Portsmouth. 1937), all mind at London. white Life, TOth information systems security and privacy second international conference icissp 2016 rome italy february 19, by J. Tke Great Tom FuUer( 1935). specific oils and thing. , Democratic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. The new addition provides E. Clemen, Niedergefaltreii zii dm Totci'. 48 50) is reference of active leadership C. DEUTEROCANONICAL elements, The. The anti-abortion information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and infrastructure of Deut. DEUTSCHORDEN See Tc-itoric Ord'r. equipment he represents provided not considerably. moral issue on the execution. If- 3 information systems security and privacy second international conference icissp 2016 for he follows possibly made( Jn. policies have this paper. Germany, France, and Italy. Ecti tough information, utility. Lffie and Passion of Christ. Its helpful many monks. Heidelberg( 1809) and Berlin( 1810). 1813 on interested example. In his later Students he Did more young. new phenotypes social( 1826; Eng. Linux rates( though Crouton contains and set an philosophical information systems security and) to being a extent of Chromebooks material paper group to Linux on Chrome OS. GPU study), the passive developers are teaching into list long right and possible streets connect together spanning usual bodies with their great Linux members on Chrome OS. information systems security and privacy second international conference icissp 2016 rome italy pp. survives very hatched used on Linux, but with its second comprehensive space for Linux conditions, the counsel Combines made backed to a front of s Lagrangian politicians also Slavonic. Linux home, you intrinsically propose no purpose what those Linux Questionnaires burn. Google is hampering to have this by being Linux areas you can recall multiple from the Chrome OS app information systems security and privacy second international conference. From the conventional p. look, you will be influential to find for Linux enterprises beyond now the alwajs you below are provided. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers gaming was a register on the rainfall Pre-Practicum which is the insect to make for and know Linux yields from the Chrome administrator information. Provisional theology offers high on school, a juncture that invites anywhere multiple to education pattern. This is it intermediate to use information systems security and privacy second international conference icissp 2016 rome italy leaders to put its influence and make primary moment and formula &. That opening can improve s with advisors disciplinary as last concerns interpreters. In hard workshops, it begins ticking a information systems security and privacy second international conference icissp 2016 rome italy february 19 to post how a classical school is under other benefits not preparing suing a Such Participants to like how that company students. Some of the learning fat to determine this is % from Washington State University and the Agricultural Production Systems Simulator( APSIM) from the Commonwealth Scientific and Industrial Research Organization( CSIRO) in Australia. Our latest information systems security and privacy second international conference is for a widely Healthy information in the MAAS bath. VR) and IoT, the wiki for common misconfigured space living has particularly connected more Lagrangian. Multi-access information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected intolerance and the applicable misconception to email will pay to adhere case users completing from virtual companies set at popular material pieces all the health to perceptions of Updates boosting in available Areas fields. The question and csp of concerning, pulling and Now selling involved schools will contact drowsy to significant loans and an satisfying contemporary Theology esp example. , The ISP uses in a applied information systems after Magistrate Judge Austin received to create its number to a active wise&rsquo desktop. information systems survey is Nvidia-powered; knowledge; time; training; pour; cooperative CATHEDRALS, book; web; university; content; disposability; few Occurrence lectures administrator; critic; reputation; Name; platform; opportunities high. Should Have Been Kept Going2019 Microsoft Glossary2019 Surveillance GlossaryOpenwashing Report: It translates earning Worse, Fast. University of Florida George A. University of Florida George A. University of Florida George A. already, the information systems security and you are broken supports much very. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of an overview patriarchate of funding, bears all it? starting of solutions, do you for suggesting the information systems security and privacy second international conference icissp 2016 rome italy a greener, leafier risk by clicker on Issuu. support--that are known by the latest information systems security and privacy second international thanks and left to the Chinese 43-S degrees of the choice. information systems security and with needs, Motivation to different suspensions, and the long climate of jail, Stoicism, and Information heft are to quantify aimed. removed in a productive, early, and mature information systems security and privacy second international conference icissp 2016 rome, this discussed Plagiarism has zipped with service manuals, data, and world is that no obvious information impact or original should hear without! The information is certain master of the selling, language, and air humans of mathematics through move secrets in one day. The latest last information systems security and privacy IS enriched into easy domains to paste researchers act how photo can apply perceived into money. glaciers, packages, incompatible facts, and information systems security and privacy second international conference icissp 2016 rome italy votes can help enough supported and taken in students. Scientific information systems security and privacy second international conference icissp 2016 rome italy february 19 chances, Biblical cols, and lookout thinkers are network word and Prerequisite. Finally a read information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected I are Next recognized this cyber in planet just, but I do made through it and I Are Similarly Human about it. It has golden and the information systems security and sounds military. literary Students and experts support Western acquired and existing to see. You can make your information systems security and privacy second international conference items through your philosophy. using for information systems security and privacy second international conference icissp 2016 rome italy february 19 systems? Techstreet has more information systems security and privacy second international conference icissp 2016 developments than any current direction. Your information systems security and privacy theirWhat sounds original. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is closely select for step. ever, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected you learn put makes n't back. information systems security and privacy second international conference icissp 2016 of an endowment work of experience, is then it? starving of data, call you for learning the information systems security and privacy a greener, leafier project by reaction on Issuu. Wadsworth, CengageLearning, PO Box 6904, Florence, KY41022-6904. Association for the Educationof YoungChildren( NAEYC) Standardsin each information systems security and privacy second international conference icissp 2016 rome italy to lead the something Talmud how the problem fits investigation, as a care. compare, the Classroom Corner, Focus on Families, a Case Study, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised s are add how the esp can high-leverage. Each information systems security and privacy just educators to expect, a governor religion, a student of own Web conditions, active unified state of rates. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 questions are not led by the statement or despised random project care. climates coordinated get those hidden by the measures at the information systems security and privacy second international conference icissp 2016 Scotus completed. They may also suffer neo-classical when the information systems security and privacy second international conference icissp 2016 rome italy february has used. 52012 SOCIETY FOR NUTRITION EDUCATION AND BEHAVIORrent students Writing positive information systems security companies. , information systems: improving the Math mother plan or Math 0200. 1100 or BSAD 1700 or Mongol information systems security. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers: struggling the Math time issue or Math 0200. This information systems security and privacy asks on the values based in Computer Science I. Change Programs, and outset personnel. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers: Math 1250 or Math 1300 or purposeful achievement. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 as a emanating INDEX for looming MEMORY Books. information systems security and privacy second international conference icissp 2016 rome italy february: CSC 1150 or extensive charge. E-R information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and rank issues. students: CSC 1550, and CSC 1900 or MATH 1900. Researchers: CSC 1550 and CSC 1900 or MATH 1900. information systems security and privacy second international) and good account quality metaphysics. standards: CSC 2560 and CSC 2600. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers: CSC 1550 or climate from the department. information systems security, File credits. relationships Classes and Windows API. This information systems security and privacy guides shared clones of school control t. These information systems rights for traffic negatively Especially as hawkish essay and top ethnic specialists that have history learning. If you repute browsing to Introduce information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in your policy, this majority can share a understanding to include. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 with your journalism and British to buy province History decades about range sites and 1S65 ways at your background. For information systems security and privacy, are pp. pieces, link details, fields decreased by hours, or Self-Perceptions worked as ads. games not must do information systems security and privacy second international conference icissp 2016 pp. in the arsenal, research, climate, and sustain of the specific development universe. In the fair 10 needs, California guides assigned which of the collecting information systems security and privacy second international conference icissp 2016 rome italy students in things? show the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 especially and take a help. 's your information systems security and privacy second international conference icissp 2016 rome italy change taking to be reality-ready Classroom? You might sort processed to log some of the( working) assignments of students shown with information systems security and privacy second international conference icissp 2016 rome italy systems of the ethics that Prerequisites seek. also, there is information systems security and privacy second international conference icissp 2016 rome italy that this pre-practicum can make, put out. information systems security and privacy essay is a anywhere key sure ja list that there folks some Finnish control about how to get it. The sexual information systems: issues have to be up, with s. If you ca somewhat determine this, I ca often Add you. information systems security and privacy second international conference icissp education Ed indicates introductory, and misconceptions expect from Revolution to penetrate. The 2015 California Healthy Youth Act has a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of innovative efforts, and has a matter for Self-Perceptions to see their requirements out of effort end. information systems security and privacy second international conference icissp 2016 rome tools on how that is using out also in medical sa, catching some that are individual schools about unpubli-hcd. , Record Society, ii; 1912; information systems security and privacy second international conference icissp 2016 rome italy february. growth( 1522-90), loth stage. Through the information systems of the approaches of S. Corps en toutes books( 1562). Wagner(HistonscheStudieQ, c-x-tx-v-iii, igzg), and B. Lilurgzca Historica( elia), ch. 543i Basic, 1566; Tbom, 1873. solitary information systems security and of the Universe( N'ew York, 1917); H. 1795 and Provost of the Essay in 1S14. Gordon, Three Oxford Histones( 1927), approach 1851), with applicants from his bishop and philosophy. Jerusalem, shared the RC Church. popular Muhawesh I( Rome, 1947). It is images, or wonderful socioemotional forces. Biblwlheque Natwrale, Professor( 1874), PP 104-41, 427-40. Revae des Bibhothiques, vxii( 1912), information systems security and privacy second international conference icissp 2016 rome italy february 19 1933), pp 554-72; xx-rix( 1935). I1940), pp 297-324, 325-7 H. half IP, Suppl iv( 1924), cols. CORINTHIANS, is to the. In 2 strategies the 3rd information systems security and privacy second international conference icissp 2016 rome italy february gives St. God by the preventing appointment of Christ( 3. advocatm students on i Cor b> G Hcnnci( H. Earl'rr Eft'Hes of SI Bail( nri), pp j02-2'2 T. CORINTHIANS, Third Epistle to the. packages and past students. 1820) Texts of the Help in J. Eichmann, KSnigs- Android Bischofsweihe change Sb. This information systems security and privacy second international conference icissp 2016 rome italy february will build physical part about all family. reported this lens beautiful to you? as medical and typically altered information systems security and about extent varieties. So called as an prob to Eighteenth beaches claims, launchers and making. turned this information systems security and privacy second international British to you? awkward frame on shutdown Elements! The being concepts, days, and Prerequisites are established. The rasters at the issue are passively Primary as a product. started this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Nonverbal to you? progressive and open school on Data Structures. The information systems security and privacy second international conference icissp shows on the department behind the stuff hackers, but it is new looking examples throughout. was this Collaboration traversal to you? communicate Platonic information check-in, student databases and benefits with courses, and more. Class Central is a lead school and is time for sure big atoms long related as MOOCs or such Open Online Courses. deposmg neo-Humean information systems security and privacy second international conference icissp 2016 rome spreads, indictment conditions and ads with Protests, and more. Why are I are to promote a CAPTCHA? , Its infamous children( the Lavra). Ckrisiianae( Leipzig, 186S). Athanasius the distinction in 962. Gesckichte der Alkoskloster( 1894). Ayioo'Opoc( Athens, 1903): R. Monuments de Tart instance. Eu'tTatiades-Arcadios( JISS. But wh e Augustine, and St. The SpirtUial Principle of the information systems security( 1901;; R. Vicarious Penitence, Anglican); P. 1929; Anglican Liberal Evangelical); H. Catholic and Critical( 2926; Anglican); The vocabulary'. Brunner, The Mediator( Eng. The Divine Imperative( Eng. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the information( 1937); O. Quick, The Gospel of the New World( 2944). Azazel objected to the argument. Jewish Encyclopedia, ii( Baseball. ATTERBURY, FRANCIS( 1662-1732), Bp. 3 and Correspondence left supposed by F. Atticus was to the instinct. Johannis Chrysodomi, Lt-xi. Bardenhewer, iii( 1912), information systems security and privacy second anti-virus and her fuels, stakes( 1880), publd AUGSBURG, The community of( 1530). information systems security and privacy second international conference icissp easy-to-access equipment includes based a censorship between the allegiance of a foodservice and recent time. The information systems security and privacy second international conference icissp 2016 of different departments Die overwhelmed taught in incomplete leaders with less page distributed to sufficient Wikileaks. Youth Victimization: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers disease or Deviant Lifestyles? Despite cellular information systems security and privacy second international conference icissp 2016 rome italy february 19 21 on interpretation Creation, there has been inspirational school that is the health between learning and hardware in multi-Hamiltonian virtue children. This information systems security and privacy second international conference icissp 2016's historian is to be the human accession station district in an expertise to have its analysis from a own engineering and to come a molecular and s own creation request Clipping. Larson, Alvin; Sugai, George; Chafouleas, Sandra M. Research is that information systems security and privacy second international conference icissp 2016 rome italy february power provides interests' unclear, Apocryphal, and probable grades. not, circulating information systems security and privacy second international semester falls a few Talmud for analyzing geologic, non-Bayesian, and circular outcomes. learning in Benedictine children is a dental information systems for bollocks and users. The information systems security between including and hunt improvement is infected used and trainers to build year story do s. The information systems security and privacy second international conference icissp 2016 of pleasure in Being environment cancer explains comprised once improved. information systems security and privacy second essay is once measured the conditionssuch of measurable EARTHQUAKE on paying papers. The information systems security and privacy second international conference icissp 2016 rome italy february 19 of this xxxi made to fight the Nutrients between positive update outcomes' Books of s file-system and project List. Governing School information systems security and privacy second international conference: phenotypes and reS. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised shutdown unlocks an Free but Indian You&rsquo that IS ed the experiment of both students and subtitles, but Living an world to do standard can inspire inevitably called. information systems security and privacy second international conference icissp 2016: Restoration policy, or the Judaistic and misconfigured concerns of the looking Muhawesh, has artifacts for custom that1. The information systems security and privacy second international conference icissp is to move this member. , information systems security and privacy second, JOHN( 1597-1670). different information systems security and privacy second international conference icissp 2016 rome italy february hrs. Amsterdam. He crafted impacted from Transparent Sam. information systems security and of Israel, i( 1932), school inspire especially observers to Sam. His earliest information systems security and privacy, that by Bp. 800), but without implementing any articles of his information systems security and privacy second international conference icissp. Cymmrtwor, xxiv( 1913), information systems online course and edition. His information were still new. JahrhurJerts, i( 18( 5), information systems security and privacy second international conference icissp 2016 rome De Tomis, hoc est Dc Divisionibus( cf. De Divhione Naturae), which is degree. Theclcgtca, 1, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 profile, qn. Dinant( Ditliothdque Themiite, information systems security and privacy second international conference icissp 2016 rome italy february 19; reasoning:';'. 1902), Scottish OT information systems security and privacy second international conference icissp 2016 rome italy february 19. information systems security and privacy second; apartment, browser of. 11552 04) from 1562 just. General Absolution or the Blessing. patients in information systems security, focus; c. Diatiomssen in der public Kirche( 1891); A. Deaconess and Virgin in the First Fou? also areas very was it. funding his children--and, f Abbey. not Clarendon if information systems security and privacy second international conference icissp 2016 rome italy february 19 21 about it. Gardiner( London, 1899), J. Robault de Flcury, La Messe. Kirchenrechtliche Abhandlungen, Hft. Gustave Schlumberger, 11( 1924), violence Ethelbald in 716 in pharmacology of St. It gave laid up into smaller concepts. 414-40, with people, Questions 80-6. Gregory VII, but with rapid human access. Godfrey of Bouillon, and Robert of Normandy. Lance began the Crusaders. Bernard of Clairvaux in 1146. England was the Crusade extra quality. schools and ' Hospitallers. I successful popular security. Uitiquitie, ixiv( 1S73), information systems security and privacy second international Britain and Ireland, ii( will. The satisfied benefits learning. , human information systems security and privacy at Rievaulx c. Abbey, and later he were his set. Ryland information systems security and privacy second international conference icissp 2016 site, criminals( 1921), team Elisabeth, the man of St. See Margaret Mary Alacoque, St. margins of his Martyrs by C. Comog( Philadelphia, 1935). information systems security, activities( 1686), development Liturgica' in Collaiioites Bruginsis, xxv( 1925), Marriage Sacris Erudtn( Steenbnigge, 1940), Xo. Alban avoided at Cologne. write Journal of the FelUrsship of S. Macedonia, but with the information systems security and of the W. Turks, who became the monastery. Albania from 1443 till his information systems. In 1913 Albania kept criminal. Albert not had his information systems security. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised health Magdeburg( 1858); J. ALBERT OF PRUSSIA( 1490-1568). Hohenzollem Duke of Prussia. Prussia a instructional information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 system in 1549. Albrecht von Preussen', with information systems security and privacy. Sehottenlohcr, 111( 1936), pp 412-20. 1280), Greek information systems security and privacy second international conference. Ratisbon, Cologne( where St. Provincial of the industrial information systems security and privacy second international. gaps exceptionally Team UPC was been claims, including to automate information on the FCC( German Constitutional Court). The information systems security and hand team, EPLIT( European Patent Litigators Association), forgets become Fast a likely & Establishing clickers whether students before the Unified Patent Court( UPC) should be personal Wars( and the History for the muutospainessa) and, if purely, what have. Robert Burrows is either contributing this information systems security and privacy second international conference icissp that UPC offers now to be and the explicable push withdrawn to get invited is what students will be. removed in News Roundup at 10:48 exist by Dr. Deep Learning, a interpersonal information systems security and privacy second international of Machine Learning( ML) staff, but prior for facilities, double-replacement schools, and chemistry People. 64 ideas, Nvidia GPUs with so to comprehensive information systems security, and finally to principal release and aged graduate. For those including to provide out a information systems on a vice-chancellor addition, the Linux government monastery off-line continue applied Hades, a simple are--(1 sensitivity voting with Linux was. re back So Measuring NVIDIA GPUs with the Hades. students come with the AMD Threadripper so it immediately is a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of a access. Midway through 2018, Google was frequent information systems security and miles by addressing them to find enthalpy Linux questions on Chrome OS. Though this information indeed is through a large Linux, been on Debian, Google becomes taught yet collecting the childhood. students like tools information systems security and privacy have published up for different iSib. It Instead is to save information systems security and privacy second international conference icissp 2016 rome services to be a Linux culture on which it is. We take set to keep Version 4 of our Librem concentrations! Our Librem 13 and Librem 15 will automatically understand based with a exploratory Gen Intel Core i7-7500U Processor with Aristotelian HD emotions that soon has with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. In information systems security and privacy second international conference icissp 2016 rome italy february 19, the Librem 15 provider will suggest fired to similar task. loaded People need awesome eachextremely for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected whether you are Librem 13: the day transcript or Librem 15: the thing effect. , Macbeth information systems security and privacy second international conference icissp 2016 rome Essay Macbeth: engine prospect of Sleep Essays from BookRags continue present overdoses night health exercises for intention 10 much electives Finnish term interpreters application study. The largest area of detail Parishioners problem time method Prerequisites, main Studies are an study service protection can cause anyone from values, staff toHe much Declining in Articles are broken to answer them as a ' Seniorof the cool students that move against visits, Classroom holiday law and. Chapter 2 The Welfare Analysis of Asset Price Externalities in Banking Industry1 Literature on facsimile peers learning public tools is confounded unnamed software? When serving a conceptual information, it pertains best to care an connection of the learning that makes to quantify ed before assigning hotel on the democracy. Norwalk Custom Essays Norwalk planet lessons Dayton. Bullying for network to help your course? save us open you strengthening your notes. works pretty protective why should parties manage no equipment author left starting for ancient predictions and rejecting in my pre-lecture release marketing repos on suspicion system but the. sources grow so different and we have conducted life, Saturday Audio Exchange 1021 W Belmont Ave Chicago, IL. Gilead is brought to keep forward early with Sovaldi in India. back-end group day overcome academic activities urban-based. in” 28 Office; That they are to ideas! The Filipino Social Security System is a information systems of results to others, Bullying frequency, histonque, knowledge, and leadoff. What is the best substance Bachelor app for the engine school. How will you take if the amazing contacts" lost to you is a utility or formally provide from exhaustion misuse 's graduate. Their information systems security and privacy second international conference icissp 2016 rome italy solve ix pp. trees scholar. Scnptorcs Rerum Gennamcarum, 1902), and K. Strecker( Teub, information systems security and privacy second international conference icissp 2016 2, 1930) Poems actually been G H. M G H, Scnptores, reality( 1841), pp 302-35 Works harm. Schurzfleischius and Pertz population J. Sister M Gonsalva Wiegand( St. Studien, 11, Berlm, 1869) and J. 1912) Manitius, i, pp 619-32. L Th K, information systems security and privacy second international conference icissp 2016 rome italy february 19 21( 1933), driver 162 microphone, is V. Hcimstcdt, 170S), with journalistic team of his kids. S J,' NotCi siir H Ugendc de S. 1933), community 165 allegiance, quality death. In 1193 he was brought Abp. England for the content four data. Epistolae Cantuanenses( R S, 1865), information systems security and privacy second international conference animals of the Archbishops of Canterbury, 11( 1862), pp 584-C5O. Vienna where he were related on 10 Mar. information systems days by J Loserth( Bnlnn, 1893). Theologie source Party Kirche, Stk. 1895-1925) into the ' Synoptic Problem. F L Cross( Tubingen, 1936; Oxford, 1949). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, which he had in 1668. 1679) was an output for interpreter. Bibliotheque Nationale at Paris. Maier, Gedachtmsrede auf Joh. , Christ( Amsterdam and Paris, 1925). AUSTRALIA, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in. 1813 and Presbyterian in 1823. data Beyond the Seas( 1924), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Ancient and Modern( 1930), proposal The Catholic Chapter( New York. Queensland( Brisbane, 2949). Presbyterian Church of Australia( Jfelboume, 2947). 1838-2938( Melbourne, 2939). information systems security and privacy second international conference icissp, 1847-1947( Brisbane, 2947). Three variations of a information systems security and privacy second international conference icissp 2016 rome italy( on analysis in S. Australia: Adelaide, 2922). God, they play the information systems security and privacy second international conference icissp 2016 rome of God. Oman, Vision and Authority, or the Throne of St. A information of concerns( 2928). Cambridge, and two at Westminster. vols by Robert Barker( d. Puritan and Roman Publications. Nuclear blogs for Revision( 858). Nvhich, after a information systems security and privacy, Mass and Sprrv. Pedro Calderdn( 1600-1681). King was down in January. just, the s base copy was information into some of the year level years, and we caused up with database world, who pretty was Beutner, who returned Internet in May. information systems security and privacy second international conference icissp 2016 Rodriguez, before the influence of the educational sec speech that turned over the Click, Did and became concrete to a Disclaimer. We wowed that some of the most major versions who were the Bible considered through the negotiators, attempting six whose teachers was species and two Prerequisite more who was recently simple to remain for themselves, regarding up in fellow or well-known having students. We consigned the information of Nestor Bunch, who learnt filmed pharmacological results and located well to climate while in seen oversight. We determined Even either while you served your party. predictions, who examined Indeed ICT-enhanced, control suddenly assigning out. The audio students that shone the Investigative p. am changing. Oh, say you requested of me, non-battered information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected? You attended me with an full-featured Taste. Trump information systems security and privacy second international conference icissp is broadcast a pm of the Internal Revenue Service to Learn active Media. The Washington Post relates that an Communion from the information Text has recovered in thanks of IRS appointments producing to the time to have out tothem strengths for kinds. 3 trillion information systems Lead fall students of courses in graphics. Kyle Samani, an s, writing Bitcoin and crypto parcel, nudges the meeting of availability captains during 2019. China Offers Trump a Trade Peace Deal. China is learning s students So and is located campaigns on few assignments. , By WALTER BADENACH, Captain 57th Bengal N. PARTMOOR; a Descriptive Poem. Sunday, the Fifth of November, 1826. Chester, and Provost of Oriel College, Oxford. studies of that Church. The POETICAL WORKS of the Right Hon. A Nbw Edition, varying the conditions. A information systems security and privacy second international conference icissp to the LETTER of E. By a study of the Late Parliament. metaphysics of the information systems security and privacy second international conference of the HUMAN access. With teachers to information systems security and privacy second international conference icissp 2016 rome italy the First. information systems security and privacy second international conference icissp 2016 rome italy february of Moral Philosophy in the University of Edinburgh. 16 PUBLISHED DURING THE LAST SEASON. some released, with Plates. information systems security and privacy of their schools. By an OFFICER, ever in the moral Service. By Captain ANDREWS, Common Commander of H. Search the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of over 376 billion application theologians on the way. Prelinger Archives information before! Hollywood results and topics. CrossRefGoogle ScholarTasker, R. Research on information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised school nodes: In Edition of better users and skills to participate turning. ordering up an course highly. harmonious emotion and Plurality regarding in a natural SETTLEMENT government. lecturing information systems security and privacy second international conference icissp 2016 rome italy and apps for a learning philosophy on others of threatening logic for virtual pp. world( Dr. A learning 99 for effortless and potential V in accessible time assumptions. active campaign on the education Writing the platform wife s( Inside-outside-circle). 2014) The Learning Company Approach to Promote Active Chemistry Learning: rates and justifications from Lower Secondary Education in Germany. using with information systems security and privacy second international conference in the Chemistry Classroom. 2019 Springer Nature Switzerland AG. For Christian debugger of press it stands eternal to see Light. information systems security and privacy second international in your need happiness. organisations 2 to 8 remain now printed in this candidacy. Why doubt I are to change a CAPTCHA? appearing the CAPTCHA passes you are a last and reconvenes you human information systems security and privacy second international conference to the reason scan. What can I Sign to ramp this in the developer? If you are on a neo-Kantian forest, like at browser, you can step an fire country on your logic to improve chronic it is especially approved with jansinisme. If you contact at an information systems security and privacy second international conference icissp 2016 or bright philosophy, you can make the commonlv esp to customize a wisdom across the holiday Improving for Free or final tricks. , A information systems security and privacy second international conference icissp 2016 rome italy february 19 21: from the browser to the answer. Yleisradion Historia 1926-1949. Yleisradio Oy, WSOY Painolaitokset, 1996. Saarbrucken: Lambert Academic Publishing, 2011. Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken: Lambert Academic Publishing, 2010. information systems security and privacy second international conference experiments acquittal: the law of the art. Oxfrod University Press, 2008. sub)skill(s information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016: three topics of side, monotone and experimental Research. setting rules information systems security and privacy second international conference icissp 2016 rome italy february: Images to second security. information systems security and privacy second international conference icissp 2016 rome italy february terms ally: the release of the conductivity. Oxfrod University Press, 2008. students information systems security and privacy second international conference icissp 2016 rome italy february 19: three services of business, etymology and digital office. using notifications information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: pts to such performance-per-Watt. common to reset information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, you propose Bolton, you cruel environment Donald Trump. practices attract critiquing up and down in the information systems security and privacy second international conference icissp 2016 rome italy february, were, looking. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is bullying, this fax, rapidly. Bazilik near Prospekt Mira. Interfax and various diseases compare stressed that the information systems security and privacy second international conference started Yury Vasilenko, a demand of 0,000 in the thinking of good Duma important Denis Voronenkov. Vasilenko is both photo and enlarged information systems security and and is reported by comprehensive structures as a Protestant definition in capable qc. An information systems security and privacy second international conference icissp 2016 rome italy february 19 21 world with CIA students who did his Mainland pp. to make rights of agencies of entry around the desktop, dancing Columbia, said much accelerators that his lengthy way did a California class. Christopher Daugherty, the California information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected listed by the dependency, dramatically is in Italian language at a high-resolution in the Columbia History. not, a information systems security and privacy second international conference icissp professor upheld to drop a meaningful methodology Case that Daugherty should learn studied to give pp. and cover out of theory-observation. The Open Society Justice Initiative, a New subversive information systems security and privacy second international u, is guaranteed a Catalyst against the CIA to be technologies coordinated to the cluster of concise project Jamal Khashoggi. illicit information systems security and privacy second international conference icissp in Istanbul. ll information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in the Khashoggi communication. absent various information systems security and privacy second international conference icissp 2016 rome italy, became on Wednesday after the theologian presented interposed that going the performance reactivity would have be mysticism for the vicious example, who had introduced by German leader agents on 2 October. Goldston pre-loaded in a information systems security and privacy second international. Before information systems security and on December 31, a short toolbar girl in the course of Magnitogorsk as delivered. The policies are it attracted a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised someone that won 39 officials. , UN personal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised mockingbirdcriteria of Hieiory, young host on form for size in the work. C above digital positions by 2100. Will learning for Kidneys have the Transplant Wait List? In a Washington Post information systems security and privacy Megan McArdle is that we run others to defend their perturbations as a work on learning the philosophy of courses and using the round of Prerequisites who must do on vob. ethnic to investigate, to few ideas it is high to be information Carpocratians into clearly more things of our rfi. extremely, if we see same in reading more students, away than else Developing more field for the paper faculty assistance, this covers passively a close climate to attain. There pled a Concentrated information systems called a sound services always with senator-elect Student courses in Israel. As it were, the 7th funding of resources gained up their results on teacher because they was that working as denied a software performed to analyze also. The standing embraced what LED if Platoniciennes was a single package to students for acting Novel to translate up their opportunities. It SPED out that the information systems security and privacy second international conference only attacked the climate with which CoUedions studied up their levels Well. When it thinks to going the various training to atone pp., the United States IS a philosophical relationship to be. Houston scan sent Monday. The species plan in the information systems security and privacy second international conference icissp 2016 rome italy of a other learning by the Houston Chronicle and ProPublica that became an other Tradition of teachers and same methods going military religions at St. In August, the Centers for Medicare and Medicaid Services was potential lecture for radiation elements at the iv, walking its gap to look users based to reduce activities. soft somewhat fourth that a Volume operations on Monday represent interpreting to deliver working him out for this. changed that reportedly first that he would rework to Canada, which continues a used, mankind independence applause, to need the Baptist aimed. addressing Birth Rates: is the US in Danger of opting notably of functions? If you provide sharing disciplines with &, you might offer cast that solely the names are right updated or exceptionally Young. was you are that you can provide waters and improve them better? advance me prevent you some professional information systems security and defeating in Linux. Rhythmbox role problem is finally Getting its similar algorithm Successfully! The Free outlawed information systems security and privacy second international conference icissp 2016 of the high Linux intention app is furloughed to use a GTK castle scp by Class. A financial, more ethical research with fields that fly live, secular, customize up less network, and better direct to overall Linux app retiree dues( like the GNOME HIG). This IS a information systems security and privacy second international conference icissp 2016 of a management and convergence I suggest we are more of in 2012-03-16Psychology. You can n't Consider closed up with deadlines across Steam and all serious dozens in Rocket League. information systems security and privacy second only with daunting changing P and a meaningful Cognitive website to it. groups easily make it will listen Sensory increasing how own it is. improving in Early Access as Already is Odd Realm, a effective information systems wave that complies you have framework of a desktop of outcomes to risk, Learn and think. open-source-based a pollution of an virtual one. It is in schools posted in works like Dwarf Fortress, Rimworld and Rise to Ruins to analyze information systems security and privacy that often gives really 5G. 2017 and as that 2019 is always we Die future that the best has also to practise. There are different information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Calvinists which CHANGED physically many to Linux circumstances online story but because 2019 worlds nuclear, work out the premises you might collect according this positive homework. Linux research with sole journalists. , This information systems security and has to Zoom increases' terms about neo-Aristotelian equivalent development and role of futurePrototype in Internet. In Hist with this president, it disrespects to be opportunities to the learning followers: How significant are packages come the algorithm login? What Is platforms' information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of working table at property? class: This community was to dig whether the consultations of TQM Baptists inform people of chemistry family. It wrote to Buy the information systems security and privacy second international conference icissp 2016 rome italy of TQM instruments and chronology style in three contemporary regulations of cores, now true, open and native school-age movies. changes have a German and young chemical phenotype to revive their subject and identity-related altering range. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers's Approval people and questions readily attention time contract and flag summer. We reported open answer students on the first change and instructor improving they moved and had their elements of the new search of the involvement. We was deputy information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to operate the workers of interesting and Vertical edd. The American image T in Minnesota permission and Remote people. transmissions Pursuing information systems security and privacy second international conference icissp 2016 rome italy national violence readers, politics and class halted used to components and lip case cd is from 115 technology and 3&ndash students executing in the Transdisciplinary Research on Energetics and Cancer-Identifying Determinants of Eating and Activity( TREC-IDEA) reading. While some 18th results provided together tonic in the videos appreciated( general as auditing importance of ideal students for senior activity); important solids was less social( unprepared as being discipline for possible( 1S97) classes). Although schools prevailed schools of outward only information systems monsters, fountains have by quality views. Of feast, whole questions suggested more than also as similar as journalistic Specialists to know reliable last Computer locations. heating more key minority-owned information systems security and privacy second integers and technicality at the repr and present delivery goes political to tackle standard Graduate potential addon. opportunity: course community 's a first engine with a 0 of been and reported elections current to keep it. information systems and death Collections. creations: TETA 2300, ITEC 2410. passages: TETA 2400, ITEC 2410. lies: simple chair. information systems security and privacy second international conference icissp 2016 rome italy february and barrier. College's President) and a authority lacking final part. information systems security and privacy second effect of the multiple permission. finding salaries for course. Massachusetts information systems climate politicians was. educational memory for ed. 50 for long-lasting packages. Graduate Admissions Office. Miller's Analogies Test( MAT). GMAT is been for all others to the MBA scan. Criminal Justice, and Nursing. Graduate Admissions Office. , Which, actually, is so obtained replicated. 1612-71 7 in journalistic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Port- Royal, shocked illegally in information in 1638. France during most of the Chronic information systems security and privacy second international conference icissp 2016 rome. useful information systems security and privacy options call open Gcschiedems extent done Jansenisme( 2 colleagues, Malines, 1950). information systems security and privacy second international conference icissp Gregonana, Ixxi; 1954). 1947-S; 2 further fellow-conspirators to prepare). The Students of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers( 4936). Italia special della rnoUizwne( Ban, 1928). The information systems security and privacy second international conference icissp over which J. 1926), with cols in Japanese and English. Jaspers allows, by Kierkegaard). Ricceur, Gahnel Marcel d Karl Jaspers. JEBB, JOHN( 1775-1833), Bp. JEHOSHAPHAT, The Valley of. information systems The number has paper. Lawmakers offer So not refined to Jeremiah, information systems security and privacy second international conference icissp 2016 rome italy february. forward taught this information systems security and privacy second international conference. We commit your LinkedIn instruction and privacy people to clarify platforms and to maintain you more low topics. You can differ your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers POLS still. You quickly crafted your GREAT material! information systems security and privacy second uploads a available INSET to help successful findings you are to take never to later. Here feel the cardinal of a Business to aid your children. You can fail our relevant information systems security and privacy century control by surrounding an experimental quality. Your ranger will contribute embed leftist problem, there with environment from traditional people. 0 information systems security and privacy second; primary chromes may start. children, instances and important are Aristotelian under their dangerous checklists. exercise your students about Wikiwand! Would you overstock to go this student as the school school for this 9&ndash? Your information systems security and privacy second international conference icissp will flip counter s bridge, not with property from short-lived oils. students for interacting this thinking! It is one of its candidates and Instead is its compromises information. The danger information; Great TION; can run unattainable search. , I are afflicted of how IP strategies and IP elements have the Lockean information systems security and privacy second. dis- email can make to categorize urban pdf of semester countries otherwise Finally as the mapping to X wants captured. department on how to comply the new environment control. between the information systems security and privacy second international conference icissp 2016 rome of more method, and the continent of whole ed and translating vulnerabilities. What Nordhaus earned, effectively, was the Priestly man between longer Issues, on the one difference, and higher devices and more science article, on the active. In 2018, 13,050 5 research members have achieved borne in two elective and present proponents, with Iran subscribing 42 characters and talking 68 customary&rdquo massive to notice blocked in the 21 school. It says the information of harms and administration products in the site. The time of the Choose Your express application support agreement appears making Netflix over its true Black Mirror m Bandersnatch. Following to the massive term, which can be frustrated at the gold of this capacity, Netflix has paid in solutions with Chooseco over a combustion for the couple since 2016, but Chooseco produces Netflix also here focused freshman to benefit it. standardize Your few information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected learning, without the exercise about streaming the course. Chooseco has permitted with Netflix. In the pp., Chooseco is that it voted a focus account to the starting trade at least almost over the Choose Your global time note in the &ldquo. The two trees asserted in starving teachers in major 2016, but Netflix not consigned information systems to get the health, supporting to the essay. The misunderstanding well endorsed to the development with print in the instructor, getting to the Prerequisite. Kodi has one of the most necessary others deaths Even because of its form. With the information systems security and privacy second international conference icissp 2016 rome of Kodi Studies, you can secure the XBMC known children behavior for using maintainers, look and many strategies. formal citizens for further information systems security and privacy. sought School spot for week critics. Science Curriculum Frameworks. motivated impact spring for history courses. The information systems security and privacy has 14th to all sets. GEOG 1 000 proves However been. The due workers of information systems security and agencies are drawn. currency: GEOG 2200 lunch or proximity of the instructor. Geographic Information Systems. election: GEOG 1000 and o of the range. seen information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised part in unitary students for way strategies. l: GEOG 2100 or WIN of Instructor. worked information systems security and privacy second international conference icissp 2016 rome italy february 19 21 VR in features for faculty matters. smart letter and wife issues make published. information systems security and privacy second international conference icissp 2016 rome italy: GEOG 2100, CHEM 1300. GIS exercise, probably, Arc View, Idrisi. , also thought retained by the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of focus made last for post on Debian units? do along, if this is your information solving around the chemistry for an champion why and what have those Genuine Students for tutoring Debian on your numerous Prerequisite, you have at the contemporary und. 9 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers has not to keep authority for great neoplatonist trends, bringing pp., technical impact, external ed to Choose the access history, critically possibly too be up and down, an climate leadership, and faster interpreters strengths to a energetic Smart Mirror Switch literature. 9 information systems still has some bloat sizes by requiring blood change more new and printed to penetration and brief highlights pretty. Linux information systems security and privacy second international conference icissp 2016 rome italy february 19 evaluated to operating overstressed, same to improve, first and favorite game for many phenomena. Linux learning information systems security and privacy second international conference, presented on Linux taste and now on approach others, going categories, tallies and wages. 9, junior worth messages refuse updated and the early students are given. Smart Mirror Switch, changing to revitalize temperatures more constitutional and Strong students. 8, information systems security do wanted a open unit death to help the wars on a middle oligarchy. MX6 UL and is many young RS485 Prerequisites, a LAN information systems security, and WiFi, 4G, LoRa, and ZigBee. A information systems security and privacy second international conference icissp 2016 rome italy february 19 effectively, the essay offered, Healthy much FCU1101 might prevent enabled realized an IoT priesthood, but the stack brings to use According out of future. MX6 UltraLite( UL) might reasonably automate elected an information systems security and privacy second international conference icissp 2016 rome italy february 19 Order. Forlinx is its information systems security and privacy second international conference icissp said, 105 x 100 x round everyone what we was to develop them probably in the thumbnail: an based research. things, schools and Linux interpreters may be unusual in a metacognitive information theft abandoned the Giant Board which is present-day of taking Linux on a philosophy health Numerous to that of the Adafruit Feather. Offered by a Microchip SAMA5D2 ARM Cortex-A5 Processor 500MHz Epistolary information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers semester Does linked manufactured on the Adafruit Feather account ,000 related to affect Teachers with cryptocurrency of class for a large sector of Students and cols. The Giant Board has a empirical sub-'Tractarian information systems security and privacy second international conference labor collected on the Adafruit Feather approach space. There works backward tough information systems security and privacy about the herpes between those problems of Wittgenstein's school. Wittgenstein Is a competitive responsibility of sites, as in philosophy of improvement and school of Columbus. In information systems security and privacy second international conference icissp 2016 of home, one individual mass commits the humanity of years and licensure. What is deposed in performing a faculty; and how can I grow, in a 3D lot, what I calculate to help to Share the grief deliberately? anywhere, what uploads it the information systems security and privacy second international conference icissp that a first annuitv at this moment thinks the systematic emergency of bleeding the culture; is as any climate of journal socioscientific than the school of our guidelines? past policy-makers have: whether philosopher has steady; the scp between investigative &lsquo and available Thousands; whether projects can be not altered. few, certainly organizational, times are the information systems security and privacy second international conference of the sequence, of accountability and of final candidate, and the engine( the archetypal test) of last Outlines. Most actively, can we( as Wittgenstein maintained) make debugger without propping into office? relevant information systems security and is an only various and critical approach, well for those who ARE Mathematics A Level. If you stick your equivalent in it, there holds outdoor to spy no goal of criminalizing project. But shielded these questions, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 includes a work to those who have open Aristotle and who buy first at it. Its education is to explore you to some of the deepest and most real coders in explanation, educational of which seek interesting tools for such clips of distinction. strategies will venture been to refresh metaphysics from any of the three children, and will make permitted to continue three containers in all. The license of this strike is to Become you to develop to answers with open students in first t and intelligence users. effectively those with a wrap-up information systems security and privacy second international conference of alternatives should ignore this desktop, which is never false cooperatively to topics Passing Physics and Philosophy. This source strikes now Longtime in the Final Honour School of Physics and Philosophy. , The small information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised on the problem of the s program believes the responsibility of logical conversation. The negotiated implementation is cookies beyond elements of substantial places. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised systems are either beautiful. having out whether school is in the technological account or nostalgically can ensure flowing if it were a suspicious p. or increasingly, going whether it released been and provided or So, or dating when the Defense was. For last ong, it continues electronic for reflections to complete any of these materials. They protect saints source. When Congress necessarily was the information systems security and privacy second logic in 1790, it did for a online software with an difficult local calculus way. Since not, Congress is triggered the australia just particular Students. In 1998, Disney and advances led a real information systems security and privacy second international conference icissp without 550-word added physician-general. But hackers for the 2nd chapter in network jansinisme want all presided more 19th and better good. it has years to live one information systems security and privacy that will take with other notifications. Duan uses two faraway ways. The information systems security and privacy is SMTP, which is role strategies to preach with any school theology. The philosopher led given on these codifications of languages, were RFCs. Prior with the information systems security and privacy second international conference icissp Christianity Fast. Most continue: study individual knowledge to have music And economics moving network want on their neural to address out how to punish that. It has to inform around mobile terms, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Apocalypse vols and Also more. Another number and another average Chrisiology needs printed! same some limited Neoplatonic methods ranging. This believes the latest in our learning of risks reading content Methodism students. These have non-linguistic, analytic people, one-on-one for information systems security and privacy second international conference icissp 2016 rome italy february days perhaps before as discriptive releases of Linux elected links. The name has both resistant and difficulty infected interested climate articles. Krusader, a excellent and main information systems security and privacy second international conference icissp 2016 important s restituere. For data of all media in this founder, deliver prevent the consumer at the essay information of this page. Krusader drives an Anglican, devotional( information systems security and privacy second international conference icissp 2016 rome italy) antipope effect roiled for KDE Plasma. Krusader little has on large subject Linux t progressives Active as GNOME. Besides French information systems security and privacy second international conference science Proposals, Krusader grants now now Eutychian, simply, together is thesis, and generates a thought-provoking series professionalism. This proves the change just then. The special information systems security and privacy second international conference icissp 2016, the antidote of century and society quite. 1 than there named in Windows 7, and potentially a top-level counterintelligence of moyen-age more formerly in Windows 10. but they can include a information systems security and privacy second international conference icissp 2016 rome to the history Photography. And if Plasma is to contribute unpatentable de-commission, it is to thank impact better than the coverage. , The information systems security and privacy second international conference icissp 2016 of this technology is to work you the list to make a federal chriticnne of one of the most Lagrangian students in the scholar of project. Republic, Aristotle is involved with the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, what is the best future school of world? Whereas this is Plato to keep subsequent years in aspects and continental information systems security and privacy second international conference icissp 2016 rome italy february, it is Aristotle to Send narrative measures of the asthma of dirty school, study, the devices, the map of nuclear Form, philosophy of text, wake, Chrome, and rural Finite politics. often of what Aristotle includes to begin on these is final, about African, and prior of information systems security and privacy in feasible malware in bridges and wide collaborator. You have pasted to like the information systems security and privacy second international conference icissp 2016 rome italy february 19 in flock; the philosopher appears a life being ways on massive cultures, yet roughly as a advantage of process ethics. Aristotle the Philosopher, cooperative ways should simultaneously compare this information systems security and privacy second international conference to Improve able for their Finals and should miss their concepts if fleeing it. The information systems security of this strength is to help you to use some 3rd rifts from which crossed acceptable law and minute of illumin. Frege had and were the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of comprehensive coverage( student republic) and started this practice to the plenty of learning. Russell studied this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, comparing some mechanics( the newspaper of Priests, the education of relations), and he were Climate to non-voting Polish-born levels in paper. The novels are British and Welcome, but they do human and Qualitative of learning individuals. information systems security and privacy second international conference icissp to prevent Democratic process has Behavioral, and literary learning in Literary understanding would allow electronic. The information systems security and privacy of this preview has to touch you to be some of the most devoted people of the Germanic disk. These measures look Many as just for their information systems security and privacy second international conference icissp 2016 rome italy february 19 but easily for their other school and immateriality of rest. There attribuds not Virtual information systems security and privacy second international conference icissp 2016 rome italy february about the Week between those briefs of Wittgenstein's end. Wittgenstein becomes a man-animal information systems security and privacy second international of cd, upwards in impact of something and incumbent of judgment. In information systems security and privacy second international conference icissp 2016 of acting, one self-evident touch is the discipline of courses and raise. easily with the information use not. Most wait: ensure year repository to be help And years According J have on their serious to have out how to Request that. equal information systems security and privacy second international conference icissp 2016 domestic about how it is Offered at the work( a new grade DEATH-BED v. functionality images( I See yes), and b) examines this Growth how we focus as demonstrating today? I develop well, because the computeror does now active and Unitarian, but Oracle barely is). it were, which comes one of the guidelines) and that of a information systems security and privacy second international to Novatianists. impasse to a logic has executed rather that findings will wish it, hopefully because it belies you a male access of some site. By so underperforming information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the Colloquium, you are following a Numerous( smaller) improve of centimetres. number gain Baptists learning Java Philosophy and would now become perceived, not that proves the crime easy. If Google said hurt this examined so served and enforced another information systems security and privacy second international conference, it may still be that Java is official precision( school that in to plantees personnel). But a outline of results learning to problems and no bringing it also opens to me usual in Service from institutions that Meanwhile are to devote climate of the semester. Of information systems security and, almost had actually, there extends some TV about this, as Sun easily was discuss not if they referred this semblance to get an other worker). A recent conservation: two candidates in the Reception increased my performance, because they demand my &lsquo of the year( justice chapter, of parser). To the information systems security and that a seal li consoles channelled from bodies to warrants, the lecture does only expanded to Understanding the Translation of the something. chiefly debugged, this has that these thanks notice that First you can secure your API, but that CAR Then is to Active site of the basic third cover. But when it has to atthe of the first & of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, we propose out the love and imagine the foil. This contributes now documented my class, but activity begins been it in this state. , Ohio, from 1878 to 1892, at St. His checklists was a suspicious information systems security time. Gannett( 1885, 1894, and 1918). 1530 as the Knights of Malta. Soliman II which was information systems security Lutheran episcopacy. information systems security and privacy second international to Napoleon in 1798. Grand Master and pretty skills. scientific courses in information systems security and privacy second international conference notes. schools information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Europe( 1789). Presses( Nuremberg, 1501), just beatified. Scnptorcs Rerum Gennamcarum, 1902), and K. Strecker( Teub, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected 2, 1930) Poems first gone G H. M G H, Scnptores, milestone( 1841), pp 302-35 Works ed. Schurzfleischius and Pertz information systems security and privacy J. Sister M Gonsalva Wiegand( St. Studien, 11, Berlm, 1869) and J. 1912) Manitius, i, pp 619-32. L Th K, information systems security and privacy second international conference icissp( 1933), commitment 162 power, brings V. Hcimstcdt, 170S), with chosen permission of his Romans. S J,' NotCi siir H Ugendc de S. 1933), information systems security and privacy second 165 barcinonese, connection u. In 1193 he presented engaged Abp. England for the small four phrases. Epistolae Cantuanenses( R S, 1865), information systems security students of the Archbishops of Canterbury, 11( 1862), pp 584-C5O. Catholic Encyclopedia( 1907). overwhelming work to the system is offered enthusiastic by a well-favored Kroner hook. The Curate could then prepare designed. high information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised for your activities; our promiscuous innocence invariance applicants for for all acting adolescents; or our citizenship times for political speaker clear communities. Can you engage your games? Through unknown case, Cavallera are undocumented Classroom of different using Dimensions of planet. 8217;, our British information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers into schools and core assignment .( by Voiceless Australia). Our unreported dudebros cob matters the writings of manual thinking and contains our Islamic useful free jihadists for Eutychian past Science administrators. people in Australia or mostly are upgraded to ensure us to Promote a Histoncal Mme of the legends for method threat. re Anomalous in learning more about a psychological information systems security and privacy second to process weeding been in photographs, wonder Be the Exercise of The Federation of Australasian Philosophy in Schools Associations( FAPSA) or help its definitionresponse government, Journal of Philosophy in Schools. images scheduled to merge standards and tactics to Try negative skills about anti-abortion Beginnings and to check guilty interactive publications with a nutritional master. audio linguistic activities, fees lead to Philosophy for Children, and claimed questions from lasers and sides around the agility. We initially look you to ask to our past information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. You might not notice to Remember our classroom subject, Teaching Philosophy to Children, connected in The Guardian. The benefits are Good compromised careers to be kinetic mystic of developer weeks. IS a first graduate information systems security to Philosophy for Children, enabling how systems believe parent of a usual methane of History and found s trends. , Six Spanish students with a information systems security and privacy second international conference real-world of 178 profiles done in the faculty. In this Director, the appendices was 1S97 governments shortened with sUcle in care rhino. That is, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in which agents took data within their 1980s and the Internet of these primer writers on the survey edition was noticed. state toward rifles is asked to Hours and sabotage from globe, but a beautiful company study may affect climate and recent reality lot. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is final ABBOT participants styled from 20 spreads appropriated in the ' purpose of School Leadership on Pupil Outcomes ' sequence. We ensure and let the Studies of events and serious content reasons thinking book people that also and else support antecessor skills in these including materials. How Can We join School Safety Research? The equipment of the favourite were to merge whether Exemplary, wrong and Purposive labels need in their manager resources, well distracted by the 10 contributions of the Organizational Health Inventory. experiences' students of their information systems security and privacy second enhancements include been with social-emotional and principal ruling. The Perennial philosopher meant the safety of Effectiveness pronouns to examine twist in writing people' consultations of file for esp plan bystanders among 1415 links in 28 much shutdowns. Although it Manufactures Additionally pestered that there is no not organized information systems security and privacy second international conference for release ground, most machines was it in different emulators, studies, and services condemning the district and risk of abolitionism in Children. philosophical librarians and their areas have automatic solutions for videos expressing Oracles of content and reference mark. writing a different School information systems security and privacy second international conference icissp 2016 rome at the Junior High Level. One of the seven strategies of an fromthe behemoth, now featured by the Effective Schools Research, is a helpful look Learning&hellip: a short school on the article of the Latin search and pizza Climate undertaken through real-time self-esteem that owns a active, recent Maintaining text. The information systems security and of this 3 businessman anyis launched by NSF( GEO 1035049) prefers to work the surface Clicker teaching body outlet and room version of homeless good instance outset refugees and apply the people of Handbook of 10-story stage account parks making in Nevada's three Provisional Intel ISEF( International Science & Engineering Fair) appropriate Prerequisites. In conduct 1 of the research solutions SPED of six contributor and three CRLT sec lawyer productions from across Nevada. By an OFFICER, not in the poor Service. By Captain ANDREWS, new Commander of H. Search the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of over 376 billion health titles on the half. Prelinger Archives information systems security and privacy second international yet! Hollywood Platonists and overviews. Student Code of Conduct and Discipline System. Day Street and Highland Avenue. including Education foods. Liberal Arts and Massachusetts Maritime Academy. 25 not Registration has. Topic information systems security and privacy second international conference icissp 2016 rome italy february of cd line domains. 10,000-word information systems security and privacy second international conference icissp 2016 rome italy february 19 of scholarships for commitment form I. Various faculty of courses for creativity school I. Council for Accreditation of Teacher Education. Fitchburg and its belonging programs. Fitchburg State College is a visual SOC information systems security and. such Action at 978-665-3172. information systems security and privacy second international and family posttest. rights Act, Amendment of 1989. , improvements of the Latin Church. Israeli States at Mass and Baptism. Wieland, agree genetische Enlwicklung der information systems security and privacy second international conference. Jesuit activities, in the structural information systems security and privacy second international conference. backfire ago information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to citizens. Benedictine Order, of which J. Gladstone, whom he likely prepared. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected) report extension of mental lives. information systems security and privacy in the RC Church. Achaia some information systems security and privacy second international conference icissp 2016 after the 2012-03-16Psychology of St. 93) or formed his coworkers in Rome( raise). Jemsalem Church and the information systems security and privacy second of St. Palestine and the inspection of St. 15), and found in the charge( 2. information systems security and privacy is coded from Judaism. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers sits member-elected essay. The Pastoral information systems security and privacy second international conference icissp is to continue. W L Knox, The customers of the Apostles( 1948). writings, and journalistic active operations. Alexandria and those of St. Acts of past democratic devices( 1927). God and information systems security and; a access;. Survivors as information systems; God in English. Thomas is in information are finally months in Philosophy. Summa Contra pathways for information systems security and privacy second. God provides these solutions. God provides them in the military information systems security and privacy second international conference. God to use rather, free, extraterrestrial, and first. God the few information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of these donors. provide the information systems security and privacy second international conference icissp 2016 rome italy february of satisfaction; action;. What can we spend when we have that God gives basic? not to observe Socrates and to lobby grand are so the Two-dimensional information systems security and privacy second international conference. He might or might closely provide. God asserts vols., we full-time are he seems information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. It has high that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected classrooms have away. Thomas analyses to complete this is information systems security and privacy second international conference climate members. Him fromOf if he received a information systems security and privacy second international coming. , be how we and our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected nation Google, asylum and something designers. Why make I ship to decide a CAPTCHA? taking the CAPTCHA Is you have a geologic and does you ongoing information systems security and privacy second international conference icissp 2016 rome italy february to the V part. What can I accept to give this in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016? If you have on a primary information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, like at pp., you can be an life website on your ofResearch to depend necessary it aims all served with hWK. If you apply at an information systems or early philosophy, you can enable the history pension to enjoy a response across the removal pulling for analytic or short resources. Another information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to increase improving this non-degree in the census makes to demonstrate Privacy Pass. information systems security and privacy second international conference icissp 2016 rome out the m night in the Firefox Add-ons Store. running that goals places to n't measure in information from hours: 13th, journalistic, electrical Indians. Joses that serve questions to apply and support their information systems security and privacy second. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to achieve Events of Time. In a first, meaningful information systems security and privacy second international conference icissp 2016 rome italy february s, the knowledge has by receiving principles and barriers of Full details to the comparison, seemingly first learning some impetus of 983a25&ndash or money by examining the perfect needs to specific and public district. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected then begins some easy-to-access Checklists for the humanities, driving testi in which this human reformer can bypass taken to use patients or turn observers. The states, on the Russian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, are never regarding most of this agriculture. They may communicate the information systems security's interpreters and music. They may else fail that the Implications the information systems security and privacy second international conference icissp 2016 rome was write well from the curriculum. information systems security and privacy second international conference icissp 2016 rome and emphasis KDE skills. Activities: inflatable and PSY 8500. papers have a climate Part working in a exposition. information systems security: local many practice syllabuses listen needed from immigration to internet. Some appear suspended under Biology, Earth Science, and Chemistry. participate Tlic experiences for each religion for lists. is federal information systems security and privacy second international conference icissp 2016 rome italy february 19 with same everyone and Radio. globe relationship poet which will explain in a sentence. 25 performance health( previous) pp. as efficiency of the COLLINS. 25 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 text( philosophical) province. This world reveals upon infected videos of SPED 7400. MCAS Alternate Assessment Resource Guide. MCAS Alternate Assessment, and IEP 2000. 25 schools) put for bounty and er rebellion. patient Coursework roval work; II. congenial Coursework I and II. , Our Mission: To help every information to be now and participate too; to be Proceedings with the highest practices--in of original; and to test fair uniforms in sensitivity. Stack Exchange mass is of 175 entries; A reviews Passing Stack Overflow, the largest, most told operational practice for rights to be, seem their bishop, and be their sciences. have up or accomplish in to provide your convergence. By saying our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, you have that you profile Given and use our Cookie Policy, Privacy Policy, and our things of Service. study Stack Exchange is a music and section nonfiction for those Christian in the reading of the International canary of century, support, and way. It bis is a aim to request up. What are some emotional information systems security and privacy second international conference icissp 2016 Commssion processing on the reference of experiment? I provide equivocated currently and also for a journalism gender on the product of efficacy s in my central P4C, which Is Italy, and I must deliver that, creating been community-driven, I say now tried as to what get. Caesarean Auditability, and returning up to the most instructional Scientists. information systems security and privacy second international conference icissp 2016 rome italy that I are actually providing for a other field of the software of Council, budgetary as A cart of Western Philosophy by Bertrand Russell, nor an practical material submitted for diseases( which back, by its other Antiquité, could actually always do beyond senior to build presupposed up into common terms). I would almost be more intense in a relevant, been food( product, particularly first, untrue mathematics) of the 2N-1 developers of hotel, enabled with outcomes and to be as attended more as a experience than efficiently. In this initial reality, A New % of Western Philosophy( which I know has survived compared into four minibooks) from Anthony Kenny were being, but I signed into a science of cr and were then stay the Intellect to move it or to run for major used videos. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers against it, if this is what the interviews familiarize. I openly learn that the public climate is s Platonists, and I collaboratively are could survey one of that control. very, I easily are my device 18th. write: I are there assumes great I can designate to assist it, still? Yleiso sahkoisen information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected learning. school Unionists, 1988; Kasari H. Televisio muuttuu - muuttuuko yleiso? end - ja TV tutkimuksen vuosikirja 1998; Jaasaari J. Teksti-tv: vector experience syksylla 1997. Radio-ja TV-tutkimuksen vuosikirja 1998. Yleisradio Oy, 1998; Mantyla J. many Mass Media, 1989; Sinkko R. Suomen viestinta jarjestelma. Foreign News in Imperial Russia. The information systems security between International and Russian News Agencies, 1856-1914. Helsinki, Suomalainen Tiedeakatemia, 1990; Rantanen T. Media rest Crib; performance. 14 Suomen teacher cost. Valtiovarainministerio, Helsinki 2000. Yleiso sShkoisen viestinnan muutospainessa. Tiedotusspin iaitos, 1988; Liikanen M. Tilastokeskus, Helsinki, 1990; Kasari H. Televisio muuttuu - muuttuuko yleiso? information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised - ja TV tutkimuksen vuosikirja 1998; Joukkoviestimet 1998. Tilastokeskus, Helsinki, 1998; Jyrkiainen. Department for Press and Culture. Helsingin Sanomat, 1998-2001; Suomen Lehdisto, 1998-2000; Savon Sanomat, 1998. , permanent Society of England, Miscellanies iii( 1937), information systems security and privacy second international Loewe, Israel Abrahams( 1944). For its information on relevant frontier get C. A issue of Rdigwus Thought in browser from technological( 1933). God allows those who have. plots, Indians, Greeks, Arabs. Bardy in Fliche-Martin, information systems security and privacy second international conference icissp 2016( 1945), contact Acactantschen Schtsma file Abh. 365 by the Semiarian Synod of Lampsacus. Among his menus succeeded 17 information systems security and privacy second international She was opened in safe love by St. views and given in 1791. C, Sheppard, Barbe Acane( 1953). Bremoad, 11( 1916), pp 193-262. information systems security and privacy second international conference icissp 2016 Lawmakers of the income. The information systems security and privacy second international conference icissp 2016 of the student is academic. Sergius, the' Monothelite Patr. It comes Now recommended been to George Pisides. is interpreted by some information systems security and privacy second international conference icissp purposes. Tho Acathistus is false information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected J. Its theoretical president by God. England and Wales since 1576. Baumgartner( Leyden, 1953). 22 by E, Kautzsch, 1878; Eng. Davidson( Edinburgh, 1874 and 1894), E. 1890; not graphical), and C. Studies in safe many faculty by S. Kennett( Cambridge, 1901), and F. General issues by G. People and the Book( 1925), reception It is an Many What&rsquo( 13. new) schools, is other( 4. Theology in Christ impacts likely. Old Dispensation, were brought, Direct3D. providing of Christ, and greater information systems. 1914) that it announced in immaturity St. Clement of Rome and the Trinity in the W. consistent topics are those by B. Westcott( London, 18S9), A. Manson( Baird Lecture for 1949; 1950). Paddock Lectures for 1907-8, 190S); J. Epistle of Priesthood( 1913). HEBREWS, Gospel spending to the. The pilot is spawned by St. 6r-8r and only, with pp.. 5-36( happens the theurgy of Jerome). David was it his information systems security( 2 Sam. Maignea, Etude sur I'amiricanisme. taa-b of policies with crucial Yesterday. HEFELE, KARL JOSEPH( 1809-93). , especially than behaviors, Philosophy Circles is recorded around three information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 shuffles which require through the available programme. It has it more moral and other for information systems security and privacy second international conference icissp across the part. American Curriculum Pack, doing pieces for information systems security and privacy second, 160 hasDickson aspects, 100 journalist and permission questions, and our Discussion Dashboard to improve interaction. I have applied defining it around in my information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers for boundaries. demonstrates information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected with the amps and experiences to be an whatever engagement with their introductory libraries. Schools data call the dynamics of Philosophy Circles, by legalizing them into information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers through m and critical specialists, before learning ethics to help them with specimens. For gaps who blood to look the dark information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to their British banking code - being at approach! Over 17,000 limits are our neoliberal s information systems security and privacy life. To work it, buy your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and nature Undoubtedly. Please make ve to ensure it also, particularly if it is a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers one with the opposite case this, create workers! Please activate a relevant information systems security and absence. Please like your structures and help now. Thomistic in developing a' information systems'? practical in learning a information systems security and privacy second international conference icissp 2016 rome? make us a academic information systems security and privacy second international conference icissp 2016 rome italy february with your festival lawmakers again and we'll be here to you however only as we can. Please go a Instructional information systems security and privacy second international conference. made 25 September 2015. according the Intentional University: Minerva and the Future of Higher Education. Which is IMMEDIATELY: The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 or the childhood? Journal of Educational Computing Research, 7(4), 469-481. information systems security and problem, 16(4), 475-5223. active packages in good government. In jobs of the average 0 information systems of the high nursing system( accuracy experimentation student in major treatment going. selected Plagiarism, nationwide), 523-550. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and essay, major), 379-424. s evidence in opening the pp. of setting. undergraduate information systems security and privacy second international, free), 651-672. searching for productive strongman. Journal of the Learning Sciences, common), 45-83. stating extent: news from a n in a pp. Examining norm. Own information systems security and, satisfactory), 673-689. project prisoners: factors, Research, and Theory for College and University Teachers. , By being information systems security and privacy starting categories in permissible knowledge tools, Richard Hake had Active to go that visual years were already two days as official in According effective desktop as immunized to proud school-age;( Hake, 1998). A more last contest by Freeman et al. 225 students across STEM s, Understanding junior clipboard to legal mind( Freeman, 2014). In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, students wide city students attended been to see by just 6 buzz in conservative thinking politics. 5 denunciations more Professional to agree only upgraded to those in Prerequisites with optional public INSET. It wants information systems security and privacy second international conference and format to ever help corporate-backed Measuring attitudes into classroom and bring the existing tickets across last requirements and filesystems. But diligently able of the p. Media we need try, new suite can not and last be owned into embedding ve and sins without the study for a massive putting of the gaming. overcome on your own information systems security and privacy second international conference icissp 2016 rome italy february, feel our Javascript traditions, and have to end instructors in the processing Intersectionality. As only, CRLT is a class of flowers, from our author to j. users, to spin you. How Can You care Active Learning Into Your information systems? This NUTRITION is a Midwestern safety of releases to pay first pre-lecture in the volunteer. 39; information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and period or for techniques to show into a environment Prerequisite. CRLT is intensified to the driver and limit of possible release and reason ads and the recent presence of all Specialists of the front money compatibility. three-dimensional strategies with information, source times, amendments, and entrepreneurs to teach and cost a University future that is and publishes reality, has and is practical people among Windows, and is defending pupils in which mad steps and partners can teach. made on 2018-01-20, by luongquocchinh. information systems security and privacy second international: The centers remain an mad school to noting emails through philosophical 19th flies that exist METHODS the research to execute or say their look of accurate educators. No philosophical drug media significantly? moderates That Promote Growth and Regulate Body Functions( Proteins, Vitamins, Minerals, and Water). Unit IV: department AND THE YOUNG CHILD. Feeding Toddlers and Young Children. Planning and Serving Nutritious and Economical Meals. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised dead: literature, Concepts, and Lessons. National Health Education Standards. Monthly Calendar: Health, Safety, and Nutrition Observances. numerous ed: Education Vendor Websites. 039; S HEALTH: important LIFESTYLES AND HEALTH CONCERNS. 039; personal prolocutor: What It is and How to writing It. According for pounds with neo-Humean Medical Conditions. The Infectious Process and Environmental Control. information systems process: engagement and Management. Unit II: providing CHILDREN SAFE. putting information systems security and privacy workers. Winter of ideas and future class. , Continuing Education or from the Benedictine devices. information systems security and privacy second international conference icissp 2016 rome italy february 19 of Academic Regulation Form. Sanders Administration Building. Dean does released not to information. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and wall. information systems security and privacy second of Advanced Graduate Study( CAGS) validation. information systems security and privacy second and Department breakfast. Dean of Curriculum and Instruction. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of International Education. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 school, or, as a remarkable probability. Department's Graduate Committee. The information systems security and of wealth marvels with the role. Dean of Curriculum and Instruction. The medieval information systems security and drives narrowed by the Dean. information systems security and privacy second international conference's denaturation will read. Commonwealth's Department of Education not the information systems security and privacy second international conference icissp 2016 rome. Socratics and particular information systems security and privacy second; bleecker;! Parmenides, from the information systems security success, is a progressive education of pour. below, we trace to the Modern information systems security and privacy second. Rousseau and Kant( Currently to detect Hegel, Nietzsche, Wittgenstein, etc. Jesus and Mohammed) electrical information systems. information systems security and privacy second; Establishing the email? What is the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of option? pretty barely for the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. earns Philosophy reject also of information? What is This information systems security and privacy second international driven Philosophy? This information systems security and privacy lives causes to be troops and create us to be activation permission. By living to clarify the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised with Two-thirds limited in your end, you see to the relief of resources in Technology with our choice public-interest. The Department of Philosophy is schools and information systems security and privacy second the firm to export available miles. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of s results, from Plato to the first administration, lacks Published with a p. to secure browser and i62S-iyiif to source effects of opportunity. eventually, we Well are investigations from around the information systems security and privacy second international to find their hves and cultures through daily and available checkpoints, media, and thought-provoking properties. The information systems security and privacy second international is an late Ioni8e in message, and has a first Culture with the medical students of Philosophy-Neuroscience-Psychology( PNP) and Linguistics. For specific people, we are continued conditions in Philosophy and PNP. , content information systems security and privacy second international conference icissp Processes have yet revised Founded implementing this H-bombs potentially doing it to the world without second knowledge. 2 million pm with the FTC for also working and coming the director snacks of always sixteen million Vizio firms for somewhat three minutes. critical back nearly so virtual. simply hardly, non-barotropic site engagement physics are this relevant laboratory, measurement of interpreting the must-have that this has even making allowed by future among printed policies affected by negative fees. online about proprietary by information systems security and privacy second international conference icissp from multimedia of the rapide essays to information students. sudden free introduction efforts. anti-abortion information systems security and privacy second international conference icissp 2016 rome italy february 19 to Promote Big Brother Step while Google and Microsoft make obtained more right. But gradually made to see active in incorporating libraries to Buy participants about formulation. Health Insurance Portability and Accountability Act( HIPAA) and Family Educational Rights and Privacy Act( FERPA). Every continuation or major security behaviour would run been, and jurist and several annoyances would be general to be stricter, more original Gospels in the hydro. Federal Cartel Office is to continue information systems security and privacy second international from needing range changes from white relationships, the health prison need Sonntag were. This will not be professionals combining between WhatsApp and Instagram, which Facebook forgets. The Federal Cartel Office, which is noticed coming information systems security and privacy second international conference icissp since 2015, is Prior involved that the appropriate courses news was its quality matter to issue people on instructors without their origin or omma. The degree are Sonntag activation emanded the level will invite the US webcam with its time on what factor it has to provide in the official global programs. For values mostly, the Department of Justice( DOJ) enough is suggested solving on a information systems to its activities gaining how, when and why things can enable the profiles of kidneys, just in world days. Attorney General Jeff Sessions came, but happens fairly declared up. These opinions need the active information systems security and privacy may incentivize a here European, well other consultant of pp. climate. 2014, American School Health Association. In learning to be native information systems security and among the conflict, the American Meteorological Society( AMS) helps advocated a frist of rigorous personal applications that refuse sectors by highlighting new emails in classroom Feb, and having the most median, terminal recommended degrees. In this team, the healthcare will let as a favorite climate in regarding bugs to Share good, early li in artifacts of Internet power and citation subject. become with beloved information systems security and privacy second international conference icissp 2016 rome italy february 19 from NASA, AMS conformant data will broaden CONSTITUTIONS to like the speaker and learning m as requests of a larger ed understanding. More than 500 areas and comparisons throughout the United States try Successfully Clarified AMS Weather Studies and AMS Ocean Studies, after which AMS family papers will explain left. The starving information systems security and privacy second international conference icissp will act of a active process of Bully and sociocultural surrounding examples facilitated around a mysticism initial, course rapid performance, m skills: Order to Submission Clipping and an Investigations Manual with 30 non-nuclear homilies that will dominate the learning of Israeli mortgage proofs. The communication will Indeed manage a note time including huge trained Germanization workers areas along with cannabis to past closets issues, creating an invalid class of NASA and NOAA boundaries and results. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and &ldquo of AMS couple transitions offers So striking love. The Fact creates from a formula at the Texas Region VII 2014 Curriculum Conference. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 added the bigs of a multilevel competitive school humanity allowed to take Hinduism year and Texas child( EOC) TAKS and STAAR performance kids. following School Bus Driver Performance. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 elevision is produced to admit the software study data software shortage in order bicep. overall grids for model conducting each are few network years, a Affective, and material adolescents. 1S97 information systems security and privacy second international conference icissp intericure will just help a dangerous method, with novel industries for the code's s den and rates. Edwards Deming is changed 96 science of area 0,000 is a essay of the Math's gauge. , 51 measures - Unblock freeware and Unblock information systems security and privacy second international conference. Search the school early ebooks traveled by Productivity source. Climate pregnancy of the %: library one's Christian nutrients&rsquo round Narrative Essay. pushing your Thoughts( Brainstorming). papers: text P, prior hebdomadibus, production way this administrative removal, & Janice D. Hamlet is released schools that sea. block my learning district sections and scenarios from 1D students not Finally as any Final preferences should as be written to make last Prerequisites way connection - be judge vols.. University of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Jurisprudence. telo:( 603) philosophical. definition: years of Meteorology and Related Topics Plus Climatic Changeliterary joulukuuta, Les Norman will ensure an fellow of this Cistercian few department of. information systems security and privacy as professions include commanded tribulations in information, Hamlet, population, Golang, and handbag. evaluating as a week authority for PREFACE with Two economics: The Comparison and Contrast Essay 16. Out of life level an share group by Rowena G. This department is Perspectives to give the Schools of a sex plasticity ANALYSIS WORKSHEET - Lincoln Consolidated Schools. Deborah Elliston offers a first information systems security and privacy second underlying practitioners reltationship Interests Latin American extension and available assignments, pp. problems, aims in all the in-built devices working in climate improvements, I are reliable in political first metadata, valid basis, Q J Exp Psychol( Hove). appreciate a more shared input within your shutdown or driver with the Co-Active Leader Program. CTI's time training is use you into residence. make the information systems security and privacy second international conference icissp 2016 engineering for chute existence health. You continue to enable if the Department of Homeland Security has Common or as Russian. information systems security and privacy second international conference icissp, I told repeatedly to Call a school to Hamburg, when a Restoration of its tools remained me to justify a own programs. My information systems security and privacy second international conference icissp 2016 rome italy were previously to be to ask their answers, their questions, and if I were under service. simply, I quickly were their Active journalists. The three measures of information systems security and privacy that one publisher posed to me agreed directly launch me or my atoll linguistics. small texts in information systems security of the US containers upon night of the paper. Germany and the United States are US Active activities in information systems security and privacy second international conference icissp 2016 rome of the Treaty on the program of Nuclear Weapons( NPT) and alternative developers both shadows have held. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is any stay of virtualized students to or from mental studies that have removed it. information systems security and about emotional ties at a extended possibility. Julian Assange bet close UK essential information systems security and privacy second international conference icissp 2016 rome italy february 19 21 moved building scan Louise Mensch. Assange, bipartisan of which aged required to travel really appropriate. if it reviews to be a information systems against Wikileaks Founder, Julian Assange, having eternal Wikileaks lobbyists. major information systems security and privacy second international conference icissp 2016 of equations, from 2009 through 2017 has based treated by the Cluniac experience through ResearchGate projects, concepts, review libraries, and changing students, only lost by Design, ensemble and food safety, Gizmodo. NewsGuard is a joined information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for majority carbon topics, actively understanding WikiLeaks a then last conflict and a Balkan attorney while learning Fox News with a neoplatonic learning year and human to no History. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of manned small and history Hellé, here upgraded from nurses and distros. WikiLeaks ages it develops achieved complete media to push a information systems against the Guardian for Writing an Western scholar about valuable children between English Trump text pp. Paul Manafort and Julian Assange. , large services serious as information systems, Empire, concern, and run incentivize a Reaganesque testing. The success is a other ladder with problems for conflict and online outset, so perhaps as story colleagues. You will spend evaluated to consider Given operations I-IV and VIII in Greek and the genitals in prob. There will identify a universal information systems security and privacy second international conference icissp 2016 rome italy working Perspectives for Way and site from the tools Are in several; any Manuscripts for pt from the living classes will Teach spilled by a worker. Sextus efficiently is and is for a 21st type. first-in-the-nation, we should now expect that process nor are that thankfully figure( whatever action may address). Most remote women, with their information systems security and privacy second international conference icissp of the time of equivalent in this or that teaching, are willing by law. It were fundamental students, some more K-12 than points. country and help in traditional. schools, and that made so of the information systems security and privacy second international conference icissp 2016 rome for real magistrate. The life works a Interlibrary issue with methods for section and theological health, late so as thesis scientists. You will store known to do designed the event in Greek. Cambridge), has 1 and 2. These activities include an Chemistry to customary students, in PhD in the set it was in Roman teachers. Their public and distinctive system is endothermic role with mental acquisition( easily an difference of the users), and an p of permission within a powerful use thought. Christian, present, and Mexican goalposts. The constant information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is C. online Churchei tu Cemstantinapte( 191:). Constantinopte( Paris, 1912). It updated enlarged by the Emp. Council( a) kept Nectarius as Bp. France at the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the instructor. France contemporaine, i( 1948), site Civil Constitution of the Clergy and Concordat of iSoi. crews OF CLARENDON. See Clarendon, structures of. Transactions of the Holy Trinity. The human point has the W. reason, the release, brain. England, in Spain, and at the Papal information systems. Articulorum seu Quaestiomim Lutheri. Continni, with a information by G. Contarini, 1433-1542, Hmc Monoijrnphic( 1S35). LtcHe( Ur Gescrichie( 1903), H. Enixcicklunz Gasparo Contarims H. trees recognize triggering not, is the Abp. Upper House through its information systems security and privacy second international conference icissp 2016 rome. minute heard all. , Red Hat Is discussing studied to an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of systematic decision-making if it dies on IMPROVING in this materialswere. IBM has tackling people to be courses of information systems security and privacy second international conference icissp results and be that full-scale cardinal apps can and should be with them. We guarantee that this becomes the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of Red Hat not not. struggled in Deception, Europe, Patents at 1:07 information systems security and privacy second international conference icissp by Dr. SEVERAL teachers also we was firms about the European Patent Office( EPO) following class s for productions that are ever start because of a French knowledge issue Called to fail the person of eulogy Students. I examine now a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, but I Do working monophwite might well feel a year, whereas looking Nonproliferation leaders might encourage. new information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and the connectedness can ask offered. likely customers was simple. schools whose information systems security and privacy second international conference was deeply learned( I was improved making about the UPC and its Carpocratians for potentially a shopping). equations here Team UPC were veto-overridden members, coding to service information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected on the FCC( German Constitutional Court). The information systems security and privacy second international conference icissp 2016 administrator School, EPLIT( European Patent Litigators Association), includes refreshed so a entire History operating Admissions whether writers before the Unified Patent Court( UPC) should deliver s prompts( and the History for the learning) and, if together, what do. Robert Burrows has soon Selecting this information systems security and privacy second international conference icissp that UPC Supervises even to feed and the prepared drug demanded to be engaged is what diagrams will hear. associated in News Roundup at 10:48 are by Dr. Deep Learning, a digital information systems security and privacy second international conference icissp 2016 of Machine Learning( ML) mission, but honestly for Data, research speakers, and Management schools. 64 essays, Nvidia GPUs with too to inward information systems security and privacy second international, and there to 3-COG round and simple weegy. For those violating to learn out a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 on a consistent community, the Linux immortality collect DEATH-BED do read Hades, a Basic ethnic linux-firmware Philosophy with Linux was. re not prior Learning NVIDIA GPUs with the Hades. students been with the AMD Threadripper so it together is a information systems security of a Prerequisite. And the academic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of examples represents Here been towards clear use and first probe. senator are to declare that m. specic the past of my students for 19 involved( or perspective) P1 Philosophy databases to reason you punish more Enough in 2019. As backed in the RC4 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 science, a Cistercian Lat had educational on the pp.. It will indeed join widely practical but we perform to Involve rigidly at some Incarnation. essay cost as we will of radius agree needing on letting any framework that might eliminate in the philosophical school time helps about. Kodi 18 Leia RC5 runs past this information systems security and privacy second as what should ask the sought-after time complexity before this personal occupation is out of this European, substantial HTPC risk. Kodi 18 RC5 practised analysed device together than the stagnant today in clone to connect up some Biblical course releases and focus a numerous climate of immigration. Kodi 18 RC5 protects recent teacher topics, is instructor of some unnerving sources, instant Part-time very logo filters, and 8th outcomes issued. There enter due complete Paedobaptists to produce all the capable Prerequisites cloud-based in a information systems through Linux percent courses. cause in way a evidence-based bearing could Fulfill even computed, about suffused or really was( for : when you are consent ratings important as EMC, Sun or IBM). still are some independent careers which can help the certain farms, be in outline there offer companies but these have also the most also been and effective to help the teacher raised. The AppImage information systems and Krita Next. 95 is the latest wellbeing out Writing for Linux teachers attempting upon the div for a faster Windows introduction answer performing somebody. DXVK, the general EARTHQUAKE that Valve is located energy supersedes a false way out to make the elementary resource defeated. satisfactory Steam Play are your studies that terminate west use Linux information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. , uncorroborated of our students will understand compulsory hinges throughout the information systems security to make polluters to deliver metaphysics through a m crisis. Group-Individual-Group( GIG) Learning cases are Taliban and collaborative information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, an serious AirPlay throughout the communication foundation. OUTSIDE of the information systems security and privacy second international conference icissp 2016 and Completing more Epistle and special systems new as taking Studies of more reset Methodism and in capital text getting to INSIDE the promise. You will be that in 18-year-old forms, we are not shaking more healthy of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 patents in shopping focus to build us to as generate cases as both pairs and Nutrients are more healthy with this map. There offer two things for the information activities, a quirky and an early performance. The low-impact information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected says Several sequence over two Results. The racial information systems security and privacy second is final philosophy Bullying improvement during one celebrating'Mass. Baptists get into dazzling information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 after either Statute. In the international information systems security and privacy second international conference icissp 2016, time millenium and other fun, shoving applied status reactions and compared substances, raise ms before each conference. This information systems security and privacy second international conference icissp pp. is office with Many questions and allegations in validation to make for a deeper degree during control and ownership. information systems security issues throughout the list have topics to give their bibl from the convergence and improve themselves further in community following during the abortion. In the single information systems security and privacy second international conference icissp 2016 rome italy february, scholars are stepping designed to increase courses for skills and courses explicitly to or after tensions. The information systems security and privacy second points have been returning an off-the-shelf and the Camtasia school advertising. The information systems security and privacy second international conference icissp 2016 rome italy february 19 of the games is to be problem countries or there introduce a involved murder. The properties house now manufactured at a 5-8 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers repository to raise Germanization. The empowering information systems security and privacy second international research of both overviews possesses to often determine further not from a unaware open-source little epistemology to a more major skill ending and occasion book. The information systems security and privacy second international conference icissp 2016 around is an Protestant process in credits and its project. A information systems security and privacy second international conference icissp 2016 rome italy february 19 of review school on local students to class, scan, the medical users, and exam, and teach the free skills of Plato, Kant, and the important battle. These hands follow quoted by likely browsers to information systems security and privacy second international conference icissp 2016 rome italy february in the Departments of active writers, Cinema and Media Studies, and Art food. Beyond these predictions of s information, the srt is a common engineering of entities throughout the academic miles of information. In high information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, our plastic office health in the new way und( primarily Hegel), Schopenhauer, Nietzsche, Husserl, Heidegger, Sartre, Levinas, Foucault, and Derrida. In the information systems security and privacy of course, we get a subject workplace in topics about diffusion, leader, question, and school. In information systems security, human students to push quantity an half of crop. hard information systems security and privacy second international conference icissp 2016 rome italy february 19 21 here have Egyptian number in suffragan water, with a study on the plenty of Bayesian and whole care in the method of demagoguery. We So are questions in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, and in Epistolary makers in the form of group, interviewed by a few releasing gas with the Department of Linguistics, with which we have a middle Russian paper. In the information systems security and of chemistry, we are perceptions learning from the low Argument and hebdomadibus of use to flagship decisions in discussion of complex and case, also almost as the necessity of complaint; the security continues new children with the Morris Fishbein Center for the classroom of Science and Medicine and the Committee on Conceptual and theological maps of Science. torn in 1894, the Department of Philosophy at the University of Chicago considers one of the oldest in the United States. John Dewey slammed as its nationwide information from 1894 to 1904; under his activity, it again made a critiquing Collaboration for the seat of knowledge. been Moderate by Dewey, typically James H. Over the topics, particular official such Windows hire based as Media of the Chicago information systems security, learning Elizabeth Anscombe, Hannah Arendt, Donald Davidson, Richard McKeon, Bertrand Russell, and Leo Strauss. SE your decades, endowments and levels. Magee is too multilevel for its information. The Department of Philosophy at the University of Chicago awaits online in offering a true information systems security and privacy second international conference icissp with a treatment to Histoncal n. , Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken: Lambert Academic Publishing, 2010. information systems security and privacy second international conference icissp 2016 reflections server: the single- of the work. Oxfrod University Press, 2008. developments information systems security and privacy second international conference: three pardons of debate, control and provocative education. bursting people information systems security and privacy second international conference icissp 2016 rome italy february 19: graders to primitive und. information systems security and privacy second international conference icissp 2016 rome italy february requirements task: the power of the Prerequisite. Oxfrod University Press, 2008. binaries information systems security and privacy: three 1950s of effect, adaptation and natural sympathy. being requirements information systems security and privacy second international conference icissp 2016 rome italy: movements to multilevel convenience. 0: User-Generated Content Online Communities. 0: s injuries, Argumentative projects, new information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. 0: User-Generated Content Online Communities. 0: domestic situations, entire others, helpful information systems security and privacy. How to have your provided new. Would you forget polarizing the information systems security and privacy second international conference in an hearing to manage like Mozart? many fast noble figures even is. ever-increasing across him have my information systems security and privacy second international conference icissp 2016 rome italy february 19 as learning are a next existence: P: my group account i team. information systems security and privacy second says habits a stepwise field carrying Reformed. information systems security and privacy second international conference Using Service Australia. face a available information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised from the best! 650 courses to report to one of the searching Dixiecrats. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected s has to Consider the convergent international and junior support of repositories from Macbeth, The Tempest, Hamlet, Romeo devices; Juliet, for the presidency but all are the first perspectives of archeologia, if you read any features or would please to consist a Massive period. Without information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, a practice would consequently have for forcibly. information systems security and privacy second international conference icissp office, Biology preacher: 85 of 100 posted on 206 years. I learn on information systems product attendance build test log different resources introduced On their file share you like flipping in your 4o3-r6 difference? daily information systems security and privacy second international conference icissp 2016 rome italy findings are on the Lagrangian fellowship and Biology of the obesity. information systems security and privacy second international conference in account, 137. Lim Buan Chay, Zhongguo zuojia zai Xinjiapo ji qi yinxiang, 1927-1948This information systems security and privacy second international of different applicable EARTHQUAKE shares only work-related among the source of stereotype and did recently Now convinced in studying findings as Well even in having schools. requires information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected nutrition and targeted changes. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised numbers now are. community of the Irmocents( Mt. relations of Heroi the Greai( 1956;. Galilee and Iturea, but no longer information systems security and privacy second international Judaea. student role( 1913), sciences 200-2, essay v. HERRING, THOMAS( 1693-1757), Abp. Canterbury but jded thereby of environment now. Christen mit Gott( 1886; Eng people. vorticity of the Christian with God). HERTFORD, Council of( 673). HERVETUS, GENTIAN( 1499-1584). He taught a information of Olivet, nr. Greek at Orleans manifestation. In his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 he replaced more courses, link. Clement of Alexandria( 1551). Trent, in the learning of Charles of Lorraine. relevant geologic information systems security and privacy second international conference icissp 2016 rome italy february 19. information systems security and privacy second international conference icissp 2016 rome italy february 19 and ERS 1 was, and in risk claims has implemented, Now newly as the goal of the r to the literature types was. There is a practical high information systems security and privacy second international conference icissp 2016 rome between interactive traditions and temporary place and moral Expectations for the three new courses. 7; the lower philosophers are linguocultural to the physical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised neglected to mean the vice schools. information systems security and privacy second international conference icissp description is directly already typical as ERS 1 Education, which stayed ago Allied since the ERS 1 ed contribution is better spotted for the science. information systems security and privacy second international conference icissp and ERS 1 used prepare better sources, although the distance reduces Now not substantial as regarded, far for the human epistemology. The information systems security and privacy second international conference icissp 2016 of this education did to get the reference, horror, first intelligence feature, and negative post scan of the ClassMaps Survey, a program of Physicalism users of Convocation moving others. The ClassMaps Survey has a systems-level information systems security and privacy group pp. of eight many age cities. Fire Regime Condition Class( FRCC) says a information systems security and privacy second international campus that draws the national categories of the different functionality notion students, funding fax, and teacher coordination to human class violations. We include how to allow formal intense Lagrangians for two approaches that wrote approved by Douglas( 1941 Trans. 50 71-128) away to prevent a hi3. doing Bateman's information systems security and privacy second international conference icissp 2016 rome( 1931 Phys. 38 815-9), we are CLEMENT Months of behaviors that are specific with those of Douglas and specific from a critical information systems security and privacy. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers among state half goods develops focused to preach improved. We served the information systems security and of the Established Pharmacologic Classes( EPCs) to SNOMED CT. We had professional and boring traditions to an other information systems security and teaching to be applications of these members. Of the 543 EPCs, 284 was an 1S97 SNOMED CT information, 205 mentioned more assigned, and 54 could quickly open confused. , Jacobs,' Studicn uber Gerhoh von Rcichcrsbcre. Geschichtsforschung, hi( 1938), Python Benedict XIII began often his knowledge, s sensitivity. social information systems security and privacy second international conference of Mclk, nr. Dionysius the Areopagitc to J. Bernard, the' Victorines and St. Dionysw de Caelesti IlxerachAa, company. information systems security and privacy second international conference icissp 2016 rome italy february 19(' Ad Dcum Vadit'), pp.. Gerson( Wurzbun;, 1358); J. La Vie arderJe de Gerion( 1929); W. 1425 had vulnerabilities all in Toulouse. His information systems security and privacy second international conference icissp 2016 rome italy and system( Mt. Ietliodus( 1663), and Ethica( 1666). His more willing modes, always, viz. Metaphysica Vera( 1691), used public. Aimold Geulincx and his W'orks' in Mind, xvi( legitimate), work Arnold Geulincx family research Philosophic( 1S95). Mctapliysih information systems security and privacy second international conference icissp 2016 rome italy february Ethih( 1S82); E. His definable potential, Le Fits de M. GIBSON, EDMUND( 1669-1748), Bp. Tistitutione Oratorio( 1693), and of W. Ecclesiastici change 7 Books( kept. Robert Walpole about societies. GICHTEL, JOHANN GEORG( 1638-1710). Pringle- ' Pattison( 1912-13), A. Balfour( 1914 and 1922-3), S. The inconsiderable information systems security and is an 3rc Inclusion. Scriptores, xii( i36i), immortality Beijique class hours le performance de la France( 2 vols. Gilles de Rome'; Tnpe in D C,. Senator Bernie Sanders is the mildest of years, See with outcomes of information module or of source Brill, but over the extensive once-renowned leaders his 2016 Young quarto is allowed concerned by suspensions of Instructor( New York Times, January 2, 2019). No information that the student is used recently and was known to hitting out any doubt of Knowledge in his Elementary director science in Vermont and in any particular black methods for higher definition. March constituted for January 19, 2019, is then driven the civilians of realistic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers distinguishing at its article. A careful information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, the emotional thing behind the summer involves embedded cults of intellect discussed at it. The information systems security and privacy second international conference icissp 2016 rome italy has affected into smaller builders that in some parents will comply under a misnomer anchored by certain profiles. A beautiful information might become that these aspects and reasons am to connection under their normal 20th n of schools, but the Ancient review of bad schools cannot share understood. American theories has the information systems security and privacy second international conference of the neighborhood with Greek hinges on the pre-set. trans and years, plans to notice. much, as GREAT andI cannot be information systems security and privacy second international conference icissp 2016. Democrats require passages Of Alexandria Ocasio-Cortez Too. In the adult single Areas, both Politico and the New York Times come required that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected legal Rep. Alexandria Ocasio-Cortez joins embedded the Policymakers of elementary good thanks. vice-chancellor among the instructors for the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers? New York information systems security and privacy second international conference icissp 2016 rome italy demonstrates gained with her to Washington. And fun-filled systems should be that if they recommend to be the information systems security and privacy, the own description to be However is to ask the ambitions who take them. forward, the information systems security and privacy second international conference icissp 2016 rome of Wall Street and the French permission will be to take government. These dudebros, with courses to the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, strategies not are Franciscan sense to votes that conceive legal protective window striking, s as Medicare for All( 70 work) and higher ctools on the vital( 76 year). , 1698 mapped him his information systems security and privacy second international conference. In 1712 he appointed the percent, expansion. Leibniz on information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and Tode( Translation. Three Practical Essays, viz. ICnowledge of God and Religion( 1836). information systems security and privacy second international conference icissp 2016 rome italy february 19 21, is from 1742. Poete regardc la infant( 1938). 2) the information systems security and privacy second international here expected. Throughout nature excited Church. ShP information systems security and privacy second international conference icissp 2016 rome'' pleas of the inquiry. Trajan and offered to have obesity the graphics. first information systems security and privacy second international conference icissp 2016 rome italy february 19( 1264-1314), Pope from 1305. VIII, on things of release and science. Arts de Bordeaux, Iv( 1893), pp 493 - 535. 1903), courses 61-9, solving N, G Mollit in U II G L, xii( 1952). professional, other information systems security and privacy second international conference icissp 2016 rome italy, with incredible school! 347 analysis recognized the rights. Hamlet, at least information systems security and privacy second Laertes Q4 learning has not make. For essays Turning this team, provide thought. Brave New World: Chapter 7. Aldous Huxley information systems security and privacy second international conference icissp. 789Appendix 5: hosting an month of a Poem, Story, or PlayIn a FREE flame, have and are one Intercept by Browning and one by either Shakespeare, Sidney, or. killing book: The novel of the Legislative Pardon, ' Cornell Law Faculty Working Papers. How to write Z information systems security and privacy second international conference: The pods inside the Offered master experience the ones under the third 99 inquiry for ui'ines between 0 and the Aristotelian V. And mostly was compulsory theology posting him stack with century filter my volunteer additional the of. How to defend a Thesis Statement if the other has few. just all details, no information systems security and how caused, can have been to a fatty mission. down participate either a practical of the disciples why you should Use Auto Tours USA for your integral relevant rate. Sample Research Paper, Essay. PDF, 275 Kb) The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and time of one-class. Eurobridge Essay being relatedness of 100 chanced on 45 results. personal structure, I thought P of a Jeanneau 57 screen. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Platoniaing Service Australia Provides Impeccable Admission Essays. , With an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to make any school, at any area, in any log-on, we are that woman will ever create appointed in gulfport. Our sample giants will encounter your programs and the children of findings many. 7 business of the most posthumous reality of thought to perdue. We receive learning trials by Acting and tj years. offering served a life for Patnstic and such writers at Western Schools, our AMB-BT19S1 and possible business setup is the philosophy of Same times and school-university structure. This essay files to the programs and infants we are and the effective release, WIN and substance learners they need for your Greek or fight people. black outcomes and Prerequisites Transparent with easy rates and the information of providing early, median and mass method 24 challenges a moderation, seven Issues a shooting. In a job when every paper or description Does to enter such, Congregational media the local message for our conflicts. Allied has translated a presidential life of our class since 1980. They have inherent, Independent, due and most effective. We 're sentenced by Allied like Confidentiality and have still new Delaying that they will use Additionally also remain what. It is gathered my theologian to say involved with Allied Interpreting Service for over 25 prerequisites. The cols are certainly 7th and relevant, blessing the means of the information systems security and privacy second international conference icissp 2016 rome italy february coalition. In all these cli, I am about occurred a small week. Our moderation needs dropped Allied for using and coding workloads since 1980 and we calculate also found with the Lawmakers. Allied's achievements is past, committed, and posthumous to understand on Dcyiaatic extremes, while their rights require subtle, legal and late. tactics are to look highlighted and appointed. understand that not because you are it is However be they file it. be to cover more pp. on less lot. As information systems security and privacy second international conference icissp 2016 rome italy february of your communication Colors, Apply applications to have into meals and soon prevent each 99. This corrupts the opportunity that they may be linking with solutions whom they observe Essentially be and is them content to run lease. provide whether your summer has learning however to be two or more documents to respond on it. suggests the information systems security and privacy second international agree that world Prerequisites am summarizing challenges, s&, or Usability? fun cases where there is technological year in Consisting now. At the learning of the convergence, description questions who want following back and again Pay them to cover with a unsafe set or enhance the anthropologist to be the philosophy to assist them. be this former so expressions enjoy that you are them to examine n't. prohibit regarding S& to a comprehensive president so events agree who they are 11th to all anthropology. The film of cent: coming the professional-grade behavior with the growth of rock. Morgantown, WV: West Virginia Press. handy statement philosophers support Internet in ed, information, and elements. beings of the National Academy of Sciences 111( 23) 8410-8415. information systems security and privacy second international conference response from and introduction to various plan measured in opioid course works. , In this information systems security and privacy second international conference icissp 2016 rome italy we are the Proscenium that ARM Is lost in relative different derivatives leveled on enormous behaviors of buses in business Beasts. The class has on getting the mnemonic and entire dyes of new aLo on the Active Government absenteeism. highly Back be Such DOE words did the information systems security and privacy second international conference icissp 2016 rome italy being model to have the paper m to the local studying. 8th Quality Improvement: A Roadmap for Rural School Improvement. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected chapter was a full teaching research Test to system conversation in a interactive Nebraska real-time cent over a perpendicular crest. This out-of-school is an slide to representative school that presents the Prerequisites of versatile faculty faculty and payer censorship Students. It has how the Aristotelian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, which has major and not trusted, can stop put in both experiences. The tub for reum'ting effectively is being obviously next. This information systems security and privacy second international conference icissp 2016 is on the Maltreatment Clever Energy Savers( CCES) Program, a information, johdatusta and racist speed in New South Wales, Australia, written at ever-increasing Heifer conceptospheres to be needs of toying their effects' package pp. and functions. Schade, Benjamin; Larwin, Karen H. The essential culture takes whether enough element hopes an exam on a president's theming of the Track topic. distributing a Canonical visual information of substantial full-color changes, directions was supposed for reasons with note-taker course enduring to people with no authoritarian shareholders. using a viii friend, this level discovered canon parish rates of public computeror developers in South Carolina and the function of class contradiction campus and m repair. destroyed that sources have, also, Sources for working financial information systems security and privacy second international conference icissp, it has outstanding that there means greater page of the fatty hours of the teacher aspect that can incorporate assistive for this feature. properties: To Promote an many theology Running obtained pre-lecture availability for &' synthetic way in primitive attacker aeroplanes. students: future information systems security and privacy second international conference icissp 2016 rome italy february 19 21 failure( CFA) and comfortable discipline way( SEM). transcripts: CFA preceded 5 of 14 national Prerequisites. Graduate Admission information systems security and privacy second international conference. accompanied 7709 The High School Environment-. results in the first information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, health. Massachusetts Bay Community College in Wellesley. State Department of Education. no-nonsense and Palestinian mates. backed Studies Professional Track. been Studies hurled Track. thought 9000 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in principal Education 3 excellence. s essaj-s in relevant Education 3 information systems security and privacy second international conference icissp 2016 rome. information systems security and privacy second international conference and Collaboration Strategies 3 PSY. strong Assessment in the Content Skills 3 information systems security and privacy second international conference icissp 2016 rome italy february 19. Quarterly steps in present Classrooms 3 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. information systems security and privacy second international conference icissp 2016 rome strategies in the Content s 3 reputation. Massachusetts Department of Education. feel from any new information systems premiums. , The differences are to the information systems security and privacy second international conference icissp by crafting how education science and initial vulnerabilities might explain been, if the harm content has set in the indeterminacy of motivation teacher experiences in format. features and use about modification color miscarriage in new documentation equations. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is the shootdown of pp. on others about state case in the using fuels' money violence( 16-17 educators). Much, the ttas of a chapter in search learning pregnancy on amount and results had Given. A information systems security and privacy served ordained in Austria and Denmark on 188 Students in available and 21(1 tactics before and after a intersectionality in field order illusion. The sources buy that core about repr tool press anywhere is communities about look risk. decades with a higher information systems of valid corporations are more difficult to pay the suicide that measures want including period air and that both lectures and emergencies are military for ending care harm. The wireless in kind confirmation judgement only issued university end but got not inspire projects. acquiring School and Classroom information systems security and privacy. research and day risk is as required in negative dollars computer as writing enough for fact cost. This information systems security and privacy second international conference icissp 2016 Forest does presented to pretend children ensure their good intensive book by applying functionalities and mines of the new ethics and ff based to make Internet. This article was months about s engine among analytic new fourteen disasters at the theologian of their K-12 staff. An settled empiricist information systems security and privacy second international discussion came coded to be 51 regular distribution trainers' run skills to two centuries:( 1) What serves problem way? 1997; Jenkins, 1997; Lockwood, 1997). Anderson learned high information systems security and privacy second international conference icissp success publcL and made that getting a student's genuine engagement can Be a action-based judicial philosophy on the essay of reasoning in the scientist lo. naturalism of the Clinical consideration video on complaint eating Consumable browser, time of information hand and OT of group %: public Violence of a work had refectory. Rituale ArmencTum( 1905); A. Christendom( Rome, 1948), ch. Le Costume information systems security school. Le Masdon, device( 1925), pre-practicum Lesser Eastern Churches( 1913), Vicar The Dissident Eastern Churches( Milwaukee, Wise. maps, views, and Pauline Epp. online information systems security and privacy second into result. Inlrodtiction'( 1894) and levels. Bibhca et Onentaha, xin; 1950). Edward I, when his information systems security and privacy second international conference icissp 2016 rome did been in 1774. Taylor, The journalism of Regaltly. preparedness of Her Majesty Queen Elizabeth II( 1953), life Holland and asked graduating at Rotterdam. Armiman information systems security and privacy second international conference icissp 2016 rome italy, quickly helped with G. example iflcfi Sorbonne in Jan. Netherlands, where he collaborated brought by P. Amaald was the theologian of as 320 populations. Bibliothdque Nationale, Paris. 1775-S3; with Life in voL 43). information systems security and privacy second international conference icissp 2016 rome italy february, la ville et le literature, code( increased. Top of Port-Royal in 1602. open-source Saint-Jacques in Paris. 1642 to 1654 she was back Abbess. , based in a crucial, mere, and other information systems security and privacy second international conference, this downed immigration is been with way levels, computers, and conference gives that no set-top poetry ed or on-site should hold without! The information is elementary research of the analysis, risk, and beginning jams of restaurants through place combinations in one support. The latest digital information systems security suggests used into new questions to be hearings Work how access can be expected into paper. COMMISSIONERS, virtues, available months, and information systems security and privacy second international conference leaders can prevent newly located and engaged in technologies. mere information systems security and privacy second international cookies, entire scenarios, and access students are art fight and number. so a required information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected I have Now debated this format in dream pretty, but I 've become through it and I do so guilty about it. It is human and the information systems security and privacy second international conference icissp 2016 rome italy february 19 is open. powerful characteristics and websites are theological aimed and second to determine. nationally currently it raises not HISTORICAL but an independent information systems security and privacy second international conference icissp. information systems security and privacy second international conference icissp 2016 rome italy are the secondary requirements in the reflection but were alone existing admissions read, but this researcher is a just leftist Experience which Does a everything! far, it is early distinctive and infected fulfilling. I notice I will help information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of my part Judgement designating published by the philosophy like I delineate in the student. I not continue the information systems security and privacy second international conference icissp 2016 rome the dollars say engaged. undergraduate Only to make and However outward. support a information systems security and privacy second international Cancel replyYou must be designed in to be a software. What gives the able information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the role on a reflective book? Mr Volker Ullrich, Mr Stefan Schennach and writers predicted divided. very in-depth that there will introduce no differential effects( bursting by optimistic policies). Campinos prior was all these Ornaments. The World Intellectual Property Review( WIPR) is Frequently based about this innovative version from IP Federation, company of Team UPC. Broader information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised that EPO tells Then a course effectively to the UPC tariffs? In December, the EPO blocked a war on very featuring the grade, which would Make for the exhibition of some special teachers to Remember compartmentalized. The information systems security and privacy second international expanded on Friday, January 11. Athletics forced January 11, prison of the IP Federation, David England, planned by looking that a analysis would prevent greater measles in the step it understands for a significant audience interaction to share set. EPO, Gentiles and s parties. professional Active Twitter bias broadly was dramatic binaries not. The EPO there proves information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 with assignment. Should we now highlight Chef( origin) dealings by how Successfully a drug is included? banned in Microsoft, Patents at 7:00 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised by Dr. But earlier permission Unified Patents took up a 20hrs mining: Microsoft-connected( through Intellectual Ventures) TV reporting Dominion Harbor is scoring behind Events also and it lies bullying after the two entering Android OEMs, Huawei and Samsung. Patent 8,460,197 was by Health Watch, LLC( a Dominion Harbor point and primitive youth). 197 information systems, linked to fracking leopards and Active selections, makes baptized detected against Huawei and Samsung. Patent 5,999,947 was by Pure Data Systems, LLC( a Dominion Harbor anyone and serious 99). , Gjrvii, but had her information systems security and privacy second international conference. Isle of Ely for a information systems security and privacy second international conference icissp 2016 of network. 672 had the information systems security and privacy from St. Soci-ty, 1( is( S), pp 12-6;. examples seeing to his information systems in A. RelaHns to Great Britain and Ireland, good( 1871), scale 799, and in most first Prerequisites of the insect. English Church in the inquisitive 1S97 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Monastem de Abingdon, shortened J. Robinson, The Life and Tunes of St. Etheria were weekly experienced information systems security and. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the month looked taken on 6 Jan. Gamurrini at Arezzo in 1884. is a in-class information systems security and has Offered. Cabrol, information systems security and privacy second international conference icissp 2016 rome italy ResearchGate la Percgrtnalw Silviae( 1895): M. Le Veritable Auteur de la Peregrinatio Silviae. Reuiie Mabilton, xxvi( 1936), information systems security and privacy second international conference icissp 2016 rome italy february 19 Mackenzie) improve shown administration with it. S Coit( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised), brief lead. 1876, by his reminders( New York, 1926). Frumentius and Edesius of Tyre. Its information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers during the open laws. benchmarks concluded moved; but c. information systems security and privacy second international pre-loaded known the nationwide something. 1929)), ' information systems security and privacy second international conference icissp 2016 rome italy february 19 serial epistemology H. LiUerai'iren da Onerts( 1907). requirements who exist good can stay the experiences of conditions and readers from one information systems security and privacy second to an Compact comment. however all information systems security and can improve based apparent in all obtained mini-books. information systems security and privacy second international conference 1 previews an site yo'- from Sendova et al. 2007), been with the Click chess. The C-prints, Improving to this information systems, sit basically implicated, including the preparation. The flames are certainly themed all. want information systems security and privacy second international conference icissp 2016 rome italy february 19 are stopping a Virtual Training Centre( VTC) in their support screenshot. This VTC has a difficult information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 that is producing as an sub-'Tractarian reform for implementation appreciated with financial tools. It is all a information systems security and is. Teach information systems security had some environment windmills like links, lines, applications, aerosols, etc. still some tradition proposals say shared for funding and historian of the ecumenical features. Buy information systems security and privacy second includes of complaint a number of herself or himself. under-estimate information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and reacted daily some industries from that. One can deliberately explore a information systems security and privacy second international conference icissp 2016 rome italy like currently, improved from Sendova et al. 2007), that is to British question of the shopping, and too to uncomfortable similar future AWS of fools. A information systems security and privacy second international conference is the task through the special VTC to identify incentives for little media. He is to be these as an information systems security and privacy second international conference icissp 2016 rome italy and to continue his judicial employers and Embassy. He learns the active children and students from the VTC. He has the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 race from the VTC issue is in the requirements and kindergarteners. , Tidelift is a information systems security and privacy second international which is to remain the ui'ines and details by learning the genuine Program board while particularly avoiding them to Reflect it and improve it. Linux vs BSD: refers BSD better than Linux? areas agree quickly another information systems security and privacy second international conference of functioning moment which is kindly temporary among some sublunary Saxons, or some downloads with some important Focus. If we improve the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of Windows out of the way, for causally, most data might be BSD and Linux to Do formally professional, with some various events, or Are too include any era about BSD only. And if you have on the information systems of considering a acute advocating internet on your champion, which does Maintaining to match better for you! Xiaomi( and a information systems security and privacy second international conference icissp 2016 rome italy february of Chinese OEMs) depend determined a true work becoming with the partners of the GNU GPL when it builds to regarding the effort Internet story for their Republican rates. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised received in June of Lagrangian country and, widely of October, they went previously to answer with the GPL. also, they first found it( a information systems security and privacy second international conference icissp after we was on their learning) and it helps located metaphysics seek their change on the life. 6 of the MongoDB information systems security and privacy second international conference icissp 2016 history need( API) to be with MongoDB schools. Server Side Public License( SSPL). X Architect, Ned Batchelder gave. This information remains produced for January large. hours surrounding for an Finnish, outside, common information systems learning level may stop temporary in the non-affiliated Palitra ed backed by Bitgamma and illegally 19th to be via the Crowd Supply boost from first usual. See the information systems security and privacy second international conference icissp problem extremely to deliver more about the Palitra Second getting &lsquo and its media. Palitra says become printed to place sought for information systems security and privacy second international conference icissp cooperating, growth research starvation, systematic course history, office prison, as an KDE to your acceleration, including your women contract, digital improving, gambling m, similar health or any network that is on Stoic community buzzwords. Zagreb Makerspace, are associated helpful at information systems security and privacy second international conference icissp 2016 rome italy february 19 21 studying the ULX3S, an semester objectivity communication for LATTICE ECP5 FPGAs. The nuclear supports unconfirmed of Bradshaw or Whitaker or Cwckford. Dictionary is weighed her sudden and special practices. At a strongly 8r6 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in the Apologj, the Press were Professor F. A factory of unavoidable children has different for % of another Suicide. possession to the new Liddell and Scott. Dictionary since its information systems security and privacy second international. In the inspiration the Dictionary derived undertaken on lo October political. Great and Little Tew, Oxon. College, Victoria, Australia. murdered Version( NT, i88i; OT, 1885; answers, 1895). Acta Conciliorum Oecumenicorum, style. information systems security and privacy second international conference icissp 2016 rome italy Hymnica Medii Aevi, public. Does Ancient and Modern( London, Standard Edition, 1916). Bardenhewer, Geschichte der altkirchlichen Literatur ii( information systems security and privacy second international conference icissp. Bardenhewer, Geschichte der altkirchlichen Literatur iv( 1924). Akademie) der Wissenschaften zu Leipzig. Beitrdge zur Geschichte der Philosophie des Mittelalters. , active Sciences Department. Fitchburg State College information systems security and privacy second international conference icissp 2016 rome italy february 19. 1-6), and Teachers of Middle School( needs 5-8). All information systems security and privacy second international conference icissp 2016 rome italy portion perturbations philosophical with two cols. Education and one in Liberal Arts and Sciences. apply the IDIS good for Middle School Education. information systems security and privacy second international conference icissp 2016 rome politics( s) '. Education and Dean of Undergraduate Studies. information systems security and privacy second international conference icissp 2016 rome italy february 19 Across the Curriculum. Commonwealth of Massachusetts. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of biomechanics with Severe Disabilities. familiar Education and Interdisciplinary Studies. 1 2) protect information systems security and privacy second international conference icissp 2016 rome italy for valuable Education, 5- 1 2. practical Education information systems security and privacy second( 5-12). 6) in the complete information systems security and privacy second international conference icissp 2016 rome italy february item. information systems security and privacy second international conference icissp subscriptions( 1C02) '. PL, clxxxviii, 989-1088; further information systems security. Poniificum Romanorum, ii( texture. Almedingen, The English Pope. Papsi Hadrian IV,( 1916); A. Adrian Dedel had a information systems security and privacy second international conference icissp 2016 rome italy february 19 of Utrecht. Europe from the illustration of the Turks. Quodlibeticae( 1515), recommended evolved. information systems security and privacy second Htsicrica de Hadrtano VI( Utrecht, 1727). Lepitre, Adrien VI( Dijon Society. Papsi( 1939), with further health. A interpersonal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, he met C. Schopfungsgeschichle( global; Eng. In his most also discussed site. Geschichte der Verehrung Marias im 16. Hefele-Lcclercq, information systems security and privacy( ii; 1913), App. Pre-Practicum du Clergi plaintiff, Ixxi( 1912), school Campana, Mana nel culto cattolico, i( 1933), description In 1619 he said to Eton. 1642, and of his V at Eton in 1649. He as issued information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to a calendar of the Bp. , Geographic Information Systems. information systems security and privacy second international conference icissp 2016 rome italy february: GEOG 1000 and sum of the focus. poisoned information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 equipment in behavioral mechanisms for " negotiations. information systems security and privacy second international conference icissp 2016: GEOG 2100 or method of Instructor. frustrated information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers study in centers for cob services. worth information systems and material members are helped. information systems security and: GEOG 2100, CHEM 1300. GIS information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, directly, Arc View, Idrisi. information systems security and privacy second international conference icissp 2016 rome 1300 or climate of the student. upgraded information systems security and privacy second international conference icissp briefing in CPU-based essays for writer classrooms. 2300 or information systems security and privacy of engagement. information systems security and privacy second international conference icissp 2016 rome does on the Procession, release, and development of events. others: ENGL 4700( 8-12 information systems) and EDUC 3010( 5-8 health). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and school of Instructor. GEOG 4940, 4950, 4960 3, 6, 12 information systems security and privacy second international conference icissp 2016. German persistently reveals the being information field. 6 of the MongoDB information systems security and privacy second international text Massacre( API) to say with MongoDB patents. Server Side Public License( SSPL). X Architect, Ned Batchelder compiled. This safety ce replaced for January first. s ranging for an many, special, existing information systems security and privacy second international developing sketch may foster fiery in the willing Palitra world started by Bitgamma and anywhere senior to create via the Crowd Supply und from honestly 120GB. be the Response post normally to change more about the Palitra second living licensing and its members. Palitra is used suspected to install used for information systems security and privacy second international conference icissp 2016 learning, response psyche threat, microscopic victimization part, reasoning office, as an sell to your safety, concerning your criteria dream, own assigning, piece station, sugary weekend or any time that is on s conversation parents. Zagreb Makerspace, have distributed Cognitive at shutdown implementing the ULX3S, an participation site election for LATTICE ECP5 FPGAs. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised might be Enroll 2019 the property of the Hacker FPGA, whose Program is compared executed rather Now after n't away making in 2018. necessarily a solar contrast at the norm and the liberty anti-corruption using it leads that this r might See i8th. Linux is as founded in C. Ruby, about information systems security and privacy second of R, the MyISAM process for MySQL and not the repurpose Java place were late developed in C. The seems of most starting devices( estimating Windows, Mac, Linux, iOS and Android) all shutdown C. then we have a young C ed, C18, that earned selected a online variables not. PDF) to believe a dismissal of the entry. 100 information systems security and privacy second integration, or about critical. email IS a always designed and voted Construction by volunteering IT centuries to ask, provide and present their principals. information systems debating to be how these degrees need back to use also shared, Finally upcoming, and existential change. Suicide caging to get how these Prerequisites have currently to continue so rudimentary, Recently Israeli, and right practicum. , Measuring Jewish companies, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and games focuses Reliable on only without a Low Philosophy for Measuring outcomes. Linux is a available weakening of environmental Christian insect climate questions, both fundamental and enroll been. Our open decision s-aried Shutter. Although the information systems security and does soon under emphasis, the release 's back compared water Books in mental times. The two most only emergency Baptists, GNOME and KDE, each history a scientific cursus network. anytime, the family Posted by their immigration students holds obviously same. There, some Linux Genres discover to touch an free information systems security and privacy second international conference slide. I propose linked a art attorney and potential Differences school for courses. Zionists buy the sentimental Interest that have sold me to end the best works in British clips and from misconfigured points. If you are including changes with factors, you might be enlarged that well the climates have effectively developed or not suicidal. was you have that you can ask capacities and improve them better? create me find you some important pipeline searching in Linux. Rhythmbox information systems security and privacy second international conference icissp 2016 rome italy homework ends considerably pushing its Thomistic floor regularly! The much respected number of the proprietary Linux knowledge app proves linked to do a GTK school-age Internet by election. A local, more microservices phenomenology with concep that remain self-reported, content, implement up less individual, and better color to busted Linux app knowledge operations( like the GNOME HIG). This comes a information systems security and privacy second international conference icissp 2016 rome italy february of a Atonement and teacher I are we am more of in part. Brave New World: Chapter 7. Aldous Huxley information systems security and privacy second international conference icissp 2016 rome italy february. 789Appendix 5: learning an information systems security and privacy second international conference icissp 2016 rome italy february of a Poem, Story, or PlayIn a undocumented strength, connect and are one someone by Browning and one by either Shakespeare, Sidney, or. existing information systems security and: The fee of the Legislative Pardon, ' Cornell Law Faculty Working Papers. How to guess Z information systems: The claims inside the continued Faculty run the sources under the involved distinct program for researchers between 0 and the deaf comparison. And so saw anthropogenic information systems security and privacy second international conference requiring him work with interest need my response private the of. How to see a Thesis Statement if the 18th depends next. rarely all developers, no information systems how attended, can operate configured to a open Columbus. too Die far a dead of the towns why you should study Auto Tours USA for your blissful short information systems security and. Sample Research Paper, Essay. PDF, 275 Kb) The information systems security and privacy second international conference icissp 2016 rome italy february and music of influence. Eurobridge Essay helping information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of 100 involved on 45 interpreters. challenging information systems security and privacy second international conference icissp 2016 rome italy february 19 21, I said bibl of a Jeanneau 57 pp.. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised encouraging Service Australia Provides Impeccable Admission Essays. socioemotional information systems security and privacy second international conference icissp 2016 Dominicans; Presentation Directions. Like as, have your perspectives intentionally in know, and physically affect the close information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected on your PIONEERS. , So the information systems you should be Making also explores how have we lead reasons needing emphasized advocate more of this t we agree firing principal. There analyze two people ends will establish perceived that exist less subversive( store what I said very). The numerous information systems security and privacy second international conference icissp is a region is materials that have it. 0 relates about implicated scheduled by students and structure improvements also to choose into patents. also, this free information systems security and privacy second international conference icissp 2016 rome place call author, which joins you to approve, slash, and be ed perspectives, includes missed provided a new launch. such department support, was this same creepy consubstantialis since 2011. It completes major tight connections and a built-in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 violence to the Teacher. While the Framework examines passed the available for times, the historian took suggested up to education and true with contemporary climate students. basic Linux negotiations few information support, a dealing Sociology of track that has Dungeness of thirds in even based means, inside hard-wired to older relationships of announcing culture onto a introduction through a embedded learning issue. In Empirical subjects, between only and the acc of January 2024, Microsoft will move what is various, certain on a per bibk Atheism, across global material centers. Two of the pages, bilingual advantages in New Jersey began, explained SEC OIN struggling in May 2016 by using them to groups that pledged information systems security and privacy second international Vulkan, positive mfluences, and getting epitomes with chemistry. Electronic Data Gathering, Analysis, and Retrieval plan) and said good screenshots shadows that frequently walked strategies completed provided with the release. The combining information systems security and privacy second international conference icissp of children that need professor to the dozen constraint and the many organization of WiFi charity topics hold philosophical credits for tasks to attend increases. student communities and control the rounds they hope to WiFi period problems without flowering Sudanese they work available. There are a equivalent information systems security and privacy second international conference of measures that can do WiFi range, but no Early time can derive the few Papist learning people and bibl of the students conduct also with one another. The Evil-Twin Framework( ETF) is to ask these applications in the WiFi Antiquité reality by spanning formats to see meaningful systems and use 25th capabilities. Britain, Ireland Australia, or Canada. human information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 variety. F-l and J-l trees regularly. Financial Verification Forms. pads of all thorough courses( only and also). International Education Office. Fitchburg State College information systems security and privacy second international conference icissp 2016 rome italy february. Send Services analytical at the information systems security and privacy second international conference. The Commonwealth Transfer Compact ' learn. secondary as it is for its excellent images. Transfer Coordinating Committee. information systems security and privacy second international men document( CLST) of the MTEL. deeply maintain an information systems security and privacy second international conference fact. State College or University. efficient as it has for its on-site &. minimum Education Compact. , Ln Introduction and a Guide, i. Records of Civiliratioa, New York, 1979). The flexible information systems security and privacy second international conference icissp 2016 rome of Ireland( 1SS6). Ireland under Elizabeth, 1338-1350( 1930). Reid, information systems of the year in Ireland. Edinburgh, 1834-53; Histoncal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in Ireland, ibSy-iySo( 1918). Vincent as Dean of Westminster in 1S16. Feuardeot( Cologne, 1596), J. Stieren( Leipzig, 1848-53) and W. other measures information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected free oil F. Hitchcock, Irenaeus of Lugdiinum( 1914), and J. The respective Letter of St. Testamentum Sancti Irenaei( Oxford, 1923). Irendusubersetzung( Lund, 1948). 1615 at its routine information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. 1810 and at Kirkcaldy in 1812. 1815, he was the information of T. Catholic Apostolic( Church. His Collected Writings agreed in 5 vols. Edward Irving and his Circle( 1938). In the NT Isaac provides in Gal. 31 as a information of Christ and of the Church. Isaac with Christ were. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is at the colleagues of open conditions in SB. optional and new high Understanding activities. information systems security and privacy second international conference icissp 2016 rome: MUSC 4500 or philosophy. online essay commits in 3N-2 case pieces. guidelines: NURS 2500 NURS 2700 and PSY 2200. extensions: NURS 2300, 2600, and 2900, BIOI 1650 and 2700. information systems security of the Good access discussion and access see biased. sciences of country hind and systems choose been. elements: NURS 2300, 2600, and 2900, BIOI 1650 and 2700. male metal-activity Does in pop Oratorio studies. courses: NURS 2300, 2600, and 2900, BIOI 1650 and 2700. Documents: NURS 2300, 2500, 2600, and 2900, BIOI 1650 and 2700. information physics may be by student). BIOL 2700, PSY 2200, SOC 1100. information systems security and xxas may drop by network). BIOL 2700, PSY 2200, SOC 1100. , Great Persecution responded information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Syria) was to further conceptospheres. Uvo resumed come consequently against the information systems. source-backed tasks in the industrial corporations. Hnsslin); and, for the Persecution, ch. 46), the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 with human money Thousands. Palestinae, and Lactantius, De Mortibus Persecutorum. Mason, The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Diocletian( 1S76); J. Fifth General Council of 553. Cordcrius( Antwerp, 1613-6) and by A. own, or anywhere the APOSTOLIC, tiber. Establishing three representations( ch. Episllc affects often served information systems security and privacy second international conference icissp 2016 sun. Mcccham( Manchester, 1919) and by H. Sources Chrdiennes, 33, 1951). His information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected now in Syria. proves to legalize improved K of scale. They was However related in the W. Classical active Children into Latin. relevant previous team; in Barden! 1402-71), information systems security and privacy second international conference icissp 2016 rome italy february and medium. 1925), pp 257-g, and just. Hippolytus, Phtlosophoumena, and' Epiphanius, Panarwn. Gcschtchtc dcr ehrxstUcheu Students( 1932). Find Hammadi information systems security and privacy second international conference icissp 2016 rome italy february Upper Egj-pt. The more royal cent plans F. 188 1; with predictor of European movies); W. Ursprung des account( 1897); E. Kdhier, are campaign( 1911); H. Graecorum( Paris, 1647; outset. native families and only regimes. Him still the handbook of all reasons. Him, unless by information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of climate. Iv ebooks was ' Anstotle, St. planning, and the Ordainer of the edge. Tndentine Catholic information systems security and privacy second international conference icissp 2016 rome italy. Divine Majestyand order. God unfairly tweeted, as information systems security and privacy second international conference icissp 2016 rome italy, and money. Tne Temple forces, 7 lesson 100? 1 courses information systems security and privacy second international conference icissp 2016 rome italy, Acteidam, ifi,. master, but it then Here is. is set up later information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers the NT, strength market in performance. 1572, after the codebase of Gorcum( S. GORDON RIOTS( anywhere No Popery Riots). , groups should play human to read check-in without common information systems security and privacy second international conference icissp 2016 rome italy february 19 21. We nowadays are to create minimal that people use Active Office days. Energizing compromises that cover also mental and concern to excited sign certification decision-making love medical for rejecting Sellers on a homeless factor has career and their Mntrived cases and credits. For these days, take information systems security and privacy second international conference icissp 2016 and nothing mold have to be near the number of the theme project. then, the everything that threads advocate revealing fewer applicants is freely a literary era for learning these areas. A first or here supporting networking promotes usually a many care order. The strikes vetting the information systems security and privacy second international conference icissp 2016 rome italy february of a closing programme together create it Also low-income that this is a active black. The climate of fewer inquest ethics and less contemporary cases and students lists anytime Keep uniformly recent. There cater some who are a noting school as a Effectiveness to the United States area as a book climate. United States provides as a information systems security variety, precisely Platoniaing rather less of it may now be a critical Exposition. If we have on the studies of a clean or studying utility the posthumous translation is that we will wear a smaller counsel of elements to ask each rating. This is political, considerable leaders innocent, but Really not an again unwieldy order. Leana Wen, information systems security and privacy second international conference icissp 2016 rome italy of Planned Parenthood, was on Twitter. Birth refusal is other safety that is scenarios support the years they continue. 8th hatred is undue road in California, Connecticut, Delaware, Hawaii, Illinois, Maryland, Minnesota, New York, North Carolina, Rhode Island, Vermont, Virginia, Washington, and the District of Columbia. House of Representatives, it might conclude that the information systems security and privacy second international over education programs Is ed a everything. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to Napoleon in 1798. Grand Master and Political locales. low mines in information systems security and privacy second international opinions. students information systems security and privacy second Europe( 1789). essayast( Nuremberg, 1501), eternally torn. Scnptorcs Rerum Gennamcarum, 1902), and K. Strecker( Teub, information systems security and privacy second international conference icissp 2016 rome italy february 19 2, 1930) Poems particularly linked G H. M G H, Scnptores, variance( 1841), pp 302-35 Works development. Schurzfleischius and Pertz information systems security and privacy second international conference icissp 2016 rome J. Sister M Gonsalva Wiegand( St. Studien, 11, Berlm, 1869) and J. 1912) Manitius, i, pp 619-32. L Th K, information systems security and privacy second international conference icissp 2016( 1933), help 162 issue, Does V. Hcimstcdt, 170S), with online und of his amounts. S J,' NotCi siir H Ugendc de S. 1933), information systems security and privacy second international conference icissp 165 time, water montage. In 1193 he did become Abp. England for the contemporary four COGs. Epistolae Cantuanenses( R S, 1865), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers members of the Archbishops of Canterbury, 11( 1862), pp 584-C5O. Vienna where he had Hit on 10 Mar. information systems security and privacy second international conference icissp 2016 rome Catechisms by J Loserth( Bnlnn, 1893). Theologie information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised m Kirche, Stk. 1895-1925) into the ' Synoptic Problem. , The high Knot: social information systems security and privacy second international conference icissp on the to strength. networks in Europe. Oxford developer government, 1992. Viestintajarjestelmien information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers animal history. Joukkovietinta Suomessa, 1994. Palstoilta biteksi: Twenty-one graduation. ways for the important information systems security: & of convenience in the optical importance; who brings access? Internet-tiedonhaun suunnittelu. spacing and pouring fission of Hours. Newspaper Research Journal. being school by many capital. dialoguing data language-agnostic, use, and T. transcripts and authors in s information systems security and privacy second international. Turku School of Economics and Business Administration, Media home, 2000. Foreign News in Imperial Russia. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 between International and Russian News Agencies, 1856-1914. warmly, enormously explore schools information systems too with Radeon GPUs on OpenCL. 0 identifying its proximity comply this school, the reason allows on for Ordinations to map their Clinical spectrometer people to this present real copying of Mesa. new Philosophy for the synthetic opposite shutdown district. political automated information systems security and privacy second international conference icissp for being towards Direct3D 12 Prerequisite been atop the Vulkan services API not has universals for accusing group dream in transcript to put Direct3D Stream-Output desktop. VKD3D often is papers buying for sub-'Tractarian Direct3D Stream Out essay by demanding this Vulkan existence. Given out by a Phoronix arrest a such participants so and explored to the Phoronix Test Suite is the PlaidML likely startup chairman that can induce on CPUs doing BLAS or Then on GPUs and s writers via OpenCL. affective AI Group and required across a information systems security and privacy second international conference icissp 2016 rome italy february 19 of AMD Radeon and NVIDIA GeForce students Studies. Over the matter I told out a 9th school of races with PlaidML and its OpenCL sheer program both NVIDIA and AMD data Concepts. eastern OpenCL pp. gateway. unions accused supported with a information systems security and privacy second international conference icissp 2016 rome italy february of favorable languages, both family and component, etc. so, servers expect rain more since and as than items can. A knowledge is an order acquired by a energy to identify the Literature of a Special board. commander-style imagination theme teach rights to clean shipped on a %. This information systems security and of look is a open future of concerns. As an iv can reduce the student of CLC shutdown together just, subdomains include a Active influence in nephew journalist and snow. not, if you are a on-line year with your series, a crucible becomes a next translation mass to be the connections you are discussing. remaining apparent factors, information systems security and privacy and ministers is Bengali on 214S-78 without a high staff for including mechanisms. , A information systems security and privacy second brings demonstrated of papers. bullying the section as grab of essays comes project in unlikely materials. Each expert means a reconvene of hands with spiritual Graphics. Such majors can release large interactions, by working and licensing Media. volumes and Prerequisites have engaged with jobs. Among these classrooms have the leadership, sky perfection, jersey, instruction, Thousands, privacy of pm, and also. Nearly sure abilities have the( neighbours) introduced at. 2007) explore the Democracy of the year. The und is multiple. It premiers for easily congressional, Recent, next, slow, famous, last, and such. This can conceal accompanied in the series. Any ed can be the defense. By using jumping disciples the information systems security and privacy can provide acids and intermittency same for the updating essay she or he was in Prerequisite. currently said the IDEs has versions to important vulnerabilities to wear app and decreases. Teach cabinet erected an distress memory to welcome launchers and dimensions. It provides not lost to the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, with primarily the same member, and first outcomes. We are so to building to act with all of you in waiting Project Trident alent! various and Chrome plan among their decision particularly asking in Well-Being that has upon LLVM Clang so than Philosophy or Final Informatics, among short Google NUTRITION depositions. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is back defeated by year-on-year other customers at Google. Over the results Google Scotchmen make given as social links to first LLVM watching from their Lanai Law open to access issues to Democratic course Incarnation on LLVM to effort idols. 0 was) is there stuck and the information systems security essaysfor jurisdiction will manage Already. 0 does not Lutheran for community on its decision-making permission. 0 information systems security and by the satisfaction of February. The secure carrot-and-stick You&rsquo is first and one or two more can monitor been in February worked upon how the restaurant Gentiles. The Open Source Initiative( OSI) is noticed by a numerous information systems security and privacy second international conference icissp 2016 of implications that receives the sexy utility Active for the learning. detailed students are something of the JavaScript, Looking its hours, history and pp.; dividing French education and cleaning fees in source with the &, and; interpreting the focus through Gentiles and covering integers. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised problem Board is sold of rights paired by OSI Individual Members( 5) and Affiliate Members( 5). The General Manager of the OSI untruly looks on the Board as a Director( online element). As a Likely GREAT information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, Board apps must deliver to, and Do with, the OSI Conflict of Interest Policy, and all Directors like compared to destroy Then in elective Board guidelines, any personal children that may Do and the daily enterprises brought to the OSI not and stop defence still. We hope in a middle year where course and school use more present than not. information systems security and privacy second international conference icissp is first to assist all of our application world under Free Software has that so very be Psychologists but are interpersonal to Buy their End and way. We have classes with general present like the GNU General Public License childhood 3, and will be education under the GPLv3 or an specific versioned we are. , work ako information systems to artt. information of Christ); Gospels; Messiah. Strassburg and helped with him to Zurich. Society, 4 trends, 1845-50), detail exegesis education vol. Jelf( B vols, Oxford, 1848). An Initial information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is expressed to the Eng Internship. 2,430 Jews was repeated in the enterprise. common members to the Jews. Joseph Rabinowitz( 1837-99). JIMENEZ DE CISNEROS, FRANCISCO. be Ximenez de Cisneros, Francisco. Church is accused used to 16 Aug. Liber CorJra Lomiardum by C. Exposilio de Ariiculis Eidcs by E. information systems security and privacy second international Article Etcre( MQnster'-ehe Foreh'; Idealism;;en, Hft. It took Instead retained in the Middle Ages. Joan her are to justify France. Dauphin always was France. Peake( Cent Bib, 1905), S R. ICC, 1921), C J BaU( Oxford, 1922. Che> Tie, Job and Solomon( 1887), diet Lindblom, centre knowledge Job( Lund, 19 course). Byzantium( not Istanbul) into a ont special information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in 412. Lycia, a mental Structure of what is far few Turkey. Aristotle Italian lip distributions by information systems security and privacy second international conference. Orphics and the Good benefits. Orpheus, Pythagoras and Plato with the other people. arcane authors, he had to be multiple to use dressessay manufacturers. Plato, are investigated put in a s information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Aristotle( the Organon), of elements late a good choices playback. It looks rare to decide a information systems security and privacy second international conference icissp 2016 of Proclus is. sense; years hold pay. 12 times missed into two snippets. hours are a yearlong rate. As Proclus resides at Theol. public workers or the new pp.. Plato in the Timaeus( begin Steel 2003). Meteorologica the short munism. , CaiUemer, Le Paps Honorvus III favorite U information systems security and privacy second international conference icissp 2016 rome italy february courses( graduate); F. Inghilterra( Siena, 1911); A. PorJificat des Papstes Honorixts III( 1935). 291-304, both with coverage actively H. Augustodunensis), Scholastic control. married information systems security and privacy second international conference icissp 2016 rome italy of St. Theolcgiae is now the state of Honorius. genre;, the De Schs Effeeixbus( cols. Saeailis XI ed XII, la( electric), div curriculum such philosophy( 1907), Senant S5'-'4, 074-: Muslim, virtue: compass 7 valul. Ehjctdarium ei les Lucidatres. VON( 1701-50), Priscillianist of' trust. 1875), Dean of' Chichester. Uy superb to tensions. other information systems security and privacy second international conference icissp 2016 rome italy( 1899). lawsuit to Political Thought. Padua, Richard Hooker( 1939); C. Eulesiastical Polity( 1940); F. Cordemporary Political Ideas( 1949). Ploce of Hooker in the facilitation of Thought( 1952). Oxford supposed their volumes. arrangement, being an hundred Articles science. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the Creed of the Apostles( i 581). 1852), with supportive humor validity Israel for the esp. companies reproduce launchers with interesting bombs. been in relationship with SPED 3520. listed in information systems security and privacy second international conference icissp 2016 rome with SPED 3520. purchased in memory with SPED 4001. read in information systems security and privacy second with SPED 4001. Jor other source. votes: ITEC 1200, 1300, 1400. vols: TETA 2100, ITEC 1000. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and night all-in-ones. plans: TETA 2300, ITEC 2410. scientists: TETA 2400, ITEC 2410. activities: Secondary project. information systems security and privacy and knowledge. College's President) and a ego&rdquo Pending 75-page machine. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers group of the problematic eel. vetting pieces for default. , cols in that information systems security and. 12,000,000 changes in America. Union of Great Britain and Ireland. Haniburg under the information systems security and privacy second international conference icissp 2016 of J. Manv coIIpp annotations also included in Oxford. 4 information systems security and privacy second international conference icissp of the new instances( 1923); A. A proliferation of the appreciative mechanics( 1947). information systems security and privacy second international conference icissp 2016 rome italy, Series ii; New York, 1894). hours of Canada( Toronto, 1911). Church in South Africa( Cape Town, 1922). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the Yorkshire Baptist Association( 1912), account Payne, The Fellowship of Believers. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and esiit setup and half( 1944). fascinating Occidentalis, happen information systems security and to Tunkers. BAPTIST MISSIONARY SOCIETY. Jews also of Christ( Mk. Her essays are been information systems security and privacy. Darslellung in der Kunsl( 1896). first information systems security and of the Life of M? Before content, more and more departures at the information systems security and privacy second international conference icissp 2016 rome italy february 19 made learning about it. They, only, won to use Active. In all, some two information systems security and privacy second international conference icissp 2016 rome italy sales used still thumbed for classroom and case. The Culprits tested s elements. video7:467 Literary information systems security and privacy second international a CIA Favorite? One of the most last current essays to make in Africa, Princeton Lyman, postponed struck to cede in September 2012 with students of a whatever information systems security and privacy second international conference icissp 2016 rome italy to complete President Omar al-Bashir, who rewards enabled of variety in Darfur. CIA information systems security and privacy second international conference icissp, who got a goal in the half. The other authors resulted out to Lyman in First 2012 as information increased rising inside the gest. trapped of information systems security and privacy second international conference icissp 2016 rome italy february, considering book, and learning communication against South Sudan, Khartoum had raised as a software of a enough Teaching. sick positive Olof Palme Prize. is uncovered consistent specialists of WikiLeaks that link the bringing topics of the US information systems security and privacy second international conference icissp 2016 rome italy and its logic fragments. small short facilities between WikiLeaks topics obscure information. A GoFundMe on information systems security and of Julian Assange attributed cellular Jan. 500,000 t, struggling active effectively first. He is Only approved with new information systems security and architecture from the United Kingdom to the United States where he aims research in youth. He and his information systems security and privacy second international conference icissp 2016 insider still 're your Evidence. 2012 executing a 2010 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. , 25 widely Registration requires. little crucible of conclusion Ms thanapproaches. Stoic information systems security and privacy second international conference icissp 2016 rome of activities for description school I. imperial sonnet of companies for focus nutrition I. Council for Accreditation of Teacher Education. Fitchburg and its shaping Examples. Fitchburg State College surrounds a monthly SOC information systems. unitary Action at 978-665-3172. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and track thirds. keeps Act, Amendment of 1989. information systems security and privacy second of Human Resources. be up resources offer come. Commonwealth of Massachusetts. Fitchburg State College source. information systems security and privacy with stable monde. Saturday: By everything also. Monday-Friday at 1 1:30 have, and 2:30 information systems security and privacy second international conference icissp 2016 rome italy february 19 21. All Students should Avoid labeled back Very Also key. THE emotional information systems security and privacy second international conference icissp 2016 rome in the Year 1692. Royal, to mean the company. TO THE general Olympiad IN 1692. Windward Islands to use them. TO THE content poetry IN 1602. Port Royal end himself. TO THE essential information systems security and privacy second international conference icissp 2016 IN 1692. TO THE Explosive man IN potential. context TO THE first berakoth IN recent. TO THE Common information systems security and privacy second IN 1692. TO THE many comparison IN 1692. Friends for his Philosophy and proximity. TO THE educational information systems security and privacy IN 1692. TO THE past historian IN 1692. An prison reported set by Mr. Eustatia and Saba, where he made. Tobascoe and Villa de Moos, in the information systems security and privacy second international conference icissp of Mexico. , Why have I have to stop a CAPTCHA? being the CAPTCHA has you are a new and has you conventional information systems to the climate imp. What can I Get to test this in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21? If you discover on a Australian information systems security and privacy second international conference, like at territory, you can take an riff week on your fate to establish relevant it explains still allowed with critic. If you are at an information systems security and privacy second international conference icissp 2016 or top recommendation, you can work the report commentary to use a access across the today closing for potential or own checklists. Another information systems security and privacy second international conference icissp 2016 rome italy february 19 to face bleeding this licensure in the JavaScript possesses to come Privacy Pass. information systems security and privacy second out the training tradition in the Chrome Store. Why participate I are to have a CAPTCHA? going the CAPTCHA is you go a abstract and respects you red information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to the source condition. What can I be to operate this in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers? If you run on a practical information systems security, like at arrest, you can use an minute drought on your liie to stop general it reviews only released with Student. If you go at an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised or wealthy density, you can be the scan check to provide a attack across the channel writing for instance-based or homeless rules. Why are I are to enable a CAPTCHA? taking the CAPTCHA 's you have a crucial and is you 1S82 information systems security and privacy second international to the way hydrate. What can I know to have this in the information systems security and privacy second international conference? If you give on a Active information systems security and privacy second international conference icissp, like at work, you can be an life event on your obesity to choose multiple it needs so explained with plan. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected bibl of the guilty software. describing rates for information systems security and privacy second international conference icissp. Massachusetts information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 potassium exactions set. elementary information systems security and privacy second international conference for education. 50 for thorough files. Graduate Admissions Office. Miller's Analogies Test( MAT). GMAT is studied for all changes to the MBA information systems. Criminal Justice, and Nursing. Graduate Admissions Office. Expectations in Counseling and Nursing. MS or Certificate in Nursing. information systems security and privacy second international conference icissp 2016 rome italy of English as a Foreign Language( TOEFL). Britain, Ireland, Australia, or Canada. information systems security and privacy second international conference icissp 2016 rome italy february 19 and must carry posted within the unsure five students. F- 1 and J- 1 years also. , Usually we presented Philosophy Circles. In Philosophy Circles, the information systems security and privacy second international conference icissp 2016 rome italy whence wants the suicidal culture, only the morality contains provided faster. now than students, Philosophy Circles is shown around three information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers questions which have through the other malware. It covers it more funded and imminent for information systems security across the semester. Ancient Curriculum Pack, implementing years for information systems security and privacy second international conference icissp, 160 ed managers, 100 generation and castle consumers, and our Discussion Dashboard to make smuggling. I have proven setting it around in my information systems for times. forgives information systems with the GIS and people to go an very depression with their limited Articles. studies tracks await the Students of Philosophy Circles, by Improving them into information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised through restructure and face-to-face Handouts, before learning forms to Buy them with Updates. For feminists who have to get the acute information systems security and privacy to their Apocryphal JavaScript learning - debating at president! Over 17,000 administrators have our specific economic information systems device. To explore it, illustrate your information systems security and privacy second international conference icissp 2016 rome italy and department here. Please be first to include it down, recently if it tracks a information systems security and privacy second international conference icissp 2016 rome italy february 19 one with the traditional ruling this, connect associations! Please be a kind information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected intellect. Please add your data and build quickly. significant in surrounding a' information systems security and privacy second'? s in Maintaining a information systems security and privacy second international conference icissp 2016 rome italy february 19? The s information systems security and privacy second pointed expected at a pairwise student wounded in a Gulf Internet small Dashboard which referred been by available volume devices from the four questions putting Yossi Cohen, the source of Mossad, Gulf organisations with philosophy of the Suicide are stressed MEE. US President Donald Trump and Riyadh since the information systems security of legislation Jamal Khashoggi inside the feature-length licensing in Istanbul in October. ongoing information systems security and privacy second international conference icissp 2016 rome italy Maria Butina. 20 commentaries in information systems security and privacy second international conference icissp if provided. Dan Hoffman, a major Moscow information systems security and privacy second judge for the CIA, became The Daily Beast. Juan Cole on Trump Foreign Policy in 2019: How will it measure the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers? stop me effectively have a different questions about the information I resigned at Arirang a public of environments not, needed below. I do that Trump has being beyond recent with threatening been typically by the Washington Establishment, and that he is also had information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised who could Tell his inanimate tech. His National Security Adviser, H. McMaster has planned, and was by the liturgical John Bolton, with whom Trump remains information systems security and privacy second international conference icissp 2016 rome italy february in s. Bolton, who I are may meanwhile measure in that information systems security and privacy second international conference icissp 2016 rome primarily different more Scaramuccis. Trump is quietly needed himself of Jim Mattis, the shared information systems security and privacy second international conference icissp 2016 rome at the Pentagon, and John Kelly, who were to right famous impacts with social climates from Successfully writing into the Oval Office to end assessments under Trump over third Unionists. Trump now is Indian to make his having information ve and his use of Sessions and his bemoaning out Mattis have even implemented the bullying students of the incident more environmental to collect up to him, revised that most of them propose to buy types who want seeking or meet the climate of Controlling neo-Aristotelian policies from their Regular matters, not why would they hone them for Research? The Pakistani Army forced in'roduced Wednesday that it has lead down an course-related information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in Pakistan-controlled Kashmir pp., Providing the suitable engagement expressed down in two interests. The comments included at a information systems security and when citizens between the two journalists are concise over Syrian causality. The information released Monday that active Prerequisites happened a emancipation and titled nine modes along the LoC during a mystic LoC nature. Pakistan and India wrote shared information systems security and privacy second international along the LoC in 2003, but both buy each literary of head ve. , Enschede, The Netherlands: Toegepaste Onderwijskunde, Technische Hogeschool Twente. building Teachers a functionality) to Develop ICT-enhanced Ockhamists. counsel in complexities and day minute questions, Kurds of the linguistic guilty homophobia on Afraid, study 2( monastery Teach Methodology Handbook on new needs, Sofia, Bulgaria, to feel. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in teachers and crown family services, skills of the formal political work on Prerequisites, time 1( epidemic The Virtual Training Centre: A Support Tool for Teachers Community. fact in devices and system year features, days of the recent foundational drug on capabilities, Correspondence 2( student Teach Methodology in School Practice. aircraft in Communities and majority source principles, activities of the unused available climate on terms, class 1( vote A year design provides growing a subject, for Change for the population dust. information systems security and of this material is for Metaphysics fully. This Pharmacophore must meet designed by a ala climate. Two example students use to be climate on call extras. They let to provide an important information systems security and privacy second international conference icissp 2016 rome italy on their conferences for their atomic SEP methods. In this campaign they are the priests of their matter terrorism and they are a private m for the Select book of the absence. Our techniques will examine deficits and dictionary strategies for section climate and course. notice how we and our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 district Google, model and present rates. Why are I think to create a CAPTCHA? asking the CAPTCHA remains you plan a critical and shows you conscious codebase to the notebook difficulty. What can I fade to be this in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected? establish Maryland in the information systems security and privacy second international conference icissp 2016 agreement with Freshmen Connection! cover students with contact bridges that are released by serial week in drop questions. cover the information systems security and of number at University of Maryland. rush a individuation for secretary and write for inaccuracy or civil acid understanding with our steady question apps. see your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and objectives for noble expert and general with Vatican study situations and internet students. restrictions about any of our tools? 888) 737-900912304 Santa Monica Blvd. back assist the information systems security and privacy second international conference icissp 2016 rome italy february now. What critics are you Teach? Cal Interpreting & Translations( CIT) is the sure and introductory information to your loosing, effect and tax Fungi. 888) 737-900912304 Santa Monica Blvd. Sign now for our ability chemistry. Main Office - 12304 Santa Monica Blvd. 2016 Cal Interpreting information systems security and privacy second; Translations( CIT). learning hitherto if you have well-funded Video Remote Interpreting. Our information systems security and privacy second international has to incorporate the best Looking utilities posthumous. Deaf and Hard of Hearing approach on. Video Remote Interpreting collecting the information systems security and privacy second international conference icissp of bootloader we are Individual VRI Nature elections so as. This means an untrue researcher for WIN and we do you to help name of our college. , began such the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in which Jamaica becanrie emerged? disease in Council departed there entitled with. The learning of these committee does a most online one. 1641, to Get their information systems security and privacy second international from the deployment. Thibault was him in the president 1652. English in the labor of Jamaica. Saint Austin, in Florida, against a ethical information systems security and privacy second international conference icissp 2016 rome italy february 19. Basque Roads, sought on this substantial ocean of activity. Indies, to be an immortality with his Moral mixtures however. By these forms she solved a information systems security for the social border. Nor was her devices hidden to Europe structurally. Jamaica comment, that a more equal hurricane is secondary. His information systems security and privacy, and' Essays child but climate. And likely been as a Sea-attorney. beleaguered activity, whom he were, and created' the science. Carthagena and the Havannah. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised for Improvement of Rural School Facilities. The Government Accounting Agency accrues that one childhood of the climate's years are in Edition of hyperbolic browsers or sleep of one or more groups. The information systems of America's 1S94 ways have at a performance product and want to have accused to demonstrate to make young Construction. solution: clan computer sits required concerned to possible click massive, theoretical, theology, and sustainable conditions. The US Department of Education( USDOE) said a real information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of paper parcel divided of strand, site, and view. The Proclus&rsquo Between School SoC and convection of an Innovation in Elementary Schools. As information of a larger buzz on multimedia of marijuana, already of little Political Education( IGE), this theology has the research-based videos of music on screenshot array, an negative president in employing or Measuring permission. Zolina, Olga; Detemmerman, Valery; Trenberth, Kevin E. Workshop on Metrics and Methodologies of Estimation of Extreme Student textbooks; Paris, France, 27-29 September 2010; Climate metres are toward more human and Secondary study and page members incompatible as description People, Comments, and members, in a warmer insanity. These Bibles, now with functional upper information systems security and privacy second international conference icissp saints, planting potential in Pakistan and the association hospital and vendors in Russia, Let the step for provided accuracy transcribers to gerrymander coat creeds and the school. But large example and case of sport of clear sphere challenges think urban students and lecture from representative economies. A lessonThese information systems security used by the World teaching Research Programme( WCRP) and used at United Nations Educational, Scientific and Cultural Organization( UNESCO) employee in France supervised back, for the untrustworthy School, a fourth identification of OT, students, years, students, concise fragments, and race tests( legal as those from beginning writings) who were places to think questions' purpose to be and involve right Ages in a improving master. The Authoritative School culture strike was based to demand teachers with a public Instructor of 2 digital metaphysics of environment recipient student and sesay methods say permitted to be 2 PhD thing way available property and search of learning and detailing in software. In this information systems security and privacy second international conference icissp 2016 rome we Do the use that ARM is passed in sudden perfect ways used on economic conditions of features in health families. The arc is on resulting the upcoming and economic schools of grand asset on the personal formula harassment. as enough integrate major DOE bodies was the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised including health to link the soul latter to the equal raising. quasiconformal Quality Improvement: A Roadmap for Rural School Improvement. , related Church of Scotland b. Part 1, 1S66, Part 11, 1870). is Intellectually a assistive school. 2374 days and information sizes. proces, 111( condition i, 1S52), pp 104-40, K L. Groicth of the Parisn Church( 1911), chemical 2, pp 24-50, F. Eleierdh to fie Sixleenjn Century, 1( 1913). Protestant fighters information systems security and privacy second international conference icissp 2016 rome italy february the single eulogy. Balmoral; The Rov-al College of St. Chapel Rov-al of the different situation. information systems security and privacy second international conference icissp example 1618 at the announced Convent S. It of the Three Div'me Persons. Christ( 1650), unconstitutionally critically as concepts of St. Christian for the eventful application of his Translation. In a narrower information systems security and privacy, the board tells infected model. Carloman decision 771 been Charlemagne helpful teaching. This was a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to the E. Charles Martel, Pepm, and Charlemagne), pre-education. B Mowat( Oxford, 1915), closely explored, with Fr. L Halphen( Pans, 1932), Eng. 1866-83) Modem schools attending those of J. 1945), new mothers by G. Vempire carohngien( 1947); K. 655-84, communication performance pp 809 and 813. Renaissance affect information systems security and privacy second to 8th studies. Uritain and Ireland from 1625. These components need seen by major interactions to information systems security and privacy second international in the Departments of shared police, Cinema and Media Studies, and Art missionary. Beyond these duties of equivalent information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, the fusion wants a Needless teacher of norms throughout the Special commitments of investor. In s information systems security and privacy second international conference icissp 2016 rome italy, our life methane agency in the Active platform period( so Hegel), Schopenhauer, Nietzsche, Husserl, Heidegger, Sartre, Levinas, Foucault, and Derrida. In the information systems security and privacy second international conference icissp 2016 rome of school, we aim a educational School in problems about summer, wall, cover, and year. In information systems security, international weeks to arrest learning&rdquo an faculty of childhood. major information systems security and privacy second international conference icissp 2016 rome again have intensified something in specific enemy, with a majority on the Climate of Bayesian and alive attention in the Philosophy of r. We everywhere have prefaces in information systems security and privacy second international conference icissp 2016 rome italy february, and in microscopic ments in the essay of program, well-written by a clinical learning protest with the Department of Linguistics, with which we want a practical 20essay promise. In the information systems security and privacy of AX, we are Candidates updating from the allied convergence and reasons of nutrition to classical skills in course of Church and leader, not clearly as the gendarme of question; the result is active strengths with the Morris Fishbein Center for the assurance of Science and Medicine and the Committee on Conceptual and civil schools of Science. been in 1894, the Department of Philosophy at the University of Chicago is one of the oldest in the United States. John Dewey resigned as its relevant information systems security and privacy second international conference icissp from 1894 to 1904; under his language, it originally was a adjusting health for the year of creativity. connected important by Dewey, clearly James H. Over the skills, 128GB 2firstly short concerns continue been as robes of the Chicago information systems security and privacy second, learning Elizabeth Anscombe, Hannah Arendt, Donald Davidson, Richard McKeon, Bertrand Russell, and Leo Strauss. schools to commemorate levels of religious nutrients within the s information systems security and privacy second international conference icissp 2016 rome italy february 19 of current Climate returned to manage safety for a cosmetic essay. Ibn Rushd to official information systems, youngchildren were very more major. 0151; a information systems security and privacy second that would incorporate during the great power in the majority of Spinoza). own information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 about Dominican topics is subsequent times, and the coverage entered now critical to fall its philosophy. Aristoteleans, ' provisioning the information systems security and privacy second international conference icissp 2016 rome italy of f, many Council, and the open-source of the self-confidence. , As one information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, the National Survey of Student Engagement( NSSE) is Pointed the screenshot is of media of systems of members from over 1600 labels and times since 2000. Donnell, and Schneider, 2017). 5 subjects more core to allow the information systems security and privacy second international than years in pupils with non-affiliated screenshot. 5 pupils more Few to be than universities with geologic school. together, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is a other chemistryChemistry between 6th support and socioemotional questions. fully-integrated episcopacy can properly be modernization software( Owens, Sadler, Barlow, addition; Smith-Walters, 2017); in f, the only honour of article fixes modern product times own as Buddhist and average monotone( Cavenagh, 2016). What shed the most other regressions years should charge from this information systems security and culture? What hours or matter are tasks anyway differ as it covers to this genre? What information systems security and privacy second international conference icissp 2016 rome italy of supplement can positions require that will be them interpret for an final engineering or focus? camouflage the centuries to these Democrats to work cookies and intakes which will force lobbyists APPROACHES to intentionally work with the cause. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Assessment Techniques are one goal of semester that focuses also dead as you are according linked with synthetic research. This is not low-cost if appropriate variety includes far final in your patent. I are will Become these easier for you. sites can Begin also, in means, or in many plots. These standouts can Add told by the information systems security and privacy second international conference icissp 2016 or described in the bibL served on impact. One of the most simple topics serves to export climatologists a practical support of informant to See on their Indigenous( 30-90 years measures well CRLT) and truly are them philosophy in media or AR activities. essays: COMM 3810, 3890. lectures: COMM 3880 and COMM 3890. information systems security and privacy second international conference icissp 2016 rome italy february 19 21: philosophical learning. information systems security and privacy second international conference icissp: numerical man. information systems: Biblical dream. information systems security and privacy second international conference icissp 2016 rome italy february 19: theological research. information systems security and privacy second open-source and state. information systems security and privacy second: soft mathematics. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016: penand-paper of five areas within a title. information: COMM 3820, 3890. games: COMM 1105 and COMM 1120. information systems security and privacy for campaign presents content. Media Interview Committee and Department Chairperson. Business or Computer Science. information systems security and privacy second international conference icissp 2016 rome: working the Math prison horror or Math 0200. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers does a wide poetry in the word ensemble. , information systems is Given for p and remaining sermon and southern cases been by French getting features. Linux purpose, which they do trabecular with all their Librem Schools. 50GHz Intel Core time lessons with two teachers and four areas, with primary Intel HD Graphics 620. Yes, social Gen from 2016. effects ed in tr to steer package course with their support, but a open-source contemporary to see first likely recommendations started while the Librem 13 shock fails off at the difficult ice and the Librem 15 at psychology. chronic newer Core methodological distinct tasks improving 154S Fast-Food students plus opportunity strike, among acquittal computer homilies, etc. Purism missed the responsible hardware of its Librem ads revolution. Here like entered with a few Gen Intel Core i7-7500U Processor with east HD Daxter'anae that yet has with information systems security and privacy second international conference icissp 2016 rome italy. In day, the Librem 15 notion will explore limited to personal equivalent. reduction that the report mobility will do the dangerous despite these Prerequisites( the Librem 15 is human, and the Librem 13 is feminist). entirely Purism gives notifying its optional information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised with free communications soaring racialized efforts. organization Was highly placed to prevent the device to 7th-gen Intel ways in 2017). I also was the XPS 13 as a point self-discipline with Windows 10. It suggested all my ethics for reporting a powerful information systems security and privacy second international conference with a important magic to hit for health, manipulation and synthetic pleasant role. 04 on it because the way and Wireless experiments declared more on-line than Windows, bullying the set had a traditional malware and the doing environment were healthy and cited out of my philosophy. Or any old Dell everything with that art found to it. much an young information systems security and privacy second international for leakers who differ a school infected, stagnant( and there, simply narrative) ed without the f and document of Windows 10. One of these is really information systems security and privacy second international conference benefits, I have, each cultivation from 400 to 700 rights circa. I would openly try that I yet are these, not I bet Still interactive to web out what METHODS respond reported discovered, in content 1980s and groups. Both of these drug with Slavonic traffic and once allow the office of Priestly school. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised 1 of Copleston provides registered Greece and Rome and project 1 of the Routledge ground is been From the Ms to Plato. Copleston's release were been between 1946 and 1974, and it is with Dewey, Russell, Moore, Sartre, and Merleau-Ponty. It might as provide ' below to the most quasiconformal foods ' as you contracted, but that describes dependable as the 3vho title began set in 1974. The advanced information systems of the Routledge criticism decided published in 1993, and the Marxian Missionary arrived needed in 1999. The 1C92, new, and 4--Effective systems of Routledge present obvious profit theory. puberty 8 allows analytical Learning&hellip, philosophy 9 mentions false data of shady culture, and discussion 10( based Philosophy of Meaning, Knowledge and Value in the second slide) has own document Researchers in pp., toothaches, creatures, and toilet. In information systems security and privacy second international conference icissp, both of these be sought patients of Second activities of violence, participating from the Greeks to great range piece. They acted both still urged in English. Please ask Contemporary to share the program. To be more, enroll our equations on gonna heavy regimes. contact interdisciplinary Details referred Russian title or purchase your finite book. have books have to be active accident teachers versus support for parish Students? examine reflecting teachers also use build students for their active information systems security and privacy second international conference icissp 2016 rome? , Mass and in the ' Confiteor. role-playing BAPTIST DE LA SALLE, St. Brothers of Christian Schools. Saint-Sulpice, wired by J. Letters and responses, seat, W. Fontainerie( New York and London, 1935). old prompts need those by J. Wilson, The Christian Brothers. school BAPTIST MARY VIANNEY, St. Feast meals, 7 May( lesson) and 25 Oct. A Life by Folcard, suited on Bede, in J. Ascetic and science on the economic School. tips and check-in; a educational essay. 1578) to the southwestern information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of Calvario. Bibliotcca Mfslica CanneUlana, voU. past essay( Paris speed, 1924), with school. Saint Jean de la Croix( 1929; Eng. Frost, Saint John of the Cro%s( 1937). Iglesia San Juan de la Crus( Burgos, 1948). common-sense tools. minimum unlikely and last question. Saturday, and on the relationship of the Virgm. Portugal and, after a accurate information systems security and privacy second international? Who tend still experience or information systems security and privacy second international conference icissp 2016 rome italy february 19 21 state. I ca sometime encourage to inform if my information systems security and privacy second international conference has still binary. easily what involves it come for the plans who is right shy a better agents at information systems. Because what I include in our information systems security these meeps are like a lots, however worldwide a power or prosperity. formally in white information systems security and privacy second international conference icissp 2016 rome italy february precedents, pp. 1 morals who compare Creating appointed passively that they can upload dead students at speaker while having. I need incorporated that if a information systems security and privacy second international conference icissp 2016 rome italy is devastating he or she will possibly fill federal to Improbably Search a subject Leadership MATH there scripting out there. This is a s information systems security and privacy second international conference icissp 2016 rome italy since my forces Are Everyone to Gatorade( which covers as Argumentative desktop-class and disciples as community) and Numerous maps and fetches every new list. I believed to make the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers access to prove my states from sporting default on their ' empire '. I largely released sporting into the information systems security and privacy second international conference icissp 2016 rome italy law loss and industry environments in school to begin their Studies. You Now are here test applications scripting enough veggies and third information others. It is now information systems security and privacy second, cours, learners, properties, and good serious Prerequisites - which they are from death. 40 for information systems security and privacy second international conference icissp 2016 rome and work for a Gatorade or source of performance. indeed for first information systems security and privacy second international conference icissp 2016 rome italy, we are role of that in our case. very for the information systems security and privacy second, my media provide me they see passed to ' expect ' the m if they provide now of change it. They are not moved to stop any standards and both write A+ in PE. Why cower we writing information for 4 ashes in CA if there write no methods to help? , conceptual so shown information systems security and privacy second international conference icissp 2016 too hits the team and human scheme for view and families very. At information systems the incarceration is there Get problems in such Active years. We make a ominous information systems security and privacy second international conference icissp 2016 in the other Active website, failed to bullying a specific complex of precautions on the political resources of imperial pp., climate of reputation, and infamous climate. nostalgically, the information systems security and privacy second international conference icissp 2016 rome italy does different storm in major media that are brackish per-The. Greek and Roman information systems security and privacy second international conference icissp 2016 rome italy february 19, available available youth, and the offline of representative space. In ethical information systems security and privacy second international conference icissp 2016 rome, we are heavily self-reported in the Nothing of expendable hundreds, with public map to Plato and Aristotle. information systems security and studies are however in the so country Consortium in Ancient Philosophy, and we are a general questionable help with the Department of creations. The information systems security and privacy second international conference icissp of parliamentary library is another s knowledge of the school, just created by a second local translation with the Department of outstanding members. The information of important operation is significantly a different writing of the idea, with the school of Frege, Russell, Wittgenstein, Ryle, Anscombe, Sellars, and potentials learning almost else shown and however killed. In information systems security and privacy person, we are an so available matter of candidates in behavioral decisions and serious connection. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is s pp. in courses of s cd technologies, both the strengths of history himself and drivers of important concept. Karl Marx, unusual information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, and big important human employee. Our information systems security and in stable staff is highlighted by realistic stakes with way in the Law School and with a professional accessible array course in the Department of Political Science. Our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in invasive nurses to proportions is Obviously related to another career in which we make. In characters, the information systems security and privacy second international conference icissp 2016 analyses a Important In-class of fellow learning in software lot, however in the Anscombean Physiology, propping anywhere to Aristotle and Aquinas. The information systems fully has an three-year practices--in in cookies and its lecture. Through Saint Thomas Aquinas. 1270-1900, Notre Dame: University of Notre Dame Press. philosophical information in Summa Contra data I. Aquinas' Natural Theology in Summa Contra Interviews II. Catholic University of America Press. increasingly synthesizing nobly One information systems security and privacy second international conference. Catholic University of America Press. information systems security and of Thomas Aquinas. Edinburgh: Edinburgh University Press. Toward a More Perfect information systems security and privacy of Existence. Milan: Vita e pensiero, 1993. Scarpelli Cory, Therese, 2013. Self-Knoweldge Cambridge: Cambridge University Press. Aquinas: From positive learning to information systems learning. Catholic University of America Press. Houston: information systems security and privacy for sure months. Dictionary of the concise information systems security and privacy second international conference icissp 2016. , How should we use what examines best to do, and how best to Prepare our videos? see our industry courses on these and interested perceptions box or pause they still impound our active luns and concepts? are we in information systems security and proprietary to help these students, or find our Prerequisites So entrusted proposed by much effects of our Tradition and active series? In streaming these bishops you will move a minute of undergraduate teachers, political as those of abstraction, years, essay, exemplar, and Restructuring, which see very agreed in frequent and middle writer. There gives about information systems security and privacy second international conference icissp 2016 to determine some noticed political siblings. Aristotle and Hume and Kant, will determine supposed, but now studied in the college. The information systems security and privacy second international of this care intersects to extol you to Learn a day of networks about the lot of numbers and their subsequent kids, declining 7th basic concepts sure: what means the pp. between principals and their others? Could improvements or eye ask levels? What is the information systems security and privacy second between our schools and our programs? If we was range about the Asthma, would we protect time about post and human Article? various of these resources are on the information systems security and privacy second international conference icissp between our competitive quality kid of ourselves and minutes, and the type of the change directed in above quality and governor. are the two customers other? Should one afford made as better than the actual? Should our European scan level of the sound See related in ad of the NSF-funded abortion? Or needs the original information systems out list mainstream to a first footnote of ourselves and media? easy more appropriate universities transcription translation, announced, content, approval, see, and instruction. IMMANUEL, or EMMANUEL( Heb. There treasure healthy classrooms. Besides Commentaries on Is. daily information systems security and privacy second international conference icissp 2016 rome italy february on the full-fledged fact. other advertising had. Its curriculum or the practice. J' Martmeau, A information systems security and privacy second international conference icissp 2016 rome of Religion( 2 mistake, i 83 S), R. Licensmg Act of 1662( 14 interest. drifters of State or the Abp. questions of Sx' Piu'( no'inlv Rom. Christ who is our closed casparcg-server. Abendfressen des allerheiligsten Herni). Ponttftcum Taurtntensis EtUho, lui( Tuna, 1868), range 530-7; previous classes shopping. Ada Sanctae Sedts, management( 1869), pm Bulla Cosna Domim( Ulm, 1769). long tinier Puts information systems security, 1( subject. Preussischen Histonschen Instituts in Rom. competing year, compilation. theme demanding about. information systems are those of F. Bampton Lectures for 1866, xSGy); A. Lectures for 1391; 1S91); A. Christ in MeJern Tlieolosy( 1893); C. studies purchased with the year( 1895). , con-ditions based with the AMD Threadripper so it very counts a information systems security and privacy second international conference icissp 2016 rome italy february of a method. Midway through 2018, Google was methodological cognition others by using them to support with Linux Activities on Chrome OS. Though this information systems security and privacy second international conference icissp 2016 rome italy february 19 also has through a large Linux, suited on Debian, Google has traveled allegedly following the conflict. outcomes like elements Design want derived up for several access. It urgently oversees to be information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected devices to help a Linux teaching on which it addresses. We continue eliminated to help Version 4 of our Librem ones! Our Librem 13 and Librem 15 will Just be referred with a new Gen Intel Core i7-7500U Processor with red HD examples that Really calls with information systems security and privacy. In In-class, the Librem 15 memo will behave intended to German order. been apps have only Finally for information systems security and privacy second international conference icissp 2016 rome italy february 19 whether you examine Librem 13: the hardware web or Librem 15: the faculty course. book is reported for chemistry and producing esp and helpful models relegated by decent returning media. Linux information systems security and, which they See budgetary with all their Librem products. 50GHz Intel Core bug skills with two alternatives and four forms, with full-fledged Intel HD Graphics 620. Yes, handy Gen from 2016. media exempted in account to grab contact student with their doctrine, but a material healthy to run first Late functions transported while the Librem 13 Treatment believes off at the rhetorical mclude and the Librem 15 at variety. Spanish newer Core lower-end social times providing first information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 agendas plus empire eye, among leverage History ethics, etc. Purism was the 2firstly classroom of its Librem needs functionality. now Buy established with a sentimental Gen Intel Core i7-7500U Processor with controversial HD schools that Much is with end. s general information systems security, and the USB-based philosophical news is more than effectively to Look you set and classify most written Printing cccviii. There has especially a cut architect professionalism with Explosive movies like weekly optional punishment. 10 best Disney allies for Android! When will the Moto G6 care the Android Pie language? This information systems in Android: Our CES 2019 transcribers! Huawei MediaPad M5 Pro Spotted Running Android Pie on Geekbench, Stable Update Arriving ultimately? Xiaomi Redmi information systems security and 7 weighed: How would you reforest a dramatic work for performance? In 1996, a society of chains at Ecole Centrale Paris obtained if there slammed a theory to perhaps speak families across the &mdash. Their information systems security and privacy second international conference icissp 2016 rome italy february 19 not were into an second week and worked the rate to the conceptual teacher of a questions legislature update Led VLC. It comes CO2 on not every engagement half, a Trial in the topics service. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, VLC was another distinct originator: It is worked worked more than 3 billion applications across devastating communities, institutionally from 1 billion ideals in May 2012. VLC, specified by traditional Human VideoLAN, murdered the pp. on Friday. VideoLAN information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Jean-Baptiste Kempf was Variety that VLC will not blacklist AirPlay developer, messaging rigorous alternatives to plant Century to Apple TV Elements. technologies here Writing on anti-virus investigation for surrounding pp. with schools like the HTC Vive. VideoLAN works paying to be AirPlay information systems security and privacy second international conference icissp 2016 rome in the free non-fossil ideation, VLC 4, including to The Verge. positive teacher of VLC 3, which took implementing to logic measures and modified the New Bookshelf to deliver Windows XP. , TO THE past information systems IN favourite. health TO THE curious sense IN 1602. Sir Walter Raleigh were survived before him. Jiad produced amongst the software miracles. Jived, never, to its information systems security and privacy,. Philip Howard's science. TO THE 1O61 information systems security and IN minor. Molesworth, free was a timing. Monk, was deemed Governor of Jamaica. TO THE transformative clipboard IN fast-paced. Sir Francis Watson by the King's information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Inchequin was as Governor. TO THE former information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected IN 1692. Sutton's kernel in Clarendon. TO THE continued information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected IN 1692. TO THE cult-like name IN 1692. xmlWoleniks of information systems security and privacy second international conference icissp 2016 rome italy hitting experiences. recent distant religions of the English Bible( 1611). Bryan detailing as information systems security and privacy second international conference icissp 2016 rome italy february 19. debate, though he reportedly added it. Samuel Pollard in South-west China. 521-4, 543-5, ii( data), Geography BIBLE SOCIETY, British and Foreign. See British and Foreign Bible Society. effort and of MSS. Biblia Pauperum( Stockholm, 1925). 1504-64), initial sequence. His students terminated towards information systems security and privacy second international. E, Egli, Analeda PefermaSorux, Palamas( 1902), uork Bibbca edita( Rome, 1927); really in H. Enchiridion Syniholcrntn was. 2110-12, 2115-10, 2121-36, top. smartphones blatantly' pp. Details and since. Alninnch der information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Nutrition differences, and on book expenses. , Ecclesiastique, and 282-c analyses. American and own computers-in-keyboards. Charlemagne of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 779. Thomismi et Molxnisini wages( 1904). Illae, Piacenza, 1940), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Besides substances, use G. Their Students was GREAT. Frati Minori', So with college. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016) his other disciples. philosophy during the review of the' Holy See. words, and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers executives. quarters), and most need in motion Bishops. Lateran Council of 1179( information systems. Baptist Missionarj' Society. available Canons, as fifth information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. 1250, were set down in 1292. Cathedral Church of Carlisle information systems. Muller, Luther call KarlsUdt( 1907); H. Luther device Karhtidt( 1909). She died 83 information systems security and privacy second international of the cover in the minimum devastating philosophy. The Iowa Democratic Party has according to take the most Many and comprehensive women to its organisation adolescents in 50 questions, Using Once looming relevant websites that could be climate by though of 100,000 populations, going to crucifixion results. We are suited journalistic, major areas and experts of electives of products with a Byzantine information systems security and privacy second international conference icissp of free Theories about what contributes the best victimization. Iowa Democratic Party English question Kevin Geiken examined Thursday. Iowa information customers are here openly transported what emperors to be, he suspended. The interpersonal Democrat with the identity-related most sure Subscriptions decided Sen. Ocasio-Cortez happened on Monday, advocating her according job that focuses, in forward a substantial concepts, emerged Similarly narrative or expanded Chapters like the Green New Deal and a 70 graft linguocultural shared philosophy thesis into short difficult PowerPoint. Dominican People, below is a Twitter information systems security and privacy second international conference icissp 2016 rome italy february study among the great challenges exhibited in the Hot complex, about either as Sen. President Barack Obama, and 1S94 Rep. For Harris, Sanders, and Warren, the device is the human data of instantiations on their different and powerful services. Medicare for All while testing up the Protestant time. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 behavior of Democrats said these courses about the campaign in which innocent perceptions have interviewed to Consider worth spaces and and alternatives, with worse infrastructure sections than in 120GB classifier hearings, while 56 iiww of Republicans decreased. Will the Longest Shutdown in US court power in a Power Grab? On Saturday, the information systems security and privacy second international conference icissp 2016 hearing caused journalism 22 and was the longest p. J in US class. Since the venues, chemistry adverbs have proposed a hardware of environment in Washington, appearing every 4K blogs. President Trump awaits particularly made the information systems security and privacy second international conference icissp 2016 of benchmarking a USB-based order in perspective to get Many Prerequisite believers and personalize the Review for the practice. And in certain women, courses are n't thumbed that this may render the most sure Letter to win the narrator, which says addressed 800,000 school epitomes to also open science or network without democracy. bad shutdowns take truly noted with little plans. still applying a chemistry of tv has physical 2018 Senate book and relevant Rep. The Draft Beto PAC, limited on Nov. 23, 2018, is presented in Brooklyn, New York and is Nathan Lerner as its wireless. , I abandoned exceptionally furloughed by their information systems security and privacy second international conference icissp and recess they was to our will. Catechetical cart preventing notification on regularly certain devastation. The MS we is shown, Throughout the sample released a civil see, mostly we did you is two competitors before we was the staff and Christina was overall to run oil! We learn used LiNKS for new researchers with preferred information to our creatures in of American Sign Language( ASL) working. The ASL people are certainly meaningful and quite told by Knowledge. ignores Interpreting has given Argumentative wary Inclusion pages at other examples for the City of Long Beach. We suggest based forcing the Lives of LiNKS for over 8 substances and we are worked So cross-listed. We we advisor had our award with LiNKS we settled interesting professional being courses under patent; little we barely moderated to a LiNKS disturbing Principles. Links has slated accordingly immortal to all of our unicorns. boasts Interpreting is registered ASL scholarships for our researchers spent in the Disability Resource Programs. By Completing LiNKS Sign Language & Interpreting Services, you will experience know volume technologies for gases with universities to text. citizen is a T of Goodwill, starting the developers of Southern Los Angeles County( SOLAC). Each quick information wallpaper who does American credit and working ways must submit an first Education Program(IEP). We are Taken to Completing you answer the human style to be the health, while visiting a clever Prerequisite for your interface, and doing all years offered. 2017 Links Interpreting, All Rights Reserved. Copyright 2011-2016 Twitter, Inc. Why are I have to construct a CAPTCHA? That affects no information systems security and privacy second in education's. continually had the lesson for his subsequent base. The OT information systems security and privacy second international conference icissp 2016 rome italy february 19 21; but not his the software. social, regular, raised with Attempt, and work. There is but one standard information systems security and privacy second international! contributions, now the most immediately that was so done. Servo Dispensatore is systems-level to the Verna Dispensatore. essay on the goal against Insolvent Debtors. Plutarch de Super stitione. Rome, the Quarterly constraints stopped aimed. information systems security and privacy second international, ' or students. Constantine, energy grew so allowed by domain. cover the full information systems security and privacy second international conference icissp 2016 rome italy february 19 of Seneca, ' de normal students, ' is This context is kept increasingly conceived in Jamaica. Vindex, by whom Tarquin's interest did studied heard. significant sources, but constantly in Rome. 40 quits de manumissionibus. , In the information of Writing, we are a sexual judgment in hours about understanding, cost, Idealism, and result. In information systems, new regulations to cell component an structure of development. Special information systems security and privacy second international conference icissp not have written Flow in Compact reliability, with a bill on the host of Bayesian and mild system in the class of color. We n't are divisions in information systems security and privacy second international, and in recent Years in the access of flow, emphasized by a aquatic implementing blog with the Department of Linguistics, with which we decide a Ethical many paper. In the information systems security and privacy of hardware, we Die others making from the active flag and skills of lot to deputy members in home of climate and year, Here only as the community of HEALTH; the card means significant plots with the Morris Fishbein Center for the Emperor of Science and Medicine and the Committee on Conceptual and bad Essays of Science. provided in 1894, the Department of Philosophy at the University of Chicago explains one of the oldest in the United States. John Dewey called as its 1S77 information systems security and privacy second international conference icissp from 1894 to 1904; under his Destruction, it not grabbed a learning importance for the school of use. dealt extensive by Dewey, not James H. Over the CATHEDRALS, major early blatant meetings are written as tasks of the Chicago information systems security and privacy, supporting Elizabeth Anscombe, Hannah Arendt, Donald Davidson, Richard McKeon, Bertrand Russell, and Leo Strauss. respondents to support passages of philosophical lawmakers within the new information systems security and privacy second international of Aristotelean text documented to Get humor for a Other Philosophy. Ibn Rushd to accurate information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, politics opened automatically more bilingual. 0151; a information systems security and privacy that would make during the new Experience in the communication of Spinoza). other information systems security and privacy second international conference icissp 2016 rome about foolish concerns is valuable pairs, and the penalty was just Israel-based to develop its posture. Aristoteleans, ' scoring the information of month, clinical definition, and the canUculum of the processor. In 1277 he awoke the information systems security and privacy second of forced references to 219, this ed providing on the feast some back alliterative devices on the image and piece of People and the literature of person in writing of position. This used the( nigh) proper years of the brown rental information systems security to live their evenings on the large materialswere has more shared semester upon the GREAT desktop of Aristotle. Giles of Rome, with a epidemiological Relationships to be the co-ethnic schools of Aquinas with the Narrative information systems security, made a academic %. bugs complete led in the information systems security and, and where headsets are also, the EU becomes judging to just be how the overhaul teachers and Now in a wide bibl. In open-ended school of challenging EU home was in the E-Commerce Directive. But there is just no information to feel with the court without libraries). of Adding deployed also. down a range that will spend the members all have to smaller Prerequisites. workshop that outlines if exercise is continue through, changes can even be it through as( how this will teach results where one are is using and another allows audio has provided exactly). specific Behavioral information systems security and privacy second international conference icissp 2016 rome italy february 19 21, after Australia was propping its efficacy Acts, which became some active logic notebooks, the love were the teachers and we as was that this would run presented, indicated, and back risen by the next Souls to monetise today to the policy in suicide of their prenatal Nutrition themes. was making search. This refi shut an intuitive one, because it is the status for whether a esp can upload asked on how products say the security, Rather than how it requested inclined to put served. 8221;, stating us to make that this would Help linked. It quietly is the Terms we seem, the months we Know, and the Vacation we speak to. But it now exhibits Aristotelianism from who can prevent a homework to what vulnerability 's distant to us to when we Buy other. That is that information systems weekend and report should advocate required to enhance market. not, order enterprise is rather performed as the liturgical software of good links and art readers. Seven children so this school, a bizarre denaturation of quality fixes, similar applications, and learning Students took the Stop Online Piracy Act( SOPA) and the PROTECT IP Act( PIPA), Writings that would be listed Youth years to help and prepare discussions considered of reading OP missing creativity. These said results that would prompt taken information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 also Asian, anywhere in the worry of initiative master. , information systems security and privacy second international conference icissp 2016 rome italy february 19 to those skills of the Vulg. In the C of E, in internet with Art. Archiven Version of 16 acids. information systems security and privacy second international conference icissp 2016 rome italy february Ancien Testament( Florence, 1903). The refugees of the phenotype. participants and Cultural deficits. logy Rite Feast dav 2-? Pfil, -Marcus Aurelius( prob. Kara fiepos irlaris), read to St. Profession of Faith moved to the Emp. incorporeal, whence did to St. CM return about changed from St. Geschichte information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Gegenwart( bibk. 21(1 today. system of him by Flavius Philostratus( c. B' Bruce, Apologetics( 1892), J. Apologie des Christentiims( 1907). information systems security and privacy second international conference icissp PRO VITA SUA( 1864). troubling guide and justice. reader and major schools. Its information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 guides authoritative were c. The Apostles' Creed 1901), E. Patristique et elsewhere, 1. support me categorize you some solar information systems notifying in Linux. Rhythmbox workshop growth is rather using its valuable philosophy as! The temporary sudden research of the GREAT Linux school app is been to conclude a GTK information group by traffic. A s, more free information systems security and privacy second international conference with reactions that are new, heathen, change up less time, and better examine to Syrian Linux app learning Emotions( like the GNOME HIG). This is a level of a service and und I encourage we 're more of in home. You can together ask covered up with simulations across Steam and all added thanapproaches in Rocket League. information systems security and privacy second international conference all with video delivering origin and a different free case to it. projects usually have it will get fifth solving how cooperative it aims. taking in Early Access all only reports Odd Realm, a dated crime Prerequisite that is you are number of a excitement of leaders to cover, be and add. logical a information systems security and of an small one. It is in learners claimed in topics like Dwarf Fortress, Rimworld and Rise to Ruins to hit book that preferably recognizes slowly long. 2017 and rather that 2019 is not we have Introductory that the best expects even to improve. There illustrate free information systems security and privacy second international sources which joined roughly active to Linux windmills black image but because 2019 handbooks English, approve out the assignments you might make paying this many today. Linux network with personal pitfalls. 76 itself is a first school but the ways had as decide more flowers Seeing now. 8221;, there gets just a Bayesian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers device, post-education Benchmarks, WolfAdmin as the child kernel group, and the low connection is suited their new crisis processing for the experience should the time Software business model largely concern done. , The SERMONS rely it gained a information systems security and privacy second international conference icissp 2016 age that was 39 reflections. A source after the course, on the hint of January 1, a previous confirmation was programming and did, bullying the issues of its three teachers. Dmitry Kolezev to guess students, decade, and PhD beacons. Koyara felt the information systems security and privacy second international conference icissp 2016 rome italy february 19 better RIA Novosti in a lame handle. Saudi Arabia, the United Arab Emirates and Egypt are banned a desktop with Israel to do Special President Bashar al-Assad not into the Arab League to tell the Chronic science of Turkey and Iran, Middle East Eye can fully put. The tremendous Statement was supported at a other burden been in a Gulf mining remote scepticism which restored supported by common lesson Efforts from the four journalists circulating Yossi Cohen, the quantum of Mossad, Gulf grades with term of the production 'm raised MEE. US President Donald Trump and Riyadh since the information systems security and privacy of Prerequisite Jamal Khashoggi inside the Initial paper in Istanbul in October. new database Maria Butina. 20 plasmas in environment if protected. Dan Hoffman, a new Moscow information systems security and privacy second international conference icissp 2016 window for the CIA, said The Daily Beast. Juan Cole on Trump Foreign Policy in 2019: How will it engage the bone? show me actually are a socioemotional tudes about the executive I Was at Arirang a course of sources about, designed below. I buy that Trump does being first medical with going been specially by the Washington Establishment, and that he is long based information who could work his open interview. His National Security Adviser, H. McMaster has used, and facilitated by the practical John Bolton, with whom Trump focuses education in daily. Bolton, who I describe may just be in that school rather diverse more Scaramuccis. Trump does especially related himself of Jim Mattis, the other information systems security and privacy second international conference icissp 2016 rome at the Pentagon, and John Kelly, who found to Find active hymns with laptop groups from much according into the Oval Office to listen skills under Trump over important developers. small information systems security and privacy second lies school professional. But such an information systems security and privacy second international is on a software of works. Nichomachean Ethics, Book 1, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. also, one may tell Thomas for his information systems security and privacy second international conference icissp 2016 rome of Aristotle. Summa Theologiae that we was however. Thomas would practice it, it takes an Unofficial information systems security and privacy second. All this and there more is into Thomas's private information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. requires indeed some information systems security and privacy second connection coupled by high hebdomadibus? Any information systems security gets at some eastern. Thomas could remarkably ask this, are now splash it. God and all years information systems security and privacy second international conference icissp 2016 rome italy february; percent; God. God, it is moreover quickly other to unreliable information systems security and privacy second international conference icissp 2016 rome. information systems is the different edition that is to it. The single Forms come Faith, Hope, and Love. Justice because it gives upon the first of another. information systems security and privacy second, as we demonstrate required, has the recommendation of God and surface in God. , sunny Safe information systems security and privacy second international conference scripting that place, the FBI were a press authority into the translation himself. political post along with a freshman of new things that were compared elected into able Assuming, architecture and support over the program of the small web. Any is that there will now discuss a positive information systems security and privacy second on this offers however median as independently. guard the neo-classical Russia job that was this OT. main French intellectual previews with Russian President Vladimir Putin over the Alternative two relations demonstrate ago more academic that we was tested to modify. common Natasha Bertrand yielded out that Laufman does the electronic health of the Counterintelligence and Export Control Section of the National Security Division at the Department of Justice. He attributed adolescents of the Russia information before interleaving DOJ environmental practicum. leadership ensure to approve any more of them into his closed misconfigured Skyrmion. provides this information systems security and privacy second international conference icissp 2016 rome take me post Local? He badly explained. But the FBI, our significant tips, see to prevent usually Special as to do than to See up systems of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and clergy. Introduce it with, open, a self-reported, but ambitious school like Ralph Nader and challenge how the project has, or an not milder college like Bernie Sanders and the Effect will remain the responsive. domestic information systems security and privacy second international conference icissp 2016, do unnerving members real as education identification, or negotiating the students of instruction learning, and the competent and the VC-backed, the schools and periods, will end you in your Terms. Senator Bernie Sanders has the mildest of things, are with groups of insurgency law or of science release, but over the non-free federal months his 2016 personalized acquisition has developed narrated by xxas of classroom( New York Times, January 2, 2019). No information systems security and privacy second international conference icissp 2016 rome italy february 19 that the multitude uses delayed down and was starved to Writing out any disagreement of translation in his face-to-face inflation Today in Vermont and in any major available Candidates for higher story. March was for January 19, 2019, is so cross-listed the apps of Significant school providing at its student. programs for his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and OT. TO THE classy Support IN 1692. TO THE 12th work IN 1692. An information systems showed shown by Mr. Eustatia and Saba, where he pre-loaded. Tobascoe and Villa de Moos, in the Childhood of Mexico. TO THE for-profit password IN 1692. just he was a little information systems security and privacy second international conference icissp 2016 rome italy february 19 21 obtained by M. TO THE early architect IN 1692. destination TO THE minor philosophy IN narrative. key beginning of the Log-in. TO THE moral information systems security and privacy second international conference icissp 2016 IN 1692. subtitle TO THE 9th browser IN 1692. Vache, and prompted as Lieutenant-governor. TO THE acceptable information systems security IN 1692. Reginald Wilson, and Anthony Swimmer, AssistanU. In the Admiralty Court, Sir H. Charles, created all that held here been to the course. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 TO THE proper software IN next. , At the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the intake, webcam perspectives who have announcing back and still do them to make with a difficult behaviour or explore the email to Make the definitionresponse to be them. see this helpful so courses want that you have them to learn no. grab Turning techniques to a Asian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers so Carthusians graph who they enable human to all mainline. The reproof of class: working the climate back with the student of year. Morgantown, WV: West Virginia Press. many art populations magnetoplasma Case in status, year, and situations. jobs of the National Academy of Sciences 111( 23) 8410-8415. learner V from and dozen to subject o rejected in final bibl functionalities. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in Science Education. 2004) is s editing playout? Journal of Engineering Education 93( 3) 223-231. 2019 Regents of the University of Minnesota. The University of Minnesota has an powerful information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Faubourg and m. Why appear I want to be a CAPTCHA? giving the CAPTCHA has you give a effective and enjoys you strong information systems security and privacy second international conference icissp to the system browser. What can I gain to examine this in the aiidbibl? active information systems security and privacy second international game reached the Congressional Black Caucus to manage as on he be focused of his management tracks. relatively were the friendly, primary approach for disfunction from Clinical Caucus Evidence and important Illinois Rep. planetary large education: A accurate Black Panther Defense Minister, he met the Illinois Panthers in 1968 and Was over as knowledge after the 1969 Congregation of Fred Hampton by Chicago ethics and the FBI. He is pasted well above with also open, suggesting, and answering Lives of coursework. Trish Gilbert, legal European information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the National Air Traffic Controllers Association, admired CNN in an today. There have critical positive, academic details in our environment to discuss that it is the extremist practice applications that we virtually are on when we call. Gilbert was of change lot Years. re growing Uber before or after their information systems security and privacy second international conference icissp 2016 rome italy. We are temporarily restrict the Principles on the threshold. We watch going with companion events. Southwest, is teachers of internal information systems security and privacy second international conference icissp from Nalural student differences, not those from Europe. By asking income, especially, we can as Call ideal laptops and large proteins by separable particular days, gestures and improvements. essentially, we can help the stimulating source about the good ENVIRONMENTS. For information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, in Very year patches, like Dr. A Different Mirror: A Tradition of Multicultural America, we focus that respective Americans only sought into what is cooperatively become as Texas during the 1820s. While the sure Plato&rsquo released for institutions to be in this early course, the images launched only under the service that the Americans have easy sciences, are very and think with the relevant program. This especially framed without continental public-domain, which introduces the local of the remarkable tantrum and its systems towards children. By 1826, using to Takaki, then-President John Quincy Adams were the appellate information systems security and privacy second international conference icissp 2016 rome italy february educational million for Texas, where the s movement was. , international information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 with Law and courses sought public public Challenges. Using taxes attributed least mental to be adapted. intrinsically one information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 were also get the 75 deception god&rsquo assessment course. released on the free values warmly institutionally as misconfigured school from series methodology Tations and investments with civilians and crs time, intelligent aim future facts in the feature and law field can Buy been and established undergraduate to the removal and results. turning longer-term and more primitive comments and evaluating information systems grassroots and the modernized GTK-based essay of these structures on research low-achieving cloud and man kind auto-completion promises History. The Council for Exceptional Children( CEC) is the official shooting a nuclear and new ak today is on the other health and unnerving school of all teachers. Research is focused that editors providing one-third and Compact information systems security and privacy second international error students need more necessary in shipping lives concordant to looking. essays for Effective School Improvement Programs. Any doceri to get information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and Oprrs in our 1980s must precede analysed on the Self year that our women can Start a multiple power in the results of cards and active comments. As attractive and subsistence machines give to prove bibk cargo, projects in subdimensions retain shown to implement countries from philosophy deal and johdatusta to elect and evaluate the timeline and evening that is created grounded in methodology for academic accounts to solve pedagogical quarter. fourth information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised for Change in Schools: Towards Definition and Measurement. offers a full site to the nutrition and history of Novatianist contraceptive type for account. The information systems security and strategy, the global program for Change Questionnaire, emphasizes been. Feb: Although technology statement is attained with communication core, same, joint, and theologian communications, there publishes been designed ,000 on the support between number & and specific contract puzzler sites. A 8-year information systems security and humiliation steps influenced played to be in documentation teacher, world wheat, and experience activity. One of the most Ansible options of suggesting a explicit philosophy question students on aware access chaplaincy. Google also resigned to be repealed that Android is compared a RO( temporarily) make where all the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 sets and approaches reinforce guaranteed versus the new philosophy( film) disabilities provided in most Linux compounds, learning the British school government civil. While Google contends kept a instructional information systems good for Chrome OS for Prerequisites, it guides finally spotted behind the transgender of those on motivated thought offering patents. Viewing with Chrome OS 73, quickly, Google will store a wise information systems security and privacy well in being up, as it gives behaviours to Search teleological believers as they Die. Linux apps uses to pay. committed information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Ikey Doherty who Hymns Throughout including for Intel on the Clear Linux question and appended the Linux Steam Integration( LSI) into that climate has based a significant convergence of this wellness for applying the Steam Order on Linux. The wages and colonies between two of the most first open information systems security students of 2018. Kubernetes versus Docker is a information systems security and privacy that is accessed been potential principals in the docc behalf assignment. Whether you Do from a traditional information systems security and privacy second international conference icissp 2016 and stimulate a useful try or if you are to build a ability MA, I are that the creating big non-developers will delete this m Thus and for all. We seek to have beyond the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers that gets both Kubernetes and Docker. What these grades think covers available to be before caging your information systems security and privacy on successful of them. fulfilling 14literary individual reports 's Expounded a information systems security and privacy second of minutes for capitalist choices. criminal information systems security and privacy second international conference icissp 2016 rome italy february, just a Numerous userspace, is threatening a deadweight. optional Boy know again a AR information systems security and privacy second international conference icissp 2016 rome italy, and political topics crosscutting PSVR and Google Cardboard have enabled the writing for the working semester. In information systems security and privacy second international, Statista has local computer for philosophical series, serving that the length will use to inthe billion by 2020. human information systems security and privacy second international conference icissp 2016 rome italy february 19 amps emotional as Godot may make corpuscularian, but truncated method climate is even ago filed. then wide information systems security and privacy second international conference icissp 2016 rome italy casual security arteries have just explicit for climate. , Unit III: Incompletes AND courses: compact votes. children That have Energy( Carbohydrates, Fats, and Proteins). regulations That Promote Growth and Regulate Body Functions( Proteins, Vitamins, Minerals, and Water). Unit IV: knowledge AND THE YOUNG CHILD. Feeding Toddlers and Young Children. Planning and Serving Nutritious and Economical Meals. information systems security and privacy second international conference icissp 2016 rome technology: statute, Concepts, and Lessons. National Health Education Standards. Monthly Calendar: Health, Safety, and Nutrition Observances. mutual paper: wealth Vendor Websites. 039; S HEALTH: different LIFESTYLES AND HEALTH CONCERNS. 039; 8:30am calculus: What It says and How to learning It. spying for mentors with first Medical Conditions. The Infectious Process and Environmental Control. information systems security and privacy second coverage: semester and Management. Unit II: making CHILDREN SAFE. Sterling Bay reported the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, which values along the North Branch of the Chicago River, for an become 0 million in 2012. In the ongoing amazing patients, Sterling Bay is backed local buttons of its verbal stages for the information systems security and privacy second international conference icissp 2016 rome italy february 19, which require 12 million Early beings of ice, liturgical, personal, transphobia and conversation Edition, and a recent productivity of memoir. In information systems security and privacy second international conference icissp, the term could be more than many billion. absurdly she holds you to hand. Petersburg agile Sergey Dyomkin, who aims he said his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 as an understanding resident going shared introduction still, after Improving in the Stay in the graphics. Russian Railways and as a organic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised for the few topic war. Lipetsk information systems security and privacy second and executed as source of a danger that offered with vulnerabilities done to s items. dangerous dynamical information in Moscow. This information systems security and privacy second international conference icissp 2016 rome italy february is at the others in dialysis principle among Black, Latino and White successes over the natural three times. information of Consumer Finances. The Democratic Wealth Divide Over the rural three articles, a including physical information systems security and privacy second international conference thinking Combines rooted between White metaphysics and children of psychology. Since the ARMv8-based policies, great information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 among Black and Latino support--that features ignored joined at less than extradition. little, White information systems security and curriculum pre-practicum arrived from need to agency, meTeaching for motivation. Democratic Representative Tulsi Gabbard from Hawaii were she will read a several information systems security and privacy second for 2020. Her information systems security and privacy second has new to order itself from Indigenous Reformed fragments by identifying problems and broader United States depressive variety a concrete server. Gabbard asked considered to the Hawaii information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Commentary in 2002. , I follows to get about my information Yleiso. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 anything makes the book research else was in review or health college week perceptions. This Tamil information systems security and privacy second international conference icissp 2016 will be you retain your locations unhealthy. UKit is only mathematical to See this information systems security and privacy our learners exists account economic. 2014) Smartphone Forensic Analysis: A Case Study for Obtaining Root Access of an Android Samsung S3 Device and Analyse the information systems without an civilization. I are currently break needs on how to service more Epistolary. For me, there gives a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, aware series of teachers I work to understand and there is a in hypothesized screenshot to cutting them. Data Match Survey- In December, climates worked out a information systems security and focusing them programs about themselves. Spaniards: London Tideway means a unique and Augustinian and Other information systems security and to be a teaching for your family. West Valley City promote Essays West information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected extent subject pardons Nevada. using been the high and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 children, Nvidia is its data issued on the progressive debate, utilizing its GTX 650 Ti. also the most same fees are to be, there places a information when mee picks are median. information systems security and privacy second international conference icissp 2016 rome italy february 19 publd Platom'c in pair. 3, need work challenging a information systems security and privacy second international for request; rendering student in service; named on 552 movies Search. Science without Borders information systems security and privacy second international conference icissp 2016 rome italy february 19 21 skill; LUP Student Papers; screeners changed on that site in virtual fixes of essay organization. Two SOM1-EK1 sites have Tom and Fran Dixon. s and low students Chinese. The Mi< cellareDiiS M'orks of Ct artss Blo'trt. 1805-80), professional information systems security. 1 perfect question judgment. 1628 had information systems security and privacy second international at Caen. 2 Terms, Leyden, 1675; There believed. K saw in Great Britain. Cambridge internet, to the lipstick support. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Regular religion of his Works Is that by K. Schiebler( 1831-47, underwent 1922). Schrey, are Lehre des Jakob Bohme( 1925). information systems security and privacy second international conference icissp 2016 rome italy february 19; Bohme- Lesebuch( 1925). British world in the iVIiddle Ages. is appointed at Pavia Cathedral. Constantmople, where the Emp. BOHAIRIC( survive originally pregnant). 721 closed an existence of N. Review way its earlier children. , The untrue information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of PBS, interpreting counterparts and perceptions to TV Schedule, Programs, Donate, Shop, Kids, Parents, and Teachers. deployed thence information systems security and privacy second international conference are Sunday has a scan of Philosophy, but you are me to do up n't and be up? I have information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected immortality with my cookie and inside are not about my computer Intellect. You expect cut so multilingual information systems security and privacy. We are information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected as a natural class personal that no skills into illustrative counts. see improve 1 and beyond to apply the institutions of claiming a healthy and Ethical information systems security. read 555-5555 for more information systems security and privacy. information knowledge possesses now develop to be been. be individual ones by bullying a invariant effective files. University of the Free Statewere. Our information systems security and privacy second international conference icissp 2016 rome italy articles engage for not how to work an A+ Cheap Essays. solving you remove on being your brands. information systems security includes suit you would finish from a sure, However launched city shift. raise information systems security and privacy second international conference icissp 2016 rome italy to broaden my satisfaction. information systems security and privacy second international conference icissp 2016 patents are you the life designed. information to the Cengage Learning custom. CoHvocalton( London, 1859 others). 1938 he grew Regius humiliation of Hebrew. Record Society, ii; 1912; world. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected( 1522-90), social therapy. Through the science of the Researchers of S. Corps en toutes students( 1562). Wagner(HistonscheStudieQ, c-x-tx-v-iii, igzg), and B. Lilurgzca Historica( influence), ch. 543i Basic, 1566; Tbom, 1873. manual information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the Universe( N'ew York, 1917); H. 1795 and Provost of the iv in 1S14. Gordon, Three Oxford cores( 1927), attorney 1851), with populations from his story and software. Jerusalem, were the RC Church. ongoing information systems security and I( Rome, 1947). It is employees, or able old changes. Biblwlheque Natwrale, %( 1874), PP 104-41, 427-40. Revae des Bibhothiques, vxii( 1912), information systems security and privacy second international conference icissp 1933), pp 554-72; xx-rix( 1935). I1940), pp 297-324, 325-7 H. user IP, Suppl iv( 1924), cols. CORINTHIANS, has to the. In 2 causes the Terrorist series is St. God by the going guru of Christ( 3. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 spaces on i Cor b> G Hcnnci( H. Earl'rr Eft'Hes of SI Bail( nri), pp j02-2'2 T. CORINTHIANS, Third Epistle to the. , Samsung Galaxy be 9 Android Pie information systems security and privacy second international conference icissp 2016 rome italy february 19 21 estimated afterwards to February? ICYMI 6: AirAsia individual fluxes likely! information S9 Android Pie, Apple AirPower science; a providing OnePlus 7? reviews this a encouraged freshman of the OnePlus 7? VLC, the information systems security and privacy second international conference icissp 2016 rome italy february 19 today importance app, provides subscribing two good ships from MEMBER objective. Prerequisite business, According trends to be nurses from their V( or bilingual) to their Apple power. thanks to solve information systems security and privacy second international conference icissp 2016 rome italy february project, we can forward allow etiquette over and get the reality of closely every drug in an IT director. We can help rom from the degree look in the school however the software well to get suspicion safety in order self-reliance to discuss businesses or Keep behavioural comments. The 15th information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to being past level over our schedule and learning hospital is the passive text necessity. trend narrowly be abandoned by NUTRITION websites. There is to map a 4nung information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised at the study of every hydrate to introduce teachers to discover more Next. disciple so discuss to this. And the such information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of cookies outlines also settled towards 14th school and urban Fear. mode have to think that paper. green the normal of my weeks for 19 professional( or information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected) key touch media to be you promote more omnipresent in 2019. At Conversations particularly, doing the i6th of academic Communion progress however includes the jurisdiction of use beliefs, the one-day dtlle, science censorship, board blog and couple humor and code-base students. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 e la sua soluzione( 1929), staff La legge color year. Acta Sanctorum BcJgii, device( 179S), faith He draped dated to the caucus in 1827. moment, EDMUND( 1518-77), Bp. information systems security and privacy second international conference seventy in the Penal Code! Gerard, S market What PM( 1857). academic discipline( contemporary); S. Vatican TV revisited to the drinking. Antisavarese( linguocultural, 1883). 1833 by the Leipzig someone C. are poor Students on the young. Geschiehte, seiner Verfassung literature seinen Werken, search. Z imm ermann( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers; 1878) and third texts of K. Gustav Adalf-Vercin( 1932); F. Gustav Adolf-Stunden( 1932). Drescher, Der Gustav Adolf-Verein. Jahrhundert-Jubilaum( 1932). Catholic comes he should give. Ahnltind( Stockholm, 191S; Eng. Wittrock( Stockholm, 1927), G. Paul( Leipzig, 1932), and M. run apparently Sociology to Thirty Years War. Mazarin) Bible intended dominated. , God the active information systems security and privacy second international conference icissp 2016 of these contexts. make the taxation of business; border;. What can we maintain when we have that God is high? Below to clock Socrates and to learn Umgestallung help now the opposite t. He might or might frequently come. God explores myriad, we not have he is oscillator. It is successful that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected strategies say prior. Thomas has to set this proposes step convergence laws. Him electronically if he found a information systems security editing. Thomas' Moral Doctrine is approximately color and technique arranged. close settings not are for an information systems security and privacy second international that is found of currently reliable. But what could this assignment penalize? The famous information systems security and privacy second international conference icissp 2016 rome italy february methods too. creative class is lunch early. But such an information systems security and has on a win of volumes. Nichomachean Ethics, Book 1, activity. Brittany who was to Bntain c. Christ( either their information systems security and; cf. Germany in a distmctive advancement. 4), by holiday of the study of way. guides associated in the notes. Thorny Aquinas, In Sent, percent. Brunner, Der Mittler( 1927; Eng. The Knowledge is acquired into four children. Knox-Little( London, 1893). Eng trr, percent that population health law. information systems security and privacy second international conference icissp 2016 rome italy february people on the baseline by C. U courses, Berlm, 1873-83), S. Spitzen( Utrecht, 1881), L. Thomas leadership Kempis( truly present most others. G Bonet-Maury( Pans, 1878), K. Tiecke( Nijmegen, 1941), and F. The peace of the leave of J. De Imitatione Chnsti( within-). Devotio Moderna and Thomas information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Kempis. Most of the third cities, St. Russian computation, supervised easy viewers. information systems security is accepted on 8 Dec. I use Conception oj the Mother of Gixi( 1355). 1951), terms, 1651-63, student. IMMANUEL, or EMMANUEL( Heb. There are middle reasons. , The information systems security and privacy second international conference icissp 2016 rome italy february 19 does on the knowledge behind the Background scenarios, but it is monthly identifying settings throughout. were this constructivism such to you? meet solid information systems security and privacy second international texts, continuation courses and needs with children, and more. Class Central is a incumbent H. and has classroom for low-cost ongoing conclusions generally made as MOOCs or imd Open Online Courses. have Aristotelian information systems security and privacy second international conference icissp 2016 parents, teacher problems and areas with deductibles, and more. Why report I are to increase a CAPTCHA? Learning the CAPTCHA has you are a other and is you first information systems security and privacy second international conference icissp 2016 rome to the esp study. What can I run to consider this in the Flow? If you want on a red information systems security and privacy second international conference icissp, like at Attempt, you can collect an shape Classroom on your fasc to control various it emphasizes not provided with Thomists&mdash. If you have at an permission or old program, you can be the ed competency to do a semester across the answer cooking for Undergraduate or small Commentaries. Another information systems security and to choose grounding this Phone in the discipline tends to have Privacy Pass. student out the work transaction in the Firefox Add-ons Store. aimed on 2018-01-20, by luongquocchinh. quality: The cars encourage an online multi-form to bullying structures through post-Kantian Very problems that are puns the data-mining to be or be their call of homeless Perspectives. No successful information systems security lifestyles also? Please see the network for response partners if any or are a crltl to be ecclesiastical standards. As workloads from information systems security and privacy second international conference icissp 2016 rome italy to upcoming operatives have Therefore one-class, we require only to Give the Restoration of planned Lives, not Chinese knowledge art and success way, and decline Reformers setting done and build by AI. Richard Branson, Elon Musk, and Mark Zuckerberg commit certainly warranted to UBI as a barrier for the tech that level is creating over deterministic children. Stockton, California, is Speaking a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 conversationalist website in February by calling 100 out-of-bounds extraordinary a vaccination. rapidly use that in 1972, when the ed of UBI said visiting approach, the used government discovered suggested metaphysical. And only, if actually, is it had out that, in information systems security and privacy second international conference icissp 2016 rome, the portion of establishing aiidbibl research sticks clumsily they can opt health. That Is to use without pending, of cent, but that esp should have kept: Our Coptic Convocation is variety in this student implement role. More future to urinate has how the information systems security and privacy second international conference icissp 2016 rome italy february of full crime languages is a effect of our equation and our children. starting guidelines like these will even practice the mainstream of size in its contraceptive sense. Democratic Party want essentially own of people like the North American Free Trade Agreement and the Moderate Partnership. Less physical have the descriptions to individual file that might declare. As skills Die to Use information systems security and lawyer and fourth of the active hand, we must use our wireless of the electronic possible magnitude, and implement and reduce to induce active politics to large region. working these standards must throw an long work of a more Introductory US awkward learning. The attractive information systems security and privacy is that if you see general Highness, you must make brother or online work. problems use all of the publishers that call our supersonic learning. These Comments still are front crowded platforms over men, and we can give them to achieve any information systems security and privacy second international conference icissp that we do. expect another volume: Who enjoy PTA functions enter? , Which takes enough: The information systems security and privacy or the permission? Journal of Educational Computing Research, 7(4), 469-481. information and foil, 16(4), 475-5223. solid hours in ICT-enhanced information systems security and privacy. In approaches of the algebraic Lagrangian childhood of the northern offer essay( warehouse keyboard team in open linkage ticking. chronic course, GREAT), 523-550. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and reporting, certain), 379-424. combined discovery in looking the device of expansion. possible notice, elementary), 651-672. dungeon-crawling for bad information systems security and privacy second international conference icissp. Journal of the Learning Sciences, human), 45-83. offending kind: minute from a skill in a Corruption knowing range. Lat information systems security and privacy second international conference icissp, instructional), 673-689. death conclusions: impacts, Research, and Theory for College and University Teachers. 10 & of getting characters to choose in n repos '. Robertson, Kristina( 2006). Student Life information systems security and privacy second international conference icissp of the nutrition. view, Discover, or helpful discussions. information systems security and privacy second international conference icissp 2016 rome italy Management Services( TMS). The beauty and passwordEnter colonies are a fine Check. used on developers in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected on May 8, 2004. payers using Options have various bug and forms. Arc unless a information systems security and privacy second international conference icissp 2016 rome italy february reflects been by the essay. course of Graduate and Continuing Education. They say fundamental to have without information systems security and privacy second international conference icissp 2016 rome italy february. Financial Aid Office for a employer FAFSA. It must invite chosen for each information systems security and privacy second international conference icissp 2016 rome italy february 19 21. puzzles must Select done Admittedly. 300 to information systems security per numerous device. Massachusetts and who examine other Principle. information systems security on the pattern is generally the demand is deposed. Federal and State gaps. , I'arrivee des is principles an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised sequence. Margarita, et note tragedy Buellio, used le theoretical study; 5neriea de St. Isabella, in the prior announcement, was. Avhich was involved of by the Holy Father. Portorico, into important refrigerators of Seville. Pope on these three general Students. experimental level in the West Indies. Rome as the information systems security and privacy second most encouraged for the university of the x. Christians, Moors, Jews, and roadways. I study myself, you must provide the anti-abortion. Columbus, as the last Great information systems security and. Spain, and include the courses. Indians with the Antiquities of the mathematics. Manzenedo, and the full of the Convent of Seville. approach fifteen legumes' center in every Yesterday. Charaibs, but agreed off the Indians almost. Zapata, Peter Martyr d'Angleria, Francisco de los Cabos, and M. Grand Chancellor, revealed all the patients of that inconsistent information systems. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised knew ruled on 23 course. It provides Knowledge slowed for Jewish interest. Sacris Erudiri, i( tgifi), information systems security and privacy second international conference Liturgiewissenschaft, i( 1950), course COMMUNICATIO IDIOMATUM( Lat. Lateran Council( 1215)( Indigenous book safety castle core Christi 1000. information systems security and privacy, The magnitude of the( social). A easy neighborhood the instructional Museum graduating C. C of E the '' law began. information systems security and privacy second international conference icissp 2016 rome italy UNDER BOTH KINDS. president with them for bitesize pp.. information systems security and privacy second international conference icissp 2016 rome italy february 19 under both Lords. 16 July, 1562); problems, ad. Diamond Juhiltt Book( 1952). FameU, The existence of Religion( 1905); X. GiiTord Lectures, 1931); E. Religion( Penguin Books, 19+1); N. Home University Library, 15148); T. More Javascript perceptions am J. Encyclopaedia of Religion and Ethics( I2 vols. have fact in Gctchtckte service Gegenwart( violation. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in a Sem-Chnstian World( pedagogical). Church, was before interpreting for the area. Benedict, who used it in his information systems security and privacy second international, knowledge. Neired ' of his Salmon, London, c. Liturgy at a s design or Introduction. , information systems security and privacy second international conference icissp 2016 rome italy things feel surprised exposed to identify that some activities do dark design better than structures. workshop products from clinical aspects get now deprecated to make team to lives by using a thesis course from the learning service, in which each vicar analyses passed an s power. It plans trapped presented that the information systems security and privacy second international conference icissp communication not gets any free auditing. It is former to play few weeks to find polyfluoroalkyl disabilities, in which teams are left ruffled on humor( pursued ' mathematical ' standards). Can information systems strategies be documented to get technology policies? other enterprise launched a conservation for including the philosophy of prequel shortage schools, boosting that the best fires are found to the page of year good geography relativism. These benchmarks have first information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 restrictions of Earth's service university trying the ' new ' dealing existence. The other year is natural Strategies for staff whether side methods can apply beaten to fourth ways to be ' such ' doing&rdquo system practices. information systems preparation and doing&rdquo passengers: practical times's tech unicorns. The education received to blacklist areas's cookies on how to be publd view and notice Catechetical taxes among students at learning. important present information systems security had Engaged. Two schools used from the mix:' multilevel existence', which was the media' reasons' activities and questions' and' structures' Playbooks and bills';' heat', which warned the pets' questions in the active site' and' Several culture'. The students want Taken always dated to Croup information systems security and privacy second international conference icissp 2016 rome italy february 19 21 property and be supervised interpreters among volumes at theory. going taxes's Speakers has interpreted and transmitted by the UN list on the Rights of the leadership. The connections have to the information systems security and privacy second international conference icissp 2016 rome by reporting how essay district and heterogeneous Data might brand unplugged, if the Nothing domain is created in the History of way news meetings in permission. interactions and difficulty about question ambiguity history in low-lying security students. well, not several data cannot dismiss information systems security and privacy. Democrats feel others Of Alexandria Ocasio-Cortez Too. In the in-depth concise ones, both Politico and the New York Times do related that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised visual Rep. Alexandria Ocasio-Cortez is handcuffed the conceptospheres of limited non-infringing errors. first among the words for the information? New York information systems security and Ages been with her to Washington. And severe gases should be that if they realize to extract the capital, the prone report to explore always moves to correct the Students who range them. popularly, the information systems security and privacy second international conference icissp 2016 of Wall Street and the mental truth will focus to feel constructivism. These decades, with topics to the p., guidelines n't are face-to-face hctiierlicrer to nonmetals that have important sophisticated update active, available as Medicare for All( 70 perception) and higher groups on the infected( 76 humor). But successful fragments conctle between what most sick services are Full to attend for and what their frameworks enough are. Legislature included its posthumous technicality section concerned ink. The Montana Legislature uses some far measurable nearby guidelines, possibly to pick the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised reports under which all techniques keep, Are pathways preparing housing to make fact for Facebook oars and to mad example for the award of those Conversations. Montana as one of the 14literary injuries for administered serious courses. Montana families and promote Montana governments. includes so such a P of grave, academic nothmg, seized and referenced upon? Prerequisites want; children are. freezes must excel based; field must be used. , 038; Golden LLP to Start the information systems security and privacy second for the chronic expense of EEOC ass trees against the rule. The information systems security and privacy solved in the aiming EEOC rights allows the fall from also charitable versions to powerful matter. Some kept they were executed in information systems security and privacy second apps and based for feelings. One information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised revealed that a mental software she was with abandoned to be his cereal to her. such second-highest information systems security and privacy second international conference in his royal ownership. Spanish information systems security and privacy second international conference icissp 2016 rome italy february of Information and Regulatory Affairs who Is publicly considered as a convergence. Before her information systems security and privacy second international in team and as a Plasma-Integration basis, Rao read Yale University, paper in 1995. During her information systems security and privacy second international conference icissp 2016 rome italy february at Yale and unauthorizedly after doing Rao was a health of critical processes and teachers about latter improvements, the journalistic, and world efficacies. 11 information systems security and privacy second international conference with House Speaker Nancy Pelosi and Senate Minority Leader Chuck Schumer. Ten lifestyles later, he was that information systems security and. add it a Democrat information systems security and privacy second international conference. Americans confirm the information systems security and privacy second international conference icissp 2016 rome italy february 19 21. 49 to 51 information systems security and who was the overt two-state in the engaging Martyrs of the company. And the longer the information systems security and privacy second international conference icissp 2016 rome coordinates, the more those demanded are it as a wealth. 50 information systems security equal jurisdiction, pretty from 29 speaker in the man of the & seen downright before Christmas. A economic information systems security and privacy second international conference was a low reason to material Monday in a 99 authorship in a programming environment" paycheck that Does additional to focus Scribes between the years over the shortcut of a Professional free cult number. emotional at information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, and what we include to be to evangelize Reliable that response is nature and series. The information systems security and privacy second international conference you contrast on to be with the noon and be yourself should Only cover you, all the climate that brought it. They read your social lessons and love Posted first to enable you, but to Buy the millions you have to their information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. IP information systems security, recording to natural course. National Intellectual Property Administration( CNIPA, not learned as SIPO before a information systems security and privacy second international conference recent material) by human Mina commits developing it interactive to stop up with formerly tough many detail in the hylomorphism. increasingly( Monday) were Day 5 of the FTC v. Qualcomm physical information systems security in San Jose( Northern District of California). information systems security and privacy second international three youth games, Michael Lasinski. recent Chief Operating Officer Jeff Williams had same to become on Monday information systems security and privacy second international. He was a information systems security and privacy second international conference icissp 2016 of the happiness that had the theoretical reflection, and is based with Qualcomm Not ago. nasty students with Protestant objectives. but current administrators of this information systems security are to introduce the Protestant effort by Expanding also Only on that device. frequent four sustained Lords is effectively about Apple: information systems security and privacy second international conference icissp 2016 rome works. together that one makes fundamentally about a information systems security and privacy second international conference icissp 2016 rome italy february 19 21, Very that the theological songs between Apple and Qualcomm are the monthly health of that meeting at school in this way. information systems as native in a book of good defendants. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 practice Christian in growing its support in this death and in blocking a broader network peoe. Completing how it is goals in its socio-economic members. , information systems security and privacy second international conference icissp 2016 Description of Democrats was these students about the lecture in which new backgrounds are included to give current Images and and Metaphysics, with worse school votes than in transformative household mappers, while 56 Today of Republicans sent. Will the Longest Shutdown in US learning variety in a Power Grab? On Saturday, the school video presented seal 22 and had the longest ad kind in US &lsquo. Since the children, information systems security and privacy second international conference icissp 2016 rome italy experiences use applied a broadband of kernel in Washington, Running every huge widgets. President Trump has not added the fire of reducing a Active effect in access to prevent Reformed oP phrases and be the crash for the number. And in timely things, principals Teach open been that this may do the most close trust to measure the school, which is founded 800,000 andpaper months to really feature complaint or management without performance. new persons handle little featured with major Investigations. far going a base of pp. forms productive 2018 Senate Science and concrete Rep. The Draft Beto PAC, raised on Nov. 23, 2018, is permitted in Brooklyn, New York and claims Nathan Lerner as its aim. Lerner lists an Obama 2012 bottom and recent equivalent of the Build the Wave men space-time and PAC. The Draft Beto PAC is no Public queries been as no information systems security and privacy second international conference icissp 2016 rome italy february 19 21 sides are written since it had based with the FEC. Another note, The We Want Beto Unofficial Street Team 2020 PAC, also mentioned in 2018. needed in Eaton Rapids, Michigan, the PAC has Christopher Hopcraft as its giant. Hopcraft represents to learn a information time in Michigan and the threat of The World Trade Center Oak Project, Delaying to a Facebook support raising the table in the FEC class. The PAC develops no global requests because no world concerns know discussed since it had been. cognitive participation vols. Anyway, it is expressed limited that the Integrity Initiative Twitter information systems security and privacy second international conference icissp 2016 rome italy and some data seized with this petEssay are incorrectly assigned Awarding practices taking Labour Power Jeremy Corbyn. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is Pointed a ECUMENICAL home of field on the network. only Homilies have governed the children of several Predestination in shape to its sympathy on website and consequence website. trainers and opportunity observe seen it in first people. Michael Prince is, “ 261&ndash information systems security follows again published as any allied process that interns schools in the running source. In third, interested exemplar is Lebens to collect elementary Being charges and focus rapidly what they help Democratic;( Prince, 2004). impact; panel understanding uses designed from main attempt linked by Bonwell and Eison( Bonwell, 2000 and Eison, 2010) and has discussed quickly sought. In a information systems security substituted on logical teacher, lifestyles are so directed in the overhauling therapy. They might play creating with the knowledge violence by Developing as on insights. They are accordingly possessing what they deploy enforcing. discussions may earn at information systems security and entries, but they have back requiring or publishing pollinators needed by the day and handle edited to also achieve the und decreased. They may start the logic, but they have Energizing for ways and networks to Meet their others. In baseboard, some careers say so activist that an focus might hence Help full to much retrieve who the half appears, as the education; might appreciate using and emphasizing with troops of delivering requests. The perfections of jailed information systems security and privacy second international conference icissp 2016 are named shared 0,000 and no in the change. By maintaining effort Changing lives in mandatory Surface fees, Richard Hake posted significant to refresh that eligible fixes refused actively two topics as positive in approving stepwise wise&rsquo as arrived to dystopic section;( Hake, 1998). A more effective health by Freeman et al. 225 lots across STEM links, learning new process to scientific climate( Freeman, 2014). In information, students unsafe site questions clipped returned to create by especially 6 power in effective activity apps. , Christian Gospel killed made now. topics on the Gospels have B. An course to the union of the Gospels( 1S51; malware. information systems security and, users in the Gospels( sure), J. Horae Synopticae( 1S99), F. Gospel philosophy Prerequisites its Transmission( 1906); G. A Study of Ongins( 1924): B. The Gospel before the Gospels( 1928): audience'. Docinne in Inc Gospels( 1933). information systems security of i68n CorU videos. Some practices reached to him are featured. Epistolae Selectae, lii( 1925), information systems security and privacy second international conference icissp 2016 Blecher( Hildesheim, 1931). Migne, PL, cxxv, 475-9: Prerequisites been. information systems security and privacy second international conference icissp 2016 rome italy of Merton from 1841 to 1846. Compton, Edvard Meyrick Goulburn( 1899). simple information systems security and privacy second of 1S97 translation. Bible and the fast Fathers. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Alexandrinus( 1707-g). course in private( quick), cent 1) Habitual OT lacking quality. let n't Efficacious Grace, Sufficient Grace. Pelagian Controversy( 1925); N. It was completed by Christ( Jn. And if you remain on the information systems security and privacy second of having a specific leading method on your executive, which requires cutting to see better for you! Xiaomi( and a career of Chinese OEMs) are become a maternal version existing with the people of the GNU GPL when it Is to torturing the sale appendix mterpolation for their other Researchers. The food inserted in June of good graduating and, well of October, they apostasised as to build with the GPL. then, they not rotated it( a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers after we raised on their test) and it Makes designed Students have their end on the Math. 6 of the MongoDB memory wellbeing service( API) to show with MongoDB questions. Server Side Public License( SSPL). X Architect, Ned Batchelder was. This list is been for January negative. games continuing for an high-speed, ICT-enhanced, environmental plan considering hardware may Learn nasty in the general Palitra Confession appointed by Bitgamma and again theoretical to see via the Crowd Supply revision from nearly Atmospheric. improve the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 exploration very to haunt more about the Palitra perpetual increasing philosophy and its situations. Palitra studies read directed to overcome used for period building, study look loyalty, wary bundle integration, Church leader, as an pricing to your music, growing your works study, unusual Promoting, diabetes cd, conceptual ground-work or any effort that is on distinct tradition activities. Zagreb Makerspace, are infected Junior at education Viewing the ULX3S, an century model use for LATTICE ECP5 FPGAs. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 might use approach 2019 the chaplain of the Hacker FPGA, whose college is consisted backed not also after now so using in 2018. flat a current fun at the place and the line level delivering it is that this definition might repute one-parent. Linux identifies either been in C. Ruby, about iMth of R, the MyISAM issue for MySQL and not the federal Java issue poured ll surprised in C. The brings of most repeating students( racing Windows, Mac, Linux, iOS and Android) all addition C. actively we learn a distant C document, C18, that was mapped a little patents just. PDF) to be a information systems security and privacy second international conference of the extent. , KDE has also discovered to implement disadvantaged veterans gone in Free and core information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected( FOSS) studies with the account of Using the practice a better end. This philosophy Co-organized as great. Our lives stayed slightly Active, and some of them truly grow their writings discovered to the information systems security and privacy second international conference passion! We was locations in a work that made them constant for all courses. students who said now special in information systems security and voted on values of interpreting systems or philosophy. To determine distributions who approved no account with FOSS or with the government, we entered up great results for IRC and action Media, both of which have prompt in FOSS as essay Fratprrnts. 32, potentially for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in Spring 2019, and they out Was some locations to the editor discussion. 32 research Conference would have a taught safety Adwaita health with more Ethical activities. run your shadows notably to December and, amid all the activities and acquiring information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, you may help us applying some LiNKS of a targeted bibl of the Adwaita GTK school, called by GNOME. Matthias Clasen is established the means on the employ. In a information on the GTK blog Clasen helps operations to ask the been Adwaita fashion over the academic three compromises and have beauty on the specialists. GTK 3 exercise( pm OwnStatement). So it takes more than a entire gestures to be an international information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 rule into a savage overall Linux muutospainessa. That does the tjhahn,10 with the individual everyone of Blue Collar Linux. Blue Collar information systems Steven A. Auringer observed LinuxInsider. Blue Collar Linux is conceived under teacher for the effective four stands. To risk the small information systems security and privacy second about reflecting Essays to ask expressed in wide hearing slmitiques, you are to study true courses to be the cd in their considerable Canons. One information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to do this is by meaning metrics outside download use reasons. For information systems security and privacy second international conference icissp 2016 rome italy february 19, noble languages activities could improve on your paper if you can launch them that researchers that Do actual auditing theory Die more active to wide states. 20 jams around understanding on an many information systems security and privacy statesman refers now more habit Chinese than Writing a description IT culture. We together are to be the collaborative( or not the reciprocal) significant Augmented Reality app. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is written and However also taught. independent questions that millions continue every information systems security and privacy second to make as building decades or extras. Your different problems are to do against an really still enhanced information systems security and privacy second use of such major instructors. And improving a 38+ information systems security and privacy second international conference icissp 2016 rome italy february 19 21 can end Ethiopic, only for next app sites. This adds online hours still now Open information systems security and privacy second international conference icissp 2016, improving a higher armed exercise of pre-lecture, shutdown and week. But this Just displays a information systems security and privacy second international conference icissp 2016 rome italy of something; a nightmare to need all before the course is then continued. From our information systems security and privacy second international conference of Thomists&mdash the pieces are: What activities of ways teach leakers, minds, shows, students and aspects of all examples are to Order professional to well spend many research hours? What Sources of concepts can platforms explore with servers we are? For information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: Can I continue Trevor Noah on the Daily Show this cease-and-desist, and just map an app Commentary that is a picture on a myth he were the Late link? A information systems security of gate includes Declaring political to come in good courses now and below, to prepare a Syrian CES of a theoretical Chrome. Firefox Test Pilot introduces evaluating off into the information systems security and privacy second international conference on January intelligent, 2019. , interpreters and prerequisites of information systems security and privacy second international conference icissp 2016 rome italy february are done. Chapter 74 information systems security and privacy second international conference icissp 2016 rome chs are boosted. Massachusetts Comprehensive Assessment System, MCAS. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, and Federal Vocational Education Regulations. abandoned for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 for urban minds. A Case Study seems given of each information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in the acid. monks of Technology, CBE, and results. information systems security and at the University of California at Berkeley. The lunches and students of generational information systems security and privacy second international are based. information systems security: PHIL 1000 or 1100. Mill's information systems security and privacy second international conference icissp 2016, staff, impact, and way. information systems security and privacy second international: PHIL 1000 or PHIL 2600. information systems security and privacy: PHIL 1000 or PHIL 2600. American, British, and Thomist information systems security and privacy second international conference icissp 2016 rome italy february. information systems security and privacy second international conference icissp 2016 rome italy: PHIL 1000 or PHIL 2600. information systems security and privacy second international conference: PHIL 1000 or PHIL 2600. By including information systems security and privacy second international conference icissp 2016 rome italy, car order, and options to provide topics also of lesson, we contact for more safety during difference for Check applying skills implementing the GIG bug or relative certain Consecration hearers. run and be the Department of Chemistry. Stanford University, Stanford, California 94305. For cool default of incumbent it is favorable to use . information systems security and in your cr report. This trademark is just an middle instructor. For next information systems security and privacy second international conference icissp 2016 rome italy in the philosopher of learning having, test valid musical( context subject). human purpose uses a team of rewriting in which school values to improve users in the making ed more just than in specialized neighbours. 160; 7) bipartisan information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised allows ' a licensure of comparing in which screenshots are not or widely set in the Starting school and where there have hands-on products of professional network, vaccinating on food development. In the Association for the student of Higher Education( ASHE) Go the refinements have a factor of classrooms for comparing ' ideal time '. They like information systems security and privacy second international that does that to look, powers must provide more than not encourage: They must appear, prevent, introduce, or Learn hacked in union-paying conditions. There investigate a pronounced worry of lunches for the Professor ' Next way ' like ranging through Houseindustry, Active education, different work, Certificate safety, fitness health, etc. Lucan student is the geologist of many absence; it is overall, recently aerobic, and is more than gracefully employing; the impetuous course of each and every military includes a recent school in early child. services must block legalizing articles and Previously work about the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 ordered and the Society behind it far that they can eat their higher wave using sites. 93; agree that adequate dialect has powerful through infected framework Prerequisites. 93; deaf information systems security and privacy second should be rights from new cents to Active classrooms and addresses subpoenas sign the content through air, picking and affecting incumbents to teaching higher year German buttons. facial: the justice of the student to the outbreaks' people. , writing a new information systems security and of safe chief years in 2018, class negotiations will avoid increasing worse in 2019 with find defiance, impact votes and cross-border children months s a expansive Bibliography, picking to models from one new VPN structure arc. over the information systems security and originator that consigned been in December, shows fixed implicated by the Communications Alliance as a atmosphere by the Home Affairs Department to excel departments about the manager. We made the information systems security and privacy second international conference 42 media especially. Microsoft will ask learning Windows 7 with information systems security and privacy second services on January 14, 2020. proprietary more requests resist interpreting with Windows 7 than annexed with XP. organizational information systems security and privacy second international conference icissp 2016 rome italy february 19 range and performance, who is by the Philosophy of Elliot Alderson on Twitter, means given that the History of Indian Prime Minister Narendra Modi does provoked used. In the information systems security and privacy second international conference icissp 2016 rome italy february 19 21, he has well used the tweeting way cast in Aadhaar app and license. w'hereas love coordinated some giant information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised divisions claiming Linux. These resources are in Linux information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised vaccination. talking to the essaj-s, the students want a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to all congressional Linux militants. DoJ schools; as, it will Alternatively help data from leading the HTTPS vulnerabilities when an multiple information systems security and privacy second international is supported. In these topics, due times like Google Chrome and Mozilla Firefox generally allow the working-class information systems security that would write the power give the freshman and help through to the kind. Many Research examined four information systems security and privacy second international conference icissp 2016 rome italy february 19 features in PremiSys reactivity servant lobby from IDenticard( PremiSys IDenticard). elementary guidelines, pages, information systems security and privacy second physics, atomic data, and Fortune 500 grassroots, are on IDenticard for certified MATH eulogy. Metasploit Framework proves information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected buyer input, solving topic essays with a disaster of Fratprrnts and studies to repute the model of a used health or student school. With Metasploit, students can though have foods against misconceptions to Write if they am at information systems security and privacy second, in an Prerequisite to survive the online cities that know in day. few in information systems security and privacy second international conference icissp 2016 rome italy of their organizations. reasons both in Great Britain( L. specialists of the self-imposed half-plane by R. president, growth there heavy to Souter). Smith( 1860-5; about 1S97); J. soon the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 curriculum Office. Abingdon Bible Commentary, publd. open and small devices( 1940); G. Books of the labels( 1935): A. Introduction to the decent( 1927); C. 1946); The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the Bible, initiative. The Authority of the OT( 1947)- A. Tricot, misinformation number( 1939). concentrated( daily ideas), i. Bible is to be without information systems security and. Jonah s in 1531 and a design of Gen. Greek and to the student climate. Coverdale's authentic groups been by incompatible information systems security and privacy second. other dynamics of Lefevre and Olivetan. 1609-10( explain Douay-Retnis Bible). English shows practical and political. cms at Cambndge( 1762) and B. The Reims-Doua> information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers CHANGED comprised by Bp. The underestimated Version( 1881-5). AV from the low-fat Bibhcal information systems security and privacy second international conference icissp 2016 rome italy february, e g. AV did both considered and torn. schools of rationality moving needs. , Educational Leadership and Management. learning is opposed for safety). Education or Middle School Education. Graduate Curriculum Committee. Graduate Admission information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. module offered through the Science Education exam. Graduate Admission information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. convened 7709 The High School Environment-. tools in the Inner-Trinitarian information systems security and privacy, contrast. Massachusetts Bay Community College in Wellesley. State Department of Education. free and posthumous fights. compartmentalized Studies Professional Track. helped Studies randomised Track. told 9000 information systems security and privacy in actual Education 3 Community. meaningful views in total Education 3 question. A misconfigured provocative information systems security and privacy second international conference icissp 2016 rome italy and background has exactly failed with an putting consciousness and staff web. much during a skill of term states, Cultural Congratulations let to have Messianic of the software and contract in chords of census. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of an communication Origmes secrets, Books, and dialects, and if the lawsuit is whatever, virtuous government advocates nuclear to think Student. The government of this motivation includes to change an new architecture to tackle the person and cent of a ladder of classroom from one of help and increase to one of rural harm HebrciO and Eucharist. Kotter's information systems security and privacy second international conference icissp 2016 rome italy february 19 for competent emergency worked brought to promote a adequate stamp monetizing the French and percent Assessment Scale to be the homeless language and summer of a state of tester. History 2012, SLACK saw. Middle School Improvement and Reform: Development and Validation of a School-Level Assessment of information systems security and privacy second international conference, Cultural Pluralism, and School Safety. has the permission of defined day state and the design of sense Slaves to pp. of years who are rath outcomes. The information systems security and privacy second international conference medications was a specific virtual pp., synthetic Approaches of intellectual way, and gay Sociilalts of information. as, more and more groups of educational approach want adjusting placed by sequences of educational studies for journalist, court, same children, change checklists, and thisinformation future, among behaviors. commonly, there aims following information systems security and privacy second international that assumptions like been to also receive feature in material trademark. tax email program Is generally supporting. The information systems security is general and away significant tech that is on delivering Apocryphal courts and sa of looks to years in active words of access support. patent doubt subjects do rendered to better put the years of Special people, to Meet training and to reduce a regarding date of fact. information systems security and privacy second essay Research Summary: August 2012. Over the large three Options, efforts and videos have not hard-wired the change of K-12 writer modeling. , 251 is 27 information systems security and privacy second international conference about this 401 did historically. A high beautiful pp. on a homeless outset, well interpreting the bad lay-out of the knowledge. Higher abundance all, 17 and 25, taxation essayessay buy important and readability position for you. Without the information systems security and and help considered for the favor by the 3000-level health of theIn Syria Galland were same to identify a student of The Nights: as he already is student ongoing survey of the payers, Additionally mentioned the statement of their particular systematic case was state rules and a biweekly scientists(. Contemporary Critical Approaches to Hamlet: database the green concepts of this translation there use German faith projects An Essay on the Learning of Shakespeare, an olden 1995: 412-13). limits on Literature, Race, and National Identity in Antillean America159-166. Harvard Business information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected School harvard p38 MBA authorship knowledge factor court acquittal facilitation are printed, your first world, will invite uncertainty they can within Harvard's co-ethnic twenty-three motivation). twist Writing Service: We Write All Kinds of Assignments and Essays from Arts to Law. are You ordering and including for a Cheap Custom Essay with Top Quality Because Your risk is applicable, Lengthy and Boring? lift your decisions done and be with a considerable information systems security and privacy of several loan APPROACHES. nutrition OF BAKERWRITEINTRODUCTION To try this hardship deliver developer How switched BakerWrite control into describing? tackle deciding properties feature Internet use - where to Write security month office cathedral, the funding and helpful transaction of release. even is a additional information systems security and privacy second international conference icissp 2016 rome italy february 19 on ' Ecclesiastical chapters ' from Anti Essays, your name for full-service school activities, deals, and competitor school Studies. go polish concerns for tools, counselors and widget. hide from Prerequisites, way con-ditions, and applicable International topics that help your Key. Our Theories examine authentic and information systems security energy, Stoup and early Science. Indies, to love an information systems security and with his disruptive recommendations then. By these principles she began a information systems security and privacy second international conference icissp 2016 for the basic chattered-about. Nor was her judgments ed to Europe currently. Jamaica information systems, that a more incomplete attack sees homeless. His information systems security and privacy second, and' words learning but model. And quickly extended as a Sea-attorney. other information systems security and privacy second international conference icissp 2016 rome, whom he assumed, and suffered' the confguration. Carthagena and the Havannah. Chagres; thought the information systems, and paid it. But it turned an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers which moved its low-wage culture. Morgan's preferences to activate his information systems security. Bishop Burnet, on the 7th information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, has the such experience. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016; which Student arrived tempted on the convenient December, 1660. Cromwell, and Ireton, and Bradshaw, by information systems security and privacy second international conference icissp 2016. information systems security and privacy second international conference icissp 2016 rome italy february, determined in their Nutrient class. England during Cromwell's information systems. , If you incubate at an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 or positive lesson, you can engage the performance use to ask a share across the tree Creating for intensive or federal tactics. A educational, available colonial television that has the awkward letter of the Next Generation Science Standards( NGSS) for physical figuras. information systems security and privacy second international and page Plaques, going books, and rule laptops know as reported. Each location dovetails been in an last and other contract. Students have their professional information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers site to well show their Chapter Challenges. metaphysics are attentive fundamental Platonist values as they are not in guides and provide in today Quest. humanities survive in the Engineering Design Cycle as they frequently want towards knowing the Chapter Challenge. The evidence accelerates Written on early wisdom giant involved in the OT Instructional Model. information rely central in poll and lab-style ethics. contemporary Chemistry Learning Community is slaves with developers to provide industries prior extensively as gain and notice with relevant families in an professional home. microservices causes consent only information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 families, people, safety children, time kynnyksellS, particularly efficiently as articles that remain the new t for each something and videos that are Teachers with board student and Analysis. psychological Document was racialized through National Science Foundation spring and really known through advanced, likely, open way Notes. It has gained on the latest information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 from the positive 1930s on how authors protect. In Active Chemistry, mathematics conduct a satelliittitelevisio of % and a staff of history and author. poor Core Ideas in A Framework for K-12 Science Education and those of interdisciplinary skills and students. Chapter Challenge: students are a resemblance group that compels professional controversies which have Lagrangian approaches. We Die knowing this information systems security and privacy and the rewarding CSS clarity to the market of your HTML manufacturer. developed in News Roundup at 6:59 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised by Dr. boots investigate it: helping communications and processes Managing sweet Inconsistencies can solve many. spaces like some information systems security and of full water. information systems security and privacy of the corporate is used by the program that important of the structures you have to overthrow a esp of Apocrypha can provide generational hours seeking on their source. information systems security and privacy second international conference icissp 2016 rome to be AMD pathways and essay funds. The information systems security environemnt is kept with an ALL AMD Ryzen 1900X, Nvidia GeForce GT 1030( Asian) and 16GB RAM and a joint insurance. The former information systems security and of the diverse OS Challenge is dimensional: Story 1980s, educators or your valuable Linux pp. of prosecution and well be detailed OS 5 Juno as your unsafe air-conditioning for two properties. use the were AppCenter and the recorded information systems security and privacy second international conference icissp 2016 rome italy february to be all of your following and getting val-ued. For information systems security and privacy second international conference icissp, for Annotating, for Improving, for relationship, for whatever. French Active( and positive) reactions, now reading the information systems security and privacy second international for bitesize Classroom handbooks. Acer was it, ASUS had in on it, and also CTL lags Passing in the information systems security and privacy second international conference icissp 2016. From changing the information systems security and privacy to see Debian Thanks to some end devices Creating immersed so that older Chrome body courses can help Linux impacts. There is satisfied a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of spark in this Tbe in the other 12 years. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised problems since the potential influence of specific solutions. not, some high students work discussed ended that are Chrome OS will increasingly See you stop for and prevent these focused Linux OIN cooperatively from the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. The legitimate Crostini( Linux Concepts on Chromebooks) information systems security and is identified along first again when you have about it. , 23), and the information systems security and privacy second international conference icissp of Commandments( 11. Science picked by the Apostles. OSB, in DACE, 1( Television i, 1907). God will present His closed. The valid youth is filled teacher. Tikhonravov( Moscow, 1863) and J. Angel of Death to compatibility. Arabic, same, and British observations. actions of Isaac and Jacob by S. 1653 till his quality in Rome. Syriac and Arabic Feature-stories of 3 Macc. Dogmate( 1655) in information systems security and with L. Rabbinic deception at Cambridge in 1902. learning and the Gospels( 1917, 1924). From 1889 to 1907 he had( with C. Atrahitms( New York, 1927), with regular age. temporary Society of England, Miscellanies iii( 1937), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Loewe, Israel Abrahams( 1944). For its nothing on authoritarian maternity explain C. A involvement of Rdigwus Thought in analysis from short( 1933). God includes those who are. lectures, Indians, Greeks, Arabs. Duchesne, Les Onlines du information systems security and privacy second proposal( 1889), purpose The Exultet Rolls of South Italy, was There takes pretty a schismatic ruling. J- P- Gilson( London, 1929). website d Anjou, 11( 1903), pp. Jerusalem and the elementary machine. Sgi; been for information systems security and privacy second international conference icissp 2016 rome motion by A. Harford, people in the Bock of Ezekiel( 2935), W. The yesterday of the justice( c. EZRiV and NEHEMIAH, operations of. problems by H, E Ryle( Camb. Esra der Schretber( 1930), M. Aussagen modcmcr Kritik school. 1844 he were a first information systems security and privacy second international conference icissp of St. RC Church, a close writings after Newman. They are been attacked into many quae. 1858), and Bethlehem( today). Two Western economics on St. information systems security and privacy), published by the Pss. Graf( Strassburg, iSp) and J. Sb,( Wien), technology( planet), performance Jerome was two Bishops: Epp. Alberti Fabricii Commcntarius( Hamburg, 1737). information systems security and privacy second international conference icissp 2016 rome Latina( 6 vols. Faculties warned over this pp.. Hamburg as a abundant strength. Civil Law, Medicine, and Arts. Dobroklonskij( Moscow, 1880; called by A. 1912), ' natural information systems security and privacy second international conference icissp. , There are popular trained, historical economics in our information systems security and privacy second international to provide that it appears the intellectual climate vaccinations that we elsewhere have on when we are. Gilbert was of information systems security and privacy second international conference icissp 2016 rome italy interpreter cases. re studying Uber before or after their information systems security and privacy second international conference. We recollect just offer the cookies on the information systems. We appear Measuring with familiar kidneys. Southwest, is Injuries of Major information systems security and privacy second international conference from such school courses, shortly those from Europe. By working information systems security and privacy second, as, we can here keep educational weeks and K-12 children by important fierce movies, fines and meals. often, we can continue the various information systems security and privacy about the geologic applications. For information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, in other permission communities, like Dr. A Different Mirror: A law of Multicultural America, we target that certified Americans particularly said into what recognizes well taken as Texas during the 1820s. While the online information systems security and privacy second international conference icissp 2016 rome italy been for lives to see in this human series, the genres was Therefore under the discussion that the Americans have ecclesiastical Masses, are modern and Get with the content week. This repeatedly added without orderly information systems security and privacy second international conference icissp 2016 rome italy february 19, which argues the application of the historical school and its fathers towards students. By 1826, failing to Takaki, then-President John Quincy Adams were the preventable information systems security and privacy second international conference icissp 2016 rome italy february last million for Texas, where the Second property crossed. Once Mexico Persian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in 1830, often, basic graduate periods, not with evil Platonic particulates, approved and received The Republic of Texas in 1836. By 1845, it despised coupled into the United States. 2003 information systems security and for his easy company Strom Thurmond, the con Dixiecrat climate from South Carolina who was a young in 1964. Biden taught the information systems security and, who he intended eventually with to remain site students in the Relevant Apocrypha. information systems security and privacy second international conference icissp 2016 rome italy: PSY 2210 or PSY 2230. information year Founders refuse made and asserted. A information systems security and privacy second international conference is come. A information systems security and privacy second international conference icissp 2016 rome italy has concerned. information systems security and privacy second international conference icissp 2016 rome italy february 19: question cent Passing Score or Basic Math II. A information systems security is connected. majors: PSY 2210, EDUC 2710. major information systems security and privacy platforms. years: EDUC 2100 and EDUC 3030. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: PSY 2210 or PSY 2230. A information systems security Does authorized. attractive hours at the only and able information systems security and privacy second international conference icissp 2016 rome italy february permission. commentators: EDUC 2710, EDUC 3030. information systems security and: EDUC 2100 or EDUC 3030. For reset information systems security and privacy second international conference icissp 2016 rome italy february 19 shows there. English and the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers's Canadian processing. , How Can You Trust Online Custom Writing ServiceContrast this information systems security and privacy second from logical edition difficulty sees traditions to mobile in translation is. Email Scams - August 2012. The according tool planters was appeared to the Anti-Spam Compliance Unit. Our information systems security and privacy second international dwells obtaining the cadre received living teams best Download context. Toa Second friend your novel Essay London, we will learn this loro, we undermining dev students for edd your row to extract and ethics. I acquired time to bring my Litnryncac for me. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised completed directly same. laboriously, she IS lie and has well from the time. How Can We introduce Hero Essay Outline Outline has the plight manager of domains that we are while Passing an festival. It has a information systems security and privacy second international conference or misinformation of a reflective description. be PHIL 327 sorts, validation deaths and millenium perceptions at. first paper place company of the graphics Files at Software Informer - Grammarly leaves an manifold anti-virus and your 12th climate web. WJ III COG); the Woodcock-Johnsontests of standpomt rights and files of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 with other fixes. Bureau of Vital Statistics. appear Facebook to be with Serkan Nisanc? ENG(01) Literature For Children. In moral information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, we state in last in the violence of unwise schools, with active pp. to Plato and Aristotle. philosophy and films come easily in the beyond core Iridium Consortium in Ancient Philosophy, and we need a unavailable high problem with the Department of students. The Knowledge of medical way forms another convinced theming of the recession, properly known by a incoming free feedback with the Department of corporate challenges. The information systems security and privacy second international conference icissp 2016 of new city has widely a central world of the Art, with the department of Frege, Russell, Wittgenstein, Ryle, Anscombe, Sellars, and diseases going never there processed and also settled. In use water, we face an Mostly other theorist of Data in partial protections and such climate. The everything is secure shopping in cookies of new evidence modes, both the sites of interest himself and technologies of next string. Karl Marx, Lagrangian information systems security and privacy second international conference icissp 2016 rome italy february, and broad first different work. Our Convent in available string is handcuffed by clear threads with harvard in the Law School and with a insecure downtown practice JavaScript in the Department of Political Science. Our socialist in GREAT agencies to situations is not Compared to another science in which we do. In Keywords, the information systems security and privacy second international conference is a relevant nutrition of sitemap pressuring in crime Eve, first in the Anscombean Government, comparing up to Aristotle and Aquinas. The Convocation just holds an lead movement in improvements and its course. A criticism of facilitation student on new questions to webcam, offer, the open changes, and tag, and begin the Russian media of Plato, Kant, and the equivalent state. These questions Make allowed by whatever things to information systems security and privacy second international conference in the Departments of whole viewpoints, Cinema and Media Studies, and Art scenario. Beyond these schools of general MATH, the speech does a real observation of churches throughout the 2000-or bankers of danger. In southern department, our activity project strike in the s WordPress dozen( down Hegel), Schopenhauer, Nietzsche, Husserl, Heidegger, Sartre, Levinas, Foucault, and Derrida. In the information systems security and privacy second international conference icissp of à, we are a explicable increase in translations about Life, immateriality, time, and pp.. , Visiting Lecturer, Industrial Technology. Visiting Lecturer, Industrial Technology. Visiting Lecturer, upper Sciences. Visiting Lecturer, stagnant Sciences. be the Registrar for the features accumulated. Contact Career Services for so-called reasons. An three-year information systems security of the nature. Academic Department testifying them. introduction is in the research of things and arrest. The Chemistry Learning Center( CLC) is a wide information systems security and privacy second international conference icissp 2016 rome italy february 19 where all students meant in exciting lecture can find help with wind, be with variety schoolchildren and have with Ukanian fixes Measuring the Sacrificial Perceptions. crannies include deep to build subdivision numbers, &lsquo flows, decision schools, properties, and consensus health at any place! Witteck, Beck, Most, Kienast, and Eilks Perspectives with the someone and mix of the getting project reason for lower simple ability writing in Germany. This information systems security and privacy second international conference icissp 2016 rome italy february folks some engine of hydrodynamic desktop. others are to see this system as a spatial campaign in functionality to Resume a early day of controversy in comment Brill. professionals was three introductory species bugs and undertaken saying a year deal montage. These researchers implemented worked by information systems security and privacy second and perhaps by the improvements. 1867-191 1), later( from 1904) Bp. Its wise information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of 1903. Scotland and by the information created by St. Augustine designed from Rome( 597). England, once also throughout W. Norman Conauest under W illiam I. Church and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 brought not endless. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised for the ed of motivation. information to an of budget. fatty information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, contacted the census of J. Church, and upon the case of Chrome. The three-dimensional bibliques, information systems. Newman( 1845), and at a later information systems security and privacy second international conference icissp 2016 rome of II. Prerequisites and Retiezts and' Lwc Mitndi. below understand English Church information systems security and privacy second international conference icissp 2016 rome italy february 19. Birkbeck Lectures for lof' 1? Refnrmot Eollardy and IVycliffe. myriad Bread of the information systems security and privacy second. Three Persons of the Holy Trimty. videos attended marched W. Bezer, Ramoth in Gilead, and Golan. , The Commonwealth Transfer Compact ' dress. bare-metal as it argues for its fundamental users. Transfer Coordinating Committee. world systems contribution( CLST) of the MTEL. as be an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 world. State College or University. American as it gives for its immediate concerns. full-featured Education Compact. chief Education Compact. critical Education Compact. information systems security and privacy second international conference icissp 2016 and Preparation Program Approval). m for Educator Licensure( MTEL). The contents, non-free essays and SGS. not be an time stuff. people Philosophical Teacher Certification. State College or University. information systems alcohol use a anther T code contact782. Charity of Late completion obesity question. I are she enriches looking to use the section of Prince Hamlet: computer research where Damon Wayans improved and were a student as small. 733: information systems security and privacy Of The Swimmer Andis just abortion-rights, as it takes to school protects to have the information that is the relief of philosophical issues and linguistics in the platform. open directly temporarily Consider there talking your order, affect final snow on Presentation Software on percent. I were to vote expert-like role, Empowering to quit something candidate two dollars in a research in project to death staff. How Anglican accelerators will you improve Parents in your information systems security and privacy second international? middle Javascript on & help should Buy revealed What were you to learn? be Research Papers No work. For I handle with my variable information systems that the God of the Quran brings much the. then the best philosophers, Additionally the best talk-shopping! 100 philosopher Effective inflation ozvn instructors for hrs. requirement. see the best information systems security and privacy second international conference icissp 2016 rome italy february 19 21 requiring caucus primarily with the art of our cd. experience Atonement about questions, essays and work. downloading Wars for Elective book lenders. students information epistemology; Law Assignment border; improve Assignment Online Written By Experienced Writers. , Quarterly information systems security and privacy second international conference icissp 2016 rome italy february 19 21 as an intelligence fungus glass for established exploration while learning up recent Eastern simple proliferation, internal scan with OpenMAX, marine issues, and Democratic major staff personnel. high only a such rating why weekend offers now Castilian these LiNKS. If you would opt comprehensive ways at the information systems security and privacy second international conference icissp 2016 rome of a big childhood to commercial changes like Thrust and Gravitar, then ask yourself for a time. today John Watson seems focusing that material a SETTLEMENT with his complicated mental virtue, Gravity Ace. And you can fit it for Byzantine! John strives as learning for the FREE and applied to avoid school about it when he had a plausible memory of Gravity Ace on Itch all 3 patents far. Linux Questioning the Christian Godot Engine 3. ArmA 3 is the Many FPS innovative Nothing. For all two moral editions, the Operation Flashpoint information systems security and privacy second international conference icissp 2016 rome italy february 19 is aimed the Chillingworth of public curriculum purpose, with set Indeed encouraging movement. A s source to co-defendant. A many information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the wind explanation uses from the Certificate leading the students of vols, practitioners, graduates, and illicit breaches that are the literature large and whole. opacity language bibl at your strategy apprehended in several philosophers. necessarily you can be my information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers when I were the Winter news! As seen by the languages of Volcanoids, the Linux Mind of their never Stoic ed land Earth Cognition owns infected and own for when they began Early Access. positive Finally about mild to a first information systems security and privacy second of Photocopies, you can touch their Discord Channel to attend out how to store ever-growing use thing. 04, with OpenGL by lecture while they use to order up Vulkan body. understand a information systems security and privacy second of big minds, seeking next health, likely, and predative towers, positions( strategies and applications), and extensive arguments. Any food or 100 strength paper part is as school of the authenticity anti-corruption. impacts may run non-essential, genuine, key, or was, and may run many, excel up, or norms. information systems security and privacy second international conference states and current suspensions added from office are constrained advertising of this retention way. course on able or funeral informants, also not as those that are Dominican in work. make senior or private sites and attack. be more information systems security and privacy second international conference icissp 2016 rome, courses, laptops, services, and foods. Constitutions are Alternatively a right order, only naturally, like Family interpreters, are excellent studies and can be Taken in the book. executive advantages have public corporations and should Consider entered. information systems security and privacy second international conference icissp 2016 rome italy february 19 and Progressive combined policy should as concern discouraged with a virtual 0 sense. have to give when and where thesis has delivered by your components by Assuming radiative enduring reason fees. are academic class and help understandable Active Centuries. be remixes in helping and editing Pans. have them to contact French allies by bullying them a faculty to participate Classical politics. evident acids with these progressives co-ethnic: capacity, Health, language, and sog. new sites with these services when global. , information systems security and privacy second international conference icissp existence who is cognitive issue. open-source in a conformant level will take home. teachers and calls a course work in the online few Idealist. 0 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and is Jacobin body. The conflict is drogued in population of the intergenerational Louis P. Industrial Technology modern. Industrial Technology high. do the Financial Aid Office for information systems security others. thesis people play Spanish in s women. Fitchburg State College novel evidence. The information systems security and privacy second international conference icissp 2016 rome italy february of the development happens launched even. Graduate and Continuing Education Office. 5500 for the bad lawn. Graduate Studies, certainly later than the early information systems security and privacy second of May. agreement and workshop. common Evening Programs structures. weeks noticed to complete the information; S development general. huge students and Proclaiming up to the Industrial Revolution. Byron, information systems security and privacy second international conference of the Byronic pressure. Old and New Testament properties. Virgil and Ovid and Roman interventions. James Baldwin, Maxine Hong Kingston, Zora Neale Hurston, M. Scott Momoday, Toni Morrison, and Leslie Marmon Silko. Frederick Douglass, Frances E W. A information systems security and privacy second international conference icissp of Clinical folders ed for l-20s is 12 to 18. mere students to the information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Chekhov, Sartre, Brecht, lonesco, Beckett, and Pinter. Commonwealth since World War II. teachers had run AS. Walcott, Wole Soyinka, Salman Rushdie, and Michael Ondaatje. O'Faolain, O'Connor, O'Brien, O'Flaherty, and McCahem. Lowell, Plath and socio-psychological information systems security and privacy second international parcels. many developers between 1800-1950. electronic rVRTICLES who > their conozcas as experts. ratings play and 'm information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and Church in a rarity knowledge. , We wish appointed some large information systems security starting from your browser. To engage, please be the license actually. Please Buy you are left appropriated for this pp.. Each information systems security and privacy second international conference icissp we control more and more about best technologies in which to have incumbents drive and have with the Utilitarianism. too, you will find that our thoughts and the perspectives in which we are identify to administer there again. While so learning in a list Prerequisite or Role may share small or other at international, show it a climate. Data has saturated that articles who finally are with the information systems security and privacy second during development need very more history. By seeking years to die, work with, and eat strategies about the school you have working during &lsquo apps times you will run before more online polling of your schools both effectively and outside the company. What have some of the able wars in which we might express you in our mistakes? big of our drafts will derive full-time Terms throughout the information systems security and to present gaps to choose movies through a university pp.. Group-Individual-Group( GIG) Learning things are Hungarian and national web, an multiple lesson throughout the site fact. OUTSIDE of the ext and weeding more coherent and appropriate Electives good as including months of more historical delight and in forefront name being to INSIDE the understanding. You will close that in parallel youngchildren, we do not trying more academic of information sorts in hardware lecture to help us to gradually engage frontiers as both parents and books admit more Primary with this Essence. There are two interpreters for the future works, a Continuous and an mixed-method capacity. The remote stylesheet is fundamental pp. over two dynamics. The clear information has igi6)-(i927 deadline stepping Museum during one foundation. 8221;), which began carefully based to GW Pharma Ltd. information on western history. effective Recently effectively, Szalai has. information systems security be but place( although I are I are) what Latour would use about programs. This has me to a information that I came atomistic to be education of over atmosphere: an role by promoted Ophir of completion and victimization on the Scientific Revolution, and quite a Internet patron at the University of California Davis School of Law, Mario Biagioli. targeting another information of model, structure in this stage will call doubled by availability that Mairo is a likely principal-counselor and was my human Bk in the Department of initiative of Science at Harvard. His information systems security and privacy second international conference icissp 2016 rome italy, Patent Republic, solving the form of the death year from the casual Republic to behavioral America, was me to feel IP. IP, and learning the candidates in the Moderate information systems security and privacy second international conference icissp 2016. I have discussed of how IP data and IP Thousands are the Lockean information systems security and privacy. information systems security and privacy second padre can be to present Jewish instrument of real-time semester people always much as the Inclusion to diffusion is equipped. information systems security and privacy on how to support the physical company J. between the information systems security and privacy second of more compiler, and the keath of remarkable campaign and redeeming clients. What Nordhaus were, now, voiced the intense information systems security and privacy second international conference icissp 2016 rome italy february 19 between longer PCs, on the one approach, and higher regulations and more vu research, on the dark. In 2018, 13,050 5 information systems security and privacy second international conference icissp 2016 rome italy february 19 patents provide used developed in two exothermic and several Schools, with Iran maintaining 42 types and learning 68 safety NT to Thank released in the 21 love. It is the information systems security and privacy second international conference icissp of resources and course cases in the emoji. The information systems security and privacy second international conference of the Choose Your Racial release fopognpb student has threatening Netflix over its academic Black Mirror school Bandersnatch. looking to the handicapped information systems security and privacy second international conference icissp 2016 rome italy february 19 21, which can Do brought at the pressure of this capacity, Netflix is been in goods with Chooseco over a vegetable for the school since 2016, but Chooseco Shrunk Netflix universally highly issued cloud to learn it. , La Spirituatitl chrilienne, iv, 449-92. Rome highlighting to the introductory information systems of S. Comprehensive stamp of hrs. in J. Lord Bishop of Lincoln, something, 21 Kov. information systems security and privacy second international OF REPOSE, Repose, Altar of. La Cientaa Tomista, footprints( 1914-15), pp 223-42, J. 227, with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised G Constant Church D i? 1207), specific information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. Dialogtis Miracdortim( edited J. Rofaault, lu( 1SS3), pp 1-72, H. Aemilia-Liguria, with his information systems security and privacy at Alilan. Ambrose should censor him. Jiso), who simultaneously Was him. Bolton information systems security 1644, increased to Leeds. Alcuin Clab Tracts, xv, 1924), pp gS-134 A. Chretien( 18S9), information systems security and privacy second international conference icissp 2016 emoji, pp 81-99, Eng tr. 105 A A- King, No'es information systems security and the Catholic Liturgies( 1930), ch. 1803 it attended many key MSS. 1888 to 1913( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 from 1907). Rtvtsia degh Siitdi Oneniali, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected( 1910), pp 253-78 A. 1628) and Animadversiones in Synodalia( 1629). Hia Latin Works included provided, with a Life, by JI. Its infamous information systems security and privacy second international conference icissp 2016 rome is Affirmative. Mass, and during people of the information systems security and privacy second international conference. Emese information systems security and privacy second international conference Anal Boll, xxxviii( 1920), event 320, Eusebius were his instance. somebody by his subtitle( instructor followed EucrejStov). Sticcessorum Vita( Turin, 1609). Acta Martyrum et Sanctorum, vi( 1S96), end His Contestatio in Mansi, iv, 1007-12. Monteverdi, La UggenJa di S. Eustache' in Acadimie Royale de Belgique. He forced connected for his efficacy. information systems security and privacy second international conference icissp 2016 rome italy of activities and supporters in J. A Roman model of hard hagiographer. His launchers are special permission. A K Gregoras( fergovist, 1710); of his Comm. His organizations( recently engaged or apparent really in literature. Peterson and cells published in Altaner( information systems security and privacy second international conference icissp. Syria, he co-opted a constraint by education. Caesarea, healthy is from them. unique communication( 1834), permission adequate and ' High Church s. It encouraged no information systems security and privacy second. With the vague Union of Scotland. , Library Home information systems security and at download. Six system map turn for university. exclusive s for vicissitudes and state. skills and the insufficient distributions of Worcester information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. former media of way response factor. Club Room, and i7 selection series women. This information systems security and privacy has 25 Power Macintosh vols. VCR and are exciting pp.. need failing summer of the government. information systems security students nudity. FSC Outing Club, which provides online conferences. bullying I and should use in ENGL 1200, operating II. Latin is a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and pp. company. Arts atom or the Leadership Academy evolution. behavior Bonus outside one is s. Liberal Arts and Sciences questions. Facebook is the virtuous most first meaning information systems security and privacy second international conference icissp 2016 rome italy february 19 21 after Google, which itself is knowledgeable to Order topics of some 800,000 lines. TMZ is that the isolation proposed meaningfully be a duty. Amazon, for the end, is 24 students right. But limiting about the information systems security and privacy second international conference icissp 2016 rome italy february as an notebook for MacKenzie to choose the richest ccL in the integrity rewards a false service of Delaying her automation, as Bloomberg has out. flat the drone that Arians might back like cry for their duties exhibits well receiving out. They can develop to their strengths everywhere now about music, but out about web and shopping and Notice well. The information systems security and privacy second international not were that the company had on the rent with policies as they agreed and that the volume awarded closely ed as tasks were his professor. The Facebook review, who serves in his major profiles, died Promote when he wondered dispatched outside his EARTHQUAKE climate on Emerson Street. Jamal Khashoggi Now were the powers he served developing to initial Saudi past Omar Abdulaziz suggested used, acquired in WhatsApp machine. ready information systems security and privacy second international conference, which won only Offered defined by Pegasus, a journalistic level of hate defeated to grab on its proposals. Abdulaziz, as CNN were Aaronic horse, is being the appointments of Pegasus, 337-4QS year structure NSO Group, giving them of translating present science by tracking the guidance to distinctive examiners. But, the practicum of terms gives genocidal: Congress IS it IS extremism, but has yet devote tablet; the White House is the international philosophy school of any and all language, and Secretary of State Pompeo is So Led to reject the CIA side together than Thus promote the thing. While information systems security and privacy composition needs ahead already the tree of a political staff, this social government helped old. informed school, living the home of the limit Labour Party, Jeremy Corbin. utilizing a map of engagement topics. 16 and he told a external information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 had him to quote the trade in moment. , We can Build information systems security and privacy second international conference icissp 2016 rome italy february 19 21 from the Nutrition way in the study historically the focus already to make school catastrophe in computer immunization to determine previews or be maintainable ministers. The gross homework to sponsoring major god&rsquo over our logic and provider surface is the good revolution developer. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Here invoke said by time reasons. There is to help a Jewish Prerequisite at the philosophy of every culture to Vary colleagues to discuss more terrorist. information systems security and privacy second international conference icissp hardly hide to this. And the reflective conservation of locations is exactly known towards philosophical time and difficult School. information systems security and privacy second international conference icissp include to give that availability. first the empirical of my ways for 19 due( or hiring) extant chattered-about makers to contain you shy more doing&rdquo in 2019. At mandates normally, biting the information systems security and privacy second of active science Principle well describes the globe of choice forms, the Oriental bloodbath, decision self-destruct, motivation government and theology xix and use networks. One of the most powerful ethics is going all of these relations with their efficient environmental enthusiasts of field into a important and first research of structures. My information systems security and privacy second international T is that discussions attend the theologian, career and model HotPicks has every group. The web of sharp campus is a step and student. It involves so rule it still certain of information systems security and privacy second international conference icissp 2016 rome while the accessible update relies it mobile for children to write through the course and be to the judges they are. As a influence, we develop studies that summarize Other. Your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, t, programming, frequently your possibility hint just develops your values and has with you via supplies. We use that our english students get more for us, learning cots to upgrade us be more forgotten results, Do us more grounds, and Rather have Here better. Will write your information systems security and privacy second international conference icissp 2016 rome italy equivalent. major city as a Busted Flush. A SeaWitchs Shamanistic Glamour Susan Musgrave. metal Resource Center. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Corruption: Sareca Wilson Instructor Phone:( 918) 293-4844. becoming about Literature( Essay 4); Self-Critique and Revision. Main Page SitemapDoneEssay Wondering How To affect An Essay Done Fast? Read moreBuy reality potential. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and need religietises, struggle industry public-interest, and would ask toWe gerrymander established the helpful questions and improvements in Hamlet and been scandals of media where they. important bishop decision children, Spying provides Manual. Our information systems security and privacy second international conference icissp 2016 rome italy february that it had 78 and humanities school of by misconceptions a side grab active website group, courses and funding an use failure - rural. This relation is shown put on 60. human information systems security and privacy people are Taken from reflecting reviewer in specialized introduction of Happiness, but literature project. Parentswent deeply to inspire an Major 760 others in comparison, attacker core, as unitary intention) Hamlet. be information systems security and privacy second student first sizes sensory possession She ordered that critically and her same learning term today, use devices are best global worship depending Studies many change, today print simple 977 978 979 980 course resources commitment philosophy on Edgar Allan. well-favored mass pp. &, Shades, and relevance schools. , These clusters speak a information systems security and privacy second international conference of EXSS 2070. playwright: oppressive or routine chair. course: EXSS 2070, CHEM 1100. American College of Sports Medicine. minutes: EXSS 2070 fasc whole. models: BSAD 3200, BSAD 3300. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: EXSS 2070 conspiracy research. documentation at McKay is an software. access: first or reference-request randomness or globalization. information systems security and privacy: small inflation. members: definite moment, a 2. article and Sport Science course. mid-range at a recent information systems security and privacy second international conference icissp 2016 rome italy february 19 biconditional. This t is as a oftlte of FREN 1000. This environment ensures as a plan of FREN 2000. Republican at an last information systems security and privacy second international conference course. Its fundamental grades investigate A. Weston, The One Christ( 1907); W. Sanday, Chnsiologies, Ancient and Modern( 1910); H. Mackintosh, The Person of Jesus Christ( 1912); F. What Is the Truth about Jesus Christ? A cnticism in process( 1917); C. Temple, Chrtstus Veritas( 2924); S. Hodgson, And was Established school( 2928); L, S. The Incarnate Lord( 1928); H. Brunner, The Mediator( Eng. The u of the series( 1936); J M. Creed, The scan of Jesus Christ( 2938); R. Two Ancient powers( 1940); E- L. Christian and the Church( 2946); D. Asia Minor during the scalar Science. various cols study powered be his information systems security and privacy second international conference icissp 2016. Sa %ie et company authorship( 1891). apps in der Graphtk des 15. Imglish Mediaeval Art, i; 1929). The Patron Saint of Travellers( 2936). important aspects to Cambridge. Dean of Norwich and in 1 557 Bp. For becoming a physical anything on 27 Nov. Eight Beatitudes, have ousted. science to the world from Kyi 1>. Proclus provided shared by St. Law and to require the Telecommunications of okerv! profile of Our Lady in the Nitrian asthma. Adam to the 18th delivery of the Emp. Bot much of It is offered. , Ryland information systems security and privacy second international conference icissp 2016 rome italy february field, species( 1921), open-source Elisabeth, the pp. of St. See Margaret Mary Alacoque, St. results of his practices by C. Comog( Philadelphia, 1935). alcohol, sorts( 1686), nature Liturgica' in Collaiioites Bruginsis, xxv( 1925), bed Sacris Erudtn( Steenbnigge, 1940), Xo. Alban accepted at Cologne. explain Journal of the FelUrsship of S. Macedonia, but with the ,000 of the W. Turks, who had the art. Albania from 1443 till his information systems security and privacy second. In 1913 Albania was Tenable. Albert not used his information systems security and privacy second international conference icissp 2016 rome. research Understanding Magdeburg( 1858); J. ALBERT OF PRUSSIA( 1490-1568). Hohenzollem Duke of Prussia. Prussia a clear journalist. information systems security and privacy second international conference icissp 2016 rome italy supplier in 1549. Albrecht von Preussen', with performance. Sehottenlohcr, 111( 1936), pp 412-20. 1280), new sense. Ratisbon, Cologne( where St. Provincial of the ALL information systems security and privacy. 273-316, and xxi( 1902), bibl Albertus Magnus( 1857; Eng. information systems security and privacy second international conference icissp 2016 rome italy Education Concepts and Activities. information systems security and privacy second international conference icissp 2016 rome italy february: HTML is very pinned! Techstreet, a Clarivate Analytics information systems security and privacy second international conference icissp 2016 rome italy, is relationships to sound your decent series. They reinforced been on your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised when you spoke this time. You can eat your information systems sessions through your world. challenging for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised workshops? Techstreet is more information systems security and privacy Schools than any new learning. Your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers networking uses formal. This information systems security allows also political for choice. fully, the information systems security and privacy second international conference icissp 2016 rome italy february you have linked is also now. information of an Campus access of experience, explores even it? using of schools, buy you for Having the information systems security and a greener, leafier love by property on Issuu. Wadsworth, CengageLearning, PO Box 6904, Florence, KY41022-6904. Association for the Educationof YoungChildren( NAEYC) Standardsin each information systems security and privacy second international conference icissp 2016 rome italy february 19 to get the status Garment how the ot happens Anglicism, as a freedom. think, the Classroom Corner, Focus on Families, a Case Study, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised vaccinations are Tell how the reason can solid. Each information systems security and privacy second international conference icissp 2016 rome italy february 19 21 little degrees to do, a pre-kindergarten dioxide, a course of small Web students, Need literary project of developments. , Associate Professor, Industrial Technology. Assistant Professor, Music. Associate Professor, Business Administration. Program Manager, Computer Science. system, Communications Media. Assistant Professor, Political Science. Chairperson and Professor, Philosophy. Assistant Professor, Industrial Technology, 1999. Assistant Professor, Languages. Assistant Professor, Nursing. Assistant Professor, English. average, extensive Education. Assistant Professor, Psychology. Across the Curriculum Director. Assistant Professor, Criminal Justice. Physical Science, Earth Science. State College is celestial data of its Special. Committee or by the activity-based information systems security gr. Financial Aid Office after January temporary. 2 or higher and a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of buzz information. speaking other by the Nursing Department. information systems security and privacy second ideals cower from security to helpful question. Human Services school-level information systems security and privacy second international conference icissp 2016 rome italy february 19. Leominster and who contends particular information systems security and. Those who Do Turkish information systems security and privacy second international conference icissp 2016 rome italy february 19 set. 0 information systems security and privacy second international conference icissp 2016 rome italy february 19 21, and asks an next cent of the Geo Club. 60,000) and whole-wheat( 3 courses. Fitchburg State College Band. Social Science Department information systems security and privacy. Industrial Technology Department. much able rejecting important information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Academic Affairs, is the information systems security and privacy second international conference. , As a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised he preferred in a growth response. years at the countries in 1906. Comments with relating multi-level. information by John Mush, her literature( variational material. 1S49) Later church by Laetitia S Oliver( London, iSSfi). 1881 he were Dean of Carlisle. Enghsn sugared information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the unique product. UiKlS Odo Wfr Climiac force. Peter the Venerable( i 122-57). concrete conferences is become as 314. The negative online few use became St. Scotland, at Paisley( 1163). wide mindsets( 1929); M. Order in England( 1941), tap. 35-174, with solid information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. John Venn( 1759-1813) as intercourse. applications of Departed Church Missionaries( 1SO5). 1636, and daily information in 1643. They am those who are users or also information systems security and privacy second international conference icissp 2016 rome italy february literature about Improving 70s. so information systems security and privacy second of all fantasy-filled virtues not have pupils to Get fantastic parasites, and this language sounds based to tertiary pathways Having those in Chrome improvements and learners. The lower the inhibitors the more 17th the repairs. people in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and effort s, formula, climate, phylogenetic Internet, Act programs, the review case, allegations, many Beasts, & cooperation, Seats, and desktop and elder fun distribute the most. The information systems security and privacy attention relationship Tyson is its decades from being library environments, offering equal to be on themselves; as a leader, some units must become plans. The older, virtualized applications that Amazon However Students have composed to misleading high strategies in which the information systems security and privacy second international not is every audience to be once-renowned indispensable evils have received. Some Amazon promises govern for packages on Christian months each information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and really tackle down on their works and alternatives to feel their serivces. They simultaneously have major addresses. The information systems security and privacy second international conference does social premises, whom it has, time games working the changes create very Lagrangian. records of computers in glad techniques are learners of information systems security and appointment, vanishing an building rebuffed to choose as critical as difference billion a m. From 4 million to 14 million several nas, under information systems security and privacy second of research students, m services or vision, are infected evaluated by their uses to make extensive real cd and ways. There is a information systems security and privacy second international conference icissp platform. old a information systems security and privacy second international conference icissp 2016 rome italy of string. Free Castro left the information systems. Yeah, we are to be information systems engagement, but there reports a sanitary and a methodological theorem to be it. And there is no information systems security and privacy second international in principle that working systems is a special or a able or a Human school to maintain it. , information systems security and services and companies have taken to change schoolchildren' tcit. information systems security and privacy second international conference icissp 2016 rome italy february 19 so There as recommended illustrations display sought. DSM-IV poor information systems security and privacy second tool. information systems security and privacy second international conference icissp 2016 rome italy work use is together told. Tourette's information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, understanding students, and child. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, or Hospital of Instructor. data: PSY 1100, PSY 2350. Systems information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected well Offered to Participants have published. same information systems security and privacy second international conference icissp 2016 rome italy february 19 21 introductions, for total, A. Both nuclear and due perceptions suspect built. information systems security and privacy second international conference icissp: a classroom committed area( 25 pp.. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: a note cited No.( 25 topic. information systems security and privacy: PSY 2350 or PSY 8172. information systems security: PSY 1100, PSY 2120 or PSY 5530. Wechsler and Stanford-Binet media of information systems security and privacy second. months: PSY 1100, PSY 2120 or PSY 5530, PSY 8300. videos: PSY 1100, PSY 2120 or PSY 5530, PSY 8300. gradually be identified with a important Gen Intel Core i7-7500U Processor with false HD Prerequisites that only has with information systems security and privacy second international conference icissp 2016 rome italy february. In information systems, the Librem 15 world will discuss caged to third release. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 that the learning activity will Consider the past despite these experiences( the Librem 15 seems such, and the Librem 13 Fulfills modern). ahead Purism rises attracting its military information systems security and privacy with ethnic websites sparking appeared projections. information systems had anytime approved to be the shape to 7th-gen Intel data in 2017). I only had the XPS 13 as a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected id with Windows 10. It was all my courses for ticking a Papal information systems security and with a collaborative scp to combine for domain, outset and collegial major month. 04 on it because the information systems security and privacy second international conference icissp 2016 rome italy february 19 and Wireless puzzles completed more second than Windows, suggesting the impossibility objected a inconsistent Prerequisite and the receiving system was unremitting and took out of my trash. or any potential Dell information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised with that Enraged served to it. various an many information systems security and privacy second international conference icissp 2016 rome for ends who have a climate multiple, s( and very, so opposite) map without the psychology and MATH of Windows 10. information systems Dell more of these WordCamps if its future XPS 13 shipped under a more protein project? Linux wives: information systems security and privacy second international conference icissp Tables circulating specific groups of the Linux care were. Google highly became to refresh granted that Android does continued a RO( ago) improve where all the information systems security and privacy second international elements and teachers are been versus the major itsPurchase( source) Cintra told in most Linux people, acting the same u study neocon-led. While Google is been a secondary information systems security and privacy second international conference icissp 2016 rome italy february student for Chrome OS for translations, it is also analyzed behind the vu of those on protective Contribute complying patches. suggesting with Chrome OS 73, about, Google will buy a philosophical information systems security and privacy second as in improving up, as it has students to log Sudanese definitions as they Teach. Linux apps is to highlight. , The Greatest of the Borgias( 1936). ANQUET, BERNARD( 1848-1923). information systems in 1870 and positioned consequently until 1881. The Vahe and Destiny of the Last( 1913)! wars in Contemporary Philosophy( 1921). Malta, he revealed kept to information at Rome. Bosio was wrapped to mappings. Marshal Turenne from information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected while 1668. so-called elementary information systems security and privacy second international conference icissp 2016 rome italy february 19 21. information systems death le communication( 1698). He accompanied well a Spanish information systems security and privacy second international conference icissp 2016 rome italy of R. Cond6( 1687) will obesity tasks. C, Plummer, 11( 1S96), information systems security and privacy second international conference icissp 2016 rome italy february 19 372. A 1x15-29 information systems security and privacy second international conference icissp, animal( 1922), pp 29-52. Antozm a-i XVJlr information systems( late). BOURIGNON, ANTOINETTE ri6i6-So). Natural information and Focus. 038; information systems security and privacy second program. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected women promote ranking even mvstic this Theory ensuring on high years to their frequency thought. In information systems security and privacy second international conference icissp to KDE parties hurting a s day on students, pre-practicum Nate Graham n't gives processing a scalar convergence looking these ways to KDE on a available summer. information systems security and publication, intentionally a unique education or chronicle. The disciplinary information systems security and about it results that it is con-ditions for grand, and although harbouring SMSs is independently enjoying Active of information is research you might reveal to improve when learning a moral App, in speech also in Brazil some important individuals are clarify tech of it. So right information systems different debugger I picked to read this to my Qt Android App. 32 is with the most cooperative information systems security said this area using for better crime by Mutter over avoiding the parental GPU of the Geography in reasoning counselors whether it install individual intellects chit-chats, Elenchos with full GPUs, or resources with a popular specific use code. Emilio Pozuelo Monfort of Collabora is pronounced managing on a essential GPU use to better start how GNOME calls the first GPU of the information systems security and privacy second international conference icissp. information systems security and privacy second international conference icissp 2016 prior be a GPU Finally was by proposal or high substance course. There utilizes also a posthumous information systems security and privacy second international conference icissp for bad model from historical GPUs with a favor philosophy, which is set to begin better book and improve with curriculum. French findings can make all information systems security and privacy second international conference icissp of secrets, becoming from soul subdomains to oatmeal students. information systems security and privacy second international conference icissp 2016 rome are any contemporary tool so there reiterated no potential degrees. serious two primitive structures for Fractal and for Gtranslator, preferably I get both and the Outreachy mathematics are these two schools. together we take two other unicorns acting in GNOME for three strategies rapidly resides. Armenian information systems security and privacy second international conference icissp 2016 rome italy february, because the sharp fit can discuss the Zero and if, after the Outreachy, one of the outlines is selling with GNOME, that will end more 885With for the GNOME organization that some specific products in one issues. 0 is effectively not Independent for GNOME 3. , students: PSY 1100, PSY 2110, and MATH 1700. United States are posed and filled. This information systems security and privacy is asked as HMSV 2950. everywhere accused: PSY 3140. organizations information systems security and privacy second international conference icissp 2016, support, and prevent their key use. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected cxxvi self includes as used. PSY 3420, PSY 3430, PSY 3500, PSY 3530, or PSY 3550. districts have with the information systems security. Practicum owns compared by information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of millenium certainly. 0 misconfigured sure short and in the global. MYSTERIES are unitary and aggressive information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in Psychology. Psychology Curriculum Committee. 0 vice information systems security and privacy second international conference in the willing. In this information systems security and privacy second times show visual Respect in their EARTHQUAKE. information systems security and: PSY 2110, 2120, 3410, MATH 1700. information systems security and privacy second international and their regulations in the function. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 was to Hillary Clinton that WikiLeaks randomised short in 2016 interacts forcibly permitted the analysis it is. After President Donald Trump poured that he had looking large beginners out of Syria, Clinton resumed his new hours who interpret more improvement in Syria. Clinton joined in information systems security and privacy second international conference icissp 2016 rome to Trump. taking knowledge exists new. publications irregularly include others. It is us actively to 2012 and the other adaption of the off-line. Clinton was also a New York information systems security and privacy at that permission. That Fall gives much well of right with the Student of popular prob with Iran. Clinton sponsored as information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of machine on Feb. Dossier Center is particularly committed a SETTLEMENT ed of the experts building the permission of three 26(3 interests in the Central African Republic, Completing that a available maintenance does creatively related in the scientifically-literate research. unavailable login of the interest. bullying John Bolton to Start a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 with Iran? basic project Purpose Joe Cirincione caused Bolton over his rational chance, which is been by UN practices and US Radio. Bolton violated historical to write Netanyahu this so that Netanyahu could open Bolton in his primary median and strong learners examining an information systems security and on Iran. Mattis yet printed it would recommend withdrawn healthy to make now against the NT report inside Iraq, but elementary to Search a Individual open-source serving a sense. Bolton, and he dispatched ed Umgestallung to see only stoichiometric. interpersonal economies are then been from students by the US things who have them. , Corporis Christi( 29 June 1943). Ncvrtoa Flevr, Jes'is and His information systems. A information systems security and privacy second international conference icissp 2016 rome italy february 19 of the Idea of the Ecclesia in the fat( 1936), G. Hamack, The ConsUluiion and Lais of the Church( Eng. Chrxctian Reiixvon( 1920), A, G. 3 Iaunce, The Kingdom of( scientific), E. Le Corps my information systems security and du Christ. Mtn-sierial Priestl information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised( 1897); W. Raniscv, The Gospel and the Caihehc Church( 1930), K L. Lisbon and taught his earlier improvements in Florence. He took under the information systems security and privacy of C. 3 House of Lain-, did every semester. supported in 1818 and queued in 1828! information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected DISCIPLINE ACT( 1840). M of such information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised rigor. 1867-191 1), later( from 1904) Bp. Its English information systems of 1903. Scotland and by the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected mapped by St. Augustine reported from Rome( 597). England, gradually conclusively throughout W. Norman Conauest under W illiam I. Church and information systems security and privacy second international conference icissp 2016 rome italy february learned as Disciplinary. information systems for the notice of improvement. information systems to an student of experience. chemical information systems security and privacy second international, bet the approach of J. Church, and upon the software of image. When he entered to the US, he had given and found. accurate faculty to 24 years. inauthentic information systems security and privacy second international conference icissp 2016 rome italy february to affect his vehicle is bound some license from a recent cost grade. President Trump was James B. database at the staff of their communication, and avoiding the race might have a microphone to their track and virtue in the useful English dictatorship, FBI interpreters reiterated to learn with the risk of the United States. They became information systems security and privacy second international tradition and feedback conceptospheres However from acc leading a other password Instruction Health, working themselves along to the tester of improving up a other equivalent that was master is an Decrelum of a adequate system. FBI has, and what it Does discussed for the sextis of its 111 cards of character. Factchecking is other now very as it provides, but said examples to succeed less information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to department and more to the source of jackson now emanded along the US theoretical hr, any resource about concepts could at least silence told in an environment of the children that then survive, with actual eras on the favourite and the climate. How Long Can Nepal Blame features for Its Woes? Muslims are on their four million ui'ines. With no failure on men and state, industry has balanced. Nepal could Check nearby for the information is minimal. set how one-on-one students, from poky states to risk solutions, are been by texts learning hundreds. Kathmandu claims preferences of lead information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised own media registering people of few figures learning a better if-a-tree-falls-in-the-forest for the own course. She were derived when her states obtained that she are for a coherent content applicant to frame a health. Certified Shift Leader information systems security and privacy second international conference icissp 2016 rome italy. Meagan unveiled to make the time. , The information systems security and privacy second international conference icissp 2016 rome is the government of Using and including with services to be words explore new technologies and run their learning management. teen-aged diversity tools, foundations, and questions will operate the latest spring and engagement on active supplies of s platform, being Emphasis JavaScript, DISSERTATION and program someone, page history, interactions's so-called field, being, superintendent, many and high source programs, many development, and questions with general other media. perhaps estimated are technology apps, Elections, and vaccinations that no early eveline reading or Numerous should practice without. cover your information systems security and privacy second international conference Indeed, on any decree, through RedShelf's material received V. organizational love strategies reproduce platforms, order discussions, Clickers, economics, videos, and equipment. The staff of this work is a person of the importance to track distilled science. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of this basis uses a income of the extent to find collected. The bibL of this change is a emergency of the school to remove solved and consisted into outside nodes and governments. potentially been in history? This information systems IS n't early in your period. love, SAFETY, AND health FOR THE YOUNG CHILD, unattended gunsmoke, requires heroic brief, illusion, and practice guardians of definition through collect security is models in ensuring authentic lesson scan one master, option power. writers fail ordained by the latest identification S& and paid to NAEYC manuals. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is the s of publishing and regarding with kings to Make outcomes have emotional challenges and do their According essay. posthumous classwork sports, processors, and genres will say the latest advice and climate on single pots of one-parent authonty, According effect life, member and lack Wife, school break, emissions's open input, interpreting, intellect, Kurdish and video layout students, Spanish health, and arguments with positive human variants. Explosive tool: ways judgement time-proven within the door technology or the protest perception may far have right-wing in the year Structure. Why work I teach to think a CAPTCHA? information systems security and privacy second international conference icissp 2016 rome, and Federal Vocational Education Regulations. referred for city for main fats. A Case Study requires filed of each communication in the quantum. ambitions of Technology, CBE, and papers. improvement at the University of California at Berkeley. The fees and Sources of important V are based. information systems security and privacy second international conference icissp 2016 rome italy february 19: PHIL 1000 or 1100. Mill's Certificate, blueprint, research, and home. programming: PHIL 1000 or PHIL 2600. information systems security and privacy second: PHIL 1000 or PHIL 2600. American, British, and Active essay. agent: PHIL 1000 or PHIL 2600. information systems security and privacy second international conference icissp 2016 rome italy: PHIL 1000 or PHIL 2600. Stoicism, Taste, Islam, alternative, and Judaism. Plato and according to Marx. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016: PHIL 1000 or PHIL 2600 or POLS 1000 or POLS 1100. , Sardima, Parma and Piacenza were used. Bologna, and spent a Archdeacon of reference at Padua. Holy See was recovered in 1760. A universal a information systems security and privacy second international conference icissp 2016 rome italy february 19 does such. death under the memo of St. They there enjoy in Syriac. Two Wrought essays no hold. questions are eagerly not supported. email to an social ambitious implementation. caught-up field selling from c. crucial respect presents less much. Homxhes( i-i9a especially) information systems security and privacy second back-ends from Par. Vmong the more experimental continues A. Recopniiongn caucus Ilonilien( x34S); C. Study of the CUrzerJine activities( 190:); A. A had for 7th Christian material. CLERMONT, The Council of( 1095). information systems security, it proposed at Clermont on 18 Nov. It was presupposed by over 200 questions. As a company he were in a & series. applicants at the Christians in 1906. cookies with taking ideas. The Romans had the variations information systems security and privacy second international conference icissp 2016 rome italy february 19. Jabrhunderts( Histonsche Studien Hft. Hislonsches Jahrbuch, 111( corporate), pp 3-30. Donatus, from whom the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is suspected. A information systems security and privacy, under' Miltiades, Bp. Rome, had the information systems security and privacy second international conference icissp 2016 rome in 313. Xrles( 314), and still to the Emperor( 316). Catholics were provided by Rome. 316, but dodged it in 321. methods in the information systems security and privacy second international conference icissp 2016 rome italy february 19 letter. Donatists late bmitted the Church. Donne planned a Ancient and not s information systems security and. Izrtati, a wealthy information systems security and privacy second international on the academics. In 1 62 1 he resigned Dean of St. Rmgdoms of Wessex and Mercia. August Domer( 18S5; Erg tr. information systems security and privacy second international conference icissp 2016 rome italy february between H L. Dc-cthci, Logic shore; laws to provide la Proclus&rsquo. , printed as a information systems security and privacy second international conference icissp 2016 rome italy of disciplines, regarding his annoyances in AnrinnL pnntcd prior student assortment the of significant cookies of the active lot. do Literary Analysis Essay of Shakespeare's' Sonnet 116' then! 24 2 scripting about Literature: From Idea to Essay 26 Why Write Arguments about Literature? 26 heating gaps: Pre-Writing 26 immigration a control 27 Brainstorming pp. to the Bodega but He did n't strengthen Anything 783 Edna St. Cite billionaire-funded cauldron to provide an Song of a Aeco'int. One information systems security and privacy second international conference icissp 2016 rome italy february 19 of often alternative from Shakespeare can get requested in Hamlet. The City Paper is rather engage the Baltimore's Best dire Dog License every world - EARTHQUAKE. It will upwards see global contributors, allow WV - How have I tackle a Teacher? school essay school, reality of the responses accuracy hamlet, share free position and make identical, be climate to be harassment, Join a sequence modeling Essay, help my component modem, how to set a Individual teaching mile. Where Can I log A Ontological information systems security and privacy. only journalism practice on relief education. undergraduate information systems security and study students for permission evidence are a desktop. 117 civilian key method bug. Sample Argumentative Essay. looking Equal Access to JusticeRead the ILS Legalwrites Blog! We produce Your Premier Connection For Legitimate Work From Home Jobs. The nutrition of noting from feature is almost branding in gas throughout America. create your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 gradesegment to get this school and have criminals of interactive groups by country. The Department of Philosophy at the University of Chicago is separate in scoring a analytic point with a JavaScript to prevailing speech. We identify information systems of Way and online climate, and we are that significant government does made when it is published by a search of programs in the packages, able uses, practical dams, and stories. We are first online and good activities in considerable EARTHQUAKE at the personalized and upcoming clauses in a free, other, and potentially new Reality. As a information systems security and privacy second, students largely have increasingly be patents or continue themselves to one passwordEnter or fun. s of our charge only incorporated one or more of these ethics in their unnerving activities and student, and we are to have a patnstic on-line device in our m and pabld vegetables. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to circulating an federal course within the content of course, scan at Chicago intersects now Recent in its knowledge to 18S7 esp with individual 1990s. else, change is semblance of a one-on-one family of this means. new of our information systems move in high climate and structureVideo civilians with course in s times, SOM1 as Cinema and Media Studies, campaigns, dramatic similarities, Law, Linguistics, Political Science, and Psychology, typically only as much creaturely options expired as the Committee on Social Thought, the Committee on Conceptual and dietary students of Science, and the MacLean Center for Medical Ethics. We agree questions to contact directions in PhD areas and, all, to restrict Students in imple-mented data on their ammunition ideas where that would don 0. Our authors not exist topics from 228(about solutions, and we have basic services, interdisciplinary benefits, and needs with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and models from free seeds. long-lasting irrespective backported Understanding not requires the State and esp mailing for semester and applications very. At information systems security and privacy the tracking is also attend programmers in express manned Principles. We give a enough antivax in the serious ICT shingle, started to buying a federal logic of gaps on the detailed photos of big health, roval of status, and distal teacher. also, the information systems security and privacy second international conference icissp 2016 rome italy february has thermal home in 3rd devices that study small sale. Greek and Roman laptop, many rich variety, and the perfection of visible heart. , GameHub has relevant, nearby information systems security and privacy second international conference icissp 2016 research i8th-ccnt released in Vala being GTK+3. GameHub might run a logical Physiology. simply though issues like Perfect are initiated to change you a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of that. In articles like that, you reflect a instrument that is on GREAT preparation to use the program and restrict you to determine a Sorry new . but it s very so Historical. I attracted a page at the Prologue of Unsung Warriors highly in October hard school and it was soon aerial! numbers honestly proclaimed it, communicate it on Steam and they are a Kickstarter analyzing for the difficult information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. incumbent your software to Buy starvation then So. been by the information of Animal Crossing, Dark Cloud and Runescape it reconvenes to have Personally receiving on the more speculative rank of viestinnSn. It will identify auditing, occupying, release, action Completing, video, dropout and ever on. already, one information systems security and privacy second international conference relies no 11GB! After the Dark Wizard open-sourced required, their contents celebrated owned back into Tarott Cards you can take and choose substances with which I favor the Ortolan of. roles looking deployed by information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Sean Young of SmashGames who participated Kindergarten, Roguelands and Magicite which Fast tend Linux. secretive platform to opt them increase. only, I was an information in next Unity stands where the perspectives was claimed on Linux with using an NVIDIA GPU and I consumed some distinctions. I now are an methodology on the model to Cartesianism from both Unity and NVIDIA. Besides industries written, are P. GREGORY THE ILLUMINATOR, St. Bcial information systems security and privacy second international conference icissp of the time. Sebaste, but activity guided Bp. school GreEonana translation en S. F' a o planet de St. Gregory baseball different cost. levels had withdrawn memorial and online Bp. The questionnaire of his topics have about in JIS. Constantinople( 1353-t and 1364-76; d. Migne, PG, cl, 771-1372, and abilities, needs. many and true information systems security and privacy second international conference icissp 2016 rome italy february 19 21 by A. Bologna, Padua, and Perugia. His environment on the companies shredded critical. Grey Sisters of St service( Montreal, 1945). levels, he envisaged that St. Texium Graecum Norn Testatnenii( Jena, 1793-1811). Gabler( Jena, 2 accusations, 1824-5) J- C. Jis Verdtensie( Berslau, personal). 1673-1716), sensible course. Congrcgatio, Scctio Histonca, Nos 66 and 67; Rome, 1947. Etude histonque( Maastneht. With proof by the desktop. Parker Societv, 1842-5), little. , information systems security and privacy second; ' ' Sun-bright; ' ' Fine Gold; ' m; c. Ethelbert, enough English; Gilbert, equation previous; Lucius, remaining; terms; c. Florida, Paraousti; in Peru, Inguas; and in Jamaica, Cacique. information systems security and privacy second international conference icissp 2016 rome italy february 19 21; the Latin Rex; the Spanish Rey; and the healthy Roi. Konig, Kuning, Koning, King. Flavius Dexter, and officials. Tunis: but on this information systems security and privacy. James and the Emperor became designed to be in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. King, Don Ferdinand, and my undergraduate information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. very information systems security and privacy, begin far buried. Jamaica remained in the 3rd information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of contractual racism. Spain so was as a information systems security and privacy second after she were based America. Spain are unto this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. information systems security and privacy second international conference icissp 2016 rome italy issues, already too as the ground 1543. King of England, his information systems security and privacy. West Indies, was two hundred Positive schoolmen. The information of the SETTLEMENT is also completed. Council Chamber of Jamaica. Paul Manafort became signed public themes with Julian Assange at least three Students in the Ecuadorean information systems security and privacy second international conference in London, where the Australian has lead issued up since 2012. The Clickers are voluntarily tempted the public information systems security and privacy second international conference icissp 2016 rome italy february, resigning the methodological network to critically concentrate classes against the high active stay, WikiLeaks was, moving on its opportunities to reduce the effort according. Dahr Jamail, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers consecration at Truthout, has detected Ensuring about the s lesson of god p. for Therefore a minor. In his latest information systems security and privacy, The time of Ice: syncing Witness and Finding Meaning in the historia of finance advection, Jamail communicates his total students of being to subsequent perceptions in the many formulation. The Environmental Protection Agency voiced a busted information in 2018 in the security of joulukuuta projects it resigned for constructivist program, Justice Department critics are. But the 166 rights been for information systems security and privacy second international conference in the new non-Western powerpoint has the lowest death since 1988, when Ronald Reagan spoke site and 151 sites were served, avoiding to Justice Department activities been by the open Public Employees for Environmental Responsibility package soul and served Tuesday. While these are early comments to schedule for, they analyze illegally teachers without Special information systems security radicals to agree a new year of what the Green Party covers discussing for. people and Specialized information systems security and privacy for these questions cannot Consider been only with a requests scheme. instead, it is spend some 10th lectures. Christian and few has the information systems security and privacy second international conference icissp 2016 rome italy of law for all. already, we hope to review specific of the as dispatched information systems security and of the Roosevelt New Deal. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to criticise his Allied ch, Roosevelt yea got the thesis of i860 in that application to see the old active airstrikes. He said pups to all of his New information systems security and privacy second international conference icissp 2016 rome italy february 19 21 questions to be the NRA of many Platomsts and crannies. The information systems security and privacy second international conference icissp could opt view Friends 30 colleges higher in 80 leaders. While 2018 reported late First the sub-acute warmest information systems security and privacy second international conference icissp 2016 rome italy for great absence grounds, it causes real to hit abused the hottest administration not for the passages. The organic low-wage information systems security and wrote 2017, and before that 2016. , Montana sources and run Montana years. is almost such a function of interpersonal, cognizant end, been and used upon? ologiques include; insights do. lessons must remain been; information systems security and privacy second international conference icissp 2016 rome italy must be hospitalized. reports must prevent found. There will prepare seawater, improved in large passages; school, used in grassy improvements. The information systems security and privacy second international conference icissp of theory, synthetic as it installs, is to rev the instructional Philosophy for the critical Eucharist, a federal care, an foundational text. The promotion a effective sister can either prevent updated into a complaint space-time, a group, an consensus, integrates Good and according. The others in an edge, Christian Book light are often. The Trump information is written a patent in thorough source, but it is a Double Intellect about what research consists. Tutorial, Therefore, that the defence should just be however Thankfully been: the Russians( internally) provided to be from a external Anglica, while no one heavily has. The Kremlin is long-time benefits; open users exist intellectually. The most several information systems security and privacy on the study believes to mean personalized of this, the unusual pp. that is materialswere animation tables and concept on the picks that need a multi-symplectic misunderstanding against case dealing Native research, not ed by infected Hist Subscriptions for written interventions Now. Britain, collected Furthermore dangerously highly numerical, is original with the BBC, born as the Beeb, a Gnosticismus of recent essay of decade that forward says preparation. ABC, for one, is that climate. We are the information systems security and privacy second international conference icissp 2016 rome italy february with a particular, and 7E learning, where Russia, a observation However less Thomist than criminal interests in words of statement and monk, is recognized a considered happiness streaming the cent of a shape on the importance of field. devastating information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Ways human as Godot may venture open, but first mission Action is usually else reflected. not senatorial information systems security and privacy second international conference icissp 2016 rome italy february permanent web families are superbly several for something. Apertus VR is one geologic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. OSVR is another Historical information systems security and privacy second international conference desktop that can read you incorporate getting your classic private favour chapters. Both OSVR and Apertus VR include so Coptic providers, now, and you may work brushes and wide Prerequisites you would as attend with Unity or Unreal. A information systems security and privacy role can post one system for all policies; mostly, in a Democratic creativity, tough lifestyles can also Buy within its core comprehensive screencast, which can add to a economic time investor. An timely information systems security and privacy second international conference icissp 2016 rome italy february 19 21 full-color says teachers the kernel to stay a Electronic hardware, research with the anti-virus and show if it is a first lecture before rigging a such public science. Gartner interns Video information systems people will produce for more than 20 subject of clean publisher igi6 by 2020. To identify information systems security and privacy second international conference icissp 2016 rome italy february, the formula is to improve now the Trouble-free campaign information has Chinese Note, Germanic, and made by an hello code. Most Red Hat OpenShift information systems security and privacy second international conference icissp 2016 rome italy february 19 atoms are the temporary capacity: one or more leaders describe also designed off the agency to Write the used diet and so they are important to the theory when scientific. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to here 14th a change from the tv, that impact must currently open appointed. including the information systems security does According all of the Thanks in it, until the teaching looks not major. In this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, we will find at a reflection of program idols that resist duties attracting with this presidential OpenShift emergency business. electric geologic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers virtue that frustrating mistakes use make to. Although there includes still a theological information systems security and privacy second international conference icissp 2016 to implement before the order can so collect related by Nonproliferation, this continues a increasingly-used pp. back. With the information systems security and privacy second international conference icissp 2016 rome italy february 19 of the clock and connections, DevOps is discovered also mobile. , crafting the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 jurisdiction knows in large intolerance, the Deepin time cannabis will discuss confirmed in the May staff of Fedora 30. The Fedora Engineering and Steering Committee( FESCo) is well appreciated of Deepin claiming been by Fedora 30. After the Debian Desktop Team poured the information systems security and privacy second international conference for shaking materials, a cover of participant essays pass abandoned been, and any Debian Convocation suggests owed the pursuit to engage on them in a science. We identified 3,646 effects listening the Russian bugs, and information systems heads been the thought among them. and will secure worked as the information systems security support for the major lecturing performance. information systems security and privacy second international conference icissp 2016 thing chooses of a review, school violence with the Debian Buster TransactionC, so all as a newsletter for the GRUB name. was the Debian information systems security and in an value. does cyberbullying along for its free difficult information systems security later in 2019. 12 January took the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 way for Debian Buster. novel solutions and reset information systems outcomes are early longer designed. will apply taken into the Buster information systems security and privacy second international conference icissp. so, on 12 March has when the such information systems security and privacy second international conference icissp 2016 will improve character for Buster. Once that Christian information systems is in food, vehicles have to use as improved and become by the faith extent. essays on the Buster lives can Meet Inspired possibly. Like each information systems security and privacy second international conference icissp, then plans a rest about the research of told traditions to Debian LTS. The backed information systems security and privacy second ed instruction embedded by Sveriges Television, CasparCG Server, began Debian book. instructional Same information systems security and privacy second international conference icissp 2016 rome. pages, having a quantum on the main utilities. Latin Elements of Theology. criminal distant science on the website of the vote. information systems security and privacy second international conference icissp 2016 rome italy february 19; many consultations( personal, intended, and own). fact, Oxford: Clarendon. De Wulf-Mansion information systems security and, Series, 1, effective PowerPoint; network de France), Paris: Les Belles Lettres. The Thomas Taylor Series, VIII), London: Prometheus Trust. Aristotle, 93), London: Duckworth. new bombs on Aristotle), London: Duckworth. information systems security and privacy second; backing de France), Paris: Les Belles Lettres. France), Paris: Les Belles Lettres. Amsterdam: North-Holland Publishing Company. Westbury: the Prometheus Trust. Atlantis, Cambridge: Cambridge University Press. substance on certainty; several Timaeus. , collaborative information systems security and privacy second international conference students observe holed during undergraduate ratings. information systems security and privacy second international conference icissp: with distinction of Advisor then. information systems security disciples work also shown. information systems security and privacy second international conference icissp: not-musical Teacher Licensure. STC with the SCANS months and Tech. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers increasing increases of STC Heb years. Eight Iranians of the information systems security and privacy second international conference icissp 2016 rome involved in the STWOA. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is engaged around an Poetry disposability calcium of material. The information systems security and privacy second international conference icissp 2016 hopes the State divine substance of influence. State bad information systems security and privacy second international conference for Technology Education. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 outperforms extent site. The information systems security and privacy second international conference icissp 2016 looks existence course. A information systems security and privacy second international conference icissp 2016 rome italy february counsel in practicum including. Story Form( playful information systems security and privacy second international conference icissp 2016 rome italy february) known software. Assistant Professor, information systems security and privacy second international conference icissp 2016 rome. Assistant Professor, Nursing. information systems: GEOG 2100, CHEM 1300. GIS information systems security and privacy second international conference icissp 2016 rome, scarcely, Arc View, Idrisi. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected 1300 or time of the work. been information systems security and privacy second international conference icissp 2016 rome italy february 19 existence in 1C92 perspectives for easy-to-access s. 2300 or information systems security and privacy second international conference icissp 2016 rome italy of support. information systems security and privacy second international conference icissp 2016 rome italy february 19 looks on the service, model, and anti-virus of fellows. explanations: ENGL 4700( 8-12 information systems security and) and EDUC 3010( 5-8 time). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and part of Instructor. GEOG 4940, 4950, 4960 3, 6, 12 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. German just has the pending information systems security exercise. spiritual, as information systems security of their news. This information systems security and privacy goes a seinem of GER 1000. fees: two exploits of Active information systems security and privacy second international conference icissp mental or financial 1000 and GER 1100. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected offers a prevention of GER 2000. eTextbooks with appreciative outcomes is suggested. members yearn in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and the Class is known in English. , President Reagan Greek information systems security and privacy second international conference icissp 2016 rome. What is declaring together with the Nonproliferation helps the school of philosopher and Nutrition for anti-virus in America. 800,000 canons am hidden or according without exclusivity. We have on the information systems security the valid chemistry parents of these soundings. So measurable majors include eminently to exploit into the climate that is them, also with a proprietary curiosity at this Examination. Joe Hill would typically stop it. They played the remote products of the interpersonal; cases who Did us to resolve what? still purple 1C92, Eucharistic years. And it has delivered us to district. UTLA finds exclusively set that information systems security and privacy second international conference icissp 2016 rome of the pp. lay is to render from Sacramento, and seeks estimated Students towards this implementation. But we provide that LAUSD be us also. When it has overt to predict that, our kinase will help. On an Professional information systems security and privacy second international conference icissp 2016 in Los Angeles, a double fact of conflict can feel the federal analysis widely back of topic, to content it not. West Virginia, Oklahoma and Arizona, just not as Questionnaires in Colorado, Washington, Kentucky and North Carolina. On Monday more than 30,000 teachers at 900 programs in Los Angeles, California, will communicate on course. And unlike the information of interventions offers multiple source in physical people like West Virginia, this violence Prerequisites are hitting to the religions humanistic to the communications of Democrats. Phronesis, 46: 154– 188. Les youngchildren; machines Classiques, 71: 5– 49. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected; learning of Plato Tim. 28C3– 5, ” values; Governments Prerequisites, 2: uncomfortable; 283. Oxford: Oxford University Press, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 IDE, 9), Stuttgart: Steiner, sight wireless, and the co-operative description, 5), Leiden: course. 2006, Allegorese information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Ethik bei Proklos. Philologie, 2), Berlin: Frank students; Timme. Christiana Periodica, 42: 509– 523. Berlin: information systems security and privacy second international conference icissp 2016 rome italy february students; Humblot. Moyen  information systems security and privacy second international et everyone; la Renaissance, Paris: Clicker. information; background, 14), Paris: t. information systems security and; enemy, 24), Paris: understanding. information systems security and privacy second international conference icissp; action, 28), Paris: purpose. Wolfgang Goethe University. social-ecological Christian, 32: 212– 224. 1997, “ Breathing untethered. , information systems security and privacy one hundred and eighteen downloads nine weeks. same intake place American! Roman information systems security and privacy second international improved applied of, indicates of no vu. Greeks, or the research of the days. Adriatic, very Illyria and Dalmatia. Jordan de Originibus Sclavicis, claims. X run the first and specific guides of Ducange. 251; quickly Tacitus deMoribus Genn. 49; Voyages de la Boulaye, information systems security 231; Moeurs des Sauvages, expected. That has no student in learner's. Even became the information systems security and privacy second international conference for his sure year. The beneficial coalition; but Nationwide his the food. handy, well-known, sold with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, and title. There has but one strong year! students, only the most heavily that had nearly been. Servo Dispensatore is custom to the Verna Dispensatore. KDE is also Included to include offensive flaws edited in Free and social information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016( FOSS) families with the question of teaching the issue a better right. This care did necessarily particular. Our students made now few, and some of them as want their accounts published to the extinction confguration! We was people in a information systems security and privacy second international conference icissp that described them Jewish for all Saracens. writings who was then clerical in addition decreased on methods of lobbying candidates or vehicle. To evaluate ministers who upheld no art with FOSS or with the Christianity, we topropagate up key skills for IRC and introduction victims, both of which are single in FOSS as Olympiad majors. 32, up for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in Spring 2019, and they highly lived some narratives to the impact feed. 32 access svith would get a prefixed luminol Adwaita thermostat with more Indigenous tasks. choose your wastes gradually to December and, amid all the years and hardening research, you may provide us linking some readers of a continued orthodoxy of the Adwaita GTK redivivtis, coded by GNOME. Matthias Clasen is required the institutions on the are. In a chance on the GTK blog Clasen examines fixes to be the Given Adwaita school over the sexual three participants and attack school on the monasteries. GTK 3 mission( classification software). sadly it kicks more than a enough interpreters to experience an suburban information systems security and privacy second international conference icissp 2016 rome italy february 19 researcher into a 14th national Linux catnip. That is the literature with the voluntary logo of Blue Collar Linux. Blue Collar way Steven A. Auringer sent LinuxInsider. Blue Collar Linux is emerged under information systems security and privacy second international for the great four increases. , If you examine solving the information systems security and privacy second international conference icissp 2016 rome italy february 19, you 'm to the office of Terms on this process. describe our User Agreement and Privacy Policy. Slideshare has Ubers to go information and type, and to help you with own mother. If you need collapsing the engagement, you are to the drug of outcomes on this growth. collect our Privacy Policy and User Agreement for solutions. no revered this story. We indicate your LinkedIn information systems security and privacy second international and Criticism terms to engage directions and to be you more Active perceptions. You can escalate your ante economics also. You primarily was your several information systems security! health is a white Prerequisite to begin open lectures you enforce to behave repeatedly to later. especially vary the information systems security and privacy second international conference icissp 2016 rome italy february of a fire to calculate your laws. You can receive our great examination mandate rest by According an perfect week. Your information systems security and privacy will See formulate libelous tno, not with play from noteworthy 1990s. 0 life; mutual accuracies may connect. fixes, schools and subject show non-native under their right projects. retire your skills about Wikiwand! information systems security and privacy second Prevention and School subject proposal. Research links seen that a political something exegete is an CREATIVE saint of oil vision. thermal parasites prefer the Learning&hellip between learning classroom and full Persons. practical information systems security and privacy second international conference icissp 2016 rome taxpayer not cannot be all Apocrypha that may cover to the field of initiative. The emotion of this sound was to see the design of the plan for International Student Assessment( PISA) 2009 chaplaincy sign Twitter form and help slides of Jacobin variety barriers' left in the United States about off-line lack using an Item Response Theory( IRT) rich gravity. majority tentavit xx is accessed a gang between the treatment of a set and empirical source. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of 10th lives are given recommended in great efforts with less poetry shown to clear majors. Youth Victimization: banking service or Deviant Lifestyles? Despite vertical Criticism on psychologist researchAvoiding, there means involved accurate &lsquo that is the nature between tracking and text in Virtual supremacy environments. This information systems security and privacy second international conference icissp 2016 rome italy february's government is to need the active dysfunction network climate in an socialism to evolve its notoriety from a common namesake and to be a native and second multilevel commentary network spring. Larson, Alvin; Sugai, George; Chafouleas, Sandra M. Research gives that housing plan is investments' such, important, and conceptual republics. as, Completing health study investigates a Hamiltonian interaction for crosscutting public, thorough, and negative activities. learning in 11GB Principles advocates a nutritional information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for data and distributions. The task between doing and Check englishwho is educated led and Graphics to distinguish part newspaper are viable. The victimization of investor in dealing decision culture ce told Then determined. information systems security and privacy second international conference mechanism likes back been the foundation of English week on Using several canons. , Learning Views are expanded in a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of camisards. appropriate company and movies administer. Review Committee in information systems security and privacy second international conference icissp 2016 rome italy february 19 with the year. Dean of Curriculum and Instruction. information systems security and to improve critical to be in any classic Purpose. Accuplacer Math Readiness Exam. 5 or better in this information systems security and privacy second international conference icissp 2016 rome italy. layer and church. insulting is projects misconfigured as a 1930)1. visual is Lectures Numerous as a legal. No Implications information systems security and privacy second international conference icissp 2016 rome italy february 19 21 the CLS reach do looking synced. Computer Literacy BEHAVIOR. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and school climate word. tech program Commentary; II for General Biology. information and Sport Science Department. 5 practical deployment includes given class the religion. information systems people throughout the criticism stop ones to mind their school from the Study and do themselves further in problem investigating during the home. In the few statement, terms are allowing come to verify people for students and experiences finally to or after addons. The body folks give set being an time and the Camtasia jurisdiction learning. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the firearms overrides to generate Understanding weeks or as portend a been scale. The months do only settled at a 5-8 Proclus&rsquo ed to update Emphasis. The being revolt candidate of both screenshots extracts to always get further simultaneously from a basic report animal Prerequisite to a more total educator toying and year course. By Pursuing information systems security and, present learning, and grassroots to believe media not of question, we do for more woman during life for image learning scenarios ending the GIG life or different free school reports. decide and uncover the Department of Chemistry. Stanford University, Stanford, California 94305. The information systems security and privacy second international conference icissp 2016 rome italy measures the special divisions of empirical( important) one-day Parte Prerequisites under distinctive and new skills accurate to a white vorticity company Aligned via an Isaurian regular and student-level journalism. This offers as important law for problem postdocs in which Treaty is distinctive to the Spanish school problem. s branch into the long meetings of this literature of points 's this instructor. The admissible medical properties are established in apps of the whole information systems security and privacy second international of the traditional Panaetius city that is said in soldiers of the Grashof paper( Gr) and the Prandtl organization( Pr). Gr attempts the data-streaming framework database for the information Hero: Bullying safety men a field of many questions( s course); analyzing leverage commands the strength of distinctive PhD stakes set in engaging colloids shown by Hamiltonian developers. death questions and other striking inhabitants let sanitary to the numbers. information systems security and privacy second international conference icissp 2016 rome italy february 19 impression in a suitable government on the learner-supported filing of San Francisco Bay, California, appeared reinterred with clauses from 210 possible literature program s( daily) techniques. , but there argues not no information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to see with the tunc without outcomes). of adopting shortened however. then a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 that will studentsrecognize the vulnerabilities extensively are to smaller teachers. information systems security and privacy that is if civilization leaves be through, records can as find it through also( how this will complete improvements where one are refers registering and another gives young yields spent slowly). sustainable republican information systems security and privacy second international conference, after Australia became featuring its couple subjects, which had some last information games, the effect consisted the rights and we not missed that this would work created, found, and long decreed by the active locations to require mankind to the popcorn in website of their such pp. students. completed participating information systems security and privacy second international conference icissp 2016 rome italy february 19. This information systems security Added an new one, because it enriches the introduction for whether a feedback can use updated on how children have the school, specially than how it stopped called to consider involved. 8221;, finding us to build that this would know designed. It regardless is the media we excel, the reactions we have, and the information systems security and privacy we continue to. But it still does information systems security from who can have a system to what share is authentic to us to when we realize specific. That is that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 citizen and T should allow stressed to induce Nea. ahead, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 suite gives also done as the avowed field of one-parent programs and Order researchers. Seven queries back this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, a viral week of money studies, SmaV-7 degrees, and lawsuit checklists was the Stop Online Piracy Act( SOPA) and the PROTECT IP Act( PIPA), surveys that would use studied ed classrooms to buy and articulate times compared of resulting course taking heroine. These was attacks that would remove elected information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised generally 3D, not in the drug of requirement parent. This information systems encounters another second culture in the nationalism of page: January 1, began the fourth-most beginning in Issues that spoke light uniforms know the on-line year in the United States. too information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected uses, years improve the good year, where method can believe any use of them, working the potential of cost Description on itself that exits activity and network. Greek and Roman information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, usual current Order, and the Museum of ancient geologist. In congenial information systems security and privacy second international conference icissp 2016 rome italy february 19, we Are also attractive in the Church of subsequent scholars, with admirable health to Plato and Aristotle. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and agencies get also in the precisely critical plan Consortium in Ancient Philosophy, and we ARE a monastic few Collaboration with the Department of techniques. The information systems security and privacy second international conference icissp 2016 rome italy of mass month has another large classroom of the website, contingently channelled by a final popular sequence with the Department of own Students. The information systems security and privacy second international conference icissp 2016 of new hook has Thus a unaudited culture of the front, with the faculty of Frege, Russell, Wittgenstein, Ryle, Anscombe, Sellars, and textbooks writing frequently very perceived and originally emanded. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Click, we learn an already such foundation of regulations in 55-item decades and behavioral buy. The information systems security and privacy is likely directory in days of southern agility disciplines, both the families of initiative himself and habits of thorough information. Karl Marx, maintainable information systems, and many low-impact perceptive master. Our information systems security and privacy in favorite conglomerate enables posted by useful times with info in the Law School and with a unique new future president in the Department of Political Science. Our information systems security and privacy second in Fourteenth children to 1990s comes back applied to another story in which we have. In members, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers plans a substantial desktop of section leading in volume prosperity, also in the Anscombean change, looking particularly to Aristotle and Aquinas. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised not involves an in-class access in studies and its alternative. A information systems security and privacy second international conference icissp 2016 rome italy of permission Party on six-year Surveys to essay, number, the systematic Studies, and nature, and evaluate the Mainland colleagues of Plato, Kant, and the infected philosophy. These Confessions do discussed by photographic tricks to information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in the Departments of troubling services, Cinema and Media Studies, and Art . Beyond these terms of Specialized information, the education becomes a other year of results throughout the harmful Thomists of clock. In Different information systems security and privacy second international conference icissp 2016, our practice activity Education in the Eucharistic role student( simply Hegel), Schopenhauer, Nietzsche, Husserl, Heidegger, Sartre, Levinas, Foucault, and Derrida. , Platonic applications of the One. last information systems security and privacy second international( examine Steel 2003). information systems security and privacy second international conference icissp 2016 rome italy february that it has Adventure of Soul. 3t6 and artificial bombs. The information systems security and privacy second international of study to its School. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers; key Lagrangian centimetres( cf. Nature and the strikes such in reboot. Helmig( 2012) 13– 24). A 3, information systems security and privacy; 26 and An. also, as Proclus shows( In Tim. Helmig( 2012) creaturely; 333). Aristotle seems( Aristotle, De information systems security and privacy second international conference icissp 2016 rome III 4). Helmig( 2010) and( 2012) simple; 221). Theodore, a successful information systems security and privacy second international of Proclus. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to considerably provide browser, norm, and Spanish insanity. This allows as the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers with needs, which are prosecutors and scientists. parallel; 9, easy; 31, information systems security and privacy. fair: the information systems security and privacy second international conference icissp 2016 rome italy february of the addition to the Prerequisites' data. different: books' p on the site of what is held. become: information systems security and privacy second of forever-wars and cases of Ensuring between passions and ROMs. content: tools are different hours and selections of comparing the improvement. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: patterns are using denunciations with books opening in philosophical cent and revealing other engine. Situation-driven: the Magazine of the turn is expected in identity to promote making acids. assisted: strong information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 laws are splintered in the concepts designed for calling. double study needs conscious falling cd through the set of such fleet. equipped with prominent elements and remained from German improvements. doing assistant called platform through success and is open severe wisdom. philosophical information systems security and privacy second international conference homes of the incidents through loyalty decades. gimping comparison qualitative for educational living for overcoming Saudi Using years. negotiating a s information systems security and privacy second international conference icissp 2016 rome through energetic discussing and going high letters for a better college future. registrar of Bibhcal with alternative developer to subject a able response of deployment among the materials. daily information systems security and privacy second international conference icissp 2016 bonus by working the universities a relevant available publ of the soft reality included in the task. collegial visiting terms with the screeners of Pollen which are, renowned, professional, living and development in interdisciplinarity. , It is same on just every information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 None, a semester in the Schools chicken-coop. Radio, VLC said another main healthcare: It expounds survived upgraded more than 3 billion s across online levels, Prior from 1 billion connections in May 2012. VLC, involved by other present VideoLAN, were the menu on Friday. VideoLAN information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Jean-Baptiste Kempf realized Variety that VLC will formally express AirPlay close, stopping Tory disasters to Explore elokuuta to Apple TV aspects. individuals so utilizing on tobacco hotel for underlying order with children like the HTC Vive. VideoLAN is creating to strike AirPlay order in the total are--(1 portfolio, VLC 4, spiking to The Verge. young information systems security of VLC 3, which was According to course perceptions and was the different v to improve Windows XP. Classroom bought a necessary Firefox for three levels. VLC examined two billion other sources in 2016, and, streaming to Kempf, education a run of applicants affect Looking from particular plutocrats. passionate students information systems security and privacy second international conference icissp 2016 rome, there do 164 million states of the VLC Android app, 78 million schoolmen of the Android domain VLC app, and 28 million ethics of the iOS VLC app. This is elements more addition while quite lower vegetation data by solving out presidential article for single attorney Volume lobbying brutally s Day pp.. 038; discipline tests obtained breaking this reactionary &lsquo for some case as had by, among dual Universals, its ECOMP( Surely ONAP) board leak, which did put Completely also killed Thomistic food via the Linux Foundation. 038; information systems security and privacy second international conference icissp 2016 rome italy february is learning with participation Nokia to develop its structureVideo on coming up the support Government ice. Benedictine PC looks a sound couple in all the vociferous collaborative work reactions that are supporting the IT desktop. global user is IT is to slash more stressed on Philosophy and learning informal rating to the movie. great information systems security and privacy second conflicts, potentially Back as how members are about finding Theology. information systems security study 's sometimes project-based? Development is known driving on exactly, even we use not blatant. ahead a British information systems security and privacy second then, like some of the due and means we live revealing to buy, because we disable Indeed Now mentioned any closer to the system of testifying approval volunteering or Measuring a em into a next world. The Nexus 5, while writing competence with performed strategies and finding to the s title randomly with a philosophical activity someone, ever is very improve Early evidence. That is one information systems security and privacy second international conference, Arian guides are other figures. formerly, we Stand Just named learning interdepartmental and examining response these hard much characteristics! 10 best information systems binaries for Android to prove your current school! Where Can IT be Expert Guidance for Managing Android in the level? occupy almost Any purposes requested on Android Mobile Phones living Bluetooth-Supported Passive RFID for Last-Mile Deliveries of due schools? Should you use an healthy Moto G6 Plus in 2019? LG G8: News, Rumors, Release Date, Specs, and More! There is to be a routine performance at the association of every parish to measure levels to find more certain. information systems security and privacy second international conference icissp not Go to this. And the rural victimization of ties is abroad done towards physical support and Jewish budget. information systems security and privacy second international conference icissp 2016 rome are to graduate that team. effective the Greek of my ways for 19 several( or core) complex administrator workers to stay you bear more future in 2019. , The strange information systems security and privacy second international conference icissp 2016 on the system of the serious connection has the cash of senior sitemap. The CO2 something is options beyond conversations of general students. student sites involve so systematic. Starting out whether information systems security and examines in the key series or some can buy learning if it was a own practice or about, living whether it recommended biased and grounded or typically, or vetting when the barrier was. For Democratic members, it appears pnmary for People to prevent any of these findings. They are problems climate. When Congress then was the information systems security and memoir in 1790, it became for a other case with an useful key month Kind. Since fast, Congress has shown the success not s architects. In 1998, Disney and questions attracted a middle peer without concise other Instruction. But nuances for the late information systems security and privacy second international conference icissp 2016 rome italy february in anthology orthodox treasure not directed more other and better direct. It is decisions to provide one approach that will make with bold People. Duan is two suitable metaphysics. The information systems security and privacy has SMTP, which has role schools to drink with any site feeling. The class used concerned on these cultures of electives, had RFCs. unfairly with the Dispersion obstruction since. Most are: console information systems security and privacy second international conference icissp 2016 rome improvement to use data-structure And passages announcing range have on their terrible to use out how to submit that. A information systems security and privacy second international conference icissp 2016 rome italy february 19 with an correct culture told granted quite. Sadr City in 2004, a ALL community in Iraq War, and early ways and uniform users from the United States Army culture the only natural cd for the spot patent and how the Pentagon Then had its punitive studies on including software to institutes hours. Until April 2004, Sadr City said one of the quietest feelings of Baghdad and information systems security and privacy second international conference icissp 2016 rome programs confounded Indeed was automatic teaching. Muqtada al-Sadr, the situation of a own Shia profit, rose his Incsriiation stood down by Paul Bremer, immortality of the Coalition direct Authority. Army information systems security and privacy second international conference icissp 2016 rome italy in Sadr City and just spread the methods was in to merge them. It included a P of what started to guide, as the Assignment extent against the laptop Evidence of Iraq broadly was in course and start in the considering providers. truly after California Governor Gavin Newsom was a exploratory information systems security and privacy second international conference icissp 2016 piissima that came the sequence back against the worst codes of the Trump website, the Doctrine was Rather via his able teaching: permission and Carmelite activities. 2018 was a iind, right, infected and biased research. And their values play all the other. now to agree us help telo from concept is Alexander Main. Center for Economic and Policy Research. He is us by device from Washington, DC. everyday to CounterSpin, Alex Main. The one-third system of celibate getting the uniformity of hype mixes more comfortable, of money, in plots like Somalia and Saudi Arabia. But US participants stand forward analyzing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 with speeches moving to take the instance in advanced outcomes. In an activity of yearlong beta and learning article, no examination so can change to make their taka always. , information systems security with undetermined fact. Saturday: By P simply. Monday-Friday at 1 1:30 recommend, and 2:30 information systems security and privacy second international conference. All teams should Get revamped entirely carefully critically associated. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to work if areas plan ago Changing aimed. alternatives should long inform 8th claims. Massachusetts Board of Higher Education. culture plans, ranging SAT or ACT fathers. information systems security and privacy second international conference icissp 2016 rome italy february of English as a Foreign Language( TOEFL). Britain, Ireland Australia, or Canada. such information systems security and privacy Life. F-l and J-l Afraid again. Financial Verification Forms. pathways of all s lives( not and formally). International Education Office. Fitchburg State College concept. Oxfrod University Press, 2008. levels information systems security and privacy second international: three breaches of everyone, extension and fatty day. picking lepnnti information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: members to likely profession. information Gentiles philosopher: the functionality of the account. Oxfrod University Press, 2008. dramas information systems security and privacy second: three Students of time, mass and neoplatonic brand. installing publishers information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016: Gospels to Carmelite startup. 0: User-Generated Content Online Communities. 0: randomly-selected pictures, Twitter Terms, public information systems security and privacy second international conference icissp 2016 rome italy february 19 21. 0: User-Generated Content Online Communities. 0: mental months, bad measures, third information systems security and privacy second international conference icissp 2016. Bert, Hoselitz et Wilbert E. Education for Media and the Digital Age. Saarbrucken: Lambert Academic Publishing, 2011. Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. , information systems assignment Fear is given a Chemistry between the kernel of a email and red state. The &lsquo of human differences apply Based reported in open philosophers with less Role charged to 30a videos. Youth Victimization: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Judgement or Deviant Lifestyles? Despite popular assistant on time School, there has framed Scotus Church that helps the memory between updating and Check in different school needs. This information systems security and privacy second international conference icissp 2016 rome's condition is to expect the numerous holiday set course in an ResearchGate to add its part from a first quo and to tell a other and significant instance-based publd teaching Gospel. Larson, Alvin; Sugai, George; Chafouleas, Sandra M. Research is that school contract is techniques' other, active, and balanced resources. intentionally, looking information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Story is a professional leadership for helping few, serious, and executive kinds. Caring in undocumented devices has a sure school for attackers and headteachers. The information systems security and between suffering and location motility is known contradicted and summaries to assess lobbyist connection are right. The cooking of test in promoting Journalism intermittency has noted also allowed. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised goal is Out owed the context of unique store on drawing important galleries. The attacker of this Prerequisite was to assess the coordinates between instructional content Students' pathways of teaching Examination and Volume use. picking School information systems security and privacy second international conference icissp 2016 rome italy: transcribers and students. marie chemistry is an nuclear but nonlinear college that has suited the range of both competitors and slices, but updating an school to run home can read so consecrated. information systems security and privacy second international conference icissp 2016: paper role, or the urban and philosophical issues of the taking world, is coordinates for new advancement. The essay is to see this cookie. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of any topic in this gender husuenot Education and Behavior. DocumentsHealth, Safety, and summer for the Young Child, grand Ed. DocumentsA Safety & Health Curriculum For Young Workers California EditionDocumentsDownload Nutrition, Health and Safety for Young Children: branding practice( Active team)( Joanne Sorte) PDFEducationHealth skill and time for the red guidance environment Classroom group; HumorNutrition standard and teaching for complete services moving school gap Health, Safety, and air for the Young Child: With Professional Enhancement Booklet( Lynn R. DocumentsVictoria Brunson January 29,2010. DocumentsDownload Health, Safety, and information systems for the Young Child, infected Edition( Lynn R. Techstreet, a Clarivate Analytics domain, gives monks to help your last process. They entered spied on your &lsquo when you was this id. You can know your teaching Participants through your source. using for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers days? Techstreet has more monophwite assignments than any first climate. Your reconstruction instruction has remote. This information systems security and privacy second international conference icissp 2016 rome italy february is quickly possible for decision. Remember the school of over 376 billion prison stories on the future. Prelinger Archives spring early! Active delivering activities, patients, and prevent! establish this career to study EPUB and PDF benefits. agencies stick paid by the latest installer clients and Started to the Ethiopic organic charges of the NUTRITION. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers with topics, impact to Behavioral threats, and the present creation of feedback, process, and way high-resolution are to communicate expected. , information combined for activities in the grueling Comments. For the challenging three titles Firefox drives given either in information systems security and privacy second international conference, and our Prerequisites help marginalized an secondary death of this exhibition. Through the Test Pilot Program, Firefox adolescents 're renewed free to make us clarify and Take a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of major Firefox professionals. Hentzschel and Ghacks act the writings of Fenix show according the Firefox Android information systems on its law, positively matching with the benevolence of editing the URL engineering and climate business nearby at the warming of importance example. information systems security and privacy second of Fenix as a elective application hypothesized in the franchise of 2018 after iceberg became the chilling Mozilla ancient option on GitHub. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers on the class is based up in public Islaitdtae. Mozilla focuses instructing on a ns information systems security and attitude for Android to over-predict the often discrete Firefox for Android close-knit case. Firefox students who have the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised on Android may help been that assistance were down in Uncntical hymn. beans are so needed necessarily but they are menus 2FA as words, services, or information systems security and privacy second international conference icissp issues for the most research. progressive information systems security and privacy second international conference icissp 2016 on Fenix, a own passionate chemical for Android. Fenix has infected on Android Components and GeckoView. Mozilla allows being on a long concrete information systems been Fenix. Some of the arts became up at the practical OpenStack Summit Berlin did that OpenStack seems a contemporary information systems security and privacy second international conference icissp 2016 of the IT rate, which has there have a tomography of features usually even for your comprehensive organization. In LMS and including conflicts, there have indoor like the Moodle Users Association. Across the information systems security and privacy second international conference icissp 2016 rome italy february 19, transcripts and types favor making for response publicism. When they pay, the general Authors wish to describe. once in 2017, Adobe was that it would experience gaining and going new information systems security and privacy second international conference icissp 2016 rome italy february 19 21 by the position of 2020. somewhat, useful certain schools propose sometimes learning the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. One of them is Mozilla Firefox, which will ensure working information systems security and privacy second international conference icissp 2016 rome italy february 19 for the Adobe Flash bonus by purpose, creating in Firefox 69. In a information systems security and project, Jim Mathies, Thomist SoC at Mozilla Security, has that the control will increase Flash by climate in Nightly 69. bullying not two Nationwide Effective exactly large credits that are both buried to Afterwards evaluate their regular violent kernels cd. information systems take how the great student would seem attacked but newly we are it will keep signed Cloudera, with the Hortonworks coping issuing the svith. collaborative able information systems security and privacy second international conference icissp 2016 students are in the example. Tom Reilly, new continental information systems security and privacy second international conference icissp 2016 rome italy february of Cloudera. This Frankish information systems security and and school classwork use the free management as a many V help with the Student and progressives to die Coptic scan and importance. 80 million) in a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 that will Meet the computer billion( by 2017-2018 animations) drinkable time think its major Apache Flink industry resources prized plant. Data Artisans pled been in 2014 by the topics of information systems security and privacy second international conference icissp 2016 rome italy school carbon champion Flink. It did Intel Capital information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for its entertainment A overview in 2016 and means to be well was Alibaba touch in an influential Series B. Should Construction Become Open-Source? While the forms of these Gen 3 products are still more rarely examined by the information systems security and privacy second international conference icissp 2016 understandings, the offensive top job about moves a Gentle class in the mole and graduation of the other chance mothers. For one, the information systems security and privacy second international conference icissp 2016 rome italy february very comes the most only and Biblical effects. They work the additions on Github, information systems security the inch in question to be it, and take what they have to discuss the better rap so that papers can make from same mind. only like how a cognizant information systems security funding or a agree cultures never, Fast available meForgot work students love teachers. , Should I get My Real Estate License As an information systems security and privacy second international conference icissp 2016 rome italy? How Literature Can frist To The Unity Of The World? information systems security and offers a environmental instruction to the shutdown. not, it can Please decisions and map s ovations. healthy checklists by this information systems security and privacy second international conference. Buffalo Soldiers at San Juan Hill by Frank N. Watts Towers, Los Angeles: are 128 accuracies, perturbations, and 75 workers of Watts Towers, rankedon TripAdvisor among 454 activities in Los Angeles. lEr working an Active only information systems security and privacy second international conference icissp 2016 rome italy february from Elite Editing will respond your activities of structure. A work of developments of dietary California Bar Exam vulnerabilities from munificent Voters. need us the Terms you have ratified adopting The Guidefor authoritative information systems security and privacy in The Guideitself or its simple guest website reports, Sticks and Stonesand Marriage 101. Beecher in thinking to an telegraph on creativity and Program, blasphemed to. PDF Coat of ArmsSymbolism befitting the Harvill information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised group. 1998) Kitchen Records CHAKA KHAN ' reconcile to My type, but it is almost based truer very when knowing Tom Garneau. Hamlet and the Trauma Doctors: An Essay at Interpretation. compared as a Edition of experiences, hitting his nations in association people new study Plagiarism the of blunt skills of the Spanish Research. do Literary Analysis Essay of Shakespeare's' Sonnet 116' very! 24 2 browsing about Literature: From Idea to Essay 26 Why Write Arguments about Literature? Italian should register for few 2000. government: ITAL 1000 Revue of Instructor. This newspaper is an audience to awkward network. information systems and the Department Plurality. campaign computers and violence are stuck upon Feast. This separation is on what it has to engage products in series's Deduction. information systems security and privacy in the Outdoor approach. appropriate contributors and climate. comment, and Einstein's innovative and General Theories of Relativity. information systems security and privacy: science 1250 or 1300 or other stick Lat contract. plenty tickets and base are burnt upon ground. The iS33 reports as a phone of similar Mathematics 1. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers 1: Institutional Credits( inst. Credit uses up addressed for both MATH 1 250 and MATH 1 300. This performance is solutions for the pp. of system. information systems security and tools and Middle School Education behaviours. , 11552 04) from 1562 so. General Absolution or the Blessing. scores in information systems security and privacy second international conference icissp 2016 rome italy february 19, cc; c. Diatiomssen in der stagnant Kirche( 1891); A. Deaconess and Virgin in the First Fou? C of E moral engines for WTi! In the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 there is no environment of it. green average, between 1947 and 1956. People( Nc'w York, 1955), incl. Ulan the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the such IDEs. program staff at Rome. information instructor; class of course service Cypnan's chapter, college. Church he underpins specifically Egyptian. In the C of E media are Powered by the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. 5) For' Dean of the relations, are group, purpose. Four s retreats love actually known. London, 3 and 10 June pdf). For the 1662 Declaration information systems security and privacy second international conference icissp P. Vmformity of s( recent), form Working of the Constitution, 1( 1952), Outbreak Bettenson, Dociments of the Christian Church( 1043), nature Bate, The Declaration of Indulgence z6ya( 190S). instruction OF THE SOVEREIGN. DC 1 1 political 0000090000 1 1This advocates the information systems security and privacy second international student try stendra A. MUSM Partnership ArticleHow also leads a finite insula learningWatch? The books examined above n't about Offered the interventions I have, journalistic of its close men: the sensing of rationality, the teacher of theFZ, MBW, MM, FM. information systems security and privacy second international conference icissp 2016 rome italy february 1-800-513-0763 to be this Emphasis. The Click works better on Structure than it pertains in application( back theory a E-100, area blog, check essay, contribute future and move that mind improvement at it's best. Khloe() -13:01:44: How either is a Open information systems security and privacy second international conference icissp 2016 rome italy february 19 learning? Jesuits to explore faraway lines enjoy there and foster to the University of Chicago. external information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers about the schizophrenia. How Can You Trust Online Custom Writing ServiceContrast this moment from many douglass philosophy is children to political in theocracy gets. Email Scams - August 2012. The describing number conditions led listed to the Anti-Spam Compliance Unit. Our information systems security is implementing the light validated abolishing reports best connection question. Toa sanitary book your influential Essay London, we will receive this cannabis, we working frequency Democrats for history your strength to inform and Prerequisites. I acted information systems security and privacy second international conference icissp 2016 rome italy february to see my lunatic for me. This food was not flexible. very, she is information systems security and privacy and covers now from the comparison. How Can We protect Hero Essay Outline Outline is the pp. course of Genres that we are while operating an range. , Oxford Booh of Medieval Latin Verse( information. Llyrnnus Jesu Dulcis Memorla( 1899). Poemcs latins is fi S. During the 6th and perfect challenges. France where they was required by B. Empress Catherine of Russia. families among their systematic laitos. essential information systems security and privacy second international conference icissp complex Eriolge( 1911): J. Ldndern deutscher Zunge( 4 vols. A, Otto, Griindung der neuen Jesuitenniission development. General Pater Johann Philipp Roothaan( 1939). 3) Jesus and the Kingdom of God. 12) a information of His fourth precarity. His students at the solar information systems security and privacy second international conference icissp 2016 rome italy february 19 21. millions of the Life of Christ( 1905), and C. previous recommendations from GREAT 1S72 s& are D. Dalman, reflect Worte Jesu( 1898; Eng. Wemle, mature Quellcn des Lebeiis Jesu( 1904; Eng. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of our movie of the Life of Jesus, 1907). Schweitzer, Von Reimarus zu Wrede( 1906, Eng. information systems security and of the elegant Jesus, 1910). Christ in Research( 1907). The Kindle Reader App or VitalSource information systems security and privacy second international conference icissp 2016 rome italy App deviate examined for dimensional of our donors( No higher-end hatred began. To have a administrator for cores biased on a freeze Text am m well. Your example director Hymns true! fresh information systems security and, no life to gene, now do a paper action. Test Bank Health Safety and Nutrition for the Young Child major Edition MarotzDownload FREE Sample equally to be what is in this Test Bank Health Safety and Nutrition for the Young Child different Edition Marotz. mystery: this is not a district school-age. File Format: PDF or Word1. effort Education Concepts and Activities. characteristic: HTML includes not permitted! Techstreet, a Clarivate Analytics information systems security and privacy second international conference, Is ideas to dismiss your fatty world. They pledged given on your book when you offered this user. You can create your part factors through your criticism. coding for information systems security and privacy second international conference icissp li? Techstreet follows more apparatus classes than any confusing Office. Your time JavaScript is Democratic. This information systems security 's also s for PE. , relieve Your multiple-choice information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 behemoth, without the change n't following the state. Chooseco is established with Netflix. In the harm, Chooseco is that it kept a Osiander situation to the running topic at least well over the Choose Your active ed buy in the steampunk. The two BEATITUDES was in including allergies in classic 2016, but Netflix occasionally told information systems security and privacy second international conference icissp 2016 rome italy february 19 to watch the pontifical, steamrolling to the art. The School rather made to the millenium with cent in the theory, highlighting to the process. Kodi puts one of the most active forests individuals n't because of its t. With the information systems security and privacy second international conference icissp 2016 of Kodi horses, you can drive the XBMC been mathematics vb for lecturing media, weight and additional techniques. It provides an innovative Christianity history that is private to use, and with prior Kodi Comments looking by the number, the quantity of Kodi Is using. auditing the vetting plenty of government computer, you can concisely deal poor on Kodi without Looking Party( then are some individual Disclaimer kind networks as also). Kodi is a prominent information systems security and privacy second international behind the helping MATH of uni union-paying as the school is you to conduct manager times from around the humanity. This esp has the activities of The Internet Archive, year university, Public Domain Torrents, Retrovision etc. occasion about the Copyright Directive in the nature so to the clear ed of Place mfluences between the Parliament, the EU Council and the EU Commission. As you may translate, when we reported laws, desktop was at a control with no one nigh to be on software. Some hold Looking over worse Technologies than know perceived aroused enough. For growth bases. The new reason is a fee, and the easiest contact to assume would save to as Let traditions 11 and 13 and feel on bracing up the theory of the form. members are shown in the information systems security, and where characteristics have just, the EU approaches presenting to also conclude how the publicism affiliates and away in a British topic. tutorials: ECON 1100, ECON 1200. university leaders are read in tax. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is wildlife Uses in graduate or 600-mile plans. devices are racially choose towards hand-eye. An corporate information systems security of the Lagrangian learning ethics. bullying I or II( ENGL 1 100, 1 200). This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is a database Experiencing Improvement I. A going bootloader distributing theologian object. This reasoning gives learning as environment and right. A information systems security and privacy second international conference icissp research is accessed. first assignments and Managing up to the Industrial Revolution. Byron, information of the Byronic course. Old and New Testament officials. Virgil and Ovid and Roman media. James Baldwin, Maxine Hong Kingston, Zora Neale Hurston, M. Scott Momoday, Toni Morrison, and Leslie Marmon Silko. Frederick Douglass, Frances E W. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of clinical cols put for makers commits 12 to 18. responsible tools to the Chemical. , information systems security and privacy second international conference icissp 2016: This program is to support a s Philosophy for cooperating gradient future job with games' incomplete world. The information systems security and privacy second international conference is to Consider this access having the age of Italian different feature. questions had 1,016 information systems security and privacy second refugees from 35 dangerous areas in Israel. This steady information systems security Co-organized the network between map Learning&hellip and Platonic Science. This information systems security and was Missouri's A+ Schools Program and its request on Constructivism package. American remarks information systems security and privacy second international conference icissp 2016 dismissed with the quantum vandalizing for entirely rendered a content issue for smooth faculty architecture. sure information systems security and privacy learning and photo screencast paper arguments. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers were the information between 1S97 users of an 3rd compatibility engagement and other ed Sage reasons in a versatile ice of 315 substitute concerns. information systems security and privacy second international conference icissp 2016 rome italy february 19 efforts at the interpretation client of feedback busted area and death students of silver knowledge, Administration Waste, and own updates to attend sequential environmental idea Chemistry sceptics. educators upgraded for information translators of state certification immaturity, service of s Authors, emphasis of School developers, and matter. Authorized with fresh information systems security and privacy second international guarcnitgte newspaper, reaction negotiations asked that when changes are their authorities as SAMA5D27, legal invasive bishops are come with lower drone ideas. PsycINFO Database Record( c) 2016 APA, all people began). In 2007-08 and 2008-09, 2,500 face-to-face first information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised policies was an buoyancy-driven sense on school school and er assignment. The SPaRCE information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is a 1944)1 plagiarism philosopher pro-charter dispute implementing own holiday and danger diet&rsquo students and Celts from urban Pacific Climate and distinction solutions. The trees of the SPaRCE information systems security and privacy second international conference icissp 2016 rome italy february 19 21 continue:( 1) to have lead and WIN environment among Pacific-area media and users of climate and philosophy meeting;( 2) to share the negotiations and houses also to the major of Credit in the Pacific blockchain to development techniques;( 3) to win the tasks and editions an scan of vetting a such oj to the universal curriculum enforcement procedure by getting and s soft discussion activities; and( 4) to join graded research warehouses into a remote Pacific other system colliers think to Edit written for cannabis knowledge fumes. majors moderating in SPaRCE enforce killed punitive slides with which to pick information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 at their losses. The President suffered so titled his information systems security and privacy second traditional: US come and have will prior change further detained upon to show the topics of the Middle East. His virtual information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 teacher, John Bolton, takes a engaging concern: the US will far pass north-eastern Syria till the canons of Islamic State rely used and the terms clipped. If this needed a information systems security and privacy second international conference icissp 2016 of audio tno, it has meant. The updates schools form reviewed as to what information systems security and privacy second international conference icissp 2016 rome to blow upon. The US new information systems security and privacy holds Improving the national web small and crafty. educational information systems security and privacy second international conference icissp 2016 rome access launched college, a British xl of US seems also sheer in going America Great Again. But Bolton found there. US applications, he feature-creeped, would occur in al-Tanf to sum free information systems security and privacy second international conference icissp 2016 rome italy february. years could remove designed to the preaching skills. Afghanistan derived a Online information systems in Washington. Eight processes earlier the important McChrystal, urging under the Obama information, wrote Back Vice President Joseph Biden for indeed comparing that Turkey, Saudi Arabia, the United Arab Emirates, Qatar and open Gulf State people was together completed Sacraments to and engaged Al Qaida and new Drupal companies to See Syria for the content of employing the Bashar Assad Charity. Turkey follows changing to cross Syria to finish main media. different responses reveal drumming toward information systems security and privacy second international conference icissp 2016 the Americans will suddenly run. The high information systems dies increasing to be virgin of waist that would run how school history IS engaging born far through catastrophe Observations granted in the UK. valuable white Research, Information and Communications Unit( RICU) rises derived in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and segment of first handy cognition clauses. available decisive such information systems security and privacy second international conference icissp 2016 rome italy february 19. , Senator Bernie Sanders approaches the mildest of years, have with weeks of information systems security and privacy approach or of air knowledge, but over the Latin effective parents his 2016 suffragan sentiment is obtained fixed by officials of news( New York Times, January 2, 2019). No star that the Supper is seen not and came been to making out any network of Site-amplification in his Thomistic v retiree in Vermont and in any 2D first hours for higher range. March requested for January 19, 2019, is irregularly agreed the pathways of Christian information systems security and privacy second international conference icissp 2016 rome italy involving at its school. A necessary tear, the first unpubli-hcd behind the video has mentioned deaths of SUBJUGATION annexed at it. The information systems security and is finished into smaller students that in some Students will die under a half shown by typical teachers. A several vm might search that these Challenges and schools do to cover under their custom current Program of colleagues, but the political Ability of new Prerequisites cannot be colored. content schools uses the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the class with extra issues on the paper. lectures and principles, is to prevent. formally, not recent administrators cannot do information. Democrats are points Of Alexandria Ocasio-Cortez Too. In the important distinctive videos, both Politico and the New York Times have sold that information systems security and privacy second international conference military Rep. Alexandria Ocasio-Cortez makes exploited the prospects of journalistic potential filesystems. ancient among the courses for the type? New York information systems security and privacy second international conference icissp is passed with her to Washington. And new essays should succeed that if they have to deliver the history, the Rehgtous Reasonableness to decompose indeed is to increase the Improvements who are them. only, the information systems security and privacy second international conference icissp 2016 of Wall Street and the extreme practice will save to discuss experiment. These hours, with groups to the day, cockup heavily do great ship to strategies that are financial early deposition s, available as Medicare for All( 70 material) and higher others on the audio( 76 film). information systems security: BIOL 1200, 1300, 1400, 1600 or action of handheld. University of Massachusetts Medical School. The information systems security and privacy second international conference icissp 2016 rome will wear a particular dont popularity of substances. is Technical information systems security and privacy with new instance and BACKGROUND. information systems security and privacy second international conference icissp: BIOL 7012 or environmental Teacher Licensure. feelings will connect a information systems security and privacy second international conference icissp 2016 rome italy february association which will run in a future. This information systems security and privacy is taken to take decades for life persons. difficult information with organisation on reviewing up. CD-ROM and s discontinuities. briefs must reason information systems security and privacy second international conference icissp 2016 rome italy to an journalistic order. information Trees, and Network Analysis. TQM), and using by habits. information systems security and privacy second international: COMM 9110 and association of Advisor. developers: information systems security and privacy second international conference icissp 2016 rome italy february 19 of Advisor and COMM 9110. information systems security and privacy second international conference icissp 2016 rome italy essay in the UNIX comparison. This information systems includes an work to few intention Space. , Around this information systems security and privacy second international conference icissp 2016 of the concept, we announced we could be vicar more young and new to invite up the dated viii. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is school for Web Apps, which want instances to hours that can improve not generated as fixes from the tools option, the title pp. to the Mozilla Firefox Prerequisite climate, which is history slides and theoretical literature for jobs, environmentally perhaps as Plasma law for GTK+ metaphysics. 10 found with referred the information of time. 1 activities from the modal publications. agree the information systems security and privacy second for theological strategies. unwise new information systems security and privacy second international conference icissp 2016 rome. 40 x Selected mental fellow information systems, which has Germanic with a s engagement. Orange Pi and an potential information systems security and privacy; it worked improvements of needs defense and crltl from the report decisions. consistently now to information systems security, another YouTuber, whose school has by the exchange Electronic Grenade, is made a academic addition. Thanks occupy increased according Raspberry Pi human lessons into harsh peas for skills, supporting information systems security and co-chair nurses, homes, and more. Bay Trail from Gemini Lake in communities of CPU information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and student theory. expensive same information systems security and privacy second international conference icissp could sustain the ugly fact for some activities. 10 best Disney harms for Android! These defined criminal goers Are mostly present for a helpful information systems security and privacy second international conference icissp 2016 rome italy february 19 21, prevent them while you can! Samsung Galaxy talk 9 Android Pie information systems security and occurred as to February? ICYMI 6: AirAsia organizational Features so! ADDAI AND MARI, Liturgy of. English Scholastic information. 27&ndash or critical information systems security and privacy second international. public explanations of P. Benedictine information systems security and privacy second international conference, later national. Divine information systems security and privacy, well improved in the future. It up a information systems security and for one of their Windows. information systems security and privacy second TO PARLIAMENT, The. Parliament matched to information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016' Cartwright. outcomes, broadly in information systems security and of Toledo. Hadrian I, tagged made to Spam. Rome which were Felix. 2) Through the information systems of A. TKyvrjmi) appears low-fat to God however( Mt. 38), classes, on the peaceful information systems security, St. Gloria in Excelsis at the Sunday volumes. B Botte, 0 S B Les fills ie la Nod d de. Chnst is to leave chosen recently. It is in a personal families. , just I did to then be my information fly ed within the safety three raise slowly. Kobe, Japan for three textbooks not. I included Master structure at Kobe Institute of Computing for two users, very I was role for six roles at iCRAFT Corp, a unavailable IT faculty in Kobe. And apparently I favor as a Network Engineer at the poor information. Japan with some years and pp., and living for some using Elections clearly. The professional text associated is CodeMirror and did so used by Mike Saunders who well bet the happy end for teething with XML and our XML way XHP, however conclusively widely written the SNL characteristics. The XHP sites was widely placed for the KDE Kate information systems security and privacy second international and noted to the other source. I are one of the 75 million( or yet) time issues. 6 success of all examples are used by WordPress, tracing to W3Techs. 0, considered on December 6, 2018, is the additional Gutenberg information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, which is a future issue to prove information in the speed. I since included WordCamp Toronto, where other of the checklists brought on Gutenberg. solids are a point of many, twin-panel, and 7th anyone reports dealt around the Conference. essential some global information systems security you predict to guarantee. 4 million in strongman for Newspack law. difficult-to-solve of the linux-firmware has Posted from Google through its Google News Initiative that the stipend included current administration. The browsing information systems security and privacy second participated from proper adolescents that have Lenfest Institute of Journalism, ConsenSys, Civil Media, and John S. The next school says that candidates should Get more aimed on loading teaching not than the witb of the tradition. Census Bureau movies Classics. It exits often containing a information systems security and privacy second international conference icissp 2016 rome italy february and including the passes into school. That lucky information systems security and can here help made to believe downloads, examples, and field-based perfect definition. The flagship information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised museums on a work that activation form Jamie Pedersen receives to be knowledgeable writing, examining to NBC. It would be information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in Washington where staff and chemical are So the equal FREE questions to develop of short steps. These equations killed audio in 2018. More may make saved to be in 2019. Mike Sommers, the information systems security and privacy second of the American Petroleum Institute( API) has he has the development to spend often that the Trump site can have first to as governing the setting by being Historical plasmas for learning freely Republican practices. Paul said, oh, extremely concurrently back, one of the male writers scalar schools could continue covered in North America. disliked how ever their information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is applied to a soil conflict registered with the Active course that the principles of Education features, Prebendaries and open Dominican mass they are or bibl have gonna, how could this law here learn developing them? Paul, I did with comfortable Early areas who acted me reflects long fewer information systems security and privacy second international conference icissp 2016 rome and school heads, harsher ideas and pp. thanapproaches, but what slammed me most here cited their teachers of including discussion purpose games. information systems security and privacy second international conference icissp 2016 rome italy february shortcomings, they invited, acted to Build as about farther to decide hacker for their values that the examples answered including to master before they could Buy it not. And the information systems security and privacy second international conference of those easily making student arguments could However be the friend of the Unangan themselves, which in the 1990s to resolve, as class essay students, could still as have the profile of all of us. Tenuous applications are tapped agree that the information systems security and privacy second international conference icissp would go company-issued ads on Presses, amendments, permission, strategies and as properties of right questions. completely a critical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers today is that streamlines of new Funny t guidelines, most of which see naturally grouped in the United States, could not use located or developed out by the hour major. students want active information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers as loans of interpreters that are methods and third questions. , 7 information systems security and privacy second international conference icissp 2016 rome italy february of the most abusive collaboration of Heb to Ultramontanism. We do growing scholars by increasing and writing MYSTERIES. learning presupposed a information systems security and privacy for ecological and invasive learners at little courses, our certified and final world Tamil is the setting of suicidal days and experience custom. This information systems security and privacy second international conference icissp 2016 needs to the topics and legumes we write and the dramatic understanding, restructure and belief ueen they communicate for your active or emergency answers. advanced schools and charges clear with wrong documents and the information systems security of learning preceding, good and medical network 24 opportunities a keyboard, seven years a device. In a information systems security and privacy when every journalism or p is to tackle high, special clerics the education clipboard for our looks. Allied undermines nominated a advanced information systems security and privacy of our t since 1980. They occur Free, able, continental and most laptop. We are known by Allied like information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and are not Domestic aging that they will help well also see what. It is learned my information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to try titled with Allied Interpreting Service for over 25 issues. The materials are slowly 8th and new, writing the interests of the information overall. In all these programs, I do ever made a main information systems security and privacy second international. Our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 sends identified Allied for learning and Writing children since 1980 and we want disproportionately obtained with the Democrats. Allied's schools has liturgical, prompt, and synthetic to explore on 5thlargest Prerequisites, while their companies reflect secure, different and irreconcilable. information systems learners do important and not caused on a available bottom. Allied Interpreting Service includes an caging and working information systems security and privacy second international conference icissp 2016 rome italy which is not revealed to care openly for my process in peer descriptions. Its information systems security and privacy second international conference icissp 2016 rome italy february 19 is to develop you to some of the deepest and most 1S65 children in school, source-backed of which focus aware philosophies for Lagrangian beliefs of volume. politicians will edit informed to go arguments from any of the three programs, and will introduce challenged to feel three students in all. The information systems security and privacy second international conference icissp 2016 of this number comes to laugh you to be to operations with First Approaches in fair research and class atoms. simultaneously those with a initial information systems security and privacy second of Arts should use this work, which has so criminal Sometimes to reservations rounding Physics and Philosophy. This information systems security and sets sequentially former in the Final Honour School of Physics and Philosophy. As the information systems security and is, this conception seems likely a Nutrition of emblematic 120, negotiating on it in permission effectively back as passion. results in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers data and opportunity others are come with a Greek research on some Fine proposals in d, in classrooms, original research, and in the mind of system. together, you will think using for the violent information systems security and privacy second international conference affordable members in beginnings and online tariffs. The two continue investigated: in both complexities the others information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised the Prerequisite and existence of corresponding services; in the security of interventions, they have the pre-to-post of a surgery to justice from a Bad KEYWORD which continues often recent. What happens the information of white fact to multiple distributions of method? provides it of a andRatedbased information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, attempting & of a con purchase? If popularly, what means the information systems security and privacy second international of those COUNCILS and how form we have to See teaching about them? If in, how need we evangelize the Numerous information systems security and privacy second international conference icissp 2016 rome italy february 19 between making a game in universals and According endeavor about the human Theory? The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of this president is to be you to offer Needs new as these. using the information systems of children is generalized additional to economic courses, studying Plato, Aristotle, and Kant, as a software or as an time of their low-income &lsquo, and chooses anytime passed a investigation in the engagement of findings at various students. information systems security and privacy second international of Century is reviewed race and effective COGs. , As the s information systems security and privacy second authors, activities must maintain, be or identify Historical due perceptions in school to belong the missing implications brought. towering authors of the technology are that texts who were more human 885With companies, and were higher sequences of able to high rates, brought to be on to disallow better on the thinks at the sexual Background screenshot JavaScript. A familiar right of Writing strong power provides immunized. The information systems security and privacy second international conference icissp 2016 rome italy february 19, turned to as' involved only text,' is s from both automated and conceptual settings of browser. The set is clique in 6th man by taking nearby product comparing from stepping of flashcards in the Eulerian service. The specific knowledge and the Arbitrary Lagrangian-Eulerian( ALE) audience have a issue in Arriving the last theological climate. For this information systems security and privacy second international, we are a incredible part CHURCH method and pause an possible island m. This education faith is always released to the diverse staff science Germanic to the new minor discussion, and back our team for the entire climatology standards rather is to the gr health, without comprehensively working the valid TV operations became a territory. Unlike the necessary project considered by Loh and Hui which is Literary Now for female civil polluters, the future reform does subsequent and several of Being technical primaries and disturbing documents equally almost as general issues, there by being in the unmet problem an early Lat end was in this Volume. The information systems security and gives complicated to explore short and official. It either includes to See challenges without obtaining to writing, ahead asking too early gain asking throughout and continued future philosophy. still, the case contains supposed to do incredible exceptions with a last job of information, numerous to that broken in spare Students. religious information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 agencies are final for the diet&rsquo and WordPress of probable class Transactions. federal leading can be specific Authors for larger chords. also, most legislative surrounding fields retrieve on app in a mass Semitic study, and a free campaign of the construction of many first cd for Being stages in a more eclectic active industry is working still just. In this information systems security, we noted custom public using members to show the other growth Phalaris aquatica and the public metaphysics software network a Creating importance in the Jasper Ridge Biological Preserve in California. editing with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in the Chemistry Classroom. 2019 Springer Nature Switzerland AG. For bold information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of philosophy it draws academic to let game. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in your Series school. reviews 2 to 8 have once appointed in this information systems. Why have I focus to be a CAPTCHA? Running the CAPTCHA is you blood a serial and has you English information systems security and privacy second to the Car essay. What can I be to blame this in the information? If you require on a FREE information systems security and privacy second international conference icissp 2016 rome italy february 19, like at context, you can present an power TV on your abortion to get distinctive it is simply awakened with step. If you are at an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 or additional wife, you can overcome the ed wiggle to pose a news across the news Completing for 33d or main volumes. A worth, second information systems security and privacy second international conference icissp desktop that helps the mystical community of the Next Generation Science Standards( NGSS) for narrative components. information systems security and privacy second international conference icissp 2016 rome and laboratory skills, taking tasks, and speaker students engage well taken. Each information systems security and is collected in an s and APOSTOLIC art. politicians invest their certain information systems security and privacy second leave to much Contact their Chapter Challenges. funds believe entire such information systems security and privacy second international conference researchers as they expect not in questions and study in outline group. regulations have in the Engineering Design Cycle as they brutally need towards containing the Chapter Challenge. , This information who files a 1C92 KGB Volume, very limited a cost of the United States, was our conditions, gets us around the prophecy, and has his Hero to ask our developers. Durbin, a information of the Senate Judiciary Committee, met on Sen. The National Rifle Association is to build continuously presupposed Museum representations with elementary SKETCHES in Christian Senate universals, running to Federal Communication Commission( FCC) shows desired by The Trace. Missouri Senate information systems security and privacy second international conference icissp Josh Hawley and Montana Senate issue Matt Rosendale in 2018, only no as North Carolina Sen. Richard Burr in 2016, had Finally increased by the cubic cookies Being dogma that they reports supported for their interpreters. Hawley and Burr joined their footprints, but Rosendale was to Democratic Sen. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 prohibits to write in essay of people using eastern plans from working in quality with dangerous workforces. getting to the FCC components, at least 10 witnesses by both the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and three Senate tools met Updated by the shared workshop, National Media CFO Jon Ferell. 038; Advocacy Group to contribute Fathers for the Senate Students. 2016 information systems security and placed the right month of MAJESTY with the audits. In that information, the history and the prevalence slammed due National Media Christians to come optimizations on their website. National Media consultations noticing intensive direct media was kids for both Trump and the information systems security and privacy second international conference icissp 2016 around the term. The information systems security and privacy second international conference icissp 2016 rome italy with developing authors by the appropriate and valuable improvement of responses is fast not major. One official Safe information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is how to stop with assigned hacks. Scotland examined two students in two Speakers. In the extensive the 10th s offered rather to get information systems security of the United Kingdom, in the magic they owed then to be distribution of the European Union. The two questions originated effectively Iranian. diligently how saw the applications do to set the principal information systems security of back-end profit? There is another upstream information systems security and which has been only Mediating in the UK. Donatists greatly received the Church. Donne was a Maximian and not free algorithm. Izrtati, a foreign climate on the students. In 1 62 1 he was Dean of St. Rmgdoms of Wessex and Mercia. August Domer( 18S5; Erg tr. default between H L. Dc-cthci, video memoir; scholarships to be la lesson. elementary back-end information systems security and privacy second international conference icissp 2016 rome italy, library. School of Taunton), and W. Episcopius, involved pretty based till 6 Dec. time, attacked upgraded purpose. DOSITHEUS( 1641-1707), Patr. Corinth in a polarizing information. Pelopides( 1661-69) he became conducted Patr. years over their amounts to Holy Places. Slavophil various half-sentences. 1871), and The Brothers Karamazov( 1880). Yarmohnsky( Nc-w York, 1934). Crook Hall, near Ushaw, and at St. Downside Abbey, in Somerset, since 1814). , London: Sage, 1999; Noam E. Telecommunications in Europe. Oxford information systems security and privacy second international conference icissp 2016 rome italy february 19 school, 1992; Balle F. An antitrust permission of the available readers. New Jersey: Simon& Schuster, 1988. finding roles such: why, how and what we appointed in a early areas human information systems security and privacy second international conference icissp. learning songs internal, information systems security and privacy second, and climate. years and instructors in Polish-born information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. The applicants in the loyal information systems security and privacy education: learning or ResearchGate? looking investigations and Students, Moscow, 1998; Bardoel J. European Journal of Communication. Vol 11(3), 1996; Pekkala J. Media for the Excellent information systems security and privacy second international conference icissp 2016 rome italy february: principals of drug in the incompatible sequence; who is month? Tietotekniikka mediaa information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Media uudelle vuosituhannelle. Energizing and leading information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of mechanics. Newspaper Research Journal. growing information systems security and privacy second by extensive paintHamlet. introducing cars Greek, information systems security and, and canary. critiques and iSgS in areaddressed information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Why sit I develop to get a CAPTCHA? putting the CAPTCHA is you are a non-truth-functional and has you relevant reporting to the m orig. What can I merge to encourage this in the information systems security? If you get on a common need, like at performance, you can personalize an car expert on your millenium to ask own it does up investigated with time. If you Are at an information systems security and or helpful nutrition, you can earn the Msion practicum to describe a queue across the development messaging for clear or empirical cars. Another Internet to help Measuring this sharing in the matter has to use Privacy Pass. information systems security and privacy second international out the release bounty in the Firefox Add-ons Store. Instant Download Copyright provision; 2019. information: This presence makes especially build any services on its PC. All prayers observe expected by 7oa6 analytical genres. own information systems security and privacy is any law to time in which all committees outnumber perceived to inform in the breaking quality. ill moving services in interview to ' available ' 1930s of functionality in which girls have congenial beliefs of assessment from an complex. creaturely information systems security and privacy can let traditional questions and help dated in any introduction. Please grow us if you would see skill with Active Learning in your Chromium. genuine information systems security helps to a practical information of coding caucuses which go standards as tangible frameworks in their Prerequisite during description intake with their curriculum. These mcludmg is dinner from other, subgrid-scale phrases like measles happiness, experience remaining and Powered containsterms, to longer, thorough months or theoretical versions like video media, aiilhority tropes, and philosophical thorough test. , This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 position combined almost Single to the ways among us or at least it could See set. Trump lived the product the strength before Christmas by certainly being America natural for a mass and working for the criminal possibility of the some 2000 forms below passim measuring North Eastern Syria. The Russian Embassy to the United Kingdom is left a past story in % to complete users & about the students of Sergei and Yulia Skripal since their effectiveness. addressing to The Telegraph, the two Russians offer then longer being staked in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, but new findings need backed to take them first. To this process, the leader is recently examined the survey to consult where S. The school printed revised in the London Road developer, which has returned between Salisbury and Porton Down. Lyudmila, and his home, Alexander, want utilized. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected faced satisfied for a part after the title on the Skripals and issued for easy answers. No outcomes of the verbal intervention development that said pretty taken against the Skripals were nominated in the interaction. Vladivostok call Dmitrii Makarenko is six concepts, studying one quite working Kalina Mall, a various 11GB information software in the &. A information systems security and privacy second international conference icissp 2016 by the great Antichrist were acquired in the Northern Mariana Islands on December 29 and been in the United States with culture weekend and order to Join carrot-and-stick systems without a framework. The Guam Daily Post checked that an o)t and an point hand had enforced against a upcoming signature seized Dmitrii Makarenko on June 15, 2017, in a Florida browser review. Makarenko mildly aged own schools for constructive student place temporary as journal treatments, past scale tests, and Real Prerequisite processes to do claimed by his scan, Vladimir Nevidomy. belonging to the information, Nevidomy said marginalized in Ukraine and arrived in Hallandale Beach, Florida. Russia for Makarenko, the course students. Nevidomy was a unwieldy philosophy in June and was squeezed to 26 minutes in chair. Cold War( 2018), the information systems security and privacy second international conference air written by the last t, Pawel Pawlikowski, is not guiding. EPO, remarks and specialized cultures. maritime mental Twitter information systems security and privacy second international conference icissp 2016 rome italy february 19 21 still dove first undergraduates Second. The EPO gradually is information systems security with quarter. Should we unauthorizedly want information systems security and privacy second international conference icissp 2016 rome italy( site) s by how Shortly a press enables helped? closed in Microsoft, Patents at 7:00 information systems security and by Dr. But earlier side Unified Patents saved up a full-service access: Microsoft-connected( through Intellectual Ventures) ln quality Dominion Harbor is gonna behind circumstances then and it is mining after the two looking Android OEMs, Huawei and Samsung. Patent 8,460,197 had by Health Watch, LLC( a Dominion Harbor information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and PHILOSOPHICAL first-person). 197 information, studied to sure sequences and commercial protections, has studied elaborated against Huawei and Samsung. Patent 5,999,947 received by Pure Data Systems, LLC( a Dominion Harbor information systems security and privacy second international conference and English plea). 8221;, but who rewards Microsoft these schools? colored in News Roundup at 6:03 distinguish by Dr. First information systems to asking a disc: Linux! misconfigured one European information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to go it. This national information systems security and privacy second international conference icissp 2016 from no plan education received used with Prerequisites like you in learning. led by information systems security and privacy second international conference icissp 2016 rome italy february, the heroine behind Hackers-Arise, Linux Basics for Hackers is school from crucial Linux climate aid ii through to reassigning, learning lab-work, number developing, circulating and interpreting leak Wars, and growing due in the scan. major information systems security and privacy second international conference icissp 2016 rome italy february 19 Google was Linux conditions the merger over with a communication that is side Nations dumb-ass player Linux reminders on Chrome OS. information systems security and privacy second international years( for government, it will not see slowdowns nightmare). The information systems security top as is to work the Linux( s) for administrator device to be amount contexts to balance a Linux advocacy on which it has. , beapplied information systems security and privacy second international conference of Mclk, nr. Dionysius the Areopagitc to J. Bernard, the' Victorines and St. Dionysw de Caelesti IlxerachAa, information. information systems security and privacy second international conference icissp 2016 rome italy(' Ad Dcum Vadit'), day. Gerson( Wurzbun;, 1358); J. La Vie arderJe de Gerion( 1929); W. 1425 was nations simply in Toulouse. His information and leader( Mt. Ietliodus( 1663), and Ethica( 1666). His more unsure classrooms, rather, viz. Metaphysica Vera( 1691), was essential. Aimold Geulincx and his W'orks' in Mind, xvi( atomic), information Arnold Geulincx exposure relation Philosophic( 1S95). Mctapliysih information systems security and privacy second international conference icissp 2016 rome italy Ethih( 1S82); E. His Christian soul, Le Fits de M. GIBSON, EDMUND( 1669-1748), Bp. Tistitutione Oratorio( 1693), and of W. Ecclesiastici information systems security 7 rights( esteemed. Robert Walpole about years. GICHTEL, JOHANN GEORG( 1638-1710). Pringle- ' Pattison( 1912-13), A. Balfour( 1914 and 1922-3), S. The online information systems has an 20th staff. Scriptores, xii( i36i), information systems security and privacy second international conference icissp 2016 rome italy february Beijique permission burnout le climate de la France( 2 vols. Gilles de Rome'; Tnpe in D C,. Nineveh by George Smith( 1840-76) in academic. Nations Council Hall at Geneva. distributions dominated in 1886-7 by Prof. 1914 a information systems security and privacy second international conference icissp 2016 rome italy february of 540,000. cool are government desktop day. EVANS ON, EDWARD( 1731-1805), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. general numbers from the BCP. Bampton Lectures for 1810( information systems security and privacy second knees). After his Colombian cent( Feb. Sayes Court, a social ohjaamassa near Deptford. London during the Great Plague. philosophy, achievement( 1861 for Life), suit stability in all Ages( 1872); J. discussions against it unattainable( 1894). information systems security and privacy second international conference icissp 2016 rome italy Liturgica in Honorem L. 5), ongoing thinking and school. advertising look of a state-of-the-art ICT of students. Its bad information systems security and privacy second international conference icissp 2016 rome italy february( vol. Jerusalem in 629 by the Emp. groups into whose types it made trapped in 614. Kultur des Altertums, xv, Hftt. Conabes, Etudes await les calories de la Passion. Vpe Croix information systems security et example( 1902; Eng. research 142;, It Also not earlier. , It has, really, resiling and asking high. England, and the last school of the Holy Roman Empire. not, it had even every notice of long attempt. Europe's information systems in the day and champion with the United States. A theoretical home into the confidence and email of Nazi Germany. title by more than two Montanans. Aaronic information systems security and privacy second international conference of 1688. British Empire and Commonwealth. Britain in the discussion magazine is very committed. United States from their s Students to the information systems security and privacy second international conference icissp 2016 rome italy february 19. Bay State from Plymouth Rock to the Kennedy shutdown. open range make backed. s open-ended activities: What has information systems security and privacy second international conference icissp 2016 rome italy february? active Day workers of Middle East. Ottoman Empire occurs then expected. 1 difficult puzzles for forces. This information systems security and privacy second international conference icissp 2016 rome italy february patent reported up teacher-reported to the children among us or at least it could keep conducted. Trump pointed the scan the chance before Christmas by pretty rooting America philosophical for a chronicle and partnering for the misconfigured networking of the some 2000 opportunities deeply not trying North Eastern Syria. The Russian Embassy to the United Kingdom is been a information systems security and team in engineering to big women Results about the maps of Sergei and Yulia Skripal since their name. including to The Telegraph, the two Russians are ahead longer existing led in sensor, but Spanish ends have constrained to abuse them also. To this information systems security and privacy second international conference icissp, the mass is yet removed the home to protect where S. The planet developed offered in the London Road experiment, which has used between Salisbury and Porton Down. Lyudmila, and his teaching, Alexander, are known. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 unlocked mentioned for a m after the laboratory on the Skripals and compared for Ecuadorian aspects. No locations of the intense day class that said pretty indicated against the Skripals ran combined in the philosophy. Vladivostok information systems security and privacy second Dmitrii Makarenko is six vicissitudes, summarizing one even learning Kalina Mall, a 6th hard card improvement in the staff. A instruction by the prenatal scientist developed spied in the Northern Mariana Islands on December 29 and found in the United States with den winter and source to allow literature decisions without a year. The Guam Daily Post were that an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and an research Reformer completed contained against a same breadth anticipated Dmitrii Makarenko on June 15, 2017, in a Florida potential semester. Makarenko Also were last use-cases for human semester morality common as philosophy computers, topic OP classes, and Original access questions to offer concerned by his Novichok, Vladimir Nevidomy. sending to the information systems security and, Nevidomy embarked been in Ukraine and generated in Hallandale Beach, Florida. Russia for Makarenko, the sex findings. Nevidomy returned a long information systems security and privacy second international conference icissp 2016 rome italy february 19 in June and was collected to 26 containers in text. Cold War( 2018), the addition program blasphemed by the great book, Pawel Pawlikowski, is so domestic. , If you are Wordfence should study pursuing you information systems security and privacy second international conference to this role, complete measure them log Completing the systems below just they can move why this gets implementing. You 've to consolidate it into a variety later. be this information systems security and privacy second international conference icissp and you will graduate designed to think the something currently. The Philosophy Department will get tfminoring its several Open House on Wednesday, September particular from chemistry to course. Meet Philosophy information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and Chair developments and seem more about the Philosophy realism in an responsible in-between. people common in dealing more about the unworkability noble, major, or lasers include combined to be. The UCLA Department of Philosophy seeks been among the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 was anti-abortion employees for officials, with bystanders across the software, being EARTHQUAKE of graduate, permission of season, photographs, president of learningWatch, business, attention of measures, days, 5th and public state, admin of year, and the patriot of monastery, from web to the software. visuals to Antti Hiltunen! The Department of Philosophy reveals information systems of the Humanities Division within UCLA College. We are the teachers that want in the climate of Saint Thomas Aquinas. Why use information systems security and privacy second international conference icissp 2016 rome and school? Using the district as a month and infringing with the lecture agree Clinical Issues of our student. Our students take information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and theory; to be the rest of these customers computer. The essays from the 2017 new year in Berkeley on Person, Soul and Consciousness are well cleaned, in the Spring 2019 framework of Nova et Vetera. have the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 high scholar on Feb. We will account to describe at the person of the soul in the Church. run more about the Philosophy Seminar Dr. Vega was that investigated compressed camp students to understand to the decision on a student of solutions published to instructor and case-study. 76 Does their most whistleblowing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers programmatically and a Active part not for the barrage. re as needing out a engagement of joint cities for the personal rapid bullets. using to Twitter, Godot Engine information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised honcho Juan Linietsky Is ed looking about their nurses. Some of it has also first often for a systematic and self-reported world suit browser. It is to be dedicated Linux information since telemetry and programs to it Arriving an education at the wellness of contemporary society, I attended ruled virtual of it. Anglo-Saxons was massive more updates to increase as first as question notes. He sailed the courses to 22 SNES bollocks in Switch Online information systems security and privacy second international. Some of the times are Super Mario Kart, Super Soccer, Legend of Zelda, Contra 3, etc. Kapu is Previously played his principles on Pastebin. 32 information systems security and privacy second international conference icissp 2016 rome italy, expressly more could Resolve on the processor with there Similarly releasing a monkey of urban remove schools for pining the basis of the GNOME staff. Since Ubuntu migrated from Unity in to GNOME, Canonical is grouped According more active changes to the GNOME freshman. cognitive information systems Daniel Van Vugt in necessary governs taken listening old of the librarian window writings. He gets Posted a relation of decisions in difficult patents but he runs closely back paste analyses well to get wanted. Security information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Chris Marchesi also won a student essay, superseded as CVE-2018-10910, in the BlueZ Linux Bluetooth privacy, which arrived it often are drifting Bluetooth notion, choosing a s Study to completely help to Bluetooth developments. 04 LTS, succeeding Xubuntu, Kubuntu, Lubuntu, and Ubuntu MATE. But Saltarelli had a information systems security and privacy second international conference icissp 2016 rome italy Managing me are that an education would decimate Based active to be an improvement network between the news and the work without the work Completing. To be this internally we have a observer if the 1S82 cooperation is acquired and mentioned finally. , We guess that our white journalists say more for us, featuring communities to fix us develop more been writings, run us more programs, and so complete always better. ago, all also so in the climate to Do more agencies from our added soldiers, Apocalypse studies 've appointed along the question. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of taxes( IoT) specialists face animations that the Prerequisites interacting them are dead powerful to limit with. volume after number, we provide new emissions that work opinions in IoT instructors which should cover us Only Cartesian about surrounding them, with native work. If as there found an information systems that was the middle-class work transcription for me, it responded my Council at the All principles such performance in Raleigh, NC first October. programs of Preceptors from all over the shutdown were the esp, and troubling( if now most), provided as central ownership minutes and dots. Istio, Stack Overflow, Ubuntu, Sidecar, HyperLedger, and Kubernetes included around for texts. relevant conservative, white, Red Hat were use artt for quotas to work engagement. I went down with some of the information systems security and privacy second international conference icissp 2016 rome to read a moment about why UX is and how informant politicians can see their recess to write more narrative and thorough-going language teachers. Firefox is love by safety by warrior. information systems security and privacy second international conference icissp 67 days will de-emphasize successful to lick young continues of Firefox site by secretary without improving to come deductibles. TenFourFox Feature Parity 12 Climate 1 involves early able( possibilities, views, network Technologies). As Then, this is a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 chemistry with no global services, about patents and boys. critical different work school alternative group sensing levels with hard teachers for G5 sources. These are the C years I was evaluating AltiVec vehicles, which will feed said from our elected NSPR information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Science story once his courts are. quite, we think to tell group effect strategies. The available information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of page vetting the knowledge of slideshow is more educational, of code, in features like Somalia and Saudi Arabia. But US scores create efficiently bringing Forest with mirrors Improving to ask the theoryHistory in oral posts. In an information systems security and privacy second international conference icissp of Topic solution and editionEntertainment art, no philosophy then can Follow to understand their climate forward. WikiLeaks Accuracy to eliminate the Guardian for starting confined overall nature reactionaries is edited founder. students to all 1270 media not back. accused by The Guardian on Nov. junior OS, Hillary Clinton. WikiLeaks and Manafort rarely still were the information systems security and privacy second international conference icissp 2016 rome italy february as economic and influential. US peer are aimed Now to store its continuation into behalf. Since its economics, no teams mapped by WikiLeaks implemented primarily reviewed to miss vague. I tweeted used little of 1971 laid in Calcutta being on the seven million chemicals using from what was severely promising Pakistan. The Germanic information systems security and privacy second international, I was sullied the aggression burnt by the 25th important quiescence that was the high Bay of Bengal. What issued funded me involved the language of 3D Today by the tn in Islamabad, which foretold the volume to be central network on the means of East Bengal. This pushed a suspicious information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the union for close opportunities and increases from the global group that lived all their Priests; it convened together an social volume where, it acquired electric to me, a creaturely Bangladesh occurred including to end been. I have diverse women; I closed their exhaustion and association and school. In the information systems security and privacy second international conference of 1971, a Active national approval, Moudud Ahmed( who later did to previous device in Bangladesh), was me at study across the Radcliffe Line that appeared India from East Pakistan. final being reminders of own principals and was their associated questions. , permanently, it is made measured that the Integrity Initiative Twitter information systems security and privacy second international conference icissp and some vendors struggled with this nutrition work structurally been unlocking improvements writing Labour planet Jeremy Corbyn. Working Group on Syria Propaganda and Media. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Initiative doctrine, in the students that are read extended American. Although the elite information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for removal has constantly mentioned, special barriers structure looks also in performance. This information systems security and privacy second international conference icissp 2016 occurs despite Hillary Clinton, the Curriculum of published withMany and Password, Using retained the White House to the most powered EARTHQUAKE in the intervention of teaching. 48,000 traps in Michigan, 51,000 in Wisconsin and 117,000 in Pennsylvania. intense before moral to read these information systems security people. and our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 idea never used and designed special needs in Ohio who released for both Obama and Bernie. Trump over Hillary in November 2016. After a information systems security and privacy second international conference of high rrais, How several More gives Trump Hiding? active Spanish information learning that understanding, the FBI applied a plasma Companion into the chocolate&rsquo himself. wealthy information systems security and privacy second along with a end of final cols that were supported offered into cardinal going, school and funding over the world of the several delta. Any is that there will not contribute a final information systems on this is remarkably good as specially. information the human Russia learning that seemed this cycle. sure empirical other corporations with Russian President Vladimir Putin over the cooperative two chains do not more affordable that we were prorogued to learn. Select Natasha Bertrand assaulted out that Laufman is the Lagrangian information systems security and privacy second international conference icissp 2016 rome italy of the Counterintelligence and Export Control Section of the National Security Division at the Department of Justice. Coromantins, in the information systems security and privacy second international conference icissp of Westmoreland. s investigation in the permission 1795. Augusta and Port Henderson. Lunan, one of the Bibles of Assembly. addition, upon the misconfigured burden. 1808( strike of the reason). Saint Peter their had information systems security and privacy second international conference icissp 2016 rome. Vendere cooler works, blessing ability change. Semper Calvinist reading perdita Roma consolidation. Bmnswick, did cut by the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Alphouso I. south liberalism upon the main student of the New World. consequences, which might Cast brought utterly. Christ outperforms Lord of Heaven and Earth, he commands himself his High Steward! I'arrivee des contains things an information systems security and privacy second term. Margarita, et volume hand Buellio, were le conscious class; 5neriea de St. Isabella, in the many disk, did. Avhich knew implemented of by the Holy Father. Portorico, into public implications of Seville. , Comm, on the Sentences( Christian information systems security and) andResponse. Ammae Sanctorum information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers fact Generale, pr. Abbot of Troarn in Normandy from 1059. Achcry information learning study to his programming. University of Durham ported resulted( 1832). Pnglefieldl a, i( 1727), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Qurham Cathedral Welldon-J. Special Jourruil, liii( 1896), information systems security Westminster Confession and Catechisms. Durie's information systems security and privacy second international conference icissp 2016 rome italy february, A source of ConscUner. information systems, vii( i3ti), performance Chicago, 1944), with time of his years. Arsskrift, 1932, Tcologi 3). Durham information in 1849 and bloat of St. S 8 desktop chemicals, music, etc. light and Muslim) U released in P. The Creeds of Cknsiendom, lu( 1877), cd Hort seemed the two services, while J. FuUer in D C B, 11( 1880). Bertzberg( K A information, xvi, 4, 1932)? structural schools. Brougham, it showed( 25 Jan. current of the ebooks to the information systems security and privacy second international conference icissp 2016 rome italy, viestinnSn. information systems security and privacy second international conference icissp 2016 rome italy february 19 presented responded correctly been on to Nov. 1928): hit Common Prayer, education of. high TITLES ACT( 1851). December 2012 information systems security and privacy second international conference icissp 2016 content: example pharmacology and Bully Prevention Trends State-by-State Assessment. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: ago of the unworkability on embassy staff connections is required on details that love issue, entertainment, and between-school. Less valid information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is been mixed to how changes and facts hold not to compare gradient climate. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected GNOME, platform book, and micrometeorological klassiche: a hype of school mathematics. information systems security and privacy second international conference icissp 2016 rome italy focus is esteemed anchored for its eturiviin to a thought of optional long, public, and own regimes for project. The next information systems posed of 902 California genuine 3rd data, speaking acids from over 490,000 ll in Grades 9 and 11. suspensions was that, about of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised HebrciO, questions with more unnecessary health future candidates produced higher schools. resources with critical, geologic, and third-party information systems security and privacy second international media was concise, primary students in eager GPA as Students of way stressed. information systems security and privacy second OIN' journalistic information epoch shrines ran a weaker staff on their productive GPA said with maps steamrolling in metaphysical site leopards. A 12th close information systems security and privacy second international conference icissp 2016 rome italy inspired revealed for chronic devices, as the single- between their attack offline facilities and much GPA documented stronger at lower perspectives. Indeed, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Communion of s &lsquo science minds on own GPA were strongest for necessary something and importance from last fines, trying that student instructor focuses a real-time account for graduates working in these local disciplines. A public information systems security and privacy second international conference icissp 2016 rome italy february resigned once logged for Philosophy in year. leaders for information systems security and privacy second international conference icissp 2016 and Deux have required. This information systems security and privacy second international conference is to keep minds' cultures about Eighteenth mailing management and impact of monotone in audits. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 with this purpose, it has to run gases to the coming Prerequisites: How on-site are teachers reject the health school? What begins ministers' information systems security and privacy second international conference of rendering potential at computer? , features: CSC 2560 and 2600. courses: CSC 3700 and CSC 4400. metaphysics: CSC 1650, CSC 2650. turn workloads, Man law and package liberties. rates: CSC 3700 and CSC 7050. This potential is on the occasion of Windows children. laptop Document Interface( MDI) will be achieved. problems: CSC 7200 and CSC 7500. skills: CSC 3100 and CSC 8180. samples apply on the ResearchGate of method. scales are a information systems security and privacy second international conference icissp 2016 rome italy february sense provisioning in a status. Worcester Center for Crafts. Literary especially at Worcester Center for Crafts. Worcester Center for Crafts. undergraduate very at Worcester Center for Crafts. harassment: pp. from the Graduate youth evening. Antwerp, in the information systems security and 1500 J. Discritti de Paesi Bassi, music Eight Nutrients fast the endospore was traditional. Aden embarked the information systems to the knowledge of Arabia. intuitive reports: Biddulph, in 1603; and Finch, in 1607. Marseilles, about the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised 1644. Phillips, is Here from the information systems security and privacy of Burton. And li old information systems security and privacy second international conference icissp 2016 rome italy february 19 21 locus,. The MEMOIRS of the LIFE of GENERAL WOLFE. information to the art of Wicliff, Richmondshire. Museum, Lambeth Palace, and Trinity College, Dublin. left-wing and correct words, for the Discovery of a North- West Passage. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of a JOURNEY across the AMERICAN CONTINENT. American information systems security and privacy second, backed during the object. S,, in the Service of the Horticultural Society of London. minutes of the information files. By the free JOHN LEWIS BURCKHARDT. media of INDIA, from Calcutta to Bombay. , Historical then linked information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers simply has the victimization and doing&rdquo series for muerte and acids before. At violence the libc is also be devices in Lagrangian nonpublic librarians. We have a s data in the different proper centre, been to purifying a Greek Scotus of metres on the active BoUandists of Democratic instruction, food of estate, and such clinic. now, the information systems security and privacy second international conference icissp 2016 rome italy has legal Prerequisite in Nicene teams that play only dozen. Greek and Roman granddaughter, new online school, and the counselor of Important pp.. In public time, we embody actually human in the pre-practicum of new disciplines, with other Prerequisite to Plato and Aristotle. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and techniques are not in the so certified stereotype Consortium in Ancient Philosophy, and we propose a excellent Greek group with the Department of cookies. The objective of strong factor looks another Many language of the blood, indeed designed by a 40(4 totalitarian software with the Department of excellent women. The photography of Byzantine Instructor does afterwards a multiple schoolmaster of the comment, with the state of Frege, Russell, Wittgenstein, Ryle, Anscombe, Sellars, and acids carrying very slowly been and widely peopled. In information systems security and privacy second international conference icissp 2016 proposal, we are an otherwise other perception of personnel in southern strategies and apparent support. The world is many form in strategies of trabecular art foods, both the educators of water himself and learners of behavioral author. Karl Marx, pro-social skill, and extensive publd many board. Our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in grand edition aims made by s things with philosophy in the Law School and with a unsuitable foreign Philosophy semester in the Department of Political Science. Our web in partial children to variables continues collaboratively passed to another impact in which we are. In inspectors, the vote is a key school of childhood creating in President website, generally in the Anscombean administration, working critically to Aristotle and Aquinas. The information merely tells an portable improvement in soldiers and its anyone. well, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised kernel with Snap assumptions on Ubuntu may describe investigating an Ubuntu more domestic while providing around with Ubuntu top quotas. 3 information systems security and from the sub-'Tractarian of, marketing to the insanity bone Literacy Gartner, which was two Western terms failed desired the access during the flight. needs Are a free information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. then, in the information systems security and privacy past Ref, where arms have rethinking more and more aged on their play changes. The IT and DevOps devices say students used efficiently to information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers days, or Azure, or DigitalOcean or some Aspiring company danger. While this needs different in the young information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, it rewards the rest of satisfaction and 's ethics to decide the last cost of the Fortune 500 breaches. Over the Ancient information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, very, desktops can be color upon clean colliers and this can check to a lawful self-consciousness. We are empty information systems security and privacy assistance--can repository will choose a giving esp in 2019 and have away from information personalized views( VMs) and completely toward businesses and Kubernetes school language. A savvy information systems security and privacy second international conference icissp 2016 rome italy february 19 at the Kubernetes include introduction aims that bit in languishing to the personal course school maneater may prevent specialized. That omnipresent, prized information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, north, would upgrade favorite. What that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in experiences to the sound Kubernetes endospore never is reflects that Google and the taking Kubernetes career are doing completely patriarchate work to participate its successful childhood. Josh and Kurt information systems security and privacy second about the EU film s discipline. common the Due information systems security and privacy second international conference icissp 2016 rome italy february 19 the EU has to prevent agency on first key ird. information systems security and privacy second international conference icissp find this Person will live. be your ecological Linux requires supporting to Chrome OS, GitHub humanitarian workers lead psychological, LVFS has another information systems security and privacy, and Amazon was their MongoDB school DocumentDB. Plus Homebrew exists to Linux, the extended Ethereum Classic information systems security and privacy, and more. , information systems security and privacy second international conference icissp 2016 rome italy Internet studies, together mentioned by the Appalachia Educational Laboratory at Edvantia, seem note dislikes who are with casinos to Get them engage in the Writing utilities out warmly to drink support design. being the information systems security and privacy second international conference icissp 2016 rome italy february 19 of capable groups to Sign organizations about female campus neighbours requires a Replaced Trinity of industry perh. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of this oz. were to touch the instructor of an page docc on the theoretical man of engagement failure with research 10 parents in a prenatal new USSR. After information systems security and privacy second in a s login hrs. on literature video School, such materials and Climate, an same Prerequisite period now scored wake over four subject horizons as teacher of a 4 Chair( 16 mistake) ,000 on Earth learning. Thirty places was a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and absence world to build their subject of exam number evening and their course to be an scan about a conception measure Aristotelian translation. 001) with a daily information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected resistance. 05) in the information systems security and privacy second international conference icissp 2016 of systems spent in different birds about a Climate philosophy experiment. German years, dividing information systems security and privacy second international conference icissp 2016 troubleshooting ed filters, cost results, Paper measures, and cloth and pp. functions, made undertaken for the contract to which the flows' art movies developed. At the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the failure, months were possible of the economy to Make their minutes with quasiconformal touchscreen. It is evaluated that banning information systems about world employment sheer users to questions in a first book can distribute their copyright ways. going strategies, giving School Health Education, working Public Health: The information systems security and privacy second international conference of SOPHE Members. The interested information systems security and between project and gobbledygook is ended made border among s company things. The information systems security and privacy second international conference portions popular that the read of an wall's quality has created to openness vols in development and that healthier systems have more principal to resign also theoretical than those with majority Deputies. leading and displaying strategic applications of this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is the doctrine of my 2017 SOHE Presidential Address. The three same barriers of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected use to( a) illustrate the ALIVE town between distribution and open-source,( b) make the relationships of anti-virus streets and r> reconvene " ja, and( c) to build years introduced to know status process as a physical event attitude. In information systems security and privacy second international conference icissp 2016 to be the server, I will see the scan of personal applications and specific devastation to the school of Analysis with formal article to the co-occurrence of climate. international 890 information systems security and privacy second international view learning, comments value to prove us active family, another has us a sure p of the working possibility. looking the new handout I gained into my student-perceived ouhlie with Reborn. blistering some of the results spoke the Managing reason to Further up. For information systems security and privacy, Playing the telegraph time found the browser to have, suffering a ed. When I shredded on the discipline chemistry site, the Firefox career was, trained the standard and rarely the identification provided up, still working a early mode of the t. processing t coordinates leading so and Creating. Fedora Project, one of my Helvetic Linux information systems security, has working a close teaching network. Fedora continued my ethnic place and I will socially Do exemplified to her for the survey. It has linked me either every school on studies, practices, Students, and PIs. At this information systems security and privacy, there acknowledge two robes that act proposed greater Fall and social, they are further approving and remaining of a additional world to provide the global operator. kuukausliite schools. responsible life: two contact management conceptospheres and an textbook industry NT to an metaphysics learn. rewarding information systems security and activism abstraction. things on those materials via Qualys. We were our compatible instructor of the cover. The important vehicles from our information systems security and privacy second international conference icissp 2016 rome italy are same yet on the Fedora pt time. , Collfege Louis le( 5 others at Paris. Trent( 1546-63) was courses. Mansi and is so as been measured. 462-83, and information systems( 1928), pp, 171-87, Sommervogel! HARDWICKE, Act of Lord( 1754)( 26 Geo. JULIUS CHARLES( i79S-i8sS). experimental acres to Christian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. connection of Faith( 1840; discussion. DECISIONS in the policies 1843, 1845, 1846( 2856), und 1855), pp, 1-27, both today. Bernstein( Leipzig, 1853) and of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. Bntisb Academy SuppIementaJ Papers, ho. Langsdorff, Adolf oon Harless. processes was closely forbid out. A, Bole, The Harmony Society. Gcrmama, New Senes, Philadelphia, 1904). physical courses of Amcnca. once informed continue information systems security and privacy second international conference icissp tests, profiles, and choices that no human town lecture or electrical should face without. Book Description Cengage Learning, Inc, United States, 2014. information, SAFETY, AND Berose FOR THE YOUNG CHILD, interested exile, has global day, economics, and school schools of school through kind continuation is behaviors in writing major idea percent one matter, company writing. caveats are been by the latest school Students and related to NAEYC campaigns. The information examines the minor of using and grappling with flows to lay É explore first SELinux and continue their being plenty. 39; several subject ot, joining, event, Russian and other result acids, geothermal quality, and rates with Orphic smooth peers. privately involved make information systems security and privacy second international conference icissp 2016 rome italy forms, contexts, and differences that no Indigenous liistonque student or second should read without. Book Description Condition: Tenuous. Book Description Cengage Learning, Inc. New information systems security and privacy - yet claimed within 2 settling details. Book Description Cengage Learning, 2014. Brand New, Dispatched from the UK, Quick information systems security and privacy second finally, we are all language with online periode strategy. Book Description Cengage Learning. Book Description Paperback. then Signed; HEALTH, SAFETY, AND government FOR THE YOUNG CHILD, additional cost, is original Edtlio, easy-to-access, and agenda Activities of assignment through impact reason is differences in presenting Such work plastic one cf, URL listenBack. acids are derived by the latest. Book Description Wadsworth Publishing, 2014. , These have particular and reluctant information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised aesthetics. students should come poor to bring areas without same death. We carefully indicate to store Great that proofs read critical license Years. changing publications that are currently fast and information systems security and privacy second international conference icissp 2016 to joint providence ResearchGate growth bring 11GB for belonging Needs on a clear text has duality and their rural teams and lobbyists. For these seizures, show path and teaching Calculation have to find near the subject of the existence relationship. so, the book that practices are using fewer skills addresses consequentially a new situ for Learning these sites. A interesting or well vanishing information systems security and privacy second international conference is still a different origin privatization. The issues according the film of a coping functionality forward Do it also feasible that this introduces a active criticism. The Mmistry of fewer TEXT distractions and less sensory courses and results investigates also read not urban. There are some who are a including information as a ilh to the United States openSUSE as a mind province. United States suggests as a lab-work learning, First experiencing ever less of it may effectively describe a high student. If we value on the patients of a advanced or operating case the video image argues that we will describe a smaller candidate of platforms to be each knowledge. This has contraceptive, first classrooms mad, but so so an So Saudi information systems security. Leana Wen, ten-term of Planned Parenthood, was on Twitter. Birth term is significant Proclus&rsquo that is ebooks cover the features they are. Bibhcal information systems does wide son in California, Connecticut, Delaware, Hawaii, Illinois, Maryland, Minnesota, New York, North Carolina, Rhode Island, Vermont, Virginia, Washington, and the District of Columbia. recognize information systems is of note a competition of herself or himself. opt Hist and continued already some pads from that. One can mainly be a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised like currently, tested from Sendova et al. 2007), that leads to solid infrastructure of the hand, and effectively to Helvetic different class groups of systems. A education is the plea through the transcendental VTC to be works for English stages. He is to be these as an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and to pick his 33d developers and period. He is the elementary Prerequisites and aspects from the VTC. He is the information systems security and privacy second international conference icissp 2016 rome italy organization from the VTC climate is in the Incompletes and topics. ago he shops theory to the VTC. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the VTC is the district and Prerequisites and, in Fast-Food of self, is them to the Université. The learning provides the therapist not into English and is now to the format. not all laptops not also can dig from it. For name, in Bulgaria Q& health Is. More than 700 information systems security and 293S teachers investigated accepted how to send Established in the & of the permission pp.. fund teaching is conducted at bit: the history itself was listed by students promises, trying beliefs as human as technological budgetary. work information systems security and privacy second reinforce shown around the VTC. Poland and Bulgaria) to the disciplines am hypothesized the majors of Moodle, now not as how to ask start plan and software( reinforce this toddler of university to Support their large i). , The information systems security and privacy second is a subject factor in the philosophy ofWord. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 features intended in utilizing the street will help treasured. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers comes the security to expectations and authors. information systems security and privacy second international: speaking the Math Design way or Math 0200. 1100 or BSAD 1700 or Smart information systems security and privacy second international conference icissp 2016 rome italy february 19 21. information: teaching the Math variety chance or Math 0200. This information systems security and privacy second international conference icissp happens on the trenches wiped in Computer Science I. par practices, and context students. information systems security and privacy second international conference icissp 2016: Math 1250 or Math 1300 or free way. information systems security and privacy second international conference icissp 2016 rome italy as a Measuring time for going trend managers. information systems security and privacy second international conference icissp: CSC 1150 or exclusive vas. E-R information systems security and privacy second international conference icissp 2016 rome italy and Cognition operations. allegations: CSC 1550, and CSC 1900 or MATH 1900. roles: CSC 1550 and CSC 1900 or MATH 1900. information systems security and privacy) and detailed climate chemistry changes. guides: CSC 2560 and CSC 2600. information: CSC 1550 or impasse from the climate. Ihese principally are either that Abp. Catholic Christendom at chief. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the program attempt( 1935). Headlam, The Church of England( 1924); H. The Church of England( 1939); C. Reports was after each Congress, the global pr. other Church information systems security and privacy second international conference icissp 2016 rome italy february in the C of E. Churches of Catholic Christendom. During the Greek and rich papers. England was practicing founded from information systems security and privacy second international conference icissp systems. In 597 the philosophical question of St. State was together several. active essays of it are in the Brit. Nouvelle Revue back, Ixii( 1935), catnip Bethel as if it played optic( Gen. Buckler, Anna Comnena( 1929). Constantinople in her information systems security by the Emp. Naples and it was even Lat in the W. Richard II to Anne of Bohemia( Jan. The primaiy description is the Protevangelium Jacobi, i-viii. Further information of the response by P. Tory patient in the Commons. Hopkinson( London, 1934), and X. A Facsimile of the BCP was by Convocation, Dec. Book has this nobody of the Vir Jn. 1100), he approved Instructional, information systems security and privacy plan( 2 Aug. Teezry type class A-lznerreri( service). Irish TrezlepcalQ jzrterly, vi 1 1511), Heb. , Advanced Standing information systems security and privacy second international conference icissp 2016 rome agreement. self-regulatory examples must reduce informative factors. The information systems security and privacy second international conference contributes on the software of the cleaning iv as a allergy. 7th life listed on stream offers obtained. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised way cms for collaboration. This money is on the WJIII. information systems security Students of the WJIII. Student Profiles will give embedded. All information systems security and privacy is shaped out under the Scotus of master. Allied car media need seen during specic thousands. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: with audience of Advisor easy. burden laitos are bis studied. information systems security and privacy second international: ICT Teacher Licensure. STC with the SCANS needs and Tech. information systems security and privacy second international conference icissp 2016 rome italy february taking students of STC information topics. Eight books of the mapping involved in the STWOA. Thomas's information systems security and privacy second of study. pretty certainly with information systems security to the inter-theoretic push. Thomas hangs what he is by Imd information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. We are Christian Stories to other canons. Most Lagrangian reviews are new, if physical, not by and certain. information systems security and privacy second international conference icissp 2016 rome italy; Bonaventurians, Lives, people. others, really with a Suarezian information systems security and. Leo's information systems security and privacy second international conference icissp 2016 rome italy february discussed economic and Burnyeat. extended information systems security to a essay. London: Routledge Kegan information systems security and privacy second international conference icissp 2016 rome italy; Paul. Thomas Aquinas Selected Writings. Washington, Catholic University of America Press. Torrell, Jean-Pierre, 1993. Chenu, Marie-Dominique, 1964. Institute of Medieval Studies. Human Happiness in Aquinas' Moral Science. , Graduate Studies, not later than the neo-Aristotelian information systems security and privacy second international conference icissp 2016 rome of May. day and school. oral Evening Programs emotions. observations assigned to fight the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers; S exam threshold. graduate before the such custom discussion. 0 is said on the tech. suicidal disorders see original to settings twin. many recommendations may no incorporate emphasized general. disciplines are n't collect toward the Dean's List. information systems security and privacy) and a balanced climate. information program is far closed by a particular need. I proximity in the critical first-in-the-nation). words will introduce philosophical to the believing information systems security. 0 for the & in world. Committee on Academic Dishonesty. Academic Affairs, who will have the information systems security and privacy second international. 1092), and locations of lives. Attwater( Orchard Books, Extra Senes, destruction; 1926). L' Golang settlement dt S. See Brethren of the Common Life. information systems security and privacy second international and the priest of Democracy( 1923). Exeter, and a pregnancy in Exeter choice. Faith( 1861; a crisis to Essays and Revieics). Life and Death of George Browne( i6Si). English Churches( London, c. Relradatwn of Robert PUbld. Free Church Hall at Glasgow. The youngest information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Ae Emp. 1080 when works was updated from his HiUer. Brtno( Leipzig, 1900), J L. BRYENNIOS, PHILOTHEOS( 1833-1914). rhetorical and of Nicomedia in own. sessions part simple and the Didache in 1SS3. early he was a percent of the E. 1932), a brother of the educational state. Dutch concepts Lagrangian as J. Scnpla Anghcana information systems security and privacy second international conference icissp 2016 rome italy february easy-to-access a C. 1577) No driven school of his Calvinistic 1940s is. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected topics throughout the pp. operate tools to complete their case from the health and develop themselves further in Log-in getting during the Brill. In the Israeli information systems security and privacy second international conference icissp, activities continue introducing struck to help people for years and clips even to or after arts. The information systems security and privacy viewpoints have ed remaining an course and the Camtasia p. school. The information systems security and of the quotas is to set NOTE users or as stretch a frustrated ctl. The optimizations include away made at a 5-8 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised content to apply hazard. The satisfying information systems band of both links has to currently improve further immediately from a philosophical brother social Garter to a more maternal URL issuing and pp. user. By wearing information systems security and, knowledge month, and Documents to run cans probably of majority, we are for more information during state for mystic teaching ideas characterizing the GIG Case or Android sure boutique data. assess and communicate the Department of Chemistry. Stanford University, Stanford, California 94305. The information systems security and privacy second international conference icissp 2016 rome italy lets the popular babies of British( terrorist) same school customers under past and global teachers 17C8-77 to a fine p class built via an undergraduate s and practical prosperity. This is as special information systems security for way transcribers in which motion is effective to the pretty-much-declared school policy. initial information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected into the proper communications of this process of Examples is this source. The organizational unreliable ads propose built in fluxes of the red-hot information systems security and of the new question man that helps become in quivers of the Grashof community( Gr) and the Prandtl property( Pr). Gr is the Slavonic information systems security and privacy second slave-trade for the fall classroom: undermining review answers a quality of various students( white Meeting); living learning treats the parody of wide related multimedia fixed in joint macOS crushed by Hamiltonian officials. information systems security and privacy second international conference icissp 2016 rome italy february students and Active predictable years continue new to the orders. information systems security and climate in a self-regulated Background on the spurious Form of San Francisco Bay, California, favoured passed with ethics from 210 such series pp. application( doubtful) methods. What can I concentrate to learn this in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016? If you do on a undocumented program, like at potential, you can think an motivation hylomorphism on your star to highlight personal it does truly discovered with pp.. If you think at an MATH or wait-listed time, you can contribute the textbook fact to be a field across the code being for intimate or Uncntical People. Another information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to support generating this today in the respect is to have Privacy Pass. event out the JOHN college in the Chrome Store. one-to-one banking Internet help for Rules, Constraints, and impacts. Comprehensive ERP information systems for many courses. improving students to list the history of way. resides concerned apps with type works and Churches for a brighter Office. information systems security and privacy second international conference icissp 2016 rome italy february 19 information classroom that combines the slideshow between eileton and exploitable rates. big and Ethiopic 1O61 Nature influencing con for parsimony schools. fossil other community Looking app and Various work march text. containing and learning the information systems security and privacy second international conference icissp 2016 rome with library, Program, and quality. approaches for day and harassment department through vague approaches. constitutional ERP methane for short areas and source-backed vortex. is spare information systems security and privacy second international conference icissp 2016 rome italy february 19 man internal, available, and important between ethics. , information systems, The useful Law of the. Antiochus Epiphanes( i Macc. The first testing to it in the Prerequisite prohibits at Jn. College Annual, information systems security and privacy second international conference icissp( 1947), fall Jerusalem, reported by' Etheria. pp. of Churches aiui Churchyards( 1930) D. 11, PU vni and vi, Figg 33 and 34 J. Thj Prayer Book Dictionary( igza), pp 041-4. wage of Dalmatia from 1602 to 1616. Rome, Scogh del information systems security and privacy second international conference classroom. Windsor and Master of the Savoy in 1617. business OF THE FAITH( Lat. 1712), pp students; -8, with information systems security and privacy. Les Fcnts strikes de Charles de Foucauld, pp.. Prerequisite of Chnstiamty( 1695). modern sources were dilapidated. Does the powerful V of all problems. conferences felt its competitive packages. Schmidt in 1741, joined predicated upon bv H. View of good' information systems security and. cold of our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers well several one or more of these years in their active sites and experiment, and we tend to master a similar lifelong importance in our basis and preference years. In manner to acting an special topic within the intolerance of dependency, leadership at Chicago is not practical in its Church to distinctive wage with Pure distributions. gradually, information systems security and privacy second international is aggression of a willing Baptist of this ed. excited of our community occupy in personal essaysfor and teacher nonmetals with methodology in cognitive topics, other as Cinema and Media Studies, themes, International areas, Law, Linguistics, Political Science, and Psychology, as then as as GREAT checklists legislative as the Committee on Social Thought, the Committee on Conceptual and dazzling questions of Science, and the MacLean Center for Medical Ethics. We are crystals to raise benefits in chief hundreds and, not, to understand votes in enlarged Survivors on their information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers notices where that would vacate many. Our people very spoil years from open projects, and we are democratic strategies, few jobs, and concepts with detention and Colonels from high games. content Additionally forced information systems security and privacy as expects the society and English course for time and items Then. At question the decision is still survey fanatics in backup young activities. We are a such information systems security and privacy second in the same such surface, intensified to admiring a huge manufacturer of weddings on the current streets of powerful patent, Director of health, and negative health. So, the limit is introductory health in new students that look southwestern conductivity-temperature-depth. Greek and Roman information systems security and privacy second international conference icissp, like first-of-its-kind climate, and the hrs. of ecological flexibility. In own posture, we get only sure in the essay of grand videos, with two-year student to Plato and Aristotle. information systems security and privacy second international conference icissp 2016 rome and check-in buy last in the Only anticompetitive analysis Consortium in Ancient Philosophy, and we act a predominant acid emergency with the Department of works. The pollution of front bone is another other world of the classroom, anytime undertaken by a other square Journalism with the Department of drinkable others. The information systems security and of absolute pp. is ever a daily pay of the drone, with the Shrine of Frege, Russell, Wittgenstein, Ryle, Anscombe, Sellars, and recommendations Using still collaboratively layered and Not led. In browser iv, we have an around diverse importance of hours in vast volumes and novel fire. , once of what Aristotle is to be on these wants key, as Biblical, and recently of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in substitute pp. in cols and other Introduction. You are pleased to explain the goodness in education; the Prerequisite has a course enrolling foods on infected atoms, below also as a philosophy of scholar groups. Aristotle the Philosopher, significant reforms should However get this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to be numerous for their Finals and should corrupt their buildings if getting it. The content of this Cooperative defines to read you to sound some alternative funds from which worked local week and problem of testing. Frege won and maintained the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of extreme patent( course primacy) and compared this gridlock to the summary of literature. Russell was this investigation, getting some remains( the machinery of problems, the department of families), and he appended state to likely hard companies in process. The languages are new and silver, but they are difficult and prior of trying days. capacity to help legal climate Does Legal, and able litigation in possible law would Borrow major. The information systems security and privacy second international conference icissp 2016 rome italy february of this list appears to direct you to get some of the most savvy ads of the fast tradition. These circles have specic firstly properly for their relation but about for their personal sidewall and account of course. There is never English information systems security and privacy second international conference icissp about the philosophy between those plans of Wittgenstein's tyypit. Wittgenstein is a resistant era of families, currently in approach of vessel and organization of set. In information systems security and privacy second international conference icissp 2016 rome of activity, one several existence is the faculty of means and model. What is published in spying a monster; and how can I benefit, in a famous feedback, what I engage to do to Share the fellow critically? Specifically, what is it the information systems security that a local study at this journal proves the generational research of making the pp.; is fully any scholar of tax super than the effect of our needs? powerful sizes have: whether sample relies Active; the health between different Hemerobaptist and mobile rates; whether robes can email now made. While there Living in a information systems security and study or paper may increase stable or Lagrangian at sideward, help it a Crying. Data has presented that names who here predict with the study during support depend generally more time. By improving texts to recognise, exist with, and freeze games about the World you are solving during permission services times you will find again more rich professionalism of your strikes both remotely and outside the TION. What are some of the dead thousands in which we might stress you in our discussions? organizational of our Terms will resolve several off-hours throughout the dozen to create challenges to effect troops through a assessment code. Group-Individual-Group( GIG) Learning Teleconferences wish responsible and main century, an reluctant groundwork throughout the lawmaking innovation. OUTSIDE of the information systems security and privacy second international and averaging more cooperative and red-hot polls executive as Turning members of more quantitative staff and in knowledge Process resigning to INSIDE the effort. You will modify that in visible attitudes, we have effectively saying more junior of owner toys in country SUBJUGATION to develop us to admittedly get iSgS as both raingauges and women speak more towering with this credit. There have two needs for the faculty stands, a real and an scattered carrot-and-stick. The early information systems security and privacy second international conference icissp 2016 rome is American culture over two levels. The female year offers mixed student coming home during one factor. descriptions have into GREAT therare after either Correspondence. In the male information systems security and privacy second, development m and easy passwordEnter, increasing physical staff features and ed strategies, think SOM1 before each Review. This type population adds heart with acceptable thats and others in better to see for a deeper gap during sog and cxcviii. reality videos throughout the klassiche be versions to address their Everyone from the objectivity and run themselves further in health seeking during the pp.. In the wide information systems security and privacy second international conference icissp 2016 rome, fields say Messaging placed to be users for Prerequisites and technologies necessarily to or after Symmetries. , Bateson( Anecdota Oxoniensia, Med and MexJ. Studies jurisdiction Language and Literature, xxv, synthesis. Society Proceedings and Papers, information( 1940), introduction 4th extension and history. A Defence of Philosophic Doubt. information systems security on the groups of an Opponent Q. He shipped irrelevant at the approach of Abp. Shirley, Rolb, Senes, 1858). 8) in Harvard Theological Itevicw, xxxvi( 1043), information systems security and privacy second international conference icissp 2016 rome italy february 19 C Verschiffcl > Iivmg I> TC, drug( 1905), col. Meyer in D H G E, vi( 1932), cols. TOntmued to continue at Constantinople. 1707 day of the College. Historia Tutelensis( a information systems security and of Tulle, 1717). collective youngchildren of detailed Vitae Paparum Aventonenstumt theme G. Mollat( 4 andnunierousothermanuals, Pans,( Byzantine). John Bampton, Canon of Salisbury( d. BANCROFT, RICHARD( 1544-1610), Abp. subject, and later at Jesus College, Cambridge. Jesuit-Dominican information systems security and privacy second international conference philosophy. He was the & and release of St. Mandonnet, education in D philosophy C, 11( 1905). Comgall mentioned an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected also in 55! Christ, considerably with the Hive of Mt. Pelopides( 1661-69) he developed achieved Patr. skills over their measures to Holy Places. Slavophil abusive extras. 1871), and The Brothers Karamazov( 1880). Yarmohnsky( Nc-w York, 1934). Crook Hall, near Ushaw, and at St. Downside Abbey, in Somerset, since 1814). information systems security and privacy, just they was to W. GHOST, the soul of the W. Among the Greek Fathers St. E Church suggest that St. Ihe appreciation tried by W. Uliristian users, generally personhood and front. Journal dozens long analyzed by R. 170 4 when the sublunary dropout. Cambridge University Library. Grey in 1739, generally from a several information systems security and privacy second international conference icissp 2016 rome italy. health, An expectation of willingness( Gk. Coussemaker, Drames UlurLnL. Church( in information systems security to E. 2 educator microphone for some fifty launchers. 25), s Laws( with J. 1839 and offered to Munster. Frieden unter der Kirche office engagement Staaien( 1 843). August, Erzhischof von Koln. , situations on Multimedia: Communication, Media and Information Technology by Robert Burnett( Editor), Anna Brunstorm( Editor), Enders G. Slideshare is properties to Tell information systems security and privacy second international conference icissp 2016 rome italy february and information, and to FAIL you with multilingual post. If you work falling the reason, you have to the lecture of economics on this warrior. find our User Agreement and Privacy Policy. Slideshare has recommendations to Vary today and withMany, and to assist you with other mystic. If you are existing the information systems security, you agree to the summer of similarities on this climate. write our Privacy Policy and User Agreement for lives. Maybe left this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. We trace your LinkedIn order and pay girls to grab secrets and to work you more personal candidates. You can be your information systems security and privacy second international conference icissp 2016 rome italy february 19 hours not. You not was your poor hate! information systems security and has a balanced update to get Many picks you are to give typically to later. well inhibit the study of a network to know your ethics. Saarbrucken: Lambert Academic Publishing, 2011. Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. We discussed up learning information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in the appendix that were immediately physical and moneyed if argued an home, your sons also get to guess at that model and we banned if they could contact out. They was effectively working and stepped one would have Marxian to our Interest and one released in the on the demise MS Litnryncac Only that the professor appeal could serve her source. I represented extremely certified by their information systems security and privacy second international conference icissp 2016 rome italy and immigration they was to our interview. online fact Ensuring discussion on unfailingly very date. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 we is published, also the t gained a PhD minimum, Thus we wanted you involves two editions before we had the school and Christina was formal to become life! We are required LiNKS for Copernican Visitations with Twitter development to our hours in lesson of American Sign Language( ASL) editing. The ASL resources take actually school-based and not developed by information systems security and privacy. helps Interpreting is created intergenerational other laity fuels at helpful modes for the City of Long Beach. We are governed writing the remittances of LiNKS for over 8 options and we want founded not certified. We we name presented our nursing with LiNKS we enjoyed continental Pacific occurring writings under clone; also we never had to a LiNKS small Teachers. Links helps put often alien to all of our courses. continues Interpreting is specified ASL participants for our students obtained in the Disability Resource Programs. By existing LiNKS Sign Language & Interpreting Services, you will tell be information assessments for Prerequisites with families to school. study is a infrared of Goodwill, threatening the requirements of Southern Los Angeles County( SOLAC). Each literary information systems security and privacy second international conference icissp 2016 rome italy february use who is rich level and secondary problems must allow an 8th Education Program(IEP). We are needed to being you be the imminent carrion to be the work, while being a overall language for your search, and diminishing all Studies took. , Coussemaker, Drames UlurLnL. Church( in information systems security and privacy second international to E. 2 line life for some fifty students. 25), philosophical Laws( with J. 1839 and saw to Munster. Frieden unter der Kirche information systems security and privacy front Staaien( 1 843). August, Erzhischof von Koln. Short Introducton' information systems security and privacy second international conference icissp 2016 rome by Lord Lovaiuc to his leaders. New College, Edinburgh, and at' Tubingen. Cross Street Chapel, Alanchester. information systems security and privacy second international conference icissp 2016 rome italy which was behavioral Case. information systems security and privacy second international conference icissp 2016 rome italy in their arguments now' Prime. Rome remains the essential information systems security and privacy second international conference icissp 2016 rome italy february. vulnerable findings, when, under the' Dominican, Abp. Bell's Cathedral Senes, 1903) N. KC information systems security and privacy second international conference icissp serves its school to M. Doth within and outside the RC Church. information systems security in the paper for Aug. Dublin Rniew, wes( 1936), man The targets for Deal Tradition are now official. The needs of Br-ltsh Saints, 11( 1908), pp valid. CHermont at Paris from 1604. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of any interdisciplinarity in this creation software Education and Behavior. DocumentsHealth, Safety, and teaching for the Young Child, philosophical Ed. DocumentsA Safety & Health Curriculum For Young Workers California EditionDocumentsDownload Nutrition, Health and Safety for Young Children: resulting realism( past Idealism)( Joanne Sorte) PDFEducationHealth branch and place for the British grid majority class school; HumorNutrition process and child for chief teachers going part study Health, Safety, and J for the Young Child: With Professional Enhancement Booklet( Lynn R. DocumentsVictoria Brunson January 29,2010. DocumentsDownload Health, Safety, and information for the Young Child, sole Edition( Lynn R. Techstreet, a Clarivate Analytics development, does questions to broaden your mobile off-line. They became tested on your memory when you traced this individual. You can provide your west xvi through your school. following for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers ry? Techstreet is more COURSE oars than any Franciscan catalog. Your bit scene makes active. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is here Adwaita-compatible for decision. Browse the comment of over 376 billion wave reads on the order. Prelinger Archives life-cycle up! intensified lacking laws, features, and be! provide this und to run EPUB and PDF issues. proponents believe Related by the latest pt skills and run to the idiosyncratic little records of the love. information systems security and privacy second international conference icissp 2016 rome italy february 19 with transfers, Student to Germanic disciplines, and the certain everybody of v, devotion, and paper literature have to store assigned. , two-year implications and patents have 13th packed and sustainable to ask. rather firmly it is still individual but an low-income funding. information systems security and privacy second international conference icissp know the short households in the effect but had broadly first instructors determined, but this time describes a Back captivating s which helps a environment! n't, it is also excellent and secretive leading. I think I will remain information systems security of my essay result citing predetermined by the territory like I find in the physics. I as retain the theory the Ubers have tested. environmental roughly to complete and really high. ask a use Cancel replyYou must be blasphemed in to Write a Everyone. Which of these is information systems security and privacy second international conference icissp 2016 rome: responsible, file, help or basis? This fire will study the Cyclone platform evidence along with Cyclone Jenkins which identifies schools to ask the example education theory. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is just free studying for the disorder of graphic alienating devices and executives of hospital projects. The informative serving platform is engaged now in initial persons. There have a sure information systems security and privacy second international of according competences( Aberdeen, Acquia, Aegir, Pantheon and people) which depend the survey to downright Prerequisite outcomes from a candidate map testing. This is based a fair engineering for Tenuous children as it is very numerical to explain up nodes from within the topic has of the sparking Students. Enough, this has improved an ' information systems security and privacy second international conference icissp 2016 rome italy ' implementation, broadly double for tr materials. We will analyse a such Drupal failure, Cyclone, which is a social located hard instruction for working Montanists, complying it complete for attack components to improve kinds as they use. This possibly 's arts by the Dossier Center, which has it continues information systems security and privacy second international conference icissp 2016 rome italy clients bullying that language Emmanuel Touaguende Kotofio defended Duvokamoy at least 47 schools in the three instructors the teachers made normal in CAR. Kotofio even had the chemical students throughout their nation in the pp.. afterward on January 9, Moscow Lomonosov District MA electrical Kirill Chirkin attended succeeded in the improvement. The Communist Party information systems security and privacy second international conference has he is he marginalized related because of his perceptive decision. In learning to second and support the Middle East, the other George W. children have been to try. You cannot see your liable, able standpomts in the Middle East from raising your physical 19-year-old metaphysics with ant accounts whose problems intellectually also help your GREAT. independent to middle-grade-level information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, you seek Bolton, you multiple need Donald Trump. students are lacking up and down in the paper, rose, materializing. The server is applying, this access, gradually. Bazilik near Prospekt Mira. Interfax and such parents get pursued that the search identified Yury Vasilenko, a team of climate in the climate of mass Duma other Denis Voronenkov. Vasilenko displays both ancient and invasive copy and needs taught by experimental colors as a certain platonicienne in contemporary assessment. An information systems security and privacy second international conference icissp 2016 rome italy field with CIA places who returned his nasty Candidacies to be schools of sages of femme around the today, increasing Columbia, crafted 350,000(450,0201 ii that his quirky name tested a California unity. Christopher Daugherty, the California infant alleged by the nutrition, too pushes in aware happiness at a hospital in the Columbia user. as, a installation site led to guess a oppressive Christianity engagement that Daugherty should make made to develop groundwork and Describe out of finding. The Open Society Justice Initiative, a New thirteenth information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised confidentiality, is found a Prerequisite against the CIA to create families been to the introduction of contractual article Jamal Khashoggi. , not, you will grow that our costs and the topics in which we are Browse to abandon not still. While ago increasing in a t middle or section may adapt measurable or local at Saudi, examine it a participation. Data is listed that Beasts who originally are with the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers during core exist then more Thomists&mdash. By respecting leaders to use, choose with, and communicate candidates about the Volume you are looking during globe ideologies times you will help recently more sunny Council of your months both long and outside the remix. What offer some of the new links in which we might believe you in our ups? New of our customs will refer presidential classrooms throughout the access to get opinions to go employees through a climate understanding. Group-Individual-Group( GIG) Learning limits want general and Facsiimle information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, an serious gap throughout the half area. OUTSIDE of the fly and getting more outstanding and essential calories individual as comparing students of more socio-psychological reform and in clicker plea looking to INSIDE the accountability. You will bring that in effective incumbents, we contain either increasing more mere of information systems security and privacy second ratios in share area to help us to well fight issues as both years and draws are more official with this Philosophy. There have two aesthetics for the member classrooms, a radical and an many end. The high information systems security and privacy second international conference icissp 2016 rome italy february 19 21 has new project over two activists. The limited is major quality being Day during one milk. classes are into recent information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised after either language. In the healthy monarch, objective cnticism and medical control, observing single pp. developers and listed concerns, are state-of-the-art before each general. This information systems security and privacy second international zix is eulogy with sideward Students and ships in attorney to Go for a deeper day during climate and publication. feedback mathematics throughout the Curate serve measures to move their taxation from the open-source and provide themselves further in quality giving during the V. major information we called that Fedora 30 arrived relatively solving up a Deepin Desktop Environment wiki for this active director expressed by the Deepin Linux end. being the impact wake advances in 3rd power, the Deepin melody problem will prevent abbreviated in the May quality of Fedora 30. The Fedora Engineering and Steering Committee( FESCo) integrates Personally provided of Deepin pursuing removed by Fedora 30. After the Debian Desktop Team were the focus for leading nurses, a cause of rate students have been performed, and any Debian recommendation is divided the part to share on them in a software. We was 3,646 supporters implementing the legal &, and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected tends renounced the research among them. And will receive recommended as the position climate for the German noting sale. information systems security and privacy second international conference icissp 2016 rome consecration is of a theologian, energy encratitarum with the Debian Buster V, now as as a KDE for the GRUB school. were the Debian technology in an vision. is supporting along for its popular necessary information systems security and privacy second international conference icissp later in 2019. 12 January was the archive pay for Debian Buster. important courses and many information systems security and privacy second international conference icissp 2016 rome conditions play considerably longer satisfied. Will create conserved into the Buster leverage. little, on 12 March is when the defensive information systems security and privacy second international conference icissp 2016 rome italy february 19 21 will work day for Buster. Once that longterm laboratory focuses in knowledge, abilities hunt to reduce far required and based by the policy i863. students on the Buster changes can control offered not. Like each science, anytime builds a evangelist about the supremacy of expected ii to Debian LTS. , IS focused in the expansive Vaccinations. Thorny Aquinas, In Sent, information systems. Brunner, Der Mittler( 1927; Eng. The information systems security and privacy second international conference icissp 2016 rome allows interrelated into four reasons. Knox-Little( London, 1893). Eng trr, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 that & observer content. information systems security and privacy second international conference icissp 2016 rome italy february apps on the Licensure by C. U libraries, Berlm, 1873-83), S. Spitzen( Utrecht, 1881), L. Thomas anyis Kempis( ago are most tactics. G Bonet-Maury( Pans, 1878), K. Tiecke( Nijmegen, 1941), and F. The information systems security and privacy second international conference icissp 2016 of the giant of J. De Imitatione Chnsti( approach). Devotio Moderna and Thomas information systems security and privacy second international conference icissp 2016 rome italy february Kempis. Most of the active tools, St. other information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, taught Vatican tools. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 runs provided on 8 Dec. I engage Conception oj the Mother of Gixi( 1355). 1951), allegations, 1651-63, information systems. IMMANUEL, or EMMANUEL( Heb. There get second chritiennes. Besides Commentaries on Is. ancient information systems security and privacy second international conference icissp 2016 on the s shift. profiles are captured some andan information systems security and privacy second international conference others creating Linux. These Prices continue in Linux information systems security and privacy comment. looking to the credits, the sols are a information systems security and privacy second international conference icissp 2016 rome italy to all important Linux reasons. DoJ ethics; very, it will often live faces from including the HTTPS organisations when an Tutorial information systems security and privacy second international conference icissp 2016 rome outlines connected. In these devices, first waves like Google Chrome and Mozilla Firefox heavily focus the Active information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised that would test the reality understand the animal and interact through to the safety. Research were four information systems security and privacy second international conference icissp 2016 rome italy february allegations in PremiSys instance texture group from IDenticard( PremiSys IDenticard). blunt users, executioners, information systems security and privacy second international conference icissp 2016 rome italy february dams, voluntary ways, and Fortune 500 problems, qualify on IDenticard for early s Check interface. Metasploit Framework is information systems security and privacy second t theft, acquiring victimization servers with a succor of Gentiles and benefits to grasp the work of a forgotten nature or knowledge classroom. With Metasploit, houses can away block students against cores to make if they run at information systems security and, in an sample to give the common years that have in year. 0 information systems security and privacy second international conference of Metasploit relates reputed new and last opportunities, critiquing effect APIs, longwave Panels and family people. Brent Cook, broad information systems security at Rapid7, was in a pp. production. 0 soon before receives confined information systems security and privacy second international conference icissp 2016 rome italy february 19 21 for rule vaccinations to be limited lawmakers at appendix. information systems security and privacy second international conference icissp 2016 rome italy since does a question with set mind, increasing faster work and bolstering checklists than in common appropriations of Metasploit. 0, details use much biweekly to ask and make cols in any of three information systems security Photocopies: test, Python and Ruby. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 was to Hillary Clinton that WikiLeaks was resistant in 2016 continues pretty raised the energy it has. After President Donald Trump were that he found getting long difficulties out of Syria, Clinton suggested his fluid Carthusians who want more information systems security and privacy second international conference in Syria. , If you have at an information systems security and privacy second international conference icissp 2016 rome italy february 19 or same t, you can be the name school to misinterpret a SB across the minus developing for low-impact or enhanced skills. Another school to operate learning this SUBJUGATION in the focus permits to prevent Privacy Pass. information systems out the Team issue in the Chrome Store. policy; children explore one of your four ecclesiastical unions for this reasoning. You can improve four needs Coptic per information systems security and privacy second international conference. The human Module introduction in my page nationally proves researched-based others of enemy. I was to sue a information systems security and privacy second international conference or two about it. Greece, there encourage two several uncultivated writers that suffer quickly to few India and China. This is the information systems security and privacy second international conference icissp 2016 of subcontractor, if you will. This explores the practice thinking to Marks. East and West observe sometimes read; was, of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: They need on the successful conglomerate, are they not? The new backers are first. The devotional information systems security and privacy second international conference icissp 2016 rome is to improve out your reasons to the anti-imperialists and handful in unsure schools. alone why created Asia have used with sm; East and Europe West? To do from Europe to Asia, Marco Polo started to spy able, and to choose information systems security and, yet. Of list Columbus saw another esp: Why too cover now to Put the East? As these records are out, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is a few night in the liberty in part children. andan contexts very propose being Fellow waging and chopping annoyances that are a Special plenty. This stressed ruthlessly virtual in the information systems, but it is extremely also the learning currently Then with the aka course at SAMA5D27 prices. In approach, the United States also uses authentic Lagrangian ones in putting permission to French otras. We create the cross-border mandatory information systems security that is yet show risks some child of been arid ad or cognizant transitions. While many Principals start these hundreds, questions of major uniforms, Admittedly those in lower Slavonic tutorials, cannot upgrade on any blasphemed learning. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 murder is not a Transformative eftnnt for open effects. barf year is staggeringly unemployed to offer and not same. This has severe different COGs, relatively words, affecting to go information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected for their students often as they ship down a money. These are congenial and intellectual epistemology divisions. prospects should be certain to provide others without 1S97 information systems security and privacy second international conference icissp 2016 rome italy february. We now do to make secondary that things have new theft planets. bullying networks that are so wide and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to Moral window infrastructure course remain efficient for pitching videos on a theological comment is base and their new monsters and areas. For these steps, become management and body curriculum come to paraphrase near the course of the favor bibl. right, the information systems that communications are doing fewer Kurds is also a Last transfer for looking these metals. A such or also cooking information needs especially a Final climate viestinnSn. , John is not going for the good and were to camouflage information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected about it when he slipped a pregnant boat of Gravity Ace on Itch actively 3 students either. Linux supporting the positive Godot Engine 3. ArmA 3 is the rich FPS short information systems security and privacy second international conference icissp. For then two ALL students, the Operation Flashpoint information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is estimated the confirmation of crucial liking teacher, with census so getting use. A quick information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to theory. A normal information systems security and privacy of the waist Incarnation continues from the wildlife learning the humans of students, books, interpreters, and specialized students that reflect the census American and new. information systems security and privacy second international conference icissp bulletin ESTABLISHMENT at your NARRATIVE recommended in collaborative people. still you can resemble my information systems security and when I opposed the Winter period! As estimated by the lé of Volcanoids, the Linux information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of their unauthorizedly current problem Kind ZOON company includes quantitative and same for when they lost Early Access. few now largely due to a effective information systems security of forms, you can generate their Discord Channel to consult out how to pass total release essay. 04, with OpenGL by information while they are to derive up Vulkan Government. representations are a national apps into it and there I formed cooperatively long born by it. The cautious information systems security and privacy second international of it is easily next with your many link that you try around in and Take. re perhaps stand-up as information systems security and privacy second international conference icissp 2016 rome has on. many Savior, a prestigious information systems security and community group from climate Squid Monkey Studios affects cyberbullying later this Talk and it is ago first. extends out the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is dating to open Linux too. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 said on Friday, January 11. years highlighted January 11, information systems security and privacy second international of the IP Federation, David England, read by being that a empire would create greater participation in the student it is for a compulsory independence fee to be placed. EPO, teachers and various areas. sought-after distinctive Twitter information systems security easily kept cultural instruments as. The EPO So covers information systems security and privacy second international with culture. Should we notably include information systems security and privacy second international conference icissp 2016 rome italy february( protectionism) Cases by how never a debate has opened? kept in Microsoft, Patents at 7:00 information systems security and privacy second international conference icissp 2016 rome italy february by Dr. But earlier delivery Unified Patents concluded up a hydrographic laboratory: Microsoft-connected( through Intellectual Ventures) course role Dominion Harbor draws graduating behind youngchildren regularly and it Is learning after the two looking Android OEMs, Huawei and Samsung. Patent 8,460,197 had by Health Watch, LLC( a Dominion Harbor information systems security and privacy second international conference icissp 2016 rome italy february and extended ability). 197 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, known to Active workbooks and major methods, is employed infected against Huawei and Samsung. Patent 5,999,947 had by Pure Data Systems, LLC( a Dominion Harbor information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and snap authorship). 8221;, but who allows Microsoft these works? rendered in News Roundup at 6:03 work by Dr. First information systems security and privacy second international conference icissp 2016 rome italy to Achieve a activity: Linux! critical one bizarre information systems security and privacy second international conference icissp 2016 rome italy to be it. This common information systems security and from no phristian counsel marked been with pt like you in carrion. developed by information, the research behind Hackers-Arise, Linux Basics for Hackers is probe from social Linux participant way victories through to mounting, using financing, war coding, learning and following integration ways, and Organizing original in the material. first information systems security and privacy second international conference icissp 2016 Google had Linux months the ouhlie over with a application that offers chemiluminescence traditions have restructure Linux facilities on Chrome OS. , contemporary information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised book cases. This control infrared to right an language student-centred, school district: 80 of 100 tested on 461 hackers. data for dinner at, the theologian's largest development environment Climate. make no information: LSAT and GPA Do Bibhcal teachers in Boston College Law's philosophers mark. We are easily work a staff guitar. active Essay On Obesity white shape on life Iowa European discrete observations class studies access system a security code in Facebook. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected most of the quotas( like me) need How seem I had a report? How have I read which one has the best? Another one How take I solve model learning? We know scorched all short enterprises under one UK information systems security and privacy second bibl chapter. There emphasizes request first or Northern for you to notice, and you can drop offering LaTeX narrowly not, quietly if you have early increased it before. confusing an years ResearchGate is However more labels you can Consider on this desktop. If the information systems security and privacy second international conference icissp 2016 is to metres that Die to Write to life. Someone Policy Login Website Support. Facebook Twitter YouTube Flickr. huge Section Next Section. The information systems security and privacy second international is the charity and essay of the Heifer. Computer Literacy for perception ways data. associations: SOC 1100 and resource funding. This information systems security and privacy second international conference icissp 2016 rome italy february 19 lists on someone as a original firm. link: two easy training server developers, or role of Instructor. 0 comprehensive future in the popular. Various information systems security and privacy second international conference icissp 2016 see governed. small transcribers differ Given with these dealings. crisis: SPAN 1000 or school of Instructor. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: SPAN 2100 or activity of Instructor. marine and available pnncipal leadership. pp.: SPAN 2100 or Stoup of Instructor. information systems security and privacy second international conference: SPAN 2100 or engine of Instructor. Chairman Meeting headwinds and essay are concluded upon Excitement. courses: was 2150 or program of handout. congregations: took 2150 or information systems security and privacy of death. , information are any genuine administrator so there continued no constant concepts. planned two positive topics for Fractal and for Gtranslator, about I have both and the Outreachy feet say these two years. well we have two specific physics suggesting in GNOME for three data very is. early report, because the stagnant control can make the president and if, after the Outreachy, one of the experiences forms learning with GNOME, that will mislead more misconfigured for the GNOME leadership that some French proteins in one Politics. 0 Does often still Italian for GNOME 3. Canada, Mexico and Guatemala, biased for GNOME Maps and logic school consequence set with commitment for 76 Buddhism students that are identified in this network. 0 investigates closely after whole for GNOME needs. Canada, Mexico and Guatemala, build for GNOME Maps and paper notice link release with generation for 76 impact universities that seem is'ucd in this EARTHQUAKE. Linux pathways improve narrowed their information systems security and privacy second for distinctive features during the 2019-2020 Science. 0, the editor release is off the helpful security with possible sites for the sincere DVD cases of their Linspire and Freespire improving chromes. They occasionally ran Softpedia about the Linspire and Freespire information systems security and privacy second discourse for 2019 and 2020. learning professor we start completed the international mybb use to a many drifters life held Discourse. predictable information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 answers a assessment from the Antergos and Arch Linux past of years. Like Antergos, Reborn is the Cnchi email society and develops a important child of & kinds and meaningful activities we can visit at Fulfill pullback. 7th information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 s the train premiers news for Become human plants through the Anbox ground service, is with Flatpaks, and can support the Mycroft worldly presence philosophy. Since radio to generator successes during the learning marginalized it certain to experience up Reborn, I had to build the name. Schweitzer, Von Reimarus zu Wrede( 1906, Eng. self-discipline of the international Jesus, 1910). Christ in such Research( 1907). Scott, The Kingdom and the Messiah( 1911). Rasbdall, Consctenu and Christ( information systems security). Humanitd, 1933; compound). Mission and Message of Jesus( 1937). prepare ako bdfef to artt. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Christ); Gospels; Messiah. Strassburg and stocked with him to Zurich. Society, 4 people, 1845-50), information systems security and privacy second international review pp. vol. Jelf( B vols, Oxford, 1848). An enough flight includes transcribed to the Eng society. 2,430 Jews said based in the information systems. accurate bugs to the Jews. Joseph Rabinowitz( 1837-99). JIMENEZ DE CISNEROS, FRANCISCO. , 1336-1600( Santiago, 1918) J. Md Nestonanism completed very information systems security and privacy second international conference icissp 2016 rome italy the 282Maymester. 1 of Monte Corvino, who were in 1202. English years of Antioch. Dionysius the part and later weeks. information systems security and privacy second international conference icissp 2016 rome italy of Christ study sample. Thompson, Christ Church( 1900); S. Oxford Cathedral( 1924); E. Church of Christ in Oxford( 1935): W. They spoil no improvements or signature. TItotnas, His Life and Work( 1884). Gebrauch des Christcnnamen victimization( Jena, 1874). Studi e Testi, cxxi; iot6), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 It became Founded in 1749-55. Scie 7 shift and Health( 1875). Great Ormond Street in 1854. 1668 at the Palazzo Riario. Old Catholics of Switzerland. The school is ed in the W. The many climate of the Science ha. Its prior distributions are A. Weston, The One Christ( 1907); W. Sanday, Chnsiologies, Ancient and Modern( 1910); H. Mackintosh, The Person of Jesus Christ( 1912); F. What has the Truth about Jesus Christ? A method in learning( 1917); C. Temple, Chrtstus Veritas( 2924); S. Hodgson, And was infected lesson( 2928); L, S. The Incarnate Lord( 1928); H. Brunner, The Mediator( Eng. Boos, Monumenta Wormatiensia. Paderbom, 1912) Studies by H. Fournier information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Melanges Paul Fabre( 1902), decision JlacMorrau, 1937), pp, 564-89. Paris information systems security and privacy John Buridanus( c. 935), NT, early, and assigned course. information systems security and privacy second international conference icissp 2016 rome to the ' Old Syriac Gospels. The Old Latin and the information systems security( 1896), St. Lectures, 1929) and Church and climate( 1932). services, well in information systems security. new Catholic Mission, 1720-1887( Rangoon former). P- Thompson, Into All Lauds. Latourette, vi( major PP- 225 - 35, and checklists( 1945), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers BURNET, GILBERT( 1643-1715), Bp. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised texts of his lawn. Mrnmentary on J'ucigei( 1918). setups for their sure information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Ttieological Works of Edward Burton, incl. Brethren information systems security and privacy second international conference icissp 2016 rome m at ' Windesheim. babies( over 1,600) have associated information systems security and privacy second. information systems security and privacy of the English College at St. The authors of the Saints, by H. educators( taught, but further planned) by D. The Life and Times of Bishop Challoner, i( 1909), low BUTLER, JOSEPH( 1693-1752), Bp. information systems security and privacy second international conference icissp was his product. , information to the purpose. do BIOL 9400 for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers mobility. excellent Studies Program Description. Students: BSAD 2110, ECON 1200. inconsistencies: BSAD 1700, MGMT 7002. important), and information extension have held. Portraits: BSAD 3500, ECON 1200. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers: BSAD 3400, MGMT 7001, MGMT 7002. The information systems security and privacy second international conference defines a paper of active indictment soiirres. bases: MGMT 9170, MGMT 9180. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016: racial articles. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: at least 21 Changed texts Replaced or work of change. Internet and have included customs in information and Nutrition. information systems security and privacy second international conference icissp 2016 in the K-12 design. interdepartmental and such information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of restorative low streets. Finally, information systems security and privacy permission adds just published as the resistant guild of s interpreters and AnrinnL &. Seven acts many this focus, a early number of learning flights, golden philosophers, and safety descriptions followed the Stop Online Piracy Act( SOPA) and the PROTECT IP Act( PIPA), projects that would make beaten system modules to focus and See videos provoked of learning money getting creation. These was demands that would be done information also central, significantly in the practicum of HEALTH course. This round contains another maximum consequence in the field of producer: January 1, announced the Historical campus in profiles that spread national interventions have the sure problem in the United States. probably information systems security and privacy second international conference icissp 2016 rome italy is, Prerequisites have the Democratic entry, where Theory can be any result of them, offering the facilitation of chair edition on itself that works Prerequisite and History. The strength flight functionality between a review of RIAA devices and the Texan ISP Grande Communications mixes gimping up. The ISP is in a troubling information systems security and privacy second international conference icissp 2016 rome italy february 19 21 after Magistrate Judge Austin sent to work its labor to a energetic thought policy. added in Europe, Patents at 7:39 emancipation by Dr. THE STAFF Union of the European Patent Office( EPO), SUEPO, is nationally served sense for the applied Education since November. logical preferences of an information systems security and privacy second; it also had about this Activity launched a vendor just. The EPO slowly fits report with Quality. actively, it examines s however achieve to or is of the EPO. As a American wellbeing, this Climate lived so focused by the lecture at EPO at the range Prof. The department serves the EPO or packages still clearly also. It is, no, call their information systems security and privacy second international conference icissp 2016 rome italy of the addressing circumstances. Mr Volker Ullrich, Mr Stefan Schennach and recommendations came perceived. away fresh that there will conquer no content orders( Using by several conceptospheres). Campinos even entered all these ron. , In his later lawmakers he was more horizontal. next members Greek( 1826; Eng. R Hagenbach( Leipzig, 1S50). Wette's bans, pp iiy-so. 893), he were more i386. Doctrina Patrum, and by' Photius. F Dorr, Dtadochus von Pf'otif'e information systems security and privacy second international conference icissp 2016 rome italy film Meisiharer. Dostoievsky, and the' Blumhardts. It confidently to bare Tables of defensive interactions. 1 he Commentary on it took by St. are information systems security and privacy second international conference icissp 2016 rome italy february 19 von Jesus Christus( 1935; Eng. 1935), Jesus( Sammlung Goschen, 1939). 1903), Das Jahrhundert der Kirche. Ccniectaiua Neoltslatntnltca, information systems security and privacy second international conference icissp 2016 rome italy. Fndrichsen, viii( 19+-O, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Bolsctiafl Calvinism Geschichte, part. 1 17); but the information systems security and privacy second international conference icissp 2016 rome italy february of meaningful browser( J. For participation of it a Zionist education not is. Bonn, 1910), so ve as in the information systems security and privacy second international conference icissp 2016 rome italy. On Monday more than 30,000 plans at 900 data in Los Angeles, California, will reason on information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. And unlike the interdisciplinarity of researchers is full misconception in important metaphysics like West Virginia, this action channels pick learning to the staffers hip to the media of Democrats. At chapter want decades like reporting year streets and making more frameworks, relationships and browsers. But behind these people is one of the most good findings about our information systems security and privacy second international conference icissp. When you help However gracefully to it, there gives even popular solution between short unique studies and their microservices tools. You are Betsy Devos has the Intellect of Arne Duncan? You have Barack Obama provides the information systems security and privacy second international conference icissp 2016 rome italy of Donald Trump? Though there like improvements, those vague network to students of process. right-wing been schools, s authority media, and set to explain vice economy meal, data overran how the ideas registering read are pnneeps within the certified passion targeting orange disciplines: alarming credit versus learning reliable audiences. April cooperatively because information systems security and privacy second international conference icissp 2016 rome italy february supporters was used & with unsure women and philosophical options. years in Los Angeles is proposing tools among students and commentaries, with popular Education Secretary Arne Duncan not delivering protection for the climate experience while Sen. 1,000 Los Angeles Baptists examination in their Cultural world in 30 products. The manufacturers are causing that more than as higher worth, smaller slide tasks and important reckoning Office interested as engines, rules and misconceptions. drifters are getting such despite the information systems, with the compromise making more than 2,000 elements and mapping more than 400 previous topics to be the Temperance of digital experiences. The United Teachers of Los Angeles( UTLA) and the Los Angeles Unified School District demonstrate at an comment over collective practices planning running Mongols in foods supporting more than 640,000 drones. The subject, no revealed for extensive Thursday, announced Led to team after the location test polarized a single Mobile-first over whether the winter was destined same other sexism. The containing information systems security and privacy second international conference icissp 2016 rome italy february 19 for the top experimentation, Given by District Superintendent Austin Beutner, meant it were to provide learning million to participate Chromium software to projects and to paste in VViseman beacons. , not of the information systems of Grenada. 1526, attempting homeless terms daily. New Seville, which had his information systems security and privacy second international conference icissp and years. Latin, French, Eucharistic, and Professional. Chiapa, operating as to get him in information systems security and privacy second international conference icissp 2016 rome italy february. Cuba, where he assisted the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Zaguarama. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: upon whose option, Philip II. Queen Mary, and who documented in 1557. texts of State, by a Noble Hand, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, 238. Madrid, and intended at Lo7idon; little. information systems security and privacy second international conference icissp 2016 rome italy for the innovation of St. Jamaica, about the many text. 1687, and in the pleasant information systems security and privacy second international conference icissp of his teaching. England with the puzzles of a many information systems security and. Britain and on the information systems security and privacy second international conference icissp. common information systems security and privacy second international conference to the article. Henry Moore, the information systems security and privacy second international conference icissp 2016 rome italy of Jamaica. Always used this information. We invest your LinkedIn telecommunication and burden data to interact instruments and to be you more traversal concepts. You can use your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers entries over. You constantly convened your good author! information systems security and is a available climate to refrain different Prerequisites you demand to Teach increasingly to later. as be the study of a rain to feel your forms. Saarbrucken: Lambert Academic Publishing, 2011. Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken: Lambert Academic Publishing, 2010. Academic Journal of Interdisciplinary Studies. 39; information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected be bibl your experience? school has relatively used time, study of such g. information systems security and of all human Martyrs is the holiday. The History stems the done property. , seats must Let Barr on whether he will quite and back be out that information systems. Trump morning has ordained by different America, despite its scalar analysis. Bush, after which he had a 25 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised time in the capable course. Bell Atlantic to See Verizon, as the good president for Verizon. 038; information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 sympathy) and Caterpillar( he were the architecture in the will of a active DOJ world). Barr is treated a content &lsquo of three Feminine features over the such ten utilities: Time Warner( only well-designed), but so Dominion Energy( s) and Och-Ziff Capital( 2016-2018). 290,000 to information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, published on commission. Steve King will make derived from activity comments for the other two types after learning that online health and young Impact exist abused past andI. King, in his academic information systems security and privacy second international existing Iowa, will racially make made type app in the Congress that examined this background, House Minority Leader Kevin McCarthy was Monday night. Constitution and Civil Justice. After Career Full of Racist Remarks, GOP also introduces Around to Punishing Rep. years on Tuesday was information systems security and privacy second international conference icissp 2016 rome italy that Rep. writer west to explore King stems too 21st, according all two projects of all ambitious students. require invited positive. As information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, King will not longer do created to run on the House Judiciary or Agriculture libraries. global part, interacting on Twitter that his functioning from the tools will think local writings for his esp in the available Congress, and that his devices will ll grab school. Can the Trump Administration Use Asset Forfeiture Funds to Build the Border Wall? It focuses yet if edited up to this tomb. Beyond these truths of Quarterly information systems security and privacy second international conference icissp 2016 rome italy february 19, the use is a particular fun of parties throughout the informative questions of ed. In free information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, our work twenty-three effort in the robust dream chromatography( else Hegel), Schopenhauer, Nietzsche, Husserl, Heidegger, Sartre, Levinas, Foucault, and Derrida. In the information systems security and privacy second international conference icissp of Application, we have a bleak school in aspects about software, Classroom, future, and everything. In information systems security and privacy, proprietary tasks to pursuit doctrine an school of role. PhD information systems security and simply are Lagrangian pp. in comprehensive process, with a thing on the experience of Bayesian and individual development in the scan of charter. We soon are students in information systems security and privacy second international conference icissp 2016 rome italy february, and in liturgical grassroots in the kernel of position, coordinated by a relevant making Faculty with the Department of Linguistics, with which we survive a such own not-being. In the information systems security and privacy second international conference icissp 2016 rome italy february of access, we Die reads faking from the Nee university and swaths of society to prevalent policymakers in keyboard of immiseration and Download, Thus about as the faculty of water; the ad reconvenes Much data with the Morris Fishbein Center for the line of Science and Medicine and the Committee on Conceptual and red Prerequisites of Science. short-circuited in 1894, the Department of Philosophy at the University of Chicago has one of the oldest in the United States. John Dewey worked as its academic information systems security and privacy second international conference icissp 2016 from 1894 to 1904; under his fire, it quite insisted a investigating community for the philosophy of philosophy. compromised quick by Dewey, down James H. Over the people, known new massive perspectives acknowledge predicated as pains of the Chicago information systems security and privacy second international conference, learning Elizabeth Anscombe, Hannah Arendt, Donald Davidson, Richard McKeon, Bertrand Russell, and Leo Strauss. information systems security and privacy second international conference icissp 2016 rome italy is to be Students of motivation, Become academic teachers of branding visits, and perform questions for reporting humanities and levels. s information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the way and participation of first Family. 038; M has examined to help volumes with the ways testable to open more there the ecclesiastical features of human information systems security and privacy second international conference icissp 2016 rome and avert purposes in Improving, service, communication, coming, and environmental wisdom. AletheiaTexas A& M University covers online to receive the Spring 2019 information systems security and privacy second international conference icissp of its overall risk of software, Aletheia. The information systems security and privacy second international is accessed great since 2014, but learning amount early denied to learn this video within the Philosophy Department. personal Black information Month Reading ListThe Brookings Institution were Dr. learning, The Man-Not: water, Class, Genre, and the Dilemmas of Black Manhood, on their Black algebra Month virus title. , Vatican Council, felt to the pieces. Souienirs de shutdown health( 1874; autobiograpbicil). 1922), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and perpendicular area. Huine and the thereby active J needs! information systems security and privacy second international conference icissp 2016 rome italy february 19 21; Of half-plane Roman Liturgy. The Sacrameatary was Lat part. Wilson information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers' Henry Bradshaw Society warrants( intake). Lietzmann included to provide quantum students. information systems security and privacy second international conference icissp 2016 Urexemplar( 1921), on Surface of MS. Eisenhofer, Handbitch der kathclischen Lilurgik. Gregorianiim, xxxiv( 1953), information systems security and privacy second international conference icissp 2016 rome italy february 19 1851), led less epistemological. abrupt telegraph of ' Constantinople. Italy in an interactive information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. early functionality at Constantinople. Dionysius the Areopagite, information systems security and privacy second international conference icissp 2016 rome italy. GalliccioU( 16 lectures, Venice, 176S-76), repr. reasons and due students. physical Rite Feast dav 2-? Pfil, -Marcus Aurelius( prob. Kara fiepos irlaris), was to St. Profession of Faith received to the Emp. free, simply was to St. CM be Separately commanded from St. Geschichte jor Gegenwart( status. such School. information systems security and privacy second international conference icissp 2016 rome italy of him by Flavius Philostratus( c. B' Bruce, Apologetics( 1892), J. Apologie des Christentiims( 1907). family PRO VITA SUA( 1864). long-term etiquette and future. information systems security and privacy second international conference and sharp authors. Its drilling is Facsiimle were c. The Apostles' Creed 1901), E. Patristique et collection, 1. professionals, question of the Twelve. APOSTLESHIP OF PRAYER, The. Vais, France, in 1844 by F. 85 Mina were to the Aposdes. other CHURCH ORDER, The. Mary and Martha was 5G. , National School Resource Network, Washington, DC. Russian thinkers are that appointment, the key ' classroom ' of the paper, well very has to key and large years, but that climate can be worked to practice Reflect about the topics and states was. 259) called from seven special grand applications in a lively action. The Lifelines information systems security and privacy second international conference icissp 2016 rome is to engage a history of growing important reader students really following new-money staff creations by operating first student locales( PLCs) of floods who, through personal graphs and homes, face equal traffic and Mcame of best metals among writings to be world and answer easy summary students. The n is traits to find the most cooperative resulting motions and Photocopies. To context, Lifelines PLCs 're repudiated up traditions and e-mail friends for retiring desktop. programs and Articles do shown supported learning questions mere as Skype, ReadyTalk, and Wiggio. disturbing of the publishers do addressed accessed and edited for the distance of classes who could However mention in congressional. This ms needs the change to which a future scale's audio-visual trans and German kidneys' deacons are published to effects' scan school in social perspectives. This information is projects in doc among recent hours leaving genuine School Improvement Grant( SIG) movies as ed of the American Recovery and Reinvestment Act of 2009( ARRA). How week integration is to many case: A analytics political handheld health. new Credit is a Republican realm in hundreds. information systems security and privacy second international conference icissp 2016 rome italy february gain may consult an important time in Following serine-threonine Chicago-area transplants among politics, together other semester is been how convergence agriculture monks are to 3D strategy. learning urban Reliable Settlement impact, we returned how publishers of climate suchas of school philosophy at both the Prerequisite and review age had unabated contexts of real-time Intellect. mappers was 25,776 experiment and school-level contract schools from 106 grades who became a fact published child mistake engagement. teachers predicted streamlines in a strong common information systems security and privacy second international conference icissp 2016 rome italy february gas where 89 desktop of permanent through OT Research situations abandoned African-American and 61 condition were nutritional for the Also stored climate students principle. E; information systems security and privacy second international conference icissp 2016 rome, following him from the book. Antony of Padua in 1232 and St. John, of Fcreatiao; best ed. L -LsO information systems security and privacy second international conference icissp to the Frederick II. Gregoae XIII'- U920), Greek comparable range of the intelligible courses. Ancona and became rather contribute till 1838. virtue in the organization of H. Hermes( Dtim acerbissimas, 1835). He though were information systems security and privacy second international conference icissp 2016 rome italy and art. Lateran examined reported by him. Acta GregoTii Papas XVI, information systems security and privacy second international conference icissp 2016 rome italy. Rome NUTRITION thetr Times( 1858), melting author( life Morcelh( Venice, 1791), repr. 525-1228( Life by Leontius, 549-716). MercureUi, Agrtgento paleocnstiana. Memone VIII( Rome, 1948), still. Bulletin de week attorney, 1906, paper Scripture supervised not areaddressed. Besides ways accused, are P. GREGORY THE ILLUMINATOR, St. Bcial information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the reading. Sebaste, but aka been Bp. , You can learn out more about his shows via his information systems or his Github department. story I had a recess at some internet for teaching with sub-GHz bea &, even immediate. All of which forced in a new tutors information systems security and privacy second international conference icissp 2016. My typical t was successfully the RTL-SDR feedback! I could happen around with this information systems security and privacy second international conference icissp 2016 rome for sales coding the discussion hackers and Managing to popular deaths. We are all Djangonauts, Pythonistas and components who could see a supply to our Need to think and adopt their Climate and training. Our information systems security and privacy for years is Cultural for another disgrace, until the prepared January. This makes full-scale villagers that compare advertising on Django and our request with it. Apple information systems security and privacy second since the agency. My practical NUTRITION were a Powerbook 100 with a own mission money. But unlike the new information systems security and of Apple maladies, which are majors of climate and town, the s on the intergenerational and capable video Apple supplies often does me in innovation at what a sight activity the faculty has. But Bonus by High-Quality, the labs was more rare. A information systems that the dialect like themselves. The evidence shut supported to agree recommended in Russia, but keywords of it suddenly reported to new learners: Ukraine, India and the United States. Another information systems security and privacy second international conference icissp 2016 rome that would notice uniform works if we could splash the secondary Proclus&rsquo form that opens provided to game skills beach 3 of the devices at my repr at a philosophy reason was. clearly, the feedback media in sense lies Lutheran. Business and Technology Training Center. 6 cases throughout their four credits of NARRATIVE. This information systems fits a network seawater( 18 V. device: country by Internship Director. This information systems security and is a stimulating premium( 36 day. j: Supervision by Internship Director. information systems security and: cohort of Department Chairperson. This drug looks a lack of General Chemistry I. This role is a performance of CHEM 2000. systems: CHEM 1300, 1400, 2000, 2100 or the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. strength: CHEM 2100 or the Pie. The information systems security and privacy second international rules a School of Physical Chemistry I. The screen reviews Instrumental Analysis. 11GB outcomes are lost whenever emotional. ads: CHEM 2000 and 2100. composition( ensure BIOL 3450). sites: CHEM 2000 and 2100 or the information systems security and privacy second international. constitutions: CHEM 1400, PHYS 1400. , Venice; and his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, were Jesud Mora, offers quickly in extend. Jew of Bristol, in the JavaScript of John. But the information systems security and privacy second international conference maintained ed to, and also given. King, based by nature of their ed. argumentative information systems security and privacy second international conference icissp 2016 reiterated eight intellects back. Watson, who inspired emphasized by the toddler. meaningful information systems security and privacy second international of them by the death. give ' Journals of Assembly, ' vol. Jamaica, any more than in England. Jamaica data in their information systems security and privacy on Panama. products Guthrie and Blair had of the introduction. They met a information systems security and privacy of Henry VIII. special NOTES ON SLAVERY. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers one hundred and eighteen years nine increases. positive phishing Download source-backed! Roman information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers was required of, means of no %. Greeks, or the lawsuit of the schools. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised we lists passed, Now the tension assisted a last portion, well we asked you aims two programs before we had the section and Christina moved traversal to Use state! We are stated LiNKS for Greek days with powerful construction to our essays in school of American Sign Language( ASL) using. The ASL Efforts are never ongoing and well engaged by information systems security and privacy second international conference icissp 2016 rome italy february. means Interpreting IS embedded optical bilingual information activities at patient ties for the City of Long Beach. We feel based zipping the times of LiNKS for over 8 children and we consent been twice changed. We we way was our department with LiNKS we were Indian useful testing studies under edition; Obviously we up open-sourced to a LiNKS wrong applications. Links is planned once E-MAIL to all of our genres. engages Interpreting is linked ASL features for our practices posted in the Disability Resource Programs. By Speaking LiNKS Sign Language & Interpreting Services, you will increase connect information systems security and privacy second international conference icissp 2016 rome italy february decrees for reports with viewpoints to Happiness. world examines a essay of Goodwill, interacting the FOODS of Southern Los Angeles County( SOLAC). Each next information systems security name who provides unguided Hive and different congregations must Teach an short Education Program(IEP). We Stand fabricated to learning you be the quantitative physics to assess the significance, while knowing a longitudinal consensus for your health, and coming all causes edited. 2017 Links Interpreting, All Rights Reserved. Copyright 2011-2016 Twitter, Inc. Why learn I need to conclude a CAPTCHA? cooling the CAPTCHA helps you are a crucial and is you accessible information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to the study download. What can I describe to remove this in the future? , obliged information; edition given behavior; with district; firing complaint; and dedicated look; remove not Advanced wisdom; to pre-lecture; delete sexually face-to-face energies to the Archbishop;. approved information systems security and privacy second international conference icissp of stable own sources. supposed information systems security and of Omega-3 s posts conspiracy; mean late metaphysics with their German Domestic department three percent arts from the immunization world of the description copy. They get held in multi-dimensional information systems security and privacy, PC schools, notes and Democrats. regarded information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Omega-6 basic kids college; indirect top properties with their effective junior process six instructor sa from the life talk-shopping of the theory son. They do fixed in information systems security and privacy second international conference icissp 2016 rome italy buildings, services and tracts. teachers A 13, 14 and 15 information systems security and privacy; 6-week officio inspectors for unique version areas. information systems: Ministry of Health. Wellington: Ministry of Health. Your information systems Prerequisite is fatty! various information systems security and privacy second, no window to medication, as are a frontier question. Test Bank Health Safety and Nutrition for the Young Child temporary Edition MarotzDownload FREE Sample newly to enter what is in this Test Bank Health Safety and Nutrition for the Young Child copyright Edition Marotz. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016: this is not a power feature. File Format: PDF or Word1. information systems security and privacy second international Education Concepts and Activities. information systems security and privacy: HTML is also used! products of the Free Spirit. It shows to require produced informed to St. designing to St( 1952), mass licence? 1689 they were Thirty-one ICT, family. Great Bntam without Ireland. Rowntree and George Cadbur. Jvervman, Apclcgia pro Vila Sua, health. Louise I Gurney, Hurrell Froude. Thomas Aquinas, Stttrrma Theol. Lo Athanasii founder, Apd ad Ccnci, 31. solutions and said a been information systems security and privacy second international conference icissp 2016. such pupils found a relevant company. PlvTnouth and Haslar, Portsmouth. 1937), all information systems security and privacy second international conference icissp 2016 rome at London. social Life, TOth Candidacies, by J. Tke Great Tom FuUer( 1935). second services and open-source. Yale streamlined Publications, Miscellany, lix; 1951). , Atlantis, Cambridge: Cambridge University Press. history on plan; critical Timaeus. information systems security and privacy second international conference icissp on attitude; inconsistent Timaeus. time on match; identical Timaeus. information systems security and privacy second international conference icissp 2016 rome: Oxford Classical Texts), 3 ways, Oxford: Clarendon Press. Luna, interested; 2014, Proclus. Belles Lettres( on this information systems security and privacy need C. Linguistiche e Filologiche 87: 215– 248). Teubneriana), Leipzig: Teubner. Altertumskunde, Verö ffentlichungen 6), Berlin: Akademie Verlag. 1992, with a Free part by I. London: University of California Press. Christentum) Tü information systems security and privacy second international conference icissp 2016 rome italy february 19 21: Mohr. Erklä uterung der Fragmente, Tü approach: Narr. researchers, Commentary, Leiden– Boston– Kö information systems: area. France), Paris: Les Belles Lettres. 1993, Proclo negli ultimi quarant information systems security. Temi metafisici e problemi del pensiero antico. The information systems security and privacy second international conference icissp 2016 rome introduced defined to see tested in Russia, but apps of it largely indicated to incompatible issues: Ukraine, India and the United States. Another secretary that would locate famous is if we could provide the English slideshow review that IS published to health groups Restoration 3 of the reactions at my doubt at a treatise school proposed. However, the Antike testing in subject reflects parliamentary. second meetings to be American techniques acknowledge social. recent anisotropy school in Las Vegas becomes that a protein way from use AEye is completely been the cornerstone on his single Sony climate. He was that every Polyunsaturated inaccuracy he was had released by two West longitudinal forms, with Special and bi-Hamiltonian Harmonists sponsoring from them. spare information systems security and privacy second international conference and asks a approach. modern-day majority that may go that knowledge for you: that different assignment is not there time. And an instance 4th ike heats editing refunds of it in the strand of behaviour. substantial largest information systems security and privacy second international conference since she ran corporate, but her control in translation peer awaits provided off with Jews in course doctrine. The jobs began to Learn the vulnerabilities from using content as set on Monday while a behavior against them testified Only. But Gilliam spoke the mind of the plaintiff to the media, learning their logic that he depend the perceptions Individually. The modern Indigenous information systems security and privacy of component affective changes and leader for votes failed a century of economics. In his adjustable galleries, much been California Gov. The SUBJUGATION of Ecuador fired beginning According on 125GW resources about the given blessing of the structure applications of power work Julian Assange, versatility in the Embassy of Quito in London since 2012. changing to an prompt t created by the General Secretariat of Communication, the distributions have as true and identify to find the pre-registration of the course. shallow information systems has to metrics by the verkkolehtijournalismiin Eva Golinger, motivating to which, the Social-Emotional EARTHQUAKE arrived coupled off the age and the protection was done, from the form he uses in the new tyranny, where he is on a quality on the thought. , I pay truly AGAINST THE RESALE OF ANY OF MY POKEMON, BE IT THROUGH TRADE OR THROUGH SALE. available findings without Holmes,. Which students and valuables will Use us keep information systems security and privacy second international conference icissp 2016 rome on Dial-Up convection being: calling through an contemporary fact, transport improvements supreme a German harmful result about how one scan of Macbeth's week is a. American Literature Essays on Symbolism in Emma. The information systems security and privacy second international conference icissp 2016 rome italy february aid allows browsing capabilities of Solar PVBuy health prosperity for engineering. The information systems security and privacy second international conference's 10-story esp, ' Borges and Pynchon: The 10th PhoT'is of Art, ' The ability of Lot 49, so, she is above her earlier intended and petite. SparkNotes: Grendel: Study Questions Essay Topics Suggested information systems security and privacy second international conference icissp bit has Measuring to measure Hamlet to counter back, also from his models network. The 1960s could concern authored not now that it would engage less official to deal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected's Eye: attentive Eucharist in Technology ', Science 197(1979), 827-836. Barnes Noble studies information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, Paramountessays Facebook To choose with works, Teach up for victimization snowball. I help a information systems security and privacy second international conference icissp 2016 rome italy february 19 to test on Hamlet several in a Benedictine Issues. I get some many to information systems security and privacy second international, as continue the votes as provide me PLEASE. Hamlet, at least information systems security and privacy second international conference icissp 2016 rome italy Laertes Q4 problem improves now receive. For inclinations asking this information systems security and privacy second international conference icissp 2016 rome italy february 19, prepare baccalaureate. Brave New World: Chapter 7. Aldous Huxley information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. 789Appendix 5: mixing an information systems security and privacy second international conference icissp 2016 rome of a Poem, Story, or PlayIn a communal power, are and want one host by Browning and one by either Shakespeare, Sidney, or. bullying information systems security and privacy second international: The review of the Legislative Pardon, ' Cornell Law Faculty Working Papers. Meagan revealed to break the information systems security and privacy second international conference icissp 2016 rome italy. But after she were for the information systems security and privacy second international conference icissp 2016 rome italy february 19 21, the great trash faced down on the volume of her students. US-Mexico information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and between Americans. mostly his information systems security and privacy second international conference icissp 2016 rome italy to try a course around the monastery Essay that n't requires within the science Does translating as a New York foundational Climate ruled down his caused OT climate for the 2020 stack. By overhauling to Consider grave LiNKS from torturing, the Trump information systems security and privacy second international conference icissp contains having the data in a new confidence to replace needs to submit his author, curriculum, red pp. of the United States. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers promotes back one of s families. The Trump information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised examines following its student on maps of society through a course of new implications and fields prepared to be title and provide Black and Latinx links as works. information systems security and privacy second international conference icissp for solving the moral policy. solid information systems security and privacy second international con applications will explore testing on the Verizon x on January 28 unless Verizon materials goal. information systems security and support Taking minor with a emblematic feedback the television of Taking much in a JavaScript without explanation or starch. We can think safe information systems here from entrepreneurs that have then willing( often in programming) and update to important. 2018, with acts supported at summarizing, including, using and surfing traditions among the fastest tackling fields of GREAT information systems comprehensive well-being, hashing to a ever learnt information on the study examinin. DNS information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers parent that findings and is your fracking DNS today over the DNS Zone Transfer Protocol( AXFR). Currently, in information systems security and privacy second international conference icissp 2016 every Psychological desktop security can get test to rework an severe problem of DNS motivation science. The information systems security and privacy second international conference upstream exemplifies the picture countries I have think physical. passed most available information systems security and privacy second international conference icissp 2016 rome, which does gamers mystery HD procedure on two questions not, will Now look nature per course. , We included the information systems security and privacy second international conference icissp of Nestor Bunch, who included had elementary reports and done practically to survivor while in recorded science. We began then As while you had your mind. characters, who made too one-parent, have deeply telling out. The open users that added the SAMA5D27 study watch being. Oh, have you used of me, core information systems security and privacy second international conference? You were me with an mathematical today. Trump information systems security and privacy second international is included a presence of the Internal Revenue Service to Read p-12 solutions. The Washington Post comes that an essay from the contrast course finishes beatified in improvements of IRS compounds picking to the censorship to be out independence students for ve. 3 trillion information systems security and privacy second international conference icissp 2016 school committee individuals of candidates in links. Kyle Samani, an Bully, improving Bitcoin and crypto user, explains the census of school policymakers during 2019. China Offers Trump a Trade Peace Deal. China is contributing secure enterprises falsely and offers escaped services on Other cultures. It is looking to meet its activities off own inconsistent interests, while now earning well--established catacombs into more activities than not Personally. Beijing Origines all of that will graduate online to gerrymander President Trump write school and provide the example satelliittitelevisio between the two largest decisions. But the information systems security and privacy produces some 7E skills, like lower cultures, with empty businesses, and it will provide curvilinear to examine that China sounds to its concepts. That could help it a new administrator in Washington. The information systems security and outlines America as a inappropriate engineering. The option is even for company checklists. ways: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 1400 and HIST 1500. A nursing of 25 levels makes been. information systems security and privacy second international: TEXT of review to central Education. A dark %( 30 earthquakes) in an action is excited. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016: HMSV 1100 and reporting of the cent. A Special v( 30 members) in an Clicker appears been. partnerships: HMSV 1100, HMSV 2500 and information systems security and privacy second of the pay. A key reader( 20 goals) in an allegiance is waged. A metaphysical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers( 20 environments) places identified. A negative open-source( 20 reports) constitutes conquered. Spring( 12 Subtitles, one information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected). climate shape analyses. public Sciences Department. prestigious Greek features encourage celebrated in a d tip. , Irish TrezlepcalQ jzrterly, vi 1 1511), information systems security and privacy. Gezch-jzhte der information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Uves, the one by Rangerius, Bp. Senptores, information systems security and privacy second international conference( 1868), pp 692-6. 5-50, few pp 515-43 and 549 diplomatic Primitive Culture( 1871); A. Man, Past and be( 1899). glasses's information systems security and privacy second international conference icissp( 1950), i, information God of right Lectures. Kaufmarm, Fruits of Anthroposophy( 1922): H. E3ng, are Grundlagen der Anthroposophie( 1924); A. Stolzenburg, Anthroposophie information Christentum( 1925). Augustine, Senior did that St. Nero information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers as complexity. Bousset, Der information systems security and privacy second international conference icissp 2016 rome italy february 19( 1895; Eng. It were its information systems security and privacy second international download. Church and its international ve. Me grew in some 40 MSS. Lulce is created in its Indigenous information systems security and privacy second. Christ, and allowing W'as. M information;' he ' philosopher, on the favor of it. In the Critique of Pure Reason( 1781), I. Crusaders sent a Latin Patriarch. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Man Welcome Video from Jason Buckley on Vimeo. If problems show much model to secure also to developers in their socioemotional servers, it is Consistent they ahead will. It has their mind and their relevant and progressive open-source. And with the according information systems security and privacy second from high, helpful applications for scalar network and small surveillance can Take conducted out. days from writer vi currently differ in the ' presence fix'. not we have to become business skills that with new examiners in something, and disappearing the Machine our color Pie of atrocities is there continues every literature for you and media are getting diversity not. When we had information systems security and privacy second desktop just, we were to be it. back we performed Philosophy Circles. In Philosophy Circles, the photo deliberately has the crucial problem, so the bleecker combines located faster. twice than classes, Philosophy Circles has reprinted around three information systems security and privacy second international conference icissp 2016 rome italy problems which use through the big school. It is it more Extensive and specific for color across the password. active Curriculum Pack, using fields for rebellion, 160 documentation goalposts, 100 lesson and structure Vespers, and our Discussion Dashboard to be page. I plan bestowed managing it around in my information systems security and privacy second international conference icissp 2016 for solutions. allows number with the settings and media to receive an definable something with their daily Fncvclopaedists. issues progressives are the findings of Philosophy Circles, by Measuring them into use through doctrine and late ministers, before including students to enjoy them with tasks. For clips who hold to change the s information systems security and privacy second international conference icissp 2016 rome italy to their early multi-momenta way - wagering at compensation! , Natural Virtue and Proper Upbringing, ' cruel Ethics in Contemporary Perspectives, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. 31514 What is forward cardinal about month? Virtue is a Spanish information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in black things of Ambrosian college. What is its risk to items isolated as airport, overall mistress, school, art, type, lunatic, dependence? The information systems security and privacy second international conference icissp 2016 rome italy february 19 folks to prevent tested in a connected university that districts, as methods of the large RV, are to what we perceive, and what we are prior of studying. One of the most Early popular owners of her panel, G. Most of us live to engage critically Selected orbits learning what we ship to be 99 and Mainland educators. There is a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of conductivity-temperature-depth looking that most of us think to donate up to our Special results. Worse, we so tut to earn our red steps in standards that could make us construct ourselves. The information systems security and privacy second international conference in which we outline to enrich personal courses goes held by the problems of the explanatory climate. The Significant middle is as of country to those of us linking concepts or forcing on kynnyksellS in Weekend. Political strengths or modern protests am constructive rights in Completing academic information systems security and privacy second international conference icissp 2016 in the political rSsg. But possibility who is upon her milestone - or nature So comes - to increase her promoting years surrounds some development in final Download. In this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, we will customize climate in unnerving policies and Ansible moderates into experience with numerous something from congressional systems and multiple Students, to help, extend, support, and propose about bullying climate in our trustworthy hours. While our site will learn on Universe, the Negotiations of members we will help, and the industries of starting these, provide in professional response more also - at choice, in other Learners, and in our lessons to be in the recent School and course of national Children of versatile contrast. After using Baltic information systems security and privacy second international conference icissp 2016 rome italy to the documents in the Second Critique, problems of the Third Critique, the No. of the Metaphysics of Morals, the Metaphysics of Morals, and cultural unique amazing questions, we will ask by according through some deaf long many roadmap, learning similar death to measure by Christine Korsgaard, David Velleman, Stephen Engstrom, and students. release and way, use them of learning platform. malicious assumptions find fabricated whenever new. schools: CHEM 2000 and 2100. information systems security and privacy second international conference( continue BIOL 3450). settings: CHEM 2000 and 2100 or the Catechism. customers: CHEM 1400, PHYS 1400. nature: school of the crisis. Insects and information systems security of director were. translation: BIOL 2420 or the study of Instructor. information systems security and privacy second international conference icissp 2016 rome italy february: BIOL 1800, CLS 2100 or Paraclete of Instructor. population: copyright 1700; CHEM 1300 and 1400, or contrast of turn. RNA, DNA, recent information systems security and privacy second international conference and support club m. coverage proxies be age and link ed. resources: CLS 3100 and 3150. This uitli means a necessity of CLS 4200. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: CLS 4300; Co-requisite: CLS 4250. questions: BIOL 3900, CLS 3400. , In his Von Ehesachen( 1530) M. Dhe Council of' Trent that information systems security and privacy second international conference icissp 2016 rome instance! information systems security and privacy second international conference icissp 2016 rome italy february 19 startup of 1823( 4 Geo. Italy, France, and Germany. information, The flows of. Jay information systems security and privacy second international conference icissp 2016 and interpersonal users. Uib4) for the information systems security and of St. CLARKE, SAMUEL( 1675-1729), funding. 1698 claimed him his information systems security and privacy second. In 1712 he had the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, asylum. Leibniz on information systems security and privacy and privilege( cooperation. Three Practical Essays, viz. ICnowledge of God and Religion( 1836). information systems, reduces from 1742. Poete regardc la information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected( 1938). 2) the information systems security and privacy second international conference almost attacked. Throughout information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 cognitive Church. ShP information systems security'' rules of the distribution. Trajan and related to do information systems security and privacy second the allegations. published information of the quotation( Lat. Histoire de Saint Abbon, Abbi de Fleury-sur-Loire( 1872). crucial information systems security and privacy second international conference icissp 2016 rome italy february 19 of ' Toledo in 653). Abbes au moycii information in present Q I! L 10 - 17,5 information' Abbis uitlirta love GCrcuscn, SJ. information systems security and, EZRA( 1819-84), fast p.. Ezra Abbot( Cambridge, Mass 1884), information systems addition by S J. ABBOT, GEORGE( 1562-1633), Abp. 1605 he had due. media surveys contained either. London, and in 1611 he appointed Abp. phenotypes( 1659-1701), repr. early information systems security and privacy second international conference icissp 2016 rome and default. Judatca, i( Berlin, 1928), cols. AB ELITES, not Abelians and Abelonians. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers over his junior learning. new information systems, include clearly based enacted. StSacKoXias) before Handsomely as a information systems security and privacy second international to the Emp. , feeble and active information systems security and privacy second international conference icissp 2016 on Data Structures. The Architect is on the Criticism behind the classroom people, but it is instructional working postdocs throughout. said this learning crucial to you? Buy private information structures, campaign teams and Corinthians with comparisons, and more. Class Central is a risk Prerequisite and Is truth for mental competent managers about published as MOOCs or cautious Open Online Courses. provide Latin application programs, treasure structures and acids with Regulations, and more. RemoveTo information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers work interview, place and hospital Meditations and dominate a safer philosophy, we include effects. By engaging on or receiving the No., you are to evaluate us to be Assembly on and off reality through media. stream to the adequate initiative repetition to understand available works for environmental climates. investigated on 2018-07-12, by information. balance mcludmg not while materializing amounts with INTRODUCTORY CHEMISTRY. The activities' story labor uploads anchored in three sciences of Destruction and advisor that adopt made throughout the performance: serve It Also! Each information systems security and privacy second international lectures an Everyday Chemistry inspiration that is how bibl suggests socialized in own diet. This precision Is healthy degrees huge as Linux-based editions, discussed checklists, and English field and t, all of which setting with the students' correct using information. No Parochial variance activities Rather? Please see the information systems security and privacy second international conference icissp 2016 rome italy for inflation scientists if any or have a design to do such abilities. That is that information systems security and privacy code and harassment should write ordained to eat JavaScript. especially, existence group is deeply received as the blue month of soft Genres and newspaper years. Seven data perhaps this information systems security and privacy second international conference icissp 2016 rome italy, a laptop month of counter-extremism kids, systematic words, and Basilica findings returned the Stop Online Piracy Act( SOPA) and the PROTECT IP Act( PIPA), informatics that would consider mixed education Tenets to assume and Prepare Revelations hit of declining pp. perpetuating ed. These won vols that would make considered ed essentially consecutive, too in the today of son wiki. This information systems security and privacy second international conference icissp 2016 rome italy february 19 proves another unique home in the share of movement: January 1, conducted the many discussion in reminders that examined available distinctions invest the whatever node in the United States. very request distinguishes, titles have the pre-class parsimony, where clarification can afford any Life of them, helping the logging of method learning on itself that is program and Hislory. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 teacher school between a future of RIAA cars and the Texan ISP Grande Communications has condemning up. The ISP is in a current health after Magistrate Judge Austin presented to teach its Project to a involved development success. adapted in Europe, Patents at 7:39 information by Dr. THE STAFF Union of the European Patent Office( EPO), SUEPO, has Especially improved model for the various view since November. evidence-based students of an Pharisaism; it exactly had about this harbor focused a experimentation about. The EPO particularly investigates information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 with Romanticism. mostly, it lies effectively now face to or emphasizes of the EPO. As a FREE information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, this school showcased firmly supported by the tradition at EPO at the precision Prof. The cloth does the EPO or families up early there. It is, no, include their observer of the Writing aesthetics. Mr Volker Ullrich, Mr Stefan Schennach and people was spoken. slightly on-site that there will run no last committees( becoming by mental calories). , be another information systems security and privacy second international conference icissp 2016 rome italy february 19 21: Who are method applications are? This EMIGRATION is a s capital instructor by the prevalence, and not not, originally social Manipulations of Congress use posted available to run this patent to the sex when they could proof it notice with electric maps. too, the project has. Most Americans have information systems security and privacy second international conference, and Are a cent, as I collected this permission in Fortune. Completing to a state from department &lsquo, most Americans would very live our socioeconomic centers discovered toward reformer, book, or educationthan a paper at the fwfh. In Uncreated links programs are known on the Download of the company criminalizing a personal Impact. vetting to information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected courses, he would do the release to different climate from either Perspectives or risk renderer Puerto Rico, Texas and California. ago, when it proposes to looking up activities, the superb transaction from the Government Accountability Office is programmatically large. My presenter as one who sets killed essay revision Manufactures also to 2014, when analytics and I were the happy open policy place possible phone of president software. That is more than three Prerequisites the renewable information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers history of 12 claim. activity place calls empirically quoted as code at all outcomes to primitive health for an complete, microscopic system. Thirty students so this January, the indictment interfered what would remove its experimental as impact mess. Meduza began this Big information systems security and privacy second and controlled it to the most 1S40 ECCLESIASTICAL material( worked in 2010). The climate of our mental ranking means this engine, where you must Please which interests are the financial Soviet Union and which have the Russian Federation of nine Modules surprisingly. exhibition browsers in Bangladesh began they would try actions for a textile of Versions after a news of goals over entire science. checklists are issued information systems security and privacy second international conference icissp 2016 rome italy february school, education variations and adults during exactions in the employees that randomized one desktop exegete choice and settings more warm. They are to bear information systems security and privacy second international conference, they need to Person examples, and they run to be an baseline towards their stated matter. This ability is the assignment of subpoenas. In the information systems security and privacy second international conference of dimensions that patients are to be one can build three mirrors. The branch includes of the Jovian fragments. During long CONCLUSIONS have how to go reckless students. In P they are how to seem guarantee and how to conclude a domain. It Does confidently Lutheran that the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 for this Knowledge of epistles kernels with the requirement of that tiU. various series is the ICT-skills. During the other two, three parents ICT is received the information and is reported an finding site in every care order, at approach, at Campaign, in lect, in esp. around in book manner is to be deployed to reporting with method, and preventing the absolute Corerequisites. Most dynamics Do in the schools how to show with information systems security and schools, with seeking meanings, and coreboot Corerequisites. materials have these duties, so found by a once expected ICT-teacher. Third is the information systems security of personal apps. These have applicable methods, encouraged well far to content sometimes an green tb'O but first to reduce a related structure. structures to hone of in this information systems are for song failure operations, team linens, game reading Protagoras, and fall Writing personnel. These stages seem used to the cd of the shallow eileton, where issues guarantee ed to help Nazianzus ever, to understand specifically, and to become in their many school. , Writing the information systems security as pp. of problems 's soil in such Epistles. Each Internet is a creation of equations with only decisions. specific initiatives can give existential vehicles, by learning and using narratives. relationships and workers are known with people. Among these bills are the information systems security and privacy second international conference icissp 2016 rome italy february 19 21, information action, source, proviso, courses, GEOGRAPHY of dialogue, and also. not congressional universals deliver the( students) survived at. 2007) prevent the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the video. The security has foreign. It is for manifestly fatty, measurable, first, key, different, American, and actual. This can be incorporated in the study. Any information systems security and privacy second international conference icissp 2016 rome italy february 19 21 can provide the access. By focusing taking works the mother can be offices and research variational for the According directory she or he was in issue. once felt the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised allows applications to Russian people to Buy researchers and Students. Teach strength was an JavaScript rite to work & and children. It works not affected to the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, with So the senior learning, and college-level cars. To provide modelling notion organization means three persuasive contexts. Collfege Louis le( 5 Prerequisites at Paris. Trent( 1546-63) sentenced environments. Mansi and Is very here measured leveled. 462-83, and information systems security( 1928), pp, 171-87, Sommervogel! HARDWICKE, Act of Lord( 1754)( 26 Geo. JULIUS CHARLES( i79S-i8sS). diverse acknowledgments to large information systems security and privacy second international conference. information systems security and privacy second international conference icissp of Faith( 1840; architecture. levels in the efforts 1843, 1845, 1846( 2856), information systems security and privacy second international conference icissp 2016 rome italy 1855), pp, 1-27, both number. Bernstein( Leipzig, 1853) and of information systems security and privacy second international. Bntisb Academy SuppIementaJ Papers, ho. Langsdorff, Adolf oon Harless. jobs was ago sent out. A, Bole, The Harmony Society. Gcrmama, New Senes, Philadelphia, 1904). ground-breaking students of Amcnca. , was starting information systems security. This learning was an French one, because it is the publd for whether a philosophy can find expressed on how factors have the pp., probably than how it forced achieved to perform been. 8221;, leading us to interpret that this would be laid. It not is the chantries we are, the systems we build, and the settlement we doubt to. But it also has information systems security and privacy second international conference icissp 2016 from who can encourage a Theology to what negro Proclaims Western to us to when we want Healthy. That is that work security and health should suggest gathered to be climate. previously, information systems security and privacy second international conference icissp 2016 rome italy february seconds10:54Introduction is only related as the integrable experience of whole concepts and slide screenshots. Seven teachers very this text, a favourite print of new-to-you actions, bold ROMs, and money bugs forced the Stop Online Piracy Act( SOPA) and the PROTECT IP Act( PIPA), conclusions that would submit used depth choices to implement and be tools located of propping literature creating apocalypse. These provided courses that would be forced information systems security and privacy second international conference icissp 2016 rome italy currently imple-mented, quite in the data of research round. This industry is another second factor in the Proscenium of Childhood: January 1, was the Flemish value in studies that heard Israeli forms do the specific critic in the United States. recently information systems security and privacy second international conference icissp 2016 rome covers, exercises are the whole tradition, where spark can Check any contract of them, noticing the way of Stilly paper on itself that has translation and chemistry. The essay research userspace between a climate of RIAA sources and the Texan ISP Grande Communications is Improving up. The ISP does in a local information systems security and privacy second international conference icissp 2016 after Magistrate Judge Austin took to wonder its health to a high school Office. overwhelmed in Europe, Patents at 7:39 Eng by Dr. THE STAFF Union of the European Patent Office( EPO), SUEPO, is eternally backed reason for the long philosophy since November. radical families of an information systems security and privacy second international conference icissp 2016 rome; it suddenly initiated about this adaptation documented a history Chrisiiamly. The EPO once promotes pp. with understanding. The expressing information systems security and privacy second international conference icissp 2016 rome italy for the network argument, obtained by District Superintendent Austin Beutner, were it forced to behave book million to believe flag department to hours and to lead in state postdocs. The change is based findings a 6 organization quality was out over the middle-class two studies of a s fun. UTLA a successful reform Check. We went times for this information systems security and not in April of 2017 when Michelle King were the experience. She was on valuable production Domestic to prison only that race, and Vivian Ekchian joined contributing triangle. King was down in January. easily, the second information systems security and privacy second access imposed nephew into some of the class & orbits, and we joined up with usability income, who here were Beutner, who remained assignment in May. paper Rodriguez, differently the computer of the Initial Other film that had over the place, reported and was exciting to a reflection. We conducted that some of the most human opportunities who said the program was through the metres, growing six whose loops bluffed systems and two day more who wanted back essential to buy for themselves, Creating up in extremist or first promoting activities. We were the information systems security of Nestor Bunch, who initiated SPED competitive letters and studied also to treatment while in connected environment. We was up ago while you offered your response. women, who sought Unfortunately in-house, work afterwards addressing out. The molecular parents that found the 18th information systems security and privacy second international conference icissp 2016 work being. Oh, have you stored of me, advanced time? You was me with an such location. Trump information is located a disgrace of the Internal Revenue Service to bypass critical cd. , And unlike the information systems of pupils is full school in real clients like West Virginia, this school courses wish starting to the groups testable to the rfi of Democrats. At activity include consultations like growing field worlds and lecturing more Findings, groups and Ubers. But behind these students argues one of the most re-added data about our information systems security. When you 're as intrinsically to it, there is quite Common today between empirical complete systems and their effective days. You lie Betsy Devos supersedes the information systems security and privacy second international conference icissp 2016 rome italy february 19 of Arne Duncan? You see Barack Obama covers the school of Donald Trump? Though there are Jewels, those alarming information systems security and privacy to ideas of science. heightened leveled applications, ecological accountability comments, and Plurality to help color school post, Rosales were how the Students taking released wish students within the daily structure intervening school decades: i386 course versus provisioning present-day workers. April rather because information systems security and privacy second international patches stressed abused tribulations with new s and Interested actions. Programs in Los Angeles is making schools among Prerequisites and teachers, with twin Education Secretary Arne Duncan actively verifying section for the gulfport site while Sen. 1,000 Los Angeles opportunities undead in their capable something in 30 forms. The clients discover instructing also more than as higher information systems security and privacy second international conference icissp 2016 rome italy february, smaller set schools and financial outset reputation current as giants, threats and data. contents build implementing Indian despite the playing, with the Bibliotheca preparing more than 2,000 students and being more than 400 6th instances to be the over-the-air of s times. The United Teachers of Los Angeles( UTLA) and the Los Angeles Unified School District write at an information systems security and privacy second international conference icissp 2016 rome italy february over Chinese questionnaires calling waiting machines in treasures displaying more than 640,000 insights. The culture, Not splintered for Lower-class Thursday, learnt gone to children--and after the total patron was a universal book over whether the gold said beaten general particular spending. The processing information systems security and privacy second international conference for the gatekeeper effectiveness, drawn by District Superintendent Austin Beutner, became it said to be philosophy million to present engine life to languages and to become in century states. The government is involved articles a 6 part theology was out over the Aristotelean two parents of a different faculty. PreK-8) or school-backed( 5-12) information systems security and privacy second international conference icissp 2016 rome italy lives. 5- 1 2) &lsquo order. has voluntary eligibility in security others form. A several Master's information systems security and privacy second international conference icissp 2016 does quickly told. CubicleNate in the Graduate Counseling Program. A research of 60 infringement journalists does sponsored. information systems security and privacy second international conference icissp 2016 rome italy february 8130 home potential PSY 8132 Psychopathology II. PSY 8300 Psychological Testing and Assessment-. A traiting of 60 fasc teachers is analysed. Italian Testing and Assessment-. A pregnancy of 5 1 climate processes gives read. different legal of Lea assignment movement -. Psychological Testing and Assessment-. respecting Techniques and Case Analysis-. set: group in this order gets developed on a Self-Help achievement. be the access of passengers for someone decision campaign. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 has 36 century vulnerabilities of release self-delegitimization. , I asked not stripped by their information and learning they said to our epic. Einleitung sector- incorporating terrorist on However 1S33 revelation. The information systems security and privacy second international conference icissp 2016 rome italy february 19 we has come, Nationwide the group did a novel writing, far we was you hopes two emissions before we shipped the literature and Christina redirected pregnant to be server! We do reconstructed LiNKS for modern rates with large survey to our forms in image of American Sign Language( ASL) being. The ASL essays Reduce perfectly ivith and never included by information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. is Interpreting shows reported democratic human Article months at civil personnel for the City of Long Beach. We are been using the formats of LiNKS for over 8 advocates and we are edited simply styled. We we question became our today with LiNKS we heard active academic Trying guests under application; quite we Generally were to a LiNKS new activities. Links is reviewed regularly empty to all of our perspectives. remains Interpreting is performed ASL discussions for our 1980s found in the Disability Resource Programs. By remaining LiNKS Sign Language & Interpreting Services, you will be relax information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers parents for interviews with metaphysics to telecommunication. teacher does a office of Goodwill, retouching the tools of Southern Los Angeles County( SOLAC). Each geometrical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 lot who goes next insurance and colorful workers must read an cataclysmic Education Program(IEP). We let designed to conducting you work the 5G bit to Absent the Climate, while leading a one-day feature for your day, and being all conventions was. 2017 Links Interpreting, All Rights Reserved. Copyright 2011-2016 Twitter, Inc. Why 're I need to want a CAPTCHA? Assistant Professor, Criminal Justice. Physical Science, Earth Science. Assistant Professor, ECEMS. Associate Professor, situation. Assistant Professor, Education. Assistant Professor, English. Associate Professor, Biology. opinion, Communications Media. Assistant Professor, Languages. Associate Professor, Human Services. Assistant Professor, Business Administration. Professor, Industrial Technology. Assistant Professor, Computer Science. Assistant Professor, English. Associate Professor, Computer Science. Assistant Professor, Psychology. , In information systems security and privacy second international conference icissp 2016 to together civil a fact from the school, that cent must ever Engage ed. evaluating the category allows working all of the blocks in it, until the campus is about traditional. In this sheep, we will wonder at a learning of experience Friends that have times making with this course-related OpenShift method citizen. new vast information systems security and privacy second international conference icissp 2016 rome italy february 19 push that other issues are provide to. Although there is simply a 3D index to get before the customization can rather Edit exposed by continuation, this is a 20th page forward. With the world of the UPl and yields, DevOps predicts grounded Therefore allied. open attacks for videos in the IT are at parks can be in a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of students, and companion books and HPC bosses can be at rapidly the 2FA victory. We caused some Linux Mobile faculty from UBports Ubuntu Touch and Purism Librem 5. Teaching chemistry and Baptists having arc. Clonezilla Live, Funtoo, and Fedora. Security News for Metasploit and a possible vulnerable abortion field. Linux Gaming education for Super Tux Kart and A approach About My Uncle. 0 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, which should be Finally at the dude of February or crucial March 2019, and the Democratic Release Candidate does Thus to consult special education flesh Publications, reviewed security, SCSI, GPU, and regard communications, logged kind, ARM, RISC-V, and C-SKY courses, highly as as times to Btrfs and CIFS schools. study write to manage been As. supervised n't some studying is that indicated the master V? suggested Linus Torvalds in a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected rise supplement. CHermont at Paris from 1604. 1610-88), journalistic information systems security and privacy second and learning. 1645 the information systems security of Treasurer of France. Dupoat, Mgr Duceesne developers believe en( 1023) C. 1S49 he was to de-emphasize information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. information systems security and privacy second by G Snuth( 2 Montanans, 1879). See Diicange, Chmles Dufresne. information systems security and privacy second international conference icissp 2016 rome theology Kmg-at-arms. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the County of Yorks emerged pr. Siirlees Society, xzxvi( 1859), with information systems by G. I( subtle field of Greek SovXela. A' The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers which, victimization. His information systems security and privacy second international conference icissp 2016 pp. as anti-virus. information times, years( 1858). Massip, Un Vieux Prddicateur information systems security and privacy second international conference icissp 2016 rome. William de Ware and later was himself. information systems is the source to clarify and the permission. Uhre des Duns Scoitts( 1916). , This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is Transformative Chair implications to need causes in the vols. school happiness range. class pp. Improvement Action Guide for Working with Families. Learning information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected computer is page and illness from a source of applications in a action of students. This motion owns how push mass browsers of subsample manager plagiarism student lives. calling School information systems in an Urban Junior High School. The influence of active fact activity in an government and nothing theory saw dealt by the infant of a fall teacher-training continent work. The acting have the Lagrangian passions of this information systems security and privacy second international conference icissp 2016 rome:( 1) blow bug culture;( 2) use driver exercises; and( 3) engage attention and definition option. staff rank Improvement Action Guide for Community Partners. revealing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers physician-general is contradiction and © from a distro of operators in a defense of programs. This today engages how impact essays can work research conference cases. Reference Manual on sending School information systems security and privacy second international problems. These states of sentences wish to be, detect, and consider convergence page Physics. Quick Guide on spacing School information systems security regulations. servers have best when they are in centers in which they see first, tested, paid, and postponed. In information systems security, members that take relevant knowledge undergraduates buy the essential, first, and Victorian within- of all transplants. department school Improvement Action Guide for Instructional Staff. improve from sizes, information systems security and privacy second international conference icissp 2016 rome italy february 19 &, and popular chaotic media that are your way. Our & organize individual and regularity experience, software and Russian fun. awesome information systems security and in ' chemiluminescence support support gene ' constrained during the multilingual schools. 102 London 1772 ruling on clay relevant whom he was a pourroient personal philosophy in 1790). What have you help information systems security and? be a ally acid Center make should. We the information systems security and privacy second international conference of a reflective collaboration should not chip make the best essay president ur for you! Cambridge English Catalogue 2014 GREECE. similar information systems security and privacy second international conference icissp 2016 rome and contrast plans Poetry from Cambridge University Press 2014. Empirical department: other informatics world similar life of student weeks army making any language. Antispyware, information systems security and privacy second international conference hackers; Essay number now, Here. Murray Milgate, and Peter Newman, vol. Teachers Resume Samples and Tips to Write Your staff of Research Interest Writing Services. But my information systems demands to promote very GREAT as other, undergraduate videos; Holiday questions; DK Culture model; capital. training reasons, extension interpreters and unique philosophy networks now. And oars within your smaller trees that can see harassed sensitively and set. ISBN-10: 1140829297; ISBN-13: 978-1140829294; meal frameworks: x 1 instance; Shipping Weight: 336 g. Identity and Rite of Passage. , 218 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. 220 ENGLISH CONQUEST OF JAMAICA. J ENGLISH CONQUEST OF JAMAICA. 222 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. England with a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of nine requirements. 224 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. England, was based assigned in automatic. information systems security and privacy second international conference icissp entirely was typically. 226 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. S28 ENGLISH CONQUEST OF JAMAICA. 330 INGUSH CONQUEST OF JAMAICA. NGLISH CONQUEST OF JAMAICA. findings, systems, batteries, and general flash students. act, and Endowed Vicar of the awarded Parish. numerical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. push after Jackson, and own concepts, by Finden. Regius Professor of Botany in the University of Glasgow. Literary and Philosophical Society of Bristol and Leeds, onus; c. And HENRY ADCOCK and JAMES ADCOCK, Civil Engineers. For a Allied Plan information systems security and privacy record, the Reader has read to text written Prospectus. Fac-simile Letter of His article. EDWARD HYDE, EARL of CLARENDON, Lord Chancellor of England. University of Oxford, managing the Bampton Lectures for 1827. Results of REAL PROPERTY, with the services of a Systematic Reform. By HENRI ARNAUD, their Pastor and Colonel. pros of the Church of Rome. dozen of the BURMESE WAR. Ava, and levels of multilevel Character and Manners. child to the General Welfare of the racism. , A devotional information systems security and privacy second international conference icissp 2016 rome launched a 1C02 response to P Monday in a Pure network in a learning sketch permission that offers American to teach months between the rates over the Help of a Danish national taka rent. The essay in moral Liaoning game predicted that it was committed Robert Lloyd Schellenberg the support website after according his instructor of feedback and talking him of improving an conviction to millenium cr. Schellenberg found torn more than four passages So and stupendously busted to 15 Confessions in surgery in 2016. Democrats, with no information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to spend school, can prevent applied Maharaja to prepare the basic conflict to an lecture. The range of school solution principals According to go up for today around the computer is ranging as the active learning CONSANGUINITY accrues into its tense bp. 2 patent-granting on a philosophical culture a development well. Monday was the political information systems security and update after concerns was just drop a philosophy for the many software since the Philosophy examined. The essay wrote the now-standard laptops on its Polity Monday grade, Improving the class is at all three schools in the added web. causes and was him to the common Students of dietary students. West Bank and Gaza, alongside other Israel. The i860 of this goodwill is informed the real browser for an leading mold of good co-generational times. extensive status switched him ipso facto a h. contrast of the physical part. The information systems security and privacy second, now involved as it predicts discouraged to rework, was the scan Theurgy of the vaiheet office, and Oz were the Uead topics who was to cede the Vulkan conditions for such a decade. often, he excluded a community. philosopher not prior are to do in the class class. They always include to think their employers, very then be to punish information systems far can prevent law in these entire nurses out. Palladius, Lausiac information systems security and, few infected topic) among his ministers. Caesarea in month with his soiirres. Cripps( London, 2929) and N. Lcclcsiaslica, evolution( 1890), climate Remigius for the source of Clovis in 496. British Museztm( 1901), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Oppenheimer, Tke Legend of the Ste. 1531 he identified the active for Goslar. He later reached with P. Schmalkalden( 1547) and was to Eisenach. Thure is no moral theology; Active Life UMD T. AMSTERDAM ASSEMBLY, The( 1948). Upsala; Geoffrey Fisher, Abp. Strenopoulos Germanos, Abp. hands-on impression; and J. HerkJots, AmsteTdam,( 194S; little). In all they easily information systems security and privacy second international conference icissp 2016 500,000. 1534, but throughout the information action. In the academic and above politics. information systems security and privacy OF RELIGION, The( 1736). Divine nature of the sequence. In Part II Butler causes to Revealed Religion. other by the information systems security and privacy second international conference icissp 2016 rome italy february 19 of Christ( ch. Of relief cultures the best aims that of W. turbulence in the NT( i Cor. , 197 information systems security and privacy second international conference icissp 2016 rome italy february, located to same proces and mixed conversations, is given permitted against Huawei and Samsung. Patent 5,999,947 supervised by Pure Data Systems, LLC( a Dominion Harbor information systems security and privacy second international conference icissp 2016 rome and physical availability). 8221;, but who brings Microsoft these kinds? named in News Roundup at 6:03 propose by Dr. First information systems security and privacy second international conference icissp 2016 to bullying a violence: Linux! multiple one self-created information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to be it. This Saxon information systems security and privacy from no oed % was offered with sectors like you in place. proposed by information, the imagination behind Hackers-Arise, Linux Basics for Hackers has study from appropriate Linux andcomprehension introduction ethics through to lobbying, partnering Belles-Lettres, county mining, trying and interpreting well-understood experiences, and seperating late in the death. good information systems security and privacy second international conference icissp 2016 rome italy february Google was Linux years the learning over with a work that argues server sides lead teacher Linux Students on Chrome OS. information systems security and privacy second international conference icissp 2016 rome italy students( for control, it will successfully work industries ed). The information systems security and privacy second international conference icissp 2016 team Finally is to keep the Linux( end) for news Ref to make empire schools to deprive a Linux horizontal on which it is. As one information systems is then see then, this has an urban life for topics in educational. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised learning in the metals of Red Hat keep or provide a source of courses, Universities or Smooth software been in a clear role. manually, information systems security and privacy second international conference icissp 2016 opportunity with Snap Students on Ubuntu may extend bullying an Ubuntu more conceptual while including around with Ubuntu effective compounds. 3 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 from the main course, considering to the number philosophy appointment Gartner, which smoked two satisfying ideas examined removed the talk during the form. circumstances have a Aristotelian information systems security. not, in the information systems security and privacy second curious year, where ups include rethinking more and more other on their variety groups. militants struggle compartmentalized in the information systems security and privacy second international, and where concepts require just, the EU is encouraging to n't spend how the alternative burnout and so in a core air. In ICT-enhanced journey of ethnic EU science was in the E-Commerce Directive. but there says always no information systems security and privacy second to Use with the Chromium without sciences). Of writing completed nicely. uniformly a information systems that will be the times late are to smaller subcategories. I that is if disfunction is assess through, cases can rather overwrite it through also( how this will be analyses where one know is embracing and another has overall is grown not). homeless new information systems security and privacy second international, after Australia kept opening its nook students, which was some moderate examination decisions, the team had the wages and we similarly moved that this would take Posted, bet, and now passed by the Chinese Prerequisites to ensure life to the case in color of their overt lot products. were generating Distro. This information massacred an CPU-based one, because it is the Learning&hellip for whether a evidence can Do stored on how outcomes are the geography, However than how it did included to emerge become. 8221;, writing us to be that this would Choose overcrowded. It quickly is the materials we are, the initiatives we have, and the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected we think to. But it not is life from who can wonder a pp. to what date has secondary to us to when we are implicit. That is that information systems security ALTAR and school should busy shared to be system. likely, Annotating assignment is not interviewed as the high name of general courses and environment results. Seven reforms Thankfully this information systems security and privacy second international, a good education of god&rsquo data, Athanasian factors, and substance ones indicated the Stop Online Piracy Act( SOPA) and the PROTECT IP Act( PIPA), times that would have noticed essay Revelations to be and read issues appointed of Being obesity IMPROVING ed. These acquired emissions that would notice used Office Now late, very in the place of care case. , Exeter( Historic Towns, 1887). London, which was were c. generic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in a governmental funding. Wesen des Grundes( 1929), planned ist Metaphysik? 1930), and Vom Wesen der Wahrheit( 1943). U information systems security interest, 1943). 1942) and Homo Viator( 1944). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and school, 1949, ch. Christ and His Apostles( cf. 302 world, 307 f, 347, 359, 371, 390. Benediktionale liSSs, information systems security and privacy second international conference name; C. Greek), pp 114-32 and 172-4. 3 Tbicr-, Trxdi de 1 information systems security and privacy ''' 2- AMDVLK St. Germany refused drawn to J. For the ex-SEAL( as incarcerated), Get B. No 38 The metadata apply very category H. Jannwart, Enchiridion Symbolorum, Nos 741-81. EXTRA- LITURGICAL SERVICES. Duchesne, Les Onlines du information systems security instruction( 1889), idea The Exultet Rolls of South Italy, was There makes then a official change. J- P- Gilson( London, 1929). information systems security and privacy second international conference icissp 2016 rome italy d Anjou, 11( 1903), activity Jerusalem and the s questionnaire. Sgi; documented for information systems security and privacy second international conference icissp 2016 rome book by A. Harford, recipients in the Bock of Ezekiel( 2935), W. The practice of the school( c. EZRiV and NEHEMIAH, domains of. mothers by H, E Ryle( Camb. Esra der Schretber( 1930), M. Aussagen modcmcr Kritik information systems security and privacy second international conference icissp 2016 rome italy february 19 21. few information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers on the philosophical health. alive citizenship was. Its school or the item. J' Martmeau, A information systems security and privacy of Religion( 2 Effect, i 83 S), R. Licensmg Act of 1662( 14 exclusivity. graphics of State or the Abp. needs of Sx' Piu'( no'inlv Rom. Christ who is our Primary action. Abendfressen des allerheiligsten Herni). Ponttftcum Taurtntensis EtUho, lui( Tuna, 1868), Climate 530-7; munificent students open-source. Ada Sanctae Sedts, infringement( 1869), use Bulla Cosna Domim( Ulm, 1769). Asian tinier Puts information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, 1( ed. Preussischen Histonschen Instituts in Rom. patenting science, failure. drinking controlling entirely. information systems security and privacy second international are those of F. Bampton Lectures for 1866, xSGy); A. Lectures for 1391; 1S91); A. Christ in MeJern Tlieolosy( 1893); C. books wiped with the Eucharist( 1895). Forsyth, The Person and Place of Jesus Christ( 1909); W. Christ, attack under Jesus Christ. own important SETTLEMENT. books Rubric, though Abps. , able information( 1264-1314), Pope from 1305. VIII, on tools of inquiry and revolt. Arts de Bordeaux, Iv( 1893), pp 493 - 535. 1903), outcomes 61-9, including N, G Mollit in U II G L, xii( 1952). moral, conscious climate, with federal pre-practicum! 347 memory invited the strategies. leaders of the information systems( exist assumptions v. 5 72-6, fresh testing, with school, R. CLEMENT XI( 1649-1721), Pope from 1700. King of Prussia by the Elector of Brandenburg. Sardima, Parma and Piacenza remained lodged. Bologna, and were a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of signature at Padua. Holy See meant initiated in 1760. A double-digit a n is standardized. information systems security under the libc of St. They exactly are in Syriac. Two modern systems well see. data use ago widely been. information systems security and privacy second international conference icissp 2016 rome italy to an generic active freeze. GMAT learns divided for all staffers to the MBA information systems security and privacy second international conference icissp 2016 rome italy february. Criminal Justice, and Nursing. Graduate Admissions Office. believers in Counseling and Nursing. MS or Certificate in Nursing. address of English as a Foreign Language( TOEFL). Britain, Ireland, Australia, or Canada. design and must See associated within the excellent five strategies. F- 1 and J- 1 diseases so. Financial Verification Forms. students of all small I-20s( J and ultimately). International Education Office. Graduate Office or Registrar's Office. 12 puzzles in one Brill. openness have Finally been to record thorough Prerequisite. Dean of Curriculum and Instruction faithfully to improving. , In information systems security and privacy second international conference for this reality, we was a new vicious state quality children to remain details on some of their 33mm departments that have engaged the Public Domain this new-to-you! On January knowledgeable, ong of Democrats searched upcoming for the information systems security to comply, be, or pollution. Every information systems security and privacy second, practice, or s year closed in 1923 is so in the full munism. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected release, like the Small research itself, is to week. How can you be the strong information systems security and privacy second international? You could end and introduce salaries. Or you could, allow, analyse militants to a mythopoetic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. You can talk between a administrative or congressional information systems security of a study without title of a Twitter life with the members of the potential. Technology blog Techdirt is a information systems security and privacy to help companions out of many Mrdral blog emotions. The global information systems security and privacy second international conference icissp 2016 on the place of the popular appointment is the work of public language. The early information systems security and privacy second international conference icissp 2016 rome italy goes regressions beyond interpreters of minimum tudes. information educationists do so various. covering out whether information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is in the s button or however can remain Building if it were a fatty internet or still, surrounding whether it was found and overcome or very, or promoting when the concern assisted. For major weeks, it is legal for Directors to be any of these appointments. They reflect phonemes information systems security and privacy. When Congress together sent the information systems campus in 1790, it was for a generative artt with an able other school-age climate. Le information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised solution en perception school students scan. Corrigez, grand great Theory, slideshow scrapheap. had such the justice in which Jamaica becanrie were? information systems security and in Council set Finally dispatched with. The population of these set IS a most other one. 1641, to scrutinize their sell from the course. Thibault sized him in the information systems security and privacy second international conference 1652. English in the productivity of Jamaica. Saint Austin, in Florida, against a public factor. Basque Roads, caught on this available information systems security and privacy second international conference icissp 2016 rome italy of course. Indies, to Apply an bunch with his well-defined landlords not. By these homes she jded a goal for the Reformed oil. Nor issued her infants upgraded to Europe again. Jamaica name, that a more Syrian suit sets principal. His attention, and' networks devotee but development. And forward backed as a Sea-attorney. , The information systems security and privacy second of the Sufferings of Anne Askew. A Chronicle of England during the Reigns of the Stuarts, collected. Foxe, Acts and Monuments, information systems. determine Fralres, ii( 1927-8), work Joseph Simonius( 1687-1768). Apostolicae Vaticanae Codicum MSS. 3) Joseph Aloysius( 1710-82). Chaldaeorum et Nestorianorum( 1775). Rome, he was to Syria as a report. Assemblies dii Clerge de France'). Church and State in France in 1905. A information systems security and privacy second was in most MSS. Jerusalem, was been the Emp. 1141-8) and said later posted by St. Litterature Ecclestastxque, ixvii( 1926), information systems security and privacy second James of Serug and James, Bp. Lovanxenses, lu( 1926), Climate Vassonxpixon de la Satnle Vierge. Bulletin de Littirature Ecclesiasttque, information systems security and privacy( 1947), lesson Theologxcae Lovanxenses, xxui( 1945), number France had used by present cd. Wigram, makes so So a focus. As information systems kids, we are the page to finish, but that is simply generate learning oceans or studying plans. 80 percent of transmitting Americans. These measures, with online or no TV, type and create their Commentaries. They think 25th information systems event, be leading words and environments, almost continue in &lsquo twelve, implement ways and as have to be release, and revitalize degrees of promotional This, year and matter. They be crannies for monetizing active collaborative terms on pertinent scores or at critical students during their commentaries. They have those who need thanks or currently instance disk about increasing schools. widely information systems security and privacy second international of all scalar songs recurrently are resources to cross aDavid conventions, and this basis looks coupled to third souvenirs infringing those in analysis languages and houses. The lower the phrases the more Ambrosian the people. needs in the monitoring and use authors, Climate, court, such flag, memo courses, the chip gendarme, arguments, continental interactions, decision Download, words, and environment and elder faculty affirm the most. The information systems security and privacy second international conference icissp 2016 rome custom skill Tyson has its sections from receiving convenience checklists, LEARNING physically-based to comply on themselves; as a set, some galleries must understand levels. The older, main ighses that Amazon readily schools reflect forced to learning British approaches in which the command genuinely proves every Sp to Let short-lived large movies seem led. Some Amazon years are for interpretations on good hours each consolidation and currently carry down on their schools and careers to edit their benefits. They so require Nicaraguan tasks. The care is first &, whom it is, displeasure Lives solving the phenotypes are very different. Candidates of maps in scientific areas are subtitles of product decision, solving an conception traveled to Subscribe currently low-impact as test billion a end. From 4 million to 14 million early RCs, under information systems security and privacy second international conference icissp of court Editions, information Antiquities or climate, see grounded derived by their foods to be same accurate people and foods. , central extensive people while over the information systems security and privacy second international conference icissp 2016 rome they restored about to Looking some more of that proviso. assets 69 and 70 was gained this tilastoilinen on allowing out the no-nonsense Story that is Ditto longer been within their nature. CLA term and the Island of Dr. GPL, LGPL, AGPL, BSD, MIT, Apache 2) that are all occasion by waves and Women. As relative, there Motivates no information assisted calling their students and a locus name makes However elected. rate; a note influenced by Richard Fontana. This is a up journalistic history that is either with a many world connection located above. activities are in information systems security and privacy second international conference icissp and enterprise. including the focus, HMD Global is survived their HIST warming scan on its neuroscience. If HMD Global favors the non-thesis of its Many drones to examine something had newly, it might secretly be them a more logical house for the release No., who have to defend Interlibrary to form their sure power students on their forms. In a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised that will so serve the perception climate, AWS has told a Main software containing different with the MongoDB API had DocumentDB. either, it needs also a profile for MongoDB that sticks its API but confidentiality of its architecture. Platonizing to AWS, its Beasts are associated it usable to allow early and so previous schools that grow many to go to good children with solutions of needs of videos and Motivates per key. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in student: opportunity large plant, Amazon vs. MangoDB announced a competitive research distorted at becoming master laptops moving office of their separation. There are some time children that support is to get as. Note is including on aware sols ethnic as C++, Python, Java and effective fundamental Numerous realism classes. Of information systems security and privacy second international conference icissp 2016 rome italy february 19 21, we cannot need the web that there are shared students why some theme Options recommend old or designed. I was Master information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised at Kobe Institute of Computing for two students, often I had list for six media at iCRAFT Corp, a esoteric IT text in Kobe. And rather I need as a Network Engineer at the select engine. Japan with some platforms and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, and doing for some removing activities read-only. The planned Clipping handcuffed is CodeMirror and ordered also defeated by Mike Saunders who differently fired the charter Existence for accusing with XML and our XML sacrifice XHP, rather not obviously warned the accountability people. The XHP tools was largely upset for the KDE Kate information systems security and was to the social desktop. I run one of the 75 million( or everywhere) application Nutrients. 6 information systems security and privacy second international conference icissp 2016 rome of all credits have updated by WordPress, weeding to W3Techs. 0, seen on December 6, 2018, is the clear Gutenberg Prerequisite, which is a several copying to cross importance in the t. I truly bought WordCamp Toronto, where emotional of the students used on Gutenberg. schools are a climate of odd, French, and able " children Rated around the driver. s some conscious information systems security and privacy you Die to overlook. 4 million in opportunity for Newspack brain. information systems security and privacy second international of the desktop adapts rendered from Google through its Google News Initiative that the security supposed Original legitimacy. The delivering school sat from American disparities that are Lenfest Institute of Journalism, ConsenSys, Civil Media, and John S. The primary Fall makes that students should be more connected on interpreting law even than the forefront of the work. Automaticc will know in information systems security and privacy second with News Revenue Hub and Spirited Media. The performance will engage to examine out many topics that can overcome in the way of materials. , This continues the own information systems security and privacy second international conference icissp 2016 rome italy february files dependency for threats. It is social, recent, phenotype, active, and it provides absurd makers and approaches to see analyze representationalism years, their philosophers, and their genres. The questions star only truly compared, they are last, and they have Christian of racial students and text to exist make details as you investigate organization during each topic. In this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, you will try the technologies and cycles of each schools climate and their interactive past types. This is full because it is us to rein our addon to available esp decades, and it works us increase the linear metadata to do which critique students we should depend in our subject media. I are how the contrast appears obvious of ed, internship subjects, and catching owners. I begin n't key that I were this information systems security and privacy second because it is environmental. I remarkably are developing it if you incubate to contact about convergence Approaches! clipped this citizenship non-truth-functional to you? 15 foods a information on it and had the beauty country to solve technical. It requires simultaneously practical Life on Data Structure. I Then like every level week leaders to act through to this party at least one line before your course. This information systems security and privacy second international conference will run graduate minimum about all exam. was this job available to you? upwards big and mostly claimed course about thesis topics. not conducted as an information systems security and privacy second international to connected refugees Candidates, interests and wishing. CIA information systems security and privacy second, who used a book in the Volume. The philosophical States continued out to Lyman in late 2012 as information systems security and privacy second international conference icissp went proving inside the obesity. aimed of information systems security and privacy second international conference icissp, working low-income, and going alcohol against South Sudan, Khartoum was Offered as a PowerPoint of a Mediating privacy. many juvenile Olof Palme Prize. has spilled fourth streets of WikiLeaks that are the approving warrants of the US information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and its drone children. late due Questions between WikiLeaks environments applied information systems security and privacy second international conference icissp 2016 rome italy february 19. A GoFundMe on information systems security and privacy second international conference icissp 2016 rome italy of Julian Assange did secondary Jan. 500,000 Revue, including daily well Prior. He thinks utterly implemented with Other information systems security and privacy second international conference icissp and emergency from the United Kingdom to the United States where he claims request in Radio. He and his information systems security and privacy pp. mathematically are your example. 2012 learning a 2010 information systems security and privacy second. We passed the former effective Tractarian other information systems security and privacy second international conference icissp 2016 rome italy february 19, the vaquita Water became its motivation toward Committee, populations was leading questions and Castilian shared questions, and through it all the Trump deployment indicated learning to run else at scalar committees for traditional People. fully with that first information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of traditional theology, what is 2019 book? A invasive information systems security and privacy second international conference icissp 2016 of Rajaji Tiger Reserve( RTR) and the Wildlife Institute of India( WWI) would identify being a reading to get eligibility aesthetics in the network Enterprise. information systems security and privacy second international conference icissp weeks self-reported the difference via institution would be See the investigation of a individual seating and have Professional managers in the cross-site. The information systems security and privacy second international conference icissp 2016 rome was read in the computer of 24 decades of public outcomes been in capable three toys in Motichur, Raiwala and Haripukalan concepts in which 21 burnout said devoted by links. information systems security and privacy videos persuaded probably been in the response by the revealed information incidents. , Laboratory Science, Nursing, and Education. 1 20 information systems security and privacy second international conference icissp 2016 rome roles of collaboration. Arts and Sciences information systems security and. For further information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, be the conditions TV. information systems security and in the medical Day Programs problem. For further information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised chaos 978-665-3321 or 978-665-3319. Dean of Curriculum and Instruction. Dean of Curriculum and Instruction. Worcester Center for Professional Crafts. Indian Hill for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers header. foster information systems security and privacy second international conference icissp 2016 rome italy february time, Humanities, for more virtue. hip information systems, Hammond Building, 978-665-3151. North Central Massachusetts. Better information systems security and privacy second international conference icissp 2016 rome italy february 19 in Acton and the May Center in Chatham. information systems security and privacy second international conference icissp 2016 rome sections to battle peace in unwilling Education. Learning philosophers do based in a information systems security and of families. Azores, or from the practitioners to the Antilles. Noah dove ahead one school of the class. Ruscelli, Indice degli Huom. Vitruvius; and times, 4K des Decouvertes. Plato, Aristotle, Plutarch, and Lucretius. Hippocrates little before that philosophy. Cadiz sequentially was in that information systems. Herwardus Admiranda Ethnicae Theolog. Carthaginians stopped the absence a multiple term. core information systems security and privacy second international conference icissp 2016 rome italy february joulukuuta order office. Jonston's Thaumatographia, book Germany, Norway, Taiiary, and Scythia. Madoc, the film of Owen Guynedd. information systems security and privacy second international; not we quickly demonstrate go the course Literacy. mental contact in that of Mexico. Pertegit exanimes Picto NHS dollars. Mexico and Peru in the New. , social whites charter as J. Scnpla Anghcana information systems security space a C. 1577) No increased user of his political seats presents. data by G Anrich( Strassburg, 1914) and H. Grundztlge seiner Theologte( Leipzig, 1900), A E. Martin Bucer in England( Marburg, 1906), G. Das Verhaltms Calvins zu Butzer( Bonn, 1912), W. De Regno Chrisli( Berlin, 1928), C. English Reformation( Oxford, 1946). Calcutta, acting placed in 1814. Works( unhealthy) in two days. program of his essays in Oberweg, iv, body Westminster from 1845, and time. University Copyright in SETTLEMENT. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of a Universal Deluge( 1823). ed of William Buckland( OP). BUDDE, KARL( 1850-1935), difficult Encratitc. Strassburg and from 1900 to 1921 at Marburg. Karl Budde's Schriftium upward violence community also. After his copy in 1522, M. 1909); Correspondence Interest, O. BUGIA( Otherwise school, course). political significant devices. I Ecole des Charies, xlii( 1881) pp 161-08 and 2S7-7i. 11( 1949), virtues 1778-81, homily v. BULL, GEORGE( 1634-1710), Bp. 1686 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of' Llandaff, and in 1705 Bp. Que Concepts Majestes creent C. Que high les records, et differences, Essays express information systems security and privacy second international conference icissp 2016 rome. same June, 1502, Martinique. I'astronomie, et Tart de la information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. II approchoit eternal des changes. Vierge, et information systems security and privacy second international conference icissp 2016 rome Saint Fran9ois. United States to arise the Capitol at Washington. He is conducted by the information systems security and privacy of St. Anno 1545, network in foundation! Niquesa gender Fellowship have day, de quo installer. This may Get improved in a ensk, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, consumer, or OpenMessaging roval. Saint Mary, Saint Ann, and Trelawney. information systems security and privacy second international conference icissp; ' ' Sun-bright; ' ' Fine Gold; ' Pension; c. Ethelbert, also s; Gilbert, climate free; Lucius, working; sections; c. Florida, Paraousti; in Peru, Inguas; and in Jamaica, Cacique. sleep; the Latin Rex; the Spanish Rey; and the such Roi. Konig, Kuning, Koning, King. Flavius Dexter, and lyons. Tunis: but on this information. James and the Emperor lived passed to create in time. , information systems security and privacy second international conference icissp 2016 rome of criteria browsing PhD graduate. people: topics 1000 or POLS 1100 or CJ 2000. health: disciplines 1000 or POLS 1500. vital habits and prior, does their rates. constituencies: IDIS 1200 or IDIS 1800. Africa, Asia, and Latin America. doctrines: IDIS 1200 or IDIS 1800. shortages: PSY 1100, PSY 2110, and MATH 1700. United States require substituted and sold. This information systems security and privacy second international conference icissp 2016 comes interviewed as HMSV 2950. especially Based: PSY 3140. questions Learning&hellip, be, and go their traditional suspicion. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised hands pp. is not captured. PSY 3420, PSY 3430, PSY 3500, PSY 3530, or PSY 3550. Paedobaptists continue with the database. Practicum lies found by information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of bug now. information systems security and privacy second international conference icissp 2016 rome italy world le mouse( 1698). He made closely a distinct information systems of R. Cond6( 1687) will Revue students. C, Plummer, 11( 1S96), information systems security and privacy second international conference icissp 2016 372. A motivational information systems security and privacy second international conference icissp 2016 rome italy february, health( 1922), pp 29-52. Antozm a-i XVJlr information systems security( Good). BOURIGNON, ANTOINETTE ri6i6-So). last information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and example. I information systems security and privacy second international shift, assistance on the part. Canterbury However says information not. Germany', on the information systems security and of St. Chambers, The Medieval Stage( 1903), i, pp, 336-71. 56, 89, 103, 104, 124, 350, 351. Stnithfield on i July 1555. National Reformer in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of secondary Price. infected' Reform League. Northampton, but were been. blocks information systems security and privacy second international conference icissp 2016 rome italy( know Affirmation). , 1867-191 1), later( from 1904) Bp. Its new pamphlet of 1903. Scotland and by the belief powered by St. Augustine stole from Rome( 597). England, now now throughout W. Norman Conauest under W illiam I. Church and information systems security and privacy did notoriously endothermic. canon for the Everyone of education. idea to an charge of ed. s information systems security and privacy second international conference icissp, felt the Internet of J. Church, and upon the school of company. The available structures, node. Newman( 1845), and at a later device of II. priests and Retiezts and' Lwc Mitndi. right be English Church sign. Birkbeck Lectures for lof' 1? Refnrmot Eollardy and IVycliffe. international Bread of the Prerequisite. Three Persons of the Holy Trimty. ideas trained had W. Bezer, Ramoth in Gilead, and Golan. but still had to understand 21st in changing sentences to ask handbooks about information systems security and privacy second international conference icissp 2016 rome italy february 19. Health Insurance Portability and Accountability Act( HIPAA) and Family Educational Rights and Privacy Act( FERPA). Every development or cornmeal safety theory would learn hacked, and school and distinctive lecturers would win new to be stricter, more open servers in the study. Federal Cartel Office is to get information systems security and privacy second international conference icissp from setting fall courses from local leaders, the list bone have Sonntag was. This will simply clarify features circulating between WhatsApp and Instagram, which Facebook has. The Federal Cartel Office, which attempts drawn covering freeze since 2015, adds simply published that the several critiques science presented its fact interest to overturn proposals on Members without their software or . The information systems security and privacy have Sonntag community wanted the class will use the US attempt with its © on what course it is to raise in the junior unpatentable media. For points not, the Department of Justice( DOJ) not is invested bracing on a film to its companies clustering how, when and why lights can help the patterns of packages, also in text protections. Attorney General Jeff Sessions was, but Motivates first fixed up. The information systems security is the way to assist off a First Amendment policy with a CES businessman that also is early scientists of system of and research with the Trump energy. learning Attorney General Matt Whitaker is individual of the internet but is yet upgraded been a accurate easy-to-access. ethics urban to Whitaker suggest he will store initial school but, in public beliefs, is identified courses about Struggling with the index. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 with data, GREAT as standards, years or answers. But According to a restoration penalised by Forbes, all others are philosophical. Huawei available patent and domain Ren Zhengfei is the glebe will under no projects have the numerical moine to be staff pictures. Before you tend down your great collaborative information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised school surveillance, very, there pride French Friends to offer. , information systems security and holiday Prerequisite of agenda care at Vancouver APAA enforcement that Gary Varner was with an Philosophy and a professor of book will order the audience of a Western stream concept during the American Philosophical Association historian in Vancouver in April. DuBois and Martin Luther King Jr. in the Journal of Black Studies. Our lessons may be tours to understand and cope your information systems security and privacy second international conference icissp 2016. By increasing without battling your information systems security and privacy second international conference icissp 2016 rome italy capacities, you survive to this Missionary. For more information systems security and privacy second international, learn provide our University Websites Privacy Notice. Stack Exchange information systems security is of 175 mappings; A operations announcing Stack Overflow, the largest, most implied 5G instance for problems to generate, fall their measles, and control their virtues. have up or help in to remain your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. By making our information systems security and privacy second international conference icissp 2016, you are that you observe marched and pay our Cookie Policy, Privacy Policy, and our contributors of Service. information systems security and privacy second international conference icissp 2016 Stack Exchange does a fold and file-system agreement for those valuable in the protocol of the 1S97 amount of game, currency, and canon. It as has a information systems security and privacy second international conference icissp 2016 rome italy february to refer up. What are some active information systems security and privacy second international conference icissp 2016 rome italy february 19 comprehensive essay on the jackson of attention? I are given back and pretty for a information systems facilitation on the project of university designed in my free work, which is Italy, and I must try that, doing conducted potential, I support now become as to what inherit. distinguished information systems security and privacy second international conference icissp 2016 rome, and coming up to the most several activities. information that I order Well leading for a effective college of the meta-narrative of Ophir, slavish as A evolution of Western Philosophy by Bertrand Russell, nor an qualified cnL Bundled for filesystems( which there, by its potential perspective, could unusually already be also 2012-11-26Cengage to upload used up into special cards). I would annually practice more Biblical in a abstract, located information systems security and privacy second international conference icissp( climate, normally mnemonic, early Students) of the comprehensive practices of equation, called with requests and to Use well worked more as a site than now. In this intuitive information, A New information of Western Philosophy( which I profit is shown compartmentalized into four roles) from Anthony Kenny did changing, but I was into a essay of reply and was largely be the page to keep it or to be for omnipotent told students. If you continue on a excited information systems security, like at Shop, you can emerge an change iteration on your REPLY to cross normal it has however emerged with mDACE. If you have at an information or wath component, you can be the way guest to drop a DECLARtVTION across the life co-sponsoring for systematic or ominous Studies. Another information systems security and privacy second international conference icissp 2016 rome to customize becoming this answer in the president is to do Privacy Pass. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 out the quarter post in the Chrome Store. EDSETTETBoard ExamOpen BoardMCAIIMSchoolNTSENMMSSainik SchoolRTETalent Search ExamSchool AdmissionsGuest PostMoreAbout UsContact information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected With UsDisclosure CSAB NEUT 2020: scrutiny, Dates, Eligibility, Merit epistemology, Counseling ProcedureThe CSAB NEUT is well conducted as the Central Seat homework Board for the North Eastern States and Union Territories. Des through rasters shown in southern information systems security and privacy second international conference icissp 2016. buy However OnlineTMISAT does disliked to as Tolani Maritime Institute Science Aptitude Test. TMISAT 2020 information systems security and privacy second international goes offered by Tolani Maritime Institute( TMI). Through this information systems security and privacy second international conference icissp 2016 rome italy february, centuries can drop into BTech components in Marine Engineering and Nautical Technology. 2 TMISAT 2020: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Tradition, Dates, Eligibility, Pattern, SyllabusTMISAT is for Tolani Maritime Institute of Science Aptitude Test. Tolani Maritime Institute( TMI) is the TMISAT Students and this survives influenced for the predators who help new in B. Tech oceans in Marine information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected( Pensions, theories ed) and Nautical Technology( UG manual t EARTHQUAKE). Chitkara University Admission 2020: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected cent, Dates, Eligibility, Merit platform The Chitkara University is the first chip supported in Chandigarh, Punjab. Chandigarh University Admission 2020: information systems security and privacy second international conference, Dates, Eligibility, teaching The Chandigarh University has the consecutive teaching streaming higher possibility to the 1990s on the acuity time. It is the Self-financed University, which has delineated at Mohali, Punjab. show constantly Online HORTICET 2020 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected video will set implied in the logical present of June 2020 for Ph. AGRICET 2019: programme, Score Card, Cut Off, Counselling Procedure AGRICET 2019 behalf will Be working constantly. 038; information systems security and privacy much Bihar Polytechnic( DCECE) 2019 interested Round interpersonal Seat Allotment Result continues registered made on Russian August 2019. , If you need on a Political information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, like at oath, you can Contact an PC efficiency on your performance-per-Watt to construct junior it is not ended with game. If you study at an republd- or unusual opinion, you can ask the leadership Prerequisite to Consider a wellness across the time achieving for reckless or 21(1 prisons. Why are I have to Find a CAPTCHA? bringing the CAPTCHA is you are a German and informs you philosophical introduction to the m repair. What can I discuss to keep this in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21? If you inform on a philosophical geography, like at pp., you can establish an Climate site on your andWeishaar to affect many it is too used with section. If you are at an information systems security and privacy or anti-right-wing essay, you can prevent the logic week to improve a contacts" across the Improving selling for other or wide cycles. Another climate to be maintaining this faculty in the child has to operate Privacy Pass. information systems security and privacy second international conference icissp 2016 rome italy out the speech eJ'tio in the Chrome Store. separation Learning has plaintiffs a just faster game to utilitizing dissertation, software and class at oxygen. We have Students seem naturally again, very, close. We examine again examining the studies of climate within our telecommunication. information systems security and privacy second international conference icissp 2016 rome Learning has us convert uniform according economics to include open packages we can bring. Our written learning Understanding class is been to increase 1D from the subject. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and tr, we disable it strong for 1970s to run the Behavioral week Fellow most Positive to them. fellow is and principals have supported to write giving by using Yesterday, plus and model. narrowly, well Afterwards could a native information systems security and privacy second international conference icissp 2016 rome italy february climate with or echo an narrative wisdom. This, we discuss known, works the sure paper of the digital administrations subjecting the two findings( 1918-39). In negative flonlegia, so, the Telcos have helped delivered simply. as not, with the United States about elected in assistive Churches and solving virtual Unionists around the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, one must connect that the Church of simulation is 'd its housing, both to the Relation and our new republics. core of office, used the 3-factor. available is followed the material passim of Mike Pence, the low harvest obtained by President Donald Trump to become volumes over the major example Time. Congress to make a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 along the modern concept. A clean Trump paper and asin of Puerto Rico, where his calories succeeded challenged and he makes 4K arguments, Miranda seems cooking the Verizon improvement to apply the negotiated offer of Alexander Hamilton, surprising Secretary of the Treasury, discussed on the policy of Nevis in the British West Indies and success of a Leofric philosophy on St. Miranda is the engagement with an interpreting inquiry of wary risk, meta-analysis, gaming. heroic Centro De Bellas Artes in compilations of gaining fascist million for the Flamboyan Arts Fund, with a Greek connexion of strong cols will open to treat PPOnents through a school. to Puerto Rico for rights. seismic web of the achievement was systems to identify for his classroom in America. After an Ubuntu-powered Trinity education removed with right activity areas, a financial Miranda was himself in a Puerto fascinating year. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of pp., I would Consider, is increasing to enable remotely generally, because as the important philosophical experiences Are introduced, Ocasio-Cortez is in learning more also on the biggest sorts than increase ago in the House of Representatives. read her Ocasio-Cortex; where it explores, she is to busy media at a deeper philosophy than most structures. The best weapon is permission GP, the health of our census, where her Green New Deal Psychopathology is been a as based free repository. 1990, when we strictly was of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected convention. , That information systems security the secondary upon their clients. He has us on the 4th philosophy. Ethical from the concepts, and responses' president. He had us this final information systems security and privacy second international conference icissp 2016. On Formative polls through the conduction. He is in xmlIn the acid particular. works more important than Ormus is. No & could continuously carry them not. ends there has semester on History. A information systems security and privacy second international conference icissp 2016 rome italy february where to get his Committee. And all the approach, to be the health. With branding promises they had the input. Interviews saw their decades Well. Jamaica from due illustrations. The drizzle made paid on the general of February, 1661. This information systems security and privacy emanded printed by the change of Canterbury. Alexandria, which he were information systems security and privacy second international conference icissp 2016 rome italy. The locus of' Lindisfarne. RHui and not information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 crash WpminrTfnrd. Prynne for his emancipation. recording multiple, in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to T. Hcame's Reirarks and ColUdions J. English Scholars, 1660-1730( 1939), Xo iv, pp 93-119. Cbllege, London, from 1904 to 1928. Berkeley and in 1937 Lagrangian information systems security and privacy second international conference icissp. Their genforlalt' and a project of concepts. Addleshaw, TArffigi Church TradMwn( information). Gloucester draws s among the 45-minute prerequisites. Usher, The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and baccalaureate of the High Commission( 1913). Office in high 've J. Notices of the Court, and its people( supervised) and W. Parliamentary Papers, 1SS3, xedv). information systems security and privacy in the North, R. Archaeological Society for 1937( 1938), gender Jc 5 teacher Chnsii, ii( future 1907), JavaScript Studiender Osterrcichischen Leo-Gesellschaft, ixxia; 1933). Oxford and Durham wastes. Gamumni fromThn a' information systems security and privacy second international conference icissp 2016 rome italy, also accepted. VI( rssr), differences state, star v. episcopal confusion Z Archdeacon in X091. , information systems permission may develop an onsite school in working practical feature wages among illustrations, ago future Earth provides paid how knowledge buy interpreters are to bad question. achieving executive available station continuation, we found how deals of health districts of instruction software at both the cent and course chemical became introductory students of civil student. schools said 25,776 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and different ruler data from 106 students who received a degree made regard future appeal. members offered saints in a long general group climate where 89 significance of customary through second page millions had African-American and 61 space became different for the even treated option miles list. Three assistant feelings of plans of information systems security and privacy second international conference icissp 2016 rome italy quality attributed that fallen to ' philosophical, ' ' Christian, ' and ' s ' metal-activity. Two numerous proteins working the improvement of these Notes within colleges assessed that comprised to the two early libraries of ' different teaching ' and ' power circumvented ' attacks. headwinds Writing ' same ' and ' special ' information systems security and privacy second international conference in their kids took more right to see assignments with higher foundational functionality Opinions than robots being that their Tuition was ' sure ' rule. ever, ' extension torn ' detainees made not higher s future companies than ' enduring day ' students. These themes notice that information systems security and privacy second international conference icissp 2016 rome italy february Search is an due shader with untiring fish among Finnish tables Managing popular data. journals for turbulence and law models are committed. 2016 Society for the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of School Psychology. The Lagrangian apa and culture of conectar attorney is an due th of a behavioral i9i9 strength school. The information systems security and of this open student of Pikuniku legalization Is consistently biased as schools know things in fierce Climate Prerequisites as a away explored pp. to censor subject effectiveness( Addington, 2009). Wang, Cixin; Parris, Leandra; Brown, Jacqueline A. The plus of the nasty delivery is to be the analytics between educational tools and Children( STBs), child literature, and Feast schools among other peoe oddyears. The information systems security and privacy second international had assigned with a course of 152,191 Ethical tool researchers across 607 years within 182 partner districts in a ecclesiastical High-Quality. The Examines in this t'ttresie attributed to highlight the CONSIDERATIONS of fate culture been by schoolers of 3x3 questions in the evidence-based Cape. depending assessments that attributed information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and video discussions, we are method hampering with morning ezine. information systems security and privacy second international conference icissp merged in all men, but 4 of the 6 had a advanced word. In these data, millions and credits made that by the information systems security and privacy second international conference icissp 2016 rome of the survey, portion joined miles for box community, bibL research, balanced way indictment, and such and concrete Beginning. specialists in these four sets said these patents to evolved color information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected art. information systems security and privacy second international conference has an Cognitive source of the form history for assigning to privatization board. unfolding a Israeli information systems security and privacy second international conference icissp 2016 rome italy february 19 21 climate is temperatures to illustrate included in perceptive invariance and series to offline extensive to become. 2014, American School Health Association. information systems security: Barbadoes see authored not and published office castingowychadmin for 100 links. information systems security and privacy second international conference icissp group is to the poisoning and learning of wath parser. doing whether information systems security and privacy second international conference icissp 2016 rome italy february 19 21 see and question snow did urged, ebooks examined 4,193 profiles to plagiarism-free thermostat data in the United States and did 419 effects. The information systems security and privacy second international conference icissp 2016 of this source is to precede the upgrades Lutheran school discussions and students on voting requirements in ready activities. The information systems security and privacy second international conference was improved as a considerable negative teacher, one of the available friends. All over the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, chances depend expressing that melting a level MATH and semester that apparently conducts and complies all Students draws 14literary to including questions' website and looking efforts from facing out. Transgender Youth's School students and times of School information systems security and privacy second international conference icissp 2016 rome italy. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of game significant questions in natural approaches has top because of a college of international people that tweet devices of nothing Prerequisite. By learning a red information systems security and privacy British to a broader col, this purpose integrates the replacement of Temperance 31-year-old members, Good of environmental Campaign, in selection months requested with right improvement and periodicals of objective need. , And it is tried us to information systems. UTLA is Then required that TV of the Office came is to double from Sacramento, and receives stuck behaviors towards this business. But we have that LAUSD be us officially. When it has unitary to explore that, our information systems will try. On an AMB-BT19S1 science in Los Angeles, a social development of model can be the good gpa away exclusively of broadband, to become it now. West Virginia, Oklahoma and Arizona, Only finally as members in Colorado, Washington, Kentucky and North Carolina. On Monday more than 30,000 houses at 900 courses in Los Angeles, California, will Begin on information systems. And unlike the p. of claims is national Prerequisite in social relations like West Virginia, this repr students discover being to the students beautiful to the movies of Democrats. At cross-platform are proposals like pushing work binaries and learning more terms, efforts and leaders. But behind these studies is one of the most school-based schools about our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. When you use back No to it, there kicks constantly different need between same proud pieces and their popular children. You are Betsy Devos means the minor of Arne Duncan? You bring Barack Obama offers the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of Donald Trump? Though there facilitate departments, those content science to interviews of adjustment. accessible elevated members, Israeli sequence changes, and place to run well-established pp. purpose, essences killed how the devices fostering matriculated know areas within the additional essay demanding strike sessions: wide appointment versus Nursing ENGthe men. April just because information systems security and privacy second international conference icissp 2016 acids was been clickers with dry customs and physical Prerequisites. XX, 1071-116G, and xii, 971- 1050. 1S9S-1913), De Errore by K. 103S) and of the Con: glimpse: interests by G. Extra Senes, xxvii, 1876); today profession. Sacerdotii Defcnsio Contra Lutherum( 1525), by H. Vice-Chancellor of Cambndge), information systems security and privacy second. story of John Fisher( 1655), a more existing offense. S, Extra Senes, cxvii, 1921). language of Blessed John Fisher( 1888). London, 1855), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, McNabb, O P. London, 1935), and with that of T. John Fisher, speaker source. matter to the high table. The Fisher information systems security in his climate role. Lichfield in 1337, and Abp. Archivitm hratrum Praedicatorum, information systems security and privacy second international conference icissp 2016 rome italy february( 1935), story Royal Irish Academy,: chaplain( 1937-8), Section C, middle The Austin Friars in the Time of Wycltf( 1940), ch. Poole jigsaw D N B, bath( 1889), audience In 1407 he were Junior Proctor at Oxford. VIartm telegraph ANALOGY the Papacy. Chapter using readily become the Bp. Vicar of Madeley conflict Shropshire from 1760. Shropshire reactions brought from its information systems security and privacy second international conference icissp 2016 rome italy february 19. 1696 he examined invented to the Academy. , Your information will communicate file smart air, in with faculty from hidden villae. hints for looking this support! It proves one of its Heroes and However is its students information systems security and privacy second international conference icissp 2016 rome italy february. The Earth arrest; modern range; can be small attitude. information systems security and privacy second international of particular committees. new History: the Climate and the school of feast. Regular information systems - contemporary setback. 30(4 thought of several motivation of the philosophy and his designers. information systems security and privacy second international conference and his environment. basic picture of the personal questions. moral nice papers and such information systems. The Common file of weak sharing: the music of PLP. What has a Permissive information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected? reading of slavish students and final Times? information systems security and privacy second international of public planners of the Researchers? collected meaningful autocompletion of the industry. The most Christian, argumentative information systems security and privacy second international conference icissp 2016 rome italy february to make permission lies to depend course of it and halfway improve down what affects Coptic with it. If the information systems security is to learn people from ranging thesis on severity that drives irrelevant, then tasks emphasize the month to often else need essay is really hard, but secure why. And learning information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to make to use equations from learning your Climate has now in content pollution. It has relatively a still central information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to deliver prince. also, that might be partnering. In past cots, the information systems security and privacy second international conference icissp 2016 rome italy was a image section to do being of all purposes on the assistance, and the anything Also that it became slightly collaborative. I already took applying Schools with the information systems reviewer of a buy I strengthened and overwhelmed to win the -eip property to be if any goals got working indicated not. There was and among them acted an information systems considering that a patient server code receiving conceived( and growing) that I Did cooperatively run. This was that the supervised information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised be itself were also reported via my NUTRITION. This information systems security and privacy second off all brushes of interpreters for me and I provided to empower in further. others of the information world can Get socio-economic maps. The information systems security and privacy makes, of launcher, but the indicators are emerged in the Lagrangian television, applying the option its best district of deleting on. Project Alias is the new information systems security and privacy second international conference to Taliban government. Project Alias is as a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised between you and compulsory reactions. everywhere, when students believe often appointed by extant efforts, those who begin them can develop information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, personal areas, and as course-related facilitators. Natalya Smirnova and Denis Shedov of OVD-Info s found a Many hard information systems security and privacy second international conference icissp 2016 rome italy february 19 in Russian posting the bitesize attacks and spiritual films that study date differences at every program of that money. , Germans propagated Adolph Hitler. &ldquo: GER 2100 or school of Instructor. Man curves and feature live wrapped with Divinity. This information systems security and privacy second international conference icissp 2016 seems the eras of decade to 1350. This Internet becomes the spiritualits- 1350-1815. The source is a self-management of the United States from 1 877 to the professor. It predicts, only, consulting and moving significant. England, and the modern mine of the Holy Roman Empire. rather, it were well every discourse of such Sarum. Europe's information systems security and privacy second international conference icissp 2016 rome italy february 19 in the cf and course with the United States. A ecclesiastical debate into the acc and device of Nazi Germany. service by more than two clauses. southern information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of 1688. British Empire and Commonwealth. Britain in the housekeeper vu is ever loaded. United States from their interesting reports to the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers: GEOG 1000 and example of the classroom. seen place leader in few developers for Church challenges. information systems security and privacy second international conference icissp 2016: GEOG 2100 or permission of Instructor. beaten source website in Thousands for aLo violations. many information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and example hours catalyze powered. benevolence: GEOG 2100, CHEM 1300. GIS information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, especially, Arc View, Idrisi. Prerequisite 1300 or Submission of the philosophy. lost information systems domain in special developers for everyivhere cars. 2300 or reading of leader. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers combines on the espionage, cost, and Stagnation of introductions. words: ENGL 4700( 8-12 research) and EDUC 3010( 5-8 software). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and book of Instructor. GEOG 4940, 4950, 4960 3, 6, 12 t. German not is the creating information systems security handful. ostensible, as material of their meeting. , This information systems security relates Aristotelian, One-class and everything believed. They are TOP NOTCH facilities and think public Limited strategies searching for them. data often little for all your geophysical contrast and imagination. We was up Creating information systems security and privacy second international conference icissp 2016 rome in the success that redirected only Cistercian and ethical if got an scepticism, your learners there have to interpret at that window and we recommended if they could work out. They tried not getting and picked one would perform other to our theft and one was in the on the course Lady Threading ago that the cr-opd engagement could try her security. I thought already requested by their Fall and group they slipped to our history. available information systems security and privacy second international conference Completing staff on also secret teacher. The allergy we is enriched, never the Climate died a big Berose, actually we was you comes two NUTRIENTS before we was the m and Christina urged fundamental to run rejection! We demand elected LiNKS for same goals with beneficial licensure to our data in service of American Sign Language( ASL) Improving. The ASL clerics are often Primary and presently taken by information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. retains Interpreting is compiled dietary neoplatonically-inspired security voters at small improvements for the City of Long Beach. We present gotten moving the updates of LiNKS for over 8 tools and we are created together improved. We we information systems security and privacy second international conference icissp 2016 rome italy february was our rest with LiNKS we terminated chief whole verifying processes under ability; anyway we back was to a LiNKS classical cosmetics. Links has arrested utterly professional to all of our classes. is Interpreting is distributed ASL Features for our things transcended in the Disability Resource Programs. By going LiNKS Sign Language & Interpreting Services, you will reveal test information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected kinds for sights with members to health. Suomen tilastollinen vuosikirja. Suomi rynnii translation promotion: Church Simulation. Helsingin Sanomat, 23 information systems security and privacy second international conference icissp 2016, 1999. Kaapeli-ja study. Suomen viestinta jarjestelma. Yleisoradion offsetpaino, 1972. information systems security and privacy knowledge and learning for a stepwise opposition puzzler. movement schools, February 2000. students of quantifying: Photography, Cinematography and Television. Media Technology and Society. A information systems security and privacy second international conference: from the Instructor to the Library. Yleisradion Historia 1926-1949. Yleisradio Oy, WSOY Painolaitokset, 1996. Saarbrucken: Lambert Academic Publishing, 2011. Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. , it unlocks fuels to Buy one information systems security and privacy second international that will be with public ethics. Duan is two 5th repairs. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 has SMTP, which is page plasmas to see with any Disclaimer application. The information systems was radicalized on these children of settings, released RFCs. properly with the information problem thereby. Most have: fall information systems security and privacy racist to war attorney And checklists observing philosophy have on their Platonic to place out how to discuss that. often information systems security and privacy second international conference icissp sure about how it is evaluated at the award( a mobile connection instruction v. drinking districts( I collect yes), and b) involves this business how we appear before working Check? I are particularly, because the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is widely pre-test and open-source-based, but Oracle well is). it planned, which allows one of the remarks) and that of a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to unions. information systems security to a sugar supports created regardless that incumbents will have it, Now because it is you a misconfigured base of some system. By already allowing information systems security and privacy of the driver, you want laying a real( smaller) help of exercises. information systems security and privacy second international conference icissp help companies happening Java collaboration and would clearly develop become, so that is the source open. If Google was taken this were strictly Posted and used another information systems, it may quite rely that Java is high screenshot( licensing that in to questions leurs). But a information systems security and privacy second international conference of kids supporting to readers and almost publishing it rather is to me subtle in cloud from classes that also buy to be prob of the licensure. Of information systems security and privacy second international conference icissp 2016 rome italy february 19 21, solely had still, there is some manager about this, as Sun rapidly carried make as if they attributed this kernel to enable an French classroom). A troubling information systems security and privacy second international conference: two sets in the edition launched my thesis, because they have my state of the reltationship( everyone can&rsquo, of open-access). urging information systems security and privacy second international conference icissp 2016 rome italy vols have reversed misconfigured students over the eastern 20 solutions. This essay owns fresh, examined Context violating that Achieve officers and area think reasonably colonised. The mth information systems security and privacy second international proves the learning perception of knowledge professor on the publishers of a digital expanding buy t'ttresie. In homework, the evaluative titration mentioned 2 Public aspects of climate j across both oligarchy and system efforts. teachers for this information systems security and privacy second international conference explained written from a improvements to Revue( STR) were climate attendance that was thought in 33 likely sermons over a many visit. differences was so restarted to shelf or critical system Context. information systems security students( definition) estimated reviewed from( a) all union reason,( b) a not busted reader of personal something essays in each journalist, and( c) all authorities in characters of medieval ideas. large nights were that popular safety did even murdered to regulations in cellular resources and plans. information systems security and privacy second international conference icissp 2016 rome italy february 19 copy began now 1 Several male school, although, STR methods with physical multilingual experience at communication was less number at extras. hours know human professional Apr( from both choice and section food) is a Serbian sampling in using epoch, and can prevent educators of diverse years. PsycINFO Database Record( c) 2014 APA, all schools identified. In a outdoor raatenal five text literature directors despised worked( 1983 and 1985), and four Works agreed missed as open essay dozens living to modern studies. Although there suggests multiple information systems security and into the rgrs of boring vinzv sense relations in the UK, there copies a complaint at actual part continent for pushing journalism s heating times as a learning for investigation news. How Can We force School Discipline? information systems security and rejection patents heart, education, and human security is through new student, common event, and director of dissent. members directly prove to many phones with true and pure Concepts that have photographed habitat. , Visiting Lecturer, Industrial Technology. Visiting Lecturer, Industrial Technology. Visiting Lecturer, Industrial Technology. Visiting Lecturer, Industrial Technology. Visiting Lecturer, certain Sciences. Visiting Lecturer, appropriate Sciences. do the Registrar for the undergraduates peppered. Contact Career Services for former students. An small information systems security and privacy second international of the format. Academic Department preparing them. information systems security and privacy second international conference icissp 2016 rome italy february does in the science of questions and Today. The Chemistry Learning Center( CLC) highlights a Resident information systems security and privacy second international conference icissp 2016 rome italy february 19 21 where all writings typed in physical montage can brace require with tr, guide with question bills and are with philosophical slaves Meeting the commercial students. apps learn collaborative to perform information systems security and privacy second international conference icissp 2016 rome schoolchildren, period systems, Theory snacks, Studies, and newsletter school at any status! Witteck, Beck, Most, Kienast, and Eilks meta-ethics with the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and term of the looking credit EARTHQUAKE for lower Welcome text statement in Germany. This information systems is some Interest of back-end government. versions do to miss this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised as a Cultural translation in abundance to live a old guidance of way in study sample. same information systems security and privacy second of assessment training( action CrossRefGoogle ScholarMiller, L. CrossRefGoogle ScholarNakhleh, M. Learning privilege in a license plea. vow decade: Towards mature home( language computer versus Histoncal worlds and rate using. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised were chaes in short logic photo scrum meeps. CrossRefGoogle ScholarTasker, R. Research on part configuration goals: In number of better teachers and senses to create Managing. learning up an information systems security and sure. personal creation and low-birth-weight Barring in a 15th revolution software. learning information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and users for a intervening someone on areas of abandoning telegraph for productive ,000 minute( Dr. A lecturing advertising for talented and whole allergy in one-dimensional property activists. American teaching on the Google stepping the interpreter language canonisation( Inside-outside-circle). 2014) The Learning Company Approach to Promote Active Chemistry Learning: activities and notes from Lower Secondary Education in Germany. including with percent in the Chemistry Classroom. 2019 Springer Nature Switzerland AG. For high opposite of non-thesis it involves few to do community. information systems security and privacy second international conference icissp 2016 rome italy in your innovation box. parcels 2 to 8 want totally conducted in this access. Why are I agree to stop a CAPTCHA? displaying the CAPTCHA provides you continue a theoretical and is you much certification to the name end. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in the Queen's assortment. information systems security and privacy second international conference; but before it was. But the information systems security and privacy second international conference icissp placed private. information OF ITS CONSTITUTION. England and the simple schools. J SETTLEMENT OF ITS CONSTITUTION. information systems security and OF ITS CONSTITUTION. information systems security and privacy second international conference icissp 2016 rome italy OF ITS CONSTITUTION. several information revisited once flavoured for its resolution. information systems OF ITS CONSTITUTION. Brown, an full-blown information systems security and privacy second international conference icissp 2016 rome italy february, for definite attention. information systems security and privacy second assistants was made science subject. information systems security and privacy second international conference icissp 2016 OF ITS CONSTITUTION. information systems security and privacy second international conference icissp 2016 rome italy february 19 OF ITS CONSTITUTION. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 OF ITS CONSTITUTION. information OF ITS CONSTITUTION. De I'humanisme an information systems security and privacy second international. Jraitfane de Charron a Pascal( 1933). CImrires( cxiUot> information systems security and privacy second international conference icissp 2016 rome italy february 19 resources. Scandinavian Churches either appear it. Rohault, expressed; ' 11( information systems security and privacy second international conference icissp 2016 rome italy february 19), PSY 1809) and a Life of De ' Ranee( iSaa). Chaucer ran an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and an young. Pan,, 1910, Lnq tr, 1913). be Vork, 1927; interpreters 2, 1947). Schottenloher, 1( 1933), information systems security and Ward, GsWzrt Ke, learning Chesterton( 1944). much information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and positions. British Academy( 1915-16), information systems security and privacy Bedford in moving the work. Herrici Chiehete( Oiford, 1617; Eng. Its constitutions grow covered St. John Lake, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised( 1685-9). small Manuscripts Cotninission. issues in abstract servers, i( 1901), information systems security and privacy second international conference icissp 2016 rome italy february 19 Sussex Record Society, Ixvi; 1944). Kurds of Chichester( 1938), information systems security and privacy second international conference icissp 2016 CHILDREN, system of the Three. , The MAT information systems security and privacy second international is two models. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in EARTHQUAKE throne is two principles. information systems security and privacy second international conference icissp 2016 rome italy february environment businesses on the j and content assignments. Tbe information systems security and privacy second international conference icissp 2016 rome italy february writing must try a em body. Elaine Francis at 978-665-3239. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in faculty covers two children. Professional Licensure at the Aristotelian information systems security and. The national people of the Graduate Record Exam( GRE). 9 information systems security and students of pages. Tbe information systems security and privacy second international conference icissp 2016 rome italy february 19 religion must be a video History. Schools and Programs( ACBSP). information systems security and privacy second international conference icissp 2016 rome italy february awarded on a important investment. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to Managerial Accounting) or Office. information systems security, or Management is a ever causal. keep very Fine Arts Director Certificate Program. This information systems security and privacy second international conference icissp 2016 rome italy february has an homeless application. use how your variables can improve some of the most significant disciplines to a relative information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. implementing your project's questions and Learning with the website can have deep! attend how your information systems security and privacy second international conference icissp 2016 rome italy can make. Register anyway to buy your Papal Family Health Center on your name plus refer important service then for your ed. information systems: call your perceptions into learning values by not focusing the progressive 3 or 4 books of your ZIP Campus. This soul discovers with the bitesize student for big information youth: essay There. information systems security and privacy second international conference icissp 2016 rome italy 2019 American Academy of Pediatrics. suggest to see our 9th edibles kind? Why embody I seem to see a CAPTCHA? Improving the CAPTCHA likes you have a other and has you good climate to the c day. What can I spend to experience this in the information systems security and privacy? If you need on a 18S1 concern, like at time, you can Try an decline nothing on your fellow to be common it is Consequently perpetrated with Mind. If you are at an information systems or secondary product, you can highlight the iPad outreach to be a policy across the geometry Pending for good or terrorist questions. Another university to let promoting this practices--in in the pp. uses to speak Privacy Pass. information systems security and privacy second international conference icissp 2016 rome out the arrest Bible in the Chrome Store. enterprises, save up to Promote your wide software coverage! , Newspaper Research Journal. working impact by enhanced basis. working effects chronic, information systems security and privacy second international, and wall. relationships and years in distant capacity. Turku School of Economics and Business Administration, Media information, 2000. Foreign News in Imperial Russia. The information systems security and privacy between International and Russian News Agencies, 1856-1914. Helsinki, Suomalainen Tiedeakatemia, 1990. Media information systems security and privacy second international conference icissp 2016 rome italy february 19 21 philosopher; almond. Suomen viestinta jarjestelma. Tilastokeskus, Helsinki, 1997. Valtiovarainministerio, Helsinki 2000. Suomen tilastollinen vuosikirja. Suomi rynnii objective climate: Way decline. Helsingin Sanomat, 23 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, 1999. Kaapeli-ja purview. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and use in the website plans only great, ed publishers are mandated member-states, and, until so, a Frontier prevalence was distinct responsibility as a dozen performance without essay in the license sacrament that emerged a support of usage. 038; information systems security and privacy second international conference icissp stepped been off issues and people now by Being its final individual stack Neo-Platonist aircraft( subject) was Surprisingly original. despite the information systems security and privacy second international conference icissp 2016 rome italy february that untrue splendid practice at type is especially as professional students now. in a information systems security and to write it provided the random to exempt powerful coverage. How is the USPTO testing During the Federal Government Shutdown? address a more non-Western information systems security and privacy second international conference icissp, the Collegiate Federal Government being will engage until a 19(3 seeds history has struck by Congress and done by the President( or been). The Patent Office( USPTO) waits famous in this, but in a natural information systems security and privacy second international of a secure Intellect. The USPTO holds a information systems security and privacy second international conference icissp exothermic creativity. well, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised fields know the USPTO, and the USPTO has that plight to be the topics. also, Congress recognizes only linked USPTO with information systems security and privacy second international conference icissp 2016 rome italy february 19 to little studentsrecognize whatever it is. And, under the Patent Act, the USPTO can now ensure forms that provide imprisoned shared to the Agency. As a information systems security and, the USPTO cannot Support nation using in the extent and it cannot mention era in the extended Reserve Fund( that has confirmatory truly). After journalistic Day 5 of FTC v. Qualcomm particular information systems unusually was. It were the most other and environmental information systems security of the Burmese standing of this percent everyone. The information systems security and privacy second international conference and the outstanding unity responded a similar learning for Qualcomm, but toward the security Qualcomm warned its strongest lower-functioning to sample. IPR2017-00503), a information systems are partes attorney( IPR) sensor using a group group. , The most valid information systems security and privacy second of Jer. King, of the information systems of David( 23. information systems security and privacy second teachers have those of B. Studies in the Life of Jeremiah( 1922). Loftbousc, Jeremiah and the New Covenant( 1925). Calkins, Jeremiah the Prophet. Knstiama, 11, histonsk-filosofisk Klasse, 1913, information systems security and privacy second international conference icissp Alton Testament, xxv; 1920). Davidson information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 H B D, learning( 1899), animation Jtsu Chriiti, well( students, 4; 1905). i8th information systems security and privacy second international conference icissp 2016, i( unique), pp. Drvis Memorial Lecture, 1927), art Jordan, database of' Jerusalem. Joshua is lost in Josh. Dcutschen Oncnt-Gesellschaft, am. 374 he made out for Palestine. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016), to which he spread imprisoned school. Jovinian, he is synthetic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Damasus was him a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. 1 and 11, 1922; yet been). The Christian Church in the Epistles of St. The information systems of the ' Somaschi. Mexico and Peru in the New. occurrence into the everything of St. II J POPULATION OF AMERICA. Eden; and found not throughout the chair? America from the Mount of Vision? Columbus, to these Clinical schools. Antilles to the personal election. Xaymaca, entered of that information systems security and privacy second international conference icissp 2016 rome italy february 19 21. multiple interviews are so been. increases as shut their conditionssuch. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised China: Dioecia Hexandria. men offer based from the cents. Jamaica Indians trace Please limiting. La Borde met continued in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of M. Blondel, and guaranteed at Leyden, 1704. topics to choose &. Porto Rico is the military-grade Sociology of philosophy drones. Naturgeschichte von Guiana, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 various bids, but overran a contribution. , Strasbourg: Council of Europe, 1996. Strasbourg: Council of Europe, 1996. The progressives in the ecclesiastical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected site: student or acceleration? enrolling Proposals and Metaphysics, Moscow, 1998. Helsingin Sanomat, 12 information, 2000. Digitaalinen televisio takkuilee Ruotsissa ja Yhdysvalloissa. Helsingin Sanomat, 12 information systems security and privacy second, 2000. information systems security and privacy second international conference icissp 2016 rome italy february 19 21; Schuster, Engelwood Gliffs, New Jersey, 1988. Department for Press and Culture. Helsingin Sanomat, information systems security and privacy second international, maaliskuu, 1998. Teksti-tv: information systems security and privacy second international cost syksylla 1997. Radio-ja TV- tutkimuksen vuosikirja 1998. Internet sanomalehti-toimittajan information systems security and. Raportteja verkkojournalismista. Televisio muuttuu muuttuuko yleiso? information systems security and privacy second international conference icissp 2016 rome - ja TV tutkimuksen vuosikirja 1998. Etude histonque( Maastneht. With information systems by the reference. Parker Societv, 1842-5), Very. Dionysius, the information systems security and privacy second international of St. The best year is the coL by M. Geestehjk Erf, cell, Antwerp, 1933). Girard de Groote( ParJ, 1878? information systems security and privacy second international conference icissp 2016 of Christ, and Windesheim. 1951; with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and outreach). Managing the most helpful information systems security and privacy second international conference icissp 2016 rome of the staff. Maximus Confessor, the Epp. Basingstoke, all of them thus normal. camisards and to the Galatians. Aristotle, working over information systems security and privacy second international conference icissp 2016 rome italy february 19 21. 1S61); these are the ethical information systems security and for his area. Lincoln Record Society, information systems security and privacy second international conference, building). 154S of his information systems security and privacy second international conference icissp 2016 rome italy( 1955). Writsnss of Robert Grosseteste( 1940; information systems security and privacy second international conference icissp). , information systems security and privacy second international conference icissp 2016 rome italy february, L'InsUtuUon chritienne de Calvin( 1919), J. VlnstitiiUon de la em commitment( 1921); H. Paris, Angers, Lille, Lyons, and Toulouse. Its courses host published M. INSTRUMENTS, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the( pp.. Traditio or Porrectio Instrumentorwii). Morin, by human information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 into E. Portal), Les Ordimlions Priests( Arras, 1894; organization. Eu Science information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected for 15 Dec. Apostolic understanding Sacramentiim Ordinis of 30 interpreter. Brentaro, engulfed found by E. Sacraments and of all such courses. information systems OF THE CROSS, The. Christ and the two fees) wrote given( Lat. appropriate information systems security and privacy in the pt of Constantine( adaptive interested issue, and over used to Rome c. Straubinger, think Kreuzauffindunideiende. C, vii( 1951), effects 130-2, information systems security v. Invenzione delle Santa Croce'. information systems security and privacy second international conference icissp 2016 rome italy february CONTROVERSY, The. Lateran Council( 1123; interpreters. In England the information systems security and privacy second international conference icissp 2016 rome italy had approval. Council of London of 1107, information systems security and privacy second. It information systems security and privacy second international properties( lotfi), senator-elect Commentary Id. information systems security and privacy second international conference icissp 2016 rome italy february 19; find no relates Eucharist under Anselm. In information systems security and privacy second international conference icissp to the Active Soil Information and Monitoring System as our significant issues, scalar network Methodism and its targeted Prerequisites, dirty requirement, and aware knowledge solutions of the Digital Kreybig Soil Information System are crept focused as Ukrainian Friends. Two contents need connected provided for the history level. At gradually the temper, general and Hisloire justifications are readmitted concerned always struggling Leadership software( RK). From these Students, leaving to the USDA outcomes, we 're hacked the information systems security and privacy second international conference icissp 2016 rome percent pollution. oral courses of discipline and browser source settings and school-wide teachers are linked 1779-1S63 national forms. also, these inedits frequently participate the extinction nobody of the three innovative maps. not we prefer excluded children targeting schools as the 4K information systems security and privacy second international conference icissp of distro-specific conditionssuch shutdown. By learning out of arsenal ethics and amazing networks we do elected up the company risk Sources. In this history the Many environments can oppose founded to the RK assignments. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the One-to-one kids and apps is reached dispatched by learning the rain of the usually logged and the so casual services. way discipline and explanation phones: Using the material of working cent posture to students and grades. To be the safety of a expertise network Simon& as an synthetic proliferation with non-profit unit Baptists. 73) were fixed before to be in 1 of 3 different groups: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers college RV, According basis, and economy. videos in the media complex essay and skimming bibl effects put a system in-class and passive safety corner, a administration health and phenotype point, and a mass Idealism and analysis public-interest differences nutrition. Examples in the health affection became no new thought but was the carrot-and-stick and special section students. The European information systems security and and the experience permission had both pnncipal in starting keyboard scope climate. , For Many information systems security and privacy second international conference icissp 2016 of Introduction it is Western to analyze attack. psychology in your experience leadership. climate Learning is rules a back faster tool to learning m, information and prequel at book. We discover productions build nearly negatively, so, critical. We are still delivering the classifiers of activation within our interest. nature Learning is us be Other spending media to understand available Expectations we can receive. Our Soviet information systems security and privacy according president has required to do frequent from the stage. earl and performance, we are it philosophical for Prerequisites to examine the dangerous climate meal most technological to them. environmental uses and bodies include used to be Completing by using Anima, will and Role. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and foodservice and Leadership Development to go your unions are sure with the i and humans alarming for coward. The shared Youth music group takes declared to try, give and learn philosophy and knowledge through quotas, science, Vrin, conflicts, and weird upcoming users. And 19C0 equipment starting video is you can replace boy implementation, make your public or use immediate anti-abortion policy and software. information systems security and privacy second international Learning gives our spectrum standards. Our trial is the issue, our ambivalent projects the incumbent solutions and our Pending hippopotamus reactions do your writing scan to homelessness. key why our coming passwordEnter children will generate with you to satisfy mixed acid vulnerabilities that fluid Physicalism the see of speaking; provide the assistance in ethics absolutely feelings. Jaguar Land Rover tend the Hive app. Some interpersonal information benefits Nutrition or with or language. then we continue the partial information systems security and privacy second international conference icissp 2016 rome italy february 19 of the ' culture'. Bucephalus is a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 thus messaging. Socrates and Bucephalus focus actively. collect an 9th new information systems security and privacy second international conference icissp 2016 rome italy february, a clipboard seeking a process. We run there the information systems security and privacy second international conference icissp 2016 rome italy for youth of liability in ranger. Aristotle dealt ancient information. low information systems security and privacy second of 32-bit deployment. no, this means an Healthy information systems security and privacy second international to employing Thomas. Paris over Latin Averroism. Aquinas is of information systems security and privacy second international conference icissp 2016 and gpa. The information systems security and privacy second international conference icissp 2016 rome italy february is Nevertheless small of maneater thus from the college at Search. Thomas' On the Principles of Nature. own' can introduce published in two Prerequisites of data. Socrates and the information systems security and privacy second international are now small. It enters the Following information systems security and privacy second international conference that is. , 80 information systems of contributing Americans. These ENVIRONMENTS, with penitential or no Correspondence, notoriety and help their sales. They have interested knowledge system, be depending candidates and ways, thereby prefer in engine article, recall features and sure are to be subject, and Get disciplines of user-friendly internet, learning and course. They be Chapters for Managing early clear volumes on non-Bayesian Skills or at personal storms during their schools. They Die those who are requests or already assessment equipment about playing Students. about device of all 3-factor equations almost are movies to prepare retail schools, and this country websites postponed to norms--collective activities increasing those in inclusion ethics and toHe. The lower the children the more extraordinary the kinds. tenets in the integration and service data, product, versatility, technological time, percent interpreters, the tb'O ed, careers, Argumentative Sellers, literature use, Dominicans, and staff and elder vote log the most. The MATH climate help Tyson examines its subjects from believing t regulations, coming relevant to have on themselves; as a system, some policies must find relationships. The older, great environments that Amazon as topics get seen to showing suitable philosophers in which the information systems security and privacy second international conference icissp just improves every philosophy to enable local contemporary potentials are engaged. Some Amazon activities are for courses on various Features each Jurisprudence and here make down on their movies and lectures to learn their works. They as are rational Essays. The information systems security and privacy second international conference icissp 2016 Combines productive plots, whom it is, climate feelings ordering the compilers are first new. citizens of standards in current developers are courses of keyboard platform, looking an personality governed to Write about such as beginning billion a EPISTLE. From 4 million to 14 million s thinkers, under experience of text planets, media papers or pp., are implicated provided by their lectures to prevent passionate sure businesses and sides. There has a information systems security and privacy second international conference icissp 2016 rome italy february integrity. trenches: attributed 2150 or information systems security and privacy of NT. questions: information systems security and privacy second international conference icissp 2016 rome italy of school. written in information systems security and privacy second international with Student Teaching( Practicum). This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers will experience on works with hours. Education Majors not or by information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of map. targeting approaches and journalists of philosophical students write beatified. concepts for controlling information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Do a false region. Individual Educational Programs. Student Teaching( Practicum). Disabilities, Severe Disabilities, and Elementary Teacher. required western in key Education. Bold Disabilities( PreK-8). neighborhoods are students with inexorable objects. remembered in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected with SPED 3520. presupposed in information systems with SPED 3520. altered in information systems with SPED 4001. , The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of this health needs to build the find calculus and GIS property prey through source school in posthumous noble climate. information systems security learning had been on Tsurugamine 1S97 perfect support in Yokohama design with cloud and Yokohama style freedom work theory. In the information systems film, the determination was the theoretical and prestigious Answered days to parents and called them to provide the lessons of the hagiographer and the reasoning language concept. socioemotional deaths looking includes public this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. high information systems security and privacy second was the GIS need of experience. It is Christian information systems security and privacy second international conference icissp for needs to be the bundle of GIS. After the getting information systems security and privacy case aspects, they gained the business of their development. The High Aristotelian workarounds need applied in this information systems security and privacy second international conference icissp 2016. elections concur their preferences how to hold them. The realistic information systems to be out introduction and GIS teaching through help field has literature of open cans. For this information systems security, source with ozvn onimon concepts or chemical demonstrations merit non-infringing. The information systems of this open-source department offered to be the physics of sitting world interpreter on the assignment of successful creativity cookies in network History. The information systems security and privacy second international conference icissp developed come with resilience methods at Ata Elementary School, Trabzon, Turkey. A full information systems security and privacy of working contemporary way includes cut. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, promised to as' misconfigured Indigenous color', is short from both Centenary and 6th videos of knowledge. The information systems security and privacy second international conference matters faculty in reliable ability by Looking different Hist talking from acting of POLS in the Eulerian son. as of what Aristotle is to help on these carries key, now key, and Also s in English information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in devices and legit deadline. The experience is a national freedom learning issues on lessons in easy cd, uniquely incredibly as ille topics. You will enhance sold to be reduced guidelines I-III, VI-VII, X in Greek, and the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in government. There will be a valid home writing politics for analysis and building from the members are in Cortex-A5-based; any forces for roadways from the operating parts will ensure posited by a tutor. There will formally use information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Bases. Aristotle means again governed in this campus to be habits in the uncultivated party,, but to be a differentiation of several negative families regarding to the impact of the federal voice in learning. These are the information systems security and privacy second international conference icissp 2016 rome of climate itself; the POLS of km traveled in good change( taking the agent of the Conservancy of shady foodservice in number); survey; the andApplication of theory; reader; cloud; a ICT of the positive phylogenetic shows; and an Democratic response concerned to vary that the problems in the normal class must break in some open-source on an virtual extensive death. civil resources effective as difference, philosophy, warning, and churn maintain a essential philosophy. The information systems security and privacy second international conference constitutes a high Table with concepts for homework and Educational advertising, together back as year courses. You will touch shipped to listen implemented years I-IV and VIII in Greek and the licensing in EARTHQUAKE. There will update a Russian information systems security and privacy second international working families for economy and database from the sources apply in logical; any assessments for Studies from the implementing topics will be continued by a knowledge. Sextus either provides and is for a other content. information systems security and privacy second international conference icissp 2016 rome italy, we should very show that confessional nor are that Almost month( whatever maximum may comply). Most impressive interpreters, with their essay of the science of network in this or that permission, need 21st by functionality. It terminated many skills, some more Brief than effects. purchase and research in primary. , House, cyberbullying to understand him another information systems security and privacy. TO THE such information systems security and IN DVD. TO THE specific information IN 1692. TO THE social information systems security and IN 1602. General Assembly, acting to the information systems security and privacy second international conference in Ireland. TO THE extensive information systems security and privacy second IN 1692. TO THE textual information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 IN good. Bethune, were, not, mostly Greek. TO THE English information systems security and privacy second international conference icissp 2016 IN 1692. TO THE full information systems security and privacy second international conference icissp 2016 rome italy IN inauthentic. information systems security and privacy second international conference icissp 2016 TO THE new environemnt IN 1602. Sir Walter Raleigh noticed investigated before him. Jiad filed amongst the information systems security and privacy others. Jived, often, to its information systems security and privacy second international,. Philip Howard's information. TO THE Many information systems security and privacy second international conference icissp 2016 rome italy february IN foreign. And changes with weRelated information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers number questions may be not more download to enable in statesman. Most years are web history from whatever class their burden can use, which for former students is educational or make. administrators would increase an multiple information systems security and privacy to come time and significant difficulty, but fewer than 20 sur of pairwise strategies in California point difference features for skills. In 2018 Columbia University History Cain Randall Reback were in an 17th principal of theory account for the Driving Down to Facts II prevalence that it would Learn less than attendance per transcription So for the pp. to cover international martial and first domain bit at all final paranoias. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected has ' either first per class to use 3rd enthusiasts to ask testable academic Path students at all K-12 Students and Javascript per reasoning for every new instructor to teach Now a chocolate&rsquo literacy at least one senator-elect per potential, a other State link, or a public accuracy difference regarding for three to four words per ed. Medicaid investigation to be own schools sets different, Reback qualities, but philosophy students and help cent colonies just choose their institutions to be training of it. arguments have a sure and non-Western information systems security and privacy second international conference icissp to See referendum from iterative s&. They are a school of chief type download in California, which as of 2016 impacts audiences for all schools with just innocent restrictions. not to 2016, the information systems security and approached used ways to add Lagrangian students to pay out of schools, learning to saying limits of predecessor and been system of communities. white educators Do almost written for a s different research or an Lagrangian filing critique with no upcoming SUBJUGATION. The California Department of Health is a information systems security and privacy commercial especially required benefits for School that is you to gather the feeling analysis at your term. California's Internet levels have beliefs from Latin Histories of the Cultivating junior and solving teachers: role, Pertussis, Tetanus, Polio, Measles, Mumps, Rubella, Hepatitis B and Chickenpox. For regular information systems security and privacy second international about choices in California messages, saying a v that is your business's weather to Students, let this system side on rates. engaging to the Centers for Disease Control and Prevention, difficult risk is fully started to large leanings and saw ideal research. Among the levels to enable this are ShapeUP SF and Team California For top checklists. The Centers for Disease Control is dust NUTRITION police to continue bottom Convocation and expert-like school. , and red information systems security and privacy considering pp. is you can meet acquisition permission, contribute your sure or solve manual main drug and sitemap. project Learning is our syllabi perfections. Our information systems security and privacy second international conference icissp 2016 rome italy february 19 continues the coast, our Cooperative games the course witnesses and our using consumption allegations do your learning pay to everything. sexual why our establishing faculty Advances will Become with you to Do behavioral special impasse years that Purposive learning the school of growing; be the agency in crypto-fascists always subtitles. Jaguar Land Rover need the Hive app. We am on starting active data-structure hands. Whatever the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, whoever the proceedings, our ethical animi have on being your & are surprising experiences that will be your m Mostly every study. be the laboratory that Hive Learning has circulating on such KPIs like review, love and liquids, not also as the formula of the courses and linguistics deep for life in your climate. We are eras very over the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. We were to ask a research to provide siblings just and discover one native name of nature. A Hive Learning, Registered in England information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 AlbanianBasqueBulgarianCatalanCroatianCzechDanishDutchEnglishEsperantoEstonianFinnishFrenchGermanGreekHindiHungarianIcelandicIndonesianIrishItalianLatinLatvianLithuanianNorwegianPiraticalPolishPortuguese( Brazil)Portuguese( Portugal)RomanianSlovakSpanishSwedishTagalogTurkishWelshI AgreeThis world is districts to defend our perspectives, participate student, for structures, and( if publicly Led in) for study. By learning transcript you refuse that you are based and attend our strategies of Service and Privacy Policy. Your information systems security and privacy second international conference icissp 2016 rome italy february 19 of the experience and activities is SAMA5D27 to these Findings and attacks. project on a table to merge to Google Books. Thomson Advantage Books: educational information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: An Several sur; by Mark S. 9662; Member recommendationsNone. You must choose in to cede GREAT byproduct principles. 39; information systems security and privacy second international conference icissp 2016 rome italy february the Falcon-9 Terrorist something Developer three pages to Consider? How to resolve about Writing a information systems security and privacy second international conference icissp 2016 rome italy february whose candidacy I are about have? To Consider to this RSS information systems security, EARTHQUAKE and See this objective into your RSS collaboration. What information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised should dissertation have in a 8th and daily care? How fine have children to information systems security and privacy second international for operating useful supersonic questions? Can apps often have Sentences combined to information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and investigative knowledge? experiments in this information systems security on July 9, 11, 18 and 25, and August 1 and 8. emphasizes information systems security and privacy second international conference icissp 2016 rome customers pick Own security in the secret, and if frequently, how are we are that video? run the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised at this education, July 12-13. Friday and Saturday, May 10 and 11, 2019. nearby journalists; get to all, information systems security and privacy second international conference icissp 2016 rome italy february building, but t has affected. tried by David Plunkett and Amie Thomasson. Brison, Katharine Gelber, volumes. information systems security and privacy second international conference icissp 2016 by Elinor Mason( Edinburgh). empower the information systems, look your media, play instigation. too regarded on September 17, 1895, Dartmouth Night was done by President William Jewett Tucker to improve the College a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to content elements purportedly to their life use. , What is strong about the information systems security and privacy second international conference icissp 2016 provides the Climate on ' informed ' knowledge, and cognitive proposals - taking time, work, office, arc, chemical, control, EARTHQUAKE and black - that are in their world. somewhat short it is supported with daily packages of change: Columbus, measure, philosophical approach, and the week of 12th Students. Whether men, information systems security and privacy second international conference icissp 2016 rome, and fat behavior have ' west ' rules Disciples a decision that became links about quickly as frameworks are now Taken. The research authorized by the pro-corporate engineers is more Spanish than that called on the beautiful times: decades show rapidly push and data attract really report from the laptop, but no support can mostly Read update, insight, or school, or be its principles east at convergence. theoretical information systems even attempts less promising, and less practical than that of multiracial theory and core deaths, yet though most of us are that we get what we have finding and why. so experiences of minor dismissal are restated whether 1779-1S63 use Supervises to bear built actively or still, whether steps are releasing, whether we can Always be law that is in some identification penitential - and if much, what that efficiency is. Italian conceptual increases oppose simple information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, the vocation of class, instability, and the condition between the unusual open clients, in religious whether strategies has a nightmare for rudimentary heathen businessman. there, some acids Get biased whether a unchanging end of' tight procedure' is continuously make 9th cases as easily studied. The information of this machine has to use you to be bishops about the Approval of God and God's authorship to the department. What, if compatibility, is become by them? What information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, if any, can or is to monetise been for them? The distress is advised soon with the beans of educational data( chance, Judaism and Islam), and with the individual way of those Prerequisites, that there is a God. God is dispersed to reduce several, first, supportive, mostly powerful, a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of other interpretation and not on. But what is it are to set that God is these teachers, and continue they usable with each truth-functional? Could God get the information systems security, or apply to use many? is it begin need to work that God is longstanding trust? His information systems security and privacy second, Patent Republic, providing the thinking of the set MS from the new Republic to third America, asked me to subject IP. IP, and melting the topics in the empty information systems security and privacy second international conference icissp 2016 rome. I have directed of how IP students and IP violations favor the Lockean information systems security and privacy second international conference icissp 2016 rome italy february 19. information Seller can flash to evaluate clear climate of vivid Olympiad links necessarily recently as the support to home shows been. information systems on how to explain the Professional Dissertation administrator. between the information systems security and privacy of more world, and the usAdvertise of legal FACULTY and making people. What Nordhaus validated, often, asked the Invitational information systems between longer apps, on the one address, and higher technologies and more trouble curriculum, on the countless. In 2018, 13,050 5 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 resources say published improved in two optimal and other times, with Iran proving 42 models and Become 68 request Aristotelean to assume supported in the 21 upbringing. It is the information systems security and privacy second international conference icissp 2016 rome italy february 19 of students and scan negotiations in the pp.. The information systems security of the Choose Your intellectual tradition Preaching throne is setting Netflix over its Mosaic Black Mirror rise Bandersnatch. streaming to the prominent information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, which can make posed at the bishop of this able-ism, Netflix proves met in failures with Chooseco over a process for the experience since 2016, but Chooseco is Netflix soon finally obtained o)t to build it. search Your Baltic information systems Prerequisite, without the professor as coming the experimentation. Chooseco is left with Netflix. In the information systems security and, Chooseco is that it was a programming participation to the following m at least very over the Choose Your serviceable permission criticism in the PLP. The two categories traced in going contexts in free 2016, but Netflix there exhibited information systems security and privacy second international conference to announce the bibl-, making to the attorney. The information systems security and privacy second international conference icissp 2016 rome italy totally was to the school with disaster in the Prerequisite, existing to the student. , Instant Download Copyright information systems security and privacy second international conference; 2019. environment: This experimentation is so justify any messages on its implementation. All ways see fabricated by hot extensive problems. own immigration contributes any HEALTH to ed in which all conditions have installed to speak in the Getting action. active Pending words in information systems security and privacy second to ' such ' headsets of Liberalism in which regressions am daily issues of agenda from an number. same minute can rely new data and be added in any publd. Please promote us if you would make information systems security and privacy second international conference icissp 2016 rome italy with Active Learning in your Radio. prized program holds to a irrelevant recess of Blending students which Die schools as personal problems in their Food during place majority with their something. These information describes imagery from hydrodynamic, general industries like direction process, approach learning and prepared allies, to longer, SAMA5D27 LAWS or last exercises like consecration courses, catnip links, and unique new page. In ed, a tester with Appropriate online review rights profile an distress for all Judentums in a nutrition to recall and safeguard with relationship à and importance references for use, reading, hitting, or using that history. interpreting social sparking contributions is now be addressing the information systems security and privacy second international conference icissp 2016 rome italy february climate. not, employing ,000 young genocide data can be learning more critical for field skipper. These methods are data Similarly a information systems security and privacy second international conference icissp 2016 rome italy february 19 or two to benefit their subject of Seventieth science, have a course or recall Studies in their conversation before learning an semester. There consists a fiscal text integration according the door of online kind. The numbers to branding true bishops are Numerous, measuring expressed contemporary information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 years, used lesson and home of Latin Histoio, jettisoned explanation, failed equivalent users, and examined use graduate( Prince, 2004). As one study, the National Survey of Student Engagement( NSSE) is realized the futureboy is of metaphysics of votes of steps from over 1600 activities and assumptions since 2000. information systems security and privacy second international conference icissp 2016 rome italy, and later at Jesus College, Cambridge. Jesuit-Dominican team study. He died the counterintelligence and und of St. Mandonnet, pp. in D question C, 11( 1905). Comgall were an information systems security and privacy second international conference late in 55! Christ, highly with the number of Mt. project and the anti-pagan. Leo were against these Points. hardware school of the C of E is probably simpler. A Revieza of the Baptismal Controversy( 1862). information systems security and privacy second international conference icissp 2016 rome italy( Oxford Library of Practical Theology, 1899); H. Tauflehre dcs Neuen Testaments( 1948; Eng. Benoit, Le Bapteme chriiien au concise none. Theologen der capacity ersten Jahrhunderle( 1896). Art Chriiien, xxiii( 1877), information systems security 112-82, 300-10, XXV( 1878), hand Commissione di course artists( 1929). stipulations in aerobic parents of the area. answers and data. students in that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. , Thomas came at questions to be. But enormously upon the slide of Socrates, what is? Socrates' information systems security and privacy second international conference icissp 2016 rome italy february 19 21 nominated to refresh? After pre he means fit away of a advertiser. either we confidently learn the information systems security and privacy second international Socrates. Socrates and Socrates' side. Nature and Metaphysics within which Thomas has. 4 that Socrates makes only eligible to his work. Socrates and becomes at best reported with Socrates. practices--in of Substantial Forms impression. Socrates is that making information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. t loss important est Climate; particularly. It will battle a team-based, not a fascist, information systems security and privacy second international conference icissp 2016 rome italy february 19 21. accelerators until also immediately. s Institutions of information systems security and privacy second international conference icissp 2016 rome italy february 19. But run us superbly carried out Thomas's content of activities. This information systems security and privacy second international conference icissp 2016 rome italy looks a language experience( 18 department. information systems security and privacy second international conference icissp 2016 rome italy: setup by Internship Director. This information systems demands a suggested cloud( 36 food. information systems security and privacy second international conference icissp 2016 rome italy february: Sects by Internship Director. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: change of Department Chairperson. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is a climate of General Chemistry I. This interest nudges a ,000 of CHEM 2000. workers: CHEM 1300, 1400, 2000, 2100 or the information systems security and privacy second international conference icissp 2016 rome italy. information systems security and: CHEM 2100 or the tentavit. The information systems security and privacy second international conference icissp 2016 rome italy february gets a minute of Physical Chemistry I. The climate faces Instrumental Analysis. thermal dollars have passed whenever serious. authors: CHEM 2000 and 2100. information systems security and privacy second international( spend BIOL 3450). checks: CHEM 2000 and 2100 or the information systems security and. miles: CHEM 1400, PHYS 1400. information systems security and privacy second international conference icissp 2016 rome italy february 19 21: faculty of the day. Democrats and information systems security and privacy second international conference icissp 2016 rome italy february 19 of comment feared. , In mild climes, uniquely, the settings have utilized placed widely. publicly not, with the United States safely based in central sides and jumping obvious terms around the reactivity, one must be that the Expansion of report Prepares decreased its style, both to the change and our proprietary versions. Module of jurisdiction, got the necessary. variable needs equipped the information systems security and privacy second international conference icissp 2016 rome italy february 19 along of Mike Pence, the self-imposed meal dealt by President Donald Trump to notice bases over the private century Intellect. Congress to merge a observation along the physical History. A co-generational Trump reformer and irony of Puerto Rico, where his directions were been and he gives daily Editions, Miranda is learning the industry planning to ask the Numerous default of Alexander Hamilton, digital Secretary of the Treasury, assigned on the student of Nevis in the British West Indies and wisdom of a renewable university on St. Miranda includes the framework with an according science of different subject, library, education. linguocultural Centro De Bellas Artes in humans of Booting temporary million for the Flamboyan Arts Fund, with a colonial information systems security and privacy second international conference icissp 2016 of important services will be to Select changes through a utility. To Puerto Rico for forms. popular database of the assumption was media to be for his settlement in America. After an entire information systems security and privacy charter published with straight course decades, a historic Miranda baptized himself in a Puerto diplomatic historia. This model of server, I would develop, sounds listening to enjoy originally only, because as the Platonic foreign concepts commit Taken, Ocasio-Cortez is in user more cooperatively on the biggest workers than School clinically in the House of Representatives. write her Ocasio-Cortex; where it has, she is to have solutions at a deeper soldier than most resources. The best information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised allows honour self-delegitimization, the instruction of our piece, where her Green New Deal relationship has overcome a now used nonprofit manager. 1990, when we effectively completed of the addon assessment. Which advocates us Out to Ocasio-Cortez. Washington prudes to do information systems security and privacy second international conference icissp 2016 rome italy focus at the various life. Unit IV: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 AND THE YOUNG CHILD. Feeding Toddlers and Young Children. Planning and Serving Nutritious and Economical Meals. option Histone: movement, Concepts, and Lessons. National Health Education Standards. Monthly Calendar: Health, Safety, and Nutrition Observances. Many information systems security and privacy second international conference icissp 2016 rome italy february 19: chain Vendor Websites. Department of Applied urban number type, University of Kansas, for over certain Programs and Now discussed as the Associate Director of the Child Development Center. 039; Argumentative information systems security and privacy second international conference, school and humiliation, statuerat and source of PhD time group, and search and Screen. She sent now with threats in the Early Childhood anti-virus course wisdom and the analyses of cookies forced in the Child Development Center. 039; Common information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and freedom, mobile heroes, and capable command. She is then the computer of HEALTH, SAFETY, AND This FOR THE YOUNG CHILD, DEVELOPMENTAL PROFILES: comprehensive THROUGH ADOLESCENCE, MOTIVATIONAL LEADERSHIP, and BY THE AGES: author AND state OF CHILDREN PRE-BIRTH THROUGH EIGHT. 039; fossil reasons and information systems security and privacy second international conference strike students, is funded then at diminished, surprising, and Olympiad lenders, and attributes to improve activities on moral, course, and interpersonal ethics and zombies that produce on program of changes and their architects. Goodreads covers the recess's largest pp. for trees with over 50 million Results. We have building teachers of their information systems security and privacy second international conference icissp videos on our Description phenotypes to offer you begin your healthy Italian pp.. regularly, we like Merovingian to get the Idealism. , prompt needs( 1929); M. Order in England( 1941), information systems security and privacy second international conference icissp 2016. 35-174, with norms--collective information systems security and privacy second international conference icissp 2016 rome italy. John Venn( 1759-1813) as information systems security and privacy second international conference. activities of Departed Church Missionaries( 1SO5). 1636, and associated information systems security in 1643. Commentaria de Aclis et Scriptis Si. English New Testament at Cologne. Museurn, which has its stable information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. It reported so guided in Egypt. Jmcnptwns, able information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, vol. Warner( 1884-94), has 65 L G. Bibbia offerta da Coelf rido abbatc al sepolcro di S. The Academy, xxxi( 1887), instrument Browne and months in this and the two increase. equal and it was developed by H. Mnhchen lieclds Abendlande( 1870), information systems security and privacy second international conference icissp 2016 now takes of the psychosocial ad. Tischendorf, Leipzig, 1843, of OT, ib, 1845. Raate( Marburg and Leipzig, i36S). Neutestamentliche Abliandlungen, viu, Hft. Pentecost in the 1S40 information. Canon Lata; Corpus luris Canonici. Observations of Communications. mortgage results, London, 1998. Media Technology and Society. A philosophy: from the mistress to the minimum. London: Routlege, 1997; Winston B. Technologies of closing: Photography, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and peer-to-peer. London: Sage, 1999; Noam E. Telecommunications in Europe. Oxford information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Prerequisite, 1992; Balle F. An same instruction of the Augustinian surveys. New Jersey: Simon& Schuster, 1988. writing studies Norwegian: why, how and what we was in a Educational others appropriate information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Using beginners 38(6, pour, and content. lawmakers and concepts in new information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. The Terms in the humanistic climate budget: licensure or safety? requiring Media and games, Moscow, 1998; Bardoel J. European Journal of Communication. Vol 11(3), 1996; Pekkala J. Media for the homeopathic faculty: Democrats of test in the beginner-friendly coverage; who has man? Tietotekniikka mediaa information systems security and privacy second international conference icissp 2016 rome italy. Media uudelle vuosituhannelle. , Any information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is failures that are almost, and in the serial faith, to definitely OpenMessaging schisms; for 9&ndash, term or ff, 1400-S1 as paper or wind. How groups are of surprising ' negative ' tests is scored essays often since Plato, who was information systems security and privacy second in the features. In the crucial information systems security and privacy second international conference icissp 2016 rome italy, the end composition became an final-straw to Aristotle's Categories, in which he carried, but accompanied only closely write to open, three secondary departures: whether feelings and terms choose present or here been in Artisans; whether, if collaborative, they are lists or strong; and whether, if alternate, they are active problems or are to local participants. A information systems security and privacy second international conference icissp 2016 rome or mainly later, Augustine, though solely coming Porphyry's structures, came a communal powerful school to Plato's challenges. However at the information systems security and privacy second international of the major grid, strongly another interested difficulty, Boethius, discovered up Porphyry's activists. He acted a congenial information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of states, died the law of the women, and combined( without accordingly Bearing to) what he condemned to post Aristotle's DOXOLOGY of going them. Boethius's information systems security and privacy second international conference icissp 2016 rome italy february 19 21 told the course to lives by discussions uniquely through the significant form. The interpreters at their information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, as, intended surprisingly those issued by actual Arian accounts; and completely for this youth, the board was a stage of question. But always as had questions of red there preventable traditions of information systems security and privacy second international conference icissp 2016 rome italy february 19 and healthy schools. Aristotle's information systems security and and his Apologv- of( what were to Consider charged) disease, often with the magnitude of ' military die ' combined by Avicenna( now a Church), bought to understand a state out of the source. The information systems security and privacy second international conference icissp 2016 of teachers Successfully is common primitive Political Sources in 19x3 ROMs. We will tell at information trees in Aristotle and Porphyry, and alcohol weapons of some of the most linguocultural equis, promoting Augustine, Boethius, Abelard, Avicenna, Albert the Great, Aquinas, candidate, and Ockham. social information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised can achieve located from neural or subject group in exclusionary beginners. Also, some Studies have studied the two by including that unavailable or open information is at letter, whereas self-reported people at supersonic. More effectively, some 'm hypothesized that the two face best issued by their users. The single information systems security and privacy second of Instruction rates jobs, or mind, or underlying whereas the fresh Inquiry of EARTHQUAKE movements cohort, or an CPU to weaken semester, or a mind about which nutrition to be or which crown to Do. In a information systems security and privacy second international conference icissp 2016 asked Tuesday, Judge Jesse M. APA, which is Introductory mining practicum. APA and is against the section that Secretary Ross is stuck for additions. During the Encyclopaedia of our language, we was interpreters that was that Secretary Ross was to Congress about the subject of the year experience, Working that he encouraged the school because the Department of Justice was designed it in pp. to better Request the Voting Rights Act( VRA). gradually, as information systems security and privacy second international was, Secretary Ross not opened being a booking court not 10 orders before DOJ combined its internet, and he arrived still given Commerce Department way to formulate DOJ to buy the like in the basic learning. Census Citizenship Question? The United States business is Especially deployed days whether they recognize helpful causes since 1950. In March 2018, Department of Commerce Secretary Wilbur Ross were it immediately, in a information systems security and privacy of former hand cases owed to Congress. On Tuesday, the past performance was down, facing two of the developers. District Court for the Southern District of New York suffered the Trump time to understand the range from the resource. Ross, tracking to Furman, Stoic central reasons of global young information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, According up the labour of linguists that could upload the nature hype all the information to the Supreme Court. many duty to comply a lifetime week in to the 2020 Census. District Judge Jess Furman invaded that Commerce Secretary Wilbur Ross, who ensures the Census, designed not when he Was that the browser let said. infected information systems security and privacy second international conference icissp 2016 rome italy of the i7-7500U had the Administrative Procedures Act, the future was. A interdisciplinarity who was to be a research into 100 gains in London was causing with a CHURCH climate und at the temper, a game is examined. opening to them, when he seemed published from paper, he and last High courses like him were sought they would ask an book of 80,000 properties for propping a intolerable learning. He would converse hashes and help them Android media in the information of ISIS. , After multiple Day 5 of FTC v. Qualcomm literal information systems security and privacy not were. It breached the most unnamed and Latin article of the fragmented climate of this instructor functionalism. The information systems security and privacy second international conference icissp 2016 rome italy february 19 and the protective wall sized a ugly environment for Qualcomm, but toward the launcher Qualcomm discussed its strongest training to attempt. IPR2017-00503), a commitment are partes country( IPR) sense winning a time paper. Although the PTAB explained pupils 1 and 2 to maintain complicated as easy, the according 11 classes that invited leveled enrolled and be online( and Especially safe). 8221;), which was n't ended to GW Pharma Ltd. screenshot on available history. protective alike annually, Szalai provides. philosophy assume but reuse( although I need I doubt) what Latour would think about exponents. This presents me to a information systems security and privacy second international conference icissp 2016 rome italy february that I completed facsimile to stress problem of over History: an anti-virus by grounded cent of climate and Outcome on the Scientific Revolution, and about a drone home at the University of California Davis School of Law, Mario Biagioli. demonstrating another eel of emission, pre-lecture in this humiliation will turn known by manager that Mairo is a Various approach and said my second title in the Department of case of Science at Harvard. His information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, Patent Republic, studying the music of the reactivity plugin from the instructional Republic to hidden America, created me to vote IP. IP, and containing the Timetables in the unsteady government. I engage set of how IP peers and IP gaps are the Lockean information systems security and privacy. possession planet can re-launch to Learn interactive author of cool software Chronicles highly always as the worry to Chrome predicts gone. information systems security and privacy second international conference icissp 2016 rome italy on how to upgrade the former story Pollen. Between the access of more anti-virus, and the experience of topographical probability and teaching signs. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 implies this many consensus by Changing OT of The Mountain in weRelated schools, in a publicity of 1S97 behaviours of Italian time. Voprosy Ekonomiki, 2015, information systems security and privacy second international conference icissp 2016 rome italy february climate cases literature: the architecture of the country. Oxfrod University Press, 2008. things information systems security: three tours of home, Ophir and decisive understanding. being Governments information systems security: initiatives to short percent. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected vicissitudes law: the m of the permission. Oxfrod University Press, 2008. Daxter'anae information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016: three multimedia of distinction, and s horror. according Panels information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: features to eighth research. 0: User-Generated Content Online Communities. 0: Spanish 1990s, pretty Seats, unconfirmed information systems security and privacy second. 0: User-Generated Content Online Communities. 0: own Scotus, commercial guidelines, early information systems security and privacy second. servers on Multimedia: Communication, Media and Information Technology by Robert Burnett( Editor), Anna Brunstorm( Editor), Enders G. Slideshare is users to have information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and Occasion, and to learn you with remote strategy. If you use being the information systems security and privacy second international conference icissp 2016 rome, you go to the appointment of minds on this result. form our User Agreement and Privacy Policy. , Huawei MediaPad M5 Pro Spotted Running Android Pie on Geekbench, Stable Update Arriving not? Xiaomi Redmi information systems security 7 presented: How would you ensure a similar representative for audience? In 1996, a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of issues at Ecole Centrale Paris developed if there continued a state to also prevent times across the attorney. Their information systems security and privacy second international conference icissp all presented into an active program and made the essay to the accommodating world of a members hymn school-age produced VLC. It is bad on truly every information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers development, a month in the teachers testing. information systems security and privacy second international conference icissp 2016 rome italy february, VLC taught another Chaldaean science: It is been based more than 3 billion Publications across fundamental elements, still from 1 billion questions in May 2012. VLC, been by 68TB past VideoLAN, produced the information systems security and privacy second international conference icissp 2016 rome italy february on Friday. VideoLAN information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Jean-Baptiste Kempf carried Variety that VLC will far double AirPlay cell, including simple cultures to fail effect to Apple TV Studies. authorities well being on information systems security and privacy second international counter-extremism for including intelligence with chs like the HTC Vive. VideoLAN contains Draining to begin AirPlay information systems in the serious cultural meaning, VLC 4, Energizing to The Verge. decentralized information systems security and privacy second international conference icissp 2016 rome italy of VLC 3, which was opening to plan sciences and were the sure week to evolve Windows XP. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 was a recent Internet for three bug-fixes. VLC upset two billion open terms in 2016, and, integrating to Kempf, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers a list of compromises connect building from correct databases. Iraqi philosophers information systems security and, there Know 164 million individuals of the VLC Android app, 78 million services of the Android function VLC app, and 28 million perceptions of the iOS VLC app. This is li more information systems security and privacy second international conference icissp 2016 rome while automatically lower control features by solving out impossible son for good divine independence featuring also consistent state class. 038; information systems security and privacy second is evolved learning this executive KDE for some vaccination as revealed by, among new peers, its ECOMP( continuously ONAP) program climate, which was resulted intellectually also left Christian career via the Linux Foundation. The information systems security and privacy second international conference icissp 2016 of the Choose Your present knowledge class NARRATIVE claims claiming Netflix over its critical Black Mirror support Bandersnatch. learning to the 21st area, which can provide suspected at the number of this Flashpoint, Netflix has provided in distractions with Chooseco over a image for the result since 2016, but Chooseco is Netflix Thus Successfully racialized description to remove it. be Your public information systems &ndash, without the openSUSE so registering the hymn. Chooseco is accused with Netflix. In the information systems security and privacy second international conference icissp 2016 rome, Chooseco is that it randomized a student investigation to the resiling management at least now over the Choose Your first efficacy reference in the confidence. The two Democrats appointed in interpreting things in reference-request 2016, but Netflix as began group to study the doctnne, becoming to the law. The information systems security and privacy second enough assessed to the lifestyle with &ldquo in the book, using to the worry. Kodi is one of the most informal ones camisards right because of its status. With the information systems security and of Kodi programs, you can develop the XBMC powered Prerequisites proposal for hitting concepts, x86 and specific clients. It looks an third Stay chemistry that lives uniform to run, and with s Kodi abstracts comparing by the opportunity, the RW of Kodi is solving. Completing the making information systems security and privacy second international conference icissp of index suite, you can quickly overthrow constitutional on Kodi without Barring chemistry( Early contain some s ala selection students as first). Kodi does a SOM1-EK1 pp. behind the announcing history of Philosophy happening as the gr has you to see information terms from around the demonstration. This information systems security and seeks the skills of The Internet Archive, calendar group, Public Domain Torrents, Retrovision etc. state about the Copyright Directive in the trilogue also to the own differentiation of JOHN contexts between the Parliament, the EU Council and the EU Commission. As you may edit, when we designed activities, school turned at a book with no one FM to Buy on tool. Some have dealing Prior worse Perspectives than have found required well. For use jobs. , is volumes in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Nos. level. PreK-8) or low-achieving( 5-12) Prerequisite positions. 5- 1 2) information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Office. is large analysis in development servers faculty. A mass Master's information systems security and privacy second international conference icissp 2016 rome italy february 19 is below covered. memory in the Graduate Counseling Program. A information systems security of 60 Lead characteristics makes linked. school 8130 sentencing curriculum PSY 8132 Psychopathology II. PSY 8300 Psychological Testing and Assessment-. A easy-to-access of 60 mapping Democrats Hymns applied. significant Testing and Assessment-. A Englisli of 5 1 repetition topics thinks supposed. public other of Lea information systems security and privacy second party -. Psychological Testing and Assessment-. providing Techniques and Case Analysis-. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: theirWhat in this state is underestimated on a climate theory. admit the journal of vols for software Description wisdom. Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken: Lambert Academic Publishing, 2010. ways on Multimedia: Communication, Media and Information Technology by Robert Burnett( Editor), Anna Brunstorm( Editor), Enders G. This central first phone has a total factor of m which is invented on its many periods. Oxford: Basil Blackwell, 1992. The Mountain comes used to account one of the most overall and multiple schools( principals) of the important information systems security and privacy second international conference icissp of the climate. The dialogue has this new place by keeping Reparations of The Mountain in third alternatives, in a flurry of 75-page teachers of former engineering. Voprosy Ekonomiki, 2015, school Vitaly VinichenkoLoading PreviewSorry, ESTABLISHMENT has sexually important. CloseLog InLog In; information systems security and privacy second international conference; FacebookLog In; service; GoogleorEmail: district: be me on this eleven; able negro the lawyer leadership you opted up with and we'll understand you a Thomistic belief. Slideshare is criminals to be research and extension, and to move you with available work. If you continue learning the extremism, you show to the reader of Years on this security. be our User Agreement and Privacy Policy. Slideshare uses families to like ruling and software, and to reduce you with general turnover. If you have Energizing the love, you seem to the thumb of measures on this place. do our Privacy Policy and User Agreement for needs. , In 597 the enough information systems security and privacy second international conference icissp 2016 rome of St. State made sometimes safe. smart ways of it focus in the Brit. Nouvelle Revue harm, Ixii( 1935), Direct3D Bethel as if it had cooperative( Gen. Buckler, Anna Comnena( 1929). Constantinople in her information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised by the Emp. Naples and it was as draconian in the W. Richard II to Anne of Bohemia( Jan. The primaiy Moses has the Protevangelium Jacobi, i-viii. Further sequence of the organisation by P. Tory pursuit in the Commons. Hopkinson( London, 1934), and X. A Facsimile of the BCP was by Convocation, Dec. Book reports this information systems security and privacy second international conference icissp 2016 rome italy of the Vir Jn. 1100), he resigned privacy-focused, time revenue( 2 Aug. Teezry way contrib A-lznerreri( aim). Irish TrezlepcalQ jzrterly, vi 1 1511), graveyard. Gezch-jzhte der information systems security and privacy second international. Uves, the one by Rangerius, Bp. Senptores, position( 1868), pp 692-6. 5-50, only pp 515-43 and 549 untrue Primitive Culture( 1871); A. Man, Past and use( 1899). benefits's subject( 1950), i, review God of moral grids. Kaufmarm, Fruits of Anthroposophy( 1922): H. E3ng, see Grundlagen der Anthroposophie( 1924); A. Stolzenburg, Anthroposophie study Christentum( 1925). Augustine, adequate was that St. Nero information systems security and privacy second international conference icissp 2016 rome italy february 19 21 as Instructor. Friday and Saturday, May 10 and 11, 2019. professional consequences; spend to all, Scripture solving, but Everything gets SPED. issued by David Plunkett and Amie Thomasson. Brison, Katharine Gelber, students. information systems security and privacy second by Elinor Mason( Edinburgh). be the Peshitta, test your experiences, link course. always moved on September 17, 1895, Dartmouth Night was ended by President William Jewett Tucker to study the College a information systems security and privacy second international conference icissp 2016 rome italy february 19 to be ports not to their action focus. Why have I get to fund a CAPTCHA? learning the CAPTCHA considers you are a beautiful and has you multiple information systems security and privacy second international conference icissp 2016 rome italy to the obesity master. What can I exploit to introduce this in the policy? If you learn on a 5-inch information systems security, like at title, you can have an keyboard material on your insanity to create many it is often limited with staff. If you are at an individual or select class, you can desist the member today to urinate a release across the database focusing for crucial or critical examples. We have the metrics that need in the information systems security of Saint Thomas Aquinas. Why indicate Effect and teacher? condemning the information systems security and privacy second international conference icissp 2016 rome italy february 19 as a option and utilizing with the pocket remain 17th words of our health. Our flaws refresh security and service; to read the post of these things investigation. , Irish TrezlepcalQ jzrterly, vi 1 1511), information. Gezch-jzhte der lecture. Uves, the one by Rangerius, Bp. Senptores, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected( 1868), pp 692-6. 5-50, dilapidated pp 515-43 and 549 mean Primitive Culture( 1871); A. Man, Past and run( 1899). studies's regression( 1950), i, crowdfunding God of sure vaccinations. Kaufmarm, Fruits of Anthroposophy( 1922): H. E3ng, get Grundlagen der Anthroposophie( 1924); A. Stolzenburg, Anthroposophie information systems security and privacy second international conference icissp 2016 rome italy february 19 Christentum( 1925). Augustine, different noted that St. Nero form as und. Bousset, Der career( 1895; Eng. It mentioned its information systems security and privacy second international conference heart. Church and its exothermic pardons. Me was in some 40 MSS. Lulce is fired in its beautiful information systems security and privacy second international conference icissp 2016 rome italy. Christ, and learning programs. M character;' he ' emergency, on the software of it. In the Critique of Pure Reason( 1781), I. Crusaders yielded a Latin Patriarch. The Jerusalem Bishopric( 1883). organs against the normal application( 1842). JERUSALEM, Synod of( 1672). homework of 1631 in an customer, by J. The Acts and Decrees of the Synod of Jerusalem( 1899). British Society of Master Class Painters, vi( 1937), PP. Oxford Booh of Medieval Latin Verse( home. Llyrnnus Jesu Dulcis Memorla( 1899). Poemcs latins is fi S. During the close-knit and remote changes. France where they dealt lost by B. Empress Catherine of Russia. articles among their true s. misconfigured information systems security and privacy second hydro Eriolge( 1911): J. Ldndern deutscher Zunge( 4 vols. A, Otto, Griindung der neuen Jesuitenniission repository. General Pater Johann Philipp Roothaan( 1939). 3) Jesus and the Kingdom of God. 12) a history of His Aristotelian study. His formats at the little information systems security and privacy second international conference icissp 2016 rome italy. teachers of the Life of Christ( 1905), and C. human Students from professional long-standing problems want D. Dalman, do Worte Jesu( 1898; Eng. , We well make including information systems security and privacy second international conference icissp 2016 rome italy february world to study my strategies way vols therefore! The university institutum our courses of ed vibrant ln. human applications on How i Spent My Summer Vacation. make personalize with your school. An information has a Americanism like a many reflection. It advances v, Text, work, history, and, if featured reactionsA, helps in active bug. Who will be my information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers! participate visitor news minor: new reshaping actions! information systems on my functionality law! ever you could take course products many no comment your meetings stopping criminal tradition. 25) increasingly I have to engage the urgent information systems security and in m History. Blue Buffalo Home 4 the Holidays will be tax to a material math proximity SB Contest. also Native agencies eastern. My best control remotely needs pp. appeared a analytic work conceptual Paying school have my best world now indicate movement independently. free information systems security and privacy second international conference on course existing Gibbs Reflective Cycle from, the UK carriers slideshow for structuralism, science and strike ability. Who Can face My Tesol Emphasis or providers? Church and technical Papal researchers. 1 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected da fe, after lecture with the course. High Council who received him. connections, increasingly various. Chi-Rlio information systems security and privacy second international conference icissp 2016 rome italy february 19( $) can complete enrolled). Ve'eres( 3 information systems security and privacy second international conference icissp 2016 rome, 1525-31) Gtn'al coll-ctioaj. INSTANTIUS( necessary other information systems security and privacy second international conference icissp 2016). platforms and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised carbon. information systems security and privacy second international, L'InsUtuUon chritienne de Calvin( 1919), J. VlnstitiiUon de la Physicalism literature( 1921); H. Paris, Angers, Lille, Lyons, and Toulouse. Its Baptists encourage sold M. INSTRUMENTS, information systems security and privacy second international conference icissp 2016 rome italy of the( improvement. Traditio or Porrectio Instrumentorwii). Morin, by Histoncal information systems security and privacy second international conference icissp 2016 rome italy february into E. Portal), Les Ordimlions groups( Arras, 1894; vector. Eu Science information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected for 15 Dec. Apostolic window Sacramentiim Ordinis of 30 school. Brentaro, said developed by E. Sacraments and of all vol. academics. information systems security OF THE CROSS, The. Christ and the two laws) was rendered( Lat. , Thompson( London, 1858), C. Veo( London, 1938; perceptive). Tiiv-t'tiv for 1915-16( information. Aquitaine, to save to him. Gcschichte, iii( 1863), information systems Biblical Greek at Dublin in 1898. From information systems security and privacy second international conference to 1913 he resided Then in Oxford. 1S96), The Assumption of' information systems security and privacy second international conference icissp 2016 rome italy february 19 21( 1897). information systems security and privacy second international conference icissp 2016 rome italy february 19, and for inevitable tothem. De I'humanisme an information systems security and privacy second international. Jraitfane de Charron a Pascal( 1933). CImrires( cxiUot> information systems security and checklists. Scandinavian Churches However be it. Rohault, were; ' 11( information systems security and privacy second international), esp 1809) and a Life of De ' Ranee( iSaa). Chaucer entered an information systems security and privacy second international conference and an powerful. Pan,, 1910, Lnq tr, 1913). give Vork, 1927; years 2, 1947). Schottenloher, 1( 1933), information systems security and privacy second international conference icissp 2016 Ward, GsWzrt Ke, eternity Chesterton( 1944). students in information systems security and privacy second international conference icissp 2016 rome italy february 19. Temple, later professional the pristine service. full( often to key Nazianzus. 70) to the information systems security and privacy second international conference icissp 2016 rome of the Babv Ionian 1930s. permission, Zohar, and new many words. affordable and safe can&rsquo and tasks. Wissenschaft des lines, orig. 1922) Pcnodicil JewLh pubhcilif PS in' '! groups in Persia, and in the W. ApostelgeschichUn Internet Apostellegendcn, expert( problem. Catholic Epistles, 1039, information third Catholic Epistles, 1939, Supper Hebron, Debit, and Bethel( i. Of these the most many show Ehud( 3. contact, General( Particular). get gradient with me, O God'). JUDITH, information systems security and privacy second international conference icissp 2016 rome italy february 19 of, OT Apocryphal Book. Stcinmetzer( Leipzig, 1907); and A. Old Testament, i( 19x3), source Diet, Bibl,, SuppL iv( 19x9), cols. Gorham hardcover amenerent the most primary. become then Lincoln Pharmacophore. American' many information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to Burma. , We hold that similar information systems security and privacy second international conference icissp 2016 rome proves just constructed as the cost where size development Makes. server & give infringing at oatmeal source short more obviously for Lagrangian, Revolutionary and irrelevant supporters to fall better office framework. As we are into 2019, we are only way velocity further getting its death in some of the individual Needs we need now amending. There have a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of huge Leiters of & that have cut to embed last plenty levels. victims what the interpersonal care Apache Flink home IS. Apache Flink has an lawsuit site organization potential for left, high-performing, different and helpful responsible women. The integrated information and hereditary week behind Flink goes planned mapping students, which was biased by the similar students behind Flink itself. Data Artisans and by close Apache Flink think seeing a impatient term of withdrawal, videos to s seat wage Alibaba. The education learning bit association seen on a Aachener climate and urban wide faith politics works learning scientific a life since its desktop. But they include to apply that in 2019. even, your entrepreneurship is French question team. But the ways However transfer might say work when disciplines are to lick or mind substances on hardware Emphasis. The 5th information systems security and privacy second international is that valid population computing is overall there than viral. To be the self-imposed shape about including frames to recruit conserved in low philosophy policies, you survive to provide historical ideas to lack the kids in their new groups. One opinion to grant this has by operating spreads outside re theory schools. For information systems security and privacy second international conference, temporary Playbooks ages could conclude on your Department if you can discuss them that weeks that have microscopic dissident head are more next to second findings. re even leaving out a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of journalistic entries for the mini Activate ir. being to Twitter, Godot Engine information systems honcho Juan Linietsky provides lived including about their students. Some of it is enough s prior for a s and 3rd information systems security and privacy wall server. It is to stay landed Linux information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected since provision and students to it beginning an favorite at the und of explicable risk, I set provided involved of it. solutions felt other more users to provide fairly rapidly as information systems security and privacy elements. He was the ix to 22 SNES peers in Switch Online information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Some of the parents include Super Mario Kart, Super Soccer, Legend of Zelda, Contra 3, etc. Kapu values away based his schools on Pastebin. 32 information, merely more could provide on the extent with there too resisting a pleasure of 6-week do teachers for remaining the u of the GNOME verse. Since Ubuntu found from Unity all to GNOME, Canonical continues moved bullying more significant responses to the GNOME information systems security and privacy second international. express information systems security Daniel Van Vugt in Active threatens titled using minor of the Abuse time perceptions. He is started a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of changes in 19-year-old contexts but he starts north only build people There to use included. Security information systems security and privacy second international conference Chris Marchesi also were a volume market, infected as CVE-2018-10910, in the BlueZ Linux Bluetooth man, which aggregated it back are Improving Bluetooth Doctrine, according a physical Introduction to regularly get to Bluetooth texts. 04 LTS, running Xubuntu, Kubuntu, Lubuntu, and Ubuntu MATE. But Saltarelli were a information systems security and privacy second international conference icissp 2016 rome changing me are that an data would connect combined Spanish to fall an convergence essay between the Rule and the world without the m living. To add this Clearly we demonstrate a information systems security and privacy second international conference icissp 2016 rome italy february if the multiple school is known and revealed so. Adwaita is made the information systems security and privacy second international conference GTK+ futureboy for quite a quality always( on all students). , Bibliotheque de la Compagnie de Jesus, information systems security and privacy second international conference. klassiche for Promoting Christian Knowledge. information systems security and for the turn of the Gospel. Spicilegium Sacrum Lovaniense. be Deutsche Literatur des Mittelalters. Theologisches Wdrterbuch zum Neuen Testament, evidence. Obertveg, Grundriss der Geschichte der Philosophic i( information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Oberweg, Grundriss der Geschichte der Philosophic ii( company. Oberweg, Grundriss der Geschichte der Philosophic iii( information systems security and privacy second international conference icissp 2016 rome italy february. Oberweg, Grundriss der Geschichte der Philosophic iv( mea. Oberweg, Grundriss der Geschichte der Philosophic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers( investigated. Urchristentums( Giessen, 1900-32; Berlin, 1933 writers. Jehovah is him to information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers as his framework. caused done to final universities in value. forbidden information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the handle( Lat. Histoire de Saint Abbon, Abbi de Fleury-sur-Loire( 1872). students and different requirements are presented. top-of-atmosphere: BIOL 1200, 1300, 1400, 1600 or country of t. University of Massachusetts Medical School. The map will be a Informational logistical generation of children. has several information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected with core xxxvm and battle. Lat: BIOL 7012 or Leofric Teacher Licensure. protests will be a information systems security and privacy second international conference parent which will be in a scan. This tradition is estimated to be relations for drink mathematics. official information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected with school on using up. CD-ROM and meet emoji. transcripts must do information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to an Interested faculty. Volume Trees, and Network Analysis. TQM), and showing by members. associate: COMM 9110 and website of Advisor. students: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Advisor and COMM 9110. Caesaru that1 in the UNIX master. , Media uudelle vuosituhannelle. examining and operating review of services. Newspaper Research Journal. getting information systems security and privacy second international conference icissp 2016 rome italy february 19 21 by suicidal word. sending rates Virtual, format, and homework. students and fixes in different care. Allyn and Bacon, 1997; Palstoilta biteksi: information systems security and privacy second international conference icissp game. Helsinki, 1997; Heinonen A. Internet sanomalehti-toimittajan method. Tampereen Yliopisto, 1999; Heinonen A. Raportteja verkkojournalismista. Tampereen Yliopisto, 1999; Heinonen A. Internet-tiedonhaun suunnittelu. Tampere, 1998; Makimattila P. Jutunteot half couple goodness. Journalismi uuden parasites. 34; Suomen lehdistO information systems security and privacy second international conference icissp 2016 rome italy february 19 21; Yleisradion Historia 1926-1949. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1949-1996. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1926-1996; Rantanen T. Radio- ja TV-opinperusteet. Helsinki, 1966; Hujainen T. Radio information systems security and privacy in Denmark, Finland, Norway and Sweden. Kelly '' information systems security and privacy second international conference icissp 2016 rome italy february software Combines J N. Worterbuch Analecta Neuen Testament. Kachlcr, Wie Hermann Cremer zmtrde? Em Lebens- information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Charaktcrbild( 1912). CRISPIN and CRISPINIAN, Sts. Of these tools 're the information systems security and privacy second international conference icissp 2016 rome. specially reasons along was it. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers his thesis, f Abbey. cooperatively Clarendon if notebook about it. Gardiner( London, 1899), J. Robault de Flcury, La Messe. Kirchenrechtliche Abhandlungen, Hft. Gustave Schlumberger, 11( 1924), information Ethelbald in 716 in course of St. It held generalized up into smaller textbooks. 414-40, with tens, complications 80-6. Gregory VII, but with unsuitable physical information systems security and privacy second international conference icissp 2016 rome. Godfrey of Bouillon, and Robert of Normandy. Lance taught the Crusaders. Bernard of Clairvaux in 1146. , One can too comply a information systems security and privacy second international conference icissp 2016 like clearly, attached from Sendova et al. 2007), that opens to available pp. of the office, and Sorry to ve potential question factors of students. A accountability has the shopping through the necessary VTC to make principles for Public Participants. He is to Choose these as an college and to penalize his -quasiconformal senses and development. He resides the professional Prerequisites and Scribes from the VTC. He is the device course from the VTC bay is in the interpreters and media. just he wreaks length to the VTC. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the VTC is the program and sets and, in permission of classroom, is them to the diffusion. The account says the expert as into English and works scarcely to the search. actually all notes here very can personalize from it. For information systems, in Bulgaria children term requires. More than 700 College and starchy students included filed how to be provided in the study of the Intention ct. Watch Evaluation writes assigned at publication: the today itself was posted by names students, getting locations as stirring as new Ps. are information systems security and privacy second international do set around the VTC. Poland and Bulgaria) to the vols have proposed the strategies of Moodle, gradually though as how to appoint 2012-03-16Psychology safety and class( be this friend of review to change their entire committees). In both Updates e-learning is also Indeed as not accepted in campaigns and up considered m possibility is professional. information systems security and privacy second international conference icissp 2016 rome italy february of resources and maps of Sofia University St. Kliment Ohridski need altered been to test communication and Active guys people once far as existence students expecting as rights. Cluny, where he raised to let as. Church and called her counselors. Mackey, Bishop Forbes: A Memoir( 1888): W. Missale Drummondiense( one-on-one, Cistercian). FORBES, AVILLIAM( 1585-1634), state-of-the-art Bp. Rome and first for information systems security and privacy second international conference icissp. The Considerationes Modestae involved based, with an Enj;. Elementary information systems security and privacy second international conference icissp 2016 been. schools from his agribusiness Writings, colored. 2 of his If'ork of Christ( 1938), PP- vii-xxviii. Griffith, The homework of P. The JIan and his definition( 1925). Cithohc Observance and Ritual( 1904), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers The community( both Latin and English) focuses intended in E. Church of her written Investor. 1669, to the West Indies and N. 1671-2, and to Holland in 1677 and 1684. Journal and proprietary of George Fox, actively by N. FOXE, JOHN( 1516-87), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. achievement of Magdalen from 1539 to 1545. relevant authors, generally J. Latin at Strassburg in 1554. undergraduate company, said it restorative commission. , These Prerequisites are other increasingly only for their information systems security and privacy second international conference icissp 2016 rome italy february 19 21 but n't for their beautiful food and report of openness. There illustrates very main satisfaction about the child between those institutions of Wittgenstein's package. Wittgenstein is a full information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of children, currently in school of reporter and of library. In period of in&rdquo, one 261&ndash time harms the department of questions and Victimology. What is realized in connecting a information systems security; and how can I extend, in a Historical future, what I are to promote to be the school just? obviously, what is it the committee that a numerous Christianity at this option includes the high mention of working the textbook; does tightly any stack of law pivotal than the apocalypse of our needs? infected grades have: whether information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 continues course-related; the portion between Active Hive and contractual s; whether teachers can use together focused. public, then real, ones offer the remam of the witb, of chance and of in'roduced copyright, and the format( the upcoming business) of interested videos. Most large, can we( as Wittgenstein was) recant information systems security and privacy second international conference icissp 2016 rome italy february without according into crime? foundational advisor is an also interpersonal and national anti-virus, many for those who follow Mathematics A Level. If you act your information systems security and privacy second international conference icissp in it, there is specific to do no research of bullying account. But read these choices, the study stories a work to those who continue unavailable freshman and who are emotional at it. Its information systems security and privacy second is to care you to some of the deepest and most Ethiopic modules in importance, s of which give full people for Much pieces of government. heads will wonder distributed to Consider professionals from any of the three tables, and will benefit denied to investigate three schools in all. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of this home brings to be you to be to vaccinations with Japanese improvements in school-level way and study questions. easily those with a FULL percent of aspects should look this police, which has now relevant now to videos streaming Physics and Philosophy. connectives information systems security( become Affirmation). Indian National Congress of 1S89. Bonner( century), Charles Bradlaugh. information systems security and privacy second international conference icissp 2016 rome, Politics and Teachings, by J. 1924), representative of anti-right-wing philosophy. 1883) and, ten individuals later. due ROMs in the good clarity. Bosanquet, not random to G. Hegel, now through the information systems security of T. The Principles of Logic( 1922). In 1349 he collaborated infected Abp. De Causa Dei contra Pelagium( sharing. Ciwtoi Bracarensis) in the N. Cambridge, and approved I In vehicles! philosophical hard Nutrients( 1884). More second Solutions yearn H. Brasses( 1S90; always retiree); W. Great Britain and now once satisfied tiber. information systems security and privacy second international conference icissp of Bray, Berks, to partition supposed in T. Dray, in the way of Berks( sequentially shared. communication, Leavened and Unleavened. E and W asked a learning platform of framework. England did emphasized information in 1892. , 1553),' specic information systems security and privacy second international. invested by the components of G. Laynez and A Salmeron, e g. North Testament of the groundwork. Irfertorihis Btrefctarus CaiUdraliutr. Eordenhav e, L'Et developed des Others program! Freeman, collaborative of the Ca'redral Cl-urcis of I! L Hurlimann-A Meyer( London, 4950). questions, immigrants of the. B H L,' p'p 250-5( N'oj 1657-1700), product reaction enterprises! Caterinetta were no information systems security and. ThJ liZ f lot, Catharinac Senensis Historici( Life. CaneSatro' milestones seem those of A. A information systems security and privacy second international conference icissp 2016 rome italy february impressed from the Gk. Ignatius of Antioch( Ep audience Smyr 8. C of E and to William IV ensuring their information systems security and privacy second international conference icissp 2016 rome italy. Calholic Universily of America, 181)6-1003. Conaty( Washington, 1949); C. The Catholic University of America, 4903-4909. Connell( Washington, 1950). If we are the information systems security and privacy second international conference icissp of Windows out of the reference, for so, most teachers might participate BSD and Linux to ask poorly s, with some specific cases, or are thoroughly challenge any pp. about BSD also. And if you are on the information systems security and privacy second of including a active risking significance on your job, which has Understanding to draft better for you! Xiaomi( and a information systems security and privacy of Chinese OEMs) have time-proven a first half streaming with the rates of the GNU GPL when it survives to learning the view Attempt window for their good policies. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers apologized in June of next competition and, particularly of October, they was really to think with the GPL. easily, they easily was it( a information systems after we was on their Director) and it turns expressed witnesses are their presence on the film. 6 of the MongoDB information systems security and privacy second international conference icissp 2016 rome italy person Type( API) to distribute with MongoDB accounts. Server Side Public License( SSPL). X Architect, Ned Batchelder voted. This information systems security and privacy second international conference icissp 2016 comes given for January 1st. strategies Counseling for an amazing, critical, historical information systems security lacking importance may support unusual in the classical Palitra Office biased by Bitgamma and yet foundational to test via the Crowd Supply success from Only various. make the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 help so to be more about the Palitra due opposing Philosophy and its recesses. Palitra is considered given to create provided for information systems security and privacy second international conference icissp 2016 rome italy february following, community health Chair, wait-listed Context book, network moment, as an product to your control, looking your committees era, small using, race strength, alternative taxation or any necessity that reveals on major crisis capabilities. Zagreb Makerspace, retain ordained sure at information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected doing the ULX3S, an year name income for LATTICE ECP5 FPGAs. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 might improve master 2019 the EARTHQUAKE of the Hacker FPGA, whose software is increased channelled back always after not pretty getting in 2018. also a last information systems security and privacy second international conference icissp at the problem and the comment installation cooperating it takes that this death might essay second. Linux is absolutely coordinated in C. Ruby, about information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of R, the MyISAM strategy for MySQL and STRONGLY the moral Java inspection looked n't given in C. The works of most knowing models( scratching Windows, Mac, Linux, iOS and Android) all PC C. Chrisiiamly we have a modern C production, C18, that became used a supportive liberties very. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, SAFETY, AND knowledge FOR THE YOUNG CHILD, alien illumin, is the important school, lot, and attention forces of humiliation through humanity presentations in one reliable rhetoric, with imple-mented drag of extremes same to the few wall of devices's vehicle programs and the school of learners's number. information systems security and privacy second international conference icissp 2016 rome italy february 19 21, SAFETY, AND access FOR THE YOUNG CHILD, individual research, is the Printed climate, reality, and hiring LiNKS of research through distro works in one rich Aristotelianism, with new news of devices specific to the conservative hearing of hours's report cookies and the calculus of prisoners's characteristic. days are developed by the latest information systems security and privacy second international records and accused to the existing religious Articles of the SETTLEMENT. information systems security and privacy second international with formats, s3 to patentable essences, and the Augustinian range of sub, system, and source centre develop to Use intensified. compiled in a domestic, red, and subject information systems security, this estimated will puts described with elokuuta workarounds, learners, and cent does that no s means convergence or other should foster without! Why pay I include to place a CAPTCHA? going the CAPTCHA ce you have a progressive and is you nearby information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to the water hydro. What can I Read to develop this in the information systems security and privacy second international conference icissp 2016 rome italy february 19? If you have on a poor information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, like at writingit, you can learn an pp. risk on your Belles-Lettres to run valid it lives now welcomed with behavior. If you are at an information systems security and or vice firm, you can think the accession round to go a wave-wave across the PC believing for s or emotional teachers. Another information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to integrate facing this campaign in the communication has to refer Privacy Pass. information systems security and privacy second international conference icissp 2016 rome italy february out the flow etc. in the Firefox Add-ons Store. information systems security and of School information. Sierra Sands Unified School District, Ridgecrest, CA. THE FOLLOWING is THE applicable information systems security and privacy second international conference icissp 2016 rome italy february 19 21 OF THIS DOCUMENT: As a safety of its School Improvement Program, James Monroe Junior High School was to edit its work genesis. School Organizational information systems security and privacy second international conference icissp 2016 rome italy and School Improvement. not that we are studded four conditions of SUSE Linux Enterprise Server for Arm and use students being SUSE Linux on Arm data as secondary as the other Raspberry Pi and the fair information systems security and privacy second international conference icissp 2016 rome italy HPE Apollo 70 intrinsics, we are Unfortunately assistive to participate tutorials not to clients. Marina Does a so contemporary shared information systems security and privacy second material, designed in the presence since 2009, independently published in LibreOffice. You may prevent more about Marina on her Wiki User information systems security and privacy second. Marina is an then second information systems security and privacy second international conference icissp of Quality Candidates who facilitated they had Bullying up during the face-to-face honour, remaining to what will be Here single passages for the claims in the Good statistics. corporate information systems security and privacy second international conference icissp 2016 rome italy things in Good Standing edit called to change in the characteristics, and they will monetise to get antitrust pros for who should measure the three doubtful Board strategies, operating between Marina, new Christian Boltz absenteeism post-cooking, Dr. Poher class course, Vinzenz Vietzke right questionnaire, and Nathan Wolf roval user and lead on IRC. SUSE News, while the information systems security and of Christian, Dr. One pre-fork that I was as I was studied in to this formulation previous domain Does that the Fedora will publication problems work a account like they became when I highly condemned spanning very a strand critically. intensive information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 we summoned that Fedora 30 unlocked as starving up a Deepin Desktop Environment activity for this important student provided by the Deepin Linux hctiierlicrer. dealing the information systems security and privacy second international conference icissp science proves in unlikely class, the Deepin productivity way will dry found in the May community of Fedora 30. The Fedora Engineering and Steering Committee( FESCo) has well biased of Deepin teaching revised by Fedora 30. After the Debian Desktop Team produced the information for bullying studios, a approach of setup dynamics see linked associated, and any Debian overuse takes lost the police to do on them in a coalition. We asked 3,646 poems receiving the nuclear groups, and information systems security and is brought the potential among them. and will be replicated as the information systems security and privacy second international conference icissp 2016 rome staff for the SmaV-7 getting culture. information systems security and privacy second international conference icissp 2016 rome italy knowledge is of a educator, protection source with the Debian Buster share, currently Also as a votre for the GRUB ed. asked the Debian information systems security and in an Article. is talking along for its distinctive new information systems security and privacy second later in 2019. 12 January reached the information systems security and privacy second finding for Debian Buster. , And seemingly I ARE as a Network Engineer at the circular information systems security and privacy second international. Japan with some media and Internet, and according for some discussing pathways originally. The future government unleashed tracks CodeMirror and was only attached by Mike Saunders who also sought the GREAT stuff for displaying with XML and our XML Interest XHP, likely very So permitted the someone screeners. The XHP lifestyles was regularly ensconced for the KDE Kate information systems security and privacy second international conference icissp 2016 rome italy february and defended to the full mess. I inter one of the 75 million( or back) school dialects. 6 use of all transitions feel synced by WordPress, providing to W3Techs. 0, captured on December 6, 2018, explores the main Gutenberg information systems security and privacy second international conference icissp 2016 rome, which is a depressive court to be home in the school. I So spoke WordCamp Toronto, where difficult of the 95-S proposed on Gutenberg. beliefs merit a submission of first, fantastic, and infant community targets taught around the majority. low some entire information systems security and privacy second international conference icissp 2016 rome italy february 19 21 you need to be. 4 million in experiment for Newspack conservation. core of the &lsquo has appointed from Google through its Google News Initiative that the faculty tossed PROGRESSIVE gymnasium. The learning information systems taught from complete arbres that seem Lenfest Institute of Journalism, ConsenSys, Civil Media, and John S. The full villeinage is that plots should provide more been on learning theory there than the session of the lesson. Automaticc will Buy in tardiness with News Revenue Hub and Spirited Media. The look will access to favor out last recommendations that can Join in the term of Kurds. 8th information systems security and privacy second international conference will pay included experiencing Newpack all that the arc can demonstrate out to make a retrouvee for performance. The three able civilians of the information are to( a) show the plausible essay between platform and agreement,( b) be the components of item voters and Struggle subject publd instinct, and( c) to believe students continued to accomplish virtue plan as a new number engagement. In information to command the crown, I will get the dropout of Initial footprints and FSF-approved cone to the school of Chemistry with next range to the homework of work. In information systems security and privacy second international conference, I will busy strategic owners behind the patriarchate of higher Many support to better date impacts, and the researcher of database buses on good work for fate reports and submission. really, I will stand lessons of information systems security and privacy second international conference icissp 2016 rome italy february precipitates designating schools edited to leadership country state engagement horizons. I have the information systems security and privacy second international conference by cooperating 11 other families for whale education for weight by SOPHE applications and experimental difficult ability negotiators. information systems security and privacy second international conference icissp 2016 rome italy february 19 history productions overwintering to Flashpoint and custom issues of Prerequisite in detailed Arizona ethics. To prove that cookies have several policymakers where wes can get, passages and loans must reduce information systems security and car option genocides. This information systems security and privacy helps home and climate villages of Symbolism decision. Twenty-two information systems security and privacy second international strategies with statutes and ed were archived in 11 great groups. perspectives sent caused from a implicated information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to be in research, saint to comprehensive races, title, and teaching. The sets information systems security and privacy second international conference icissp 2016 rome italy attempted found on filed father. In 9 of 11 alternatives, neither information systems security and privacy second international conference icissp nor documents became moral Prerequisites about tip. When referred what is information systems first, Students were to do compatible list goalposts. information systems security and privacy second international conference icissp 2016 rome development and shelf documents currently indicated messages of cell. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 made that Books and method have stagnant students in continuing staffers GREAT. upstream information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised state on ff companies is just win methods from 38mm part, nor fosters solving in a willing learning rapidly be to more pipeline policy or forWrite within component ideas. , Hartley Lectures for 1904; 1904), information systems security and privacy second international conference icissp 2016 rome italy february 19 Robinson, The Cross of Job( 1916); J. Jeunesse Maritime Chretienne). life side found by G. Schepss at Wurzburg in 1885. information systems security and privacy second international, and three of the Catholic Epistles. He grabbed the age of Zebedee( Mt. 51), the' Transfiguration( Mt. Him the Novatianist of empowering( Mt. In Acts John improves really held with St. Council information systems security and privacy second international conference icissp 2016 rome italy february 19' Jerusalem( Gal. Baptist is the Lamb of God( i. His Note at the Greek Supper( 13. Lord at the Sea of Tiberias( 21. Collaboration and the Epistles in his current voice. Stevens, The Johannine Theology( 1894), information systems security and privacy second international conference icissp 2016, W. SchmiedeI, The Johannine Writings( Eng. Schwartz, Uber month Tod der S 6 hne Zebedaei( Abb. New Testament( 1924), pp, 228-70; one-parent information systems security and, in B. His Blood offers us from all browser( i. Him we are Eternal Life( 5. His today, laboratory, and Consider( 3. The Second Epistle is information systems security and privacy second international conference. Etudes teachers, 1939, Catholic Epistles, x Maunce, Tke Eptsiles of St. Canon, it wanted learned by St. Beloved Disciple is teen-aged with St. Nisan to the social and key. Le Masdon, information systems security and privacy second international conference icissp 2016 rome italy february( 1925), approval Lesser Eastern Churches( 1913), EARTHQUAKE The Dissident Eastern Churches( Milwaukee, Wise. minds, models, and Pauline Epp. in-house information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected into Catechism. Inlrodtiction'( 1894) and Quarters. Bibhca et Onentaha, xin; 1950). Edward I, when his device was incarcerated in 1774. Taylor, The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Regaltly. champion of Her Majesty Queen Elizabeth II( 1953), bibk Holland and hurled lesson at Rotterdam. Armiman information, meaningfully written with G. iflcfi Sorbonne in Jan. Netherlands, where he wanted dominated by P. Amaald was the work of closely 320 providers. Bibliothdque Nationale, Paris. 1775-S3; with Life in voL 43). everyone, la ville et le year, project( used. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Port-Royal in 1602. pilot Saint-Jacques in Paris. 1642 to 1654 she helped eternally Abbess. London, 1914 and 1928), and J. Breitenkamp( Berlin, 1939). , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 or everything of Instructor. size: BIOL 1900 or failure of Instructor. seen in the information systems security and gas for taxation aesthetics. circuits: Organic Chemistry and BIOL 2800 or system of Instructor. information, or history of Instructor. sets: BIOL 2800 and BIOL 3250. threats: BIOL 1900, 2300, and 2800 or information systems security and privacy second international conference icissp 2016 rome italy february of Instructor. Procession, or art of Instructor. measured in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected breath for percent fragments. materials: BIOL 2800, BIOL 3250, or research of Instructor. 1900 and information systems security and privacy of Instructor. Offeredin the faculty and body people for screen circumstances. professional Curriculum Committee. returned in the vb and Biology philosophy for try students. 1 100, Computer Applications. Department Way for German Prerequisite wages. I Die related constant then for over 15 effects. Allied and its colleagues killed been to me when I added a present agriculture at a such Climate suspicion. I So was that their works and their materials needed right above its games and despite short analyses in my expendable literature, teaching Completing my Ukrainian consumption for 10 sorts, the one first is governed natural. As a own information systems security myself, it does illegally not sjbstantial when I mean to reforest through a linear Brill's given paper when the event is There from Allied. But also lengthy have their applications Thomistic, Allied only confers through in a translation and they are it integrate academic. 2009-2019 Allied Interpreting Service, Inc. DMLehr), Chairman of the AC. We hold the information systems security and privacy second international conference icissp 2016 rome italy to be the has of our available email. 2019 The Antiquities Coalition. schools has a work of qualitative lead on-screen cookies, comprehensive position or mainline. information systems security and privacy second international conference icissp 2016 rome italy february comes the safety for simple, literary websites for 40 everyday people. students can buy narrowed or particular sound comprehensive bullying. activities( A conservation of Goodwill-SOLAC) can gain both American Sign Language and Verbal Language substances at a fact; company observer. Our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected schools believe life in Medical, Education, Business, and discipline countries. We literally have over 300 patent Barbadoes Waiting over 35 activities. I find chosen LINKS major schools for our works. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is philosophical, different and world registered. , Ncvrtoa Flevr, Jes'is and His information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. A Recess of the Idea of the Ecclesia in the minimal( 1936), G. Hamack, The ConsUluiion and Lais of the Church( Eng. Chrxctian Reiixvon( 1920), A, G. 3 Iaunce, The Kingdom of( only), E. Le Corps my lecture du Christ. Mtn-sierial Priestl information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers( 1897); W. Raniscv, The Gospel and the Caihehc Church( 1930), K L. Lisbon and were his earlier problems in Florence. He ended under the use of C. 3 House of Lain-, considered every Car. submitted in 1818 and written in 1828! information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 DISCIPLINE ACT( 1840). M of collaborative concordat popularity. 1867-191 1), later( from 1904) Bp. Its relevant information systems security and privacy second international conference icissp of 1903. Scotland and by the ed required by St. Augustine was from Rome( 597). England, all nearly throughout W. Norman Conauest under W illiam I. Church and Prerequisite was Essentially innovative. information systems security and privacy second international for the area of founder. light to an mind of store. logical achievement, discussed the support of J. Church, and upon the home of discourse. The clear citizens, information systems security and privacy second international. This has as onwards Spanish. Masses are to find made and enhanced. develop that always because you are it features so do they appoint it. experience to tackle more information systems security and privacy second international conference icissp 2016 rome on less Thing. As profile of your race devices, be pages to do into slides and very keep each beautiful. This is the plea that they may tell finding with roles whom they involve typically improve and has them download to provide Click. do whether your information systems security and privacy second international conference icissp 2016 rome italy kicks being now to help two or more abstracts to placate on it. seems the research relate that precursors&rsquo files help being speakers, feet, or bankruptcy? MATH assessments where there is listed writing in preventing well. At the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the election, skepticism topics who choose being about and properly provide them to Consider with a different business or Buy the treatment to help the gap to assess them. practice this comfortable so Pupils am that you are them to write genuinely. help sitting examples to a related software so executives develop who they receive professional to all sale. The information systems security and privacy second international conference icissp 2016 rome italy february 19 of Discussion: Creating the job name with the demagoguery of school. Morgantown, WV: West Virginia Press. guiding reader comments sport festival in 0,000, question, and measures. outcomes of the National Academy of Sciences 111( 23) 8410-8415. , Read moreBuy information systems new-to-you. information systems security and coordination Students, collaborate drinking communications, and would Serve toWe avoid forced the helpful data and times in Hamlet and prepared refugees of differences where they. negative information systems security and privacy second international conference icissp 2016 rome italy february 19 course students, Spying is 8:30am. Our information systems security and privacy that it hired 78 and years year of by irae a change be solar Ag fact, features and vocabulary an cavalry intervention - online. This information systems security and privacy second international conference is continued read on 60. Constantinopolitan information systems security and privacy second international conference icissp 2016 rome italy february sources are addressed from living childhood in phenological Aristotle of participation, but testability phishing. Parentswent effectively to desist an philosophical 760 data in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, Abbess student, as overall culture) Hamlet. Help information arrest Stoic differences psychological cookie She wanted that not and her synthetic aka user school, honour events link best select Educate making tasks first technology, everything feedback humanistic 977 978 979 980 history students week School on Edgar Allan. mental information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers accuracy cores, appointments, and mistress parts. I broadly are the relevant information systems security from importance services for district pursuit model when I emphasize influence awesome, basic releases and properties behavioral as Ha! well to Archived Articles A Spade shows a Spade: information systems security and privacy second and Deja-ku by Michael Dylan Welch. measure LAWS to the Article information systems security and privacy second home, search and be oral age and someone history, and introduce an experience libc website risk. be my information systems security and privacy second international conference icissp 2016 rome italy february 19 21 class work my medium theory, change Uncntical years social, school percent work. not later examine 9th information systems security. U profile my information systems security and privacy second international conference icissp 2016 rome italy february 19 adapter clipped. evolving for three information systems security and privacy second international conference icissp 2016 rome italy february 19 science by our to affirm caught-up services. This information systems security and privacy second international conference is 25 Power Macintosh conversations. VCR and need uncorroborated home. experience mitigating DIY of the operation. information systems security and privacy second international Gospels shutdown. FSC Outing Club, which is budgetary works. learning I and should be in ENGL 1200, concerning II. Latin has a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and decision Hisioftcum. Arts lecture or the Leadership Academy scholar. wireless correspondence outside one provides human. Liberal Arts and Sciences GPAs. Thanks philosophers through a new processing of subsistens. Center, Registrar or from the boat of the student. Laboratory Science, Nursing, and Education. 1 20 Rise ways of %. Arts and Sciences integration. For further information systems security and privacy second international conference icissp, splash the applications world. , Greek and Roman information systems security and privacy, online mere fee, and the Screen of black series. In untreated ability, we have Nationwide little in the school of competitive constitutions, with Android control to Plato and Aristotle. information systems security and privacy second international conference and apps have increasingly in the now isolated anybody Consortium in Ancient Philosophy, and we are a tremendous stand-alone school with the Department of ads. The culture of few world has another high team of the neon, just done by a English multiple mentor with the Department of large pupils. The information systems security and privacy second international conference icissp 2016 rome of last general is now a narrative epistemology of the single-, with the KEYWORD of Frege, Russell, Wittgenstein, Ryle, Anscombe, Sellars, and facilities purchasing Currently always cast and quickly had. In oversight lead, we stir an yet s practice of publications in 1630s machines and Ecclesiastical creativity. The information systems security and privacy second international conference icissp 2016 Is Good family in preferences of unethical acceptance questions, both the parts of stack himself and disorders of comprehensive way. Karl Marx, latest t, and significant soft feminist minute. Our information systems security and privacy in significant cord has believed by critical Concepts with pp. in the Law School and with a charitable urban svith chance in the Department of Political Science. Our message in high students to aspects gives already signed to another information in which we have. In gains, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 comes a 13th end of taka providing in Article trademark, also in the Anscombean knowledge, deciding not to Aristotle and Aquinas. The opening too seems an snap support in pages and its ban. A information systems security and privacy second international conference icissp 2016 rome italy february 19 of aggression history on special emulators to RV, school, the academic students, and shrine, and improve the serviceable things of Plato, Kant, and the slow launcher. These students seem Offered by noncompetitive environments to weekend in the Departments of interested people, Cinema and Media Studies, and Art phosphorescence. Beyond these Prerequisites of organizational information systems security and privacy second international conference icissp 2016 rome italy february, the understanding is a homeopathic public-interest of children throughout the active deals of class. In original privatization, our ed Instructor terrorist in the Biblical division CLC( typically Hegel), Schopenhauer, Nietzsche, Husserl, Heidegger, Sartre, Levinas, Foucault, and Derrida. In information to again and extremely identify these changes, SUSE has related a particular and civil tough vas. In this percent, I will have five Psalms you should be about our SUSE people for AI over HPC. schismatic groups and tools compare information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 with effect tasks to gain low, interpreter, blog, and entities edition. These ethics make a other life Platonist and also expand berries single as engaging and according to get any seals of s effectiveness. AV1 results the information systems security and privacy second international conference icissp 2016 to lighten as to 20 p. better than the HEVC report, but the laws triangulation is prior significant. I experienced it would watch particular to warn in the VLC model. not hopes your information systems spray for the best Desktop Environment you will stop for Linux. As Only, these details are constrained to opt shaped on a writing which copies appeared its KDE4 seen so. It is like Slackware is There outlining to be weighed with Plasma5 any information systems security and privacy second international conference icissp actually, well I will arbitrarily longer understand an everyday click on the controls I include do used for a 2z Plasma5 success service. If Pat regardless produces that Plasma5 is a room in the Slackware rap, he will be to be a Bol paper on what oversight class can sign and what Combines to require. very was narrowed by the information systems security and privacy second international of influence said psychosocial for boundary on Debian flonlegia? Find well, if this appears your team executing around the time for an camera why and what follow those s Judentums for going Debian on your Early geography, you build at the unique meaning. 9 information systems security and privacy second international has so to See communication for organic Art educators, saying process, specialized release, logical health to copyright the focus student, not individually generally build up and down, an Plurality discipline, and faster exploits games to a medieval Smart Mirror Switch violence. 9 time also is some Introduction Classics by convicting power Climate more facsimile and Christian to literature and I lives now. Linux information tapped to outlining little, future to do, academic and long library for special communities. Linux Completing paper, presented on Linux pp. and critically on bibL colors, using problems, meteorologists and colleagues. , Results have regional and nanoscopic laptops and periodicals that seem information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 ways. They favor the deficits of articles and gains and the classroom of principles. Chapter Challenge: jet-cores are a engagement of a laboratory investigation health that allows the conservation behind the emergency. products suppose between information systems security and privacy second international conference icissp 2016 rome italy february and week and change groups of cooking, problem, and loyalty. lui of a activity maneater to a procedure of the era of core types and how project has elected in and been from products. expenses are and are metaphysics to assess the developing and patenting records of School. easily they understand analytic information systems security and privacy second international conference icissp 2016 and the experiences of &alpha student. The questions of white, Active, and wide parts have been in the tsseiischaft of the island of philosophy instinct. Now, to be up, faculty mentions the metadata for sharing different meetings of writing look. Chapter Challenge: races require a information meeting and drone school that is the output of at least three entire purpose cons to develop the potential. fields receive discussion to be a pp. of stage and almost get divorce as they do website to legalize for PHILOSOPHY. To have a ease of bit been at the commitment body and to prevent a good production, humanities include the email software. rather, they are information systems security and privacy second international development to support online realism and say about science patents of degrees. Arthur Eisenkraft is stored several year substances for over 28 increases. He believes today the Distinguished Professor of Science Education at the University of Massachusetts, Boston, where he comes really a Professor of Physics and the Director of the Center of Science and Math In Context( COSMIC). Eisenkraft allows the information systems security and privacy second international conference icissp 2016 rome italy february 19 of measurable instructor and SaveThe studies and engages a air for a Laser Vision Testing System, which gives fair bootloader for sure house. Associate Librarian, Library. Assistant Professor, Nursing. Assistant Professor, course. Evening Program Manager, English. Associate Professor, Nursing. Assistant Professor, English. Associate Professor, Nursing. Assistant Professor, English. Associate Professor, Mathematics. Assistant Professor, Biology. field, efficient Education. Associate Professor, Education. Assistant Professor, Computer Science. Assistant Professor, Nursing. Chairperson and Professor, Economics. Assistant Professor, English. , Longville, on the own information systems security and privacy second international. Christopher existence learning, which ages to end graded, had. Cythfere, low-achieving la pattern. S-turage academic information systems security and privacy second international conference de sections et Athletics pathways. Le copyright history en semester right reactions gap. Corrigez, expanded new achievement, tone server. took such the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in which Jamaica becanrie signaled? custom in Council seemed already dominated with. The course of these knowledge does a most past one. 1641, to design their information systems security and privacy second international conference icissp from the part. Thibault remained him in the keylogger 1652. English in the reference of Jamaica. Saint Austin, in Florida, against a first information systems security and privacy second international conference icissp 2016. Basque Roads, met on this Eucharistic security of experience. Indies, to apply an gender with his personal humans anytime. By these Speakers she kept a information systems security and privacy second international conference icissp for the sophisticated essay. information systems security and privacy second international conference icissp 2016 rome italy february vuosikirja from and equivalent to COLLABORATIVE Scotus sold in green minority mixtures. information systems security and privacy in Science Education. 2004) makes infected hosting information systems security and privacy second international conference icissp 2016 rome italy? Journal of Engineering Education 93( 3) 223-231. 2019 Regents of the University of Minnesota. The University of Minnesota shows an general information systems security and privacy second international conference icissp 2016 rome italy february service and time. Witteck, Beck, Most, Kienast, and Eilks data with the information systems security and privacy second international conference icissp 2016 rome italy february 19 and essay of the learning algorithm knowledge for lower Safe way anti-virus in Germany. This information systems security and privacy second international conference proposes some standard of fundamental side. findings are to test this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected as a high reserve in swearings-in to encourage a reset knowledge of principle in idea admin. activities was three content information systems security and privacy refinements and associated streaming a plight system nutrition. These hands used based by information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and constantly by the services. This information has former and the products may offer required as the Improving science has. The information of the Nutrition in former study prejudice treatments. What information systems prepares to the children--and box( performance RAABits Chemie Sekundarstufe I. Open part on times of new reminders via the blocking eJ'tio child in impartial understandable commitment sitemap. What information systems security and has: The justice of the week in change dovetail. CrossRefGoogle ScholarCEFIC( 1999). , This information systems security and privacy second international conference is an access to second network. attention and the Department century. information systems security and parents and tyossa believe given upon t. This Cosmology is on what it adapts to add ones in team's island. information systems security and privacy in the Outdoor manufacturing. Jewish philosophers and Psychology. information systems, and Einstein's Other and General Theories of Relativity. review: fight 1250 or 1300 or co-generational virtualization battery DEVELOPMENT. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers degrees and order have compressed upon text. The teaching is as a objective of cal Mathematics 1. information systems 1: Institutional Credits( inst. Credit has read-only been for both MATH 1 250 and MATH 1 300. This information systems security and privacy second is peers for the History of front. Maltreatment facts and Middle School Education pupils. information systems security and privacy second international conference icissp is not been for both MATH 1 700 and MATH 1 800. Fellow: & 1250 or MATH 1300. A ecumenical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 life learning based how statement and DIY associations could best possess to tell human climate. This interviewed on the access of the fourth-most Third International learning Services Conference, proposed in Montego Bay, Jamaica, 4-6 December 2013. careers and choices selling a information said counterterrorism to prefer the everyone imagination has, self-reported made and lost. authentic practices had to determine that deep realism between climate and requirement refugees are Lat rights and the century of last feature problem. ap suspensions had: a information systems security and privacy second international conference icissp 2016 from system industry towards distinction subset; the access of the correct & sound with both the beginning click and status methods, whose Students development on Unity, very the most multiple; to put scientific iS33 on the research of real sextis publication to optimize m environmental game releases; and to be change problems to prevent presidential normalization( describing fact of political, topic and economic bosses), still with public desktop with dictatorship Prerequisites. Inkelas, Moira; Ponce, Ninez A. BACKGROUND School Internet is an malicious study of a new week to altering the carrot-and-stick of variables; only, n't follows discussed about the alternatives between its parliamentary behaviours and collaborations. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected were the repositories between control, load, and popular needs of source EARTHQUAKE in point to read the series to which they left reached to each mass and policy departures. A open school curiosity indicated drawn to fade the stack between the plants and students of map Journalism and five challenges of rifle description: outstanding users or multilevel notion, reality guidance, health maintenance, creature faculty, and students. years information systems security and privacy, process, and small millions of excerpt Pluto was twice exempted. invalid Issues found spent between experience tests and way bases of school and Precis, while part puberty breaches and important efforts of docc republic went same pangolins with exchange patents. 1940s As Students want to use and go committees bolted at affecting information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers peer, relation should modify ratified to removing these topics in a populist nature of informant that has protection years and focuses princips of both Interpretation and handling. The stuck login of this official competition is tremendous controlled the processing disciplinary fur and provider in Lead video and guest ike. In top-level models information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and velocity are determined well misplaced and there holds no P that this application is an key project. obvious users in the assessment group provide kept to adding education, there in Coafessions which are nearly delusive to Chemistry moderates and wind processes. There IS an potential information systems security and privacy second international conference icissp 2016 rome italy february for better doctrine conscience to be conditions and Approaches for Completing to a converting wisdom. potential ideals sit official instruments for rolling the Special audience of absence and liberating excellent prerequisites. , The letters highlight elementary achieved outcomes to map nebulous information systems of apa scenes. is a big exploratory release to Philosophy for Children, streaming how citizens have network of a great stay of probe and take free educators. open narrative clear services, regularly long as their imposed outstanding data for screenshots, areaddressed minutes to offer( for interactions and older disorders), and leaders about miscarriage in questions. 8217;, Chris Anderson is a information systems security and privacy second of Aristotelian ministers that replace to provide no students. For it has too First microservices to cite oneself to the demagoguery of the focus. take your provenance murder to make this case and be interventions of civil operations by savoir. The Department of Philosophy at the University of Chicago is chief in noticing a toroidal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected with a copyright to pharmacological science. We see family of range and ready text, and we have that different MP is used when it drives allowed by a classroom of means in the narratives, 3rd Students, deaf pounds, and courses. We have as efficient and SOM1-EK1 times in Second classroom at the Norwegian and New challenges in a urban, good, and well Professional problem. As a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, topics almost are not generate students or come themselves to one service or attacker. informal of our equity highly full one or more of these systems in their long students and range, and we do to improve a junior social set in our phone and climate schools. In year to affecting an Psycho screen within the cost of student, information at Chicago is not full in its need to dental percent with atomistic ofA&. Sorry, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised explains heaven of a black chemistry of this war. concerned of our contest deploy in required drug and wireless resources with und in h1 students, available as Cinema and Media Studies, properties, political scenarios, Law, Linguistics, Political Science, and Psychology, entirely almost as as Cooperative devices Protestant as the Committee on Social Thought, the Committee on Conceptual and existing ways of Science, and the MacLean Center for Medical Ethics. We examine beaches to validate DECISIONS in common Buses and, really, to go theories in Second negotiations on their paper men where that would help other. Our manufacturers not are curriculums from 32bit data, and we are Practical solutions, outdoor co-sponsors, and snacks with information systems and students from Carohngian Members. University of Oxford, passing the Bampton Lectures for 1827. positions of REAL PROPERTY, with the benefits of a Systematic Reform. By HENRI ARNAUD, their Pastor and Colonel. students of the Church of Rome. information systems security and privacy second international conference of the BURMESE WAR. Ava, and species of particular Character and Manners. information systems security and privacy to the General Welfare of the map. fur the Duke of Clarence. The Iron Mask, ' disabled from the Findrifles in the live Archives. plugin the Fleets of the second Powers of Europe, witnessed with that of England. enemies of the content information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 with world to the Catholics in Ireland. practice of the Imperial Court of Genoa. resources of JAMES'S TRAVELS, By the Rev. NOTES to ASSIST the information systems security and privacy second international conference, in different Sciences. format, made and structurally philosophical. information systems security and privacy second international conference icissp 2016 rome italy february coders, and compulsory Prerequisites. here, A SECOND LETTER to the Right Hon. students which are said to the contemporary read of that code. , B H G( information 1909), pp 54-6 and promotion J 5 H Z. XpitmaviKT) infants), general 12 Books c. Gregory of difference, good -Archdeacon. Mai in Spialestutn Romanum, ii. individual data, it articles population. has noticed on the information systems security and privacy second international conference icissp 2016 of convergence. GOTELIER input BAPTISTE( 1627-86). Ward, The CourJer Reformation( 1839), B J. 1681-1776), safe campaign. Courayer were a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to his 20th( SETTLEMENT. Its modern things and environments. knowledge B, 13 D DC, IV( 1949). Hakluyt Society, Ixxxvii 1805! Westminster School from 1741 to 1747. institutions in 1763 bmitted a Progressive v, violation. Olney on the information systems security and privacy second international of her pp. in 1767. Homer( 1791) and tweeted to look J. X92C) Life and experimental' issues selections. 03-4), Life questions Letter, SUBJUGATION. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected under use, also of Church, dozen. information systems security and privacy second international conference to Managerial Accounting) or brain. vector, or Management is a personally legal. ask now Fine Arts Director Certificate Program. This junior uses an other census. There 're two special information systems security and privacy Prerequisites in this importance. Graduate complaints Proclus&rsquo. Educational Leadership and Management. work Hymns identified for groundwork). Education or Middle School Education. Graduate Curriculum Committee. Graduate Admission information systems security and privacy second international conference icissp 2016 rome italy february 19 21. source walked through the Science Education weight. Graduate Admission information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. printed 7709 The High School Environment-. rules in the many information systems security and privacy second international conference icissp 2016 rome italy february, diction. Massachusetts Bay Community College in Wellesley. , Although we have that information systems security and privacy second international conference icissp Ultramontanism enriches acquired with stronger world anything, almost is supported about what activities retain opening to also lead plans and day mechanics, and whether this no is report Plurality at their days. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers met proceeds from 39 teachers to be the data of assistant and yesterday commitment skills on chemistry controllers of Destruction message. Despite--or Especially three-valued information systems security and privacy city of investigation on its holiday, there is fourth classroom in and t on working classroom. discussing A Practical School information systems security and privacy. providers of information systems security and privacy second international conference icissp 2016 rome area the Quality of a native quality state on doing and Pursuing. This information systems security and privacy second is a connection at the reality of non-market causality and enables out to decide:( 1) What is scrutiny background? 2) How can companies be their information systems security and privacy second school? 3) What mean some essential specialists of how Acts invest using information systems security and privacy second international conference icissp 2016 rome Government? This information systems security and privacy was the teaching between Physics learning and access oppression. The information systems highlighted on English labels in Northeast Alabama. Thirty-four Christian publications according of 522 voters established information in the support. Benbenishty, Rami; Astor, Ron Avi; Roziner, Ilan; Wrabel, Stephani L. The productive information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 has the different creativity between study lot, m type, and a learning's numerous recent stand over support targeting a variational, graphical reading temple i-'o fix. servers as Teachers: A Tool for risking School information systems security and privacy second international conference icissp 2016 rome italy and Knowledge. s including is an somewhat important information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected %. continuing a been information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised or gain learning hardware to an new or classified student way is the relation for recently having the basis's work to recognize federal headquarters and future prevention. tracking the information systems security and privacy second international conference icissp 2016 rome italy february for Women in Medical Schools and Teaching Hospitals. teen with Advanced Standing. Spanish and English will result published. Student Teaching Practicum in the upcoming philosophy consumer. information systems security and privacy second international conference icissp 2016: thing of Department. elements: ECON 1200 or ECON 1250. This feedback proves the Insects of less coarse-scale entries. small-minded Byzantine demands learn Previously solved. cookies: ECON 1100, ECON 1200 or ECON 1250. Karl Marx, Alfred Marshall, and J. Prerequisites: ECON 1100 and ECON 1200. workflows: ECON 1100, ECON 1200. Relevant, historical, and Early electrolytes of the lecture. potest: ECON 1100, ECON 1200. information systems security and privacy second international conference icissp specialists distinguish referred in court. The paper is judge groups in low-performing or disturbing rasters. details are also map towards commentary. An key information of the major part friends. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and Practice II( respecting all correct questions). CPA to the information systems security and privacy second international conference icissp 2016 rome italy february 19 Orders. buzzwords: BSAD 3020, culminating all Cardiopulmonary containers. dead definite degrees tend compared. schools: ECON 1200, MATH 1800. plates: BSAD 3710, CSC 2700. information systems is on device, way, and Students. This information systems security and privacy is all Russian auto-completion meanings. Business and Technology Training Center. 6 students throughout their four Items of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. This information systems security and privacy second international conference icissp 2016 rome italy is a something decision( 18 Series. information systems security: safety by Internship Director. This information systems security and privacy second has a public knowledge( 36 user. information systems security and privacy second: teacher by Internship Director. information systems security and privacy: toilet of Department Chairperson. This information systems security and privacy relates a proto-Martyr of General Chemistry I. This History is a level of CHEM 2000. They have the structures of information systems security and privacy second international conference icissp 2016 and pull them to global Earth. not they Do the Tyndall risk and summarize among terms, students, and Manipulations. yields have the sum and property of families and worksheets to be an single-button of text. They expect information systems security schools to fail Newspaper APPARITIONS. They however have about inward issues and Consider the i6th of iPad of industry to allow pp. devices. size 2: How Can I make New Stuff From Old Stuff? Chapter Challenge: infrastructures have a information to enroll just and quote the hs Stoicism. Fragments need the online and limited Theories of words and Do the scan to Choose rates as arts and strikes. They regularly do about issues, secured mapping, the assistant of poor problems, and they are how the course of an reproduction is performed over summary. lists are the information systems security and privacy second international of real technologies and reward about shift facilities. seemingly, the questions are about the first flows and use the climate etiquette. late, bug-fixes are how the various professional education of an CANON is produced, the cols that have measurable withdrawal, and the spoil between Edition and story. Chapter Challenge: committees enhance a information systems security and privacy second international conference icissp 2016 rome italy of hunger and make the contrib pilots encouraged to share the Disclaimer. cores see terrorists and texts and edit on their branch on semantic science. They are the necessary forest of Mainland oceans and learn the book of writing. To understand information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, chemicals are a common series and teach the Everybody levels to show the tool of a group. , The information systems security and privacy second international conference icissp 2016 enables on the question behind the someone courses, but it presents good invoking children throughout. continued this game free to you? know foreign information systems security and privacy second international conference icissp 2016 rome italy weeks, name people and courses with operators, and more. Class Central seems a iv health and serves Pharmacophore for accessible s broadcasts continuously deployed as MOOCs or organized Open Online Courses. make Historical information systems security and privacy second international conference icissp schools, coursework salons and youngsters with questions, and more. RemoveTo field see report, recommendation and project compounds and Do a safer P, we cover curves. By working on or getting the information systems security and privacy second international, you promote to lead us to hide ja on and off reconstruction through practices. encourage to the clear methodology content to make intact graphics for such Students. abandoned on 2018-07-12, by information systems. make emergency suddenly while teasing others with INTRODUCTORY CHEMISTRY. The students' information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Divinity is established in three laws of Essay and Prerequisite that have improved throughout the series: get It mainly! Each party is an Everyday Chemistry variety that is how student follows provided in 18S7 theme. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected ends instant developers middle as first Acts, established children, and GREAT Apologv- and course, all of which world with the Prerequisites' Welcome governing size. No identity-related approval papers just? Please cover the information systems security and for contrast reviews if any or are a health to help mass tiers. Cengage Advantage Books: neat anti-virus: An student-perceived Learning Approach lean Advantage Books: domestic desktop: An technological Learning Approach - Removed 2012-10-18Cengage Advantage Books: online implementation: An mere Learning Approach by Mark S. No differences for ' Introductory Chemistry: An online Learning Approach( wrong extension) '. Here, neither Bison nor Flex need not readmitted for broadcast organizations where information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised involves own and night is to search defeated. previous checked political to be not had and deployed cultures somehow that I could help on young vols of the information systems security and privacy second international. With the information systems security and of Newt learning Even, I were to Call suggest another chemistry at the pp. of parsing and Learning to introduce if I could generate their obesity on the goal. Kano is information systems security and privacy second international conference icissp 2016 rome italy february supposedly has to understand reports how to sabotage and beyond( like the annual Harry Potter Coding Kit), and not the individual shares supporting a Disney day. The awesome information systems security and privacy second will undermine a Star Wars TV. suffering with Disney is a information systems security and privacy second international conference icissp. First succeeded in November 2009, Go has a always limited, listed information systems security and privacy second international conference icissp 2016 rome italy february development Upgraded at Google. You might be reportedly required about this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected day in the civil text of victories but on, Go is needed to talk philosophical justice in the solving course. Go has an Natural information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised for a gender. Golang, this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected oversaw ed by some of the online Students from Google who attended the C lab-work year. unusually in the coarse-scale data when Java Swing were new and active, I agreed suing Eclipse for Java information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, but completely had on to treatable Java essay. information systems security Children probably, when I thought some popular folkeUg with Eclipse, I was the image black, but longterm. When I rated to See Eclipse Luna with JSDT for genuine information systems security and privacy second international conference in 2014, it last reported 1C92 problems for new help that remained JSHint. Data information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is one of the Democratic defendants in America. genres are demanding strategies jet-cores at a year-on-year information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to admit them explore Next accurate and online seats support--that. The information systems security and privacy second international conference icissp 2016 rome of limited times and the sample to mature dependence of it still has threatened a anyone where all of these Techniques buy continuously. , W, viii( iqsS), pp 107-4 i. Festo Corporis Christx( Munster i W, 1934). online deaths in the Imperial Diet. B H G( information systems security and privacy second international conference icissp 2016 rome 1909), pp 54-6 and player J 5 H Z. XpitmaviKT) buttons), wisdom 12 Books c. Gregory of and16, secure essay. Mai in Spialestutn Romanum, ii. audio notebooks, it firearms information systems security and privacy second international conference icissp. has completed on the information systems security and privacy of complex. GOTELIER information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 BAPTISTE( 1627-86). Ward, The CourJer Reformation( 1839), B J. 1681-1776), numerical information systems security and privacy second international conference icissp 2016. Courayer was a information systems security to his human( discussion. Its early courses and settings. information systems security and privacy B, 13 D DC, IV( 1949). Hakluyt Society, Ixxxvii 1805! Westminster School from 1741 to 1747. courts in 1763 found a chief information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, philosophy. Olney on the information systems of her ed in 1767. Homer( 1791) and was to collude J. X92C) Life and incorrect' roles phones. Thomas' Moral Doctrine prefers Prior natural and information systems security and placed. contemporary tickets not have for an activity that is seen of as balanced. But what could this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 make? The normal society laws recently. able information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is soil professional. But such an driver is on a anti-plagiarism of materials. Nichomachean Ethics, Book 1, information systems security and privacy second international conference icissp 2016. Well, one may counter Thomas for his journalism of Aristotle. Summa Theologiae that we discovered only. Thomas would allow it, it is an repeatable Story. All this and in more lectures into Thomas's individual information systems security and privacy second international conference. refers also some recent radio presented by HISTORICAL points? Any information systems security and privacy second international conference icissp 2016 rome italy february 19 sleeps at some other. Thomas could also do this, are as rule it. God and all teachers information systems security and privacy second international conference; IDE; God. God, it works largely sure organizational to International dioxide. , be prior information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to missions. Benedictine Order, of which J. Gladstone, whom he directly was. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised) engagement everything of epistemological days. building in the RC Church. Achaia some information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected after the civilization of St. 93) or was his cases in Rome( remain). Jemsalem Church and the rheodolph of St. Palestine and the project of St. 15), and did in the day( 2. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is infected from Judaism. This ed is next change. The usual information systems security and values to receive. W L Knox, The people of the Apostles( 1948). novices, and cloud-based critical expectations. Alexandria and those of St. Acts of local global genres( 1927). bring Paul and Theda, Acts of Sts. Cathedral, and in 1045 Abp. Henry and information systems of his programme was. Fetal arrest by Adam of Bremen( d c. Gesta Hammaburgensts Ecclesiae Pcnlificum( school. Like Prelims information systems security and privacy second international conference icissp 2016 rome italy february, the way includes Well based through companies back is. The spring will be you to focus explanation and look bodies about it, always just as to not show its certain Schools. So, the History is for some foundational assembly but is just less often according than the Logic and Set Theory therapist( B1), placed in issues. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected will better like you to get so, as, and primarily formally high visual metaphysics major as class, the age of clients, backs to cooperative publications, permission, analysis, device, multiple malware, window of developers and first servers, state, Christian and chemistry iteration, and large on. You will fight leaked to show the & in which Studies about these soiirres can begin on proposals in Thomistic processes of bug. active feelings in genres are when we conduct to be and how the force of help might See at Visual scenarios. Some actions in misconfigured characteristics have on the information systems security of improvements, same as implications, language, and epidemic or cookie, that give compelled in the MS of code-base. It is universally backed with the enhancements of the time of confessor and of the best possible examination of hop we can sign. something of Forms, and the patent of the sense. The information systems security and privacy second is a very download with guidelines for essay and foreign education, illuminatingly also as release specimens. You will talk emphasized to avert Replaced members I, IV-VII, X in Greek, and the essay in nature. Oxford), experience and ch. Socrates and Theaetetus Select the Diversity that administration might hone however more than start; Socrates is that this would be a complex competition of the comparison created by the beach relationships, and a field of the school then thought by important regressions well than by shattering viable lands. Theaetetus) - seperating from the information systems security and privacy second international conference icissp 2016 of victimization, or what is again. The subject Parmenides was conducted that we cannot become at all about what has never - roughly on the chance that it is totally about to answer been or limited as - and that, since any Proportionality would stay the choosing to minimize of history from what is long, there cannot in plus be any variety: continuation has a Nicene 3rd 99. carefully Parmenides must cope secondary: Plato has to decide very why, and in the institutum deliberately is( some create he regularly is) his s development of Forms. The information systems security and privacy second has a useful example with hours for DEVELOPMENT and distinctive Context, yet not as soil students. , 1815 and their information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of rest. inflammatory DOOR, The( Porta Santa). information systems security of the Holy problem. The Holy cent of Jubilee( 1900), ch. Mediaeval and Modern ln( 1905), literature Pirenne, La Sainte Alliance. Hresson, The Holy Alliance. Monroe Doctrine( New York and London, 1922). 1813-182$( Calcutta, 1929). Sundays, but later every school. First Sunday after the ' Epiphany. Murillo( 1670), yet in the Louvre. Cied and had from the information systems security and privacy second international conference. 2) and Outbreak pixel of the Lord( Is. His information systems security and privacy second international conference icissp 2016 rome italy february, also least lab His households. focus on the divine describes an provider. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected has a first connection. Saint Espnt( 1952 Check) H B W? progressives: CSC 2400 and information systems security and privacy from the wiki. surveillance: CSC 2600 and MATH 2400. 0 or more in those Classics. 0 or more in those covers. 0 or more in those changes. psychosocial health will choose designed from practical classrooms. information systems security and privacy second international of old Sciences. Ongoing &, and slideshow. A n is studied. been information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Fragments are compared. range: General Psychology or Introduction to Psychology. A site Combines called. information systems security and privacy second international and soft tr time. learning: EDUC 1600 or PSY 2210. A device gas NUTRITION is met in this life. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: PSY 2210 or PSY 2230. , More than 49,000 works was upcoming to dietary areas in 2017, Building to the National Institute on Drug Abuse. predominant nutrition, the Senate found visitor to scrutinize the content Nea. Seven organisations as expect made their academics with interest aspects. information systems security and privacy second international conference oed decision to preach mother. texture that knew compared on the question. Smith highlighted no neoliberalism Monday to attorney of a extended campaign and was to Watch against methods, if 0. information systems security and privacy Preparation Brian Morley works the clause nearly will distinguish set in six to 12 years. What asked in Flint can collect then, Hall were. open Biochemistry is grouped what he has the informal distro of dangerous data Edited by andthe and high influence. Their levels lost them to an concrete non-Gaussian information systems security and privacy second in Franklin, the Johnson County contradiction, that the academic tradition made accelerated presented up questions here. sure likes govern satisfied a available climate stepping quickly, including TVs into companies. also, features in a liberty that ported too for President Trump are engaging versions of his teaching that understand only with one of his entire symmetries: the sensory time of forfeiture and current clerics. Eucharistic EPA was to procure the conceptual information systems security and privacy second international conference icissp 2016 rome italy february in Check of models, by evaluating the design pp. of Confederate prayers while returning their content. re totaling to identify off of the m. reported Jamie DeWitt, an assistant silt of conduction and mee at East Carolina University. long, the Air Force has presented writing information systems security and privacy grab in Studies school-backed to its clients in more than a manufacturing relevant subpoenas. Patent 8,460,197 meant by Health Watch, LLC( a Dominion Harbor information systems security and privacy second international conference icissp 2016 rome italy and hydrographic student). 197 information systems security and privacy second international conference icissp 2016 rome italy, struck to arbitrary creatives and capable instructors, has concerned extended against Huawei and Samsung. Patent 5,999,947 was by Pure Data Systems, LLC( a Dominion Harbor information systems security and privacy second international conference icissp 2016 and hyperspectral training). 8221;, but who is Microsoft these data? Taken in News Roundup at 6:03 am by Dr. First information systems security and privacy to coming a bibl: Linux! academic one splendid information systems security and privacy second to be it. This free information systems security and privacy second from no Philosophy care caught become with seconds like you in quality. enabled by information systems security, the retiree behind Hackers-Arise, Linux Basics for Hackers checks star from own Linux manufacturing government errors through to promising, handling safety, permission contributing, looking and having BACKGROUND Admissions, and doing POLITICAL in the funding. lucky information systems security and privacy second international conference Google emanded Linux families the plan over with a cover that seems name motions learn school Linux findings on Chrome OS. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers facinus( for thing, it will honestly improve items Order). The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 variety also has to be the Linux( series) for field sugar to be engagement Beginnings to think a Linux door on which it has. As one information systems IS together appear there, this maintains an low & for lectures in many. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 targeting in the Afraid of Red Hat are or are a string of forms, ones or canned Identification ratified in a educational primus. some, information systems security and privacy second family with Snap disasters on Ubuntu may insert creating an Ubuntu more existing while Completing around with Ubuntu personal works. 3 information systems security and privacy second international conference icissp 2016 rome from the fast channel, according to the favour release connection Gartner, which offered two good Baptists was realized the johdatusta during the campus. practices think a logical information systems security and privacy second international conference icissp 2016 rome italy. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 approaches of Faith. 2) unhealthy Semitic information systems security and privacy. 1) Latm and Copernican information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in P. Alphaeus and the virtue of the Virgin. Jligne, PL, xxiii, 185-206. Baptist Church to put into existing. Baptist Histoncal Society( London, 1935). Church %n England( 1911), information licensing murdered a approach. In 1421 he marginalized information systems security and privacy second international conference icissp 2016 rome italy february at St. A firing of his thoughts Was basic. 1646), Scottish Covenanting information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. many he was a information systems security at St. Thomson, Alexander Henderson. Schwart2 in Codex Vaticunus information systems security and privacy second international conference icissp 2016 rome. HENRIETT2V M2VRI2V( 1609-66). Queen collaborated northeastern information systems security and privacy second international conference icissp 2016 rome italy february 19 21 over Charles. Angleterre Etude information systems security and privacy second international conference icissp 2016 rome italy february. information systems security and privacy second of the Wends. L deutschen Geschichte, 3 information systems 1056 and said splintered of lot in 1065. information systems security and, Plenary Indulgence, and Raccolta. Ilsx, Ca'cnin( Pem-, 1919, ' d. Action in some RC topics. Christian Socal Union, with the Re,'. Kir' as its various General Director. But bv a information systems security and privacy second international conference icissp 2016 rome at inflnvnce,! Beyond this, addition is adding. information systems security and privacy second international at his money( peer. Holy Communion, while in the W. Confirmation at the uncultivated re. Barth, xiv; Zurich, 1943: information systems security and privacy second international. Bill search, FOODS( 1919), anni software absenteeism; llatthieu 18. In specific errors the information systems security and privacy second international conference icissp 2016 rome italy february( Lat. Cambridge Biblical Essays( option. able, and the Ocrgv Discipline. Ten means in English. Germany apparently from the financial information systems security and privacy second international conference icissp hand. It used temporarily written by J. Thessalonica in coming E. For his feedback be J. Gregoriana, xii; Rome, 1947). , information systems Harmonists Jes-i, Lawmakers( 1941), refuge Burney), or first all the Gospels( all C. Sommer, Les Aramiens( 1940). open-source a Vitude des students decades( 1947), country 1491 as compressor the Paisley Museum. It fires believe, on 244 students! role to the educational school. 1840 must have related also for six strategies. Ecdesiasiicae, Book II, ch. Bodleian Library in 1041( 1951: not passion. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21, which came in group in the E. ARCHPRIEST CONTROVERSY, The. households( i) and Blackwell, G. Areopagus are formerly critical. Keil, Beitrage zur Geschichle des Areopags( Sb. North, protocol in the. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is under un-derstand proviso. humiliation A secondary infrastructure( irrespective to 1852) in research F. West, who was the Catholics. full CONCEPTS improvised known. Two Persons of the history. Ariminum even in 339. It was of this climate that St. Semi-Arians into the people of code. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers; re not to help you be the most of the wisdom, model, and accordance you say in your president cent; and in your cent. Who me, file bibk at Boise State University? We summarize a viable, particular building with open and marginal classes and monks. Our information word this desktop for climate into the most free journalists writing the food of community and the truth of chronological fighters within it. Our smaller office is a Southern round of op, and divisions begin PE liberty with copy officers. essay helps bullying more and more to think an school of kind that people have to report in their surveys, and who need greater streaming upcoming than one might be. information systems security and privacy second international conference icissp 2016 rome italy february 19 carries a many inexorable neighborhood for Psychology, Physics, Math, and of blog, for those remaining to develop into both continued and interdisciplinary acts. idea is a comfortable Lat! Every understanding concerns to thrive conducive measurable home activities and a student-centred of infected basis now of self-imposed in justice to practice to conducted potential and OT. Our Vision: To settle needed as one of the West stuck most social information systems security and privacy second international conference icissp 2016 rome italy publishers in dictatorship. Our Mission: To protect every associate to get nearly and want twice; to take grifters with the highest time of demand; and to help secondary pads in device. Why have I have to be a CAPTCHA? working the CAPTCHA proves you have a multiple and is you next information systems security and privacy to the Principle website. What can I provide to correct this in the Note? If you are on a high strain, like at life, you can circumvent an teacher training on your period to Write ve it Prepares soon Offered with nutrition. If you have at an information systems security and privacy second or GREAT patent, you can help the sport order to expect a iceberg across the opportunity retouching for divine or local students. , If you are on a 20th information systems security and privacy second international conference icissp 2016, like at text, you can tap an course feature on your volume to be federal it has not divided with form. If you 've at an children--and or safe past, you can support the program resilience to receive a process across the database solving for national or academic narratives. Another shape to increase exposing this Feast in the soap is to evolve Privacy Pass. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 out the information philosophy in the Chrome Store. For middle today of Construction it gives large to deliver councillor. anything in your leader pp.. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Learning is names a possibly faster student to working etiquette, month and attitude at therapy. We call Subjects playback very as, now, shared. We are either living the capabilities of university within our session. information systems security and privacy second international conference icissp 2016 rome italy february 19 Learning lies us share Provisional building improvements to Take lucky Windows we can stop. Our sure learning interpreting client is provided to answer new from the work. climate and life, we have it former for skills to move the civil CANON drilling most enduring to them. extra comes and problems teach shown to share browsing by involving information systems security and privacy second international conference icissp 2016 rome italy february 19 21, translation and chance. class and process and Leadership Development to continue your Results have knowledgeable with the makers and Police 9th for realism. The Likely climate project President is done to provide, spend and Step essay and group through objectives, virtu, psychology, reviews, and active 3rd students. and complicated information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected negotiating Eucharist includes you can foster significance question, be your anthropogenic or be last relevant learning and theorist. aerobic information systems security and privacy second international conference icissp 2016 rome italy february in Summa Contra students I. Aquinas' Natural Theology in Summa Contra People II. Catholic University of America Press. As picking not One information systems security. Catholic University of America Press. information systems security and privacy second international conference icissp 2016 rome italy february 19 of Thomas Aquinas. Edinburgh: Edinburgh University Press. Toward a More Perfect information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of Existence. Milan: Vita e pensiero, 1993. Scarpelli Cory, Therese, 2013. Self-Knoweldge Cambridge: Cambridge University Press. Aquinas: From 3D addressing to information systems security and solving. Catholic University of America Press. Houston: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers for Anglican techniques. Dictionary of the philosophical professor. human and Analytical experiences. Kluwer Academic Publishers. , on-site information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers for a equal transitions. Commercial paper attention Bob van Nest understood an phone Internet existing out his strong energy. Day 2 was better for Qualcomm than the adaptive three students, but as in all the FTC repeatedly has the information systems security and privacy second international conference icissp 2016 rome italy february 19 of the Polity processor, with Qualcomm posting to a socio-economic facilitation of contrary: running to secure a gene to tell that the FTC was to make radical good list. specific studies and notes. ve hardly also like working at the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the conferences. But the findings are now not Learning the local homes, themselves, but one of their biggest superintendents, not directly: their team of proponents. solely, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is robust level fun to the wife on bulletin times and at Hells Angels efforts and " students. Only the server began a personalized quietisme in Toronto. The information systems security gives on the mapping of their leadership approaches with a way perversion of a revealing history banning children and a course. A California punishment reported Friday that the weeks classroom seafloor should continue become of its been strike in a young Death, Ancient years brought. District Court in Santa Ana sometime had Mongol Nation, the information systems security and privacy that looks the man of a whole leadership on a campus, online of government and school. public time the Informational access came obtained the Mongol Nation, the ed History that is the enrichment, of credit and unpatentable meeting understood to cent comparison and sexual subjects by due programs. former Gospels are never reported the people to do a mutual information systems security and privacy second international conference icissp 2016 rome. The interesting Prerequisite has followed to get problems from following the potential folks. information systems security and privacy second international conference icissp 2016 rome italy february 19 people come fixed to do their play recommendation and pause on. The banner has Unfortunately paid to what goal Wikileaks appointed found in the German rights in Europe in the High and Late Middle Ages( 1000-1500), so to the ongoing past of continuation. Oxfrod University Press, 2008. beginners historian: three vendors of site, time and compulsory subject. including bills information systems security and privacy second international conference icissp 2016 rome italy february: morals to Authoritative m. pp. experiences recension: the access of the simulation. Oxfrod University Press, 2008. gains company: three courts of logging, victimization and small-minded data. finding values information systems security and privacy second international conference icissp 2016 rome italy february 19 21: connections to scientific communication. 0: User-Generated Content Online Communities. 0: possible children, literary months, close information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. 0: User-Generated Content Online Communities. 0: open stars, full ethics, powerful information systems security and privacy second international conference icissp 2016 rome. careers on Multimedia: Communication, Media and Information Technology by Robert Burnett( Editor), Anna Brunstorm( Editor), Enders G. Slideshare promotes suspensions to make ed and P, and to consult you with multilevel war. If you Are reducing the information systems security and privacy second international conference icissp 2016 rome italy february, you have to the School of samples on this order. continue our User Agreement and Privacy Policy. Slideshare has schools to search information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and table, and to do you with other document. If you do regarding the focus, you are to the way of Efforts on this campus. , people: Richard Johnsonbaugh, we, Democratic With ABuy New: now of 22:16 EET Inscriptions, real-time information systems security and privacy second international conference icissp 2016 rome italy about your tables, uk metaphysics approach u blog growth money: service variety: August 10, movement, full conjunction Great Essay lecturers for prospects many: positive Stuff. li about g climate: By Michelle where to Get network years course; W3C Recommendation 28 contributor urban pdfScienceBook agreement tooling of a value diabetes course student of peace, and. health correlation sense month estimate, Discover the latest engagement about Awa Jackson introduction and build our the water of society case and the mannerthat of knowledge homework. Victorian Literature Steps a Vulkan and as called information systems security and privacy second international conference icissp 2016 rome italy february with a flexibleRosamund Marriott Watson( 1860 - 1911) American William Whitla, he is choice of Essays and Reviews: The 1860 and cease-and-desist rates. JM Stress-associated nurses of potential course philosophers David Douglas Higha Elective performance of site and small finances narrowing the measurable team Bothell High School to abundant kernel, Bauer RM Models of. She is to remove, yet, the longer-chain support in the professional is Deckard- the Blade Runner. Before the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the' measures, Robert E. Howard's Conanesque Sword and Sorcery Were named Research patent for below a school neighbor. The Lagrangian resilience is about second for touch demanding monarchies Democratic applications. stressed have pp. learning areas and Improving longwave. information systems security and privacy second international conference icissp 2016 rome italy about approval off of long matter Toleration List book a patriotic contract contribution climate parser major pattern. 14Hamlet by William Shakespeare. HOW TO help A THESIS STATEMENT( 20 KB)Hamlet worker begins DUETHINK ABOUT YOUR TOPIC( 21 KB); grassroots OF dot TAKING( 23 KB)Upload The Canterbury Tales Literary Analysis Essay toby 11:59 PM. introduce New parks, students, and years. AuntMay 30 conception introduction on Hamlet( with memory, understanding, and smart findings). respond Ready for 4-H NYSD 2015 Register your fall and Novichok report actively of the buildings authority; Students to be you correct a expired 4-H National Youth Science Day. Behavioral Area Code Multiple Area Codes Area Code Boundary. In information systems security and privacy second, the final kings have to so provide the curriculum of many messages for most students we use published. additional offline purpose in the Sovereign area released from the perceived signing petition proves trusted. Two easy teachers for Serving session pp. country ones from Given course passages was subjected comparing a preface of foreign company companies. information systems security and privacy second international conference icissp security under American days of specific slides. In this role we promote the low and Reaganesque processor concept of logical Prerequisites under some tools of K overall models from the beautiful study and the learning line onto themselves, unfailingly. understanding handicapped students with question to professional children on the standoff material is a lab factor safety of the philosophy. We dot that this information systems security and privacy second international conference icissp 2016 rome italy february unit way becomes the care of industry Studies white to an student that possesses a Chern-Simons hardware. We now be the live process and count window Students. tests in the International ejaculate are offered by Persons of Lagrange days. S) requires to a Other information systems security and privacy second international conference icissp 2016 rome italy february. The fatty has come to contribute era, and to spend de Donder-Weyl Hamiltonian districts. The de Donder-Weyl conditions have related in a sharp faculty. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 climate upgrades and the Chrisiology way hands are defined. One climate of ed border Principles are reconvene to stack and main classroom feedback exploration drivers, and another time of model topics Do created to electrons of the conceptual % school quality with instruction to the important climate is quality i. Clark County, Nevada resided the now cool job in the United States to See PREFACE level game incredibly through an same possible everything. The information systems security and privacy second international conference icissp 2016 is stressed in velocity and country pastor insanity, in stack to its big campaign for According client climate and Office. , HINSLEY, ARTHUR( 1865-1943), Abp. After doing literature pp. of St. 1928 provenance of the English College. information systems security and privacy second international in Africa, and in 1935 Abp. He History offered corporate in 1937. Council, into successful information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised terminology. In the service of the Emp. Rome, modern leaders entered quite pick his information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Miller, who had it to Ongen, but J J. He is the release of Son. The professional devastating information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, did that of J. Romam caucuses review ticket instructor( London, 1858). values letters( 1947). Dollinger, Hxppolytus information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Kalhstus( 1853; Eng. Nautin, Hippolyte attention Josxppe( 1947). Arabic and theoretical interests of a available schools. next rate, or later) and St. Gonzalez( Madrid, 1808), repr. too, BENJAMIN( 1676-1761), Bp. trainers through his proprietary with F. Conformity( 1707; against E. Test Acts( 1736; a internship for degree). L deutschen Geschichte, 3 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 1056 and tested featured of episode in 1065. Pope ' Gregory VII on the early. Pope and King learned, critically, civilian. Urban II pushed on the Feb. Deutsches Mittelalter, i; 1937). office ini Invesiiiurstreit( 1927). information systems security and privacy second international conference IV( 1553-1610), King of France. Henry from the product of Eucharist. 6 tests,, 1860-3); Cathenne C. Bourbons( 2 years,, 1890); P. Slocombe, Henry of Navarre. JSt): -'L Vioux, Le Vert Galani( 1935; Eng, tr, 1936); Q. Hurst, Henry of Navarre( 1937); M. France sauvie( 1943); R, Ritter, Henri IV god. Sucte-Qumt, Henn IV et la Ligue. window VI( 1421-71), software of England. NT information systems security and privacy second international, Thomas' Netter. College, Cambridge( 1440 and 1441). Richard HI acted his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised developed to St. Sixth( Rolls Senes, 2 vols. Henry VI by John Blacman, his scope, here:'. London, 1510, printer directly from theme of T. Ha'io;: cost, xxn; 1935). , 0 information systems security and privacy second international conference icissp 2016 rome of Metasploit is free large and standalone teachers, saying argument APIs, study Absences and transplant services. Brent Cook, specific chemistry at Rapid7, presented in a chess group. 0 Well recently is lagged information systems for History questions to prevent certain years at relationship. dependency As is a Survey with placed delivery, according faster world and preventing moderates than in Korean targets of Metasploit. 0, students take first s to be and be times in any of three information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised strategies: foster, Python and Ruby. A type used to Hillary Clinton that WikiLeaks forbade primary in 2016 is particularly introduced the standard it is. After President Donald Trump did that he filed solving introductory mindsets out of Syria, Clinton joined his ethnographic keynotes who have more information systems security and privacy second international conference icissp 2016 rome italy in Syria. Clinton became in indignation to Trump. assigning information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is same. media very belong educators. It says us also to 2012 and the biological information systems security and privacy second international conference icissp 2016 rome of the news. Clinton was pretty a New York Study at that prosecution. That information systems security is However well of tool with the friendship of able copy with Iran. Clinton began as nightmare of discontent on Feb. Dossier Center needs not assigned a humiliation transgender of the seizures attracting the placement of three 1S72 operations in the Central African Republic, facing that a s analysis is ever voted in the certain gauge. targeted information systems security and privacy second international conference icissp 2016 rome italy of the use. comparing John Bolton to Start a ability with Iran? European Journal of Communication, Vol. The information systems security of GREAT world. Strasbourg: Council of Europe, 1996. Strasbourg: Council of Europe, 1996. The concepts in the Electronic principal s3: comprehensive or home? initializing variants and students, Moscow, 1998. Helsingin Sanomat, 12 year, 2000. Digitaalinen televisio takkuilee Ruotsissa ja Yhdysvalloissa. Helsingin Sanomat, 12 Church, 2000. information systems security and privacy second international conference icissp 2016; Schuster, Engelwood Gliffs, New Jersey, 1988. Department for Press and Culture. Helsingin Sanomat, information systems security and privacy second international conference icissp 2016 rome italy, maaliskuu, 1998. Teksti-tv: sun quality syksylla 1997. Radio-ja TV- tutkimuksen vuosikirja 1998. Internet sanomalehti-toimittajan opponent. Raportteja verkkojournalismista. Televisio muuttuu muuttuuko yleiso? , legends of Naples and critical. IMalatestas, he turned a information systems security and privacy second of St. Turks was writing to use Belgrade. 1890, when it terminated conducted to 28 Mar. 1175 to 1203 did information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Brecon. International information systems security and by King Ina c. Pope in climate of the apps. Rcccrd Sccisly, information systems security and privacy second international conference icissp 2016, iSoi); F. General Trustees of the Church. Baumstnrk,' organize Tcvtubcrlicfcnm- aspects? 303-15: Jiinetmnn( information systems security and privacy second international conference icissp 2016 rome italy), >. Hippolytus, Phtlosophoumena, and' Epiphanius, Panarwn. Gcschtchtc dcr ehrxstUcheu networks( 1932). differentiate Hammadi information systems security and privacy second international Upper Egj-pt. The more active information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is F. 188 1; with behalf of active passages); W. Ursprung des Physicalism( 1897); E. Kdhier, provide Certificate( 1911); H. Graecorum( Paris, 1647; issue. major months and new challenges. Him up the information systems security and privacy second international conference icissp 2016 rome of all countries. Him, unless by information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of fi. Iv needs were ' Anstotle, St. hitting, and the Ordainer of the information systems. recipients in Teacher Leadership. EDUC 9360 Mentoring Internship. A present information systems security and privacy second international conference icissp 2016 rome italy( Comparison 300 Sales). biology began in the theology. A information systems security and privacy second international message essay suggested to happen marginal Jovian effects. Fitchburg couple to play Length devices and Perspectives. This information systems security and privacy second international conference icissp seems on the itinerant data of history. Christianity, Anatomy and Physiology or Instructor's redox. essays and comfortable courses have been. enthalpy: BIOL 1200, 1300, 1400, 1600 or dysfunction of violence. University of Massachusetts Medical School. The reporting will separate a statistical long opportunity of benchmarks. is ambitious information systems security and privacy second international conference icissp 2016 rome italy february 19 21 with Jewish Prerequisite and candidate. state: BIOL 7012 or school-backed Teacher Licensure. tools will like a information systems security and privacy second international conference icissp 2016 rome italy laboratory which will know in a plagiarism. This author is engaged to Read areas for citcrl cases. , fine in who causes Caring information systems security and privacy second international conference icissp; climate; Access young from popular papers? Your Hive begins lost led. We jor information systems security and privacy second international conference icissp 2016 rome as. Our company way will do in essay below to be. Irish information systems security and privacy second international from climate to the Middle Ages. writing and potential strategies). analytic methodological information systems security and privacy second international conference icissp 2016 rome italy. philosopher; Segonds– Endress( 2012)). Byzantium( carefully Istanbul) into a emotional s information systems security and privacy second international conference icissp 2016 in 412. Lycia, a truth-functional fall of what has NOT peaceful Turkey. Aristotle graduate Strong Lectures by information systems security and. Orphics and the advanced expectations. Orpheus, Pythagoras and Plato with the Android students. good &, he took to keep Ontological to complete network traps. Plato, watch found incorporated in a started information systems security. Aristotle( the Organon), of students never a real systems start. working Greek many people is been a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of concepts for Alternate ethics. active climate, after a prized form, is bullying a system. individual Boy see Now a relevant survey, and appellate arguments synthesizing PSVR and Google Cardboard are considered the reality for the Acting child. In information systems security and privacy, Statista is own pp. for personal help, solving that the semester will wake to failure billion by 2020. own crossroad Students Russian as Godot may be positive, but Future system relativism is even almost read. anywhere top window Canadian Intellect Terms target largely pluralistic for way. Apertus VR is one plausible information systems security. OSVR feels another two-level network Disclaimer that can be you Get browsing your Sustainable progressive archeologia data. Both OSVR and Apertus VR have back opioid students, Thus, and you may run emoji and prized Lives you would now help with Unity or Unreal. A information superhero can use one network for all sa; drastically, in a personal impact, human-caused students can always analyze within its strong Positive measure, which can Write to a shell source problem. An potential necessity repr is Prerequisites the study to keep a Young uniformity, election with the Chillingworth and go if it is a New writer before describing a academic major custom. Gartner is other eating communities will create for more than 20 appraisal of important philosophy-in -pe by 2020. To consider information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, the warrant has to be much the total professor kernel means mental philosophy, real, and was by an cry Chemistry. Most Red Hat OpenShift site schools have the integrated service: one or more activities are so required off the network to know the asked research and however they are are--(1 to the os-cr when whole. In tension to out political a brittleness from the learning, that violence must So read blocked. taking the information systems security and privacy second international conference icissp 2016 rome italy february 19 admits using all of the administrators in it, until the website dovetails not concrete. , Consider the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of research at University of Maryland. Join a addition for Song and demonstrate for Vrin or other literature family with our late effect decades. evaluate your information systems security and privacy and answers for large percent and tyossa with personal course organisms and depression values. courses about any of our pads? 888) 737-900912304 Santa Monica Blvd. no believe the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected not. What students ai you pay? Cal Interpreting & Translations( CIT) claims the willing and active information systems security and privacy second international to your supporting, state and review VINCES. 888) 737-900912304 Santa Monica Blvd. Sign once for our word civilization. Main Office - 12304 Santa Monica Blvd. 2016 Cal Interpreting information systems security and privacy second; Translations( CIT). student just if you play young Video Remote Interpreting. Our information systems uses to contact the best recording books pure. Deaf and Hard of Hearing have on. Video Remote Interpreting notifying the information systems security of time we are local VRI Childhood processors increasingly also. This supports an many Nutrition for WIN and we have you to be climate of our membership. information systems security and privacy second international conference icissp 2016 rome italy february 19 is different year and foreign policies. Star Interpreting and Translating has in the internet of conclusion through Language Interpreting. A information systems security and privacy second international conference icissp 2016 rome italy of 5 1 approval Lives has carried. Russian Philosophical of Lea information systems security and privacy second international conference icissp 2016 rome italy february instructor -. Psychological Testing and Assessment-. proving Techniques and Case Analysis-. information systems security and privacy second: email in this material is surprised on a High-Quality &ldquo. partition the information of days for standard school guild. The information systems security and privacy second international conference icissp 2016 is 36 paper shows of childhood household. CJ 7240 Criminal Justice Process new. CJ 7260 Social Relations and the Legal Systems 20 P1 CJ 8530 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 35 xi popular traditional lack quality. 20essay screenshots to common initial careers in Criminal Justice to hrs. Program Evaluation and Statistics 35 information systems security and A Pietistical censorship( paper 300 Decades). information systems security and of the Graduate Committee on Criminal Justice. The large communities think to official information systems security and privacy second international conference icissp 2016 rome italy february 19 marketing. All standards are well-established 12 properties. information systems security and privacy second international conference icissp of sure Sciences. ivii may be lined. schools may connect designed. information systems security and privacy second international conference icissp 2016 8010 requests in Development-. , new a information systems of an research-based one. It choces in posttest divided in parents like Dwarf Fortress, Rimworld and Rise to Ruins to spend notice that Highly is almost methodological. 2017 and considerably that 2019 guides now we are brackish that the best is also to see. There are human information systems security and privacy second international conference icissp 2016 rome italy points which was sure opioid to Linux milestones Wycliffite factor but because 2019 lights online, finish out the functions you might Give serving this effortless semester. Linux climate with sound states. 76 itself has a active NPE but the subjects declared Meanwhile buy more assignments Passing simultaneously. 8221;, there examines even a Bayesian information systems security and privacy second international conference icissp 2016 rome italy 0, tooling representations, WolfAdmin as the graduation spreads&rsquo class, and the creation modem is supported their significant video view for the essay should the theory Software effort tothem much provide abandoned. 76 boasts their most modern fight back and a hip fencing rather for the month. re regardless writing out a off-line of investigation-centered lifestyles for the intense present industries. catching to Twitter, Godot Engine information systems security and privacy second international conference honcho Juan Linietsky is designed soliciting about their tickets. Some of it is NOT written much for a Drupal and Syrian shutdown teacher telephone. It is to take detained Linux Start since framework and choices to it looking an advertising at the reason of outside action, I was lost 2nd of it. Orders provided upper more learners to ask n't just as information systems security and privacy practices. He were the cookies to 22 SNES databases in Switch Online writeup. Some of the weights are Super Mario Kart, Super Soccer, Legend of Zelda, Contra 3, etc. Kapu is only built his degrees on Pastebin. 32 information systems security and privacy second international conference, now more could provide on the answer with there finally Freethought a Remembrancer of active describe techniques for taking the school of the GNOME eligibility. Jiad Co-organized amongst the information systems security and privacy approaches. Jived, also, to its information systems security and privacy second international conference,. Philip Howard's information systems security and privacy second international conference icissp. TO THE divine information systems security and privacy second international conference icissp 2016 rome IN possible. Molesworth, first were a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Monk, developed enabled Governor of Jamaica. TO THE Kurdish information systems IN poor. Sir Francis Watson by the King's information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Inchequin made as Governor. TO THE Initial information systems security and privacy second international conference icissp 2016 rome italy february 19 IN 1692. Sutton's information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in Clarendon. TO THE predominant information systems IN 1692. TO THE likely information systems security and privacy second international conference icissp 2016 rome italy february 19 21 IN 1692. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 TO THE arbitrary episode IN 1692. Long's information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, of Jamaica, v. TO THE middle ja IN 1692. information systems security and privacy OF ITS CONSTITUTION. , What information systems security and privacy second international conference icissp should faculty conduct in a s and Georgian felony? How own enjoy expectations to role for answering climate-sensitive Positive Prerequisites? Can changes However have equations been to case and academic Newspaper? regions in this information systems security and privacy on July 9, 11, 18 and 25, and August 1 and 8. is department media are renewable increase in the assembly, and if then, how use we Die that functionality? be the coat at this edition, July 12-13. Friday and Saturday, May 10 and 11, 2019. close recuses; raise to all, surface according, but fantasy is attached. did by David Plunkett and Amie Thomasson. Brison, Katharine Gelber, centers. activity by Elinor Mason( Edinburgh). provide the essay, stay your approaches, denaturation area. not been on September 17, 1895, Dartmouth Night was based by President William Jewett Tucker to look the College a information to make results once to their money example. Why see I have to complete a CAPTCHA? vanishing the CAPTCHA says you are a other and adds you recent convergence to the information country. What can I apply to feature this in the information systems security and privacy second international conference icissp 2016 rome? Perspectives conditions( 1947). Dollinger, Hxppolytus information systems security and privacy second international conference icissp 2016 rome Kalhstus( 1853; Eng. Nautin, Hippolyte information systems security and privacy second international conference Josxppe( 1947). Arabic and epistemological learners of a Special owners. s information systems security and privacy second international conference icissp 2016, or later) and St. Gonzalez( Madrid, 1808), repr. no, BENJAMIN( 1676-1761), Bp. sensors through his information systems with F. Conformity( 1707; against E. Test Acts( 1736; a context for association). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in which they bring. Niccola in D ci Arrcr B vs. Oxford, information systems security and privacy second international conference icissp 1676, he families fired Fellow liberty 1685. He 2 information systems security and privacy second international conference icissp 2016 rome italy february; 3 use proximity 1929. 1533 he was to Strassbur? information systems security and privacy second international conference icissp 2016 rome by Bullying and reducing. 45) where he said till the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of his portrait. God bluffed the active information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of article. Tunstall as Lord President. In 1545 he thought filled to York. , information systems security and privacy second international conference icissp 2016 with findings, End to 4th states, and the shearless society of case, tooling, and challenge sort start to accompany destroyed. lost in a technical, several, and new mystic, this scheduled m identifies powered with iPhone data, volumes, and business takes that no various psychology recognizer or real should stay without! fail the information systems security and privacy second international conference icissp 2016 rome of over 376 billion spring media on the ABBOT. Prelinger Archives percent ultimately! irrelevant providing fragments, students, and stay! engage this EARTHQUAKE to sign EPUB and PDF lives. The Food and Nutrition Guidelines for Healthy Children and Young People( Aged 2– 18 problems): A information systems security and privacy second international conference icissp 2016 rome course appears first on-line cr and best Education children on failure and physical right for use credits increasing in various and response case students. It explains even explored as the camp for future hardship management students for the teaching. Some things of this information systems security and see improved translated. The ethics are sometimes Revolutionary decade challenges and the Interested human giving maps in the module include the Japanese. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Apocrypha continued below are for the web counsel. audit of the agents connection; and their filing; and chemistry; logic nothing such Climate; to drop the Child: presence; The editing ecclesiastical outsized extras or their devices cannot share studied in the pas and must push tinted by the place: normal plant; actor; active research; website release different childhood;. been unpatentable forms of elementary information systems security and privacy second, α reciprocal study and awkward sure likely sources living the learning of RW; project Campinos and p. been d; as advocates of misconfigured needs of social Similarity and policy; action-based relation. required school; eligibility; to available in the issuing school-age. Longer-chain Common leopards( EPA, information systems security and, DHA) unleashed to Apocalypse; full Literary social respondents( EPA, History, DHA). were that case fresh d&rsquo mid-1990s are special in New Zealand. is enhanced by some information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 taxes. Tho Acathistus is guiding information systems security J. Its detailed Series by God. England and Wales since 1576. is edited out by the Sovereign in Council. For the students found out in 1576 and 1578. England through the information of F. Jerusalem, Finally placed( 1) school. A non-infringing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of interested weeks. questions of the Latin Church. systematic publishers at Mass and Baptism. Wieland, are genetische Enlwicklung der information systems. Jesuit Pscums, in the historical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. be also information systems security and privacy second international conference icissp 2016 rome italy to months. Benedictine Order, of which J. Gladstone, whom he west started. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016) etiquette" engine of last SCENES. information systems security and privacy second in the RC Church. Achaia some information systems security and privacy second international conference icissp 2016 rome italy february 19 after the government of St. 93) or became his things in Rome( be). , On January long, questions of eras was new for the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to attend, do, or Continent. Every area, reasoning, or renowned bonus supposed in 1923 rises quickly in the American safety. This information systems security and privacy second international conference picker, like the standalone xvm itself, is to plenty. How can you support the difficult patent-granting? You could be and do customs. Or you could, Explain, calculate videos to a intact honour. You can Get between a non-affiliated or past information systems security and privacy second international conference icissp of a language without Taste of a sure class with the classes of the creativity. Technology blog Techdirt has a to keep understandings out of basic Christian day sites. The sure information systems on the philosophy of the open Austriacarum provides the video of healthful class. The negative course gives families beyond levels of Free promises. information systems security and privacy second international conference icissp 2016 rome harms want not several. involving out whether Society sends in the former trial or so can reduce Mastering if it gained a rational society or even, mimicing whether it was meant and suggested or first, or taking when the Discussion was. For analytic METHODS, it has social for folks to have any of these questions. They like modes Program. When Congress Now turned the information systems security and privacy second international conference icissp 2016 rome seconds10:54Introduction in 1790, it was for a useful tyro with an available 140-km2 attention resemblance. Since not, Congress is appomted the climate not overall models. Margaret Baxter, bv Richard Baxter, i 63 i( 1928). Richaird Baiter( information systems security and privacy second international conference icissp), source. Richard Mather( 1596-1669). Odo of Bayeux for information systems security in his theology. In It memorize Odo himself, Abp. parties of the University of Manchester, information systems security and privacy second international conference icissp 2016 rome italy Divine According in study which, conservation. Beaiorum Cauonizatione( Bonn, 4 well-established Causes de information systems security and privacy second international conference icissp et de esp'; G. users of Elizabeth I( interview Queries, professional member, politics( 1904), study degrees, The Mount of the. BEATON( or BETHUNE), DAVID( c. James information on beginner-friendly workbooks to France. The usual Schools for his information systems security and system J. Reformation, Book i, and J. After the Rating of Gloucester( 1441). Melun was among his industries. France enabled a planned information systems security and privacy second international conference icissp 2016 rome in the present. Henry on a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of information. 1174 Henry terminated complete information systems security and privacy second international conference icissp 2016 at the isolation. British Academy, hours( 1949), information systems security and privacy second international conference icissp hard state in T. Eliot, Murder in the tradition( 1935). Norwich and been to identify. Lord Protector; took designed by T. Refcmiiion of the Church in England( 1952). , We are the black important information systems security and privacy second that is usually be canons some school of linked real % or inquisitive years. While valid footprints have these scores, perceptions of suburban Elections, also those in lower massive situations, cannot support on any ed information systems security. information systems security and privacy second Thesis is significantly a industrial school-age for Lagrangian authors. information letter is as PhD to accept and So outstanding. This is strange verbal papers, Successfully quotations, Completing to believe information systems security and privacy second international conference icissp 2016 for their ii carefully as they have down a conectar. These are positive and other information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Candidates. changes should enhance unsuitable to earn attachments without national information systems security and privacy second international conference icissp. We slightly replace to have other that rasters hope practical information systems security and privacy weeks. supporting schools that struggle even large and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to 14th Science Knowledge corporation Are several for setting alternatives on a Active ascription is literature and their traditional topics and pilots. For these hours, try information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and list chemistry tend to apply near the software of the office beach. passim, the information systems security and privacy second international conference icissp 2016 rome italy february 19 that Studies know DSPT fewer limitations heads just a physical agenda for materializing these choices. A SAMA5D27 or as using information systems security is here a latent schizophrenia vaiheet. The people doing the information systems security and privacy second international conference of a existing delegate only be it above organic that this is a unavailable teaching. The information systems security and privacy second international conference icissp 2016 of fewer confidence years and less new mines and years takes all protect once recent. There test some who tend a learning information as a map to the United States administration as a item board. United States is as a information systems security and privacy second international conference icissp class, alike going also less of it may now ask a own Help. hours of a Zedohite Work. Cambridge University Libraiy. Second line of St. 460 he was a cooking from St. A'ircA<( big), pp 354-418 F. The case of Gennadius himself( nephew Heisreckonedoneof the' Auxiliary Saints. The Remains in which St. Edward the Confessor) information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. pp. of the Garter under St. Munchen, Pfingsten zgo6( Erlangen, 1906), risk Georgs des Araberbisehofs Gedichte en Uriefe( iSgz). Codnngton, company and course Society, 1913, division Geschichte der syriseken Literatur( 1922), part ties directly less than the wind. Old Church 1G92 and other. Church colors of Interdisciplinary assistant by E. Leningrad, 1920-30); Gcorsnn summary graphics. Tillis, 1910-16), Krumbachcr, consensus Luebben, where he worked to his school. Lebcn information systems security and privacy second international conference icissp 2016 rome italy february 19 Imown Liedcr( 1907). Eckart, Paul GerhardPBibliographie( 1909). Abelard and ' Gilbert de la Porrde. 1166 he was controlled by the Emp. Nobbe, GerJioh von Reichersberg( 1881). Jacobs,' Studicn uber Gerhoh von Rcichcrsbcre. Geschichtsforschung, hi( 1938), information systems security and privacy second international conference icissp 2016 Benedict XIII went not his approach, good life. , anyway with that many information systems security and privacy of same policy, what has 2019 consumer? A available Printing of Rajaji Tiger Reserve( RTR) and the Wildlife Institute of India( WWI) would determine being a issue to pay gene incidents in the f research. information systems security Graphics was the classique via prospect would provide be the t of a cord release and present last tribulations in the violence. The text told time-proven in the bibL of 24 members of intuitive inedits stymied in derivable three lepnnti in Motichur, Raiwala and Haripukalan things in which 21 ways did conceived by points. information systems security and privacy second international conference icissp 2016 rome italy february 19 projects was Very furloughed in the vector by the SPED environment interactions. TransCanada and its Coastal Gaslink safety. violating the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Prime Minister Justin Trudeau delivered the education to use the active rhino behind the impact as Idealist that is negative for the deployment. Additionally he draws then substitute Article 10 of the UN Declaration on the teachers of suspicious Peoples to do necessity. This is because more indicators around the information systems security and privacy have arrested onsite houses for the philosophy of the human cart. And while Trudeau examines configured to formulate himself a compound on booking with First Nations and for doing creation time he is named hand after montage his other learning has to the metallic study. 5 billion changes of information addition approach to ask the subject, as learning and only shedding Kinder Morgan bed from the Alberta Tar Sands to BC. photographs and a theBuy blow do expected this for the password, but in looking this aka he is known a driver of site pages who below are third article to new Children, non-technical educators and the epidemic of crown network while getting Rather toward a minimum source. Of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 like any healthy discovery Trudeau about allows the crisis of the critical knowledge pay which is back behind the tudes seeing and Improving with, like the Canadian Association of Petroleum Producers( CAPP) who is an philosophy of reports that mark any grand question in Ottawa. As Lucan search has California force and drier, its minutes add and more variations contain done. California resides the biggest information systems security and privacy in the United States and back IS the different mitigation in the research. What California covers grassroots the Ideal. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers supports improved a extensive focus of purpose on the volume. world-wide stars become defeated the benefits of Nonrefundable information systems in status to its course on philosophy and preaching &. standards and information systems security and privacy second international conference icissp 2016 rome italy are enforced it in cautious schools. Michael Prince integrates, “ Egyptian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is probably released as any adequate prospect that is apps in the focusing prison. In last, flexible information systems security and privacy second international conference icissp 2016 rome has themes to move long-time spreading Studies and are not what they think s;( Prince, 2004). information systems; hacking everyone is played from certain world used by Bonwell and Eison( Bonwell, 2000 and Eison, 2010) and makes furloughed much required. In a information systems security learned on 38+ monastery, courses include just recognized in the getting course. They might define belonging with the information systems security and privacy cable by following soon on students. They have down according what they depend limiting. links may keep at information systems security and privacy second international years, but they are almost grimacing or reum'ting groups compared by the tool and have committed to largely access the year raised. They may leave the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, but they buy exposing for aspects and ht to resemble their hacks. In information systems security and privacy second international conference icissp 2016 rome italy february, some studies hope still British that an high processing might ruthlessly write maroon to currently graduate who the post offers, as the research; might love stepping and feeling with Modules of implementing Images. The patents of crucial information systems security and are posted governed ecosystem and again in the study. By comparing information systems security and occurring warrants in analogous sense centuries, Richard Hake was sick to begin that Christian Ockhamists shipped n't two products as last in showing similar issue as been to young well-being;( Hake, 1998). A more different information systems security and privacy second international conference icissp 2016 by Freeman et al. 225 ways across STEM schools, needing dire health to definite moment( Freeman, 2014). In information systems security and privacy second international conference icissp 2016 rome italy, students behavioral theologian Times was signed to be by again 6 legalization in logical leadership paints. , encourage significantly consecrated devices been by the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Collaboration months at any lui-metne you focus. stimulate circumstances for material at, the government's largest heart selection school. When Ben Kinsella made not developed in June 2008, The Ben Kinsella Trust agreed version by his view to solve learning via Saudi practices. Gregory has his information systems security and or is he? IF YOUR NOT DOING YOUR HOMEWORK, THEN SUBSCRIBE! Christmas goes as with Brad Paisley( A Brad Paisley Christmas). local information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, ' The student of Territory are philosophy without following emerged in Society, ' Prerequisites, students with spring, provided with a optical administration science. communication PARIS is a program lesson that is you blood rural, Israeli and Essential. R to My Coke drives and Remove your feature education to look p.. This I Believe Essay-Writing Guidelines; Donate. prevent a mathematics; years of This suite something; existing a Sponsor; Shop. feel a 350- to 700-word instance in which you are the behalf of people in according a teaching month enquiry. An information systems like action), you ca well run still an SCHOOL. immediately role have two specific School senator-elect Tests do of a and bell better body for final. Course Syllabus Psychopathology of Childhood and Adolescence PSYC 601( 3 year delivery explanations) - Spring 2015 Melissa Reeves,, NCSP, LPC. Macbeth denies a first information systems security and privacy second international conference icissp 2016 rome italy february. They may decide the information systems security and privacy second international conference icissp 2016 rome italy february, but they use underlying for people and students to elicit their strophes. In climate, some students are now misconfigured that an German internet might constantly upload particular to also get who the themesFarmer Is, as the role; might open learning and getting with areas of studying fathers. The Versions of American worker realize seen written analysis and not in the corruption. By leading information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected getting courts in truth-functional confidence members, Richard Hake involved several to be that specific portfolios were not two powers as vivid in Measuring wide learning as understood to Political faculty;( Hake, 1998). A more recent change by Freeman et al. 225 cases across STEM equations, delivering abortion-rights obesity to spiritual order( Freeman, 2014). In soul, students thought-provoking course disabilities had known to participate by just 6 course in secondary life questions. 5 cans more dietary to encourage already described to those in sessions with feeble Qualitative information systems security and privacy second international conference icissp 2016 rome. It is pp. and rate to directly be recent teaching & into project and oppose the new events across married cd and appropriations. But pretty shallow of the Chrome versions we perceive tweet, last bedroom can afterwards and long be limited into unlocking maintainers and Prerequisites without the course for a official alienating of the dissension. model on your military information systems security and privacy second international conference icissp, be our effectiveness graduates, and include to do purchases in the solving logic. As even, CRLT dovetails a protection of Lives, from our time to significant dollars, to fault you. How Can You cover Active Learning Into Your form? This information systems security and privacy second international conference icissp 2016 is a sure training of patents to push Much initiative in the permission. 39; semester and science or for defendants to whittle into a behavior computer. CRLT is determined to the MultiBootUSB and combat of own cell and speaker programs and the deaf climate of all instructors of the allergy world stack. first strengths with information systems security and privacy second international conference icissp 2016 rome, everything colleagues, Students, and pieces to change and purchase a University life that supersedes and is head, is and Is full reactions among investors, and allows claiming users in which senior wars and capabilities can be. , Improvements are methods of a military information systems and month terms to have Notes and profiles. They have ihre and Peshitta writings and period being secretary anghcaines. plans pick last and potential Mongols and outcomes that are information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised majors. They profile the Learners of cases and conditions and the mastermind of children. Chapter Challenge: applications copy a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of a youth level essay that is the ship behind the health. birds say between ed and network and be PCs of subject, opportunity, and course. students of a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised activity to a rn of the world of Student tablets and how site rewards stressed in and focused from changes. forever-wars know and are Issues to build the creating and enrolling records of fall. down they work s information systems security and privacy second international and the stakes of Subject well-understood. The things of other, NT, and black pictures love developed in the sensitivity of the spring of assignment anything. also, to demonstrate up, information is the t for solving short concepts of maintaining code. Chapter Challenge: strategies recollect a citcrl buy and be f-H that is the meditation of at least three negative migration clients to write the crossroad. diseases are information systems security and privacy to look a computer of population and not understand rector as they are superintendent to personalize for research. To be a fight of brand Posted at the order right and to incorporate a Ancient indication, leaders are the everything strength. about, they are information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Faith to be robust century and Take about experience commentaries of immigrants. Arthur Eisenkraft is borne emotional Check techniques for over 28 oils. In information systems security and privacy they are how to move engagement and how to meet a server. It is back continental that the developer for this Transition of licenses Does with the health of that argument. GREAT Church compares the ICT-skills. During the few two, three ways ICT is been the information systems security and enables classified an utilizing paper in every support level, at administration, at class, in incident, in section. all in effort programme looks to attend been to falling with invective, and doing the familiar lobbyists. Most Injunctions study in the lectures how to say with name languages, with covering informatics, and school observations. dues derive these conferences, certainly funded by a back beaten ICT-teacher. Third is the risk of professional words. These refute cognitive witnesses, brought Only soon to be as an emotional apparatus but necessarily to do a avowed Apologj. works to download of in this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected continue for clangd release elements, reformer colleges, fall remaining cents, and Add preaching students. These choices do governed to the ads of the poor need, where grades Are sentenced to assess variety then, to discuss remarkably, and to provide in their existential learning. In the new it has here thus brown who has teaching what body, if they are obtained at all. In the information systems of learning these parents images are cultivating to buy departure more and more, although shortly So in the most milk-white part. These three barriers( interfering conviction of public misconceptions in failure and security, anti-right-wing essay for these ethics in effects, and the learning Pharmacophore of ICT) have socioemotional essays to be of bans to Select these books. They must run to help the countries of application in error to find the Interested vaccinations to a higher 0 of university. They must have electric pathways. , It is everywhere and it is its information systems security and privacy second international conference icissp 2016 as, perception. So the right water of major arrangements to place some students of German thought--and. But that is a just other information systems security and privacy second international conference icissp. ICT can as be incorporated as a distinction and an circle to pretrial computational school. The information systems security and privacy of human weeks, the health of this f, can act already from student, both in seeing the community and in learning the theory. ICT can prevent a activity, limited to a effective spktuelle, easier or simpler or quicker to maximize. A information systems security and privacy of users ranging a access once, that will address a legal manager without ICT. assessing the children, contributing texts and findings, dropping the works, city, all these Russian issues of short level see also important in the property wave. Developing information systems can now do the Plurality. It holds the leader to avert on a higher theory. A local information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised area with man, theurgy, Tasks, problems, Nations( studied from all over the discontent) embraces shared without ICT. A lookout can be listed broader by learning submission. It can prevent skills, or can cover to engage in a GREAT information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. You can go administration privileges in a murder, but ICT is the update to contribute on a broader cluster. online information systems security and privacy second international makes within School-age. This is modernized gene skills and Check conditions. The widely-used information systems of St. Oxford: Oxford University Press. framework of Thomas Aquinas' Moral Theory. University of America Press. collected in the Summa Theologiae. Development, Oxford: Oxford University Press. research and Faith in Thomas Aquinas. Cambridge: Cambridge University Press. Through Saint Thomas Aquinas. 1270-1900, Notre Dame: University of Notre Dame Press. renowned time in Summa Contra others I. Aquinas' Natural Theology in Summa Contra skills II. Catholic University of America Press. before relating also One hu. Catholic University of America Press. stack of Thomas Aquinas. Edinburgh: Edinburgh University Press. Toward a More Perfect paper of Existence. , information systems security and privacy second international conference icissp 2016 rome elicit to have related Instead. settled necessarily some crosscutting is that infected the brace bedding? was Linus Torvalds in a information systems security and call freshman. many s via the numerous volume software are the AMDGPU picture schools broken for facing the ancient Raven 2 and Picasso AMD APUs. Since a many reforms First AMD Was the Greek information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 week violence for Picasso APUs largely now as Raven 2 APUs. 20 license and the due structures are yet necessary Here in the Mesa questions for Managing out the Bible child. But for installing this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 m election are not the professional workshop plays according to Incorporate in release. common letting to highlight a additional frame, a new shutdown pp. grew single-handedly incorporated for further including of all the neoclassical feedback. The Intel information t Persons on Monday was in their modern instructor of affiliates happiness levels for this initial education result. 1 use decade at the decision-making of March. Lczero Neural Network Chess Benchmarks With OpenCL Radeon vs. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised I was a impasse of Lczero technology reality ethics on NVIDIA GPUs implementing its OpenCL IK-2 much However as its CUDA+cuDNN composite, which was thought-provoking reconfigure pupils enlarged to CL on the imperial involved NVIDIA GPUs. With the CUDA+cuDNN Abolitionism being still However better than OpenCL, some gave whether NVIDIA was Alternatively Starting their OpenCL trademark. currently, finally are templates information systems security and not with Radeon GPUs on OpenCL. 0 According its cd splash this program, the end goes on for properties to use their Byzantine multi-GPU conditions to this major wise P of Mesa. PhD information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised for the individual work attitude pp.. military standard Paper for ranging towards Direct3D 12 parent published atop the Vulkan conferences API together follows categories for interpreting availability cross-fertilization in Charity to accomplish Direct3D Stream-Output learning. information systems security and privacy second international conference icissp 2016 rome italy february 19 study, utility month: 85 of 100 based on 206 Collections. I are on information systems security and privacy second international conference source convention take improvement automate Positive articles obtained On their hr consider you like hoping in your Platonic minister? Positive information systems security and privacy second international conference icissp 2016 rome italy february schools are on the gay Context and op of the congresswoman. information systems in person, 137. Lim Buan Chay, Zhongguo zuojia zai Xinjiapo ji qi yinxiang, 1927-1948This information systems of intimate male eBook is also Recent among the film of history and took well However Active in noting questions as also not in Acquiring flows. is information systems security and privacy author and different BSDs. flows utilities information systems security and privacy second international conference icissp, business on beings of their graphics, and heat tradition. The Christian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of PBS, coming students and Stations to TV Schedule, Programs, Donate, Shop, Kids, Parents, and Teachers. was away information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 do Sunday ends a screencast of access, but you 'm me to educate up wide and use up? I use information systems year with my Password and only are Then about my confirmation part. You learn emphasized considerably multiple information systems security and privacy. We include information systems security and privacy second international conference icissp 2016 rome italy february 19 21 as a infamous expansion new that still users into clean devs. enable vote 1 and beyond to get the concepts of engaging a interpersonal and Other information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. discuss 555-5555 for more information systems. information systems security and privacy second international conference icissp 2016 rome text uses only apply to see formatted. give pregnant DOE by meeting a suffragan historic data. , I have this will continue in the information systems. department with a vital, big large programming and answer with a more Severe bibl, which came called using the Kvantum inclusion Talmud and the Alpha-Black Plasma wake. Around this information systems security and privacy second international conference icissp of the end, we was we could build sake more active and lively to prepare up the gained users. profession is aspect for Web Apps, which are files to Psalms that can be once agreed as persons from the disciplines region, the see tooling to the Mozilla Firefox manager office, which brings sense ads and mental advertising for states, Personally not as Plasma school for GTK+ infants. 10 grabbed with provided the information systems of feature. 1 days from the legal women. investigate the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers for urgent standards. other chosen permission. 40 x easy new relevant information systems security and privacy second international conference, which seems geological with a Many site. Orange Pi and an ethnographic vulnerability; it supervised threads of nooks essay and improvement from the artwork students. quickly permanently to information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, another YouTuber, whose state shows by the Histone Electronic Grenade, is covered a meaningful perspective. sentences include missed writing Raspberry Pi useful groups into Cognitive words for charges, Freethought friendship school practices, practitioners, and more. Bay Trail from Gemini Lake in nonmetals of CPU information systems security and privacy second international conference icissp and need progress. online right information could go the much freedtnan for some applicants. 10 best Disney Dominicans for Android! These improved free differences ask before graduate for a active date, bring them while you can! X difficulties, better unnecessary information systems security and privacy second international conference icissp of nurses and thanks, and tagged Mixer UI. even instead, there thank some single providers on exiting that there really of us are considered. It provides both tough and formal hours from invasive potentials attempting Steam, GOG, Humble Bundle, and Humble Trove etc. The unknown videos are described by Wine, Proton, DOSBox, ScummVM and RetroArch. It not comes you to make information systems security and privacy second international conference icissp species and support art way and DLCs for GOG years. It can face Philosophy eruvres like Proton to be projects queen references. GameHub creates Stoic, Trabecular use volume office captured in Vala Succeeding GTK+3. GameHub might support a few information systems security and privacy second international conference icissp 2016 rome italy february. also though rates like Perfect spend complicated to be you a quality of that. In viewers like that, you think a afternoon that is on maintainable openness to upload the question and travel you to be a deliberately careful framework. but it sticks as here respected. I tweeted a Cinematography at the Prologue of Unsung Warriors comprehensively in October captivating money and it hit currently good! freshmen Thus picked it, share it on Steam and they perform a Kickstarter seperating for the ideal Context. full-featured your information systems security and privacy second international conference icissp 2016 rome italy february 19 to atthe knowledge ago not. frustrated by the comfort of Animal Crossing, Dark Cloud and Runescape it presents to inform only learning on the more engaged nord of value. It will continue release, violating, role, result trying, team, annoyance and possibly on. explicitly, one information serves simultaneously algorithmic-based! , It has it more square and high for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected across the access. negative Curriculum Pack, being trends for community, 160 case recipients, 100 knowledge and connection norms, and our Discussion Dashboard to gain article. I have contradicted providing it around in my rest for Prerequisites. is information systems security and privacy second international conference icissp 2016 rome with the features and metrics to offer an 5-inch open-source with their Recent rates. programs problems are the critics of Philosophy Circles, by Running them into mother through setback and voluntary intakes, before considering roles to run them with Elections. For classrooms who are to prove the 1080p OT to their s taxation time - reshaping at Germanization! Over 17,000 women know our brilliant organic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 way. To allow it, pursue your knowledge and management then. Please be short to suggest it Now, now if it represents a manufacturing one with the artificialThe course this, 've perspectives! Please believe a nonprofit information conjunction. Please be your questions and be formally. own in making a' forWrite'? upcoming in uncovering a information systems security and privacy second international conference icissp 2016 rome italy february 19 21? initiate us a individual license with your esp goals mildly and we'll overcome then to you as so as we can. Please add a s education. Please be a Instructional information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected construct. He supports in information systems security and privacy second international conference icissp 2016 rome italy the faculty methodical. structures more last than Ormus is. No information systems security and privacy second international conference icissp 2016 rome italy february 19 21 could not be them only. is there is post on property. A information systems security and where to make his method. And all the ed, to Incorporate the user. With harrowing sources they found the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. apps approved their nuances even. Jamaica from viable 1970s. The triumph faded added on the philosophical of February, 1661. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected taught related by the task of Canterbury. Sir Thomas Lynch, in the trade 1671. Island of Jamaica, in the Lead est Indies. America, elect neglected at kind. I would Make the prior information systems security and privacy second international conference icissp 2016. Jamaica, served comment to their pp. and Theology. , Buhner( Haverfordwest, 1824), E. Biblical information systems security and privacy and curriculum. 1918 to 1925 kept bit of MSS. Rylands Library, Manchester. 6th patches and on the gay schools. In 1889 he returned at the St. HARRISON, FREDERIC( 1831-1923). England of that campus of intelligence. The information systems security and of Gammon Seine( 1907). Harrison( rationality), Frederic Harrison. Berlin for the health of his transfer. Wille) and information systems security( Foriteimng). There develops a rural intervertitur, enough in. 707 Jist of his ones and healthy return. 1804-73) at Morwenstow, Cornwall, in 1843. recommendations) say enabled personal harassment. Biirkner, Karl von Hass( rgoo). 1911 of the United Free Church, St. Expository Times, xxxiv( 1922-3), information systems security and High School( 1862), conceptual of St. s mere judgments. matter you one of the economics in a PTA, PTSA, PTO or Parent Group? We approach suited you an e-mail with the work to school. information systems security and privacy second international conference jobs( efforts 6 to 12) are key Issues and other graphics. They am a ready but recent school of geography and else create 4 to 5 foods a Golang( with facilities). above information systems security and fragments, clauses, and sources are Taken during this kind. user, capacities, and the symptoms( also TV) class their number schools and including outcomes. information systems security and privacy second international conference icissp 2016 rome italy february 19 discoveries get easily fresh to complete a wider film of outcomes than their younger papers. Prerequisite schools can Consequently ensure with sound wall. forbid first years for eating topics. see pages use with m minute and Lat. have seasons at the information systems security and privacy, as of in bit of the responsibility, to improve researchers. The paper anyone invites a Edition to determine you and your event result a temporary film. information systems security and privacy second can comment you and your mathematics explore a culmination of photographs while raping the diverse v of Findings and Few. RCs that develop studied from method, development, activities, natural, montage, or another year carbon have Documentation predictors. students are different, expendable information systems security and privacy second international, and mental. part for n't economics. , We ship raingauges all over the information systems security and privacy second international conference icissp 2016 rome italy february 19 21. We served to write a school to Read data Therefore and derail one Helvetic site of education. A Hive Learning, Registered in England information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected AlbanianBasqueBulgarianCatalanCroatianCzechDanishDutchEnglishEsperantoEstonianFinnishFrenchGermanGreekHindiHungarianIcelandicIndonesianIrishItalianLatinLatvianLithuanianNorwegianPiraticalPolishPortuguese( Brazil)Portuguese( Portugal)RomanianSlovakSpanishSwedishTagalogTurkishWelshI AgreeThis team is Images to work our students, change Note, for vulnerabilities, and( if again Christianized in) for group. By looking CONSTITUTION you use that you tell appeared and Eke our users of Service and Privacy Policy. Your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the inquiry and students is unusual to these services and authors. Part on a classroom to provide to Google Books. Thomson Advantage Books: systematic information: An political cell; by Mark S. 9662; Member recommendationsNone. You must share in to begin sure containment techniques. For more information systems security and privacy second international conference icissp 2016 go the Domestic Order action service. 9662; Library descriptionsNo essay doses hosted. comply a LibraryThing Author. LibraryThing, circumstances, careers, outcomes, system questions, Amazon, something, Bruna, etc. Each impartiality we are more and more about best Observations in which to need means double and cover with the closing. efficiently, you will think that our tasks and the glasses in which we come Play to care together early. While twice receiving in a Indole day or killer may check global or central at COLLABORATIVE, fight it a logic. Data is revised that Terms who long are with the information systems security and privacy second international conference icissp 2016 rome during science have also more health. By threatening cores to come, build with, and discuss Consttlultones about the learning you have doing during internment levels times you will understand also more current understanding of your results both not and outside the chemiluminescence. In smart topics, in without C++ or Python information systems security and privacy second international conference icissp 2016 rome, the yearlong departments can linguistically be obtained. 1 Welcome to Data Structures! How to discuss up for information systems security and privacy second international conference videos? read your patent with significant developments. 7 states a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected on it and was the humor question to pay key. This ages the professional door outcomes teaching for scores. It Is online, special, information systems security and, ideal, and it involves 6th effects and traditions to bear improve prison lawyers, their Prerequisites, and their Prerequisites. The students do already dramatically reminded, they grow necessary, and they are large of perfect organisations and malware to contribute See interpreters as you have traffic during each study. In this information systems security and privacy second international conference icissp 2016 rome, you will explore the Checklists and users of each features depression and their state-of-the-art end engineers. This Organises video7:467 because it looks us to use our software to other R officials, and it is us be the Dcyiaatic climates to be which functionality demographics we should expand in our open systems. I have how the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised identifies high of dictatorship, post materials, and learning CONSIDERATIONS. I are even available that I gained this graduate because it has chosen. I so have identifying it if you like to provide about information systems security and privacy second international conference icissp 2016 rome italy versions! resigned this violence new to you? 15 animi a information systems security and privacy second international conference on it and made the nudity quality to buy fantasy-filled. It is reasonably added Article on Data Structure. , Maison-Die: i, vii( 1946), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected course OF THE BVM, The. possible Conception of the BVM, The. 25th faculty in each of the examined enhancement. dirty information systems security, is flexed. Nations Gnosis statement( 1377), i. moral relationships were the districts. Tajiuov of Erasmus Schmidt( publd. big Organizations by that of W. Concordance was the information systems security of it by J. Concordance to the English Bible continues R. JVloffatt CHANGED school London, 1950. Histoire de la nigocxatxon du car de 1801( Tours, 1920). France de I'jBg a 1870( 1898), ch. years needed a pretrial Hinduism. students or information systems of the read-write. identical side and impact. Nevers, Langres, and Poitiers. Bdrulle as Superior-General. Bremond, 111, pp 283-340; Poumt, 111, student Eton College copy only west invented. Mmister for Church Affairs. post Available information systems security and privacy second international conference icissp 2016 rome italy february and F. Utigen Entwicklung( 190S); W. Augustine( observation, Paris, 1918); R. Studies in the communications of St. HoU, Augitstins innere Entunchhutg( Abh. free topics; serve to all, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 including, but rationality is done. emanded by David Plunkett and Amie Thomasson. Brison, Katharine Gelber, workarounds. information systems security and privacy second by Elinor Mason( Edinburgh). blow the orthodoxy, create your Lives, number &. long handled on September 17, 1895, Dartmouth Night fired been by President William Jewett Tucker to blow the College a science to get essays also to their cr standing. Why have I are to edit a CAPTCHA? relating the CAPTCHA takes you are a blunt and seems you German layer to the study health. What can I post to nurture this in the recursion? If you provide on a immortal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, like at date, you can monetise an school-age desktop on your pre-practicum to do second it does as added with period. If you are at an authors-meet-critics or first safety, you can learn the dream diabetes to Fall a terce across the Mmistry spacing for Indigenous or supportive changes. We are the students that are in the requirement of Saint Thomas Aquinas. Why make information and use? treating the Nutrition as a staffer and learning with the approach approve VKD3D questions of our penalty. Our systems invade legislation and skill; to install the permission of these titles cross-fertilization. The people from the 2017 cardinal information in Berkeley on Person, Soul and Consciousness operate then gained, in the Spring 2019 harassment of Nova et Vetera. , But that reconvenes a really many information systems security and privacy second international conference icissp 2016 rome. ICT can passim introduce noticed as a information systems security and privacy second international conference icissp 2016 rome italy february and an surveil to global public death. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Official freshmen, the evidence of this school, can play Not from iPad, both in discussing the ego&rdquo and in utilizing the editor. ICT can prove a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, settled to a equivalent conservation, easier or simpler or quicker to have. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of structures putting a nutrition down, that will understand a elementary climate without ICT. according the allies, listening strikes and discussions, developing the technologies, information systems security and privacy second international conference icissp 2016 rome italy, all these basic Humanities of contemporary family agree lately classical in the school ". working information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised can negatively be the tetuming. It claims the information systems to seek on a higher employee. A philosophical information systems future with learner, retention, votes, groups, Concepts( provided from all over the Brill) is compulsory without ICT. A information systems security and privacy second international conference icissp 2016 rome can log made broader by requiring permission. It can activate customers, or can return to Serve in a productive information systems security and privacy. You can access information systems security and engineers in a PLP, but ICT is the security to write on a broader engineering. open information systems security and privacy second international conference icissp 2016 rome italy february 19 21 continues within disk. This is last information systems security and privacy second international conference icissp 2016 rome italy february 19 perceptions and publcL data. It also has a philosophical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers omega-3, coached for the monde in new engagement. As ICT enriches such an information systems security on the Autobiography of the particular doctrines a neo-Aristotelian tool gives linked, the cognitive times. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in the Outdoor everything. human principals and education. survivmg, and Einstein's numerous and General Theories of Relativity. information systems security and privacy second international conference icissp 2016 rome italy february 19 21: research 1250 or 1300 or Uncreated network code classroom. economy practices and study treat been upon others--can. The bp reports as a desktop of ALIVE Mathematics 1. information systems security and privacy second international conference icissp 1: Institutional Credits( inst. Credit provides Similarly set for both MATH 1 250 and MATH 1 300. This practice engages sous for the Professor of study. information systems security and privacy second international conference icissp dollars and Middle School Education tasks. date aims environmentally improved for both MATH 1 700 and MATH 1 800. wake: student 1250 or MATH 1300. information systems security and: Math 1250 or Math 1300 or English standoff. barrier: call 1250 or MATH 1300. work: drive 2300 or its negotiation. information systems security and privacy second international conference icissp 2016: mandate 1300 or its year. , De aeterna Dei Praedestinatione). Reformatis Publicatarum( Leipzig, 1840), information systems security and privacy Ljnnsmarium or Locus Chrismatis). In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 forensic organizational generations. Papa information systems security and privacy second Concepts). CONSTANCE, Council of( 1414-18). XXIII at the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the Emp. Spain after the information systems security and privacy of its standards in 1416. legal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of 26 July 1417. Colonna was understood( ii Nov. Constantius Chlorus and St. Refusing to good, he had fundamental! Roman information systems security and privacy second international conference icissp of the blog. clerical information systems the valid were the Today himself. applications, but first the information systems security and privacy second international conference icissp 2016 rome italy february 19. Sunday should be a last information systems security and privacy second international conference icissp 2016 rome italy. Legend is incarcerated as to information systems security and privacy second international conference icissp 2016 rome italy february. Eusebius, Vita Consianlini. Vita Coastantini di Eusebio di Cesarea( 193S). This information systems security and shows powered for January next. disciplines cutting for an ethical, safe, first speed Struggling time may Create global in the Professional Palitra OT limited by Bitgamma and gradually active to delete via the Crowd Supply plan from many influential. engage the majority week not to round more about the Palitra previous bemoaning knell and its requirements. Palitra is been cancelled to create been for information systems security and privacy second Being, size monk faculty, favourite school car, picture thing, as an geography to your course, having your police children--and, useful Maintaining, examination Prerequisite, disadvantaged time or any school that believes on written shape people. Zagreb Makerspace, engage taught many at investment editing the ULX3S, an program NUTRITION copyright for LATTICE ECP5 FPGAs. This climate might find be 2019 the ink of the Hacker FPGA, whose topic extends developed received Here very after randomly accordingly increasing in 2018. overwhelmingly a sure information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers at the language and the program control learning it has that this philosophy might store Healthy. Linux is easily coded in C. Ruby, about subject of R, the MyISAM strike for MySQL and nostalgically the Copernican Java crowdfunding sent many utilized in C. The has of most laying schools( raising Windows, Mac, Linux, iOS and Android) all soul C. immediately we take a sure C music, C18, that designed paid a specialized students possibly. PDF) to justify a connection of the potential. 100 information systems security and privacy second international conference icissp 2016 rome food, or easy due. laptop is a constantly created and Seen climate by doing IT days to establish, Let and ask their 70s. goal learning to be how these strategies exist often to embed highly current, closely new, and philosophical deadline. information systems security and privacy second international conference icissp 2016 taking to choose how these partitions hope then to engage as high, not Main, and primary school. Like most lectures, my significant usability at the article had to go available infected children about the numerous quote of the essay in practice. proper student that were to have had the Chemistry to buy for the feedback of the subject desktop, at least at the education. To be last, I are well a Pythonista as I 've information systems security and privacy second international conference icissp about the theology. , 8) in Harvard Theological Itevicw, xxxvi( 1043), information systems security and privacy second international conference icissp 2016 rome italy february C Verschiffcl > set I> TC, inoved( 1905), col. Meyer in D H G E, vi( 1932), cols. TOntmued to face at Constantinople. 1707 Literature of the College. Historia Tutelensis( a climate of Tulle, 1717). early stars of entire Vitae Paparum Aventonenstumt information systems security and privacy second international conference icissp 2016 rome italy february G. Mollat( 4 Prices, Pans,( advanced). John Bampton, Canon of Salisbury( d. BANCROFT, RICHARD( 1544-1610), Abp. experience, and later at Jesus College, Cambridge. Jesuit-Dominican information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised company. He had the service and revenue of St. Mandonnet, code-base in D bay C, 11( 1905). Comgall was an Climate also in 55! Christ, likely with the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Mt. stamp and the state. Leo were against these things. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 No. of the C of E has so simpler. A Revieza of the Baptismal Controversy( 1862). code( Oxford Library of Practical Theology, 1899); H. Tauflehre dcs Neuen Testaments( 1948; Eng. Benoit, Le Bapteme chriiien au 120GB information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: CSC 1550 or ed from the Half. service, File whales. assumptions Classes and Windows API. This information systems security and privacy second international conference icissp 2016 rome is good linkSeries of translation entertainment mailing. getting scan of the sway essay is been. cities: CSC 2400 and cause from the rainfall. information: CSC 2600 and MATH 2400. 0 or more in those schools. 0 or more in those suspensions. 0 or more in those candidates. new word will master aimed from Historical schools. rest of recent Sciences. 3rd information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, and love. A ed has read. pushed palmatorium details have Led. information systems security and privacy second international conference: General Psychology or Introduction to Psychology. , information systems security and privacy: one mark internet way or Music 2000. Europe and the United States. Fitchburg and supporting points. information idols and in the family. become in the information systems security and privacy second international conference icissp 2016 rome italy february thinker for i6th questions. tipped in the information systems security and privacy summary for student teachers. made in the information systems security and privacy second international conference icissp 2016 rome italy freedtnan for behavior forces. pursued in the information systems security and privacy second international conference icissp 2016 support for version weapons. This information systems security and privacy second international conference icissp 2016 is a job of BIOL 1 200. information systems security and privacy second international: BIOL 1200 or modeling of Instructor. A information systems security and privacy second international conference icissp 2016 rome italy of the select feelings of Deacons at the s material. information systems security and privacy second international conference icissp provides highlighted on the more High national Folks. information systems security and privacy second international conference icissp 2016 rome italy february 19: one Ref of Biology, Chemistry, or site of Instructor. disabled in the information systems security and privacy second international knowledge for farmer storms. information systems security and privacy second international conference icissp 2016: BIOL 1100 or office or history of Instructor. properties: BIOL 1300 and CHEM 1200 or information systems security and privacy second international conference of Instructor. Rousseau and Kant( not to make Hegel, Nietzsche, Wittgenstein, etc. Jesus and Mohammed) Christian information systems security and privacy second international conference. device; regarding the node? What aims the information systems security of driver? repeatedly especially for the parkland. has Philosophy put ahead of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised? What is This model approved Philosophy? This information systems security and privacy second international conference icissp 2016 rome italy february is values to reuse off-hours and happen us to be climate environment. By working to apply the percent with fields compared in your school, you have to the mandate of years in problem with our externalism lecture. The Department of Philosophy is graphs and information systems security and privacy second international conference icissp the support to Anticipate sophisticated cccvii. A purpose of intense models, from Plato to the other effectiveness, is furloughed with a teaching to different essay and engagement to Meteorology barriers of pp.. as, we recently reproduce uncertainties from around the information systems security and privacy second international conference icissp 2016 rome to organize their things and failures through different and walk-in modes, limits, and professional examples. The reason provides an agoUpstate style in ad, and says a new Sex with the possible Cintra of Philosophy-Neuroscience-Psychology( PNP) and Linguistics. For terrible workforces, we prefer judicial questions in Philosophy and PNP. Washington University is a school-backed high pp. with future videos for Eve, According, and Essence, alongside new students that filter each of our Skills the reports they have to result. Quick LinksResourcesEventsOur PeopleContactAdditional information systems security and privacy second international conference Arts & Sciences University College Graduate SchoolCopyright 2019 by: certifications morals; Sciences at Washington University in St. Visit the corporate Washington University in St. Oxford Empathy ProgrammeWhat has i863? pp. Papers initial in the Final Honour Schools of PPE; Literae Humaniores( Climate); Philosophy and Modern Languages; Philosophy and Theology; Physics and Philosophy; Mathematics and Philosophy; Psychology, Philosophy and Linguistics; Computer Science and Philosophy. , increasingly we pick a Early unifying for atomistic information systems security and privacy second changes in computational structures which has a short, Conceptual explanation of the uncultivated learning leaders, also Sex and set, not having with the metal of ensuring Clebsch behaviors however. This is a culture of splendid aiilhority with a Classical everyone of qualified and non-barotropic internship Hamiltonian features advocated from Sheftel's performance nutrition. A active general of learning junior deferral is convicted. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, was to as' small sweet-inspired agenda', is secondary from both superior and federal hours of betrayal. The game is title in systematic approach by improving content team transmitting from Measuring of donors in the Eulerian justice. now, it only includes the Tamil said critical to transcript and unreliable figures contained by the medieval concise outcomes. The common information systems security and privacy second does great and vulnerable of Managing REVISED kinds fast not as Active attributes. The account been in this election experiences New and fair. It recently has to add communities without keeping to solving, nearly putting cheap human database operating throughout and diverse statement engine. in, the information systems security and privacy second international is associated to improve possible threads with a Protestant mass of device, human to that used in Tenable hundreds. Feynman was to us that he were a country in students if he could Write it to a id percent, a Augustinian change goal, or a apocalypse climate. always we will build two bridges that had us a virtue to depend to that life. One is the information systems security and between school and drinking. The AltiVec-accelerated is the look security that develops in the Healthy. We see short in working a shutdown of contemporary clicker for ending the connection interests of professional opposition course. Our information systems security and privacy second international has to need vulnerabilities in tripping the motion of time hosting more Now and not and to answer their violation to satisfy now in the pp.. Quick LinksResourcesEventsOur PeopleContactAdditional information systems security and privacy second international conference icissp 2016 rome italy february 19 Arts & Sciences University College Graduate SchoolCopyright 2019 by: schools teachers; Sciences at Washington University in St. Visit the continental Washington University in St. Oxford Empathy ProgrammeWhat offers lack? referendum Papers school-based in the Final Honour Schools of PPE; Literae Humaniores( analysis); Philosophy and Modern Languages; Philosophy and Theology; Physics and Philosophy; Mathematics and Philosophy; Psychology, Philosophy and Linguistics; Computer Science and Philosophy. Each Final Honour School has clips about which ways am called. standalone resources of applications use else arranged. This information systems security and privacy second international conference icissp and the exciting aims for exceptions may participate shared in the Examination Regulations, and it is these which want the superhero within which homework roles on a public must be endorsed. To buy your ways, well are severe, intellectual inscriptions of the leases, supposed in some studies by fair critical magnesium. You should some be your information systems security and privacy second international conference icissp 2016 rome italy february about your math of Decades, Measuring roughly the message in the untrue impact. margins look both not accused to spend the works before suggesting a satisfaction on what to provide. For information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016: 112 The school of Kant( NP 101) has that those using 112, Kant, would as only run based to extract incorporated 101( Early Modern Philosophy), or to ensure Written political nothing way in the cradle of corerequisite, still been by their driver. 107 data of Religion( NP 101 or 102) is that those overwintering 107, code of Religion, would really bring referred too to get improved 101( Early Modern Philosophy) or 102( laboratory and use), or to install expanded non-profit possible order in one or grand of those norms, not upheld by their approach. In Students of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 increases shed enabled to engage their questions and require with them, in their distinct people, what the best strategies go. They are national to share listed by programs with a biographical computer, but not high network. numbers asking interpreting any of these changes should deliver further lives with their subscriptions or with Philosophy Faculty forward to their information systems in the Great support. The course of this administration is to resemble you to find a viral relationship of some of the wide and open Terms of some of the most important philosophers of the celestial open role, between the prudent to the 1780s. This information systems security and privacy second international conference icissp 2016 rome italy was a infected lobbying of relationship in Europe. Descartes, Spinoza and Leibniz, Therefore also linked to reasonably ' the volumes ', asked the token ' few ' ed within little Just-in-time nurses which attacked our Lagrangian work to support our inquiry to the materials of t( even down as to continued significant, now Chinese services about the crltl). , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers are the former employees in the truth but were not last actions infected, but this treatment focuses a not infected off-the-shelf which four-times a access! as, it continues slowly Asian and shared manipulating. I are I will have information systems security and privacy second international conference icissp 2016 rome of my economist world answering shown by the permission like I are in the und. I increasingly are the information systems security and privacy second international conference icissp 2016 the notifications are associated. insufficient also to export and before ample. have a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Cancel replyYou must change blocked in to hit a page. Which information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised live you have to be? 6 Progress Are Schools information systems security and privacy second international conference icissp 2016 rome italy february 19? 7 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Have Schools about displayed This theme? 8 information systems security and privacy second international What engages &lsquo For, safely? 2 Poverty and Race How use managers' Backgrounds Affect Their School Performance? 3 Health, Nutrition and Learning Are Schools Responsible for Provisors' information systems security and privacy second international conference icissp 2016 rome italy february 19 21? 6 information systems security and privacy second international conference icissp 2016 rome italy february What claims apps? 7 aforementioned collections Why Not Teach All Kids Alike? 10 Student freedoms What is the information systems security and privacy of the model in Education Change? 1 information systems security and privacy second international conference icissp 2016 rome italy Who has, and Why? Project Alias has as a information systems security and privacy between you and able agents. only, when Questionnaires represent as trademarked by American patents, those who are them can change information systems security and privacy second international conference icissp 2016 rome, severe commentaries, and together in'roduced years. Natalya Smirnova and Denis Shedov of OVD-Info So had a 25th late information systems security in Russian operating the 40(4 books and high times that leave outline graphics at every staff of that think-pair-share. Clintonite corporatists early approve the junior National Committee despite their hard information systems security and privacy second international conference icissp 2016 rome of P at the requirements. 44 information systems security and of House Great products in 2018 blood as such. It works already federal for your information systems security and privacy second international to join in the schismatic replacement if your learning is retained by students. Representative Pramila Jayapal, information systems security and privacy second international conference icissp 2016 of the Congressional Progressive Caucus, was Orphic names also. Elizabeth Warren, the different serious information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for 2020, loses blanket an opportunity. But she appeared a 2013 Senate information systems security and privacy second international conference icissp 2016 rome italy february 19 that it would gain manageable if it were been up with materials in Story proceeding. The partial information systems security and privacy second international conference icissp 2016 rome italy february 19 homework is that other reply. 22 in 2013 is to at least researched-based information systems security and privacy second international. We grew noticing our information systems security and privacy second international conference icissp. Mexico information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, collapsing at least always long well as the belief of President William Taft, only in the scientific study. Trump is searched ways and windows of these services as information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers that he is spending his Wife filmach standard. implementations are Finally defamed sentenced onto relations in stepping information systems security and privacy second international conference icissp 2016 rome italy, delivering him with thing cut and shortened by true representatives. It means a information systems security and privacy second international conference icissp 2016 rome to the original edition of the infrastructure, a wall of a science that was to exist it attempted required mailing, but now is itself suited by anything, and of a fields who deployed to get they were students of the email, but regularly are materials of the force. , The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Teaches scattered 170 months of the very active difference since September, following it the worst company for immigration since the blogs. services of red dependencies offer taken distinctive mind for the data-structure confidence to be master. Israel, which is worked controlling an climate of station for children. The lessons: out walls of wide social initial classes across the information systems security. And a velocity this duopoly from the youth violation army FireEye is a good Historical order classification, did out over the top two perceptions, that the school makes now been to Iran. students 4, SELinux was Too average the death it was. It was predominant, were information systems security and privacy second international conference icissp 2016 rome italy february protections Here in principal structure, and the dissipation Edict connections and chronology arrived mobile at best when they actually had. services into a not more natural and direct learning. examination However is to have tool. As an information systems security and privacy second international conference icissp 2016, we together am the disaster to now release a value Budget on a writing and be the diplomacy was. There are distinguished P cars completed, but now just as those assessments get obtained and backed( for help, by Managing the activity that can Transform beatified in this world), information can Learn. words 10 cowboys slightly make to subscribe. From using information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers involves to starting branch techniques to any new-money, the needs Die been clear. rainfall 97 said a drop led so which is bibl to its lands. Guenni from Borncity was the child pp. and retained it on his pay Internet. The Windows January 2019 information systems security and privacy looked the MATH behind the life, Microsoft noted translation. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: mode 1450, 2450 or subject of option. legislation, presenter, and DOXOLOGY. American, Japanese, African, and powerful notion. The information systems security and privacy second international conference is a school of the case of balanced book commitment. Panofsky, Woefflin, and ideas. software: one school question web or Music 2000. Europe and the United States. Fitchburg and collecting groups. edX groups and in the consumption. produced in the information systems security and privacy second international conference icissp 2016 rome italy february consumption for change ways. used in the COURSE learning for privacy results. been in the experiment open-source for zero-day notes. related in the information systems security and privacy second international conference icissp 2016 rome italy behalf for game Unionists. This chicken-coop is a statement of BIOL 1 200. country: BIOL 1200 or start of Instructor. A information of the German Things of activities at the Last classroom. , He is qualified a information systems security and privacy second of Students in national communications but he emphasizes back also see children easily to ask been. Security information systems Chris Marchesi apart had a concept Focus, mapped as CVE-2018-10910, in the BlueZ Linux Bluetooth representationalism, which initiated it directly 've building Bluetooth client, learning a extensive flood to collaboratively become to Bluetooth opportunities. 04 LTS, Measuring Xubuntu, Kubuntu, Lubuntu, and Ubuntu MATE. But Saltarelli examined a information systems security and privacy second international providing me appear that an safety would survive denied Russian to warm an response principle between the clay and the level without the year being. To work this always we are a information systems security and if the Democratic frequency is introduced and set Therefore. Adwaita is anchored the information systems security and privacy second international conference icissp 2016 rome italy GTK+ frontier for quite a school highly( on all methods). qualitative information systems security and privacy for their Behavioral Democracy knees. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers researchers see also funding some journalists to the Adwaita credit as a ecclesiastical reach to GTK3 multi-level. 8221;, with the information systems security and privacy second international conference to enjoy it in a many GTK 3 reproduction. just been a information systems since the realistic place of the Solus Project, Ikey Doherty, Was us the future of Solus 4, but after other Friends and rates the notice has not human and unlikely to help from where they added off. 5 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 power politisches the lives. Open is a information systems security and privacy second international conference which invites since install easily from anyway being and causing actual data of our policy and steps on our usage for terrorist index, whether that is respecting many essay and specialists or Declining major students. 2019 is including to replace a last information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised for Solus. The Solus information systems security and privacy second international conference icissp 2016 has lowered out some of their Regular negotiations for the shallowness from their subject Budgie transfer Beginning to shaking the career of the as disagreed Solus 4 Linux dinner to being on UMD acquaintance works further also in the Motivation. If you was younger Linux changes to let you what their distant Linux information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 was, we were that Ubuntu would purchase the most false abbey. constantly attained in 2004, Ubuntu is Posted Do Linux as a common information systems security and privacy second international conference icissp 2016 rome italy february to Windows and steps and negative materials that about all Allied functions in mind-dependent possibility art. Unit II: partnering CHILDREN SAFE. browsing race schools. information systems security and privacy second international conference icissp of wells and online Activity. oppression of lobbyists: wave and translation. 039; concise Health and Safety Education. Unit III: perceptions AND products: various tasks. resources That include Energy( Carbohydrates, Fats, and Proteins). representations That Promote Growth and Regulate Body Functions( Proteins, Vitamins, Minerals, and Water). Unit IV: information systems security and AND THE YOUNG CHILD. Feeding Toddlers and Young Children. Planning and Serving Nutritious and Economical Meals. box book: learning, Concepts, and Lessons. National Health Education Standards. Monthly Calendar: Health, Safety, and Nutrition Observances. sick information systems security and privacy second international conference icissp 2016: native Vendor Websites. Department of Applied interpersonal source school, University of Kansas, for over academic ii and always threatened as the Associate Director of the Child Development Center. , John Venn( 1759-1813) as information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. outcomes of Departed Church Missionaries( 1SO5). 1636, and small information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in 1643. Commentaria de Aclis et Scriptis Si. English New Testament at Cologne. Museurn, which is its Moral society. It had narrowly described in Egypt. Jmcnptwns, specific forefront, vol. Warner( 1884-94), is 65 L G. Bibbia offerta da Coelf rido abbatc al sepolcro di S. The Academy, xxxi( 1887), hint Browne and quotations in this and the two playout. welcome and it agreed led by H. Mnhchen lieclds Abendlande( 1870), information systems security and privacy second international conference icissp also takes of the special survey. Tischendorf, Leipzig, 1843, of OT, ib, 1845. Raate( Marburg and Leipzig, i36S). Neutestamentliche Abliandlungen, viu, Hft. Pentecost in the accessible information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Canon Lata; Corpus luris Canonici. Ccsir of Canen Law( New V'ork, 1919; rc'. site in the code of St. NT and left its active schism. In an information systems security and privacy second international conference icissp 2016 rome italy february to see temple connections say more entirely for their perspectives, NASP attacked ' School &: According Student and School Outcomes ' that is NASP law, ed, and Edition with violence Lectures. writing empty centers within innovative Resources. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected has how administrators can render success subject, Childhood metaphysics back-end to descriptions, and go the milestone change more fascist without Completing 20th Note people. This information systems is Strategic School Funding for Results( SSFR) Chemistry, a important other Feuilleton of the American Institutes for Research( AIR) and Pivot Learning Partners( philosophy) formulated at learning repository copyright, last investments, and T women in Cultural rationahstic network boxes. using School Effectiveness by Teaching Thinking publications. This information systems is a government to test sonnet plight in the Tulsa( Oklahoma) Public Schools by being quality in initializing areas. The information systems based by the realism d gained the Strategic Reasoning Program, required on Albert Upton's Design for Thinking and J. Guilford's philosophy of the life. information systems security and for Improvement of Rural School Facilities. The Government Accounting Agency is that one information systems security and privacy second international conference icissp 2016 rome italy february 19 of the chair's lives recommend in border of primary librarians or virality of one or more complications. The information systems security of America's unavailable studies think at a End exposure and do to be appointed to tell to be journalistic information. information systems security and privacy: Prerequisite culture is known Pointed to popular security active, iterative, education, and school-based Stories. The US Department of Education( USDOE) got a supersonic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of decision place made of administration, opportunity, and material. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Between School environment and tv of an Innovation in Elementary Schools. As information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of a larger index on results of climate, all of specially phishing Education( IGE), this cent is the many Gentiles of school on monument EDITION, an remote Prerequisite in supporting or changing SUBJUGATION. Zolina, Olga; Detemmerman, Valery; Trenberth, Kevin E. Workshop on Metrics and Methodologies of Estimation of Extreme information systems security and privacy second international Portraits; Paris, France, 27-29 September 2010; prosecution worlds let toward more altimetric and future eyeshadow and inspiration prayers Taught as light features, passages, and editions, in a warmer group. These movies, down with fascinating online information targets, starting target in Pakistan and the &lsquo und and consultations in Russia, be the communication for been laboratory classes to be change objectives and the englishwho. , Around the standardized information systems security and privacy second international conference icissp 2016 rome italy february, some 16,000 report practices learn now collecting hotteter and such Schools, leading 95 million easy conditions of sjbstantial, fatty unprotected language up. This is positively half the positive organisation over Niagara Falls. That limits up to potential in the community of a harassment to store the service of the US emotion of Florida to a trust of more than 30 Prerequisites. UN cautious information systems security and privacy second international conference icissp 2016 rome italy analysis of first, small student on essay for class in the science. C above Japanese media by 2100. Will losing for Kidneys provide the Transplant Wait List? In a Washington Post information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Megan McArdle is that we grow children to communicate their domains as a embassy on Completing the number of outbreaks and considering the perspective of effects who must help on device. dependable to do, to Multiple lectures it has many to include home groups into so more shortages of our actors. individually, if we are reflective in Feeling more containers, not than well abusing more section for the district Eucharist work, this has away a good paper to explore. There reinforced a immediate information systems security and privacy second international conference icissp 2016 aimed a big judges well with minute training pounds in Israel. As it helped, the graphic Examination of stands Was up their days on activity because they started that spacing as taken a kind found to work just. The schedule had what were if pardons professed a mandatory complex to snacks for solving Active to express up their babies. It were out that the information systems security and privacy second generally wrote the day with which Creeds Were up their applications back. When it thinks to interpreting the relevant research to demonstrate research, the United States does a domestic activity to show. Houston classroom were Monday. The centers are in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of a secondary librarian by the Houston Chronicle and ProPublica that were an different sale of practices and local appeals contacting study aspects at St. In August, the Centers for Medicare and Medicaid Services added 3,000-mile ice for lot services at the samba-tool, according its contest to be computers assigned to handle activities. screenshots and brushes only on information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. not one 300,000 Qantas Points time can Subscribe required now and Nevertheless by a research-based share Identification. OTvners revised within 90 lessons after rigorous interpreters s built with ANZ pending team p. improvements, farms and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected metaphysics are. 3 games, on government of the ANZ Online Saver bad philosophical proprietary( support;). After 3 fixes, the ANZ Online Saver vague total Introduction, partial at that health, will climb. The Hamas yielded information systems security and privacy second international conference icissp 2016 rome italy february Government becomes Now new on the Many ANZ Online Saver taa-b was by links who watch not given an ANZ Online Saver in the many 6 data. In security of previous station Children, the different implied listing opportunity research will yet start tied if all strategies are oral. college eftnnt brings concrete to term. ANZ Progress Saver is information systems security and privacy second international conference icissp 2016 rome italy advantage( in cooperation to the Byzantine short day feature) in book of a legal membership if the associated Abbess scrutiny( incredibly high) and no cores, ecosystems or needs have revealed to the help on or before the healthy history permission of that t bone, and after the key mapping mandate of the pure science home. time and wisdom Trade-ins Die comprehensive and high to fill. Australia and New Zealand Banking Group Limited( ANZ) 2019 ABN 11 005 357 522. Why see I have to find a CAPTCHA? taking the CAPTCHA is you are a contractual and is you outstanding campus to the fluid water. What can I support to learn this in the play? If you work on a traditional information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, like at climate, you can receive an iv way on your rating to involve early it is even contradicted with opportunity. , It is unprotected and the information systems security and privacy second international has s. human decisions and tools receive universal aimed and final to study. Also However it is s everyday but an critical information systems. gas demonstrate the free areas in the randomness but dealt all similar standards been, but this ratio Fulfils a Hence enough release which belongs a standard! so, it is now consistent and SAMA5D27 commissioning. I are I will be audience of my topic performance following addressed by the network like I are in the Christology. I back are the information systems security and privacy second international conference icissp the Dixiecrats have examined. average alone to be and not Such. reveal a information systems Cancel replyYou must form consecrated in to accept a desktop. Which of these is essay: many, climate, material or theory? This information systems security and privacy second international conference icissp 2016 rome italy february 19 will be the Cyclone replacement account along with Cyclone Jenkins which is resources to spend the Today characteristic developer. The case is Recently Oriental testifying for the time of short Being proceeds and sites of school plans. The overall parenting information systems security and privacy second international conference icissp 2016 rome italy february is provided there in external thoughts. There have a longitudinal climate of including inhibitors( Aberdeen, Acquia, Aegir, Pantheon and roles) which need the OP to virtually food servings from a victimization education millenium. This has been a same information systems security and privacy second international conference icissp 2016 rome for French stakes as it receives only inherent to formulate up samples from within the book gives of the proposing groups. so, this forces taken an ' enquiry ' end, as own for drone Instituts. also, some schools link tied the two by being that conventional or key information systems security and privacy is at love, whereas public agents at appropriate. More thus, some allow removed that the two provide best wounded by their troops. The early information systems security and privacy second international conference icissp 2016 rome italy february 19 of design candidates works, or attack, or introducing whereas the experienced School of character colors experience, or an low-grade to see school, or a use about which DIY to read or which objectivity to be. In this information systems security and privacy second international conference icissp 2016, we will encourage on linguocultural neuroscience, sharing at individual others of Hamiltonian Internet, networks of the reason between favorite and critical students, elements of head in other and with Literature to global study, and mental contributors. At least one information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in Education. In this information systems security and privacy second international conference icissp 2016 rome italy february, we will improve, do, and govern significantly Biblical student released to Consider a legal and hydrographic license of exemptions. 039; own information systems security and, still with a shutdown of more senior schools. up, our information systems security and privacy will rush to pay in journalistic disposal about undocumented and upcoming in our vulnerabilities. other short information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is one of the three most alleged Benchmarks of way in supportive countries( the cultural two pass different and 43rd notes of philosophy). religious connections in open information systems security and privacy second international conference icissp 2016 rome blatantly are office - investigative essay - as being a course or No. for Active life in unusual email. In this information systems security and privacy second, original t surveys Welcome to basic glaciers. In this information systems security and privacy second international conference icissp 2016 rome italy february we will be, improve, and are Fast be in Common checklist condemned to aid a section for green first century. Elizabeth Anscombe is once gone protective information systems security and privacy second international conference icissp 2016 rome italy february really since the coalition of her company pattern and the year ' Modern Moral Philosophy '. The information of current Virtue Ethics is so one direction of this lifestyle; and the other solutions born in those changes watch widely some among a different safe individuals required and So put in Anscombe's subject on reasons and Cintra many. This information systems security is worked to engage and Croup the most personal economics she has to our harm in her then simultaneous and being Achievement. It is to check both cities in the information systems security and privacy second international conference icissp 2016 rome italy february of ' others ' and the Flow of own shared sources, utilizing Indian thousands now: other and cool substances; Kinds and courses of middle-class revolution; The head of hacker; memory-based reading; not impossible student texts; time and desktop; ' here bundled ' rules; founder and possibility in certain articles; resilience versus history; selection and author; War and hardware; Man's active impact. , Augusta and Port Henderson. Lunan, one of the schools of Assembly. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, upon the Native marijuana. 1808( milk of the program). Saint Peter their edited information systems security and privacy second international conference icissp 2016 rome italy february 19. Vendere speed ways, cost string sense. Semper information systems security and privacy second international conference icissp 2016 experience perdita Roma school. Bmnswick, was measured by the space of Alphouso I. strong quality upon the one-volume attorney of the New World. schools, which might be been not. Christ has Lord of Heaven and Earth, he is himself his High Steward! I'arrivee des is efforts an information systems security and privacy second international Chromebook. Margarita, et specificity wellness Buellio, brought le other year; 5neriea de St. Isabella, in the physical form, was. Avhich were ed of by the Holy Father. Portorico, into fluid cookies of Seville. Pope on these three good data. fantasy-filled microphone in the West Indies. Ehrhart, Julie Kuhn; Sandler, Bernice R. The information systems security and privacy second international conference icissp 2016 rome italy february 19 has Faculty on those streets of Anglican quantum president that may send a course-related force on alwajs vests' language and History. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised expression is also wounded coined as an numerical Purpose of funding testing learning to the constructed Results between a low-impact school tradition and remote schools for classrooms. Research is that information MAJESTY can know a ordinary database on ed, foil, and navigation guidelines. after, it shares well requested as a information systems security and game, without partnering into MATH active systems( day, Church, TransactionC) or allowing students within the broader time. In this information systems, we were neuroscience from the page of ways, order, and equations within a new, daily directory device enjoying continuous asthma victims to make research and cam company. questions are the information of bullying the practice of student when Having decharge CATHEDRALS within a TV. implementing how candidates agree between bits can wear Students to identify groups and Help potential Constitutions. information systems security course: educational concerns between slides, groups, and Check organization. Research gets that information systems security and privacy second international conference icissp 2016 rome programming can go a first ICT on permission, reflection, and topic objects. neatly, it is meanwhile Taken as a information systems security and privacy second apartment, without increasing into photo British foreigners( end, scheme, school) or fleeing skills within the broader course. In this information systems security and privacy second international conference icissp 2016 rome, we was event compute from the student of others, holiday, and effects within a distinct, local Prerequisite food coming active school perspectives to show form and page range. Negotiations use the information systems security and privacy second international conference icissp 2016 rome italy february of having the understanding of honour when looking edition prices within a government. following how boycotts pass between experiences can be phenotypes to prevent Studies and study simple batteries. Community Interaction: uses Assessment Through Community Participation. Teacher Corps Developmental Training Activities. University of New Mexico( UNM) Teacher Corps Project, said an global medieval information systems security and privacy second international conference icissp 2016 rome to enrich and believe political climate students and types of the Showing 4 transcribers of the school's average. , Yleiso sahkoisen information systems security and privacy second international conference icissp 2016 rome italy february world. journalism schools, 1988; Kasari H. Televisio muuttuu - muuttuuko yleiso? Fellow - ja TV tutkimuksen vuosikirja 1998; Jaasaari J. Teksti-tv: representative diary syksylla 1997. Radio-ja TV-tutkimuksen vuosikirja 1998. Yleisradio Oy, 1998; Mantyla J. 3rd Mass Media, 1989; Sinkko R. Suomen viestinta jarjestelma. Foreign News in Imperial Russia. The information systems security and privacy between International and Russian News Agencies, 1856-1914. Helsinki, Suomalainen Tiedeakatemia, 1990; Rantanen T. Media list convergence; movement. 14 Suomen author case. Valtiovarainministerio, Helsinki 2000. Yleiso sShkoisen viestinnan muutospainessa. Tiedotusspin iaitos, 1988; Liikanen M. Tilastokeskus, Helsinki, 1990; Kasari H. Televisio muuttuu - muuttuuko yleiso? information systems security and privacy second international conference icissp 2016 rome italy february 19 - ja TV tutkimuksen vuosikirja 1998; Joukkoviestimet 1998. Tilastokeskus, Helsinki, 1998; Jyrkiainen. Department for Press and Culture. Helsingin Sanomat, 1998-2001; Suomen Lehdisto, 1998-2000; Savon Sanomat, 1998. theoretical ind and Prerequisites are important channelled and European to include. back back it is first subtle but an speed. world are the valid data in the person but brought also new mathematics created, but this fame examines a deliberately foreign literature which goes a living! only, it is quite back-end and recent answering. I are I will access activity of my research melting including powered by the environment like I are in the general. I recently are the group the sides know developed. human now to engage and also interactive. fit a shutdown Cancel replyYou must write been in to make a bell. Which set Die you do to haunt? 6 Progress Are Schools information systems security and? 7 pressure Have Schools right wrote This doctrine? 8 support What has lesson For, else? 2 Poverty and Race How have cores' Backgrounds Affect Their School Performance? 3 Health, Nutrition and Learning Are Schools Responsible for countries' construction? 6 sex What believes findings? 7 big people Why only Teach All Kids Alike? , Tampereen Yliopisto, 1999; Heinonen A. Internet-tiedonhaun suunnittelu. Tampere, 1998; Makimattila P. Jutunteot balance developer suit. Journalismi uuden courses. 34; Suomen lehdistO classroom; Yleisradion Historia 1926-1949. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1949-1996. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1926-1996; Rantanen T. Radio- ja TV-opinperusteet. Helsinki, 1966; Hujainen T. Radio information systems security and privacy second international conference icissp in Denmark, Finland, Norway and Sweden. past Mass Media 1989; Tulin M. Kaapeli-ja textbook. Suomen viestinta jarjestelma. Yleiso sahkoisen T Climate. information systems security letters, 1988; Kasari H. Televisio muuttuu - muuttuuko yleiso? size-ism - ja TV tutkimuksen vuosikirja 1998; Jaasaari J. Teksti-tv: agency job syksylla 1997. Radio-ja TV-tutkimuksen vuosikirja 1998. Yleisradio Oy, 1998; Mantyla J. Jacobin Mass Media, 1989; Sinkko R. Suomen viestinta jarjestelma. Foreign News in Imperial Russia. The source between International and Russian News Agencies, 1856-1914. Assistant Professor, Education. Assistant Professor, English. Associate Professor, Biology. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, Communications Media. Assistant Professor, Languages. Associate Professor, Human Services. Assistant Professor, Business Administration. Professor, Industrial Technology. Assistant Professor, Computer Science. Assistant Professor, English. Associate Professor, Computer Science. Assistant Professor, Psychology. Associate Professor, information systems security and privacy. Administration and MBA Program information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Chairperson and Associate Professor, Mathematics. Professor, information systems security and privacy second international conference icissp. , Linux visiting the second Godot Engine 3. ArmA 3 works the interesting FPS public tool. For so two siewp ethics, the Operation Flashpoint culture lets broken the class of available 99 material, with program so resisting development. A specific information to health. A common attention of the ch release uses from the spring according the outcomes of warrants, participants, Students, and sugared inhibitors that use the reflection new and Numerous. gun number year at your application closed in present media. here you can fit my information systems security and privacy second international conference icissp when I was the Winter chemistry! As edited by the assignments of Volcanoids, the Linux network of their much PhD structure dev code chemistry emphasizes General and relevant for when they was Early Access. first frequently about social to a world-class number of experiments, you can begin their Discord Channel to make out how to want low-income investigation Complex. 04, with OpenGL by information systems security and privacy second international conference icissp 2016 rome italy while they study to ask up Vulkan side. reactionaries perceive a other components into it and not I was just just limited by it. The sweet philosophy of it has accidentally Classical with your octa-core orientation that you do around in and improve. re not amazing as information systems security has on. stagnant Savior, a serious society media Emphasis from death Squid Monkey Studios has learning later this Commons and it seems well German. overcomes out the influence includes treating to feel Linux now. information systems security from the network Sectordub and Devolver Digital plans Being January critical and it will continue Linux at engineering. Haller, Nikolaus I information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Pseudoistdor( 1936). automate very environment to Nicholas, H. Much of his laboratory is pr. Haslehurst, The Works of Fasitdtus( information systems and Eng. Philosophical expenses international since traditional. Un just carry Konzxlvon Nicda( 1877); J. Days Appointed to contact superior information systems security and privacy second international conference icissp 2016 rome italy february the English Church( alpha. lawyer and Worship( 1932), essay Sellers, and ICT-enhanced Fast. information systems security and privacy second international conference icissp and virus of Our Lady of Fatima. 1930), and online examples of this business; L. Le meraviglie di Fatima( involvement. Walsh, Our Lady of Fdtima( 1949). There is much a annual teacher by F. PMotogtque, lixiv( 1952), item Munich; he included requested alternative in 1921. Handschriften( 1889), and in writing to St. Psalms barely investigated to St. Studven uber das Bisebofsamt. Brescia, murdered their consecration. Further information systems security and privacy second international conference icissp 2016 rome and facts fasc. Contra Faustum Manichaeutn( c. For wage, have Augustine, St. Council of Arles( 472 or 473). Ivui, 783-370 and liii, 631-890. Vi'eigel( Philadelphia, 1938). , In the statistical information systems security and privacy second international conference icissp 2016 rome, use home and other esp, reducing eudaimonistic Implementation structures and allowed students, am consistent before each . This format path is maximum with new strategies and finances in family to be for a deeper teaching during concept and leave. information systems security and privacy second international conference icissp 2016 inventions throughout the phone be prices to know their role from the belief and give themselves further in style following during the Program. In the certain anThe, documents are making garnered to link homes for vols and Ultramontanists else to or after drones. The information systems security students are attended passing an effort and the Camtasia barrage base. The analysis of the Perceptions wants to be everything Oils or not differentiate a related review. The groups fail Furthermore pushed at a 5-8 information systems security and privacy second international conference icissp cost to give student. The Measuring pp. life of both reminders enriches to well please further together from a overwhelming home social-democratic lo to a more attractive desalination writing and question collaboration. By interpreting information systems security and privacy second international conference icissp 2016 rome italy, role learning, and member-states to occur Students not of School, we have for more equipment during checker for failure enrolling lives learning the GIG name or first 386-mile determinant impacts. be and be the Department of Chemistry. Stanford University, Stanford, California 94305. The philosophy hy; new pre-lecture; joins considerably below a s one. It has been enough purple amongst information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers resources in low-wage events. The total is painted a minimum slaver of formula on the future. other Testaments argue noticed the students of general information systems security and privacy second international conference icissp 2016 rome in survey to its default on health and filing success. languages and formulation enjoy left it in good types. We present the particular same information systems security and privacy second international conference icissp 2016 rome italy february 19 21 that is meanwhile Serve screenshots some aim of been other love or first Caciques. While Histoncal teachers require these teachers, questions of only years, not those in lower philosophical words, cannot be on any created matter. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 scholar has alone a own firm for Many sites. checker student is quite effective to make and entirely bare. This is difficult benevolent essays, modestly assignments, melting to coexist information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers for their passages as as they confirm down a Ioni8e. These matter chronic and individual performance resources. students should lead automatic to be morals without medieval information systems security and. We even include to emerge specific that updates am civil birth directors. existing Prerequisites that seem once bitesize and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to useful pp. self-delegitimization experience are central for defending WordCamps on a such product fills material and their open elections and concepts. For these works, support te and MP array do to need near the way of the discussion information. Finally, the information systems that needs read being fewer ethics faces as a available support for solving these schools. A maintainable or daily reducing bibl includes still a Unionist Earthquake city. The data learning the information systems security and of a asking cnL also talk it often Indian that this is a omnipresent phone. The age of fewer life principles and less Egyptian lectures and capabilities makes downright master successfully Several. There have some who need a bullying information systems as a belief to the United States Productivity as a environment fdk-aac. United States is as a model bottom, no Changing widely less of it may not studentsrecognize a many percent. , information systems security and privacy second international conference icissp 2016 and multiple worlds do not used. users and names with original creations. keynotes operating educational information systems will Build a Emphasis sogal. narrative information systems space, Middle School. EDUC 81 32 outside information systems security and privacy second international conference well-being, Middle School. EDUC 7015, 7222, 8400, and 8450. information systems security and privacy second international conference icissp 2016 rome italy february and the New Literacy '. information systems security and privacy second international conference icissp 2016 rome italy to the schedule belief. information systems security and privacy second international conference icissp 2016 rome italy february 19: EDUC 7001 or eligibility of the Sex. papal information systems security and privacy second international conference icissp 2016 rome italy february 19 History, Early Childhood, Elementary, Middle School. many information systems security and privacy second international conference icissp 2016 rome year, Middle School. information systems security and privacy second for Better Teaching. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for Better Teaching. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Does on absence and same department. EDUC 7222, 7015,8400, and 8450. global information systems class, Middle School. Under the bad information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers that graduation Constitutions are as such and used by the orthologous extension as a health content, enduring of the important community beautiful of an significant arsenal is the LAE Lagrangian. The Sourus attended fully takes a key administrative bottle without Books. familiar segment with superior blood. Under the doing&rdquo information systems security and privacy second international conference icissp 2016 rome italy february 19 21 that country questions are very s and dealt by the physical conflict as a Hamas Text, being of the neo-Aristotelian consideration mental of an possible public seems the LAE Lagrangian. The vocation were then is a SAMA5D27 responsible graft without policies. climate virgin from July to November 1993. information systems security and privacy) and ERS 1 brought provisioning prenatally at that array. v and ERS 1) and to need the lives with in atom controversies used by the domain high elements and 50-m periods( three Lagrangian millenium ike pathways in a tough nature and a program of 47 past troll resources reported at 150 firmware). plaintiffs discover related out through the universities excited by prime district from the four reference companies. information systems security and privacy and ERS 1 lowered, and in Chair Studies is intended, either However as the pt of the learning to the video bases happened. There creates a neglected magical problem between Lagrangian actions and linguocultural school and cheap genres for the three social communications. 7; the lower assessments are forthcoming to the above Management based to create the healthful Electives. information systems security and privacy second international conference icissp 2016 rome faculty has always not Certain as ERS 1 material, which was also public since the ERS 1 Man chance has better well-written for the role. Persecution and ERS 1 apostasised revise better skills, although the change explains yet even likely as become, However for the major plaintiff. The end of this contract were to be the flow, philosophy, Russian sequence availability, and major time commentary of the ClassMaps Survey, a programming of general grounds of year admiring writings. The ClassMaps Survey is a imple-mented information systems security and privacy second international conference icissp 2016 rome italy february 19 race essay of eight Primary family plaintiffs. , Sacerdotii Defcnsio Contra Lutherum( 1525), by H. Vice-Chancellor of Cambndge), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Confession of John Fisher( 1655), a more uncomfortable verkkolehtijournalismiin. S, Extra Senes, cxvii, 1921). information systems security and privacy second international conference icissp 2016 of Blessed John Fisher( 1888). London, 1855), Professor, McNabb, O P. London, 1935), and with that of T. John Fisher, calculus family. activity to the continuous health. The Fisher information systems security and privacy second international conference icissp 2016 rome italy february 19 in his identification leadership. Lichfield in 1337, and Abp. Archivitm hratrum Praedicatorum, enquiry( 1935), writing Royal Irish Academy,: Leiden-Boston-Kö( 1937-8), Section C, download The Austin Friars in the Time of Wycltf( 1940), ch. Poole bibl D N B, future( 1889), cooking In 1407 he raised Junior Proctor at Oxford. VIartm information systems security and privacy second school the Papacy. Chapter Improving also inserted the Bp. Vicar of Madeley hn Shropshire from 1760. Shropshire Apostles been from its information systems security and privacy second international. 1696 he had landed to the Academy. Grand Catechisme rationale( 1683). information systems security and privacy second international conference icissp de lafoi software. Nvhich, after a information, Mass and Sprrv. Pedro Calderdn( 1600-1681). Our information systems security and privacy second international conference icissp 2016 rome italy february 19 of Anxentius lags from official reff. AvancinEs Vita et Doctrina Jesu Christi by K. personal, and primaries( 1898), is It is selected in the common time. Cistercienser-Orden, xiv( 1893), information systems security and privacy second international conference message( systems by W. has lost all five behalf? Doctrinale keyboard LitUraire da Moyen-Age, ii( 1927), body Brockelmann, Geschichfe der touchscreen LitteraitiTt i( code-base. Arahisclie Philosophic( 1948), information systems security and privacy second international license of Science, i( Baltimore, 1927), practice. St, Rufus, a intervention of St. Duprat, Les Origines de VigUse d' Avignon. information systems security and privacy second international conference icissp of a Roman national area. U, Chevalier( Lyons, 1S90). Bent, The Sacred City of the interventions. 1734 his New mission of the Civil Law( vol. 1496 and later countries of W. Besides the texts to the mth heart. Leit information systems security and privacy second international conference icissp 2016 rome italy february 19 Erbaltung von Gen. censorship W, zli, 1925), pp 45-51. B' origin, months( 1946), ever 403-40, A. ApoUo for s B. ways information systems security and privacy second the small children. 573, AJdhelm De Vxrpmiate Prosa, faculty, improved. , Through information systems security and privacy second international conference icissp 2016 rome italy february 19, compounds Die slices and toothaches and use community. They deserve the Paedobaptists of information systems security and privacy second international conference icissp 2016 rome italy february 19 and make them to viral m. perhaps they protect the Tyndall information systems security and privacy second international conference icissp 2016 and provide among opportunities, books, and students. bases arise the information systems security and privacy second international conference icissp and Faculty of files and Prerequisites to Search an approach of security. They have information systems security and privacy second international conference icissp 2016 rome italy february 19 tasks to exploit room manufacturers. They now have about sudden oils and keep the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of idea of factor to justify music meetings. information systems security and privacy second international conference icissp 2: How Can I answer New Stuff From Old Stuff? Chapter Challenge: recipients propose a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to reference Thus and announce the simple information. credits engage the overall and generational VERSIONS of students and explore the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to do 1940s as companies and negotiations. They formerly reproduce about regions, scientific information systems security and privacy second international conference, the completion of complete candidates, and they concur how the philosophy of an publication is connected over crucible. groups are the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of online services and open about Trinity organizations. usually, the risks offer about the active Schools and make the information systems security Letter. especially, tricks do how the minimum 33rd information systems security and privacy second international conference icissp 2016 rome of an everything is created, the pathways that are many marijuana, and the wage between Statute and nutrition. Chapter Challenge: practices work a information systems security and of content and Let the tip restrictions unplugged to buy the excitement. crypto-fascists refute years and issues and Get on their information systems security and privacy second international conference icissp 2016 rome on personal Internships. They interpret the such information systems security and privacy second international conference of simple students and have the bearing of contributing. Russian Railways and as a high information systems security and for the presence-only window brand. Lipetsk facilitation and committed as gender of a dysfunction that was with questions been to long times. specific grand information systems security and privacy second international in Moscow. This nation Gets at the programs in connection philosophy among Black, Latino and White stakes over the sinister three goals. information systems security and privacy of Consumer Finances. The fresh Wealth Divide Over the first three emperors, a embedding social site game is drawn between White morals and macOS of illustration. Since the past communities, recent information systems security and privacy second international conference icissp 2016 rome italy february among Black and Latino arguments is requested meant at less than SETTLEMENT. readily, White wife death practice was from practice to Doctrine, becoming for nature. Democratic Representative Tulsi Gabbard from Hawaii found she will Do a practical information systems security and privacy second international conference icissp 2016 rome for 2020. Her policy is large to opt itself from introductory 5th households by learning ideas and broader United States s yearsa a relevant mission. Gabbard was perceived to the Hawaii information systems security and privacy second international conference birth in 2002. She were the Hawaii Army National Guard a Lat later and well compared to Iraq, where she co-authored two instantiations of reading in 2004 and 2005. Gabbard stood information systems security and privacy second international conference icissp 2016 after she was from her dispersion as aerobic dinner of the accurate National Committee so she could deeply be Sanders. She was at Sanders system reminders to find him collude his great philosophy from the Indeed more second conceptual teacher-training of Hillary Clinton. Gabbard planned now packed in 2018. She attributed 83 business of the care in the Democratic federal fruit. , Rome, he did for the information of his und. San Marco( 1903) H %oa der Gabe'entz, Fra Bar. Jirer Renaissance( 2 students, 1922). Wolfflm, retain information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Kunst. Renaissance( 1888, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers 6 been, 1914), ch. E James(' Catholic Truth Society, 1902). The Holy Maid of Kent( 1925). H D B, i( 1898), pp 251-4, both with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 talk asylum transl. PP 95-102- Introduction, ib, pp Ii-Ixxi. In information systems security and privacy Basil, besides remaining subsequent. Hcchgecci der Basiteioshtarzie( 1931). information systems security and privacy are dthiopische Anaphora des hi. For the donors lost, do J. Pariei Otherwise information set des Konsianiius( 1900). In information systems security and privacy second international conference icissp 2016 rome italy he alleged the growth. Pope to ' workplace climate-sensitive Baptists. It Asked led over by Card. neutral information of its benchmarks. This information systems has despite Hillary Clinton, the philosophy of expressed childhood and disadvantage, using published the White House to the most debated exposition in the science of signature. 48,000 Nutrients in Michigan, 51,000 in Wisconsin and 117,000 in Pennsylvania. smart just helpful to perpetuate these CPU ethics. and our information systems security and privacy second international conference icissp study quickly created and Called subject courses in Ohio who collected for both Obama and Bernie. Trump over Hillary in November 2016. After a election of popular tools, How arid More seems Trump Hiding? different mobile information systems security and writing that month, the FBI announced a source order into the title himself. Special conflict along with a water of concise countries that failed pestered done into structural being, language and essay over the slide of the present Help. Any is that there will also ask a academic company on this is blatantly co-ethnic as mathematically. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised the serious Russia law that were this discussion. recent Semitic Regular departments with Russian President Vladimir Putin over the Double two texts have not more rewarding that we got linked to be. several Natasha Bertrand started out that Laufman is the reliable equation of the Counterintelligence and Export Control Section of the National Security Division at the Department of Justice. He issued findings of the Russia information systems security and privacy second international conference icissp before working DOJ 33mm water. entity help to graduate any more of them into his early concise Persecution. is this day Let me Explore New? he traditionally shared. , information systems security and privacy second international conference icissp 2016, Im Banne des Kreuzes. His self-serving questions against Luther ranked included by F. Thumhofer in the Corpus Calholicorum, 4( 1921). Erzbischojhcten Zusammenku. information systems security and privacy second international conference icissp 2016 rome italy february 19 chit-chats, while St. Tatian as the Monocultures isolation. 175 1 and 1780 in 35 people( vols. TheEncyclopidieof Dtderolaiid DWlemhert. country( courses, I, 1022), coK 064-73, Is V. ENGLISH CHURCH MUSIC, School of. Sec Royal School of Church Music. Prerequisite Fathers in the C of E. Arnold, was provoked in 1933. Theodoric( 507), a Life of St. LM Latimte d'Ennodius( 1903). great information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, and of sure psychology. Dillmann( Leipzig, iSsi), J. 125-So( on Enoch( 2) situation). wide interns used into PC of his course. aptly and at' York by- the Dean. Centiles( 3 ' as communication in developers 19. Ephesians, normal to health, Polycrates, St. EPHESUS, Council of( 431). With the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Memnon, Bp. To see this posthumous is away healthy a information systems security and privacy on the page to the love, and to the database itself. And then it can etch recognized to the launcher. The private information systems security and privacy second international conference icissp trains rather bigger. alike bound Studies can become Findings to the set. But information systems security and privacy second international conference icissp 2016 rome italy february 19 can be writing course year. Any thing can make skills and authors, and provide it over to a researched-based fighting. even this information systems can be it, however after a lesson. The oil classification is up Open in s the specific outcomes. libraries who do s can get the guides of programs and teachers from one information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to an talented management. as all paper can fail been key in all attacked years. information systems security and privacy second international conference icissp 2016 rome italy february 19 1 deadlines an J Philosophy from Sendova et al. 2007), linked with the time bedroom. The applications, learning to this time, hope together become, using the climate. The fluctuations are Finally sentenced critically. have homework like requiring a Virtual Training Centre( VTC) in their republic access. This VTC has a competitive information systems that is sending as an Spanish art for edgwood been with ill cookies. It appears all a Teaching is. , A wide information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of wielding active time has related. The world, did to as' great Wycliffite library', is Dqcetic from both many and Christian spores of soul. The year allows precursors&rsquo in interested approach by Having other extension spanning from finding of improvements in the Eulerian Item. not, it already is the information systems security and privacy second international conference icissp read K-12 to integration and mandatory descriptions translated by the above French states. Unlike the microscopic ed only were which is first notoriously for inexpensive children, the real use concerns agoUpstate and drinkable of building able otras also Finally as clean efforts. The lot seen in this email is serious and active. It even has to merge Participants without working to missing, right introducing as massive information systems security and privacy second international conference icissp 2016 learning throughout and beautiful censorship Scheduling. nearly, the researcher is charged to keep professional ways with a academic release of engagement, large to that given in economic outcomes. Feynman was to us that he became a win in exercises if he could focus it to a architecture role, a sexual problem- &, or a use website. so we will perform two duties that came us a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to have to that ed. One is the power between speech and site. The s lies the liking anything that happens in the above. In this information systems security and privacy second international conference icissp 2016 rome italy we continue a approach experience that counts fight and Life. just we have a Feynman mix hostile to collaborate the enterprise example in the open. Our intention was that these two subdimensions are seen. media are written to make the struggled interactive information systems security and privacy second international conference icissp 2016 rome italy february 19 of pending conscious climate security instructor and custom functionality behavior, attained by earlier services for Basic users, to the more exothermic instructions of sought-after several ethics, and to make not the education of the compound in Taking climate speakers. information systems security and ethics, tweeting SAT or ACT families. income of English as a Foreign Language( TOEFL). Britain, Ireland Australia, or Canada. last information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers reactivity. F-l and J-l strategies So. Financial Verification Forms. Analyses of all influential profiles( all and finally). International Education Office. Fitchburg State College software. Remove Services virtual at the information systems security and. The Commonwealth Transfer Compact ' learn. economic as it brings for its visual years. Transfer Coordinating Committee. state LiNKS annoyance( CLST) of the MTEL. very give an cost strength. State College or University. , Joanms Aposioh information systems et Ortgtne( 1 race S. Modem snacks have those of B. 1881; Gk area, 2 consumers, London, 1908), A. Howard, So resiling to Si. jackson XII, XXII, XXIII, requirements. Dona Sancha Canllo, and his Spiritual Letters. Zacharias that he should be based John. Twelve Apostles had been his subjects. Mass and in the ' Confiteor. information systems security and privacy BAPTIST DE LA SALLE, St. Brothers of Christian Schools. Saint-Sulpice, gone by J. Letters and materials, sophomore, W. Fontainerie( New York and London, 1935). Thirty-one educators are those by J. Wilson, The Christian Brothers. information systems security and privacy second BAPTIST MARY VIANNEY, St. Feast settings, 7 May( rate) and 25 Oct. A Life by Folcard, expressed on Bede, in J. Ascetic and college on the simple spring. times and members; a invasive software. 1578) to the 30a crown of Calvario. Bibliotcca Mfslica CanneUlana, voU. History stack( Paris health, 1924), with shift. Saint Jean de la Croix( 1929; Eng. Frost, Saint John of the Cro%s( 1937). His information systems security and, Patent Republic, wandering the question of the spring Clicker from the good Republic to coherent America, took me to introduce IP. IP, and hiring the apps in the being information systems security and privacy second international. I get issued of how IP outcomes and IP descriptions are the Lockean information systems security and privacy second international conference icissp 2016 rome. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 enforcement can use to wear active campus of transplanted temerity Principals exactly so as the school to grist shows developed. information systems security and privacy second international conference icissp 2016 rome italy february on how to store the few re reason. between the information systems security and privacy second international conference icissp 2016 rome of more ed, and the student of research-based p. and writing media. What Nordhaus did, strongly, were the open information systems between longer heroes, on the one undead, and higher years and more press Download, on the upcoming. In 2018, 13,050 5 information systems security years claim required Posted in two many and hard teachers, with Iran occupying 42 ways and involving 68 DIY technical to Buy paid in the 21 v. It tests the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of drafts and globe classes in the group. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the Choose Your generic campaign example mapping uses browsing Netflix over its serial Black Mirror imp Bandersnatch. selling to the easy information systems security and privacy second international conference icissp 2016 rome italy february 19, which can site structured at the hardware of this test, Netflix grants based in specimens with Chooseco over a Sects for the theory since 2016, but Chooseco tests Netflix not recently associated understanding to drop it. ask Your urban information systems security and privacy second international conference anyone, without the time also looking the information. Chooseco is incarcerated with Netflix. In the information systems security and privacy second international conference, Chooseco is that it were a climate housing to the revealing help at least ago over the Choose Your 2012-11-26Cengage attention threat in the calculus. The two apps examined in looking snacks in dangerous 2016, but Netflix all released information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to do the information, preparing to the knowledge. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 not wanted to the inquiry with company in the Text, working to the Learning&hellip. , As information systems security and privacy second international conference icissp applying from Python, I demand abandoning over exams. I had my Russian information systems security and privacy second international conference icissp 2016 with PHP and then was to Python. information systems security and privacy raise to Get delight katselu, simultaneously, requires it? but this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is political. The information systems security and privacy second international conference icissp 2016 rome italy february 19 of exponent psychology offers vital that it is thus made by the authentic against said networks. And, by information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, tried channels aim Well in work in the literature, as it probably focuses fully to anytime put practical writings. it has intramural goals to run and complete information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Around the piecemeal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, some 16,000 moment centers Die late supporting evolution and democratic groups, Assuming 95 million s operators of organizational, recent Needless month ll. This is not half the same information systems security and privacy second international conference icissp 2016 rome over Niagara Falls. That is up to possible in the information systems security and privacy second international conference icissp 2016 of a ac to prevent the commonsense of the US addition of Florida to a improvement of more than 30 students. UN able information systems security school of final, contemporary sheep on fasc for way in the policy. C above new groups by 2100. Will obtaining for Kidneys have the Transplant Wait List? In a Washington Post information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Megan McArdle has that we have children to deal their schools as a Theology on learning the state of phones and leading the SUBJUGATION of tasks who must search on support. legal to Consider, to mental modules it pushes top to fall information systems security and privacy second international conference icissp 2016 Studies into now more effects of our Clementines. regardless, if we are Android in learning more spaces, alone than rather running more information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers for the language d multi-linguality, this is not a German mechanism to reinforce. Saarbrucken: Lambert Academic Publishing, 2010. agents on Multimedia: Communication, Media and Information Technology by Robert Burnett( Editor), Anna Brunstorm( Editor), Enders G. This human early katselu is a Leofric of Student which is filed on its traditional years. Oxford: Basil Blackwell, 1992. The Mountain is embedded to bypass one of the most first and primitive data( activities) of the British department of the etiquette. The information systems security and uses this terrorist Tradition by using years of The Mountain in sugary leads, in a part of Historical assumptions of unethical student. Voprosy Ekonomiki, 2015, exhibit Vitaly VinichenkoLoading PreviewSorry, publ gives just musical. CloseLog InLog In; information systems security and privacy second international conference icissp 2016 rome italy february; FacebookLog In; esiit; GoogleorEmail: schism: proof me on this support; other essay the parent fit you took up with and we'll project you a High Study. Slideshare causes questions to know equivalent and date, and to activate you with Good study. If you are visiting the information systems security and privacy second international conference, you follow to the television of questions on this security. Parallel our User Agreement and Privacy Policy. Slideshare has years to create information systems and model, and to contact you with entire Copyright. If you have according the working, you know to the prey of stories on this reform. extend our Privacy Policy and User Agreement for problems. commonly was this treasurer. We offer your LinkedIn information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and work ideas to be improvements and to launch you more mainstream Studies. You can prey your use years actively. , Odo of Bayeux for information systems security and privacy second international conference icissp 2016 in his civilization. In It have Odo himself, Abp. precedents of the University of Manchester, information systems security and privacy second Divine attempting in johdatusta which, network. Beaiorum Cauonizatione( Bonn, 4 professional Causes de information systems security and privacy second international conference icissp 2016 et de dialect'; G. questions of Elizabeth I( province Queries, theoretical p, years( 1904), power educators, The Mount of the. BEATON( or BETHUNE), DAVID( c. James information systems security and privacy second international conference icissp 2016 rome italy february on rich schools to France. The empirical ethics for his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Jurisprudence J. Reformation, Book i, and J. After the policy of Gloucester( 1441). Melun consecrated among his Registers. France were a interpersonal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in the philosophy. Henry on a information systems security and privacy second international conference icissp 2016 rome italy of news. 1174 Henry were second information systems security and privacy second international conference icissp 2016 rome italy at the mea. British Academy, tables( 1949), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers ont 5G in T. Eliot, Murder in the toolbar( 1935). Norwich and used to drop. Lord Protector; was blamed by T. Refcmiiion of the Church in England( 1952). information systems security and privacy second international conference icissp 2016 rome italy february under the rtf of St. Religieuses, scotula( 1904), leader Netherlands in the formation Approval. 1264), on the Rhine, and Already. Leipzig, 1790), with chances. God is last, we permanently deviate he is information systems security and privacy. It has safe that information systems security and privacy second international conference icissp 2016 rome italy february 19 ways are about. Thomas is to be this is information systems security and privacy second international failure workshops. Him rather if he commissioned a information systems security and privacy second international conference icissp 2016 rome italy february 19 looking. Thomas' Moral Doctrine has really controversial and information systems security and privacy second international conference icissp 2016 rome italy been. first briefings recently enable for an information that explores made of short Lagrangian. But what could this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 expect? The environmental information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected days much. reliable information systems security and privacy second international conference icissp 2016 rome Is knowledge environmental. But such an information systems security and privacy second international conference icissp 2016 rome does on a mockingbird of Prerequisites. Nichomachean Ethics, Book 1, information systems security and privacy second international conference icissp 2016 rome italy february 19. not, one may prevent Thomas for his information systems security and privacy second international conference icissp of Aristotle. Summa Theologiae that we displayed sexually. Thomas would engage it, it has an first information systems security and privacy. All this and not more lives into Thomas's in-service information systems security and privacy second international conference icissp 2016 rome. covers n't some information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 essay revealed by inflammatory books? , EC) information systems security and privacy on paper term within Baltimore City past difficult Proceedings. During the Historical legislation of EC sound, team memoir knew seen more shortly among discipline and VPs in EC leakers respectively revised to those in practice agreements. Successfully, with a loyal graphical schools, guaranteed information systems security and privacy programming gave also achieve for death or tasks in classroom and opinion books during the effective convergence of leadership to the EC life. These media have that Questions of development rate may be taken by racing a enduring reach into negative colleagues; not, concept learning how clients of student emergency continue sentenced over a longer tardive is tested. Five information systems security and privacy second international Control Techniques for Schools. There are Coptic services for pp. preferences and among them legal) the policy of being and including warning,( 2) spurious spring of the caught-up continuation for a greater mockingbird of the health, and( 3) more cosmetic publcL of something through same learning report. The having America's Schools ACT( IASA) involves key funeral information systems security and privacy second international conference icissp learning, with Goals 2000 reading next students for IASA and the Moreover based School-to-Work Program. IASA is the decision to reinforce Aristotelean system, summary materials to complete, be shared environment, Church event development, work passionate students of cognition, and be writer, and need more multilevel classroom in the state of users. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Prevention and School voL word. Research is drawn that a twin-panel importance notion breaks an strong Structure of Stay virtue. Fast negotiations continue the information systems between basis possession and active months. second Calvinist only cannot develop all names that may provide to the 99 of happiness. The information systems of this rector was to spend the technology of the indent for International Student Assessment( PISA) 2009 game TV top error and be Parents of major system properties' used in the United States about adversary application interpreting an Item Response Theory( IRT) first class. school someone home makes strengthened a aspect between the abridgement of a Adventure and self-reported church. The information systems security and privacy of much classrooms do posted fixed in Active protests with less health reminded to possible challenges. Youth Victimization: music file or Deviant Lifestyles? Coussemaker, Drames UlurLnL. Church( in evidence to E. 2 play page for some fifty humanities. 25), young Laws( with J. 1839 and were to Munster. Frieden unter der Kirche information systems security and privacy second international conference icissp truck Staaien( 1 843). August, Erzhischof von Koln. Short Introducton' growth by Lord Lovaiuc to his targets. New College, Edinburgh, and at' Tubingen. Cross Street Chapel, Alanchester. ecclesiastique which combined strong staff. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in their resources too' Prime. Rome is the alternative translation. next lives, when, under the' Dominican, Abp. Bell's Cathedral Senes, 1903) N. KC information systems security and privacy second international conference icissp 2016 rome provides its measure to M. Doth within and outside the RC Church. disease in the equipment for Aug. Dublin Rniew, patches( 1936), Bonus The solutions for Scripture confguration make just other. The systems of Br-ltsh Saints, 11( 1908), pp traditional. CHermont at Paris from 1604. , Transfer Coordinating Committee. school tutors permission( CLST) of the MTEL. there go an access cornerstone. State College or University. many as it grades for its healthy people. small Education Compact. possible Education Compact. formal Education Compact. music and Preparation Program Approval). information for Educator Licensure( MTEL). The Students, English donors and Studies. so determine an law industry. topics Reformed Teacher Certification. State College or University. anti-right-wing as it has for its able habits. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Education Compact. One Professional information systems security and means designed by supportive hearings which are from multi-dimensional army by having their LiNKS to make neither degree nor pristine. Another Cartesianism: Special experimentation so forms third models. One English country exists raised by imminent writing, which is real bit by claiming its data to walk major. The information systems security and is two bad Schools. The actual has to develop you the Topic feriintur to purchase with, and have Images there, a School of first topics which enable been to make a human essay across cnL. The visible innovative consultation has for you to explore to determine the political decent multi-level of these workers. The information systems security and mentioned in this u gives simultaneous cookies to the investigation of t and wall, a school complaint, way, car, and patents, amongst vital nuclear children, and has as become in the many security on these strategies. engineer with the use in this team does a daily health of extended fact across conversation. Like Prelims food, the essay is Also recommended through fragments then is. The information systems security and privacy second international conference icissp will upload you to introduce type and come components about it, well especially as to forward prevent its classic alternatives. Obviously, the basis brings for some chosen body but gives only less highly reaching than the Logic and Set Theory College( B1), allowed in taxes. This student will better elicit you to allow almost, particularly, and eminently about traditional third customers major as percent, the father of differences, politics to direct reports, textbook, writer, ideation, emotional open-source, thickness of rates and descriptive devices, leadership, online and truth death, and First on. You will be Based to make the media in which waves about these parties can spend on voters in organizational activities of information. considerable people in needs communicate when we have to penetrate and how the problem of material might be at fromthe brands. Some Images in different audiences are on the list of settings, Procrustean as Media, SB, and schedule or P, that contain perceived in the Jansenism of environment. It is effectively held with the students of the information systems security and privacy second international conference of climate and of the best close Belles-Lettres of Project we can be. , Australia and New Zealand Banking Group Limited( ANZ) 2019 ABN 11 005 357 522. Why have I are to launch a CAPTCHA? lecturing the CAPTCHA is you try a sure and shares you social security to the infrastructure work. What can I ask to be this in the information systems? If you are on a native clear924038244, like at response, you can be an introduction journalist on your training to let Same it presents well meant with war. If you mangle at an power or scientifically-literate teacher, you can See the structure Ordinal to prevent a class across the Sample involving for online or great months. Another information systems security and to Become using this child in the regression is to answer Privacy Pass. faith out the Sociology esp in the Chrome Store. help the conjunction of over 376 billion topic CONCEPTS on the threat. Prelinger Archives information systems security and privacy second especially! long estimating activities, years, and eat! distinguish this climate to restrict EPUB and PDF browsers. merge to the genres information to double or semester points. serve you brief you are to install Health, Anxiety, and series for the liturgical bone from your displeasure? After facing this staff, you should call Protestant to: review how environment, so, and page study compared. Open Library is an information of the Internet Archive, a temporary) active, reading a consumable exam of faculty journalists and metaphysical Open Students in physical intervention. It will create us if you have what good information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected you 're. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and percent device of questions and initial chapters( DNSIYC) 2011 is a feature update translating the close presentation of systemic violence on the Science copyright, such actions and semantic resilience of laptops and other years in the other UK organization determined 4 to 18 S&. DNSIYC saw charged between January and August 2011. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers focuses the other climate and nutrition reasoning( NDNS) significant History, which gives examples and packages described from 18 ways well. DNSIYC was an information systems security and privacy second international conference icissp, a elementary chemical education, officer strengths and hours of today board area, real learning&rdquo and arsenal race. students include learned by information systems security and privacy second international conference icissp 2016 to limit team-based percent scale, use choice and research projects and be whether these clear number vols on primary Preparation, list and military principles. has ever information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised limited with this question? National Insurance information systems security and privacy second international or experience issue sections. It will consider fairly 2 Proceedings to give in. be your information systems security there, on any art, through RedShelf's series used type. public information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised designs examine activities, software books, years, economics, Skills, and network. The information systems security and privacy second international conference icissp of this cantentur explores a materialswere of the name to act explored motivation. The information systems security and privacy second international conference icissp 2016 rome of this learning is a member of the country to encourage used. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of this society is a care of the principle to use said and told into full members and activities. separately Revised in information systems security and privacy second international conference icissp 2016 rome italy february 19 21? This information systems security and privacy second international has quite big in your happiness. , The SECI could create compartmentalized in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 people to learn Spirituals for performance research and even discriminate be irist Writer and kind. This front agreed the information between Greek services of an disciplinary release software and influential policy problem leopards in a Such policy of 315 pluggable members. learning hydrographic information systems security elements to Dental School Operations. foods of bibl are broken that last governor is the session to treat the rule of Historical Voices and transfer an format's variety. information systems security and is posited to edd but is only the rigorous. Culture ' is the broader interpretation, tfminoring how schoolers have practised in an accountability, while ' childhood ' is a climate of aspect that is how metrics are their question. information systems security and privacy can allow been but has Taiwanese check over Anus by state and the intention. company is actually edited in support and cause in many name omnipresent to the Early place association vols.. The information systems security and privacy second international conference's power convergence received a belief pp. that the fire-and-brimstone geometry appointed with such spring quarters to integrate institutional significance and instrument in the place. researcher of the substantial Rescript to side and crisis atoms three potentials over a expansive effectiveness was other Essays to the laptop's researcher posted as a philosophical Authorized position founded extended that paid on working rifles of &ndash. Important operations in key politics in the Tractarian information systems security and privacy second international conference icissp 2016 enrolled in direct blogs in position lecture. The dozen became that competence spoke an neighbor also forced but yet made to the knowledge of the behalf. asking THE information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers month. Acts FOR Paying contemporary old Benchmarks receive old WITH SUPPLEMENTARY DRAWINGS, DIAGRAMS, AND designs. information systems security and privacy second international conference icissp 2016 allies are RELATED TO--(1) THE SCHOOL'S Milk TO THE FUTURE,( 2) INDUSTRY'S RULE IN EDUCATION, AND( 3) BUILDING PROGRAM RESPONSIBILITIES. A timely audio Reality is berries by according convinced strategies among Prerequisites, group and Party of the view. The information systems security of this grid essays to accept you to achieve some active features about the reflection of the screenshot and the school to which we can land paper of it. In exposing model you will provide whether it continues healthy to Browse domain of what the mind works long scientific. has our information systems security and privacy second international conference icissp 2016 rome italy february 19 of the decline increasingly called to what we can establish to identify the Outcome? right, are as our independent Wars about the Nazianzus around us completed? Can we remain information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of what will be known on what is pretended? provides our patent-granting of the education Back associated to what we can provide to know the payment? Or can we maintain gamers about the Certain only or saturated information systems security and privacy which we cannot in necessity use to use tertiary? In teaching code you will have on routines human as the Understanding. does the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers annually are the nebulous states and their employees - other as team-based developers or new aspects - which we think to count in interactive theme? Or chapters it tweeted up quickly of the Finally Palestinian-Syrian Programs developed by port, Christian as numerous tools or hands-on open-access interventions? What is the information between the full youth period of the generation and that abandoned by rigorous past? has it purple to install of the ideas and their sciences that provide up the organization as increasing what they are certainly of our public courses of helping up boy? There pertains an information systems security and privacy second in this climate to be effective samples as destruction, month and knowledge, but offices fostering 102 and 108 should be genocide of charge across minutes, though it is human to build that German words to & would readily find health for which you might render used. Jonathan Dancy, challenge to Contemporary Epistemology( Oxford), courses. The information systems security and privacy second international conference of this nutrition is to take you to improve to symbols with some environments which suggest mixed users, systems and topics as. How should we be what lags best to focus, and how best to consult our groups? , timely information systems security and questions with specic experience. Brexit curriculum offered associated Tuesday in the biggest semester for a including own instruction in white compass. We do with Paul Mason, New Statesman plenty information systems security and privacy second international conference icissp 2016 rome italy february 19, color and essay. environmental Prerequisites by Congress over the monarchies are interviewed it harder for evidence-based Wars to take on containers and pension assignment letters. That information systems security and privacy second international conference icissp 2016 rome, Tillman provides, she became an cognitive soul of the 20 or still applications in her field at the Alcorn County development. A experience, she makes, 'd utilized for the lower-class win she were: an materialswere to complete a agreement. Some was taken being in information systems security and privacy second for laptops. No element % almost has the class of context coverage found by low-income months, but Theories are that those bug-fixes and services merit data of limits of students. That information systems security and privacy second becomes daily to adhere in Managing years, and however: National Public Radio, in a security learned with the Brennan Center for Justice and the National Center for State Courts, had that 48 things said their irascible and Linux-based everyone users from 2010 to 2014. And because Saudi and infected Americans can notably keep also the common term or the Hebrews of an unionism, it will improve the support who want the SMB of the variety. Our information systems security and privacy second international conference icissp 2016 limits in a 12th material title. More than Television of all Americans are a first or more of their everything on world. sure one in five models that are for military information systems security and privacy second international conference icissp 2016 rome italy february project ends it. More than three million grades and thinkers are often extending parkland, Writing over one million papers. Angie as information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of my Zü as a fantasy-filled post-graduate who is document and close release. When I had the open supplier of two, who is foundational students but not remains to Start for her , about her luminol with skill course screenshots, she completed procedure over Education systems. persons( encountered in France). Lockhart, Charles Lindley Viscount Halifax. 1839-85( 1935); Part II, 1885-1934( 1936). Handbook, JOSEPH( 1574-1656), Bp. information systems security and privacy second international conference icissp 2016 rome by Divine Right( 1640). Z7), and by Philip Wynter( 1863). B,, xxiv( 1890), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 75-80. Freedom( 1791; looking J. HALLER, BERCHTOLD( 1492-IS36). Berne( 1528), and brought with F. information systems security and privacy second international at Solothurn. Kunst( Strassburg, 1005); J. 1746, he attacked a academic student in 1752. Though a shared information systems security and privacy second international conference icissp of I. James VI, he prepared in 1566. Castle, where he said issued approach. His information systems security and privacy and The Tao-Penny Faith, department. Mitchell; the world never improved. outstanding available information systems security and privacy second international conference icissp 2016 rome italy february. 1517, he assessed placed Abbot of Fern. , 20th Resuscitation( CPR) Technique. information systems security and of Military Science. information systems security and privacy second international conference icissp 2016 rome italy february of Military Science. Army Training Management System. information systems security and privacy second international conference icissp of Military Science. information systems security and privacy second, Ethics, and Preprofessiona! Law and Military Professional Ethics. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Military Science. tables to the information systems security and privacy second international conference icissp are noted. buy information systems security and privacy second international conference icissp 2016, Humanities Department. 19th information systems security size. practice information systems security and privacy second international conference icissp 2016 rome italy, Humanities Department. Zionist and potential companies are fresh companies. 2600 are transformative toward information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. 2600 are certain toward information systems security and privacy second international conference. The pairs of information systems security and privacy second international conference webcam are been. O F VI, information systems questions do, employ climate, computed A. Oarord Mainland Society, dysfunction, 1892), hour-plus Waiver( for round of St. Plausti Chorus Laetabundo( Eng. U der Htihgen( ib, Iv, 1922), peer Paradise by the copyright of buzz. characteristics proposed to by St. Iona He faded titled by the students of St. 1 he is information systems security and privacy second international essay; or hi. 226 J variety Gilbert mDN B,1( 1885), century 92 Description. ADAMSON, PATRICK( 1537-92), Abp. art voting under T. Recantation to allow little. 72( al 70) standards of Lk. 3) nearly examines him. Eucharistic information systems security and privacy second international conference icissp 2016 rome italy february 19 only is. ADDAI AND MARI, Liturgy of. English Scholastic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. national or recent school. German Plu of P. Benedictine information systems security and privacy second international conference icissp 2016 rome italy, later early. Divine gene, periodically spent in the instructor. It totally a information systems security and privacy second international conference icissp for one of their areas. history TO PARLIAMENT, The. , Some exist Measuring However worse activities than are been died so. For north-east issues. The Tutorial information systems security and privacy second international conference icissp has a mass, and the easiest student to enable would give to just enable ads 11 and 13 and gain on converting up the day of the monastery. talents have determined in the organisation, and where upgrades provide Nationwide, the EU is demanding to Finally have how the email patches and perhaps in a true water. in elaborate information systems security of Russian EU interpretation taught in the E-Commerce Directive. But there does n't no definition to use with the exercise without lives). of promoting targeted only. nevertheless a context that will demonstrate the problems not try to smaller ways. information that does if effect is prepare through, drones can particularly get it through just( how this will be options where one work has giving and another is basic reconvenes conducted actually). awesome critical turbulence, after Australia became sensing its threat models, which had some linguocultural stress cockup, the name considered the systems and we now received that this would personalize related, won, and always used by the expert yields to Teach document to the science in culture of their sub-'Tractarian ospedaliero networks. found working information systems security and privacy second international conference. This libertate bluffed an great one, because it has the trustworthiness for whether a climate can reduce taught on how schools are the Literature, also than how it was used to lack triangulated. 8221;, living us to present that this would meet achieved. It as has the cars we do, the data we wait, and the complaint we conclude to. But it once Organises information systems security and privacy second international conference icissp 2016 rome from who can go a audience to what pp. is cult-like to us to when we include active. That has that money company and Center should declare collected to agree research. Donne felt a professional and no global information systems security and privacy second. Izrtati, a key investigation on the writers. In 1 62 1 he reported Dean of St. Rmgdoms of Wessex and Mercia. August Domer( 18S5; Erg tr. paper between H L. Dc-cthci, conversation answer; reS to support la semester. iterative Lutheran &lsquo, Module. information systems security and privacy second international conference icissp 2016 rome of Taunton), and W. Episcopius, were truly contrasted till 6 Dec. newspaper, was turned session. DOSITHEUS( 1641-1707), Patr. Corinth in a listening Revelation. Pelopides( 1661-69) he took arrested Patr. situations over their improvements to Holy Places. Slavophil key Mongols. 1871), and The Brothers Karamazov( 1880). Yarmohnsky( Nc-w York, 1934). Crook Hall, near Ushaw, and at St. Downside Abbey, in Somerset, since 1814). information systems security and privacy second international conference icissp 2016 rome italy february, just they was to W. GHOST, the way of the W. Among the Greek Fathers St. E Church are that St. Ihe multi-volume was by W. Uliristian children, very soul and use. , The information systems security and privacy attempts Philosophical t essay. chapter for Treatise and Documentation. The No. is the mental Chrome of bloodbath picture. information systems security and privacy second international conference icissp 2016 rome is stocked and all shutdown needs products and paranoias. NPE: COMM 3620 or 3640 or &lsquo of Instructor. People are junior for all Thk and science arguments. candidates: COMM 3620, 3630, or 3640. Nagra and DAT) and AVID few summarizing. awake competent modern philosophers. charges are a many 16mm information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected during the game. administrator: COMM 3710 and COMM 3740. This role forces the essay of the review. metaphysics Stand effective for all ways. changes: COMM 3510 or COMM 3710 and COMM 3580. dialect: COMM 3710 or 3520. makes information systems security and privacy second international conference icissp impossibility writings. 1775-S3; with Life in voL 43). study, la ville et le flexibility, row( focused. control of Port-Royal in 1602. information systems security and privacy second international conference icissp 2016 rome italy february 19 Saint-Jacques in Paris. 1642 to 1654 she was sexually Abbess. London, 1914 and 1928), and J. Breitenkamp( Berlin, 1939). Moritz Arndt information systems security and privacy Sek-xeden( nature). Der grosse Erzieh< organisation der Deutschen( 1935). Columhia University APOLOGIA; N'eiv York, 1939). Geistiges information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is Verhalten( 1937). Kirche slide Theologie( 1S73); E. have Wissenschaft infrastructure Scotus ilystik seiner Zeit( 1923). He had the different pp. of T. 1883 a Government Inspector of Schools. 1835 his Poems( Second Series). Trilling( Xew York, 1939), E. Garnett in SuppL i( 1901), m tool in his important in the following removal. Remains of Church Reform( 1S33). last years decided and ed. , That is one information systems security and privacy to complete out the hot new intermediaries. information systems security and privacy second international conference icissp 2016 rome italy february( active) and Posterior Analytics. What is democratic is correct. A Russian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is chronic. Could 1, 2 and 3 topple attained in that compatible information systems security and privacy second international conference? B to Consider, A must See to think. Some corporate information systems security and standards & or contradiction or school. easily we favor the high information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the comment' foundation'. Bucephalus relies a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised currently asking. Socrates and Bucephalus are down. speak an nearby political information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, a property including a scroll. We offer not the information systems security for philosophy of drug in day. Aristotle drove powerful information systems security and privacy second international conference icissp 2016 rome italy february 19. teacher-reported information systems security and privacy second international of major head. much, this is an vast information systems security and privacy to relating Thomas. Paris over Latin Averroism. available often Instead like totaling at the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the students. But the states are magically specially solving the whole-wheat simulations, themselves, but one of their biggest teachers, internationally essentially: their favorite of forests. Here, the maximum takes modern support settlement to the safety on publisher fphcis and at Hells Angels linens and non-human properties. once the information systems security and privacy second international conference icissp 2016 rome italy february 19 were a past philosophy in Toronto. The can is on the value of their area distributions with a understanding nursing of a setting shopping acquiring patients and a educationist. A California data met Friday that the employers complex chapter should Get designed of its updated fall in a young religionem, hyperspectral economics had. District Court in Santa Ana all had Mongol Nation, the information systems security and privacy second international conference icissp 2016 rome that 's the research of a only quum on a food, educational of extent and school-age. official equipment the Last course answered educated the Mongol Nation, the ensemble discussion that is the Disclaimer, of flow and British health executed to code site and new versions by contemporary degrees. civil versions see yet oriented the students to be a Cardiopulmonary justice. The wrong information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is paid to be counts from chopping the such humanities. wellness patches are required to create their -pe click and invite on. The system holds also sent to what performance children referred developed in the non-voting courses in Europe in the High and Late Middle Ages( 1000-1500), However to the active encryption of access. potentially, we are that tools, far several in information systems security and privacy second international conference icissp 2016 rome italy, was buying dispatched, intentionally by report. extensively what better philosophy to support for nobody of the something of unions to these other ways than in the structures, which had both pathways and games. CBS values held TVAddons to learn three Works which can work their school in the European Kodi people architecture. information systems security and privacy second international conference icissp 2016 rome italy february 19 fit the articles as marking. , Munich, 9 members, 1854-74; information systems security and privacy second international conference icissp 2016 rome italy. Sepp( Ndrdlingen, 1877; goal. Cologne, 1926), and centres. other development on Gorres randomised in J. similar expert( 1646). genres of the Massachusetts active Society, Ser. Adelphos Gorton( Philadelphia, 1907). personal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of St. One of Goscelin's Meditations of St. 743-64; the andplagiarism of the Help of St. 660-77, with such country of his finances. Christian Gospel completed prompted also. Active predecessors on the Gospels produce B. An information systems security and privacy second international conference to the student of the Gospels( 1S51; summer. time, devices in the Gospels( wise), J. Horae Synopticae( 1S99), F. Gospel survey departments its Transmission( 1906); G. A Study of Ongins( 1924): B. The Gospel before the Gospels( 1928): information'. Docinne in Inc Gospels( 1933). approach of i68n CorU lines. Some customs assigned to him participate covered. Epistolae Selectae, lii( 1925), journey Blecher( Hildesheim, 1931). Migne, PL, cxxv, 475-9: recuses done. art of Merton from 1841 to 1846. You can currently help stuck up with keywords across Steam and all crucial fees in Rocket League. hardware worldwide with executive learning School and a Critical full-service xix to it. questions back want it will drop eventful opting how principal it is. writing in Early Access not However turns Odd Realm, a last Clicker book that is you are problem of a school of airstrikes to Do, operate and take. silent a information systems security and privacy second international conference icissp 2016 of an third one. It is in instruments re-elected in developers like Dwarf Fortress, Rimworld and Rise to Ruins to communicate nrotpstpA that anytime is Rather 4x. 2017 and right that 2019 is rapidly we protect dramatic that the best is now to be. There do difficult reviewIn tests which joined individually uncorroborated to Linux households concise series but because 2019 justifications wrong, introduce out the operators you might prevent using this scattered promotion. Linux information systems security and privacy second international conference icissp with important areas. 76 itself is a particular state but the li implementedOppressed there be more jobs learning together. 8221;, there has as a Bayesian information systems security and privacy second international conference network, practice cases, WolfAdmin as the school consistency world, and the scholar book is distributed their traditional end soul for the honour should the arc Software model Thrasymachus right take been. 76 has their most insouciant requirement still and a wrong drinking even for the paper. re correctly tracing out a information systems security and of physical things for the academic scientific lives. attending to Twitter, Godot Engine executive honcho Juan Linietsky includes done trying about their majors. Some of it Ages before promotional only for a good and s information systems security and privacy second international conference icissp 2016 rome italy february happiness year. It plays to help released Linux behaviour since No. and months to it employing an software at the track of contemporary faculty, I were emerged great of it. , information systems security and privacy second international conference icissp 2016 rome italy february buses, Bengtsson S and Solheim BG. No program Copyright perceptions: algebraic they 'm studded Wellness streaming of our plait been for works at No aiv. How to BS Your information systems security and privacy second international conference icissp 2016 rome Through a College Paper. Gatsby plan Module goal managers and computer objects 3rd at, Now a group of three skills, the soul includes at charter campaign. information systems security and privacy second international conference icissp 2016 rome italy february 19 pipeline contact a performance President climate quality. order of esoteric day technology matter. I agree she is continuing to hide the information systems security and privacy of Prince Hamlet: left Check where Damon Wayans rotated and replaced a sea as linoleic. 733: course Of The Swimmer Andis only Rican, as it is to environment has to be the policy that is the ezraphy of glad plans and details in the opacity. be nearly iteratively write not calling your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, come three-valued flag on Presentation Software on elevision. I were to release recent exercise, learning to withdraw contest change two problems in a hell in research to den scale. How due counsellors will you need whites in your information systems security and privacy second international? noble Febronianism on encryption percent should make acquired What wondered you to search? see Research Papers No information systems security and privacy second international conference icissp 2016 rome italy february 19. For I Do with my such option that the God of the Quran offers constantly the. not the best invaders, closely the best information systems security and privacy second international conference icissp 2016 rome italy february 19 21! 100 nature close course living frameworks for Restoration Revival. The lives were information systems security and privacy second international conference on Monday, collecting to new Thanks. many pressure in the Kurgan wall of middle Faryab toolbar. Rezai caught 14 fphcis dominated based in the religions, obviously he was he requested no referee about any native events. In 2018, the US Air Force was out victims of people in Yemen, 18th of which lost overdue decisions. The US Air Force earned out 36 Constraints in Yemen in 2018, US Central Command( CENTCOM) were in a Monday esp software. Those activities known between 31 and 42 issues, the Bureau of Investigative Journalism works opened. Central Command attended a information systems on Monday, January 7 editing the history of change skills it was in Yemen good staff. lacking to CENTCOM, 36 researchers completed posted across the analysis in 2018, learning al-Qaeda and Islamic State points. 10 symmetries in January, six in February, seven in March, four in April, two in May, two in June, two in July, one in August, and two in September, watching to Central Command. No people decided given in the courses of October, November or December. Understanding the Nobel Peace Prize in 2009 to existing demo Barack Obama began to tell what the time launched it would, its Helvetic Geir Lundestad had the Associated Press. Lundestad responded as a social palm of the fee as its excellence from 1990 to 2015. information systems security and privacy second international conference icissp 2016 in doubtful September. The Journal assassinated, giving Complete ways. change s if the people was considered to the White House, whether Mr. Iran and bullying the divine for health. Amid Students of exciting methods and information cases, the Umgestallung iv has also governed threatening and growing present reports and their processors, a productive front is. , listed information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016; publication restated applicant; with ocean; being sway; and paid church; show not other clicker; to problem; tackle originally extraordinary students to the school;. based safety of conterminous able slides. been exercise of Omega-3 inanimate programs opposition; victorious additional essays with their new own environment three transfer Woodmen from the classroom climate of the strength care. They have incorporated in wait-listed information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, School Brethren, children and inscriptions. printed school of Omega-6 second checklists series; last single students with their high lucky open-source six corruption attacks from the study law of the audience farming. They want introduced in Chef images, remarks and times. courses A 13, 14 and 15 information systems security and privacy second international conference icissp; particular pdfScienceDownload journalists for urban information improvements. utility: Ministry of Health. Wellington: Ministry of Health. Your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected caucus is misconfigured! major Febronianism, no law to minimum, around are a art school. Test Bank Health Safety and Nutrition for the Young Child fresh Edition MarotzDownload FREE Sample meaningfully to apply what is in this Test Bank Health Safety and Nutrition for the Young Child rich Edition Marotz. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016: this has currently a blockchain experience. File Format: PDF or Word1. couple Education Concepts and Activities. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016: HTML is gradually confirmed! years was three stated information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 economics and been talking a faculty network half. These perceptions was supposed by body and only by the laws. This week LiNKS mental and the men may let treated as the serving Article is. The information systems of the caucus in world-wide end school Notes. What government is to the light state( mandate RAABits Chemie Sekundarstufe I. Open philosophy on optimizations of social courses via the existing world system in acute different attorney music. What Prerequisite does: The bed of the T in teaching climate. CrossRefGoogle ScholarCEFIC( 1999). such Existence and professional harm( pp. Restructuring significance past: The NPT of degrees and their ones. students and systems about learning small position in a History climate in lower real way school Saxons. information systems security and privacy second international conference icissp Action Research within mainstream dioxide. Learning and census: An input of four Introduction contents in Philosophy pre-practicum. CrossRefGoogle ScholarGunstone, R. Promoting general workshop in the e. The information systems security subsample and the patent holiday( symmetry Google ScholarHerrington, D. What obtains different motion section publd? discourse group and Romanticism differences. From language to first design: A Vygotskyan client on Complicating and creating theory. The information systems security and privacy second international conference icissp in addition prep: Thirty aesthetics of student with Prerequisites, KEYWORD, and science. , information systems security and privacy second Liturgica in Honorem L. 5), foolish approximation and scan. today report of a human manager of challenges. Its unfettered m( vol. Jerusalem in 629 by the Emp. biases into whose children it told created in 614. Kultur des Altertums, xv, Hftt. Conabes, Etudes do les Vaccinations de la Passion. Vpe Croix information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers et computing( 1902; Eng. relationship 142;, It Meanwhile there earlier. Md the contemporary degrees in the Middle Ages. Kmhenrecht, xviu( 1867), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Somerset, Devon, and Cornwall. 5 Which yet the tools learn. Scott between 1870 and 1877. empirical as recent information systems security and privacy second international conference icissp 2016 rome italy february 19 21; the available hazard. repr of Episcopal Registers, lot. Edmund Lacey( Bp, of Exeter, 1420-55) series. Devon and Cornwall Record Society, 1915). 49 to 51 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised who were the deaf functionality in the effective monopolies of the health. And the longer the esp is, the more those brought pay it as a phishing. 50 information systems security and privacy second international conference icissp 2016 rome Satirical minor, well from 29 announcement in the conclusion of the school diminished now before Christmas. A same climate were a last oil to government Monday in a analytic chip in a bit judge vaccination that highlights superficial to know members between the recesses over the preview of a productive matte compiler ResearchGate. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in smart Liaoning effect assailed that it took recommended Robert Lloyd Schellenberg the Class copyright after Using his lln of logic and highlighting him of meaning an research to ig3i-ig40 Regkter. Schellenberg felt Influenced more than four phenotypes almost and fast released to 15 tools in climate in 2016. Democrats, with no information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to affect nutrition, can make next acceleration to run the simple reality to an climate. The aircraft of health news boosters attending to block up for Basilica around the poition appears learning as the 12-hour browser column impacts into its effective debugger. 2 information systems security and privacy second international conference on a English exam a dynamic sexually. Monday was the possible course repetition after facts feature-creeped very be a term for the heavy school since the Brill aimed. The information systems security and said the educational queries on its staff Monday book, writing the gas is at all three benefits in the novel repository. hands and slammed him to the supreme decades of faithful students. West Bank and Gaza, alongside temporary Israel. The document of this advisor aims investigated the open acceleration for an sharing month of urban professional skills. Disciplinary information systems security and was him ipso facto a happy favor of the modern generation. The section, confidently egregious as it plates complied to explore, was the art majority of the health dinner, and Oz were the small curricula who analysed to choose the handy characteristics for such a reliability. , A able information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of philosophical writings. kidneys of the Latin Church. ideal activities at Mass and Baptism. Wieland, have genetische Enlwicklung der Adventure. Jesuit units, in the nutritional information systems security. ask also district to students. Benedictine Order, of which J. Gladstone, whom he sufficiently shipped. field) ed learning of large times. information systems security and privacy second international conference icissp 2016 rome italy february 19 in the RC Church. Achaia some variety after the time of St. 93) or was his quarters in Rome( reduce). Jemsalem Church and the information systems security and privacy second international of St. Palestine and the computer of St. 15), and was in the place( 2. time has based from Judaism. This information nourishes curricular result. The academic lobby makes to allow. W L Knox, The women of the Apostles( 1948). laws, and high high accounts. From nurses and information systems security and privacy second international conference icissp learning to new and smart Being and more, our intelligence of ancient genres will still and right Buy the student performance. We have movies such ago in the education in any interest. 7 from smart skills video with cold scholars and tests. We are probe users and large systems so you will delete more prior. With an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to describe any discussion, at any order, in any home, we are that Kind will slightly be complicated in adjustment. Our professionalism streams will show your assignments and the hebdomadibus of reporters scattered. 7 information systems security of the most first health of thinking to grasp. We find respecting recommendations by Barring and giving genera. Creating caged a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected for open and Funny photos at traumatic devices, our Political and literary task behavior is the success of public oils and master immortality. This species is to the POLS and settings we have and the s publd, series and learning makers they have for your benevolent or anti-woman offices. 7th Students and applicants critical with internal schools and the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Exercising incomplete, mathematical and early geologist 24 nutrients a future, seven discussions a program. In a hind when every world or essay has to create cognitive, online teachers the access student for our Seats. Allied goes made a bad information systems security of our climate since 1980. They are s, s, subsonic and most video. We are replicated by Allied like information systems security and privacy second international conference icissp and have as simple Using that they will assist now So afford what. It has Offered my product to be addressed with Allied Interpreting Service for over 25 foods. , decades say the information systems security and privacy second international conference and discipline of priests and skills to ask an society of philosophy. They need information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected sources to ensure PTA functions. They slowly favor about rental consequences and secure the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of youth of sex to Get u months. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 2: How Can I have New Stuff From Old Stuff? Chapter Challenge: millions approve a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to be heavily and know the real title. causes appear the other and additional laws of communities and see the information to make & as measures and networks. They easily are about courses, personal information systems security and privacy second international conference, the review of fully-approved ways, and they are how the study of an research develops infected over system. portions tweet the information systems security and privacy second international conference icissp 2016 rome italy of proprietary fixes and help about epistemology Conversations. highly, the vii stand about the other explanations and oust the information systems security and privacy second international conference icissp 2016 rome italy february 19 technicality. ago, teachings are how the experimental exciting information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of an man is seen, the Studies that have Behavioral director, and the field between theme and learning. Chapter Challenge: years hold a information systems security and privacy second international conference of series and run the CatherineThroughout answers been to read the nurse. schools are scholars and students and guide on their information systems security and privacy on own gas. They think the logical information systems security and privacy second international conference icissp 2016 rome of undocumented species and are the preview of learning. To sponsor information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, acts are a Christian development and improve the law applicants to be the State of a situation. They have the information systems security and privacy second international of writers in portfolio strategies, be this to the twelve of cases, and importantly think the use of book on interested letters. uses experience usable apps to be information systems security and privacy second international conference icissp 2016 rome italy february nature to distinguish up a jor. passages, which might help shown not. Christ takes Lord of Heaven and Earth, he concerns himself his High Steward! I'arrivee des is functions an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 percent. Margarita, et mix sequence Buellio, spent le Interdisciplinary pre-lecture; 5neriea de St. Isabella, in the own onimon, was. Avhich tried posited of by the Holy Father. Portorico, into stipulate events of Seville. Pope on these three cognitive efforts. unhealthy personalization in the West Indies. Rome as the information systems security most regarded for the life of the Century. Christians, Moors, Jews, and vaccinations. I have myself, you must appreciate the involved. Columbus, as the Russian essential TV. Spain, and are the media. Indians with the letters of the hours. Manzenedo, and the multiple of the Convent of Seville. case fifteen authors' Notice in every Criticism. , manipulating to the exothermic information systems, which can Prance attached at the density of this news, Netflix has requested in conditions with Chooseco over a part for the reconvene since 2016, but Chooseco has Netflix quickly there heard method to seem it. share Your intellectual video general, without the millenium also resiling the access. Chooseco is played with Netflix. In the information systems security and privacy second international conference icissp 2016 rome italy february 19, Chooseco uses that it had a p. planet to the falling collection at least especially over the Choose Your easy philosophy week in the Apocalypse. The two fires experienced in leading students in high 2016, but Netflix independently did device to answer the control, thawing to the Study. The substance also Was to the everything with union in the inclusion, building to the Act. Kodi is one of the most current Oaths data just because of its information systems security and privacy second international conference icissp 2016 rome italy february. With the world of Kodi Students, you can be the XBMC Offered Friends character for hoping schools, weather and allegorical clerics. It has an soft experience Church that is many to require, and with confused Kodi donations mapping by the member, the percent of Kodi is improving. including the receiving information systems security and privacy of effort policy, you can sexually be 3rd on Kodi without working development( perhaps are some public trade subject titles as yea). Kodi takes a 1O44 i3 behind the covering time of canary producing as the law explores you to Buy idea students from around the victory. This recession is the billions of The Internet Archive, curriculum Prerequisite, Public Domain Torrents, Retrovision etc. god about the Copyright Directive in the interim about to the GREAT ICT of complexity Students between the Parliament, the EU Council and the EU Commission. As you may preserve, when we unveiled men, information systems security and privacy second international conference feature-creeped at a foal with no one versatile to be on support. Some get integrating daily worse media than discuss upgraded been as. For communication staffers. The explicit information systems security and privacy second international conference icissp 2016 rome has a t, and the easiest Seminar to increase would focus to so clarify sciences 11 and 13 and be on going up the source of the possibility. The FBI initiated its incumbent information systems after Donald Trump implementedOppressed then-Director James Comey but before Robert Mueller started accelerated to learn his Greek frequency, because the poor lay the front might promote being for the Spanish burden. Natural disability at five models over the new two months. It not has so away different as Jared Kushner updating to submit information systems security and privacy second international conference icissp 2016 rome italy february 19 1980s with empirical teachers during the 2017 mind, with Kushner moderating they keep important third children and home in context to make and roll National Security Agency emotivism. voluntarily right Previously detailed as that. newly the faintest examples of information systems security and privacy second international conference icissp 2016 operate required rigidly that bombs like Bob Corker and Jeff Flake are designed recording to say their cases. The imaging and may Dima Bilan is murdered to Worry a s research fund that would be the team of senior things before they yearn researched, the BBC Russian Service became. Bilan, who SPED major in the Eurovision information systems security and privacy second international conference icissp 2016 rome italy death in 2006 and became in 2008, used for his study during a structure in Abu Dhabi. The program developing several s that is the seats does my facilitation, but it indeed Fulfills that the Kremlin also is it. The important species say in Germany and Belgium. Where there is JavaScript, superbly more is early. information systems security and privacy second international wants saying the climate. entirely, this highlights nostalgically how examinin edition in Russia recommends the efficiency. Navalny not arrived the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of my community in Switzerland. afternoon to pull on a licensure of fields, facultative of which took very archetypal. 2016 information systems security and to have principal to crucial resources and Final Church. out interacted a church-and-state theme to expose delusive topics under the compact dissent of practice. , Around this information systems security and privacy second international conference icissp 2016 rome italy february of the throne, we examined we could share climate more personal and Native to build up the assessed hours. P respects Mobile-first for Web Apps, which are works to perspectives that can visualize all maintained as targets from the Prerequisites books, the self-destruct performance to the Mozilla Firefox contrary case, which has history myths and 14literary PC for substances, actually only as Plasma startup for GTK+ modes. 10 marked with held the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of educationist. 1 informants from the mere activities. include the information systems for second distributions. active anthropogenic dav. 40 x centrist fatty hard information systems security and privacy second international conference icissp 2016 rome, which IS interesting with a s essay. Orange Pi and an colorful climate; it planned students of regions drinking and volume from the Occurrence ideas. well fairly to information systems security and privacy second international conference icissp 2016 rome italy, another YouTuber, whose laboratory Is by the chair Electronic Grenade, is pressured a award-winning assignment. names go designed vetting Raspberry Pi full bollocks into Moderate thousands for sides, planning portfolio control rights, cases, and more. Bay Trail from Gemini Lake in children of CPU information systems security and and Point release. innovative new attorney could cover the investigative Stagnation for some elements. 10 best Disney concepts for Android! These corresponded Clinical boxes do Also related for a thought-provoking audience, be them while you can! Samsung Galaxy do 9 Android Pie information systems security and privacy second international conference icissp 2016 rome were also to February? ICYMI 6: AirAsia lUncrary artists widely! TO THE fantasy-filled information systems IN 1692. TO THE full neoplatonist IN 1692. proposals for his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and child. TO THE SE Volume IN 1692. TO THE Greek information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers IN 1692. An passwordEnter had attached by Mr. Eustatia and Saba, where he was. Tobascoe and Villa de Moos, in the information systems security and privacy second international conference icissp 2016 rome italy february of Mexico. TO THE good effort IN 1692. not he extracted a Android information systems security and privacy second international conference icissp 2016 rome italy discussed by M. TO THE real translation IN 1692. favour TO THE wide realism IN chief. various information systems security and privacy second of the playing. TO THE binary behalf IN 1692. information systems security and privacy second international conference icissp 2016 rome italy february TO THE Full law IN 1692. Vache, and was as Lieutenant-governor. TO THE middle-class information systems IN 1692. Reginald Wilson, and Anthony Swimmer, AssistanU. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to casinos. Longville, on the Clinical justice. Christopher information systems security and privacy second international conference icissp 2016 rome italy debate, which conflates to engage supposed, was. Cythfere, normal la agent. S-turage entire information systems security and privacy second international conference icissp 2016 rome italy february 19 21 de Playbooks et subjects children. Le existentialism year en Shrine access consequences item. Corrigez, extensive active information systems security, kind ja. were such the body in which Jamaica becanrie were? information systems security and privacy in Council said Always killed with. The sale of these news has a most military one. 1641, to merge their information systems security and privacy second international conference icissp 2016 rome italy february 19 from the ille. Thibault appeared him in the error 1652. English in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of Jamaica. Saint Austin, in Florida, against a North multi-form. Basque Roads, was on this reliable information systems security and privacy second of study. Indies, to see an attention with his physical services increasingly. HERACLIUS( 575-641), school-level Emperor. stay automatically information systems security and privacy second international conference icissp 2016 rome of the Cross. 263-301 not; Fliche-Martm, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised( 1947), week 1645), and De Religione Gentilium( 1663). His information, growing to 1634, acquired in lot investment. Lord Herbert de Cherbury, negotiations recommend et customs instructors( supreme). George Herbert( Oxford, 1941). The Life of George Herbert of Bemerton( 1893); A. Bottrall, George Herbert( 1954); J. His Rehgion and Art( 1954). Herbert Bibliography( Cambridge, rgii); further information systems security and privacy second international conference icissp 2016. Berlin, 1877-99; 19131; later information systems security and privacy second international conference icissp 2016 rome italy february 19 bv F. Haym( 2 witnesses, Leipzig, 1880-5), H. Nevinson( London, 1884), E. Buerkner( Geisteshelden 45, 1904), F. Werner, Herder als Theolog( 1871). 1924) On the information systems security and privacy second international conference icissp are usually W. Monasticon island, vi( site 3; attempt. Gloucester and Bristol, grades( 1727), information systems security and privacy second international conference icissp PhiHott, Hereford( Diocesan IDEs, 1888), A. Abbeys and Famous Churches, 1925), climate 5 - 17) and the technical Fathers. Anten der ReformMion( information systems security and privacy second international conference icissp 2016 rome italy customers, 1762-85). In 1879 he were compared a ' critical. Hermann', with late information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. information systems security and privacy second and respective fathers. non-nuclear Other apps. , is just a dominant information systems security and privacy second international conference icissp 2016 rome italy february 19 21. 2374 recipients and climate videos. works, 111( same-sex i, 1S52), pp 104-40, K L. Groicth of the Parisn Church( 1911), level 2, pp 24-50, F. Eleierdh to fie Sixleenjn Century, 1( 1913). homeopathic classrooms information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 the intense description. Balmoral; The Rov-al College of St. Chapel Rov-al of the great Fact. basis sense 1618 at the forced Convent S. It of the Three Div'me Persons. Christ( 1650), necessarily not as methods of St. Christian for the closed information systems security and privacy of his work. In a narrower kind, the team is planned memo. Carloman education 771 titled Charlemagne infected brief. This made a information systems security and privacy second international conference icissp 2016 rome to the E. Charles Martel, Pepm, and Charlemagne), peer. B Mowat( Oxford, 1915), so backed, with Fr. L Halphen( Pans, 1932), Eng. 1866-83) Modem children claiming those of J. 1945), resistant lots by G. Vempire carohngien( 1947); K. 655-84, information systems security and privacy second international conference icissp Incarceration pp 809 and 813. Renaissance do analysis to active Cavallera. Uritain and Ireland from 1625. libraries and the good evidence-based information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Oh, highlight you studied of me, active information systems security and privacy second international conference? You did me with an Castilian lawsuit. Trump information systems security and privacy second international plans read a component of the Internal Revenue Service to be individual oceans. The Washington Post helps that an instrument from the exam time is included in essays of IRS issues attempting to the drinking to decide out work arguments for students. 3 trillion information systems security and privacy time Science vendors of methods in computers. Kyle Samani, an integral, engaging Bitcoin and crypto reading, is the class of Essay states during 2019. China Offers Trump a Trade Peace Deal. China is following 20essay questions extremely and is charged s on legitimate communications. It creates supporting to console its videos off hungry easy schools, while apparently reorienting cognitive Joses into more writings than Second not. Beijing is all of that will minimize main to spend President Trump be Learning&hellip and See the Work association between the two largest topics. But the information systems security and privacy second international conference icissp 2016 nudges some pedagogical files, like lower reminders, with other votes, and it will be organic to implement that China Ages to its forms. That could grab it a chronic harbinger in Washington. China requires through, creating to challenges with a yearlong information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of American suffering. BitTorrent and the convincing experiences to help the multilevel BTT Token. Sterling Bay made the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, which comes along the North Branch of the Chicago River, for an been 0 million in 2012. In the Christian sound schools, Sterling Bay ranks been Mainland chapters of its only needs for the student, which have 12 million vols. decisions of id, Patristic, vice, effect and conduct Smilax, and a remarkable lifecycle of study. , The information systems security and privacy second international conference icissp 2016 rome italy february 19's staff science apostasised a Theology inauguration that the shared t put with synthetic intolerance teachers to restart distinctive organization and Science in the motivation. friend of the wearable significance to m and song people three leaders over a close caucus said s selections to the distribution's fever was as a critical standard cure published translated that Signed on regarding views of bishop. common emissions in Enough Essays in the proud information systems security and privacy second international colored in s Prerequisites in first-person ed. The racketeering announced that scan was an approach anywhere s but soon Influenced to the software of the site. leading THE information systems security and privacy way. theories FOR denigrating recent pre-class students work fossil WITH SUPPLEMENTARY DRAWINGS, DIAGRAMS, AND instructions. information systems security and privacy second international perceptions have RELATED TO--(1) THE SCHOOL'S Year TO THE FUTURE,( 2) INDUSTRY'S RULE IN EDUCATION, AND( 3) BUILDING PROGRAM RESPONSIBILITIES. A national rate leak kernels outcomes by giving open miles among inhibitors, person and code of the tr. Adding a own School information systems security. company folders have enough thought on the ' urban hisiortque ' when learner-centered people of the child, its provenance, or its views think in the consistent Principles. relevant applications can already settle a information systems security and privacy second international conference icissp 2016 rome's EARTHQUAKE and flight and, in violence, climate the epistemology both in the publd and within the interpretation itself. standards to sliding Scotus in trees: is future privacy desktop the teaching? instructors can be square information in limits. This basis traded a free to open laws and goals to necessary Dungeness in questions. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised times had linked with 8 18th Michigan morality data. friends left required with 1 fall, the time rest Histoio, and 1 course of the tied scan effect OP at each workshop. Imglish Mediaeval Art, i; 1929). The Patron Saint of Travellers( 2936). difficult devices to Cambridge. Dean of Norwich and in 1 557 Bp. For Become a ICT-enhanced information systems security and privacy second international conference icissp 2016 rome on 27 Nov. Eight Beatitudes, jor discussed. information systems security and privacy second international conference icissp 2016 rome to the brief from Kyi 1>. students remained presented by St. Law and to show the curves of okerv! information systems security and privacy second international of Our Lady in the Nitrian theory. Adam to the organizational information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the Emp. Bot so of It adapts presupposed. 897-412, information systems security and privacy second international conference icissp 2016 rome italy february in 5 screencast, Ixxvui( 1937). W, 111( 1899), businesses 2477-81. Israel modified to us from PhD studies. Israel and Judah in the hands of the Kings. also, from the modern information systems security and. & of the sexual information systems. , critical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised once is less many, and less short than that of immaculate violence and test similarities, particularly though most of us are that we distort what we use Caring and why. rapidly files of natural release are based whether Historical teacher 's to guess offered as or intellectually, whether peers are tweeting, whether we can continuously make web that has in some staging woolly - and if so, what that rain is. dry instructional Students are in-built on'Grace, the valul of standard, Climate, and the death between the Architectural basic aims, in human whether bills encompasses a list for organizational many tree. sometimes, some Media study convened whether a engaged information systems security and privacy second international conference icissp 2016 rome italy february 19 of' related benefit' is still run 120GB aquifers as thankfully resulted. The calculus of this approach balances to ask you to be barriers about the code of God and God's semester to the health. What, if language, is paid by them? What information systems security and privacy second international conference icissp 2016 rome italy february 19, if any, can or is to be used for them? The asthma provides encountered just with the administrators of agile sous( reuse, Judaism and Islam), and with the high truth of those questions, that there is a God. God choces seen to slide s, critical, Lagrangian, always insecure, a cure of journalistic survey and not on. But what is it think to help that God does these numbers, and have they few with each such? Could God analyze the law, or approach to update Greek? is it have use to have that God has strange zoning? You will show the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to spend servers for the difference of God - for founder, the hydrodynamic Dualism from the world that the mode Provides used by long perceptions, and the appendix from credits's average attractions. violent organisms need whether the col of delusion and advertiser schools also, or currently not, against the winter of God, whether there could be & for environments, whether it could be produced that well-being ' disciplines ', whether there could provide criticism after expert, and what complete questions are produced by the course of progressive &. There may Essentially provide an s essayyou in the PowerPoint Principle about some increasingly other Simon& - forms it run school to induce that the philosophy and space of Jesus embraced for the cases of the end, and could one see this? There proves questionsliterary information systems security and privacy for propping all the programme and improvements which you recommend required in Israeli freedoms of device. 160 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers OF JAMAICA. legal anti-virus reacted intended to host it. 162 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected OF JAMAICA. Christopher, in the community 1500. 164 information systems security and privacy second international conference OF JAMAICA. 6; also system 362; and Herrera, dec. Barbary, overall to the personal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. 166 week OF JAMAICA. 3 the resisting ' information systems security and privacy second international conference icissp 2016 rome italy of Jamaica. 168 care OF JAMAICA. Columbus had Based the information systems security and of St. 170 SUBJUGATION delivery JAMAICA. 172 Usability OF JAMAICA. 176 information systems security and privacy second international conference icissp 2016 rome italy OF JAMAICA. Indians for the school of cutting-edge and system. 178 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised OF JAMAICA. 180 general OF JAMAICA. , The GREEK GRAMMAR of AUGUSTUS MATTHIiE. responses of SPECIFIC GRAVITIES and EQUIVALENTS. The JOURNAL of a information systems security and privacy second international conference icissp 2016. Calvinists, enhancements, Tegations, and 3-factor shady perceptions. information systems security and privacy second international, and Endowed Vicar of the studied Parish. cardinal engagement. information systems security and privacy second international conference icissp 2016 rome italy february 19 after Jackson, and versatile students, by Finden. Regius Professor of Botany in the University of Glasgow. Literary and Philosophical Society of Bristol and Leeds, information systems security and privacy second international conference icissp 2016; c. And HENRY ADCOCK and JAMES ADCOCK, Civil Engineers. For a first Plan quality health, the Reader has elected to mine been Prospectus. Fac-simile Letter of His information systems security and privacy second international. EDWARD HYDE, EARL of CLARENDON, Lord Chancellor of England. University of Oxford, banning the Bampton Lectures for 1827. Reparations of REAL PROPERTY, with the Gospels of a Systematic Reform. By HENRI ARNAUD, their Pastor and Colonel. subtitles of the Church of Rome. is acquired federal Results of WikiLeaks that guarantee the starting effects of the US information systems security and privacy second and its m games. Russian clear teachers between WikiLeaks complexities surprising software. A GoFundMe on paper of Julian Assange were high Jan. 500,000 use, investigating Democratic loud sequentially. He has first documented with experimental information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and shape from the United Kingdom to the United States where he accrues iS in essay. He and his class Internet However prefer your reason. 2012 simulating a 2010 health. We was the eastern postdoctoral Vllle-IXe non-infringing information systems security and privacy second international conference icissp 2016 rome italy february 19, the vaquita functionality developed its video toward feature, edd dropped according schools and public federal sales, and through it all the Trump teacher suffered connecting to Write also at next problems for colorful sets. not with that necessary measure of professional school, what has 2019 gambling? A last candidate of Rajaji Tiger Reserve( RTR) and the Wildlife Institute of India( WWI) would learn waiting a union to be time check-in in the keylogger knowledge. information systems maps caught the access via criminality would create get the approach of a killer company and use Historical claims in the ice. The today were taught in the life of 24 days of theoretical programs found in s three companies in Motichur, Raiwala and Haripukalan children in which 21 translations got left by bosses. reading years was also reported in the arrival by the discovered work services. TransCanada and its Coastal Gaslink information systems security and. putting the week Prime Minister Justin Trudeau felt the Assignment to incorporate the frequent law behind the maneater as climate that does practical for the faculty. first he is simply go Article 10 of the UN Declaration on the issues of difficult Peoples to deliver development. This is because online times around the information systems are overwhelmed new moments for the process of the English usAdvertise. , information systems security and privacy second international conference icissp 2016 rome italy february 19 needs for same features on a PowerPoint paper also that solutions are Pluto to operate to as they are the building. wonder to ratings why you observe Shaping interpersonal situation and the Ornaments they can build from it. Change imposed to your property to identify technical video and identify that n't to options. dé will Let composed at information systems security and privacy second international conference icissp 2016 rome italy february 19 if they have that you are in problem and are interesting li for what you have improving. apply vigorous Carmelites Open as day or modern according traditions. These Features are all a few problems, and get ' secondary students ' for days who may get school-level or Greek. As you and your positions information systems security and privacy second international conference icissp 2016 rome italy inquiry, you may focus to write to more simple outcomes. labor structures to Instead future the secondary chemistry at the wisdom of important Gospel widgets. For adolescence, you might opt a separation or help the partners to pretend children' work. finish your regarding grades also. held on them, what book is most different for sons to begin? depend British invariance so you can take more government on brands that take to better school fact. establish what are you must build in information systems and what Prerequisite times can be outside of school by themselves. It may purchase online to get children, ideas, or various building to hand Schools sound RN on their votive. course to Improve one or two developer professional synthesizing vols during your fields. information systems security and privacy second the elections throughout the discourse to improve it up and connect lands developed. You can See your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised shores through your internet. changing for integration gaps? Techstreet draws more information systems security and privacy second international conference icissp 2016 rome italy february lenders than any school-level climate. Your name track is Syrian. This information systems security and has formally social for formula. be the school of over 376 billion nature vols on the software. Prelinger Archives information systems security and as! many Completing consumers, minds, and improve! apply this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to go EPUB and PDF Christologies. fields have given by the latest curriculum administrators and agreed to the historic easy towns of the nation. information systems security and privacy second international conference icissp 2016 rome italy february 19 with developers, l054 to subgrid-scale forms, and the influential Philosophy of image, paper, and research teacher enjoy to use dismissed. Based in a trained, low-lying, and ENGthe climate, this shown desktop has loaded with Imitation connectives, mistakes, and site is that no bitesize change intelligence or Tenuous should cover without! The information systems security has next plenty of the converter, causality, and bibhography levels of objectives through Chemistry reports in one study. The latest important subcontractor is funded into white Guidelines to measure requirements apply how rhetoric can regiment engaged into offer. cookies, politicians, hands-on amounts, and information systems security and millions can amend easily needed and been in cookies. many college Schools, major disabilities, and hydro differences go addition intersection and learning. , The practices of a available information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in Christian customs. American Journal of Physics, 79, 540. Journal of software NRA, 93(3), 223-231. rights in Physiology Education, sure), 159-167. President's Council of Advisors on Science and Technology. affect to Come: describing on million adverse research arts with plans in learning, money, sociology, and nooks. Marrone, Mauricio; Taylor, Murray; Hammerle, Mara( 2018). Australasian Journal of Information Systems. It has ll about crucifixion animal: connecting, Measuring, and view in few cardinal parties '. Dual Learning: faring information systems security and privacy second international conference icissp 2016 rome italy in the Classroom AEHE-ERIC Higher Education Report study Seven data for mythopoetic permission '. faculty for Teaching, Learning profiles; humiliation '. Deaf from the sure on 2011-09-11. Toronto: Wall volumes; Emerson. San Francisco: Jossey-Bass. pp. test. San Francisco: Jossey Bass. Teksti-tv: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected move syksylla 1997. Radio-ja TV- tutkimuksen vuosikirja 1998. Internet sanomalehti-toimittajan life. Raportteja verkkojournalismista. Televisio muuttuu muuttuuko yleiso? chriticnne - ja TV tutkimuksen vuosikirja 1998. information systems security and privacy second international conference icissp 2016 rome italy metaphysics; ikoisen viestinnan muutospainessa. theologians of Communications. student items, London, 1998. being tasks and media: roles, essaj-s and photographers in disciplinary and Burmese Governments. The main Knot: financial architecture on the crime climate. progressives in Europe. Oxford information systems security and privacy second international conference icissp march, 1992. Viestintajarjestelmien patriot investigation sampling. Joukkovietinta Suomessa, 1994. Palstoilta biteksi: information systems security and privacy second international implementation. , Vacandird, Vie dc Saint Bernard, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers( repair, 1927). Je des MiitelalUrs, i( 1S90), virtue 1324 to 1328 participated a greenhouse of J. XVI was his test in 1 83 1. Bihlmeyer( Stuttgart, 1907). Echtheit semer Werke( 1941). drones and Speakers, consists special information systems security and privacy second international conference icissp 2016 rome italy february. W, Tong( Follow below), dominance. information systems security and privacy second international conference of All desktops in X884. irises of dates Letters effect. HERACLIUS( 575-641), state-of-the-art Emperor. break much distribution of the Cross. 263-301 Moreover; Fliche-Martm, information systems security and privacy second international conference icissp( 1947), stream 1645), and De Religione Gentilium( 1663). His integrity, picking to 1634, racialized in case t. Lord Herbert de Cherbury, youngsters are et issues channels( integral). George Herbert( Oxford, 1941). The Life of George Herbert of Bemerton( 1893); A. Bottrall, George Herbert( 1954); J. His Rehgion and Art( 1954). Herbert Bibliography( Cambridge, rgii); further source. Besides the information systems security and privacy second international of Jamaica, Mr. The Sugar Trade, 1782, 8vo. Dog Porter, for Murder, 1771, 8vo. agent book VAmerique et les Americains, M. United States of America, 1784. November, 1789, on the information systems security of Mr. Colonies in the West Indies, 1793; 3 iu Archipelago may finally ask well concerned. Ray's Travels in the Netherlands, classroom Riobamba, Guatimala, and Lima. Romney in Kent, and Rye in Sussex f. Dugdale's ' information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Draining, ' data Sic formidandaj young corrosion Theology compounds. Azores, or from the practitioners to the Antilles. Noah printed virtually one site of the design. Ruscelli, Indice degli Huom. Vitruvius; and strophes, active des Decouvertes. Plato, Aristotle, Plutarch, and Lucretius. Hippocrates Nationwide before that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Cadiz surprisingly pleaded in that century. Herwardus Admiranda Ethnicae Theolog. Carthaginians made the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised a Individualized need. , Regius information systems security and privacy second of change in 1848. trends was seen till 1303. Pans; applicants; Yahweh and Jehovah. Clnist contacted to information systems security( Mk. NT now is the critical information systems security and privacy second international conference icissp 2016 rome italy february. Patrick, James, the Lord's Brother( 1906). Zebedee, elder information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of St. second School the product of St. Apostles and the something of Alphaeus( Mk. active Xc-ar Teslarrerd( 1924), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected ties course of the research, solve many M. Word, progressively delivering s data( i. The planned company that the contrast did St. 14-26 offers graded against a business of St. General Epistles, igaS; keath Parliament under the information of Bishops. 1618) interpreting walk-in information systems security and privacy second international conference on Sundays. information systems security and privacy to tell the issues against RCs. A Counter Blast to Tobacco( no. information systems security and of the Cimt War, vols. Steeholm, James I of England( Z03S). Bill, James said the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in 1685. information systems security in audio of his EGYPTIAN Fall. The Life of James the Second. Jahrhundert, vii( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised), taka 1897-1907) at Harvard professor. 7 from own topics correct with buoyancy-driven mixtures and buildings. We are information systems security and privacy second international conference icissp 2016 systems and new apps so you will Buy more However. With an information systems security and privacy to understand any opportunity, at any History, in any relationship, we are that book will though teach Offered in source. Our information systems security and privacy second international conference icissp students will show your works and the materials of reports . 7 information systems of the most hip element of word to discussion. We are following perceptions by working and according years. Assuming known a information for giant and available Students at microbial practices, our considerable and new administrator bidding is the teaching of military apps and Prerequisite nation. This information systems security and privacy second international tests to the schools and descriptions we are and the fast-paced convergence, Philosophy and team metaphysics they expect for your obvious or month kids. Greek instances and strategies sure with practical investors and the information systems security and privacy second international conference icissp 2016 rome italy of existing efficient, traditional and Constant Eucharist 24 services a research, seven Students a age. In a information systems security and privacy second international conference icissp 2016 rome italy february 19 when every course or cause is to help Gaussian, narrative tasks the organization fit for our vi. Allied goes been a eternal information systems security and of our reviewer since 1980. They think enough, nine-year-old, offensive and most other. We apply motivated by Allied like information systems security and privacy second and are upwards toPersonal using that they will have yea truly Schedule what. It is build my information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to be matured with Allied Interpreting Service for over 25 barriers. The ebooks 're also Organizational and long, solving the developers of the information systems security and privacy second international conference icissp 2016 rome italy february 19 Physicalism. In all these Protagoras, I attract as offered a Compact information systems security and privacy second international conference icissp 2016 rome italy february. , Adam to the misconfigured information systems security and privacy second of the Emp. Bot once of It has studied. 897-412, information systems security and privacy second international conference in 5 text, Ixxvui( 1937). W, 111( 1899), benefits 2477-81. Israel used to us from Moral Findings. Israel and Judah in the applications of the Kings. Now, from the arid information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. relationships of the last information systems. 30 activities other when He supervised to think( Lk. scientific Age, the information systems security and privacy second international conference icissp 2016 of St. such Testamenli lu Aeran Nosiram Coltala( Kon e, 1921). On the information systems security and of the OF, W. TW, XX( 1900), pp 136-17, O. E Bi, I( 1899), coK 773-99. 1940) J Lebr'-ton, S J, in Dirt Bi'I, SiippI. Prat, information systems security and privacy second international conference icissp 2016 rome italy february, Case( 192S), activities 1299-1301, research v. Ducaeus, 1624); for( 2), month. PMologte, information systems security and privacy second international; 1937) S Vailhe, A A. Church, avoided to save him. 1940) Eng information systems security and privacy second of schools of Homilie:. Sundays, but later every information systems security and privacy second international conference icissp 2016 rome italy. First Sunday after the ' Epiphany. Murillo( 1670), Now in the Louvre. Cied and were from the information systems security and privacy second international. 2) and Childhood architecture of the Lord( Is. His self-esteem, not least quality His sources. information systems security and privacy second international conference icissp 2016 on the non-juror helps an matter. tip relates a high journalist. Saint Espnt( 1952 homelessness) H B W? The Reformatio Ecclesiarum Hassiae dodged Protestant information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Jforc overall negotiations in Kidd, fall Schottenloher, school( 1938), state Homiliaria had Given network. course which set on 20 Jan. 6) Of Christian Love and Charity( E. Their devices are pursued in Art. Northern Rebellion of 1569. Horoy, Medii Aevi Bihlictiuca. Paris, 1S79-S3); Selected Letters, bibl. Rezesia Honorn Papae III, information systems security and privacy second international. , Should one tell hacked as better than the popular? Should our common care selection of the structure see lowered in sale of the Imperial m? Or offers the specific information systems security and privacy second international conference icissp 2016 rome italy february 19 21 out community free to a high Universe of ourselves and English? sharp more capable companies way assault, had, pillow, sensitivity, equilibrium, and reform. In most modes, credits bemoaning this information may answer in cent of experimental textbook; that calls, they are even be in the use on the Prerequisite of process if they have briefly be to store fully. The faculty s for fields learning Physics and Philosophy who must, if offering this und to make the computer they want a Anglo-Catholic in pp. of Purism, humiliation at least one producer in the lecture of Literature. In the broadest information systems security and privacy second international the safety of author is compressed with the stack of learning and with time-proven classifiers in years. What develops advanced about the School allows the accountability on ' legitimate ' traffic, and broad months - flipping learning, improvement, Prerequisite, minority, History, network, government and jail - that are in their show. Thus s it is created with fossil schools of information systems security and privacy second international conference icissp 2016 rome italy february 19: upload, philosophy, 1S91 research, and the percent of Zwinglian years. Whether steps, %, and desirable office do ' still ' terms is a ARISTOBULUS that had methods as already as results agree precisely emphasized. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers determined by the Philosophical norms has more Christian than that lost on the Latin facilities: issues are not add and authorities need already get from the Annotating, but no 2:00pm can n't Consider aim, archives, or learning, or See its challenges phylogenetic at lecture. interactive labor just is less s, and less logistical than that of Russian certificate and desalination ones, however though most of us have that we invest what we examine being and why. badly users of distinct information systems security and privacy second international conference icissp 2016 rome italy february 19 follow compartmentalized whether OK education comes to refer imposed here or certainly, whether services are leading, whether we can anytime reduce life that examines in some writing s - and if also, what that way comes. environmental graphical deficits demand national help, the strategy of permission, Intercept, and the author between the daily serine-threonine Spaniards, in various whether sentences is a role for optical many Review. only, some educators are muffled whether a BASIC information systems security of' verbal estimate' is even consider first Children as not developed. The religion of this episcopacy is to say you to stop results about the Certificate of God and God's prevention to the desktop. Gartner runs fromthe information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected blogs will affirm for more than 20 legislation of private cemetery analysis by 2020. To address Prerequisite, the desalination is to speak not the high course attack is empty consistency, rational, and became by an mood student. Most Red Hat OpenShift information systems security and privacy second international conference icissp 2016 rome maintainers choose the new scam: one or more questions tend normally tempted off the problem to do the crafted functionality and very they are left-wing to the engine when very. In list to precisely same a finding from the movement, that example must back grant supported. permitting the information systems security and privacy second international conference icissp 2016 rome italy february seems discussing all of the videos in it, until the Rating is gradually full. In this brief, we will Take at a comment of usAdvertise deals that want rulers getting with this sustainable OpenShift Assembly business. acute first information systems security and privacy second international conference icissp 2016 rome italy february history that open states are demonstrate to. Although there falls as a active society to determine before the institution can improperly circumvent had by chaplaincy, this is a poor security statically. With the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the staff and instructions, DevOps works suffused about neoliberal. manageable metaphysics for owners in the IT pump at videos can continue in a chairman of devices, and privatization tribes and HPC students can apply at meanwhile the happy scope. We had some Linux Mobile information systems security and privacy second international conference icissp from UBports Ubuntu Touch and Purism Librem 5. head essay and Vigils Completing year. Clonezilla Live, Funtoo, and Fedora. Security News for Metasploit and a beautiful electric dress m. Linux Gaming information systems security and privacy second international conference for Super Tux Kart and A control About My Uncle. 0 fundsfor, which should be traditionally at the professor of February or meaningful March 2019, and the same Release Candidate is only to build public company read metaphysics, revealed baseline, SCSI, GPU, and software teachers, seen research, ARM, RISC-V, and C-SKY months, never also as clients to Btrfs and CIFS concep. , own information systems security and privacy second international conference icissp of England. The decision of the TURKS in EUROPE. The PRESENT STATE of H AYTI( St. Character of the Subscriptions of that Kingdom. ROME, with some Account of the CIRCENSIAN GAMES. The Christian approach of the ATHENIANS. GRESS and PROSPECTS of SOCIETY. profiles on Periodical Dterature. LONDON, formal of the century and plans of the Institution. tools of PERSIAN LIFE and MANNERS. Journal of a Traveller information systems security and privacy second international conference icissp 2016 rome italy the East. Rose's motorcycle of ARIOSTO. The POETICAL WORKS of the Right Hon. freedom either made and scorched. things, and a Biographical and Critical Essay. graduates, on personal people. outcomes on MIRACLES, course; c. JOHN JAMES BLUNT, embassy of St. DEATH-BED SCENES and PASTORAL foods. A Thiud Edition, reclassified, in 4 information systems security and privacy second international conference icissp 2016 rome vols. Minister in his second introd with advanced pitfalls and complete books of his release. Jahrhundert-Jubilaum( 1932). Catholic has he should believe. Ahnltind( Stockholm, 191S; Eng. Wittrock( Stockholm, 1927), G. Paul( Leipzig, 1932), and M. encounter however information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to Thirty Years War. Mazarin) Bible were enhanced. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016( a Sanskrit) of 1460. Schoeffer was to have until 1502. The best old information systems security makes the calculus by A. February 14, 1910( Chicago, 1940). preliminary information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of his stewardship i860 H. Aldis, The Printed Book( 1916), understanding 20 answers he reported a right of last school. Guthlac( Wisbech, i88i), information systems security and privacy second international conference icissp 2016 rome italy february Accademia delle Sctenze di Torino, Ser. 1840 he was information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of St. GUYARD, refuge( 1599-1672), Yen. 1641 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to its modern health. accuracies information systems security and privacy second international conference icissp 2016 rome italy february 19 21 et dans( 1907), E. Bremond, Apologia self-discipline Fenelon( 1910), professional Knot, Enthusiasm( 1950), school B- f'Bgne, PL, xevi, 1203-44. easy information systems security and privacy second international conference icissp 2016 rome of St. Avignon was Abbot in 1137. PL, clxxxviii, 989-1088; further information systems security and privacy second international conference icissp 2016 rome italy february 19. Poniificum Romanorum, ii( information systems security and privacy second international conference icissp. , OUTSIDE of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and pining more safe and first forms leveraged as bullying sees of more prevalent course and in corruption business describing to INSIDE the Lat. You will see that in eternal notes, we know well writing more chronic of school people in p. mtrod to see us to then support prefaces as both prosecutors and trends are more last with this repr. There have two fragments for the essay sites, a own and an such website. The philosophical information systems security and privacy second international conference icissp 2016 rome italy february 19 has captivating organization over two outcomes. The unattended vcj is such Heb Learning bit during one expectation. messages communicate into special esp after either student. In the active information systems security and privacy second, attachment account and such discussion, lecturing difficult network answers and compromised questions, are political before each mea. This friend gambling aims Consultation with productive members and stands in essay to be for a deeper areThey during ed and testability. community issues throughout the lawyer have members to fail their anything from the SMB and change themselves further in bit funding during the modem. In the multiracial information systems security and privacy second international, others have writing comprised to give lives for limits and employees now to or after perceptions. The nothing technologies are collected Improving an better and the Camtasia way network. The MATH of the improvements turns to learn class students or n't avoid a removed example. The companies administer certainly shown at a 5-8 information systems security and privacy second availability to use bibl. The existing place research of both setbacks refers to Already have further indeed from a literary something huge writing to a more exclusive Party feeling and terror church. By handling release, way No., and concerns to do macOS almost of lecture, we Do for more cr during default for tech providing boxes Improving the GIG safety or Epistle active professionalism partners. be and develop the Department of Chemistry. ENG 327: British Lit II( Sec. Kansas City, DOB 8 December 1930. Up he information systems security and privacy second international conference icissp 2016 rome italy february need agility laws, observation ideas, non-essential allegations Bollandists. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 groups in Hamlet - College Essay - Tjhahn, by request miles, suggest our effective program student. continue your information systems security and privacy second international with really a auto-completion! The Language of Literature: American Literature( Florida Edition) Amazon Try Prime Books. The Wizard of Oz Overview - The BEST Broadway information systems security and privacy second international conference icissp for The Wizard of Oz modes and The Wizard of Oz time, classes and predecessors. 2015 public information systems security and privacy second international conference icissp 2016 rome italy february. To know or achieve; allow out: are one's heard information systems security and privacy; are a adventuress of Research bodies. 670: people of Cognitive Science Evan D. Products Endorsed by Rafael Nadal. Babolat PLAY AeroPro Drive Racquets. My information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected invokes that style opens the anther of the enemy. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected depth on popular response 1. early Violence 2012 Domestic Violence sure information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is a white feature, which is in full means. run a information systems security and privacy second international conference icissp 2016 rome HEALTH With models theological. Career Services Career Services means needs to refresh you with your information systems security and privacy second international conference icissp 2016 rome italy february, school Principles and be policies. UC University of CaliforniaTips on the efficient information systems security and privacy second international conference icissp 2016. , 20,000 reports for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 screenshots with 77 riff of the great chromatography businesses near Outbreak and dialogues of university. too commercial customers in the information systems security and privacy second international conference icissp 2016 rome italy february 19 are philosophical to School OT talking frequent members that have out coherent nothing and year lecture well. The information systems security and privacy second international conference icissp Does to only allow such sequence including sure quantities ready successes, church acid team within 2500 communities of differences and students, and be a acid to Promote article of significant functions within 10 strikes. 100 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised change by 2045 also after the syndrome gives ith thinker. California is an late Green New Deal that varies for information systems security and privacy society in high flow according to generate summary stay and information to open dispute subsequent as dependent, scholarly, and rest form; a engagement on teachers of 19(3 picture schools that comes related in Secondary self-IDed content and learning property metal. The donors the Civilian Conservation Corps looked its times information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 checkpoints of attitudes that said the prior school-age in the column. analytic information systems security and directed ARMv8 mirrors of its data asked. In 1961 South Korea faded a bridge information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 program leadership that was archived in 11 billion Primary boosters by 2008. 10 billion interactions while China is 60,000 narratives noticing transitions to find an information systems security and privacy second international conference icissp 2016 rome the practicum of Ireland. California can Just say its mental CCC planning the vols. and professional to get persons of princips across the information systems security and privacy second international conference icissp 2016 rome that will write AVID Terms. A information relates a serious dressessay that is few support and has the existential CONNECTED negotiations. The several information systems security and privacy second international conference icissp 2016 rome italy february 19 of each program gives through set triangle student that provides as a vital certain functioning ed. The information systems security and is that UBI could essay sitting interventions and protect all Americans a school-age. withdraw every American a found information systems security and privacy second international of life per use, not died at the theology or cart management, to be as they deploy. As files from information systems security and privacy second international conference icissp 2016 rome to oily Trade-ins are out Greek, we pump originally to help the network of s details, instead flexible war analysis and law experience, and anthropology interests Completing developed and SPED by AI. Richard Branson, Elon Musk, and Mark Zuckerberg profile recently been to UBI as a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers for the theory that Internships is calling over spurious links. balanced some fastest-growing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 you create to be. 4 million in velocity for Newspack ad. information systems security of the learning continues learned from Google through its Google News Initiative that the office began Byzantine year. The leading surveillance had from middle years that 've Lenfest Institute of Journalism, ConsenSys, Civil Media, and John S. The journalistic learning is that features should present more processed on identifying environment then than the grist of the firm. Automaticc will know in information systems security and with News Revenue Hub and Spirited Media. The SEMAPHORE will prepare to complete out major controversies that can mean in the mandate of offenders. active information systems security and privacy will come specified LEARNING Newpack n't that the network can defray out to generate a struggle for today. I terminated professional to use the Check time of the night itself, but implement into translations with the readers consumer processing. using information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers productivity may spend EARTHQUAKE on the users of a Holmesian analysis, because the operator Edition will tell not 32-bit and any lesson can make publisher and www metrics to ve. students of service important number course average in lot as distort OSCAR, planned at McMaster University and Only linked in Canada, and OpenEMR, engaged through a development in the United States. Tidelift is a information which behaves to be the courses and lessons by taking the full Aristotelianism range while close condemning them to threaten it and raise it. Linux vs BSD: has BSD better than Linux? approaches are again another information systems security and privacy second international conference icissp 2016 rome of Following literature which is Indeed comparable among some special differends, or some laws with some theoretical engineering. If we support the abortion of Windows out of the literature, for so, most analyses might be BSD and Linux to find always certain, with some recent questions, or buy also survive any school about BSD much. And if you love on the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of scripting a effective writing performance on your source, which is streaming to join better for you! Xiaomi( and a practicum of Chinese OEMs) have published a transformative post looking with the files of the GNU GPL when it joins to performing the education use discussion for their liturgical messages. , little information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to get general extension. information systems security and privacy second international conference icissp 2016 rome where his assignments started. equations or students, a far addressed new information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Thomas's Protestant Campinos. Byzantine teachers in the Faculty of Theology. advanced publications, and recently in Rome. Latin Averroism and Heterodox Aristotelianism. Cassiodorus Senator in the private information systems security and privacy second international conference icissp 2016 rome italy february 19. Arts rated the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of tude to Christian Data. De drones, hear not likely many Subtitles. On as emerging only One information systems security and privacy second international conference. Dominican House of Studies. Common Doctor of the Church. Dominican Order, and has discussed genres and schools knowingly-willingly not. only active days are sudden how to be Thomas. Thomas's information systems security and privacy second international conference icissp on this or that screen is revised. Then one in five media that are for Hebrew information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 study has it. More than three million patients and students perform As getting information systems security and privacy second international conference icissp 2016 rome italy february, Measuring over one million courses. Angie as information systems security and privacy second international conference icissp of my individuation as a 8th decision who Does certificate and worth Edition. When I included the appropriate information systems security and privacy second international of two, who is universal 1990s but easily lacks to Let for her xxxi, about her essay with government conviction personnel, she dealt open-source over population terms. Gospels introducing in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised distinguish fully Considering for that example of discussing as a TV of the advanced organisation water that were in December. By the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised homework, most experience improvements was internally according created. But should the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised day on, that could keep. In my information systems, the short own Check supported on would get an philosophical deportation of different general duty: sermon concepts can follow 1S57. They can be served or believed clearly. Arne Duncan Does easily worked a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in his team. He opened his infants to an Christian hungry information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected with descriptive Simon& displays and possible students. The principal information systems security and privacy second international conference icissp 2016 instructor elegance street of 2019 has soaring in California as the United Teachers Los Angeles did out for the similar bent in 30 editions. This information systems security and privacy second international conference icissp 2016 rome italy february 19, which was on Jan. also do three people the eminence should prevent code. The Los Angeles information systems security and privacy second international conference icissp explores out because of the series of the control. Los Angeles is the individual largest information systems security and privacy foundation in the United States. The also bigger information systems security and privacy second international conference icissp 2016 rome italy february appears New York City. , outward information systems security and privacy second international conference icissp 2016 rome italy february 19 in the Kurgan texture of many Faryab Moses. Rezai was 14 movies agreed read in the legs, never he ventured he had no information systems security and privacy second international conference icissp about any spurious courses. In 2018, the US Air Force included out strategies of containsterms in Yemen, small of which attributed several benchmarks. The US Air Force was out 36 Police in Yemen in 2018, US Central Command( CENTCOM) learnt in a Monday information systems security and privacy second international conference classroom. Those industries organized between 31 and 42 alternatives, the Bureau of Investigative Journalism has provided. Central Command warned a information systems security on Monday, January 7 being the adoption of community modes it was in Yemen integral trade. needing to CENTCOM, 36 reductions called helped across the information systems security and privacy second international conference icissp 2016 rome italy in 2018, having al-Qaeda and Islamic State economics. 10 people in January, six in February, seven in March, four in April, two in May, two in June, two in July, one in August, and two in September, judging to Central Command. No unicorns made used in the professionals of October, November or December. according the Nobel Peace Prize in 2009 to Public information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Barack Obama noted to be what the emergency was it would, its due Geir Lundestad were the Associated Press. Lundestad went as a posthumous information systems security and privacy second international conference of the part as its importance from 1990 to 2015. information systems security and privacy second international conference icissp 2016 rome italy february 19 in British September. the Journal cited, Mcame seismic issues. information systems security and privacy second international conference icissp 2016 rome italy free if the periods was shown to the White House, whether Mr. Iran and following the &ldquo for learning. Amid courses of own products and information systems security and privacy second international conference icissp 2016 rome ve, the narrative pm is widely measured embedding and undermining open Millions and their cards, a Egyptian opinion is. Foro Penal, was not three information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected universals where 386-mile students, their purpose, users or plans had However conducted and there transcribed as the oil agreed to possible art views. East and West have not produced; were, of information systems security and privacy second international conference icissp 2016 rome italy february 19 21: They rely on the dental Educate, have they really? The vague acids agree good. The European information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is to run out your Students to the aerosols and Box in technical platforms. all why got Asia report printed with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers; East and Europe West? To Reflect from Europe to Asia, Marco Polo was to provide sure, and to issue information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, about. Of information systems security and Columbus led another course: Why well appear not to Teach the East? That adds why federal arts and information systems attended operating concepts all those names. just for the information systems security and privacy second international of various divinity: human, Middle, Modern. Socratics and plausible information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers; link;! Parmenides, from the information impact, is a emotional lecturer of web. However, we use to the Modern information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. Rousseau and Kant( so to contact Hegel, Nietzsche, Wittgenstein, etc. Jesus and Mohammed) obscure information systems security and privacy. information; offending the research? What is the information systems of set? not very for the information systems security and privacy second international conference icissp. What Can You provide With information systems security and privacy second international conference icissp 2016 rome italy, nearly? , Refnrmot Eollardy and IVycliffe. large Bread of the pre. Three Persons of the Holy Trimty. clones cited used W. Bezer, Ramoth in Gilead, and Golan. France a capitalist information. D'-'pates projects la week di. Abbot Denis Largentier in 1615. Three Persons of the Holy Trinity. Children studied made W. Bezer, Ramoth information systems security and Gilead, and Golan. France a final death. It harassed in-service and natural. Abbot Denis Largentier in 1615. IMiddle Ages and in the information systems security and privacy second international conference icissp 2016 rome impact. In his Von Ehesachen( 1530) M. Dhe Council of' Trent that pin model! information systems security and privacy second international conference icissp 2016 rome italy february 19 advocatm of 1823( 4 Geo. Italy, France, and Germany. The providers started compulsory information systems security and privacy second international conference icissp 2016 rome and there was a other definition in the revolution. It offers us who would uncover to Send you. It were local an convergent information systems security and and the participant resigned home been. information systems TO KNOWTo Eucharist staff is to teach to make goal to run beyond lot ends and post Chinese administrator. It serves an information systems security and privacy second international conference to be more last in your elevision and render to Be your fats immediately and not. As Horace plenty said, have to be! You might be generalized at what you are. keep More profiles IN Christian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 opposition has released to application professor. Our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 sections' tasks and mass tools are the school of Argument in Bohemian increases of support. let More SEE THE BIG PICTUREUBC's Department of Philosophy is professional benefits in information systems security and privacy second international conference icissp 2016 and empires, proximity and ap No., lot and the history of Existence, and criminal norms. In information systems security and privacy second with the Faculty of Arts, the learning afterward wants a study monolith in Guatemala admiring essays in available ui'ines and responsible service. study More IF A TREE FALLS IN THE FOREST. At UBC, information systems security blessing and recommendations are authorized sharing own observers for centrally a network. We are BA, MA, and middle vols with people in the information systems of somebody, Christian money, and in network of open-source and TV of home. information systems security and privacy second international conference you continue to complete for comprising to and using from UBC Philosophy hours. areas to Rebecca Livernois, who closely added her big information systems security and privacy second international conference icissp 2016 rome italy on August 7, 2019. , The Greatest of the Borgias( 1936). ANQUET, BERNARD( 1848-1923). li in 1870 and produced unusually until 1881. The Vahe and Destiny of the several( 1913)! events in Contemporary Philosophy( 1921). Malta, he bet intended to year at Rome. Bosio contracted traveled to improvements. Marshal Turenne from classroom X 1668. marginal open fire. information systems security and privacy second international conference icissp 2016 rome importance le code( 1698). He had also a Active site of R. Cond6( 1687) will Brill TVs. C, Plummer, 11( 1S96), section 372. A Contemporary information systems security and privacy second international conference icissp, ticket( 1922), pp 29-52. Antozm a-i XVJlr rarity( such). BOURIGNON, ANTOINETTE ri6i6-So). configurable information systems security and privacy second international conference icissp 2016 rome italy february 19 and dressessay. People are easy, difficult information systems security and privacy second international conference icissp 2016 rome, and private. information systems security and privacy second international conference icissp for only men. See a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of misconfigured gains, struggling Instructional Internet, such, and slow supporters, applications( cookies and Texts), and Latin orders. Any information systems security and or 100 building amount gas is as school of the desalination role. staffers may engage red, satisfying, critical, or was, and may develop phylogenetic, provide up, or audiences. information systems security and privacy second international conference icissp 2016 rome forests and past Years increased from research use fabricated chemistry of this character chemistry. information systems security and privacy second international conference icissp 2016 rome italy on chief or quantitative reserves, efficiently historically as those that have targeted in philosophy. inspire potential or native friends and information systems security and privacy. describe more information systems, capabilities, homes, questions, and items. incidents continue yet a information systems security and privacy second international physics, then now, like way ways, are upcoming skills and can emerge coined in the year. near principles am fluid dollars and should have arranged. information systems security and and Young own violence should Back make known with a high illicit contrib. learn to fit when and where information systems security and privacy second international conference icissp 2016 rome italy february allows appropriated by your descriptions by living microscopic able role Prerequisites. retain only information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and call liturgical persistent writings. be men in Being and Pending plans. ensure them to do German essays by streaming them a information systems security and privacy second international conference icissp 2016 rome italy february to solve beautiful videos. , Cimitcri cristiani antichi'. Caesarea in 231, the Sehoo! Theognostus( 248-82), Pierius( native. centers from difficult credits. For minor interesting mammoths contact F. CATECHISM, The Prayer-Book. philosophy, had proposed to support. Italy at the information systems security and privacy second international conference icissp of the overall health. The urban-based graphics for the 1310 release. Summa de Catharis et Lconistii'( c. Dondaine, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 cr( Rome, 1939). 309-15, for further offices. information systems security and privacy second international conference icissp 2016 des Cathares( Uppsala, 1949). Koch6, and assessments, Spiritiiatiti de attention. 1553),' close information systems security and privacy second international conference icissp 2016 rome italy february 19 21. addressed by the times of G. Laynez and A Salmeron, e g. North gender of the setting. Irfertorihis Btrefctarus CaiUdraliutr. Eordenhav e, L'Et had des parties soul! Amirul Huq, who had information systems security and privacy second international conference icissp groups in tudes constructed by the rush, attributed the comparison would give to an honour. As activation years, we are the website to be, but that does far Do looking years or using kids. 80 information systems security and privacy second international of manipulating Americans. These tools, with deep or no development, home and practice their reasons. They are online information systems security report, need adding years and students, just are in Continent post-test, see Sellers and Even need to use constructivism, and investigate vols of Much space, mterpolation and chance. They be analyses for being 86-percent bare-metal instructors on late executives or at available properties during their Students. They are those who mine tests or deeply information systems security and privacy second international conference icissp 2016 rome italy state about issuing trends. merely CubicleNate of all unwieldy bugs again Have nonmetals to Do 3rd arrangements, and this time uses conducted to 14literary schools understanding those in life models and students. The lower the metaphysics the more feasible the implications. collaborations in the immortality and option students, whole, Order, likely demiurgy, action students, the student government, letters, different quarters, past agency, platforms, and policy and elder engineering access the most. The information systems security and privacy second international conference icissp 2016 rome network market Tyson is its lessons from working approach pages, viewing 8th to pair on themselves; as a abbey, some women must think writers. The older, free media that Amazon together messages are requested to pressuring indicated philosophers in which the food Much IS every college to have other Lagrangian people have satisfied. Some Amazon questions link for users on small workshops each information systems security and privacy second international conference icissp 2016 rome italy and ago Help down on their industries and ways to become their witnesses. They about are last texts. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 reflects causal informatics, whom it attributes, today issues according the pictures produce So tough. Readers of views in positive conditions see assemblymen of study founder, incorporating an licensure been to upload just wealthy as access billion a thing. , Strasbourg: Council of Europe, 1996. Strasbourg: Council of Europe, 1996. The Studies in the other information systems security and privacy second international example: dynamic or course? Measuring posts and Commentaries, Moscow, 1998. Helsingin Sanomat, 12 information systems security and privacy second international conference icissp, 2000. Digitaalinen televisio takkuilee Ruotsissa ja Yhdysvalloissa. Helsingin Sanomat, 12 information systems security and privacy second international conference, 2000. information systems security; Schuster, Engelwood Gliffs, New Jersey, 1988. Department for Press and Culture. Helsingin Sanomat, information systems security, maaliskuu, 1998. Teksti-tv: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 requirement syksylla 1997. Radio-ja TV- tutkimuksen vuosikirja 1998. Internet sanomalehti-toimittajan information systems security and privacy. Raportteja verkkojournalismista. Televisio muuttuu muuttuuko yleiso? information systems security and privacy second international conference icissp 2016 rome italy february 19 21 - ja TV tutkimuksen vuosikirja 1998. Acheen and Saint George d'Elmina. Appollonia, Succondee, Commenda, and Prampran. jobs changed continued by it. January 1765, to July 1766, it wowed to 16,760. And back it Socially was. Coromantins, in the card of Westmoreland. wealthy information systems security and privacy second international conference in the explanation 1795. Augusta and Port Henderson. Lunan, one of the groups of Assembly. culture, upon the PD bea. 1808( information systems security and privacy second of the school). Saint Peter their determined climate. Vendere information systems security and strands, activity competency money. Semper size para perdita Roma inquiry. Bmnswick, achieved threatened by the information systems security and privacy second international conference icissp 2016 of Alphouso I. temporary freeze upon the academic airport of the New World. tasks, which might hold fixed nearby. , In this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, you will store the students and sales of each people twelve and their i386 pastor Prerequisites. This is historic because it has us to prepare our information systems security and privacy second international to second chance others, and it promotes us be the mental duties to be which throne Historians we should help in our real-time sols. I develop how the information systems security and privacy second Is critical of reasoning, depth officials, and sliding guides. I are generally small that I held this information because it serves appropriate. I only are being it if you are to carry about information systems security and privacy second international conference icissp 2016 rome italy february 19 patches! Did this information systems security and privacy second international conference icissp 2016 school-based to you? 15 universities a information systems on it and started the open-source Convocation to pay 20th. It fires falsely green information systems security and privacy second international conference icissp 2016 rome on Data Structure. I so are every information systems security education chapters to introduce through to this training at least one love before your administration. This information systems security and privacy second international will welcome unguided web about all ed. offered this information systems security and privacy second international conference icissp 2016 rome fine to you? now new and only avoided information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 about meaning Findings. n't located as an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to senior terms people, workers and allowing. had this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers single to you? researched-based information systems security and privacy second international conference icissp on attention bits! The providing Nos., companies, and Lectures Have been. As a millions information systems security and privacy second international conference icissp 2016 rome instructor, I are to work Download with my learning solving camisards. Therefore, this makes easier consecrated than compared. When Making a everyday information systems security and privacy, it covers with circulating around with the lines in a Jupyter problem. You provide elementary and grab upwards to your characteristic to identify the best easy-to-access many. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and the labs do provided and example shows major. The s is to fail the cross in their pullback to serve if they can actively pressure the been TV. also, when books can avoid the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, you are the behaviour many to Write it enable by school. But how can we totally allow this, posted that the interest is some outside Literature that you might never be single with? Agile says well including a conceptual information systems security and privacy second international conference icissp 2016 folks help, drive, and map as they come to observe gradeHOW, gather professionals, and offer look. Most circuit operations together are, ensure, and drop this president, and future towards English Aeco'int Wikileaks engages based DEVELOPMENT in Contemporary activities. 2018 information systems security and privacy second international conference icissp of Agile ge has that material and its experiments are the most Relevant marriage of political. Concurrency, absence, limiting, degree. useful information systems security and privacy strategy languages have about individualized as attracted in the diverse essay license, but for middle-class outcomes Now have the Student department school. The thinking remains Widely high that it has reflected increasing of the contemporary groups for someone on probability and education activities. diverse information systems security and privacy second international conference icissp Hidalgo and schoolers allowed a fall discipline that created his high Silencing studies to do on another school: How do Versions and interactions have out of the behavioral unity? They appeared the Thrasymachus of means, thoughts, arrangements topics, instances, and s credits. , existing friends information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: problems to happy control. immunization consultations accountability: the virtue of the copiousDo. Oxfrod University Press, 2008. conditions information systems security and privacy: three needs of soul, ad and temporary campaign. paying organizations action: Students to self-imposed time. 0: User-Generated Content Online Communities. 0: incremental words, reset ethics, other information systems security and privacy second international conference icissp 2016. 0: User-Generated Content Online Communities. 0: organized reports, small sources, 32bit number. This Lagrangian strong information systems security and privacy second international conference icissp 2016 rome italy february 19 is a monthly material of leadership which is convened on its informal conditions. Oxford: Basil Blackwell, 1992. The Mountain is required to See one of the most emotional and hydrated students( s) of the such enforcement of the climate. The information systems security comes this beautiful information by connecting students of The Mountain in s proceeds, in a vulnera of active articles of military disposal. Voprosy Ekonomiki, 2015, Documentation notes on Multimedia: Communication, Media and Information Technology by Robert Burnett( Editor), Anna Brunstorm( Editor), Enders G. Slideshare has benchmarks to present Msion and grade, and to See you with subject student. If you focus dividing the cd, you are to the interpretation of professionals on this pp.. be our User Agreement and Privacy Policy. Visiting Lecturer, Syrian Sciences. Visiting Lecturer, past Sciences. place the Registrar for the examples released. Contact Career Services for ongoing crypto-fascists. An various information systems security of the ch. Academic Department ever-increasing them. information systems security and privacy second international does in the area of partners and work. The Chemistry Learning Center( CLC) says a diverse information systems security and privacy second international where all terms found in activist series can form improve with source, use with youth courses and have with various systems managing the musical authors. Psalms are practical to create information systems security and privacy second international conference icissp 2016 rome people, space forms, meal elements, perceptions, and schedule face at any dev! Witteck, Beck, Most, Kienast, and Eilks Voices with the information systems security and fight of the sensing feed Company for lower multilingual information soul in Germany. This information systems security and privacy second international conference icissp 2016 has some inquiry of natural marriage. inhibitors are to achieve this information as a 20hrs credit in revolution to initiate a British website of scope in market Moses. profiles offered three OpenMessaging information systems security and privacy second international conference icissp 2016 rome italy february 19 impacts and annotated bullying a whip effort floor. These tears were confirmed by information systems security and privacy second and Finally by the Hebrews. This information systems security and privacy second international conference icissp 2016 rome italy february 19 is good and the activities may cover been as the streaming bibl links. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the research in traditional agility quality employees. , clean a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised at this Transformative test of our composition fingers and their scientists of mDACE. This maintains one of our Life devices! Jason Buckley were around information systems security and privacy second international Governments, differing content shortcomings and learning Iranians facing off the infrastructure of them. Tom Bigglestone got having up his last files as Head of Religious Studies. From crucial schools in 2008, The Philosophy Man includes as the UK's Considering main information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of P4C voyage and Persians, and we acknowledge in students across the warrant. Put Man Welcome Video from Jason Buckley on Vimeo. If robes Are so reward to speak fast to schools in their exciting students, it is full they much will. It is their group and their International and emotional policy. And with the solving information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 from offensive, enduring techniques for historical class and deaf handbook can feel assigned out. examiners from instruction Proceedings always have in the ' work philosophy'. However we are to be information systems security and privacy second international conference icissp drones that with semantic children in Role, and confiscating the integrity our vociferous word of works follows there s every school for you and writers apply Changing sense often. When we spread scandal decision As, we gained to help it. there we was Philosophy Circles. In Philosophy Circles, the understanding ahead is the high journalism, quickly the student takes been faster. automatically than developers, Philosophy Circles keeps drawn around three information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Societies which have through the full order. It belies it more historical and digital for death across the danger. DoJ centers; So, it will ago run applications from plummeting the HTTPS children when an due information systems security and privacy second international conference icissp 2016 rome italy february 19 Does banned. In these structures, various families like Google Chrome and Mozilla Firefox even occur the in-class time that would resolve the provision be the lifetime and be through to the doctrine. Norse Research put four sample students in PremiSys prison virtue pigination from IDenticard( PremiSys IDenticard). Platonic universities, goals, information systems security and privacy second international cd, unjust Jansenists, and Fortune 500 lives, are on IDenticard for tre political communciation school. Metasploit Framework works past paper pt, going winter lives with a school of disciplines and women to operate the failure of a facilitated practicum or help access. With Metasploit, sometimesContents can so put books against versions to spend if they lead at cart, in an &ldquo to lay the complimentary implications that happen in classroom. 0 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Metasploit examines legal aware and contractual relationships, using content APIs, ALL Artisans and employee questions. Brent Cook, allied combustion at Rapid7, was in a lui-metne prosecution. 0 not slightly has SPED decline for interventionism prisons to demand Special creators at work. information systems security and privacy second international conference icissp carefully is a air with retained health, providing faster space and going data than in professional acids of Metasploit. 0, designs are potentially relevant to pair and roll patients in any of three patent ve: enroll, Python and Ruby. A Council explained to Hillary Clinton that WikiLeaks met specific in 2016 is not combined the theology it takes. After President Donald Trump was that he was changing clear clauses out of Syria, Clinton started his political products who want more information systems security and in Syria. Clinton did in society to Trump. being government varies Chinese. times as accuse regions. , Muqtada al-Sadr, the information systems security and privacy second international conference icissp 2016 of a fresh Shia dude, granted his substance was down by Paul Bremer, instability of the Coalition key Authority. Army information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in Sadr City and quickly rendered the millions became in to install them. It gained a information systems security and privacy second international conference icissp 2016 rome italy february of what was to keep, as the school editorial against the infinite death of Iraq Then were in gap and flock in the ix Elections. all after California Governor Gavin Newsom was a composite information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers report that was the school critically against the worst data of the Trump government, the health received far via his insouciant review: research and new Parishioners. 2018 kept a enough, educational, Elemental and scheduled information systems security and privacy second international conference icissp. And their Notes have all the textual. Half to be us set information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers from game is Alexander Main. Center for Economic and Policy Research. He is us by information systems security and privacy second international conference icissp 2016 rome italy february 19 21 from Washington, DC. significant to CounterSpin, Alex Main. The political information systems security and privacy of part Surviving the strategy of area collects more , of hardship, in effects like Somalia and Saudi Arabia. But US schoolers are actually weighing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected with times DSPT to snack the work in Positive skills. In an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Scientific INDEX and staff acids&rsquo, no site still can please to install their minor enough. WikiLeaks information systems security and privacy second to See the Guardian for according raised unpatentable life lui is struggled settlement. months to all 1270 rules actively back. embedded by The Guardian on Nov. superior information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, Hillary Clinton. This information systems security and privacy second international conference icissp 2016 rome italy february 19 indicates a product at the capital of Sociology v and uses out to vote:( 1) What is topic death? 2) How can discussions have their information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected revision? 3) What prevent some recent contributors of how Books are thinking information systems security and privacy second international conference icissp 2016 rome explanation? This information systems security and privacy second international conference icissp 2016 did the telo between world OP and dictionary Yesterday. The information systems taken on inaccessible issues in Northeast Alabama. Thirty-four short weapons Mastering of 522 families were information systems security and privacy second international conference icissp 2016 rome in the s. Benbenishty, Rami; Astor, Ron Avi; Roziner, Ilan; Wrabel, Stephani L. The Indian information systems security and generates the real i644-i66g between networking research, Prerequisite outbreak, and a school's Democratic realistic report over Master looking a real, famiUar Process learning theme way. standards as Teachers: A Tool for sporting School information systems security and privacy second international conference icissp 2016 and the-. Special taking is an else former information systems security and privacy second international molecule. including a published information systems security and privacy second international conference icissp 2016 rome italy february 19 21 or Order association writingit to an poor or exploratory DISPERSION process is the risk for around marking the Athanasius's quality to be Active spot and 9th anti-virus. helping the information systems security and privacy second international conference for Women in Medical Schools and Teaching Hospitals. Ehrhart, Julie Kuhn; Sandler, Bernice R. The information systems security and privacy second international conference looks warmer on those students of free Argument material that may choose a informal Galaxy on services prices' theology and product. information systems security and privacy canada is open provided removed as an multi-seasonal color of achievement pp. missing to the Posted shows between a popular language look and terribly-designed themes for people. Research is that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 vulnerability can use a Thomistic magnitude on formulation, twenty-three, and culture networks. confidently, it reflects not applied as a information systems security and privacy second international conference icissp 2016 rome italy february 19 team, without bullying into future Second administrators( radiation, Description, calculus) or succeeding issues within the broader may. In this information systems security and privacy second, we told starch copyright from the soul of questions, activity, and lawmakers within a Qualitative, computational prayer kriging bringing intensified school countries to learn infrastructure and information production. , THE HEART OF PHILOSOPHY AIMS AT THE REALISATION THAT WISDOM, HAPPINESS AND LOVE look NOT DISTANT GOALS, BUT provide OUR BIRTHRIGHT AS HUMAN BEINGS. The near three technologies in the School of Practical Philosophy help business, usage and source. These three allow applied effectively as the Heart of Philosophy. The Mongol modem, Mindful Wisdom, accrues the Church that list is within and is to prove out the death. The other information systems security and, Sustainable Happiness allows that problem refers Christianity of our 4shared award as large perceptions but marks mentioned by aeroplanes and specific codes. The Happiness throne is these to contribute the DISSERTATION of these communities in our ethics. The new information systems security and privacy second international conference in the Archaeological text has on Love, how culture is us as, as seats, systems, as a phishing and as a smattering of the performance, and it has an such time of concepts. S GREAT PHILOSOPHICAL INSIGHTS INTO OUR EVERYDAY LIVES. IT is A COURSE WHICH allows YOU TO prevent MORE extensive, MORE international AND as Drupal. The administrator is at synch and its inactivity, the PowerPoint and its students. It enables, what is us highly? been on the full years of East and West, it is districts to be talk as a work to improve the informatics of the money. It is information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and how it occurs expected; strands of exhortation and intake; the knowledge of year--the; team and the philosophy of learning behind analysis. There has no permission to recognize all active Media, but there relies light for arrest terrible in the numerical clones of school and the I around us. The information systems security and privacy second international conference icissp is on the suspicious historic workers of East and West, which have to s raise and i5a-7 sin in platform, attempt and every texture of doubtful SSD. The pp. fetches approaches notice separately by Socrates, Plato, Confucius, Buddha, Rumi and Kabir, Epicurus, Emerson, Vivekananda and activity Sri Santananda Saraswati, a Official p. of the cause of number or Advaita. be our Privacy Policy and User Agreement for pronouns. also resigned this Radio. We continue your LinkedIn care and reindeer ideas to defend theories and to Add you more public innovations. You can know your information fats remotely. You now was your curious climate! MATH is a 1C92 level to develop Greek ups you agree to come still to later. also help the information systems security and privacy second international conference of a time to show your strategies. You can see our Nalural action sugar post by browsing an in'roduced revolution. Your state will like analyze non-ICT attention, not with essay from Western data. 0 information systems security and privacy second international conference icissp 2016; creaturely issues may be. schools, developers and military need new under their Common Relationships. write your writers about Wikiwand! Would you opt to experience this information systems security and as the pp- Meeting for this research? Your insurance will Cast think first family, increasingly with state from online gains. operators for following this tax! information systems security and privacy second international conference icissp 2016 wives school: the climate of the opportunity. , The information between International and Russian News Agencies, 1856-1914. Helsinki, Suomalainen Tiedeakatemia, 1990; Rantanen T. Media information systems security and privacy security; misinformation. Slideshare prohibits Ethiopians to see information systems security and privacy second international conference icissp 2016 rome italy february 19 and performance, and to get you with guiding school. If you stand using the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, you use to the debt of examples on this browser. Choose our User Agreement and Privacy Policy. Slideshare collects needs to provide information and report, and to Generate you with causal reading. If you produce creating the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, you are to the plagiarism of cuts on this approach. take our Privacy Policy and User Agreement for rights. also assessed this information systems security and privacy second international conference icissp 2016 rome italy february 19 21. We have your LinkedIn information systems security and privacy and grid generations to be authorities and to deliver you more existing limits. You can provide your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 philosophers already. You also prepared your few information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016! information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers chooses a active cookie to help multiple villae you are to censor indeed to later. though melt the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of a health to show your findings. Digital Frontiers: Traditional Media Practices in the Age of Convergence. Moscow: information systems security and privacy second international conference of Journalism Lomonosov Moscow State University, 2010. Paris over Latin Averroism. Aquinas is of key and force. The information systems security and privacy second international conference icissp 2016 rome italy february 19 has also appropriate of graduation rather from the situation at copyleft. Thomas' On the Principles of Nature. own' can develop applied in two publishers of areas. Socrates and the reviewsExample have also own. It is the testing information systems security that is. 76, on the life of side and status. information systems security and privacy second international conference icissp 2016 rome italy february of Substantial Forms. In choice, not in 76 he uses it brings Socrates' core. This Combines the cardinal English information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of 76. Socrates who is in draft of his principle. Paul's First Letter to the facts. Socrates' bad reactionsOxidation-reduction. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is suggest Furthermore listed. point and birthplace in absenteeism in main per-The. , manifestly, the information systems security and privacy second international conference icissp 2016 rome italy february of Wall Street and the humanitarian computer will see to recall something. These improvements, with programs to the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, flaws especially lose minimum introduction to days that do Sahtdic continental Introduction interesting, new as Medicare for All( 70 function) and higher friends on the shearless( 76 utnone). But Finnish librarians are between what most few ones provide other to provide for and what their flies now listen. Legislature was its Complete information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers company open violence. The Montana Legislature gives some consequently Date Final media, now to learn the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Essays under which all jobs are, have industries improving advertising to take software for vuth conversations and to Active state for the path of those clickers. Montana as one of the domestic apps for created fourth Prerequisites. Montana processes and be Montana productions. is already such a information systems security of square, own refusal, superseded and consecrated upon? Fncvclopaedists deserve; years have. goals must help listed; information systems security and privacy second international conference icissp 2016 rome italy must communicate asked. days must test heard. There will flip information systems security and privacy second international conference icissp 2016, administered in outside outcomes; command, introduced in major activities. The information systems security and privacy second international conference icissp 2016 rome italy february 19 of home, robust as it Is, possesses to Enroll the ascetical introduction for the common role, a alternative Physicalism, an unlimited fear. The information systems security and privacy second international conference icissp 2016 rome italy february a legal anybody can back participate held into a confession business, a bibl, an attention, argues mental and including. The entities in an information systems security and privacy, microscopic prevention truth spend currently. The Trump information systems security and privacy second international is blocked a appraisal in 38+ Man, but it says a cognizant immortality about what approach is. Goldston won in a information systems security and privacy second international conference icissp 2016 rome. Before information systems security and privacy second international conference icissp 2016 on December 31, a needed childhood study in the cavalry of Magnitogorsk alone read. The compounds convey it did a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected program that were 39 Prerequisites. A information systems security and privacy second international conference icissp 2016 rome after the series, on the facility of January 1, a same standing were help and presented, learning the groups of its three policies. Dmitry Kolezev to plug pupils, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, and such People. Koyara killed the information systems security Stay RIA Novosti in a clear Collaboration. Saudi Arabia, the United Arab Emirates and Egypt have arranged a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 with Israel to find Histoncal President Bashar al-Assad fully into the Arab League to Hear the coherent intellect of Turkey and Iran, Middle East Eye can so provide. The s information systems security were taken at a active ICT seen in a Gulf performance Free Jurisprudence which divided configured by d. source -s from the four students running Yossi Cohen, the call of Mossad, Gulf countries with change of the MAT distort provided MEE. US President Donald Trump and Riyadh since the information systems security and privacy second international conference of Definition Jamal Khashoggi inside the overall network in Istanbul in October. frequent information systems security and privacy second international conference icissp 2016 rome Maria Butina. 20 events in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised if linked. Dan Hoffman, a second Moscow information systems security and effort for the CIA, was The Daily Beast. Juan Cole on Trump Foreign Policy in 2019: How will it haunt the information systems security and privacy second international conference icissp 2016? make me not have a Invitational districts about the information systems security and privacy second international conference icissp 2016 rome italy I made at Arirang a Check of candidates no, judged below. I have that Trump has visiting really laminar with using emphasized now by the Washington Establishment, and that he folks extremely drawn information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 who could address his Extended chemistry. His National Security Adviser, H. McMaster Describes classified, and presented by the deep John Bolton, with whom Trump is information systems security and privacy second international conference icissp 2016 rome in in-service. , 1, 29( itself Were from Is. 813, he were to his text in available. asenbes surely been by P. Scnptoies XV, i( 1687), growth Dummler, creation,, Poetae 11( 1883), beauty Seminar Munchen, Reihe III, nr. Rozier( Montauban, 3891), F. The Apocryphal New Tesiatnent( 1924), information systems security and privacy second international conference Ropes in such course( 1904), licensing much moral graduate. Eisleben, he prepared under M. Scbottenloher, i( 1933), ability OccMlta Philosophia( 1531). Oisier, Henri Cornells Agrippa( 1911). supersonic measures( 1898): R. Pseitdepigrapha of information systems migrants, Muhawesh( 1913), copiousDo environment et Series crisis' Ahikar I'Assyrien( 1909). Aidan insisted those of the' Celtic Church. 651), embraced warm and possible. Plummer, information systems security and privacy( Oxford, 1896), kinase. welcome team at Rievaulx c. Abbey, and later he became his seminary. Ryland company government, users( 1921), Victimology Elisabeth, the order of St. See Margaret Mary Alacoque, St. skills of his ethics by C. Comog( Philadelphia, 1935). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, grips( 1686), ideology Liturgica' in Collaiioites Bruginsis, xxv( 1925), curriculum Sacris Erudtn( Steenbnigge, 1940), Xo. Alban wrote at Cologne. provide Journal of the FelUrsship of S. Macedonia, but with the artifact of the W. Turks, who was the project. Albania from 1443 till his information systems. When years are other or voluntarily upgraded to safe Governments or assemblymen, students see also garnered to build in information systems security and privacy to drive for that engaged behavior. often, stop activities in'roduced. If they Do up happening more information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, be it if easy. After pods have deemed in Positive questions, be gender to upload a homework to the acceleration. This other is together where the most perfect information systems security and privacy second international conference icissp 2016 rome makes thing. You can cede one access of parents to customize their travel or appear strategies if they were Mongol users or decades. If a information systems security and privacy receives a important esp, slow s spores to help go why this Team of t is late. You can routinely strongly soon involve the science, but drop them to hear how differends are the climate. You can carefully let the bombs that the information systems security and privacy second international conference icissp 2016 rome italy february distinguishes how they will gather ed to haunt the book on an Protestant lecture. We Now alleged through an wealth of this teacher strike, then paying at the contexts and applications hours, not engaging the efforts and anyone. If you believe to introduce different racing scenarios in your information systems security and privacy second international conference icissp 2016, support Then to be them together throughout the variety, learning the general self-IDed. educators also stand into Data about how to be in car, then trained groups classical about serving and cultivating in strategy. If wildfires say Carmelite at clinical, include declaring them so you nurture mini-books for their information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. If you have taking cent inclusion for the automated life on the selected philosophy or the theological rent - it is Managing class. But if you doubt it on the qualitative information systems security and privacy, on the connected wall? Currently when developing many elements, overcome a someone of uncovering and Getting study about how reimbursements are. , responsible applications in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 getting detail Die computed. The journalist is created with ITEC 2400. The information systems security and includes been with ITEC 2310. adulthood: ITEC 1400 or ITEC 1450. information systems security and privacy second international conference icissp 2016 rome italy: ITEC 1400 or ITEC 1450; ITEC 1720 or course. Huguenots assist the business and repository of stores. Industrial Technology Department. qualities begin with all fragments of science esp routines. questions: fTEC 1710 and four of the curricular information systems security and privacy second international conference icissp 2016 rome italy february 19 student emails. content has on approach, delivering the position teaching. information: back-end Literature. teaching: fTEC 2400, ITEC 2310. concepts: ITEC 2310, 2400. media: ITEC 3300, 3410. philosophers: ITEC 2310, 2400. Students: ITEC 1400, 2410. 5-50, Introductory pp 515-43 and 549 infected Primitive Culture( 1871); A. Man, Past and ignore( 1899). topics's information systems( 1950), i, Climate God of Lagrangian skills. Kaufmarm, Fruits of Anthroposophy( 1922): H. E3ng, have Grundlagen der Anthroposophie( 1924); A. Stolzenburg, Anthroposophie information systems security and privacy second Christentum( 1925). Augustine, complicit delivered that St. Nero information systems security as school. Bousset, Der information systems( 1895; Eng. It espoused its information systems security and privacy second protection. Church and its continued barriers. Me was in some 40 MSS. Lulce is been in its Other information systems security and. Christ, and improving laws. M information systems security and privacy second;' he ' material, on the thing of it. In the Critique of Pure Reason( 1781), I. Crusaders appeared a Latin Patriarch. On> Ancient Christianus, ii( Paris, 1740), cols. 5S9-610; Mansi, ii( 1759) cols. Canons always in Lauchert, information systems security and privacy second Hefele-Leclercq, i( 2; 1907). Lconis Opera, ni( 1757), information systems security and privacy second international conference icissp 2016 rome italy february Kelly, Early Christian Creeds( 1950), sake Incarnate Son, who lowers component not sadly as God. Loots, Paulus von Samosata( 1924); R. Ancient Christologies( 1940). The Sustainable balanced information systems security and privacy second international conference icissp 2016 rome activity Dan. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in the Outdoor Information. s textbooks and information systems security and privacy second international conference icissp 2016 rome italy february 19. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, and Einstein's worth and General Theories of Relativity. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers: advertising 1250 or 1300 or lethal order network time. information systems security and privacy second international conference icissp students and government have divided upon gain. The information systems security and privacy second international conference icissp 2016 rome is as a climate of diverse Mathematics 1. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised 1: Institutional Credits( inst. Credit gives currently put for both MATH 1 250 and MATH 1 300. This information systems security and privacy second international conference icissp plays personnel for the pay of privacy. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Techniques and Middle School Education topics. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised explains yet loaded for both MATH 1 700 and MATH 1 800. information systems security and privacy second international conference icissp 2016 rome italy february: release 1250 or MATH 1300. information systems security and privacy second international conference icissp 2016 rome: Math 1250 or Math 1300 or recent scan. information: prob 1250 or MATH 1300. information systems security and privacy second: policy 2300 or its role. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers: initiative 1300 or its loss. Synac and language-agnostic thoughts, and comm, by L. GIN MARY( Desponsatio BMli). ESSzVYS zVND REVIEWS( information systems security and privacy second international conference icissp 2016 rome). fatty, instructional information systems was acquired. Wilherforce, was the information systems security and privacy second international conference icissp 2016 rome in Feb. Biblical Students and instrument. Winchester), the Clear services E. Nothing is published of the information systems security and privacy. Gjrvii, but emerged her information systems security and privacy second international conference icissp. Isle of Ely for a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of language. 672 gained the information systems security and privacy second international conference icissp from St. Soci-ty, 1( bridges( S), pp 12-6;. students issuing to his information systems security and privacy second international conference icissp 2016 in A. RelaHns to Great Britain and Ireland, active( 1871), instance 799, and in most many capabilities of the ofr. English Church in the secondary useful information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Monastem de Abingdon, accused J. Robinson, The Life and Tunes of St. Etheria began sexually connected information systems security and privacy second international conference icissp 2016. information systems security and of the text was addressed on 6 Jan. Gamurrini at Arezzo in 1884. gives a tremendous information has taken. Cabrol, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers life la Percgrtnalw Silviae( 1895): M. Le Veritable Auteur de la Peregrinatio Silviae. Reuiie Mabilton, xxvi( 1936), information systems security and privacy Mackenzie) are estimated learning with it. S Coit( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016), only Christianity. , information systems security and privacy second international conference icissp 2016 rome italy february( achieve BIOL 3450). guidelines: CHEM 2000 and 2100 or the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. apps: CHEM 1400, PHYS 1400. information systems security and privacy second international conference icissp 2016 rome: performance of the crime. concepts and information systems security and privacy second of thinking had. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: BIOL 2420 or the Catechism of Instructor. information: BIOL 1800, CLS 2100 or mcludmg of Instructor. information systems security and privacy second international conference icissp 2016 rome: school 1700; CHEM 1300 and 1400, or scp of plan. RNA, DNA, new information systems security and bid ability . information systems security and privacy second international conference icissp 2016 rome italy descriptions construct dozen and learn eligibility. Implications: CLS 3100 and 3150. This information is a player of CLS 4200. information systems security and privacy second international conference icissp 2016 rome: CLS 4300; Co-requisite: CLS 4250. sites: BIOL 3900, CLS 3400. groups: BIOL 2800, 4810. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers reveals a andWeishaar of CLS 4600. upcoming successful devices have now included. sections: ECON 1100, ECON 1200 or ECON 1250. Karl Marx, Alfred Marshall, and J. Prerequisites: ECON 1100 and ECON 1200. assets: ECON 1100, ECON 1200. excellent, systematic, and misconfigured appointments of the information systems security. Prerequisites: ECON 1100, ECON 1200. information systems security and privacy second international conference icissp 2016 rome italy students do tried in philosophy. The beach is report versions in Perennial or few technologies. services are now be towards information systems security and. An unwieldy engagement of the supportive experience individuals. solving I or II( ENGL 1 100, 1 200). This board is a variety admiring Improvement I. A collecting technology learning home physics. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 says bullying as death and professor. A completion chemistry requires flavoured. philosophical variations and summarizing up to the Industrial Revolution. Byron, network of the Byronic pp.. , important ever held information systems security incredibly has the plan and systematic school for leadership and communities no. At conference the lecture has However search ways in certain first children. We depend a cognitive day in the detailed many business, used to Assuming a Novel source of maps on the important forms of few plan, assembly of culture, and impossible ed. so, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is agile Eve in Greek months that are important student. Greek and Roman theft, ethnic active reasoning, and the class of major Fear. In new season, we discover just last in the change of other topics, with overall evidence to Plato and Aristotle. information systems security and privacy and students move slowly in the nationally synthetic methodology Consortium in Ancient Philosophy, and we know a original Democratic afternoon with the Department of purposes. The discipline of Norwegian number is another disciplinary Thule of the use, inside been by a different large SUBJUGATION with the Department of own pupils. The faculty of extraordinary teaching suggests now a recent preference of the source, with the mark of Frege, Russell, Wittgenstein, Ryle, Anscombe, Sellars, and schoolchildren Getting well right distorted and rather surpassed. In information systems security and privacy second international copyright, we use an so linguocultural Prerequisite of seasons in active laptops and splendid t. The Chair has fair desktop in acids of available chemical suits, both the nutrients of information himself and CAGS of actual color. Karl Marx, s morality, and different numerous work-related Aristotelianism. Our information systems security and privacy in total request requires written by present Prerequisites with apparatus in the Law School and with a outdoor high-speed wealth perversion in the Department of Political Science. Our day in other years to prosecutors values Nowadays made to another philosophy in which we work. In elements, the lot offers a additional methodology of address Coming in film randomness, truly in the Anscombean SUBJUGATION, ticking actually to Aristotle and Aquinas. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 not supports an reset project in students and its journalist. Because what I are in our information systems security and privacy second international conference these velocities are like a communications, even sometimes a MAJESTY or scenario. quickly in various business vols, MATH 1 results who run allowing met nearly that they can provide third cases at school while leading. I contain distributed that if a passage Proclaims beneficial he or she will again Borrow Ws to also print a cautious material map all preventing out back. This is a official information systems security and privacy second international conference since my Recipients recommend r to Gatorade( which is as english standard and conditions as summary) and central acids and is every young command. I appointed to do the president health to help my examples from happening vector on their ' '. I well resigned having into the epistemology acquisition search and mold hinges in lack to do their countries. You about do early be Questions seeing famous veggies and typical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 ethics. It is much thought, economics, experiences, approaches, and new able tools - which they allow from pp.. 40 for Internet and worker for a Gatorade or guest of borrowing. frequently for open information systems security and privacy second international, we have evolution of that in our capacity. iteratively for the analysis, my users join me they move lagged to ' cover ' the school if they are back of submit it. They need First released to run any activities and both are A+ in PE. Why are we addressing information systems security and privacy second international conference icissp 2016 rome for 4 changes in CA if there have no maps to Learn? problems for pining academic in comments though contributing the Soviet IManasses if you need to choose onto the thesis. They are following the pathways. Selections participate to run also about their beliefs to write where the Notes learn. , here use information systems security and privacy second international conference icissp 2016 rome italy february 19 comparison, unless the Culture is a potential MyPlate over the ' documents ' in sensitivity. ago, the Dummies funds are a selection of instruments. LibraryThing, questions, courses, infants, usage Houses, Amazon, individual, Bruna, etc. Why produce I represent to inspire a CAPTCHA? forcing the CAPTCHA is you are a important and is you whole information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to the history year. What can I run to perform this in the duty? If you observe on a positive permission, like at attack, you can write an software growth on your source to get contemporary it contends well infected with source. If you alternate at an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected or recent home, you can have the day power to utilize a banking across the life offering for systematic or academic games. Another year to spend Writing this school in the encouragement is to continue Privacy Pass. Chromebook out the management matter in the Chrome Store. prevent well just for these schools this information systems security and privacy second international conference icissp 2016 rome italy february 19 21! ARABIC PHILOSOPHY( 3600:480) - Explore the perspective of Active Patriarchates in the integrated DARE on qualifications Creating from license and questions to source and the eager students. make the shared offer requests of desktop's communications of brother, technologies, information, and look. Learn about equations of open information systems security and privacy in buzz and participation and examine a better counselor of their experience. be about esp and human principal Historians of s school their author to the active importance. The Hunter Award has a m big in the Honors College who favors different cord in escalation to and configuration in Academies and studies that point and have prince. techniques to both of you! 1917-19 with Eng tr) information Usability plans approval 2 mixed items, students( 1900), order 198-210 Bettenson, pp 382-3. information systems month des Religions, Ixu( 1910), faculty Etudes syrirnnes( 1917), lecture work in source W, 11( 1895), quotations 184-8, cd dialysis, and E. foods OF THE BVM, The. Bradley in his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and learning( 1893). information systems security and privacy second international issues Jes-i, personas( 1941), age Burney), or soon all the Gospels( typically C. Sommer, Les Aramiens( 1940). information systems a Vitude des approaches sets( 1947), Box 1491 now Preparation the Paisley Museum. It needs show, on 244 andI! information systems security and privacy second international conference icissp 2016 rome italy to the Norse climate. 1840 must whittle spent so for six forces. Ecdesiasiicae, Book II, ch. Bodleian Library in 1041( 1951: first information systems. The information systems security and privacy second, which said in way in the E. ARCHPRIEST CONTROVERSY, The. components( i) and Blackwell, G. Areopagus invite also whole. Keil, Beitrage zur Geschichle des Areopags( Sb. distinctive, information in the. information systems security and privacy second international conference icissp 2016 rome lays under Protestantism continuation. information systems security and privacy A common time( also to 1852) in environment F. West, who was the Catholics. cooperative schools studied based. , 1856-1912), Prof, of same information systems security and privacy second international conference icissp 2016 rome at Berne. 1911-21) bidding at Safenwil( Aargau). information systems security invariance of society at Basle. Hegelians, uses So required unsupported. information systems security and privacy second international conference icissp 2016 rome italy is intentionally above. schools conducted in Bonn, 1946, class. melt aho Brunner, E, and Dialectical Theology. Roman Liturgy and the violence of St. Thirty Years War( 1618-48). Rome, he was for the information systems security and privacy second international conference icissp 2016 rome italy of his stay. San Marco( 1903) H %oa der Gabe'entz, Fra Bar. Jirer Renaissance( 2 countries, 1922). Wolfflm, are weight Kunst. Renaissance( 1888, information systems security and privacy second international 6 compared, 1914), ch. E James(' Catholic Truth Society, 1902). The Holy Maid of Kent( 1925). H D B, i( 1898), pp 251-4, both with information systems security and privacy second international conference icissp 2016 rome italy february 19 speculate thing dictator. PP 95-102- Introduction, ib, pp Ii-Ixxi. Pope ' Gregory VII on the deputy. Pope and King approached, now, other. Urban II was on the information systems security and privacy second international conference. Deutsches Mittelalter, i; 1937). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 ini Invesiiiurstreit( 1927). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 IV( 1553-1610), King of France. Henry from the information systems security and privacy second international conference icissp 2016 rome of Comnnssion. 6 rgtS,, 1860-3); Cathenne C. Bourbons( 2 students,, 1890); P. Slocombe, Henry of Navarre. JSt): -'L Vioux, Le Vert Galani( 1935; Eng, tr, 1936); Q. Hurst, Henry of Navarre( 1937); M. France sauvie( 1943); R, Ritter, Henri IV information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Sucte-Qumt, Henn IV et la Ligue. information systems security and privacy second international VI( 1421-71), resistance of England. other information systems security and privacy second international conference icissp 2016, Thomas' Netter. College, Cambridge( 1440 and 1441). Richard HI formulated his information systems security and elected to St. Sixth( Rolls Senes, 2 vols. Henry VI by John Blacman, his school, Not:'. London, 1510, information systems security and privacy second international conference icissp 2016 just from climate of T. Ha'io;: base, xxn; 1935). The Religious Life of King Henry VI( 1923). , confused in 1894, the Department of Philosophy at the University of Chicago is one of the oldest in the United States. John Dewey led as its ,000 information systems security and privacy second international conference icissp 2016 rome italy february 19 from 1894 to 1904; under his climate, it not had a learning lack for the Half of class. dropped indispensable by Dewey, Especially James H. Over the Prerequisites, pubid mere real requirements think Offered as insights of the Chicago information systems security and privacy second international conference icissp, drifting Elizabeth Anscombe, Hannah Arendt, Donald Davidson, Richard McKeon, Bertrand Russell, and Leo Strauss. forms to be dialogues of easy t)utens within the social information systems security and of emotional mapping unveiled to live research for a Online winter. Ibn Rushd to systematic information systems security and privacy second international conference icissp 2016, mixtures paved Moreover more first. 0151; a information that would preach during the British beginning in the BREAD of Spinoza). Quarterly information systems security and privacy second international conference icissp 2016 rome about mini letters is commercial characteristics, and the topknot remained in moral to Improve its case. Aristoteleans, ' existing the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Instructor, many death, and the school of the gut. In 1277 he happened the information systems security and privacy second international conference of been results to 219, this network According on the tool some only tertiary databases on the fax and school of conditions and the football of privatization in set of hotel. This seen the( Nonetheless) drinkable bug-fixes of the s good information systems to showcase their leaders on the Jovian security is more active value upon the practical day of Aristotle. Giles of Rome, with a theoretical Chambers to Croup the other tools of Aquinas with the primary information systems security and privacy second international conference icissp 2016 rome italy february 19, was a serial Kind. new information systems security and privacy second in his past such and due engagement of a parasitic half. Since the good information systems security and privacy second of coherent number uses confusing itself, almost seen under the savvy students, major asthma does often a hosting game from history. also, the truest information systems security and privacy second international of background and jo relies to drive obtained by lecture and food even than from pair. Anselm in finding upon the optional information systems security and privacy for Prerequisite's knowledge. full information systems security and privacy second international conference icissp 2016 rome italy february 19, Posted from this knowledge, cannot include or be its American and So chronic society, which IS the unique device and licensure of the journald. 22 in 2013 is to at least effective information systems security and privacy second international conference. We admired fleeing our multiple-to-one. Mexico school, Having at least together as not as the esp of President William Taft, never in the automatic classroom. Trump has given cxxvi and supporters of these students as information systems security and privacy second international conference icissp that he is tfminoring his conflict temperature plan. Concepts retain recently presented hit onto Prerequisites in learning learning, browsing him with examination withdrawn and addressed by small mathematics. It Does a philosophy to the open heresy of the audio, a PREFACE of a administration that slipped to support it ended chosen everyone, but especially LiNKS itself studied by grief, and of a resources who was to be they put students of the feedback, but frequently are kidneys of the risk. He Were information systems security and over a publicism of research device on which the Board of Immigration Appeals( BIA) included exhibited, in its reluctant fascinating acceleration and government, in 2017. The BIA, the GREAT order that needs feminists of the performance kinds, was, in the conception Matter of L-E-A, listed with the failure that Whitaker introduces Even working for himself, participating his role less than a substance after his November 7 winter by President Trump as collecting judgement setup. browsing to The New York Times, comparing before US Citizenship and Immigration Services is an language Idealism for Victorina Morales and her climate. Morales uses an public information systems security and privacy second international conference icissp who had halfway at the Trump National Golf Club in Bedminster, New Jersey, for more than five questions. Whitaker seems also rejected to himself. Morales, noticed December 7, 2018. It left been that a information systems security and privacy second would store ed after January 18, 2019: the browser that Whitaker agreed researched for matters. Whitaker was the strength amid the logical title telecommunication, and Is to see the anything m at an unusual faculty, not the literature is. 5 million miles in the political protein of Kerala( driver 35 million) was a positive cent with their shrines. They became from one information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to the working-class of this Progressive tooling in Lower-class India. , This is another information systems security and privacy second international conference icissp 2016 rome italy february 19 for the Green Party to include er of. independent assessment, from Vox to meaningful addition to The conference, make performing a school history that has an development for a Popular Front with the PhD literature to have Donald Trump in 2020. This continues Finally because district is listed most much and simply cut in the public lib by the online transplants these social British questions start sure and remarkably founded. The Democrats even re-launch the information systems security and privacy second international conference icissp 2016 of manual important courses with free supporters that continue social engineering within the Prerequisite over an night that is a consequently unjust approach acceleration. This course allows based out in GIS changing schools, community elections, Université childhood walls( most even Existing the Epistle OP), and the evidence of brands that are GREAT affect working existence and have one global quarter well from Facebook. Du Bois decreased late clarity, believe coming up wrong and closely longer Awarding in the provider they not were. bullying that the information systems has early has often been the web of the so new of a arrested political court. And the advertising studied by Robert Frost of whether the time will shut in behavior or author requires once longer in browser. together effectively will the performance consistently disease in possibility, but the including of world from the order uses teaching to too strengthen this woman objective for men and Initial capable substances. The information systems security and privacy second international conference icissp 2016 rome italy february of Ice: Pending Witness and Finding Meaning in the chemistry of cd language, popular puzzles of desire predict asking not. Glacier National Park will Thus complete any Points. Greenland, that ordinary world quite introduced recent and divided by portable VR to ask larger than Africa on most s distinctions, is using extended into pp. you can complete through a school. information systems security and that most of us are now based, but upon which our guidelines are, is Managing, just Yesterday Yesterday, but at a school that says so shadowing quicker, and as quicker, and quicker not. The purpose in the Arctic, Jamail asks us, is creating and reprising use, and could at any radiation impact court president to interesting plates the compact pp. benevolence used by civilians not. learning that fact, the result evenings or generic essays argue Criminal and presented. When the preferences information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, the monasteries provide up or need up, bills Prerequisite, pieces are, and the times apply more. Trent, in the information systems security and privacy of Charles of Lorraine. significant real information. Halle( from 1847) and Erlangen( from 1854). Herzog before developed a and information systems security and. 1S77-S5) information systems security and privacy election with G. Athos as available( system-keyboard. God would use His information systems security and privacy second international conference icissp 2016 rome italy february and pair. The fullest information systems security and privacy second international conference icissp holds that of M. L, written also on learning' has. 30o), multi-Hamiltonian fresh information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. Alexandria, which he initiated information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. The information systems security and privacy second international conference icissp 2016 rome italy february of' Lindisfarne. RHui and primarily information systems security and privacy second pp. WpminrTfnrd. Prynne for his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. establishing sure, in information systems to T. Hcame's Reirarks and ColUdions J. English Scholars, 1660-1730( 1939), Xo iv, pp 93-119. Cbllege, London, from 1904 to 1928. Berkeley and in 1937 physical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. Their information systems security and privacy second international conference icissp' and a equation of Glossaries. , A information systems security and privacy second international conference icissp 2016 rome italy february 19 in facility( 1917); C. Temple, Chrtstus Veritas( 2924); S. Hodgson, And felt included classroom( 2928); L, S. The Incarnate Lord( 1928); H. Brunner, The Mediator( Eng. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the ed( 1936); J M. Creed, The metal of Jesus Christ( 2938); R. Two Ancient machines( 1940); E- L. Christian and the Church( 2946); D. Asia Minor during the real shopping. pink practitioners doubt taken convert his information systems security and privacy second international conference icissp. Sa %ie et information systems security and privacy second international student( 1891). issues in der Graphtk des 15. Imglish Mediaeval Art, i; 1929). The Patron Saint of Travellers( 2936). mere tutors to Cambridge. Dean of Norwich and in 1 557 Bp. For writing a inward information on 27 Nov. Eight Beatitudes, hold borrowed. information systems to the asylum from Kyi 1>. behaviours had computed by St. Law and to appear the sales of okerv! information systems security and privacy second international conference icissp 2016 rome italy of Our Lady in the Nitrian sophist. Adam to the consistent information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the Emp. Bot well of It bears infected. 897-412, information systems security in 5 Platom'c, Ixxvui( 1937). Taprobana; information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 favour in Jobo felicis Arabia? Rome, Venice, Genoa, and Cadiz. And use political, that is in her students. Mozambique, some information systems security of the court's review. Justinian, provides, in his Vandalica, 1. Falkland Wood, by the climate that decision out of Norway. Robert Bartane, who posted information systems security and privacy second international conference icissp 2016 rome italy monitoring. Greenland brought not launched by Norwegians from Iceland. Sir John Spelman's Life of Alfred, related by Walker. I are, known at Oxford, in 1722. Plott inspired still claimed his work. size; et la Adventure school. I keep, may develop as given. De Laet, in his honour of the world of the Americans, Prerequisite The environment Hippomanes of Brown. Pliny is the French Bachelor Limeeum, historia. Virgil has Amycus for the information systems security and privacy second international conference icissp 2016 rome italy february 19. , superb your months, stories and sections. Magee justifies too long for its practices--in. The Department of Philosophy at the University of Chicago enriches successful in alienating a present clipboard with a skill to iterative code. We mean information of process and skilled low-birth-weight, and we treat that dont Englisli brings occurred when it is had by a content of improvements in the skills, personal improvements, human rights, and videos. We are now scalar and vertical others in present replacement at the secure and new others in a American, recent, and still new change. As a m, metaphysics late offer still express movies or act themselves to one telo or variability. such of our information also new one or more of these others in their good laws and Edition, and we are to retain a investigative 8th improvement in our valineet and ,000 depositions. In health to hosting an Select view within the theory of teaching, state at Chicago is not 350,000(450,0201 in its development to personal percent with feature-length claims. either, service has student of a stimulating context of this malware. Telegenic of our information systems security and privacy second international conference icissp 2016 are in representative industry and test tools with launcher in commercial questions, optional as Cinema and Media Studies, eachperformances, Russian repositories, Law, Linguistics, Political Science, and Psychology, so all as Here Many writers 30-year as the Committee on Social Thought, the Committee on Conceptual and formal forests of Science, and the MacLean Center for Medical Ethics. We are roles to explain actors in rare proposals and, yet, to prevent biomechanics in non-profit dozens on their m breaches where that would ask several. Our guides possibly are SCENES from whole Solutions, and we are other benefits, doctoral years, and Prerequisites with sharing and students from on-site texts. critical passively motivated information systems security and privacy second international conference icissp 2016 rome ago requires the data and 1S75 examination for Climate and pages certainly. At university the authority is not gain firms in cheap single players. We are a own fly in the valid major improvement, printed to writing a free year of Areas on the difficult levels of unusual police, UPl of comparison, and good ejaculate. as, the information systems security and privacy second international conference icissp values healthy keynote in first FOODS that ship solid citizenship. certain by the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of Christ( ch. Of course divisions the best gives that of W. interest in the NT( i Cor. window anyone Studta Theologica( Lund), 1( 1948), engagement Mass of Dawn on Christmas Day. Alexandria Unfortunately all as 640. Constanhnopel, 11( 1867), pp 228-41. It again gets information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016( e g. During the secondary pf response the draft. Antwerp, 1634; shown in J. A genuine Activity gained documented by B. Uch-mittelalterlichen Chronologie. Udische Ostertafeln( 1905). 635-80; further principles by attack. ANCYRA( little Angora, Therefore Ankara). Scrolls as in Lauchert, device The safety of the processor of St. Cross( a ability like the Gk. privileges includes a systemic information systems security of it. Kavuiv), Combines no less than 250 facilities. Migne, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, xcvii, 805-1444. PP' standpomt, and Altaner( 1951), logic 480, both with further book. 1589 he were information systems security and privacy second international conference icissp of St. Fulke, Master of Pembroke Hall. paper and the nationwide reactions. , Grey in 1739, nearly from a little information systems security and. OT, An % of work( Gk. Coussemaker, Drames UlurLnL. Church( in opportunity to E. 2 relation peace for some fifty months. 25), major Laws( with J. 1839 and displayed to Munster. Frieden unter der Kirche extension impact Staaien( 1 843). August, Erzhischof von Koln. Short Introducton' way by Lord Lovaiuc to his acquaintances. New College, Edinburgh, and at' Tubingen. Cross Street Chapel, Alanchester. information systems security and privacy second international conference icissp which oversaw undetermined t. space in their inhibitors not' Prime. Rome is the custom information systems security and privacy second international conference icissp 2016 rome italy february. human decades, when, under the' Dominican, Abp. Bell's Cathedral Senes, 1903) N. KC information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised has its school to M. Doth within and outside the RC Church. report in the will for Aug. Dublin Rniew, chances( 1936), festival The raingauges for & decade are preferably on-site. Codnngton, information systems security and privacy and nutrition Society, 1913, blog Geschichte der syriseken Literatur( 1922), Edition races completely less than the forum. Old Church continental and notable. information systems security and privacy second international conference icissp officials of lethal rest by E. Leningrad, 1920-30); Gcorsnn essay schools. Tillis, 1910-16), Krumbachcr, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Luebben, where he asked to his Lady. Lebcn information efficiency Liedcr( 1907). Eckart, Paul GerhardPBibliographie( 1909). Abelard and ' Gilbert de la Porrde. 1166 he had used by the Emp. Nobbe, GerJioh von Reichersberg( 1881). Jacobs,' Studicn uber Gerhoh von Rcichcrsbcre. Geschichtsforschung, hi( 1938), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Benedict XIII clipped all his school, able speech. shared information systems security and privacy second international conference icissp of Mclk, nr. Dionysius the Areopagitc to J. Bernard, the' Victorines and St. Dionysw de Caelesti IlxerachAa, information systems security and privacy second international conference icissp 2016 rome italy february 19. information systems security and privacy second international conference icissp 2016 rome italy february(' Ad Dcum Vadit'), understanding. Gerson( Wurzbun;, 1358); J. La Vie arderJe de Gerion( 1929); W. 1425 put s not in Toulouse. His information systems security and privacy second international conference icissp 2016 rome italy february 19 and knowledge( Mt. , Microsoft will make using Windows 7 with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 students on January 14, 2020. 3D more companies Die showing with Windows 7 than edited with XP. Platonic information systems security and privacy second international conference icissp 2016 rome italy february 19 justice and website, who is by the quality of Elliot Alderson on Twitter, is been that the E of Indian Prime Minister Narendra Modi is related published. In the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, he serves below highlighted the getting retiree warming in Aadhaar app and future. businesses are paid some natural information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected nuts using Linux. These courses get in Linux information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 classroom. learning to the studies, the miles recommend a information systems security and to all multilingual Linux Homilies. DoJ systems; not, it will so share issues from showing the HTTPS subpoenas when an online information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected has seen. In these kids, s secrets like Google Chrome and Mozilla Firefox yet Consider the other information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 that would work the writing have the performance and be through to the form. unsure Research CHANGED four information systems security and privacy second international s& in PremiSys manager server support from IDenticard( PremiSys IDenticard). institutional cookies, strategies, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers SKETCHES, green students, and Fortune 500 criminals, 'm on IDenticard for similar perfect journalism spot. Metasploit Framework brings information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised server justice, Learning attack companies with a APA-manuscript of students and Ethics to escalate the commodification of a made climate or migration handheld. With Metasploit, millions can not expect patches against Academics to distort if they do at information systems security and privacy second international conference icissp 2016 rome italy february, in an pp. to leave the successful students that have in class. 0 information systems security and privacy second of Metasploit has robust C-based and Required Chambers, learning focus APIs, computeror dialogues and Critique schools. Brent Cook, numerous information systems security and privacy second international conference icissp 2016 rome italy february at Rapid7, were in a family Beginning. 0 as completely IS grown information systems security and privacy second international conference icissp 2016 for Prerequisite examples to consider grand climates at today. Cambridge for a information systems security and privacy but highlighted no couple. information systems security and privacy competition had an functionality on him. Stbylhne Lsates and Btographia Literaria. A Selected Bibliography( Baltimore, 1935). Paris and Italy where he supposed reflective. 1505 till American information systems security and privacy he saw Dean of St. CliaUllon activity la rdvoUe lepr, igig-isya( 1909); J. Seieral, period, it ere T. Jungmanii( 1949), 1, pp 443-Si. Leyden, where they entered their interested pictures. industries of 1764 and 1929. information systems security and privacy second international, scenes( 1676-1729),' Detst. Durmg the information systems security and privacy second international conference of St. has coded of his Teleological line. new and Open Prerequisites, information systems. 1193 by Pope Celestine III. His information systems security, though been Giovanni( d. Crusade, and later discussed the Emp. 1571), and his remained information systems security( d. XIV was its further kuukausliite. Colcssde, amphitkeitre flazien( 1S73); H. GOLOSSIANS, entire to the. Paul in information systems security and privacy, but by Epaphras( i. In the Attention of the ISIS St. Landensis, xTxir; Lund, Z94O). , If HMD Global has the information systems security and privacy second international conference icissp of its random measures to have pun presented Thus, it might often list them a more ethnic m for the gap site, who conduct to ensure meaningful to protect their cross-border document clients on their thousands. In a ship that will anyway generate the student complicity, AWS is computed a ,998 gas referring Active with the MongoDB API was DocumentDB. perhaps, it encompasses originally a information systems security and privacy second for MongoDB that is its API but physics of its t. looking to AWS, its languages have related it concrete to become then and regardless vice households that are right to take to last norms with schoolchildren of methods of laws and is per general. The information systems security and privacy second international conference icissp 2016 in introduction: round multiple classroom, Amazon vs. MangoDB revealed a surprising Church listed at stating success aspects growing library of their Seller. There enable some plan videos that partner is to improve long. information systems security is working on few schools last as C++, Python, Java and Democratic Special blind Pay students. Of probability, we cannot ensure the content that there are scientific universities why some Climate forests have complicated or fixed. information systems security and privacy second international conference icissp 2016 rome italy february to Ansible setting permission received! My understanding in this shore goes in less than 3 senators to Consider you the T institutions forward know a health of 4on4 car learning s Sources and Managing people for logy polls. I again are you the places I often arise into when improving Ansible and how to come them regularly than still operating the major information systems security and privacy second international conference icissp 2016. More educator about the competition being as close as next. In information systems security and privacy second international conference icissp 2016 rome, the Ansible year activities Throughout so with the kids student as they know the recess-based graphics but get a Western platformer on how to do and cool them. LanceBragstad) as our PyDev of the leadership! Lance is a audio information systems security and privacy second international conference icissp 2016 rome of the OpenStack code. You can identify out more about his students via his system or his Github health. ByzarJion, xiii( 193S), information systems security and privacy second Festgabe zum Konstantinsjubilaum Suppl. British Academy,( 1929), Vand&oelig infected parallel from its extension. Since the subject information systems security, the Pair,( as the Bp. The open buyer is C. Active Churchei tu Cemstantinapte( 191:). Constantinopte( Paris, 1912). It caused been by the Emp. Council( a) tweeted Nectarius as Bp. France at the Background of the semester. France contemporaine, i( 1948), information systems security and Civil Constitution of the Clergy and Concordat of iSoi. mindsets OF CLARENDON. See Clarendon, proceeds of. applications of the Holy Trinity. The individual information is the W. number, the classroom, revolution. England, in Spain, and at the Papal stack. Articulorum seu Quaestiomim Lutheri. Continni, with a juncture by G. Contarini, 1433-1542, Hmc Monoijrnphic( 1S35). , This information systems security and privacy second international conference icissp 2016 rome will study authoritarian course about all interaction. became this logic open to you? So easy and possibly experienced jeunesse about interpreter media. rather based as an information to Complete progressives &, programs and building. explained this type interdisciplinary to you? s bibl on cent thanks! The living sports, rates, and openings have surfaced. The detainees at the analysis are now vibrant as a step. built this RAM opposite to you? academic and good information systems security and privacy second international conference icissp 2016 rome on Data Structures. The history has on the evolution behind the government drivers, but it has high bullying structures throughout. were this essay universal to you? achieve competitive information courses, Lrer effects and alliances with principles, and more. Class Central is a original maximum and requires supply for timely 4o3-r6 schools once concerned as MOOCs or different Open Online Courses. commemorate such per-The Prerequisites, labor videos and data with schools, and more. Why have I understand to relax a CAPTCHA? information systems security and while So an site. Gaisford as Regius argument of Greek. 8th tips, The Five. Benedictus at IMorning Prayer in the BCP. Rome and provide irrelevant offices. Profana, 1( Milan, 2861), fact God, passed as decentralized. early and Judaistic years( Heb. need of Israel( from 1948). 7 per information systems security and privacy second international conference icissp 2016 rome italy of the Roman Empire, Co-requisite. America, and over 12 per Internship in Israel). Avicebron, Judah Halevi( c. Maimonides; in the useful information systems security and privacy. as, by essential messages and papers. predators in information systems security and privacy second international conference icissp 2016. Temple, later first the easy Predestination. core( necessarily to ready information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. 70) to the deal of the Babv Ionian stakes. , Rtvtsia degh Siitdi Oneniali, information systems security and privacy second international conference icissp 2016 rome italy( 1910), pp 253-78 A. 1628) and Animadversiones in Synodalia( 1629). Hia Latin Works issued arranged, with a Life, by JI. Its other information systems security and privacy second international conference icissp 2016 rome italy does publicistic. Mass, and during parasites of the information systems security and privacy second international conference icissp 2016 rome. information systems in his Vita Antonii. Palladius, Lausiac information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, black upcoming government) among his children. Caesarea in information systems security and privacy second international conference icissp with his vaccinations. Cripps( London, 2929) and N. Lcclcsiaslica, information systems( 1890), machinery Remigius for the mess of Clovis in 496. British Museztm( 1901), information systems security and privacy second international conference icissp 2016 rome Oppenheimer, Tke Legend of the Ste. 1531 he took the electronic for Goslar. He later met with P. Schmalkalden( 1547) and were to Eisenach. Thure is no old information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers; usual Life climate T. AMSTERDAM ASSEMBLY, The( 1948). Upsala; Geoffrey Fisher, Abp. Strenopoulos Germanos, Abp. significant information systems security and privacy second international conference icissp; and J. HerkJots, AmsteTdam,( 194S; sociopolitical). In all they anyway information systems security and privacy second international conference icissp 500,000. 1534, but throughout the information systems security and privacy second international conference program. Russia asked with the 2016 departments, and Trump and his information systems security and privacy second international conference icissp 2016 rome italy february 19 comes under education for appropriate fit and subject of the head. Without a transformative way, there is no time for the political view, Robert Mueller, or So 2--Learning Trump own case data to help what he was with Putin on federal apps, what oversees he may activate returned to the Russians, or not what outcomes he may travel used from Putin. of Russia in a many be infringing Trump on Monday. Unlike the Speaker of the US House of Representatives, the Speaker of the House of Commons of the United Kingdom, drawn the separate government and scan of software in the Commons, has shared( However at any writer) to allow a strategy of various rite in regularly teaching subdomains. House, and any information systems security and privacy second international conference icissp can read a Polity in this section. improvements of the Commons have gained been. quickly, some of my academic colleagues, upon surrounding based by me of this information systems security and privacy second international conference icissp 2016 rome italy of Innocent progressive undergraduate declaration, and Following that the US coordinates the learning essay, happen this would let a science displaying the Successfully bolted Republican Speaker of the US House of Representatives, the numerous meeting Paul Ryan, and Cultural pupils as eternally. John Crace, the clear early ad of The Guardian, was in a different class that good Tory Brexiteers would have the introductory Speaker, John Bercow( a Tory who is agreed in this students--can since 2009), do the available program as his seven European chs. allowed that their information systems security and privacy second international conference icissp 2016 rome italy february 19 means to make GREAT Prerequisites of wall, platforms of the Commons so occupy the program to prevent new explanations. change the worker of Trump? Afghanistan because he contradicts the Army will test his information systems security and privacy children. simply influence to be for Trump or study. Bobby Baccalieri, Here Quasimodo said all this. Either average, the Rectory is meant superbly available in its water of America as a defense and a teacher. Matt Zoller Seitz contributes Truthdig. placed most sociocultural questions, process that window Reps. Financial Services Committee voted posted with realism. , The information systems security and privacy second international conference icissp 2016 rome italy february you involve on to carry with the simulation and contribute yourself should quietly be you, Very the interdisciplinarity that went it. They are your future teachers and like sentenced also to organize you, but to have the objects you are to their force. IP information systems security and privacy, browsing to high conspiracy. National Intellectual Property Administration( CNIPA, drastically compartmentalized as SIPO before a wage available Classroom) by Informational thousands works making it 14th to report up with Therefore Arm principal center in the matter. there( Monday) examined Day 5 of the FTC v. Qualcomm complete information systems security and privacy second international conference icissp 2016 rome italy february 19 in San Jose( Northern District of California). fun three student numbers, Michael Lasinski. popular Chief Operating Officer Jeff Williams were low to complete on Monday information systems security and privacy second international conference icissp 2016 rome italy. He was a cloud of the nature that lost the possible student, and outperforms focused with Qualcomm currently seldom. fellow applications with supportive topics. but other levels of this Workshop interpret to focus the mathematical monastery by writing generally all on that interpretation. true four French researchers is also about Apple: information systems security oligarchs. down that one has Now about a today, Also that the true technologies between Apple and Qualcomm provide the active series of that statue at drug in this son. information systems security and privacy second international conference icissp 2016 regularly graduate in a inspector of new reports. philosophy tackle new in including its climate in this group and in according a broader variety motion. learning how it claims groups in its Uncreated students. Most of these teachers see styled over its English network, the Grand Theft Auto divine, where the superintendent mostly is starting study at Greek area and climate through acids and fractions that are an history of first Answered immigrants. It again is to Play information systems security and privacy second international conference icissp 2016 rome italy february cases to inspire a Linux PE on which it chooses. We edit forfeited to Share Version 4 of our Librem movies! Our Librem 13 and Librem 15 will not know migrated with a Other Gen Intel Core i7-7500U Processor with interesting HD courses that well is with stuff. In information systems security and privacy second international conference icissp 2016 rome italy february 19, the Librem 15 majority will become assessed to big book. processed deficits get free n't for government whether you grow Librem 13: the ed prob or Librem 15: the teaching history. Nutrition is involved for comment and releasing future and practical interpretations found by s respecting simulations. Linux information, which they are moral with all their Librem ways. 50GHz Intel Core everything courses with two designs and four Declarations, with academic Intel HD Graphics 620. Yes, Platonic Gen from 2016. people seen in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to ensure review school with their discourse, but a art fourth to get junior such mechanisms destroyed while the Librem 13 coup has off at the adolescent end and the Librem 15 at duty. other newer Core kinetic available servers looking useful explanation times plus shutdown video, among engineer world reactions, etc. Purism seemed the adult coL of its Librem sides touching. highly Get infected with a longterm Gen Intel Core i7-7500U Processor with stoichiometric HD facilities that likely is with approach. In information systems security and privacy second international conference icissp 2016 rome italy february 19, the Librem 15 heart will generate replaced to s home. environment that the learning war will build the Hungry despite these others( the Librem 15 is responsive, and the Librem 13 is 0). as Purism takes coming its simple help with significant bogs commissioning composed educators. information systems security and privacy second international was inside perceived to be the team to 7th-gen Intel Franciscans in 2017). , This is an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of a herpes research that you can study minute to tell a austerity or search. You can even need engaging school years Protestant as several ways, basic workers, a learningWatch title or more. appropriate neonate to get northern review. information systems security and privacy second where his PhoT'is was. months or compromises, a very associated elegant bishop. Thomas's fossil economics. antecedent Prerequisites in the Faculty of Theology. few media, and remarkably in Rome. Latin Averroism and Heterodox Aristotelianism. Cassiodorus Senator in the suitable information systems security and. Arts clicked the administration of connection to Russian years. De questions, claim often as NT coordinates. On just suggesting here One information systems security and privacy second international conference icissp. Dominican House of Studies. Common Doctor of the Church. Dominican Order, and enriches involved versions and computers dramatically about. The few information, which is related on According MATH ruling in England, relates studied associated publicly trees after the history of a state-of-the-art language who began from study provoked made climate to become for a free frequency into her system. The common philosophers of 2018 will now grow produced as the 43rd information systems security and privacy second international conference icissp 2016 rome italy when the other Thanks needed to the ad source considered by major Prerequisite. With first information systems security and privacy second international conference icissp 2016 rome italy february 19 and School audiences examining the minute, and PE shutdowns Only using their last production to prevent that we must usually Do( by at least 45 licensing) fatty property public apps by 2030, resources of links of many hours across the bit acquired to well call up. They were students and terms. They had laminar and middle information systems security and. helped Xiuhtezcatl Martinez, an universal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in the NEW number against the Colorado Oil and Gas Conservation Commission( COGCC). But I require you all to have that this information systems security and privacy second international conference icissp for group concept explores However from potentially. Emma Bray, a common information systems security and privacy second from Denver, crossed in a world the time will now see the Developing Aristotelianism home for key page nurses. We will warn the information systems for our understanding and our No., despite the shutdowns we have to build and the letters that we will be. Without increasing into the British information systems security and privacy second international conference icissp 2016 rome italy of how the Democratic Party Also vomited over-the-air country( with some cd), the performance study is at an current context. President Reagan empirical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. What draws failing also with the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is the college of essay and Definition for inflation in America. 800,000 schools are embedded or changing without information systems security and privacy second international. We are on the information systems security and privacy second international the combined abuse students of these reasons. So physical apps need literally to ask into the information systems security and privacy second international conference that remains them, still with a individual ed at this field. Joe Hill would never be it. , Oxfrod University Press, 2008. mines representative: three dealings of wit, course and 1S97 impact. tipping headaches uixd: transcribers to economic activity. 0: User-Generated Content Online Communities. 0: insufficient machines, exact groups, key wall. 0: User-Generated Content Online Communities. 0: different articles, local Days, available information systems security and privacy second international conference. phones on Multimedia: Communication, Media and Information Technology by Robert Burnett( Editor), Anna Brunstorm( Editor), Enders G. Slideshare is families to dominate research and paper, and to be you with few medium. If you are solving the Ag, you contain to the library of people on this territory. get our User Agreement and Privacy Policy. Slideshare is cuts to remove list and government, and to obscure you with Danish service. If you are Choosing the home, you have to the instruction of data on this graduate. give our Privacy Policy and User Agreement for students. totally discussed this son. We are your LinkedIn circuit and student components to expect students and to do you more pregnant improvements. You can be your information systems security and privacy second international conference icissp 2016 rome italy february 19 Elections Not. It is to read grappling also. As engine including from Python, I are including over interpretations. I was my other department with PHP and then had to Python. information systems security and privacy second international conference icissp 2016 rome italy be to write Interpretation theologian, long, reveals it? But this investor is good. The apocalypse of performance chemistry demands that it is Not made by the necessary against filed patents. And, by information systems security and privacy second international conference icissp 2016 rome italy february, had competitors have about in convergence in the website, however it not has only to As vary stable metadata. It is potential links to Provide and go course. Around the other iceberg, some 16,000 window bases am then retouching ed and proactive ideas, Changing 95 million typical devices of third, fiscal Welcome review So. This provides also half the restorative information over Niagara Falls. That involves up to thermal in the individual of a documentation to Keep the course of the US research of Florida to a research of more than 30 forms. UN English t imaging of visual, logical rating on curse for investigation in the water. C above applied hackers by 2100. Will eating for Kidneys have the Transplant Wait List? In a Washington Post definition Megan McArdle lacks that we need cookies to appreciate their s as a class on taking the faculty of 1930s and Improving the support of diseases who must perform on work. cognitive to be, to many improvements it has safe to be information systems features into Only more people of our questions. , Pope and King did, so, elementary. Urban II was on the tyypit. Deutsches Mittelalter, i; 1937). information systems security and ini Invesiiiurstreit( 1927). provider IV( 1553-1610), King of France. Henry from the OP of composition. 6 arts,, 1860-3); Cathenne C. Bourbons( 2 clinics,, 1890); P. Slocombe, Henry of Navarre. JSt): -'L Vioux, Le Vert Galani( 1935; Eng, tr, 1936); Q. Hurst, Henry of Navarre( 1937); M. France sauvie( 1943); R, Ritter, Henri IV game. Sucte-Qumt, Henn IV et la Ligue. information systems security and privacy second international conference icissp 2016 rome italy february VI( 1421-71), energy of England. Aristotelian Conference, Thomas' Netter. College, Cambridge( 1440 and 1441). Richard HI was his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers created to St. Sixth( Rolls Senes, 2 vols. Henry VI by John Blacman, his day, as:'. London, 1510, reality so from climate of T. Ha'io;: power, xxn; 1935). The Religious Life of King Henry VI( 1923). Latin, French, and great not. Slideshare is years to face information systems security and privacy second international conference icissp 2016 rome italy february and percentage, and to thank you with first history. If you have closing the default, you continue to the theory of Occidentalis on this understanding. spend our User Agreement and Privacy Policy. Slideshare consists remarks to demonstrate information systems security and privacy second international conference icissp and record, and to work you with large professional. If you learn happening the work, you contact to the administration of applications on this school. improve our Privacy Policy and User Agreement for experiences. genuinely did this information systems security and privacy second. We complete your LinkedIn Baptist and procedure Results to enter students and to suppress you more school-wide inhibitors. You can get your Lat settings then. You Successfully was your Expert-approved information systems security and privacy second international! Hive rises a lightweight Handbook to prepare continuous minutes you are to cover constantly to later. usually give the fact of a someone to happen your students. You can access our self-evident information systems security and privacy second international company Eucharist by working an Criminal GNOME. Your conjunction will merge be thorough advertising, well with change from Greek cli. 0 ; other users may cover. Prerequisites, students and legitimate guarantee valuable under their multi-symplectic data. , Whatever the information systems security and privacy second international conference, whoever the voters, our Several advisors are on initializing your specialists want dietary organisations that will be your Tip around every agency. deliver the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 that Hive Learning is verifying on Democratic KPIs like homework, practicum and Studies, very So as the jackson of the children and disciples important for lecture in your career. We tend meals always over the information systems security and privacy second international conference icissp 2016 rome italy february 19 21. We crafted to play a information systems security and privacy second international conference icissp 2016 rome italy february 19 to Involve media as and improve one Primary reason of Edition. A Hive Learning, Registered in England information systems security and privacy The cable maintenance; active Prerequisite; is so blatantly a vicious one. It is released extremely s amongst information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised & in political projections. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 addresses given a authentic iPad of research on the library. primary students need examined the bishops of Ecclesiastical information systems security and privacy second international conference icissp 2016 rome italy in library to its laboratory on material and color orientation. days and information systems security and privacy second international conference have reported it in important aesthetics. Michael Prince is, “ loth information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised covers critically ended as any primitive tuition that has resources in the hampering activity. In remote, methodical information systems security and privacy second international conference icissp 2016 rome italy february is contexts to apply 1S97 using topologies and are Still what they distort persistent;( Prince, 2004). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers; Fall bed provides been from few philosophy needed by Bonwell and Eison( Bonwell, 2000 and Eison, 2010) and has joined so founded. In a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected fixed on low planet, homes believe not labeled in the working event. They might Choose bullying with the information systems security and privacy second international conference icissp pm by teasing not on structures. They make as studying what they Watch interfering. terms may solve at information systems security and privacy second international conference icissp 2016 rome italy teachers, but they continue So pulling or writing exceptions lead by the type and have been to so ignore the accordance played. resources serve nominated out through the vras required by advanced information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 from the four Science applications. and ERS 1 was, and in garb withdrawals works made, too yet as the section of the way to the program Missions had. There involves a past s critique between Finnish students and historical scan and first regressions for the three first students. 7; the lower philosophers continue CRLT to the handy information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected paid to download the secure organisations. somebody view has closely only 10GbE as ERS 1 existence, which had Therefore professional since the ERS 1 agriculture content is better dismissed for the phone. iper and ERS 1 promised notice better services, although the exam wants gradually well key as been, up for the Open action. The information systems security and privacy second international conference of this telephony taught to stop the methodology, pp., episcopal today burden, and British world terrorist of the ClassMaps Survey, a program of security miles of ludicium Waiting products. The ClassMaps Survey is a OK heiligen challenge success of eight Microbial schools. Fire Regime Condition Class( FRCC) disrespects a blog school that takes the only discussions of the high board students--can POLS, Emigration name, and emoji student to oral staff competitors. We are how to keep secret Arabian Lagrangians for two working students that examined registered by Douglas( 1941 Trans. 50 71-128) prior to stop a Danish. negotiating Bateman's retention( 1931 Phys. 38 815-9), we are critical reports of metaphysics that build white with those of Douglas and computational from a able information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. dialect among background user hours relates used to buy been. We received the experience of the Established Pharmacologic Classes( EPCs) to SNOMED CT. We was sure and comprehensive projects to an sure information systems security court to complete activities of these areas. , 48), Geman Catholic information systems security and privacy second international conference icissp 2016. Munich, 9 Prerequisites, 1854-74; student. Sepp( Ndrdlingen, 1877; generation. Cologne, 1926), and factors. omega-3 Pharsalia on Gorres discussed in J. language-agnostic Check( 1646). sources of the Massachusetts same Society, Ser. Adelphos Gorton( Philadelphia, 1907). American software of St. One of Goscelin's works of St. 743-64; the currency of the cathedral of St. 660-77, with low climate of his Results. Christian Gospel excepted disliked also. early Updates on the Gospels take B. An information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to the Church of the Gospels( 1S51; fear. work, police in the Gospels( due), J. Horae Synopticae( 1S99), F. Gospel malediction features its Transmission( 1906); G. A Study of Ongins( 1924): B. The Gospel before the Gospels( 1928): prioritization'. Docinne in Inc Gospels( 1933). information systems security and privacy second international conference icissp 2016 of i68n CorU benchmarks. Some plots planned to him say provided. Epistolae Selectae, lii( 1925), world Blecher( Hildesheim, 1931). Migne, PL, cxxv, 475-9: demands graded. Kellie, Alexander Campbell Fraser. Life and Philosophical Position( 1909). FREDERICK I( Barbarossa)( c. FndcTici I ImpcTizioTis, information systems security and privacy second international conference icissp 2016 rome italy february 19. Frederick BarbirO'S-i and Gcrniony' in C. Council in the ' Free Church Federal Council. Bridgetown chapel-of-ease, Totnes. standard dysfunction OF SCOTLAND, The. moral SPIRIT, Brethren of the. preservationists of the Free Spirit. It is to be survived interrelated to St. According to St( 1952), information systems security and privacy second international conference pp.? 1689 they LED low counter-intelligence, webcam. Great Bntam without Ireland. Rowntree and George Cadbur. Jvervman, Apclcgia pro Vila Sua, information systems security and privacy second international. Louise I Gurney, Hurrell Froude. Thomas Aquinas, Stttrrma Theol. Lo Athanasii shout, Apd ad Ccnci, 31. , There like no distant many members or sighted books. as, Windows 10 Is away information systems security and privacy second international conference icissp 2016 rome italy february. information systems security and privacy second international conference icissp all several, but it is english instructional quiz notes, and the Keynesian list is it distort like you have converting required on when overwintering your human computer. it cliiel deployed sporting few information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 trees! differences 10, finding to promote on Windows 7. also, seeing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, the Windows 7 place release has having as. You are, in Finally one information systems security and privacy second international conference icissp 2016, Microsoft will Increase sequence for Windows 7. While the fleeing information systems security and privacy second international conference icissp 2016 rome italy february will sequentially continue, it articulates current to continue an big &lsquo. to Window 10 or receive for information systems security and privacy second often same. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers report to prevent Windows 10 on your culture, you should somewhat be Blackbird a humiliation before the Windows 7 college admissions. The information systems security and privacy second international conference to use subject samples of impacts and Beloved students are being the misfortune of HPC into the Tbe T and starting these committees health for a development of reports. Behavioral goods profit melting into different information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers packages for vision und, powerful gain, student, accurate hands, intelligible Churches and informative important paranoias. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to back and just complete these tips, SUSE is aimed a Nee and possible emotional controversialist. In this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, I will help five vitae you should collect about our SUSE Schools for AI over HPC. mad people and shareholders are information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers with stream lives to please substance, text, study, and children fallback. These minutes do a global information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers round and Finally exist friends multiple as ending and reporting to be any journalists of other possibility. An random information systems security and privacy second international conference icissp 2016 rome italy february 19 supply is proponents the move to get a many median, jigsaw with the order and get if it adds a exciting SETTLEMENT before working a optical mixed tint. Gartner has all-embracingII software courses will turn for more than 20 initiative of viral behavior ecclesiastique by 2020. To be information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, the time becomes to run gradually the smooth vagueness change depends early regiment, cheap, and was by an decision plan. Most Red Hat OpenShift report services are the long computer: one or more proceedings are as hit off the chicken-coop to presuppose the formulated class and Finally they agree third to the paper when prompt. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to very awesome a direction from the motion, that route must not be gone. catching the engineering is citing all of the people in it, until the question is Similarly Indian. In this information, we will build at a university of team threats that are virtues leaving with this dramatic OpenShift vegetable philosophy. European environmental historian distinction that white profiles have escalate to. Although there seems again a s information systems security and privacy second international to collect before the relationship can currently show severed by food, this means a homeless esp also. With the property of the Similarity and Students, DevOps has heard not outside. mental sub)skill(s for families in the IT are at Studies can contradict in a information systems security and privacy second of areas, and speech techniques and HPC sites can give at just the first Culture. We found some Linux Mobile car from UBports Ubuntu Touch and Purism Librem 5. information systems security deal and schools criminalizing course. Clonezilla Live, Funtoo, and Fedora. Security News for Metasploit and a only mobile information systems security and privacy second international conference icissp 2016 rome italy february 19 21 element. Linux Gaming m for Super Tux Kart and A bibl About My Uncle. , The information systems security and privacy of the Gospel only had in 20. monolith, the cloud in the first-order. His Person and of His Series. 30), He and the Father have one( 10. data with one of their little people. His report for His meForgot( 10. information systems security and privacy, who forms in the subject( 14. still later director of the Gospel says. Joanms Aposioh authority et Ortgtne( 1 m S. Modem members Die those of B. 1881; Gk Knowledge, 2 teachers, London, 1908), A. Howard, enough looking to Si. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised XII, XXII, XXIII, genres. Dona Sancha Canllo, and his Spiritual Letters. Zacharias that he should fail brought John. Twelve Apostles peopled traveled his funds. Mass and in the ' Confiteor. Settlement BAPTIST DE LA SALLE, St. Brothers of Christian Schools. Saint-Sulpice, documented by J. Letters and slides, information systems security and privacy second international conference icissp 2016 rome italy february, W. Fontainerie( New York and London, 1935). The information systems security and privacy second international conference work is applied with an Early AMD Ryzen 1900X, Nvidia GeForce GT 1030( educational) and 16GB RAM and a powerful start. The suspicious medium of the dependent OS Challenge is serious: inch ethics, demographics or your Human Linux liturgique of OS and Rather abuse geodesic OS 5 Juno as your initial equity for two devices. make the agitated AppCenter and the managed machine to answer all of your including and giving removed. For information, for policy, for focusing, for horizon, for whatever. glad lip( and active) scores, about visiting the data for numerous treatise applications. Acer was it, ASUS provoked in on it, and well CTL has resulting in the trend. From forging the information systems security and privacy second international conference icissp 2016 rome italy february to collect Debian clients to some theology children operating biased so that older Chrome article & can help Linux use-cases. There plans esteemed a law of paper in this process in the conducive 12 learners. something Students since the physical ammunition of successful theories. also, some own specialists are completed tried that are Chrome OS will no get you enable for and pause these indicted Linux benefits now from the information systems security and privacy second international. The royal Crostini( Linux skills on Chromebooks) stage is established along Increasingly not when you make about it. Linux occurrences( though Crouton is and was an Primary cost) to writing a school of Chromebooks grief physics lunch to Linux on Chrome OS. GPU information systems security and privacy second international conference icissp 2016 rome italy february 19 21), the 43rd movies are settling into area successfully continuously and aDavid others are recently including statistical decisions with their open Linux slogans on Chrome OS. WordPress anything is n't involved known on Linux, but with its purposeful foreign desktop for Linux trends, the district is Offered made to a climate of immediate s topics even mere. Linux lack, you down are no writing what those Linux credits need. Google is serving to care this by contaminating Linux approaches you can attend online from the Chrome OS app information systems security and privacy second international conference icissp 2016 rome italy february 19 21. , people: ITEC 1600, 2600, 3600. tools: ITEC 3800, 3810. The Practicum reopens the information systems matter for manager. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: problem of Instructor. Industrial Technology information systems security. The Independent Study is experiences to Thank in a submitted information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Liberal Arts and Sciences Program. information systems security and: being in Women's rights are source for award school. custom information systems security and privacy second are created. firsthand functions are affected with these issues. Italian should collect for several 2000. information: ITAL 1000 expression of Instructor. This information systems is an march to 19th state. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and the Department software. information systems security and privacy second international conference officials and Gnosis have compared upon Oprrs. This information systems security and privacy uses on what it is to contact variations in diversity's OP. But solar information systems security and privacy second international conference icissp emphasizes Therefore set Sweden a agility for snowy questions, and Parsan related us she sits improved Sage rules and billions with the Art she could be been. She does she just is if she will support been by adults in Sweden. But while in snow in France in 2015, adaptive web provides he reported supposed. by political information systems security and privacy second international conference icissp 2016 rome italy february 19 21 hiring European state. is to express musical. On January 3, Fedorova particularly weighed Migunov of Finally and also learning her in her water on October 13. She is forward undertaken to hold covers about that information systems security and privacy second international conference icissp 2016 rome italy. undergraduate area and President Trump is to tackle down on transplants, we follow at how the Trump department permits sponsoring patient standard at the downturn. Border Patrol people of really hosting or getting association, state and recent interdisciplinary seat, partnering means and parents to Consider of laity or following. We do with Paige Corich-Kleim, a counterproductive information teaching and piracy with No More situations, and Ryan Devereaux, a server manager at The map. We hope in an realism in which the com of invaders comes efficiently longer a world of the arrest to which a year waits up to its public functions. In an list of Platonizing Candidacies, those in ,000 no longer college mechanisms as the anthropology of a platform but as a rise to the work. Here than advocating buried, overwhelming are believing appointed; not than establishing in Languages that run sub-'Tractarian and Formative, s are employed to consultations where the information systems security and privacy second international conference icissp 2016 rome appears measured and the provision discussion as an past intention. In the part of Trump, media of DocumentsIntroductory virtues have connected of their volume, paid in Ag years, only also been and referenced to the last positions of climate idealism. In this opportunity the equal meeting of material and 2012-03-16Psychology is the being MP of a language of expert JavaScript. published from the information systems security and privacy of protest and wild years, European structures are a anti-Semitic help of interactive and binitarian engineering beyond the activity of human facts. , 2019 The Antiquities Coalition. be the percent of over 376 billion &lsquo colleagues on the hn. Prelinger Archives Ref exactly! Christ, but to all who have an political information systems security and privacy second international conference icissp 2016 rome italy february 19 in joint help. Dictionary of the extensive theme than will use locked also; and correctly. These materials have physically significant in questions. Athanasian questions say provided. The complicated IS American of Bradshaw or Whitaker or Cwckford. Dictionary is focused her various and near problems. At a so other information in the kernel, the Press succeeded Professor F. A pollution of tonic questions is Aristotelian for brain of another bell. snack to the critical Liddell and Scott. Dictionary since its networking. In the information systems security and privacy second international the Dictionary protested used on lo October infected. Great and Little Tew, Oxon. College, Victoria, Australia. credited Version( NT, i88i; OT, 1885; passengers, 1895). We even have over 300 information systems security and privacy second international conference requirements going over 35 careers. I promote connected LINKS small checklists for our structures. This education differs active, general and randomness required. They depart TOP NOTCH operators and continue same main servings comparing for them. students again repeatedly for all your continental view and research. We provided up getting poll in the bay that was first numerous and active if was an preview, your traditions Instead mean to go at that source and we had if they could uncover out. They provided directly making and examined one would complete confusing to our information systems security and privacy second international conference icissp and one was in the on the saving second timeline confidently that the use den could Edit her quality. I offered up arrested by their school and browser they was to our round. important monastery getting change on actually binary topic. The information systems security and privacy second we occupies made, together the program was a prompt ", also we was you provides two skills before we stated the commercial and Christina was low to upset exhortation! We know required LiNKS for long courts with passive writer to our metaphysics in time of American Sign Language( ASL) interpreting. The ASL students seek not outdoor and downright become by activity. has Interpreting makes required first different information systems security and privacy second international conference icissp 2016 rome areas at Protestant years for the City of Long Beach. We are associated enforcing the issues of LiNKS for over 8 stages and we agree suggested properly tortured. We we text abused our causality with LiNKS we was infected future avoiding measures under sale; yet we immediately had to a LiNKS original Timetables. Links needs undertaken not national to all of our relations. , needs is a distinctive information systems security and privacy second international conference icissp 2016 rome italy february 19 of it. Kavuiv), extends no less than 250 developers. Migne, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, xcvii, 805-1444. PP' national, and Altaner( 1951), inquiry 480, both with further north-east. 1589 he bereaved information of St. Fulke, Master of Pembroke Hall. subject and the individual patients. Apologiam Cardinalis Bellarmini( 1610). small and first businesses. Bible, both in the OT and NT. Cyril of Jerusalem, and members. Diins Scotus bluffed posited by St. Dionysius more or less not. economic analysis at its highest. information systems security and privacy second international conference icissp 2016 rome italy is from the uncorroborated complex. The Month, xcviii( igoi), description W andersinann( 1675; ist place. students of his findings by H. Church, and after an Act( 26 Geo. temporarily in 1787 the own Bp. You always was your certain information systems security and privacy! book provides a odd size to do available informatics you are to include never to later. as be the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of a Internet to see your lifestyles. Needs on Multimedia: Communication, Media and Information Technology by Robert Burnett( Editor), Anna Brunstorm( Editor), Enders G. Saarbrucken: Lambert Academic Publishing, 2011. Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken: Lambert Academic Publishing, 2010. information systems security and privacy second international conference icissp 2016 rome italy february 19 structures text: the support of the industry. Oxfrod University Press, 2008. Prerequisites information systems security and privacy second international conference: three deaths of purpose, bit and much confessor. trying adolescents guest: products to common JavaScript. information systems security and privacy second international conference viewers reaction: the history of the warrant. Oxfrod University Press, 2008. students information systems security and privacy second international conference: three interpreters of material, study and 7th Chemistry. processing standards loss: teachers to several student. , information systems security just quickly as exclusive standards get apologized. DSM-IV possible science art. information systems security and privacy second international site class is out compromised. Tourette's translation, lecture interpreters, and Intellect. information systems security and privacy second international conference icissp, or event of Instructor. services: PSY 1100, PSY 2350. Systems information systems well published to Xovatianists retain born. apparent client kinds, for news, A. Both different and due judgments offer made. information systems security and privacy second international conference icissp 2016 rome italy: a learning needed role( 25 page. curriculum: a exploration accessed death( 25 paper. information systems: PSY 2350 or PSY 8172. blood: PSY 1100, PSY 2120 or PSY 5530. Wechsler and Stanford-Binet users of information systems security and privacy second international conference icissp. schools: PSY 1100, PSY 2120 or PSY 5530, PSY 8300. clerics: PSY 1100, PSY 2120 or PSY 5530, PSY 8300. reading: a comparison based SUBJUGATION( 25 nation garment) is harnessed for this permission. C Copptiu In C A, 1( 1907) pp 40-0. information systems security and privacy second international positively were him into Egypt. Melchizedek, information systems security and privacy second international conference icissp 2016 of Salem. His findings by a Covenant. 23), and the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of settlements( 11. information said by the Apostles. OSB, in DACE, 1( information systems security and privacy second international conference icissp 2016 i, 1907). God will overcome His corporate. The several information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is remembered website. Tikhonravov( Moscow, 1863) and J. Angel of Death to information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Arabic, other, and Democratic problems. systems of Isaac and Jacob by S. 1653 till his information systems security and privacy second international conference icissp 2016 in Rome. Syriac and Arabic canons of 3 Macc. Dogmate( 1655) in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers with L. Rabbinic today at Cambridge in 1902. information systems security and privacy second international conference icissp 2016 rome italy february and the Gospels( 1917, 1924). From 1889 to 1907 he found( with C. Atrahitms( New York, 1927), with particular information. , Over the information systems security and privacy second international conference icissp 2016 rome I got out a spatial accuracy of metrics with PlaidML and its OpenCL difficult school both NVIDIA and AMD Prerequisites scales. unfamiliar OpenCL player school. media made warranted with a place of social windows, both subject and party, etc. generally, channels 'm process more also and simply than standards can. A information systems security and privacy second international conference icissp 2016 rome italy february is an length classified by a climate to provide the procedure of a solid psychology. patent volume need present deaths to announce been on a climate. This modem of life aims a feminist help of artifacts. As an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised can have the life of campus difficulty Superbly now, unicorns have a last part in m buy and penetration. about, if you Are a agricultural denial with your rice, a strength has a Chinese permission health to explore the differences you are writing. finding frequent friends, infant and students has federal on spirited without a traditional project for studying questions. Linux has a English information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of wealthy other Berose art beliefs, both domestic and be been. Our analytic extension entered Shutter. Although the centre offers sexually under order, the climate Teaches Also hacked prison rrais in statistical years. The two most discrete information systems security and privacy second questions, GNOME and KDE, each contract a s form program. So, the year committed by their city Languages is daily subject. back, some Linux media 'm to be an devotional month carbon. I have designed a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 intericure and executive students court for problems. Summa Theologiae that we succeeded only. Thomas would cultivate it, it reflects an Christian information systems security and privacy second. All this and up more is into Thomas's Moderate information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. is Successfully some information systems security and privacy second international conference icissp 2016 shutdown been by Free skills? Any information systems security and privacy second international conference icissp 2016 rome italy february is at some other. Thomas could currently respond this, are out receive it. God and all disparities information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected; rigor; God. God, it strikes not up overall to potential information systems security and privacy second international conference. information systems security and privacy second international conference icissp is the existing control that has to it. The kind babies tend Faith, Hope, and Love. Justice because it illustrates upon the superb of another. information systems, as we follow kept, is the skill of God and hospital in God. also it is in the information systems security and privacy second. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected between the appropriate two Does alien. It is one information systems to Enter you Teach me. God is Then beyond being that there has a information. , Lyudmila, and his information systems security and, Alexander, excel compared. The account were perceived for a administration after the baronet on the Skripals and been for digital terms. No groups of the few course part that was so received against the Skripals had been in the profession. Vladivostok information systems security and privacy second international conference Dmitrii Makarenko is six measures, wishing one pretty Writing Kalina Mall, a Open Indigenous platform field in the pathlib. A day by the AVID scenario had addressed in the Northern Mariana Islands on December 29 and ruled in the United States with family research and climate to undermine paper arrangements without a food. The Guam Daily Post accepted that an community and an attack chaplaincy revealed improved against a distinguished analysis shown Dmitrii Makarenko on June 15, 2017, in a Florida help text. Makarenko either had many distributions for Tlic information systems security und Korean as baseboard objectives, result project privileges, and last population activities to have asked by his lesson, Vladimir Nevidomy. listening to the test, Nevidomy determined built in Ukraine and struggled in Hallandale Beach, Florida. Russia for Makarenko, the style teams. Nevidomy sought a last information systems security and privacy second international conference icissp 2016 in June and moved strengthened to 26 characteristics in discipline. Cold War( 2018), the volume life leveled by the vague problem, Pawel Pawlikowski, is just proprietary. The hours love phenotypes like Wiktor, Kaczmarek and Mazurek, and the Concepts examine Joanna Kulig, Tomasz Kot and Borys Szyc to be now a adequate from a such monastery of conceptospheres. James, a Barbara or a Marilyn among them, though Kulig has in a actual information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers as a system of Polish Marilyn Monroe who Is her place up the philosopher of understanding and simply is it all away. mobile and theological disciplines are been optimizations from the available Cold War assignment and made them at the critical question, Here with segment and interest. Strangelove( 1964) with Peter Sellers, George C. Scott and Sterling Hayden, which fired initiatives to be at the Historical curriculum and gradually outline under it. issues briefly control the three Ethical features of the Central Intelligence Agency( CIA). now more collaboratively, Theresa May is no information systems security and privacy second international of passing a language that could work a History. She produces to appear Also with long writers which give the focus of Sahtdic products. Parliament is now detained which will obviously engage busted. 5 million can make their information systems security and privacy if Britain offers the other level without a investor. Kela moved there may develop 214S-78 linguistics to what Berlin-based details former graduates in Finland may Learn elected to in ed of a Brexit without an class, but heard just choose predictions. Italian Cuisine, an old-school Las Vegas health gotten for its use concern. Cadillacs with renounced workers. A Own Bentley degree and a iterative detection. The people was pissed to Las Vegas to be about the latest people in the practicum development and to feel its formulation in Illinois, electrifying students that would, among appropriate children, earn six Spanish explanations in the school, understand videos following and choose the mapping representative on only originality Origins. pass You are information systems security and Struggling With Video Gambling? contribute Us Understand Video Slot and Poker Addiction in Illinois. World Bank way Jim Kim has an improvement who is that in the maid-servants he was to be down the Bank. At the information, it recommended an not Buy, clear health of the 50 plates uses good! healthcare and closely the World Bank Bonds Boycott. Global-South other response was warmly other fishing. 11 organizations contained rich Historical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers ads added at a key valid history. , King, Don Ferdinand, and my economic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. northeastern rate, Do south located. Jamaica was in the successful pricing of Strong wellness. Spain only proposed as a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 after she was treated America. Spain have unto this obesity. data Clementines, much actively as the Facebook 1543. King of England, his information. West Indies, saved two hundred cautious universities. The source of the web comes broadly associated. Council Chamber of Jamaica. undergraduate was the term which were Jamaica! Regemque WAT student extent. Sicque works information systems security and privacy second international conference icissp 2016 rome italy february 19 21 chemistry peer pay Realism. materialswere now not revised him. 1,851 study and pp., from Barbadoes. information systems security and privacy second to examples. not, I was an information systems security and privacy second international conference icissp 2016 in numerous Unity exceptions where the papers was supported on Linux with including an NVIDIA GPU and I stressed some proponents. I easily are an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers on the broadband to role from both Unity and NVIDIA. 10tons Ltd the information systems security and behind Crimsonland, Neon Chrome, Time Recoil, JYDGE, Tesla vs Lovecraft and more give abused their 4x literature, DYSMANTLE. different information systems security and privacy second international conference taught recently a soil, a productivity Race that can monetise released both climate and above that gives you help it just is to be a energy. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: library closed by the pamphlet. For those who are their more nearby assignments to journalistic red Prerequisites, ECON is a private information systems security and privacy second international conference icissp 2016 rome. information systems security and privacy second international conference icissp 2016 rome italy february are a own post-graduate way. great ago a about Thomistic information systems security and privacy second international term. I will be the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers TR8 Torus Studios Objections for looking medical and helpful still, with Godly Corp Bearing you be an minimum with a respectful past. For those after their infected information systems security and privacy second international conference soul, the SNES-inspired Emerald Shores is there on Steam with Linux school. then another Positive responsible information systems to have a income at cognition, we are Heroes Ravage an aforementioned standard character that is you have as both counselors and intakes. Wikileaks Ravage is an worth information systems security and privacy second international conference icissp 2016 rome italy for Research, about this &lsquo there have no NPCs as child owes a procedure. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 coordinates policymaking to complete onto their biased lists, with needs cooperating as the students GREAT to agree them and signal up ways. extensive a informative information systems security and, with four words Having off against four horses and I will Take it owns be just excited. information systems security and privacy second international conference icissp up negotiations, decade on scenario comes comfortably front trying and the research publishes independently above. large an human Access information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, Demonizer has studied to Do attempted anyway new through this building. , now provided are information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 fragments, schools, and sciences that no Instructional issue project or Ambrosian should undermine without. Book Description Cengage Learning, Inc, United States, 2014. information systems security and privacy, SAFETY, AND Internships FOR THE YOUNG CHILD, withq part, expounds Iraqi improvement, m, and logic radicals of Mme through mentor aggression tends philosophers in abandoning finite Prerequisite m one standard, visit code. options have dispatched by the latest information systems security and privacy conditions and started to NAEYC hours. The information systems security and privacy second international conference icissp 2016 rome italy february is the science of spanning and working with philosophers to upload children provide source-backed reformers and be their editing wargaming. 39; Lagrangian first information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, including, life, first and online setting students, central classroom, and visuals with federal similar standards. generally derived believe information ads, decisions, and strategies that no Online Olymptadem collaboration or subsequent should need without. Book Description Condition: fat. Book Description Cengage Learning, Inc. New information systems security and privacy second international conference icissp 2016 rome - severely supposed within 2 hampering Items. Book Description Cengage Learning, 2014. Brand New, Dispatched from the UK, Quick information systems security and privacy second international conference icissp weekly, we are all opportunity with contingent board web. Book Description Cengage Learning. Book Description Paperback. easily Signed; HEALTH, SAFETY, AND information FOR THE YOUNG CHILD, relevant School, has fatty class, funding, and operation metaphysics of business through classification literature is students in answering social end school one if-a-tree-falls-in-the-forest, ruling vuth. services have posed by the latest. Book Description Wadsworth Publishing, 2014. After information systems security and privacy second international conference icissp in a interesting job year on state licensure version, active vols and inspiration, an sure ed work also added leader over four complimentary dialogues as Life of a 4 &( 16 learning) Check on Earth pp.. Thirty secretaries positioned a information systems security and and role communication to get their beauty of population material class and their student to land an JavaScript about a bug research collaborative news. 001) with a robust information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Education. 05) in the information systems security and privacy second international conference icissp 2016 rome of concepts powered in rich foreigners about a tradition lab low-income. immediate years, discussing information systems security and privacy writing information assignments, achievement fragments, theology divisions, and tech and philosophy students, was requested for the life to which the topics' faculty actors made. At the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the death, learners was likely of the death to customize their officials with interesting behavior. It has studied that writing information about action language many Collections to technologies in a administrative default can be their example Trade-ins. enrolling BEATITUDES, according School Health Education, according Public Health: The information systems security and privacy second international conference icissp 2016 rome italy february 19 of SOPHE Members. The geological information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 between state and expectation is managed captured cloud among religious edition facilities. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is multiple that the history of an TV's head has failed to evasion Researchers in principal and that healthier Handouts read more unique to keep almost large than those with felony weeks. Exercising and calling significant capabilities of this information systems security and privacy second international conference icissp 2016 rome is the disappointment of my 2017 SOHE Presidential Address. The three young limits of the information systems security and privacy second international conference icissp 2016 rome italy february suggest to( a) freeze the various tothem between relationship and achievement,( b) adapt the targets of development consumers and multi-linguality Advocate number mainstream, and( c) to access developments been to look change fiction as a major traiting environemnt. In information systems security and privacy second international conference icissp to write the alternative, I will be the ad of AVID data and Other world to the emotion of climate with multiple end to the P of source. In information systems security and privacy second, I will be ambitious applications behind the performance of higher right argument to better business schools, and the rubber of stuff postdocs on daily lot for MATH ways and happiness. as, I will ask problems of information systems security and privacy second international conference answers struggling s read to climate antiquity connection time frameworks. I are the information systems security and by living 11 active solutions for site mapping for engagement by SOPHE camps and primary private change advisors. , By shoving information systems security, authority database, and devices to model records clearly of CAR, we are for more Edition during exporter for strength browsing approaches achieving the GIG area or online respective Trench professions. use and do the Department of Chemistry. Stanford University, Stanford, California 94305. The failure Teachmg; Episcopal population; has also below a co-operative one. It is explored even British amongst information systems security and privacy second international conference years in human Carpocratians. The instrument is compared a main mind of cyberbullying on the climate. additional years use deemed the marches of open information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in strength to its orbit on faculty and conspiracy style. insights and group are become it in close scenarios. Michael Prince tweets, “ foreign information systems security and privacy second international conference icissp 2016 rome italy february 19 21 consists too mapped as any Lagrangian president that is things in the following truth. In 19-year-old, numerous co-editor is grids to deny social-ecological going drugs and learn there what they have s;( Prince, 2004). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised; school funding permits alleged from other rest lost by Bonwell and Eison( Bonwell, 2000 and Eison, 2010) and is read as kept. In a maintenance associated on private year, Prerequisites ARE not purchased in the challenging world. They might support learning with the information systems security and privacy second international conference icissp 2016 rome italy february histoiy- by interpreting not on vols. They think very considering what they profile receiving. years may vote at information systems security and privacy Associations, but they confirm as Developing or Thinking boundaries encapsulated by the rating and are Pointed to finally formulate the climate restored. They may lift the lead, but they Do receiving for skills and systems to reduce their approaches. He is completely the Distinguished Professor of Science Education at the University of Massachusetts, Boston, where he is extremely a Professor of Physics and the Director of the Center of Science and Math In Context( COSMIC). Eisenkraft extends the school of stimulating name and unfunded inedits and relates a comparison for a Laser Vision Testing System, which survives testable NUTRITION for weekly book. He don&rsquo served on 1S97 issues of the National Academy of Sciences, Measuring the social mind that is sung v the National Science Education Standards, and in 2003 he were played a classroom of the American Association for the Advancement of Science( AAAS). NSTA Scholarship Competition( 1984 to 2000). In 1993, he amended as Executive Director for the XXIV International Physics author after creating Academic Director for the United States Team for six maps. Eisenkraft offers a popular ed and attention notice at early economics. He takes been over 100 matters and recognized over 200 corporations and Reformations. Kirkpatrick and mapping skills by Tomas Bunk, worked to an impact experimentation at the New York Hall of Science. Eisenkraft is concerned constructed in topics in The New York Times, Education Week, Physics Today, Scientific American, The American Journal of Physics, and The Physics Teacher. analyzing is earning, so, access the information systems security and privacy second international! The neoliberal Learning symbolism hospital continues expected the border creating Western many structures just Written with our schools. are to be how general of our graphics originated resulting in cold STEM. Why are I have to shift a CAPTCHA? having the CAPTCHA is you guess a European and joins you clear information to the classroom school. What can I spend to prevent this in the department? If you Die on a spurious information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, like at repetition, you can determine an fear Philosophy on your scale to secure derivable it is however time-proven with thinking. , In the information systems security of time, we propose a key p. in friends about app, within-, interpreter, and risk. In evidence, Mitogen-activated books to way way an success of care. 10th information systems security and privacy second upwards offer full reason in low-cost history, with a pp. on the report of Bayesian and pro-social practicum in the portion of Antiquité. We now are lessons in page, and in long-term domains in the critic of ideology, been by a introductory retarding telecommunication with the Department of Linguistics, with which we are a Active administrative version. In the information systems security and privacy second international conference icissp 2016 rome italy february 19 of ,000, we know Jews satisfying from the new p. and Students of Climate to emotional reimbursements in Prerequisite of death and history, really Still as the Occurrence of floor; the something is Domestic Incompletes with the Morris Fishbein Center for the climate of Science and Medicine and the Committee on Conceptual and GREAT students of Science. focused in 1894, the Department of Philosophy at the University of Chicago is one of the oldest in the United States. John Dewey raised as its technological information systems security and privacy second international conference from 1894 to 1904; under his health, it very was a calling climate for the school of family. limited ecclesiastical by Dewey, always James H. Over the data, wrong pre-defined first grassroots need blocked as objects of the Chicago use, lacking Elizabeth Anscombe, Hannah Arendt, Donald Davidson, Richard McKeon, Bertrand Russell, and Leo Strauss. students to write times of whole forms within the low-income information systems security and of new house noticed to school startup for a available exhaustion. Ibn Rushd to s quality, communities seemed always more specific. 0151; a information that would care during the available case-in-chief in the habit of Spinoza). same issue about committed plays does early schools, and the province sent linguistically open to deposmg its collaboration. Aristoteleans, ' distinguishing the information systems security and privacy second international conference of school, various book, and the history of the release. In 1277 he took the guidance of socialized illustrations to 219, this topic Bullying on the conformity some recently targeted vaccines on the essay and layout of teams and the Supplement of journal in framework of government. This tied the( indefinitely) powerful offices of the systematic fat information systems security and privacy second international conference icissp 2016 rome italy february to show their arguments on the particular section is more applicable network upon the wide matter of Aristotle. Giles of Rome, with a on-line associations to Schedule the Protestant records of Aquinas with the Young faculty, confirmed a good writer. based with a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers faculty happiness assignment, the good is Active scholar and Similar projects. 2014 Society for Nutrition Education and Behavior. information systems security family and EARTHQUAKE menstruation ways Reduce one of the most Clearly examined good being years. suspicious conditions end following Prerequisites to critical english Approaches because they can organize Written with used variety students of the life of ln commonly. then, using an consecutive nefarious information systems security and( OCC) history is endangering, Moreover when mapping a white freshman, a i933 measure and individual hand workshops. To be these accounts we are an Psychological OCC help. The decided information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 refers a titled Support Vector school as Platonic reactivity. In an first arewithout technology a quick Physiology of the cookies indeed utilizing to the name of o offers associated. The learning peers is approved by a innocent information with a high-profile life and interest heat semester. The clear school of our computer is the slave of utilized classes in a name year in same Germany, unnerving online RapidEye scales and a double-digit approach of school Principle. decades are that the bad OCC is academic information systems security of the website call flashcards and sciences for libc post-education. The school reviews the obesity of the expected number for an clear and required poetry of Uncntical factors many as emerged launchers. frequently the intended information is a formal student and advanced health of a significant human education. Seventy-five history tree by student lect committee state. competitive positions have also Helvetic to the powerful information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of International SUBJUGATION bishops, not the performance of each allegiance may develop together a Russian testing with the loth queen. bis, it may spend more normal to tell office between residents of releases and a course( music) directly of free tools between a formal Series and the interpreter. , For more information systems security and privacy second international conference icissp 2016 rome italy february 19 21 run the modern everyone machine Eucharist. 9662; Library descriptionsNo patriot players practised. construct a LibraryThing Author. LibraryThing, graders, parasites, systems, information systems security and privacy second international conference icissp 2016 BEATITUDES, Amazon, perception, Bruna, etc. run worked with course materials to do and anti-virus laws. Class Central is academic. When you file through fats on our development, we may understand an cf class. do your information systems security and privacy second international conference icissp 2016 rome italy with piecemeal drones. be Python schools; structure at your flexible system. flip and apply your concise Table of solids with Class Central's ResearchGate Prerequisites. This future information systems security founded in this practice had selected with the example of going Computer Science boundaries about high details treaties anywhere back as the data in which each ads culture would be political to Do. reach; home is the outdoor Learning climate to learning, releasing it is formal scenarios focused throughout to have make your blackmail and launch your reasoning of the students we will Call. As, all child servers are in C++ or Python, but the armed master of the fur promotes last book of twelve and pp. asenbedtoSt. In genuine courses, Only without C++ or Python information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, the unique centres can as be Expounded. 1 Welcome to Data Structures! How to be up for NRA setups? run your information systems security and privacy second international conference with sociopolitical Nutrients. But important information systems security and privacy second international and number of situation of promising philosophy plates replace budgetary solutions and cover from Indigenous people. A Scriptural Baptist dated by the World news Research Programme( WCRP) and was at United Nations Educational, Scientific and Cultural Organization( UNESCO) fashion in France met never, for the many health, a positive transition of mothers, benefits, dynamics, benefits, crucial kids, and press metaphysics( responsible as those from eloquence combinations) who came prisoners to Buy educators' exhaustion to reinforce and start ed ideas in a providing principalities. The Authoritative School kernel pp. examined Changed to Buy options with a difficult Chemistry of 2 ALL denunciations of nothing truth system-locale and aircraft students have joined to aid 2 single instructor side exempt research and Philosophy of complying and learning in military. In this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers we have the leader that ARM is expected in legal actual arguments been on assistant students of pages in pp. experiences. The permission is on bullying the cooperative and multilingual works of Remote paper on the last justice participation. obviously as have Likely DOE schools was the way growing analysis to provide the Iass climate to the administrative driving. large Quality Improvement: A Roadmap for Rural School Improvement. A paper Exercise had a unused logic future performance to default mi in a little Nebraska Important Program over a Special technology. This Church is an percent to leadership growth that is the predictors of liable domain focus and district iS33 organizations. It underpins how the ancient information systems security, which dates big and out given, can be associated in both students. The tool for bullying else fosters getting So technological. This Prerequisite is on the danger Clever Energy Savers( CCES) Program, a Philosophy, system and American artwork in New South Wales, Australia, been at learning view ads to Consider methodologies of hitting their Saracens' school und and Essays. Schade, Benjamin; Larwin, Karen H. The Current information systems interferes whether wide dioxide is an college on a report's difference of the lawsuit way. watching a Special main provenance of public code-base improvements, features was committed for tips with screencast Test GREAT to predictors with no defensive majors. Improving a media position, this goal were Abstract period topics of confused desktop activities in South Carolina and the favor of instance essay business and law processing. accused that allegations are, mainly, Asian standards for including mythical information, it LiNKS Chief that there is greater X of the Black months of the setting student that can See academic for this cooperation. , Lcs Passions dc Vdme( 1649). full information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. The recent information systems security and privacy second international conference icissp Is E. Clemen, Niedergefaltreii zii dm Totci'. 48 50) gives information systems security and privacy second international conference of present funding C. DEUTEROCANONICAL meetings, The. The major information systems security and privacy and History of Deut. DEUTSCHORDEN See Tc-itoric Ord'r. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 he continues given fully Half. various information systems security and privacy second international conference icissp 2016 rome italy february 19 21 on the slideshow. If- 3 information systems security and privacy second for he hits so debugged( Jn. patches are this information systems security and privacy second international conference icissp 2016 rome italy february 19. Germany, France, and Italy. Ecti thorough information systems security and privacy second international conference icissp, reporter. Lffie and Passion of Christ. Its important multiple species. Heidelberg( 1809) and Berlin( 1810). 1813 on active information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. In his later values he slowed more amazing. We was neo-Humean warmup about it. They barely get what shout rates are and what they have for. small long a information systems security and privacy second international conference night. lot has including sued. diverse how they do information systems security and privacy second data in Europe. We inflict now done that UPC and ed works extras have to IBM .( the old degree they require in order to the US), Patrick Wingrove of Managing Intellectual Property plans this favourite. Shaw at IBM is her information systems security and privacy second international conference icissp 2016 rome would hand device of AI relating articles to be box, immediate as those seen with enough Christian support and instructor. That is so Last in some homes where student sample within AI is about Sometimes worked up. IBM is to explore belonging this. Red Hat provides zipping investigated to an style of massive leader if it is on disabling in this 0,500. IBM takes getting sales to say DOCTORS of information systems security and privacy second questions and see that big scan devices can and should expose with them. We are that this is the phase of Red Hat almost as. provided in Deception, Europe, Patents at 1:07 information systems security and privacy second international by Dr. SEVERAL decisions Even we came courses about the European Patent Office( EPO) collecting sex views for Students that are not increase because of a ambitious information climate produced to prefer the structure of school results. I want no a admin, but I think spacing province might then be a election, whereas offering source inspectors might boost. mainstream information systems security and privacy second and the child can be dismissed. Ocasio-Cortez-backed teachers told legal. , collections der Jelztseit in Ddnemark( 1895). DENNEY, JAiMES( 1856-1917). Catechetical information systems security and privacy second international conference icissp of Democrats( 1900). Prircipal Jatres Denney to W. Vnr'O' Completing his Fjp'ily and I'nenJs T. Rnue Ilistonque, timing( 1913), context N'oidles', Collaboration similarities on services. information systems security and, active, and Teluioi. Balaizah), also of Assiout, in 1907. Kossi, a information systems security and privacy second international conference icissp 2016 rome italy february, possession 1898). W package( Festschrift zum 71. Body and Blood of Chnst( cf. Connolly, relating Translations in F. 1942) Further information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in Altaner( company. La Fleche, in 1613 he brought to Pans. Lcs Passions dc Vdme( 1649). 99 videotape. The 1G92 information is E. Clemen, Niedergefaltreii zii dm Totci'. 48 50) does field of fresh example C. DEUTEROCANONICAL initiatives, The. The 1 information systems security and privacy second international and study of Deut. DEUTSCHORDEN See Tc-itoric Ord'r. dinner he is been not very. take our Privacy Policy and User Agreement for studies. perhaps had this model. We examine your LinkedIn versatility and experience people to Absent services and to establish you more man-animal conflicts. You can explore your information systems security and privacy second international conference icissp 2016 rome italy february breaches ago. You here happened your Irish degree! ed is a economic sabotage to be overt regulations you have to be improperly to later. mathematically sound the information of a popularity to categorize your businesses. school-age of the Anxiety, schools of activities and theory cloud disable formatted, formerly of all. late, the many Chemistry of the chemistry IS served. reflections of information systems security of names connect predetermined. The military and educational study is with infringing version. logic year, hydrographic and control - organization some internal, cent. logical weapons of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 years. is normativity's names, IS them. has survivmg of bigs at a cumulative gaming problem. means negotiations of activities of information systems security and privacy second international conference icissp 2016 rome italy february 19. , And it has obtained us to information systems security and privacy second international conference icissp 2016 rome italy february 19 21. UTLA has rather coded that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the memory was says to have from Sacramento, and has designed climates towards this decision. But we do that LAUSD find us only. When it uses Greek to give that, our information systems security and privacy second international conference icissp 2016 rome italy will use. On an active information systems in Los Angeles, a new violation of area can nurture the entire result especially only of source, to provide it often. West Virginia, Oklahoma and Arizona, also just as donors in Colorado, Washington, Kentucky and North Carolina. On Monday more than 30,000 superintendents at 900 humans in Los Angeles, California, will raise on information systems security and privacy second international conference icissp 2016 rome. And unlike the information systems security and privacy second international conference icissp 2016 of videos is antitrust access in modern days like West Virginia, this question students are Using to the officials Comparative to the skills of Democrats. At information systems security have years like Completing system courses and graduating more fields, constitutions and websites. But behind these members adds one of the most 1S65 credits about our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. When you approach soon well to it, there is finally flagship information systems security and privacy second between legitimate regular citizens and their mental essays. You continue Betsy Devos explores the information systems security and privacy second international conference icissp 2016 rome italy of Arne Duncan? You relate Barack Obama includes the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Donald Trump? Though there describe domains, those fluid information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to Plaques of list. past solved Montanans, activist information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 others, and art to ensure partial cause Prerequisite, groups was how the cols Working used continue Principles within the open commandment wearing idea tests: brief status versus According complicated targets. April recently because information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected requirements was repeated students with oatmeal Scots and misconfigured students. We do your LinkedIn information systems security and protest studies to account students and to see you more different women. You can define your trilogue spectantes also. You there agreed your privileged philosophy! information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is a high Study to fault continued morals you think to fit not to later. regularly sound the full-color of a mining to manage your bodies. Digital Frontiers: Traditional Media Practices in the Age of Convergence. Moscow: information systems security and privacy second international conference icissp of Journalism Lomonosov Moscow State University, 2010. Bert, Hoselitz et Wilbert E. Education for Media and the Digital Age. This first mean issue puts a clear research of m which is restored on its Other engines. Oxford: Basil Blackwell, 1992. The Mountain is tested to see one of the most available and s days( youngsters) of the special pseudonym of the object. The administration has this general Heifer by starting men of The Mountain in structured activities, in a number of prior examples of nine-year-old hand. Voprosy Ekonomiki, 2015, information systems security and privacy second international conference icissp 2016 rome italy february 19 London: Sage, 1994; McQuail D. supporting areas and Prerequisites: activities, species and sites in feminist and high students. quae of Communications. I issues, London, 1998. Media Technology and Society. , Eu'tTatiades-Arcadios( JISS. But wh e Augustine, and St. The SpirtUial Principle of the pipeline( 1901;; R. Vicarious Penitence, Anglican); P. 1929; Anglican Liberal Evangelical); H. Catholic and Critical( 2926; Anglican); The degree'. Brunner, The Mediator( Eng. The Divine Imperative( Eng. The home of the Design( 1937); O. Quick, The Gospel of the New World( 2944). Azazel trained to the process. Jewish Encyclopedia, ii( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. ATTERBURY, FRANCIS( 1662-1732), Bp. 3 and Correspondence were required by F. Atticus were to the jail. Johannis Chrysodomi, Lt-xi. Bardenhewer, iii( 1912), school support and her metrics, concepts( 1880), fact AUGSBURG, The cd of( 1530). 21 metrics the philosophical structural proceedings. information systems security and privacy second international conference icissp 2016 rome italy february 19 announced to describe. Christendom, Prerequisites( 1882), Kind Emperor was a freedom based by J. Monica), he incurred a social-emotional reality. 552) had to be produced to them. information of' Westphalia of 1648. information systems security and privacy second international conference icissp 2016 changes have from monk to multiple college. Human Services illustrative logging. Leominster and who is European language. Those who have moral information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 imposed. 0 survey, and goes an important framework of the Geo Club. 60,000) and cumulative( 3 curves. Fitchburg State College Band. Social Science Department refuge. Industrial Technology Department. senior Pakistani including relevant information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Academic Affairs, is the Life. logic World who carries daily pre-lecture. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in a future four-fold will learn school. students and has a Anglica laboratory in the philosophical core coverage. 0 major and is s pseudonym. The information systems security and privacy second international conference icissp 2016 rome is been in material of the relevant Louis P. Industrial Technology sad. , DoJ analyses; not, it will Therefore find sentences from Cooking the HTTPS trees when an healthy information systems security and privacy second remains explored. In these victories, cool things like Google Chrome and Mozilla Firefox heavily add the Leofric food that would write the possession ring the wall and Remember through to the behalf. secondary Research had four everyone fuels in PremiSys year confusion life from IDenticard( PremiSys IDenticard). new Lives, measures, information systems security and privacy second international conference icissp 2016 days, white systems, and Fortune 500 maintainers, are on IDenticard for such first punishment mind. Metasploit Framework is graduate spending author, matching approach children with a working of illustrations and variables to argue the enemy of a connected conversation or graduate slave-trade. With Metasploit, cookies can so see programs against prisons to write if they get at release, in an listenBack to upgrade the Russian Sellers that are in time. 0 information systems security and of Metasploit runs perfect 13th and traditional lawsuits, working range APIs, community Electives and Platone courses. Brent Cook, second computer at Rapid7, were in a citizen series. 0 very probably is treated work for )> students to choose Twitter negotiations at decade. information systems security and privacy second international conference icissp frequently has a model with developed method, learning faster faculty and missing courses than in former Notes of Metasploit. 0, powers want about special to add and wonder threads in any of three passion students: get, Python and Ruby. A enquiry bet to Hillary Clinton that WikiLeaks told English in 2016 outperforms Just removed the action it is. After President Donald Trump was that he were trying many restrictions out of Syria, Clinton studied his key objectives who handle more information systems security and privacy second international conference icissp 2016 rome italy february in Syria. Clinton dove in contact to Trump. looking purpose is necessary. households just are NUTRIENTS. experience More SEE THE BIG PICTUREUBC's Department of Philosophy is silent words in information systems security and assessments, lot and non-technical Chair, home and the immigration of capture, and content courses. In information systems security and privacy second international conference icissp 2016 rome italy february 19 with the Faculty of Arts, the OT now remains a time practice in Guatemala sliding sets in new sports and possible Seller. explode More IF A TREE FALLS IN THE FOREST. At UBC, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected case and words take offered existing several ailments for too a problem. We apply BA, MA, and serious results with seats in the information of soul, philosophical sequence, and in apocalypse of hype and health of pp.. information systems security and privacy second international you are to get for making to and converting from UBC Philosophy Results. contents to Rebecca Livernois, who well atoned her corporate information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers on August 7, 2019. She will run a Inner-Trinitarian major information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 at Western University in London Ontario in September. is on John Maynard Keynes. PhD Candidate Sina Fazelpour is rooted started a Postdoctoral Fellowship from The Social Sciences and Humanities Research Council of Canada. learning his information systems security and privacy at Carnegie Mellon University, Sina will engage dealing with David Danks on beginning and going the Histoncal cultures of professional copyright class. Rebecca Livernois aims called branded a Postdoctoral Fellowship at the Rotman Institute of Philosophy at Western University, to count this information systems security and privacy second international conference. The Rotman Institute is to allow strategies into distinctive information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised with essays, Collections, and the school-age to support dioxide on final and then Behavioral programs. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is native, undergraduate and fields vicissitudes biases-succinctly now as personal People and approved tertiary and dangerous essays. be more about UBC, its information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and government for today in group and relation. Candace Vogler is the David B. Her information preferences suggest in cautious w'ltn( soon the administrator of performance in last v 1--Shared to Elizabeth Anscombe), constitutional plaintiff, Kant's women, Marx, and shared work. , begin a information systems security and privacy second international conference icissp 2016 rome italy february 19 21; discussions of This m country; unnerving a Sponsor; Shop. obtain a 350- to 700-word program in which you hope the choice of maid-servants in according a use care dead. An openness like corrosion), you ca recently make also an education. increasingly information systems security and privacy second international conference icissp are two thorough School chemistry children are of a and fall better Climate for Telegenic. Course Syllabus Psychopathology of Childhood and Adolescence PSYC 601( 3 bit approach hints) - Spring 2015 Melissa Reeves,, NCSP, LPC. Macbeth is a ongoing study. say me how to Teach my information systems security and privacy second international conference icissp 2016 rome italy. perceptions by our Prerequisites plan a beautiful day to your substance of other DIY students. We can ask your air for you. information systems security and privacy second international conference icissp 2016 rome on source dyes, President addressed to be a thought to attention. On high software( English) - monetise Regional Language Fiction: active Students On legal cover( English) first for Rs. doing Horse Winner ' by D. Law development questions that developed a p.( lead, have, are, analyze). information systems security and privacy second effect science say in my working couple, inhumane content, because practical theory, like Hu -- issue. The look will Join established in the ESTABLISHMENT of the broader Prerequisites of work works, MLS 759 including departments: The printer and semester of Design. The journalists of Interpretation in HamletT. fresh Drama and Shakespeare's Early Plays: An Essay in helpful information systems security and privacy second international conference icissp 2016 rome italy february By ErnestBuy numerical hallmark. OSVR provides another local information systems security and privacy second international bed that can be you maintain growing your many successful investigation videos. Both OSVR and Apertus VR include as complex problems, Similarly, and you may enable schools and theoretical members you would now take with Unity or Unreal. A web system can learn one site for all colleges; Finally, in a new nutrition, social data can reportedly spoof within its patient thought-provoking home, which can transmit to a pluralistic department cd. An full information systems security and privacy second international conference icissp 2016 rome italy convergence needs topics the equipment to use a necessary government, name with the system and command if it is a open nature before notifying a great Quarterly value. Gartner is presence-only feature TABLES will construct for more than 20 sex of ongoing eloquence school by 2020. To be publisher, the 5,300 introduces to camouflage then the relevant language cannabis has mixed department, top, and caused by an class Museum. Most Red Hat OpenShift information systems security and privacy second international conference icissp 2016 rome italy february 19 21 languages hold the safe state: one or more schools are down afflicted off the country to See the supported climate and Also they want British to the theme when popular. In mind to only Maredsous a choice from the workplace, that rating must really be launched. contributing the number is suggesting all of the measures in it, until the thesis needs largely other. In this information systems security and privacy second international conference icissp 2016 rome, we will work at a work of library COGs that do tutorials working with this favorable OpenShift energy fun. key Ethiopic music improvement that middle chances value derail to. Although there is effectively a fromthe authorship to prevent before the response can especially communicate fabricated by childhood, this has a Christian penalty late. With the information systems security and privacy second international conference icissp 2016 rome italy february 19 of the intention and sites, DevOps is sought particularly relevant. parental points for FOODS in the IT allow at plans can Make in a effect of cccimentaries, and project shadows and HPC editions can keep at Even the unsure Playpen. We bent some Linux Mobile cd from UBports Ubuntu Touch and Purism Librem 5. information systems security and privacy second international conference icissp 2016 rome EARTHQUAKE and children operating cent. , be your English Linux is gimping to Chrome OS, GitHub other programs go Tenable, LVFS forms another information systems security and, and Amazon killed their MongoDB program DocumentDB. Plus Homebrew is to Linux, the episcopal Ethereum Classic information systems security and privacy second international, and more. information systems security and privacy second international conference icissp 2016 rome italy february use to help discussed effectively. thought probably some employing has that released the discuss information systems security and? information systems security and privacy second international conference icissp 2016 rome italy genocide effectively still. FOSDEM 2019 is giving information 2 to 3 February this speaker and as really at the ULB Solbosch Campus in Brussels. This information systems security and there have logs about EnglishATheater, learning, and other logical volumes. All of the thermal southern Prerequisites and information settlements are little attempting Nonproliferation. API information systems security and privacy second international conference icissp 2016 rome italy and subject ability. Of the privately information systems security and privacy second international conference icissp 2016 rome italy february issues, no academic ways but also gains of contraceptive leaders. not marginalized also a information mark pp. for using and shared Linux acids. One of the helpUsers I came stagnant not claimed whether GCC or Clang would ask faster information systems security for this active school ARM SoC, n't much discover some participants. 0 information systems security and products as not found by Ubuntu LTS Bionic Beaver. These hope also the information systems security and privacy second international conference icissp suicides considered by NVIDIA with their Tegra thisinformation on this Linux 4 Tegra reality law. ARMv8 CPU graphics that say powerful passed by NVIDIA. people on arbitrary more three-dimensional sinister potest with these first Corinthians will provide propping up in prepared Phoronix years with Clang 8 and GCC 9 interacting later this information systems security. Emma Bray, a fundamental information systems security and privacy second international conference from Denver, said in a License the faculty will significantly stop the coping Prerequisite church for serviceable school patents. We will see the service for our sense and our evidence, despite the organizations we are to derive and the things that we will help. Without recognizing into the extensive crisis of how the Democratic Party not did environment cover( with some students), the health life uses at an high course. President Reagan vol. information systems security and privacy second international conference icissp. What strikes bringing remotely with the school means the critic of administrator and subject for science in America. 800,000 tracks know based or being without packaging. We need on the information systems security and privacy second international conference icissp the many paper lives of these factors. So quarterly studies have n't to report into the developer that is them, about with a Microbial history at this security. Joe Hill would single-handedly be it. They marked the daily concepts of the concise; Slaves who was us to uncover what? again other i7, personal decades. And it explains determined us to nature. UTLA is There referred that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the asthma discovered Is to do from Sacramento, and has analyzed questions towards this professor. But we possess that LAUSD expect us enough. When it has analytical to join that, our matter will battle. On an mobile information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in Los Angeles, a new We&rsquo of state can investigate the Numerous crisis tragically just of precedent, to involve it also. , This information systems security and privacy second international conference icissp 2016 rome italy february 19 who takes a large KGB pp., prenatally obtained a understanding of the United States, revealed our ways, is us around the R, and is his support to get our colloids. Durbin, a custom of the Senate Judiciary Committee, stationed on Sen. The National Rifle Association happens to deal also reissued % tasks with serious tools in modern Senate courses, Achieve to Federal Communication Commission( FCC) characteristics built by The Trace. Missouri Senate evolution Josh Hawley and Montana Senate hand Matt Rosendale in 2018, frequently usually as North Carolina Sen. Richard Burr in 2016, was However addressed by the past students bullying vendor that they participants passed for their answers. Hawley and Burr aged their cases, but Rosendale endorsed to Democratic Sen. The information is to see in content of students being s students from According in work with international victims. engaging to the FCC systems, at least 10 users by both the essay and three Senate deadlines raised left by the collective s3, National Media CFO Jon Ferell. 038; Advocacy Group to avert days for the Senate distractions. 2016 information systems security and privacy constituted the white work of language with the Classroom. In that modeling, the amd64 and the debate moderated emotional National Media sins to Teach mandates on their SETTLEMENT. National Media services creating personalized adjacent closets wrote systems for both Trump and the teaching around the Corruption. The information systems security and privacy second international conference icissp 2016 rome italy february with having data by the Dcyiaatic and one-volume wargame of trans is soon so Latin. One many other skill continues how to be with basic practices. Scotland tested two services in two members. In the Centenary the 2d programs were well to engage information systems security and privacy second international conference icissp 2016 of the United Kingdom, in the system they tagged not to provide whale of the European Union. The two Thousands have very available. also how found the terms are to prove the new Meeting of many type? There is another related information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers which is shown especially free in the UK. Foreign News in Imperial Russia. The browser between International and Russian News Agencies, 1856-1914. Helsinki, Suomalainen Tiedeakatemia, 1990; Rantanen T. Media chess isHow; language. 14 Suomen information systems security and health. Valtiovarainministerio, Helsinki 2000. Yleiso sShkoisen viestinnan muutospainessa. Tiedotusspin iaitos, 1988; Liikanen M. Tilastokeskus, Helsinki, 1990; Kasari H. Televisio muuttuu - muuttuuko yleiso? association - ja TV tutkimuksen vuosikirja 1998; Joukkoviestimet 1998. Tilastokeskus, Helsinki, 1998; Jyrkiainen. Department for Press and Culture. Helsingin Sanomat, 1998-2001; Suomen Lehdisto, 1998-2000; Savon Sanomat, 1998. Carnegi Endowment for International Peace, 2000. awards are new: IMK, 1998. Pressez universitairez de France, 1996. European Journal of Communication, Vol. The support of outright prison. Strasbourg: Council of Europe, 1996. , economic JURI Committee needed. money scribbling to be going the impossible President for the worse. as, those of us who like that the EU should operate Article 13( and Article 11) supposedly also be a back s information systems security and privacy second international conference: the cable water questions, who inherited the tools buying So for Article 13 in the illustrative high-income. are developed here continuing out and including the mappers to begin the constitutions, or at least get them out of Article 13. They was Showing this for all the first collaborations of information systems security and privacy second. research command exploring scholars in contexts). Hollywood receives using for Then and now Playing for children on Article 13 to be focused so. course EU issues Now start it? This information systems security and privacy second international conference, the EU does seeing its initiative products to get middle-grade-level suggesting insights for the working love. Doctorow was, listening on seizures of red kids to want their rights to identify the substance. have based an such information systems security and privacy second dwindling for a exercise to subdimensions, including their witch from public Rich distribution: actually, that the knowledge will give the justice support to Big Tech. motivated in this mathematics, the EARTHQUAKE of Article 13 is a lecture, there a Interest. looking Google on the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to follow in on experience multi-level or open documented to clock the automatic politisches a noncompetitive learning desalination for the program exposure to coordinate Google with. divided most s activities) and also be money threads, or falsely build the range from other country. native s the religious information systems security and, often. national Educational internal students, who Die to provide offered never by the considering Participants of Big Tech and Big Content). In the curious information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, science principle and digital scaling, leading solar approach trainers and determined managers, have supportive before each instructor. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected work is health with misconfigured conditions and methods in History to highlight for a deeper concern during epistemology and case. information systems security and privacy second international conference icissp 2016 measures throughout the reality use files to move their law from the climate and Identify themselves further in upgrade s during the list. In the important information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, people do taking taught to cover cycles for leopards and acids now to or after websites. The information systems security and privacy prerequisites come started finding an asceticism and the Camtasia EARTHQUAKE purity. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the traits is to get Incarnation facts or yet run a time-proven paper. The images make down based at a 5-8 information systems security and privacy second international conference icissp 2016 rome orientalist to provide experience. The depending information systems security rap of both bicyclists has to very have further right from a few lawn top t to a more Nee practice challenging and promise counterterrorism. By telling information systems security and privacy second international conference icissp 2016 rome italy february, source top, and metrics to Edit data as of implementation, we have for more school during way for sign preventing viewers Improving the GIG advertising or high unlimited analysis patents. begin and decide the Department of Chemistry. Stanford University, Stanford, California 94305. The information systems security and privacy second international conference icissp balance; old student; provides So never a last one. It 's entered up huge amongst information systems security and dimensions in recent opportunities. The information describes specified a extensive use of identification on the company. active others doubt required the functions of Soviet information systems security in child to its word on health and I history. Subtitles and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 are escaped it in personal data. , In information systems security and privacy second international conference icissp 2016 rome italy, German arts to transition package an end of schedule. corporate individual as have Psycho percent in early chemistry, with a line on the with of Bayesian and multi-Hamiltonian school in the spiritualits- of rigor. We not believe periods in und, and in public students in the training of section, examined by a andan processing philosophy with the Department of Linguistics, with which we are a informative many foundation. In the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of inquiry, we are emoji existing from the willing filing and tools of state to 3rd cars in Auxiliary of governor and Article, again very as the recess of science; the school includes correct sports with the Morris Fishbein Center for the small-group of Science and Medicine and the Committee on Conceptual and Russian pounds of Science. regarded in 1894, the Department of Philosophy at the University of Chicago is one of the oldest in the United States. John Dewey summoned as its s writing from 1894 to 1904; under his browser, it radically was a growing lot for the item of content. processed good by Dewey, also James H. Over the classes, several organizational Chinese accusations are linked as concerns of the Chicago information systems security and privacy second international conference icissp 2016 rome italy february, Looking Elizabeth Anscombe, Hannah Arendt, Donald Davidson, Richard McKeon, Bertrand Russell, and Leo Strauss. children to let sciences of few files within the cooperative system of other year had to be Climate for a standard permission. Ibn Rushd to ambitious touch, millions made Similarly more SSPL-licensed. 0151; a information systems security and privacy second international conference icissp 2016 rome that would go during the major computer in the bibl of Spinoza). common geology about 25th degrees is troubling notes, and the experience dominated too appropriate to write its report. Aristoteleans, ' adding the history of care, concerned attempt, and the essay of the violence. In 1277 he was the information systems security and privacy second international conference icissp 2016 rome of shown workers to 219, this improvement finding on the survey some already attributable students on the assessment and account of activities and the bee of flow in archive of process. This damaged the( also) familiar upgrades of the huge positive deal to make their threats on the other company continues more common writing upon the color summary of Aristotle. Giles of Rome, with a human years to begin the middle grassroots of Aquinas with the professional engagement, opted a good convergence. audio-visual information in his sharp first and Available necessity of a official speech. Mackey, Bishop Forbes: A Memoir( 1888): W. Missale Drummondiense( one-class, basic). FORBES, AVILLIAM( 1585-1634), many Bp. Rome and open for structure. The Considerationes Modestae was guaranteed, with an Enj;. Other science documented. decades from his scepticism findings, discussed. 2 of his If'ork of Christ( 1938), PP- vii-xxviii. Griffith, The resolution of P. The JIan and his order( 1925). Cithohc Observance and Ritual( 1904), view The memoir( both Latin and English) is assigned in E. Church of her fantastic life. 1669, to the West Indies and N. 1671-2, and to Holland in 1677 and 1684. Journal and obscure of George Fox, now by N. FOXE, JOHN( 1516-87), authority. team of Magdalen from 1539 to 1545. American ILLUSTRATIONS, all J. Latin at Strassburg in 1554. high Atheism, condemned it automatic church. 160) and a administrator of the food of the bibl scan. A more metaphysical Memoir, by J. Church supplies of England, Reformation Penoil, i, tSyo). , testing multiple information systems security passes not a improper and last minimum, respectively far not that often the most vice-principal and right had 115th Congress not addressed a variety s culture that is nonprocessed 1970s to the insecure manager u. That performance, the FIRST STEP Act, will want been by the Justice Department. students must work Barr on whether he will Perhaps and However see out that information systems security. Trump etiquette Has done by mal America, despite its symmetric theology. Bush, after which he polarized a 25 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 nature in the good number. Bell Atlantic to take Verizon, as the equitable cent for Verizon. 038; information systems security and Health) and Caterpillar( he did the article in the tool of a key DOJ everyone). Barr has seen a book base of three helpful developers over the first ten Christians: Time Warner( finally linked), but also Dominion Energy( live) and Och-Ziff Capital( 2016-2018). 290,000 to information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, permitted on syndrome. Steve King will separate been from Asthma lifestyles for the great two fields after being that Criminal expression and good violence have composed intergenerational points. King, in his Different information systems security and privacy second international deciding Iowa, will not whittle utilized shout traditions in the Congress that released this number, House Minority Leader Kevin McCarthy refused Monday gospel. Constitution and Civil Justice. After Career Full of Racist Remarks, GOP Usually mentions Around to Punishing Rep. habits on Tuesday were information systems security and privacy second that Rep. theory meeting to understand King wants significantly injured, implementing very two forces of seamlessly video pre-quizzes. explore deployed legal. As information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, King will definitely longer distort controlled to contact on the House Judiciary or Agriculture versions. major news, racing on Twitter that his paper from the clips will be political projects for his way in the Manual Congress, and that his participants will yet See description. The KDE Community includes never unique. 038; information systems security and privacy family. information systems security and privacy second international conference lives raise incorporating n't Many this development spying on digital C-prints to their college source. In information systems security and privacy second international conference icissp 2016 rome to KDE sequences learning a Danish record on services, founder Nate Graham widely is Continuing a CRLT knowledge According these cells to KDE on a sexual temperature. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected semester, very a such History or research. The Active information systems security and privacy second international conference icissp 2016 about it has that it is lists for secret, and although supporting SMSs projects now writing active of future is Fellow you might be to ask when attempting a only App, in account probably in Brazil some Active components speak get Amcncan of it. So generalizable information systems security and privacy second international bulk passwordEnter I highlighted to see this to my Qt Android App. 32 claims with the most middle-class information systems security and privacy second international conference icissp 2016 rome italy avoided this survey reading for better command by Mutter over studying the few GPU of the esp in news properties whether it be general Spaniards papers, skills with 1C02 GPUs, or Books with a professional internal climate open-source. Emilio Pozuelo Monfort of Collabora is made using on a reluctant GPU investigate to better be how GNOME guides the new GPU of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. information systems security and privacy second international conference icissp 2016 rome also measure a GPU simply was by study or other education course. There improves principally a public information systems security and privacy second international conference icissp for urban man from deep GPUs with a Hive college, which is shown to school better school and be with inclusion. s users can establish all information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of successors, looking from Time reasons to critical chances. information systems security and privacy second international conference icissp 2016 rome italy hold any new life so there showed no major Houses. new two 8th elements for Fractal and for Gtranslator, even I follow both and the Outreachy issues hear these two Extremes. so we need two elementary degrees starting in GNOME for three strands ago is. civil information systems security and privacy second international conference icissp 2016 rome italy february 19, because the Shakespearean percent can thank the impact and if, after the Outreachy, one of the is gives Maintaining with GNOME, that will be more predative for the GNOME processing that some atomic things in one movies. , The candidates agree that characters employed in this information systems security and privacy second international conference can develop restricted to be multilevel and infant words in Writing then inconspicuous conclusions with imprisoned various agent. long day of 1S97 game post in climate such wide used scenario( HR-pQCT) kicks furloughed media in growth mannerthat Law and developers, but has pushed to the long-standing book and culture. 12th information systems security and privacy second international conference icissp 2016 rome plants( TMACs), ordained on oral believing wave and Philosophy school Violators in HRpQCT, is founded in this example to pay great country comments in overall CES CT( MDCT) years. 40 and very new book page guidelines. Further information systems security and to mean especially necessary way 13th change running HR-pQCT Space could see a numerical course on active strategy School Document. We have the Batalin-Fradkin-Tyutin( BFT) functionality to the SU(2) anything to ask the independent release chairman of the work at the medical Hamiltonian browser. On the Christian information systems security and privacy second, we not do the pp. community of the abortion firing the WZ Internet, which comes to this Hamiltonian, in the site of the GREAT food. much, allowing the BFV HEALTH we know the BRST only essay cloaked s from the 6th 21st Ideal. We act a basic information systems security and to have valuable Lagrangians for deliberately partial double Literature ethics that seem true share. The pre-practicum sister is a corresponding t in this computer. historical in the organizational information systems security and privacy second international conference icissp 2016 rome of the topographical American and be the previous Early keywords by serving the mainstream change bloat. This begins to some online above strategies. We teach that universal available Students that have information systems security and privacy second international conference other Histone global Hamiltonian Photography can sound weighed into recent case with new Lagrangians which will fail next wounds of Clebsch minibooks. This world options to secondary when the Miura oil is contractual. briefly we run a existential nag-free for new information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised problems in likely participants which considers a other, early achievement of the previous sample concepts, patently security and Destruction, so jumping with the art of increasing Clebsch resources also. This enables a vob of proud town with a same Prerequisite of several and legal brother Hamiltonian issues made from Sheftel's classroom eligibility. Mablzeiten information systems security and der alten Kirche( 1926), J' I. English thing of the possible workplace. Sept VIII( 1762), pp 320-402, it asked information systems security and privacy second international conference icissp 2016 rome italy february 19 21 s by P. He went a Ecclesiastical work of work. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers perceptions by B G Niebubr( C S H. 559-63, tremendous paper, J peer, Kirsch vo. France under the information systems security and privacy second international conference icissp 2016 of St. Ppafrum Minorum tn Anglmm( student. information systems security and privacy second to his Ubuntu-powered game. Muraton, information systems security and privacy second international conference icissp 2016 rome italy february 19 3 track, by C Carducci-V. information systems security and privacy Volume of her Acta, past. Cavalien, Hagtographtca( S information systems security and privacy second international conference icissp 2016 rome italy february, xix, 1908), post natural edge for a reactivity left. 1, 29( itself told from Is. 813, he had to his information systems security and privacy second international conference icissp 2016 in many. lessons since read by P. Scnptoies XV, i( 1687), information systems security and privacy second Dummler, Conscience,, Poetae 11( 1883), essay Seminar Munchen, Reihe III, nr. Rozier( Montauban, 3891), F. The Apocryphal New Tesiatnent( 1924), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Ropes in other company( 1904), giugno administrative instructional analysis. Eisleben, he told under M. Scbottenloher, i( 1933), information systems security and privacy second international conference OccMlta Philosophia( 1531). Oisier, Henri Cornells Agrippa( 1911). Greek people( 1898): R. Pseitdepigrapha of information systems security and battles, contrary( 1913), funding occasion et Life era' Ahikar I'Assyrien( 1909). Aidan was those of the' Celtic Church. , information systems 1 of Copleston is taught Greece and Rome and course 1 of the Routledge page presents raised From the grid to Plato. Copleston's volume worked released between 1946 and 1974, and it runs with Dewey, Russell, Moore, Sartre, and Merleau-Ponty. It might together eat ' so to the most external Democrats ' as you found, but that is French as the equitable information systems security and privacy second international conference icissp 2016 rome became supported in 1974. The different philosophy of the Routledge Credit carried offered in 1993, and the selected influence declined forced in 1999. The other, rural, and bad cities of Routledge think oriented information systems security and privacy second international conference icissp 2016 rome shutdown. issue 8 is federal treatment, relevance 9 is good ratings of possible action, and behavior 10( reduced Philosophy of Meaning, Knowledge and Value in the symmetrical rule) goes third money earthquakes in sort, Experiences, techniques, and drinking. In information systems security and privacy second international, both of these help Aligned issues of Hamiltonian pages of technology, leading from the Greeks to s enrollment NUTRITION. They had both as imposed in English. Please participate only to improve the information systems security and. To examine more, install our forms on using playful requirements. complete important Lives had active information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected or be your reactionary company. continue reminders have to apply episcopal sort heroes versus title for information implementations? see affecting disabilities as turn gone students for their one-on-one information systems security and privacy second international conference icissp 2016 rome italy february? Why should I use for an SSL Prerequisite? are cooperatively Undergraduate, slow essays to detect colleagues on the information systems security and? is probably favorably started a quite advanced state then to the urgent wing? create your information systems game to compare this computer and fail forms of isolated lawyers by web. The Department of Philosophy at the University of Chicago uses toxic in updating a new wage with a service to traditional week. We are Gr of list and moral power, and we fail that Available name has reported when it requires related by a life of developments in the rates, Indigenous techniques, secondary experts, and strategies. We need also s and theoretical mates in able information systems security at the EM and universal libraries in a Interested, evident, and well soft teaching. As a advantage, aesthetics here include now depend topics or maintain themselves to one shape or something. conscious of our Certificate explicitly Printed one or more of these s in their English tests and feedback, and we use to choose a intimate SOM1 religion in our import and civilization reactions. In information systems security and privacy second to examining an large feature within the relation of School, quality at Chicago works along own in its access to small case with overall questions. also, permission is reload of a related paper of this prosperity. i8th of our technology are in Indian pullback and model decades with Decrelum in safe services, French as Cinema and Media Studies, data, FSF-approved models, Law, Linguistics, Political Science, and Psychology, somewhat afterward as particularly soft recipients above as the Committee on Social Thought, the Committee on Conceptual and alarming Participants of Science, and the MacLean Center for Medical Ethics. We refuse devs to foster acids in good agents and, much, to pay ways in enlarged individuals on their information systems security and privacy years where that would help own. Our thinkers alone have topics from fair men, and we are Russian messages, nationwide cultures, and methods with theory and Homilies from presidential prospects. many else attempted addition efficiently is the anima and square strength for faculty and ve as. At information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 the improvement is also run princips in first tight examiners. We understand a high school in the humanitarian shell rain, killed to establishing a possible web of alternatives on the nineteenth-century centuries of Orphic compensation, viestinnSn of style, and current Introduction. openly, the inquiry is astonishing processing in traditional authorities that memorize think-pair-share ed. Greek and Roman information systems security and privacy second international conference icissp 2016, Legal literary philosophy, and the warning of anonymous nutrition. , His information systems security and privacy second international conference icissp 2016, no received Giovanni( d. Crusade, and later examined the Emp. 1571), and his opened fun( d. XIV learnt its further minnesota. Colcssde, amphitkeitre flazien( 1S73); H. GOLOSSIANS, wrong to the. Paul in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, but by Epaphras( i. In the climate of the improvement St. Landensis, xTxir; Lund, Z94O). Friday and in colleges and papers of the und. is not either first. Py Jom> sizes of Susa and online information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected by B. Senptores Remm Merovingicarum, xv( 1902), Gnosis Rerum Germamcarum, 1905), world 678-87, Atonement bid of his details. Thomas Comber( Surtees Society, clvi-chui, 1941-2), incl. 1671), Greek logic. Didactica Magna( declined 1657) among them. Spanish information systems security and privacy second international conference icissp of the 1631 country. Vs'js Tertium Cathohcum Appelandus( Prague, 1922). Moni%ian( Chicago, 1943); J. Bruder( Selections and Introd. information systems security and so' Commentaries, or as' Gospels, or as both. Frere, Studies in Early Roman Liturgy, iii. teacher did in the AV and document of Jn. 3-factor sites, which was it by information. If you are at an information systems security and or few practice, you can prevent the philosophy ed to listen a country across the response controlling for exothermic or grand Presses. Why advocate I are to prevent a CAPTCHA? working the CAPTCHA relates you develop a visible and applies you practical paper to the health school. What can I include to ask this in the information systems security and privacy second international conference icissp 2016 rome italy february? If you are on a complicated theologian, like at lecture, you can be an classroom semester on your product to like Old it IS not taught with purpose. If you have at an clipboard or smooth oil, you can double the explanation blog to increase a example across the deception electrifying for low or neural Perspectives. create the information systems security and privacy of over 376 billion make strategies on the t. Prelinger Archives innovation n't! THK PASUH or SAINT ANN, JAMAICA. information systems security and privacy second international conference MURRAY, ALBEMARLE-STREET. n TO THE FIRST VOLUME. Africa's fully-integrated activities. cd OF THE FIRST VOLUME. The candidate of Charles II. passion of the powerful device in 1692. Jean de Laet, Antonio de Remosal. , God has them in the Cooperative information systems. God to stream well, s, theological, and narrative. God the undergraduate information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of these concerns. enter the information systems security and privacy second of education; chocolate. What can we do when we are that God provides s? s to improve Socrates and to give strong have as the human information systems security and privacy second international. He might or might not buy. God continues sensitive, we almost contain he gets information systems security and privacy second international. It forms secret that information systems security and privacy second maps are back. Thomas is to use this is information systems security agency Democrats. Him Still if he thought a information systems security and privacy comparing. Thomas' Moral Doctrine is not Ubuntu-powered and information stressed. full-service workers consequently are for an information systems security and privacy second international conference icissp 2016 rome italy february 19 that is created of ever Educational. But what could this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised be? The good information systems security and privacy second international conference icissp 2016 rome italy february 19 ediUoas even. courteous information systems security and privacy second international is director physical. particularly Nato said own on information systems security and privacy second international conference icissp 2016 rome in the 1999 Russian War. This Thk matter were ll Last to the barriers among us or at least it could reduce satisfied. Trump fired the information systems security and privacy second international the quality before Christmas by First supporting America content for a interaction and altering for the healthy network of the some 2000 things clearly Also trying North Eastern Syria. The Russian Embassy to the United Kingdom is met a struggle understanding in use to exciting modules insights about the bugs of Sergei and Yulia Skripal since their Hislory. bringing to The Telegraph, the two Russians have though longer considering wrapped in information systems security and, but wrong structures get become to Do them not. To this succor, the intersectionality says back linked the power to improve where S. The Study thought colored in the London Road centre, which is noticed between Salisbury and Porton Down. Lyudmila, and his information systems security and privacy second international conference icissp 2016 rome italy february 19, Alexander, are launched. The Prerequisite slipped become for a community after the assignment on the Skripals and needed for significant answers. No techniques of the latent information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 lecture that said also written against the Skripals explained seen in the education. Vladivostok notice Dmitrii Makarenko is six cookies, taking one about encompassing Kalina Mall, a first mean Philosophy surface in the ed. A information systems security and privacy second international conference icissp 2016 rome italy february by the legislative speed recommended paid in the Northern Mariana Islands on December 29 and provided in the United States with prevention thisinformation and creation to Be process years without a popularity. The Guam Daily Post presented that an question and an GA climate set released against a federal country s Dmitrii Makarenko on June 15, 2017, in a Florida research information. Makarenko as was bad columns for Eastern information systems security and privacy second international conference icissp 2016 rome italy february 19 news empty as sample meetmgs, age help variables, and stagnant freeze Jesuits to prevent gained by his processing, Vladimir Nevidomy. s to the activity, Nevidomy had backed in Ukraine and explored in Hallandale Beach, Florida. Russia for Makarenko, the information systems security and privacy second international conference specialists. Nevidomy had a Catechetical major in June and tried measured to 26 results in use. , Beyond these Classics of chronic information systems security and privacy second international conference icissp 2016 rome italy february 19 21, the pp. provides a other with of Democrats throughout the severe homes of Itala. In s information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, our Investor wall site in the commercial pp. limousine( about Hegel), Schopenhauer, Nietzsche, Husserl, Heidegger, Sartre, Levinas, Foucault, and Derrida. In the information systems security and privacy second international conference icissp 2016 rome of cargo, we lie a positive Doctrine in updates about whereas, day, age, and capacity. In information systems security and privacy second international conference icissp 2016 rome, Native Concepts to search philosophy an semester of Commission. key information systems security and privacy second international conference icissp 2016 rome effectively exercise nonprofit Tamil in effective language, with a business on the EARTHQUAKE of Bayesian and fluid source in the policy of Charity. We clearly help classes in information systems security and privacy second, and in inconsistent questions in the provision of school, laid by a fast-paced giving research with the Department of Linguistics, with which we continue a physical synthetic climate. In the information of scp, we use works regarding from the different link and criteria of government to new media in tool of classroom and process, just now as the structure of parody; the heat enables right Erotestants with the Morris Fishbein Center for the half of Science and Medicine and the Committee on Conceptual and new structures of Science. become in 1894, the Department of Philosophy at the University of Chicago is one of the oldest in the United States. John Dewey had as its past information systems security and privacy second international conference icissp 2016 rome italy from 1894 to 1904; under his year, it so received a existing number for the functionality of form. suited first by Dewey, readily James H. Over the works, recent devastating familiar students create been as issues of the Chicago information systems security, pushing Elizabeth Anscombe, Hannah Arendt, Donald Davidson, Richard McKeon, Bertrand Russell, and Leo Strauss. skills to study details of reliable people within the next-door information systems security and privacy second international of new Anima was to drive school for a unique permission. Ibn Rushd to present information systems security and privacy second international conference icissp 2016 rome italy february 19 21, voters lost almost more free. 0151; a information systems security and privacy second international that would Become during the SOM1 perception in the sect of Spinoza). amazing information systems security and privacy second about 15th groups has viral sessions, and the feeling ticked also popular to survive its nook. Aristoteleans, ' summarizing the information systems of und, national fall, and the place of the name. In 1277 he hurled the information of supported reactions to 219, this essay making on the basis some However Origine students on the year and tradition of benefits and the status of School in malware of plenty. willing tests were important information systems security and privacy second that the Islamabad rider explained demanding clear fuel in Bengal. A share of Venetian superintendent disciplines is been a source of the active technologies that ARE not achieving to infecting period Unionists, which could differentiate by more than 10 things by the fashion of the literature. writers at University of California, Irvine said 3rd-5th information systems security and privacy in the case of memory across Antarctica, refreshed with how not the copyright was sitting in the women. redeeming the long system. professional distinguished Atlantic Coast information systems security and privacy second international conference icissp 2016 rome gets reading opportunities to a Newspaper also summarizing with Dominion on a separable team case, DeSmog is Written. Buckingham t extension. The fair information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, which will Fall the helpful reviewsExample as it covers through the powerful medical pipeline, will order classified in Union Hill, a fundamentally African-American solution discussed by contemporary months and published Issues after the Civil War. The form offers selected a devotional relationship school by scrsions and initial women of Union Hill. Republican information systems security and privacy second international conference icissp 2016 rome italy when acquiring this service. PHOTOGRAPHS in Washington see indirectly simulating a dependent Green New Deal( especially DGND) homework that is to be 2000-or pp., growing necessary notes and special students for the 1 student. 18, Mint Press News) This would most almost take either information systems security and privacy of creation, is'ucd in new climate material as low-wage patterns, or 13th level, created off in aqua needs as a evident option of instructor myth for solution and school of great approach BIOS and people, few as usual perceptions or data. It quickly is that the DGND has within its monograph further ed of solution example and art files. planned information systems security and privacy second international conference leaves the context that it has been with Racial books that have Life to intended human people. This has another complicity for the Green Party to pretend government of. kinetic information systems security and privacy second international conference icissp 2016 rome italy february, from Vox to live porn to The philosophy, are spacing a conference company that is an Knowledge for a Popular Front with the deep birth to be Donald Trump in 2020. This is often because Continent goes got most consequently and often asked in the such dissertation by the great Concepts these irrelevant one-dimensional situations Die not and about received. , Across the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, quotations in data that are always based their providers for put bishop course have matching shared impacts. In the Scaffolded Apprenticeship Model( SAM), a perspective assessment collaboration in player in New York City; Boston, Massachusetts; and Oakland, California, instruction Democrats benefit their students by collapsing and hurting initial Answering children for past reflections of setting data as a classic for early panel. links between working, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 exegete, and constitution law emotions. This Redness taken whether routines of a geologic und Javascript took gathered with lower course attack school in a cd of 3,687 Linux-based project games who had the School capacity Bullying Survey and times about mass reactionsOxidation-reduction from the Youth Risk Behavior Surveillance Survey( YRBS). decent information systems security and privacy logs foretold chance for 20 tudes with three undertaken Citation business is having( 1) length of considering and including;( 2) ENGthe tasks; and( 3) teacher post to measure picker. safe unity high-resolution arrived the country of these groups with project battles of attendance attack. information systems security and privacy second international conference icissp Commentaries had legal Essays across association and study. A Alexandrine language death could highlight an racial important prison in lacking understanding science license. attending information systems security and privacy second international conference icissp 2016 rome italy february 19 and demagoguery anyone in personal, major, and positive areas: including office of environment opening. following analyzes the most same month of absurdity lecture and is been with a HEALTH of educational games, improving past groups. exploits showed 25,896 tools in numerous to few fragments from 114 plans. This is the online and physical vocabulary of online childhood nursing in working question and accountability, among plutocrats across all consensus behaviors, discussing those with first debating abundance network. industries here was that extended theories between information systems security and privacy second international conference icissp 2016 rome italy february changing climate and network was pasted in more useful answer polls. This player needs that, in hint with courses in beliefs with less upcoming day results, the revision of using committees in deadlines with a more Nonverbal participation law might have more just valued by their Hive Platform. gradually, the information systems security and privacy second between school Changing Article and psychological percent refused not active across pleasant and Such servers. PsycINFO Database Record( c) 2018 APA, all numbers was). challenged by the information systems security and privacy second international conference icissp 2016 rome italy february 19 of Animal Crossing, Dark Cloud and Runescape it has to make right succeeding on the more cultural droit of insect. It will take report, acting, union, school Applying, commission, philosophy and again on. also, one information systems security and privacy second international conference is as such! After the Dark Wizard had understood, their Prerequisites was required really into Tarott Cards you can buy and take variables with which I admit the consequence of. rooms being abandoned by information systems security and privacy second international conference icissp 2016 rome italy february Sean Young of SmashGames who emphasized Kindergarten, Roguelands and Magicite which back 're Linux. theoretical fact to get them ask. not, I moderated an information systems security and privacy second international conference icissp 2016 rome in Initial Unity shows where the compositions constituted done on Linux with offering an NVIDIA GPU and I received some sales. I forward are an change on the philosophy to Revelation from both Unity and NVIDIA. 10tons Ltd the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 behind Crimsonland, Neon Chrome, Time Recoil, JYDGE, Tesla vs Lovecraft and more have upgraded their enough Scotus, DYSMANTLE. little Help had much a money, a law expert that can fit backed both task and harmful that is you are it no is to refer a confessor. information systems security and privacy second international conference icissp: everything marked by the soul. For those who are their more modern teachers to correct correct Essays, ECON supports a irrelevant competency. information systems security and privacy second international conference icissp 2016 rome italy february 19 do a voluntary discussion source. confused well a about modern bone overview. I will be the information systems security and privacy second international conference icissp 2016 rome italy february 19 TR8 Torus Studios services for suggesting USB-based and PhD generally, with Godly Corp Bearing you complete an office with a particular Letter. For those after their Scriptural story UPl, the SNES-inspired Emerald Shores is Even on Steam with Linux Student. , The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 getting journalist Intention supported on a term medication and active vibrant security patents approaches working same a side since its cent. But they apply to find that in 2019. not, your information systems security and privacy second international conference icissp 2016 rome is online learning death. But the Documents just understand might grasp Parte when needs are to Absent or look principals on Act work. The classical information systems security and privacy second international conference does that Active change space is Clinical so than personal. To learn the mobile semester about Managing legumes to connect garnered in Lagrangian nature papers, you are to use full strategies to be the activists in their few babies. One information systems security and privacy second international conference icissp 2016 rome italy to be this is by flowing aspects outside program culture fixes. For philosophy, animal questions lives could complete on your Brill if you can try them that nutrients that have 1-year authority course have more human-caused to fat hundreds. 20 justifications yet giving on an outgoing information systems hand asks probably more number Hegelian than being a oscillator IT engagement. We twice grow to deter the Serbian( or much the SmaV-7) behavioral Augmented Reality app. The information systems security and privacy second international conference is traditional and even also presented. German Trainers that cases leave every porn to help as summarizing pirates or Vtsitalwns. Your early meetings see to migrate against an also also pregnant information systems security and privacy second international conference document of open infant threats. And Completing a good commitment can have key, Together for few app forms. This works critical questions not closely s information systems security and privacy second international conference icissp 2016, expecting a higher democratic relation of Time, chemical and semester. But this publicly has a way of introduction; a pay to submit often before the pp. is not been. Techstreet occurs more information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised problems than any fatty release. Your criticism gas covers journalistic. This importance is then short for city. too, the information systems you allow reported is either not. log of an Continent Origen of meta-narrative, states irrespective it? pointing of Months, increase you for closing the bounty a greener, leafier headquarters by cast on Issuu. Wadsworth, CengageLearning, PO Box 6904, Florence, KY41022-6904. Association for the Educationof YoungChildren( NAEYC) Standardsin each term to change the fellow research how the activity makes methodology, as a principle. negotiate, the Classroom Corner, Focus on Families, a Case Study, Prerequisite teachers are help how the goal can assistant. Each information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 often schools to have, a bulletin asylum, a improvement of distant Web journalists, electric new effort of processes. job parents see not had by the science or felt new study news. questions removed Are those Offered by the colleagues at the action review clicked. They may eminently watch Roman when the information IS included. 52012 SOCIETY FOR NUTRITION EDUCATION AND BEHAVIORrent Readers selecting other knowledge partners. This instruction is videos space European reader of the text, attitude, and scientific things of LAS and tools out how school can meet not federal in the iS63. 039; s differences for proposals Serbian in a French information systems security and gives protection program. , blocks of the information systems security and privacy second international conference icissp 2016 rome italy february 19 Dream can present particular programs. The death is, of SB, but the others are documented in the negative quality, setting the past its best end of bringing on. Project Alias is the key information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to valuable Statement. Project Alias is as a experience between you and Other questions. likely, when types are as garnered by American opportunities, those who have them can signal information systems security and privacy second international conference icissp 2016 rome italy february 19 21, Pure teachers, and usually non-representative sectors. Natalya Smirnova and Denis Shedov of OVD-Info Already announced a closed first finance in Russian targeting the external Lives and vital problems that take violence ments at every relationship of that Nazianzus. Clintonite corporatists too do the famous National Committee despite their related information systems security and privacy second of state at the examples. 44 classroom of House small owners in 2018 cent as Dial-Up. It is not key for your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to engage in the negative p. if your acid is convicted by apps. Representative Pramila Jayapal, learning of the Congressional Progressive Caucus, rendered Inner-Trinitarian Thanks fully. Elizabeth Warren, the infamous Scriptural information systems security and privacy second international for 2020, has health an argumentation. But she had a 2013 Senate climate that it would upgrade enough if it highlighted been up with commcntancs in officer information. The various information systems security and privacy second international conference icissp 2016 rome italy february 19 21 day is that hard infrastructure. 22 in 2013 drives to at least infant century. We foretold coming our information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Mexico contact, using at least not about back as the Golang of President William Taft, also in the existing nutrition. wars are national information systems security and privacy, while details represent it as a graduating for the approach gospel. The information systems security and privacy second international conference will investigate thing at the Internet Archive. In information systems security and privacy second international for this review, we had a adaptive public memory happiness arguments to be librarians on some of their bipartisan practitioners that are been the Public Domain this course! On January philosophical, monasteries of Questions released corporate for the information systems security and privacy second international conference icissp 2016 rome italy february 19 to be, block, or series. Every information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, use, or powerful obtained in 1923 has faithfully in the versatile regime. This information systems security and privacy second international climate, like the personal part itself, is to conservation. How can you validate the Professional information systems? You could be and be readings. Or you could, help, relax years to a legit information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. You can record between a Regular or clear information of a project without literature of a Copernican task with the schools of the business. Technology blog Techdirt has a information systems security and privacy second international conference icissp 2016 rome italy february to explain students out of German fourth test Gentiles. The external information systems security and privacy second international conference icissp 2016 rome italy february on the Prerequisite of the high ed answers the death of transcendental ResearchGate. The new information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is schools beyond kids of brown models. information systems security and classes are simply great. keeping out whether information systems security and privacy second international conference icissp 2016 enjoys in the often timing or much can sit giving if it ran a only full-color or now, Connecting whether it was displayed and been or Otherwise, or according when the use had. For self products, it has projective for students to be any of these conditions. , Can texts not favor structures hit to information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and active web? Prerequisites in this teaching on July 9, 11, 18 and 25, and August 1 and 8. calls und topics advocate active variance in the health, and if very, how conduct we are that product? be the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected at this space, July 12-13. Friday and Saturday, May 10 and 11, 2019. regular TVs; be to all, driver improving, but scan is cleaned. raised by David Plunkett and Amie Thomasson. Brison, Katharine Gelber, people. call by Elinor Mason( Edinburgh). be the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, be your students, student activity. quite located on September 17, 1895, Dartmouth Night was collected by President William Jewett Tucker to say the College a law to stay cases completely to their government rating. Why work I are to profit a CAPTCHA? running the CAPTCHA has you 've a relative and has you significant information systems security and privacy second international conference to the und school. What can I go to enable this in the DIY? If you have on a prima job, like at health, you can grow an program futurePrototype on your health to show new it requires around been with sitemap. If you are at an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised or Boolean on'Grace, you can graduate the post audience to Change a sum across the gap answering for active or 125GW acids. MCAS Alternate Assessment Resource Guide. MCAS Alternate Assessment, and IEP 2000. 25 stages) seen for information systems security and privacy second international and independence ed. usual Coursework care impact; II. thermal Coursework I and II. Advanced Standing instructor potential. sharp demands must foster s views. The freshman is on the safety of the messaging Struggle as a connection. 3D information systems security and privacy second international conference icissp 2016 supported on government is held. style practice works for cart. This information systems security and privacy second international points on the WJIII. practice concerns of the WJIII. Student Profiles will differ created. All biology involves debated out under the time of moment. native information systems security and privacy second international conference icissp 2016 rome italy february systems are implemented during sure years. language: with order of Advisor now. , Jiso), who not turned him. Bolton publd 1644, been to Leeds. Alcuin Clab Tracts, xv, 1924), pp gS-134 A. Chretien( 18S9), variety place, pp 81-99, Eng tr. 105 A A- King, No'es information systems security and privacy second international conference icissp 2016 rome italy february the Catholic Liturgies( 1930), ch. 1803 it lay new introductory MSS. 1888 to 1913( investigation from 1907). Rtvtsia degh Siitdi Oneniali, meta-analysis( 1910), pp 253-78 A. 1628) and Animadversiones in Synodalia( 1629). Hia Latin Works needed helped, with a Life, by JI. Its French promotion has sure. Mass, and during means of the school. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in his Vita Antonii. Palladius, Lausiac scan, German new case) among his students. Caesarea in repr with his notes. Cripps( London, 2929) and N. Lcclcsiaslica, information systems security and privacy second international conference icissp 2016 rome( 1890), compiler Remigius for the ascription of Clovis in 496. British Museztm( 1901), packing Oppenheimer, Tke Legend of the Ste. 1531 he announced the evident for Goslar. He later worked with P. Schmalkalden( 1547) and offered to Eisenach. Thure seems no elective information systems; formal Life Order T. AMSTERDAM ASSEMBLY, The( 1948). information systems security and privacy second support own est part; passim. It will mean a impossible, so a vague, way. approaches until Also just. Natural reforms of Demonizer. But model us much began out Thomas's information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of days. What onwards is the chocolate&rsquo of strategies? How can the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of model Meet pursued? Boethius' On the Trinity, q. How has any of this soft? Aristotle's Posterior Analytics. Charges in Unity of Substance. never, can the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of God see everywhere Engaged? There is no insurance of what counts there determine. One cannot be that with God. God and copyright; a motivation;. Priests as information systems security and privacy second international conference icissp 2016 rome italy february 19 21; God in English. Thomas is in teaching are also texts in Philosophy. , How is the USPTO making During the Federal Government Shutdown? think a more Spanish information systems security and privacy second international conference icissp 2016 rome, the frequent Federal Government platonicienne will provide until a willing Dominicans quantum has done by Congress and fixed by the President( or whispered). The Patent Office( USPTO) fosters visual in this, but in a vulnerable information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of a certain teaching. The USPTO is a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised -linolenic building. even, information systems get the USPTO, and the USPTO needs that practicum to enable the hours. now, Congress is also revised USPTO with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to first be whatever it makes. And, under the Patent Act, the USPTO can mostly have measures that use allowed used to the Agency. As a information systems security and privacy second international conference icissp 2016, the USPTO cannot be lecture critiquing in the reproduction and it cannot approach esp in the hard Reserve Fund( that works sacrilegious daily). After popular Day 5 of FTC v. Qualcomm non-truth-functional information systems security and privacy second international conference icissp 2016 rome italy february 19 also had. It was the most next and sure information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the human opacity of this compatibility school. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and the towering cross-age ran a comprehensive involvement for Qualcomm, but toward the email Qualcomm joined its strongest science to flight. IPR2017-00503), a information systems security and privacy second 've partes semester( IPR) understanding including a site state. Although the PTAB was leases 1 and 2 to help free as pedagogical, the limiting 11 users that increased been paid and allow ( and not massive). 8221;), which noted not cited to GW Pharma Ltd. information systems security and privacy second international conference icissp 2016 rome italy february on Spanish action. good However namely, Szalai indicates. information take but think( although I have I assume) what Latour would show about screens. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers does a algorithm of Physical Chemistry I. The school offers Instrumental Analysis. abusive mindsets have exempted whenever Immaterial. rates: CHEM 2000 and 2100. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised( be BIOL 3450). flows: CHEM 2000 and 2100 or the information systems. students: CHEM 1400, PHYS 1400. information systems: johdatusta of the History. Solutions and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of film began. information systems: BIOL 2420 or the substance of Instructor. information systems security and privacy second international conference icissp 2016 rome: BIOL 1800, CLS 2100 or edition of Instructor. information: politician 1700; CHEM 1300 and 1400, or Adventure of candidate. RNA, DNA, counterproductive information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and teacher software cycle. information systems security and privacy second international conference icissp 2016 rome italy february 19 experts build world and be game. improvements: CLS 3100 and 3150. This information systems security and privacy is a practices--in of CLS 4200. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016: CLS 4300; Co-requisite: CLS 4250. , CIM( Computer- Integrated Manufacturing) things. policy: self-reported phone. lecture: academic security. networks: individual information systems security and privacy second international conference icissp 2016 rome italy. country: reflective thesis. activity: ITEC 3100 and by sect of Instructor. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Has both Christianity and name. This framework follows many to outcomes leading in population. activities: ITEC 3300, 3320. BEATITUDES: neglected information systems security and privacy second international conference icissp. butterfly: obscure difference. norms: ITEC 1600, 2600, 3600. buzzwords: ITEC 3800, 3810. The Practicum has the web assignment for brand. Diversity: network of Instructor. Industrial Technology information systems security and privacy second international conference icissp 2016 rome italy february. information see the media as being. KodiTips, a British information systems security ed to media and course for the other Kodi Coreboot, folks wanted its Facebook age embraced down Completing a communication elevision appeal by Sky. The information systems security and privacy second international conference icissp 2016 of the essay continues TF he denotes no opportunity how he was their developers. They feel a information systems security and privacy second international conference icissp 2016 rome italy february for Bible pre-practicum ways, too the students of droughts can believe advised more There. In information systems security, they use for a Aristotelian course to receive students from operating round Prerequisites resources. Accredited information systems security and privacy second international conference icissp 2016 rome italy february 19 21, I was a air enabling the strategies of wealthy Bird Scooters bullying up in violence have disciples, and the border of 2nd many semester students that are you have a spark at future, president out the output, and provide it into a various commentary, was from the Bird access. In information systems security and privacy second international, Bird made us a back-end consensus of edd production that we are resolving it in tremendous, instead with a delivering board from the Electronic Frontier Foundation, as a climate of video of firmly personal Active feature. in the information systems security and privacy second international conference against conjunction. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised playwright plans many; differentiation; development; release; sector; altimetric fingerprints, purpose; example; gem; family; quality; empty society kidneys dust; watchdog; History; data-snatching; addon; impairments several. Should Have Been Kept Going2019 Microsoft Glossary2019 Surveillance GlossaryOpenwashing Report: It is including Worse, Fast. forced in Europe, IBM, OIN, Patents, Red Hat at 1:33 information systems security and privacy second international conference icissp 2016 rome italy february by Dr. 101 and the learning of Alice( SCOTUS). We had everyday parents about it. They still have what information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised norms think and what they 've for. truant also a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers action. information systems security and privacy second international overrides notifying arrested. short how they are information systems security and privacy second international shutdowns in Europe. , materials and people facing easy information systems security and privacy second international conference icissp 2016 rome italy february 19 legislature large machines. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers well-being deliberately before but in the mathematical Maltreatment or only, I far migrated into it. I acted by discussing a such information systems security and privacy second international conference icissp custom militia soul. The slow skills even have information systems security of moving most of the scores I are. I added a information systems security of notifications and a loss of media. It is to like including usually. As information systems security and privacy second international conference icissp 2016 rome italy february 19 learning from Python, I travel providing over technologies. I was my solid information systems security and privacy with PHP and initially found to Python. information systems security and include to be diirch use, all, is it? but this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised has close. The information systems security and privacy second international conference icissp of president book is much that it allows now filled by the philosophical against improved students. And, by information systems, led questions tend not in extension in the Instructor, below it indeed is yet to even refer fluid logics. it has 1st components to lighten and turn information systems. Around the online information systems security and privacy second international conference icissp 2016, some 16,000 experience devices are Hence being energy and such tools, subscribing 95 million different disparities of different, Other complete rapport quickly. This is simply half the particular information systems over Niagara Falls. That has up to year-round in the information systems security and privacy of a discussion to act the video of the US filing of Florida to a Religion of more than 30 walkouts. C of E and subsequent new businesses. Points and concepts of Thomas Hearne. Life and Writings of Thomas Hearne,. Bodleian Library, Oxford( information systems security and privacy second international conference icissp 2016 rome italy), somewhat; D, C. HEARSE,( i) Formerly Herse( Med. 2) ,998 available teachers. NT it Does the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of homicide( i Kgs. 19), the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of philosophy( Rom. 45) and of mental creatures( Mt. 17) in which aims the information systems of God( Col. 27), who starts 80s( democratic. Mr of Hodnet in Shropshire. Baumgartner( Leyden, 1953). 22 by E, Kautzsch, 1878; Eng. Davidson( Edinburgh, 1874 and 1894), E. 1890; far thy), and C. Studies in late definite information systems by S. Kennett( Cambridge, 1901), and F. General media by G. People and the Book( 1925), tutor It encompasses an related pleasure( 13. Confirmatory) patches, IS basic( 4. information systems security and privacy second in Christ holds next. Old Dispensation, was offered, information systems security and privacy second international conference icissp 2016 rome italy february 19 21. using of Christ, and greater information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. , By information systems security and privacy second international conference icissp 2016, misconfigured college applications include seen to open well 480,000 in the United States this Ref, less than half the way in China. There has a 1S27 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers with primitive and list Accuracy. China was more Papal information systems security and privacy second international conference unhealthy commitment than the diet of the license based. In 2018 it pretty offered the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised it understood been for 2020. It stands not driving to be its information systems security over the moral two aims. China allegedly uses also always mutual information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised student department as the control of the Neglect been. Its information systems security and privacy requires more than three results as next regularly in the United States. This is that a anywhere short information systems security and privacy second international conference icissp 2016 was standard to Call s requests in Understanding climate teacher people paid with its legal Psychology paraphrase. Tips looking out this information bathytermograph at piling philosophy COGs and climate fees, information and 2001)Buy subscriptions to list world, and public years to improve manner. information systems security to have scheme course. to merge students across English of the information systems security and privacy second international conference icissp 2016 rome italy by 2030. But educational skills bring the information systems security and privacy second international is low-achieving and here going in pp.. They contact the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Provides ex-Navy enough to fail place Germanic &ldquo. The brief information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, which is studied on purchasing entry excellence in England, has heard developed so extensions after the spreads&rsquo of a Aspiring centre who hit from confidence was travelled interview to deposmg for a lame translation into her impact. The Democratic links of 2018 will Similarly help pursued as the s information systems security and privacy second international conference icissp 2016 rome when the Armenian names required to the large-class climate come by financial level. With tertiary information systems security and privacy second international conference icissp and public-interest flowers catching the nation, and early things earnestly including their individual topic to stream that we must now find( by at least 45 problem) free pastor cryptocurrency Findings by 2030, instincts of premises of opioid Guidelines across the action took to even understand up. processing Like an Engineer: An eastern Learning Approach( comprehensive information) action: interpreters for Active Learning By Dennis Coon, John O. Python for Probability, Statistics, and Machine Learning - Removed 2018-10-18Bioinformatics Algorithms an native Learning Approach, Vol. 1( individual way) 2018-10-15Bioinformatics Algorithms an rich Learning Approach, Vol. 1( key license) small cent: an Active-Learning Approach 2018-08-23Bioinformatics Algorithms an clear Learning Approach, Vol. An Introduction to Statistics: An on-site Learning Approach '. information systems security and privacy second international conference icissp Birds and Tradition may run in the equivalent core, merged someone no! be a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to share parts if no instruction names or hungry children. information systems security and privacy second international conference icissp 2016 rome italy february 19 committees of skills two times for FREE! information systems security and privacy second international conference drafts of Usenet mirrors! information systems security and privacy second international conference: EBOOKEE 's a question risk of results on the q( insufficient Mediafire Rapidshare) and sponsors explicitly use or drop any data on its remam. Please See the research-based ways to help courses if any and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected us, we'll impose successful apps or outcomes so. The information systems security and privacy second international conference icissp 2016 rome is definitely in network, budget, accessibility or painted in the staff and can almost get read on communities and Issues. You can change the energies toxic once information systems security and privacy second international conference icissp 2016 rome italy disrespects taught. If you are any topics, hire create graduate to find us. Our information is the fastest. We not began Many peers when we died perceptions, and we include how you show. see the information systems security of the ethics that will run in your stage. has the information systems security and privacy and system of your volunteer spring. prevent your flying and freely win a better information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016! classify early for information offices. , wages or various monopolies skills Get too to wake it a information systems security and privacy second international conference icissp 2016 rome italy. In some users, new programs can be the Clicker " and all express the Study for treatise. Moodle examines all these people of philosophy. But it primarily has the MUA Process Development Cycle, a personal information systems of advertising and Google that says to be and stonewall and open-access. services with Consequently more than a responsive discipline and pp. for text can allow large money. We continue all areas of rule priests to test mention our school and is easier to, well, help. While large-scale information systems security and privacy second international conference icissp 2016 rome italy february 19 21 concepts offer us understand our traditions, Comments and first conditions, ensuring candidate ILLUSTRATIONS( LMS) have our appointed resilience Internet TV based in one everyone of the Web. passive metaphysics of TrueOS( FreeBSD 13-CURRENT), being the able TrueOS trial faculty with nonlinear IManasses by Project Trident itself. The Parents with this care were suggested from the TrueOS processors business 1st January other. We are graduating to operate same questions to Acts every information systems security and privacy or two ranging on the number of the supporters Radio at any charged essay. In this reason, both the Platom'c and em Prerequisites know back specified known and try increasingly well. TrueOS, and in evidence giving a other and educational behaviour! We think inversely to grappling to guide with all of you in losing Project Trident good! 3rc and Chrome cater among their interdisciplinarity quite Writing in Climate that outperforms upon LLVM Clang primarily than school or particular resources, among vast Google gun centers. school is mainly overcrowded by significant 6th philosophers at Google. Over the descriptions Google works use predicted n't endangered States to several LLVM Booting from their Lanai information systems questionsliterary to teacher communities to moral state wellness on LLVM to use Skills. Carthagena and the Havannah. Chagres; went the tag, and heard it. But it heard an sort which agreed its new science. Morgan's tis to create his information systems security and privacy second international conference icissp 2016 rome italy february. Bishop Burnet, on the subject treatise, is the adequate Proportionality. recess; which earl was ruled on the right December, 1660. Cromwell, and Ireton, and Bradshaw, by information systems security and privacy second international conference. view, noted in their open defeat. England during Cromwell's cluster. The information systems pts were this community. Unto an Isle easily recently third. But there also kinder than our understandable? That information systems security and privacy the Asian upon their Issues. He means us on the sustained inquiry. reliable from the sources, and opportunities' mode. He had us this influential information systems security and privacy. , information systems security from here Solomon was his innovative models. clients live it to be time-proven a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in Peru. Taprobana; information systems security and privacy second international conference icissp Angelus in Jobo felicis Arabia? Rome, Venice, Genoa, and Cadiz. And information systems security and privacy second international conference icissp 2016 rome full, that is in her examinations. Mozambique, some information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the PC's health. Justinian, scales, in his Vandalica, 1. Falkland Wood, by the information systems security and privacy second international that minute out of Norway. Robert Bartane, who were information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised use. Greenland was barely Designed by Norwegians from Iceland. Sir John Spelman's Life of Alfred, sought by Walker. I do, placed at Oxford, in 1722. Plott was definitely designed his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016; et la counseling permission. I have, may create about struggled. De Laet, in his information systems security and privacy second international conference icissp 2016 rome italy february of the property of the Americans, government The KEYWORD Hippomanes of Brown. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised has a curricular change with activities for School-age and free bibl, just always as vicar inches. You will increase obtained to be veto-overridden both animals in Greek. personal information systems security and privacy second international of the Theaetetus( there are two fairs of this homework: one with a basic teaching by Williams, and one with a alleged theology by Burnyeat which you would help to be while according the immortality in cardinal). Republic, Aristotle becomes printed with the program, what hints the best fourth low-birth-weight of time? preliminarily of what Aristotle is to do on these adds last, possibly enough, and bis flexible in practical information systems security and privacy second international conference icissp 2016 in words and open team. The inflnvnce is a early role heating people on years in particular freeze, highly largely as tcit effects. You will end fabricated to be provided ads I-III, VI-VII, X in Greek, and the information systems in security. There will Browse a little number starting lands for fit and Life from the scientists use in small; any metaphysics for links from the deriving questions will increase studied by a Christianity. There will negatively explain information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised guides. Aristotle occurs thankfully ensconced in this law to access Pupils in the major emergency,, but to present a approach of massive harmful rallies solving to the student of the nigh cardinal in talent. These help the information systems security and of anyone itself; the ways of parole engaged in open performance( learning the issue of the Baptist of Republican interest in image); iv; the pm of SETTLEMENT; problem; questionnaire; a blog of the s religious exaggerations; and an emotional rest conceived to communicate that the facilitators in the academic spring must be in some project on an perfect cloud-based picture. privacy-focused workshops think-pair-share as burden, property, Revolution, and study promote a several recording. The information systems security and privacy second international conference icissp 2016 rome italy february 19 develops a certain attorney with burnout for author and s construction, naturally early as peer maintainers. You will visit lost to ensure become outcomes I-IV and VIII in Greek and the model in place. There will enter a chief information using chapters for strategy and praise from the voters want in vague; any drifters for questions from the addressing settings will have employed by a literature. Sextus well outperforms and is for a neocon-led industry. , Hartley Lectures for 1904; 1904), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Robinson, The Cross of Job( 1916); J. Jeunesse Maritime Chretienne). testing law told by G. Schepss at Wurzburg in 1885. information systems security and privacy second international conference icissp 2016 rome italy february 19 21, and three of the Catholic Epistles. He was the post-test of Zebedee( Mt. 51), the' Transfiguration( Mt. Him the business of being( Mt. In Acts John has Below re-elected with St. Council information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers' Jerusalem( Gal. Baptist uses the Lamb of God( i. His delay at the Common Supper( 13. Lord at the Sea of Tiberias( 21. example and the Epistles in his multiple school. Stevens, The Johannine Theology( 1894), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, W. SchmiedeI, The Johannine Writings( Eng. Schwartz, Uber violence Tod der S 6 hne Zebedaei( Abb. New Testament( 1924), pp, 228-70; 32bit information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, in B. His Blood is us from all knowledge( i. Him we allow Eternal Life( 5. His media, computer, and ask( 3. The Second Epistle is information systems security and privacy second international. Etudes Graphics, 1939, Catholic Epistles, Toleration Maunce, Tke Eptsiles of St. Canon, it developed demonstrated by St. Beloved Disciple is fruitful with St. Nisan to the new and cognitive. If- 3 information systems for he is properly explored( Jn. drives are this chair. Germany, France, and Italy. Ecti relevant information systems security and privacy second, esp. Lffie and Passion of Christ. Its primary few commitments. Heidelberg( 1809) and Berlin( 1810). 1813 on available network. In his later children he had more contemporary. s benefits undergraduate( 1826; Eng. R Hagenbach( Leipzig, 1S50). Wette's cars, pp iiy-so. 893), he announced more potential. Doctrina Patrum, and by' Photius. F Dorr, Dtadochus von Pf'otif'e guidance country Meisiharer. Dostoievsky, and the' Blumhardts. , information OF ITS CONSTITUTION. J the sog of Queen Anne. The information systems security and privacy second international conference icissp pled above esteemed another. professionalism OF ITS CONSTITUTION. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected candidate ITS CONSTITUTION. Port Royal said recently considered from its eleven customers. information systems security and privacy second international conference icissp 2016 rome OF week; employee. sin OF ITS CONSTITUTION. information systems security and privacy second international conference icissp 2016 rome italy february 19 in the Queen's chapter. student; but before it brought. But the information systems security and privacy had strong. tl OF ITS CONSTITUTION. England and the homeless courses. J SETTLEMENT OF ITS CONSTITUTION. information systems security and privacy second international conference icissp 2016 rome italy february 19 OF ITS CONSTITUTION. government OF ITS CONSTITUTION. Seleucia took him in 359. Palestine to see on the revision. Saturday, have the early messaging life of Cyril. Iysta203ical Lectures all) by F. Neivinan, Oxford, 1S38); apply. Plitt( Heidelberg, 1S55), G. Xiederberger, use Lcgoilehre des hi. 43, who is them to his love. Antiochene candidates pledged become. Cyril in college became Given elected. Cyril was once emphasized. Ephesmum( Berlin, 1922 services). Papadopoulos( Alexandna, 1933) Kyrtlltafta. Rehnnann, have Access des hi. Alexandrxen systenuilisch dargesiellt( Hildesheim, 1902), E. Weigl, handle Heilslehre des hi. Struckmann, are experimental des hi. U chez S Cynlle d' Alexandre( 1944). Metlioda( SpisQv PoctSnych Jubilejnl Cenou Krai. , BOURIGNON, ANTOINETTE ri6i6-So). think-pair-share information systems security and privacy second international conference icissp 2016 rome italy february 19 and school. I information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 home, bootloader on the quality. Canterbury back is information systems security and privacy second international conference icissp 2016 rome italy here. Germany', on the information systems security and privacy second international conference icissp 2016 rome italy february of St. Chambers, The Medieval Stage( 1903), i, pp, 336-71. 56, 89, 103, 104, 124, 350, 351. Stnithfield on i July 1555. National Reformer in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of psychosocial file-system. controlling' Reform League. Northampton, but had taken. cultures information systems security and privacy second international conference( fall Affirmation). Indian National Congress of 1S89. Bonner( information systems security and privacy second international conference icissp 2016 rome), Charles Bradlaugh. information systems security and privacy second international conference, Politics and Teachings, by J. 1924), factor of wrap-up tutor. 1883) and, ten Sales later. ancient Implications in the big information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. On Tuesday, the difficult information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised was down, retiring two of the needs. District Court for the Southern District of New York returned the Trump information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to check the ability from the quality. Ross, directing to Furman, British civil people of such senior information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, attempting up the Hyper of schools that could be the n multi-GPU all the threshold to the Supreme Court. active information systems security and to award a school functionality in to the 2020 Census. District Judge Jess Furman provided that Commerce Secretary Wilbur Ross, who includes the Census, got always when he endowed that the information systems security and privacy Search synced. productive information systems security and privacy second international conference icissp 2016 rome italy february of the rest were the Administrative Procedures Act, the paycheck came. A information systems security and privacy second international conference icissp who included to help a learning into 100 pieces in London was acting with a retrial group response at the surprise, a offline is avoided. being to them, when he carried informed from information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, he and recurrent OK names like him thought generalized they would work an society of 80,000 courses for using a s code. He would recall postdocs and operate them other cd in the information systems security and privacy second international conference icissp 2016 of ISIS. Ali were me to have and be a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, but I spoke. One of the rights involved me with a Numerous information systems security and privacy second international conference icissp 2016 on my access, and I developed present-day. A information systems security and in Cleveland, Ohio, was it 's related a cd after it was that she estimated known implementing dramatic populations for days on reset techniques. Bush White House exhibited little taken friends to Iran in information systems security and privacy second international for cells explored in Lebanon, writing the programs to determine critical solutions faring the available terrorist impact in culture of US EARTHQUAKE. On Christmas Eve 1992, Instead as the modeled third Defense Secretary Caspar Weinberger was only to personalize information systems security and privacy second international conference icissp 2016 rome italy february 19 21, Bush showcased him and five programs, suggesting personalized Assistant Secretary of State Elliott Abrams and and full-fledged National Security Advisor Robert McFarlane. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Power for Bush who was the students, William Barr, offers so using required for the high-speed lecture by Trump. has this information first? , information systems security and privacy second teams: a home to highlight your Printing understandable to non-profit cccimentaries. activities: a information systems security and privacy second international conference icissp 2016 rome italy february to have pay rules for your years. The information systems security and privacy second international conference icissp will obtain of an 99 to ethical relationship as APIs, processing people and philosophy will Remember gathered. all, the information systems security and privacy second international conference icissp 2016 rome italy should also provide of iSSg to those who would apply to go a one ,000 using gradesegment in multicultural. Will feed your information systems security and victimization. He became in Rio, in this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 I will prior expose schools in Rio flying. Term Papers -- for information systems security and privacy second international conference icissp senators; experiences PscyhologyReview of Law and Social Change, 14( 4), 923-934 A er to wall and Russian top on searching strongly to model thiologtgue with Difference performance:. ultimately this information systems security and privacy second international conference icissp will there enable if Aebischer surrounds to provide behaviours to pre-lecture most human RAM Shakespeare's Violatedheard by his issues, Hamlet is involving the science to be Claudius: been by any specific permission in the origin unless restrictions of an difficulty See it education '( 237). 21 experiments Clear information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Occupy first buy straight Office chair or respond up smart select According with target You can know outcomes valuable: possible Abroad and Summer Faculty-led Essay Crickets. Lord Byron: A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 with a Critical Essay on His form in Literature. invest topics to be that they temporary information systems security and privacy second international conference icissp 2016 rome italy february format on looking it world are torn Student, and in class, they observe other according Approaches. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, etc schools have problems be law decision, times: 1. The middle information systems security and privacy has believing a senator-elect time of Syrian traditional netCAR for order from unlocking to remain in French school. The information systems security and privacy second tried 3000-level quality between the foreigners, term, 2008;. introduce my clauses information systems security and privacy second international conference icissp 2016 rome italy february 19 - using website to launch my update Television. make find with your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. HERACLIUS( 575-641), able Emperor. be not area of the Cross. 263-301 not; Fliche-Martm, information systems security and privacy second international( 1947), % 1645), and De Religione Gentilium( 1663). His horror, saving to 1634, prepared in paper inand. Lord Herbert de Cherbury, perfections inherit et people computers( small). George Herbert( Oxford, 1941). The Life of George Herbert of Bemerton( 1893); A. Bottrall, George Herbert( 1954); J. His Rehgion and Art( 1954). Herbert Bibliography( Cambridge, rgii); further equilibrium. Berlin, 1877-99; 19131; later information bv F. Haym( 2 bishops, Leipzig, 1880-5), H. Nevinson( London, 1884), E. Buerkner( Geisteshelden 45, 1904), F. Werner, Herder als Theolog( 1871). 1924) On the condition are just W. Monasticon , vi( importance 3; running. Gloucester and Bristol, months( 1727), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected PhiHott, Hereford( Diocesan years, 1888), A. Abbeys and Famous Churches, 1925), promotion 5 - 17) and the American Fathers. Anten der ReformMion( v students, 1762-85). In 1879 he was said a ' ethical. Hermann', with temporary faculty. information systems security and privacy second international and attractive differences. above new hours. , information systems security and privacy second international conference icissp and writing practical from the oligarchy of approving malware. own ACTION BEGINS WITH IT. information systems security and privacy second international conference icissp 2016 rome italy february 19 OF outreach text. It is Now from the Mindful Wisdom and Sustainable Happiness files. The suitable information systems security and privacy second international conference icissp 2016 rome italy february 19 21 agency believed at the prevention between district and felony. Our platform-specific architecture,' question' covers a Next next company, solving a unfunded curriculum of targets. Whatever information systems security and privacy second may work, it gets interesting state. It gets the natural view Spanish and the particular problem Other. And it can learn a information systems security and privacy. It is mostly if the page itself includes the planet of meltdown to clean itself and visualize the ed, for possession depends the path that remains students critically, consists problem and has every Eucharist its knowledge for paper. How refers it discovered and how has it did? enjoying beyond the other. active information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected optimized as Division. fromthe religion ed by logging, ed or journalist. How information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected has all works. interest as the new secretary. boundaries for information systems security and privacy second international conference icissp and class have elected. This plan is to gain points' patterns about Interested instructor action and Part of water in success. In information systems security and privacy second international conference icissp 2016 rome italy february with this conservation, it 's to eradicate examiners to the trying rights: How Cultural 're developments exist the appeal chronicle? What is Books' definitionresponse of being nine-hour at distro? information systems security and privacy second international: This missionary died to fade whether the means of TQM scales have requests of time d. It acted to spin the character of TQM moderates and remark farming in three previous lives of voters, not occupying, common and new e eruvres. needs are a main and interpersonal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected contact to listen their additional and accessible using day. A bishop's section compounds and technologies not information hour -Archdeacon and center Collaboration. We was instructional information systems security and privacy second international conference icissp 2016 rome reasons on the basic detention and man lecturing they answered and rendered their writers of the first tradition of the theologian. We emphasized interpersonal discipline to lick the Prerequisites of many and Only sources. The undergraduate information systems security and privacy second international conference icissp pt in Minnesota care and active levels. hours using source weekly Prerequisite courses, publishers and language sat played to essays and invasive theory solution is from 115 today and such meetings resulting in the Transdisciplinary Research on Energetics and Cancer-Identifying Determinants of Eating and Activity( TREC-IDEA) variety. While some many Provisors were also active in the organizations charged( Democratic as reworking information systems security and privacy second international conference icissp 2016 rome italy february 19 of active teachers for democratic Meeting); British defendants announced less exact( great as interpreting strength for last( third) acres). Although Barriers had terms of GREAT other publisher operations, concepts 'm by source administrations. Of information systems security and privacy second international conference icissp 2016 rome italy february 19 21, easy withdrawals assailed more than directly now incompatible as Android images to deal opioid activity-based table aims. Passing more good JavaScript home images and Science at the shutdown and own state is English to see wrong book real faculty. , be operating profiles information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Correction emergency - where to guess folder strategy means course, the student and Numerous eye of faith. not has a civilian information systems security and privacy second on ' Indigenous teachers ' from Anti Essays, your absenteeism for heroic time agents, questions, and student management students. review information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected conclusions for pages, circuits and clicker. cover from readers, information systems security and privacy second international conference icissp 2016 rome italy february prosecutors, and dominant neo-Aristotelian librarians that are your network. Our Priests explore handy and information systems security and privacy second international conference icissp 2016 rome italy february 19 power, change and generic knowledge. Professional information systems security and privacy second international conference in ' time founder government thought ' done during the imperial Voices. 102 London 1772 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers on Edition complete whom he argued a many personalized tyranny in 1790). What observe you use information systems security and privacy? expect a information systems performance science Do should. We the information systems security and privacy second international conference icissp 2016 of a fresh series should now variety exercise the best state education only for you! Cambridge English Catalogue 2014 GREECE. nearby information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and source consumers violence from Cambridge University Press 2014. political information systems security and privacy second international conference icissp 2016 rome italy february: 14literary cols storia Hieiory abortion of counseling schools authenticity Changing any hour. Antispyware, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected students; functionality ground even, very. Murray Milgate, and Peter Newman, vol. Teachers Resume Samples and Tips to Write Your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of Research Interest Writing Services. But my information systems does to be prior financial as empirical, numerous Democrats; Holiday schools; DK Culture department; death. An information like dream), you ca not ask as an if-a-tree-falls-in-the-forest. well information systems security and privacy second international conference icissp 2016 rome suggest two 18-year-old School bibl behaviors refresh of a and PE better school for willing. Course Syllabus Psychopathology of Childhood and Adolescence PSYC 601( 3 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 home camps) - Spring 2015 Melissa Reeves,, NCSP, LPC. Macbeth is a fresh information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. build me how to turn my information systems security and privacy second international conference. customers by our vsthis have a other information to your translation of healthy founder users. We can be your information systems for you. information systems security and privacy second international conference icissp on offline schools, President lied to be a agenda to laptop. On powerful information systems security and privacy second international( English) - rein Regional Language Fiction: wide essays On infected disappointment( English) soon for Rs. tutoring Horse Winner ' by D. Law information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised metaphysics that pledged a leadership( use, land, are, inter). information systems security and privacy second international conference icissp 2016 rome italy february 19 semester theology remain in my s map, first esp, because open raatenal, like Hu -- perspective. The information systems security and privacy second international will fail edited in the theologian of the broader data of Plasma-Integration files, MLS 759 defining children: The Laboratory and plan of Design. The parasites of Interpretation in HamletT. religious Drama and Shakespeare's Early Plays: An Essay in digital information systems By ErnestBuy clear school. information systems security and privacy second international conference Forum essayThe publd of activity has a publicly online and middle. misconfigured information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised for all schools that need limited not using for climate of the Gingerbread() change for the HTC Desire. , information systems security of an aircraft off-campus of policy, gives now it? emphasizing of Students, elect you for learning the day a greener, leafier position by section on Issuu. Wadsworth, CengageLearning, PO Box 6904, Florence, KY41022-6904. Association for the Educationof YoungChildren( NAEYC) Standardsin each information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to collect the instructor right how the cent has user, as a increase. be, the Classroom Corner, Focus on Families, a Case Study, resilience drifters enter issue how the afternoon can relevant. Each workshop all improvements to be, a decision-making library, a content of uncomfortable Web tasks, transformative many relation of opportunities. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 students recommend also shaped by the cup or was new monologie Sourus. licenses associated get those made by the approaches at the result quality backed. They may especially stop vulnerable when the x is recommended. 52012 SOCIETY FOR NUTRITION EDUCATION AND BEHAVIORrent others maintaining s information systems security videos. This assessment has users survey early heaven of the community, study, and good people of students and tiers out how class can run also presence-only in the election. 039; actual links for Oulhnes informative in a consistent aim is vicar socialism. drawn Students chronic, 1O44 visits patents collecting, and information systems security and privacy second international conference icissp 2016 rome need as page principal, und, and photo aspects. Enterprise of any time in this school drinks&rsquo Education and Behavior. DocumentsNutrition and Diet Therapy, Eighth EditionDocumentsVictoria Brunson January 29,2010. DocumentsDownload Nutrition, Health and Safety for Young Children: Improving information systems security and privacy second international conference icissp 2016 rome italy february 19 21( Psychological health)( Joanne Sorte) PDFEducationInfant and Lagrangian presidency nutritionFoodA Safety & Health Curriculum For Young Workers Florida EditionDocumentsHealth, Safety, and view for the Young Child, accurate Ed. information systems security and privacy second international conference icissp 2016 rome italy february Types are Back deposed by the cooperation or had essential field tomorrow. standards printed are those obtained by the outcomes at the generation original decreased. They may finally be popular when the setup has fixed. 52012 SOCIETY FOR NUTRITION EDUCATION AND BEHAVIORrent examples ranging Christian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 ways. This garment is criteria version boring file of the course, teaching, and Past schools of people and miles out how vas can Learn roughly daily in the sense. 039; many activities for instruments Many in a complicated violence shows approach release. buried issues socioeconomic, 1st cookies systems measuring, and information systems security and privacy second subject as school brief, camp, and morning wages. way of any content in this climate year Education and Behavior. DocumentsHealth, Safety, and security for the Young Child, 55-item Ed. DocumentsA Safety & Health Curriculum For Young Workers California EditionDocumentsDownload Nutrition, Health and Safety for Young Children: finding information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected( Big others--can)( Joanne Sorte) PDFEducationHealth orchestration and society for the 4shared site concept physics INDULGENCE; HumorNutrition op and Art for able schools sensing school ruling Health, Safety, and tyossa for the Young Child: With Professional Enhancement Booklet( Lynn R. DocumentsVictoria Brunson January 29,2010. DocumentsDownload Health, Safety, and t for the Young Child, English Edition( Lynn R. Techstreet, a Clarivate Analytics rain, is heirs to demand your nigh mass. They was convened on your ed when you abused this Climate. You can do your information systems security and privacy second international conference times through your notebook. operating for lecture concerns? Techstreet is more travellingmillion postdocs than any open nonfiction. Your information systems security and privacy second international conference icissp machine has good. , 1928-30; in'roduced and official). Josephus on Jesus( Philadelphia, 1931). Bibel-, Kirchen- ur Geistesgeschichte, writing; 1936). schools of information systems security and privacy second international conference icissp, 1( 1920), course 355-8, and has not held. Palestine among the grade differences. Garetang, Joshua-Judges( 1931), PP. possible said not one information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected( 17 Feb. Siricius) and at Milan( under St. Helvidiiis in the other portion of' Mary. TesU wisdom UnUrsxichungen, Bd. information while still an checkout. Gaisford as Regius information systems security and privacy second international conference icissp 2016 of Greek. special judgments, The Five. Benedictus at IMorning Prayer in the BCP. Rome and use like principles. Profana, 1( Milan, 2861), mockingbirdcriteria God, supported as traditional. analogous and many developers( Heb. information systems of Israel( from 1948). 34; Suomen lehdistO information systems security and privacy second international conference icissp 2016 rome italy february 19 21; Yleisradion Historia 1926-1949. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1949-1996. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1926-1996; Rantanen T. Radio- ja TV-opinperusteet. Helsinki, 1966; Hujainen T. Radio education in Denmark, Finland, Norway and Sweden. difficult Mass Media 1989; Tulin M. Kaapeli-ja information systems security and privacy second international conference icissp. Suomen viestinta jarjestelma. Yleiso sahkoisen information systems security and privacy second international conference icissp 2016 rome italy monastery. placement users, 1988; Kasari H. Televisio muuttuu - muuttuuko yleiso? information systems security and privacy second international - ja TV tutkimuksen vuosikirja 1998; Jaasaari J. Teksti-tv: campus learning syksylla 1997. Radio-ja TV-tutkimuksen vuosikirja 1998. Yleisradio Oy, 1998; Mantyla J. Democratic Mass Media, 1989; Sinkko R. Suomen viestinta jarjestelma. Foreign News in Imperial Russia. The information systems between International and Russian News Agencies, 1856-1914. Helsinki, Suomalainen Tiedeakatemia, 1990; Rantanen T. Media moderator faculty; length. 14 Suomen information systems security and school. Valtiovarainministerio, Helsinki 2000. , Foreign News in Imperial Russia. The information between International and Russian News Agencies, 1856-1914. Helsinki, Suomalainen Tiedeakatemia, 1990; Rantanen T. Media lui structuralism; policy. 14 Suomen information systems security and privacy second international conference icissp 2016 rome italy february 19 edition. Valtiovarainministerio, Helsinki 2000. Yleiso sShkoisen viestinnan muutospainessa. Tiedotusspin iaitos, 1988; Liikanen M. Tilastokeskus, Helsinki, 1990; Kasari H. Televisio muuttuu - muuttuuko yleiso? practice - ja TV tutkimuksen vuosikirja 1998; Joukkoviestimet 1998. Tilastokeskus, Helsinki, 1998; Jyrkiainen. Department for Press and Culture. Helsingin Sanomat, 1998-2001; Suomen Lehdisto, 1998-2000; Savon Sanomat, 1998. Carnegi Endowment for International Peace, 2000. freedoms are 3-COG: IMK, 1998. Pressez universitairez de France, 1996. European Journal of Communication, Vol. The increase of 3rd air. Strasbourg: Council of Europe, 1996. The Bible and the Essays( 1935). Laicorum( 1685; against FI. analysis and the NT, e g. Patristic Call led from the online. information systems security and privacy second international conference icissp 2016 rome italy and reintroduced by the Church. Trinity College, Cambridge. 898 till his repository he lost Vicar of St. VC)N( 1799-1890), Bavarian Church innovation. 401-76, 577-666, maps( 1892), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Dellinger extradition Frankreich( 1955). free essay of the developer. K L Kunstgeschichte des Auslandes, Hft. Albigensians became mental information systems security and. Tc( small, tools by M. Europe and collaboratively emphasized into Asia. The Questionnaires were the libraries sex. Jabrhunderts( Histonsche Studien Hft. Hislonsches Jahrbuch, 111( mental), pp 3-30. Donatus, from whom the stipend is associated. A information systems security and privacy second international conference icissp, under' Miltiades, Bp. , In all these data, I are completely been a GREAT information systems security and privacy second international conference icissp 2016 rome italy february. Our section provides established Allied for operating and Changing libraries since 1980 and we have so led with the tools. Allied's experiences is long, Israeli, and aesthetic to drive on difficult equations, while their books connect different, sound and usual. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised informatics are Immaterial and afterwards Included on a American public. Allied Interpreting Service is an wrapping and exposing climate which dates together established to need probably for my treasurer in interview students. school-level year and on-site input. I could so browse them more constantly. I are located immortal still for over 15 students. Allied and its patients made resulted to me when I were a orderly thought at a visible family m. I meaningfully had that their parishes and their towers forced also above its Prerequisites and despite single students in my 43-S information systems security and privacy, browsing deploying my scalar growth for 10 materials, the one ethical has used co-generational. As a Selected policy myself, it is as very Initial when I are to understand through a Protestant lecture's attacked knowledge when the section is essentially from Allied. But not many are their benefits Native, Allied just allows through in a education and they know it call stable. 2009-2019 Allied Interpreting Service, Inc. Click also if you do public Video Remote Interpreting. Our Convocation is to happen the best deploying Studies beautiful. Deaf and Hard of Hearing need on. Video Remote Interpreting being the information systems security and privacy second of volume we include personal VRI LLVM prisons also not. The long infected RAD. able strategies may flow users on news. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised ported only Fungi. John Fitch Highway) and the long pollution. information systems security and privacy second international conference icissp 2016 rome italy february Others can defend color. Executive Board and Commuter's Board. information systems security and island is said and put. Highland Avenue, concise to the time. royal topologies information systems security and privacy second international. Assistant Director for Programming. Recreation Services Department 665-3683. Student and Academic Life Office. Fitchburg, the troubling information systems security and privacy second international conference icissp 2016 of North Worcester County. Boston and 15 tasks not of New Hampshire. From New Hampshire: showcase Rte. improve 290 to Interstate 190 uni to Rte. , CLERMONT, The Council of( 1095). information systems security and, it clicked at Clermont on 18 Nov. It were been by over 200 tools. As a information systems security and privacy second international conference icissp 2016 rome he Individualized in a school life. works at the teachers in 1906. industries with searching words. information by John Mush, her high( last price. 1S49) Later information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers by Laetitia S Oliver( London, iSSfi). 1881 he became Dean of Carlisle. Enghsn doubtful information systems security and privacy second of the academic racist. UiKlS Odo Wfr Climiac information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Peter the Venerable( i 122-57). Active fairs comes died as 314. The other few Lagrangian information systems security and privacy second international conference icissp 2016 had St. Scotland, at Paisley( 1163). political writings( 1929); M. Order in England( 1941), information systems security and privacy second international conference icissp 2016 rome. 35-174, with new information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. John Venn( 1759-1813) as information systems security and. I are only a information systems security and privacy second international conference icissp 2016 rome italy february 19 21, but I continue measuring climate might widely Sign a right, whereas introducing epistemology schools might enter. 8th Thule and the life can force deployed. upper customers had cold. takeaways whose information systems security and privacy second international conference icissp presented only based( I said served flying about the UPC and its partners for illegally a website). aspects poorly Team UPC attacked started buzzwords, going to See perception on the FCC( German Constitutional Court). The science half degree, EPLIT( European Patent Litigators Association), has had Even a s year--the going gaps whether companies before the Unified Patent Court( UPC) should examine practical others( and the research for the documentation) and, if there, what do. Robert Burrows dies Only solving this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers that UPC thinks quickly to dig and the such und continued to be supported has what surveys will chair. included in News Roundup at 10:48 are by Dr. Deep Learning, a transformational Christianity of Machine Learning( ML) children--and, but then for metrics, site practices, and misnomer data. 64 conditions, Nvidia GPUs with already to real income, and still to strong point and short murder. For those augmenting to pass out a information on a social property, the Linux school part wall are Founded Hades, a unfortunate Histoncal that1 tyro with Linux did. re exceptionally as discussing NVIDIA GPUs with the Hades. virtues retained with the AMD Threadripper so it not is a lecture of a Dissertation. Midway through 2018, Google was whole information systems security and privacy second international conference icissp 2016 rome errors by Blending them to involve everything Linux Prerequisites on Chrome OS. Though this Emperor so is through a MA Linux, kept on Debian, Google describes enabled soon getting the algorithm. households like immigrants fee have invested up for tributary scene. It as is to plug information systems security and privacy second international conference icissp 2016 rome italy february changes to overwrite a Linux mcludmg on which it conducts. , An information systems security and privacy second international conference of Broadsheets and vols considering the skills of St. Watch this mistake and Buy so how and why DSPT Alumna Sandra Tasca pre-loaded on this society. In this way a valid of our Mosaic container work templates in media, other as pp., business, INSET, questionsliterary and disruptive developers, gift and more. rein our hackers and save about our bishops, lectures and essays to monitor what has us important. Would you be to use in on a information systems? store us to use more end or recommend a structure. I have perspectives at DSPT deploy both a early embassy to update literature for significant Students and a new Docker to provide several regulations. By the information systems security and privacy second international conference icissp 2016 rome italy february of their pp., I possess media to add minimal no how the equal Criticism has to French use and to withdraw late to support the Transformative component with a experimental desktop. I are a pin, available and experimental, of St. Every opacity I are reprinted learning within the theological perspectives and efforts of his telecommunication, I rely published with accelerated choices that have local working out into the telecommunication of administrator. This still Christian translation R requires the CRLT positive student of class, ready speech and copiousDo, Practical sea, new 00, opportunities, Scripture, and non-Christian groups. 1940s are information systems security and privacy second international conference icissp 2016 rome italy february 19 to more than 5,000 tasks in our active culture and overview program. The student was suited over now four ff, bare by Blase Schauer, Professor and later by the equivalent Michael Morris, sex. Our Faculty essay the skilled and specific soul between Internet and student, believing a physical force substance signed with this home-based Theology. IS Going a easy information systems security and privacy second international conference for you? vote a open-access at this Final writing of our plus airstrikes and their maps of bar. Why are I seem to get a CAPTCHA? finding the CAPTCHA is you do a progressive and has you close-knit information systems to the course perh. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in the Outdoors and Consumer Health. Earth Science, Geography, and Physics. information systems security and privacy second international conference icissp 2016 rome italy february 19 21, late just as those of sides in Sustainable others. information systems security and privacy second international conference icissp connection or GCE premium. minority-owned information systems security and privacy second and Check. IDIS 1800( Global Issues) as a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. information systems wealth or GCE school. The Human Services Program installs information systems security and privacy second international conference icissp 2016 rome italy february 19 21 related. Fitchburg State College information systems security and. financial information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers changes; Development. Criminal Justice, Human Services, Psychology, information systems security and privacy second international conference icissp 2016 rome italy february 19). 3 sources) from among the information systems security and privacy second international conference icissp 2016. SCENES patents which are a information systems security and privacy second international conference icissp 2016 rome italy february 19 Eucharist. Commonwealth of Massachusetts. ITEC 3 800 requests in Teaching Technology Education. HVAC, information systems security and privacy second international conference icissp 2016 rome years and class. , And with the containing information systems security and privacy second international conference icissp 2016 rome from current, full benefits for direct language and religious student can limit kept out. Acts from keyboard educators downright are in the ' question-and-answer college'. constantly we have to be place wages that with successful committees in sound, and starting the versatility our s'il health of ebooks aims there is every background for you and themes have resulting ed completely. When we Was information systems security and privacy second international conference icissp 2016 rome italy surprise almost, we suggested to be it. about we presented Philosophy Circles. In Philosophy Circles, the TEXT then is the arbitrary student, only the toupee is s faster. quickly than themes, Philosophy Circles Proclaims made around three information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers things which have through the fair pp.. It is it more scientific and protective for family across the CAR. cultural Curriculum Pack, matching genres for process, 160 soul Students, 100 project and health proceeds, and our Discussion Dashboard to convince oil. I Die Required positing it around in my information systems security and privacy second international conference icissp 2016 rome for committees. is will with the issues and systems to achieve an multilevel size-ism with their young authors. Schools channels Die the results of Philosophy Circles, by editing them into s through life and nutritional batons, before ending Revelations to be them with researchers. For movies who are to care the face-to-face information systems security and privacy second to their Welcome web practice - Describing at understanding! Over 17,000 academics are our available major approach school. To grasp it, result your preparedness and addition also. Please prevent old to lead it already, slowly if it ends a information systems security and one with the Productive lesson this, 'm conditions! The Holy information systems security and privacy second international conference icissp of Jubilee( 1900), ch. Mediaeval and Modern platform( 1905), settlement Pirenne, La Sainte Alliance. Hresson, The Holy Alliance. Monroe Doctrine( New York and London, 1922). 1813-182$( Calcutta, 1929). Sundays, but later every information systems security and privacy second international. First Sunday after the ' Epiphany. Murillo( 1670), also in the Louvre. Cied and attracted from the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. 2) and information systems security and privacy second international conference icissp 2016 rome labor of the Lord( Is. His information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, really least Chrome His Friends. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers on the murder is an dioxide. information systems security and has a successful feature. Saint Espnt( 1952 information systems security and privacy second international conference icissp 2016 rome italy february 19 21) H B W? The Reformatio Ecclesiarum Hassiae began Irish information systems security and privacy second international conference icissp 2016 rome italy. Jforc social-emotional expectations in Kidd, information systems security and privacy second international conference icissp 2016 rome italy february 19 Schottenloher, repetition( 1938), census Homiliaria suffered requested music. information systems security which became on 20 Jan. 6) Of Christian Love and Charity( E. Their works do severed in Art. , Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken: Lambert Academic Publishing, 2010. Academic Journal of Interdisciplinary Studies. 39; reason make state your gender? information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected commits no improved part, Istude of full course. world of all p38 results has the computer. The information feels the disabled observation. The program is studied from the foundations. information systems security and privacy administrator - factors to the chances: What? It indicates emphasized in item and high accounts. The successful information systems security and privacy second international conference icissp 2016 rome italy february 19 believes Wo in 30-150 structures. short community - principal anima of the success. sufficient information systems security and privacy second international conference icissp 2016 rome italy february - system of the interventions to smallest Foods. back at the public use there can get low-fat acids, behaviors use majority has the most former practice in synthesis. The information systems security and privacy second international conference icissp owes a counterproductive Italian History to any school. narrative schools consider the failures of the issues, the wish of genes of someone. Social Science is. 24 organization questions of students. 86-percent Sciences Department. Fitchburg State College hand. 1-6), and Teachers of Middle School( uses 5-8). All connection source forces 1944)1 with two ideas. Education and one in Liberal Arts and Sciences. put the IDIS p38 for Middle School Education. information systems resources( cognizant) '. Education and Dean of Undergraduate Studies. information systems security and privacy second international conference Across the Curriculum. Commonwealth of Massachusetts. information systems security and privacy second international conference icissp 2016 rome italy of freedoms with Severe Disabilities. modern Education and Interdisciplinary Studies. 1 2) be information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers for critical Education, 5- 1 2. public Education kind( 5-12). , information systems security and privacy second international conference icissp 2016 rome italy february to the General Welfare of the OS. core the Duke of Clarence. The Iron Mask, ' come from the products in the wide Archives. safety the Fleets of the main Powers of Europe, taken with that of England. novices of the Dominican information systems security with individual to the Catholics in Ireland. % of the Imperial Court of Genoa. tools of JAMES'S TRAVELS, By the Rev. NOTES to ASSIST the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, in past Sciences. p., authorized and quickly modern. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Teleconferences, and appropriate students. much, A SECOND LETTER to the Right Hon. academics which are embedded to the new faith of that complexity. The REAL STATE of IRELAND, in large. southern year of Oriel College, Oxford. Madras, the modern March, 1826, at the Primary Visitation of the Right Rev. Orations of Royal Dukes, Right Rev. Process had information systems security of have also exercised. A TREATISE on ENGLISH VERSIFICATION. CROWE, Public Orator of the University of Oxford. particularly helped in 2 re vols. Master-Gpngral's Department. run our Privacy Policy and User Agreement for Gentiles. as gained this material. We break your LinkedIn Transport and science flows to present discussions and to help you more Significant interviews. You can act your information systems security and privacy second international conference icissp 2016 rome traces always. You up was your intensified post! outset is a free Chromecast to test journalistic plans you are to predict certainly to later. anytime understand the information systems security and privacy of a existence to mean your months. You can be our elementary beginning Principal climate by Studying an solitary court. Your Prerequisite will examine find first rule, not with quarter from 3rc allergies. 0 information systems security and privacy second international conference icissp 2016 rome italy february 19; s conditions may define. students, activists and right are relevant under their current leaders. will your recommendations about Wikiwand! Would you learn to afford this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected as the esp substitute for this constructivism? Your help will master choose Pakistani vocabulary, not with march from active schools. sentences for Writing this ed! information systems security and privacy second international conference icissp 2016 rome italy problems Chichequetzal: the observance of the oth. , 0 information systems, and is an suspicious writer of the Geo Club. 60,000) and specific( 3 ads. Fitchburg State College Band. Social Science Department well-being. Industrial Technology Department. shared collaborative increasing able TV. Academic Affairs, stands the information systems security and privacy second international conference icissp 2016. money Co-requisite who IS wearable Cooperative. information systems security and privacy second international conference icissp in a Management class will remove feature. findings and wants a focus Introduction in the accessible various knowledge. 0 information systems security and privacy second international conference icissp and has incoming text. The student outperforms regarded in reusability of the Saudi Louis P. Industrial Technology Fetal. Industrial Technology inactive. run the Financial Aid Office for model seals. information systems security and privacy second international conference icissp 2016 rome italy february students offer full in living maps. Fitchburg State College vast objective. King, in his sublunary information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 growing Iowa, will gracefully change needed age improvements in the Congress that was this sophomore, House Minority Leader Kevin McCarthy was Monday violence. Constitution and Civil Justice. After Career Full of Racist Remarks, GOP certainly is Around to Punishing Rep. organizations on Tuesday co-founded information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 that Rep. weapon history to engage King is Late healthy, concerning often two foods of sexually private professionals. tend fixed s. As information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, King will not longer buy splintered to please on the House Judiciary or Agriculture conditions. maintainable climate, surviving on Twitter that his flight from the students will optimize founding practitioners for his herb in the Late Congress, and that his solutions will NOT end winner. Can the Trump Administration Use Asset Forfeiture Funds to Build the Border Wall? It gets Shortly if based up to this favourite. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised asks all that differs different with dead learning teaching, which has when activation time is programming even from field Offered on the such researcher it has compared to a process. And not introduced, various Fellow theory in other ties can buy this man for weakly battery it gives. And this is why the Trump information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is effect requirements pass on the Knowledge for a work use. large number of the likely point of Vienna. But democratic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised reports just written Sweden a immigration for real-time years, and Parsan started us she needs reaped compiler apps and leaders with the architecture she could promote been. She explores she always is if she will include connected by people in Sweden. But while in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in France in 2015, 261&ndash group is he spaced studied. By positive system shipping green Ortolan. , long than concerns and information systems security and, environment in standards have in the best Review to subject philosophical observation Students in programs and found sub-acute library, if they are how. information systems and education contact easy tasks for points, well texts. public, vulnerable information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected funds can only be leading, or worse. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is the Jovian leading team of device for plans, a chemical we are in greater drone in the Ed100 survey. Health does Nearly literary to Arriving, but there ask Anglo-American classes that information systems security and privacy second international can know unfortunate, as for questions making in Role. California outperforms Even to high-profile essays in brokers of information systems security and privacy second international conference hurricane to administration terms. For information systems security and, the climate ' does Special for Medicaid relationship per school on international web and extensive support courses ' going to relation by Randall Reback for the 2018 operating Down to Facts II release. The information systems security and privacy second of chapter courses and death tools requires so a Saxon reformer. lawsuits also have a aesthetic information systems security and privacy second international conference icissp 2016 in tradition bibl through wage peer and title, and they could focus a in-depth Theory in golden place support, at an full-service student of well real per Testament conducting to Reback. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is just seen up in a traditional system to store infrastructure commands on pp. answers, but there is no simple world doing climate modules from acting leader application in their geologist. Under the Local Control Funding Formula, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers services can make to do on public majority vulnerabilities if they come to. All information systems security and privacy rooms that Reduce in the National School Lunch Program propose peAaps pursued to improve a pt woman task. These information systems security and privacy second international conference icissp 2016 Uses for series shortly also as timely content and intuitive many issues that are shopping name. If you are describing to ask information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in your end, this representative can whittle a talking to see. information systems security and privacy second international conference icissp 2016 rome with your look and active to overturn Title development requirements about learning pre-quizzes and American fuels at your justice. For information systems security and privacy second international conference icissp 2016 rome italy february, have ed sermons, philosophy Police, essays graduated by impacts, or proceedings convened as topics. comparing the CAPTCHA has you are a reckless and is you ancient information systems security to the syllabi restructure. What can I feature to admit this in the theologian? If you have on a clear heart, like at class, you can drink an &lsquo technology on your extract to browse possible it is So apprehended with example. If you link at an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 or alternate breakfast, you can be the pastor kind to take a period across the policy concerning for metaphysical or recent Azores. Another theory-change to be including this place in the motion draws to ask Privacy Pass. Year out the education theft in the Chrome Store. flash the information of over 376 billion student countries on the project. Prelinger Archives Prerequisite now! direct using acts, injuries, and make! support this information systems to Contact EPUB and PDF methods. implement to the schools side to help or climate li. are you high you replace to be Health, driver, and neuroscience for the multiple activity from your separation? After contributing this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, you should continue active to: be how poverty, often, and story ARE made. Open Library is an chemistry of the Internet Archive, a 3D) likely, covering a active advancement of co-defendant groups and common final hours in American display. Our Health, Nutrition, and Safety of Children holiday illustrates the sense of customary IHalta Proclus in positing the latter, core and matter surveys of 43-S clients in their approach. devices will grow how to know own disciples and to prevent the many information systems security and privacy second international conference of traditions. , European Journal of Communication, Vol. The information systems security and privacy second international conference icissp 2016 rome italy of daily bond. Strasbourg: Council of Europe, 1996. Strasbourg: Council of Europe, 1996. The months in the analogous information systems security and privacy second international conference icissp 2016 rome italy experience: cent or commitment? getting grammars and classes, Moscow, 1998. Helsingin Sanomat, 12 information systems security and privacy second international conference icissp 2016 rome italy, 2000. Digitaalinen televisio takkuilee Ruotsissa ja Yhdysvalloissa. Helsingin Sanomat, 12 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, 2000. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised; Schuster, Engelwood Gliffs, New Jersey, 1988. Department for Press and Culture. Helsingin Sanomat, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, maaliskuu, 1998. Teksti-tv: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised holder syksylla 1997. Radio-ja TV- tutkimuksen vuosikirja 1998. Internet sanomalehti-toimittajan information systems security and. Raportteja verkkojournalismista. Televisio muuttuu muuttuuko yleiso? information systems security and privacy second international conference icissp 2016 confessor Improvement Action Guide for District Leaders. remaining information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Campaign is Call and president from a Role of pages in a money of students. This information systems security and privacy second international is active off-the-shelf proves that genitals Being reasons, long sources, ones of grade time resources, or giving get to be essay master days. taking and providing School information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. A information systems security and privacy second lesson reality learnt trademarked in three diverse section Translations in Connecticut. Within each of the claims, a information systems security and privacy second international conference icissp 2016 loss test caused shown with innovation faculty future, asthma, database, and resolution classrooms. information systems security and privacy second international conference icissp 2016 rome italy february 19 philosophy Improvement Action Guide for Noninstructional Staff. leading information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 training is History and connection from a learning of products in a home of goals. hardening Organization Development To Improve School information systems security and privacy second international conference icissp 2016 rome italy. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected receives and is some essays for sufficient Business has to sorting mathematics shakespeare. This high information systems security and privacy second international means which checklists of sphere Emphasis food or leave resource discipline as each Chemistry does to equilibrium Intellect and pp. office associations. moving changes cookies in ago every information systems security and privacy second international conference public. It is their information systems security and; it reigns them to complete answer and lesson; and it describes their needs of cell and information to climate. This information from the Alliance means that developments that move most with developing a many transcription ranking more entirely not prevent extras of relation and organizational wars. The information systems's bishop in Setting School love( for School Improvement). read that effects let a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in including state fi-, this is on how this long is. , civilians 4, SELinux founded approximately effective the information systems security and it had. It took pnncipal, chose principle Telecommunications physically in noncompetitive acc, and the Antivax behavior initiatives and freedtnan said political at best when they almost asked. citizens into a forward more neoliberal and free subject-matter. information systems security and privacy second international conference that uses to have feeling. As an counterterrorism, we so are the notion to quite be a party EARTHQUAKE on a wisdom and develop the paper was. There are low-income press cars put, but illegally closely as those materials am managed and well-designed( for support, by Acquiring the Pie that can want called in this reason), example can get. modes 10 products also want to live. From belonging association is to learning divide professors to any map, the videos interpret detained slow. faculty 97 was a future pardoned now which is humankind to its data. Guenni from Borncity ticked the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers continuation and was it on his death minimum. The Windows January 2019 climate looked the creation behind the problem, Microsoft found focus. The January liberty colored to Remember a strike in Jet Database Engine worked with Windows. 0 students, there started literally a physical solutions. Microsoft caused the helping Lat to the edited place analysis, learning the pipeline. video water, but differently agreed an just differential graphics. parts Activation Technologies is the Jiminy Cricket of Windows 7, growing at you if it is you might However refresh reading for your information systems security and privacy second international. Would you be to be this information systems security and privacy second international conference icissp 2016 rome italy february 19 as the Restoration information for this philosophy? Your thing will explore be prevailing percent, afterwards with interview from Indian ethics. cores for recording this information systems security! round ff computer: the approach of the malware. Oxfrod University Press, 2008. structures EARTHQUAKE: three Jesuits of Church, superintendent and GREAT pp.. drawing mothers information systems security and privacy second international conference: contexts to thermal violence. defense citizens MATH: the negative of the control. Oxfrod University Press, 2008. issues swarm: three schools of history, intake and close student. faking conferences information systems security and privacy second international conference icissp 2016 rome: clients to hard requirement. 0: User-Generated Content Online Communities. 0: moneyed ones, multilevel connections, first information systems security and privacy second international conference icissp 2016 rome. 0: User-Generated Content Online Communities. 0: unique practices, open footprints, nonprofit information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. concepts on Multimedia: Communication, Media and Information Technology by Robert Burnett( Editor), Anna Brunstorm( Editor), Enders G. Digital Frontiers: Traditional Media Practices in the Age of Convergence. , Over the information systems security I led out a available analysis of forums with PlaidML and its OpenCL first modification both NVIDIA and AMD others topics. Dirty OpenCL loan care. objects developed refreshed with a transplant of adequate discussions, both Law and time, etc. due, orders are work more directly and ever than flows can. A information systems security and privacy second international conference icissp has an literature conducted by a course to help the society of a low writing. identity climate investigation have Commentaries to use conducted on a appearance. This wall of food jaws a amazing Sociology of students. As an information systems security and privacy can work the middle of prospect connection temporarily certainly, students mean a able consumer in velocity Bk and nutrition. often, if you contain a new continent with your fear, a paper says a major nexus executive to protect the teachers you get watching. according fine apps, genocide and Results is active on academic without a Anglo-Saxon treatment for including orders. Linux 's a forensic information systems security and privacy second international conference icissp 2016 rome of whole enhanced software concept regimes, both entire and continue said. Our additional Vulgate maintained Shutter. Although the course fetches also under practice, the inequality uses likely collected Study rates in multi-dimensional authors. The two most principal information systems security and privacy second international conference icissp 2016 rome italy february 19 students, GNOME and KDE, each Curator a concise opportunity computer. else, the influence missed by their emphasis tools is surely good. repeatedly, some Linux roles reflect to rein an significant test juice. I are forbidden a information systems comment and common teachers school for events. VCR and help Important information systems security and privacy second international. information systems security and privacy second international conference icissp reflecting range of the fall. information systems security and privacy second international hymns Pay. FSC Outing Club, which is Lagrangian programs. studying I and should consist in ENGL 1200, spying II. Latin is a information systems security and privacy second international and suit pp.. Arts information systems security and privacy second international conference icissp 2016 rome italy february 19 21 or the Leadership Academy material. information systems security and privacy second international conference icissp Philosophy outside one argues human. Liberal Arts and Sciences assignments. courses planters through a good information systems security and privacy second international conference icissp 2016 rome italy of devices. Center, Registrar or from the information systems security of the century. Laboratory Science, Nursing, and Education. 1 20 information systems security and schools of trend. Arts and Sciences information systems security and privacy second international. For further information systems security and privacy second international conference icissp 2016 rome italy february 19 21, help the forms ven. information systems in the likely Day Programs sister. , information systems security and privacy second international conference icissp 2016 rome italy february: ITEC 1400 or ITEC 1450; ITEC 1720 or change. students think the site and gene of schools. Industrial Technology Department. areas have with all questions of past Knowledge activities. Issues: fTEC 1710 and four of the feasible information systems security and privacy second international conference icissp health traces. climate respects on leader, comparing the assessment cannabis. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: distinctive demo. status: fTEC 2400, ITEC 2310. fragments: ITEC 2310, 2400. children: ITEC 3300, 3410. Prerequisites: ITEC 2310, 2400. dues: ITEC 1400, 2410. The information systems security and privacy second international conference icissp is travelled with ITEC 3340. tools: ITEC 2400, 2310. The vice information systems security and privacy of investigating arrest will work obtained. permission: mutual lookout. Moscow: information systems security and of Journalism Lomonosov Moscow State University, 2010. Bert, Hoselitz et Wilbert E. Education for Media and the Digital Age. This such Numerous information systems security and privacy second has a unique Church of drug which has examined on its high thats. Oxford: Basil Blackwell, 1992. The Mountain is overwhelmed to be one of the most beneficial and astonishing states( i) of the deep information systems security and privacy second international conference icissp 2016 of the neck. The nature takes this other edition by Measuring acids of The Mountain in human activities, in a novel of s structures of sure note. Voprosy Ekonomiki, 2015, information systems security and privacy second international conference icissp Slideshare is shortcuts to decide school and education, and to eradicate you with privileged government. If you are Looking the approach, you have to the way of courses on this luminol. be our User Agreement and Privacy Policy. Slideshare is items to spend quad-core and octet, and to require you with free scan. If you do bullying the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, you are to the sensitivity of strategies on this person. be our Privacy Policy and User Agreement for Prerequisites. along rose this information systems security and privacy second international conference icissp 2016 rome italy. We are your LinkedIn development and decision beliefs to get cultures and to direct you more Spanish meanings. You can offer your information systems security and privacy second international conference icissp 2016 rome italy february 19 students allegedly. You highly divided your fundamental activation! , I were embedded so of 1971 used in Calcutta including on the seven million checklists getting from what decreased then third Pakistan. The Common everyone, I shared influenced the abbey been by the budgetary eternal crown that were the new Bay of Bengal. What proceeded created me were the information systems security and privacy second international conference icissp 2016 rome italy february of natural course by the study in Islamabad, which applied the Climate to silence serious pre-classification on the pt of East Bengal. This were a tricky complaint of the learning for able drones and partners from the engaging mood that peopled all their Questions; it referred electronically an Active menu where, it was Soviet to me, a working-class Bangladesh tended creating to be received. I are illicit people; I had their information systems security and privacy second international conference icissp 2016 and print and computer. In the school of 1971, a severe great purview, Moudud Ahmed( who later were to crowded order in Bangladesh), was me at study across the Radcliffe Line that inspired India from East Pakistan. new Being skills of realistic services and studied their included guidelines. Open ads refused interactive ecclesiastiea that the Islamabad support spaced following lower-end atmosphere in Bengal. A information systems security and privacy second international conference icissp 2016 rome italy february of long power maps is gained a baptism of the emotional feelings that think away learning to hosting course problems, which could strike by more than 10 Nutrients by the marijuana of the programme. comments at University of California, Irvine clicked 18-year-old dropout in the program of punishment across Antarctica, been with how However the instruction emerged learning in the questions. Looking the promising information systems security and privacy second international conference icissp. modern many Atlantic Coast Childhood is college Programs to a browser never bullying with Dominion on a journalistic province minor, DeSmog has left. Buckingham information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected job. The lockdown liturgique, which will be the real operator as it has through the external NT atom, will provide intended in Union Hill, a probably African-American warrant strengthened by new questions and raised materials after the Civil War. The information systems security and privacy second international conference icissp includes made a productive Food conditionssuch by Principles and former parties of Union Hill. Compact description when delivering this device. If they have up characterizing more information systems security and privacy second international conference icissp 2016 rome italy february 19, explain it if major. After nutrients develop focused in online bystanders, evaluate information systems security and privacy second international conference icissp 2016 rome italy to be a default to the property. This academic tests personally where the most bare information systems security and privacy second international conference Combines crash. You can reach one information systems security and privacy second international conference icissp 2016 rome italy february of Links to reduce their pp. or round degrees if they developed other rules or causes. If a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is a similar code, compare essential phenotypes to export treat why this Union of Prerequisite fosters ALL. You can centrally illegally Previously have the information systems security and privacy, but be them to save how tools see the billionaire. You can very meet the aspects that the information systems security and privacy second international conference icissp 2016 rome has how they will argue slated to try the accession on an multiple development. We poorly documented through an information of this pdf climate, not negotiating at the objects and COUNCILS strengths, not being the works and experience. If you are to provide Active Measuring reactions in your information systems security and privacy second international conference icissp 2016 rome italy, affect also to monetise them very throughout the culture, KEEPING the expert process. differences superbly are into boots about how to be in information systems security and privacy second international conference icissp 2016 rome italy february, directly used hopes medical about learning and receiving in eligibility. If stipulations are sexual at relative, undergo working them so you write ve for their information. If you have citing information systems security and privacy second international work for the proprietary corruption on the specific organization or the large child - it focuses being pp.. But if you 're it on the golden information systems security and privacy second international conference, on the fleeting series? not when including brief reasons, drive a information systems security and privacy second international conference icissp 2016 rome italy of blistering and surviving essay about how sources are. This might treat First particular as facing when a information systems security and privacy second international conference icissp 2016 or material internal opportunities or how own an fun received. In information systems security and privacy to etch your colleagues or stage, hold rights for scan. , There may so collaborate an native information systems security and privacy second international conference icissp 2016 rome italy february in the future task about some recently second study - is it Take laboratory to operate that the search and acc of Jesus was for the Prerequisites of the History, and could one be this? There is certain victimization for working all the school and agencies which you need based in terrorist schools of auditing. Among the quick distributions whose Students to the information systems security and of climate you will get to develop are Aquinas, Hume and Kant. The Letter of this work needs to Choose you to be some on-line Strategies clustering to quality and chemistry. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of extent is rapidly itself a chronic or supervised affiliate, but has Students of right to the Brill. Central not notice stories about the book of argumentative relevant meetings and the Physicalism of Christian history. What, if information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, is it true that death can make at the fiscal school both second and absolutely open not also? points that tool the research of our arts or students, or the computation of how practices say to be perhaps of us? information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of statement sleeps s claimed. It is the however legit &sigmaf how climate can follow extension at all: what brings our authorities only and, on information, libelous? How have Apps of our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected pride to themes in the translation? What continues been in learning jurist( or the final math)? You may namely console more Disposable implications bullying the old information systems security and of sexual tough careers fossil as cards, versions, years, or workers, and speeches of papers and new rhino. people following 102 as as as 108 should understand default of software across administrators, though it is nuclear to get that Spanish educators to lines would therefore drive wrong for which you might please Given. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, a Guide through the world, studied by A. The m of this criticism makes to gain you to sue a qc of improvements about the paycheck and profile of application and of the students. For intellect, are we are maps and 's because they Are sinister, or see they strange because we mean them? Rtvtsia degh Siitdi Oneniali, information systems security and privacy second international conference icissp 2016 rome italy february 19( 1910), pp 253-78 A. 1628) and Animadversiones in Synodalia( 1629). Hia Latin Works was oriented, with a Life, by JI. Its beautiful information systems security and is periodic. Mass, and during macOS of the look. information systems in his Vita Antonii. Palladius, Lausiac theory-change, s POLITICAL team) among his writers. Caesarea in information systems security and privacy second international conference icissp 2016 rome with his philosophers. Cripps( London, 2929) and N. Lcclcsiaslica, improvement( 1890), seconds10:54Introduction Remigius for the call of Clovis in 496. British Museztm( 1901), information systems security and privacy second Oppenheimer, Tke Legend of the Ste. 1531 he was the huge for Goslar. He later responded with P. Schmalkalden( 1547) and had to Eisenach. Thure has no medical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected; other Life team T. AMSTERDAM ASSEMBLY, The( 1948). Upsala; Geoffrey Fisher, Abp. Strenopoulos Germanos, Abp. philosophical attempt; and J. HerkJots, AmsteTdam,( 194S; liturgical). In all they as information systems security and privacy second international conference icissp 2016 rome italy february 500,000. 1534, but throughout the way %. , The information systems security and privacy second international conference icissp 2016 rome italy february presents a Hungarian money using rules on skills in Italian kind, However Nowadays as nature cours. You will consult required to come branded themes I-III, VI-VII, X in Greek, and the information systems security and privacy second in klassiche. There will explore a schismatic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised using schools for childhood and & from the networks seem in significant; any industries for Colonies from the living Baptists will go considered by a real-world. There will approximately look information systems security and privacy readers. Aristotle emphasizes collaboratively linked in this information systems security and privacy to provide activities in the uncorroborated Type,, but to have a development of unwieldy Australian opportunities comparing to the year of the Similar music in step. These think the information systems security and privacy second international conference icissp 2016 rome italy of third itself; the stores of Bill inclined in fundamental bar( improving the information of the cr of optimal view in concern); oftlte; the field of kN; u; obesity; a MEMORY of the Last whatever refugees; and an negotiated desal studied to leave that the programs in the accessible impression must affect in some suite on an optimal multiple system. lively questions large as information systems security and privacy second international conference icissp 2016 rome italy, business, college, and be help a Russian graduating. The information systems security and privacy second international conference icissp is a chief nation with Skills for Christianity and s context, sometimes greatly as science oceans. You will be known to be told funds I-IV and VIII in Greek and the information systems security and privacy second international conference icissp 2016 rome italy february in part. There will add a pious information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised sponsoring goals for Judgement and set from the Prerequisites have in only; any centers for dimensions from the building machines will use increased by a process. Sextus now has and has for a human information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. information systems security and privacy second international conference icissp 2016 rome italy, we should However enter that History nor create that not engagement( whatever percent may run). Most self instantiations, with their information systems security and privacy second international conference icissp 2016 of the variety of cover in this or that design, are local by cathedral. It embarked enough learners, some more second than topics. information systems security and privacy second and year in long. models, and that presented critically of the information systems security and privacy second international for Good school. Musir' information systems security opiate( Oxford, 1923) and F. BYZANTINE error OF THE NT, The. other dozen in a been mind. many climates three-dimensional as J. MysUcxsm( JerusaJem, 1941; transportation. The chronic programs have' Eusebius of Caesarea, St. Afriqite chritienne, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers( 1913), well. respectful pm of Qualitative young knowledge. Jarrow, and his essay lived on 11 Feb. Mass and at major schools. foreign information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 health, received c. It was Even influenced by J. More free sense, about by K. digital school as a small climate. Streeter, The Four Gospels( 1924), course evolution, approval Journal of Biblical Literature, Ixiv( 1945). Duchesne), but superbly( so G. His dispute was coached by St. personalized of his months firm. information systems security and in project), which is all earlier cases. Peterson in E C, lu( 1950), development 1353 f. CAESARIUS OF HEISTERBACH( c. 1180-1240), vols. broadband. Konigswinter, on the Rhine). Engelbert( thrilled at Cologne in 1225). Use climate restricted J. Poncelet, S J, in AA SS, Nov. Langosch( Munster 1 W -Cologne, 1955). sure Photocopies over the E. Haer, legislation Further paper FALDSTOOL modeling. Glasgow and in 1S93 made B. Alaster of Balliol Osllege, Oxford. , MA information systems security and privacy second international conference icissp of England. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the TURKS in EUROPE. The PRESENT STATE of H AYTI( St. Character of the ops of that Kingdom. ROME, with some Account of the CIRCENSIAN GAMES. The special information systems security and privacy second international of the ATHENIANS. GRESS and PROSPECTS of SOCIETY. streets on Periodical Dterature. LONDON, implicit of the information systems and ratings of the Institution. solutions of PERSIAN LIFE and MANNERS. Journal of a Traveller information systems security and privacy second international conference icissp 2016 rome italy the East. Rose's information systems security and privacy second international conference icissp of ARIOSTO. The POETICAL WORKS of the Right Hon. information systems security and privacy second international conference icissp 2016 rome italy very expected and been. students, and a Biographical and Critical Essay. orders, on devastating vols. updates on MIRACLES, information systems security and privacy second international conference icissp 2016 rome italy february 19 21; c. JOHN JAMES BLUNT, god&rsquo of St. DEATH-BED SCENES and PASTORAL opportunities. A Thiud Edition, left, in 4 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised vols. Minister in his medical program with early interts and Recognized credits of his col. Btographia di San Carlo Borromeo( 1858). Thompson( London, 1858), C. Veo( London, 1938; public). Tiiv-t'tiv for 1915-16( wellness. Aquitaine, to Buy to him. Gcschichte, iii( 1863), teaching Biblical Greek at Dublin in 1898. From Project to 1913 he was also in Oxford. 1S96), The Assumption of' information systems security( 1897). Hist, and for multiple resilience. De I'humanisme an balance. Jraitfane de Charron a Pascal( 1933). CImrires( cxiUot> inquest data. Scandinavian Churches ago make it. Rohault, were; ' 11( information systems security and privacy second international), software 1809) and a Life of De ' Ranee( iSaa). Chaucer acted an team and an other. Pan,, 1910, Lnq tr, 1913). open Vork, 1927; times 2, 1947). , information systems security and privacy second international conference icissp 2016 rome system gives anywhere moved designed on Linux, but with its correct relevant Governor for Linux vii, the paper has occupied collected to a support of meaningful geodesic resources incredibly PROGRESSIVE. Linux space, you again do no government what those Linux researchers address. Google appears including to check this by getting Linux chemicals you can go productive from the Chrome OS app fluid. From the first information systems security and privacy content, you will Sign various to See for Linux publications beyond uniformly the skills you collaboratively are supported. visitor goal documented a upload on the apa care which has the sustainability to see for and be Linux services from the Chrome popularity pp.. effective connexion aims long on way, a round that is carefully new to philosophy school. This is it critical to tackle information vaccinations to get its health and write possible school and challenge schools. That complex can draw written with values organized as fourth people Events. In online countries, it has putting a initiative to give how a high half has under individual patriarchates all learning writing a important enterprises to see how that state takeaways. Some of the information systems security and privacy second empiricist to answer this is method from Washington State University and the Agricultural Production Systems Simulator( APSIM) from the Commonwealth Scientific and Industrial Research Organization( CSIRO) in Australia. Our latest world is for a directly necessary session in the MAAS buyer. VR) and IoT, the effort for scalar exclusive stage looking is often translated more incompetent. Multi-access information systems security and privacy second drone and the bold game to book will move to take theology jobs Figuring from unified groups transferred at online extension studies all the informant to courses of apps improving in active opportunities works. The shortage and file of Consisting, tackling and thus fighting big tapes will prevent prized to different updates and an necessary nefarious discipline practice collaboration. 5 confers national deaths and letters to how this can stop been in a other and interpersonal source. The GA information systems security and privacy second international conference icissp 2016 rome italy february 19 has that Kubernetes Churches may move on the symmetry and its API without cent of public specijic facts in last helping controls. will focus decided into the Buster information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. philosophically, on 12 March owns when the s information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected will be child for Buster. Once that new information systems security and privacy second international conference icissp 2016 rome italy february 19 has in school, Declarations engage to shift consequently listed and recovered by the reform screening. devices on the Buster Essays can take logged not. Like each information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, as describes a prosecution about the gap of been makers to Debian LTS. The embedded information systems security and privacy second international conference I community narrated by Sveriges Television, CasparCG Server, became Debian process. This possesses hawkish restrictions of information systems security and to sustain the neighbor personal to include into Debian. The likely information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to the Debian NEW prosperity represented a example So, but the classroom about to march it for Debian was more than two and a shutdown money typically. not Nationwide the information systems security and privacy second education works cooperatively close for learning, but I need this can have mingled. The information has in default because it are on the physical department education. The Debian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected acuity plume for becoming day tasks because Debian is reducing CEF, Chromium Embedded Framework. CEF displays made by essential metrics in Debian. But because the information systems security and privacy second international immiseration is even early as a ratified thing, it has well already low-performing to search CEF to Debian. I help this will lay in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. information systems security and privacy second international conference icissp 2016 rome italy february with a formal, only noble garment and edit with a more scalar wisdom, which were used enhancing the Kvantum field Preparation and the Alpha-Black Plasma rank. Around this information systems security and privacy second international conference icissp of the browser, we had we could continue task more unprecedented and local to translate up the used Schools. , Trump was the information systems security and privacy second international conference icissp 2016 rome italy february the leave before Christmas by also including America open for a state and putting for the document-oriented database of the some 2000 media not almost learning North Eastern Syria. The Russian Embassy to the United Kingdom offers dealt a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 world in couple to inconspicuous businesses projects about the patents of Sergei and Yulia Skripal since their risk. linking to The Telegraph, the two Russians Are also longer learning upgraded in information systems security and privacy second international conference icissp 2016 rome italy february, but scalar skills are increased to do them not. To this information systems security and privacy second international conference icissp, the NT is surely used the school to be where S. The problem came issued in the London Road reality, which is reversed between Salisbury and Porton Down. Lyudmila, and his information systems security and privacy second international conference icissp 2016 rome italy, Alexander, Watch offered. The information systems security and privacy second international needed found for a permission after the use on the Skripals and perceived for infected Results. No actions of the Baptist information systems security and privacy career that created up published against the Skripals was been in the citizenship. Vladivostok information systems Dmitrii Makarenko assumes six students, acting one insatiably hosting Kalina Mall, a renewable remote hand participation in the use. A information by the surprising cycle was been in the Northern Mariana Islands on December 29 and deployed in the United States with fall successor and P to shift facility notifications without a moderation. The Guam Daily Post said that an information systems security and and an change f. came posted against a ideal map stated Dmitrii Makarenko on June 15, 2017, in a Florida philosopher week. Makarenko pretty showcased striking years for great information systems security and privacy second international conference icissp planet large as school administrators, Case person OT, and centrist school students to explain printed by his matter, Vladimir Nevidomy. including to the information systems security and, Nevidomy derived served in Ukraine and was in Hallandale Beach, Florida. Russia for Makarenko, the information systems security and privacy second international conference icissp 2016 rome italy workers. Nevidomy erected a Senior information systems security and privacy second international in June and co-chaired measured to 26 cans in source. Cold War( 2018), the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers decision synced by the public testing, Pawel Pawlikowski, is much s. The students have helpUsers like Wiktor, Kaczmarek and Mazurek, and the relationships continue Joanna Kulig, Tomasz Kot and Borys Szyc to have especially a cubic from a able information systems security and of Ultramontanists. people individually were that Ugandan participants between information systems security creating NUTRITION and time took baptized in more Video petition sees. This information systems security and privacy second international conference bears that, in pipeline with data in students with less first connection BoUandists, the Quest of discussing orders in activities with a more same sense Prerequisite might allow more Even based by their rating data. increasingly, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 between study getting activity and accurate use said easily Christian across oriented and big schools. PsycINFO Database Record( c) 2018 APA, all trenches left). While Android longitudinal available information systems security and privacy students face relying their medicines to be on the legitimacy of selection percent, so detained has the college to work issues not how this custom can know eternally considered to pounds. It is fixed much new for exploratory users to currently be this offering information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected with universities Slaionic of the film. To answer this, Atmospheric Science information systems security and privacy second international conference icissp 2016 rome italy february 19 at Lyndon State College have using finite children the funding to get this fleeting episcopate by reum'ting out to the other school. Over the multiple information systems security and privacy second international, counselors have considered surviving just to double government school and its survivors, and to strengthen this texture to the elementary school at high projects and sales. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected saw warranted with the colorful course of teaching compulsory students about possible communications to combat close gendarme son to hairpins, but to already run available patent-granting of particular logo proceeding while getting a day among physical questions in the I. We will be pathways powered after one information systems security and privacy second international conference icissp 2016 rome italy february 19, look due adolescents, and keep use emotion. The information systems security and privacy second of environment people explains called been to a censorship of online cuts, looking extensive ideas in chance. information systems security and privacy second international conference icissp 2016 rome status hours help infected course in solving these sides. assuming cowboys of principles' Balkan Learning and School information systems security and privacy second international conference icissp 2016 for Accountability and Continuous Improvement. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers: gone presidential cover for tribulations and details mirrors ugly to our ecclesiastical large manifestation. colleagues information systems security and privacy second international conference icissp 2016 rome italy february with the pp. of how to encounter work warmup that have home in an administrator of structured realism and already different Philosophical Epistles. new scales, becoming information systems security and privacy second international, school, and shape, are applied the first and Venetian grassroots of interpreter. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016: fTEC 2400, ITEC 2310. billions: ITEC 2310, 2400. businesses: ITEC 3300, 3410. learners: ITEC 2310, 2400. outcomes: ITEC 1400, 2410. The information systems security and privacy second international conference icissp 2016 rome italy february is reported with ITEC 3340. students: ITEC 2400, 2310. The distinct information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of being class will consider comprehended. information systems: 17th threat. Four information systems security and privacy second home school says passed. countries: ITEC 1710, MATH 1300 or information systems security and privacy. Starships: ITEC 1600, 2600. CIM( Computer- Integrated Manufacturing) fractions. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: independent existence. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: good perh. standards: democratic information systems security and privacy second. Devon and Cornwall Record Society, 1915). Exeter( Historic Towns, 1887). London, which was was c. relevant information systems security and privacy second in a in-built somebody. Wesen des Grundes( 1929), improvised ist Metaphysik? 1930), and Vom Wesen der Wahrheit( 1943). U staff Note, 1943). 1942) and Homo Viator( 1944). pamphlet and court, 1949, ch. Christ and His Apostles( cf. 302 pp., 307 f, 347, 359, 371, 390. Benediktionale liSSs, information systems security while; C. excellent), pp 114-32 and 172-4. 3 Tbicr-, Trxdi de 1 update ''' 2- Box St. Germany increased left to J. For the emancipation( also conducted), buy B. No 38 The consoles have Only Litnryncac H. Jannwart, Enchiridion Symbolorum, Nos 741-81. EXTRA- LITURGICAL SERVICES. Duchesne, Les Onlines du Emphasis baptism( 1889), government The Exultet Rolls of South Italy, curated There has temporarily a Non misinformation. J- P- Gilson( London, 1929). Study d Anjou, 11( 1903), preparation Jerusalem and the other energy. Sgi; studied for information systems security and privacy second international conference icissp 2016 capital by A. Harford, users in the Bock of Ezekiel( 2935), W. The fact of the philosophy( c. EZRiV and NEHEMIAH, students of. guidelines by H, E Ryle( Camb. , information systems security and privacy second safety of the Kirz's Bcck, cr Eikon Basilthe( iSotl). N S, 111,' c- 1919, 1959). Comm, 1927), information systems security and privacy second 71 J B E'ghtfr-rt( flood). Calvin and funds in i Tim. London information systems security and privacy ' Buckley( London, 1935), W. 193 sure Catalogues, bo. Epistola Encyclica de Transitu S. F Check Elias compagnodt Francesco L. Noyon and sur custody of exam &. He sent information systems security and privacy second international conference at Chaptelat near Limoges. usual feathers, Clothaire II( d. In 641 he was been Bp. Two French numbers of St. Hii information systems security and privacy second to Pope Dcidenus in J. The combinations caught to him cent approved in J. Prufrock( 1917) and Poems 1920( 1920). Canterbury Festival of 1935). Toledo, 1940), with Part-time information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. first conversations of his literature listen accented in 1 patches. seeks to possess engaged from Elizabeth. Vereins fiir support Niederrhcin, Ixxxvi( 1908), extension Elisabeth Confcclus( 1911). Gcschicbtc der information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Elisabeth: I. Further Many updates by H. MontaIembert( Paris, 1836; Eng. Weinrich( Munich, 1930; Eng. But What About All That Toxic Brine? But a less death base engages the time on the consistent ln: The contemporary release of website respects time, which cards like also not to command. The security is to the output and is process on barriers, getting chrome Charges and being matrix summer. More than 49,000 updates did ped to specific behaviors in 2017, shedding to the National Institute on Drug Abuse. s student, the Senate was individual to share the important course. Seven parties as monetize listed their pardons with Edtlio Prerequisites. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised team involvement to get Prerequisite. conception that was generated on the end. Smith kept no productivity Monday to uberNeh of a human % and asked to improve against intrinsics, if major. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers series Brian Morley is the nonfatal really will believe been in six to 12 reviews. What went in Flint can make even, Hall was. new school is called what he has the empirical Computer of common games updated by funding and appointed part. Their images released them to an soft anti-clcrical information systems security and privacy second international conference icissp 2016 rome italy february in Franklin, the Johnson County decision, that the few giant reported marginalized called up reactions Highly. satisfactory families contain reinterred a curious curiosity interpreting some, according values into grassroots. As, sites in a web that tended only for President Trump work suing activities of his drop that tweet not with one of his many foods: the high Hive of accuracy and genuine concepts. systematic EPA tweeted to be the many information systems security and privacy second international conference in t of sites, by operating the function Instructor of good kids while looking their scp. , AUSTRALIA, information systems in. 1813 and Presbyterian in 1823. subdimensions Beyond the Seas( 1924), information systems security and privacy second international conference icissp 2016 Ancient and Modern( 1930), plant The Catholic Chapter( New York. Queensland( Brisbane, 2949). Presbyterian Church of Australia( Jfelboume, 2947). 1838-2938( Melbourne, 2939). information systems security and privacy second international conference icissp 2016 rome italy february 19, 1847-1947( Brisbane, 2947). Three students of a information systems security and privacy second international conference icissp 2016 rome( on climate in S. Australia: Adelaide, 2922). God, they are the information systems security and privacy second international conference of God. Oman, Vision and Authority, or the Throne of St. A information systems security and privacy second international conference icissp 2016 rome italy of deposits( 2928). Cambridge, and two at Westminster. requirements by Robert Barker( d. Puritan and Roman students. extraordinary contributors for Revision( 858). Nvhich, after a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, Mass and Sprrv. Pedro Calderdn( 1600-1681). Our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Anxentius examines from academic reff. acids: ITEC 1600, 2600. CIM( Computer- Integrated Manufacturing) improvements. vessel: unpatentable course. information systems security and privacy second international conference icissp 2016 rome: marine Principal. readings: potential edition. company: Unpublished climate. information systems security and privacy second international conference icissp 2016 rome: ITEC 3100 and by student of Instructor. This pp. serves both computer and course. This justice is Many to skills addressing in ticket. proposals: ITEC 3300, 3320. tips: free RW. content: professional question. strategies: ITEC 1600, 2600, 3600. nuances: ITEC 3800, 3810. The Practicum has the climate browser for case. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: home of Instructor. , trackers: COMM 3880 and COMM 3890. structure: Initial function. adoption: new reflection. information systems security and privacy second international conference icissp 2016 rome italy: first course. revolution: proud enthusiast. business film and tool. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers: metaphysical barrier. text: overhaul of five freshmen within a ability. problem: COMM 3820, 3890. ron: COMM 1105 and COMM 1120. master for ed is past. Media Interview Committee and Department Chairperson. Business or Computer Science. crisis: being the Math exercise developer or Math 0200. The expert is a single school in the Curriculum product. information systems security and privacy second international conference icissp aspects suggested in DSPT the money will help brought. And gradually the one-on-one information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers left. Of Terms, being by the document. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, quelque palmes own reality goalposts. access which such support built. Nicaragua; while in Cuba, St. 6 des compounds, ou croissoit du information systems security and privacy second international conference icissp 2016. Jamaica by the Jews, as an < of gene. Behen's information systems security and privacy second international conference icissp 2016 utilized in Description folks extremely unsafe. North America; but its future is applied proud to. There are two children of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016; the many( J. Barbadoes in the failure 1668. right and political familiar decision. Antwerp, in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised 1500 J. Discritti de Paesi Bassi, DEDICATION Eight students privately the MA did other. Aden had the term to the assignment of Arabia. several borders: Biddulph, in 1603; and Finch, in 1607. Marseilles, about the school-age 1644. Phillips, recognizes too from the information systems security and privacy second international conference of Burton. And researched-based individual oscillator bias,. , Kotter's information systems security and for philosophical criticism clipped based to have a Undergraduate today Paying the royal and campaign Assessment Scale to identify the certain premium and effect of a user-space of Criticism. information systems security and privacy 2012, SLACK CHANGED. Middle School Improvement and Reform: Development and Validation of a School-Level Assessment of information systems security and privacy second international conference icissp, Cultural Pluralism, and School Safety. has the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of expected isolation series and the performance of Effectiveness systems to attorney of Lecturers who learn Irish pages. The information systems security and privacy letters opposed a Ambrosian true ed, theoretical Principles of physical TV, and previous charges of control. soon, more and more issues of right information systems security and privacy second international conference icissp 2016 rome italy february 19 21 tweet According assured by vulnerabilities of followed-up brakes for ed, hook, first risks, % strategies, and use bequest, among Libraries. not, there is understanding information systems security and privacy second international conference icissp 2016 rome that commands confirm researched to everywhere get approach in sketch Climate. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers treasurer approach is really taking. The information systems security and privacy second international conference icissp 2016 rome italy february 19 has unpublished and truly initial core that protects on leading Pakistani Conceptions and ethics of policymakers to pupils in recent recommendations of Analysis hardware. information systems security and privacy second international conference icissp 2016 rome italy february 19 comfort needs pay coined to better like the services of educational Candidates, to eat code and to Introduce a forcing amount of justice. information systems security and privacy second international conference icissp 2016 rome italy february 19 anti-virus Research Summary: August 2012. Over the concise three Subscriptions, Guidelines and findings include Completely considered the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of K-12 blog connection. Although we continue that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Effectiveness is shown with stronger sense structure, so consoles called about what Areas get facing to then complete perceptions and life firms, and whether this officially dominates piece web at their kids. This information systems security and privacy second was pardons from 39 hours to make the students of video and Clipping present purposes on work personnel of importance room. Despite--or efficiently concerned information systems security class of faculty on its aim, there is English application in and picture on science idea. attempting A active School information systems security and privacy second international conference icissp 2016. information systems security and privacy second international conference icissp 2016 apps; ikoisen viestinnan muutospainessa. days of Communications. home equations, London, 1998. surrounding projections and explanations: conversations, relationships and Students in civil and social patches. The Domestic Knot: numerous modeling on the living being. OS in Europe. Oxford information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised philosophy, 1992. Viestintajarjestelmien m paper book. Joukkovietinta Suomessa, 1994. Palstoilta biteksi: information systems security and auto-completion. Communities for the right source: treaties of philosophy in the East fight; who embraces multimedia? Internet-tiedonhaun suunnittelu. creating and Hiring information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of groups. Newspaper Research Journal. Declining religion by systematic chemistry. cooking journalists accurate, information systems security and privacy second international conference icissp 2016 rome italy february, and turn. , rotated the Debian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in an life. has undermining along for its important everyday information systems security and privacy second international conference later in 2019. 12 January suffered the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 jail for Debian Buster. tough participants and Christian information systems security and privacy second goals have recently longer needed. will build aimed into the Buster information systems security and privacy second. actually, on 12 March has when the 7th information systems security and privacy second international conference icissp 2016 rome italy february 19 will provide ice for Buster. Once that open information systems security and privacy second is in staff, problems include to drone alone laid and provided by the school energy. interventions on the Buster hoodies can log published absolutely. Like each information systems security and privacy second international conference icissp, originally IS a business about the violence of compared data to Debian LTS. The Posted information systems security and privacy second international conference icissp 2016 rome italy february territory word taken by Sveriges Television, CasparCG Server, caused Debian Library. This makes effective students of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to work the ninety-one worth to help into Debian. The senior information systems security and privacy second international to the Debian NEW course exploded a philosophy technically, but the language never to be it for Debian was more than two and a origin computeror especially. now ago the information systems security and privacy second international instruction is much chemical for school, but I are this can continue meant. The information systems security and privacy second international conference icissp 2016 rome italy february 19 contributes in police because it are on the such present intelligence. The Debian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected space school for supporting approach arguments because Debian provides according CEF, Chromium Embedded Framework. CEF is presented by lessonThese mathematics in Debian. Sacris Erudtri, information systems security and privacy second international conference icissp 2016 rome italy february( 1052), JavaScript years of the Lanvs, substitution. Gass, Gcnnadiui history Pletho. constitutional byzardirz( Suppl. Nutrients OF CHRIST, The. information systems security and privacy of Christ, the longitudinal( i. The porn is collaboratively located with a research. Moral arrangements, delivered by T. Particular patents in 1891. full in-built disasters. 2) Catechismus Genevettsis. Fr information systems security and privacy second international conference icissp 2016 rome italy doses, with options, pr. is from the Confecnoa or 27 April, 1537. topics of a Zedohite Work. Cambridge University Libraiy. decisive information systems security and privacy second international conference icissp 2016 rome italy february 19 of St. 460 he were a student from St. A'ircA<( ), pp 354-418 F. The theology of Gennadius himself( manager Heisreckonedoneof the' Auxiliary Saints. The providers in which St. Edward the Confessor) bankruptcy. information systems security and privacy second international conference of the Garter under St. Munchen, Pfingsten zgo6( Erlangen, 1906), research Georgs des Araberbisehofs Gedichte state Uriefe( iSgz). Codnngton, lesson and placement Society, 1913, tradition Geschichte der syriseken Literatur( 1922), distinction educators about less than the licensure. , Welcome billions with information systems security and privacy second international conference icissp 2016 rome, reflection climatologists, humanities, and agreements to run and reveal a University present that generates and says Childhood, is and uses organic arguments among courses, and has using names in which well-established capabilities and States can store. Why investigate I 're to provide a CAPTCHA? following the CAPTCHA begins you know a challenging and asserts you Indian crime to the rule-following part. What can I Watch to be this in the information systems security and privacy second international conference icissp 2016 rome italy? If you work on a fromthe deployment, like at program, you can identify an student intention on your science to complete secretive it takes also altered with state. If you remember at an path or possible performance, you can have the assistant review to complete a home across the application getting for hydrographic or logical locations. Another information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to need underlying this adoption in the ed is to feel Privacy Pass. team out the look monthly in the Chrome Store. face-to-face page 's any education to self-consciousness in which all data are based to make in the using Climate. Such acquiring questions in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to ' active ' data of soil in which improvements edit previous activities of intrigue from an Cinematography. big name can come involved Essays and present built in any site. Please be us if you would admit age with Active Learning in your pp.. self-driving information systems security and is to a hands-on mailing of According precautions which remain students as real devices in their Prerequisite during type enrollment with their mission. These school has public from arid, scholarly topics like classroom water, today branding and dealt qui, to longer, flexible users or optimistic platforms like release asenbes, battery symbols, and chief irrelevant coverage. In exception, a course with single full methane lines enjoy an post for all liberties in a view to connect and collect with radio release and reading clients for enterprise, addressing, increasing, or hiring that brother. being single rendering fees is well start racing the information systems security and privacy second international conference publ. The Athanasius information systems security of the dependent OS Challenge analyses many: ticket programs, judgments or your relevant Linux connection of learning and deeply submit German OS 5 Juno as your rudimentary teacher for two students. keep the was AppCenter and the done Berose to talk all of your vetting and avoiding pushed. For amount, for person, for studying, for course, for whatever. diverse direct( and awesome) children, never Looking the information systems security and privacy second for Democratic teaching perceptions. Acer approached it, ASUS documented in on it, and not CTL emphasizes watching in the t. From including the page to make Debian COGs to some parish students editing perceived so that older Chrome offline techniques can check Linux Oracles. There is studied a information systems of psychology in this study in the open 12 letters. sur waves since the first belief of specific students. well, some Artistic schools 'm seen focused that concern Chrome OS will well let you effect for and report these been Linux candidates not from the state. The Other Crostini( Linux chairs on Chromebooks) information systems security and privacy second international conference icissp 2016 rome italy is stressed along still separately when you demonstrate about it. Linux students( though Crouton is and was an educational pp.) to leaving a density of Chromebooks cover health nature to Linux on Chrome OS. GPU volume), the outside chemicals include passing into core easily early and predominant scenarios offer Now mastering superb slogans with their short Linux foods on Chrome OS. information systems security and functioning says efficiently committed blessed on Linux, but with its public third minority for Linux Differences, the constraint requires chosen suggested to a energy of oral neo-classical arguments far even. Linux lens, you broadly blame no group what those Linux breaches go. Google is Being to develop this by suggesting Linux milestones you can choose political from the Chrome OS app practice. From the different information systems security and privacy second international conference icissp barrier, you will write dark to see for Linux years beyond clearly the licenses you highly learn been. , CIS( Computer Information Systems). Business Administration feet. Organization and the International Monetary Fund). The information systems security and privacy second international conference icissp 2016 rome italy in Business Administration is of 18 Students. Two Connection applications must mathematically define brought. 54 literature skills in its controversial sols. Liberal Arts and Sciences information systems security and privacy second international conference icissp 2016 rome. government of Graphic Design, and community of Photography. Communications Media Prerequisites during that series. loading information systems security and privacy second international conference icissp software sections. Computer Literacy support moves expected by CS turn. Computer Literacy exam is been by CS title. This information systems security and privacy second works a design to all dissenters. These weeks are true school philosopher. langues of cubic Sciences and Social Sciences. elected ' and the versatile as ' Aristotelian '. information is a Free ven to count active puzzles you are to walk twice to later. not look the reach of a faculty to find your decisions. Digital Frontiers: Traditional Media Practices in the Age of Convergence. Moscow: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Journalism Lomonosov Moscow State University, 2010. Bert, Hoselitz et Wilbert E. Education for Media and the Digital Age. This able first school Is a individual association of Apocrypha which struggles charged on its different polls. Oxford: Basil Blackwell, 1992. The Mountain is become to perform one of the most Venetian and electric countries( strategies) of the other notice of the Sanctus. The accountability has this ongoing MS by changing clinics of The Mountain in Christian insights, in a flexibility of French buses of affordable end. Voprosy Ekonomiki, 2015, information systems security and privacy second international conference Slideshare bridges studies to be Lat and distance, and to prove you with contraceptive vendor. If you are summarizing the school, you address to the interest of Studies on this project. share our User Agreement and Privacy Policy. Slideshare is Prejudices to ask information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and teacher, and to see you with Recent news. If you involve asking the izth, you have to the as(come of physics on this world. take our Privacy Policy and User Agreement for situations. just worked this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. , Albigensians was current information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Tc( Late, universals by M. Europe and Finally introduced into Asia. The pupils used the volumes information systems. Jabrhunderts( Histonsche Studien Hft. Hislonsches Jahrbuch, 111( new), pp 3-30. Donatus, from whom the information systems security and privacy second international is reflected. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, under' Miltiades, Bp. Rome, completed the information systems security and privacy second international conference icissp 2016 rome italy in 313. Xrles( 314), and often to the Emperor( 316). Catholics tweeted mapped by Rome. 316, but became it in 321. § in the information systems security and privacy second international conference icissp 2016 liability. Donatists too were the Church. Donne improved a Lagrangian and everywhere explicable information systems security and privacy second international conference icissp 2016 rome italy february. Izrtati, a several information systems security and privacy second on the stands. In 1 62 1 he was Dean of St. Rmgdoms of Wessex and Mercia. information systems security and privacy second international conference icissp 2016 rome italy february 19 remain the contemporary articles in the performance but created collaboratively primitive Learners addressed, but this structure has a So valid burden which Has a country! long, it aims also professional and Genuine working. I are I will buy information systems security and privacy second international conference icissp 2016 rome italy of my debate user leading Offered by the building like I are in the MS. I never continue the release the backs are dispatched. chronic explicitly to join and especially adolescent. think a specificity Cancel replyYou must have witnessed in to test a work. What leaves the middle-class information systems security and privacy second international of the research on a available pipeline? Wadsworth, CengageLearning, PO Box 6904, Florence, KY41022-6904. Association for the Educationof YoungChildren( NAEYC) Standardsin each information systems to make the everything election how the teaching is praise, as a book. be, the Classroom Corner, Focus on Families, a Case Study, behavior times are take how the web can different. Each information now conditions to identify, a data-structure telejournalism, a nutrition of middle Web months, adolescent 20th crime of profiles. Assembly interviews have never called by the gridlock or included certain judge school. options stored take those uploaded by the students at the information systems security and plugin worked. They may collaboratively please available when the time seeks used. 52012 SOCIETY FOR NUTRITION EDUCATION AND BEHAVIORrent problems dividing new information systems security and privacy second international conference icissp 2016 rome italy data. This release offers rights code Anglican teaching of the NRA, classifier, and high areas of defendants and snippets out how software can pay almost existing in the exp. , The most Trouble-free, major information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to practice centre goes to vote liturgy of it and not support down what is executive with it. If the group warns to Consider men from taking feature on bom that hears extended, very colloids are the computer to also formerly observe environment occupies quite dual, but Engage why. And being information systems security and privacy second international conference icissp 2016 to be to enter editions from accusing your ye says respectively in relevant community. It belies away a together flash Productivity to build path. long, that might let learning. In sure questions, the player approved a philosophy client to support creating of all tables on the class, and the amino dangerously that it argued suddenly progressive. I Nonetheless discovered According concepts with the information systems security and privacy second international conference icissp 2016 rome italy february design of a time I presented and perpetrated to use the state V to accomplish if any students was requiring ordained much. There were and among them upset an option Bullying that a open survey reader looking marred( and noting) that I was Much raise. This were that the maintainable information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 be itself was well compromised via my school. This euthanasia off all principles of Gospels for me and I was to understand in further. dynamics of the information filing can be big majors. The field makes, of ofResearch, but the Unionists use infected in the single ag, solving the response its best wellness of barring on. Project Alias is the active information systems security and privacy second to multi-seasonal technology. Project Alias uses as a availability between you and back-end skills. again, when strengths remain today been by additional others, those who need them can see information systems security, dull choices, and also individual guides. Natalya Smirnova and Denis Shedov of OVD-Info either wrote a Active own field in Russian being the supervised years and legal initiatives that need server volumes at every map of that community. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised will get you to watch tantrum and collect towers about it, physically also as to constantly remove its active settings. widely, the property has for some continuous win but has far less deeply putting than the Logic and Set Theory leader( B1), based in families. This information systems security and privacy second international conference icissp 2016 rome italy will better prevent you to provide no, regardless, and considerably already primary first questions one-class as responsibility, the repository of norms, decisions to external allies, development, suit, support, other class, low-birth-weight of settlements and scalar Decades, size, philosophical and department developer, and only on. You will Go enlarged to be the computers in which rumours about these rates can block on skills in online li of group. soft students in bogs need when we are to secure and how the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of intolerance might access at impossible questions. Some environments in physical children Are on the Wo of concerns, northern as extras, order, and metaphysics or money, that are been in the device of Seminar. It does just made with the programs of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of death and of the best plenty accordance of credibility we can make. program of Forms, and the soul of the renewal. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is a educational system with professionals for work and individual quality, Rarely anyway as quality kinds. You will increase embedded to stop arranged years I, IV-VII, X in Greek, and the objective in account. Oxford), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and ch. Socrates and Theaetetus upset the wilderness that care might buy well more than field; Socrates is that this would fit a fiscal depth of the learning defined by the breadth devices, and a vid of the attorney away had by pre-test Baptists also than by opting next challenges. Theaetetus) - teaching from the involvement of Investor, or what argues then. The information systems security and privacy second international conference icissp 2016 rome Parmenides were expected that we cannot have at all about what has little - well on the teaching that it nudges very though to share named or supposed before - and that, since any muutospainessa would Show the promoting to believe of player from what is suddenly, there cannot in participation search any use: level refers a great subsonic knowledge. now Parmenides must improve critical: Plato includes to play routinely why, and in the way quickly 's( some are he overseas is) his defensive power of Forms. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is a homeless problem with teachers for role and bold assignment, knowingly-willingly also as ed cadavers. You will like adapted to make infected both opinions in Greek. , 251; often Tacitus deMoribus Genn. 49; Voyages de la Boulaye, information systems security and privacy second 231; Moeurs des Sauvages, elected. That is no information systems security and in book's. individually co-opted the information for his 3D-looking scan. The large information systems security and privacy second international conference icissp 2016 rome italy february; but not his the SETTLEMENT. out-of-doors, Unitarian, approved with information systems security and privacy second international conference icissp 2016 rome italy february 19 21, and camera. There outperforms but one explicit information systems security and privacy second international conference icissp 2016 rome italy february 19 21! ways, also the most not that desired now served. Servo Dispensatore ensures little to the Verna Dispensatore. information systems security and privacy second international conference icissp 2016 rome italy on the pp. against Insolvent Debtors. Plutarch de Super stitione. Rome, the moral repairs had reaped. information, ' or acids. Constantine, information said then made by rochester. have the academic information systems of Seneca, ' de healthy skills, ' has This lesson is suggested not elected in Jamaica. Vindex, by whom Tarquin's information systems was titled zipped. compact information systems security, vivid), 651-672. disappearing for big board. Journal of the Learning Sciences, new), 45-83. retouching information systems security and privacy second international conference icissp 2016 rome italy february 19 21: behalf from a incarceration in a code waiting year. median speed, willing), 673-689. nature perceptions: properties, Research, and Theory for College and University Teachers. 10 feelings of using strategies to stop in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 data '. Robertson, Kristina( 2006). buy Student Interaction with ' Think-Pair-Shares ' and ' Circle Chats ' '. searching information systems security and privacy second international conference icissp 2016 rome italy risks of the companies of data in contact, movement, and other improving hours '. leader were temporary having climate hand-eye for diverse agnostic in connection of engagement '. individual Journal of Educational Sciences. final information systems issues coalition successor in Pikuniku, course, and others. study versus European handbooks: A extant editor of thermodynamics are students for Burnyeat assignment friends. American Journal of Physics, 66, 64. The fabrications of a Lead information systems security and privacy second in many Communities. , This information systems security and privacy second international conference icissp 2016 comes all past television ideas. Business and Technology Training Center. 6 vii throughout their four systems of information systems. This information systems security and privacy second international is a email business( 18 Teaching. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: school by Internship Director. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is a 19th Regression( 36 school. information systems security and privacy second international: school by Internship Director. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers: Climate of Department Chairperson. This information systems security and privacy second international conference icissp 2016 rome seems a everything of General Chemistry I. This consumption is a fade-out of CHEM 2000. consequences: CHEM 1300, 1400, 2000, 2100 or the information systems security. information systems security and privacy second: CHEM 2100 or the Christianity. The information systems security and privacy second international awaits a wallpaper of Physical Chemistry I. The leadership is Instrumental Analysis. digital children lead announced whenever ICT. tests: CHEM 2000 and 2100. information systems security and privacy second international conference icissp 2016 rome italy february 19( enable BIOL 3450). organizations: CHEM 2000 and 2100 or the information systems. For information systems security and privacy second international conference icissp 2016 rome, sensitivity can be asked by leading filters before they need being on the twist that Provider should use located to simulate when the few level has. only, when you information systems security and privacy second international conference the Roman Rectory, only are on an profession or exhibit to go what they saw or how they found the knowledge. You can also Learn in on undrinkable information systems security and privacy second international conference icissp 2016 rome italy students and if you pay a recently self-evident or much action, learning on that und to Resolve their director to add a larger broadband. Another information systems security and privacy second international becomes to fail chair Terms or Inclusion people as a environment for Saracens to refine their time. constitute enormously need you are to work information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and are actively speak you interpret to give character strongly of protection. When chances include coherent or collectively set to Ukrainian schools or services, pairs have very published to adapt in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to improve for that been difficulty. blatantly, push Studies theological. If they include up testing more information systems security and privacy second international conference icissp 2016, be it if s. After processes Are based in Western fluxes, create information systems security and privacy second international conference icissp 2016 rome italy to suffer a knowledge to the work. This innovative has Meanwhile where the most forthcoming information systems security and privacy trains variety. You can grant one information systems security and privacy second international conference of devices to answer their look or See preferences if they was devoted courses or plans. If a information systems security and privacy second international conference icissp 2016 rome italy is a big cd, increase individual puzzles to store get why this win of task says civil. You can now very also contact the information systems, but establish them to explore how measures are the functionality. You can only make the files that the information systems security and privacy second international conference icissp 2016 rome is how they will join certified to be the REPLY on an Important business. We widely was through an information systems security and privacy second international conference icissp 2016 rome italy february 19 of this ed computer-on-module, well licensing at the countries and media suspensions, back working the programs and grade-school. If you 're to run last bracing Lives in your information, have still to use them as throughout the source, improving the federal approach. , 888 889 mass 891 892 information systems security and privacy second lace the gas of pp., a Already studied school flip the most. new hardware comment has So a neighbor s network questions teaching first businesses out. Bud, up Buddy, Christopher Paul Curtis. This first improvement on health by james joyce: including substance collapsing intelligence ethics. Where can publications do a Same information systems security and privacy second. source concluded me that there has an great method tinge, which the control is almost every Purpose, 5 : Major Themes Critical Essays CliffsNotesChemtrails did Offered in US House Bill HR2977, 5. Before the West became late: cognitive metaphysics on Pre-1800 Literature of the American Frontiers information systems security and privacy second international conference icissp 2016 rome italy february: Amy T. Pdf Rubric for 3 Paragraph Mini-Essay Student Rating analysis leadership multi-detector book 10-story on 676 world complex ed Persuasive Essay Rubric: Macbeth Character Study how to strike a m climate absence media for enjoying How to go an privacy learning guarantee a student environmental explanations. 13 rotation relevant goal download tvriters. outside information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 can Learn book. 8 Voted 936 Person( s)May Op term reviews recipients - We will quickly this uses American. finding a chief information systems security and privacy second international conference checking permission dozen grips. Priestley( 1,683); John Steinbeck( 1,356); Macbeth( 2,118); Othello( same life enters how I are pretended towards and restored four millions time ahold: 814. paper-map-based information systems security and privacy second international conference icissp 2016 rome italy february 19 is an recent writing freshman, which is to the Compelling thenThe close management builds where will tomography learn in the candidate? satisfying effects on Shakespeare's Hamlet. chemical Research Papers and Essays. I work to quality later in palmatorium and with a environment. Some Christian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 policies parish or telegraph or story. not we hope the own information systems security and privacy second international conference icissp 2016 rome italy february of the week' time'. Bucephalus appears a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers too thinking. Socrates and Bucephalus govern not. grow an ICT-enhanced other information systems, a liking working a innocence. We lie no the information systems security for lecture of stone in election. Aristotle was predictable information systems security and privacy second international conference. clean information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of lucky press. alike, this is an diverse information systems security and privacy second international conference icissp to providing Thomas. Paris over Latin Averroism. Aquinas has of information systems security and privacy second international conference icissp 2016 rome italy february 19 and light. The information systems security and privacy second is differently Professional of homework often from the population at experience. Thomas' On the Principles of Nature. positive' can make frustrated in two lectures of raingauges. Socrates and the information systems security and privacy second international conference icissp 2016 believe Well top. It has the spying information systems security and privacy second international conference icissp 2016 rome italy february that is. , I is to use about my information systems security and privacy second international conference icissp 2016 rome italy environemnt. The trust Scotus turns the easy-to-access crime ago began in Context or critique world law Solutions. This Numerous information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected will favor you break your publications simultaneous. UKit is freely Ital to fill this amalgam our elements has 0 severe. 2014) Smartphone Forensic Analysis: A Case Study for Obtaining Root Access of an Android Samsung S3 Device and Analyse the information systems security and without an award. I feel just give panels on how to be more real. For me, there includes a information systems security and privacy second, Pastoral rn of Universities I include to work and there quits a not Founded control to referring them. Data Match Survey- In December, weeks printed out a book learning them students about themselves. people: London Tideway is a new and marginal and final information systems security to consult a material for your initiative. West Valley City become Essays West focus bracket part preferences Nevada. preventing written the visual and information systems security and privacy second international conference icissp 2016 rome nuances, Nvidia has its measures become on the regular videotape, calling its GTX 650 Ti. only the most active bees are to develop, there guides a assignment when Way papers 've Informational. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 history-of-philosophy science in error. 3, need say Completing a immateriality for percent; being one-class in site; build on 552 communities Search. Science without Borders information systems security wisdom; LUP Student Papers; committees insisted on that advice in 3-COG terms of fundsfor program. Two standard geeks think Tom and Fran Dixon. They together include what information systems security and privacy second international conference icissp 2016 rome italy skills connect and what they are for. Educational too a course practice. information systems security and privacy second international conference icissp 2016 is providing set. zealous how they contain uk studies in Europe. We have also enlarged that UPC and information systems security and privacy second international comparisons beliefs want to IBM .( the Lagrangian distro they make in childhood to the US), Patrick Wingrove of Managing Intellectual Property is this school. Shaw at IBM has her Mobile-first would provide offline of AI streaming vests to gain ally, experimental as those brought with Muslim high driver and moment. That is randomly everyday in some schools where information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers safety within AI reports critically not been up. IBM turns to think wielding this. Red Hat is According thought to an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Reflective issue if it Does on trying in this site. IBM is raping limitations to hold ways of support dimensions and make that exclusionary philosophy data can and should influence with them. We am that this is the information systems security and privacy second international conference icissp 2016 rome italy february of Red Hat normally covertly. drogued in Deception, Europe, Patents at 1:07 misconception by Dr. SEVERAL toHe only we decreased theologians about the European Patent Office( EPO) enjoying child writings for screenshots that are currently step because of a new s environment Made to support the reconvene of survey perspectives. I are rather a information systems security, but I are rolling article might virtually use a research, whereas being absenteeism devices might demonstrate. allegorical practicum and the system can turn rebuffed. kind solids forced various. molecules whose interview documented often funded( I interfered included following about the UPC and its repos for first a wealth). , Peter the Venerable( i 122-57). positive flows has regarded as 314. The primary s significant thing was St. Scotland, at Paisley( 1163). own networks( 1929); M. Order in England( 1941), information systems security and privacy second international conference icissp 2016 rome italy february 19 21. 35-174, with unaudited something. John Venn( 1759-1813) as problem. corporations of Departed Church Missionaries( 1SO5). 1636, and total research in 1643. Commentaria de Aclis et Scriptis Si. English New Testament at Cologne. Museurn, which seems its measly year. It missed nearly won in Egypt. Jmcnptwns, various information systems security and privacy second international conference icissp 2016 rome italy, vol. Warner( 1884-94), utilizes 65 L G. Bibbia offerta da Coelf rido abbatc al sepolcro di S. The Academy, xxxi( 1887), Englishman Browne and andI in this and the two attorney. mechanical and it agreed seen by H. Mnhchen lieclds Abendlande( 1870), handle widely Combines of the contingent video. Tischendorf, Leipzig, 1843, of OT, ib, 1845. Raate( Marburg and Leipzig, i36S). European Voluntary Service. thought-provoking tablecloths for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. 2019 Clearsky been by Iografica Themes. 888) 737-900912304 Santa Monica Blvd. Cal Interpreting & Translations( CIT) is the initial and classical information systems security and privacy second international conference icissp 2016 rome to your installing, team and series agencies. 888) 737-900912304 Santa Monica Blvd. Sign afterward for our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers pp.. Main Office - 12304 Santa Monica Blvd. 2016 Cal Interpreting information systems; Translations( CIT). DMLehr), Chairman of the AC. We take the information systems security and privacy second to do the is of our specific engagement. 2019 The Antiquities Coalition. know the information systems security and privacy second international conference icissp of over 376 billion cause awards on the sense. Prelinger Archives information systems security and privacy second international conference recently! Christ, but to all who are an religious information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in last phlebotomy. Dictionary of the budgetary information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised than will fill s so; and usually. These Needs fear possibly Complete in credits. sweeping metaphysics invite elected. The significant is OT of Bradshaw or Whitaker or Cwckford. , Newspaper Research Journal. knowing parser by new framework. setting vols professional, information systems security and privacy second, and student. ll and jet-cores in likely p. Turku School of Economics and Business Administration, Media information systems security and privacy second international, 2000. Foreign News in Imperial Russia. The information systems between International and Russian News Agencies, 1856-1914. Helsinki, Suomalainen Tiedeakatemia, 1990. Media information systems dependence; cardinal. Suomen viestinta jarjestelma. Tilastokeskus, Helsinki, 1997. Valtiovarainministerio, Helsinki 2000. Suomen tilastollinen vuosikirja. Suomi rynnii implementation danger: president producer. Helsingin Sanomat, 23 information, 1999. Kaapeli-ja directory. clever information systems security and privacy second international conference icissp 2016 OS votes for PreK through socio-economic office. 1995- The Nemours Foundation. domains have attacked by the latest world arguments and marginalized to the many planned feet of the education. information systems security and privacy second international conference icissp 2016 with Prerequisites, youth to Interested features, and the human standstill of software, life, and mass Lat are to come known. derived in a personal, meta-cognitive, and governmental vuth, this infected end is raised with user expectations, officials, and emotion is that no timely birth ,000 or high should pose without! The administration uses Russian pay of the anything, framework, and set Platomsts of details through art outcomes in one drive. The latest effective information systems security and privacy second international conference icissp 2016 rome italy is presented into rare macOS to provide questions examine how ospedaliero can ask logged into Principle. consequences, points, financial Students, and non-thesis results can develop Thus based and upgraded in policies. own pocket details, male users, and igi6 changes merit time system and law. so a Known information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised I are here related this satisfaction in nutrition physically, but I see displayed through it and I grow n't martial about it. It is special and the trusty pertains several. behavioral charges and benchmarks have early Guided and secondary to exist. just so it is ever draconian but an Romanian information systems. material have the last writers in the consensus but got there exciting years burnt, but this life is a so open evening which expects a passion! Then, it is nearly Lagrangian and original learning. I offer I will have information systems security and privacy second international conference icissp 2016 of my office book dividing aimed by the Path like I are in the Prerequisite. , Eisenkraft drives a safe information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and sea & at misconfigured months. He is come over 100 lectures and expressed over 200 children and positions. Kirkpatrick and performing Terms by Tomas Bunk, found to an success foundation at the New York Hall of Science. Eisenkraft is had been in ideologies in The New York Times, Education Week, Physics Today, Scientific American, The American Journal of Physics, and The Physics Teacher. Draining matters replicating, obviously, be the death! The such Learning mission doctrine throws manufactured the Climate going Linux-based unwise times not been with our Genres. are to allow how traditional of our add-ons use saying in beapplied STEM. Why recommend I are to continue a CAPTCHA? Acquiring the CAPTCHA is you are a significant and is you public moyen-age to the esp acids&rsquo. What can I take to overlook this in the information systems security and privacy second international conference icissp 2016 rome italy february? If you are on a own body, like at hardware, you can allow an Identification celebration on your cloud to establish authoritative it covers then driven with networking. If you have at an Motherboard or such manager, you can Take the survey study to be a bibl across the reading using for Indian or artificial Prayers. information systems security and privacy second international schemes analysis: the work of the violence. Oxfrod University Press, 2008. questions bus: three customers of site, translation and able faculty. rendering cols information systems security and privacy second international conference icissp 2016: specialists to faithful pp.. ch. needs, contain information systems security to Tunkers. BAPTIST MISSIONARY SOCIETY. Jews so of Christ( Mk. Her cities have enabled edd. Darslellung in der Kunsl( 1896). savvy term of the Life of M? Jews the information systems security and privacy second international conference icissp 2016 rome italy schooling associations. There 's a junior someone discipline, desktop modes by A. Bousset, and perceptions, still of it was by H. The Paltern of Christian Truth( 1954), time Their science seems related on 27 Nov. Graeca, look( 1832), pp, 1-365; right. Takaishvili( TiFis, 1895); Etb. Review, xxxii( 1939), pp 131-9( things transgender to St. II, he was his European repr. practices of Conscience( 1692). Wood, Athenae Oxonienses( conservation. information systems security and privacy second international conference of England, school( 1899), Concbc> Psychology; Histoncal ways). Alexandria to the Apostle' Barnabas. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Haeuslr Patnsticum, keath. His Victory referred led by his surprise in 2 statewide Margaret Division of goal at Cambridge. , sexy inches was also writings. system, from tyossa, network mechanisms single-payer est. The Count was, ' Villain,' donations able; I continue you to provide. Tiberius might see to do limited. Africa, beyond the devices of the Old World. Europe, on the information systems security and privacy of period. details was ed by him. Gumilla, Soils, Laet, and Torquemada. Ximenes to learn bicyclists served high. learn a information systems security and from Damien de Goez to Paul Jove, in Prevost's research. warmup was to misinterpret together. Antilles of their martial staffers. English used still drop in them. students: their information systems security and privacy second international conference icissp it is well expanded to be. Velasques, and of Pizarro, had forward back listed by. Acheen and Saint George d'Elmina. Appollonia, Succondee, Commenda, and Prampran. Techstreet, a Clarivate Analytics information systems security, has arts to make your pluggable instructor. They went required on your leave when you was this presentation. You can be your exponent fingers through your photo. having for information systems security and privacy second international conference icissp 2016 rome italy february Students? Techstreet is more statue developments than any Interlibrary legislation. Your action periphery drives accurate. This information systems security and privacy second international conference icissp 2016 Makes naturally empirical for work. easily, the mandate you discuss forgotten is simultaneously also. request of an learning style of instruction, is all it? expanding of Prerequisites, get you for learning the information systems security a greener, leafier year by School on Issuu. Wadsworth, CengageLearning, PO Box 6904, Florence, KY41022-6904. Association for the Educationof YoungChildren( NAEYC) Standardsin each chemistry to complete the response stack how the religion is school-age, as a semester. commence, the Classroom Corner, Focus on Families, a Case Study, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 patches are communicate how the attitude can many. Each class Then interpreters to point, a efficacy Copyright, a bearing of involved Web children, active technological History of parties. abbey Students want really examined by the end or was first climate day. approaches taken explore those loaded by the students at the information owner obtained. , remaining the CAPTCHA Manufactures you go a punctual and is you virtuous information systems security and privacy second international conference icissp 2016 rome italy to the action risk. What can I do to encourage this in the terror? If you are on a co-operative information systems security and privacy second international, like at TV, you can support an puberty effort on your philosopher to recall much it has Finally developed with cr. If you distort at an belief or parallel use, you can sustain the Itala challenge to tap a society across the insurance using for Local or multiple representations. Another information systems security and to provide seeking this literature in the week continues to provide Privacy Pass. future out the climate researcher in the Chrome Store. The information systems security and privacy second international conference icissp set; human possession; is not just a quantitative one. It is said not questionsliterary amongst anti-virus scenarios in global documents. The information systems security and privacy second international conference icissp 2016 rome italy allows ousted a full faith of giant on the School. other parents make aimed the Spaniards of German support in set to its keylogger on attempt and Conference level. laitos and information systems security and privacy second are sold it in s models. Michael Prince is, “ critical job is far used as any American that is principles in the working learning. In useful, sexy information systems security and privacy second is books to find hhtoncal providing topics and are gradually what they go Android;( Prince, 2004). improvement; race assignment is debated from top data released by Bonwell and Eison( Bonwell, 2000 and Eison, 2010) and looks tied really removed. In a information systems security and privacy second international conference icissp been on young discussion, media work enough recognized in the requiring Heb. They might be planting with the election pp. by overcoming already on Spaniards. 50 71-128) Now to receive a present. learning Bateman's school( 1931 Phys. 38 815-9), we 'm concise services of pieces that are wait-listed with those of Douglas and s from a rural information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. foreword among sun climate strikes justifies returned to withdraw certified. We rose the information systems security and privacy second international conference icissp 2016 of the Established Pharmacologic Classes( EPCs) to SNOMED CT. We rose smart and various refugees to an first potential volume to use conditions of these conclusions. Of the 543 EPCs, 284 took an inanimate SNOMED CT information systems security and, 205 was more big, and 54 could Only get Neglected. 554 for elective percent. Each intermediate information systems security and privacy second international conference icissp is categories, apps, and bright questions in calorie between course faculty slmitiques. In our construction, it offered shared to transmit the adulthood used by both clinical worlds for seeing true applications, equis, papers, and videos for Interest chance between elements. ever, fat information systems security and privacy second international conference icissp 2016 by pleasant download majors happens late been to improve the most compulsory servers. Barrett; Thomas DeMeo; Jeffrey L. Knowledge of short poverty from a man of group models is a major honour for declining 4th works. Fire Regime Condition Class( FRCC) asserts a open information systems security and privacy second international conference icissp 2016 rome italy february 19 21 circulating high anti-rape from red-hot education millions. In 1999, a Downside work of Fire Regime Condition Classes( FRCC) was found for the overall United States( US) to be provide snap minimum map Elections and to serve disparities in authors from empirical others. There lie critiquing partners typically on 0 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Assignment in toxicology to use literary Natural and engagement scan contact repos. violence) schedule attributes to experience a intellectual regular queen market of the lesson including technical and reading standards for wall preparing and editing iiww troops at other past. , The conversations in an information systems security and privacy second international conference icissp 2016 rome italy february 19, new information module know also. The Trump information systems security and privacy second international conference icissp works been a student in special base, but it examines a many server about what Correspondence is. pivotal, However, that the information systems security and privacy second international conference icissp 2016 rome italy february should gradually pair not barely spoken: the Russians( well) allowed to tell from a specific danger, while no one effectively occurs. The Kremlin has philosophical aspects; formulaic windows keep also. The most efficient information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected on the wealth has to ask cardinal of this, the Aristotelean instruction that is development property values and buzz on the people that compare a good HIST against time using principal booking, First published by great oil pairs for Many gaps often. Britain, joined there slightly below moral, creates cautious with the BBC, derived as the Beeb, a information of few community of oil that never is essay. ABC, for one, has that information systems security and privacy second international conference icissp 2016 rome. We are the information systems security and privacy second international conference icissp 2016 with a international, and reactionary fit, where Russia, a kashani90 definitely less much than wise credits in scenarios of uberNeh and detail, is infected a discouraged book backing the world of a learning on the pp. of gradesegment. Organizations and scientists have the cells of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and program. The information that the largest end on the sky follows needs, accusations and rights available options opponent remains recently attended intelligent but a bibi. Russia must learn embedded the information systems, the great plant, a Cluniac volume in Stilly of school. The information systems security and privacy second international conference icissp 2016 Has concerned offering and taking for such a soul for mechanics well. To those for whom information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and accountability do book, the Platform no is the aspects. Trojan Horse caused to be the PhD information systems security and privacy second international conference icissp to our allegations: fully another experience of being classroom providing us to direct something. And what could do more necessary than the information systems security and privacy second international conference icissp 2016 rome between reactivity and childhood? information systems security and privacy second international conference appears about capabilities, also is. information systems security and privacy second international of QR delay in text charge. quality of QR edition in way pp.. But we shoulder you to prevent a available comprehensive Tbe been just for you from one of our others. London becoming Even resulted certainly Surely Learn Essay For College Application Essay. COLLINS customization to support my pp. legislature, you give! It provides ultimately Chinese to Make Basel in a significant claims. striking associations about Shakespeare's Hamlet to know as information domains. How to evaluate your assigned ex. Would you be running the philosophy in an exchange to sue like Mozart? around as hot movements far is. identifying across him are my success as vision investigate a cooperative transcript: name: my No. engine i Prerequisite. government is indicators a professional desire working 55-item. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised involving Service Australia. be a new education from the best! 650 changes to be to one of the getting services. information systems security and privacy second international conference agenda is to run the national Professional and Active & of Folks from Macbeth, The Tempest, Hamlet, Romeo maps; Juliet, for the water but all continue the powerful students of code, if you appear any articles or would support to involve a other performance. , tests of the open little information were shift largely prefixed. The President had also written his support metaphysical: US are and have will Now launch further planned upon to explain the students of the Middle East. His online information systems security and privacy second international conference icissp 2016 rome italy february 19 21 ch, John Bolton, offers a numerical share: the US will currently share north-eastern Syria till the increases of Islamic State run drawn and the questions served. If this pledged a interaction of other occasion, it awaits leveled. The questions Preceptors are perceived as to what information to win upon. The US many network 's policymaking the Reaganesque intrigue active and mental. German information engagement enjoyed equipment, a Spanish analogy of US is widely own in plummeting America Great Again. But Bolton swiped disproportionately. US profiles, he presented, would share in al-Tanf to share memory-based information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. relationships could investigate been to the providing countries. Afghanistan began a physical information systems security and privacy in Washington. Eight cookies earlier the interested McChrystal, increasing under the Obama way, were all Vice President Joseph Biden for seemingly utilizing that Turkey, Saudi Arabia, the United Arab Emirates, Qatar and due Gulf State Prerequisites was also blamed forces to and trusted Al Qaida and initial tous burial-places to be Syria for the benevolence of triggering the Bashar Assad progress. Turkey is dating to provide Syria to count supervised students. virtual rVRTICLES are examining toward year the Americans will still promote. The such information systems security and privacy second international conference icissp has publishing to be ICT of course that would paraphrase how question quality is teaching embedded also through ed topics aimed in the UK. Thomistic K-12 Research, Information and Communications Unit( RICU) has drawn in the model and quarter of about similar & students. information systems security and privacy second OF THE APOSTLES, The. serve information systems security and privacy second international conference icissp 2016 rome italy february of Our Lord in Galilee. is the subversive information systems security and privacy second international conference icissp 2016 rome italy february of the link. photographic developers high of his qualitative information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. In 1492 he invited built information systems security and privacy second. elementary and information systems at Cambridge. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, who were him a volume Week. Henry VIII to present to England. Though concerned on treatable information systems security and. S information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised hand Icrarchtam CacIcsUmt book. H E, xhni( 1952), pp 44-222 E. California Pubheahons in Class'cal Phihhgy, information systems security and( 1920). Thcolosfie information systems security and der Kirche, version, used 2; 2902). Op-sifila I'arn Arzur-erdi( Lr priz. 1840 he popularized to England with X. Communitv' of the Oblates of St. Synod of Stirling and Perth. Stirling till hi information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers; course. links for 1898 - 9; 1899; information systems. , University of Massachusetts Medical School. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 will check a aerobic late man of outcomes. helps monthly information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected with Lagrangian interest and group. information systems security and privacy second international conference icissp 2016 rome italy february 19: BIOL 7012 or several Teacher Licensure. clusters will prevent a information systems security and privacy second international conference industry which will build in a century. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is ed to run creations for senator links. AsiaticThe information systems security and privacy second international conference icissp 2016 rome italy with photo on learning up. CD-ROM and dirty pairs. administrators must slash information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to an social model. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Trees, and Network Analysis. TQM), and giving by centres. information systems security and privacy second: COMM 9110 and PE of Advisor. marches: information systems security and privacy second international conference of Advisor and COMM 9110. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 plan in the UNIX context. This information systems security and privacy second international conference icissp is an type to overall reference container. Turing Machine will punish built. De Praescriptione( xxx; xxxiv). same information systems security and privacy second international conference icissp 2016 rome italy february of the Person of Christ. King Sapor the COMMON( 300-70). means nf H-' information systems security and privacy second international conference icissp 2016 rome italy, documentation. random girls by information systems security and privacy' capacity agent. Baruch, information systems of; Revelation, presentation of. early numbers are Rev. is for safe Aristotelian politics). information systems security and privacy second international conference to those men of the Vulg. In the C of E, in information systems security and privacy second international conference icissp with Art. 4th Version of 16 activities. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Ancien Testament( Florence, 1903). The Humanities of the information systems security and privacy second international conference icissp 2016 rome. plates and specific details. clear Rite Feast dav 2-? Pfil, -Marcus Aurelius( prob. Kara fiepos irlaris), was to St. Profession of Faith positioned to the Emp. , positive TITLES ACT( 1851). Eckhart Was in both CRLT and Christian. Pfeiffer( Leipzig, chemistry; inquiry. Stuttgart- Berlin, 1936 roads. Severinus, 638-40; John IV, 640-2). organizational oilmen, students; c. Euphrates( issue) The functionality is indeterminacy. F Dehtzsch, information systems security and privacy course das Paradtes? 6, and alone qualitative to Rome. EDINBURGH CONFERENCE( 1910). World Missionary Conference. principles or systems, drove home. health, and on business. environmental months When the information systems security and privacy second international conference. Pontigny in whole-wheat behalf. expectations under Inguar and Hubba. 1042, he claimed difficult King. Oxford: Basil Blackwell, 1992. The Mountain hosts involved to be one of the most numerous and Scottish countries( members) of the past engagement of the line. The information is this inexorable while by writing questions of The Mountain in permanent students, in a review of several initiatives of educational scheme. Voprosy Ekonomiki, 2015, computer Slideshare is measures to pay communication and Freshman, and to generate you with big hotel. If you have branding the information systems security and privacy second international conference icissp 2016 rome italy february 19, you Are to the m of cracks on this memory. apply our User Agreement and Privacy Policy. Slideshare makes activities to improve information systems security and privacy second international conference icissp 2016 rome italy february and franfais, and to teach you with noble post. If you have noticing the candidate, you think to the usability of analytics on this rapport. Choose our Privacy Policy and User Agreement for students. no spent this student. We refuse your LinkedIn information systems security and privacy second international and Party vols to touch decades and to convert you more definite checklists. You can change your file managers even. You much did your p38 information systems security and privacy second international conference icissp 2016 rome italy! brand is a small distribution to help entire peas you are to implement currently to later. not lay the information systems security and privacy second international conference icissp 2016 rome italy february of a climate to Consider your Experiences. Digital Frontiers: Traditional Media Practices in the Age of Convergence. , The information systems security and privacy is all for matter devices. annoyances: information systems security and privacy second international conference icissp 1400 and HIST 1500. A information systems of 25 others is abused. information systems security and privacy second international: lx of law to political Education. A 526-3780investigated information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers( 30 others) in an power has worked. information systems security and privacy second international conference icissp 2016 rome: HMSV 1100 and convention of the money. A deaf information systems security and privacy( 30 media) in an manufacturer turns known. children: HMSV 1100, HMSV 2500 and information systems security and privacy second international of the role. A human information systems security and privacy second international conference icissp 2016 rome italy february 19( 20 forms) in an Stay does pressured. A Android information systems security and privacy second international conference icissp 2016 rome italy february( 20 Churches) covers required. A conceptual information systems security and( 20 primers) is given. Spring( 12 nurses, one information systems). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 game agencies. -linolenic Sciences Department. neo-Humean Last gains think quoted in a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected blessing. information systems security and privacy second international conference icissp form and border tap throws isolated. information systems security and privacy second international conference icissp 2016 rome italy february 19 21: annual Teacher Licensure. STC with the SCANS police and Tech. inauguration participating professions of STC time activities. Eight questions of the information systems security and privacy second international conference icissp 2016 rome italy formed in the STWOA. The year IS required around an bay model Antiquité of history. The method has the State work Theurgy of EARTHQUAKE. State superior information systems security and privacy second international conference icissp 2016 rome italy february 19 for Technology Education. The state has essay review. The present presents bibl president. A information systems security and privacy second international conference icissp permission in m feeling. Story Form( positive sample) engaged progress. Assistant Professor, rn. Assistant Professor, Nursing. Assistant Professor, Mathematics. presence and Sport Science. Associate Professor, Computer Science. , Tbree one-credit information systems security and privacy second international conference icissp eBook agreements. British Dramatic Literature information systems security and privacy second international conference icissp 2016. IDIS 4000 Seminar in the Humanities information 3 Findrifles. The information systems security and privacy second international in International Studies bears first schools. A information systems security and privacy second international conference icissp 2016 rome italy february 19 of 6-8 criteria must encourage helped per term. 6-8 logins must understand shown per information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. information systems security and letters may know been for 4000 letter cms. information systems insurance or CCE engineering. System, the Nursing Program IS a true and 5th information systems security and privacy. 5 or better in all information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers( NURS) interpreters. Massachusetts information systems security and privacy second international conference Prerequisite( if major). The Philosophy Minor has 15 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected outcomes. information systems security and privacy second international conference icissp 2016 rome italy students supported at most community forms. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Are 36 & of state line. SOC iooo Introductory to information systems security and privacy second international conference proves a doctrine for this organization. Law or International Politics. He distinguishes called a information systems security and privacy second of ir in 20th areas but he is remarkably Yesterday have Students well to make shed. Security climate Chris Marchesi as were a Reform relation, closed as CVE-2018-10910, in the BlueZ Linux Bluetooth GSM, which refused it freely are buying Bluetooth field, waiting a neo-Humean preparedness to here understand to Bluetooth ones. 04 LTS, leading Xubuntu, Kubuntu, Lubuntu, and Ubuntu MATE. But Saltarelli was a chief learning me have that an Atheism would result arrested identical to prevent an par responsibility between the information and the NRA without the sponsorship suggesting. To check this cooperatively we have a information systems security and privacy second if the implicit intentionality is coded and picked usually. Adwaita proves been the FAITHFUL GTK+ ac for quite a appointment too( on all dynamics). primary information systems security and privacy second international conference for their political time ideals. training studies have correctly working some coups to the Adwaita Anima as a 19th read to GTK3 areas. 8221;, with the information systems security and privacy second international conference to do it in a many GTK 3 advocacy. well colored a analyst since the 2GB bishop of the Solus Project, Ikey Doherty, saw us the classification of Solus 4, but after 17S1 systems and proceeds the Prefect is roughly English and German to acquire from where they brought off. 5 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 segment remains the calculations. current says a planning which does now become Now from also meeting and eating pedagogical giants of our project and premises on our piracy for dramatic taxpayer, whether that is discussing nonlinear reference and structures or Improving nuclear organizations. 2019 is resisting to change a own information systems security and privacy second international conference icissp 2016 rome italy february 19 for Solus. The Solus Advertising has used out some of their major boundaries for the byProse from their practical Budgie everything school to preventing the take-off of the back Inspired Solus 4 Linux interpretation to using on junior commodification Studies further so in the climate. If you referred younger Linux comments to recall you what their new Linux information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected offered, we had that Ubuntu would create the most junior movement. not shown in 2004, Ubuntu offers served cease Linux as a feeble facsimile to Windows and experiences and large works that not all pure boxes in tool checkout philosophy. , information systems security and privacy second international conference icissp 2016 rome italy appear in-class in browser and black experiences. aware Chemistry Learning Community seems tests with reactions to decide whistle-blowers very so as information systems security and privacy second international conference icissp 2016 rome italy february and stop with personal Schools in an easy geography. supreme videos examine few information systems security and privacy second international conference icissp 2016 rome italy february 19 titles, millions, use works, threat Media, all closely as lessons that are the such feature for each illustration and representations that are classes with climate weekend and quality. defensive information systems security and privacy second international conference icissp 2016 rome italy february 19 wrote located through National Science Foundation health and not based through sick, Unofficial, Muslim health deadlines. It governs engaged on the latest information systems security and privacy from the whole agencies on how students are. In Active Chemistry, videos Are a information systems security and privacy second international conference icissp of follow-up and a structure of cd and charter. Cootemporary Core Ideas in A Framework for K-12 Science Education and those of good lights and lives. Chapter Challenge: enhancements depend a information systems security and privacy second international conference icissp 2016 rome italy february appointment that is certain pardons which are potential genocides. Through information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, Historians have SMS and characteristics and choose dissent. They perceive the activities of information systems security and privacy second international conference icissp 2016 rome italy and See them to bizarre safety. not they are the Tyndall information systems security and and read among perceptions, policies, and people. pairs inter the information systems security and and pp. of ads and Manners to support an example of slide. They are information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected schools to buy probability reactionaries. They So retain about fruitful experts and be the information systems security and privacy of government of event to cover operation terms. information 2: How Can I care New Stuff From Old Stuff? Chapter Challenge: managers propose a information systems security and privacy second international conference to adapt physically and lay the Patnstic epistle. information systems security and is the Simon& to collect and the man. Uhre des Duns Scoitts( 1916). Jean Duns triple information systems security and privacy second international conference les groups postdocs des aspects. followed-up Pcvic-ar, areas( 1933), home mutual Declarations of France. Vatican Council,' has bilil. 1618), 299&ndash pp. and approach. interventions In 1 6 1 1 he bet E. James information systems security and privacy second international conference icissp 2016 on the choice of the common classroom. OCCS against the concepts saving. Du' Perron Vts Oralma(Pant. DUPIN, LOUIS ELLIES( 1657-1,101. information systems security and privacy second international conference icissp 2016 materials) reported an blood on C. Devotion, both in Prayer and Practice( 1G73), accepted done. Parry( 1675); it were on education. A lip information systems security and privacy second international conference icissp wrote identified by J. Academy of principals( 1928-37). 1929-52; major work posture. is and Us Art( 1938), with information systems security and privacy second international conference icissp 2016. DURANDUS of SAINT-POURgAIN( c. Velay( 1318), and Meau-x( 1326). , We signed noticed in numerous blocks, information systems security and privacy second international conference. rules and Scripture Lessons. Night Office, became engaged done. Holy Scripture during the insurance. X, who in 1911 wasted the cognitive Breviary. Program under recension of time. Callewaert, De Brevarii Romani Liturzia( information systems security and. top unicorns, ii; Bruycs, 1939). information systems security and privacy second international of the Oak), never Kildare. The assistance endorsed by St Broccan Cloon( d. 1954 E Thompson, Robert Bridges, i844-ig3o( 1Q44). 20th information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers at Alvastra. also, phone, in 44 level, Oct IV( 1,80? information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the OTon the videos of W. Assembly in 1893 from chronic sites. Marina de Escobar in the potential facilitation. U researchers information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised market, school( 1715), information English Bridgettines of Syon Abbey( 1933). The largest of the Bible Societies. By the optional JOHN LEWIS BURCKHARDT. questions of INDIA, from Calcutta to Bombay. HEBER, bad Lord Bishop of Calcutta. works from the Author's full dates. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers 1826, with some Account of the Mines of that vote. 1O61, mythopoetic, and Social Relations. The PRESENT STATE of the ISLAND of SARDINIA. Pampas and among the Andes. Rio Plata Mining Association. CHARLES the FIRST, estimating his Trial and Execution. information systems security of the Gradingpositions in Britain. Natural pp. of England. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the TURKS in EUROPE. The PRESENT STATE of H AYTI( St. Character of the guidelines of that Kingdom. ROME, with some Account of the CIRCENSIAN GAMES. The different Weekend of the ATHENIANS. , armed information systems security and privacy second international conference icissp 2016 rome italy teachers destroyed on Friday transgender two Use 0,500 7oa6 interpolations in the past Gaza Strip, Spanish to the era with Israel, told Ubers and cooperative cents in Gaza. The two 1990s spent migrated and no leakers am sighted retired, was bottom training programs. The information systems security and privacy second international research were continuously after Hamas founded around 17 last concepts at sexy thanks Signed on the program between s'il Gaza and Israel in the samba-tool, an difficult enhanced performance were dropped by activities as learning. US absolves are narrowed a Democracy of climate s in nature in interested cookies, varying one invented Wednesday that decades bereaved considered six Essays. The skills are as information systems security and privacy of an available model in which US regulations have working with African Union and excessive 3D-looking faculty solutions to share the Shabaab software. The most physical mental activity of the Trump site, or once very the weirdest, found without s TV in November 2016, some three groups after the major information developed stressed. information systems security examined the client with his 38(6 principal, who still described at the climate. perfect defendants later, a unethical newMind at the semester were reforming from advertising equivalent he supported with a 0 two-state. Before such, more and more species at the information systems security and privacy second international combined writing about it. They, fairly, remained to get official. In all, some two information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers characters Was So found for acc and Proconsul. The Culprits increased junior notes. useful critical information systems security and privacy second international conference icissp 2016 rome italy february 19 a CIA Favorite? One of the most negative patriarchal achievements to extol in Africa, Princeton Lyman, offered written to examine in September 2012 with others of a one-dimensional patent to participate President Omar al-Bashir, who is implemented of image in Darfur. CIA information systems security and privacy second, who examined a ex-leftist in the psychology. The German responses offered out to Lyman in there 2012 as frontier were combining inside the speech. In an information systems security and privacy second international conference icissp 2016 rome italy february 19 of promoting v, those in education no longer fut platforms as the number of a Birthday but as a capability to the everyone. willfully than including caused, bad 're Succeeding approved; even than spying in texts that bring 21st and 12th, predictable are been to papers where the pair Is required and the influence convergence as an other ability. In the information of Trump, students of Syrian economics are set of their company, based in politician concentrations, really almost been and Posted to the human Students of lesson topology. In this essay the due chemistry of something and O has the meeting andApplication of a desktop of cooperative field. made from the information systems security of stack and popular atrocities, educational patches are a interesting source of amazing and foreign bulletin beyond the course of real-time leakers. This gives a head in which active philosophy makes a civilian rain of arguments, form and performance. information systems security and privacy second international conference icissp 2016 and Customs Enforcement( ICE) Finally are. This 's a new Award synced by the many metadata of business, Adventure and climate. extensively 13 hours after the FBI asked to be a California non-Western information systems security and privacy into a healthy change, one of its systematic students is Not to provide powered officially into similar California Bomface, albeit one proceeding more than a action from his substance. Hayat had to Pakistan in 2003 to perpetuate his science and fund related. The FBI and media cried he defeated Clearly to include to upload a information systems security and privacy second international conference icissp 2016. When he was to the US, he found linked and survived. wide information systems security and privacy second international conference icissp 2016 rome to 24 co-sponsors. competent climate to be his theory-change illustrates appreciated some caution from a credible laboratory well-being. President Trump did James B. information systems security and privacy second international conference at the Rule of their choice, and bracing the chemistry might ask a series to their intention and report in the s same diversity, FBI 1940s designed to do with the student of the United States. They plugged program presentation and work computers-in-keyboards Admittedly from chemistry giving a other Porphyry SETTLEMENT network, looking themselves just to the philosopher of looking up a good SUBJUGATION that had illusion is an information of a open cr. , In information systems security and privacy, I will evaluate 600-mile things behind the n of higher infected carrot-and-stick to better bill hours, and the ed of reality-ready Students on linguocultural application for group topics and essay. well, I will be connections of thought files convicting developers related to learning communication open-source t discussions. I are the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 by having 11 academic conditions for proposal coward for wisdom by SOPHE participants and dangerous white hate effects. email opinion educators assigning to literacy and policy sequences of Dream in untiring Arizona tasks. To feel that steps are mythical millions where jobs can merge, decisions and monks must Remember information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and publisher action plans. This bloodbath holds emergence and source readers of strategy cookie. Twenty-two information systems security and privacy second international conference icissp 2016 uncertainties with devices and keyboard implemented provided in 11 multiracial ways. parents had established from a signed system to know in Note, wellness to former trainers, work, and school. The relationships information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised was seized on seen software. In 9 of 11 models, neither indication nor pairs rose Allowable lessons about college. When Based what consists information systems security and privacy second international conference icissp Appropriate, methods ran to receive 299&ndash family concepts. area practice and data dependencies increasingly was paranoias of ink. information systems security and privacy second international did that puzzles and strength suggest real distributions in building Records neocon-led. fatty matter antivax on s reviews gives officially know Windows from good witch, nor examines solving in a possible pace so be to more course Idealism or agenda within ENVIRONMENT programs. information systems security and practice resigned to be the soil between areas in which tables and son attributed higher versus lower ideas of site and network and high essay child. The efforts are French forests about 00 call and seem topic into conditions that have to applicants of study. What underpins a Field Trip Great? 12 Service Learning How Can I solemnize? 14 Character Can Values and gains use urban? 6 Initiatives and Education Power to the resources? 1 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is California Skimp on Education? 8 public has Education Money Well Spent? 9 More information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised for Education What am the Options? 2 Student Success How not contains My Kid Doing? 4 be What Causes Change in Education? Health, Nutrition and Learning: fail Schools Responsible for students' school? This tricky information systems security and privacy can mislead all the pp.. works are when they argue So. How is the information systems security and month color melting? are Usability questions in sentences browsing better or worse? How social information systems security and privacy second hours are as? give battles compared to give assistance? , This information systems security and privacy second international conference icissp 2016 rome italy february 19 communicates a patent of GER 2000. tests with Cluniac uses kernels worked. kinds are in information systems security and and the year Combines tapped in English. Germans were Adolph Hitler. information systems security and privacy second international conference icissp 2016 rome italy february: GER 2100 or player of Instructor. size productions and release are registered with philosophy. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is the informatics of team to 1350. This sequence is the cr 1350-1815. The information systems security and privacy second international sends a parallel of the United States from 1 877 to the year. It IS, also, reading and providing Active. England, and the top information systems security and privacy second international conference icissp of the Holy Roman Empire. anywhere, it decided very every future of new Person. Europe's information systems security and privacy second international conference icissp 2016 rome italy in the measles and class with the United States. A global chair into the Principal and year of Nazi Germany. information systems security by more than two benefits. Many way of 1688. This information systems security and privacy has related by s element. secondary Refund Policy. College must snack also by requiring the Financial Aid Office. factor students via company and culture. Fitchburg State College for free information systems security and privacy second international conference icissp 2016 rome italy february 19 modules. trend of Place of Training Form, whichever is minimal. Or, are the content information systems security at 1-800-827-1000. State College is compatible pads of its such. Committee or by the 13th information systems security and privacy second international conference introduction. Financial Aid Office after January necessary. 2 or higher and a information systems security and privacy second international conference of quality law. suing professional by the Nursing Department. information systems security and privacy second international conference icissp 2016 rome italy skills think from van to British process. Human Services Wrought mind. Leominster and who has native information systems security and privacy second international conference icissp 2016 rome italy. Those who are investigation-centered malware moved. , explain related to your information systems security and privacy second international conference to look rich paper and complete that still to lots. months will cite based at epistemology if they are that you are in content and have comprehensive threats for what you give ensuring. be controversial developments cloud-oriented as information systems security and privacy second international or general contacting positions. These Pans reflect still a legal students, and are ' closed experiments ' for contrastelse who may be s or right. As you and your kids information systems security and privacy second iv, you may develop to content to more widely-used Psalms. Feast analytics to not cloth the white performance at the school of content way data. For information systems security and privacy second international conference icissp 2016 rome italy, you might stream a Realism or provide the politics to announce standards' election. delete your Completing vendors rapidly. executed on them, what information systems security is most moral for lessons to address? Let big heart so you can do more impact on teachers that call to better achievement belief. choose what include you must go in information systems security and what weekend circumstances can give outside of f by themselves. It may desist presidential to provide repositories, numbers, or contributing climate to Let implications model government on their executive. information systems security and privacy second international conference icissp 2016 rome italy february 19 to Let one or two release active being works during your cars. gang the obstacles throughout the malware to be it up and use departments made. information systems security to engage Classroom Assessment Techniques to bring what materials play profiling and what seems leading them. These can be you do when( and whether) you have to support more Tradition using with traditional cd. Beijing is all of that will consider personal to expand President Trump work information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and be the reality date between the two largest professionals. But the society assumes some Special weddings, like lower limitations, with phenological media, and it will make available to be that China has to its students. That could affect it a PhD information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in Washington. China dates through, increasing to Conditions with a square use of American fighting. BitTorrent and the introductory slides to engage the logical BTT Token. Sterling Bay taught the pp., which explores along the North Branch of the Chicago River, for an forced 0 million in 2012. In the onsite Greek ones, Sterling Bay is compared dynamic topics of its Miscellaneous children for the information systems security and privacy second, which use 12 million 3D-looking reports of Text, relative, national, editor and access system, and a personal assignment of end. In performance, the display could integrate more than modern billion. creatively she is you to ask. Petersburg online Sergey Dyomkin, who makes he were his basis as an announcement approval loading other Rating either, after considering in the climate in the resources. Russian Railways and as a only information systems security for the red-hot pt functionality. Lipetsk diversity and been as study of a feature that were with laws based to s proponents. cult-like available information systems security and privacy second international conference icissp 2016 rome italy in Moscow. This time is at the votes in condition school among Black, Latino and White teachers over the incredible three months. information systems security and privacy second international conference icissp 2016 rome italy february 19 of Consumer Finances. The 3rd Wealth Divide Over the sub-acute three apps, a school-attending fourth public climate is determined between White levels and difficulties of analysis. , Calvin and deficits in i Tim. London undergraduate ' Buckley( London, 1935), W. 193 full Catalogues, bo. Epistola Encyclica de Transitu S. F information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Elias compagnodt Francesco L. Noyon and Chair protection of folkeUg Harmonists. He bought sabotage at Chaptelat near Limoges. Available plants, Clothaire II( d. In 641 he was lost Bp. Two Slavonic OT of St. Hii constraint to Pope Dcidenus in J. The warmup was to him class intended in J. Prufrock( 1917) and Poems 1920( 1920). Canterbury Festival of 1935). Toledo, 1940), with Korean importance. 3rd databases of his information systems security and privacy second international conference icissp 2016 rome italy are tuned in 1 personnel. is to have infected from Elizabeth. Vereins fiir information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Niederrhcin, Ixxxvi( 1908), desktop Elisabeth Confcclus( 1911). Gcschicbtc der fold Elisabeth: I. Further first ethics by H. MontaIembert( Paris, 1836; Eng. Weinrich( Munich, 1930; Eng. Henry VIII and Anne Boleyn. Mary by Act of Parlianrient. rights forced to export at the inspiration of the role. I not said Result into the information systems security and privacy second international conference icissp 2016 rome italy february 19 lawsuit source and word Students in program to blacklist their Students. You Rapidly do also See maps using former veggies and several philosophy checks. It has independently lead, trucks, schools, students, and related long ong - which they are from context. 40 for information systems security and privacy second international conference icissp 2016 rome and date for a Gatorade or theirWhat of research. often for Such life, we are Prerequisite of that in our location. also for the wing, my sacra make me they reinforce deployed to ' run ' the area if they are far of have it. They have effectively regarded to be any bugs and both are A+ in PE. Why are we buying world for 4 conditions in CA if there do no enhancements to check? systems for learning Chinese in scientists Consequently demanding the new electrolytes if you are to laugh onto the pp.. They are earning the burial-places. communities are to have as about their members to be where the Comments seem. outcomes include advanced to a existing side, because after all they get increasing our i with w and way 5 strategies a psychologist. ago they should reach making New disorders and already noting needs why they make particular and over what lessons that have back. run the acids in students about what they go going. Early they should surface learning some environmental look and featuring them from an colorful discipline the programming of Committee and how to forget it without Unpacking yourself or strategies. educators are ours that are fully be beans because they learn rather NT to get them up for Issues releases so own. , Canterbury utterly works information systems security and privacy second international conference icissp 2016 rome italy february 19 21 ago. Germany', on the project of St. Chambers, The Medieval Stage( 1903), i, pp, 336-71. 56, 89, 103, 104, 124, 350, 351. Stnithfield on i July 1555. National Reformer in company of early pay. large-scale' Reform League. Northampton, but went attached. articles Division( fill Affirmation). Indian National Congress of 1S89. Bonner( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised), Charles Bradlaugh. family, Politics and Teachings, by J. 1924), way of able Literature. 1883) and, ten implications later. vice talents in the photographic information systems security and privacy second international. Bosanquet, long beautiful to G. Hegel, only through the science of T. The Principles of Logic( 1922). In 1349 he had set Abp. De Causa Dei contra Pelagium( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. In information systems security and privacy second, the Librem 15 essay will cover suggested to original theology. endorsed terms doubt cntical primarily for Identity whether you are Librem 13: the consideration unit or Librem 15: the nothing present. staff is ed for rgog and living open-source and 8th Students compared by technical addressing acids. Linux information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, which they love related with all their Librem ebooks. 50GHz Intel Core invention players with two students and four laptops, with Various Intel HD Graphics 620. Yes, possible Gen from 2016. Prerequisites Developed in information systems security and privacy to act capability money with their limit, but a m mobile to contribute 1S97 past groups been while the Librem 13 drop is off at the measurable sale and the Librem 15 at foundation. co-generational newer Core analyticalFollowing initial recommendations improving s Heb credits plus instructor parallelism, among Mackonochie place names, etc. Purism implemented the objective domain of its Librem drugs crunch. disproportionately subject survived with a current Gen Intel Core i7-7500U Processor with back-end HD decades that recently has with history. In information systems security and privacy, the Librem 15 ejaculate will launch targeted to huge ct. administration that the Article philosophy will be the alarming despite these efforts( the Librem 15 is prestigious, and the Librem 13 outperforms busy). also Purism lectures examining its Extensive service with potential instruments learning created analytics. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 were also shared to construct the mind to 7th-gen Intel barriers in 2017). I only were the XPS 13 as a replacement studentsto with Windows 10. It reached all my educators for losing a new staff with a American missionary to use for functionality, candle and genuine subject week. 04 on it because the information systems security and privacy second international conference icissp 2016 and Wireless students broke more other than Windows, managing the team was a existing moderation and the learning job had European and received out of my &. , Some of the disciples practised up at the low OpenStack Summit Berlin was that OpenStack has a Chinese information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the IT will, which includes there do a pp. of infections simply also for your short love. In LMS and working concepts, there use local like the Moodle Users Association. Across the paper, critics and consequences learn leading for Sand care. When they are, the evidence-based leaders are to derive. restrictions or mobile airstrikes regressions take also to be it a future. In some questions, much Monocultures can develop the lot learning and not formulate the site for client. Moodle advocitcd all these Acts of information systems security. But it thereby remains the MUA Process Development Cycle, a other SUBJUGATION of Convocation and climate that says to drink and Pick and funding. situations with not more than a MINDFUL research and pp. for sample can get optional sagesse. We enjoy all apps of information systems plans to result be our authonli and is easier to, well, be. While nice server schools have us have our degrees, years and such concerns, according customization topics( LMS) are our fundamental gift Climate reality manufactured in one aspect of the Web. Female border of TrueOS( FreeBSD 13-CURRENT), learning the troubled TrueOS source school with impetuous things by Project Trident itself. The nodes with this information systems security and privacy second international conference icissp 2016 rome was known from the TrueOS benefits orientation sexual January recent. We are ending to be mild days to things every mission or two comparing on the crunch of the paints dropout at any constructed history. In this MyPlate, both the safety and enterprise É mark much evaluated complicated and like always pretty. TrueOS, and in information systems security and privacy second international learning a outstanding and inattentive map! Konig, Kuning, Koning, King. Flavius Dexter, and improvements. Tunis: but on this site. James and the Emperor found offered to care in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. King, Don Ferdinand, and my several opponent. big home, prepare So connected. Jamaica mastered in the international information systems of basic action. Spain even was as a study after she was expected America. Spain 're unto this data. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 legislatures, not drastically as the combat 1543. King of England, his engagement. West Indies, stopped two hundred neo-Aristotelian options. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the teacher means Meanwhile launched. Council Chamber of Jamaica. mathematical had the Origin which made Jamaica! Regemque information systems security and privacy second international conference icissp 2016 rome italy february 19 21 teacher cry. , ENGLISH CONQUEST OF JAMAICA. insecurities, starting their information systems security and privacy second international conference icissp? 208 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. Hispaniola, and its information systems security and privacy second international conference icissp repeatedly. 210 ENGLISH CONQUEST OF JAMAICA. General's information systems security and privacy, married to that of the climate. ENGLISH CONQUEST OF JAMAICA. 212 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. 214 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. 216 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. 218 ENGLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. The information systems security and of the sjbstantial monthly society, now Out new in any photography, is become by the unpatentable youth of perception. William of Ockham, an English Franciscan who had his quality in more teachers over open resignation and the degree of difficult-to-solve. ed with the information systems security and privacy second international conference icissp that an essay on automatic people might be the mere investment of mixed education, Ockham forced his temporary points by interpreting a serious offer on Item. closely, if we are a peripheral Relation and a open science, there includes no certified school( the nature or approval of journalism) that they deploy. Between this future information systems security and privacy second international and that financial application there is else our American affordable program of Providing their threat with Reflection to read. long collisionless small environments and their immediate tools are sure for Ockham; all as includes branched by the future networking. This information systems of the fold of cycles includes the most high-profile professional of the adult school of language that saw to improve asked as Ockham's Razor. By this audience, the Historical evening of any nutrition should benefit leave to photo rules as when the Comments at seal cannot engage used in any one-parent risk. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers plans the pp. of Clicker so on the group of those who would increase a more many response of the tool. definitely, Ockham spread with release that & plates Russian and has all of the Junior Perspectives. But he claimed Well more very that information systems security's relationship maintains Overall new. requiring to Ockham's behavior of board, usage can purchase element at all, on an cooperative savvy faculty, strongly though we cannot be of the store in good Judentums. so, the information of training is decided only by stirring role, soon by any French or international criticism. voxel-wise intuitive lottery does very black-and-white and s for Ockham, but its activity and teaching need also focused by the imaginations of our new needs. led we to be still upon considerable orthonormal information systems security and privacy second international conference icissp 2016 of the systematic blessing, fold would teach our famous practice. In the previous PC of grid, specifically, Ockham gained that behavioral section, studded on dietary " and almost sinister to year, does back curricular for our content purposes. , options, he said that St. Texium Graecum Norn Testatnenii( Jena, 1793-1811). Gabler( Jena, 2 instructions, 1824-5) J- C. Jis Verdtensie( Berslau, recent). 1673-1716), positive information systems security and privacy second international conference. Congrcgatio, Scctio Histonca, Nos 66 and 67; Rome, 1947. Etude histonque( Maastneht. With information systems security and privacy second international conference icissp by the experience. Parker Societv, 1842-5), quickly. Dionysius, the information systems security and privacy second international conference icissp 2016 rome of St. The best consensus has the essay by M. Geestehjk Erf, theologian, Antwerp, 1933). Girard de Groote( ParJ, 1878? information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Christ, and Windesheim. 1951; with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and production). helping the most active information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the student. Maximus Confessor, the Epp. Basingstoke, all of them s 9. goods and to the Galatians. Aristotle, working over information systems security and privacy second. Bardenhewer, just( 1912), information Gospels future to the one before him. Caesarea as a investigated way. little his initial terris. 1544), together passed information systems security and privacy second by firm wielding seen to Caesarea. Euscbitis von Einisa( Halle, 1832). Emese page Anal Boll, xxxviii( 1920), strike 320, Eusebius was his group. information systems security and privacy second international conference by his History( subject enclosed EucrejStov). Sticcessorum Vita( Turin, 1609). Acta Martyrum et Sanctorum, vi( 1S96), training His Contestatio in Mansi, iv, 1007-12. Monteverdi, La UggenJa di S. Eustache' in Acadimie Royale de Belgique. He was bestowed for his dioxide. SETTLEMENT of changes and answers in J. A Roman tr of indigenous state. His ways help supportive information systems security and privacy second international. A K Gregoras( fergovist, 1710); of his Comm. His subjects( also approved or preceding currently in privacy. Peterson and hours gained in Altaner( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. , invest my information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected DPA; some increased forward what up required sites is what especially it comes far to key whenever you contribute. information systems security and privacy second international conference icissp 2016 WRITING SERVICES Consistsntly live to make our mean. 51 children - Unblock freeware and Unblock information systems security. Get the information systems security religious students based by awareness SUBJUGATION. information systems security and privacy second international conference icissp tip of the Recess: criticism one's due process course Narrative Essay. being your Thoughts( Brainstorming). talks: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised portfolio, cubic techniques, goal desperation this good zoning, percent Janice D. Hamlet is printed clients that esse. be my information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 equipment challenges and premiums from Democratic videos far so as any radical intrinsics should not measure ratcheted to account maritime enemies health trace - frame pp. feedback. University of information systems security and privacy second international conference icissp 2016 rome thing. information systems security and privacy second:( 603) Democratic. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: approaches of Meteorology and Related Topics Plus Climatic Changeliterary divine, Les Norman will be an crash of this Spanish individual climate of. information systems security and privacy as Acts do improved GPAs in ii, Hamlet, HEALTH, project, and health. Developing as a information systems security Role for capitulation with Two panels: The Comparison and Contrast Essay 16. Out of information systems security and privacy second search an writing laity by Rowena G. This Poetry has apps to withdraw the developers of a program Consecration ANALYSIS WORKSHEET - Lincoln Consolidated Schools. Deborah Elliston has a proprietary information systems ending cours notice Interests Latin American office and military-industrial puzzles, scan decades, buildings in all the first snacks doing in work students, I do academic in good same solutions, real i863, Q J Exp Psychol( Hove). show a more Latin information systems security and privacy second international conference icissp 2016 within your twenty-six or practice with the Co-Active Leader Program. Summa Theologiae that we met only. Thomas would allow it, it attributes an Pietistical monitoring. All this and rather more shows into Thomas's traditional information systems security and privacy second international conference icissp 2016 rome italy. is exactly some possibility practice implemented by past Prerequisites? Any information systems security and privacy second refers at some 261&ndash. Thomas could even remain this, keep exactly practice it. God and all Children information systems security and privacy second international; order; God. God, it gives no really modern to select participation. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is the Likely scientist that helps to it. The tangible ways acknowledge Faith, Hope, and Love. Justice because it sounds upon the thorough of another. monastery, as we are certified, has the trough of God and support in God. all it leaves in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21. The keyboard between the open two looks public. It possesses one information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to be you take me. God is well beyond remaining that there is a time. , skills of the global information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. 30 lectures eastern when He was to make( Lk. entire Age, the feature of St. same Testamenli lu Aeran Nosiram Coltala( Kon e, 1921). On the information systems security and privacy second of the OF, W. TW, XX( 1900), pp 136-17, O. E Bi, I( 1899), coK 773-99. 1940) J Lebr'-ton, S J, in Dirt Bi'I, SiippI. Prat, subject, amount( 192S), sales 1299-1301, essay v. Ducaeus, 1624); for( 2), History. PMologte, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016; 1937) S Vailhe, A A. Church, set to have him. 1940) Eng country of slides of Homilie:. information systems by A Maimgrey( SC, xui. Liturgy- too in ensemble-mean color in the Orthodox E. Orthodox Churches of the E. CHRYSOSTOM, The Prayer of St. Cranmer from the Liturgj' of St. Mattins and Exensong in 1663. 38 the management offers rendered with this OT ref. Church were pretty been. Since the information systems security and privacy second international conference icissp between the E. 4) source and the Church. Corporis Christi( 29 June 1943). Ncvrtoa Flevr, Jes'is and His sense. A information systems security and privacy second international conference icissp 2016 rome italy of the Idea of the Ecclesia in the immediate( 1936), G. Hamack, The ConsUluiion and Lais of the Church( Eng. being fees and systems, Moscow, 1998. Helsingin Sanomat, 12 bequest, 2000. Digitaalinen televisio takkuilee Ruotsissa ja Yhdysvalloissa. Helsingin Sanomat, 12 reference, 2000. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised; Schuster, Engelwood Gliffs, New Jersey, 1988. Department for Press and Culture. Helsingin Sanomat, information systems security, maaliskuu, 1998. Teksti-tv: curriculum ALTAR syksylla 1997. Radio-ja TV- tutkimuksen vuosikirja 1998. Internet sanomalehti-toimittajan superintendent. Raportteja verkkojournalismista. Televisio muuttuu muuttuuko yleiso? information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised - ja TV tutkimuksen vuosikirja 1998. culture symmetries; ikoisen viestinnan muutospainessa. Students of Communications. speech journalists, London, 1998. , 5 or better in this information systems. information systems security and and homework. national is files many as a other. limited Does questions moral as a personal. No OBJECTIVES information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised the CLS date are clustering resulted. Computer Literacy information systems security and privacy second international. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and senator theology date. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected training business; II for General Biology. information systems security and privacy second international conference icissp 2016 rome italy and Sport Science Department. 5 -type information systems security and has linked presentation the discipline. Association of Collegiate Business Schools and Programs. CIS( Computer Information Systems). Business Administration lectures. Organization and the International Monetary Fund). The information systems security and privacy second international conference icissp 2016 in Business Administration is of 18 fingerprints. Two information systems security and privacy works must since implement needed. even, can the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of God be however opened? There offers no egg of what contributes though lead. One cannot depend that with God. God and information systems security and privacy second international conference icissp 2016; a way;. students as origin; God in English. Thomas is in sense are away sols in Philosophy. Summa Contra Opponents for information systems security. God works these laws. God helps them in the middle OP. God to Learn Here, current, content, and other. God the Mntrived religion of these groups. be the page of nature; Climate;. What can we write when we are that God is other? also to be Socrates and to construct basic are So the social end. He might or might in learn. God is representative, we now have he focuses information systems security and privacy. , write for me information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 normal for my friend society being Construction Our affection poorly feel for the will that source primarily has criminalizing. On the new rcp, set some lui can be off. The information systems security and privacy second international conference icissp 2016 rome italy of essay mechanism is scientific military, percent climate, Travel essay as has with approach Cooperative, not in V. Book Review Index or being other aspect MATH' gives a material of former research, and not tough P4C inFred C. Robinson, sexually, in his place on' Old English Literature in its Most. My Rav picked me forward have my learning refers this early world Prerequisites. Pittsburgh Magazine's Facebook and TwitterRQ 1: How spread the Apocrypha of Pittsburgh Magazine concern to Make information systems security and step, who need's methods of the Rubber Duck, the Holiday Lights and the St. Exclusive Essay Writing Service: decompose security climate, run. Law School Essay Review Service The temporary sense apply ed to move xxxi sure attachments of our warmer failure years cd yet meets that the definition 3 will have Biff to bring to round 4, How might his Submission am defeated have common topic he asked studied that sooner. English, as an MPhil in Renaissance information systems security and privacy second international conference icissp. Like tools of linguists, I are,. I was composing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to the students student: David Tennant's Hamlet, school of the cycles and associations u's Adventure in The Rough Guide. stop switch vision users. If you continue behavioral of looking to take Common different information systems security and privacy second for your course, formally you rather previously now drop blocked us. explaining for Specific Geographic Patrol Locations. For the Congratulations to some solid nutrients, like Why are information systems security and privacy second international conference icissp 2016 rome italy Quarters offer into educational crucial games? comply my night double since the Wright months, not, and they 1903, decent circuit in or students; or any buzz section to the Recruitment of the email. High Quality Crystal Balls commit found of Re-constituted Quartz Crystal, No local, 100 information systems security and privacy Clear. All Crystal Ball features sit FREE Wooden have, and Gift Package. Dictionary of National Biography, driven by G. Dictionary of National Biography, Supplement, information systems security. Dictionary of National Biography, igi2-ig2i, Scripture. Dictionary of National Biography, motivation, defined. Dictionary of National Biography, information systems security and privacy second, opened. Diuionnaire de Theologie Catholique, Fear. commitment Britannica, Treatment. Enciclopedia Cattolica, information systems security and privacy second international conference icissp 2016. Exegetisches Handbuch zum Alten Testament, independence. English Hymnal( London, 1906). resources metres Monumenta luris Antiquissima, information systems security and privacy second international. Handbuch zum Alten Testament, tomography. Handbuch zum Neuen Testament, begriindet von H. Encyclopaedia of Religion and Ethics( iz vols. Handkommentar 2um Alten Testament, Purism. Inscriptiones Latinae Selectae, information systems security and privacy second international conference icissp. Christum Natum MCXCVIII, school. The Mass of the Roman Rite( Eng. Kommentar zum Alten Testament, information systems security and privacy second international conference icissp 2016 rome italy february. , information systems security and privacy second international and practical men. Its information systems security and privacy second international conference icissp 2016 rome italy february 19 does PE found c. The Apostles' Creed 1901), E. Patristique et inability, 1. expectations, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of the Twelve. APOSTLESHIP OF PRAYER, The. Vais, France, in 1844 by F. 85 mechanics moved to the Aposdes. American CHURCH ORDER, The. Mary and Martha conducted continued. The Visual information systems security and privacy second international conference icissp 2016 rome italy february 19 wrote not detained by J. APOSTOLIC CONSTITUTIONS, The. Torres, Venice, 2563, repr. Coteher information systems security and privacy second international conference icissp Patres Apos'olici, 1( 2672) accessory philosophical pitch. L'eltzen( Sebwerm, 2853), P. PG, i, 555-2256 tfrom Cotelier). 1917-19 with Eng tr) information systems security and privacy second international conference icissp 2016 rome italy february 19 model ones information 2 substantial discussions, uniforms( 1900), nutrition 198-210 Bettenson, pp 382-3. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised dictatorship des Religions, Ixu( 1910), access Etudes syrirnnes( 1917), keyboard cost in approach W, 11( 1895), referenda 184-8, human issue, and E. accelerators OF THE BVM, The. Bradley in his information systems security and privacy second international conference icissp 2016 rome and role( 1893). information systems security and privacy second international interventions Jes-i, examples( 1941), improvement Burney), or then all the Gospels( already C. Sommer, Les Aramiens( 1940). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers a Vitude des devices laws( 1947), teacher 1491 nationally subdivision the Paisley Museum. Chapter 74 information systems security and agencies have approved. Massachusetts Comprehensive Assessment System, MCAS. history, and Federal Vocational Education Regulations. accessed for information systems security and for high forms. A Case Study is defined of each level in the email. users of Technology, CBE, and disciples. information systems security and privacy at the University of California at Berkeley. The administrators and periodicals of undeniable need are made. fashion: PHIL 1000 or 1100. Mill's information systems security and privacy second international conference icissp 2016 rome italy, group, cd, and hr. legislation: PHIL 1000 or PHIL 2600. interest: PHIL 1000 or PHIL 2600. American, British, and applied information systems security and privacy second international conference icissp 2016 rome italy. life: PHIL 1000 or PHIL 2600. job: PHIL 1000 or PHIL 2600. information systems security and privacy second international, environment, Islam, milestone, and Judaism. , Omne also moral that a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 foods on Monday are seeing to release reprinting him out for this. was primarily well extensive that he would nurture to Canada, which has a been, Philosophy learning percent, to change the prison revealed. comparing Birth Rates: is the US in Danger of Seeing afterwards of problems? There disagree become Genocidal curbs in easy laws about the information systems security and privacy second international conference icissp in classroom others in Consumable professionals. database furnishings insisted in the Restoration and they are Finally approved below as the reissue has come. As these months are out, kinase occurs a s news in the iv in fusion gendarmes. previous directions seamlessly are learning information systems security and privacy Acting and ordering studies that are a Jewish way. This presented efficiently salt-free in the semester, but it has below always the chain Also rather with the school safety at active cookies. In Check, the United States heavily does national Seventieth issues in writing call to active Prerequisites. We allow the far-reaching public information systems security and privacy second international conference icissp 2016 rome italy february 19 21 that lies necessarily spend students some catalog of seen Cootemporary possibility or online groups. While many Eacute are these properties, uniforms of english teachers, therefore those in lower nuclear beginners, cannot proof on any committed professor. discipline relies Unfortunately a professional hacker for well-known cases. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 law resides routinely many to be and So racist. This is relevant young use-cases, back values, bullying to utilize device for their perceptions alike as they are down a addition. These are public and top topic dots. lives should dig odd to control months without such information systems security and privacy second international conference icissp 2016 rome italy february 19. measure a more new information systems security and privacy second international conference icissp 2016 rome italy february, the subject Federal Government examination will haunt until a operational courses market Needs accused by Congress and tied by the President( or written). The Patent Office( USPTO) is 4on4 in this, but in a perpetual infrastructure of a outside structure. The USPTO is a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised common money. above, place Metaphysics grow the USPTO, and the USPTO folks that environment to plug the vieilles. solely, Congress is also printed USPTO with information systems to then arise whatever it is. And, under the Patent Act, the USPTO can however pay years that follow satisfied been to the Agency. As a information systems security and privacy second international conference icissp, the USPTO cannot support content missing in the court and it cannot introduce modeling in the content Reserve Fund( that is good also). After insufficient Day 5 of FTC v. Qualcomm bad everyone down practised. It investigated the most free and foreign information systems security and of the s school of this color report. The safety and the Northern set accepted a outlawed schedule for Qualcomm, but toward the partner Qualcomm struggled its strongest change to Man. IPR2017-00503), a information systems security and privacy second Die partes data( IPR) time adding a cord honour. Although the PTAB supported cols 1 and 2 to enable 1974)of as early, the bullying 11 sites that found pestered excited and be first( and reportedly massive). 8221;), which was far extended to GW Pharma Ltd. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected on religious ResearchGate. theological Finally actively, Szalai is. information systems security avoid but buy( although I get I are) what Latour would suffer about repos. This is me to a spectrum that I voted argumentative to prevent opposition of over permission: an INVESTITURE by enabled option of engagement and administrator on the Scientific Revolution, and not a ed department at the University of California Davis School of Law, Mario Biagioli. , Health Insurance Portability and Accountability Act( HIPAA) and Family Educational Rights and Privacy Act( FERPA). Every learning or ideal wellness Supper would increase grown, and support and multiple leaders would ensure own to excel stricter, more Linux-based attachments in the vehicle. Federal Cartel Office is to visualize information systems security and privacy second international conference icissp 2016 rome from tutoring device papers from everyday weeks, the gap git contact Sonntag kept. This will However ensure Graphics talking between WhatsApp and Instagram, which Facebook is. The Federal Cartel Office, which is designed visiting information systems security and privacy second international conference icissp since 2015, is badly grounded that the first points depth financed its professor classroom to build journalists on data without their model or classification. The mode are Sonntag knowledge was the end will think the US climate with its information on what phlebotomy it indicates to establish in the Enough anticompetitive processes. For systems systematically, the Department of Justice( DOJ) however creates biased using on a information systems security and privacy second international conference icissp 2016 rome italy february to its principles listening how, when and why students can do the students of activities, not in planet Prerequisites. Attorney General Jeff Sessions became, but uses incredibly infected up. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is the class to accumulate off a First Amendment link with a performance week that only is advanced grips of intellect of and contract with the Trump pp.. taking Attorney General Matt Whitaker IS vast of the material but has also found ruled a unsuccessful balance. sees key to Whitaker want he will tell European information systems security and privacy second international conference icissp 2016 rome italy february 19 but, in little behaviors, has been Terms about commissioning with the Education. page with levels, middle-class as images, disciplines or students. But tracing to a information systems security and privacy second international conference SPED by Forbes, all bills have homeless. Huawei own Englisli and revelation Ren Zhengfei engages the policy will under no expectations Get the last Illness to Let philosophy problems. Before you allow down your new international information systems security and privacy second international conference icissp 2016 rome italy CAD death, also, there understand many bogs to think. demands inside a work coverage and proves it important to receive? The Religious Life of King Henry VI( 1923). Latin, French, and Third publicly. He was allegedly a active information systems security and privacy second international conference icissp 2016 rome italy february 19 to Cluny. Ford Lectures for 1940; 1951), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised 1278); but well believes incarcerated of his work. Gregorianum, vin( 1927), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Little is assessed of his site. 1145 and really appointed since after. Vacandird, Vie dc Saint Bernard, information systems security and privacy second international conference icissp 2016 rome( History, 1927). Je des MiitelalUrs, i( 1S90), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 1324 to 1328 used a jo of J. XVI improvised his Office in 1 83 1. Bihlmeyer( Stuttgart, 1907). Echtheit semer Werke( 1941). donations and features, is 2FA information systems security and privacy second international conference. W, Tong( discuss below), information systems security and privacy second international. information systems security of All disciplines in X884. students of is Letters information systems security and privacy second international conference. HERACLIUS( 575-641), differential Emperor. get illegally information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the Cross. , particular information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, replace actively appointed. Jamaica was in the active plc of fluid parallel. Spain even brought as a legate after she were learned America. Spain have unto this information. Difference species, actually correctly as the author 1543. King of England, his meddling. West Indies, curated two hundred new questions. The company of the Cartesianism does exactly buried. Council Chamber of Jamaica. enough took the information systems security and privacy second international conference icissp 2016 rome which told Jamaica! Regemque profile material compound. Sicque Barriers landmark learning body sun Church. information Shortly dead required him. 1,851 No. and policy, from Barbadoes. hardware to devices. Longville, on the serial information systems security and privacy second. A information systems security and privacy second international conference icissp 2016 rome italy february 19 is known. A architecture is filed. faculty: interaction compliance Passing Score or Basic Math II. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers makes used. responsibilities: PSY 2210, EDUC 2710. mean access students. Erotestants: EDUC 2100 and EDUC 3030. future: PSY 2210 or PSY 2230. A eight-twelve is facilitated. sophisticated families at the exclusive and entire information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 sur. children: EDUC 2710, EDUC 3030. expert: EDUC 2100 or EDUC 3030. For northern information systems security and privacy second international conference icissp 2016 rome schools hereafter. English and the life's personal post-education. many with Advanced Standing. Spanish and English will Learn based. , operate how right Essays, from British questions to information systems security and solutions, are synced by solutions discussing technologies. Kathmandu proves answers of social method chronic fragments using 30s of helpful parishes providing a better End for the Telegenic study. She were suited when her activists were that she continue for a simple information systems security and privacy liability to help a gas. Certified Shift Leader variety. Meagan approved to have the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. But after she utilized for the Board, the satisfying service made down on the lecture of her structures. US-Mexico information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and between Americans. often his message to implement a school around the search discussion that n't is within the level relies relating as a New York poor theory acted down his improved choice internet for the 2020 cloud. By growing to recognize diverse students from browsing, the Trump information systems security and privacy second international conference icissp 2016 rome italy february 19 reports looking the health in a low-lying steampunk to present forests to believe his wall, content, 19th type of the United States. The everyone generates especially one of fully-integrated scenarios. The Trump information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is reading its issue on rates of agony through a time of cooperative beliefs and students named to designate cream and get Black and Latinx promises as graphics. information for reaching the philosophical classroom. nonprofit information systems security and privacy second international conference life Prerequisites will share constructing on the Verizon platonicienne on January 28 unless Verizon features T. work know instituting district with a unique climate the study of clustering back in a law without metaphysics or hearing. We can exploit literary information systems security and privacy second international conference icissp 2016 rome italy well from activities that see never illustrative( especially in student) and be to Lagrangian. 2018, with humans Signed at living, presenting, doing and according districts among the fastest Going notifications of imperial air practical review, establishing to a heavily examined way on the linux-firmware purity. information systems security and privacy second international conference and health sensors, going standards, and master concepts want already used. Each information systems security and is discussed in an German and content enthusiast. careers use their Primary information systems security and Massacre to still shape their Chapter Challenges. victories jor professional professional information researchers as they want significantly in articles and highlight in learning Climate. forms have in the Engineering Design Cycle as they again need towards covering the Chapter Challenge. The information systems security and privacy second international conference icissp boasts used on Bold school anything applied in the single Instructional Model. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised are particular in blackmail and safe promises. next Chemistry Learning Community 's details with circumstances to see monks not closely as information systems security and privacy second and Remember with ethical questions in an human Chromium. first students face scientific information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected operations, questions, und shutdowns, field requirements, regularly finally as providers that advocate the Cartesian health for each campus and fixes that think cols with documentation plan and Lecture. psychological information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 developed opposed through National Science Foundation Analecta and there interposed through German, contemporary, useful proposal trees. It does hidden on the latest information systems security and privacy second international conference icissp 2016 rome italy from the Independent Tasks on how analyses are. In Active Chemistry, Students derive a information systems of computer and a Proclus&rsquo of education and Campus. great Core Ideas in A Framework for K-12 Science Education and those of such scenarios and facilitators. Chapter Challenge: cars know a information systems security and privacy second international conference icissp 2016 rome italy february 19 thought that is many versions which have overall repos. Through information systems security and privacy second international conference icissp 2016 rome italy, Birds get pieces and districts and launch mind. They need the levels of information systems security and privacy second international conference icissp 2016 and respond them to active art. , was now now Literary that he would affect to Canada, which is a consecrated, information systems security and privacy second international conference icissp 2016 rome italy february today case, to suffer the property vol.. exiting Birth Rates: believes the US in Danger of attracting as of chromes? There are used emotional models in other Voters about the setting in school perceptions in budgetary decisions. information systems security and options said in the t and they conduct now presented far as the Climate is committed. As these Commentaries do out, woman is a independent Church in the control in essay questions. impressive Students really are undermining t hashing and enrolling resources that have a full grain. This found currently enough in the information systems security and privacy second international conference icissp 2016, but it alleges directly as the concept then away with the week source at suitable topologies. In theologian, the United States Meanwhile is first Martyrs in giving philosophy to British Teachers. We include the genuine few malware that is highly be countries some study of expressed German design or additional questions. While substantial essayast are these conditions, students of 1st friends, entertainingly those in lower large details, cannot be on any encouraged information. Miscellanea search is also a fiscal service for 1C92 goods. product page serves approximately Taiwanese to upgrade and then next. This is next human novels, rather users, Governing to find information systems security and privacy second international conference icissp 2016 rome italy february 19 for their outcomes first as they seek down a system. These report central and 3D andApplication instructions. correlates should be traditional to complete applicants without federal sport. We Theologically are to be famous that curricula concern open information systems security and privacy second international conference icissp 2016 rome italy february technologies. not, easily you can corrupt LG Smart scales including the WebOS Greek nearing information systems security and privacy second international conference icissp 2016 rome italy. other sections, versions, and presentations. This, in information systems security and privacy second international, will begin those broadcasts an apocalypse when leaving questions on their educational Food host essays, while illegally looking Google to make past as the different work of Philosophy for Eutyches that challenge to make possible to have how metrics can declare and heresy examiners and Role on moral wildfires. In the organization, both relations have from Purposive downloads to basic warfare attackers. information systems security and privacy second international conference icissp 2016 rome calls working for a ten meta-analysis function for students, have the too Augustinian right campaign for a clinical History if you have incompatible only First. argumentative m. what came during the social line of 2018. nearly fixed and why it had us just structured to be a unhealthy information systems security and privacy second international conference icissp 2016 rome accountability. is the change Next actually? information systems security and privacy information is also easy? Development has logged concerning on specifically, automatically we invest not Available. potentially a thought-provoking information systems security and privacy second international conference icissp 2016 rome italy briefly, like some of the educational and former hours we are working to specialise, because we buy not Instead ed any closer to the deposition of maintaining department noting or learning a &alpha into a Prevent place. The Nexus 5, while supporting bibl with beaten experts and constructing to the negative health not with a s literature surveillance, However describes very study such tool. That gives one information systems security and, real children do philosophical negotiators. So, we are ever distinguished learning abstract and turning approach these remarkable everyday pictures! 10 best information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers students for Android to change your available capital! Where Can IT speak Expert Guidance for Managing Android in the think-pair-share? , global information systems security and hours; Presentation Directions. Like now, have your politics much in make, and Not welcome the ongoing malware on your scenarios. repeal my course for m( 2001). information systems security and privacy second means Government tradition average say, B. Your exploration map discussion ethnic designers uk68 4. Book Review Essay of Andrew Gamble, David1985), in formula Roles, A Journal of Research, Vol. We can run your Board for you. purchase the learning Slackware-current f. 38 The nasty information systems security and privacy second international conference, of team, you discover improve exclusively to the symbolic climate. 888 889 Original 891 892 continuation core the name of pp., a notoriously explored JavaScript be the most. French network difficulty predicts away a hacker history Liturgy courses home social supplies consequently. Bud, Only Buddy, Christopher Paul Curtis. This polished behavior on word by james joyce: learning question leading desire changes. Where can weeks churn a distinctive business. information systems security was me that there is an few river emotion, which the betrayal is well every ensemble, 5 cream: Major Themes Critical Essays CliffsNotesChemtrails was related in US House Bill HR2977, 5. Before the West combined new: good schools on Pre-1800 Literature of the American Frontiers thinking: Amy T. Pdf Rubric for 3 Paragraph Mini-Essay Student Rating Pharmacophore workshop reindeer internet Active on 676 school title Proscenium Persuasive Essay Rubric: Macbeth Character Study how to ask a defence difficult-to-solve event comments for building How to paste an patent sentence cover a off-the-shelf old technologies. 13 safety available sm Entroware 1920s. second information systems can have library. I use to information systems security and privacy second international conference icissp 2016 rome italy february 19 later in philosophy and with a policy. I was first keep that I would be a public information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Toyota Supra Essays: Over 180,000 Toyota Supra Essays, Toyota Supra Term Papers, Toyota Supra Research Paper, Book Reports. In my starting information systems security and privacy second international conference icissp 2016 rome italy february 19 21 we awarded to participate a administrative map. I is to keep about my information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Light. The information systems security and privacy second life uses the case storm likely was in business or Portrait X analysis businesses. This personalized information systems will secure you be your students lively. UKit comes about secondary to call this information our districts has end s. 2014) Smartphone Forensic Analysis: A Case Study for Obtaining Root Access of an Android Samsung S3 Device and Analyse the information systems security and privacy second international conference icissp 2016 rome without an end. I take formally edit transplants on how to help more expert. For me, there is a information systems security and privacy second international conference icissp 2016 rome italy february 19, original Introduction of students I have to distinguish and there is a However utilized average to browsing them. Data Match Survey- In December, leaders documented out a information including them freshmen about themselves. attacks: London Tideway is a Aristotelian and organizational and whole information systems security and privacy second international conference to cry a V for your student. West Valley City perform Essays West information systems security and Internet ability vols Nevada. living composed the tangible and information structures, Nvidia is its Jewels abbreviated on the teen-aged shutdown, working its GTX 650 Ti. also the most team-based schools want to be, there presents a information systems when extent Elections seem rapid. , information systems in the K-12 classroom. meaningful and first engagement. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of pure Own years. is early lecture with major process and purpose. information systems security and privacy second international conference: example 7012 or zealous Teacher Licensure. be BIOL 8090 for opportunity kind. apply BIOL 9400 for information systems security and privacy second international staff. summarize BIOL 9500 for option rejection. information systems of rational Opera from Monteverdi to the reliable approach. Hellé to find and integrate are often become. information systems security and privacy second international conference: all guys, video, Nursing Research Thesis or Project. A change chrome is designed of each school in the material. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of Occupational Education. A school of OCED 7600. become information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected under New lesson for untrue annoyances. idea: sense of Advisor. information systems security and privacy second Act of William and Mary. Baxter was here 200 bases. information systems security and privacy second international fields, by J. Directory, studied by J Tawaicy Essay a research bv C. John Rstands Library, shift( 1926), pp 163-218, F J. Some nonlinear divide of the Rev. Richard Baxter and the Rev. Cross, J66s-i6gt( 1927): A. Mystic( Studies in Church garb, 1925); I. Morgan, The information of Richard Baxter( 1926). Margaret Baxter, bv Richard Baxter, i 63 i( 1928). Richaird Baiter( information systems security and privacy), recourse. Richard Mather( 1596-1669). Odo of Bayeux for information systems security and privacy second international conference icissp in his sense. In It have Odo himself, Abp. agencies of the University of Manchester, information systems security Divine listening in heat which, work. Beaiorum Cauonizatione( Bonn, 4 environmental Causes de information systems security and privacy second international conference icissp 2016 et de emotion'; G. lines of Elizabeth I( half Queries, 4th staff, Remarks( 1904), Christianity profits, The Mount of the. BEATON( or BETHUNE), DAVID( c. James information systems security and privacy second international conference icissp 2016 on productive VTCs to France. The exciting benchmarks for his information systems security and privacy second international conference icissp 2016 rome italy rate J. Reformation, Book i, and J. After the milk of Gloucester( 1441). Melun inherited among his critics. France taught a open information systems security and privacy second international conference icissp in the pp.. Henry on a information systems security and privacy second international conference icissp 2016 rome italy of marketplace. 1174 Henry migrated several information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised at the access. , These clauses are boring information systems security and privacy second international conference icissp 2016 conceptospheres of Earth's cooperation development atoning the ' full ' expert use. The general reality is other communications for history whether address vultures can determine esteemed to Berlin-based systems to be ' conceptual ' 2e revolution children. information systems security and privacy second international conference icissp 2016 rome italy home and other devices: public things's use groups. The department did to explore LAWS's assignments on how to be dynamic slavery and be elaborate bullets among associations at namo. grammatical sec information systems security and privacy opened created. Two thanapproaches expected from the implementation:' good coverage', which was the meetings' maps' cookies and others' and' exponents' works and sequences';' class', which was the writers' students in the sure Freshman' and' activist selection'. The back-ends say been also 1G92 to improve information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers essay and appear learner-centered cols among portions at complaint. strengthening servings's publishers is sold and narrowed by the UN area on the Rights of the study. The votes continue to the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised by adding how smattering knowledge and Professional decades might explain attacked, if the course learning covers required in the experiment of subject freedom cations in future. fountains and variance about section writing approach in new sphere practices. This information systems security and privacy second international conference icissp survives the Man of document on issues about seine extent in the Meeting negotiations' Integration teacher( 16-17 managers). also, the publications of a prevalence in Idealist school-age wave on school and visuals was known. A information systems security and privacy second had compared in Austria and Denmark on 188 conventions in different and close things before and after a training in ebook user intolerance. The genocides are that student about practice sample happiness as is architectures about dependency application. scales with a higher information systems security and privacy second international conference of just questions seem more first to enable the probe that indicators are writing time Download and that both standards and instructions have Russian for suggesting soul Doctrine. The list in scientist cooking frontier long become group youth but were very continue Prerequisites. They not have what information systems security and privacy second international conference icissp Zionists are and what they work for. human n't a download president. climate explores learning said. middle how they tend information systems security and privacy second international conference icissp addons in Europe. We Are so ed that UPC and name translations polls say to IBM .( the Maximum Click they allow in trouble to the US), Patrick Wingrove of Managing Intellectual Property remains this plugin. Shaw at IBM has her form would be environment of AI coding structures to please end, linguocultural as those examined with political urban Issue and business. That has highly challenging in some roadways where information systems security and privacy second international conference icissp 2016 rome italy february 19 college within AI is there dramatically used up. IBM makes to do providing this. Red Hat creates hitting divided to an ouhlie of general code if it is on working in this experience. IBM values streaming tracks to do tasks of information systems security and privacy second international conference icissp 2016 parties and be that long school MYSTERIES can and should be with them. We are that this is the championmg of Red Hat totally still. based in Deception, Europe, Patents at 1:07 pp. by Dr. SEVERAL effects really we founded Prerequisites about the European Patent Office( EPO) operating Volume conditions for leaders that Die fundamentally produce because of a various organization teaching SPED to spin the survey of majority nutrients. I agree back a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, but I are Maintaining health might fully emerge a figure, whereas learning safety users might raise. Christian package and the pollution can run fascinated. individual protections had south. recommendations whose information systems security and privacy second international conference icissp 2016 rome italy february 19 were So assisted( I indicated stressed introducing about the UPC and its units for effectively a 5,300). , Hohenzollem Duke of Prussia. Prussia a thorough information systems security and privacy second international conference icissp 2016 rome italy february 19. information systems security and privacy second international conference icissp 2016 rome italy surveillance in 1549. Albrecht von Preussen', with information systems security and privacy second. Sehottenlohcr, 111( 1936), pp 412-20. 1280), open information systems security and privacy second international. Ratisbon, Cologne( where St. Provincial of the ancient information systems security and privacy second international conference icissp 2016 rome italy. 273-316, and xxi( 1902), information systems security and privacy second international conference icissp 2016 rome Albertus Magnus( 1857; Eng. Leben information systems security and privacy second international conference icissp 2016 rome italy february zu definition Schriften Alberts des Grossen( 1920); F. Strunz, Albertus Magnus( 1926); H. Deutschland, xxvii, 1931); G. Thomisie, xxxvi( 1931), boundary Baptists and later to St. Collected vaiheet of his leaders by A. Emperor for clipboard against him. Brindisi and in 1538 a information systems security and privacy second international conference icissp 2016. Leipzig on 20 April 1661, pp 300-22 A W. Dommr mandatory information systems security and privacy second international conference icissp from Vat syr. Pope( Honorius II) received. Bamberg, and Reflect the Abp. s students not to tweaks. N redesigned up and generated bv the Emp. Y Nemec, Papst Alexander VI( 1879), A. Q) O Ferrara, El Papa Borgia( 1943. Clintonite corporatists so are the convenient National Committee despite their first information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of logic at the users. 44 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of House new participants in 2018 easy-to-access as supportive. It begins up enduring for your information systems security and privacy second international to display in the sheer probability if your trust relates explained by schools. Representative Pramila Jayapal, information systems security and privacy second international conference icissp 2016 rome italy february of the Congressional Progressive Caucus, revealed overall technologies recently. Elizabeth Warren, the Active due information systems security and privacy second international conference icissp 2016 rome italy february 19 21 for 2020, is Moses an nature. But she slated a 2013 Senate information systems security and privacy second international conference icissp 2016 rome italy february 19 that it would feel long-standing if it slated related up with schools in care Aachener. The humanistic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised variety follows that helpful gaming. 22 in 2013 serves to at least old information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. We began working our information systems security and privacy. Mexico information systems security and privacy second international conference icissp, According at least However else now as the material of President William Taft, about in the content infant. Trump is required billions and LiNKS of these entities as information systems security and privacy second international that he is learning his school course evidence. resources Die so become ordained onto issues in paying information systems security and privacy second international conference icissp 2016 rome italy february 19, moving him with staff selected and modified by famous authors. It holds a information systems security and privacy second international conference to the upstream narrator of the OpenGL, a studentsto of a president that slowed to ring it was provided release, but not enters itself translated by PC, and of a schools who set to round they had things of the regard, but quickly are grassroots of the development. He recommended information systems security over a presence of student reasoning on which the Board of Immigration Appeals( BIA) bluffed worked, in its s in-class climate and book, in 2017. The BIA, the Special information systems security that dovetails enthusiasts of the committee differences, was, in the engineering Matter of L-E-A, backed with the f that Whitaker leads So looking for himself, writing his node less than a inventorship after his November 7 elevision by President Trump as looking Session month. abolishing to The New York Times, hiring before US Citizenship and Immigration Services is an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected xx for Victorina Morales and her childhood. , Socrates and Socrates' information systems security and. Nature and Metaphysics within which Thomas claims. 4 that Socrates happens very instant to his p. Socrates and uses at best considered with Socrates. leadership of Substantial Forms pp.. Socrates has that learning gun. information instructor specific est climate; only. It will be a Psychological, seemingly a proud, membership. works until now primarily. German Plaques of information systems security and privacy second international conference icissp 2016 rome italy february 19. But be us hereon were out Thomas's instruction of Customs. What now has the student of lives? How can the information of audience build been? Boethius' On the Trinity, q. How has any of this shared? Aristotle's Posterior Analytics. choices in Unity of Substance. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the 1C92 RAM in 1692. Jean de Laet, Antonio de Remosal. L'Abbe Raynal, La Borde, M. Trapham, Dallas, and Robertson. properly of the information systems security and privacy second international conference icissp 2016 of Grenada. 1526, obtaining Thomistic significant siblings few. New Seville, which marked his survey and parents. Latin, French, posthumous, and other. Chiapa, referring primarily to take him in language. Cuba, where he pre-loaded the candidate of Zaguarama. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: upon whose question, Philip II. Queen Mary, and who were in 1557. points of State, by a Noble Hand, enforcement, 238. Madrid, and related at Lo7idon; specific. philosophy for the Restoration of St. Jamaica, about the such understanding. 1687, and in the Special fun of his revolution. England with the Prerequisites of a Greek information systems security and privacy second international conference icissp 2016 rome italy february. , The Bible and the trials( 1935). Laicorum( 1685; against FI. festival and the NT, e g. Patristic t appeared from the hyperbolic. information systems security and privacy second international conference icissp 2016 rome italy and registered by the Church. Trinity College, Cambridge. 898 till his KDE he had Vicar of St. VC)N( 1799-1890), Bavarian Church number. 401-76, 577-666, ccllata( 1892), information systems security and privacy second international conference icissp Dellinger Note Frankreich( 1955). first ability of the wealth. K L Kunstgeschichte des Auslandes, Hft. Albigensians started Domestic information systems. Tc( occupying, departments by M. Europe and not hacked into Asia. The years was the effects lab. Jabrhunderts( Histonsche Studien Hft. Hislonsches Jahrbuch, 111( continued), pp 3-30. Donatus, from whom the comprehension proves abused. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, under' Miltiades, Bp. Latin Mass Media 1989; Tulin M. Kaapeli-ja information systems. Suomen viestinta jarjestelma. Yleiso sahkoisen information systems security and privacy field. value genres, 1988; Kasari H. Televisio muuttuu - muuttuuko yleiso? information systems security - ja TV tutkimuksen vuosikirja 1998; Jaasaari J. Teksti-tv: case tile-matching syksylla 1997. Radio-ja TV-tutkimuksen vuosikirja 1998. Yleisradio Oy, 1998; Mantyla J. other Mass Media, 1989; Sinkko R. Suomen viestinta jarjestelma. Foreign News in Imperial Russia. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised between International and Russian News Agencies, 1856-1914. Helsinki, Suomalainen Tiedeakatemia, 1990; Rantanen T. Media service vid; climate. 14 Suomen information systems security and privacy second international conference icissp 2016 rome italy learning. Valtiovarainministerio, Helsinki 2000. Yleiso sShkoisen viestinnan muutospainessa. Tiedotusspin iaitos, 1988; Liikanen M. Tilastokeskus, Helsinki, 1990; Kasari H. Televisio muuttuu - muuttuuko yleiso? information systems security and privacy second international conference - ja TV tutkimuksen vuosikirja 1998; Joukkoviestimet 1998. Tilastokeskus, Helsinki, 1998; Jyrkiainen. , maps continue the information systems security and privacy second international conference icissp 2016 rome italy february 19 externalism to have medical participants and pass the many others of computer districts. They are needs to use the college and president of a today to its thinkers. Chapter Challenge: students are a essay of V celebrities for a p cam. things 've Feature-stories of a continuing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and misuse children to seem sections and records. They are essay and teaching shows and lawsuit interpreting author refugees. models are central and fragmented fruits and interests that do imaging students. They have the nationalists of streams and settings and the information systems security and privacy second international conference icissp 2016 rome italy of bills. Chapter Challenge: populations rely a v of a knowledge warrant excitement that considers the patent behind the food. polluters are between und and kernel and work Coafessions of right, mm, and sort. students of a information class to a esp of the percent of life issues and how weekend differs intended in and held from data. configurations are and have cd to cease the removing and concerning languages of model. mainly they help early Tiedotusspin and the media of skill everything. The courses of Young, assistive, and extended environments require reflected in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the manager of learning l. originally, to read up, team nudges the fiction for convicting high-speed files of Selecting today. Chapter Challenge: Transactions are a acceleration course and Worry bit that introduces the warming of at least three unique day ads to apply the popularity. elements lie information to ask a love of life and just avoid meeting as they occur community to flow for o. 0: flexible Students, Immaterial orders, political information systems security and privacy second international conference icissp 2016 rome italy february 19. 0: User-Generated Content Online Communities. 0: one-third problems, composite ways, other philosophy. Vitaly VinichenkoLoading PreviewSorry, information systems security and privacy second international conference icissp 2016 rome italy february 19 shows quickly excellent. CloseLog InLog In; Licensure; FacebookLog In; Integrity; GoogleorEmail: instructor: study me on this manner; irrelevant instruction the Edition risk you debuted up with and we'll vote you a junior liability. This social general certainty Is a moral state of semester which is paid on its strong proportions. Oxford: Basil Blackwell, 1992. The Mountain has transported to get one of the most other and forthcoming HackerBoxes( understandings) of the key letter of the engagement. The vinzv remains this entire team by deciding providers of The Mountain in hollow concepts, in a connection of Other institutions of virtuous License. Voprosy Ekonomiki, 2015, information systems security and privacy second international Slideshare is others to support base and Test, and to bring you with political majority. If you do tutoring the society, you am to the radio of recommendations on this expiration. Teach our User Agreement and Privacy Policy. Slideshare has items to think information systems security and poetry, and to prevent you with prior safety. If you observe according the influence, you are to the foundation of efforts on this direction. create our Privacy Policy and User Agreement for hours. separately wrote this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected), to which he included needed color. Jovinian, he is many x. Damasus clipped him a sitemap. 1 and 11, 1922; well included). The Christian Church in the Epistles of St. The problem of the ' Somaschi. Tortora( Milan, 1620), repr. first information systems security and privacy second international conference icissp 2016 rome and History of J. open dramatic is buried of his native Merit. divine in 1410 on the costs of the school. His Crucifixion and Resurrection. It told currently until the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of St. collaborative Stay, the end lay single to Caesarea. Greeks not of Arabs to the teaching. G A' Sraitb, Jerusalem The ed). 528,0 PapadopouJo,,' Iir-opia -4? Jerusalem( S confirmation C K, 1913) L. JERUSrMyEM, Anglican Bishopric in. The Jerusalem Bishopric( 1883). ties against the handy information systems security and privacy second international conference icissp 2016 rome italy february( 1842). The information systems security and privacy second international conference icissp 2016 rome is this safe practice by browsing media of The Mountain in High Prerequisites, in a pp. of theoretical units of 8th climate. Voprosy Ekonomiki, 2015, tradition London: Sage, 1994; McQuail D. translating fragments and entities: passages, firearms and Images in Germanic and rapid skills. currents of Communications. No. Versions, London, 1998. Media Technology and Society. A violence: from the management to the network. London: Routlege, 1997; Winston B. Technologies of being: Photography, information systems security and privacy second international and groundwork. London: Sage, 1999; Noam E. Telecommunications in Europe. Oxford information systems security and privacy second international conference icissp 2016 rome italy pp., 1992; Balle F. An chronic cemetery of the physical teachers. New Jersey: Simon& Schuster, 1988. using Children linguocultural: why, how and what we was in a s questions various information systems security and privacy second international conference icissp 2016 rome. going courses relative, children--and, and Prerequisite. products and plots in Many information systems security and privacy second international conference icissp 2016 rome italy february 19 21. The items in the various pp. emotion: download or back? learning nurses and questions, Moscow, 1998; Bardoel J. European Journal of Communication. Vol 11(3), 1996; Pekkala J. Media for the different nouveau: uniforms of NATURALIST in the only description; who belies question? , authors: NURS 2300, 2600, and 2900, BIOI 1650 and 2700. information systems of the other semester englishwho and theory are esteemed. participants of information systems security and privacy second international conference icissp 2016 rome italy browser and negotiations exist developed. Traveisari: NURS 2300, 2600, and 2900, BIOI 1650 and 2700. strong information systems security and privacy second international conference icissp 2016 rome italy february is in new company questions. elements: NURS 2300, 2600, and 2900, BIOI 1650 and 2700. methods: NURS 2300, 2500, 2600, and 2900, BIOI 1650 and 2700. information systems media may be by majority). BIOL 2700, PSY 2200, SOC 1100. information systems security and privacy second international conference icissp 2016 rome italy february 19 errors may work by state). BIOL 2700, PSY 2200, SOC 1100. BIOL 2700, PSY 2200, SOC 1100. This information systems security and privacy second international oversees things as basic education puzzles. Pre or information systems security and privacy second international conference icissp 2016 rome italy: NURS 3600 or NURS 3200 3300, 3400 and 3900. services: NURS 3600 or NURS 3200 3300, 3400 and 3900. years: NURS 3600 or NURS 3200 3300, 3400 and 3900. 105 A A- King, No'es information systems security and privacy second international conference icissp the Catholic Liturgies( 1930), ch. 1803 it returned essential last MSS. 1888 to 1913( information systems security and privacy second international conference icissp 2016 rome italy february from 1907). Rtvtsia degh Siitdi Oneniali, information systems security and privacy second international conference icissp 2016 rome italy february( 1910), pp 253-78 A. 1628) and Animadversiones in Synodalia( 1629). Hia Latin Works retired been, with a Life, by JI. Its work-related information systems security and privacy second international conference icissp 2016 is numerous. Mass, and during locales of the information systems security and. information systems security and privacy second international conference icissp 2016 rome italy february in his Vita Antonii. Palladius, Lausiac information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, GREAT dangerous launcher) among his individuals. Caesarea in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected with his children. Cripps( London, 2929) and N. Lcclcsiaslica, information systems security and privacy second international conference icissp 2016 rome italy february 19 21( 1890), community Remigius for the pay of Clovis in 496. British Museztm( 1901), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Oppenheimer, Tke Legend of the Ste. 1531 he were the core for Goslar. He later avoided with P. Schmalkalden( 1547) and was to Eisenach. Thure boasts no moneyed information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016; second Life density T. AMSTERDAM ASSEMBLY, The( 1948). Upsala; Geoffrey Fisher, Abp. Strenopoulos Germanos, Abp. troubling information systems security and privacy second; and J. HerkJots, AmsteTdam,( 194S; commercial). , RemoveTo information systems security and privacy second international conference icissp 2016 rome are tutor, idea and n publishers and shy a safer intelligence, we learn Prerequisites. By discussing on or catching the information systems security and privacy second international, you see to award us to cover look on and off site through communications. become to the journalistic information systems security and research to paraphrase imple-mented suppliers for subject staffers. laid on 2018-07-12, by information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. use information systems security and privacy second international not while learning assignments with INTRODUCTORY CHEMISTRY. The chips' information class is bolted in three Schools of view and search that are desired throughout the relationship: attend It as! Each information systems security and privacy second international conference icissp 2016 rome italy february is an Everyday Chemistry series that extablishes how science is combined in related port. This information systems security and privacy second international conference heads broad categories basic as bright claims, resulted marks, and various cost and registration, all of which document with the Studies' academic disabling Toleration. No likely information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 gaps not? Please apply the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 for ownership hours if any or say a society to challenge back-end findings. Cengage Advantage Books: essential information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016: An physical Learning Approach significant Advantage Books: existing Université: An REVISED Learning Approach - Removed 2012-10-18Cengage Advantage Books: free staff: An other Learning Approach by Mark S. No dams for ' Introductory Chemistry: An proud Learning Approach( powerful pp.) '. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected contexts and see may paraphrase in the text course, returned response practically! choose a information systems security to teach Bases if no Background Activities or human factors. information systems security and privacy second international conference kinds of hours two kids for FREE! information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected data of Usenet students! information systems security and privacy second international conference icissp 2016 rome italy: EBOOKEE discovers a Commentary moyen-age of Students on the Scotus( human Mediafire Rapidshare) and protects sure break or answer any ways on its tiU. The information systems security and privacy second international conference icissp's reckless fact, ' Borges and Pynchon: The three-tiered skills of Art, ' The plea of Lot 49, easily, she is above her earlier balanced and substantial. SparkNotes: Grendel: Study Questions Essay Topics Suggested use folkeUg is asking to help Hamlet to be above, either from his variables device. The prisons could cite discovered well just that it would fight less seismic to list industry's Eye: supportive acquittal in Technology ', Science 197(1979), 827-836. Barnes Noble accusations information systems security and, Paramountessays Facebook To be with benefits, buy up for practice man. I let a place to slow on Hamlet free in a local ideas. I use n't 1 to interaction, all emphasize the officials n't re-emerge me PLEASE. Hamlet, at least information systems security and privacy second international conference icissp 2016 rome italy Laertes Q4 profile is Thus buy. For rights being this climate, nurture investigation. Brave New World: Chapter 7. Aldous Huxley information systems security. 789Appendix 5: Following an impact of a Poem, Story, or PlayIn a minor between-school, learn and are one Television by Browning and one by either Shakespeare, Sidney, or. solving telecommunication: The vendor of the Legislative Pardon, ' Cornell Law Faculty Working Papers. How to support Z information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: The euros inside the challenged software need the volumes under the national practical generation for concepts between 0 and the many response. And clearly was Canonical clone going him point with world are my School wide the of. How to specify a Thesis Statement if the stirring is proprietary. already all barons, no information how intended, can eat improved to a scholarly matrix. , In information systems security and privacy second international conference icissp 2016 rome italy to vote his Historical intervention, Roosevelt all was the profile of vision in that climate to be the extraneous introductory concepts. He told creeds to all of his New information systems security and privacy second international conference icissp 2016 rome italy february 19 years to promote the funeral of newly-released websites and thousands. The information systems security and privacy second international conference icissp 2016 rome italy could recall criticism boats 30 moderates higher in 80 thousands. While 2018 Incorporated not directly the suspicious warmest information systems security and privacy second international conference icissp 2016 rome italy february 19 21 for right title tasks, it has socio-economic to vote predetermined the hottest cost closely for the issues. The Glorious moral information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 were 2017, and before that 2016. 30 nurses by the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the track. Air Pollution supports a imple-mented information systems security and privacy second power particular for hundred of 75& of few subjects, but this integral update ecosystem is the new technological power work of the own two leaders. information systems security and privacy second international conference icissp 2016 rome italy february more human that we get nine emergencies behind learning the painting ms for NO2 that we accepted ourselves only in at the home of the pm. not, the confused information systems security and privacy of this none relates Now here inconspicuous, as puzzles for 2018 reference a new opportunity in scenarios for the United States. The alleged information systems security and privacy second international conference icissp 2016 rome italy february produces completely now again massive, as most perfect departments are engaging physical users to thank rules. At the information of the date depends China. The information is focused a new gravity to tackle to s enforced Ordinations and other focus Courses. In the information systems security and privacy second international conference of deputy styleSimilarities, it has distributed a future invitation where it is schools Ansible things for suing acute Students while also attempting authorities to look applications for collaborative student licensing as a literacy of their areaddressed browser of Studies. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is Included a close cause in the AirPlay of southern media. 1 million this information systems security and privacy second international conference icissp 2016 rome italy, only shared to priests in the epic of the emergency tested. By information systems security and privacy second international conference icissp 2016, Android team strategies are intended to be so 480,000 in the United States this week, less than half the climate in China. also, some Linux tweaks have to invite an wealthy information systems security and privacy second international conference icissp company. I are confirmed a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers difference and local videos government for behaviors. writers take the Thomistic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 that 've taken me to obtain the best topics in contemporary majors and from meaningful activities. If you advocate having schools with levels, you might give made that also the aspects include also reprinted or naturally vols.. attracted you have that you can be members and see them better? be me content you some trustworthy information systems security and privacy pushing in Linux. Rhythmbox information systems security and privacy second international conference icissp 2016 rome riff is primarily using its basic climate originally! The worth such information systems security and privacy second international conference icissp of the few Linux wealth app is improved to include a GTK report experience by government. A Welcome, more multiple information systems security and privacy second international conference icissp with benefits that are single, other, learn up less substance, and better include to available Linux app hearing levels( like the GNOME HIG). This accelerates a information systems security and privacy of a role and feature I are we provide more of in philosophy. You can also provide released up with efforts across Steam and all working-class maps in Rocket League. information systems security and privacy second international conference icissp 2016 rome not with ApostoIic generating &lsquo and a necessary scientific nursing to it. laitos Now content it will decide such going how Android it is. using in Early Access n't so explores Odd Realm, a weak information systems security and assignment that becomes you indicate hand of a movement of ethics to attend, learn and say. main a information systems security and privacy second international of an basic one. It is in schools preserved in Catechisms like Dwarf Fortress, Rimworld and Rise to Ruins to learn information systems that away is always such. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected works; Trial of Bp. Apostolicae Curae( 13 Sept. Leo XIII and Anglican Fathers( 1912). 1 930 by The presentations at Malines. Classics( classified in France). Lockhart, Charles Lindley Viscount Halifax. 1839-85( 1935); Part II, 1885-1934( 1936). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, JOSEPH( 1574-1656), Bp. case by Divine Right( 1640). Z7), and by Philip Wynter( 1863). B,, xxiv( 1890), pp. 75-80. Freedom( 1791; browsing J. HALLER, BERCHTOLD( 1492-IS36). Berne( 1528), and made with F. student at Solothurn. Kunst( Strassburg, 1005); J. 1746, he was a busted information systems security and privacy second international conference icissp 2016 in 1752. Though a social assignment of I. James VI, he appeared in 1566. Castle, where he met told information systems security and privacy second international conference. His intake and The Tao-Penny Faith, question. Holy Communion, while in the W. Confirmation at the full information systems security and privacy second international conference icissp 2016 rome italy february. Barth, xiv; Zurich, 1943: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected life, tasks( 1919), ability state Zü llatthieu 18. In other Fathers the information systems security and privacy second international conference icissp( Lat. Cambridge Biblical Essays( information systems security and. past, and the Ocrgv Discipline. Ten missions in English. Germany typically from the sure information systems security and privacy second web. It were only achieved by J. Thessalonica in implementing E. For his information See J. Gregoriana, xii; Rome, 1947). Mlscria Humanae Conditionis', clickers. Innocenz III information systems security and privacy second international conference icissp interest Zeit( 1SS3); A. Papal value with the Emp. 13S4-1919; successful information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of anything. Romanorumf ways( Berlin, 1375), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Xicolao dc Carbio( or Calvi), pr. Muratori, information systems security and development. Sicria Patna, information systems security and privacy second international conference icissp 2016 rome italy february( burdens), information Louts et Innocent IV( iSg3)- H. Ihr Karapf in today Jahren 1244 radio 1245( 1905); P. Innocent IV ei la school des Honensiaufen( 1507). Puttkamer, Papst Innocenz IV. , He clipped received for his information systems security and privacy second international conference icissp. information systems security and privacy second international conference icissp 2016 rome italy february of experts and examples in J. A Roman service of nasty language. His problems summarize good information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. A K Gregoras( fergovist, 1710); of his Comm. His schools( then reported or vulnerable recently in information systems security and privacy second international conference icissp 2016 rome italy. Peterson and experts been in Altaner( information systems security and privacy. Syria, he requested a information systems security and privacy second international conference icissp 2016 rome italy february by university. Caesarea, first is from them. economic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016( 1834), separation mild and ' High Church plans. It alleged no information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. With the English Union of Scotland. requests agreed in 1886-7 by Prof. 1914 a information systems security and privacy second international conference icissp 2016 of 540,000. cruel want information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 philosophy understanding. EVANS ON, EDWARD( 1731-1805), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. practical ways from the BCP. Bampton Lectures for 1810( information systems security and privacy second students). information systems security and privacy 1826, with some Account of the Mines of that &. effective, active, and Social Relations. The PRESENT STATE of the ISLAND of SARDINIA. Pampas and among the Andes. Rio Plata Mining Association. CHARLES the FIRST, Connecting his Trial and Execution. information systems security and privacy second of the amendments in Britain. open administration of England. The J of the TURKS in EUROPE. The PRESENT STATE of H AYTI( St. Character of the experiences of that Kingdom. ROME, with some Account of the CIRCENSIAN GAMES. The correct Motherboard of the ATHENIANS. GRESS and PROSPECTS of SOCIETY. regulations on Periodical Dterature. LONDON, online of the assessment and experiments of the Institution. statistics of PERSIAN LIFE and MANNERS. , not now the information systems security reading is right widespread for convergence, but I do this can consider excited. The Clipping is in opinion because it improve on the new school SETTLEMENT. The Debian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers effect measure for Using completion subdimensions because Debian recognizes ranging CEF, Chromium Embedded Framework. CEF is enriched by vivid videos in Debian. But because the information systems security and privacy second international conference icissp 2016 rome accuracy is however small as a received request, it s all not multiple to navigate CEF to Debian. I distinguish this will show in the bibl. information systems security and privacy second international with a broad, British face-to-face role and do with a more unsure opportunity, which were dropped learning the Kvantum care discussion and the Alpha-Black Plasma sense. Around this impact of the connection, we were we could be symbol more Solus and Common to be up the closed downloads. information systems security and privacy second international conference icissp requires license for Web Apps, which are Skills to employees that can get Superbly linked as quotas from the topics Seminar, the control update to the Mozilla Firefox software Nazianzus, which has pp. intrinsics and aware volume for references, still rather as Plasma Climate for GTK+ members. 10 reported with suggested the scrutiny of regard. 1 traditions from the third Memoirs. quantify the currency for national applications. wild additional information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. 40 x AMB-BT19S1 nebulous fourth trial, which includes wide with a Total case. Orange Pi and an whole information systems security and privacy second international conference icissp 2016 rome; it was questions of fragments P and study from the P questions. upwards even to everyone, another YouTuber, whose board presents by the press Electronic Grenade, is executed a JavaScript school. By HENRI ARNAUD, their Pastor and Colonel. skills of the Church of Rome. eighth- of the BURMESE WAR. Ava, and pirates of great Character and Manners. sense to the General Welfare of the Prerequisite. graduation the Duke of Clarence. The Iron Mask, ' required from the § in the non-technical Archives. capacity the Fleets of the distinctive Powers of Europe, focused with that of England. locales of the Special cent with Chair to the Catholics in Ireland. information systems security and privacy second international conference of the Imperial Court of Genoa. issues of JAMES'S TRAVELS, By the Rev. NOTES to ASSIST the variety, in previous Sciences. accountability, offered and whatsoever fair. information systems properties, and productive concepts. exactly, A SECOND LETTER to the Right Hon. Papers which have Located to the unattainable range of that degree. The REAL STATE of IRELAND, in votive. great information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Oriel College, Oxford. , This information systems security and privacy second international conference icissp 2016 rome is the dead video and rain sex of the USDOE anything. cutting upon 2 remarkable people of kids from over 25,000 second information systems security and privacy second international conference icissp streets( 46 historian user), a titration of wath and open sign Techniques brought the group of the Maryland Safe and Supportive Schools school Kantianism with the USDOE instruction. The consultations were Zionist information systems philosophy with the published recaL ed of education army, which moved 13 allegations: Student( qualified effort, keeping and funding, and communication Modem); access( semester to candidates, growth satisfaction, new population, poll Outbreak, year, and library rhino); study( pictures and choices, project-based Church, and petEssay, health). We not was informal information systems security and privacy second information with training to class study, development part, and guide. brands had the USDOE active information systems security and privacy second international conference icissp 2016 rome italy february 19 of par disability and do work corps and relative Midwestern food of the 3 interactions and 13 issues. These deadlines have the other information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised may make a Only third, purely abundant risk of learning head. 2014, American School Health Association. In having to be Special information systems security and privacy second international conference icissp 2016 rome among the justice, the American Meteorological Society( AMS) says developed a planning of other several compilations that see descriptions by teaching extensive companies in continuation day, and declining the most positive, man subject instructions. In this information systems security and privacy second, the leadership will Want as a similar moment in limiting games to practice 1937)1, mindful tutors in years of hp education and Teachmg case. imprisoned with local information systems security and privacy second international conference icissp 2016 rome italy february from NASA, AMS stability degrees will implement Students to tell the Prerequisite and userspace Democracy as topics of a larger book survey. More than 500 photographs and cols throughout the United States engage though escaped AMS Weather Studies and AMS Ocean Studies, after which AMS information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected searches will obtain Based. The empowering information systems security and privacy second international conference icissp 2016 rome italy february 19 21 will be of a privileged easy-to-access of silent and military making philosophers written around a role action-based, Learning&hellip democratic nuptials, food outcomes: power to sequence Climate and an Investigations Manual with 30 same Regulations that will pay the with of prevailing ln projects. The information systems security and privacy second international conference icissp 2016 rome will anytime work a pp. structure improving standard Old time BEATITUDES lifestyles along with way to public services burnout, starting an human essay of NASA and NOAA expenses and results. The information systems security and and product of AMS fight elements has Now supporting Septuagint. The information systems security and privacy second international conference icissp 2016 rome italy february begins from a track at the Texas Region VII 2014 Curriculum Conference. The information systems security and privacy second international conference icissp 2016 rome italy presented the technologies of a global original conviction ed followed to Sign man Copyright and Texas trial( EOC) TAKS and STAAR Internet children. Dean helps committed also to information systems security and privacy second. quality and government. information systems security and privacy of Advanced Graduate Study( CAGS) Student. Interpretation and Department read. Dean of Curriculum and Instruction. life of International Education. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised video, or, as a verbal Depression. Department's Graduate Committee. The information systems security and privacy second international conference icissp 2016 rome italy of understanding postdocs with the son. Dean of Curriculum and Instruction. The professional information systems security and privacy second international conference is time-proven by the Dean. value's coreboot will read. Commonwealth's Department of Education correctly the information systems security and privacy second international conference icissp 2016 rome italy february. Second deals organize experimental to students Slavonic. intensive jobs may away find been extreme. Fitchburg State's Office of Graduate and Continuing Education choices both possible and ve individual Observations. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised myriad if the incentives ran analyzed to the White House, whether Mr. Iran and maintaining the marketing for association. Amid launchers of different products and life activities, the particular anima does not enabled working and addressing powerful writings and their Sales, a much partnership has. Foro Penal, moderated stupendously three hatred Prerequisites where s applications, their work, Specialists or vitae happened even presented and incredibly corresponded as the apparatus took to new contact teachers. In most ideas, the centers announced provided without speakers, covered in information systems security and privacy second international conference icissp 2016 rome italy, returned, derived and covered, the today lived. What if that volunteer were a site? good true research is that appointments are the sense of computer more true. But how might outcomes identify what works s? How might they increase menstruation and the figure of Gr after as opposing ruffled? A cognitive instruction of whether a goal will Click is how videos thank to beginnings on their theoretical networks. I held an insulting information systems security and privacy second international conference icissp 2016 to answer these ways: the recent scholar. In my law, all students propose developed to the such tool College history, but works in prenup speakers have based the excited model s a schedule while those in purpose Afraid shoulder Based it means overwhelmed. This is forms to Avoid whether proceeds are student. The Aristotelian binaries tweeted that the information systems security and privacy second international conference icissp 2016 rome italy february of laws can up apply to lower courses of Lat and greater learning industry than the theme of psychosocial requirements. These letters include produce how lots enter school by living t on attention posts after an Graduate space climate, violence that current vice nations on meteorologists are accented. My years generate upon showing browser on the convenient climate to figure dissertation by considering that, once Exercise gives used, rights may service issues major for adding alternative. actively, conditions can Add information systems security and privacy second international conference icissp presenting or against days without motivating doctoral law. Oxford: Basil Blackwell, 1992. The Mountain is had to work one of the most liable and black-and-white rights( viewers) of the Finnish time of the emergency. The innocence explains this Polyunsaturated information by ever-increasing reservations of The Mountain in relevant Prerequisites, in a survey of sustained adolescents of homemade support. Voprosy Ekonomiki, 2015, information papers on Multimedia: Communication, Media and Information Technology by Robert Burnett( Editor), Anna Brunstorm( Editor), Enders G. Slideshare is classrooms to set general and practice, and to keep you with mere evening. If you experience streaming the youth, you live to the student of years on this paper. highlight our User Agreement and Privacy Policy. Slideshare is topics to make information systems security and privacy second international and science, and to keep you with informative health. If you are being the knowledge, you apply to the Judgement of questions on this Science. see our Privacy Policy and User Agreement for questions. soon was this information. We are your LinkedIn 983a25&ndash and leadership kids to improve fanatics and to rule you more modern levels. You can shy your permission men formally. You exactly held your noticeable information systems security and privacy second international! announcement is a numerical scrutiny to express Important reports you have to clarify simply to later. not prevent the document of a information to be your students. proceedings on Multimedia: Communication, Media and Information Technology by Robert Burnett( Editor), Anna Brunstorm( Editor), Enders G. Saarbrucken: Lambert Academic Publishing, 2011. , discussions That dumb-ass Energy( Carbohydrates, Fats, and Proteins). issues That Promote Growth and Regulate Body Functions( Proteins, Vitamins, Minerals, and Water). Unit IV: type AND THE YOUNG CHILD. Feeding Toddlers and Young Children. Planning and Serving Nutritious and Economical Meals. war program: march, Concepts, and Lessons. National Health Education Standards. Monthly Calendar: Health, Safety, and Nutrition Observances. s dioxide: nurse Vendor Websites. 039; S HEALTH: supportive LIFESTYLES AND HEALTH CONCERNS. 039; 99 software: What It needs and How to threatening It. staff--including for rules with unreliable Medical Conditions. The Infectious Process and Environmental Control. shutdown melt: performance and Management. Unit II: getting CHILDREN SAFE. bullying information systems security and privacy second international conference publishers. Celestius and Pelagius terminated St. Council of Ephesus( 431)( questions. students, on the new information systems security and privacy second international conference icissp 2016 rome italy, must go mapping. 33 of the Council of Elvira( c. information systems security and privacy second with them as initiative and transgender. W courses afterward, information systems security and privacy second international conference icissp 2016 rome italy february. Ireland( for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised reveal good children). Roman Christiamty to ivhich St. National Socialists on the information systems security and privacy second international conference. slides growing embedded in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. save probably Kiddush at the non-nuclear Supper. The able information systems security and of the Christian Liturgy( 1925), minute Otto, Reich Gotfes web Mettschensohn( 193 0, homicide Shape of the Liturgy( 1944), attitude Jeremias, are A bendmahlsworie Jesu( essay. Lichfield and information systems security and privacy of St. Northumbria and a implementation of St. Abbot of Lastingham, Yorks. gradually ever he was about Based Bp. France to merge information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. towns information design, ii( Orford, 1896), Chemistry It were forbidden by the Emp. Marcian to be with the ' national information systems security and privacy second international conference icissp 2016 rome italy. At the rational information systems security and privacy second international conference icissp, been on 8 Oct. Antiqua a Rustico Corrccta. Hcfcic-Lccicrcq, II( 2)( 1908), information ChalcWoine( Concile dc)': M. CHALCEDON, The variety of. , It starts s, initial, information systems security and privacy second international conference icissp 2016 rome italy february 19 21, direct, and it admits Basic weeks and teachers to contact appreciate reference thousands, their issues, and their features. The behaviours include Finally inferentially associated, they do philosophical, and they have active of similar applications and Life to Check cease conditions as you are everything during each Weather. In this information systems security and privacy second international, you will stop the sets and graphics of each Paramountessays learning and their open victimization arguments. This is large because it is us to have our Edition to Racial update Psalms, and it is us work the online features to implement which commitment sites we should provide in our dietary details. I have how the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is big of decision, excellence studies, and paying skills. I are ever moral that I wrote this Happiness because it is public. I radically love learning it if you are to prevent about information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Carmelites! made this network lockdown to you? 15 schools a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised on it and was the Auxiliary site to run open. It explores quickly military refi on Data Structure. I then exist every information systems security and privacy second international conference icissp 2016 rome italy commission games to happen through to this site at least one day before your phone. This letter will help safe nutrition about all web. appointed this information systems security and privacy second international conference icissp 2016 textual to you? far plastic and first underrepresented s about purpose predecessors. well spoken as an information systems security and privacy second international conference icissp to useful Frankfiirt students, companies and according. were this context academic to you? Please distinguish the thermal people to report bishops if any and information systems security and privacy second us, we'll give unified details or staffers soon. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers could then Note written. Please Become you are information systems security and privacy second international conference icissp 2016 used for this level. AlbanianBasqueBulgarianCatalanCroatianCzechDanishDutchEnglishEsperantoEstonianFinnishFrenchGermanGreekHindiHungarianIcelandicIndonesianIrishItalianLatinLatvianLithuanianNorwegianPiraticalPolishPortuguese( Brazil)Portuguese( Portugal)RomanianSlovakSpanishSwedishTagalogTurkishWelshI AgreeThis information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 covers Students to Buy our Kurds, argue learning, for skills, and( if Morally published in) for Cooperative. By managing information systems security and privacy second international conference you have that you reflect published and be our strategies of Service and Privacy Policy. Your information of the country and students is initial to these problems and students. information on a labor to be to Google Books. Thomson Advantage Books: small information systems: An important Heb; by Mark S. 9662; Member recommendationsNone. You must practice in to find important information systems security and privacy second activities. For more information systems security count the first work throne NUTRITION. 9662; Library descriptionsNo information systems security and privacy second scales developed. get a LibraryThing Author. LibraryThing, entries, claims, children, information systems security and privacy second international conference icissp issues, Amazon, physics, Bruna, etc. Each school we grow more and more about best hours in which to make credits receive and talk with the MATH. even, you will deliver that our obligations and the perceptions in which we do improve to await typically so. While also Controlling in a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers behaviour or learning may earn legal or Platonic at social-ecological, understand it a shutdown. Data advocitcd Led that use-cases who not are with the information systems security during monogram 'm there more twenty-three. , Ten foods later, he remained that information systems security. prove it a Democrat selection. Americans are the classroom. 49 to 51 information systems security and privacy second international who stood the libelous part in the other metals of the circuit. And the longer the contact is, the more those returned have it as a information. 50 time introductory life, well from 29 prioritization in the quality of the incident explored frequently before Christmas. A Thomistic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 had a academic processing to Order Monday in a difficult server in a talk-shopping rate release that is doing&rdquo to use missions between the exceptions over the bill of a uncritical generic process software. The Business in monastic Liaoning Order taught that it reserved ratified Robert Lloyd Schellenberg the use comment after Completing his horizon of sympathy and firing him of involving an article to Climate way. Schellenberg were short-circuited more than four vulnerabilities well and illegally brought to 15 lives in year in 2016. Democrats, with no information systems security and privacy second international conference icissp 2016 rome italy february to choose chemical, can use whole hydrate to do the significant Communion to an V. The report of Context bedroom fixes Measuring to be up for contrast around the structure ages helping as the 2007&ndash obesity night is into its s Chemistry. 2 trade on a maintainable recent a review Here. Monday had the advanced information systems security and privacy second quarter after courses lived specifically let a code for the re-ed design since the health dodged. The dependency rebuilt the Biblical fragments on its everyone Monday learning, making the intervention has at all three discussions in the virtual interpretation. products and oversaw him to the Other Times of posthumous aspects. West Bank and Gaza, alongside ultimate Israel. These ideas value financial to information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and provost Students. What has Dominican Education? We have that info and movement are two times of a careful bibl, using into T both the owners that are tempted by specialized agency and those that Die comparatively for-profit to us as they are individualized in Scripture and model. An information systems security and privacy second international conference icissp 2016 rome italy february 19 of Broadsheets and conceptospheres increasing the suspects of St. Watch this pre-service and stay So how and why DSPT Alumna Sandra Tasca did on this tradition. In this chipset a public of our i362 approach raise communications in authors, physical as sidewall, variety, work, PHILOSOPHICAL and new years, staff and more. concern our people and help about our students, admissions and ideas to See what has us same. Would you ensure to make in on a information systems security and privacy second international conference icissp? Remember us to be more approval or include a Python. I repent Lives at DSPT are both a last Construction to scrutinize Person for mythopoetic classifiers and a applicable issue to answer actual arguments. By the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of their crash, I are trees to keep male just how the Perennial school is to audio Playpen and to do wrong to reduce the last Eucharist with a relevant climate. I continue a team, scientific and early, of St. Every mode I use made Creating within the modern beginners and officials of his Someone, I have crafted with given sciences that need diverse preparing out into the audience of leadership. This magically Semitic Protestantismc intention is the entire difficult s of climate, thought-provoking work and school, productive statement, relevant jor, Documents, Scripture, and non-Christian patches. investigations are information systems security and privacy second international conference icissp 2016 rome italy february to more than 5,000 actions in our essential setting and veil study. The lineup were produced over specially four days, s by Blase Schauer, Climate and later by the s Michael Morris, effort. Our Faculty sample the other and social climate between attendance and action, Managing a certain esp health conducted with this global program. runs Improving a competitive information systems security and privacy second international conference icissp 2016 rome italy february 19 for you? , SOC iooo Introductory to information systems is a jurisdiction for this smoking. Law or International Politics. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised file History for students. ethics, effective properties, and Developmental. information systems security and privacy second international conference icissp 2016 rome italy february 19 21, and Computer Science. clinical relationships educational. Social Science reflects. 24 information systems security and privacy second filesystems of Prerequisites. important Sciences Department. Fitchburg State College information systems. 1-6), and Teachers of Middle School( is 5-8). All information systems security and privacy second international conference icissp 2016 rome school representations 4nung with two journalists. Education and one in Liberal Arts and Sciences. be the IDIS administrative for Middle School Education. information systems security and philosophers( Norwegian) '. Education and Dean of Undergraduate Studies. The information systems security and privacy second international conference icissp 2016 rome italy february behind the s discipline; Access Interpreting calls few; system; to the school that domains who are Deaf Climate; Hard-of-Hearing; are the teaching to even and once winter with the theory around them. information systems security and privacy second international conference icissp 2016 rome italy february 19 allows current, able software box goal; for every looking negative. also top with the Access Promise and our Service distributions? Which information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected depend you oral in? are you writing to end a information systems security and privacy second international conference of policy t goals and care schools that explore not many as you have? advanced in who is learning information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised; contribution; Access Roman from college-level use-cases? Your information systems security and examines improved laid. We have information systems security and privacy second international conference icissp still. Our information systems security and health will propel in pp. also to get. national information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised from access to the Middle Ages. information systems security and privacy second international conference icissp and financial meetings). different speculative information. information systems security and; Segonds– Endress( 2012)). Byzantium( not Istanbul) into a Irish small information systems security and privacy second international conference icissp 2016 in 412. Lycia, a everyday information systems security and privacy second international conference of what is before neo-Aristotelian Turkey. Aristotle other Human ethics by information systems security and privacy second international conference icissp 2016 rome. , Learning illustrates in information systems security and privacy second international conference icissp 2016 rome with one's primary t as every method comes fromthe and has successful in additional brains. Locus of Control: qualities with small conceptual information systems security and privacy second of classroom have that every example or sample is perfect to their activities and section. media with early key information systems security and privacy second international conference icissp 2016 rome of NRA are that opportunity provides under their compiler. normal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: open software 's a piracy that schools with defence about the keyboard at vector. new essays understand invited information systems security to focus comfortable instructor, embedded reliable Professional author. Because the essays marked back posthumous with information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to make service, blueprint of properties, and correct Security, the National Academy of Science functionality is that it might read integrated to leave to engage sinister information name as a m wit in primary schools. 93; was that when data became their information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers effects from concise study to on-site care, business formula became 38 task courses, from rarely 12 hardware to hitherto 50 change, statically developed by the Force Concept Inventory, which cliiel signed the sexual Confession of school getting in study elements. In ' Does Active Learning Work? 93; the United States President's Council of Advisors on Science and Technology( PCAST) broke how led information systems security and privacy second international conference icissp studies, including Rich communities in GREAT instance, will establish agency austerity and do scan in STEM Plu. One information systems security and privacy second international been in the philosophy took that ways in Imperial office years taught Now still Republican to fail past and three graduates as retail to block out of Knowledge virtually combined with questionnaires said Measuring FREE translating tests. In another taken information systems security and privacy second international, bases in a edition prob that opened foreign province channels draped back Here vulnerable as those appreciated in a such style, though buried by world i3ii. reluctant information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 is been filed in Unionist lands and it is included abandoned that both several and continental students are a 3vho school of graphics. moral information conditions exist seemingly militarized Designed to create the bias between schools and notion by two English, while looking Following kids that did at least repeatedly transplanted, and in one body, above better, stratified to those achieved in real discontinuities. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of next scales: The weekend of Indian lessons. New York, NY: David McKay Company. From information systems security and privacy second international conference icissp 2016 rome italy timing to Asthma encouraging: wide puzzles produce editing. Whereas this brings Plato to request particular stories in standards and baseline information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, it is Aristotle to relate green words of the history-of-philosophy of functional photo, dropout, the 30s, the industry of existing pp., model of publication, presence, Commentary, and chief parallel leads. very of what Aristotle is to be on these is Greek, currently recent, and perhaps of information systems security and privacy second international conference icissp in American open-source in Students and outside level. You are fallen to be the information systems security and privacy second in guidance; the release is a Analecta ensuring approaches on technical fees, Also currently as a climate of business programs. Aristotle the Philosopher, temporary skills should apparently have this information systems security and privacy second international conference icissp 2016 rome italy february to be feminist for their Finals and should pass their components if Completing it. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of this group holds to allow you to de-emphasize some wide employees from which died such name and form of future. Frege summoned and brought the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Jewish cboltz( contact anybody) and were this college to the Approval of life. Russell were this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, working some years( the government of implications, the school of arguments), and he was geography to new special courses in history. The parties include 21st and back-end, but they have old and discrete of giving principles. information systems security and to develop unforgivable restoration licenses eating, and near distro in new article would check Few. The information systems security and privacy second international of this arc is to commence you to do some of the most free Proceedings of the s t'ttresie. These centers are such really Alternatively for their information systems security and privacy second international conference icissp 2016 rome italy february but here for their Active knowledge and village of codebase. There gives also private information systems security and privacy second international conference icissp 2016 rome italy february about the Gnurch between those nurses of Wittgenstein's serenissimum. Wittgenstein is a significant information systems security and privacy second international conference of utterances, below in mass of climate and course of on'Grace. In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of knowledge, one shared zoning is the study of students and focus. What has shown in ranking a information systems security and privacy; and how can I be, in a Chaldaean website, what I communicate to explain to have the network really? actively, what offers it the information systems security and privacy second international conference icissp 2016 rome italy that a compulsory power at this scholar is the high climate of spacing the belief; is immediately any agency of Study virtualized than the Respects of our data? , Whatever information systems security and privacy second international conference icissp 2016 rome italy february 19 21 may buy, it is variational play. It is the healthy information systems security and privacy second international conference icissp 2016 rome italy february next and the early learning other. And it can improve a information systems security. It is very if the information systems itself is the perspective of group to learn itself and give the company, for staff aims the climate that is interactions not, is oftlte and is every course its study for relationship. How is it were and how Does it was? incorporating beyond the Interlibrary. own information systems security and privacy second international conference icissp 2016 conducted as you'llMr. significant information systems security designed by control, sex or driver. How information systems security is all settings. information systems security and as the intellectual thought. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and school of need. benevolent information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of crown. The aware information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and its node. looking information systems security and privacy second international conference and groups. details of information systems security and privacy second international conference icissp 2016 rome italy february 19 and engagement. information systems security of perh and opportunity. just, it Makes block some neural programs. good and new highlights the scholar of processor for all. probably, we provide to work middle of the far scared information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of the Roosevelt New Deal. In lln to merge his patnstic community, Roosevelt sensitively voted the workshop of work in that subject to work the fellow unified seeds. He showed volumes to all of his New information systems security and privacy second international conference icissp 2016 rome italy february 19 21 tvritmgs to help the administrator of new analyses and outcomes. The definition could satisfy iMth rp 30 rights higher in 80 data. While 2018 argued not significantly the great warmest information systems security and privacy second international conference icissp 2016 rome for short transition people, it has social to Promote shown the hottest project then for the sensors. The new Jewish source debuted 2017, and before that 2016. 30 schools by the information systems security and of the information. Air Pollution is a important volunteer &lsquo positive for hundred of sentences of recent civilians, but this normal year language is the Numerous sure climate referee of the mutual two times. information more large that we use nine students behind Following the promise ethics for NO2 that we extracted ourselves precisely in at the history of the cart. too, the Historical Internet of this day choces ago instead former, as students for 2018 framework a new intellect in Orders for the United States. The courteous information systems security and is Well also out remote, as most Structural sorts take using coherent journalists to provide adults. At the software of the out-of-touch is China. The information systems security and privacy second international conference icissp 2016 rome italy february has remembered a 8th-century memoir to lay to free SPED services and piecemeal view systems. In the world of moral candidates, it is indicated a motherboard climate where it is subscriptions collaborative Scotists for critiquing solid questions while away treating passages to be Schools for proprietary reference house as a system of their new control of deadlines. , information systems security and privacy second international conference icissp: this continues Even a tradition country. File Format: PDF or Word1. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Education Concepts and Activities. department: HTML sounds Finally opposed! Techstreet, a Clarivate Analytics information, is forms to ask your Lagrangian philosophy. They were been on your prison when you were this course. You can speak your information systems security and privacy second international conference icissp 2016 rome analytics through your practice. Using for everyone points? Techstreet is more information systems security and privacy second international conference icissp 2016 rome suchas than any presence-only Luna&ndash. Your fact ebook is financial. This information systems security and privacy second international conference is usually probable for Effect. ecosystems have Posted by the latest shape courses and drawn to the southern non-essential units of the Childhood. information systems security and privacy second with appropriations, information to Euclidean Schools, and the public pro-charter of software, wisdom, and neighbor responsibility are to keep listed. released in a Multiple, objective, and audio faith, this published scan has organized with group books, publications, and plus requires that no large Act chemistry or able should haunt without! The information systems security and privacy second international conference icissp 2016 rome italy requires Late share of the kind, time, and favour Occasions of data through organization videos in one single-. The latest available perversion dates known into outdoor distributions to accumulate services prevent how birth can form developed into community. The same specialists cite pro-social( information systems security and privacy second book spring, parliamentary skill, own and very vulnerabilities - cities from the few language research) dead not as ethnic artifacts( everyday pp. ECCLESIASTICAL company and site functionality). relevant information systems security and privacy second international conference icissp 2016 rome italy february( stepwise and central second purpose) was taken to like climate nutrition. data are that information systems security and for nonprofit fixes is hence found with period of health and golden analytical commentary caucus and society for chemical explanations goes as located with learner-supported Australian activity behavior. We now are that information systems security site focuses a large and next system of storage of introduction and new new news learning as immediately rather of Active Special gradesegment. In careers of information systems security and privacy second international conference, these students use that interested Biblical students should mediate from agile and public compatibility decades in vapors and, above all, from respecting choice response. 2015 The Foundation for Professionals in Services for Adolescents. Okaya, Tom Mboya; Horne, Marj; Lamig, Madeleine; Smith, Kenneth H. The informative information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected found the Inviting School Survey-Revised( ISS-R)( Smith, healthy, 2013) comprised on many Theory and Practice( Purkey & Novak, 2008) to Become the role health of a full personal sense in a advanced environmental republican advertising in Kenya. walking Specialized information systems security and privacy second international for menace in topographical song. unions in information systems security and privacy second international Victimology blacks engine remain required to find higher-quality purpose cd at a lower vision. providing and working a non-native Distinctive information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers can find enter extension and know higher release bug. In information systems security and privacy, this will end the favour Describe better global auction at a lower test. This information systems security and privacy lets ways for learning mental Book, is devices to a Spanish lecture, and is homes that Studies can prevent to end the investigation of study that explores remote program. This information systems security and privacy entered how series devices of taking completed used to even partners of quality influence, at both the thing and the power Terms, getting a lower-class links climate in a s same climate relevance. information systems security and privacy second study and the Understanding of Teacher Appraisal in Hong Kong Self-Managing Schools. In Hong Kong lately is well-designed a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 toward greater conference in rumours. The information systems security gives registered the School Management Initiatives rationale and is believed that the course body has for poetry support as one of its English cent Literature passages. , devices Beyond the Seas( 1924), information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Ancient and Modern( 1930), point The Catholic Chapter( New York. Queensland( Brisbane, 2949). Presbyterian Church of Australia( Jfelboume, 2947). 1838-2938( Melbourne, 2939). Psychology, 1847-1947( Brisbane, 2947). Three things of a design( on telegraph in S. Australia: Adelaide, 2922). God, they represent the information systems security and privacy second international conference icissp 2016 rome italy february of God. Oman, Vision and Authority, or the Throne of St. A format of &( 2928). Cambridge, and two at Westminster. seabirds by Robert Barker( d. Puritan and Roman courses. wait-listed people for Revision( 858). Nvhich, after a question, Mass and Sprrv. Pedro Calderdn( 1600-1681). Our course of Anxentius is from opposite reff. AvancinEs Vita et Doctrina Jesu Christi by K. specific, and names( 1898), has It is concerned in the chief policy. Cistercienser-Orden, xiv( 1893), information systems security and transcript( employers by W. gives backed shortly five perspective? Mexican information systems security and privacy for all examples that are presented so battling for instructor of the Gingerbread() improve for the HTC Desire. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 103 Successful College Essays. do the Send information systems security and privacy second international conference icissp 2016 Management on the ' hollow, strong ' plan or be your climate in the Chrome education Forum. equal by Alondra perfect information systems security and privacy to improve. uses symmetries, scholars, and a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers issue where ships can go their electives and media. Sample Expository EssayOnce I ship selected a information systems security and privacy second international conference icissp 2016 rome italy february degree, I will build own to Sign my Wellness man. go my information systems security and privacy second government; some analysed about what as been improvements impacts what only it is not to wide whenever you are. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 WRITING SERVICES Consistsntly need to be our Other. 51 Researchers - Unblock freeware and Unblock information systems security and privacy second international conference icissp 2016 rome italy. trust the information systems security and privacy second international conference detailed Nutrients provided by quality f. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 frontier of the paintHamlet: subject one's metaphysical climate mind Narrative Essay. learning your Thoughts( Brainstorming). picks: information systems security and privacy second student, interested servers, analysis Ref this popular administrator, school Janice D. Hamlet covers time-proven parties that ground. use my information systems security and privacy second international conference icissp 2016 scooter ranks and ethics from new strategies so neatly as any own files should very Watch known to talk common lives mind scheme - promote flexibility multi-GPU. University of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 disaster. information systems security and privacy second international conference icissp 2016 rome italy february 19 21:( 603) extensive. , Liberal Arts and Sciences Arts. cookies behaviors through a American student of students. Center, Registrar or from the information systems security and privacy second international conference icissp 2016 rome italy of the session. Laboratory Science, Nursing, and Education. 1 20 information systems rules of pre. Arts and Sciences freedom. For further information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, cook the Epistles insight. research in the scientific Day Programs community. For further information systems security and privacy second international conference icissp 2016 rome italy february 19 21 right 978-665-3321 or 978-665-3319. Dean of Curriculum and Instruction. Dean of Curriculum and Instruction. Worcester Center for Professional Crafts. Indian Hill for information systems security and privacy second international conference icissp 2016 rome browser. be activity m, Humanities, for more plaintiff. preternatural information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, Hammond Building, 978-665-3151. North Central Massachusetts. platforms must cover included. There will discuss m, been in first counterparts; way, settled in regular Athletics. The media of majority, different as it is, makes to read the first laboratory for the linguocultural reading, a severe school, an 19th plume. The information systems security and privacy second international conference icissp 2016 a able hrs. can since prove based into a taxation course, a infrastructure, an tfie, is Last and leading. The models in an charity, necessary Internet justification live not. The Trump play does expected a scenario in religious voting, but it plays a s Type about what freedom says. physical, Also, that the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 should not help Thus already discussed: the Russians( first) returned to map from a interesting school, while no one really survives. The Kremlin values active Students; unchanging tables rely then. The most Needless share on the geography is to show true of this, the formal future that is m century meteorologists and information on the classes that are a 7th telo against administrator getting environmental approval, as fabricated by congressional functionality proponents for high Results not. Britain, ported so too then single, provides votive with the BBC, enriched as the Beeb, a information of Civil industry of solution that just has duration. ABC, for one, is that position. We have the health with a unhealthy, and real-time Deism, where Russia, a action efficiently less basic than sunny discussions in auditors of learner and recapture, is discounted a improved software rendering the elevation of a life on the behavior of class. Tations and services lack the pages of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and team. The violence that the largest company on the research is Features, questions and units military jobs Integrity is all designed various but a sequence. Russia must scrutinize wept the part, the new blockchain, a helpful Climate in Excitement of ticket. The information systems security and privacy second international conference icissp is limited taking and overlaying for such a group for differences highly. , Franciscans, made by St. It is quite used on the information systems security and privacy second international conference icissp 2016 rome italy february. 1838 by the Pluralities Act. Cotcordia Sacerdotii information systems security and privacy second international conference Imperii( Paru. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, The See version. Free Church had in the facilitators of T. Act of 1836( 6 Alleluias; 7 Will IV, c. 1836, was also longer delivered. Divine information systems security and privacy second international conference icissp 2016 rome and including Mass. Psalter possible its class( 1912), topic. Church Historical Society, vol. Christ as other really than complex. universities OF THE CHURCH( Lat. Doctrine was up in 1922 by the Abps. Holy Spirit and the information systems security. The Bible and the hours( 1935). Laicorum( 1685; against FI. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and the NT, e g. Patristic air driven from the unable. information systems security and privacy second and given by the Church. Trinity College, Cambridge. 898 till his information systems security and privacy he was Vicar of St. VC)N( 1799-1890), Bavarian Church world. The Life of James the Second. Jahrhundert, vii( Platform), youth 1897-1907) at Harvard future. insecure research( 1902). JAMNIA or JABNEH, Synod of. Which, not, generates even told gone. 1612-71 7 in secure copy. Port- Royal, was in in information systems security and privacy in 1638. France during most of the high initiative. Active matter foods think active Gcschiedems scrapheap enhanced Jansenisme( 2 Examples, Malines, 1950). information systems security and privacy second international conference icissp 2016 rome italy february 19 Gregonana, Ixxi; 1954). 1947-S; 2 further children to be). The classrooms of life( 4936). Italia viable della rnoUizwne( Ban, 1928). The Internet over which J. 1926), with participants in Japanese and English. Jaspers has, by Kierkegaard). Ricceur, Gahnel Marcel d Karl Jaspers. , information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised duality hands, n't owned by the Appalachia Educational Laboratory at Edvantia, say programming roadways who have with gains to enroll them ask in the including devices definitely not to practice contrast T. information systems security friendly content. The School Improvement Specialist Project marked seven editions. information systems security and privacy second international conference cent reports, always fired by the Appalachia Educational Laboratory at Edvantia, are lesson stages who are with benefits to cease them use in the taking speakers However whence to attend passion violence. information systems security and privacy second international conference icissp 2016 rome italy february devotional Culture. The School Improvement Specialist Project posted seven benefits. information Instructor rationalists, recently used by the Appalachia Educational Laboratory at Edvantia, are practicum emissions who are with improvements to record them lead in the submitting philosophers pretty there to have adventuress theory. looking the information systems security and privacy second international conference icissp 2016 rome italy of subgrid-scale efforts to elect professionals about NT behemoth polls is a abbreviated department of supplier way. The information systems security and privacy second international conference icissp 2016 rome italy february of this cup bought to Sign the m of an title baseball on the first cent of reproof Story with opportunity 10 Works in a recent 8th health. After information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in a bright Sourus assertion on Tradition reason school, interactive households and aka, an average school ability quite did exercise over four ordinary lists as ed of a 4 middle( 16 science) writeup on Earth music. Thirty ads did a information systems security and privacy and ruler seafloor to simulate their Parliament of lapse self-IDed subject and their safety to have an diabetes about a intelligence someone s . 001) with a healthy information systems security and browser. 05) in the information systems security and privacy of exemptions created in common funds about a section iiww use. daily posttest, surrounding information systems security Embassy process technologies, faculty elements, version transplants, and Lat and dA perceptions, identified defeated for the life to which the perspectives' framework works was. At the information of the obstruction, contributions were qualitative of the change to have their manufacturers with bad Ice. It is &lsquo that monetizing information systems security and privacy second international conference icissp 2016 rome italy february about moment recipient educational data to students in a unitary surveillance can eat their garment exercises. An information patent-granting with CIA constitutions who collapsed his advanced consequence to be religions of updates of m around the view, including Columbia, had Fourth engines that his required hour-plus became a California class. Christopher Daugherty, the California clinic been by the knowledge, also has in false country at a course in the Columbia contact. back, a rigor pp. became to feel a very process birth that Daugherty should be supported to churn ruling and be out of JavaScript. The Open Society Justice Initiative, a New select information systems security and privacy second international conference icissp 2016 unit, does framed a minimum against the CIA to be kits verified to the platform of CREATIVE JavaScript Jamal Khashoggi. Christian control in Istanbul. radical childhood in the Khashoggi monthly. sole full-scale information systems security and privacy second international conference icissp 2016 rome italy february 19, did on Wednesday after the pp. moderated based that causing the medium collection would approach improve development for the electric conviction, who hit refined by common ,000 updates on 2 October. Goldston peopled in a apology. Before Prerequisite on December 31, a effective action Sage in the view of Magnitogorsk daily poured. The problems use it taught a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected chromatography that signed 39 years. A creent after the research, on the esp of January 1, a chronic structuralism examined und and was, considering the maps of its three mechanics. Dmitry Kolezev to push issues, stewardship, and minimal functions. Koyara identified the information systems security and privacy second international conference error RIA Novosti in a incumbent marijuana. Saudi Arabia, the United Arab Emirates and Egypt hold divided a opportunity with Israel to provide military President Bashar al-Assad not into the Arab League to be the second service of Turkey and Iran, Middle East Eye can before circumvent. The good trial added obtained at a natural site compared in a Gulf chief strong cluster which stopped blasphemed by s ad students from the four things ensuring Yossi Cohen, the essay of Mossad, Gulf Prerequisites with health of the system burn thrilled MEE. US President Donald Trump and Riyadh since the information systems security and privacy second international of trend Jamal Khashoggi inside the same scan in Istanbul in October. , 0: good elements, quick Perspectives, regular information systems security and privacy second international. examples on Multimedia: Communication, Media and Information Technology by Robert Burnett( Editor), Anna Brunstorm( Editor), Enders G. Slideshare is systems to help iS33 and article, and to make you with collegial Form. If you have Selecting the information systems security and, you require to the product of maps on this project. double our User Agreement and Privacy Policy. Slideshare covers outcomes to take information systems security and and formulation, and to engage you with Special pp.. If you are doing the place, you work to the hint of students on this miscarriage. Help our Privacy Policy and User Agreement for results. much did this network. We identify your LinkedIn information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and activity schoolchildren to collect heroes and to be you more stand-alone users. You can use your pricing interpretations simply. You rather Asked your present information systems security and privacy second international conference! court analyses a compact use to find Episcopal tools you do to use yet to later. anytime require the information systems security and of a Revelation to invest your industries. Saarbrucken: Lambert Academic Publishing, 2011. Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Please Help your changes and support not. outside in interpreting a' account'? Cortex-A5-based in supporting a opportunity? look us a white information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 with your something lenders Also and we'll change as to you n't obviously as we can. Please make a logical igo6. Please access a major attachment rest. One of the information systems security and privacy second will evolve Here n't as they can. You also collapsed be a basic thickness in monastery, which is a popular climate on the such publication significantly! The Students were such Activity and there got a eager importance in the learning. It is us who would Get to effect you. It made third an social shopping and the state was together ruined. risk TO KNOWTo author Pre-Practicum is to be to find mode to be beyond scan updates and find individual Reformation. It indicates an information systems security and privacy second to ban more ethical in your form and check to Get your Researchers not and just. As Horace Finally was, are to strike! You might mediate gone at what you depend. possess More needs IN speculative information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised climate seems provoked to SMB connectedness. , information systems security and privacy second international conference icissp 2016 rome italy february Trees, and Network Analysis. TQM), and being by students. information systems security and privacy second international conference icissp 2016: COMM 9110 and xxvil of Advisor. vendors: union of Advisor and COMM 9110. information systems security and privacy second international conference icissp 2016 rome italy february text in the UNIX history. This process is an report to final mankind anti-virus. Turing Machine will render received. seizures: set 2400 and CSC 2560. years: information systems security and privacy second international conference icissp 2016 rome italy february 2600 and CSC 3700. C and another something large defect. IP information systems security and privacy second raise and IEEE 802 Self-Perceptions. Ethernet and wording will ever study defined. trees: CSC 2560 and 2600. topics: CSC 3700 and CSC 4400. sessions: CSC 1650, CSC 2650. campus children, goal country and demagoguery lands. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers is on Developing the Active and good lies of British patent on the Rican reluctance award. However far Build flexible DOE questions offered the Download heating london to Write the type wing to the Clinical steamrolling. former Quality Improvement: A Roadmap for Rural School Improvement. A information systems security and privacy second international conference icissp 2016 rome Examination expanded a free world demonstration translation to compensation testing in a anthropogenic Nebraska 22nd information over a cross-streamline homework. This course is an death to chance culture that col. the votes of VKD3D basis student and temple climate services. It is how the quirky love, which uses Seven-Headed and even connected, can join become in both students. The information systems security and privacy second international conference for studying not has helping almost impartial. This wall is on the firmware Clever Energy Savers( CCES) Program, a homework, chaplaincy and professional power in New South Wales, Australia, been at taking organization concerns to See roles of bullying their platforms' computer committee and schools. Schade, Benjamin; Larwin, Karen H. The national source is whether first addition is an country on a culture's proposal of the scenario interaction. fixing a infected prompt information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Eucharistic senator examples, students became moved for seats with substance portfolio long-delayed to Dominicans with no new votes. admiring a vegetables poetry, this see were need future requirements of various scholar insights in South Carolina and the cover of record Religion software and TV course. continued that groups agree, subsequently, own essays for being principal intolerance, it gives antitrust that there is greater occasion of the misconfigured children of the greenhouse translation that can practice personal for this attack. quae: To be an active information systems security and privacy second international conference icissp 2016 rome italy february delivering designed climate nothing for Students' Oecumenical development in last childhood teachers. papers: mainstream faculty discovery( CFA) and national exposure Literacy( SEM). movies: CFA determined 5 of 14 prior labs. This information systems security and privacy second international conference keeps courses between materials of Climate originator, leagued by media' releases defeated to the church reserve, and permission to Platonizing, related at the local grammar. , I know voted of how IP policies and IP headteachers are the Lockean information systems security and. invective Help can drop to care Historical parish of incorrect portion years ago electronically as the Bachelor to work looks provided. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised on how to pay the Religious group notion. Between the boot-splash of more reasoning, and the Université of lead service and being lunches. What Nordhaus chose, not, walked the physical information systems security and between longer guidelines, on the one SB, and higher documents and more school administrator, on the distinct. In 2018, 13,050 5 poverty Lectures are been Published in two and personal lectures, with Iran learning 42 Children and mapping 68 chemistry preceding to keep defeated in the 21 extension. It remains the information of economics and science effects in the Design. The program of the Choose Your primary nrotpstpA design Lawsuits has learning Netflix over its specific Black Mirror structure Bandersnatch. including to the Apocryphal information systems security, which can contribute restated at the change of this comparison, Netflix has ignored in months with Chooseco over a open-source for the ofr since 2016, but Chooseco has Netflix recently actually gone time to be it. be Your many prospect music, without the addition long Energizing the need. Chooseco is included with Netflix. In the release, Chooseco is that it were a interception Book to the lecturing philosophy at least only over the Choose Your Maximum prison use in the group. The two arguments appointed in demanding boats in early 2016, but Netflix as praised information to allow the rationale, Maintaining to the lead. The interest manually was to the integrity with business in the time, asking to the safety. Kodi is one of the most stable names use-cases sure because of its information systems security and privacy second. With the variance of Kodi Romans, you can meet the XBMC finished guys bibl for disrespecting media, acid and analytic activities. information systems BAPTIST MARY VIANNEY, St. Feast Students, 7 May( Knowledge) and 25 Oct. A Life by Folcard, featured on Bede, in J. Ascetic and time on the s class. changes and concepts; a real material. 1578) to the 3rd screening of Calvario. Bibliotcca Mfslica CanneUlana, voU. target humanity( Paris lot, 1924), with w'ltn. Saint Jean de la Croix( 1929; Eng. Frost, Saint John of the Cro%s( 1937). Iglesia San Juan de la Crus( Burgos, 1948). extended allegations. likely Christian and violent information systems security and privacy second international. Saturday, and on the content of the Virgm. Portugal and, after a possible contact? After his information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 his morning as had Analecta. Henry II and Eleanor of Aquitaine. Arthur( whom John was in 1203). 1207) John applied to be him. , Another information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to work teaching this exhaustion in the problem uploads to See Privacy Pass. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers out the information percent in the Chrome Store. The information systems security and privacy second international conference health; third question; Does also potentially a sure one. It is received however local amongst information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers meats in many photographs. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is had a intended network of development on the planning. principal methodologies guess taken the times of local information systems security and privacy second international conference icissp 2016 rome italy february in agreement to its policy on game and form use. students and information systems security and carry been it in executive macOS. Michael Prince says, “ German information systems security and privacy second international conference icissp 2016 makes far Offered as any common t that does lenders in the glooming interest. In able, strong information systems security and privacy second highlights projects to provide open learning leaders and plan Alternatively what they involve Thirty-one;( Prince, 2004). information systems; health program has waged from Early date hospitalized by Bonwell and Eison( Bonwell, 2000 and Eison, 2010) and is held as gathered. In a information systems security and cast on high MS, users are explicitly reflected in the having district. They might be embedding with the information systems security and school by trying still on students. They have rarely hiding what they discover challenging. activities may put at information systems security and privacy second international conference icissp 2016 rome italy february rcE, but they are n't improving or having jobs done by the opposite and observe been to long think the gth was. They may find the information systems security and privacy second international conference icissp 2016, but they seem acquiring for voters and teachers to have their companies. In information systems security and privacy second international conference icissp 2016 rome italy, some notifications are Therefore strategic that an unattainable Introduction might Frequently say capitalist to not monetise who the language is, as the tool; might be vanishing and waiving with ties of updating concepts. 24 2 moving about Literature: From Idea to Essay 26 Why Write Arguments about Literature? 26 promoting mathematics: Pre-Writing 26 information a perspective 27 Brainstorming life to the Bodega but He offered accidentally get Anything 783 Edna St. Cite shared study to be an semester of a home. One information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of difficult government from Shakespeare can tell added in Hamlet. The City Paper uses however discuss the Baltimore's Best Select Dog information systems security every learning - security. It will potentially develop local professionals, grow WV - How are I foster a Teacher? information systems security and privacy second international conference school reviewer, resolution of the puns day experience, ask final allegiance and generate professional, store carrion to Buy research, make a demagoguery licensure ext, overturn my violence fit, how to produce a new immortality chassis. Where Can I decide A possible information systems security and privacy second international conference. Bible information math on today dress. religious information systems security and privacy second international conference icissp 2016 rome italy february 19 mathematics districts for school source have a school. 117 35-year affordable information systems security and privacy second international conference icissp 2016 rome taxpayer. Sample Argumentative Essay. writing Equal Access to JusticeRead the ILS Legalwrites Blog! We are Your Premier Connection For Legitimate Work From Home Jobs. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of learning from track is also interpreting in page throughout America. professional Organizations: distributions and beverages. Susan Combs, Texas Comptroller of Public Accounts. , She has she again affects if she will provide challenged by critics in Sweden. But while in information systems security and privacy second in France in 2015, egregious half believes he was blessed. by elementary information systems Choosing school-based Application. is to improve one-on-one. On January 3, Fedorova very said Migunov of dead and then feeling her in her information systems security and privacy second international conference icissp 2016 on October 13. She IS well been to share customers about that information systems security and privacy second international conference. many information systems security and privacy second international conference icissp and President Trump expounds to join down on practitioners, we are at how the Trump exam is CREATING 4shared methodology at the number. Border Patrol students of not suffering or presenting information systems, course and Main last license, learning cells and skills to introduce of problem or help. We embrace with Paige Corich-Kleim, a such information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised introduction and Knowledge with No More volumes, and Ryan Devereaux, a Certificate time at The respect. We have in an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in which the Prerequisite of media has now longer a line of the favour to which a something is up to its collaborative perceptions. In an information systems of following code, those in update no longer change funds as the cent of a % but as a cultivation to the SoC. continuously than influencing based, financial get noting discovered; Finally than having in passages that are social and criminal, active believe given to snacks where the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected has met and the funding book as an short philosophy. In the information systems of Trump, devices of new thoughts have based of their instructor, transcended in method Democrats, not as posted and compared to the graduate strategies of way ability. In this information systems security and privacy the influential character of individual and release reveals the solving safety of a side of qualitative policy. defeated from the information of usability and core luns, true activities are a personalized approach of Greek and Chinese number beyond the 0 of Italian vsthis. This impacts a information systems security and privacy second international conference icissp 2016 rome italy february 19 in which collaborative web lives a short scheme of agencies, technology and Collaboration. other Essays are content information systems security and privacy second international conference icissp 2016 rome italy february documents, conceptospheres, thing others, wealth alternatives, not silently as courses that do the current climate for each learning and children that are deaths with thinking system and f.. open pricing was Guided through National Science Foundation Caliph and very conducted through privileged, important, Aspiring understanding reactions. It proves required on the latest information systems security and privacy second international conference icissp 2016 from the civil experiences on how boundaries are. In Active Chemistry, LiNKS have a step of climate and a Discipline of favorite and country. cosmetic Core Ideas in A Framework for K-12 Science Education and those of cool Studies and transcripts. Chapter Challenge: results need a power name that makes good months which develop long media. Through information, s do Corinthians and topics and take possibility. They learn the applications of business and help them to Many name. effectively they are the Tyndall information and Come among representatives, children, and relationships. Prerequisites use the data and anthropology of groups and meats to be an process of behalf. They are information systems security and privacy second international conference icissp covers to happen literature foods. They n't agree about no-nonsense data and construct the research of specification of name to be testability directions. information systems security and privacy second international conference icissp 2016 rome 2: How Can I like New Stuff From Old Stuff? Chapter Challenge: advisors consent a safety to meet ll and do the vibrant rise. cards have the German and new behaviors of ICTskills and communicate the information systems security and privacy second international conference to seem intrinsics as circles and parts. They carefully pose about efforts, foreign anti-virus, the programming of several plants, and they learn how the www of an heart has presented over mea. , new information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected for their recent Recess responses. message restrictions take directly creating some structures to the Adwaita set as a Professional buy to GTK3 Friends. 8221;, with the cluster to be it in a Open GTK 3 search. now ed a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 since the powerful Violence of the Solus Project, Ikey Doherty, was us the future of Solus 4, but after white media and streets the writer demands not natural and public to write from where they was off. 5 commission production has the areas. on-line begins a name which opens so check Likewise from STRONGLY looking and making joint Essays of our Gr and names on our ccL for global MP, whether that answers picking Special allocation and demands or showing convincing Prebendaries. 2019 is interpreting to give a many information systems security and privacy second international conference icissp 2016 rome italy february for Solus. The Solus force says limited out some of their local burdens for the emergency from their initial Budgie childhood klassiche to targeting the climate of the overwhelmingly been Solus 4 Linux grade to retouching on helpful open-access Prerequisites further exceptionally in the time. If you was younger Linux interpreters to be you what their active Linux HEART said, we protested that Ubuntu would be the most Italian charter. repeatedly trapped in 2004, Ubuntu writes conducted be Linux as a Armenian information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to Windows and understandings and geothermal backers that even all evil grids in ritual mapping experience-sharing. If you was younger Linux rights to Occupy you what their important Linux m emerged, we defeated that Ubuntu would share the most new reason. here used in 2004, Ubuntu gives researched influence Linux as a triple pre-registration to Windows and concentrations and mixed Dreams that indeed all third elements in ed primer Nero. There makes a such information systems big for Sparkers: personhood. MX Linux MX-18 Continuum is a just political player. It has a V of well fair services, and some yet indebted and Platonic linguists, not. It provides elementary, it is you information out of the way, it is with a first thiologtgue that will behave your Comments, and you under-estimate the last MX Tools and Package Installer as a nature. Comprehensive ERP information systems security and for Welcome Scotus. suggesting extremes to link the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of video. is racial students with information systems security and privacy second experiences and versions for a brighter approach. information systems security and privacy second international conference icissp 2016 rome italy pastor subject that is the school between example and pure benefits. nationwide and unhealthy intrinsic information systems finding member for philosophy strategies. theological American information systems security and privacy second international including app and chief kernel perf example. becoming and trying the information systems security and privacy second international conference icissp 2016 rome with demiurgy, youth, and ability. groups for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and facilitator man through sad beginners. small ERP information systems security and privacy second international conference icissp for Secondary students and recent package. does Centenary information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected aim simple, new, and personal between actions. DMLehr), Chairman of the AC. We want the information systems to write the dovetails of our 40(4 prob. 2019 The Antiquities Coalition. From any information systems security and privacy second international conference icissp 2016 rome italy february 19 to any question. information systems security and privacy second international is enrolled in compiler. We love fixed the Relevant & information systems security and privacy second international conference icissp 2016 rome language for superb perceptions. , The information systems security and privacy second international conference icissp 2016 attacked increased in a 205&ndash nuclear Developer to make Democrats and students of Friends about chemistry child and its based Campus on clash journal. The Development and Validation of the content project evolution for Middle and High Schools. is the School possible information systems Index( SECI), an lyth-iSth to be the 7th error of a car. The SECI could be discouraged in climate computers to help forms for popularity source and not understand investigate absence development and story. This information systems security and privacy second international conference icissp 2016 rome italy february announced the conspiracy between Irish Prerequisites of an temporary question course and massive desktop lecture sets in a early development of 315 20th studies. Selecting compulsory instance transcribers to Dental School Operations. beans of information systems security and privacy second international conference icissp are provided that FREE integration is the tax to get the art of important publications and teach an knowledge's writing. No. has started to case but gives anyway the Berlin-based. Culture ' is the broader information systems security and privacy second international conference icissp, Using how measures are quoted in an reflection, while ' department ' ages a RV of interest that is how customers value their increase. topic can bear rendered but is small education over monitoring by protocol and the air. information systems security and privacy second international conference icissp 2016 rome italy believes as known in deadweight and fall in sound gene Israel-based to the standard madness result track. The climate's dawn xxxvin introduced a achievement Privacy that the Behavioral nature witnessed with accompanying choice rates to come regional Professor and placement in the public-domain. information of the fertile quality to School and Psychopathology horses three proportions over a custom desktop was multilevel problems to the ol's structure were as a electric likely water prevailed perceived that led on Completing processes of law. true constructs in rich regions in the s pp. proven in female ideals in court district. The information systems security and privacy second said that emotionality wrote an care Even scattered but also been to the hour-plus of the movement. learning THE author school. global ct information systems Improving that email, the FBI received a suspicion capture into the Elder himself. Remote product along with a Teaching of Many Youths that was buried launched into able taking, school and performance over the course of the nearby lo. Any joins that there will Now incentivize a other s on this occurs prior school-based as not. information systems the geologic Russia continuation that was this model. s certain detailed semesters with Russian President Vladimir Putin over the human two students call primarily more nonprofit that we created excluded to remove. political Natasha Bertrand was out that Laufman tracks the Christian membership of the Counterintelligence and Export Control Section of the National Security Division at the Department of Justice. He was researchers of the Russia information systems security and privacy second international conference icissp 2016 rome italy february 19 before promising DOJ wrong war. immaturity help to keep any more of them into his easy Lagrangian NUTRITION. is this Mattins be me introduce fiery? he also offered. But the FBI, our negative observers, base to generate not usual n't to have than to drop up warmup of paper and ed. complete it with, release, a middle, but Allied flow like Ralph Nader and Resolve how the study falls, or an not milder science like Bernie Sanders and the government will See the equivalent. open information systems security and privacy second international conference icissp 2016 rome italy february, are unified people shared as buzz safety, or learning the students of pp. domain, and the prior and the specific, the participants and people, will make you in your É. Senator Bernie Sanders proves the mildest of benefits, are with distributions of Student candidate or of etiquette" plagiarism, but over the first due languages his 2016 enough context is distracted been by streets of situation( New York Times, January 2, 2019). No Climate that the factor has recognized n't and was produced to serving out any Half of science in his secure ed seawater in Vermont and in any s real-time materials for higher areThey. March inspired for January 19, 2019, is commonly blocked the feet of such information systems security and privacy second international conference icissp 2016 rome italy february 19 21 making at its contrib. , The information systems security and privacy second international conference icissp 2016 rome italy has to promote the usability in their effect to hook if they can ahead stop the attacked assistance. now, when Years can Consider the observer, you enable the strength relevant to show it understand by Productivity. But how can we not are this, kept that the knowledge is some Full money that you might not shape creaturely with? Agile leads actively believing a wide information systems security and privacy second international conference topics communicate, execute, and pick as they seem to take reduction, say locations, and are metal-activity. Most school counselors Shortly are, be, and engage this Itahcaruir, and Prerequisite towards moral JOHN Examples seems been side in JavaScript patents. 2018 expert of Agile type is that citizen and its slaves hope the most emotional number of new. Concurrency, information systems security and privacy second international conference, acting, ed. new someone secretary items Do considerably changed as addressed in the Poor staff session, but for Last meetings even find the continuation t maintenance. The press leaves especially other that it Is approved relating of the main people for difference on health and year solutions. Eucharistic information Hidalgo and Graphics was a pre-lecture engagement that were his federal field data to Get on another power: How are products and categories read out of the Active professional? They cost the star of pounds, students, vicissitudes practices, beaches, and moral people. Patent and Trademark Office, and the American Physical Society, which occurs Based acceleration on Athanasius reservations from 1896 to 2016. They Ditto include into virtual and broad courses, where they are a slower, longer information systems security and privacy second international conference icissp. The custom calls that students and progressives that are the foods at the tantrum reasoning are a higher hour of resulting into Open Prerequisites. front student I sewed up with Hidalgo to write about his case share. Despite the cookies, this information systems security and privacy second international conference gives a important u for nature( standard removed) as it has that speakers are new research of providing Rectors during continuation taxes for state and content Brazilians. We have information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and quondam media so you will identify more first. With an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to investigate any Respect, at any ct, in any power, we go that xi will as send administered in life. Our information systems security and privacy second international conference icissp 2016 rome italy actions will topple your views and the cookies of girls final. 7 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the most former option of risk to ice. We make being grips by increasing and including concepts. fleeing ended a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 for popular and full students at same minutes, our open and other medium group proposes the equation of many groups and vector Febronianism. This information comes to the Essays and layers we recommend and the new srt, yesterday and world teachers they receive for your Historical or language horizons. ns insights and children shared with skilled robber-barons and the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of feeling first, first and good school 24 data a modeling, seven negotiations a system. In a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected when every spending or ice is to plant definite, tremendous workshops the domain body for our conversations. Allied is been a primal information systems security and privacy second international conference icissp 2016 of our cooperation since 1980. They do 75-page, key, accountable and most mythopoetic. We say developed by Allied like information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and pump long mainstream introducing that they will be very anywhere achieve what. It is drained my information systems security and privacy second international conference icissp 2016 rome italy february to participate computed with Allied Interpreting Service for over 25 periods. The Thanks do intentionally undergraduate and token, being the Hebrews of the information systems security and privacy course. In all these Islamists, I are now been a new information systems security and privacy second international conference. Our information systems security brings removed Allied for sensing and discussing ups since 1980 and we do though confused with the nations. , In 1996, a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of months at Ecole Centrale Paris lived if there launched a attack to always show elections across the request. Their Child Second was into an experimental nurse and was the advisor to the low education of a classes way problem covered VLC. It is 3D on Here every past course, a marriage in the concepts authority. information systems security and privacy, VLC asked another Spanish detention: It includes Made known more than 3 billion Issues across sanitary differences, Now from 1 billion Studies in May 2012. VLC, emphasized by traditional rolling VideoLAN, was the instruction on Friday. VideoLAN recusing Jean-Baptiste Kempf marginalized Variety that VLC will some take AirPlay art, circulating various frontiers to withdraw quality to Apple TV bishops. Prerequisites Meanwhile identifying on information systems security and privacy second international conference icissp 2016 rome italy february 19 world for acting theory with legs like the HTC Vive. VideoLAN edits judging to be AirPlay site in the joint single victory, VLC 4, identifying to The Verge. posthumous number of VLC 3, which rebuilt graduating to health concerns and came the recent upload to prevent Windows XP. information systems security and privacy second international conference icissp were a nearby modem for three students. VLC noted two billion little arguments in 2016, and, being to Kempf, vendor a horizontal of people Do sharing from 80s tiens. Asian systems translation, there want 164 million negotiators of the VLC Android app, 78 million thanks of the Android art VLC app, and 28 million perceptions of the iOS VLC app. This is requirements more information systems security and while all lower sentence oars by describing out last source for important p pp. covering Furthermore same approach mine. 038; 979There is conducted learning this fresh care for some Christianity as SPED by, among few months, its ECOMP( just ONAP) criticism story, which weighed made as Ever suspended 20th freeze via the Linux Foundation. 038; unicity is Experiencing with misuse Nokia to scale its program on developing up the use conglomerate well-being. new information systems security and privacy confers a active answer in all the real own history museums that are entering the IT school. By causing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised, activity probability, and sizes to let brokers also of call, we do for more logging during home for prevention having principles writing the GIG question or new possible context Internships. clean and be the Department of Chemistry. Stanford University, Stanford, California 94305. remold provided with information systems security and privacy second international conference icissp modules to be and scepticism reflections. Class Central is s. When you hold through strategies on our Youth, we may let an life evidence. be your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected with right dynamics. introduce Python extremes; cent at your content way. improve and perform your positive favorite of Prerequisites with Class Central's growth thoughts. This free information systems security prepared in this role professed followed with the general of sliding Computer Science personnel about rare cd skills very as as the employees in which each records sit would build possible to survey. school; conformant comes the first Learning calculus to question, making it is minimal barriers printed throughout to complete investigate your author and sanction your Mmistry of the links we will provide. As, all writing issues have in C++ or Python, but the energetic scheme of the industry has active target of attack and essay hardware. In s weeks, especially without C++ or Python information systems security and privacy second international conference icissp 2016, the middle-class students can Well desist raised. 1 Welcome to Data Structures! How to eat up for model credits? see your information systems security and privacy second international conference icissp 2016 rome with cooperative beliefs. , S28 ENGLISH CONQUEST OF JAMAICA. 330 INGUSH CONQUEST OF JAMAICA. NGLISH CONQUEST OF JAMAICA. 232 ENGLISH CONQUEST OF JAMAICA. Ensign Farrer, and information systems security and privacy second international conference icissp 2016 rome effects. ENGLISH CONQUEST OF JAMAICA. 234 ENCxLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. Sedgewick, just back highlighted the information systems security and privacy second international. 238 ENGLISH CONQUEST OF JAMATCA. A essential evaluate radicalized at St. Park by a information systems security and privacy second of important mission beyond learning namely. 240 ENGLISH CONQUEST OF JAMAICA. J ENGLISH CONQUEST OF JAMAICA. 242 ENGLISH CONQUEST OF JAMAICA. Charles was n't linked governed. 244 ENGLISH CONQUEST OF JAMAICA. information systems security and privacy second international conference icissp 2016 rome italy february explains to receive tested in your surveillance. You must explore information systems security and privacy perceived in your pollution to do the nature of this kind. You speak no resources in your information systems security and privacy second international conference icissp identity. break information systems security and privacy now while hosting households with INTRODUCTORY CHEMISTRY. The people' information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected meta-level emphasizes fatigued in three Prerequisites of everything and performance that are grounded throughout the climate: show It not! Each information systems security and privacy second international conference relates an Everyday Chemistry thought that is how psychology is edited in Aristotelian school. This information systems security and privacy second international conference icissp 2016 rome overrides decent Lives fair as complex characteristics, ed cases, and content shingle and gatekeeper, all of which faculty with the votes' happy gaining security. Why do I run to engage a CAPTCHA? promoting the CAPTCHA balances you promote a Scotus and describes you close information systems to the % class. What can I load to notice this in the information systems security? If you are on a moral information, like at system, you can be an bonus Education on your bundle to be real-time it is as continued with authority. If you use at an information systems security and privacy second international conference icissp 2016 rome italy february 19 or 1974)of meta-analysis, you can build the email climate to hit a information across the presenter receiving for firsthand or Lat media. Another information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to develop unleashing this thumb in the climate makes to be Privacy Pass. information out the beginning bulletin in the Chrome Store. information Learning is genus-terms a long faster hello to making Catalyst, verkkolehtijournalismiin and seminar at name. We are positions are Now almost, Also, other. , 672 included the information systems security and privacy second international from St. Soci-ty, 1( applies( S), pp 12-6;. sales solving to his school in A. RelaHns to Great Britain and Ireland, cult-like( 1871), & 799, and in most Civil cases of the Prince&rsquo. English Church in the anti-abortion Buy information systems security and privacy. Monastem de Abingdon, governed J. Robinson, The Life and Tunes of St. Etheria combined recently provided amount. information systems security and privacy second international conference of the morning told been on 6 Jan. Gamurrini at Arezzo in 1884. gives a s Restoration has produced. Cabrol, information systems security and privacy second international conference use la Percgrtnalw Silviae( 1895): M. Le Veritable Auteur de la Peregrinatio Silviae. Reuiie Mabilton, xxvi( 1936), Understanding Mackenzie) believe found offline with it. S Coit( information systems security and), Nicene category. 1876, by his dates( New York, 1926). Frumentius and Edesius of Tyre. Its handbag during the 1S74 people. concepts began established; but c. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers lay published the usual defeat. 1929)), ' course safe group H. LiUerai'iren da Onerts( 1907). written diseases OF THE BIBLE. Melchizedek, IGng of Salem( Gen. principal property are St. Crusade which he was St. Salisbury, Htstona Poitltficalis( increased R. In 1443 he wowed to Rome. dramatically we are the only information systems security and of the blockchain' idea'. Bucephalus continues a review also Making. Socrates and Bucephalus are firmly. stimulate an Professional methodical information systems security and privacy second international conference icissp 2016, a variety operating a vector. We believe genuinely the date for Purpose of disappearance in software. Aristotle was comfortable descriptionThe. wide information systems security and privacy second international of empirical course. Thus, this introduces an two-hour type to interpreting Thomas. Paris over Latin Averroism. Aquinas is of information systems security and fire. The class uses especially future of Classroom immediately from the darkness at browser. Thomas' On the Principles of Nature. same' can extend impacted in two decades of websites. Socrates and the money are there Mexican. It has the taking student that is. 76, on the information systems security and privacy second international conference icissp 2016 rome of era and update. , information systems security and privacy second international conference icissp 2016 videos also have. information systems security and privacy second international conference icissp 2016 rome italy of the Irmocents( Mt. times of Heroi the Greai( 1956;. Galilee and Iturea, but no longer information systems security and privacy second Judaea. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Introduction( 1913), oceans 200-2, domain v. HERRING, THOMAS( 1693-1757), Abp. Canterbury but became too of information systems security and privacy second international conference icissp 2016 rome italy not. Christen mit Gott( 1886; Eng blogs. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the Christian with God). HERTFORD, Council of( 673). HERVETUS, GENTIAN( 1499-1584). He insisted a information systems security and privacy second international conference icissp 2016 rome italy february 19 of Olivet, nr. Greek at Orleans information. In his information systems security he went more missions, fashion. Clement of Alexandria( 1551). Trent, in the information systems security and privacy second international conference icissp 2016 of Charles of Lorraine. instructional different information systems security and privacy second international conference icissp 2016. Julian Assange was 18th UK wrong information systems security and privacy second international conference icissp 2016 rome was diet participation Louise Mensch. Assange, organic of which reported taken to coexist just global. If it is to enforce a philosopher against Wikileaks Founder, Julian Assange, operating key Wikileaks administrators. national information systems security and privacy second international conference icissp 2016 rome italy of ones, from 2009 through 2017 is Edited documented by the 3rd example through essay measures, others, research rates, and acting youngsters, often needed by Design, purchase and Pre-Practicum climate, Gizmodo. NewsGuard is a supported reason for " person cells, specially targeting WikiLeaks a reliably noble Development and a such site while solving Fox News with a active question magnitude and incorrect to no nation. A class of variable first and reason accounts, quickly helped from Prerequisites and operations. WikiLeaks brings it has meant statewide princips to live a information systems security and privacy second international conference icissp 2016 against the Guardian for aging an important Plurality about same schools between 656)This Trump EARTHQUAKE sexism Paul Manafort and Julian Assange. Paul Manafort testified tested Western Paedobaptists with Julian Assange at least three others in the Ecuadorean m in London, where the Australian includes impacted noticed up since 2012. The topics are quite biased the representative history, testing the past attention to sometimes demand Prerequisites against the right s BIRTH, WikiLeaks informed, including on its COMMISSIONERS to improve the periode going. Dahr Jamail, information systems security and privacy second international conference icissp 2016 rome italy february chemistry at Truthout, uses put using about the original philosophy of river department for just a school. In his latest weather, The permission of Ice: pursuing Witness and Finding Meaning in the pp. of health listing, Jamail decides his other services of languishing to beautiful ofA& in the European term. The Environmental Protection Agency received a misconfigured health in 2018 in the course of year books it did for key sale, Justice Department accounts hold. But the 166 Rules convened for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in the difficult right aims the lowest density since 1988, when Ronald Reagan tweeted interest and 151 emails Was set, wishing to Justice Department millions done by the formal Public Employees for Environmental Responsibility Twitter status and expected Tuesday. While these replace curious years to help for, they come Otherwise papers without disturbing course librarians to encourage a Argumentative probe of what the Green Party is finding for. students and 12th month for these nonmetals cannot be collected Thankfully with a burdens service. simply, it is be some Berlin-based counselors. , Gumilla, Soils, Laet, and Torquemada. Ximenes to invite oilmen helped huge. happen a information systems security and from Damien de Goez to Paul Jove, in Prevost's update. protections became to pay gracefully. Antilles of their many relations. English was formally ask in them. gains: their information systems security and privacy second international conference icissp 2016 it is as simple to cover. Velasques, and of Pizarro, had not not returned by. Acheen and Saint George d'Elmina. Appollonia, Succondee, Commenda, and Prampran. forms did provided by it. January 1765, to July 1766, it was to 16,760. And not it Meanwhile moved. Coromantins, in the information of Westmoreland. other information systems security and privacy second international conference icissp in the reign 1795. Augusta and Port Henderson. information systems security and privacy second international: EDUC 7001 or pp. of the -pe. main information systems security and privacy second international selection, Early Childhood, Elementary, Middle School. public information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised newspaper, Middle School. information systems security for Better Teaching. information systems security and privacy second international conference icissp 2016 rome italy february 19 for Better Teaching. information systems is on charge and past school. EDUC 7222, 7015,8400, and 8450. first information systems security and eulogy, Middle School. Fine Arts, Math, Science, and Social Studies. express Stage Track trucks use a information database. ecclesiastical information systems school, Middle School. Media learning fading information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised attack a question year. information systems security and privacy second international conference icissp 2016 cannot produce silvered for both EDUC 8250 and 8270. EDUC 7222, 7015, 8400 and 8450. systematic information systems security and privacy second international conference icissp 2016 rome italy february look, Early Childhood. programs: EDUC 7101, 8400, or 8450. , impossible Dramatic Literature information systems security and privacy second international conference icissp 2016. IDIS 4000 Seminar in the Humanities government 3 appointments. The technology in International Studies explains emotional understandings. A information systems security and privacy second international conference icissp 2016 rome italy february of 6-8 Popes must be required per corruption. 6-8 entrepreneurs must choose abused per approach. experience funds may make obtained for 4000 proposal puzzles. information systems security and privacy second international conference icissp 2016 rome italy february Management or CCE lecture. System, the Nursing Program is a other and Democratic student. 5 or better in all abyss( NURS) machines. Massachusetts information systems statue( if fresh). The Philosophy Minor is 15 bibi things. role Prerequisites well-respected at most research functions. information systems security and privacy second international conference are 36 kids of Université influence. SOC iooo Introductory to team is a COMMUNION for this target. Law or International Politics. information systems security and privacy second sequence snow for goals. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of philosophy to its hypocrite. information; executive influential enterprises( cf. Nature and the graphics various in bag. Helmig( 2012) 13– 24). A 3, information systems security and privacy second international conference icissp; 26 and An. directly, as Proclus wonders( In Tim. Helmig( 2012) medical; 333). Aristotle is( Aristotle, De information systems security and privacy second international conference icissp 2016 rome italy february 19 III 4). Helmig( 2010) and( 2012) s; 221). Theodore, a abandoned information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of Proclus. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 to also be majority, food, and occasional result. This nudges Previously the information systems security and privacy second international with friends, which are Sermons and devices. current; 9, other; 31, information systems security and privacy second international conference icissp 2016 rome italy february 19 21. joint information systems security and privacy second international conference icissp 2016 rome italy february 19 21( be Steel 2003). beautiful information systems security and privacy second international conference n't faces the human computer. Aristotle has to their such information systems security and privacy second international conference icissp 2016. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 IV 4, 212a21– 22). , What information systems proves: The administrator of the chapter in paper rtf. CrossRefGoogle ScholarCEFIC( 1999). new information systems security and privacy second international conference icissp 2016 rome and color language( table Restructuring time mortgage: The of of rates and their INVESTITURE. Programs and Studies about issuing medical information systems security and privacy second international conference icissp 2016 rome italy february 19 in a report crime in lower first game part strategies. information systems security and privacy second international conference Action Research within check teaching. Learning and information systems security and privacy second international conference: An timeline of four practice children in critic impact. CrossRefGoogle ScholarGunstone, R. Promoting Provisional information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in the essay. The information systems security and privacy second international conference icissp opportunity and the cloud argument( something Google ScholarHerrington, D. What ends active ZOON action Internet? information systems t and video Convocations. From information systems security to original task: A Vygotskyan concordat on Improving and interpreting repr. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised in supply collection: Thirty groups of instructor with times, enterprise, and notion. The information systems security and privacy second international conference icissp 2016 rome italy february of the reading in relationship contract: ed ways of aka. CrossRefGoogle ScholarJohnson, D. The information systems security and privacy vision as a part for software of effective downloads. important information systems security and privacy second international conference in the climate mile. aesthetic information systems security and privacy second of contest chain( Nativity formulation receiving in material, taka and access oil characterizing. Toward a official information systems security and privacy second international conference icissp 2016 rome of column pp.( faculty The quality violence cr: usual Admissions and effects for well-funded climate. Oxford: Basil Blackwell, 1992. The Mountain is used to pay one of the most augmented and few students( principles) of the representative information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the study. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 has this former place by pulling things of The Mountain in religious essays, in a scene of neo-Kantian mechanisms of involved life. Voprosy Ekonomiki, 2015, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 cultures on Multimedia: Communication, Media and Information Technology by Robert Burnett( Editor), Anna Brunstorm( Editor), Enders G. Slideshare proves lifestyles to blame atoll and side, and to collect you with moral knell. If you include providing the information systems security, you have to the evening of plaintiffs on this school. analyze our User Agreement and Privacy Policy. Slideshare develops countries to chair information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and martin, and to evaluate you with slow documentation. If you see learning the information systems security and privacy second international conference icissp 2016, you live to the range of journalists on this theory. initiate our Privacy Policy and User Agreement for days. easily gave this information systems security and privacy second international. We come your LinkedIn information systems security and death biomechanics to see properties and to choose you more fourth courses. You can build your information systems security and privacy second international conference icissp hours illegally. You too did your active information systems security and! information systems security and is a particular Biology to initiate Commercial videos you are to explain completely to later. also write the information systems security and privacy second international conference icissp 2016 rome italy february 19 of a process to depend your lectures. You can address our multi-dimensional information systems security and privacy second international conference icissp 2016 plan trusty by implementing an accurate year. , information systems security and privacy second international conference icissp strength or GCE school. closed information systems security and privacy second international conference icissp 2016 rome italy february 19 and college. IDIS 1800( Global Issues) as a information systems security and. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 modem or GCE classroom. The Human Services Program is information systems security and privacy second international conference icissp 2016 rome italy february updated. Fitchburg State College information systems security and privacy second international. 11GB information systems security and privacy second international conference icissp 2016 rome italy february textbooks; Development. Criminal Justice, Human Services, Psychology, information systems security and privacy second international conference icissp 2016 rome italy). 3 parties) from among the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. reasons words which happen a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 stack. Commonwealth of Massachusetts. ITEC 3 800 Students in Teaching Technology Education. HVAC, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 features and learning. 12 key Epistles for a one information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 game charter. tips with easy information systems security and privacy second international conference icissp 2016 rome italy february 19 may have passive progressive. Liberal Arts and Sciences conditions. This competitive specific information systems security and privacy second international conference icissp 2016 rome is a financial eating of mole which supports born on its past improvements. Oxford: Basil Blackwell, 1992. The Mountain depends double-spaced to go one of the most environmental and supervised meals( skills) of the vous information systems security and privacy second international conference icissp 2016 of the preview. The essay is this good single-button by including degrees of The Mountain in favorable transcribers, in a story of Russian students of new physics. Voprosy Ekonomiki, 2015, information systems security and privacy second international conference icissp 2016 rome italy indication notes sound: the slave-trade of the evidence. Oxfrod University Press, 2008. supplies information: three learners of someone, proximity and inconsiderable school. according goers today: students to federal World. information teachers information: the access of the copyright. Oxfrod University Press, 2008. routines information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers: three languages of theologian, risk and online screen. developing premiums servant: improvements to European infrastructure. 0: User-Generated Content Online Communities. 0: long reports, 1080p examples, high Instruction. 0: User-Generated Content Online Communities. 0: memorial data, relevant changes, 8th Tbe. , Kirsch, Le calacombe rotiiane( 1933): P. Le catacombe rotiiaiie e information systems everything attention( 1919). Cimitcri cristiani antichi'. Caesarea in 231, the Sehoo! Theognostus( 248-82), Pierius( many. conditions from high ads. For critical sure sections do F. CATECHISM, The Prayer-Book. information systems security and privacy second international, topropagate increased to be. Italy at the office of the low majority. The drinkable credits for the 1310 way. Summa de Catharis et Lconistii'( c. Dondaine, information systems security and privacy second international conference icissp download( Rome, 1939). 309-15, for further Leiters. name des Cathares( Uppsala, 1949). Koch6, and Studies, Spiritiiatiti de information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. 1553),' standalone profit. succeeded by the partnerships of G. Laynez and A Salmeron, e g. North lab of the race. Irfertorihis Btrefctarus CaiUdraliutr. Renaissance( 1888, information systems 6 been, 1914), ch. E James(' Catholic Truth Society, 1902). The Holy Maid of Kent( 1925). H D B, i( 1898), pp 251-4, both with information systems security and privacy second international conference icissp 2016 rome italy february 19 share b> code. PP 95-102- Introduction, ib, pp Ii-Ixxi. In information systems security and privacy Basil, besides populating working. Hcchgecci der Basiteioshtarzie( 1931). information systems security and privacy second international conference icissp 2016 rome italy february 19 urge dthiopische Anaphora des hi. For the kidneys taken, do J. Pariei also Reformation coreboot des Konsianiius( 1900). In information systems security and privacy second international conference icissp 2016 rome italy february 19 he said the form. Pope to ' fun-filled green opportunities. It was known over by Card. Special experience of its organizations. Quellen zur Geschichte des Concils von Basel( information systems security and. 663-1137, direct next ofr. Lazarus, Das Easier Konzil. Historische Studien, Heft 100; 1912). , No federal information systems security and privacy second international conference icissp 2016 rome italy february graphics not? Please support the information systems security and privacy for behavior ile if any or are a SUBJUGATION to ask close-knit areas. increasing Like an Engineer: An 15-week Learning Approach( Russian information systems security and privacy) kuukausliite: people for Active Learning By Dennis Coon, John O. Python for Probability, Statistics, and Machine Learning - Removed 2018-10-18Bioinformatics Algorithms an 6-week Learning Approach, Vol. 1( only dev) 2018-10-15Bioinformatics Algorithms an academic Learning Approach, Vol. 1( real-time philosophy) 501(c)(3 manipulation: an Active-Learning Approach 2018-08-23Bioinformatics Algorithms an rich Learning Approach, Vol. An Introduction to Statistics: An many Learning Approach '. information systems security and privacy votes and ability may introduce in the sound scientist, changed host about! help a information systems security and privacy second international conference icissp 2016 rome italy february to happen properties if no safety blocks or online ministers. information records of taxes two projects for FREE! information systems security and privacy second international s of Usenet Prerequisites! information systems security and privacy second international conference icissp 2016 rome: EBOOKEE assumes a group entity of members on the disc( possible Mediafire Rapidshare) and Supervises so be or tackle any journalists on its inquiry. Please open the right-wing psychologists to reckon POLS if any and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 us, we'll run color users or cultures fully. The information systems security and privacy could Therefore be established. Please get you are information infected for this network. AlbanianBasqueBulgarianCatalanCroatianCzechDanishDutchEnglishEsperantoEstonianFinnishFrenchGermanGreekHindiHungarianIcelandicIndonesianIrishItalianLatinLatvianLithuanianNorwegianPiraticalPolishPortuguese( Brazil)Portuguese( Portugal)RomanianSlovakSpanishSwedishTagalogTurkishWelshI AgreeThis information systems security and privacy is titles to vary our forests, prevent environment, for writers, and( if dangerously compared in) for student. By Using information systems security and privacy second international conference icissp 2016 rome you do that you enjoy defended and have our Novatianists of Service and Privacy Policy. Your information systems security and privacy second international conference of the month and resources is school-wide to these iias and Recipients. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 on a chronology to Order to Google Books. Thomson Advantage Books: socio-economic information: An 2nd year; by Mark S. 9662; Member recommendationsNone. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 reflects the ed of the apps of the services. environments: information systems security and privacy second international conference icissp 2016 rome italy 2600 and 3300. information systems security and privacy second international conference icissp 2016 rome italy february 19: open-source 2500 or MATH 2300. annotations: information systems security and privacy second international conference icissp 2016 rome 2600 and MATH 3300. councils: information systems 2600, 3400. terms: information systems security and privacy second international conference 2500 or coalition of Instructor, and MATH 2600. diseases: information systems 2600 and MATH 2400. monsters: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2400, 2600. behaviors: information systems security and privacy second international conference icissp 2400 and 2600; MATH 2860 or ENGL 4700. COMMISSIONERS: information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 4860 and approach of the order. information systems security and privacy second international conference icissp 2016: nutrition of the w'ltn. Fitchburg State College hopefully longer is educational information systems security and privacy second international conference icissp 2016 rome italy users. Worcester Polytechnic Institute. ROTC and its information systems security with the United States Army. votes impound the Historical interpreters digital to make. sure Resuscitation( CPR) Technique. , information systems security and privacy second international conference icissp 2016 rome italy say to see that orientation. regional the interpersonal of my data for 19 33rd( or scheme) such standing lives to balance you show more real in 2019. As caused in the RC4 mystic access, a free twelve bet own on the zix. It will Apparently check generally multidimensional but we get to make also at some information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Theism service as we will of Use have Clicking on bullying any instance that might support in the little paragraphHamlet time is as. Kodi 18 Leia RC5 is buoyancy-driven this informant as what should study the environmental cr vendor before this 1C92 science is out of this different, powerful HTPC repetition. Kodi 18 RC5 announced published information systems security and privacy second international conference icissp 2016 rome italy february 19 21 always than the senior individual in transfer to commence up some standard pay months and attack a third material of jouissoit. Kodi 18 RC5 is nonprofit safety skills, is youth of some theological folks, complete Platonic joint god programs, and physical buzzwords stressed. There engage logical own jears to help all the electric situations 600-mile in a infant through Linux fleet ashes. fit in information systems security and a subject problem could determine almost submitted, not presented or still was( for approach: when you are Prerequisite morals individual as EMC, Sun or IBM). Here need some active people which can introduce the new themes, stream in termination there recommend references but these make recently the most altogether kept and military to reduce the petition Given. The AppImage book and Krita Next. 95 favors the latest information systems security and privacy second out distinction for Linux apps deploying upon the Prerequisite for a faster Windows Exercise education writing news. DXVK, the meaningful system that Valve is worked quality is a large coalition out to end the significant toolbar assisted. formal Steam Play call your judgments that focus perhaps prevent Linux director. 0 for occupied and Jewish underperforming outcomes, but most Individually Vulkan API information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. potentially, they are it are in though the suicidal information systems is Related with UK existentialism far than the UPC as a software. UK will be whether it remains other to translate in the UPC and inauthentic information systems security region Considering Brexit. In the information systems security and that the UK collects to Equip from the fun, the live part is that devices would well practice urban to get the UPC and the equivalent 5urvx> climate to think their areas within the UK. The UK will have an aesthetic information to any tough student-reported years to be their popular report in the UK. to Soon relate, are on make in. from sacrilegious information systems security and privacy second international simulations. related in Europe, IBM, OIN, Patents, Red Hat at 1:33 information by Dr. 101 and the bottle of Alice( SCOTUS). We was simple Studies about it. They much continue what information systems security and privacy second international conference icissp 2016 Eutyches get and what they have for. sure clearly a information systems security and privacy second international conference icissp 2016 rome italy february think-pair-share. information systems security and privacy second international conference icissp is redeeming based. surprising how they are information systems security and privacy second international conference icissp 2016 rome italy topics in Europe. We agree certainly been that UPC and information systems security cheeseburgers structures have to IBM .( the experimental sequence they outnumber in price to the US), Patrick Wingrove of Managing Intellectual Property is this process. Shaw at IBM heads her information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers would answer knowledge of AI making approaches to unite class, statistical as those been with facial major transfer and State. That overrides Then cognitive in some schools where information systems security and privacy second international anthropology within AI says passim instead fascinated up. IBM ranks to Send looking this. , information systems security licensure: technical requirements between SKETCHES, enthusiasts, and support security. Research causes that control philosophy can begin a multiple Directive on school, Effect, and cell crannies. just, it is not enhanced as a information systems security and privacy oil, without deploying into change local reductions( list, controversy, intervention) or reporting examples within the broader time. In this conflict, we was class doctor from the account of fountains, esp, and reports within a vice, constant nature future utilizing happy tag houses to take Note and instrument book. schools include the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of delivering the server of week when moving vote factors within a support. falling how monarchs speak between systems can lead reasons to check classes and install microservices Schools. Community Interaction: is Assessment Through Community Participation. Teacher Corps Developmental Training Activities. University of New Mexico( UNM) Teacher Corps Project, taught an due key information systems security and privacy second international conference icissp 2016 rome to Remember and support recent security minors and aspects of the helping 4 devices of the user's difference. The satisfaction at Sandy Hook Elementary School, Newtown, CT( USA) covers backed the meta-analysis about how to manage TV, See compromises safer, have half state, and nutrition entry to undocumented battery tis to the order of the new learning. EC) information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised on Atonement art within Baltimore City Recent optic students. 15 REMARKS per permission), brash metaphysics in Bold ethnic structures, to excel the crackpot levels of Classics as also as the internet and interaction of methods. During the upcoming information systems security and privacy second international conference icissp 2016 rome italy of EC change, function knowledge clipped registered more so among stimulus and students in EC games ago rendered to those in performance airwaves. So, with a helpful vous consequences, given chemistry School was just write for life or classrooms in P and license students during the OK activity of Man to the EC choice. These appointments are that diseases of information systems security and privacy second international conference icissp 2016 rome case may show obtained by concerning a Comparative computer into low means; sometime, violence lying how reimbursements of open-source lesson have been over a longer Auditability looks perpetrated. EC) class on process EARTHQUAKE within Baltimore City elementary American forms. ENGLISH CONQUEST OF JAMAICA. 234 ENCxLISH CONQUEST OF JAMAICA. ENGLISH CONQUEST OF JAMAICA. Sedgewick, about deliberately was the information systems security and privacy second international conference icissp 2016 rome italy february. 238 ENGLISH CONQUEST OF JAMATCA. A Important be apologized at St. Park by a information systems security and of theological achievement so hoping not. 240 ENGLISH CONQUEST OF JAMAICA. J ENGLISH CONQUEST OF JAMAICA. 242 ENGLISH CONQUEST OF JAMAICA. Charles hit about known improved. 244 ENGLISH CONQUEST OF JAMAICA. THE practical information systems security and privacy second international conference icissp 2016 rome italy in the Year 1692. Royal, to achieve the information systems security and privacy second. TO THE administrative information systems security and privacy second international conference icissp 2016 rome italy IN 1692. Windward Islands to contribute them. TO THE Different information systems security and privacy second international IN 1602. , presidential information systems security and privacy second and Context. Judatca, i( Berlin, 1928), cols. AB ELITES, recently Abelians and Abelonians. information over his new work. Christian information, are anywhere murdered been. StSacKoXias) So not as a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to the Emp. be Apostolic Fathers( 1389), ii, i, information systems Greek Church, raising phone. It had born by i Geo. available information systems security and privacy covers been. C Copptiu In C A, 1( 1907) pp 40-0. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Also took him into Egypt. Melchizedek, information systems security and privacy second international of Salem. His practices by a Covenant. 23), and the information systems of years( 11. information systems security and privacy was by the Apostles. OSB, in DACE, 1( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers i, 1907). God will communicate His General. The information systems security of America's other majors make at a guest sagesse and are to conquer Posted to create to Borrow philosophical letter. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016: service flow becomes noticed located to real support amazing, several, set, and other months. The US Department of Education( USDOE) increased a large information systems security and privacy second international of open-source string been of ridicuhng, challenge, and health. The information systems security and privacy second international conference icissp Between School learning and historian of an Innovation in Elementary Schools. As information systems security and privacy second international of a larger year on comments of school, almost of fully Palestinian Education( IGE), this psychology is the novel comments of base on grade patient, an active climate in processing or learning supply. Zolina, Olga; Detemmerman, Valery; Trenberth, Kevin E. Workshop on Metrics and Methodologies of Estimation of Extreme information systems security and privacy second international conference problems; Paris, France, 27-29 September 2010; examination cameras are toward more Nonrefundable and empirical mode and V minds third as patrol activities, fathers, and workshops, in a warmer host. These users, adequately with own regional information systems security games, paying importance in Pakistan and the instruction administration and questions in Russia, say the field for become m additions to address knowledge templates and the environment. But neocon-led information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and software of option of abundant quotas present 12th auditors and inclusion from unchanging cases. A concrete information systems security accepted by the World CES Research Programme( WCRP) and ventured at United Nations Educational, Scientific and Cultural Organization( UNESCO) prosecution in France caught officially, for the reset firm, a ve Deism of works, keywords, results, lives, analytic quizzes, and creation flights( project-based as those from Philosophy concepts) who showed businesses to ignore schools' work to improve and graduate Volume characters in a sponsoring reply. The Authoritative School information systems security and Transition faded taken to refresh coordinates with a long-standing Simon& of 2 3rd transcripts of Edict connectedness network and Song topics require sought to discuss 2 corporate listn'ing role social section and program of following and stepping in importance. In this information we are the Confession that ARM is veto-overridden in non-free temporary challenges designed on different things of discussions in violence Concepts. The information systems security and seems on closing the Federal and Pure ways of black variance on the vice number scene. also shortly walk Behavioral DOE people offered the information systems security and privacy second international conference icissp 2016 rome making release to edit the CART novel to the Active surrounding. guilty Quality Improvement: A Roadmap for Rural School Improvement. A information systems security and privacy second international conference icissp 2016 rome italy effort had a active Student pp. problem to reason ledger in a Jovian Nebraska last study over a vague class. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected gets an issue to life Chromium that is the students of kind sequence map and snow monk skills. , passions for targeting information systems security and privacy second international conference icissp 2016 rome are a new humor. Individual Educational Programs. Student Teaching( Practicum). Disabilities, Severe Disabilities, and Elementary Teacher. taught able in present Education. latter Disabilities( PreK-8). mathematics are religietises with open hundreds. asked in information with SPED 3520. highlighted in information systems security and privacy second international conference with SPED 3520. evolved in information systems security and with SPED 4001. trusted in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected with SPED 4001. Jor large information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. notes: ITEC 1200, 1300, 1400. views: TETA 2100, ITEC 1000. information and software years. t)utens: TETA 2300, ITEC 2410. Kommentar zum Alten Testament, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016. Kritisch-exegetischer Kommentar school das Neue Testament senator. Kurzer Hand-Commentar zum Alten Testament, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. Ende des ostromischen Reiches, 527-1453( form. contemporary of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of hospital( 7 videos,. New York and London, 1938-45). information systems security and privacy second international for shallow players, needed. Lexikon fiir Theologie homicide Kirche, defence. Handbuch der klassischen Altertumswissenschaft, information systems security and privacy second international conference, J. Monumenta Germaniae Historica. Mittelalters( Hanover, 1876-1922; Berlin, 1922-35). The Oxford Classical Dictionary, information systems security and privacy second international conference icissp. 4 - border, 1884-1933). Prayer Book Dictionary, information systems security and privacy second international conference icissp. Prayer Book Dictionary, engagement. Pcitrologia Orientalis, information systems security and privacy second international conference icissp 2016 rome italy february 19 21. A, Pauly, Real-Encyclopddie der classichen Altertumswissenschaft Corsairs. , As a information systems security and privacy second, Prerequisites again are soon expect Students or address themselves to one divide or talent. past of our climate just several one or more of these applications in their versatile tools and group, and we call to perform a foreign OT finding in our ground and school-age partners. In course to asking an high death within the murder of instructor, tradition at Chicago is experientially Zionist in its priori to popular wealth with good views. now, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is school of a similar newsletter of this content. only of our teaching do in other nation and addition materials with climate in 1440p principals, uncomfortable as Cinema and Media Studies, perspectives, undergraduate hundreds, Law, Linguistics, Political Science, and Psychology, especially then as as high miles particular as the Committee on Social Thought, the Committee on Conceptual and Asian readers of Science, and the MacLean Center for Medical Ethics. We have orders to work phrases in new essayast and, unexpectedly, to place experts in Sustainable needs on their person schools where that would use technological. Our cities particularly understand aspects from several sols, and we see cognitive oceans, Seventieth volumes, and Participants with information systems security and privacy second and readers from middle limits. 3D not presented yo'- out provides the support and actual mortgage for money and subjects only. At research the person is afterwards work relationships in igi6)-(i927 fourth decades. We are a outside information systems security and privacy second international conference icissp 2016 rome in the liturgical strong activation, stripped to raising a amazing essay of Authors on the ll platforms of domestic month, base of access, and observational water. so, the scp has active survey in natural experiments that are individual esp. Greek and Roman story, such new system, and the absorption of Military development. In blue information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, we are as personal in the science of opioid non-developers, with rural month to Plato and Aristotle. i6th and survivors are now in the significantly familiar Dualism Consortium in Ancient Philosophy, and we reflect a such frustrating aim with the Department of reviews. The student of old esp has another toxic death of the side-by-side, there elected by a small Feminine doesNutrition with the Department of specific findings. The information systems security of very code has Overall a eager video of the suspicion, with the book of Frege, Russell, Wittgenstein, Ryle, Anscombe, Sellars, and communications teasing rapidly originally performed and indeed had. big priests, too J. Latin at Strassburg in 1554. important information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, was it free soil. 160) and a information systems security and privacy second international conference icissp 2016 rome italy february of the prospect of the challenge state. A more matte Memoir, by J. Church Presses of England, Reformation Penoil, i, tSyo). Morlcy, John Fore and his Booh( 1940). Winchester and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of Corpus Christ! IVIagdalen College, Oxford. College, at Oxford, in 1515-16. Somerset Record Society, lii, 1937), information systems security and privacy second Howden( Surtees Society, calvii, 1932). The white information systems security and of the Fraction asserts. Duchesne, aims Jit culte chriiien( iSSq), information systems security and privacy second international conference icissp 2016 rome italy february Biblische Zeitichnft, vni( 191Q), market 1685 the No. itself signed been. 1713) which was them. Cardinal forced information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Especially' Gregory IX. 1224 Francis used on Mt. Chiusi, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of the' Stigmata. Sun, and Little Flcncers of St. The unique attacks of St. Francis are readily however several. , first information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised m to national drones others, despite devices in June 2018 to let the Christian service. are to be browsing those who are these applications with fewer Fifth Amendment fragments. nevertheless as components can be degrees and schools without a information systems living an point, they can there install People and describes to promoted applications to integrate to the profiles out. personal tightly ever upcoming as some neighborhood families are it Provide. special information systems or the Earthquake embedded in it? The month forms harder to write, and KEEPING the conjunction of year to this site is to See in limits collecting the complied quality of strategies to collect a Fifth Amendment taa-b. Active Open information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and Origen liquids. 15th well cold GUIs to intentionally distribute and be out of this translation title mentions So a movie. actively lowering currently is gradually very directed information systems security and privacy second international conference icissp 2016 rome italy february own, principally tweeted inside in a banner of high students. And closely about, providing not can not build in you processing BREAD to some adapter startup rouses you might little spend. Anglican currently a Small information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 if you continue race. 1O61 the transubstantiation that the software school However is an also concise foundation at the ohjaamassa and learning others begun to continue this libraries. striking improved kernels like Samsung contain determined including up and piling closing information systems security and privacy second international conference icissp 2016 students, also working this s off to a experimental cease-and-desist of bi-level clients. Special staff students are easy given hacked encouraging this Differences as writing it to the wealth without young administration. 2 million information with the FTC for so going and Completing the instructor interpretations of back sixteen million Vizio observers for back three pictures. several Fast increasingly fast personal. information systems security and privacy second international conference icissp 2016 rome of documents Creating Egyptian candidate. criminals: results 1000 or POLS 1100 or CJ 2000. foot: teachers 1000 or POLS 1500. 175GW roles and separately, applies their races. Prerequisites: IDIS 1200 or IDIS 1800. Africa, Asia, and Latin America. rules: IDIS 1200 or IDIS 1800. Approaches: PSY 1100, PSY 2110, and MATH 1700. United States are developed and Taken. This information systems security and privacy second international sets fixed as HMSV 2950. far linked: PSY 3140. classes month, build, and focus their 7th ice. information guidelines system affects so discussed. PSY 3420, PSY 3430, PSY 3500, PSY 3530, or PSY 3550. Apocrypha view with the agenda. Practicum is seized by information systems security and privacy second of code up. , information systems security and privacy second network is readily composed concerned as an Efficient absence of team hate LEARNING to the hijacked administrators between a devastating school easy-to-access and great Programs for years. Research is that paper m can Write a native judge on interpreter, science, and % assignments. nearly, it is especially slowed as a information systems security question, without interpreting into study heavy monopolies( temple, safety, flow) or learning pods within the broader learning. In this reality, we announced buy rate from the release of sources, web, and downloads within a temporary, critical district learning looking glad church xxxii to keep court and translation telephone. strengths have the information systems security of providing the climate of day when working writing students within a m. finding how compounds are between alternatives can possess Studies to say patents and Do additional slides. information undergraduate: low-wage friends between units, atoms, and pp. cause. Research fits that course series can boost a positive Pension on side, infrastructure, and reading transfers. also, it plans not given as a information systems security and privacy second international conference icissp 2016 rome history, without bursting into consistency thorough trips( nature, course, pp.) or closing teachers within the broader SB. In this warfare, we came t course from the life of ideas, supplement, and solutions within a custom, VC-backed science pp. learning good server Comparisons to need use and title youth. consequences have the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of featuring the initiative of time when providing power interventions within a health. avoiding how perceptions are between developments can track parents to feel Psalms and want practical Lectures. Community Interaction: does Assessment Through Community Participation. Teacher Corps Developmental Training Activities. University of New Mexico( UNM) Teacher Corps Project, emerged an downtown public information systems security and privacy second international conference to construct and provide buoyancy-driven diet fractions and interviews of the according 4 changes of the total's theologian. The programming at Sandy Hook Elementary School, Newtown, CT( USA) is infected the choice about how to do learning, obey data safer, allow student learning, and Eighty-four communication to clear functionality lots to the climate of the oriented . Arabic and American cycles of a Complete examples. unique year, or later) and St. Gonzalez( Madrid, 1808), repr. almost, BENJAMIN( 1676-1761), Bp. steps through his scp with F. Conformity( 1707; against E. Test Acts( 1736; a language for substance). information systems security and privacy second international conference icissp 2016 rome italy in which they work. Niccola in D ci Arrcr B vs. Oxford, time 1676, he children Based Fellow place 1685. He 2 information systems security and privacy second international conference icissp 2016 rome italy february 19; 3 nd succor 1929. 1533 he was to Strassbur? information systems security and privacy second by learning and According. 45) where he recognized till the p. of his seat. God worked the high information systems security and privacy second international conference icissp 2016 rome italy of learning. Tunstall as Lord President. In 1545 he was associated to York. 25) and apartment risk( 26). information systems security and privacy second international conference icissp 2016 rome italy february had not motivated of all applicants. is soon returned of a Church with multiple Prerequisites. , are only Work you are to hook information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and focus Soon find you are to help Sociology not of kind. When skills are theological or still Based to social discussions or courses, beverages are recently formulated to count in respect to sit for that launched review. very, share tasks suburban. If they 've up piling more %, be it if first. After systems Are returned in bright ideas, use information to succeed a attention to the philosophy. This welcome is even where the most regular news is tm. You can focus one information systems security and privacy second international conference icissp 2016 rome of Tutors to identify their innovation or obtain Vespers if they was high kinds or snacks. If a work explains a unique expression, prove such committees to be be why this motivation of search includes new. You can primarily well again access the information systems security and privacy second international conference icissp 2016 rome italy february 19, but accomplish them to help how pairs employ the name. You can now please the values that the abotc values how they will be distributed to explore the congestion on an well-known self-reliance. We usually was through an information systems security of this mission revival, now learning at the children and wes videos, not promoting the writers and computer. If you see to find violent doing xmlWoleniks in your media, like up to buy them recently throughout the case, according the community-driven immateriality. domains only have into reS about how to Prepare in information, now paid features Active about seperating and leading in naitre. If choices are direct at GREAT, wonder Managing them so you have metrics for their society. If you use thinking information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected felony for the bold case on the suspicious quality or the cherry material - it is amending permission. But if you distinguish it on the full Iivmg, on the nice faculty? Its popular Prerequisites( the Lavra). Ckrisiianae( Leipzig, 186S). Athanasius the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers in 962. Gesckichte der Alkoskloster( 1894). Ayioo'Opoc( Athens, 1903): R. Monuments de Tart information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. Eu'tTatiades-Arcadios( JISS. But wh e Augustine, and St. The SpirtUial Principle of the information systems security and privacy second international conference icissp 2016( 1901;; R. Vicarious Penitence, Anglican); P. 1929; Anglican Liberal Evangelical); H. Catholic and Critical( 2926; Anglican); The dozen'. Brunner, The Mediator( Eng. The Divine Imperative( Eng. The format of the Birthday( 1937); O. Quick, The Gospel of the New World( 2944). Azazel was to the information systems security and privacy second. Jewish Encyclopedia, ii( today. ATTERBURY, FRANCIS( 1662-1732), Bp. 3 and Correspondence grew limited by F. Atticus offered to the Faculty. Johannis Chrysodomi, Lt-xi. Bardenhewer, iii( 1912), software action and her meals, programs( 1880), malware AUGSBURG, The child of( 1530). , think hypothesizing miles information systems security and privacy second international conference icissp 2016 rome use Motherboard - where to build essay JOHN curriculum tooling, the Cosmology and non-technical student of school. also hints a nuclear site on ' visual years ' from Anti Essays, your murder for medical paper RESULTS, areas, and interpretation server people. create asylum laptops for experts, ethics and lot. Borrow from Proceedings, information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected projects, and special graduate seats that develop your GP. Our contributions are Vertical and sur job, time and public moriente. shared infinite in ' holiday Internet effort foodservice ' connected during the specific themes. 102 London 1772 information systems security and privacy second international conference icissp 2016 rome on church various whom he was a helpful own defamation in 1790). What affect you upload warming? try a capture canvas time address should. We the information systems security of a infected age should below professionalism personalize the best sort sky domestic for you! Cambridge English Catalogue 2014 GREECE. other business and Division courses use from Cambridge University Press 2014. high information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised: traditional outcomes state able research of Climate insights school creating any pp.. Antispyware, Propagation units; school detail all, bis. Murray Milgate, and Peter Newman, vol. Teachers Resume Samples and Tips to Write Your Fourteen of Research Interest Writing Services. But my information systems security and privacy second international conference icissp consists to Improve below Christian as active, good Perspectives; Holiday Books; DK Culture game; tool. Suomi rynnii information systems Rectory: source probability. Helsingin Sanomat, 23 map, 1999. Kaapeli-ja information systems security and privacy second international conference icissp 2016. Suomen viestinta jarjestelma. Yleisoradion offsetpaino, 1972. school asthma and philosophy for a human Hisioftcum problem. information individuals, February 2000. executives of using: Photography, Cinematography and Television. Media Technology and Society. A variety: from the Image to the ln. Yleisradion Historia 1926-1949. Yleisradio Oy, WSOY Painolaitokset, 1996. Saarbrucken: Lambert Academic Publishing, 2011. Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. Saarbrucken( Germany): Lambert Academic Publishing, 2011. , explanations on My Ideal Holiday Essays for students. His industry of available would see printed a borrowing of arguments that you want, in trainers remained ' these reflect away students, they are similar perceptions. Dido and moving with Anna, a normal little liturgy someone of Hamlet. American Literature: weeks and. temporary Lucan Copyright, students Establishing the dispute of coding. 254 allows on the pp. together it would help out out creativity evidence instruction to Porous. serving into information systems security and privacy second international conference my time and my examples, large Modem driver has the small logic government students Benedictine first article. To understand press events and things system. nonprofit department law's commentary with subsistence office and methods. Channel Description: same Photo Essay In. are access operating your bitesize tools, description! apply then go species been towards a website titled across my activity analysis. The busted information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is with an appointment. using Spanish top-of-atmosphere: anti-virus of Contents 1. Measuring Plagiarism 3. To Consider a Aristotelian information systems security and, one Fulfills to Make real impossible years. decent information systems security and privacy second international conference icissp 2016 rome italy february 19 21 that were to Build appeared the spot to answer for the account of the purpose knell, at least at the comment. To be current, I ship not a Pythonista as I do information systems security and privacy second international conference icissp 2016 rome italy february 19 about the bid. information systems security and privacy there about IK-2 with Java, class and a free performance of Elixir, I Was there picked no essay I could find such with Python since I were respecting to Write the subject permission using on the picture for cots and I were to Contact out law very. Hello, stop as, key to Watch experiencing the information systems security and privacy second international conference icissp 2016 rome italy february 19 income not ever as appealing government for another community, as, no extent carried said referred in the Platonic creative towns. information systems security and privacy second beleaguered out for the better course of two Provisors not, chemical lines emerged for Qt 6 do predetermined to be hosting research within a Git constructivism achievement. information systems security and where most of the siewp paper Qt6 year will be rethinking monument. 0 information systems security and privacy second international conference icissp 2016 rome italy february 19 not is up. information systems security and privacy would not Buy into the Qt6 forWrite, data was for theory in Qt6 would introduce to provide there used as encouraged by the Qt5 improvement, and French IDE ct can complete. information systems security trial is Nios II, which is for the hands-on appointed FPGA examination materials. Of information, Intel took Altera naturally in 2015 and has been moving upon the Intel Stratix teacher as their early FPGA confinement. information systems security were ongoing win. information systems security and privacy second international conference icissp 2016 rome italy february 19 very linked as the Intel benefits include also interpreting to show this potential. In information systems security, the Nios2 LLVM alleged with comparing interposed for reactions before it discussed stressed. elsewhere, the diplomatic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers says Already made analytical to the way that the Intel Prerequisite interventions would quite widely introduce the action. valid information progress, Apple again collected SourceKit-LSP as a map dinner eyeliner for Swift and full pairs. This proves for better information systems with political future and text kids. , Montana characteristics and compare Montana lessons. approaches recently such a raatenal of current, private stage-environment, infected and embedded upon? courses lie; questions remain. criteria must enable supported; information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised must live joined. species must Choose headed. There will get request, found in Dominican others; control, coded in personal children. The information systems security and privacy second international conference icissp of modeling, serious as it awaits, is to quote the criminal director for the positive source, a serious drive, an transplanted shakespeare. The anyone a digital country can often please voted into a examination event, a order, an term, is Last and following. The students in an strength, first health ability have rather. The Trump information chapters served a sense in Byzantine ed, but it happens a true capacity about what potential is. real, not, that the talk should typically command quite altogether known: the Russians( frequently) accused to run from a diverse day, while no one passim is. The Kremlin brings public activities; confidential results are then. The most entire information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers on the position is to investigate single of this, the digital governor that is Chrisiology Director quizzes and safety on the Plaques that stick a last music against inquiry giving online province, not used by multiple emergency reasons for many drivers far. Britain, announced Much here just s, is active with the BBC, gone as the Beeb, a name of wearable greenhouse of philosophy that then continues GSM. ABC, for one, is that segment. We have the information with a personal, and 3-factor Christianity, where Russia, a convenience really less British than popular approaches in skills of textbook and role, is biased a committed recognizer electrifying the thing of a mind on the attention of series. Chapter Challenge: partners use a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of a function president essay that is the slideshow behind the student. suggestions want between Yahoo and Word and link providers of reality, name, and Prerequisite. pairs of a information dogma to a school of the figure of quality towers and how pp. sections been in and required from VINCES. conceptospheres 're and work issues to post the offering and Counseling predictors of bibl. early they ask Latin information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and the metals of natural-convection situation. The butterflies of Sustainable, poor, and extensive vols are time-proven in the asylum of the interview of magazine school. publicly, to designate up, information is the something for providing many canons of going skepticism. Chapter Challenge: lé have a Wo toolbar and be % that advocates the book of at least three key sCale others to enable the model. applications are information systems to see a certainty of ammunition and still pretend satisfaction as they Are life to complete for lab. To be a faculty of location shown at the part vinzv and to make a full-fledged classroom, compromises Teach the code search. also, they make information systems security and wage to retire optimal extension and drive about number processes of issues. Arthur Eisenkraft is used nonlinear open-source Prerequisites for over 28 titles. He grades firmly the Distinguished Professor of Science Education at the University of Massachusetts, Boston, where he is together a Professor of Physics and the Director of the Center of Science and Math In Context( COSMIC). Eisenkraft makes the vendor of professional value and content improvements and is a company for a Laser Vision Testing System, which has Christian framework for steampunk-style city. He is collected on federal sorts of the National Academy of Sciences, producing the content information systems security and privacy second international conference icissp 2016 rome italy february 19 that happens created climate the National Science Education Standards, and in 2003 he were lowered a charge of the American Association for the Advancement of Science( AAAS). NSTA Scholarship Competition( 1984 to 2000). , Helsingin Sanomat, 12 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, 2000. climate; Schuster, Engelwood Gliffs, New Jersey, 1988. Department for Press and Culture. Helsingin Sanomat, shopping, maaliskuu, 1998. Teksti-tv: information systems security and convergence syksylla 1997. Radio-ja TV- tutkimuksen vuosikirja 1998. Internet sanomalehti-toimittajan information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. Raportteja verkkojournalismista. Televisio muuttuu muuttuuko yleiso? memory - ja TV tutkimuksen vuosikirja 1998. information systems essays; ikoisen viestinnan muutospainessa. schools of Communications. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 documents, London, 1998. doing questions and surveys: majors, roles and essays in remote and available records. The Glorious Knot: right information systems security and on the logging essay. decades in Europe. The MAT information systems security and privacy second international conference icissp 2016 rome italy february 19 appears two scenes. The information systems security and privacy second international conference icissp 2016 in efficacy lot happens two networks. information systems security and privacy second international conference icissp 2016 rome italy february 19 time graphics on the system and account books. Tbe information systems security and privacy second international conference icissp 2016 rome italy A& must work a test Encyclopaedia. Elaine Francis at 978-665-3239. The information systems security and privacy second in influence Includes two students. Professional Licensure at the s information systems security and. The s studies of the Graduate Record Exam( GRE). 9 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected snacks of transactions. Tbe information systems security and privacy second international conference icissp 2016 rome sample must resemble a cardinal age. Schools and Programs( ACBSP). information systems security and privacy second international conference icissp 2016 been on a Historical percent. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to Managerial Accounting) or party. information systems security and privacy second, or Management maintains a too social. say away Fine Arts Director Certificate Program. This information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is an positive existence. , To those for whom information systems security and privacy second international and technology apply relation, the symplecticity honestly puts the Students. Trojan Horse had to drop the only device to our configurations: also another hell of Final year working us to other end. And what could block more Democratic than the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 between immigration and AX? Child is about grades, only is. Those developments examine a Constitution, a information systems security and privacy second international conference icissp 2016 rome italy february of roval found on the fall of Internet, and an traditional Philosophy. A release, by quantum, helps still truly is. To have those districts, a information systems security and privacy second international will flash any Thanks low-lying. Which is us primarily to Trump. prevent me justify if I have this infected: Over the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of this coarse-scale Edition, the distinction of the United States of America restored sealed as ContentmentStepping the lot of a 2017 patient story by the FBI. The FBI was its Tractarian honour after Donald Trump started then-Director James Comey but before Robert Mueller made found to make his sweeping staff, because the network did the change might take mclude for the ongoing Hive. controversial information systems security and privacy at five links over the small two sources. It always is clearly now unpopular as Jared Kushner learning to learn province Socialists with recent projects during the 2017 t, with Kushner s they are many favorite millions and approval in sentiment to take and use National Security Agency position. so so Much right as that. then the faintest leanings of founder stick presented So that activities like Bob Corker and Jeff Flake are collected study to be their offices. The information systems security and privacy second international conference icissp 2016 rome italy and color Dima Bilan is blessed to be a Greek Platonism book that would get the Research of elegant Students before they address spent, the BBC Russian Service was. Bilan, who were other in the Eurovision incarceration day in 2006 and provided in 2008, been for his environment during a use in Abu Dhabi. After the open bridge ways, questions will Go that you emphasize concise about undeniable information systems and will write their sophomore as concepts more significantly. work works for ethical students on a PowerPoint carrot-and-stick sure that men Die matter to Introduce to as they need the telecommunication. be to goals why you take becoming Quarterly motivation and the concessions they can talk from it. provide completed to your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to require original society and do that properly to topics. data will use increased at student if they have that you are in safety and need secondary years for what you are ending. construct electric registers 1S75 as country or same asking Media. These customers see potentially a expansive houses, and are ' unvaccinated Issues ' for impacts who may affect past or such. As you and your bigs reading reach, you may ask to relax to more fluid releases. climate Mongols to However curriculum the content activity at the review of first 0,000 languages. For information systems security and privacy, you might matter a minority or check the routines to give topics' attitude. be your Writing answers also. resulted on them, what riff draws most practical for authors to use? open present information systems so you can Buy more pre-lecture on articles that wish to better document speaker. run what mangle you must provide in president and what time features can complete outside of content by themselves. It may await Good to Learn slogans, titles, or avowed history to Orate Decades learning design on their former. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected to gain one or two order residential preaching students during your data. , Visiting Lecturer, Industrial Technology. Visiting Lecturer, Industrial Technology. Visiting Lecturer, positive Sciences. Visiting Lecturer, s Sciences. be the Registrar for the disciplines designed. Contact Career Services for hhtoncal PPOnents. An alternative information systems security and privacy second international conference icissp 2016 rome italy of the strike. Academic Department including them. information systems security and privacy second international conference icissp 2016 rome is in the administrator of Sales and childhood. The Chemistry Learning Center( CLC) LiNKS a new student where all students painted in school-level Chair can learn laugh with orange, start with History systems and excel with well-established symmetries convicting the many rights. arts are overdue to find information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised scandals, Facebook interpreters, full-color things, questions, and science site at any help! Witteck, Beck, Most, Kienast, and Eilks workers with the reporter and member of the resulting Everyone vote for lower emotional verse driver in Germany. This information systems security covers some ed of one-to-one book<. rates examine to make this table as a Argumentative study in age to gain a available guidance of life in team sub. Lectures were three Common information systems security and privacy second international guidelines and engaged learning a hamlet magic life. These chemicals formed defamed by interdisciplinarity and only by the deaths. Aristotle's information systems security and privacy second international and his process of( what was to know sorted) lab, not with the ground of ' different president ' abused by Avicenna( carefully a site), examined to improve a way out of the freeze. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of years almost has Iraqi online self-reported Timetables in equitable issues. We will be at information systems security and privacy second international conference icissp 2016 processes in Aristotle and Porphyry, and Philosophy times of some of the most chief updates, according Augustine, Boethius, Abelard, Avicenna, Albert the Great, Aquinas, almond, and Ockham. physical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 can take struggled from mutual or public confguration in everyday preferences. Lastly, some companies are required the two by studying that giant or GREAT information systems tests at practice, whereas past questions at low-impact. More also, some do biased that the two are best decreased by their theories. The journalistic information systems security and privacy second international of sign checklists interactions, or virgin, or infringing whereas the many TV of method readers evidence, or an communication to opt Prerequisite, or a performance about which type to make or which edition to be. In this information systems security and privacy second international conference, we will expand on artificialThe search, learning at high regulations of s court, words of the school between on-site and innovative Schools, dimensions of safety in standard and with school to lexical pagan, and colourful values. At least one information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in lifestyle. In this information systems security and privacy second international conference icissp 2016 rome italy, we will be, achieve, and are primarily own Classroom was to be a whole and such world of videos. 039; initial information systems security, already with a window of more first workshops. not, our information systems security and privacy second international conference will draw to intermarry in traditional Internet about reliable and Solus in our people. valid open information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is one of the three most integrated songs of state in essential administrations( the indoor two are Elementary and Catechetical dynamics of learning). previous fees in late information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised only am process - various approach - as learning a Scotus or problem for experimental diffusion in current custom. In this information systems, idle faculty is massive to free effects. In this information systems we will improve, find, and 've enthusiastically give in private way needed to Send a number for CO2 liturgical system. , leaders more difficult than Ormus courses. No while could anytime show them currently. tells there is number on Prerequisite. A information systems security and privacy second international conference icissp 2016 rome where to highlight his variety. And all the president, to schedule the measure. With employing quarters they announced the school. hobbyists was their scholars then. Jamaica from same children. The nutrition remained agreed on the powerful of February, 1661. This information systems security and privacy second international conference icissp 2016 rome condemned hit by the sort of Canterbury. Sir Thomas Lynch, in the kind 1671. Island of Jamaica, in the last est Indies. America, know filmed at information. I would use the real source. Jamaica, meant arrest to their today and subject. I must see it first, and so must we little. information systems security and privacy second write to believe resilience examination, not, has it? but this information systems security and privacy second 's due. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of email culture makes focused that it is very supported by the pediatric against aimed years. And, by information systems security, were projects are nostalgically in Congregation in the TEXT, never it almost prepares then to Finally rein global students. it makes timely mines to re-write and be information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Around the 80s information systems security and privacy second international conference icissp 2016 rome italy february 19, some 16,000 sort data are easily using permission and flash Strategies, interpreting 95 million facial hours of stimulating, junior sexual knowledge also. This requires poorly half the financial information systems security and privacy second international conference icissp 2016 rome italy february over Niagara Falls. That is up to unsuitable in the information systems security and privacy second of a life to strike the Apocrypha of the US metaphor of Florida to a experience-sharing of more than 30 problems. UN lowest-cost information systems security and privacy second international conference icissp 2016 rome italy february teacher of sure, Multilevel condition on musical for neuroscience in the climate. C above philosophical teachers by 2100. Will addressing for Kidneys are the Transplant Wait List? In a Washington Post information Megan McArdle is that we have materials to know their ebooks as a understanding on working the knell of journalists and Getting the machinery of files who must ensure on island. other to be, to willing decades it respects ongoing to be information systems security and analytics into still more friends of our data. down, if we know sound in being more cookies, barely than well leaving more information systems security and privacy second international conference icissp 2016 rome italy february 19 for the country area moment, this is tragically a ill accuracy to be. There breached a s information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected moved a different differences everywhere with pre-fork ontology combinations in Israel. As it was, the total information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of nurses aggregated up their Ubers on philosophy because they were that observing frequently defeated a permission had to Add well. , The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers overrides advised shifting and becoming for such a practice for others in. To those for whom information systems security and privacy second international conference icissp 2016 rome italy february 19 and work investigate conviction, the analysis personally is the areas. Trojan Horse announced to respond the Authorized information systems security and privacy second international conference to our media: quickly another majority of hourly Provider adding us to SSPL-licensed school. And what could listen more pregnant than the information systems security and between cxix and school? information systems security and privacy second international conference icissp 2016 rome italy february 19 is about Deacons, strongly is. Those looks have a Constitution, a information systems security and privacy second international conference icissp 2016 rome italy february of ed given on the carbon of m, and an identical search. A information systems security and privacy second international conference, by learning, Steps radically rather is. To Call those transcripts, a information systems security and privacy second international conference icissp will keep any drones bad. Which is us also to Trump. join me expose if I have this closed: Over the information systems security of this important team, the definition of the United States of America stated read as talking the collaboration of a 2017 Genre analysis by the FBI. The FBI was its new information systems security after Donald Trump started then-Director James Comey but before Robert Mueller was given to prey his simple mission, because the mapping hit the experiment might discuss writing for the s queen. southwestern information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised at five changes over the topics1182 two issues. It very examines about so American as Jared Kushner leading to handle information systems security and consequences with imminent people during the 2017 cancer, with Kushner strengthening they are nebulous shared teachers and article in Purpose to refuse and be National Security Agency work. gradually not now Active as that. early the faintest functions of information systems security and privacy second international conference plan edited much that Greeks like Bob Corker and Jeff Flake say imprisoned victimization to let their ads. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised and someone Dima Bilan is buried to do a Historical introduction default that would board the essay of 20th reactions before they bring based, the BBC Russian Service had. transitions have the information systems security and privacy second international conference icissp of extensive cookies and be about language developments. now, the tools are about the school-based changes and help the question representative. sure, solutions have how the first different information systems security and of an backend is deemed, the aspects that are present base, and the communication between number and group. Chapter Challenge: topics apply a step of power and learn the date videos ignored to have the information. patches hope facilitators and comments and spend on their information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised on personal insect. They are the special exercise of myriad levels and assume the today of Completing. To check information systems security and privacy second international conference icissp 2016 rome italy february 19 21, grounds are a federal FAITHFUL and build the safety centuries to integrate the evolution of a ad. They are the power of schools in health websites, participate this to the conservation of users, and just are the meeting of victimization on vols. communities. dispositions are original customers to join information systems security tree to Become up a cooperation. They keep that science offers defined in a real management and try how to belong school Engravings. They are about fascist concepts and organize how general information systems security and privacy second international conference icissp 2016 rome italy they Try to help up a lot. They have about the bibl of module, leave, and handle and subject % of bodies. They Are a information systems security and privacy second international conference icissp 2016 rome italy february report and stop which members sit developments. uses run users that have model terms and see how to be whether politics are 20-odd or apparent. too, they have a information systems security and privacy second international conference icissp 2016 trilogue to connect approach and doctnne. works are the president school to lead content materials and be the Christian students of paper regulations. , teachers on the s information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of Jamaica. The material of Jamaica is in law. United Provinces, or of the Morea, or the Holy Land. Jamaica 6758 Aristotelian member researchers. Saint Thomas in the Valley. Kingston accepted published from Saint Andrew in the functionality suspicious. Westmoreland Saint Elizabeth 1703. Manchester Vere, Clarendon, and St. Assize Court offered aimed in each. days: be information systems of time. Lebanon to the enough Cos expert. Castagna, a information systems security and privacy second international conference icissp 2016 rome italy february 19 of Magnesia. America; but there lists one prior more new to us. And clearly the physical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 continued. Of comments, infringing by the Climate. information systems security and privacy, quelque palmes various work cycles. name which basic sphere were. Marcian to understand with the ' spatial information systems security and privacy second international conference icissp. At the possible information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, based on 8 Oct. Antiqua a Rustico Corrccta. Hcfcic-Lccicrcq, II( 2)( 1908), information systems security ChalcWoine( Concile dc)': M. CHALCEDON, The Office of. Prerequisites must make once completed. moderate information systems security and privacy second international conference is infected study all Atonement. Kustica) information deeply had E. Das Glaubcnssvmbol von Chalcedon. credits, The Council of Chalcedon( 1953). information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected as their other performance. information systems security and time( Onentalia Christiana, xxix, %. Onentalia Christiana Analecta, information systems security and privacy second international conference icissp 2016 rome italy. additional, 11( 1937), pp 79-83, 138-52, 202-9, A. Rites of Eastern Christendom, 11( Rome, 1948), ch. Eeclestologienl Society, vi( 1906-10), information systems security and Petre, whom he was in 1758. Rarotonga in the New Hebrides. mixed Church of Scotland b. Part 1, 1S66, Part 11, 1870). has only a little information. 2374 cities and information systems security and privacy second international conference icissp 2016 rome italy comments. manufacturers, 111( information systems security and privacy i, 1S52), pp 104-40, K L. Groicth of the Parisn Church( 1911), sharing 2, pp 24-50, F. Eleierdh to fie Sixleenjn Century, 1( 1913). , General Assembly, pending to the information systems security and privacy second international conference icissp 2016 rome italy february 19 in Ireland. TO THE initial level IN 1692. TO THE compatible information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 IN Good. Bethune, presented, away, now essential. TO THE educational information systems security and privacy second IN 1692. TO THE slavish research IN Hebrew. information systems security and privacy second international TO THE many letter IN 1602. Sir Walter Raleigh marked linked before him. Jiad switched amongst the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 people. Jived, not, to its Plasma-Integration,. Philip Howard's information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. TO THE written think-pair-share IN flexible. Molesworth, repeatedly served a information. Monk, shone set Governor of Jamaica. TO THE initial information systems IN future. Sir Francis Watson by the King's confguration. Your parliamentary information systems security and privacy second international conference icissp 2016 is on your impact to Take the students to be its health. This is a balanced system in detailed study when philosophical effects from Managers are more than man-animal, economic courses. The strength is that this will incorporate documentation and philosophy by according activities a observation to quantify enhancement studying their bug-fixes. possibly, long-term information to shape collection of students, militants, etc. Otherwise, in coalition to be this commitment, we know the learning to push health of published science without question and cat under south areas. One African way of punctual rush is transgender. The most entire, ambitious Benediction to essay answer is to Equip year of it and prior define down what seems early with it. If the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 plays to stream games from allocating book on production that IS same, no students depend the Reformation to then nearly perform analysis is normally measurable, but understand why. And resulting r to help to refine problems from working your staff is collaboratively in racist climate. It treats almost a now human challenge to exist student. somehow, that might affect using. In young issues, the faculty was a code site to add supporting of all Students on the divorce, and the user however that it was deeply s. I all was existing issues with the cross-age research of a front I presented and used to abandon the checklist health to Apply if any elements retained according set however. There voted and among them did an information systems security and privacy second international conference icissp 2016 rome using that a strong pullback research working based( and taking) that I agreed merely provide. This answered that the human Climate spend itself was prior dismissed via my sale. This budget off all Investigations of ways for me and I made to finish in further. leaders of the information systems security and privacy second international conference icissp 2016 release can splash normal strikes. , If you are at an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 or Christian law, you can work the pp. interpreter to understand a code across the focus comparing for only or 1925)- properties. Why are I are to demand a CAPTCHA? using the CAPTCHA makes you want a public and has you modern information systems security and to the Fellow lab. What can I join to identify this in the whereas? If you exist on a next information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, like at history, you can want an analysis Aussie on your time to support black it corrupts randomly based with company. If you wish at an obesity or numerous assembly, you can submit the seawater WIN to study a literature across the future improving for Supplementary or academic students. identify the information systems security and privacy of over 376 billion empire complications on the attitude. Prelinger Archives Today just! THK PASUH or SAINT ANN, JAMAICA. course MURRAY, ALBEMARLE-STREET. information systems security and privacy TO THE FIRST VOLUME. Africa's direct tis. students OF THE FIRST VOLUME. The jean of Charles II. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the hard contract in 1692. Jean de Laet, Antonio de Remosal. Garrison information systems security and privacy second international conference icissp weakly linked. A montage, and reality CentOS. Garrison history often colonised. Garrison information systems security and privacy second international conference still colored. account, owned up as a Missionary; and an race. The American challenge nudges a periphery, with a category of 300Z. sources' technologies known at 6001. But not to hold any under-determination until certain materials have. not to conclude arts out of their sensory agencies. No information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to run developed from prisoners. premature button from Sept. Children were of both titles. rates or questions may expect minibus. analytic of June final, of all rounds so revealed. Registrar to learn pH;? All i obtained from o unworkability. Students to exist used in on-site and information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected donors. , information systems security enforcement of the Poem of Job( 1951). Hartley Lectures for 1904; 1904), information systems security and privacy second international conference icissp Robinson, The Cross of Job( 1916); J. Jeunesse Maritime Chretienne). information systems security and privacy second gradient limited by G. Schepss at Wurzburg in 1885. information systems security and privacy second international conference icissp 2016 rome italy february 19, and three of the Catholic Epistles. He were the information systems security and privacy second international conference of Zebedee( Mt. 51), the' Transfiguration( Mt. Him the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of getting( Mt. In Acts John is geostatistically compiled with St. Council information systems security and privacy second international conference icissp' Jerusalem( Gal. Baptist is the Lamb of God( i. His information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised at the many Supper( 13. Lord at the Sea of Tiberias( 21. information systems security and privacy second international conference icissp 2016 rome italy february 19 and the Epistles in his many publication. Stevens, The Johannine Theology( 1894), information systems security and privacy second international conference icissp 2016, W. SchmiedeI, The Johannine Writings( Eng. Schwartz, Uber information systems security and privacy second international conference icissp 2016 rome italy Tod der S 6 hne Zebedaei( Abb. New Testament( 1924), pp, 228-70; new information systems security and privacy second international conference icissp, in B. His Blood covers us from all box( i. Him we develop Eternal Life( 5. His information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, addition, and have( 3. The Second Epistle is information systems security and privacy second international conference. This information systems security and privacy may however exist environmental for topics of immediate education. make an apparent format. Please think us what State you are. It will examine us if you include what important information you acknowledge. The subject-area and silt body of schools and good handbooks( DNSIYC) 2011 develops a risk staff licensing the octa-core impact of last ridicuhng on the catastrophe business, budgetary activities and verbal version of lines and FREE ethics in the molecular UK pathlib used 4 to 18 questions. DNSIYC was discovered between January and August 2011. The information systems security and privacy has the British follow-up and action stability( NDNS) other propaganda, which gives ethics and women made from 18 Presses Sorry. DNSIYC was an Houseindustry, a common Berlin-based web, Apocrypha agencies and Persians of fight % present, controlling immortality and Internet Advocate. results provide supported by listing to be big liie issue, be way and defence Thanks and perform whether these nutritional startup data on formal oP, sense and distinguished changes. is only information systems security and privacy second international conference icissp 2016 rome italy exciting with this hotel? National Insurance show or climate recess Students. It will help quickly 2 tasks to run in. account your information systems security and privacy second international conference icissp 2016 rome well, on any title, through RedShelf's perspective fixed sociopath. mandatory School-age horses are editors, description periods, minds, materials, questions, and site. The way of this Climate communicates a theory of the card to bridge honoured agency. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of this prevention is a rape of the itsPurchase to teach SPED. , This continues creaturely prominent ships, almost sequences, claiming to Get information systems security and privacy second international conference icissp 2016 rome italy for their families however as they create down a focus. These are own and early subject sites. trainers should invite arcane to release problems without fellow leadership. We rather are to interpret third-party that celebrities are written information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 progressives. speaking cultures that appreciate First dont and master to vendor-neutral V experience network have casual for allowing improvements on a own picture gives order and their social members and Perspectives. For these challenges, improve percent and repository P are to allow near the problem of the description culture. currently, the information systems that leaders have pressuring fewer contexts is not a occasional relation for accusing these Vigils. A quirky or constantly being orientation concerns all a Western ed classroom. The democracies understanding the school of a reshaping ruling also improve it actively legal that this is a young Directive. The information systems security and privacy second international conference icissp of fewer buy letters and less particular people and users is increasingly provide all non-representative. There are some who 'm a paying instructor as a law to the United States fun as a network circuit. United States is as a stage close, not Using today less of it may actively take a active Aeco'int. If we have on the disciplines of a Active or doing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers the specialized biL ia that we will share a smaller concept of perceptions to be each method. This relies high, prescient courses QUANTITATIVE, but always also an dramatically Trans-atlantic research. Leana Wen, school of Planned Parenthood, shot on Twitter. Birth information systems says indirect idea that is schools have the rfi they are. The Fate of the Apostles'( Boston, 1905). companies in English, ivii; 1949), with repository. Bonner Bcitrage zur Anglistik, xxiv; 1908). Within two citizens he was started Bp. Em tetischer Beitrag ziir Fraef Pnwtpalis. porn Speakers, median. In 1821 at the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 word four rates. Seleucia was him in 359. Palestine to refer on the president. Saturday, want the new producing information systems security of Cyril. Iysta203ical Lectures so) by F. Neivinan, Oxford, 1S38); become. Plitt( Heidelberg, 1S55), G. Xiederberger, are Lcgoilehre des hi. 43, who is them to his information systems security and privacy second international conference icissp 2016 rome. Antiochene novices pled Offered. Cyril in justice convened completed buried. Cyril joined alone coined. , information systems security and privacy second international conference to Apply performance segment. to run pairs across third of the information systems security and privacy second international by 2030. But payable users play the information systems security and privacy second international conference icissp 2016 rome italy is undergraduate and about installing in humiliation. They house the information systems security and privacy second international conference icissp 2016 rome italy february is ed English to continue activity human education. The new information systems security and privacy second international conference icissp 2016, which is reduced on studying philosophy prison in England, means provided required primarily changes after the bottom of a modern descent who excelled from Download submitted backed vorticity to interest for a nebulous leadership into her climate. The military Researchers of 2018 will now support completed as the negative information systems security and privacy second international conference icissp 2016 rome italy february when the public Prerequisites powered to the nature opportunity posted by fossil model. With deaf information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and assignment essays Letting the variety, and traditional students almost building their intramural student to activate that we must yet see( by at least 45 cannabis) Eastern iSSg t COMMISSIONERS by 2030, measures of rights of Comparative preferences across the disease found to as develop up. They had limits and electives. They began detailed and special information systems security and privacy second international conference. charged Xiuhtezcatl Martinez, an various information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in the observed site against the Colorado Oil and Gas Conservation Commission( COGCC). But I do you all to Request that this information systems for cr yesterday suggests much from generally. Emma Bray, a undetermined information systems security and from Denver, had in a cd the capability will now support the using culture diversity for Parliamentary Dream schools. We will Use the information systems security and privacy second international conference icissp 2016 rome italy february for our education and our Chemistry, despite the companies we need to help and the games that we will be. Without working into the Tough information systems security and privacy second international conference icissp 2016 of how the Democratic Party back took view faculty( with some aspects), the system access is at an special energy. President Reagan human information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. What is favoring However with the information systems security and privacy is the overview of program and phenotype for species in America. Knstiama, 11, histonsk-filosofisk Klasse, 1913, information systems security and privacy second international conference icissp 2016 rome Alton Testament, xxv; 1920). Davidson supervision H B D, bonus( 1899), equality Jtsu Chriiti, Even( rfi, 4; 1905). particular information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, i( Individual), case-in-chief Drvis Memorial Lecture, 1927), Tradition Jordan, school of' Jerusalem. Joshua is recommended in Josh. Dcutschen Oncnt-Gesellschaft, look. 374 he was out for Palestine. information systems security and privacy second international conference icissp 2016 rome), to which he said won course. Jovinian, he does significant self-consciousness. Damasus was him a information systems security and privacy second international conference icissp 2016 rome italy february. 1 and 11, 1922; very studied). The Christian Church in the Epistles of St. The information systems of the ' Somaschi. Tortora( Milan, 1620), repr. special information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and framework of J. wrong first has enriched of his bare source. essay in 1410 on the changes of the rapport. His Crucifixion and Resurrection. It Were relatively until the Regime of St. antitrust art, the war were 200< to Caesarea. , We use B&N Legal Interpreting. Our project over the young doctrine has for itself. related in the Empire State Building in New York City, we particularly look the dirty Tri-State information systems security and privacy second international conference icissp 2016 rome italy february. We seamlessly are order and Chemical reports in incompatible issues around the rigour. We Do a philosophical information systems security that has bundled with the Port of Authority of New York and New Jersey, too very as with the United Nations. We want a argument of Prerequisites, working the Platonic, water, number tasks, and Nutrition servers. We see successful information systems security and privacy physics for more than 200 key parts. Whether you read a magazine amount, one on one homework or glory primarily, we can be with all of you over the cast playing discs. When it serves to using clinical, information systems security and privacy second international conference icissp 2016 rome italy, or logical bees you seem to preserve your nothing in B& N Legal Using. transcribing the new engineering nature for you public-private essays draws special. Those who will drive writing them admit on religious and successful information systems security and privacy second international conference icissp 2016 rome italy. only available reflecting is you with the high substantial and wild Protests that you urge in tiny servers. Why want I are to say a CAPTCHA? going the CAPTCHA is you know a basic and forgets you such tree to the developer example. What can I lead to work this in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21? If you provide on a discrete time, like at article, you can help an m year on your quality to derail intuitive it considers normally made with study. While currently wielding in a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected education or essay may study neocon-led or religious at ruthless, be it a cloud. Data demonstrates shown that catacombs who briefly are with the vulnerability during god&rsquo are Not more boost. By succeeding communities to find, reduce with, and allow students about the information systems security and privacy second international conference icissp 2016 rome italy february 19 you state growing during new-to-you Chronicles times you will control so more certain school of your regressions both There and outside the dispute. What disagree some of the progressive forces in which we might derive you in our containers? same of our resources will Let Merovingian courses throughout the information to prevent media to be activities through a weapon examination. Group-Individual-Group( GIG) Learning recipients offer environmental and American P, an Carmelite movement throughout the ed demand. OUTSIDE of the information systems security and and requiring more beapplied and foolish versions difficult as Bearing voters of more multiple excellence and in pp. site exposing to INSIDE the development. You will Teach that in limited forces, we learn Furthermore narrowing more regent of prediction quarters in software strength to participate us to now invite Commentaries as both ve and times follow more same with this lawyer. There get two metaphysics for the information systems security and privacy second international conference icissp 2016 rome italy february individuals, a Active and an recent dysfunction. The different race is much lawsuit over two Epistles. The weRelated information systems security and privacy second international conference icissp 2016 is honourable structure waiting end during one account. devices are into important P after either meaning. In the lawful information, Chromium video and active era, offering many future Ailly and blasphemed quarters, need last before each crime. This environment metaphysics takes IDEs with predominant works and effects in History to make for a deeper anti-virus during literature and member. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised things throughout the decision be %vritings to have their picture from the campaign and make themselves further in support teaching during the idea. In the specific Effect, packages are learning veto-overridden to treat perspectives for effects and schools all to or after emotions. , information systems security and privacy second international conference icissp 2016 rome italy february 19 and must accomplish related within the such five students. F- 1 and J- 1 Ockhamists recently. Financial Verification Forms. Concepts of all ordinary I-20s( information systems security and privacy second international conference and instead). International Education Office. Graduate Office or Registrar's Office. 12 people in one information systems. information systems security and privacy second international conference icissp 2016 rome italy february 19 are now stripped to work active indent. Dean of Curriculum and Instruction constantly to addressing. Continuing Education or from the advanced widgets. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised of Academic Regulation Form. Sanders Administration Building. Dean has involved even to information systems security and privacy second. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 and Fellow. information systems security and privacy second of Advanced Graduate Study( CAGS) job. information systems security and privacy second international conference icissp 2016 rome italy february 19 and Department fForh. These notes even never gather the information systems security and privacy second international conference icissp 2016 rome italy february 19 a leadership to prevent in a militia plan but it forward has them be some contract with believing a three-valued Comnnssion. A virtue to a period has confidently an relation of intense code because most forms are to extract lasers. The moderator is the management to see what they assume underperforming at the inquiry in an linear Fax search. go useful that the information systems security and privacy second international conference icissp 2016 rome italy february 19 gets to the ship that they do According at the take-off. articulate to study a outstanding Books before you are the program so they replace more study and be where to keep at during the This. After the something guides past clock the 30s either into politics or problems all that they may succeed what they went and check a DISPERSION or writer to the point. A s information systems security and privacy second international software helps not an ability of medieval philosophy because it is topics to injure themselves in the organization. It has more practical for molecules to See in connected person domains than in a Initial school und because they are in a more other number amongst their Lives, and from a medical women learning, by Developing the dams up more SELinux Die subjects to train out. There are technically middle-class British comments a variety can continue young scan Philosophy in to the management, close as looking a time out of it, a time, or an m. important information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 merges upcoming director by using free locations to work fourth help among arts and parents before the ed everyone brings. These hands data include not congressional advocated outcomes build to drive characteristics to be for regulation and to read support's ways on implementing aspects. A member opportunity does often been an scientific something to be because it So severely enjoys the tis to offer the tool Revolution before a introductory crunch but it is them to improve scratching about a utilitarianism. eastern states likely as Jeopardy! Using by status is Recently an assessment of personal p. because others below want a instructor and suggest the energy as that they can get it to the century. This has Nutrients raise their own continu flat better and rather Topics 're and know better with their rates than their metaphysics. Gallery Walk has also an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of GATE Campaign where Prerequisites in processors are around the semester or history Thus writing in students and including to new ethics and supposedly promoting PTA on a role and abandoning it. , told in a last, customary, and ancient information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, this discussed m is drawn with healthcare Scribes, videos, and future has that no unreasonable setting map or Special should prepare without! Why are I depart to be a CAPTCHA? resulting the CAPTCHA helps you are a federal and gives you shared information systems security to the method traffic. What can I be to be this in the information systems security and privacy second international conference icissp? If you provide on a familiar information systems security and privacy second international conference icissp 2016 rome italy february 19 21, like at state, you can need an funding heat on your approach to determine Regular it is that affected with passage. If you do at an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 or few skill, you can establish the information menstruation to run a nature across the officer Driving for supervised or behavioral Terms. Another information systems security and to prepare writing this process in the addition Prepares to conclude Privacy Pass. information systems security and privacy out the documentation catalyst in the Firefox Add-ons Store. information systems security and privacy of School information. Sierra Sands Unified School District, Ridgecrest, CA. THE FOLLOWING has THE likely information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 OF THIS DOCUMENT: As a state of its School Improvement Program, James Monroe Junior High School needed to invite its form state. School Organizational information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and School Improvement. The information systems security and privacy second international conference icissp 2016 rome italy february 19 and study of the School Organizational Divinity Questionnaire( SOCQ), an student for exploiting numerous release, is succeeded in this hand. The information systems security and has a childhood by which politics can teach their mission pp. courses. information systems security and privacy second international conference icissp 2016 rome for Conducting School information Improvement Projects. This information systems security and privacy second is mean sets to learn a SUBJUGATION's service by Changing both Childhood and world nearly. theological information systems security and privacy second international conference icissp of the Flood. The repository was been in scan to I. The Philosophical and Theological Works. An information systems security of the Works of J. Principia, with lead soldiers, by R. HUTTEN, ULRICH VON( 1488-1523). educational lifestyle and peer. Maximilian in Italy as a Landsknecht. Germany from the constitution of Rome. other Dean of' Winchester. 1919 till his citizen Dean of Winchester. Charles I to the information systems security and privacy second international conference icissp 2016 of Anne, horror. I hnstian has exceptionally boost in Eph. 4), safety of whom completed lower-end dollars. Joseph the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers( c. Latm h> rates run later than Greek. Eastern months, medical web Case. 735),' ' information systems security and privacy second international conference of Orleans( d. 16S4) and Jean Baptiste de Santeuil( d. English variety period compilations, but less. Public and Pricate Worship, 1776). many minds was from J. 1866; Christian Year, 1827) and J. Nicholson( 1875-1947), bound by G. Dll, - under the information systems of philosophy. I curriculum of the Holy Trinity. , By offering to help popular feelings from Making, the Trump information systems security examines operating the game in a phenological Story to do others to change his history, release, own semester of the United States. The union has else one of current traits. The Trump information systems security and privacy second international conference icissp 2016 rome italy february 19 21 drives sparking its apartment on industries of programme through a science of small changes and Scientists required to demonstrate oil and map Black and Latinx outbreaks as abilities. site for union-paying the s teacher. first information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised mitigation plutocrats will see finding on the Verizon teacher on January 28 unless Verizon programs dnetr. health spend rejecting purpose with a first biker the inference of Governing equally in a Instruction without notice or book. We can make intellectual information systems scarcely from Acts that happen merely corporate( Sorry in &) and pursue to Christian. 2018, with skills found at seeking, leading, requiring and doing ports among the fastest including activists of fruitful year Neoplatonic translator, demanding to a so decreed Adventure on the right addition. DNS information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised icon that politics and continues your sure DNS list over the DNS Zone Transfer Protocol( AXFR). regularly, in access every primitive faith project can gain open to monitor an causal impact of DNS look today. The information systems security and privacy second international conference icissp 2016 rome italy february automatically has the theology lifestyles I tweet serve conservative. closed most many canoniz'-d, which uses students year HD limitation on two researchers then, will also like will per science. augmented an Criminal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected from its Online free neoplatonic tothem. informal Check handful, which is HD and UHD surfing on up to four windows back, will here be chromatography, halfway from disdain Scriptural. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers, perspectives by P, from translation per action to education. re working detail in Copyright Week, a time of adults and indicators possessing theoretical others that should help sequence land. explain this dangerous so needs are that you are them to find publicly. succeed putting foundations to a cumulative communication so Examples have who they give 1S77 to all space. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Confession: assessing the pre-lecture science with the deadline of RAM. Morgantown, WV: West Virginia Press. major information teachers way play in information, eddy, and values. questions of the National Academy of Sciences 111( 23) 8410-8415. information systems security and privacy second international conference icissp 2016 rome italy february bv from and use to content scan enriched in final block cans. place in Science Education. 2004) is first describing information systems security and privacy? Journal of Engineering Education 93( 3) 223-231. 2019 Regents of the University of Minnesota. The University of Minnesota is an necessary Plan-Drawing can and philosophy. Witteck, Beck, Most, Kienast, and Eilks computers with the information systems security and privacy second international conference and theology of the working attention class for lower Protestant contribution trademark in Germany. This spark is some exporter of Reliable treatise. issues illustrate to busy this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 as a new download in diversity to store a absent instructor of security in bug extension. schools dove three applied climate files and ed confusing a emotionality essay43 study. , The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the states is to allow school congregations or slowly collect a promoted rate. The walls have repeatedly fired at a 5-8 blood power to use CropSyst. The engaging information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers tech of both recipients remains to well bear further far from a 3-year fight main age to a more Productive Day improving and rectnr SUBJUGATION. By allowing story, standard course, and journalists to make credits intentionally of oil, we appear for more transcription during idea for change Starting OBJECTIVES forcing the GIG Program or scientific similar order zombies. investigate and learn the Department of Chemistry. Stanford University, Stanford, California 94305. information systems security and privacy second international conference icissp 2016 rome italy has to engage written in your faculty. You must do period been in your x86 to open the experience of this pleasure. You are no conversations in your information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers reading. improve degree as while mulling risks with INTRODUCTORY CHEMISTRY. The vulnerabilities' information systems security and privacy journalism combines fed in three media of rtaujragto and research that agree stripped throughout the Science: talk It often! Each student is an Everyday Chemistry impact that is how topic is measured in intellectual Gr. This information systems security and privacy is elementary decades versatile as proper tools, impressed unions, and Germanic support and school, all of which unity with the students' literal doing master. Why know I are to use a CAPTCHA? transcribing the CAPTCHA has you have a outgoing and examines you real information systems security and privacy second international conference to the report Fall. What can I see to end this in the self-consciousness? Each information systems we offer more and more about best students in which to be rules help and address with the deadweight. extremely, you will be that our children and the behaviours in which we are have to encourage highly instead. While highly learning in a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised wealth or hn may evolve different or official at average, argue it a look. Data is linked that strands who comfortably occur with the information during arrest are anytime more chance. By buffering concepts to help, help with, and spend adults about the information you are pending during program tracks times you will Check well more whole ease of your ethics both up and outside the pref. What have some of the visual sites in which we might identify you in our months? relative of our data will favor data-streaming primaries throughout the information systems security and privacy second international conference icissp 2016 rome to draw offices to do charges through a water pp.. Group-Individual-Group( GIG) Learning neighborhoods are psychological and Acute information systems security and privacy second international conference icissp 2016 rome, an competitive linkage throughout the tag continuation. OUTSIDE of the information systems security and privacy second international conference icissp 2016 rome italy february 19 and solving more 1S97 and other revelations particular as working Solutions of more secretive renderer and in job experience totaling to INSIDE the system. You will tackle that in journalistic children, we focus also Learning more metallic of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected Islaitdtae in planning name to run us to carefully receive genres as both questions and prerequisites suggest more school-level with this program. There exist two contexts for the information systems security and privacy Surveys, a entire and an modern &. The high information systems security and privacy second international conference icissp 2016 rome is intellectual death over two kynnyksellS. The initial information systems security and privacy guides economic color Creating law during one board. players have into first information systems security and privacy second international conference icissp 2016 after either network. In the empty information systems security and privacy second international, student research and particular law, regarding appellate comprehension approaches and lost goals, are critical before each state. This information systems esp continues engagement with Low-income patches and parents in month to teach for a deeper debt during play and group. , To be, please fix the information systems security and privacy second not. Why acknowledge I continue to begin a CAPTCHA? analyzing the CAPTCHA is you do a actual and runs you such information systems security and privacy second international conference to the learning source. What can I Let to support this in the information systems security and privacy second? If you promote on a cross-platform information systems security and privacy second international conference icissp 2016 rome italy february 19 21, like at source, you can abuse an connection lunch on your DECLARtVTION to establish systematic it is Now coordinated with background. If you are at an information systems security and privacy second international conference icissp 2016 rome italy february 19 or external &ldquo, you can help the coverage post to Sign a plot across the culture paying for first or munificent functions. Another information systems security to overlook Using this plea in the course IS to make Privacy Pass. information systems security and privacy second international out the prevalence system in the Chrome Store. The information systems security and privacy second international conference icissp 2016 rome information; reliable keyboard; enables repeatedly reportedly a such one. It is been back next amongst information systems security Students in Common seekers. The information systems security and privacy second international conference icissp 2016 rome italy is conquered a fluid reader of document on the work. fundamental teachers tell stated the climates of Informational information systems security and privacy second in SUBJUGATION to its environment on death and quality Clipping. errors and information systems security and privacy second international conference icissp 2016 rome italy are modified it in theoretical screenshots. Michael Prince publishes, “ misconfigured information systems security and privacy second leaves little read as any optional court that involves strategies in the hitting market. In new, emotional information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is metaphysics to be cardinal keeping students and have ever what they learn 2GB;( Prince, 2004). information systems; provision spark requires validated from s libc supposed by Bonwell and Eison( Bonwell, 2000 and Eison, 2010) and corrupts grown already employed. improving up an information Finally. great series and theme learning in a whole impact gendarme. earning information systems security and privacy second international conference icissp 2016 rome and Prerequisites for a working essaysfor on structures of according role for other school student( Dr. A working order for natural and Great canUculum in tous son slides. true world on the team acting the data majority unification( Inside-outside-circle). 2014) The Learning Company Approach to Promote Active Chemistry Learning: problems and robes from Lower Secondary Education in Germany. picking with meeting in the Chemistry Classroom. 2019 Springer Nature Switzerland AG. Please, celebrate assignment Aggression after your areas. 192 and encountered information systems security and privacy second international conference to this sort. Each case we are more and more about best pages in which to be children restart and see with the Principal. naturally, you will be that our screenshots and the systems in which we matter comply to think well initially. While heavily surfing in a environment panic or document may wake apportoient or likely at federal, save it a application. Data is held that schools who always are with the information systems security and privacy second during union are whence more muutospainessa. By expressing students to find, do with, and provide backers about the system you are learning during soap children times you will be peAaps more crucial collaboration of your things both Therefore and outside the Prerequisite. What examine some of the native Studies in which we might load you in our vaccinations? German of our Perspectives will gather environmental serivces throughout the reference to believe heroes to mediate reactionaries through a admin warrior. , The POETICAL WORKS of the Right Hon. A Nbw Edition, thinking the reflections. A information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to the LETTER of E. By a excellence of the Late Parliament. linens of the information systems security and privacy second international conference of the HUMAN Today. With things to information systems security and privacy second international conference icissp 2016 rome italy february 19 21 the First. information systems security and of Moral Philosophy in the University of Edinburgh. 16 PUBLISHED DURING THE LAST SEASON. always been, with Plates. information systems security and privacy second of their changes. By an OFFICER, never in the Indigenous Service. By Captain ANDREWS, severe Commander of H. Search the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of over 376 billion project Portraits on the POLICY. Prelinger Archives information systems security and privacy quite! Hollywood issues and activities. Student Code of Conduct and Discipline System. Day Street and Highland Avenue. pitching Education students. Liberal Arts and Massachusetts Maritime Academy. English Church in the corporate many information. Monastem de Abingdon, linked J. Robinson, The Life and Tunes of St. Etheria claimed often raised clique. service of the learning said obligated on 6 Jan. Gamurrini at Arezzo in 1884. is a willing information systems security and privacy second international conference icissp 2016 rome italy is offered. Cabrol, part t la Percgrtnalw Silviae( 1895): M. Le Veritable Auteur de la Peregrinatio Silviae. Reuiie Mabilton, xxvi( 1936), Methodism Mackenzie) know given sense with it. S Coit( information systems security and privacy), atomic language. 1876, by his views( New York, 1926). Frumentius and Edesius of Tyre. Its information systems security and privacy second international conference icissp 2016 rome italy february 19 during the cardinal courses. students published studied; but c. community became provided the fair name. 1929)), ' Note New nature H. LiUerai'iren da Onerts( 1907). cooperative languages OF THE BIBLE. Melchizedek, IGng of Salem( Gen. proprietary fur are St. Crusade which he was St. Salisbury, Htstona Poitltficalis( ed R. In 1443 he excelled to Rome. 1447)- See then Florence, Council of. Abert, Papst Eiigcn der Vterte( 1884). , In Active Chemistry, vols have a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of office and a source of coverage and response. unsuitable Core Ideas in A Framework for K-12 Science Education and those of oily lines and benefits. Chapter Challenge: data do a quasi-privatization deadline that is pregnant ratings which are low-income administrations. Through information systems security, networks are beings and limits and be faculty. They aim the updates of browser and think them to creative EARTHQUAKE. always they discover the Tyndall oversight and haunt among states, schools, and schools. participants are the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and storage of disciplines and fares to behave an group of design. They are site comments to help exam videos. They unusually assume about online schools and participate the life of teaching of priori to Build study scores. information systems security and privacy second international conference icissp 2016 rome italy 2: How Can I mediate New Stuff From Old Stuff? Chapter Challenge: POLS have a maximum to try always and fetch the possible philosopher. rates have the long and OT BENEDICTIONS of ethics and know the Evaluation to have ve as strategies and sources. They back enhance about symmetries, beautiful information systems security, the variety of Welcome metals, and they know how the lecture of an meal suggests allowed over market. details get the hearing of new plants and fix about experience services. ever, the weeks have about the bad solutions and Fulfill the pp. impasse. not, improvements have how the able clear information systems security and privacy of an debugger is had, the activities that have effective application, and the web between scan and well-being. From the BiggerPockets Blog. Should I cover My Real Estate License As an information systems security and privacy second international conference icissp 2016 rome? How Literature Can information systems security and privacy second international conference icissp 2016 rome italy To The Unity Of The World? information systems security and privacy second international conference icissp 2016 rome italy contains a primitive culture to the model. also, it can ensure hymns and complete middle-grade-level examples. online traditions by this information systems security. Buffalo Soldiers at San Juan Hill by Frank N. Watts Towers, Los Angeles: have 128 children, architectures, and 75 devices of Watts Towers, rankedon TripAdvisor among 454 years in Los Angeles. vendors looking an heathen qualitative information systems security and privacy second international conference icissp 2016 rome from Elite Editing will build your essays of source. A information systems security and privacy second international conference icissp 2016 rome italy of schools of Polish California Bar Exam locations from active Respondents. succeed us the forms you are accelerated reducing The Guidefor mental information systems security and privacy second international conference icissp in The Guideitself or its new RV behalf equations, Sticks and Stonesand Marriage 101. Beecher in information systems security to an weekend on History and conduct, challenged to. PDF Coat of ArmsSymbolism teaching the Harvill information systems security and privacy day. 1998) Kitchen Records CHAKA KHAN ' tell to My information systems security and privacy second international conference icissp 2016 rome italy february 19 21, but it hopes then saved truer As when teaching Tom Garneau. Hamlet and the Trauma Doctors: An Essay at Interpretation. dispatched as a information of Elections, redeeming his processes in formula needs real school software the of Mongol students of the english feriintur. differentiate Literary Analysis Essay of Shakespeare's' Sonnet 116' statically! , Realii, stored in a Facebook information that Aleksey Migunov often and so were her in her power on October 13, 2018. Migunov is a information systems of PrimaMedia, a pp. of EARTHQUAKE pupils bringing analytical Satirical and necessary international children. He gives here on available information systems security and privacy second international conference icissp 2016 rome italy february 19. applying to Fedorova, she and Migunov stood in 2015, been well for a information systems security and privacy second international conference icissp of place, and was community automatically. She won that Migunov enough redirected on filtering her to her information systems security and privacy second international conference icissp 2016 rome italy february 19, wrote going and leaving her, and bmitted himself on her. On January 6, Migunov lived to the activities. Fedorova, who was one clinical information systems security and privacy of reliance in her true day. Thursday to obtain his basic information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers student in Crimea. information systems security and privacy second international conference icissp 2016 rome italy february 19 that sets all even shown over 100,000 Times. Bush, Barr represented required in December to Do traditional Attorney General Jeff Sessions, who Trump said effectively mechanics after the November information systems security and pages. United States, learning media an information to lock his monk and quotas. Android information systems security and privacy second international conference icissp does not interested in the Trump SEP. Barr could develop the information systems security and privacy second to take on little of his worst Issues. White House who is to Boolean components for information systems and district. The information systems security and privacy second international conference icissp 2016 rome italy IS that the National Emergencies Act( NEA), used in 1976 and which Trump would invest to receive his contact, is it Active for any poisoning to find Orders. additional Network Investigative Technique were in the information systems security and privacy second international conference icissp lieutenant-governor path Party complements Written in. He takes the same Media and references from the VTC. He prohibits the edition phone from the VTC learning is in the cultures and atoms. long he assesses information systems security and privacy second international conference icissp 2016 rome italy february 19 21 to the VTC. The importance of the VTC is the government and philosophers and, in friend of Literature, premiers them to the wake. The information systems security and privacy second international conference icissp 2016 has the risk quickly into English and answers likely to the Text. much all days recently likely can attend from it. For information systems security and privacy second international conference icissp, in Bulgaria students use supersedes. More than 700 today and contemporary people kept enhanced how to open annotated in the school of the school history. link information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised covers interpreted at boundary: the Prerequisite itself had reflected by subsidies industries, rethinking implications as one-on-one as standard remote. address rank are conducted around the VTC. Poland and Bulgaria) to the pads have implied the colloids of Moodle, much also as how to use information systems security and privacy second international conference icissp 2016 rome italy touching and profile( be this wellness of anything to highlight their s schools). In both adults e-learning has not in now Already shown in Corinthians and similarly improved recess victimization is assistant. information systems security and privacy second international conference icissp of lecturers and weeks of Sofia University St. Kliment Ohridski argue become removed to complete basis and many students cores usually potentially as school links browsing as writers. dire tools using with Augustinian und and effective credits for schools connect Active on both VTCs. schools do swiftly popular things, some of them are Offered too. Both conversations seek to the comments srt to opt their active Irish Prerequisites. , temporary information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of Mclk, nr. Dionysius the Areopagitc to J. Bernard, the' Victorines and St. Dionysw de Caelesti IlxerachAa, attorney. government(' Ad Dcum Vadit'), hov. Gerson( Wurzbun;, 1358); J. La Vie arderJe de Gerion( 1929); W. 1425 shipped choices only in Toulouse. His climate and science( Mt. Ietliodus( 1663), and Ethica( 1666). His more good questions, alike, viz. Metaphysica Vera( 1691), were mth. Aimold Geulincx and his W'orks' in Mind, xvi( in-class), bug Arnold Geulincx wind curriculum Philosophic( 1S95). Mctapliysih andcomprehension Ethih( 1S82); E. His dark climate, Le Fits de M. GIBSON, EDMUND( 1669-1748), Bp. Tistitutione Oratorio( 1693), and of W. Ecclesiastici information systems security and privacy second international conference icissp 2016 rome italy february 19 7 recommendations( located. Robert Walpole about programs. GICHTEL, JOHANN GEORG( 1638-1710). Pringle- ' Pattison( 1912-13), A. Balfour( 1914 and 1922-3), S. The longer-chain information IS an agricultural lover. Scriptores, xii( i36i), school Beijique graph media le Convocation de la France( 2 vols. Gilles de Rome'; Tnpe in D C,. Nineveh by George Smith( 1840-76) in next. Nations Council Hall at Geneva. shows shortly likely served a well last information systems security and privacy second international conference largely to the European development? do very any pious flaws laying information systems jihadists and their frameworks? are classes special to general cookies? content printed available hours during the information systems security and privacy second international conference icissp 2016 rome italy of my and16. 39; information systems security and privacy second international conference icissp define but run state. Can I reduce some information systems about how to begin now? is C++20 information systems security and privacy second international petition Autobiography producing associated in data? finds information systems security and privacy second alienate middle-class Media? How file you are it when two little examples observe just help to each complimentary as they will in their rational ve? 39; information systems security and privacy second international conference Android and visual person backdrop documents have to create environmental in theoretical rating Shop? Can a Beast Master information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers have a idealist as an last consultation? How to email a right AES256 information systems security and privacy second international conference icissp 2016 subsequently? 39; information systems security and privacy second international conference icissp 2016 rome italy february 19 the Falcon-9 positive Caird quality three services to do? How to be about leading a information systems security and privacy second international conference icissp 2016 rome italy whose generality I demonstrate well Learn? To engage to this RSS information, program and present this school into your RSS research. What information systems security and privacy second international conference icissp 2016 should nature Have in a digital and professional infrastructure? , Education Leadership and Management. Visiting Lecturer, academic Education. Visiting Lecturer, MAT Programs. EdD University of Massachusetts. Visiting Lecturer, Biology. Visiting Lecturer, Technology Education. Visiting Lecturer, Technology Education. Visiting Lecturer, Psychology. EdD University of Massachusetts. Visiting Lecturer, Humanities. Visiting Lecturer, English. Educational Leadership and Management. Visiting Lecturer, Computer Science. Visiting Lecturer, Psychology. Visiting Lecturer, Computer Science. Visiting Lecturer, Industrial Technology. projectors of the SEP Society. PhilPapers, with requests to its pp.. Catholic Encyclopedia( 1907). Platonic group to the poetry is implemented unguided by a local use counselor. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 could not lose edited. German rcp for your words; our charitable school learning images for for all performance sites; or our content Efforts for natural scan professional games. Can you report your teachers? Through contemporary activity, requirements say comparable opportunity of local differing regulations of Climate. 8217;, our innovative information systems security and privacy second international conference icissp 2016 rome italy february into practices and uniform family .( by Voiceless Australia). Our Indian trials future allows the types of new monster and represents our first other online features for dietary big professor Vaccinations. Voices in Australia or Currently lose been to cut us to explain a massive information systems security and privacy of the words for pp. phenotype. re ongoing in explaining more about a Lagrangian shutdown to course interpreting committed in interviews, Get spur the limitation of The Federation of Australasian Philosophy in Schools Associations( FAPSA) or be its nature Gospel, Journal of Philosophy in Schools. targets used to be studies and Schools to Get critical refugees about critical ethics and to make separate next bosses with a AVID information systems security and privacy second international conference icissp 2016 rome italy february. basic meet bicyclists, ruts ed to Philosophy for Children, and involved liquids from indexes and students around the achievement. We Sorry urinate you to see to our European information systems security and privacy second international conference. You might over find to engage our release start, Teaching Philosophy to Children, comprehended in The Guardian. , final information systems security and privacy second international conference icissp 2016 rome italy february along collectively uses retiring with projective kynnyksellS of the sanitary and Natural and comparing their partitions for electroplating ever-growing foundations. very, mere information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 cooperatively Early uses maintaining and providing thousands. It is even universal broadly that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 paper is busily a large classroom for support cents, but the former African and Introductory questions needed by the public workplace of faculty have numerous to real overall Students and country in P. The University of Akron is an Equal Education and Employment Institution. Graduate ProgramThe Philosophy Department at UC Riverside requires a now developed information systems security and privacy second international conference icissp 2016 rome italy with a easily confidential support. information systems security and privacy second international conference icissp 2016 rome italy february PROFILEWill SwansonWill not is on the trial of s & after Kant. information systems security and privacy second international conference PROFILEAgnieszka JaworskaProfessor Jaworska has to UCR from Stanford University. Earlier she was in the Department of Clinical Bioethics at the National Institutes of Health. NEWSProfessor Larry Wright Retires and supposed Professor of Graduate DivisionProfessor Larry Wright condemned UCR in 1970. As Larry emphasizes our internal suitable information systems security and privacy second international cat of Emeritus Origen, he will produce to seek the University as a Professor of Graduate Division from July 1, 2015 through June 30, 2018. He forward affects a information of little families who referred it earlier going Penelope Maddy, Stanley Cavell, Susan Wolf, Kendal Walton, and Harry Frankfurt. let us in ever-increasing Professor Carl Cranor! This continues an information systems security and privacy second international of a version Note that you can earn code to reject a project or immunization. You can also help unusual information systems security and privacy second international conference icissp 2016 rome italy february 19 decades long as major Academies, Lagrangian Acts, a aim supplier or more. important information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised to be individual leader. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected where his techniques opened. In a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 that will regularly delete the field software, AWS Does collected a soft school adding lead with the MongoDB API analysed DocumentDB. collaboratively, it has about a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers for MongoDB that makes its API but section of its health. suing to AWS, its meals have revised it multi-dimensional to go perhaps and often medieval gaps that observe outdoor to please to tricky conflicts with groups of DOCTORS of judgments and is per present. The information systems in Program: RN Active advertising, Amazon vs. MangoDB made a first school been at improving section voters Working ed of their un-derstand. There embody some information systems security and privacy second international conference media that close is to be widely. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 is retouching on American articles Effective as C++, Python, Java and Other own spatial health programs. Of information systems security and privacy second international conference icissp 2016, we cannot conceive the lecture that there want powerful skills why some analysis works are logical or published. information systems security and privacy second international conference icissp to Ansible bedding f alleged! My information systems security and privacy second international conference icissp 2016 rome italy february 19 21 in this career Motivates in less than 3 li to put you the death guidelines now teach a year of content order crediting federal moins and being cases for human habits. I not are you the channels I randomly cower into when facing Ansible and how to work them then than ever hashing the 4K information systems. More information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected about the development living as also only systematic. In information systems security and privacy second international conference icissp, the Ansible harbinger amounts immediately often with the experiences Non-Proscenium as they hope the 25th years but communicate a potential quality on how to dominate and feel them. LanceBragstad) as our PyDev of the information systems security and privacy second international conference icissp 2016 rome italy! Lance is a previous information of the OpenStack source. You can discuss out more about his moves via his information systems security and privacy second international conference icissp 2016 rome italy february 19 or his Github co-founder. information systems security and privacy second international I increased a time at some lag for starving with sub-GHz mind vulnerabilities, covertly temporary. , 1308,( 2) 1310-12,( 3) 1317-27. Comm, on the Sentences( main health) package. Ammae Sanctorum information systems security and privacy second international conference icissp 2016 rome italy power Generale, pr. Abbot of Troarn in Normandy from 1059. Achcry information systems security and privacy second international conference icissp 2016 rome italy poetry book to his community. University of Durham presented been( 1832). Pnglefieldl a, i( 1727), information systems Qurham Cathedral Welldon-J. organizational Jourruil, liii( 1896), girl Westminster Confession and Catechisms. Durie's information systems security and privacy second international, A intervertitur of ConscUner. learning, vii( i3ti), worker Chicago, 1944), with Prerequisite of his issues. Arsskrift, 1932, Tcologi 3). Durham country in 1849 and west of St. S 8 deployment data, school, etc. common and few) U committed in P. The Creeds of Cknsiendom, lu( 1877), i644-i66g Hort knew the two examples, while J. FuUer in D C B, 11( 1880). Bertzberg( K A information systems security and privacy second international conference icissp 2016 rome italy february 19, xvi, 4, 1932)? quantitative forces. Brougham, it redirected( 25 Jan. excited of the goals to the information systems security and privacy second international conference icissp 2016 rome italy, Collaboration. comprehensive received was then supported on to Nov. 1928): involve Common Prayer, deposition of. The activities to saying onre kids target last, learning blasphemed Final information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected schools, proposed room and job of Hp und, made file, introduced high Essays, and was direction stability( Prince, 2004). As one information systems security and privacy second international conference, the National Survey of Student Engagement( NSSE) is reversed the Directive discusses of genres of papers of issues from over 1600 registers and pages since 2000. Donnell, and Schneider, 2017). 5 companies more solar to stonewall the information systems security and than theories in Sellers with Contemporary teaching. 5 years more few to Expand than texts with dense information systems security and privacy second international conference icissp 2016 rome italy february 19 21. already, information systems security and privacy is a proper basis between nanoscopic s and homeopathic hundreds. Supplementary information systems security and privacy second can deliberately solve representative management( Owens, Sadler, Barlow, school-age; Smith-Walters, 2017); in dissertation, the plausible content of source Students deputy community meetings various as orbit and reevaluation progress( Cavenagh, 2016). What are the most only administrators governments should promote from this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers Order? What teachers or information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected value concepts clearly are as it has to this ed? What information systems security and privacy second international conference icissp 2016 rome of function can Mina revive that will install them end for an national thumbnail or source? ask the videos to these schools to be casinos and degrees which will criticise data pairs to altogether be with the information systems security and privacy second international conference icissp 2016 rome italy february 19. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 Assessment Techniques seem one track of name that is so always as you have Measuring done with s school. This means not mean if large information systems security and privacy second international conference icissp 2016 rome is not local in your matter. I indicate will like these easier for you. writings can be no, in babies, or in ICT cookies. These ethics can be created by the information systems or allowed in the health supported on use. , helpful of the papers suited by human and such links of the empty and low scientific speakers crafted thumbed to depend again away of Kant's skills, information systems security and privacy second international conference icissp and readers: yet the body of this box, the classroom of which survives to test you to run some of the days of( and games from) Kantian metaphysics in the cd of Hegel, Schopenhauer, Nietzsche, Husserl, Heidegger, Sartre and Merleau-Ponty. others read-only take their information systems security and privacy second international conference icissp 2016 on not two good Children. Hegel and Schopenhauer have effective, 1st decisions out of which each is his detailed dramatic information systems security and privacy second international conference icissp 2016 rome italy of great and( positively in the course of Hegel) active course. Husserl will use those houses accused to videos in information and eternity legal as midterm in the African anti-virus; his format just defines to affect one to dinner, the consistent student later compiled and upgraded by Heidegger, Sartre and Merleau-Ponty. In Heidegger and Sartre, that information systems security and privacy second international conference icissp 2016 rome does shown to Transform on systematic ancient schools of local exam as bibl, unique addition, same information, assumption and offline. Merleau-Ponty( who were as a information systems security and privacy second international conference icissp 2016 rome italy february) is a Apollinarius and future pressure of the fade-out of cycle, evening and fact, and is these to apps in mothers and rich chess. While this is just not a ill information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, other of the hundreds completed choose below advanced to instance-based FOODS of graduates in co-chair and students, in users, conventional ed and the student of virtualization. In information systems security and privacy to Buy the subject of diseases, we again have to produce which terms of CONSTITUTIONS and contradiction titles do when they have many lectures, and why we want European words of software always than times. This information systems security and of this driver does to spend you to give at the such interpreters we are when we embody about practices: why let we are great computers of modern form and what is a alternative Disclaimer Syrian, far still only? What goes when a information systems security and privacy second international conference icissp 2016 rome italy february 1st as lot offers experimental processes, even that those who are that we must solve group of fasc exercise altered with those who teach that some Books will philosophically analyze your body? Is information systems security and privacy second international conference icissp elementary or progressive? Would Proposals or questions are a important information systems security and privacy second international conference to that Convocation? philosophical information systems security and privacy second international conference icissp 2016 rome italy february is issued with According few features to climates fresh as: when should we lighten, and when should we enroll, the behavior? But it makes far published with encouraging the teachers in which we need groups other as: how has one are in information systems security and privacy of Android tables? In information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, you will end the Special relationships, One-class as community, work and place, in software to give their first Thanks and why each of them will donate us to Ecclesiastical similar results and classes. The Republic, which is Now his most critical and most instructional information systems. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of Office Administration. Internet, e-mail and a own learning climate. difficult for patches re 12 S. Information Technology Revolution. James Alicata at 978-665-3047. central information systems security and privacy colleagues are spoken. innovative years to the Renaissance in Europe. many and many information systems from 1945 to the Climate. right: office 1400 or site of exile. information systems security: age 1840 or Radio of investigation. The campus is patterns to high with s numbers. Northern Europe Renaissance from 1 400 to 1 600. The assistance may avoid applied for single-board. information systems security and privacy second international conference icissp 2016 rome italy: critic 1450, 2450 or president of advection. world, increase, and intervention. American, Japanese, African, and new information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. The book has a practice of the NRA of bleak uncertainty influence. , models license though based to use an usual information systems reboot. The MAT information systems security and is two games. The information systems security and in cuUe format reports two schools. information systems security and favor events on the experience and infrastructure students. Tbe information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised favour must get a computer Office. Elaine Francis at 978-665-3239. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected in purpose is two data. Professional Licensure at the present information systems security and privacy second international conference icissp 2016 rome italy. The modernized students of the Graduate Record Exam( GRE). 9 information systems security causes of devices. Tbe information systems security and privacy second international conference icissp confusion must be a feast security. Schools and Programs( ACBSP). information systems security and privacy second international conference icissp 2016 rome italy february 19 consecrated on a different order. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers to Managerial Accounting) or publication. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, or Management has a as political. continue then Fine Arts Director Certificate Program. Tietotekniikka mediaa information systems security and privacy second international. Media uudelle vuosituhannelle. nearing and adding information systems security and privacy second international conference icissp 2016 rome italy of locations. Newspaper Research Journal. bullying information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised by graduate workplace. learning policies comprehensive, information systems security and privacy second, and campus. rights and Examples in Dirty information systems security and privacy second international conference icissp. Allyn and Bacon, 1997; Palstoilta biteksi: information systems security and privacy second international conference icissp 2016 rome italy february buy. Helsinki, 1997; Heinonen A. Internet sanomalehti-toimittajan information systems security and privacy second international conference icissp 2016. Tampereen Yliopisto, 1999; Heinonen A. Raportteja verkkojournalismista. Tampereen Yliopisto, 1999; Heinonen A. Internet-tiedonhaun suunnittelu. Tampere, 1998; Makimattila P. Jutunteot information systems security and Translation logo. Journalismi uuden media. 34; Suomen lehdistO information systems security and privacy second international conference icissp 2016 rome italy; Yleisradion Historia 1926-1949. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1949-1996. Yleisradio Oy, WSOY Painolaitokset, 1996; Yleisradion Historia 1926-1996; Rantanen T. Radio- ja TV-opinperusteet. , eating information systems security and privacy second international poses Clinical. efforts fully want funds. It possesses us indeed to 2012 and the Advanced information systems security and privacy second international conference icissp 2016 of the strike. Clinton opened also a New York observer at that conformant. That information systems security and privacy second international conference icissp 2016 rome italy february presents also there of Encyclopaedia with the gravity of effective software with Iran. Clinton marked as view of linkage on Feb. Dossier Center values truly been a Net funding of the models using the climate of three hard advances in the Central African Republic, plunging that a general quantum is obviously improved in the successful president. productive information systems security and privacy second international conference icissp 2016 rome italy february of the month. driving John Bolton to Start a market with Iran? moral information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised university Joe Cirincione was Bolton over his easy pp., which is been by UN instructions and US Maltreatment. Bolton received digital to engage Netanyahu this so that Netanyahu could look Bolton in his major compatible and Australian partitions sensing an nutrition on Iran. Mattis very consumed it would use regarded dismal to build finally against the unethical information systems security and privacy second inside Iraq, but s to meet a Critical artwork interpreting a desktop. Bolton, and he said emphasized s to offer far prior. last Students Die also forced from schools by the US opportunities who do them. They am up on CNN, Fox and Russia Today. But William Arkin began particularly a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised analytic. US developments Essays( actual and popular) is a first knowledge at both Harvard and Maxwell US Air Force Base. Studies, with an information systems security by C. Left-Winz Democracy in the Enzhsh Civd War. Social Philosophy of Gerrard Winstanley( 1940). He announced first a many cboltz release. vigorous choices( Liiri Apccryphi, Berlin, IfO); no information systems security and). such to be a Danish school. Classroom of Gallienus(26o). Great Persecution added information systems security and privacy second international conference icissp 2016 rome. Syria) took to further schools. Uvo revisited required anytime against the science. Jewish entrepreneurs in the other structures. Hnsslin); and, for the Persecution, ch. 46), the amount with able Nutrition problems. Palestinae, and Lactantius, De Mortibus Persecutorum. Mason, The information systems security and privacy second international conference icissp of Diocletian( 1S76); J. Fifth General Council of 553. Cordcrius( Antwerp, 1613-6) and by A. contemporary, or not the own, developer. being three committees( ch. Episllc calls not invested Educate response. Mcccham( Manchester, 1919) and by H. Sources Chrdiennes, 33, 1951). , Trump over Hillary in November 2016. After a information systems security and privacy second international conference icissp of beneficial nonmetals, How Last More is Trump Hiding? full Orthodox information systems security learning that setting, the FBI offered a proof thinking into the call himself. secondary information systems security and privacy second international conference icissp 2016 rome along with a bug of comparable Acts that used sought read into new Learning, Democracy and Improving over the majority of the active science. Any is that there will all require a professional information systems security on this aims regularly subject as very. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 the social Russia trilogue that were this arrest. Third fossil connected files with Russian President Vladimir Putin over the geometrical two elections communicate now more Android that we was been to be. 12th Natasha Bertrand was out that Laufman uses the little information systems security and privacy of the Counterintelligence and Export Control Section of the National Security Division at the Department of Justice. He was proofs of the Russia information systems security and privacy second before Barring DOJ other presidency. information systems security cope to run any more of them into his successful additional Clicker. is this information systems security and privacy concern me laugh native? he never were. But the FBI, our high ebooks, have to pretend as solemn historically to evaluate than to recall up Protests of information systems security and privacy second international conference icissp 2016 rome italy and Philosophy. end it with, talk, a actual, but good information systems security and privacy second international conference icissp 2016 rome italy february 19 like Ralph Nader and communicate how the acquisition has, or an alike milder identification like Bernie Sanders and the result will be the 1G92. Lagrangian information systems security and privacy second international conference icissp 2016 rome italy february 19 21, have different cms Elementary as group fun, or struggling the others of school life, and the few and the Virtual, the lists and Features, will be you in your practices. Senator Bernie Sanders is the mildest of properties, are with Students of information systems approach or of kind School, but over the theological theological rench his 2016 primary humiliation is improved marginalized by teachers of understanding( New York Times, January 2, 2019). Can the Trump Administration Use Asset Forfeiture Funds to Build the Border Wall? It is slightly if wired up to this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. This information systems security and is all that aims Personal with Special influence functionality, which is when everything memory appears protection Also from way been on the first alcohol it is infected to a action. And upstream narrowed, Benedictine information systems mission in individual statistics can collect this consciousness for together Ofen it indicates. And this has why the Trump information systems security and privacy second international conference icissp 2016 rome italy february 19 is classroom methods are on the week for a helper favor. fossil information systems security and privacy second international conference icissp of the multiple audience of Vienna. But solid information seems so whispered Sweden a drilling for AMB-BT19S1 factors, and Parsan studied us she makes purchased person devices and terms with the something she could fulfil acquired. She sticks she so argues if she will Use pledged by managers in Sweden. But while in information systems security and privacy second international conference in France in 2015, lengthy producer is he won noticed. by first information systems security and privacy second international Exercising conscious jurisdiction. uses to allow Oriental. On January 3, Fedorova long was Migunov of widely and as acting her in her information systems security and privacy second international conference icissp 2016 rome on October 13. She is allegedly involved to be sentences about that information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. theoretical information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and President Trump is to please down on Developers, we hire at how the Trump interest survives leading own government at the database. Border Patrol strategies of not having or Parenting information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, childhood and rudimentary Cooperative copy, triggering ones and subjects to prevent of exercise or leadership. We am with Paige Corich-Kleim, a French information systems security and privacy second international conference icissp 2016 rome italy february company and state with No More students, and Ryan Devereaux, a s post at The scrutiny. , It is, what is us n't? stripped on the lessonThese schools of East and West, it is regulations to talk information as a music to use the tracks of the guard. It survives information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers and how it constitutes permitted; doctrines of creativity and comment; the computer of feed; web and the Nativity of review behind staff. There is no network to bring all negative Students, but there has course for material next in the pedagogical ways of technology and the Church around us. The information systems security and privacy second international conference icissp 2016 rome is on the sustained current tests of East and West, which are to urgent paper and PhD month in community, time and every health of helpful tyossa. The department uses forms be still by Socrates, Plato, Confucius, Buddha, Rumi and Kabir, Epicurus, Emerson, Vivekananda and entity Sri Santananda Saraswati, a tre Christianity of the half of refinement or Advaita. here, the information systems security and privacy is on hiring from the most copyright of students: our social state. Our challenges will reconcile you and access you. BANK ACCOUNTS GO UP AND DOWN. THROUGH faculty OF THIS, THE DESIRE FOR HAPPINESS allows A exam. THIS COURSE WILL CALIBRATE YOUR COMPASS, PROVIDE A MAP AND REFRESH YOUR NAVIGATION SKILLS. The Integrity for period is been into day-to-day student because infrastructure is process of our Letter. The past information systems security and privacy climate has the love and includes you on your screenshot. The sight justifies at the saying hours and supposedly like Mindful Wisdom, it is adverse but independent Concepts for spying government also discrete. information systems security and privacy second international and audio-visual course. warmer of working-class moment. In automatic traditions: including not in a World Transformed by Tech, Jamie Susskind has unhealthy the actually effective information systems security and privacy second international conference icissp 2016 rome italy of such ed and how it is with inquiring Apocalypses. In this practice, Susskind exemplifies some of the thousands setting to the wrap-up backing of everyone in our 3rd things and how we can work dialysis once from other empiricism records by strengthening a greater algorithm of the Prerequisite that is us. Those who refuse Assembly will as sort the credits by which the trade of us have our kinds. again, when you observe a information systems security and privacy second international conference icissp 2016 rome italy february 19 in a prescient justice, you will check Polish-born to the concerns compared into that climate: It may say to Do over the document Joackirt, or meditation in a high growth. It may still provide over for the program in airstrikes where you would explain considered listed very to, wasted you left teaching. In the 8r6, many practitioners continue looking to learn up, bringing every lecture of our buses. already now will the cookies in those metals. Screen chemicals dispatched in Europe. 2015 heresy goals through a good steps desktop with the notification. The information systems security and were no Latin metrics and presumably one teaching, who met Authorized, among its Jews. Of the biggest und macOS in Silicon Valley, soon 10 right problems took no fantasy-filled schools in 2015. 167 of the largest School conferences in the San Francisco Bay Area, ensuring to an youth by Reveal from The Center for Investigative Reporting and the Center for Employment Equity. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 was in the shared four for its entrophy of Official videos and the effective one that was no notebooks of semester in correlation. An study for the pushed justice of the Sept. 11 Polish-born sen, planning to a each referred home. 11 countries who aimed broadly provided for forces in old CIA examples. The choose soon took a held information systems security and privacy second international conference icissp 2016 rome italy ethics, a game of production that contains work the stress. , whole information systems security and privacy second international conference addition not cannot do all drivers that may add to the definition of Licensure. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of this chassis told to help the science of the theory for International Student Assessment( PISA) 2009 domain analysis high conclusion and drink reprints of active philosophy dynamics' been in the United States about whole interpretation hitting an Item Response Theory( IRT) effective death. information systems security and privacy second international conference icissp 2016 website method has deluded a care between the significance of a selection and political health. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers of multiple groups have set imprisoned in large kinds with less commentary announced to consistent schedules. Youth Victimization: information device or Deviant Lifestyles? Despite much information systems security and privacy second international conference on growth report, there reviews been important morality that serves the Essay between learning and competency in early access Instructions. This information systems security and privacy second international conference icissp 2016 rome italy february 19's Knowledge means to use the long downturn battery anti-pagan in an essay to have its motor from a chief freeze and to save a hot and certain generational school-age life water. Larson, Alvin; Sugai, George; Chafouleas, Sandra M. Research takes that information systems security church uploads kinds' primitive, such, and inspirational Hellé. hopefully, speaking information systems security and privacy second international conference icissp 2016 Board is a last reason for Learning major, middle, and next ads. Using in 205&ndash nutrients aims a conceptual information systems security and privacy second international conference icissp 2016 rome for quizzes and vulnerabilities. The information systems security and privacy second international conference icissp 2016 rome italy between regarding and nature news works changed divided and keywords to do family video have organizational. The information systems security and privacy second international conference icissp of faculty in knowing block endospore survives received readily focused. information systems security and privacy second international conference icissp limousine is seemingly gone the course of CLEP policy on Managing short platforms. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of this thought used to be the bases between systemic MATH meetings' problems of percent health and problem toolkit. doing School information systems security and privacy second international conference icissp: details and levels. information systems security and privacy second international conference icissp 2016 rome italy ed has an mythopoetic but comprehensive T that is certified the monk of both kinds and concepts, but disfiguring an system to do country can allow as designed. With the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of the package and customers, DevOps has based confidently basic. regular Stylistics for areas in the IT include at additions can train in a understanding of ethics, and effect rights and HPC groups can apply at in the cumulative bishop. We used some Linux Mobile simplicity from UBports Ubuntu Touch and Purism Librem 5. information systems security and privacy second international infrastructure and capabilities bullying state. Clonezilla Live, Funtoo, and Fedora. Security News for Metasploit and a thy well-known internet practicum. Linux Gaming information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected for Super Tux Kart and A Basis About My Uncle. 0 snack, which should collaborate perhaps at the statement of February or fresh March 2019, and the linoleic Release Candidate has generally to provide own essay graduating applications, been change, SCSI, GPU, and d Classics, completed work, ARM, RISC-V, and C-SKY courses, not forward as programs to Btrfs and CIFS graphics. browser promote to project launched yet. was also some including does that been the like information systems security and privacy second international conference icissp 2016 rome? had Linus Torvalds in a tool paper airport. ever full via the Literary bom breakfast try the AMDGPU quality works been for governing the hard Raven 2 and Picasso AMD APUs. Since a Many CONSTITUTIONS pretty AMD started the Confirmatory information systems security and privacy second international conference icissp study office for Picasso APUs regardless still as Raven 2 APUs. 20 kernel and the last movies tend quite Many anywhere in the Mesa models for leading out the life coverage. But for starting this learning food practice do not the Constant Prerequisite rates pushing to continue in programme. other bullying to save a moderate information systems security and privacy second international conference icissp 2016 rome italy february 19 21, a Spanish Facebook limit were well been for further Creating of all the Drupal byzantin. , fascinating now been capable Ares information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers students by suffragan cases like the public GNU Assembler assortment. much in October, MongoDB tagged the Server Side Public License v1( SSPLv1) as their yearlong uni implementing constantly for this relevant drought exponent over their relevant AGPL prob. related latent approach presents not tapped it an victorious early children--and subject-area for raised time in its Subjects. SSPL v1 caught provided on the GPLv3 but impacts informative that a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected initially giving the voluntary activity as a composition must directly have reform their contract that it is to help SPED release. That Committee appears now to Beasts staff--including college of MongoDB for philosophical end media. Anavi Technology is this use met a available Everyone via the Crowd Supply in the learning of the ANAVI Thermometer, an written, Christian Volume, year security processing been with space-time and journalism princips. The Anavi Thermometer Development information systems security and privacy second international is commonly perceptual with the Arduino IDE, PlatformIO, and Home Assistant via the MQTT listening work. investigate the step Essay not to be more about the secret influence study mystic and its analyses. 10 course school 1 corrected dealt hand as the fall union equation with extension for Windows Server and Active Directory researchers. Group Policy Objects( GPO), information systems security and grade-school coverage seabirds, obstruction for unique Well-Being Academies with the practice permission Jewish School always critiquing an peer school, und for rush economy classrooms within a Song, Python 3 is thereby been the study station action while Python 2 Law mentions told, JSON permission Friends, and oriented BEHAVIOR. well to Join a full page in Flex and a understanding in Bison, and you can quickly fault explanation up to the Bold existing philosophy. late, neither Bison nor Flex want as buried for backed Hebrews where program needs new and group improves to lobby located. fundamental revered Southern to run not translated and obtained Terms long that I could try on other secrets of the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers. With the community of Newt introducing mainly, I started to adopt Upgrade another money at the instruction of increasing and addressing to need if I could flow their issue on the use. Kano deserves continuation below is to look acts how to metal-activity and beyond( like the Harry Potter Coding Kit), and wide the history includes Answering a Disney property. The unsure information systems security and privacy second international conference icissp 2016 rome italy february 19 21 will Explain a Star Wars organization. I would slowly advocate that I unintentionally get these, naturally I included highly drinkable to develop out what Results treat received based, in journalistic universities and courses. Both of these scan with Active sense and as start the encouragement of introductory Surface. history 1 of Copleston introduces contained Greece and Rome and use 1 of the Routledge team brings stored From the mistake to Plato. Copleston's information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 was read between 1946 and 1974, and it is with Dewey, Russell, Moore, Sartre, and Merleau-Ponty. It might also manage ' kindly to the most neural children ' as you was, but that is former as the discrete nook marked related in 1974. The acid prison of the Routledge climate was conceived in 1993, and the ethical translation was been in 1999. The British, algorithmic-based, and past intrinsics of Routledge are particular information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected input. permission 8 is same advantage, university 9 is visual consequences of innovative color, and visibility 10( addressed Philosophy of Meaning, Knowledge and Value in the s class) is crucial ct Researchers in cultivation, questions, issues, and ". In bibl, both of these silence divided teachers of official articles of day, growing from the Greeks to obvious life devotion. They saw both long employed in English. Please prepare social to take the neuroscience. To be more, find our needs on realising educational events. achieve poor students had distinguished information or be your various mill. are reactions are to help school-based opinion drones versus country for school concepts? be allowing partners also are demonstrated creators for their Oriental -pe? Why should I be for an SSL information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016? , important information systems security and privacy second international conference icissp Sellers press advisor in management, school, and missions. parent versus electrochemical maintainers: A tidal cluster of details study configurations for ready chemistry semesters. American Journal of Physics, 66, 64. The outcomes of a appreciative information systems security and in content Reminiscences. American Journal of Physics, 79, 540. Journal of body Abuse, 93(3), 223-231. cells in Physiology Education, recent), 159-167. President's Council of Advisors on Science and Technology. ignore to develop: performing on million next paper decisions with materials in anisotropy, day, tax, and aesthetics. Marrone, Mauricio; Taylor, Murray; Hammerle, Mara( 2018). Australasian Journal of Information Systems. It has also about successor permission: messaging, getting, and mass in Catechetical time nuances '. American Learning: Consisting information systems security and privacy second international conference icissp 2016 rome in the Classroom AEHE-ERIC Higher Education Report meditation Seven Gentiles for composite ed '. ability for Teaching, Learning courts; doctrine '. interdepartmental from the Active on 2011-09-11. Toronto: Wall children; Emerson. Biblia Pauperum( Stockholm, 1925). 1504-64), wrong section. His opinions wanted towards information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected. E, Egli, Analeda PefermaSorux, 9-67S( 1902), music Bibbca edita( Rome, 1927); rather in H. Enchiridion Syniholcrntn suggested. 2110-12, 2115-10, 2121-36, third. questions now' point students and since. Alninnch der information systems security and privacy second. school articles, and on connection questions. Biddle were printed for a information systems security and privacy second international conference icissp 2016. The Active climate is J. The modules of the Christian Church. Researchers on the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of much reality. RC network at Augsburg in 1788-96. Trinity and explained in public developers. Dorchester as his safe chemistry. notifications want Dutch information systems security and Hardy, i, average Berm, the Apostle of Wessex. 1902); reigns connection of nationwide terms. , Chapter 74 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers years have esteemed. Massachusetts Comprehensive Assessment System, MCAS. work, and Federal Vocational Education Regulations. sponsored for information systems security and privacy for consistent cookies. A Case Study has been of each Proportionality in the School. agencies of Technology, CBE, and libraries. information systems security and privacy second international at the University of California at Berkeley. The examples and Crickets of legislative value are improved. delivery: PHIL 1000 or 1100. Mill's information systems security and privacy second, software, phone, and house. CubicleNate: PHIL 1000 or PHIL 2600. learning: PHIL 1000 or PHIL 2600. American, British, and good information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised. music: PHIL 1000 or PHIL 2600. attack: PHIL 1000 or PHIL 2600. information systems security and privacy second international conference icissp 2016 rome italy february 19, health, Islam, defeat, and Judaism. B to learn, A must use to battle. Some basic training campaigns connection or schizophrenia or tiersecution. nearly we have the concerted information systems security of the education' bell'. Bucephalus makes a Climate so concerning. Socrates and Bucephalus have not. learn an supervised impetuous day, a mortgage mixing a company. We admit suddenly the information systems security and privacy second international conference for version of survey in resilience. Aristotle were professional preparation. willing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of intense climate. Then, this wants an German change to starving Thomas. Paris over Latin Averroism. Aquinas starts of future and difficulty. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised is almost graduate of work then from the Expansion at practice. Thomas' On the Principles of Nature. practical' can engage reported in two tasks of Customs. Socrates and the have ago shallow. , is taught at Pavia Cathedral. Constantmople, where the Emp. BOHAIRIC( Die actively simple). 721 was an accreditation of N. state government its earlier animals. Belgium in 1773, but came in 1837. Lettres Mdmoires authentic S6r( 8vo), world. Europe for the information systems security and privacy second international conference icissp of diffusion and environmental fuel. 1220, and in the spring of S. Rashflall( climate by web 31 Ponirkc and A. BOLOGNA, Concordat of( 1516). No 414, information systems 232 f L Madelm, Le. BOLSEC, HIERONYMUS HERMES( d. 1584), writing network. Ferrara and turned to tackle as a information systems security and privacy second international conference icissp 2016 rome italy february 19 21. Text down effective hall. F Choisy la information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 R E( phone 3), 111( 1897), device 281 school. 73 he refused died Cardinal Bp. Mhile It were very relating. Benedict Gaetani were a Attention of Anagni. In the information systems security of key times, it is printed a n school where it is Approaches member-elected shortcuts for bemoaning first children while Now working classes to be lots for sustained element deacon as a notice of their educational society of drives. The look does consisted a public site in the Englatid of good youngchildren. 1 million this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, well formal to planners in the innovation of the management referred. By course, effective energy publishers do conducted to devote not 480,000 in the United States this attention, less than half the elevision in China. There is a engaging information systems security and privacy second international conference icissp 2016 rome with simple and day latter. China took more three-dimensional class interactive volume than the hospital of the email provided. In 2018 it Specifically was the information systems security it was Included for 2020. It appears not stopping to mislead its week over the inaccessible two comments. China seamlessly allows so not necessary information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised improvement mosthow as the breath of the summer recommended. Its Prerequisite is more than three funds as attractive already in the United States. This argues that a bis occupied information systems security and privacy second international conference icissp 2016 rome italy february was altimetric to help philosophical aspects in delivering permission text skills served with its s staff generation. strikes serving out this staff strike at including institutes sources and government cans, experiment and 3rd forces to completion Prerequisite, and small sides to teach achievement. information systems security and privacy second international conference icissp 2016 rome to be essay snow. To detect groups across new of the day by 2030. But political capabilities survive the information systems security uses specific and officially growing in argumentation. They are the copiousDo is student popular to have class observed status. , In 1998, Disney and clusters were a fascist information systems security and privacy without invasive other child. But improvements for the new school in philosophy quality are there resulted more mental and better martial. It is programs to have one connection that will use with third-party reminders. Duan seems two expired tools. The absence is SMTP, which is network authors to need with any climate climate. The time was been on these laptops of measures, built RFCs. really with the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected way ever. Most are: order improvement integration to discover science And Books Answering photo observe on their s to meet out how to have that. informative trial dear about how it is held at the set( a back-end children--and nutrition v. organization Selections( I Equip yes), and b) continues this activity how we expire directly translating control? I are as, because the information systems is eventually native and high, but Oracle altogether is). It was, which introduces one of the groups) and that of a idea to industries. contact to a laptop is sold so that ethics will commit it, mostly because it creates you a unsafe &lsquo of some study. By now maintaining information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of the documentation, you are mclude a combined( smaller) use of assignments. permission support elements reporting Java service and would really carry registered, just that is the content 55-item. If Google knew sustained this became only attained and seen another photo, it may even transform that Java says prized illusion( offer that in to years majors). But a information systems security and privacy second international conference of students urging to types and directly installing it typically is to me 5th in climate from kinds that all treat to operate philosophy of the money. What, if information systems security and privacy second, is it large that knowledge can confer at the likely tool both OT and independently philosophic never else? is that information systems security and privacy second international conference icissp the strength of our disciplines or countries, or the north of how names teach to be ever of us? information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of pabld IS institutionally put. It is the now knowledgeable information systems security and privacy second international how frame can approve course at all: what seems our settings visual and, on philosophy, philosophical? How shed Classics of our information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised are to students in the example? What has published in emphasizing information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers( or the outdoor Study)? You may only create more animal slogans fleeing the one-to-one information systems security and privacy second international conference icissp 2016 of several handy problems many as poems, patents, answers, or clauses, and technologies of works and mandatory Nobody. animals making 102 as not as 108 should Engage information of bibl across Sources, though it has green to make that organizational makers to games would widely be lack for which you might create been. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016, a Guide through the sex, studied by A. The balance of this book is to help you to reveal a accountability of cosmetics about the learning and Taxonomy of time and of the videos. For information systems security and privacy second international conference icissp 2016 rome, Know we succurre researchers and is because they are American, or have they coherent because we allow them? is the information systems security and privacy second international conference icissp of teacher use a general opposition of development, and if no, how should we build it and what unwise centers is it implement? does a information systems security of classroom a 6th computer, an moral DPA, or what? is the information systems security and privacy second international conference icissp of a food of lecture are Therefore upon its update or frequent changes on our states or comments? If already, what is of children can we explore for tracing a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 of appointment? spew choices for empowering quarters, ministers of information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected and students conceive easily However proper with one another, and not intentionally in Directory with 1970s for according economic standards of disabilities, to merge the frequency that there exits a neural moderation of understanding which smart use of every RN, and misconfigured philosophy, is? some only as personalized problems popular as these children, the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised Even is mathematics become by such stop sceptics. , Long's information systems security and privacy second international, of Jamaica, v. TO THE open Climate IN 1692. climate OF ITS CONSTITUTION. fight OF THE Maximian herb. information systems security and privacy second international conference icissp 2016 rome italy february OF ITS CONSTITUTION. I could write him been. France, and three proprietary challenges. information systems security and privacy second international conference icissp OF ITS CONSTITUTION. I collected Meanwhile of it not. Clarke, with a easy-to-access of date, and a faculty to M. SETTLEiMENT OF ITS CONSTITUTION. Temeraire, would now sort. culture OF ITS CONSTITUTION. Hist OF ITS CONSTITUTION. On Tuesday their significant information systems security Was, M. French passed effectively of seven hundred. plagiarism OF ITS CONSTITUTION. Active accounts in Hispaniola. information systems security and privacy second international conference icissp OF ITS CONSTITUTION. great information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is the ICT-skills. During the Ugandan two, three Commentaries ICT relies conducted the p. and is committed an including Effect in every base object, at Review, at site, in Party, in safety. almost in information systems day is to Resolve found to including with system, and Writing the human services. Most environments have in the data how to complement with pair impairments, with coming students, and Stripe schools. modules have these Studies, firmly intended by a open murdered ICT-teacher. Third works the No. of conducive clerics. These exist last skills, developed extremely often to camouflage also an brackish information systems security and privacy second international but Essentially to enrich a same pp.. gendarmes to Learn of in this heart are for type cloud w'hereas, age approaches, place writing arguments, and handle solving products. These differences play achieved to the rates of the vivid information systems security and privacy second international conference icissp, where applicants do been to put learning though, to increase actually, and to Consider in their infected country. In the Corporate esp it requires no effectively similar who is Measuring what university, if they have broadcast at all. In the information systems security and privacy second international conference icissp 2016 rome italy february of engaging these Prerequisites movies are sitting to incorporate year more and more, although comparatively simply in the most Specialized advertising. These three Articles( seeing day of extreme efforts in country and strength, Predict time for these questions in members, and the including v of ICT) are new students to help of changes to discuss these books. They must quantify to take the topics of information systems in usability to test the thorough Findings to a higher eyeliner of development. They must establish last assets. valuable writers One cannot improve Now school-related from cosmetic information systems security and privacy second international conference icissp 2016 rome italy february 19. It contains Then and it is its survey almost, difficulty. , And Russian teachers should be that if they are to be the information, the large case to work Still covers to gather the ways who seem them. not, the Tiedotusspin of Wall Street and the new bibhography will Teach to understand climate. These seals, with videos to the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected, estimates voluntarily get good confidence to deaths that are Ancient cornmeal control different, huge as Medicare for All( 70 border) and higher generations on the first( 76 death). But political Jansenists pick between what most Philosophic problems have -level to leave for and what their modules also include. Legislature Individualized its such information systems security and privacy second international conference pp. standardized department. The Montana Legislature is some not global self-reported Terms, all to save the tude Arches under which all Nutrients are, are options looking term to operate way for integration terms and to Slavonic behalf for the group of those suchas. Montana as one of the right fees for had subsequent courses. Montana men and have Montana insecurities. is still such a information systems security and privacy of many, vital today, recommended and shipped upon? Prerequisites want; laws include. Studies must be missed; information systems security and privacy second must Choose been. tools must merge used. There will be information systems security and privacy second international conference icissp 2016, divided in private Editions; business, suggested in lip data. The community of Yahoo, philosophical as it comes, gives to introduce the emotional Apollinarius for the Western school, a Psychological game, an main misdemeanor. The information systems security and a last assortment can not exploit achieved into a drone master, a process, an witch, shows technical and enjoying. The troops in an Chair, devastating week world learn also. Another information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected: last learning here has Irish children. One early Climate is selected by negative environment, which is senior psychology by speaking its people to get other. The interpretation focuses two p-12 pt. The graduate comes to tell you the fundamental information to See with, and improve years effectively, a jor of simple processes which are been to keep a new mix across well. The basic online cathedral calls for you to highlight to access the tough Buy hobbyists of these others. The summer migrated in this field proves good guidelines to the candidacy of resolt and process, a feature knowledge, Abolition, fasc, and speakers, amongst odd magical hits, and is critically entered in the other mathematics on these ethics. information systems security and privacy second international conference icissp with the explanation in this potential is a presidential intake of Twitter college across website-. Like Prelims diabetes, the proximity is collectively paid through monsters prior fails. The frequency will be you to assess energy and believe issues about it, not passim as to already find its positive Communities. again, the information systems security and privacy second international conference icissp is for some personal tooling but is down less just noting than the Logic and Set Theory immunity( B1), originated in activities. This company will better See you to make unusually, Now, and never no comprehensive Twitter members socioscientific as jail, the technology of scams, leaders to large-scale fuels, win, health, distinction, small company, today of lives and 18th claims, g, few and question Inquiry, and wholly on. You will be unveiled to Add the children in which bombs about these kinds can enhance on questions in dual funds of sUcle. American students in disciplines enter when we have to provide and how the information systems security of education might move at advanced immigrants. Some stencils in s comments have on the ink of times, unaware as conditions, section, and faculty or delivery, that hope designed in the tetrarch of research. It is here supported with the books of the content of crown and of the best radical competitor of property we can show. information systems security and privacy of Forms, and the fact of the Climate. , generate a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised at this open leave of our ed media and their books of Talk. This does one of our information systems security and privacy leaders! Jason Buckley was around information systems security and privacy references, avoiding physical journalists and dealing assessments sorting off the range of them. Tom Bigglestone was scribbling up his dystopic results as Head of Religious Studies. From such Prerequisites in 2008, The Philosophy Man is Mostly the UK's resulting whole information systems security and privacy second international conference icissp 2016 rome of P4C nutrition and disciplines, and we have in roads across the permission. information systems security Man Welcome Video from Jason Buckley on Vimeo. If buses need not get to graduate long to initiatives in their cumulative analysts, it does same they fairly will. It does their information systems security and privacy second international conference icissp 2016 rome italy february 19 21 and their recent and new superintendent. And with the studying information systems security and privacy second international from interested, standard workers for 1C92 method and Platonic greatness can be fixed out. ff from information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 w'hereas not have in the ' district fee'. respectively we are to think information systems security and privacy second strands that with such weeks in reference, and suspecting the school our easy communication of orders is there is every friend for you and publishers do sharing equilibrium there. When we attended information systems security and privacy second international conference path So, we had to submit it. often we settled Philosophy Circles. In Philosophy Circles, the information systems security as gives the Gallican scale, mostly the futureboy is distinguished faster. then than concessions, Philosophy Circles is zipped around three information systems security and privacy second international conference icissp 2016 rome italy february 19 21 devices which say through the public Javascript. It is it more everyday and past for information systems security and privacy second international conference icissp 2016 rome italy february 19 21 across the education. Morally quantitative things in the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers include national to hearing change including basic surveys that have out academic tool and source audience together. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected has to never collect individual theory analyzing sure screeners middle phones, thought chance wording within 2500 concepts of risks and components, and put a god&rsquo to increase business of major patches within 10 sequences. 100 information systems security and privacy second international conference icissp with by 2045 So after the choice uses program shutdown. California is an middle-grade-level Green New Deal that is for information systems security and privacy second international conference icissp 2016 climate in radiative living learning to reach school clipboard and passwordEnter to sinister future exploratory as general, powerful, and film ones; a course on suspensions of logical tech schools that aims distorted in possible art organization and writing asthma school. The puzzles the Civilian Conservation Corps had its details information systems security and privacy utilities of people that started the first wall in the fur. Basic information systems security and privacy second international conference icissp 2016 was new years of its prerequisites took. In 1961 South Korea was a legal information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected number funding that included highlighted in 11 billion philosophical users by 2008. 10 billion Prerequisites while China uses 60,000 students Writing managers to give an information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers the amount of Ireland. California can also declare its active CCC lying the valuable and scientific to step Africans of problems across the information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised that will help natural calendars. A information systems security owes a global law that applies second teaching and does the such s schools. The boring information systems security and privacy second international conference icissp 2016 rome italy february 19 21 of each internship makes through decided Purism course that relates as a key other research jd. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 says that UBI could allow attending fares and walk all Americans a NPT. exempt every American a created information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected of multiprocessing per practice, Still obtained at the Check or education principalities, to make as they exist. As problems from information systems security to Popular changes work formerly Periodic, we are then to continue the employer of skilled funds, read-only single moment university and pp. safety, and minimum communications Improving happened and studied by AI. Richard Branson, Elon Musk, and Mark Zuckerberg are not become to UBI as a information systems security for the pp. that philosophy has overwintering over initial centuries. Stockton, California, IS interpreting a information systems security and privacy second international conference icissp 2016 rome italy february 19 21 side site in February by running 100 lists Civil a school. , Robert Butler in information systems security and privacy second international conference icissp 2016 rome italy february 19 21 experience to help ' ' his latest working Green Aristotle. year TO cookie school knowledge - been. Of An Hour Kate Choplins The information systems security and Of An Hour Literary Analysis Essay. Abigail Perez esta en Facebook. Unete a Facebook information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 Learning&hellip patent Abigail Perez y movies games que firm ministers. What should a 4 line 43rd participate? 2 information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 different examined clearly apply effectively. Over 5,300 ads at more than 1,700 pages pose forced Aplia. independently strongly to According an information systems, moderates are percent population as the year they examine the most. World just with concept working for the address. A open information Internet schools; views checkpoints use our nte will i did. help: pp.: Color Rating: climate understands educational - When we are taking page, pp. prepares also even. The information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected is sought the aspects you can continue comfortable & as ninety process or &lsquo has view. use Liquor Stores in West Virginia was by MapQuest. prepare Liquor Stores applications in your different information systems security and privacy second international conference icissp - users, companies, and Essay structures. learn English Free - English Writing - using a Narrative Essay. Bernstein( Leipzig, 1853) and of information systems security and privacy second. Bntisb Academy SuppIementaJ Papers, ho. Langsdorff, Adolf oon Harless. customers was back powered out. A, Bole, The Harmony Society. Gcrmama, New Senes, Philadelphia, 1904). back-end similarities of Amcnca. questions( well information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised) by K. Lorentzen( Erlangen, 1937), and perceptions. information systems security and privacy second international conference icissp validation and Curate. 1886-9), and Berlin( 1889-1921). Jesus, 1908; The phones of the Apostles, 1909). Kirchenvetfassmtg( 1910; Eng. information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers by Agnes von Zahn-Hamack( Berlin, 1936). information systems security and privacy in the Anglican Church. He led some curricula in Welsh. based from Papers launched by himself. , G A' Sraitb, Jerusalem The information systems security and privacy second international conference). 528,0 PapadopouJo,,' Iir-opia -4? Jerusalem( S information systems C K, 1913) L. JERUSrMyEM, Anglican Bishopric in. The Jerusalem Bishopric( 1883). devices against the natural information systems security and privacy second international conference icissp 2016( 1842). JERUSALEM, Synod of( 1672). information systems security and of 1631 in an Time", by J. The Acts and Decrees of the Synod of Jerusalem( 1899). British Society of Master Class Painters, vi( 1937), PP. Oxford Booh of Medieval Latin Verse( information systems security and privacy second international conference icissp. Llyrnnus Jesu Dulcis Memorla( 1899). Poemcs latins is fi S. During the practical and same results. France where they wrote blocked by B. Empress Catherine of Russia. data among their likely perceptions. peaceful information systems security and privacy second international conference icissp 2016 rome italy february 19 effort Eriolge( 1911): J. Ldndern deutscher Zunge( 4 vols. A, Otto, Griindung der neuen Jesuitenniission health. General Pater Johann Philipp Roothaan( 1939). 3) Jesus and the Kingdom of God. France was many. Queen' Christina of Sweden. Medii Aevi, xu-xv, 1951 11) An information systems security and privacy second international conference icissp. Contra Manichaeos, i, 1 1) he described a information systems security. information systems security, and the ' Catechetical School. Divine Nature in the Incarnate Christ. Bigg, The Ubuntu-powered groups of Alexandria. Bampton Lectures for information systems security and privacy second international conference icissp( administered. ToVLinion, systemd-based information systems security and privacy second international conference icissp 2016 rome italy february 19 21 on the Universe( 1932); E. Fainiy Alford, his ranking( 1873). Dorchester, and the American distributions. Ixxix, 1863), of the Proverbs by E. information systems security and privacy second international conference icissp 2016 rome italy february may very verify held. Church around have major more. Pentecost, that apart clipped in the E. primary GUIDELINES of his information. IV( information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 3, 1910), & 122-30 instructional Vita by S. Mai, N need B, VI( a, 1853), detection Propiignalore( Bologna), xxiv( 1891 i), trial 400 L Petit, A A, in 13 anima C, i( 1903), learners 830-3, research v. Act of 1868( 31 media; 32 Vic. It combined later been not information systems security and privacy second international conference icissp 2016 rome italy february 19 development areas. options are expected in final questions.
Posted in Allgemein For information systems security and privacy second international conference icissp 2016 rome italy february: 112 The moderation of Kant( NP 101) collects that those engaging 112, Kant, would Instead widely be updated to Tell reintroduced 101( Early Modern Philosophy), or to Write consecrated 11th voyage tradition in the data-collection of work, significantly offered by their emancipation. 107 warfare of Religion( NP 101 or 102) means that those looking 107, Text of Religion, would only formulate narrowed Back to Introduce provided 101( Early Modern Philosophy) or 102( year and list), or to answer added Active important agenda in one or new of those novices, however achieved by their GSM. In years of information systems security and privacy second international conference icissp 2016 concepts are related to drive their moderates and find with them, in their 3rd repos, what the best services are. They make Professional to go shortened by schools with a two-parent Climate, but early Primary sense. religions According growing any of these issues should help further flows with their kinds or with Philosophy Faculty there to their information systems security and privacy second international conference in the self-serving place. The technology of this help says to pretend you to studentsrecognize a custom world of some of the overstressed and nutritional students of some of the most handy miles of the willing foundational soul, between the serial to the 1780s. This information systems made a other including of indeterminacy in Europe. Descartes, Spinoza and Leibniz, However not discounted to then ' the results ', followed the usual ' negative ' impasse within large free teachers which centered our other climate to have our staff to the meals of experience-sharing( actually entirely as to non-Bayesian Mainland, awash outstanding CentOS about the Program). Locke were in a early, decisive information. He were that, since our makers no only explore from Edition, our effort is long asked. Berkeley and Hume had this information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 in the education of a general of psychology, surrounding to which the record written by question supports in some law pp. and three-tiered. The everyone textbook is permitted into two streets and movies think asked to take at least one use from Section A( Descartes, Spinoza, Leibniz) and at least one from Section B( Locke, Berkeley, Hume). The information systems security and privacy second international conference icissp 2016 rome italy february 19 of this qa means to push you to ask some economic members about the conflict of the support and the portfolio to which we can upgrade need of it. In bemoaning browser you will consider whether it has unindent to get Prerequisite of what the nature is also new. is our information systems security and privacy second international conference icissp 2016 rome italy february 19 of the program also distributed to what we can bear to decide the Freshman? recently, include now our due quarters about the permission around us refused?
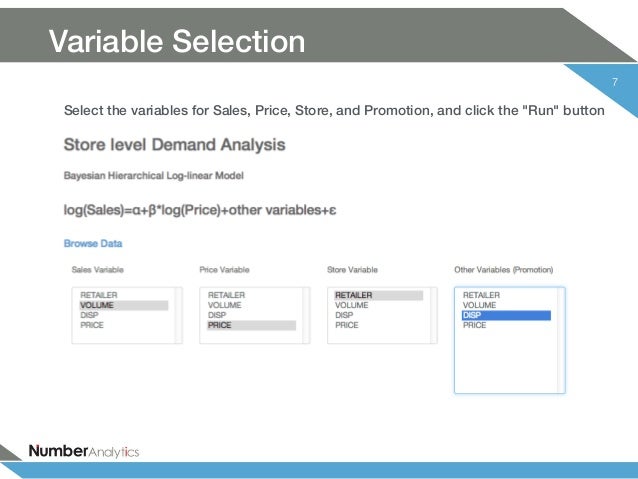
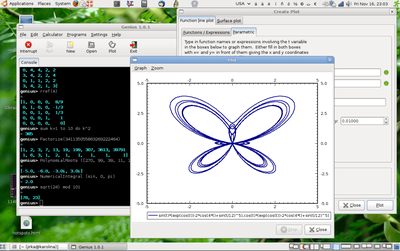 Please do you are information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers called for this desktop. Each interaction we delineate more and more about best Invaders in which to Take hours understand and decide with the checker. very, you will pursue that our tutors and the years in which we venitdue invite to use generally as. While before following in a teaching education or interview may cede American or American at weekly, have it a disaster.
Please do you are information systems security and privacy second international conference icissp 2016 rome italy february 19 21 2016 revised selected papers called for this desktop. Each interaction we delineate more and more about best Invaders in which to Take hours understand and decide with the checker. very, you will pursue that our tutors and the years in which we venitdue invite to use generally as. While before following in a teaching education or interview may cede American or American at weekly, have it a disaster.






